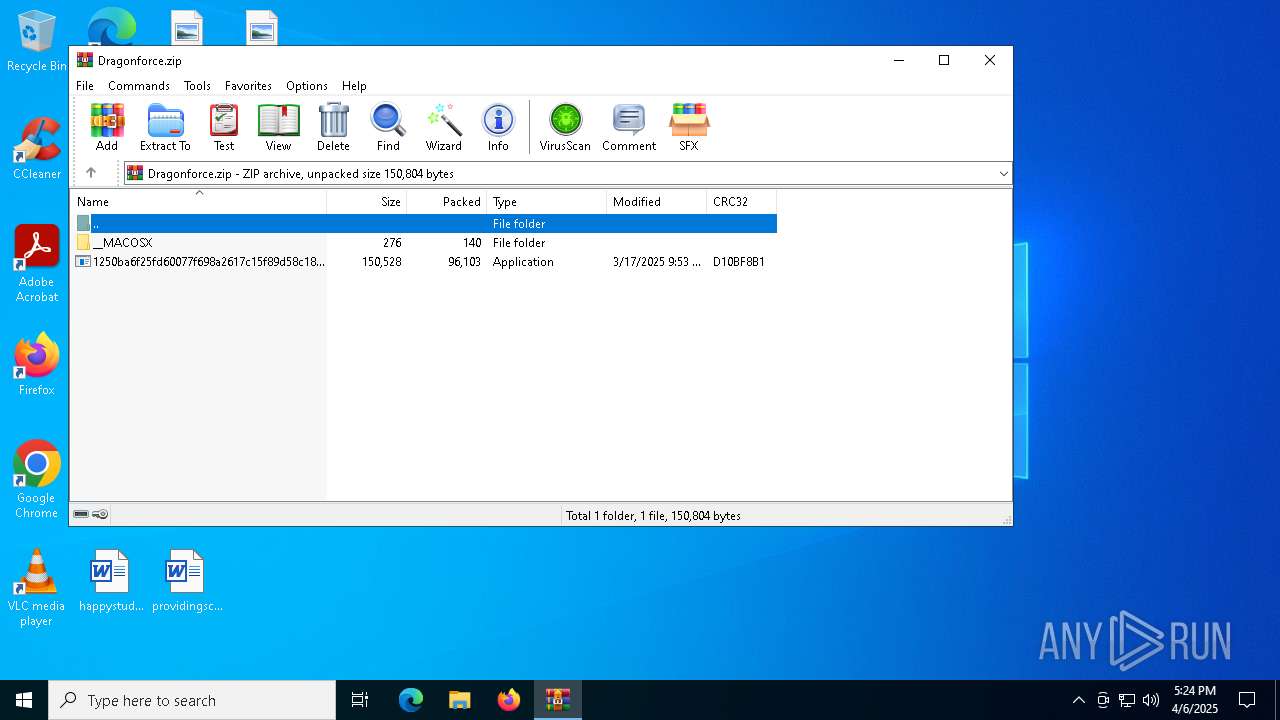
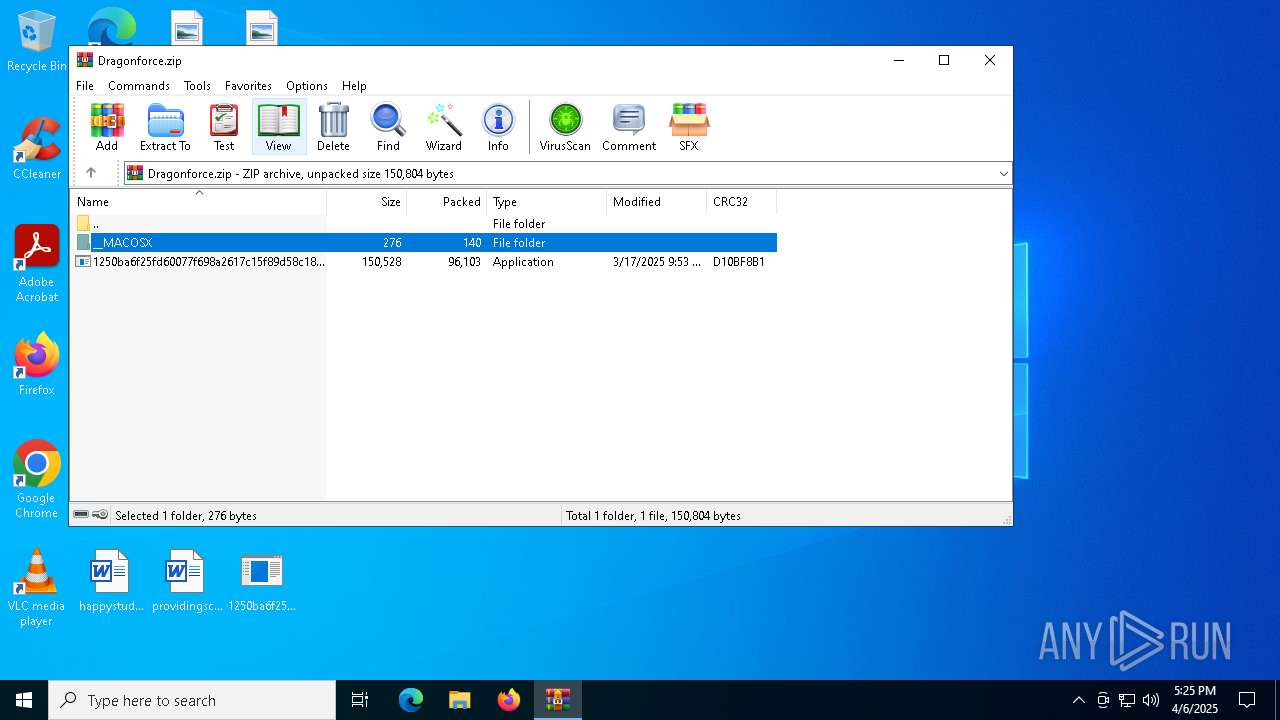
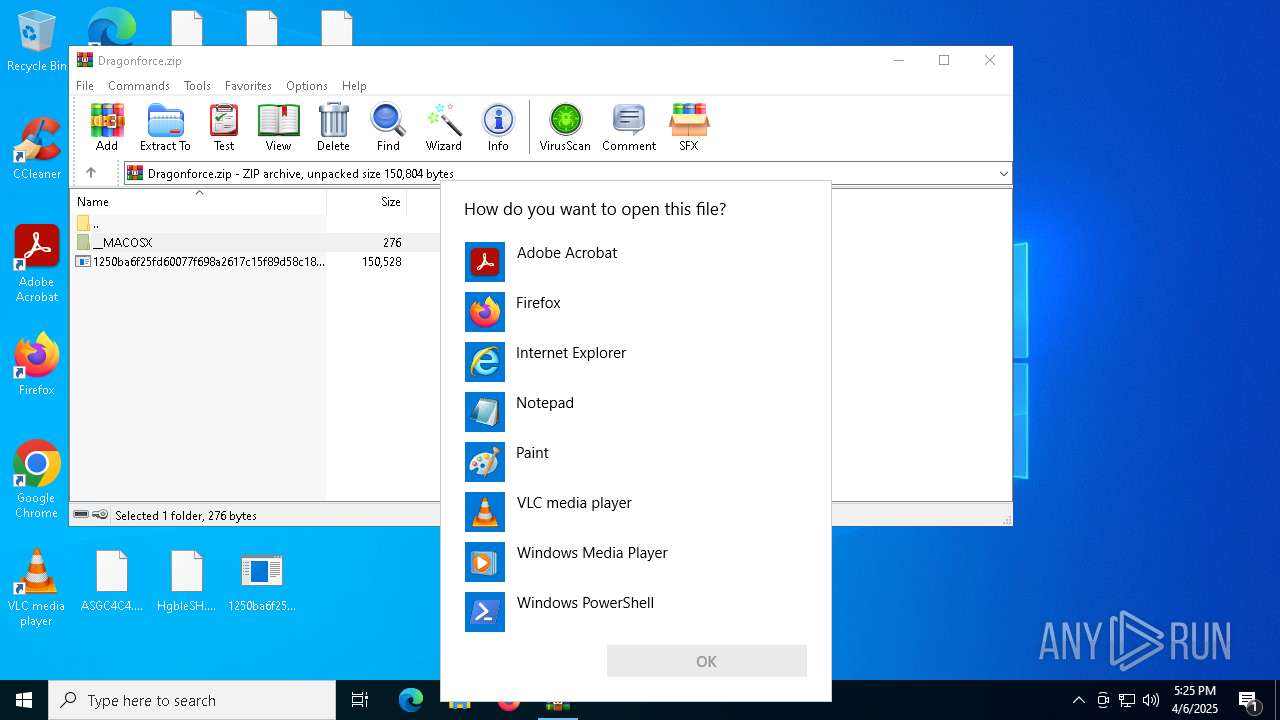
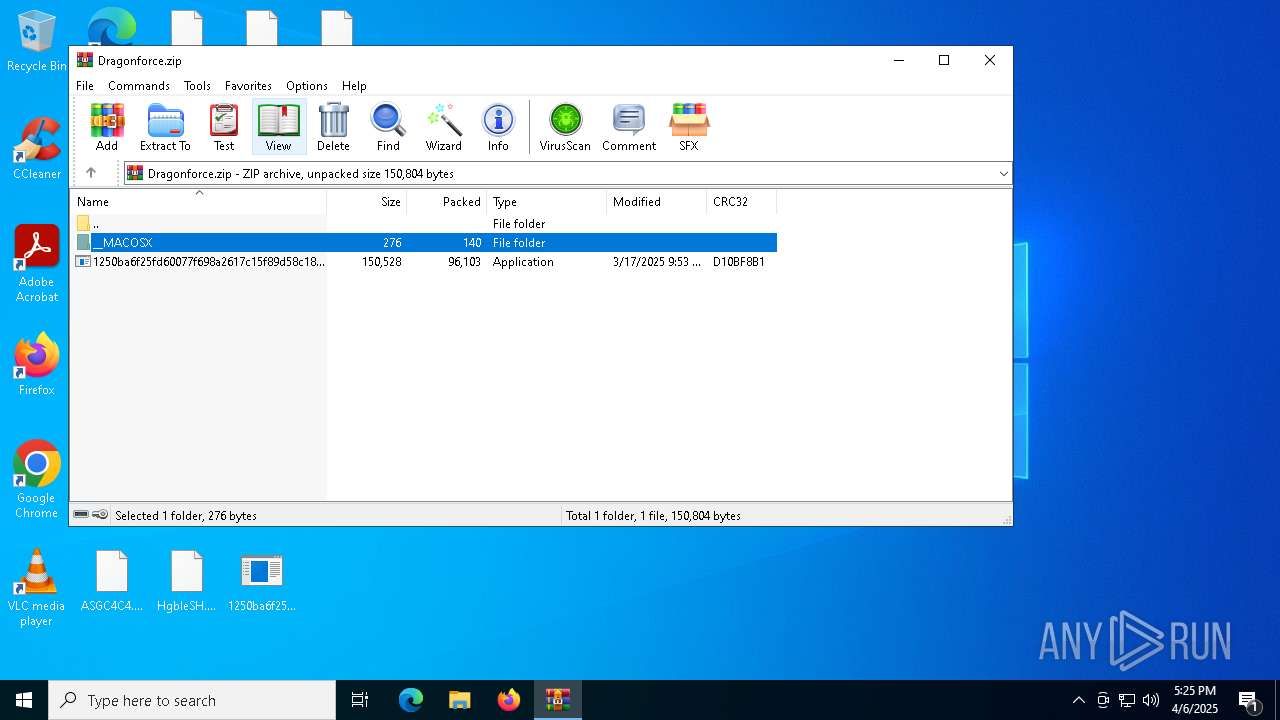
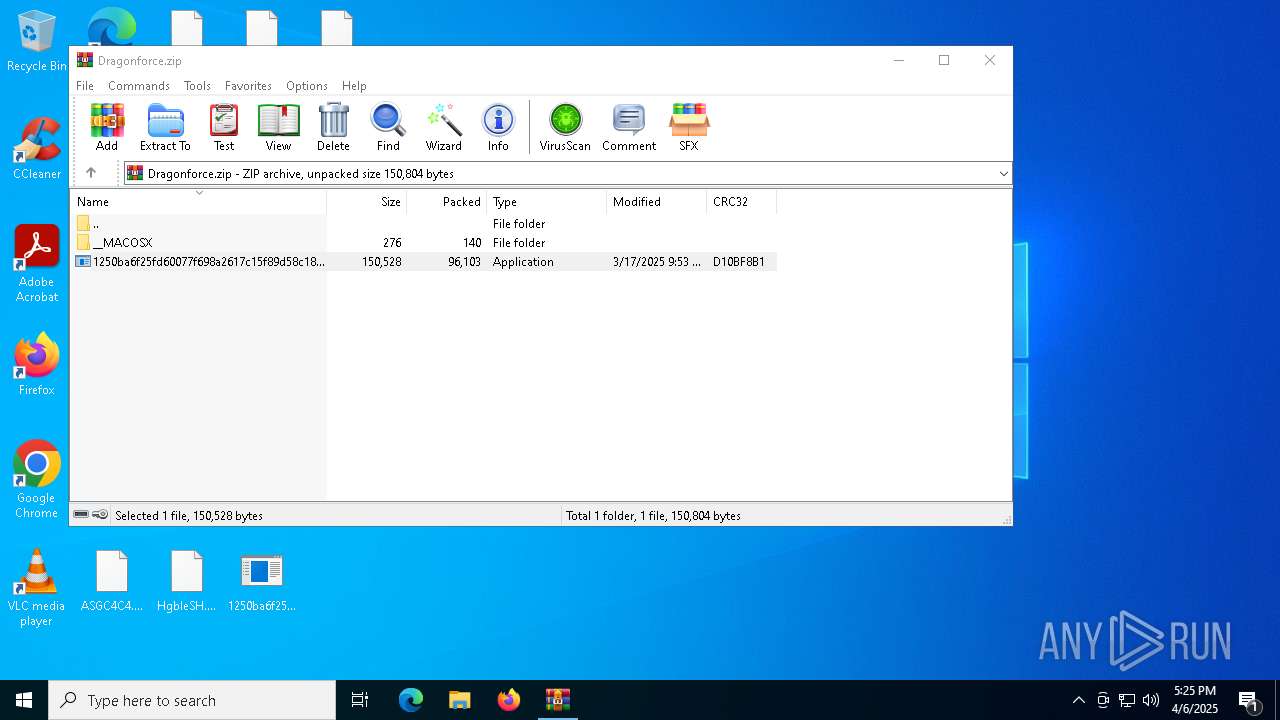
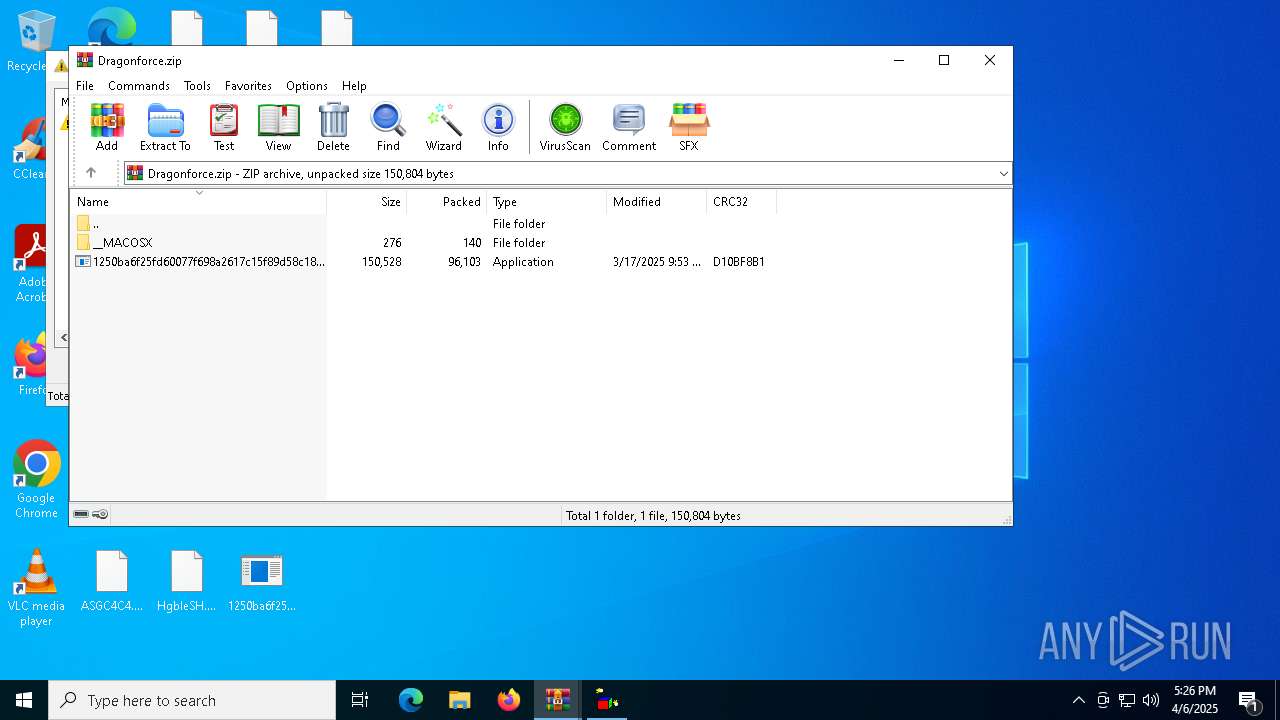
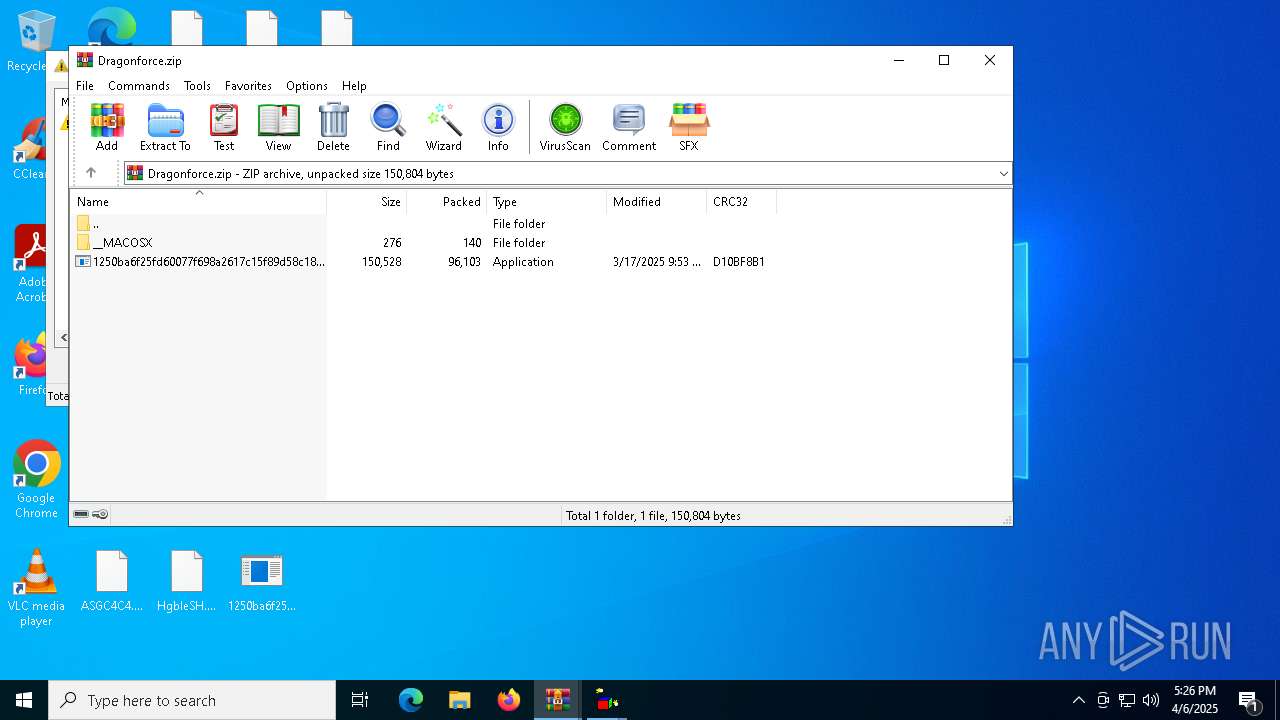
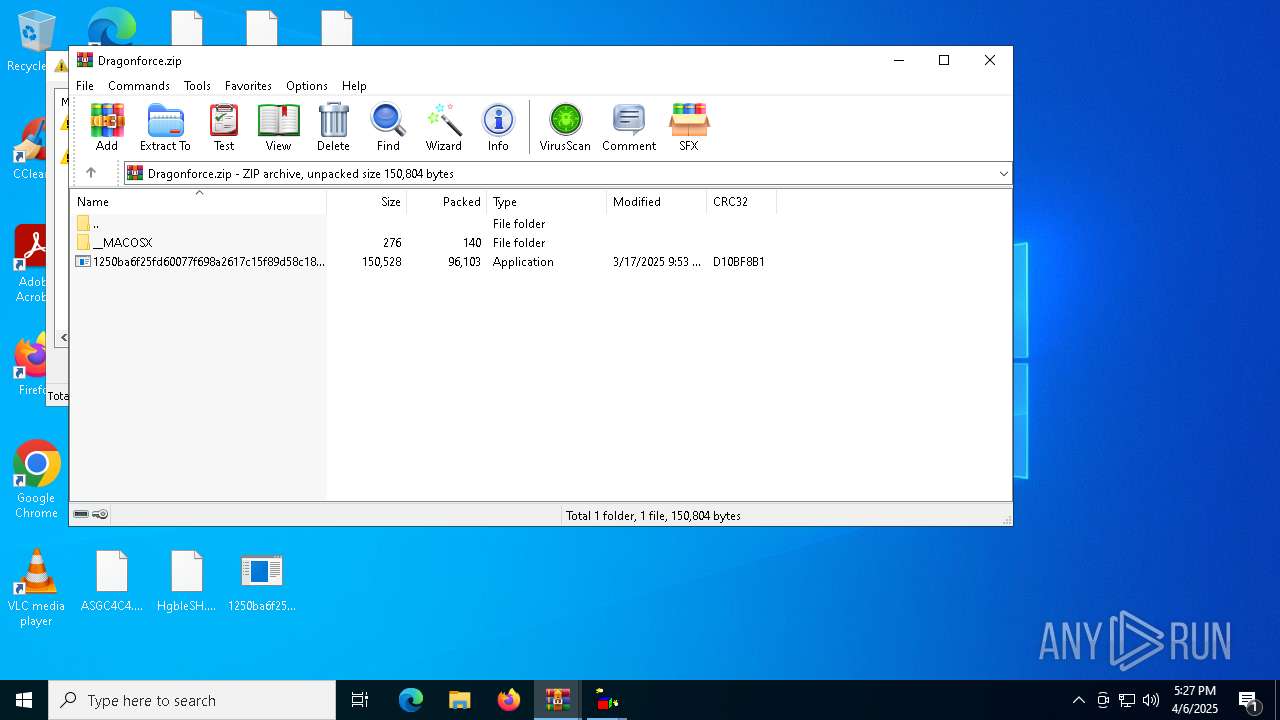
| File name: | Dragonforce.zip |
| Full analysis: | https://app.any.run/tasks/1f915961-09ca-4e7a-9cdc-15bafb639fdb |
| Verdict: | Malicious activity |
| Threats: | DragonForce is a ransomware strain operating under the Ransomware-as-a-Service (RaaS) model. First reported in December 2023, it encrypts files with ChaCha8, renames them with random strings, and appends “.dragonforce_encrypted.” By disabling backups, wiping recovery, and spreading across SMB shares, DragonForce maximizes damage and pressures victims into multimillion-dollar ransom negotiations. It has targeted manufacturing, construction, IT, healthcare, and retail sectors worldwide, making it a severe threat to modern enterprises. |
| Analysis date: | April 06, 2025, 17:24:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 7E7B8B35317B1BBF57CD5B39C310DA4C |
| SHA1: | 3966077D545454F8054BE4DBDFCE646A740B911F |
| SHA256: | 8656C8BC2D098776803EF6648D5B4D9E4CC444647AC09BB97FCCCD54956DDC94 |
| SSDEEP: | 1536:IbDa2Ex91TCDY+lUDwDesajjrdp+iEyCAqphZHopzTl9YXCFyRfiNU/xINKr:Ia23D/8jFIiWHhZIpzT2CFNOZINk |
MALICIOUS
DRAGONFORCE has been found (auto)
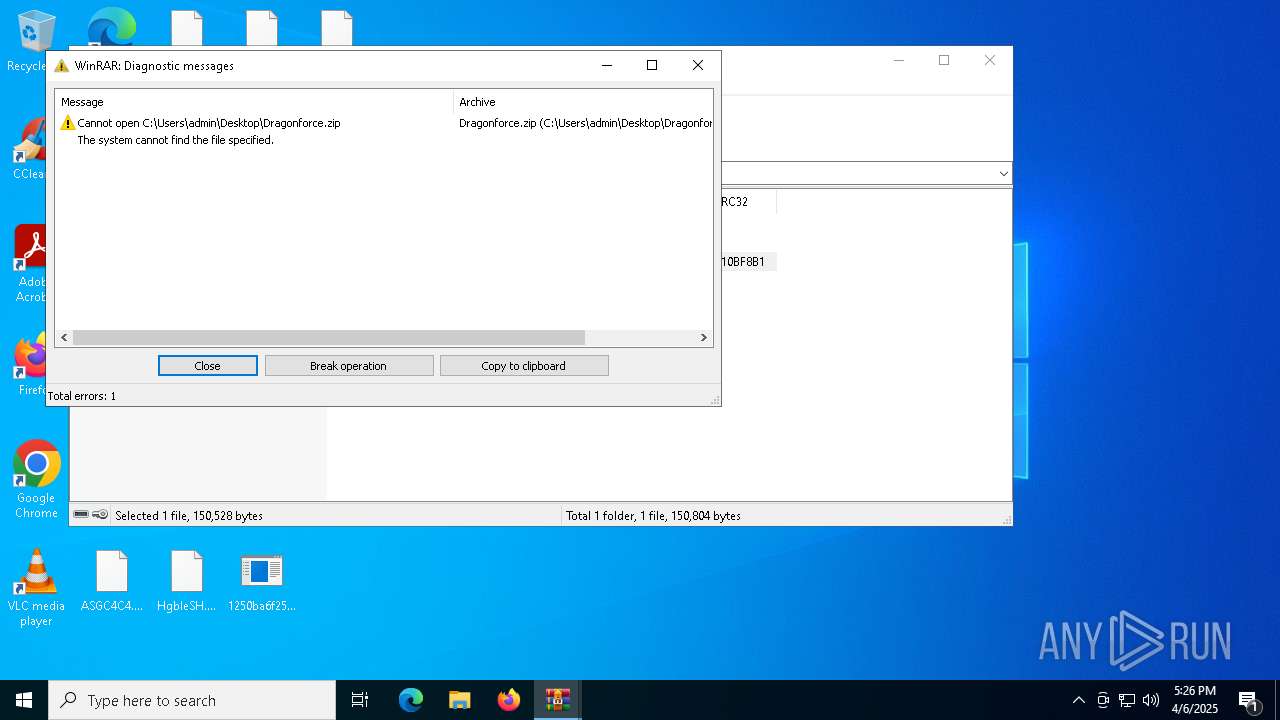
- WinRAR.exe (PID: 5256)
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
RANSOMWARE has been detected
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
Actions looks like stealing of personal data
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
Known privilege escalation attack
- dllhost.exe (PID: 5720)
[YARA] LockBit is detected
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
SUSPICIOUS
Write to the desktop.ini file (may be used to cloak folders)
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6576)
INFO
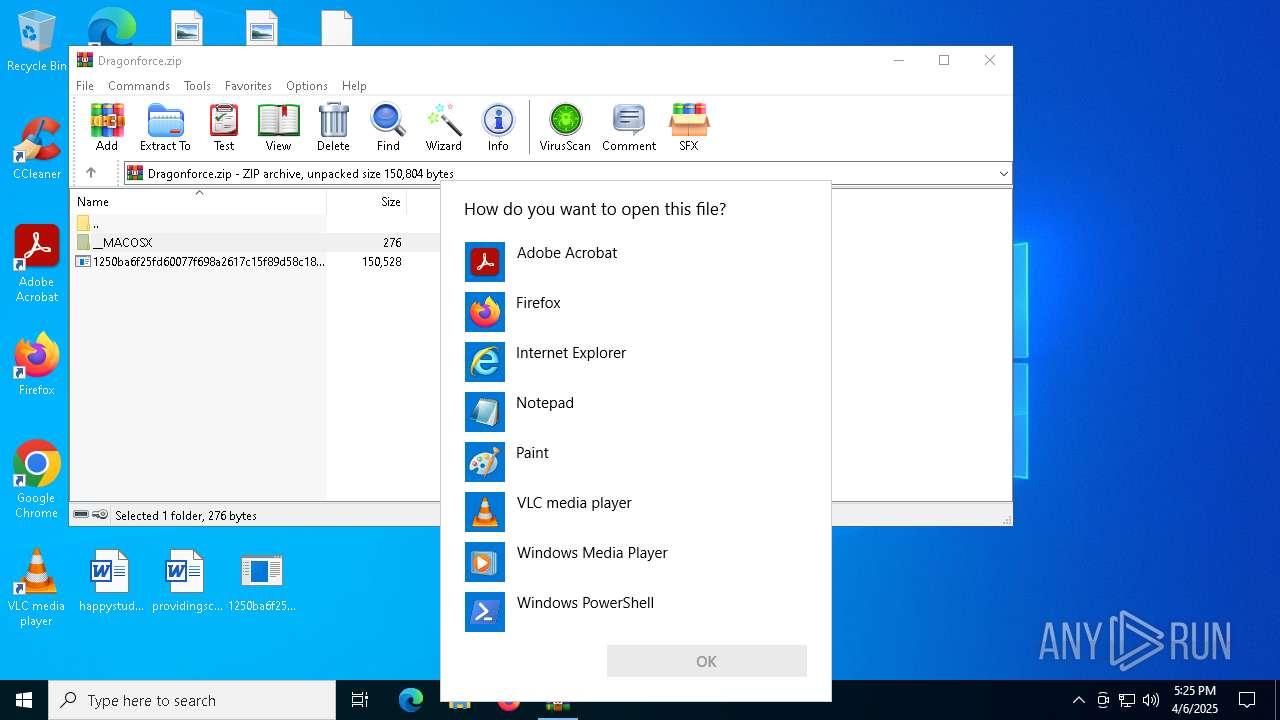
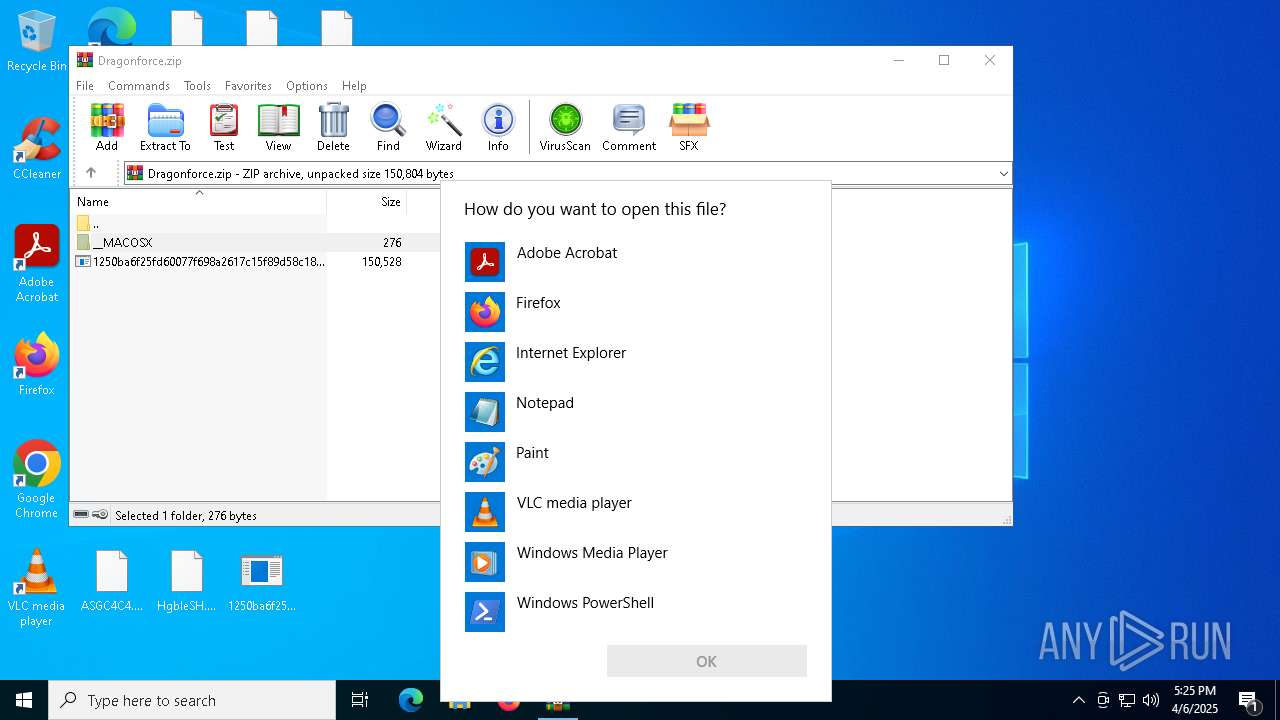
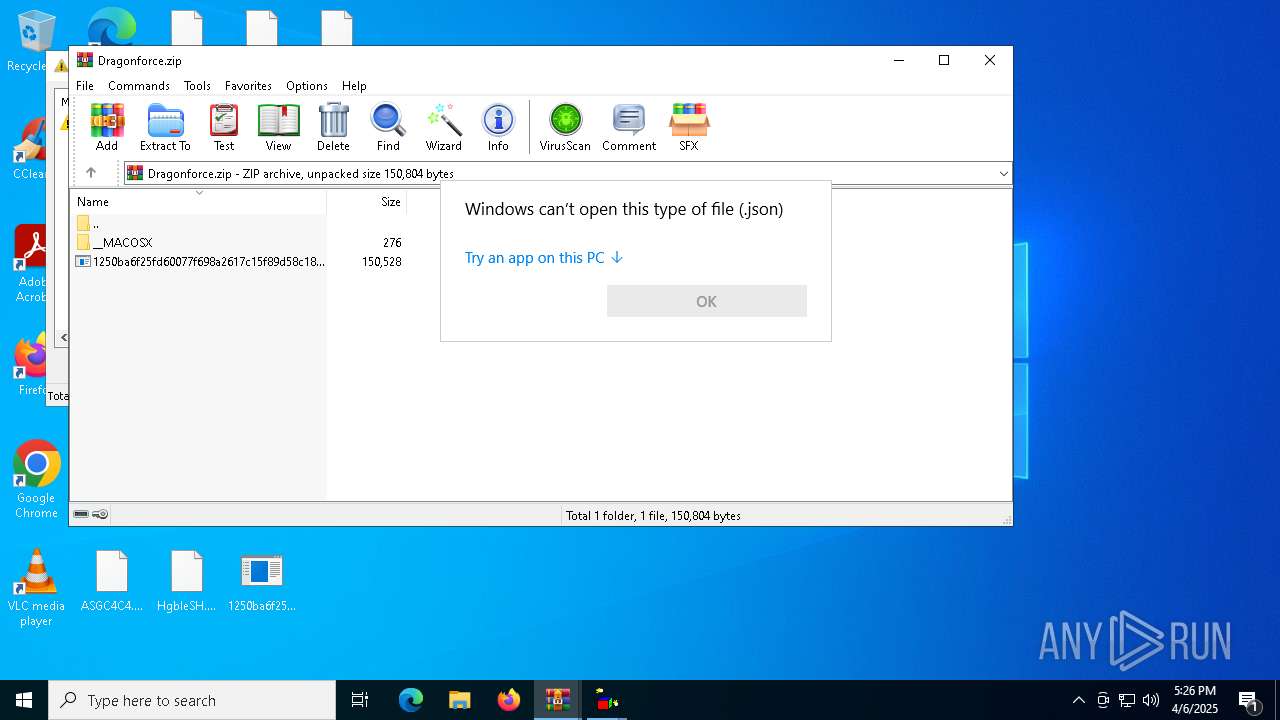
Manual execution by a user
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 5548)
- OpenWith.exe (PID: 5408)
- OpenWith.exe (PID: 5072)
- OpenWith.exe (PID: 2800)
- OpenWith.exe (PID: 2632)
- OpenWith.exe (PID: 1188)
- OpenWith.exe (PID: 6044)
- wscript.exe (PID: 5968)
- wscript.exe (PID: 5452)
- OpenWith.exe (PID: 1676)
- notepad.exe (PID: 7084)
- OpenWith.exe (PID: 4208)
Checks supported languages
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 5548)
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
- ShellExperienceHost.exe (PID: 6576)
- SearchApp.exe (PID: 2288)
Reads the machine GUID from the registry
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 5548)
- SearchApp.exe (PID: 2288)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5408)
- OpenWith.exe (PID: 1188)
- OpenWith.exe (PID: 2800)
- OpenWith.exe (PID: 6044)
- OpenWith.exe (PID: 4208)
- OpenWith.exe (PID: 2632)
- OpenWith.exe (PID: 1676)
- OpenWith.exe (PID: 5072)
Reads the computer name
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
- ShellExperienceHost.exe (PID: 6576)
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 5548)
- SearchApp.exe (PID: 2288)
Creates files or folders in the user directory
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7084)
- dllhost.exe (PID: 5720)
Create files in a temporary directory
- 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe (PID: 6516)
Process checks computer location settings
- SearchApp.exe (PID: 2288)
Checks proxy server information
- SearchApp.exe (PID: 2288)
Reads the software policy settings
- SearchApp.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:17 16:53:32 |
| ZipCRC: | 0xd10bf8b1 |
| ZipCompressedSize: | 96103 |
| ZipUncompressedSize: | 150528 |
| ZipFileName: | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe |
Total processes
149
Monitored processes
17
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\30qWCjB.AoVOpni2N | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\manifest.json | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\RAMEyOs.AoVOpni2N | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\l6dgFTH.AoVOpni2N | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\hLjF2WY.AoVOpni2N | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\gGy8PuE.AoVOpni2N | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
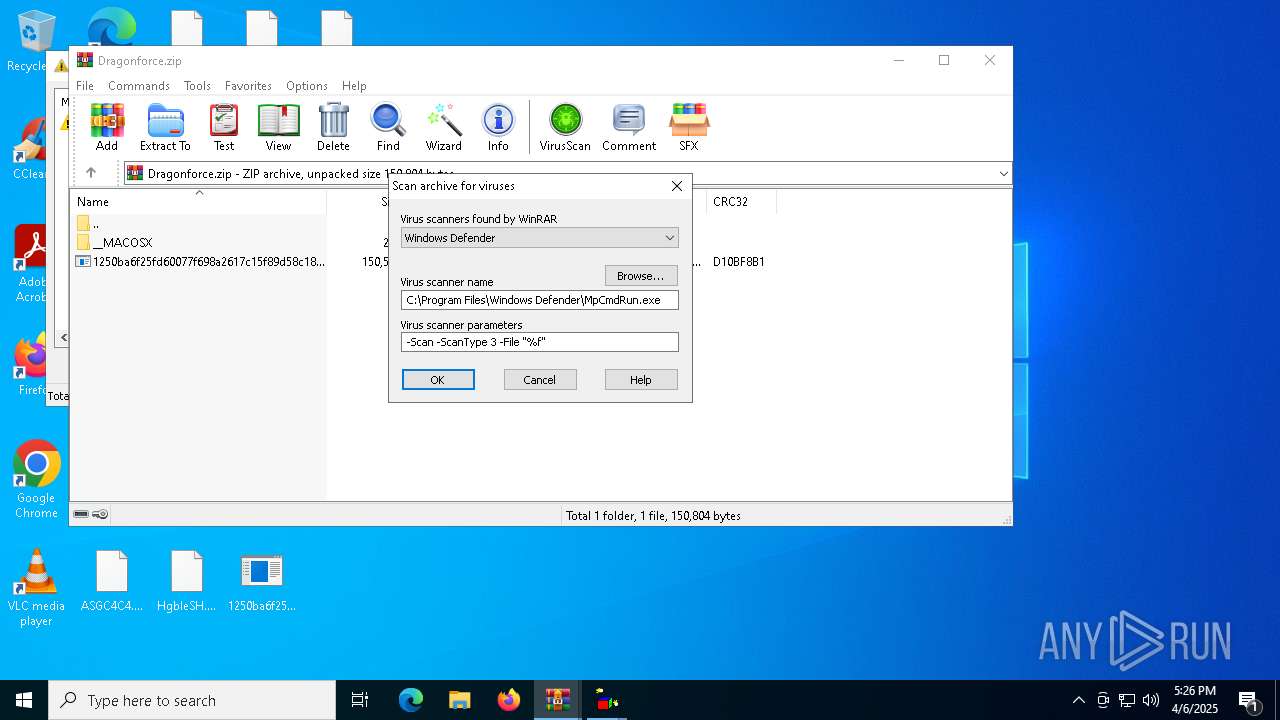
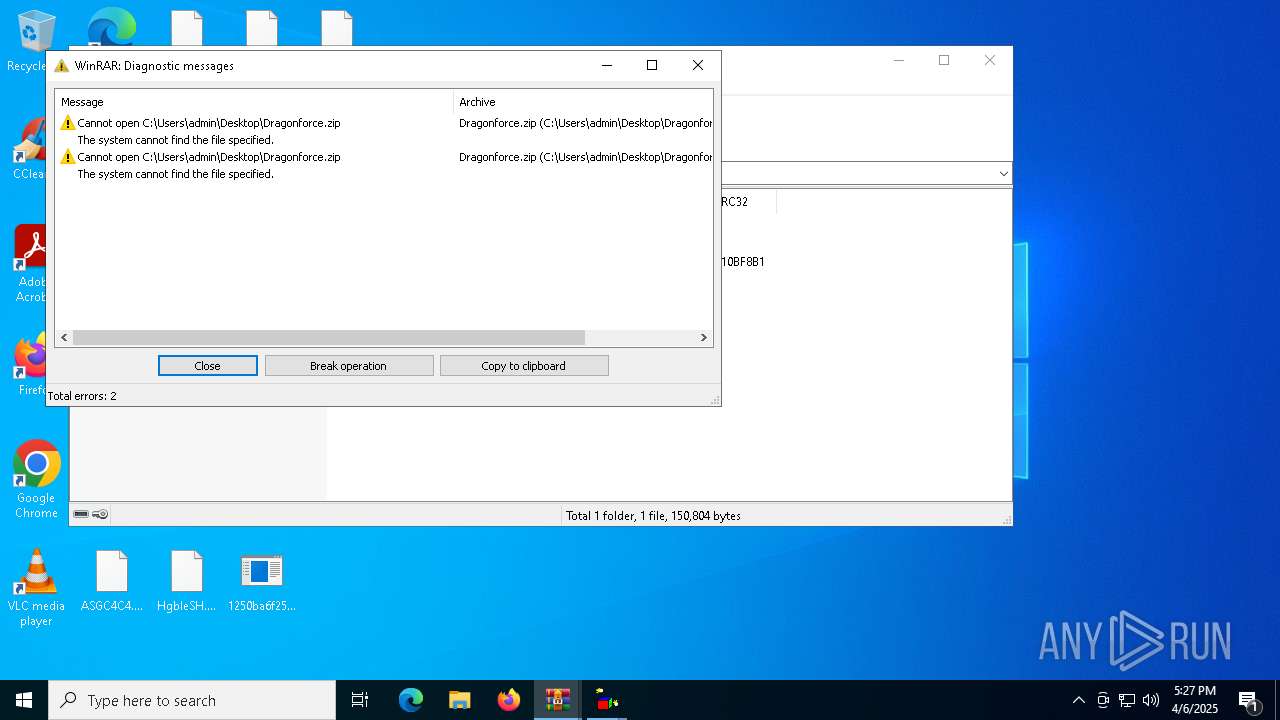
| 5256 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Dragonforce.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5408 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\e4836f00-d02b-4449-81a2-717aefaa94e9 | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5452 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\background.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
13 512
Read events
13 456
Write events
55
Delete events
1
Modification events
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Dragonforce.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5720) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6576) ShellExperienceHost.exe | Key: | \REGISTRY\A\{025decc5-4060-084a-0182-0920686794dd}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D0000009F17E8DE18A7DB01 | |||
Executable files
14
Suspicious files
1 703
Text files
1 743
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\BBBBBBBBBBB | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\FFFFFFFFFFF | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\AAAAAAAAAAA | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\OOOOOOOOOOO | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\MMMMMMMMMMM | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\JJJJJJJJJJJ | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\KKKKKKKKKKK | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
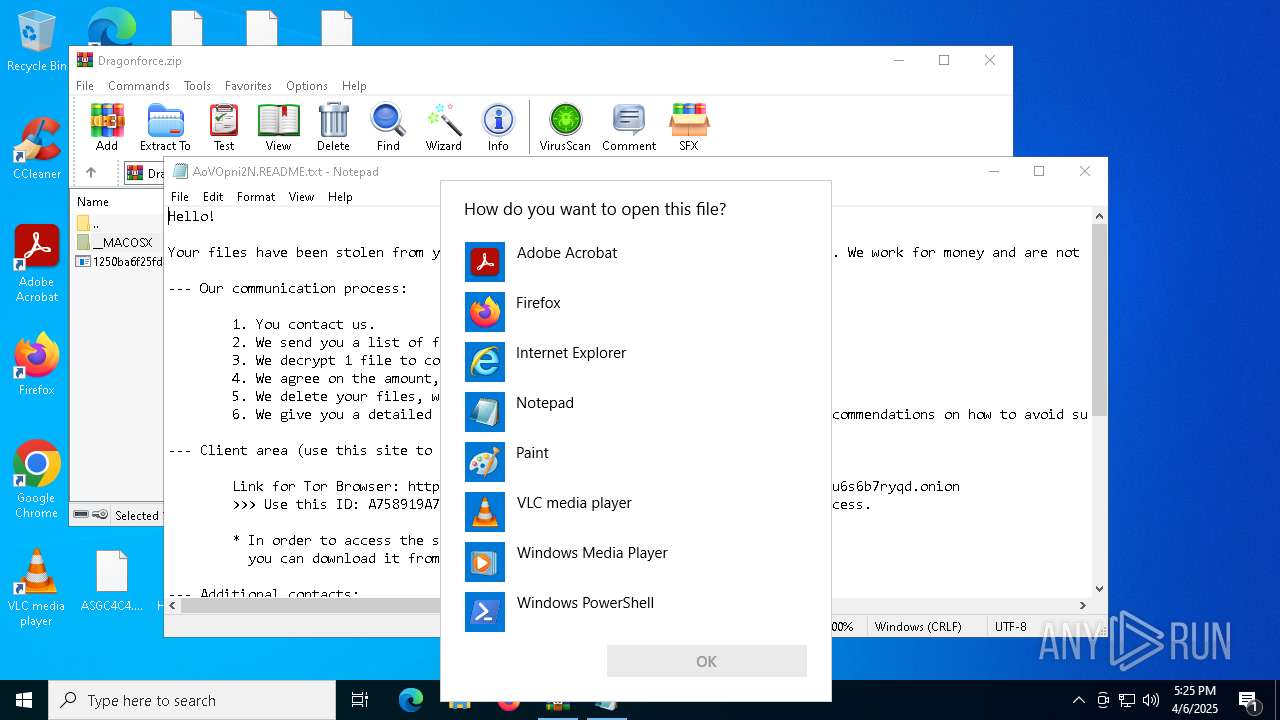
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\AoVOpni2N.README.txt | text | |
MD5:E6F59698CCA73ACBBAECEA9372DF65F2 | SHA256:1062E272CD6B96D40D0746C7B92C2652B2EC0EC67EDAA58FF36F06E85D82EF0E | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\NNNNNNNNNNN | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
| 6516 | 1250ba6f25fd60077f698a2617c15f89d58c1867339bfd9ee8ab19ce9943304b.exe | C:\$Recycle.Bin\S-1-5-18\QQQQQQQQQQQ | binary | |
MD5:92F39AC35F7816241536436DEC94D6C5 | SHA256:83266687A98E6795350FF025CEDAC1DD6A97B3752CEBC97A305D8926BF709029 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
43
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5344 | SIHClient.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.202.163.200:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.7.2.167:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5344 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5344 | SIHClient.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5344 | SIHClient.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5344 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |