| File name: | ST5430623351926_598404.vbs |
| Full analysis: | https://app.any.run/tasks/c2e1da16-ea77-4be1-aa0f-7fa0ee6b14fa |
| Verdict: | Malicious activity |
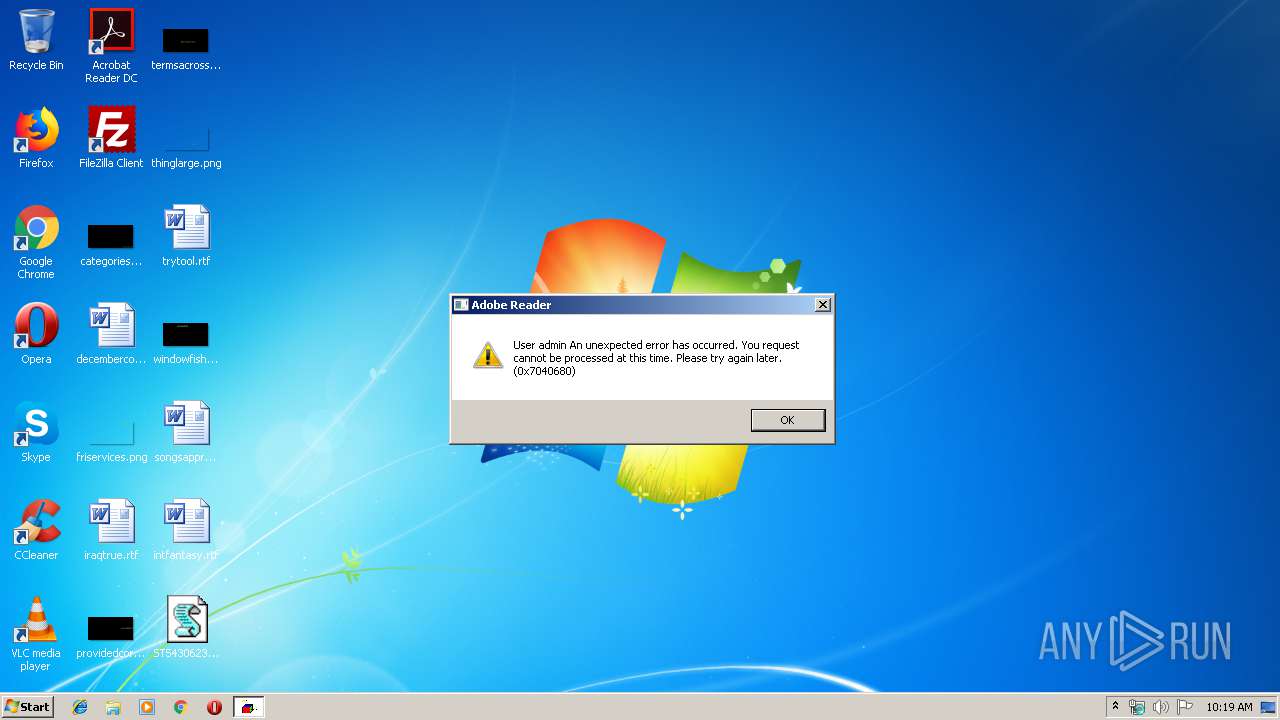
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | September 19, 2019, 09:19:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 78D2F1F43310393979AAE95AC4751147 |
| SHA1: | F18A151F4642BDE87F1AE94EB62A4F3EDB4DB77A |
| SHA256: | 83FE6142105255EF74D11291B94E0EEAF2C37C6EE6FF86057F56C8189958D472 |
| SSDEEP: | 49152:ZLgQDSQyyzvBKThZxopfy061dFUKwlr2x0CvKrj7lIVxWSALBHQShb:D |
MALICIOUS
Application was dropped or rewritten from another process
- FFzIwTR.exe (PID: 3144)
- FFzIwTR.exe (PID: 2376)
- ytfovlym.exe (PID: 2516)
- ytfovlym.exe (PID: 2748)
QBOT was detected
- FFzIwTR.exe (PID: 3144)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3568)
Changes the autorun value in the registry
- explorer.exe (PID: 708)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 2080)
- FFzIwTR.exe (PID: 3144)
- cmd.exe (PID: 3568)
Executed via WMI
- FFzIwTR.exe (PID: 3144)
Application launched itself
- FFzIwTR.exe (PID: 3144)
- ytfovlym.exe (PID: 2516)
Creates files in the user directory
- FFzIwTR.exe (PID: 3144)
Starts itself from another location
- FFzIwTR.exe (PID: 3144)
Starts CMD.EXE for commands execution
- FFzIwTR.exe (PID: 3144)
INFO
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
8
Malicious processes
1
Suspicious processes
2
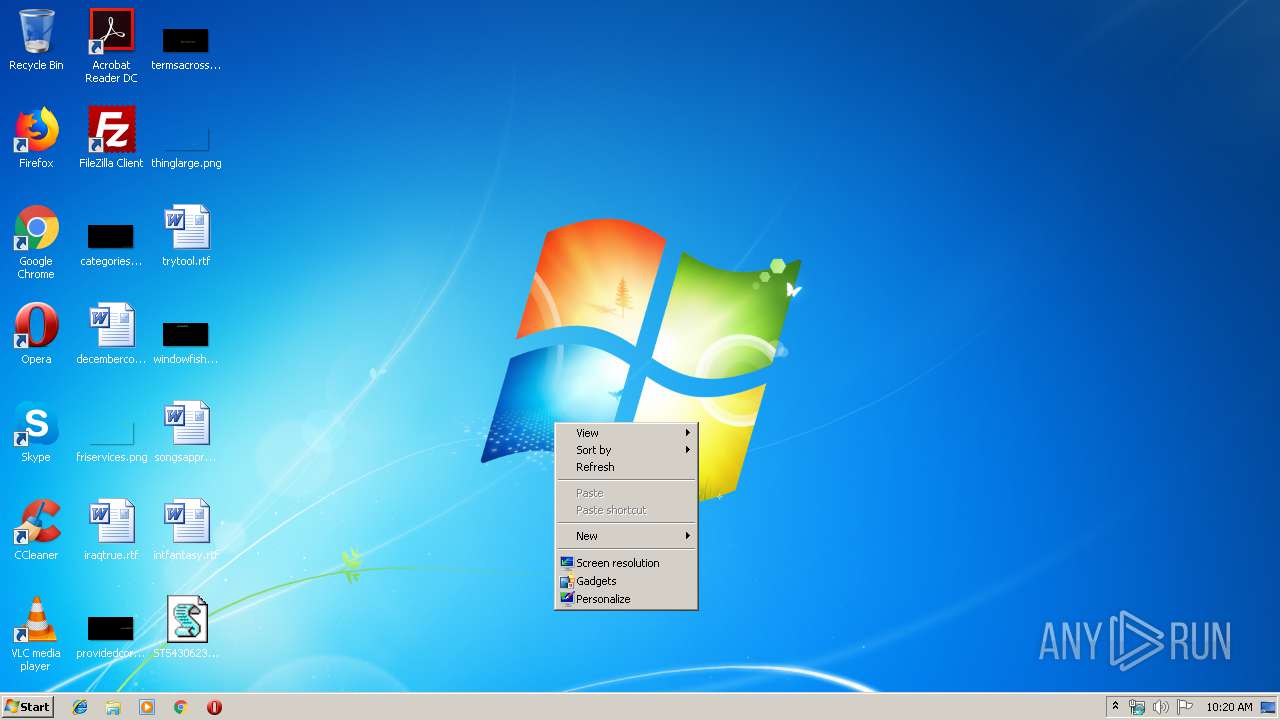
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 708 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | ytfovlym.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\ST5430623351926_598404.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2268 | ping.exe -n 6 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe /C | C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe | — | FFzIwTR.exe | |||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
| 2516 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | FFzIwTR.exe | |||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
| 2748 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe /C | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | ytfovlym.exe | |||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
| 3144 | C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe | C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Java(TM) Plug-in for Internet Explorer Exit code: 0 Version: 5.0.60.5 Modules
| |||||||||||||||
| 3568 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe" | C:\Windows\System32\cmd.exe | FFzIwTR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
484
Read events
473
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2080) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2080) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2080) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E307090004001300090013002B00F90000000000 | |||
| (PID) Process: | (3144) FFzIwTR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3144) FFzIwTR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (708) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ogrrijmwy |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe" | |||
Executable files
3
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2080 | WScript.exe | C:\Users\admin\AppData\Local\Temp\tghEVapH.txt | — | |
MD5:— | SHA256:— | |||
| 2080 | WScript.exe | C:\Users\admin\AppData\Local\Temp\tghEVapH.txt.zip | compressed | |
MD5:— | SHA256:— | |||
| 2080 | WScript.exe | C:\Users\admin\AppData\Local\Temp\NrSELpr | text | |
MD5:— | SHA256:— | |||
| 708 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 3144 | FFzIwTR.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 3144 | FFzIwTR.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | executable | |
MD5:— | SHA256:— | |||
| 2080 | WScript.exe | C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe | executable | |
MD5:— | SHA256:— | |||
| 3568 | cmd.exe | C:\Users\admin\AppData\Local\Temp\FFzIwTR.exe | executable | |
MD5:60B7C0FEAD45F2066E5B805A91F4F0FC | SHA256:80C10EE5F21F92F89CBC293A59D2FD4C01C7958AACAD15642558DB700943FA22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report