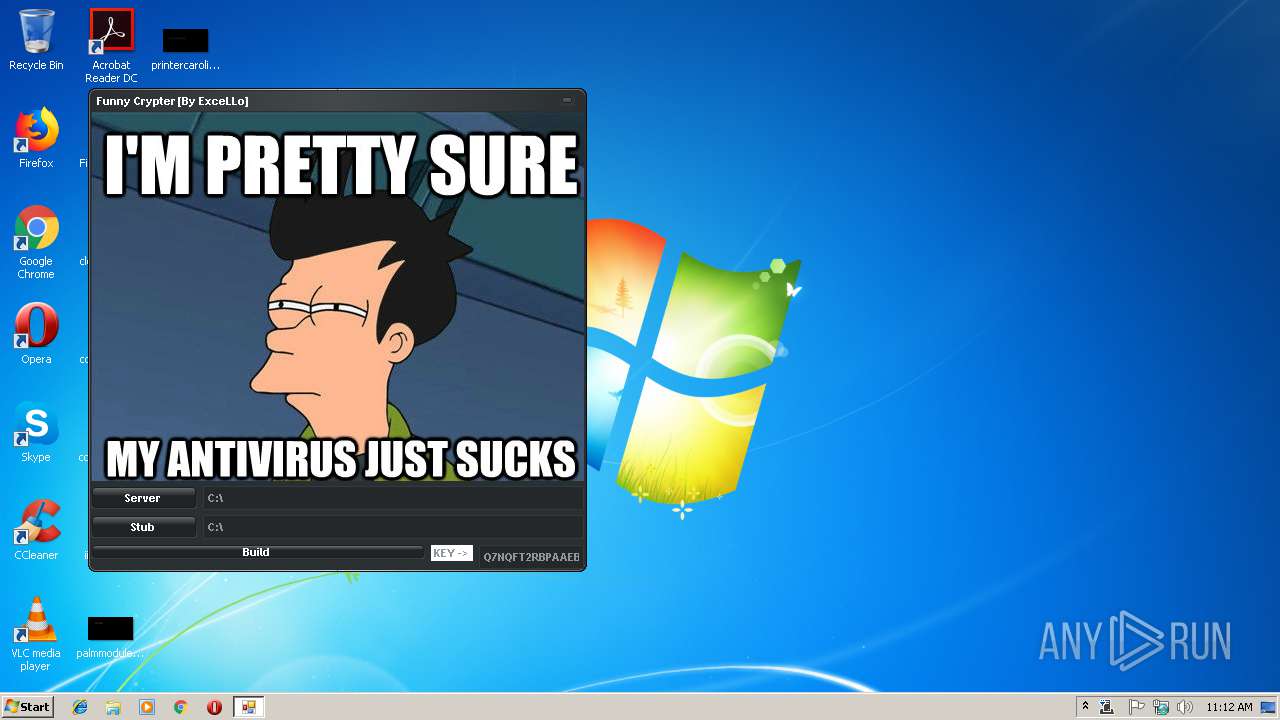
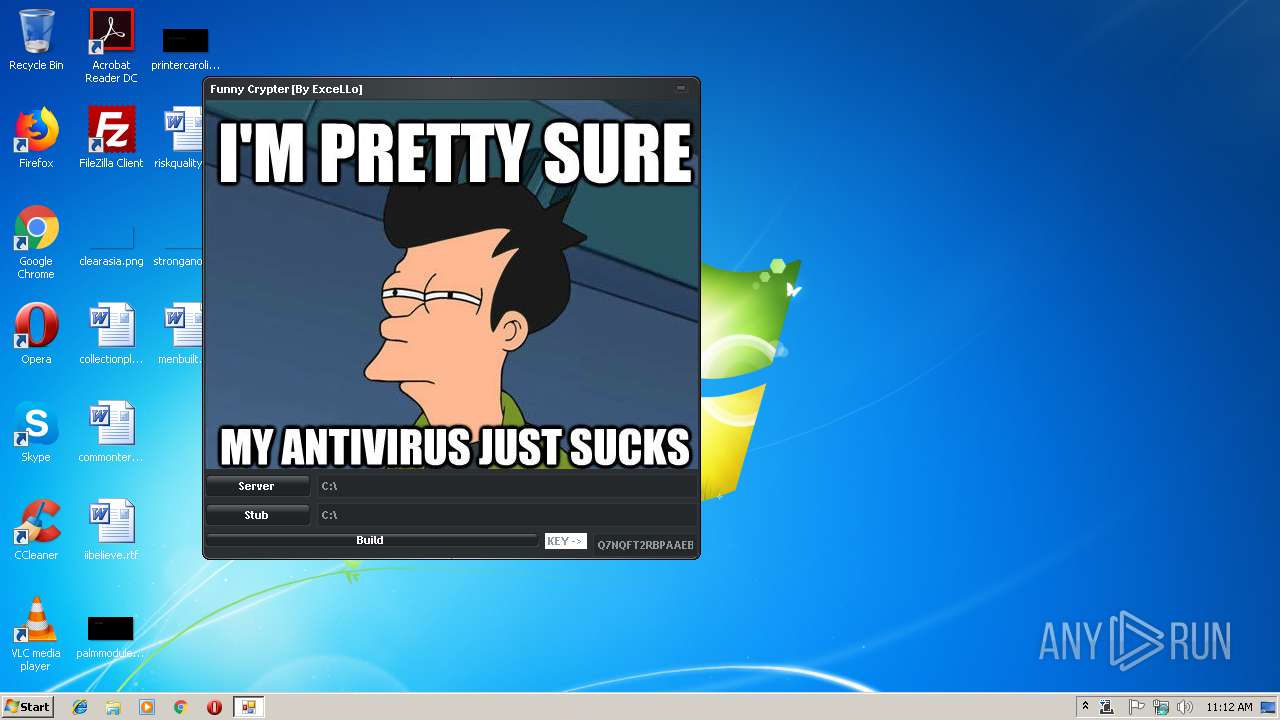
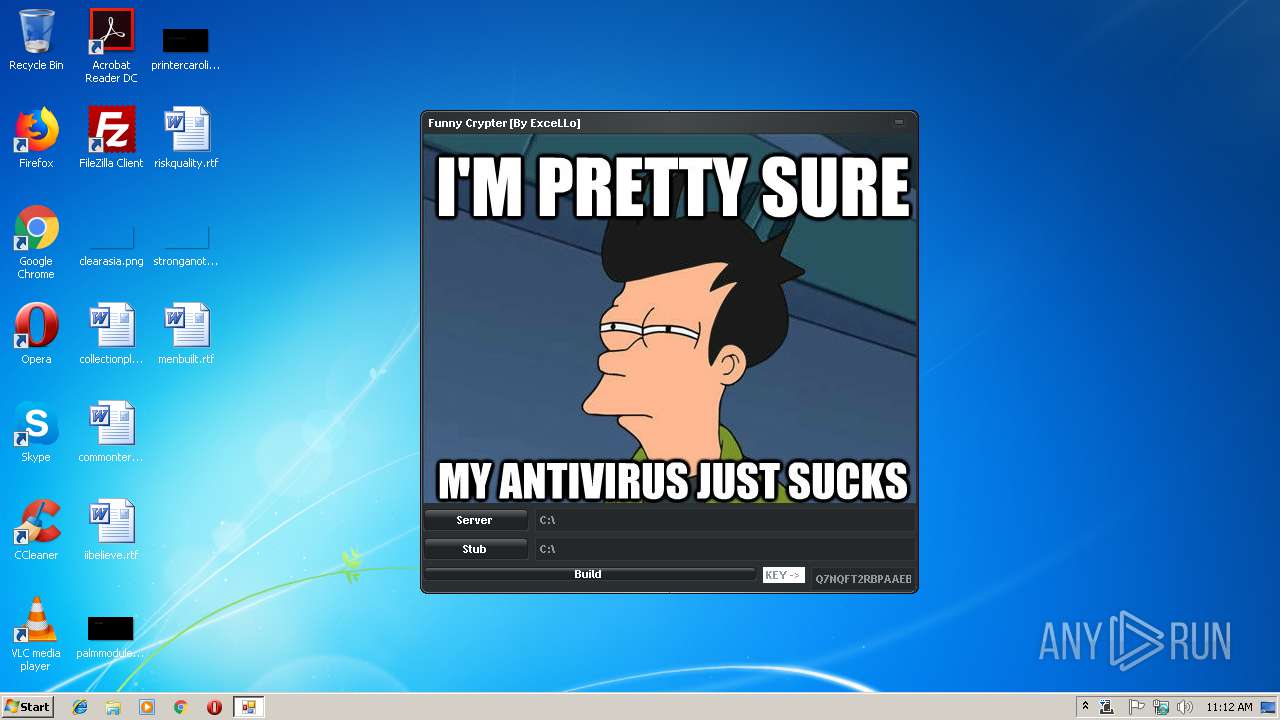
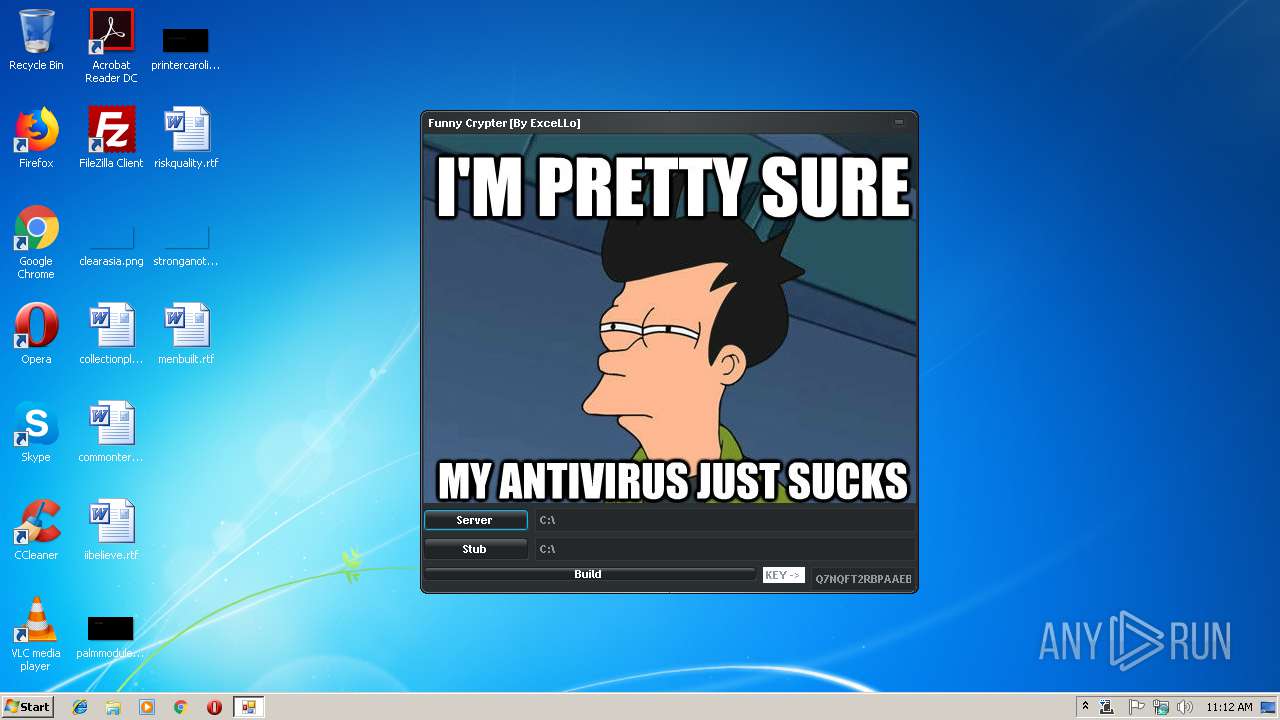
| File name: | Funny Crypter [Mod V3xD].exe |
| Full analysis: | https://app.any.run/tasks/3927ff79-eac7-4e6b-b9d4-662bd5795857 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | March 14, 2019, 11:12:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D58BEDBBD9D4729BF6BC01EB04CECDDC |
| SHA1: | D436352B9984C741BF3E7CBDF4A4F72F32003CEE |
| SHA256: | 84EF81416CE44826148A2635D2972EBA5F187D68A66FA812F365EE7A1333416B |
| SSDEEP: | 24576:sBJhYySVWkBdqz5XAFHK2XhdaNmqJmxx11xMoxZ9AmrY4OPJxuVblDnylj:2JAVWoqz5wFHK2naNjSrMoZ9/rYtBop6 |
MALICIOUS
Orcus was detected
- MServices.exe (PID: 2564)
Application was dropped or rewritten from another process
- tmpE6F9.tmp.exe (PID: 3964)
SUSPICIOUS
Executable content was dropped or overwritten
- Funny Crypter [Mod V3xD].exe (PID: 3168)
- MServices.exe (PID: 3092)
Application launched itself
- MServices.exe (PID: 3092)
Starts itself from another location
- Funny Crypter [Mod V3xD].exe (PID: 3168)
Connects to unusual port
- MServices.exe (PID: 2564)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:04 01:11:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 1240064 |
| InitializedDataSize: | 174080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x130bce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Funny Crypter mod V3xD |
| CompanyName: | Funny Crypter by ExceLLo |
| FileDescription: | Funny Crypter by ExceLLo.exe |
| FileVersion: | 1.0.0.0 |
| InternalName: | Crypted.exe |
| LegalCopyright: | Copyright © 2017 |
| OriginalFileName: | Crypted.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Mar-2019 00:11:38 |
| Comments: | Funny Crypter mod V3xD |
| CompanyName: | Funny Crypter by ExceLLo |
| FileDescription: | Funny Crypter by ExceLLo.exe |
| FileVersion: | 1.0.0.0 |
| InternalName: | Crypted.exe |
| LegalCopyright: | Copyright © 2017 |
| OriginalFilename: | Crypted.exe |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Mar-2019 00:11:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0012EBD4 | 0x0012EC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.94534 |
.rsrc | 0x00132000 | 0x0002A480 | 0x0002A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.77963 |
.reloc | 0x0015E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.38231 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.17441 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.80979 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.61649 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 1.543 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.53203 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.90508 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 3.96457 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.9976 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
33
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2564 | "C:\Users\admin\AppData\Local\Temp\MServices.exe" | C:\Users\admin\AppData\Local\Temp\MServices.exe | MServices.exe | ||||||||||||
User: admin Company: Funny Crypter by ExceLLo Integrity Level: MEDIUM Description: Funny Crypter by ExceLLo.exe Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\MServices.exe" | C:\Users\admin\AppData\Local\Temp\MServices.exe | Funny Crypter [Mod V3xD].exe | ||||||||||||
User: admin Company: Funny Crypter by ExceLLo Integrity Level: MEDIUM Description: Funny Crypter by ExceLLo.exe Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\Funny Crypter [Mod V3xD].exe" | C:\Users\admin\AppData\Local\Temp\Funny Crypter [Mod V3xD].exe | explorer.exe | ||||||||||||
User: admin Company: Funny Crypter by ExceLLo Integrity Level: MEDIUM Description: Funny Crypter by ExceLLo.exe Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
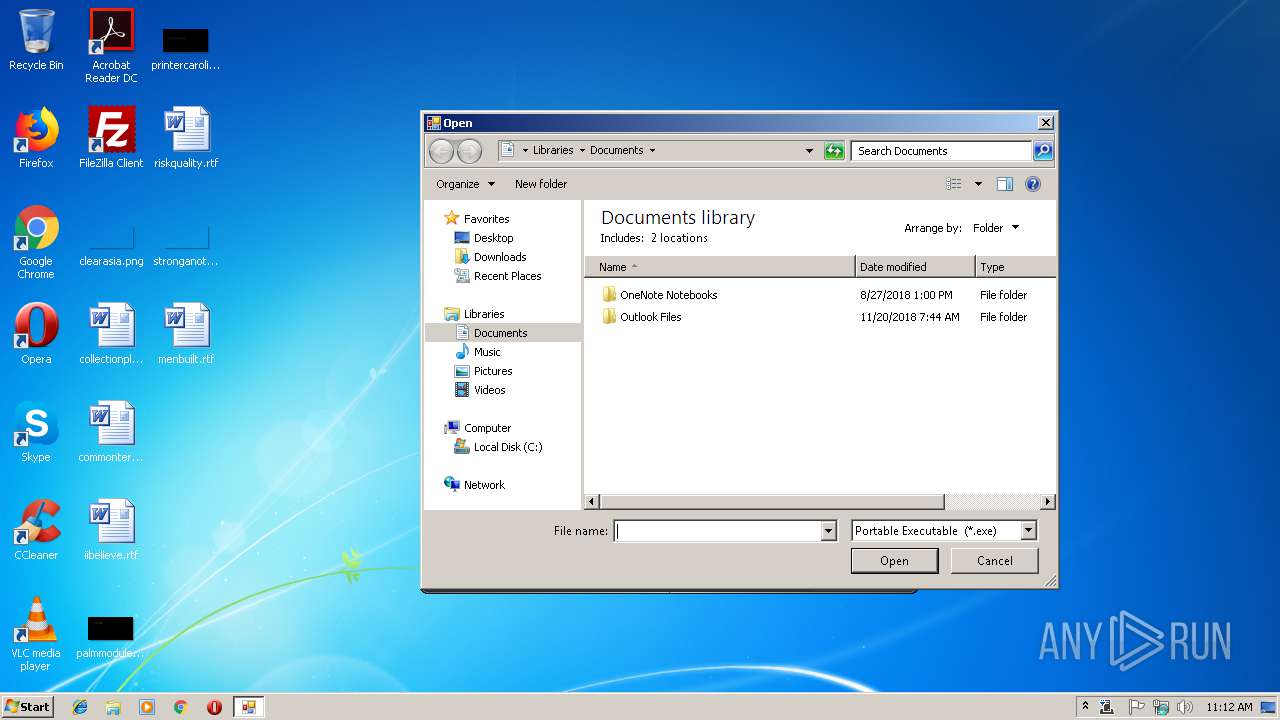
| 3964 | "C:\Users\admin\AppData\Local\Temp\tmpE6F9.tmp.exe" | C:\Users\admin\AppData\Local\Temp\tmpE6F9.tmp.exe | — | MServices.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Funny Crypter mod V3xD Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 253
Read events
1 216
Write events
36
Delete events
1
Modification events
| (PID) Process: | (3168) Funny Crypter [Mod V3xD].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Run\CurrentVersion |
| Operation: | write | Name: | MServices.exe |
Value: C:\Users\admin\AppData\Local\Temp\MServices.exe | |||
| (PID) Process: | (3168) Funny Crypter [Mod V3xD].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3168) Funny Crypter [Mod V3xD].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3092) MServices.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3092) MServices.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3964) tmpE6F9.tmp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3964) tmpE6F9.tmp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3964) tmpE6F9.tmp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3964) tmpE6F9.tmp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3964) tmpE6F9.tmp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | Funny Crypter [Mod V3xD].exe | C:\Users\admin\AppData\Local\Temp\MServices.exe | executable | |
MD5:— | SHA256:— | |||
| 3092 | MServices.exe | C:\Users\admin\AppData\Local\Temp\tmpE6F9.tmp.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | MServices.exe | 162.200.139.146:1604 | galrov.warzonedns.com | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
galrov.warzonedns.com |
| malicious |
Threats
1 ETPRO signatures available at the full report