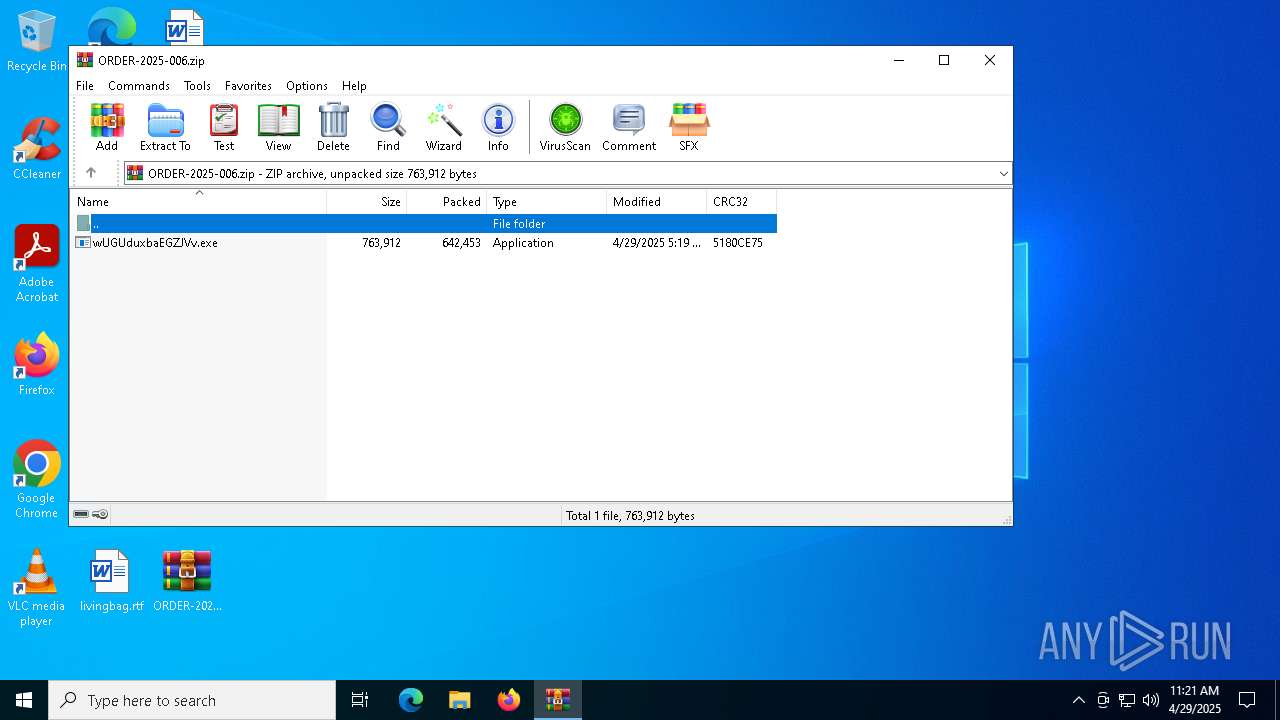
| File name: | ORDER-2025-006.zip |
| Full analysis: | https://app.any.run/tasks/bbc40479-c260-4207-8dd8-c1f18778df8a |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 29, 2025, 11:21:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | BD81A5481DF005CA7AC71502C822EC74 |
| SHA1: | EC0B64636D53E242D2E313FDF8BAEAAE16045FF2 |
| SHA256: | 83ABCAC7D026AC2E175F564B117F03CDDE60EAB2609A9C37E2D3AED0B5D6F827 |
| SSDEEP: | 24576:TsJkzrIqNw0dFA+PG6pFLyribtfjqZJ3WdxuTZYrZS0Ila8/xj/Ar/D:TsyzrIqNw0dFA+PG6pFLymbtfjqZJ3Wp |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7380)
Executing a file with an untrusted certificate
- wUGUduxbaEGZJVv.exe (PID: 7500)
FORMBOOK has been detected
- control.exe (PID: 7728)
Uses Task Scheduler to run other applications
- wUGUduxbaEGZJVv.exe (PID: 7500)
FORMBOOK has been detected (YARA)
- control.exe (PID: 7728)
SUSPICIOUS
Reads security settings of Internet Explorer
- wUGUduxbaEGZJVv.exe (PID: 7500)
- WinRAR.exe (PID: 7380)
The process executes VB scripts
- wUGUduxbaEGZJVv.exe (PID: 7500)
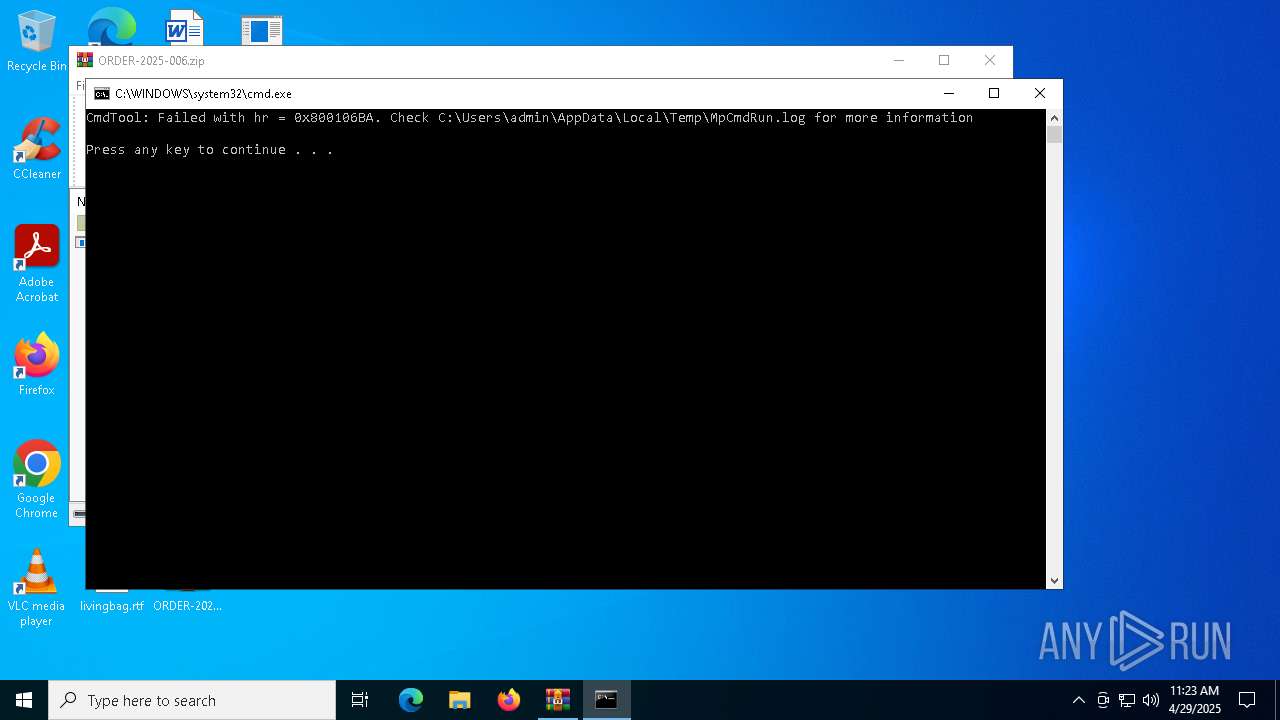
Starts CMD.EXE for commands execution
- control.exe (PID: 7728)
- WinRAR.exe (PID: 7380)
Executable content was dropped or overwritten
- wUGUduxbaEGZJVv.exe (PID: 7500)
Deletes system .NET executable
- cmd.exe (PID: 7828)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7380)
INFO
Manual execution by a user
- wUGUduxbaEGZJVv.exe (PID: 7500)
- control.exe (PID: 7728)
Checks supported languages
- wUGUduxbaEGZJVv.exe (PID: 7500)
- vbc.exe (PID: 7696)
- MpCmdRun.exe (PID: 2852)
Reads the computer name
- wUGUduxbaEGZJVv.exe (PID: 7500)
- vbc.exe (PID: 7696)
- MpCmdRun.exe (PID: 2852)
Reads the machine GUID from the registry
- wUGUduxbaEGZJVv.exe (PID: 7500)
Create files in a temporary directory
- wUGUduxbaEGZJVv.exe (PID: 7500)
- MpCmdRun.exe (PID: 2852)
Process checks computer location settings
- wUGUduxbaEGZJVv.exe (PID: 7500)
Creates files or folders in the user directory
- wUGUduxbaEGZJVv.exe (PID: 7500)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7380)
Checks proxy server information
- slui.exe (PID: 8084)
Reads the software policy settings
- slui.exe (PID: 8084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(7728) control.exe
C2www.gsp657.top/hi13/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)olidspot.shop
aise-your-voice.sbs
9ydygorig3l7z.xyz
netuzio.xyz
erspacehealthandwellness.info
hbnzk.cfd
uklor.shop
tudiofoti.pro
onety.skin
iralavinc.online
teelpath.shop
w-yudfjp.shop
betka.xyz
lx2cbhe5vee0e1.xyz
ndotoverf.pro
loud-sevice.click
enckubs.shop
anpack.shop
nity-3d-development.dev
iaolento12.sbs
xectgroup.net
avakey.shop
kfast.store
ayeewenvqzqm.top
66xq2.top
cvaultshielded.live
5zbm0.cfd
g1wszulqv7lc.xyz
rog.top
xplosion-proof.lat
aysec.net
999game.website
3a4p8gq8bojwn.xyz
x92q.top
akextow.net
t775.top
873013.xyz
tu1x120.top
9882aa1216.autos
ayarwarna21.live
ardengoal.net
8ln62.cfd
elvetvoiceskiresorts.website
kpqh.town
njjwh.info
movps.net
pb79kasy.vip
ellbar.shop
inktrim.xyz
hagrinleemotooltechus.shop
olayl
tp-batik77-1.vip
looring-services329769.sbs
130t.xyz
9gi02.cfd
elayrunway.shop
phones-br.sbs
aser-skin-treatment-95250.bond
ry-prodentims.shop
rtelegans.art
01411.club
it4n1ar4t0k7o0.xyz
igitalmilanolegacy.shop
ompanion.bio
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:28 22:19:46 |
| ZipCRC: | 0x5180ce75 |
| ZipCompressedSize: | 642453 |
| ZipUncompressedSize: | 763912 |
| ZipFileName: | wUGUduxbaEGZJVv.exe |
Total processes
132
Monitored processes
13
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
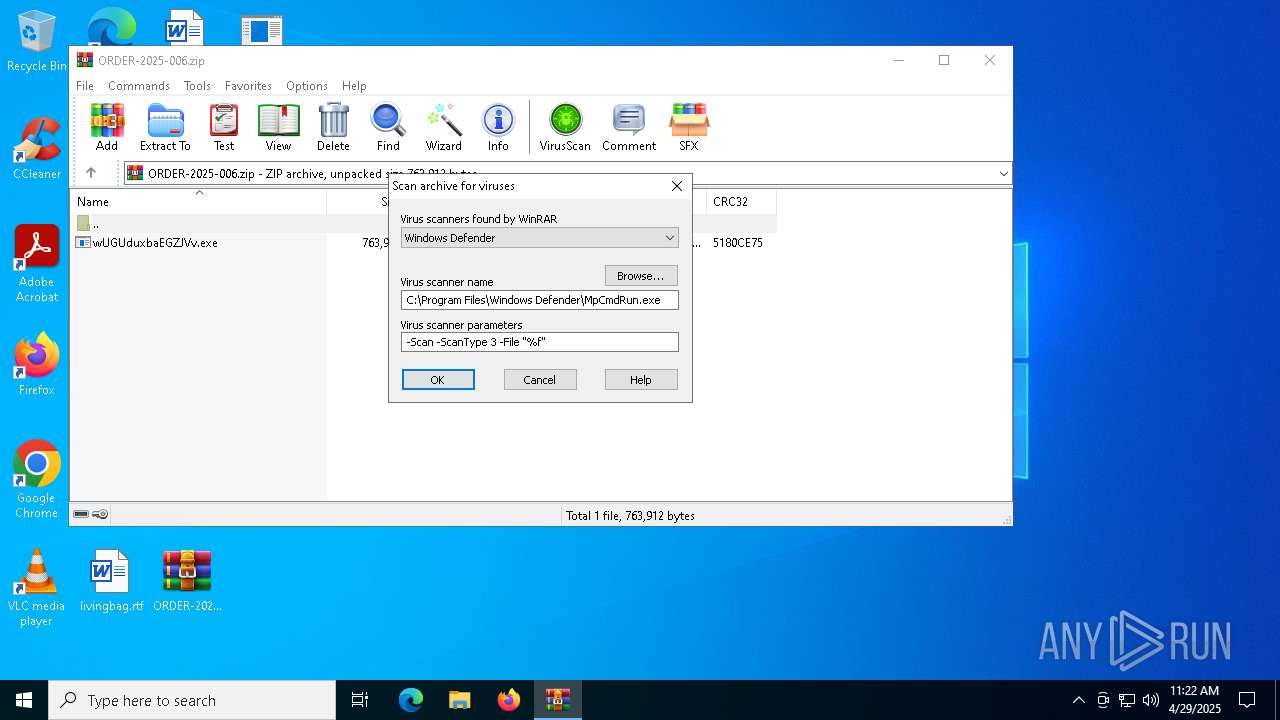
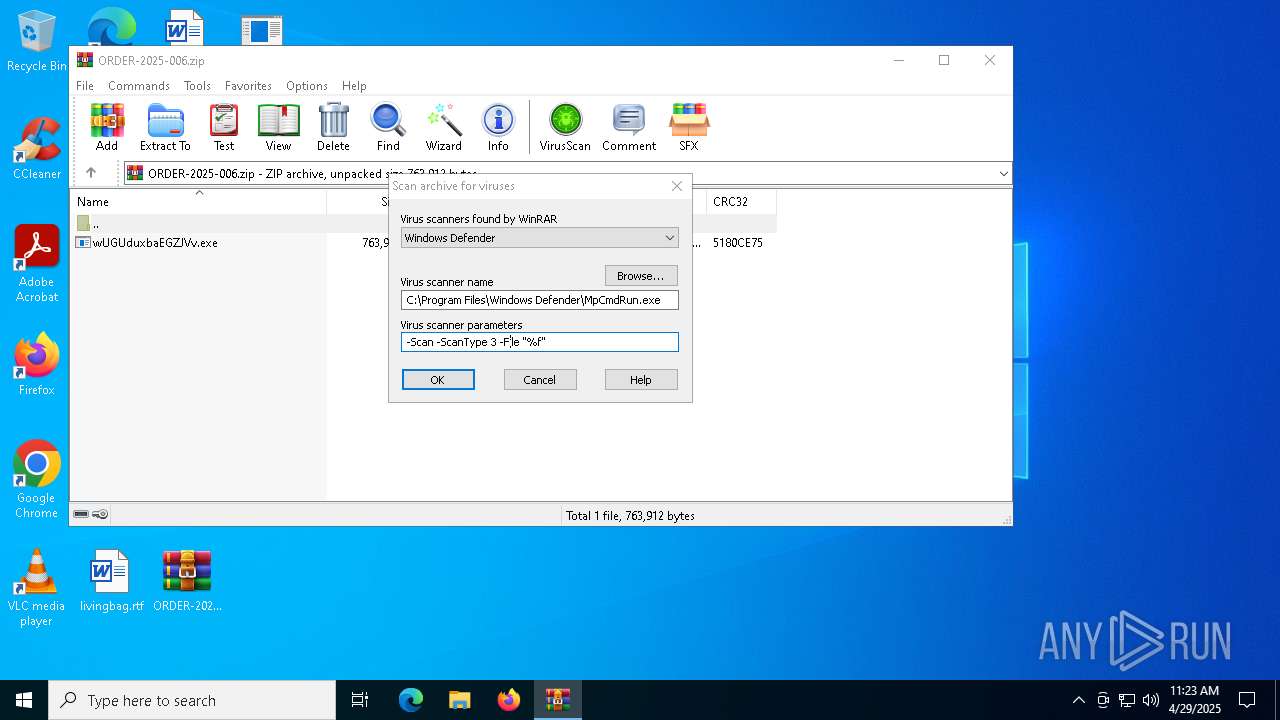
| 2852 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7380.12649" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7380 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ORDER-2025-006.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7500 | "C:\Users\admin\Desktop\wUGUduxbaEGZJVv.exe" | C:\Users\admin\Desktop\wUGUduxbaEGZJVv.exe | explorer.exe | ||||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: Sgm_Student_Information Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7628 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\jsPhfd" /XML "C:\Users\admin\AppData\Local\Temp\tmp101A.tmp" | C:\Windows\SysWOW64\schtasks.exe | — | wUGUduxbaEGZJVv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7696 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | — | wUGUduxbaEGZJVv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 7728 | "C:\Windows\SysWOW64\control.exe" | C:\Windows\SysWOW64\control.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
Formbook(PID) Process(7728) control.exe C2www.gsp657.top/hi13/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)olidspot.shop aise-your-voice.sbs 9ydygorig3l7z.xyz netuzio.xyz erspacehealthandwellness.info hbnzk.cfd uklor.shop tudiofoti.pro onety.skin iralavinc.online teelpath.shop w-yudfjp.shop betka.xyz lx2cbhe5vee0e1.xyz ndotoverf.pro loud-sevice.click enckubs.shop anpack.shop nity-3d-development.dev iaolento12.sbs xectgroup.net avakey.shop kfast.store ayeewenvqzqm.top 66xq2.top cvaultshielded.live 5zbm0.cfd g1wszulqv7lc.xyz rog.top xplosion-proof.lat aysec.net 999game.website 3a4p8gq8bojwn.xyz x92q.top akextow.net t775.top 873013.xyz tu1x120.top 9882aa1216.autos ayarwarna21.live ardengoal.net 8ln62.cfd elvetvoiceskiresorts.website kpqh.town njjwh.info movps.net pb79kasy.vip ellbar.shop inktrim.xyz hagrinleemotooltechus.shop olayl tp-batik77-1.vip looring-services329769.sbs 130t.xyz 9gi02.cfd elayrunway.shop phones-br.sbs aser-skin-treatment-95250.bond ry-prodentims.shop rtelegans.art 01411.club it4n1ar4t0k7o0.xyz igitalmilanolegacy.shop ompanion.bio | |||||||||||||||
| 7828 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" | C:\Windows\SysWOW64\cmd.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 445
Read events
5 436
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ORDER-2025-006.zip | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7380) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
2
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7380.12649\ORDER-2025-006.zip\wUGUduxbaEGZJVv.exe | executable | |
MD5:46BBF0505A2C283CF2B087C14DA68957 | SHA256:2CADED000F82486CAADE3EEB6C47D446037ABDCB39A2BA127B58C9FC67D15F33 | |||
| 7500 | wUGUduxbaEGZJVv.exe | C:\Users\admin\AppData\Local\Temp\tmp101A.tmp | xml | |
MD5:4DA024E508FB9B5F2FC5A42637498CB4 | SHA256:32D162AC36D15AF3912616EF49F4CB0748E8637D8168C4B4D47A3A66BD7E9DFC | |||
| 2852 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:BE276B8AC16C9BF1BC68176C06D6DDB5 | SHA256:1938BB36C1016F2E42C9765B4851E64101BCD0752A6652AAB7797528D4253BC7 | |||
| 7500 | wUGUduxbaEGZJVv.exe | C:\Users\admin\AppData\Roaming\jsPhfd.exe | executable | |
MD5:46BBF0505A2C283CF2B087C14DA68957 | SHA256:2CADED000F82486CAADE3EEB6C47D446037ABDCB39A2BA127B58C9FC67D15F33 | |||
| 7380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7380.12649\Rar$Scan109885.bat | text | |
MD5:05A0D7F03E6E1F74ED985D3C1990E87D | SHA256:6DED240D8C174D42548246E5C19FE33C67583317A932979A0FE00E47C57ECF6C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
40
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7816 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 23.48.23.182:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 23.48.23.182:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
7816 | SIHClient.exe | GET | 200 | 23.48.23.182:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.109.210.53:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7816 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7816 | SIHClient.exe | 23.48.23.182:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7816 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7816 | SIHClient.exe | 13.85.23.206:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4812 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.ayeewenvqzqm.top |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |