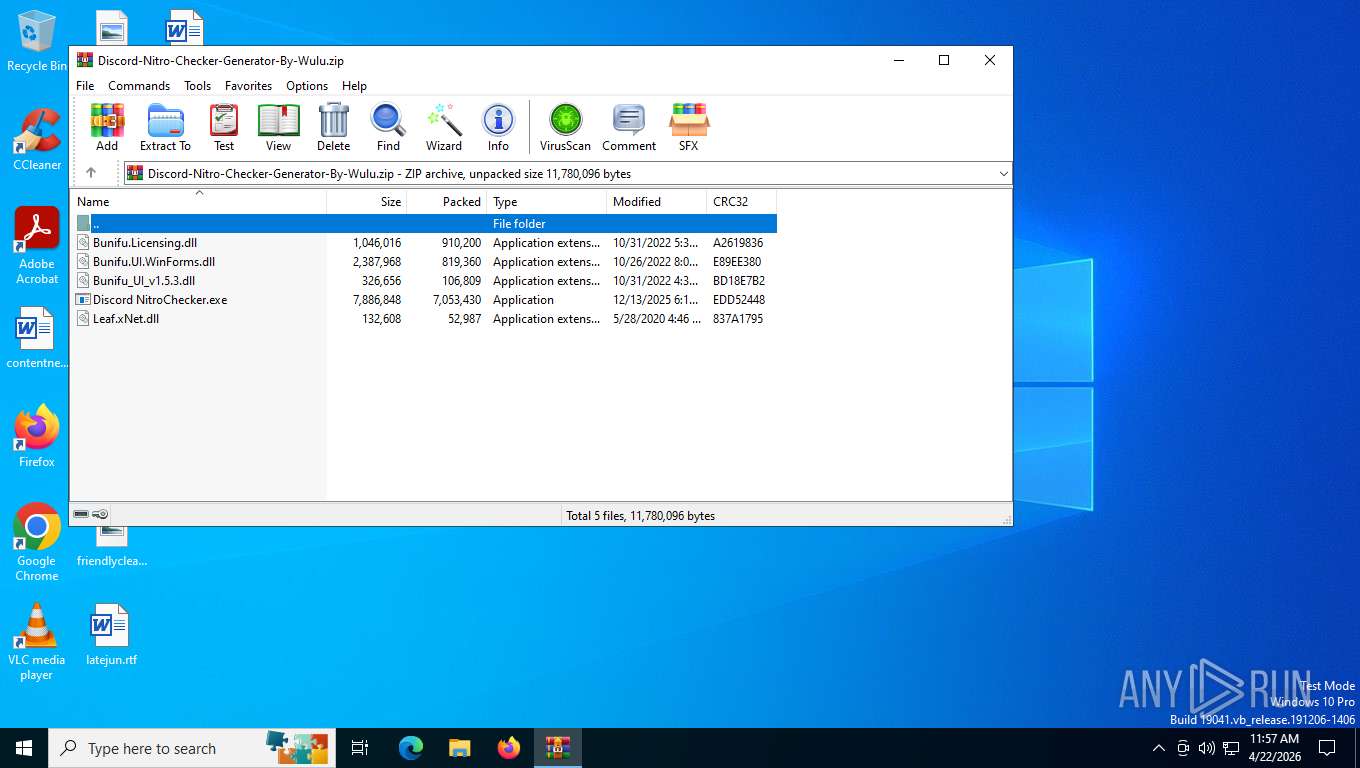
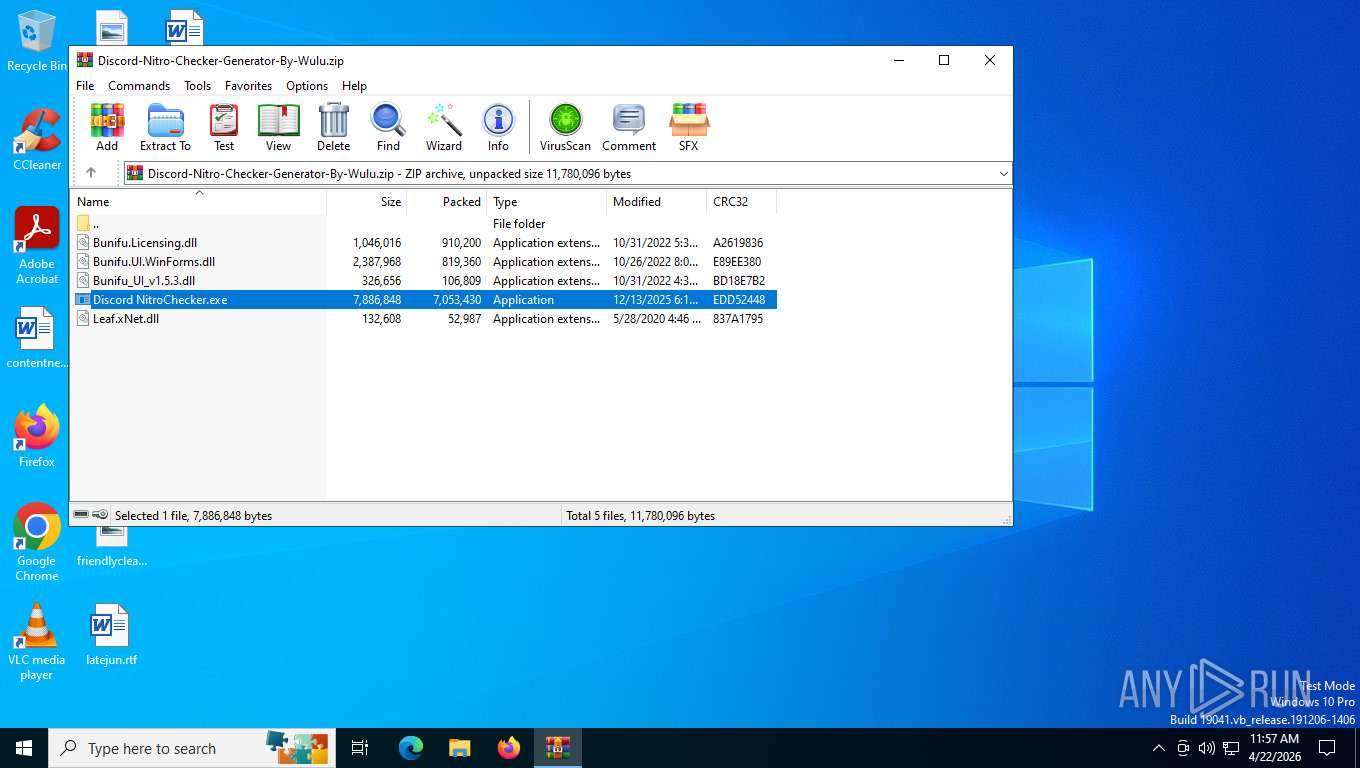
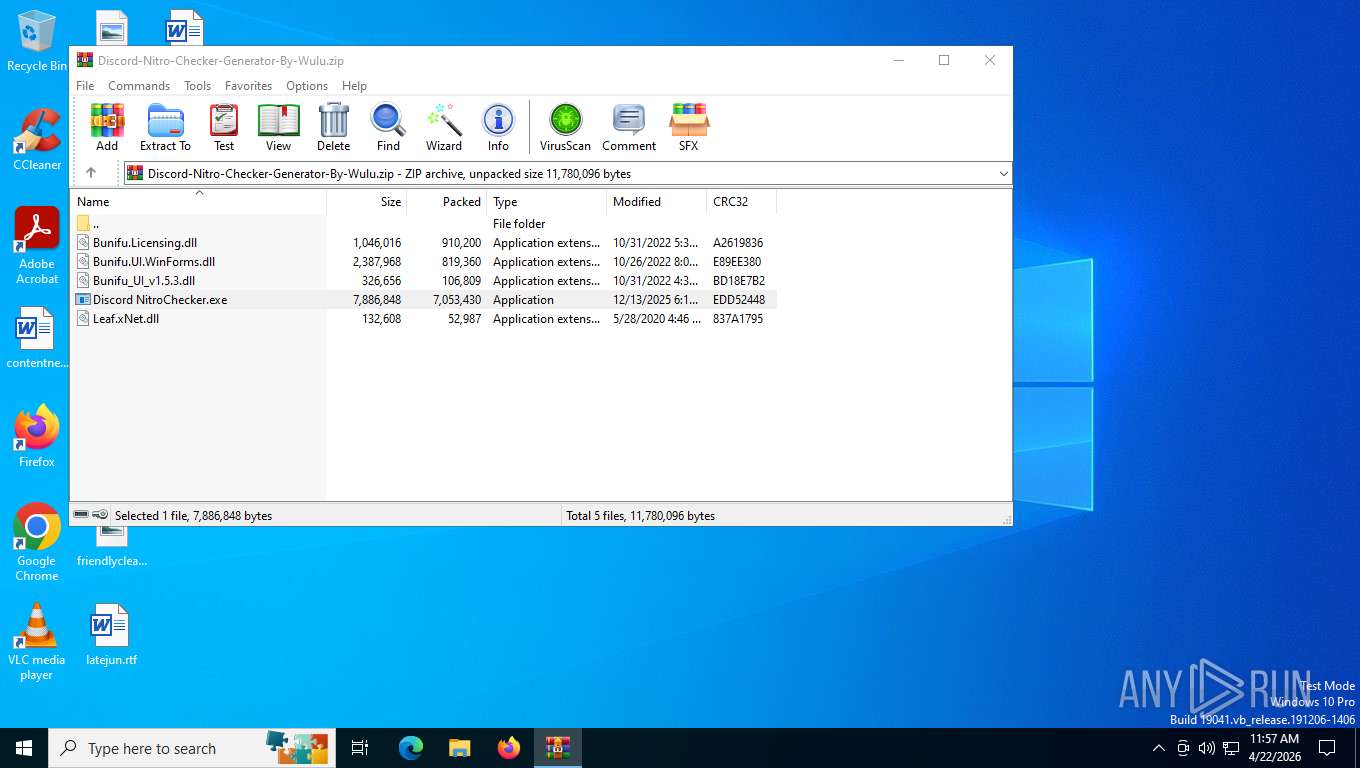
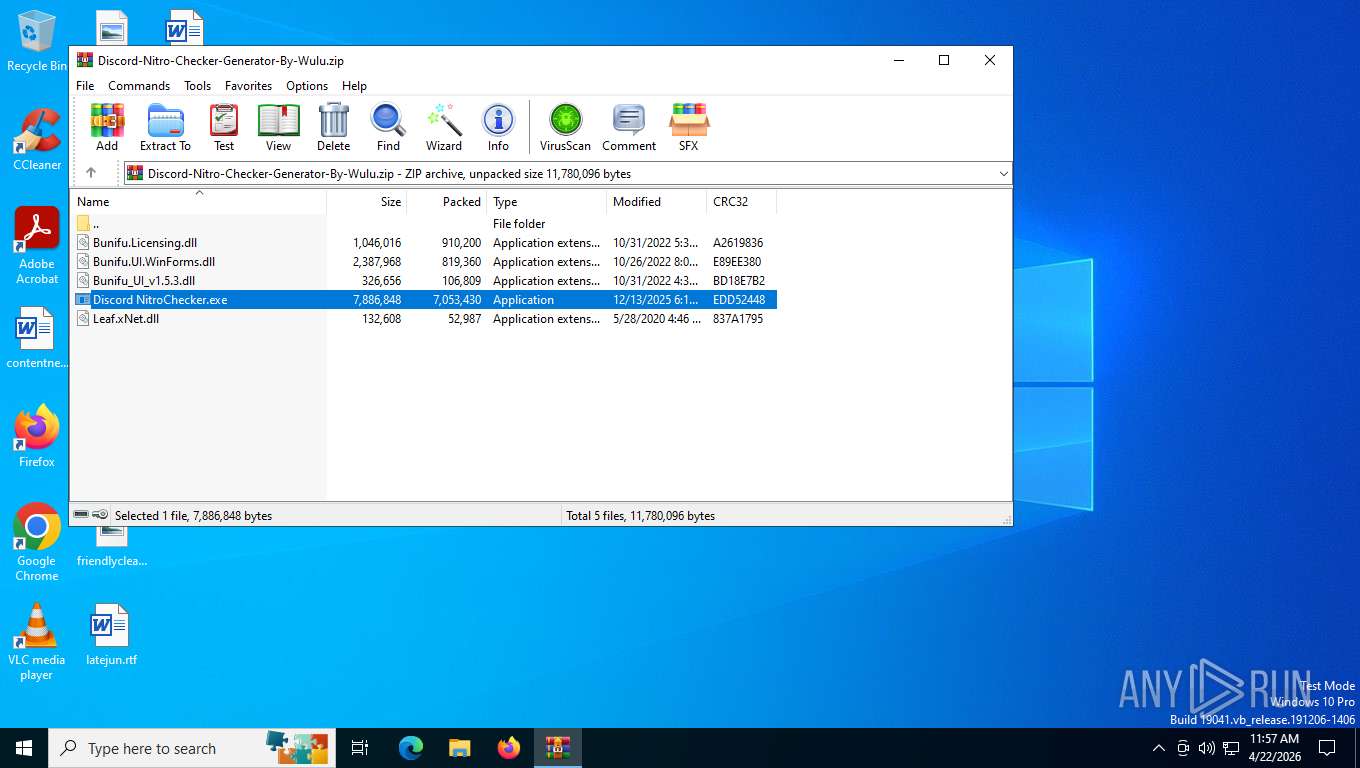
| File name: | Discord-Nitro-Checker-Generator-By-Wulu.zip |
| Full analysis: | https://app.any.run/tasks/d5b4e21d-af2e-49ac-945d-db901d49313d |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 22, 2026, 15:57:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3642386BFD91EB1EBAC6F0645326CEE2 |
| SHA1: | 6375D3AF49625C74AE1DD4A26A59F8131B01990A |
| SHA256: | 850C9A4DBD005F9142C4CE25CE867CA39CD18C47AEC6ACFEFA7E19EFBA6A4809 |
| SSDEEP: | 98304:bl+yJEZri/TO8c52uo3i0bojRY4gKtFR29M66OOc3rnaHmvy+/qed0kzFYoxfNDn:jJOCaY37PrP11W0sAKhlMfkc |
MALICIOUS
Runs injected code in another process
- defconsys.exe (PID: 4280)
- defconsys.exe (PID: 4956)
- defconsys.exe (PID: 4348)
Application was injected by another process
- explorer.exe (PID: 4696)
Changes the autorun value in the registry
- Discord NitroChecker.exe (PID: 7668)
- defconsys.exe (PID: 4280)
- Discord NitroChecker.exe (PID: 8160)
- defconsys.exe (PID: 4956)
- defconsys.exe (PID: 4348)
STEALC has been detected
- Setupxu.exe (PID: 4312)
- Setupxu.exe (PID: 7780)
Uses Task Scheduler to run other applications
- defconsys.exe (PID: 4280)
STEALC has been detected (SURICATA)
- msnetwork.exe (PID: 7660)
- Setupxu.exe (PID: 4312)
- Setupxu.exe (PID: 7780)
Modifies files in the Chrome extension folder
- sycuvhost.exe (PID: 664)
AMADEY has been detected (SURICATA)
- msnetwork.exe (PID: 7660)
- syshost.exe (PID: 736)
AMADEY has been detected (YARA)
- syshost.exe (PID: 736)
SUSPICIOUS
Reads the date of Windows installation
- Discord NitroChecker.exe (PID: 7668)
- defconsys.exe (PID: 4280)
- Discord NitroChecker.exe (PID: 8160)
- defconsys.exe (PID: 4956)
- defconsys.exe (PID: 4348)
The process creates files with name similar to system file names
- Discord NitroChecker.exe (PID: 7668)
The process executes files with name similar to system file names
- Discord NitroChecker.exe (PID: 7668)
- Discord NitroChecker.exe (PID: 8160)
Executable content was dropped or overwritten
- Discord NitroChecker.exe (PID: 7668)
- cftuniv.exe (PID: 4916)
- cftuniv.exe (PID: 2340)
Executes application which crashes
- Setupxu.exe (PID: 4312)
- Setupxu.exe (PID: 7780)
The process drops C-runtime libraries
- cftuniv.exe (PID: 4916)
- cftuniv.exe (PID: 2340)
Process drops python dynamic module
- cftuniv.exe (PID: 4916)
- cftuniv.exe (PID: 2340)
Application launched itself
- cftuniv.exe (PID: 4916)
- cftuniv.exe (PID: 2340)
Lists all scheduled tasks
- schtasks.exe (PID: 1352)
- schtasks.exe (PID: 7924)
- schtasks.exe (PID: 7668)
Loads Python modules
- cftuniv.exe (PID: 7916)
- cftuniv.exe (PID: 8176)
Contacting a server suspected of hosting an CnC
- Setupxu.exe (PID: 4312)
- syshost.exe (PID: 736)
- Setupxu.exe (PID: 7780)
There is functionality for enable RDP (YARA)
- syshost.exe (PID: 736)
The process executes via Task Scheduler
- syshost.exe (PID: 6864)
- defconsys.exe (PID: 4348)
INFO
Generic archive extractor
- WinRAR.exe (PID: 2304)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2304)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2304)
- Setupxu.exe (PID: 4312)
- defconsys.exe (PID: 4280)
- Discord NitroChecker.exe (PID: 7668)
- syshost.exe (PID: 736)
- Setupxu.exe (PID: 7780)
- defconsys.exe (PID: 4956)
- Discord NitroChecker.exe (PID: 8160)
- defconsys.exe (PID: 4348)
Reads the computer name
- Discord NitroChecker.exe (PID: 7668)
- msnetwork.exe (PID: 7660)
- Setupxu.exe (PID: 4312)
- defconsys.exe (PID: 4280)
- cftuniv.exe (PID: 4916)
- sycuvhost.exe (PID: 664)
- syshost.exe (PID: 736)
- Discord NitroChecker.exe (PID: 8160)
- Setupxu.exe (PID: 7780)
- defconsys.exe (PID: 4956)
- sycuvhost.exe (PID: 2364)
- cftuniv.exe (PID: 2340)
- defconsys.exe (PID: 4348)
Checks supported languages
- Discord NitroChecker.exe (PID: 7668)
- defconsys.exe (PID: 4280)
- syshost.exe (PID: 736)
- Setupxu.exe (PID: 4312)
- cftuniv.exe (PID: 4916)
- sycuvhost.exe (PID: 664)
- msnetwork.exe (PID: 7660)
- cftuniv.exe (PID: 7916)
- Discord NitroChecker.exe (PID: 8160)
- defconsys.exe (PID: 4956)
- syshost.exe (PID: 8020)
- Setupxu.exe (PID: 7780)
- msnetwork.exe (PID: 4692)
- cftuniv.exe (PID: 2340)
- sycuvhost.exe (PID: 2364)
- cftuniv.exe (PID: 8176)
- syshost.exe (PID: 6864)
- defconsys.exe (PID: 4348)
Process checks computer location settings
- Discord NitroChecker.exe (PID: 7668)
- defconsys.exe (PID: 4280)
- defconsys.exe (PID: 4956)
- Discord NitroChecker.exe (PID: 8160)
- defconsys.exe (PID: 4348)
Creates files or folders in the user directory
- Discord NitroChecker.exe (PID: 7668)
- WerFault.exe (PID: 880)
- WerFault.exe (PID: 2828)
Launching a file from a Registry key
- Discord NitroChecker.exe (PID: 7668)
- defconsys.exe (PID: 4280)
- Discord NitroChecker.exe (PID: 8160)
- defconsys.exe (PID: 4956)
- defconsys.exe (PID: 4348)
Create files in a temporary directory
- cftuniv.exe (PID: 4916)
- cftuniv.exe (PID: 2340)
The sample compiled with english language support
- cftuniv.exe (PID: 4916)
- cftuniv.exe (PID: 2340)
Reads Environment values
- syshost.exe (PID: 736)
Launching a file from Task Scheduler
- defconsys.exe (PID: 4280)
Reads the machine GUID from the registry
- cftuniv.exe (PID: 7916)
- cftuniv.exe (PID: 8176)
There is functionality for taking screenshot (YARA)
- syshost.exe (PID: 736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(736) syshost.exe
C2 (2)http://178.16.53.7
http://158.94.208.102
Endpoints (2)/cvdfnaFJBmC1/index.php
/cvdfnaFJBmC2/index.php
VigenereCipher
Key49f9a15edb340f721ba66e6133ed05fb
Strings (97)S-%lu-
853df70ab2
Lvpgale.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
Startup
cmd /C RMDIR /s/q
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
rundll32
Programs
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%USERPROFILE%
cred.dll|clip.dll|
cred.dll
clip.dll
http://
https://
/quiet
/Plugins/
&unit=
shell32.dll
kernel32.dll
GetNativeSystemInfo
ProgramData\
AVAST Software
Avira
Kaspersky Lab
Panda Security
Doctor Web
360TotalSecurity
Bitdefender
Norton
Sophos
Comodo
WinDefender
0123456789
Content-Type: multipart/form-data; boundary=----
------
Content-Disposition: form-data; name="data"; filename="
------
?scr=1
Content-Type: application/x-www-form-urlencoded
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
ComputerName
abcdefghijklmnopqrstuvwxyz0123456789-_
-unicode-
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
SYSTEM\ControlSet001\Services\BasicDisplay\Video
VideoID
\0000
DefaultSettings.XResolution
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CurrentBuild
rundll32.exe
"taskkill /f /im "
" && timeout 1 && del
&& Exit"
" && ren
Powershell.exe
-executionpolicy remotesigned -File "
shutdown -s -t 0
random
Keyboard Layout\Preload
00000419
00000422
00000423
0000043f
rundll32
cred.dll
https://
clip.dll
&& Exit"
Startup
-unicode-
Norton
?scr=1
------
Sophos
random
00000422
" && ren
\0000
------
/Plugins/
Avira
00000423
/quiet
&unit=
0000043f
VideoID
Comodo
S-%lu-
Programs
00000419
http://
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2022:10:31 13:38:52 |
| ZipCRC: | 0xbd18e7b2 |
| ZipCompressedSize: | 106809 |
| ZipUncompressedSize: | 326656 |
| ZipFileName: | Bunifu_UI_v1.5.3.dll |
Total processes
160
Monitored processes
30
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Users\admin\AppData\Roaming\sycuvhost.exe" | C:\Users\admin\AppData\Roaming\sycuvhost.exe | — | Discord NitroChecker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 736 | "C:\Users\admin\AppData\Roaming\syshost.exe" | C:\Users\admin\AppData\Roaming\syshost.exe | Discord NitroChecker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(736) syshost.exe C2 (2)http://178.16.53.7 http://158.94.208.102 Endpoints (2)/cvdfnaFJBmC1/index.php /cvdfnaFJBmC2/index.php VigenereCipher Key49f9a15edb340f721ba66e6133ed05fb Strings (97)S-%lu- 853df70ab2 Lvpgale.exe SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders Startup cmd /C RMDIR /s/q SOFTWARE\Microsoft\Windows\CurrentVersion\Run rundll32 Programs SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders %USERPROFILE% cred.dll|clip.dll| cred.dll clip.dll http:// https:// /quiet /Plugins/ &unit= shell32.dll kernel32.dll GetNativeSystemInfo ProgramData\ AVAST Software Avira Kaspersky Lab Panda Security Doctor Web 360TotalSecurity Bitdefender Norton Sophos Comodo WinDefender 0123456789 Content-Type: multipart/form-data; boundary=---- ------ Content-Disposition: form-data; name="data"; filename=" ------ ?scr=1 Content-Type: application/x-www-form-urlencoded SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName ComputerName abcdefghijklmnopqrstuvwxyz0123456789-_ -unicode- SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ SYSTEM\ControlSet001\Services\BasicDisplay\Video VideoID \0000 DefaultSettings.XResolution DefaultSettings.YResolution SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CurrentBuild rundll32.exe "taskkill /f /im " " && timeout 1 && del && Exit" " && ren Powershell.exe -executionpolicy remotesigned -File " shutdown -s -t 0 random Keyboard Layout\Preload 00000419 00000422 00000423 0000043f rundll32 cred.dll https:// clip.dll && Exit" Startup -unicode- Norton ?scr=1 ------ Sophos random 00000422 " && ren \0000 ------ /Plugins/ Avira 00000423 /quiet &unit= 0000043f VideoID Comodo S-%lu- Programs 00000419 http:// | |||||||||||||||
| 880 | C:\WINDOWS\system32\WerFault.exe -u -p 4312 -s 1008 | C:\Windows\System32\WerFault.exe | Setupxu.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | "C:\Windows\System32\schtasks.exe" /query /tn "Windows Defender Security" | C:\Windows\System32\schtasks.exe | — | defconsys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Discord-Nitro-Checker-Generator-By-Wulu.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Roaming\cftuniv.exe" | C:\Users\admin\AppData\Roaming\cftuniv.exe | Discord NitroChecker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Roaming\sycuvhost.exe" | C:\Users\admin\AppData\Roaming\sycuvhost.exe | — | Discord NitroChecker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2648 | "C:\Windows\System32\schtasks.exe" /create /sc minute /tn "Windows Defender Security" /tr "C:\Users\admin\AppData\Roaming\defconsys.exe" | C:\Windows\System32\schtasks.exe | — | defconsys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2828 | C:\WINDOWS\system32\WerFault.exe -u -p 7780 -s 988 | C:\Windows\System32\WerFault.exe | Setupxu.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 275
Read events
22 249
Write events
26
Delete events
0
Modification events
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Discord-Nitro-Checker-Generator-By-Wulu.zip | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4696) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000013010C |
| Operation: | write | Name: | VirtualDesktop |
Value: 100000003030445602603FA5B72DE44882A417B3949BF781 | |||
| (PID) Process: | (4312) Setupxu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
110
Suspicious files
8
Text files
193
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2304.9024\Bunifu.UI.WinForms.dll | executable | |
MD5:559E0BB848D95C95C29273BE8042B920 | SHA256:1566D30A46C499769D2CA541DEE7ADD696D633AD452ABF523DAB321F6FD566F4 | |||
| 7668 | Discord NitroChecker.exe | C:\Users\admin\AppData\Roaming\defconsys.exe | executable | |
MD5:BDCA617311A84F28B6168B0499056AFB | SHA256:FB7A8F36FA04FBBEDBE153821628187C41D60AEAFE145CF3443A64048AEF85CB | |||
| 4696 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | text | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 2304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2304.9024\Discord NitroChecker.exe | executable | |
MD5:4F742ABAB35500A3754EB258624BC884 | SHA256:3EC2BF9A32E3676DC89DE0D3EB3C92CB20784E4BEF7A04F9770621D14B156113 | |||
| 2304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2304.9024\Bunifu.Licensing.dll | executable | |
MD5:A83753C490E10C1BD49F6699DCBC4DDE | SHA256:77F8886A28AEE770E1EE86280E9E254655A0BE4440D3C480C7E9992EB7A2E1EA | |||
| 2304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2304.9024\Leaf.xNet.dll | executable | |
MD5:EA87F37E78FB9AF4BF805F6E958F68F4 | SHA256:DE9AEA105F31F3541CBC5C460B0160D0689A2872D80748CA1456E6E223F0A4AA | |||
| 2304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2304.9024\Bunifu_UI_v1.5.3.dll | executable | |
MD5:15B2639E04E5AB17CEED3BF4DC61A68A | SHA256:4C940E989A91016C1A1AEB456D9288E573C8C1BF5B64E3E38A868F98F7F2385E | |||
| 7668 | Discord NitroChecker.exe | C:\Users\admin\AppData\Roaming\msnetwork.exe | executable | |
MD5:9470E1A585B667EE743C4EF561CC7DE9 | SHA256:B981DE8AD8A8331BCDF683D4B1D711EF6FECD04C7F8D049BAF21228E58714D22 | |||
| 7668 | Discord NitroChecker.exe | C:\Users\admin\AppData\Roaming\Setupxu.exe | executable | |
MD5:45ED483B023BA254BE6ABC14262BBE12 | SHA256:8E3DFCAC7AFF05BEE60621C43FFCEF7046568C0A3F50922CCA876AE633E59D30 | |||
| 7668 | Discord NitroChecker.exe | C:\Users\admin\AppData\Roaming\syshost.exe | executable | |
MD5:C765FC5780A0F6C4571CA16A0A8B033C | SHA256:163FF316F1D211F3F91CECB272931C16733A1D1B4994584BC21011DB945272F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
61
DNS requests
14
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7660 | msnetwork.exe | POST | 404 | 196.251.107.61:80 | http://196.251.107.61/xvzpjyddlu/getdata.php | GB | xml | 341 b | malicious |
7660 | msnetwork.exe | POST | 404 | 196.251.107.61:80 | http://196.251.107.61/xvzpjyddlu/getdata.php | GB | xml | 341 b | malicious |
4312 | Setupxu.exe | POST | 404 | 196.251.107.23:80 | http://196.251.107.23/7ffc7a279c17c091.php | GB | xml | 341 b | malicious |
7660 | msnetwork.exe | POST | 404 | 196.251.107.61:80 | http://196.251.107.61/xvzpjyddlu/getdata.php | GB | xml | 341 b | malicious |
7660 | msnetwork.exe | POST | 404 | 196.251.107.61:80 | http://196.251.107.61/xvzpjyddlu/getdata.php | GB | xml | 341 b | malicious |
5316 | svchost.exe | POST | 404 | 40.126.31.131:443 | https://login.live.com/RST2.srf | US | xml | 341 b | whitelisted |
5316 | svchost.exe | POST | 404 | 40.126.31.131:443 | https://login.live.com/RST2.srf | US | xml | 341 b | whitelisted |
736 | syshost.exe | POST | 404 | 178.16.53.7:80 | http://178.16.53.7/cvdfnaFJBmC1/index.php | SC | xml | 341 b | malicious |
736 | syshost.exe | POST | 404 | 158.94.208.102:80 | http://158.94.208.102/cvdfnaFJBmC2/index.php | SC | xml | 341 b | malicious |
7660 | msnetwork.exe | POST | 404 | 196.251.107.61:80 | http://196.251.107.61/xvzpjyddlu/getdata.php | GB | xml | 341 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4872 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.241.219:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7660 | msnetwork.exe | 196.251.107.61:80 | — | FEMOIT | GB | malicious |
4312 | Setupxu.exe | 196.251.107.23:80 | — | FEMOIT | GB | unknown |
880 | WerFault.exe | 135.233.45.222:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
51.240.178.74.in-addr.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7660 | msnetwork.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 44 |
7660 | msnetwork.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Amadey associated URI (/xvzpjyddlu/getdata.php) |
4312 | Setupxu.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 44 |
7660 | msnetwork.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Amadey associated URI (/xvzpjyddlu/getdata.php) |
4312 | Setupxu.exe | Malware Command and Control Activity Detected | ET MALWARE StealC CnC Activity (POST) |
4312 | Setupxu.exe | Malware Command and Control Activity Detected | ET MALWARE StealC_V2 CnC Activity (POST) |
7660 | msnetwork.exe | A Network Trojan was detected | ET MALWARE HTTP Request to Known Stealer Payload Delivery Host |
7660 | msnetwork.exe | A Network Trojan was detected | ET MALWARE HTTP Request to Known Stealer Payload Delivery Host |
7660 | msnetwork.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Amadey associated URI (/xvzpjyddlu/getdata.php) |
7660 | msnetwork.exe | A Network Trojan was detected | ET MALWARE HTTP Request to Known Stealer Payload Delivery Host |