| File name: | exefile.exe |
| Full analysis: | https://app.any.run/tasks/8475348c-cc8d-45a5-ad67-d967e2188a7a |
| Verdict: | Malicious activity |
| Threats: | Netwalker is ransomware — it belongs to a malware family which encrypts files and demands users to pay a ransom to get their data back. Netwalker utilizes several sophisticated techniques, such as process hollowing and code obfuscation to target corporate victims. |
| Analysis date: | March 29, 2020, 00:10:42 |
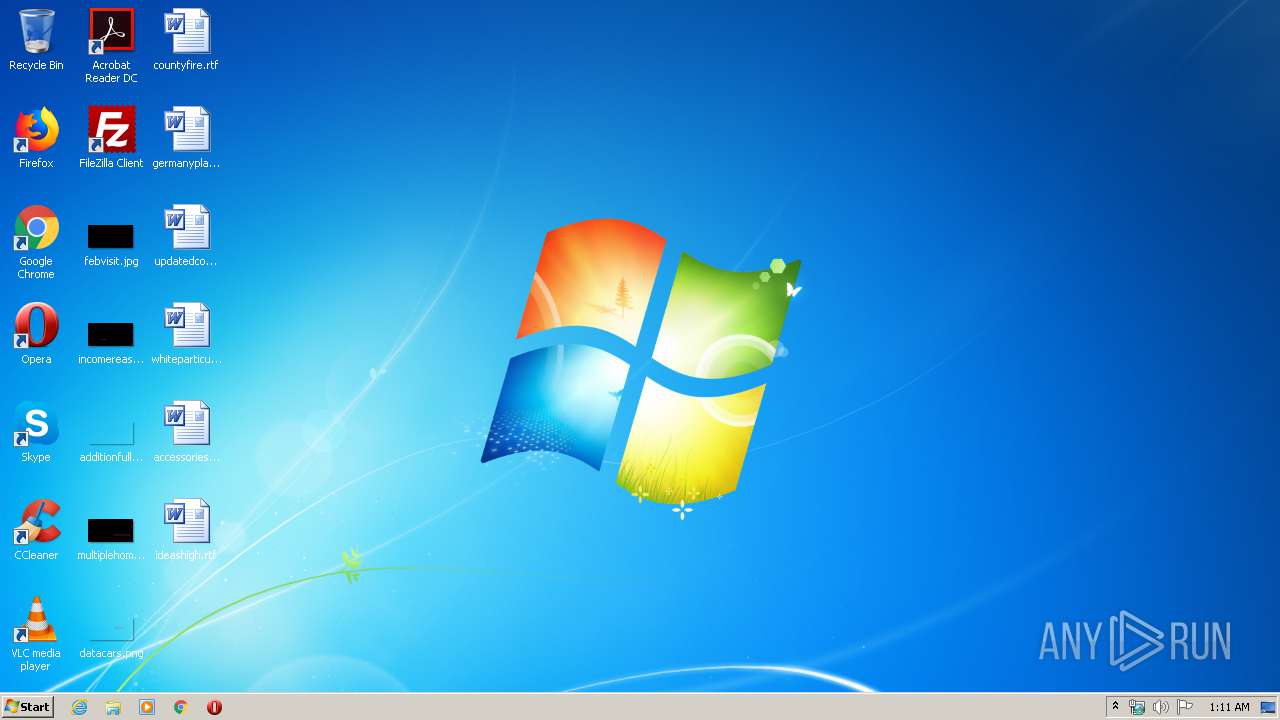
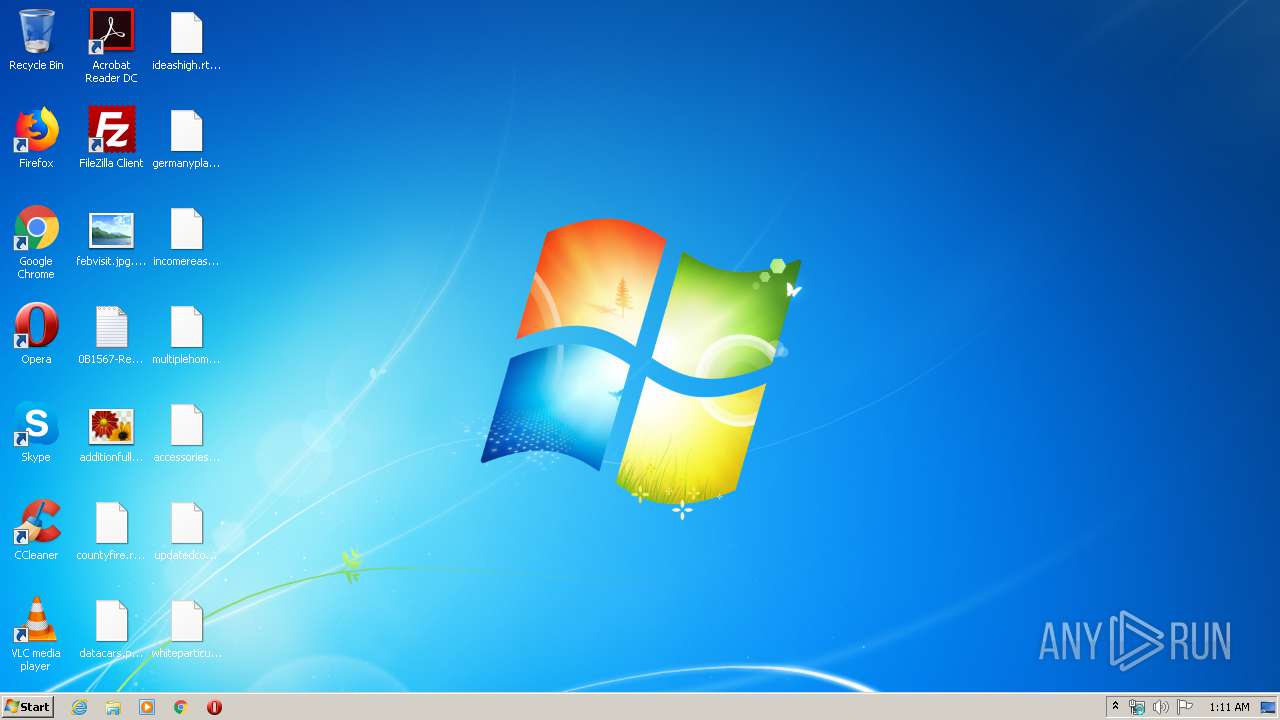
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 258ED03A6E4D9012F8102C635A5E3DCD |
| SHA1: | A3BC2A30318F9BD2B51CB57E2022996E7F15C69E |
| SHA256: | 8639825230D5504FD8126ED55B2D7AEB72944FFE17E762801AAB8D4F8F880160 |
| SSDEEP: | 3072:Kv4ZAWXDSxcoWn+v75ssiEcx7fWr5JNfb23y2O1Nm5dc:B1X7vwVspdOJND01 |
MALICIOUS
Netwalker ransom note found
- exefile.exe (PID: 2896)
Deletes shadow copies
- exefile.exe (PID: 2896)
Stealing of credential data
- exefile.exe (PID: 2896)
Dropped file may contain instructions of ransomware
- exefile.exe (PID: 2896)
Loads the Task Scheduler COM API
- exefile.exe (PID: 2896)
Renames files like Ransomware
- exefile.exe (PID: 2896)
Actions looks like stealing of personal data
- exefile.exe (PID: 2896)
Modifies files in Chrome extension folder
- exefile.exe (PID: 2896)
SUSPICIOUS
Creates files like Ransomware instruction
- exefile.exe (PID: 2896)
Reads the cookies of Google Chrome
- exefile.exe (PID: 2896)
Creates files in the user directory
- exefile.exe (PID: 2896)
Executable content was dropped or overwritten
- exefile.exe (PID: 2896)
Creates files in the program directory
- exefile.exe (PID: 2896)
INFO
Dropped object may contain Bitcoin addresses
- exefile.exe (PID: 2896)
Dropped object may contain TOR URL's
- exefile.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:01:13 22:51:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2 |
| CodeSize: | 80384 |
| InitializedDataSize: | 217088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3a80 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.7600.16385 |
| ProductVersionNumber: | 6.1.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | WTV file converter |
| FileVersion: | 6.1.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | WTVConverter.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WTVConverter.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7600.16385 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2002 21:51:13 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | WTV file converter |
| FileVersion: | 6.1.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | WTVConverter.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WTVConverter.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Jan-2002 21:51:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000139D1 | 0x00013A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.58828 |
.data | 0x00015000 | 0x000344D0 | 0x00034600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.49791 |
.rsrc | 0x0004A000 | 0x00000834 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.94408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.54463 | 932 | UNKNOWN | English - United States | RT_VERSION |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | C:\Windows\system32\vssadmin.exe delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | exefile.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\exefile.exe" | C:\Users\admin\AppData\Local\Temp\exefile.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WTV file converter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6
Read events
4
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2896) exefile.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\0b1567bf |
| Operation: | write | Name: | 0b1567bf |
Value: ECDE27997063B1A6B4B73C78C38AFD9B111D9828D91B909C1E1116066AA2FA7042B1C55D82F9AA88ECB08032BDC910CFF097EACF7370D56E2190EE5DBBC7F067AB165F4E1B76A44CE6423FF18656C765BB39B70A8ABD4C1DE15F62D99B53C1E1E6AABC84505FB7E5883C56BE54FED49F86C27AB84E4DA41B64D6CA36B1AE8B044736C6832745FE1A21CEC4CD | |||
| (PID) Process: | (2896) exefile.exe | Key: | HKEY_CURRENT_USER\Software\0b1567bf |
| Operation: | write | Name: | 0b1567bf |
Value: ECDE27997063B1A6B4B73C78C38AFD9B111D9828D91B909C1E1116066AA2FA7042B1C55D82F9AA88ECB08032BDC910CFF097EACF7370D56E2190EE5DBBC7F067AB165F4E1B76A44CE6423FF18656C765BB39B70A8ABD4C1DE15F62D99B53C1E1E6AABC84505FB7E5883C56BE54FED49F86C27AB84E4DA41B64D6CA36B1AE8B044736C6832745FE1A21CEC4CD | |||
Executable files
66
Suspicious files
1 860
Text files
875
Unknown types
338
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.EXCEL.14.1036.hxn | binary | |
MD5:8AEA5FE2092AD42390B5F1B4260EBA53 | SHA256:70CD45D27E9B32FC92AC3EE69609F8F60F4F1E927009533C424F58FF77E3610F | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.POWERPNT.14.1055.hxn | binary | |
MD5:175E5A5235D92B833450F7F4F91A202F | SHA256:A54B8F6FFF5DF6991DD1DF01D309784EAB8B5D0B7098B64C03BE208E8E75890F | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.POWERPNT.DEV.14.1041.hxn | binary | |
MD5:31921440C020EAF34927AE3BB72366BE | SHA256:C1E329B1E2BDD3FC77BFEFF3BB983721DB9A726CA7739E06A960A17863F84B67 | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.EXCEL.14.1033.hxn | binary | |
MD5:AE510308FAF836710FDC97330A278A1F | SHA256:6D6EB0F5956055B65EC1FF3C9734269E0F82140164EAB6B85C58477FF31C1CD2 | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.POWERPNT.DEV.14.1033.hxn | binary | |
MD5:A0F37FD486B76044569BF172F641EC81 | SHA256:8EDD97F24946D7493EBE0B57888446EBFC788D00F3A2F6DB82A35D19C570176A | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.POWERPNT.DEV.14.1055.hxn | binary | |
MD5:D24CC631D0256942198B2EC1C19D303E | SHA256:C8CE481423EF87F19A238131DD3A401919A04D6E08C5E049BE6F5444A1ECCB81 | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.POWERPNT.DEV.14.1042.hxn | binary | |
MD5:4E554341FE62C517C9F2BADAD2E66434 | SHA256:A0F29505CE084D3549F6F6877DB0EAC6C2F0775C9EE399D5017D02B2FA7CF421 | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.EXCEL.14.1049.hxn | binary | |
MD5:CB2B2ABCD3FF383D2A09ED3BD41BBF06 | SHA256:B195C615136775182A142D9BA8A82F7A4FE551A492C3F074D423429694F7716C | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.POWERPNT.DEV.14.1046.hxn | binary | |
MD5:DB8A0EF7A33E647E8ABD5B2C7AF7C9B0 | SHA256:FB5B8366B78DC743C8A948FA298176B7F7432069019EDE9EA555E94819A17FA7 | |||
| 2896 | exefile.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft Help\MS.EXCEL.14.1046.hxn | binary | |
MD5:5B0D679213FF9DDEE6E1554EF9B8DF56 | SHA256:A1878736D0F732336E8EBAAF66D91781046D84F4EE59038DCD2024905AEF8281 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report