| File name: | 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf |
| Full analysis: | https://app.any.run/tasks/9c5dc2f5-254e-4c23-aff5-7ab39b0258e2 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | September 21, 2024, 12:13:10 |
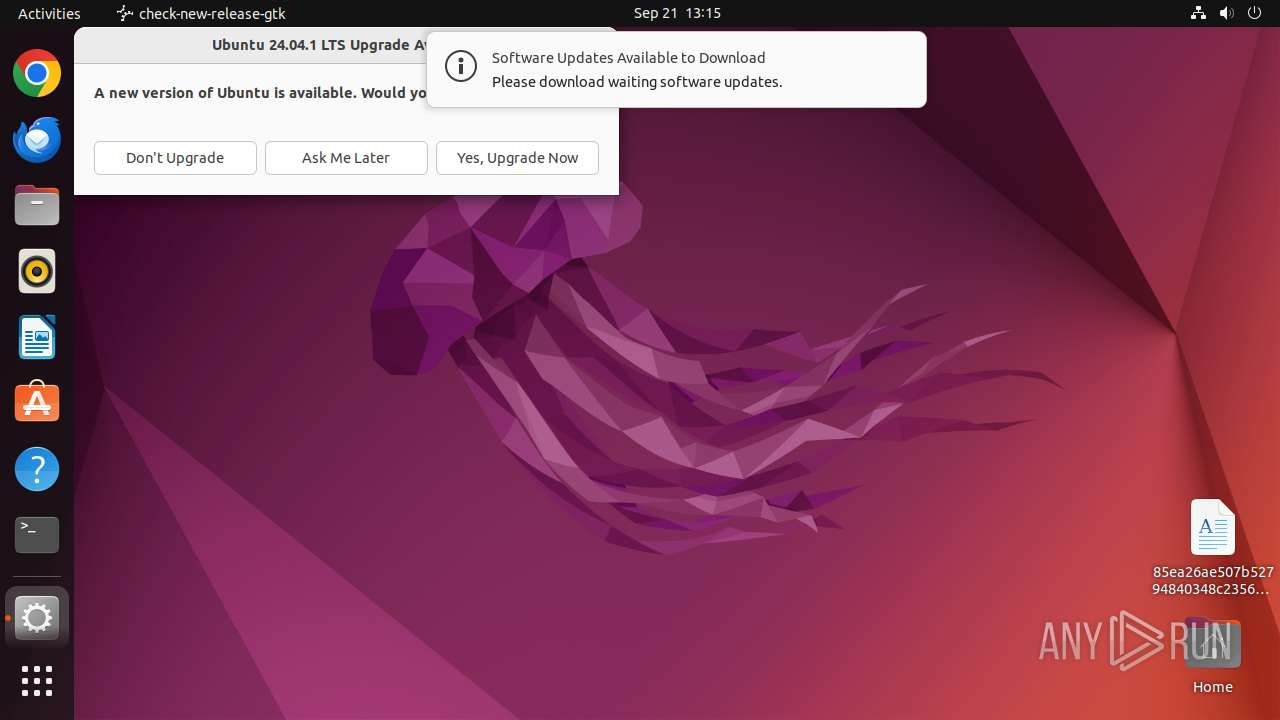
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | application/x-executable |
| File info: | ELF 64-bit LSB executable, x86-64, version 1 (SYSV), statically linked, not stripped |
| MD5: | A72D8D8FF50C92830E1F47081851376B |
| SHA1: | 43917C6C0C919F7A49D78412684CB53B7B72CD43 |
| SHA256: | 85EA26AE507B52794840348C2356B9F62D87D7EA24038C72F19BA7A8632BA4AB |
| SSDEEP: | 3072:lzd7Dtn9g9lZ0wL+7Dphauz/EIjw3mdRWaLHgb4:lNDtn9g9lZ0wq7DphauamdRWaDgb4 |
MALICIOUS
MIRAI has been detected (SURICATA)
- 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o (PID: 13918)
Connects to the CnC server
- 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o (PID: 13918)
SUSPICIOUS
Executes commands using command-line interpreter
- bash (PID: 13912)
- sudo (PID: 13907)
- update-notifier (PID: 13934)
Modifies file or directory owner
- sudo (PID: 13904)
Gets active network interfaces
- sudo (PID: 13907)
Reads network configuration
- sudo (PID: 13907)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13936)
Connects to unusual port
- 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o (PID: 13918)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Executable file |
| CPUType: | AMD x86-64 |
Total processes
246
Monitored processes
29
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 13903 | /bin/sh -c "sudo chown user /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab\.elf\.o && chmod +x /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab\.elf\.o && DISPLAY=:0 sudo -i /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab\.elf\.o " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13904 | sudo chown user /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13905 | chown user /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13906 | chmod +x /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | /usr/bin/chmod | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13907 | sudo -i /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13910 | /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | /home/user/Desktop/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13911 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13912 | -bash --login -c \/home\/user\/Desktop\/85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab\.elf\.o | /usr/bin/bash | — | 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13913 | sh -c "cat /usr/etc/debuginfod/*\.urls 2>/dev/null" | /usr/bin/sh | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13914 | tr \n " " | /usr/bin/tr | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13936 | check-new-release-gtk | /tmp/#6029335 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029359 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029364 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029378 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029334 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029379 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029381 (deleted) | text | |
MD5:— | SHA256:— | |||
| 13936 | check-new-release-gtk | /tmp/#6029987 (deleted) | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
2 507
DNS requests
18
Threats
2 539
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 212.102.56.178:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | binary | 1.58 Mb | unknown |
— | — | GET | 200 | 195.181.175.40:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | binary | 1.58 Mb | unknown |
— | — | GET | 200 | 207.211.211.26:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | binary | 1.58 Mb | unknown |
— | — | GET | 200 | 169.150.255.180:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | binary | 1.58 Mb | unknown |
— | — | GET | 200 | 37.19.194.80:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | binary | 1.58 Mb | unknown |
— | — | GET | 200 | 185.125.188.59:443 | https://api.snapcraft.io/v2/snaps/info/snapd?architecture=amd64&fields=architectures%2Cbase%2Cconfinement%2Clinks%2Ccontact%2Ccreated-at%2Cdescription%2Cdownload%2Cepoch%2Clicense%2Cname%2Cprices%2Cprivate%2Cpublisher%2Crevision%2Csnap-id%2Csummary%2Ctitle%2Ctype%2Cversion%2Cwebsite%2Cstore-url%2Cmedia%2Ccommon-ids%2Ccategories | unknown | binary | 3.98 Kb | unknown |
— | — | GET | 200 | 185.125.188.54:443 | https://api.snapcraft.io/v2/snaps/info/snapd?architecture=amd64&fields=architectures%2Cbase%2Cconfinement%2Clinks%2Ccontact%2Ccreated-at%2Cdescription%2Cdownload%2Cepoch%2Clicense%2Cname%2Cprices%2Cprivate%2Cpublisher%2Crevision%2Csnap-id%2Csummary%2Ctitle%2Ctype%2Cversion%2Cwebsite%2Cstore-url%2Cmedia%2Ccommon-ids%2Ccategories | unknown | binary | 3.98 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 212.102.56.178:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
13918 | 85ea26ae507b52794840348c2356b9f62d87d7ea24038c72f19ba7a8632ba4ab.elf.o | 5.42.98.15:4258 | — | CJSC Kolomna-Sviaz TV | RU | unknown |
— | — | 5.42.98.15:4258 | — | CJSC Kolomna-Sviaz TV | RU | unknown |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
186.100.168.192.in-addr.arpa |
| unknown |
changelogs.ubuntu.com |
| whitelisted |
Threats
2539 ETPRO signatures available at the full report