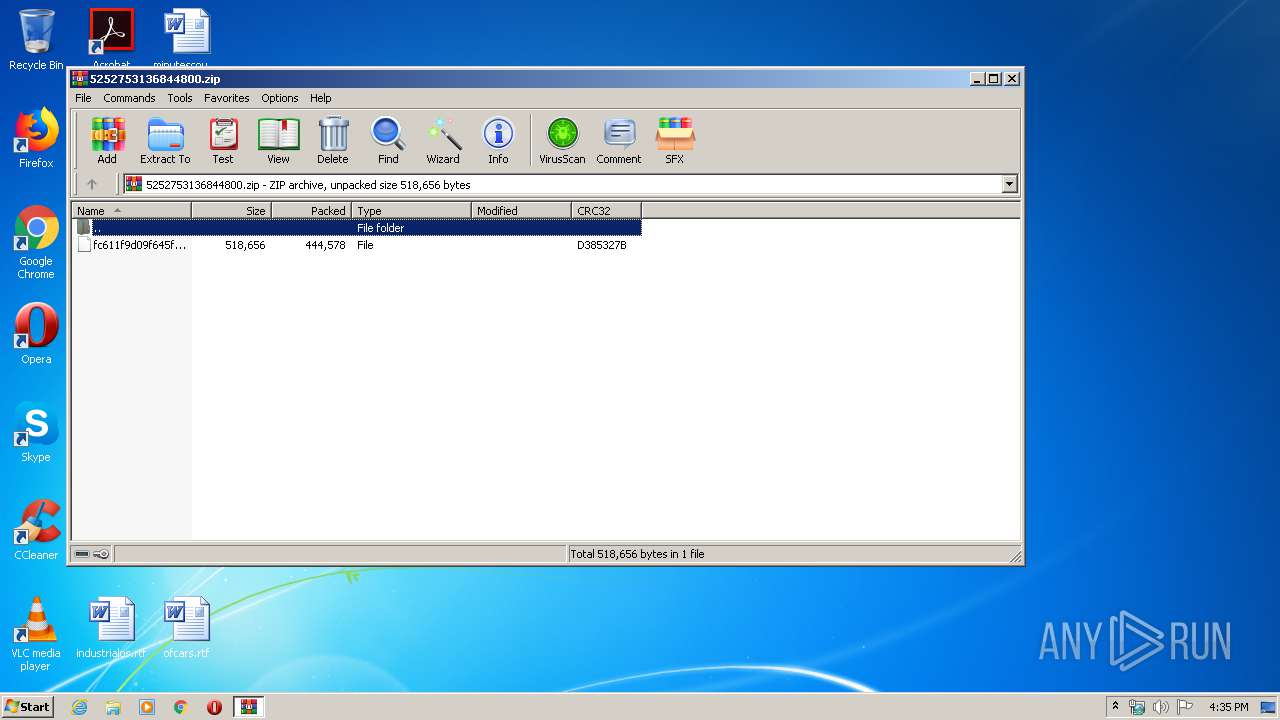
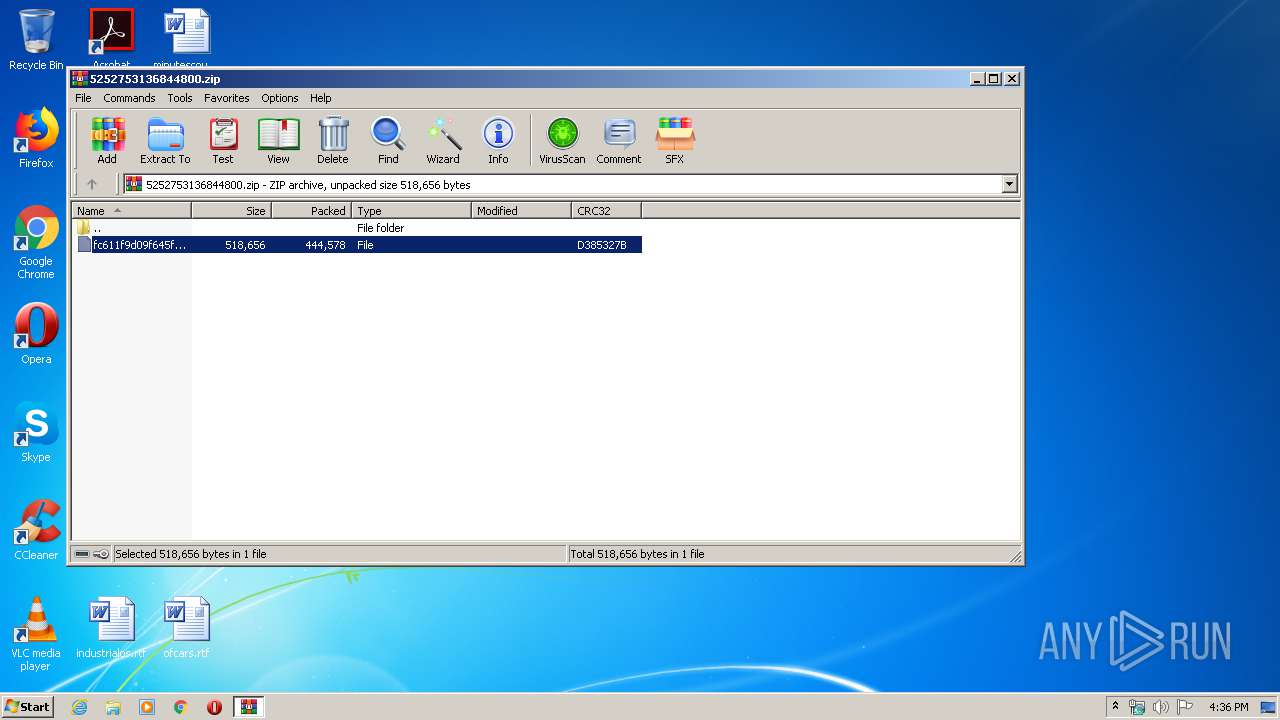
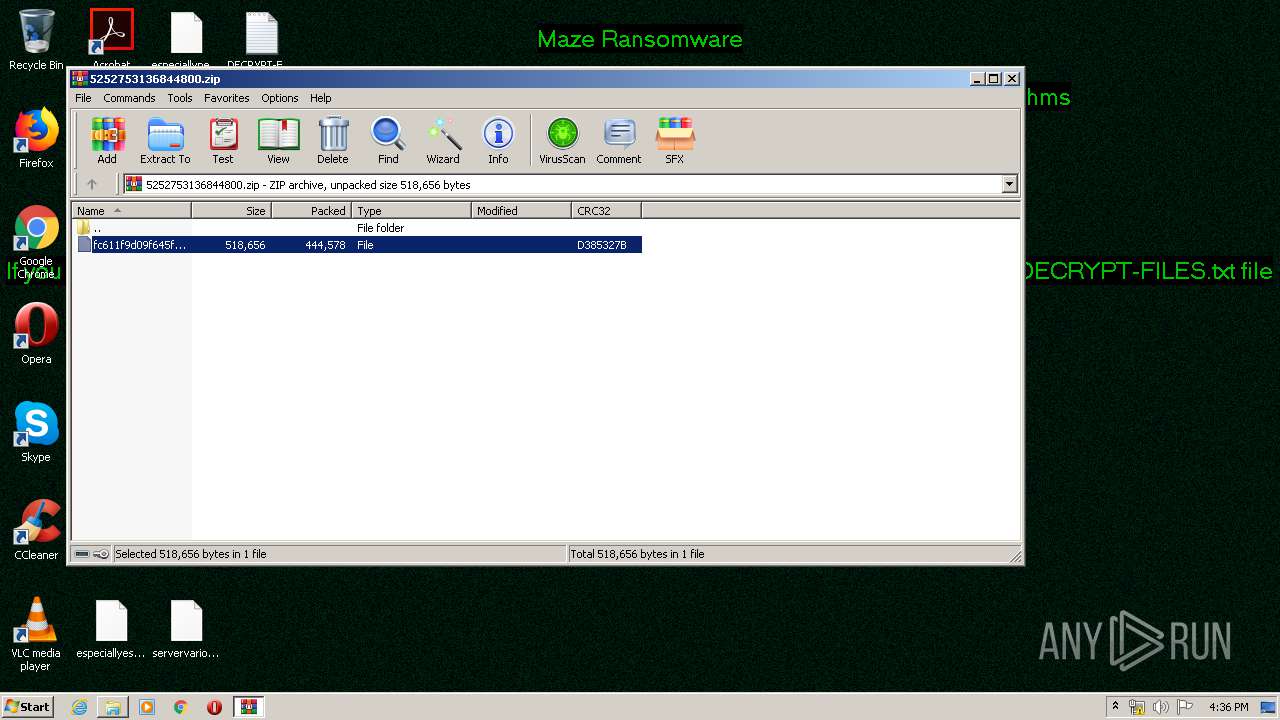
| File name: | 5252753136844800.zip |
| Full analysis: | https://app.any.run/tasks/36cfdc1d-805b-4c3a-a758-f3e36c530425 |
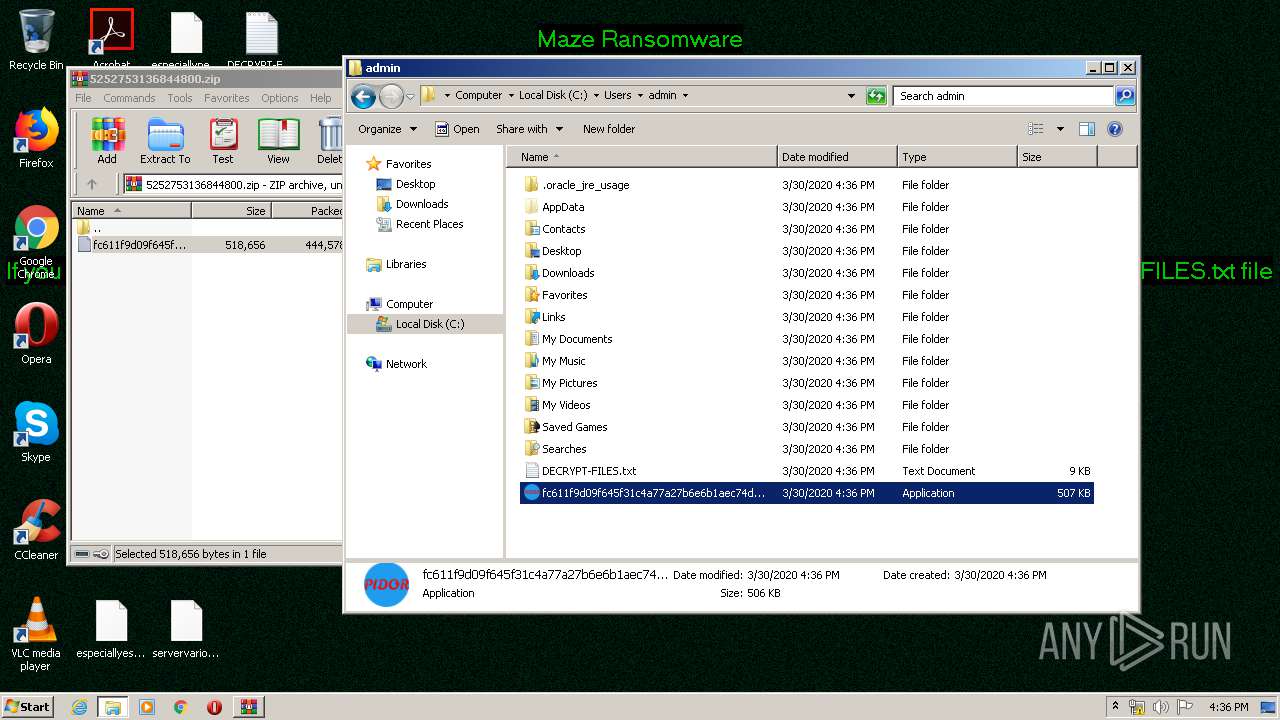
| Verdict: | Malicious activity |
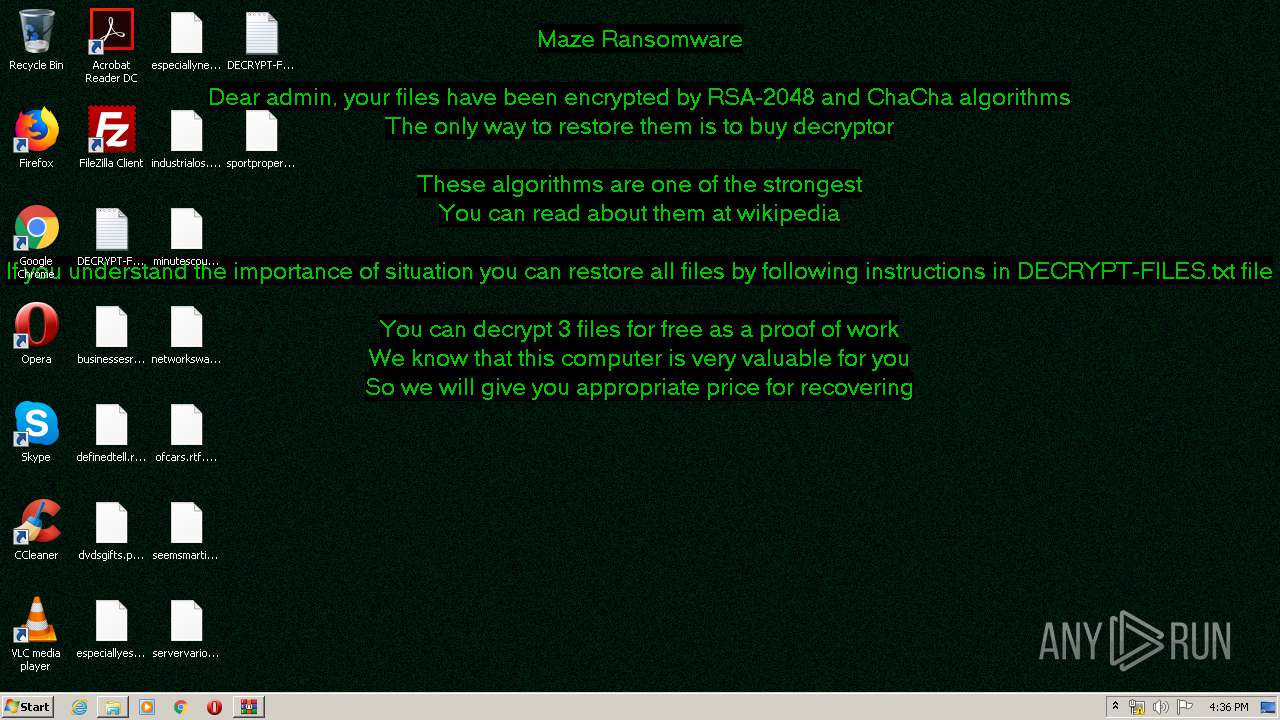
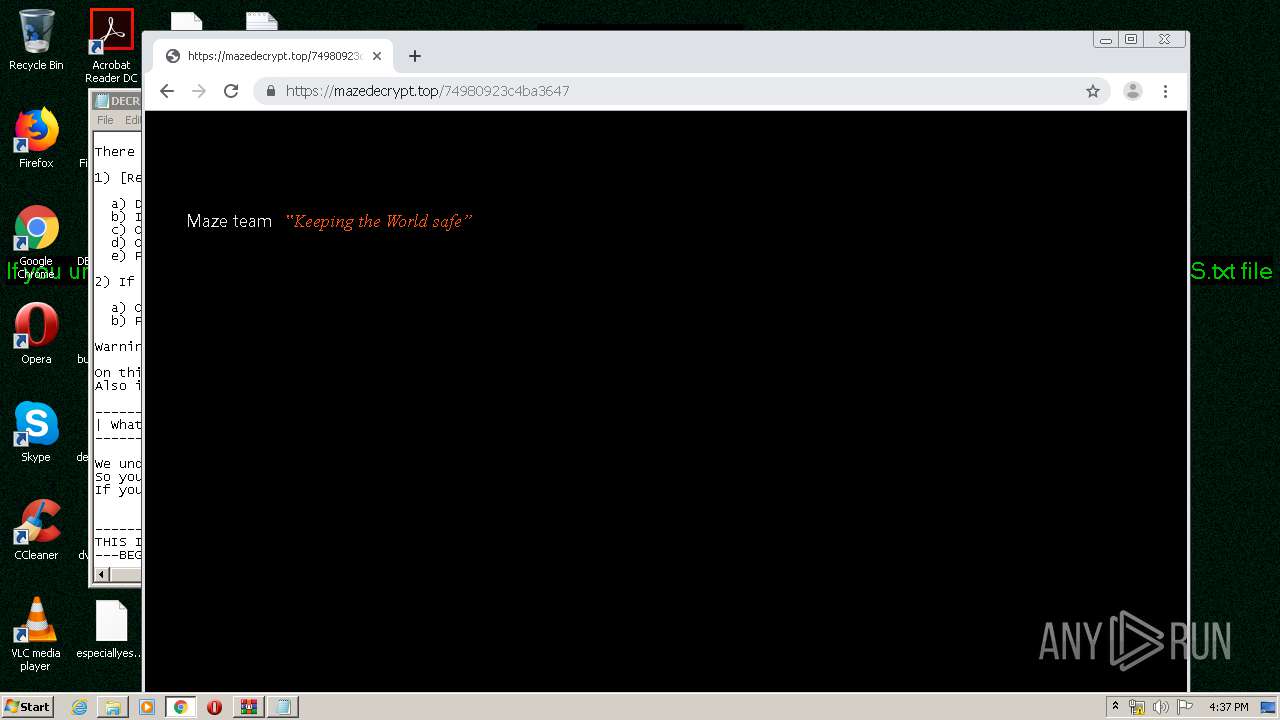
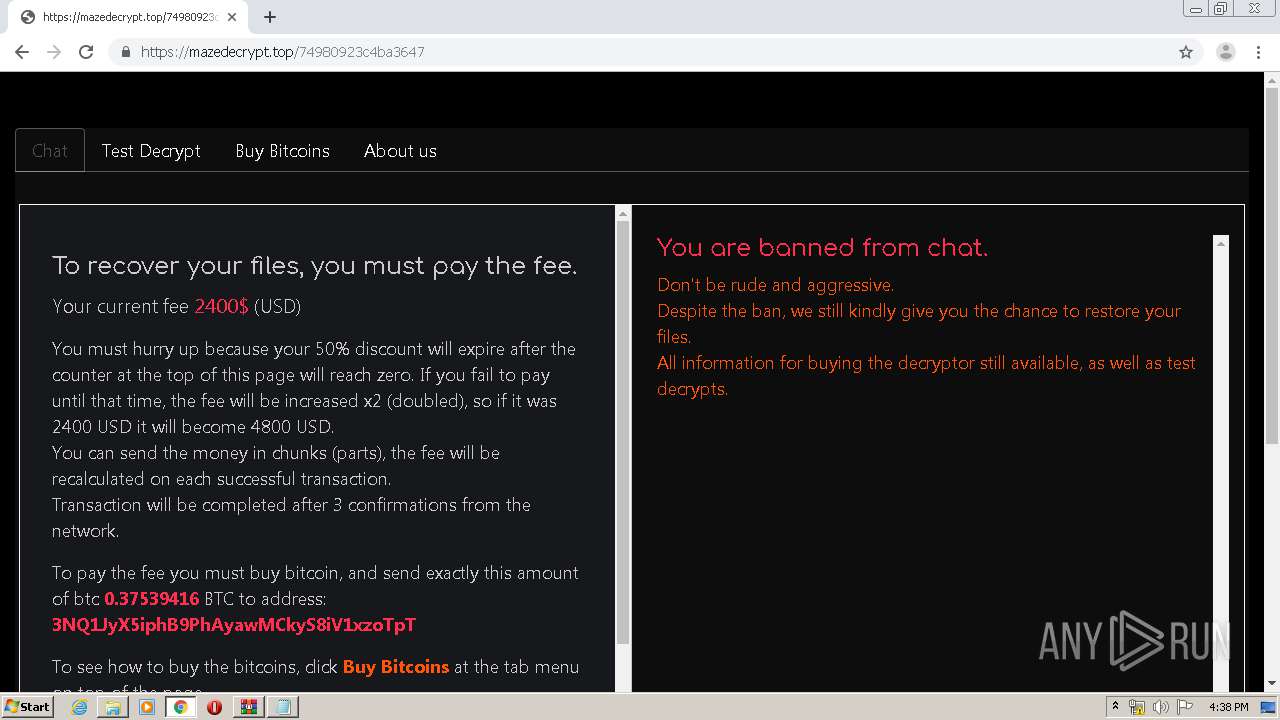
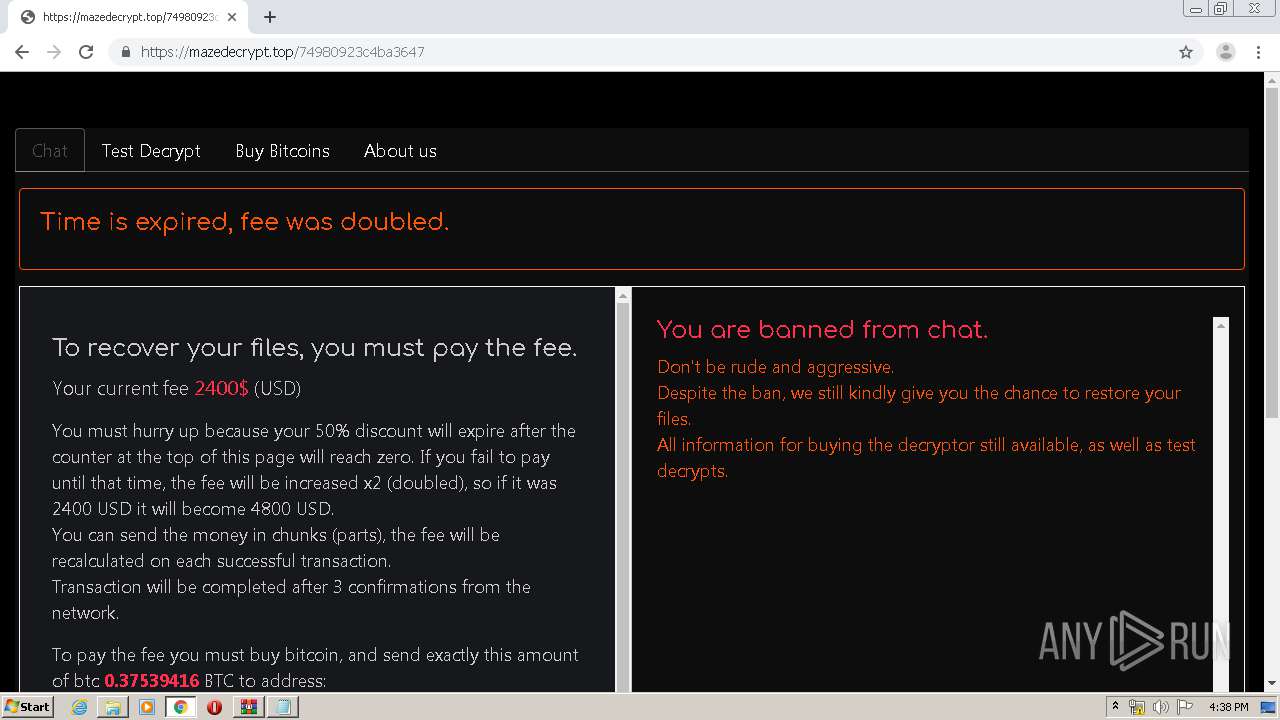
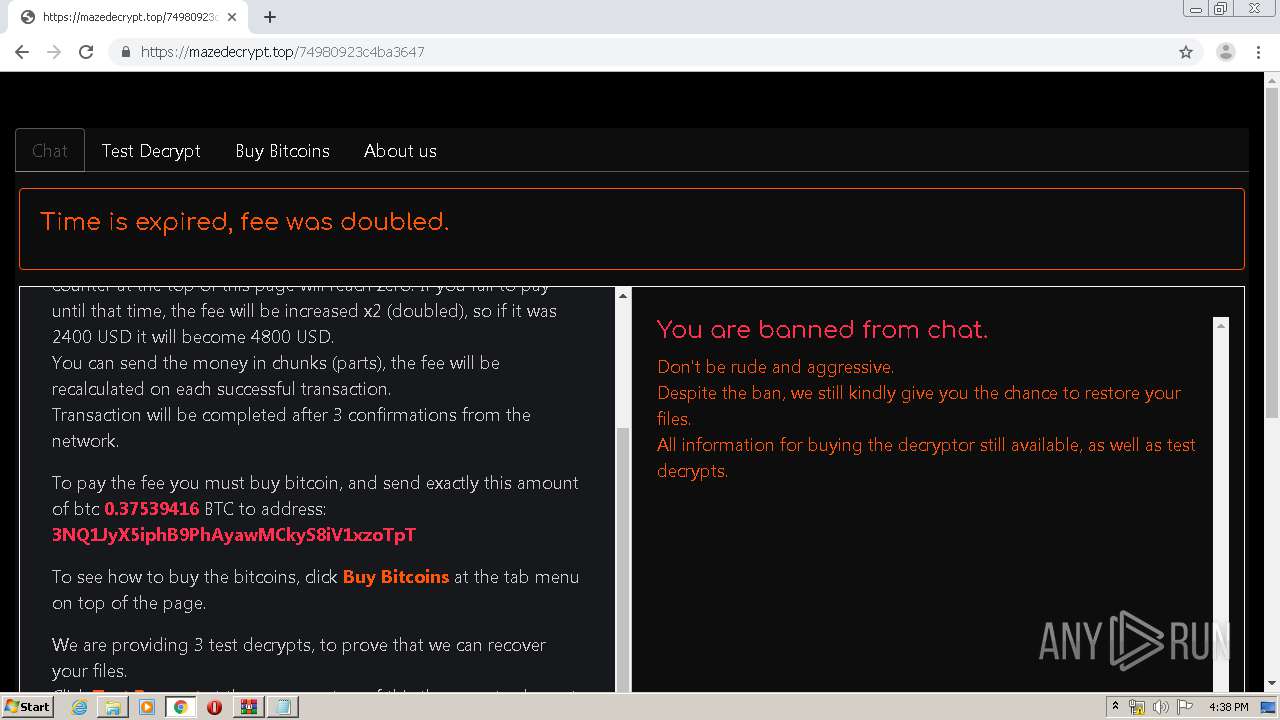
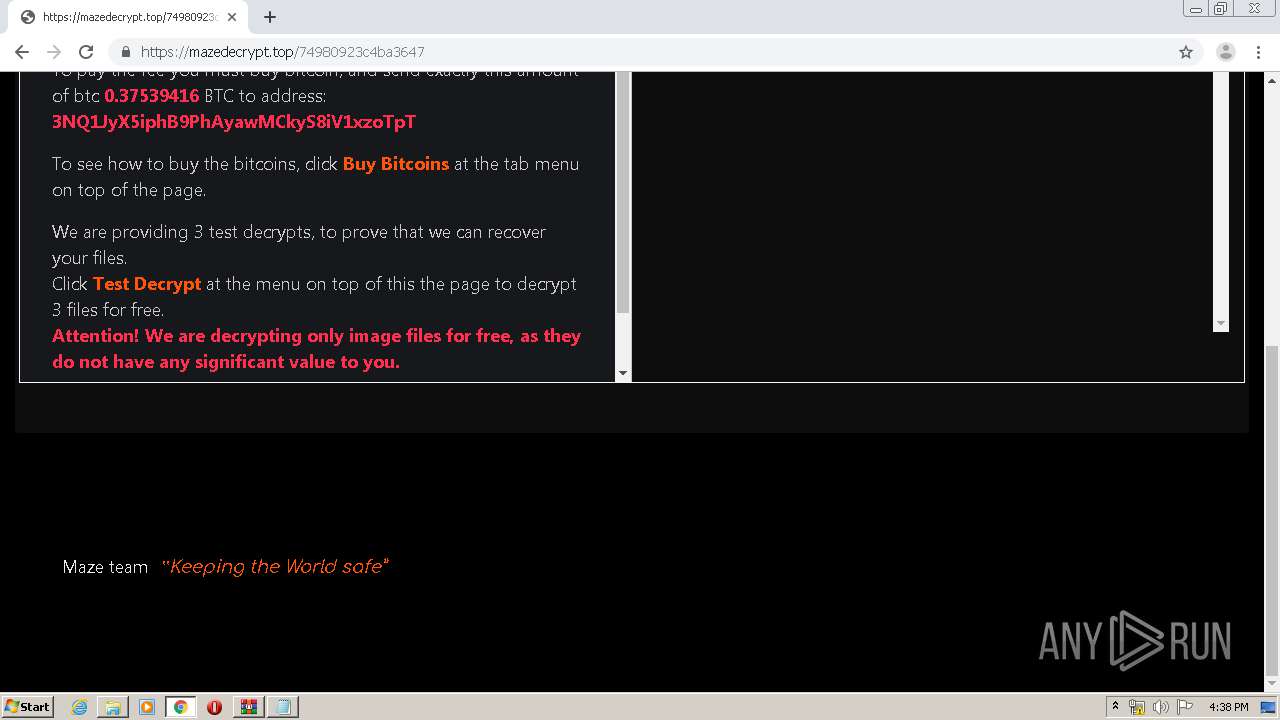
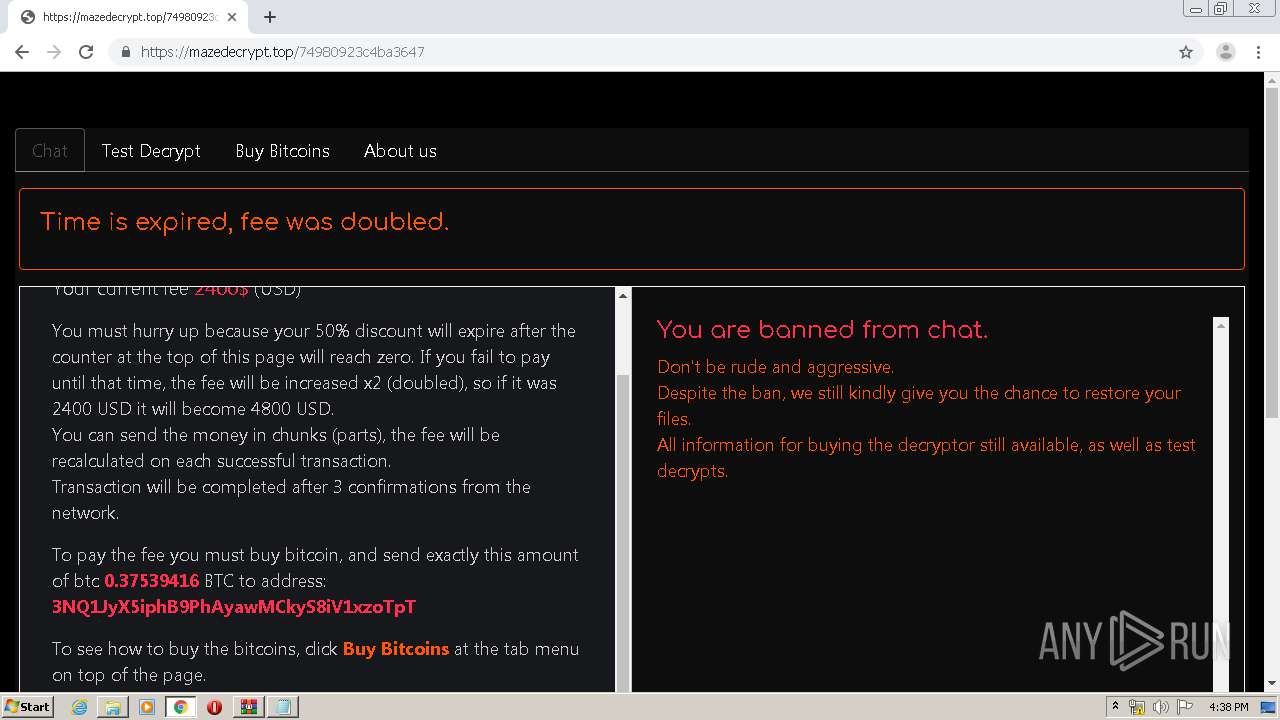
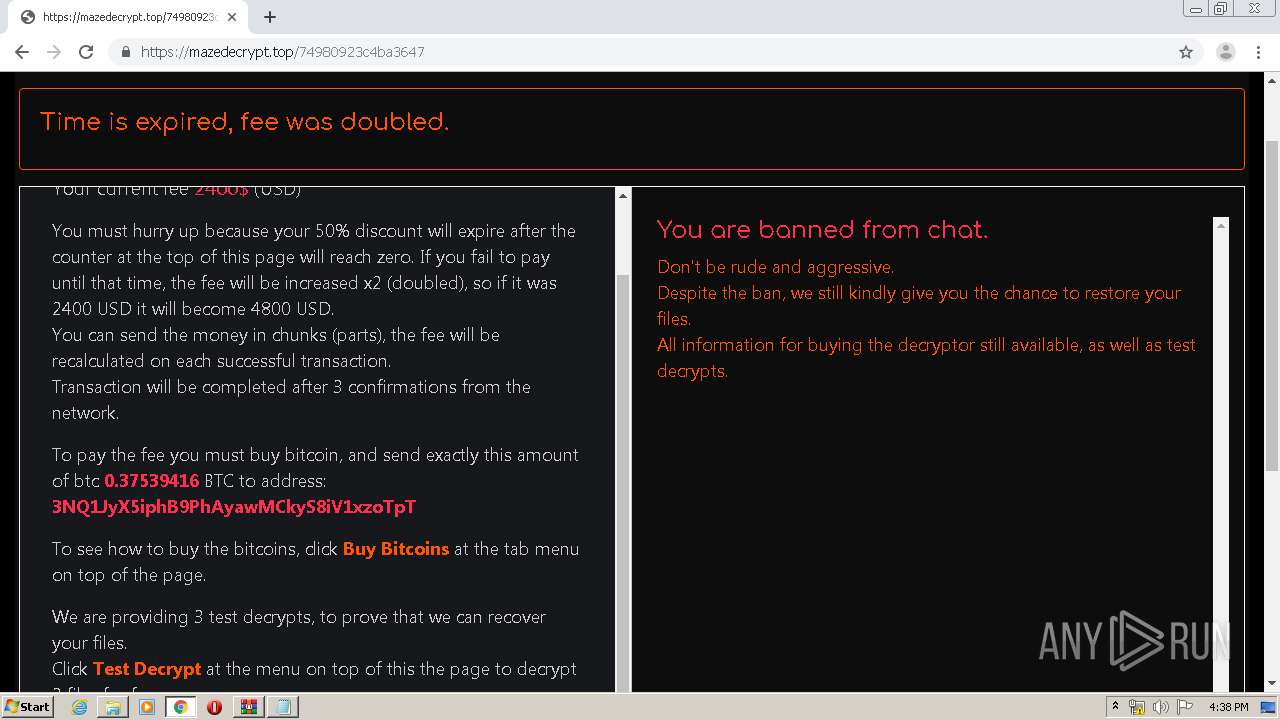
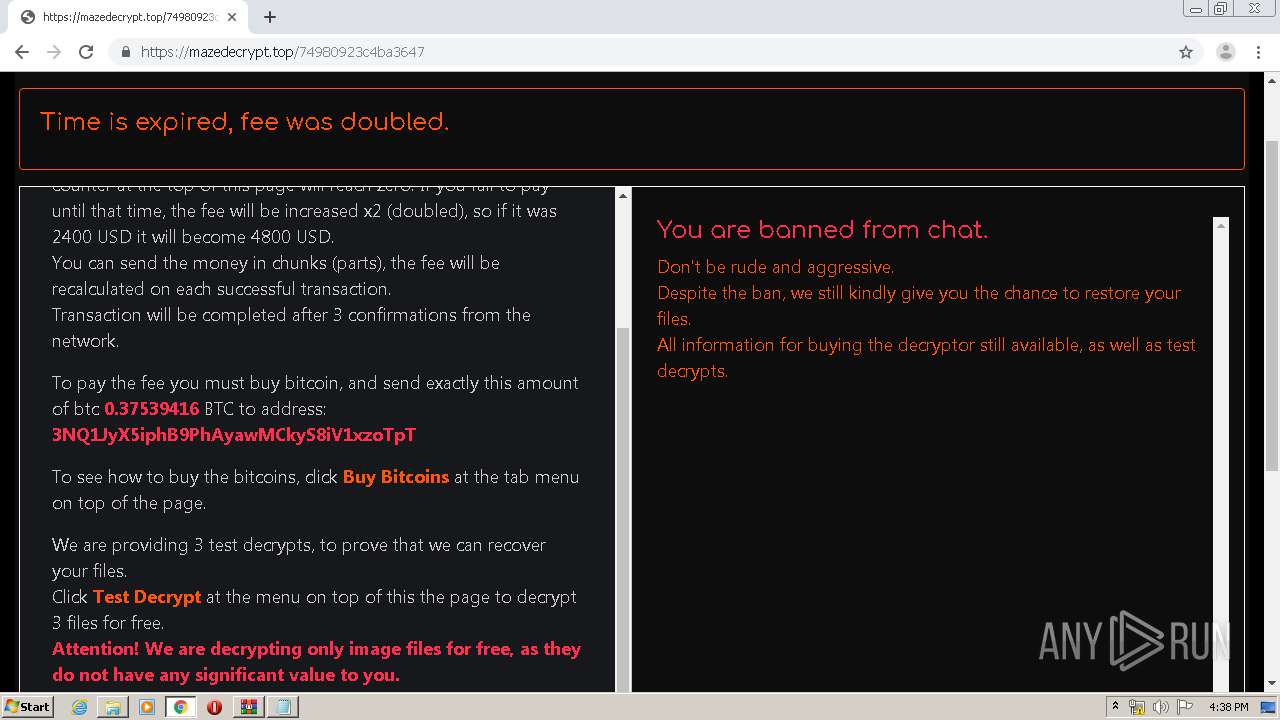
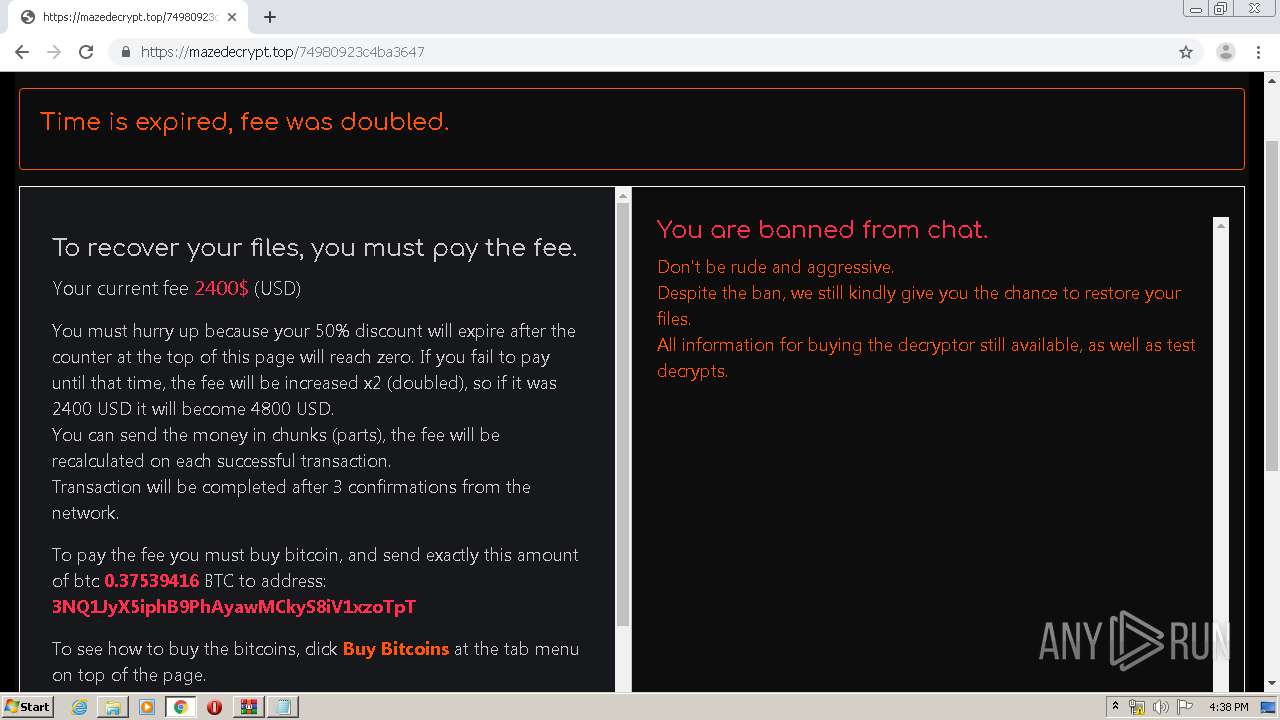
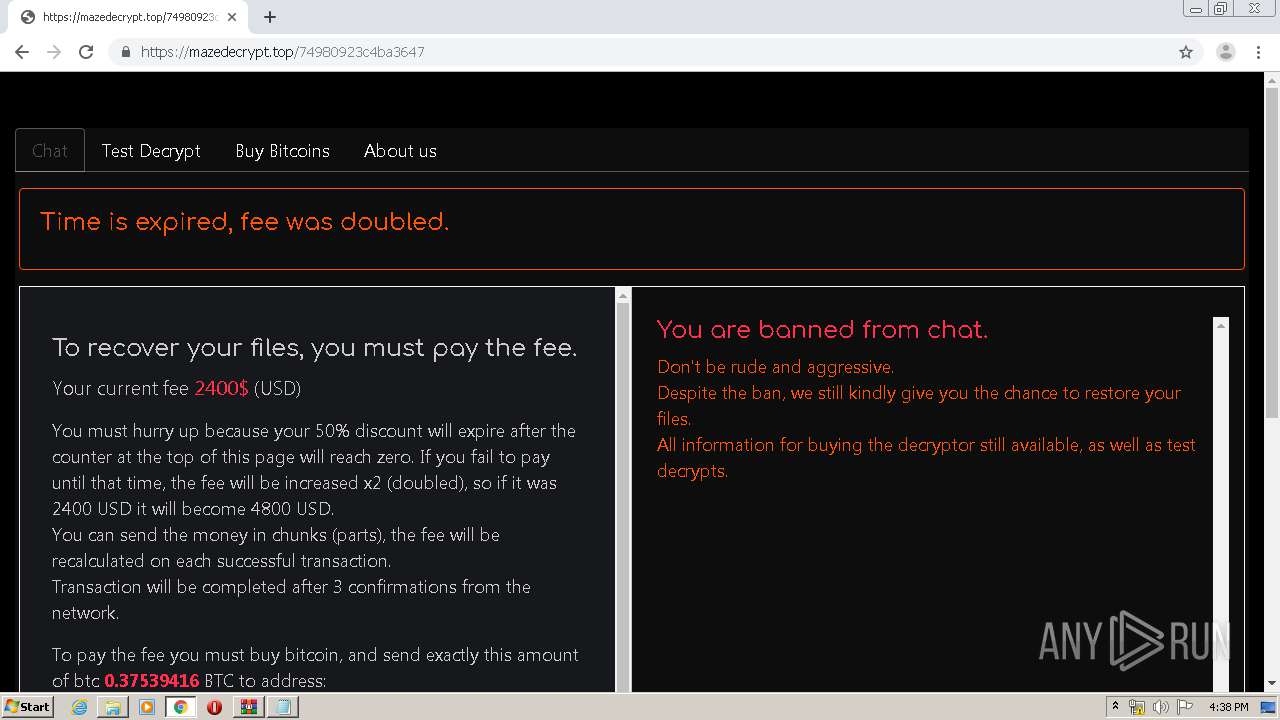
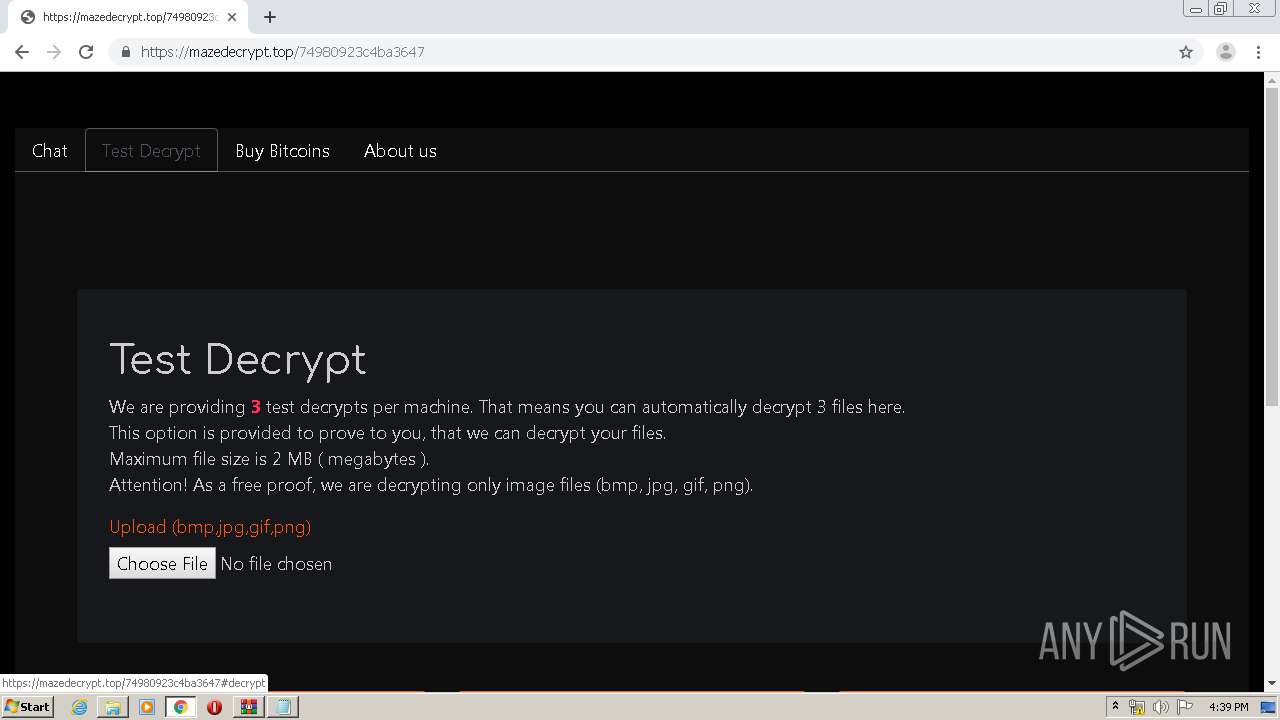
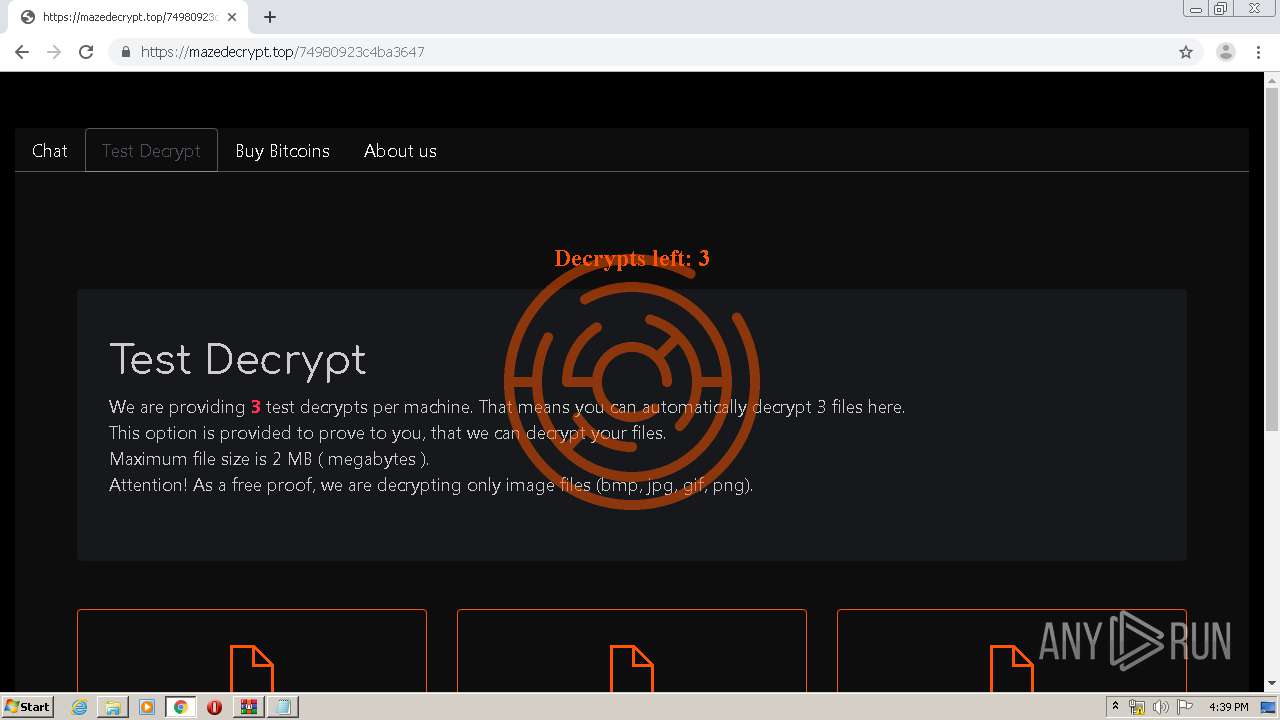
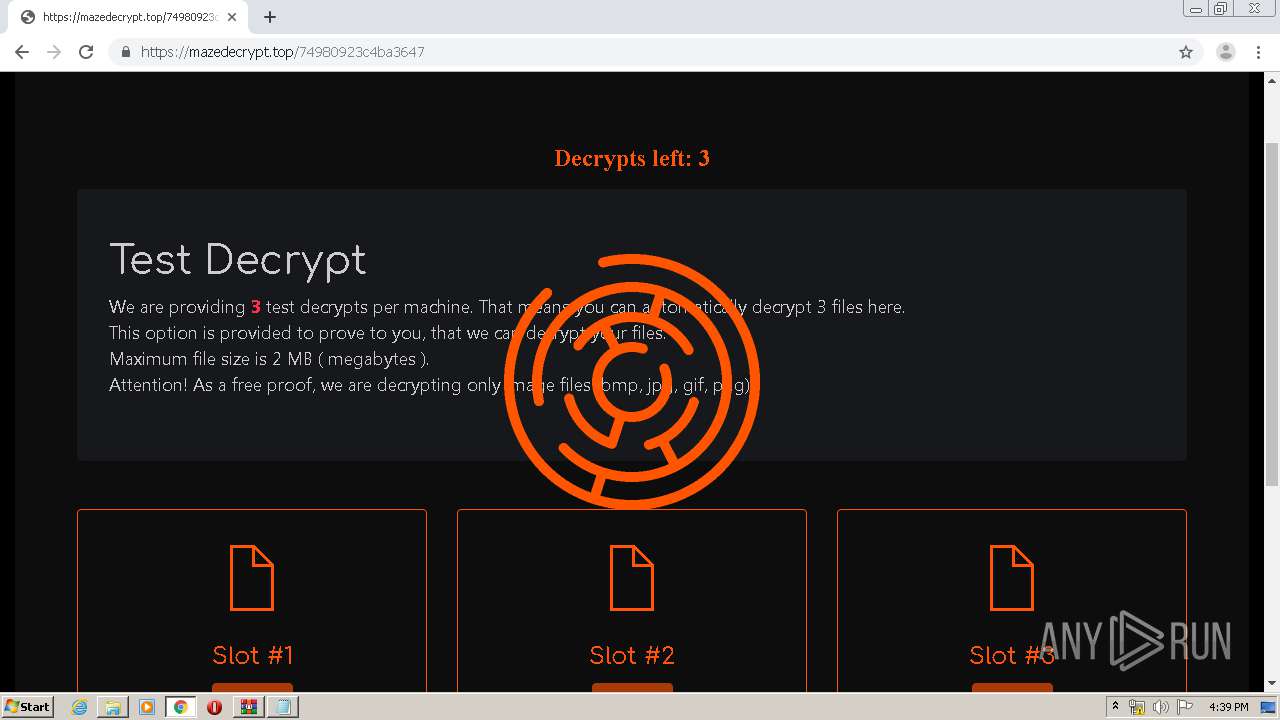
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
| Analysis date: | March 30, 2020, 15:35:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2A3C7610D1F141A9430B794CD23F49BC |
| SHA1: | CB7CF3D6D79F53760FDA7E71505D4ED310E0C2E1 |
| SHA256: | 84A7FCD0268600F7678C4A346796E2762B59F144B7A00A18349DF465A0B0597E |
| SSDEEP: | 12288:KLznYk2edCwwBCV67fITH8gTz/mPDnX5ZfUe53Qp:2nEeV6kTH8+TuDnXT7p6 |
MALICIOUS
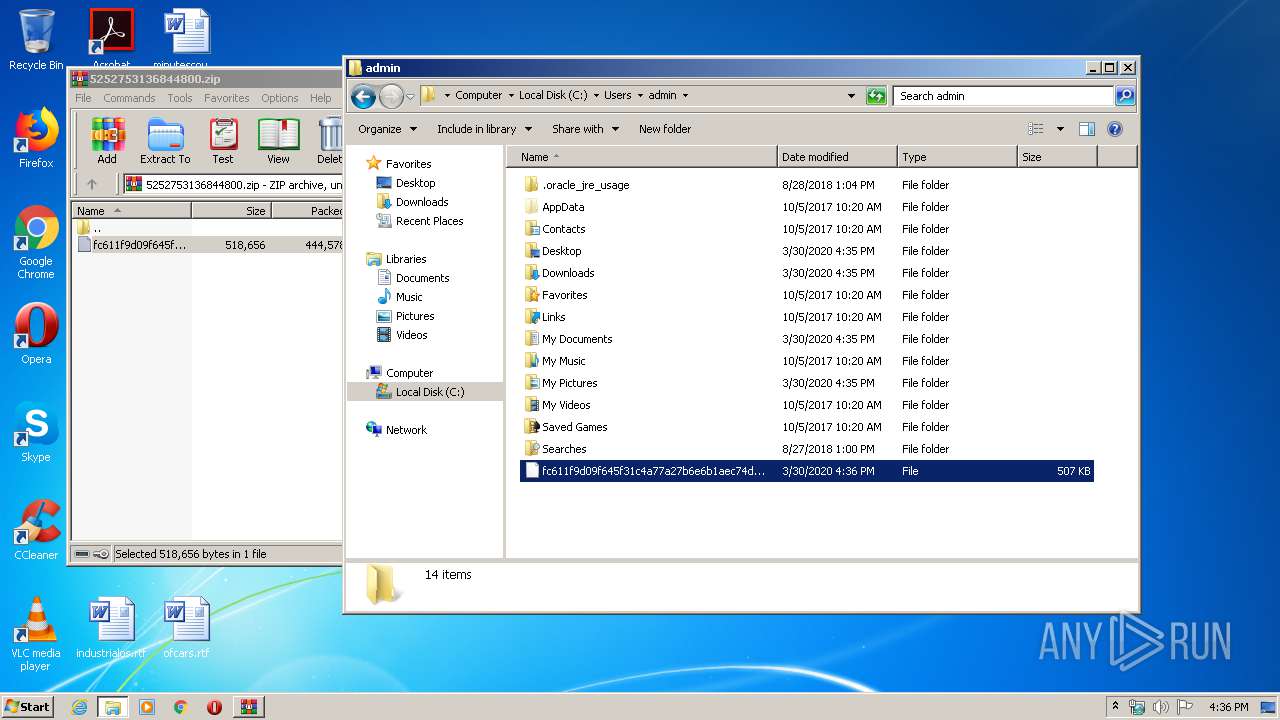
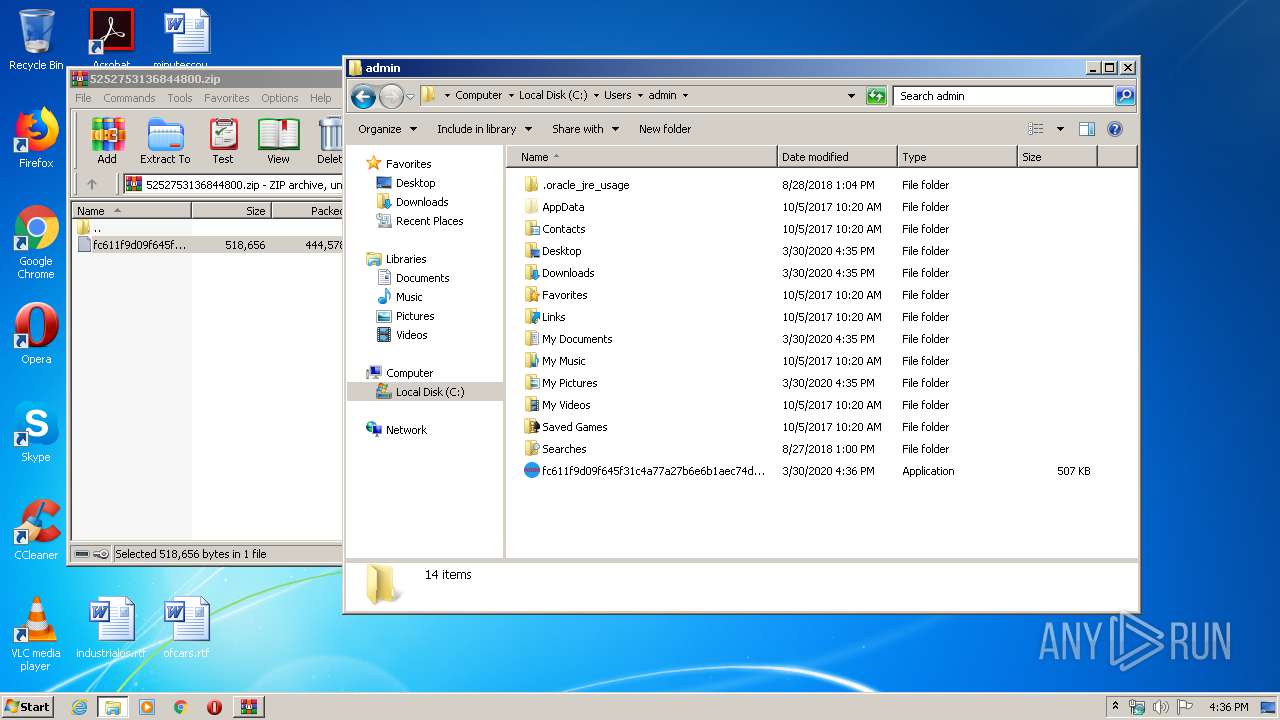
MAZE was detected
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Deletes shadow copies
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Application was dropped or rewritten from another process
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Writes to a start menu file
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Writes file to Word startup folder
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Actions looks like stealing of personal data
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
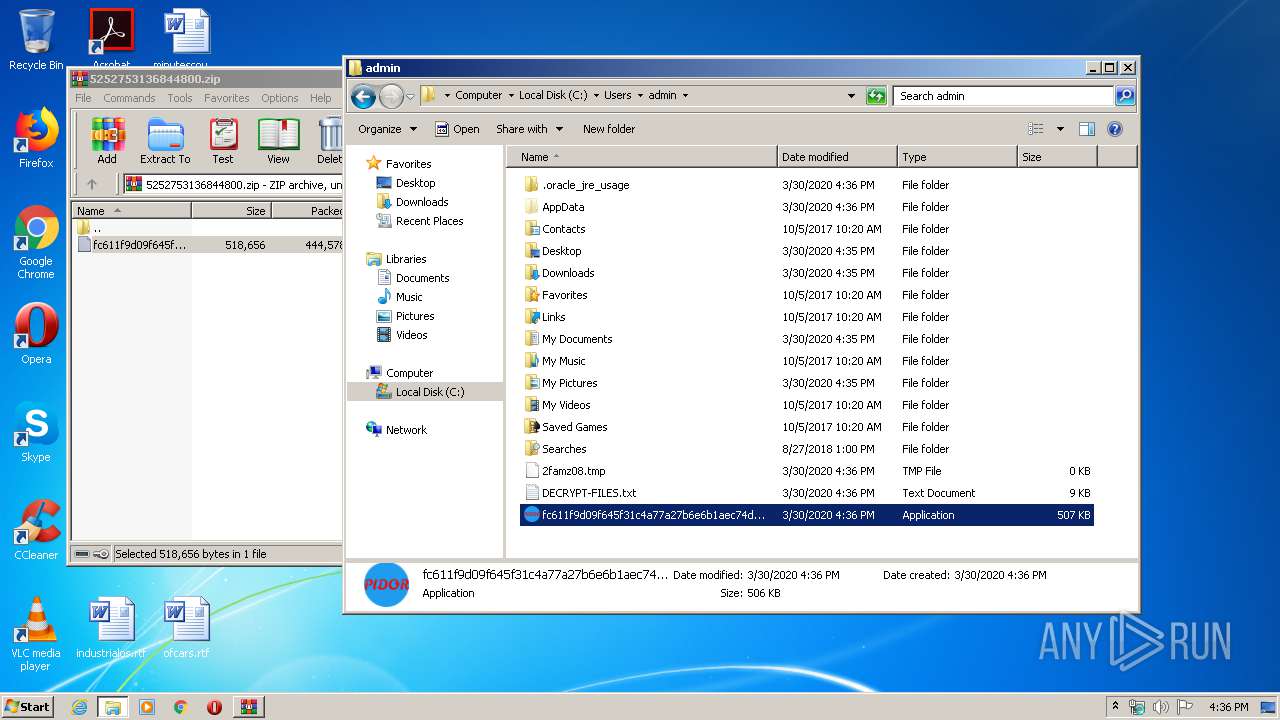
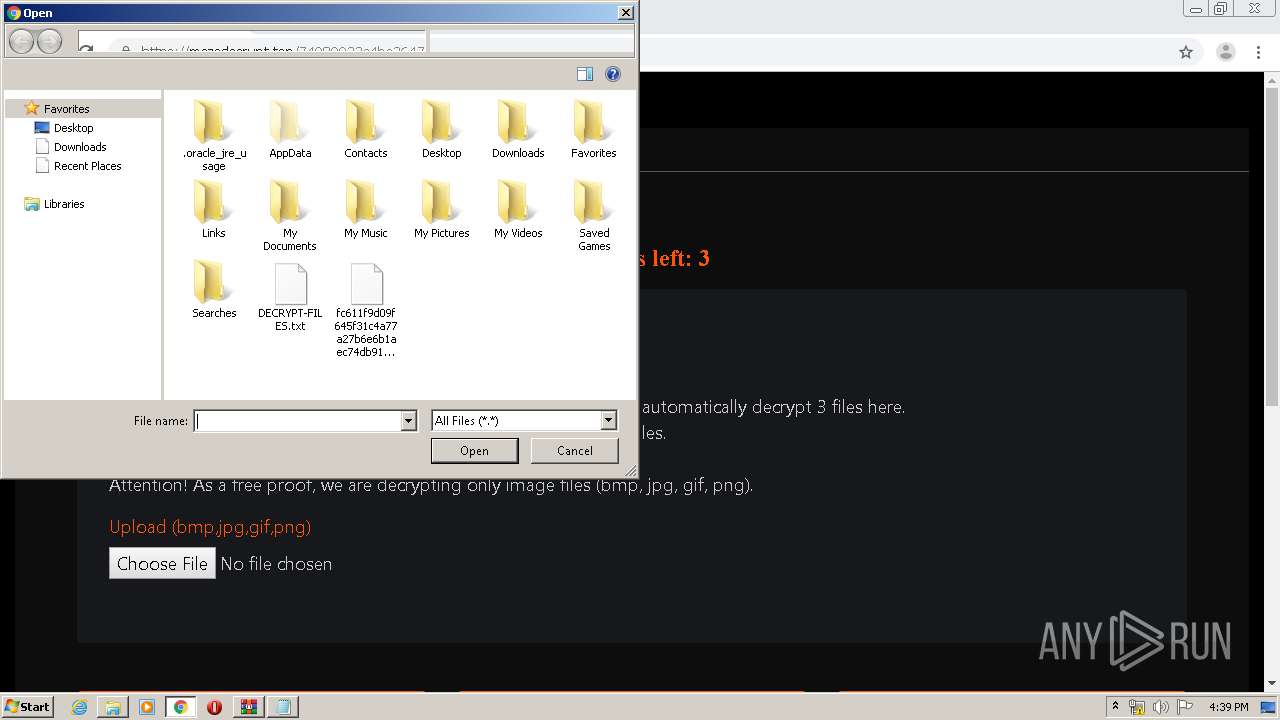
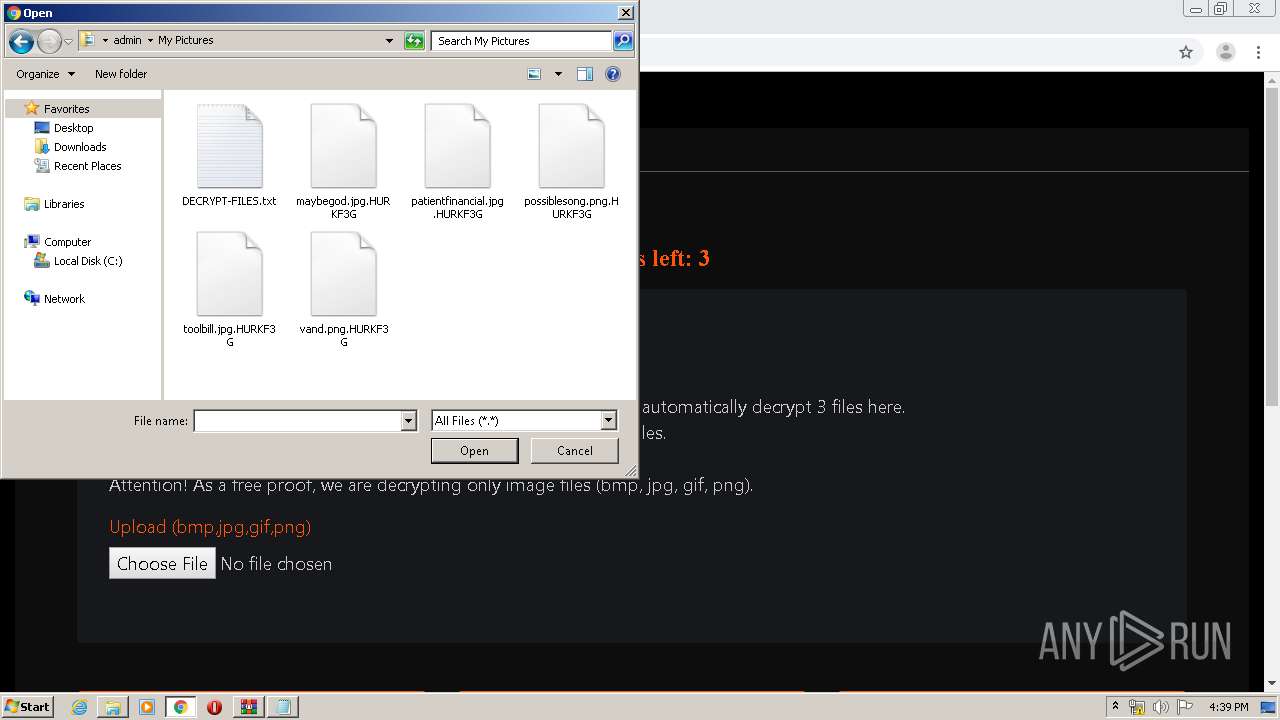
Renames files like Ransomware
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
SUSPICIOUS
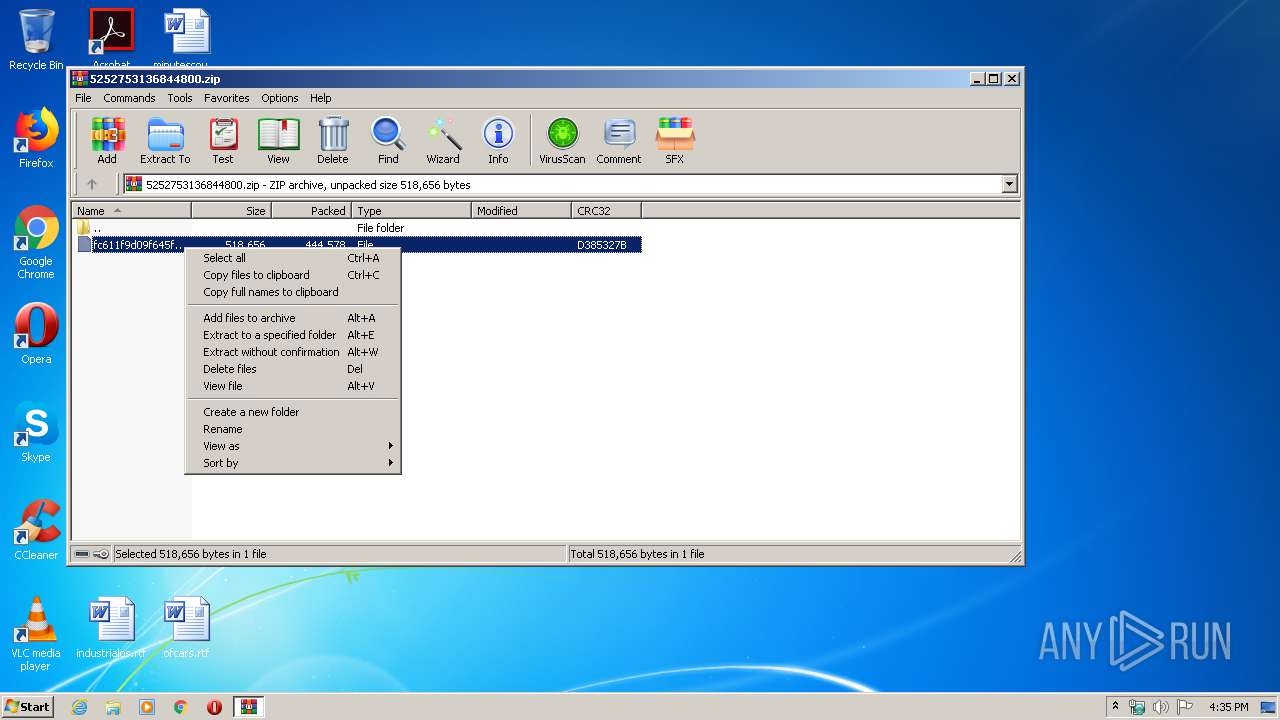
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2876)
Executed via COM
- DllHost.exe (PID: 3484)
- DllHost.exe (PID: 1732)
Connects to server without host name
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Changes tracing settings of the file or console
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
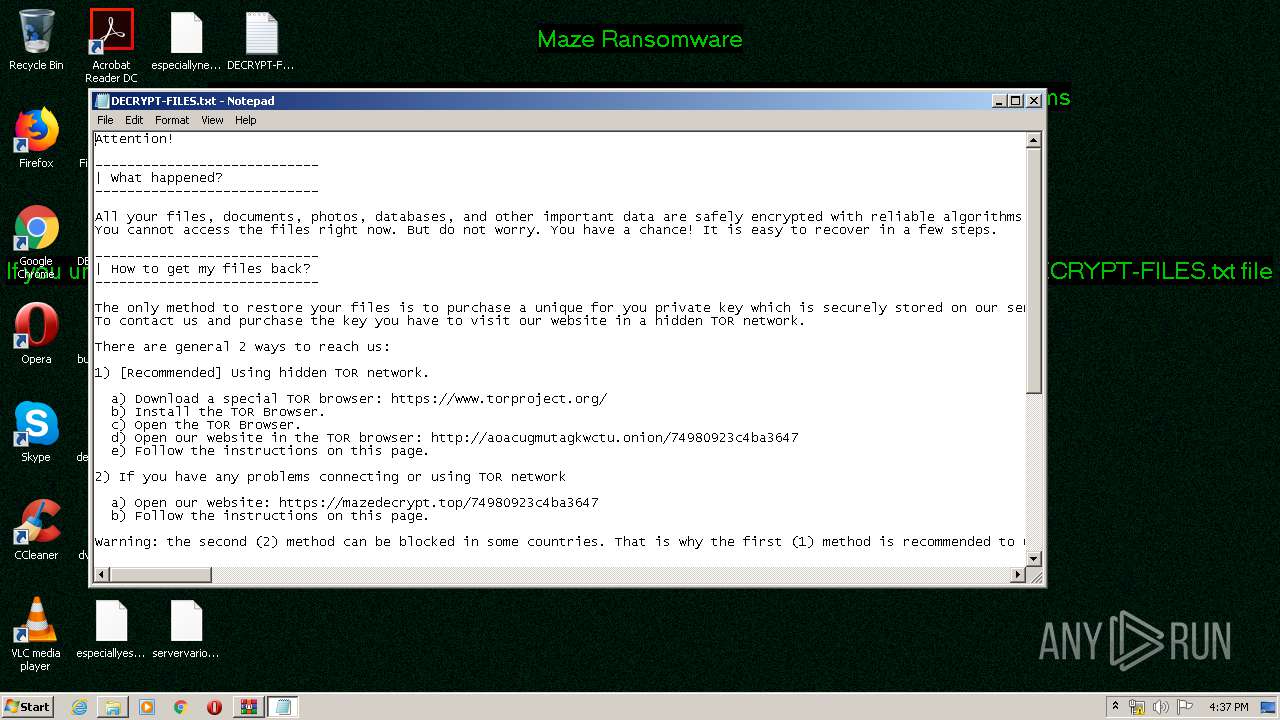
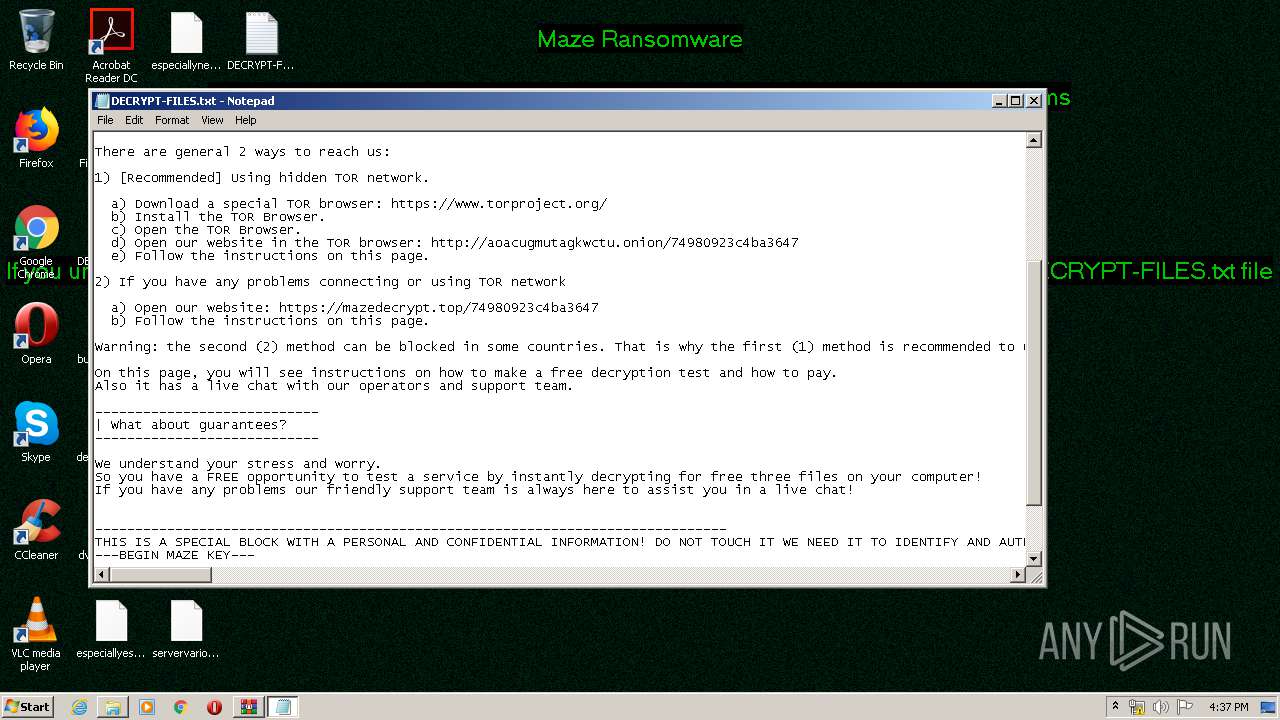
Creates files like Ransomware instruction
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Creates files in the program directory
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Executed as Windows Service
- vssvc.exe (PID: 1720)
Reads the cookies of Mozilla Firefox
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3392)
Creates files in the user directory
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
INFO
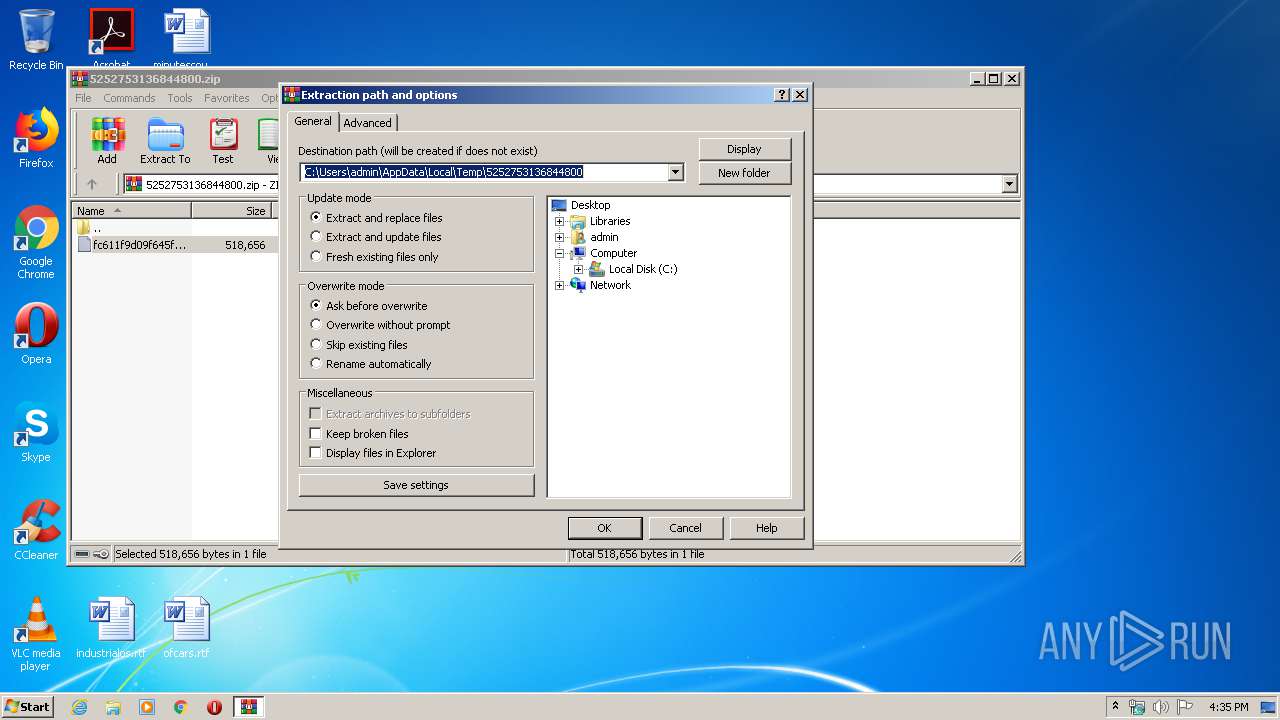
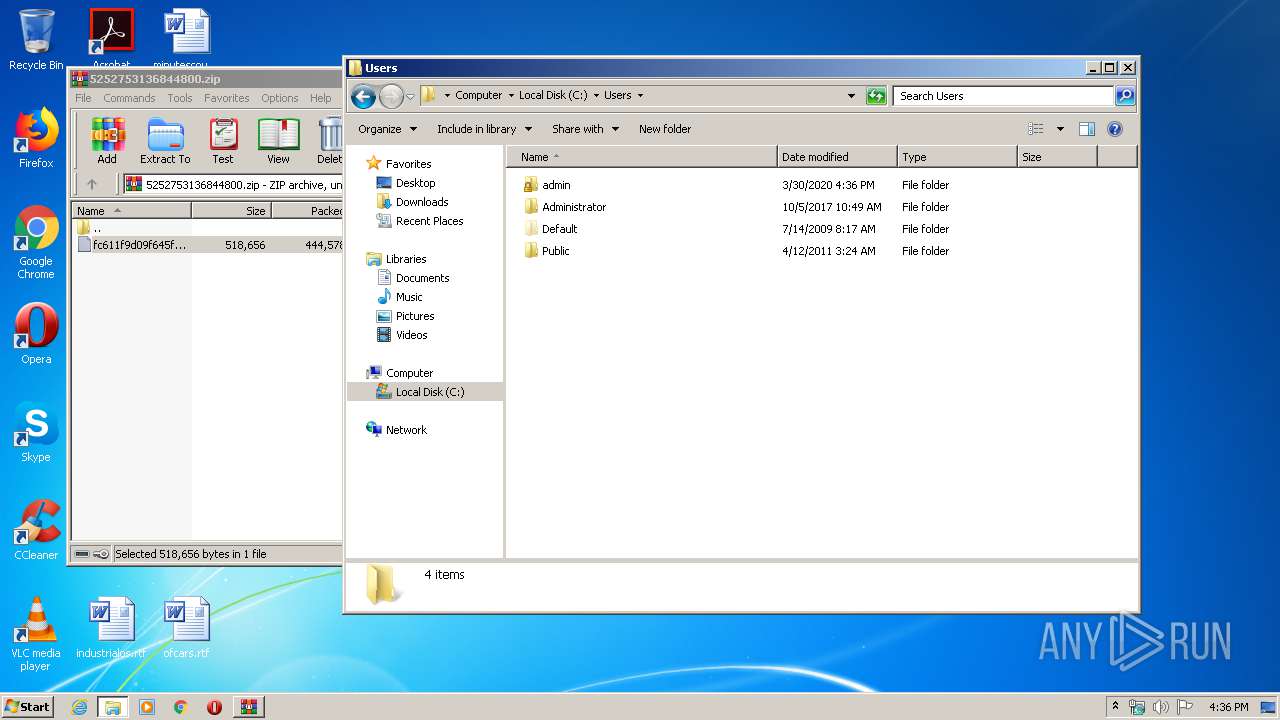
Manual execution by user
- explorer.exe (PID: 2948)
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
- NOTEPAD.EXE (PID: 3984)
- chrome.exe (PID: 3392)
Application launched itself
- chrome.exe (PID: 3392)
Reads the hosts file
- chrome.exe (PID: 3392)
- chrome.exe (PID: 2816)
Dropped object may contain TOR URL's
- fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe (PID: 3192)
Reads settings of System Certificates
- chrome.exe (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
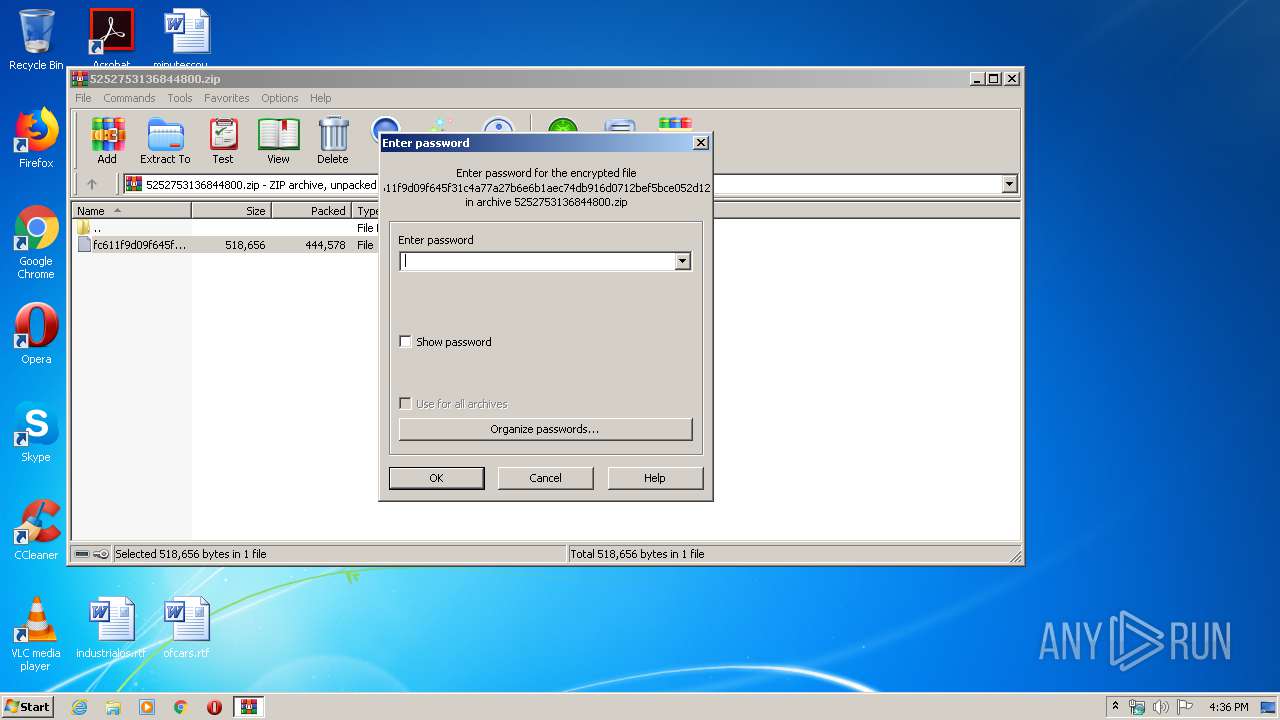
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xd385327b |
| ZipCompressedSize: | 444578 |
| ZipUncompressedSize: | 518656 |
| ZipFileName: | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f |
Total processes
90
Monitored processes
42
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5233043249798609317 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6511603166250262928 --mojo-platform-channel-handle=3192 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6000770429503560234 --mojo-platform-channel-handle=1144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10087725210940044146 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11749677113978049627 --mojo-platform-channel-handle=4048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5541943982329426690 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7003738020644401589 --mojo-platform-channel-handle=4492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,1946902350393553928,14012845430433383603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13365997405398168606 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 188
Read events
1 807
Write events
371
Delete events
10
Modification events
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5252753136844800.zip | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
441
Text files
495
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.MxcYC7W | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{02b4b32f-3d9a-4f0c-90b3-b3f695ffdbdb}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\$Recycle.Bin\DECRYPT-FILES.txt | text | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{0e2a6214-ab14-4acd-9944-51dcd3caf902}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\Program Files\DECRYPT-FILES.txt | text | |
MD5:— | SHA256:— | |||
| 3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{14e6e058-39ee-43ce-ac15-7acb7d834dae}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
59
DNS requests
20
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/rcrb.cgi?ehmt=k7&pxi=k2xpi2&b=p0q0cgj0y1 | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.25:80 | http://91.218.114.25/b.jspx | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.11:80 | http://91.218.114.11/signout/mmrcjggx.jspx?ci=7jfo15&rtk=03&is=o164db7 | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | 404 | 91.218.114.4:80 | http://91.218.114.4/rcrb.cgi?ehmt=k7&pxi=k2xpi2&b=p0q0cgj0y1 | RU | html | 206 b | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.26:80 | http://91.218.114.26/edit/pckt.shtml?hu=2 | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.31:80 | http://91.218.114.31/update/withdrawal/ccwmnlt.jsp | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/post/signin/wafsrexgtf.shtml?yah=ns3nm0xi1&mekv=e3&a=21ql85a2nw | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.11:80 | http://91.218.114.11/content/q.shtml?g=rofb4&nsep=tf1&sh=45s76830gd&m=i1i0p | RU | — | — | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | POST | — | 91.218.114.31:80 | http://91.218.114.31/update/withdrawal/ccwmnlt.jsp | RU | — | — | malicious |
2816 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | 91.218.114.4:80 | — | Mir Telematiki Ltd | RU | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | 91.218.114.31:80 | — | Mir Telematiki Ltd | RU | malicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | 91.218.114.11:80 | — | Mir Telematiki Ltd | RU | malicious |
2816 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | 91.218.114.26:80 | — | Mir Telematiki Ltd | RU | malicious |
2816 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2816 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2816 | chrome.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2816 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | 91.218.114.25:80 | — | Mir Telematiki Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
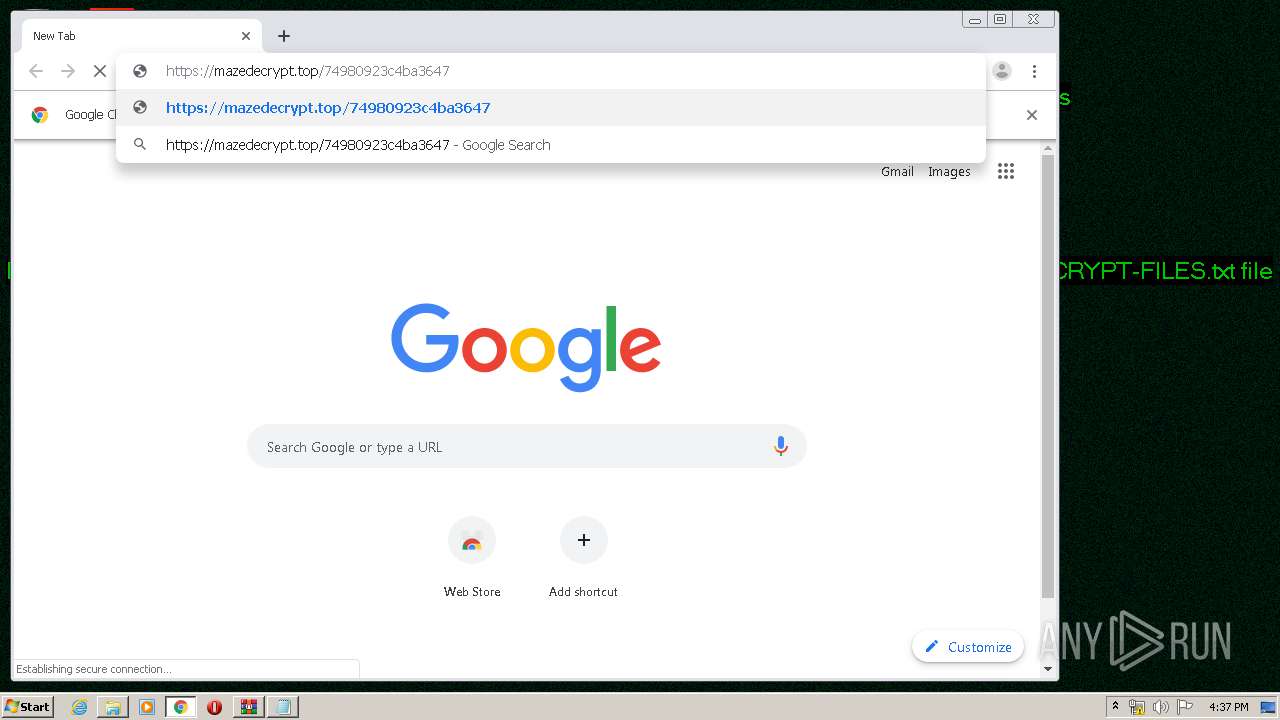
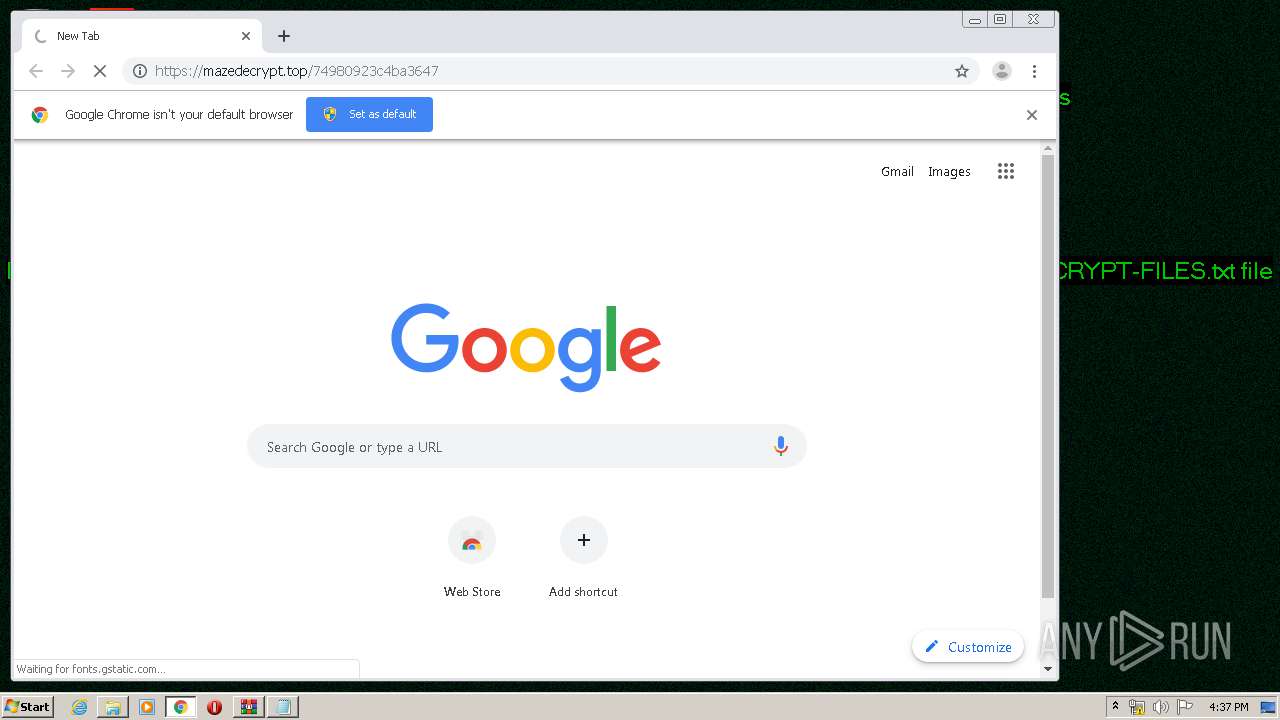
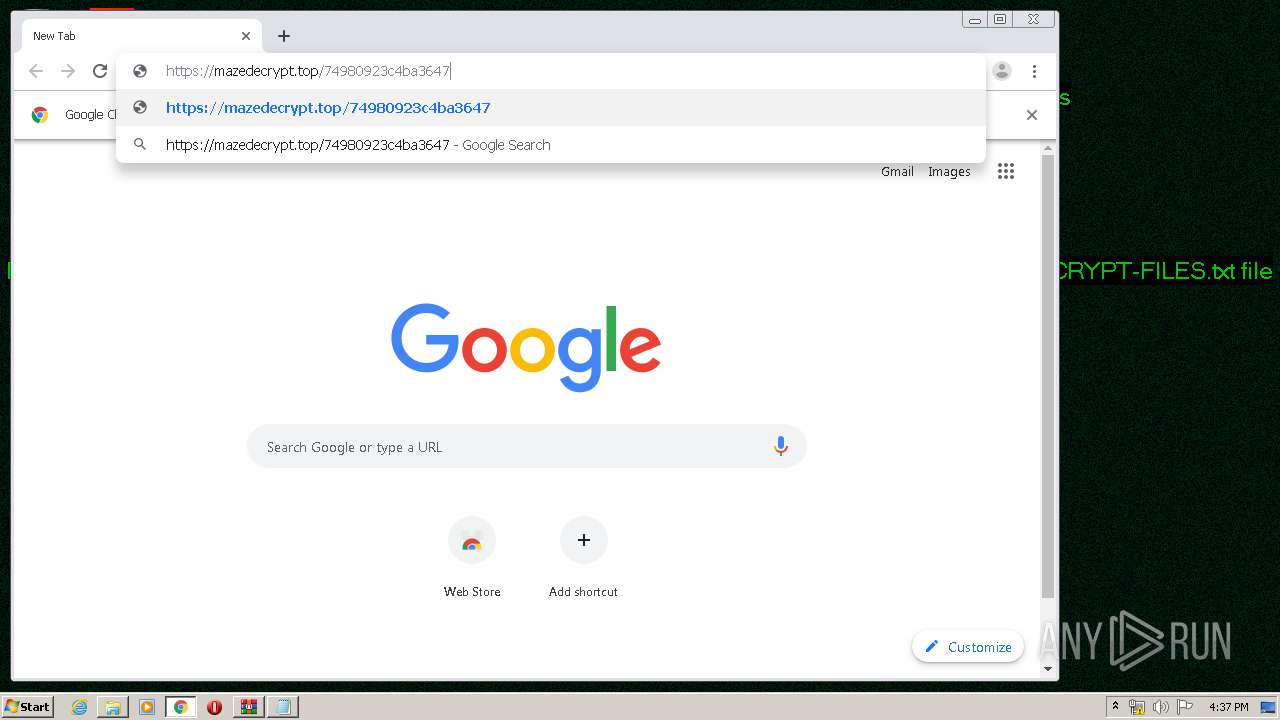
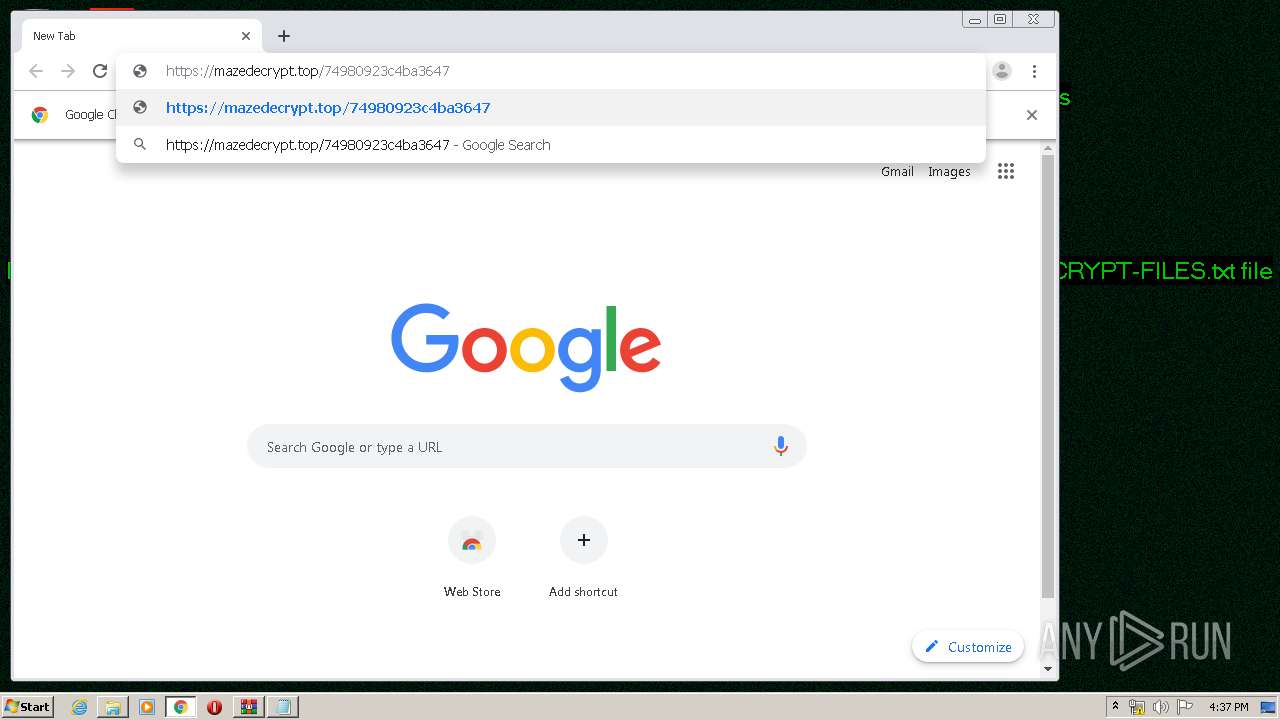
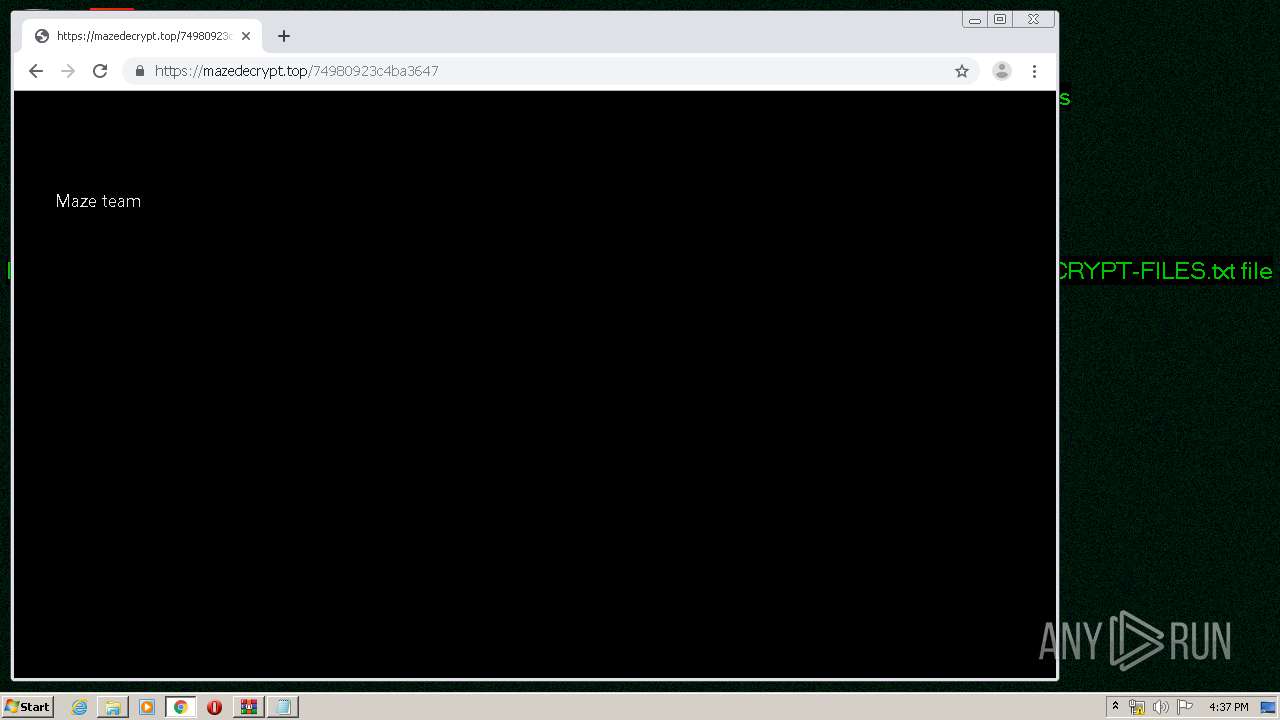
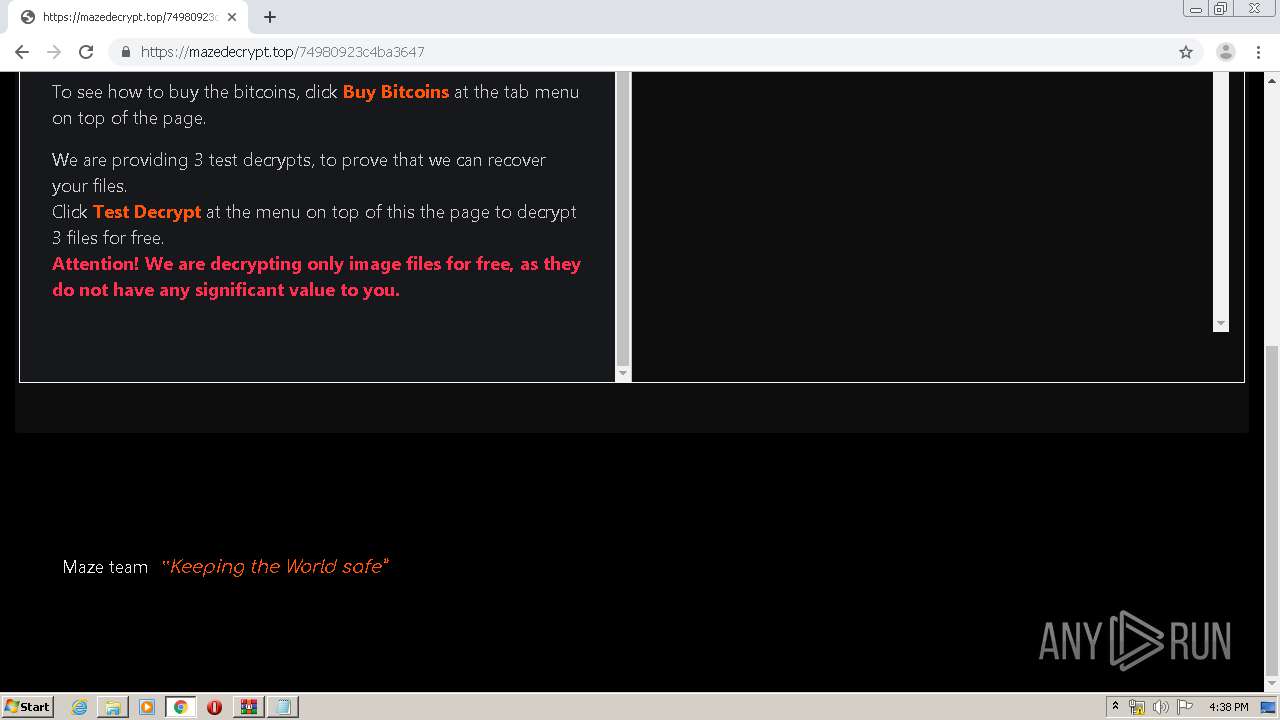
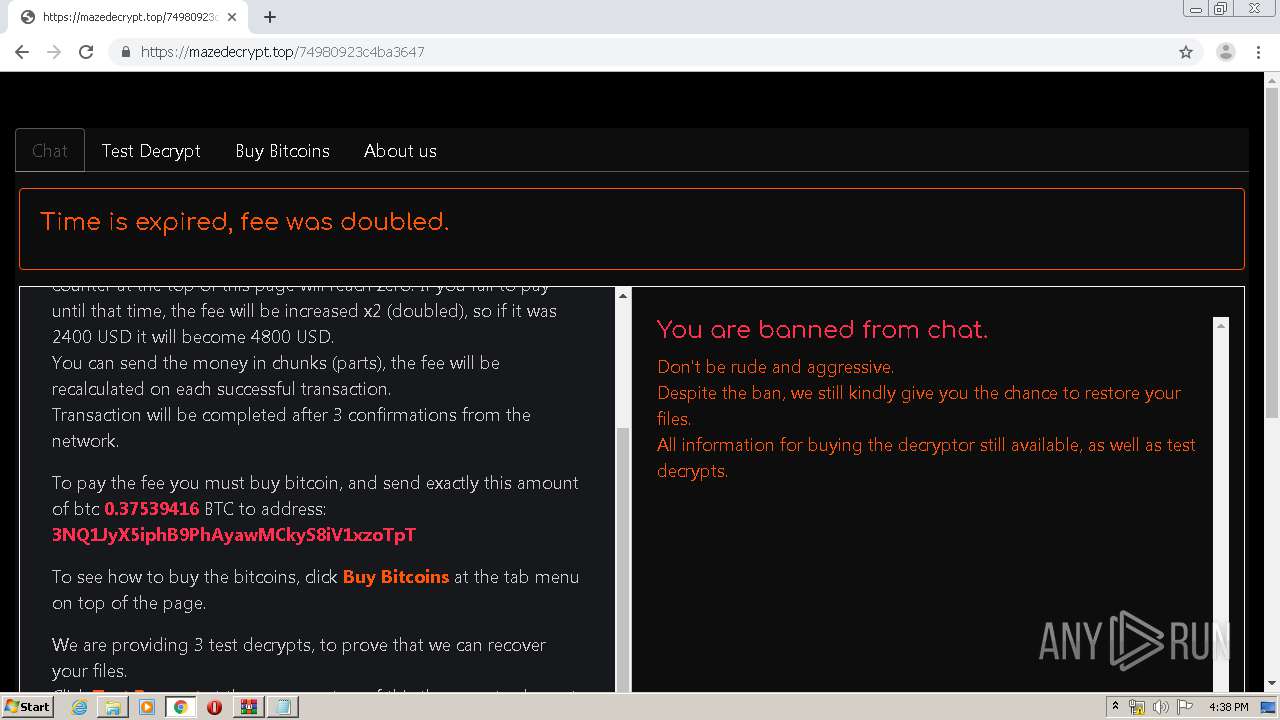
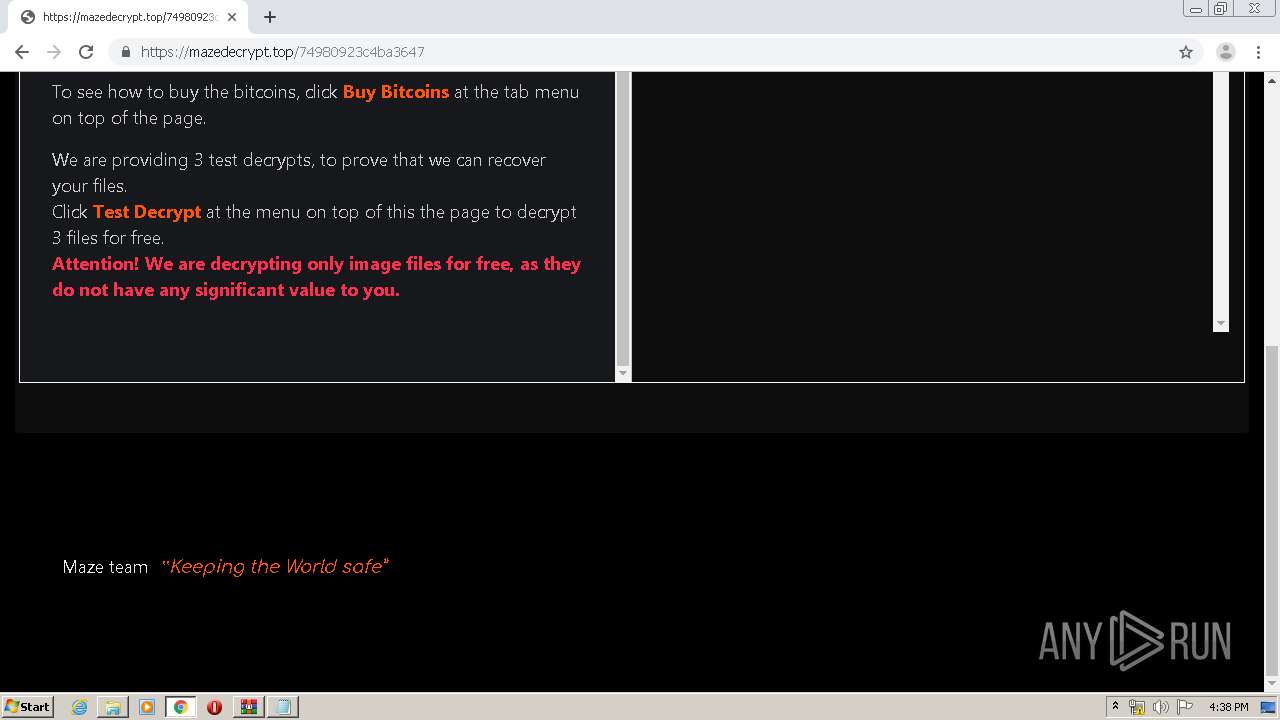
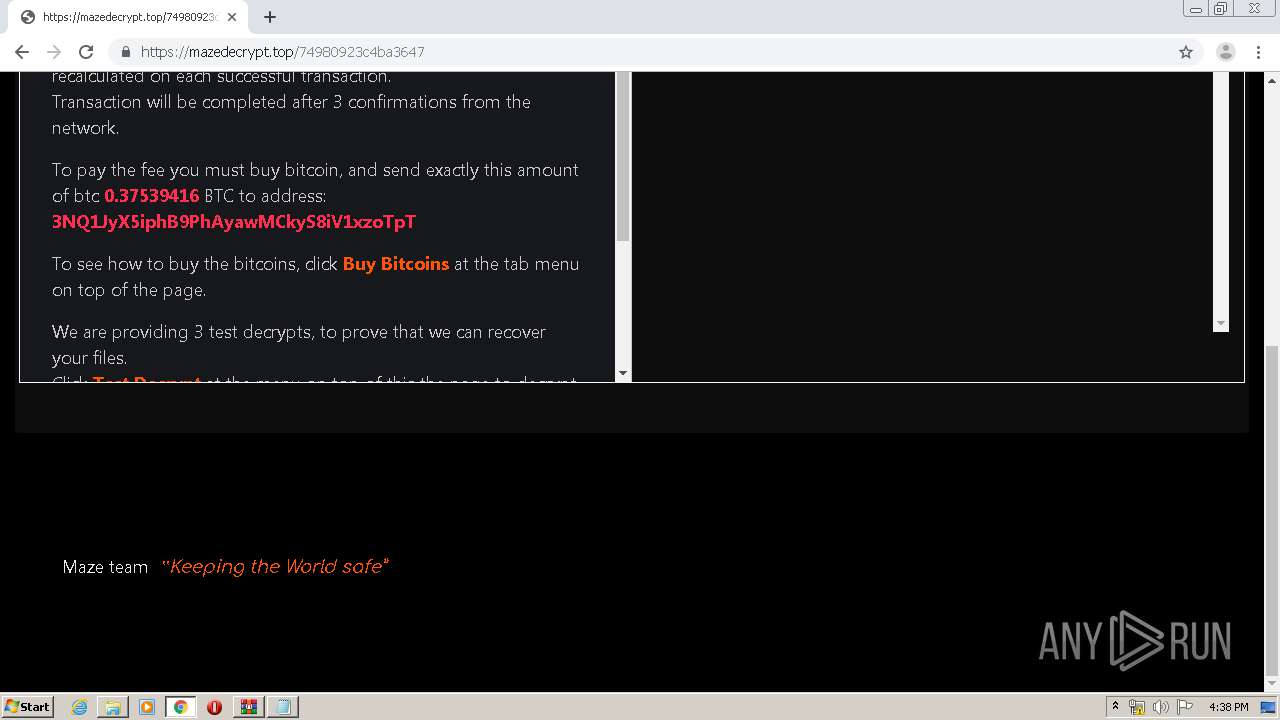
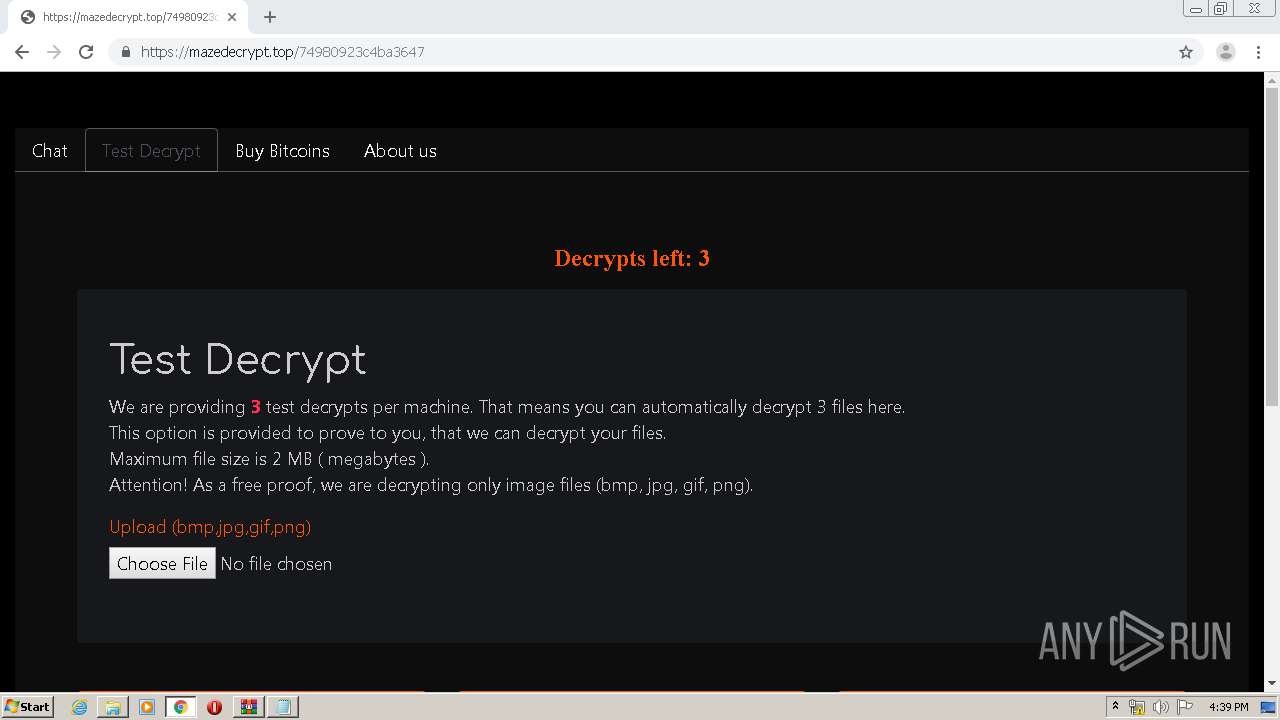
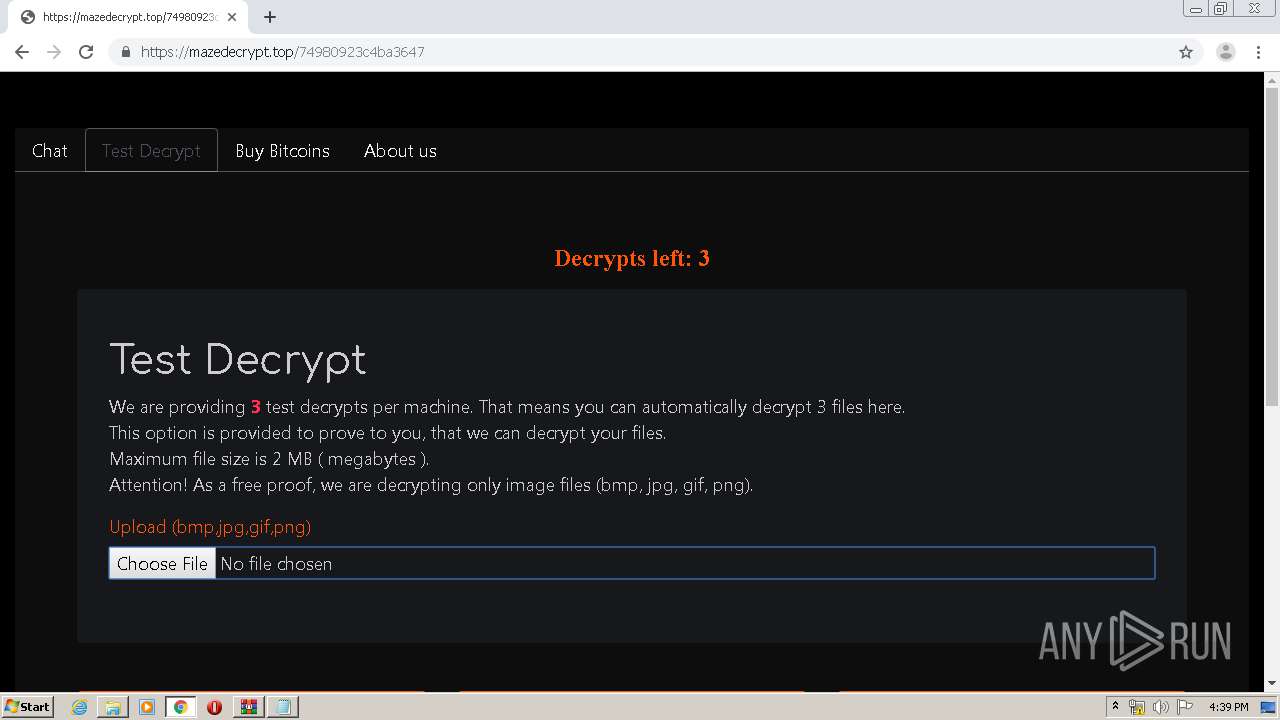
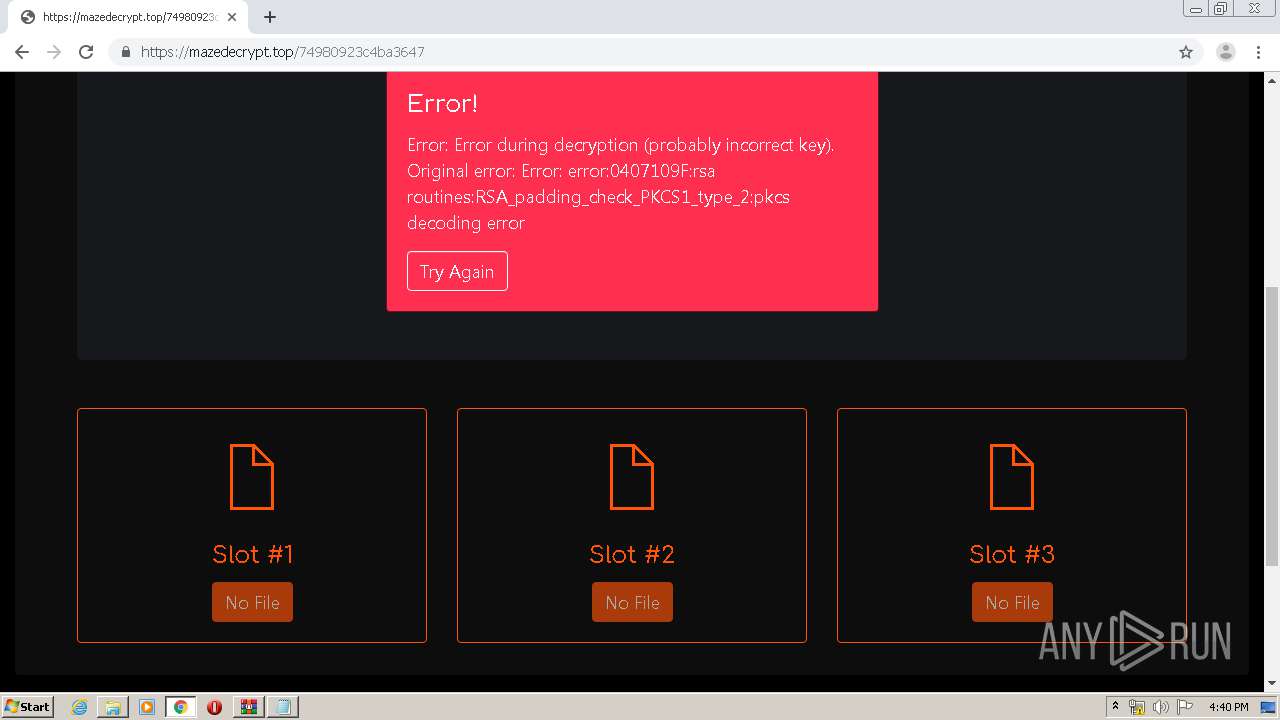
mazedecrypt.top |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
3192 | fc611f9d09f645f31c4a77a27b6e6b1aec74db916d0712bef5bce052d12c971f.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |