| File name: | DriveSecManager.exe |
| Full analysis: | https://app.any.run/tasks/d6a29756-211e-40a9-b49d-188c89216c6a |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | April 04, 2025, 20:36:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | AAD6256DB1D77092B8AA4A34D562ED74 |
| SHA1: | 235186415F51CF117E76622D24861FE01D397A22 |
| SHA256: | 859A1C23578F61549C932AE7610269E87BF63232F3218D6BEE11F74F5822C280 |
| SSDEEP: | 3072:6p/hMNfDU6NP/mAyp/8+62bSKI2agGspcFSDPO9HuQzDAD9dFUELlpMMgIEKuO2X:hSycp |
MALICIOUS
Changes the autorun value in the registry
- DriveSecManager.exe (PID: 7276)
- reg.exe (PID: 1020)
- reg.exe (PID: 7052)
PHORPIEX has been detected (YARA)
- sysldsvp.exe (PID: 7440)
Connects to the CnC server
- sysldsvp.exe (PID: 7440)
- dwm.exe (PID: 5376)
PHORPIEX has been detected (SURICATA)
- sysldsvp.exe (PID: 7440)
PHORPIEX mutex has been found
- 2101113113.exe (PID: 4424)
Actions looks like stealing of personal data
- 2101113113.exe (PID: 4424)
- 56044582.exe (PID: 516)
MINER has been found (auto)
- 187528841.exe (PID: 7268)
- 372528156.exe (PID: 4120)
Steals credentials from Web Browsers
- 2101113113.exe (PID: 4424)
Vulnerable driver has been detected
- sysdoruhgsf.exe (PID: 1180)
MINER has been detected (SURICATA)
- dwm.exe (PID: 5376)
SUSPICIOUS
Reads security settings of Internet Explorer
- sysldsvp.exe (PID: 7440)
- 187528841.exe (PID: 7268)
- 228665113.exe (PID: 8040)
Starts itself from another location
- DriveSecManager.exe (PID: 7276)
- 372528156.exe (PID: 4120)
Executable content was dropped or overwritten
- DriveSecManager.exe (PID: 7276)
- 187528841.exe (PID: 7268)
- 372528156.exe (PID: 4120)
- 56044582.exe (PID: 516)
- sysdoruhgsf.exe (PID: 1180)
Contacting a server suspected of hosting an CnC
- sysldsvp.exe (PID: 7440)
Connects to the server without a host name
- sysldsvp.exe (PID: 7440)
- 187528841.exe (PID: 7268)
- 228665113.exe (PID: 8040)
Process requests binary or script from the Internet
- 187528841.exe (PID: 7268)
Potential Corporate Privacy Violation
- 187528841.exe (PID: 7268)
- dwm.exe (PID: 5376)
Connects to unusual port
- sysldsvp.exe (PID: 7440)
- dwm.exe (PID: 5376)
Uses REG/REGEDIT.EXE to modify registry
- 372528156.exe (PID: 4120)
- sysdoruhgsf.exe (PID: 1180)
Drops a system driver (possible attempt to evade defenses)
- sysdoruhgsf.exe (PID: 1180)
INFO
Reads the computer name
- sysldsvp.exe (PID: 7440)
- 228665113.exe (PID: 8040)
- 187528841.exe (PID: 7268)
Checks supported languages
- DriveSecManager.exe (PID: 7276)
- sysldsvp.exe (PID: 7440)
- 228665113.exe (PID: 8040)
- 187528841.exe (PID: 7268)
- 2101113113.exe (PID: 4424)
- 56044582.exe (PID: 516)
- 372528156.exe (PID: 4120)
- sysdoruhgsf.exe (PID: 1180)
Checks proxy server information
- sysldsvp.exe (PID: 7440)
- 228665113.exe (PID: 8040)
- 187528841.exe (PID: 7268)
Failed to create an executable file in Windows directory
- DriveSecManager.exe (PID: 7276)
Creates files or folders in the user directory
- sysldsvp.exe (PID: 7440)
- 187528841.exe (PID: 7268)
- 56044582.exe (PID: 516)
Create files in a temporary directory
- sysldsvp.exe (PID: 7440)
- 228665113.exe (PID: 8040)
- 187528841.exe (PID: 7268)
- 2101113113.exe (PID: 4424)
- sysdoruhgsf.exe (PID: 1180)
Reads the machine GUID from the registry
- sysldsvp.exe (PID: 7440)
The sample compiled with english language support
- 56044582.exe (PID: 516)
The sample compiled with japanese language support
- sysdoruhgsf.exe (PID: 1180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:02 12:17:11+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 58880 |
| InitializedDataSize: | 23040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x76c0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
16
Malicious processes
8
Suspicious processes
2
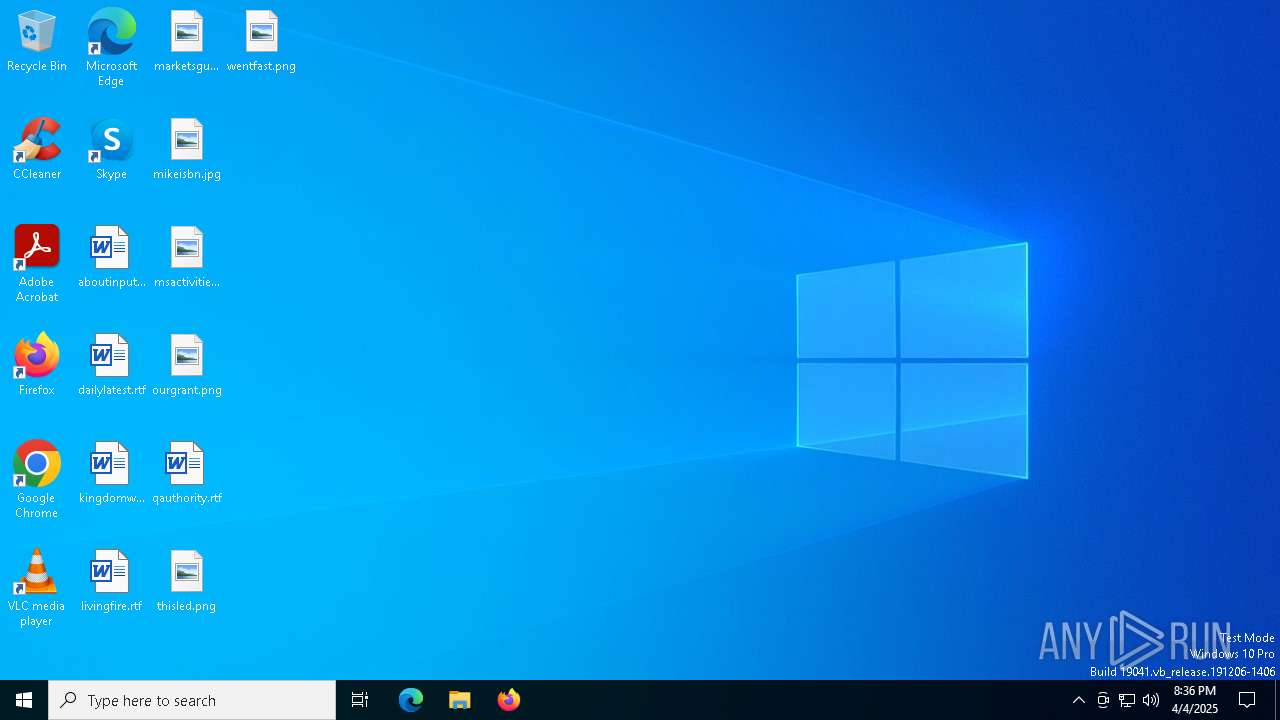
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\Users\admin\AppData\Local\Temp\56044582.exe | C:\Users\admin\AppData\Local\Temp\56044582.exe | 187528841.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\conhost.exe | C:\Windows\System32\conhost.exe | — | sysdoruhgsf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | C:\WINDOWS\system32\reg.exe add "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "MgrDrvSvc" /t REG_SZ /f /d "C:\Users\admin\MgrDrvSvc\sysdoruhgsf.exe" | C:\Windows\System32\reg.exe | 372528156.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\MgrDrvSvc\sysdoruhgsf.exe" | C:\Users\admin\MgrDrvSvc\sysdoruhgsf.exe | 372528156.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | C:\Users\admin\AppData\Local\Temp\372528156.exe | C:\Users\admin\AppData\Local\Temp\372528156.exe | 187528841.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4424 | C:\Users\admin\AppData\Local\Temp\2101113113.exe | C:\Users\admin\AppData\Local\Temp\2101113113.exe | 187528841.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5376 | dwm.exe | C:\Windows\System32\dwm.exe | sysdoruhgsf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7052 | C:\WINDOWS\system32\reg.exe add "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "MgrDrvSvc" /t REG_SZ /f /d "C:\Users\admin\MgrDrvSvc\sysdoruhgsf.exe" | C:\Windows\System32\reg.exe | sysdoruhgsf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 942
Read events
2 930
Write events
12
Delete events
0
Modification events
| (PID) Process: | (7276) DriveSecManager.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Settings |
Value: C:\Users\admin\sysldsvp.exe | |||
| (PID) Process: | (7440) sysldsvp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7440) sysldsvp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7440) sysldsvp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8040) 228665113.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8040) 228665113.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8040) 228665113.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7268) 187528841.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7268) 187528841.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7268) 187528841.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
10
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7440 | sysldsvp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\2[1] | binary | |
MD5:6F4621D1DC7F9BB63AB7E8A1CDD9EB1D | SHA256:06BE26868462421F2A4BD3D2F25C67F3FEDF573F23054B7C27C1782B35645CBF | |||
| 7276 | DriveSecManager.exe | C:\Users\admin\sysldsvp.exe | executable | |
MD5:AAD6256DB1D77092B8AA4A34D562ED74 | SHA256:859A1C23578F61549C932AE7610269E87BF63232F3218D6BEE11F74F5822C280 | |||
| 7440 | sysldsvp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\1[1] | binary | |
MD5:70E2C7DC6A7FB4444B08758ED08BBD04 | SHA256:A741E319BD50C4B1B5225969C939C80A548AD6F6C07D9C50D70404B9ABF6D8B0 | |||
| 7440 | sysldsvp.exe | C:\Users\admin\AppData\Local\Temp\228665113.exe | binary | |
MD5:70E2C7DC6A7FB4444B08758ED08BBD04 | SHA256:A741E319BD50C4B1B5225969C939C80A548AD6F6C07D9C50D70404B9ABF6D8B0 | |||
| 7268 | 187528841.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\tcoin[1].exe | executable | |
MD5:60686A27B79838583920C9A0954104C9 | SHA256:E4F7AB224BF2482B29EA1F89C60338EEE391CC2E8FFFF69BC2E85F701D049B87 | |||
| 7268 | 187528841.exe | C:\Users\admin\AppData\Local\Temp\2101113113.exe | executable | |
MD5:60686A27B79838583920C9A0954104C9 | SHA256:E4F7AB224BF2482B29EA1F89C60338EEE391CC2E8FFFF69BC2E85F701D049B87 | |||
| 7440 | sysldsvp.exe | C:\Users\admin\tbtnds.dat | binary | |
MD5:FCC5FA024E376914B1DB914550A7E2F8 | SHA256:37B46C2CA70184E8C17060FA7D763C22E38E5E82030E37B6C0CB90891B76420C | |||
| 7268 | 187528841.exe | C:\Users\admin\AppData\Local\Temp\372528156.exe | executable | |
MD5:024DD77C38676E6CE0A5A2201F6145DE | SHA256:B4553FF5D7AE98614D4856DE134F49E503F046A15FC49033AF3232FBEAB9ED4C | |||
| 7268 | 187528841.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\peinf[1].exe | executable | |
MD5:AD89DD0CCBC6CFDEA9C01D3ED1E37222 | SHA256:B25DD25B7D1DE82D2BF368146D964CCA3862A31F7EAA820E8EB45B47D808F348 | |||
| 516 | 56044582.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:DFB789E2A35C98DC0019FDC071634EF1 | SHA256:2229173D0628BC4E7B7F990A0F316EB7406B347915EE05AFB91735AF3D987606 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
31
DNS requests
13
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7440 | sysldsvp.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/3 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/2 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/4 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | 404 | 185.215.113.66:80 | http://185.215.113.66/5 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | — | 45.93.20.18:80 | http://45.93.20.18/1 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | 200 | 45.93.20.18:80 | http://45.93.20.18/1 | unknown | — | — | malicious |
7440 | sysldsvp.exe | GET | — | 45.93.20.18:80 | http://45.93.20.18/2 | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6876 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7440 | sysldsvp.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 32 |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 4 |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |
7440 | sysldsvp.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |