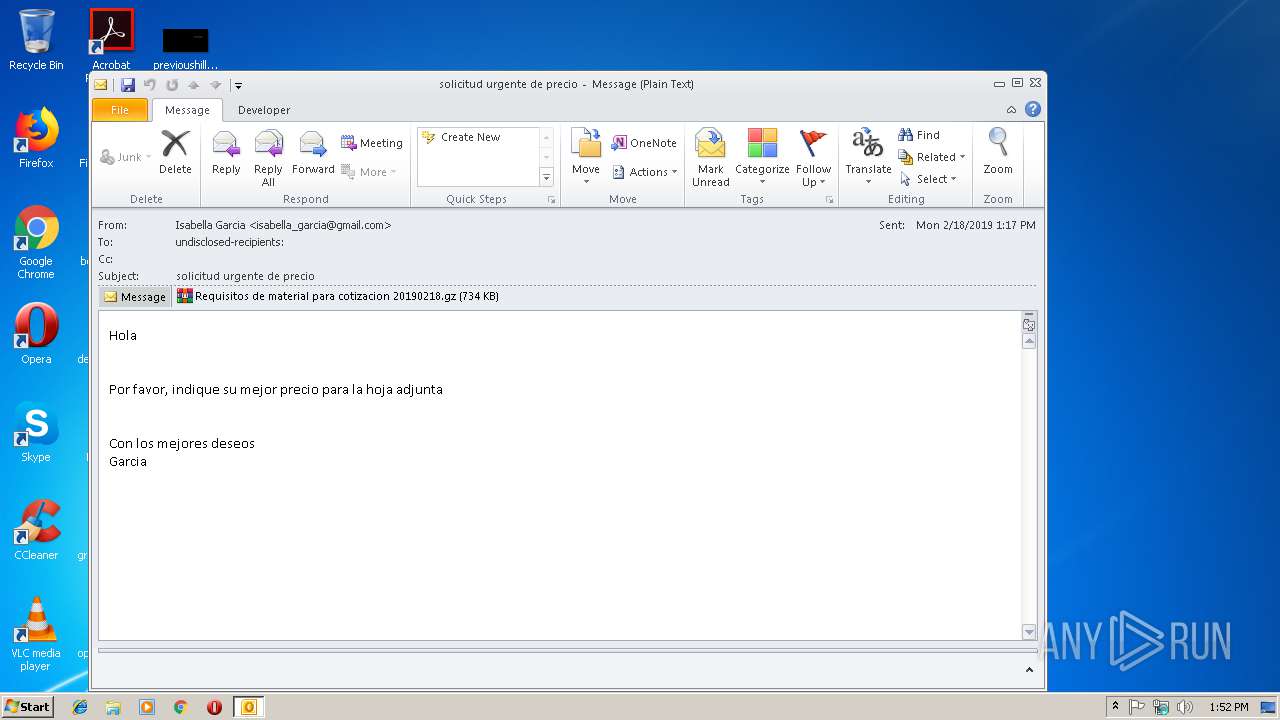
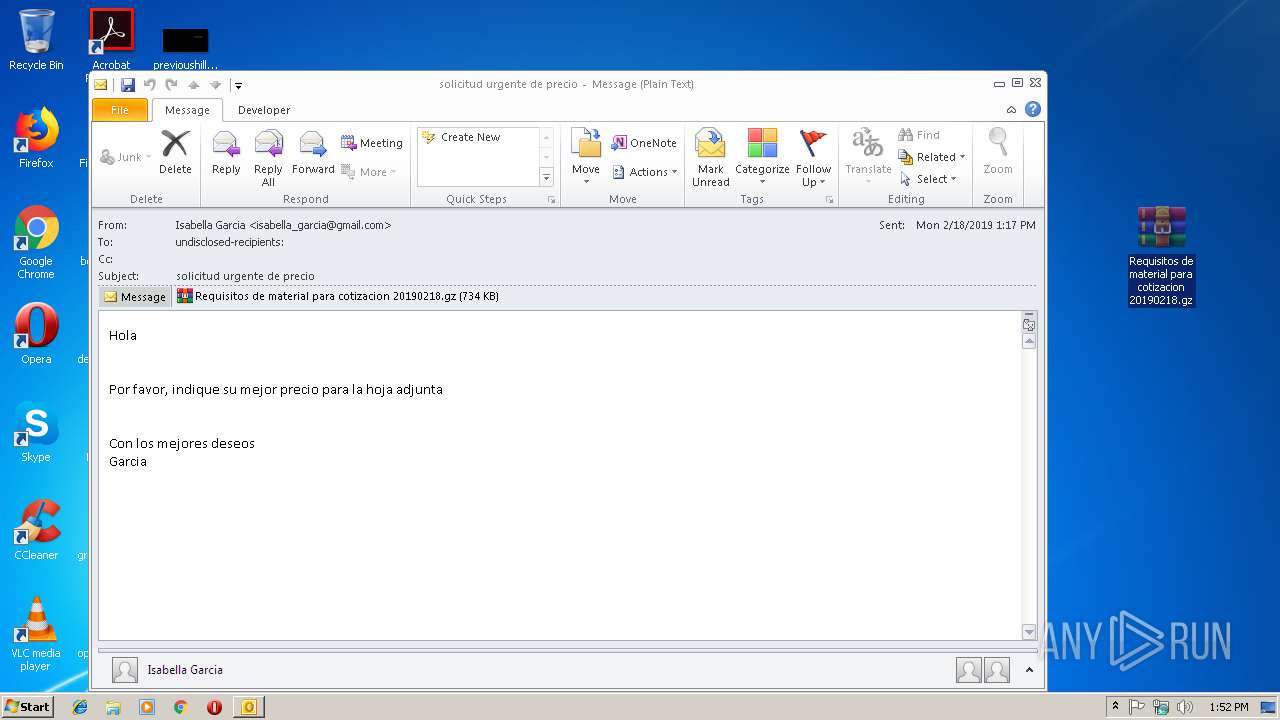
| File name: | Vir.eml |
| Full analysis: | https://app.any.run/tasks/2fa76e1f-8f26-4931-a634-9b4cac9af7bc |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | February 18, 2019, 13:52:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | A21228BB7B5D227951B67FBEDB475143 |
| SHA1: | 053969D5E1A7CD22EE09F5908477911CD09B48EC |
| SHA256: | 8369A0B40FF3FA52AF6B7A2111574B69723F220CBA1E7771BB82830EB1B5B594 |
| SSDEEP: | 12288:TqscwGixep7hvTZ2s74WMOCU6SVCzo9IMleuNIzH2hAQ92PhzQ014ZaWQa2xl8Up:+9qwp7hvT/71CnoXfaAAQjSCgRWDZev |
MALICIOUS
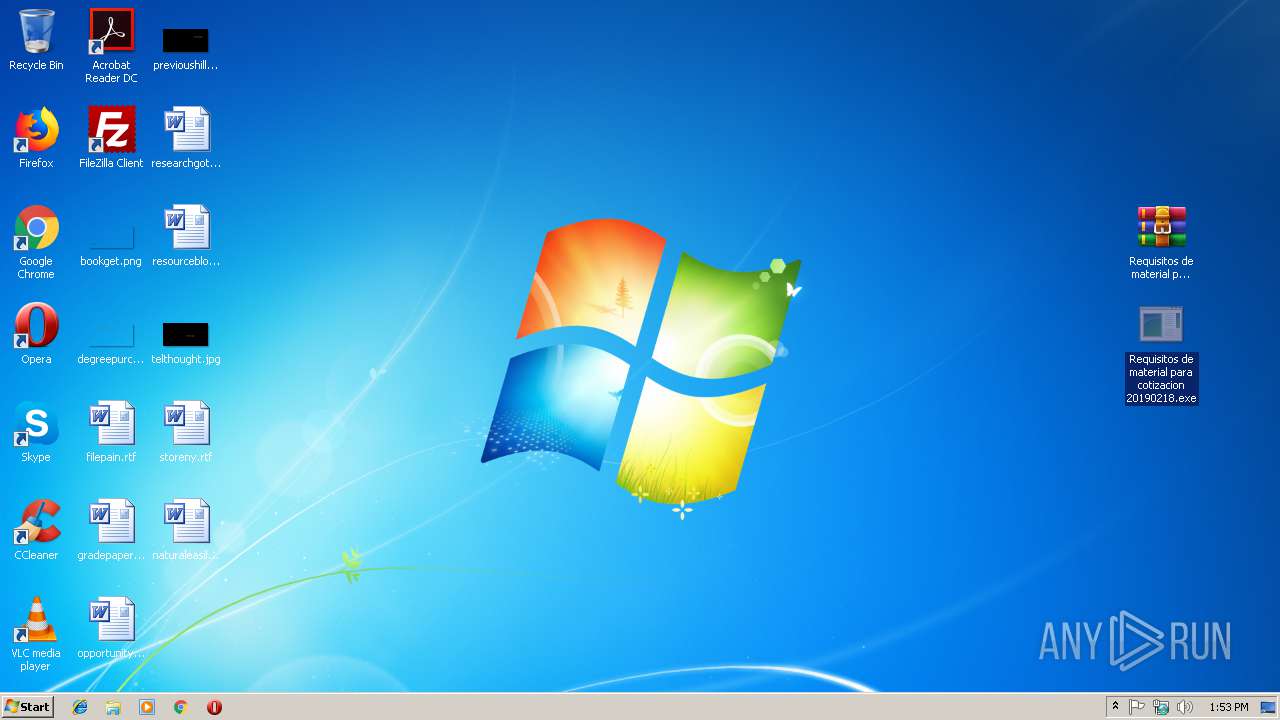
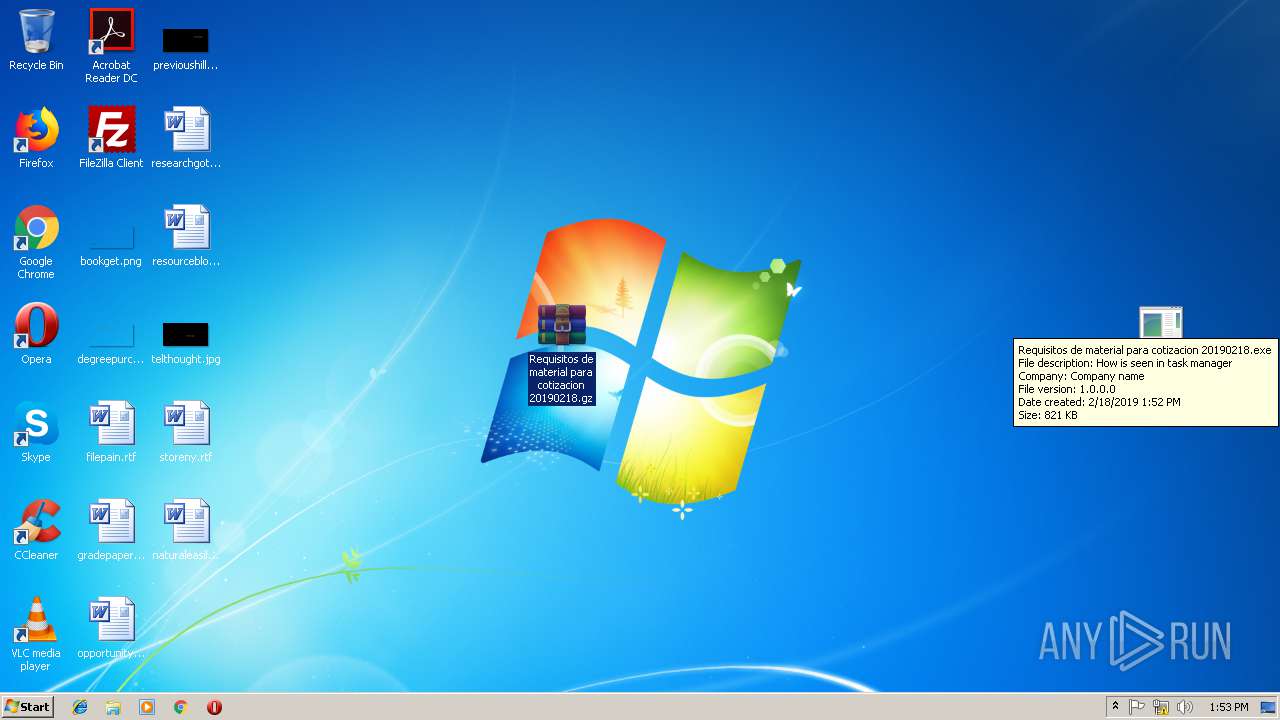
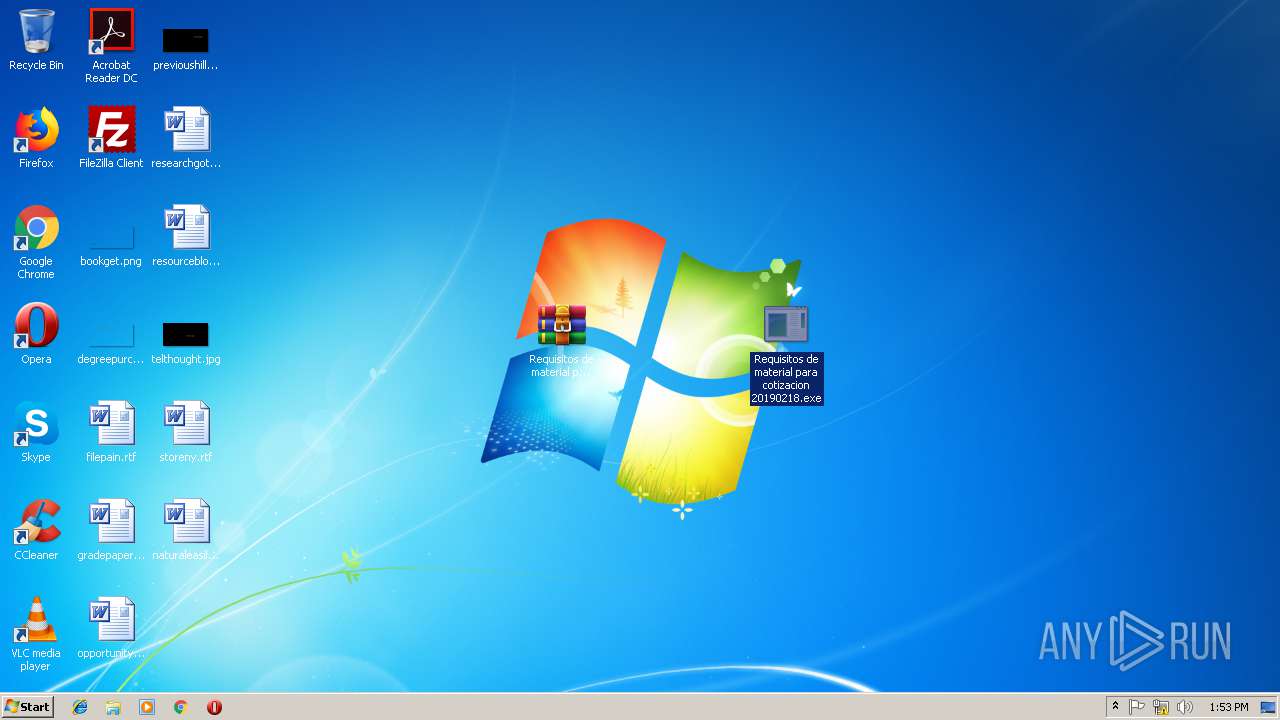
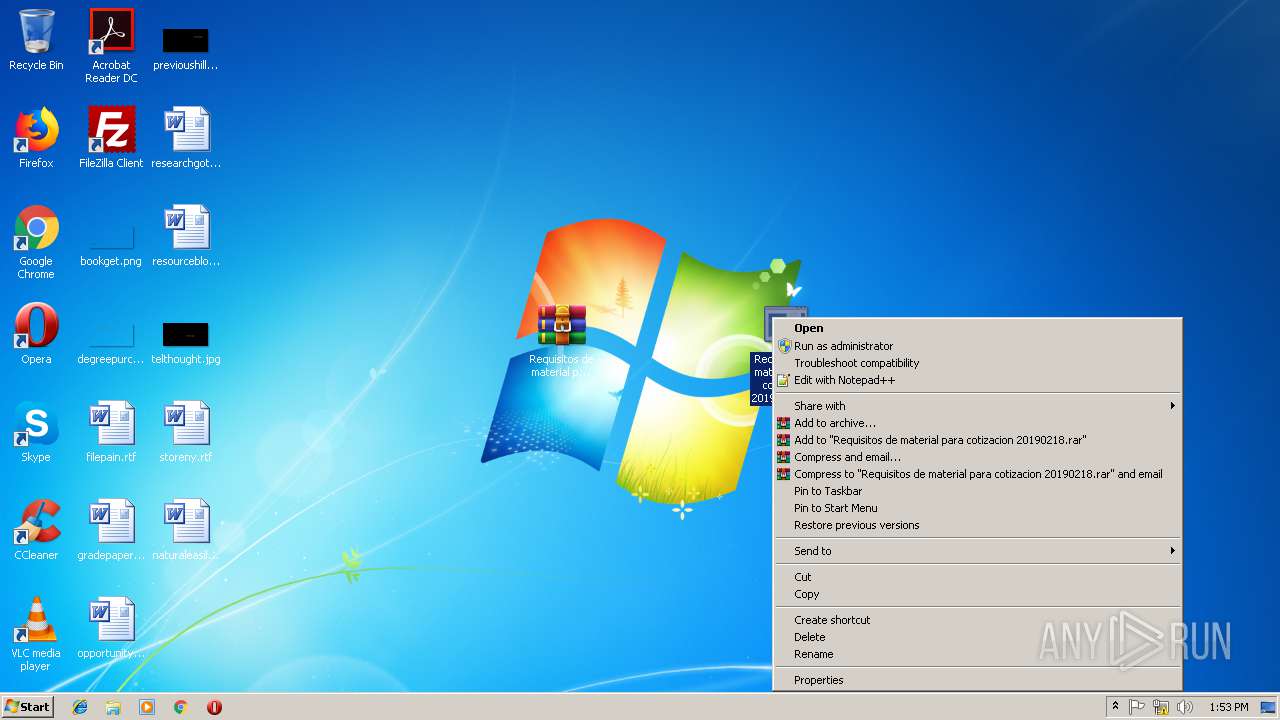
Application was dropped or rewritten from another process
- Requisitos de material para cotizacion 20190218.exe (PID: 4008)
- Requisitos de material para cotizacion 20190218.exe (PID: 3328)
- Requisitos de material para cotizacion 20190218.exe (PID: 252)
- Requisitos de material para cotizacion 20190218.exe (PID: 2508)
Stealing of credential data
- vbc.exe (PID: 2808)
- vbc.exe (PID: 3284)
- vbc.exe (PID: 2328)
- vbc.exe (PID: 824)
Detected Hawkeye Keylogger
- Requisitos de material para cotizacion 20190218.exe (PID: 4008)
- Requisitos de material para cotizacion 20190218.exe (PID: 2508)
Actions looks like stealing of personal data
- vbc.exe (PID: 3284)
- vbc.exe (PID: 2808)
- vbc.exe (PID: 824)
- vbc.exe (PID: 2328)
SUSPICIOUS
Connects to unusual port
- Requisitos de material para cotizacion 20190218.exe (PID: 4008)
- Requisitos de material para cotizacion 20190218.exe (PID: 2508)
Executes scripts
- Requisitos de material para cotizacion 20190218.exe (PID: 4008)
- Requisitos de material para cotizacion 20190218.exe (PID: 2508)
Reads Environment values
- Requisitos de material para cotizacion 20190218.exe (PID: 4008)
- Requisitos de material para cotizacion 20190218.exe (PID: 2508)
Reads Internet Cache Settings
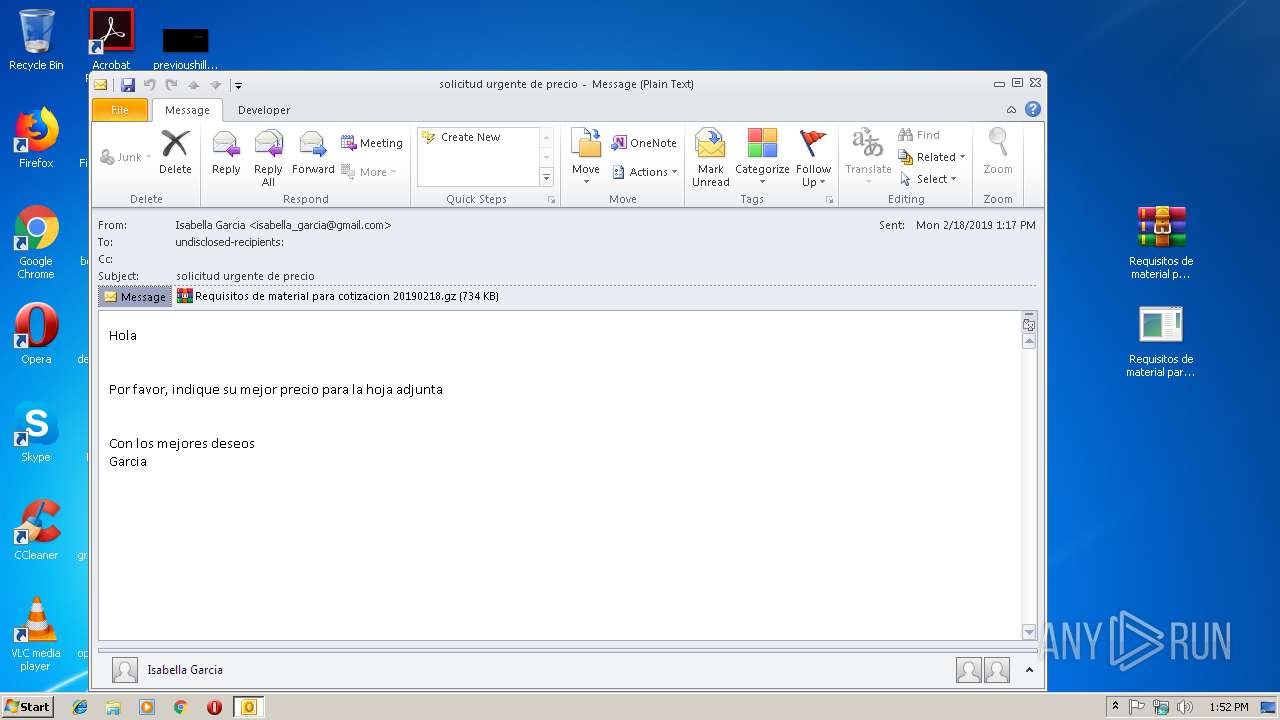
- OUTLOOK.EXE (PID: 3028)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3028)
Application launched itself
- Requisitos de material para cotizacion 20190218.exe (PID: 3328)
- Requisitos de material para cotizacion 20190218.exe (PID: 252)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3284)
- vbc.exe (PID: 824)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
10
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
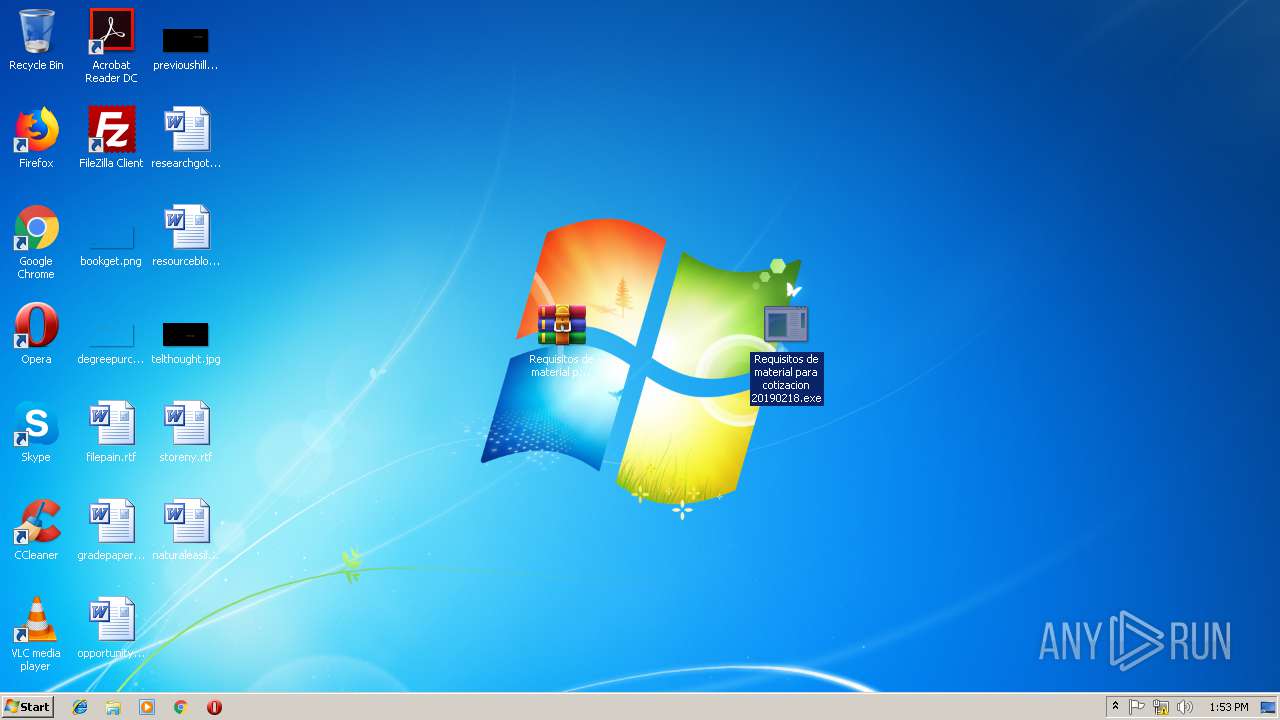
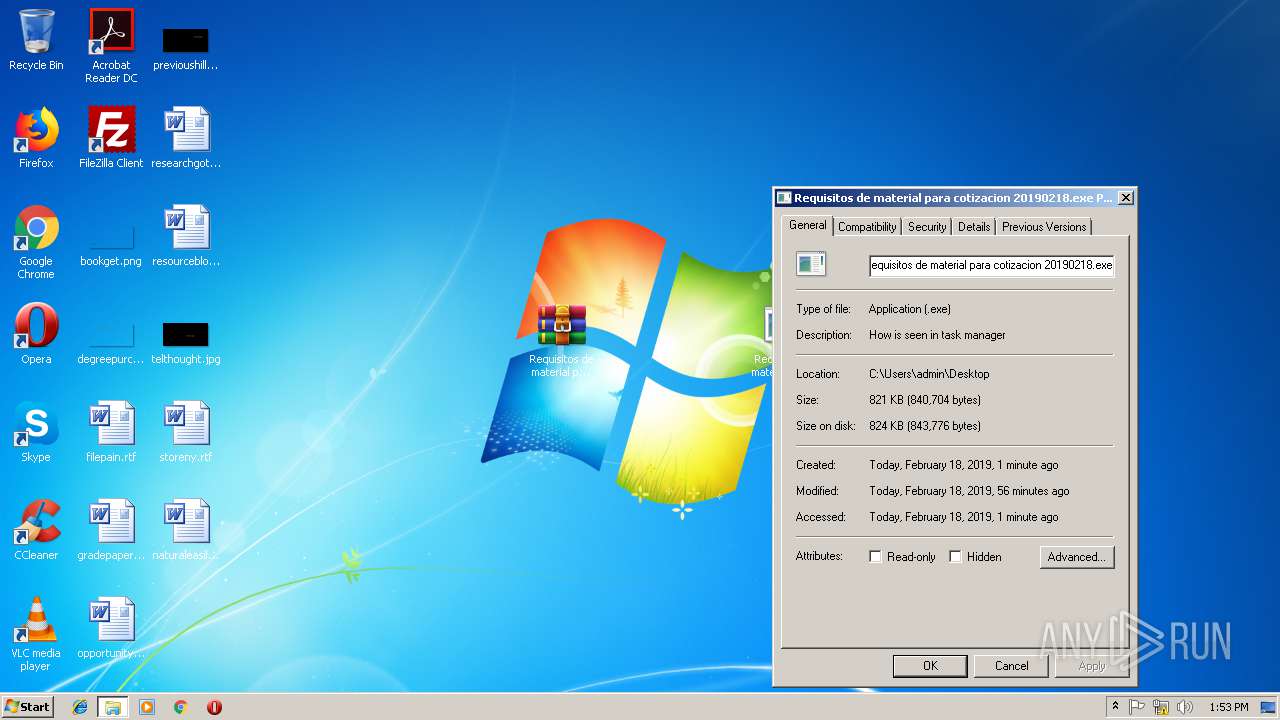
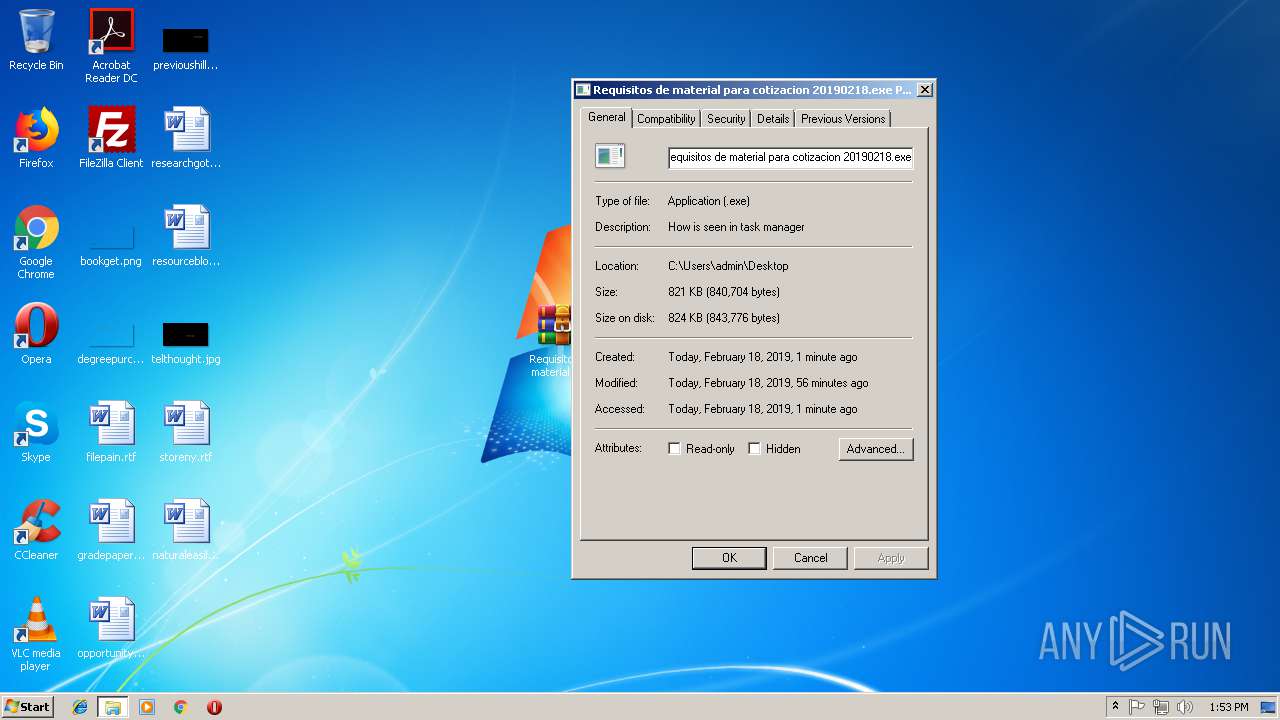
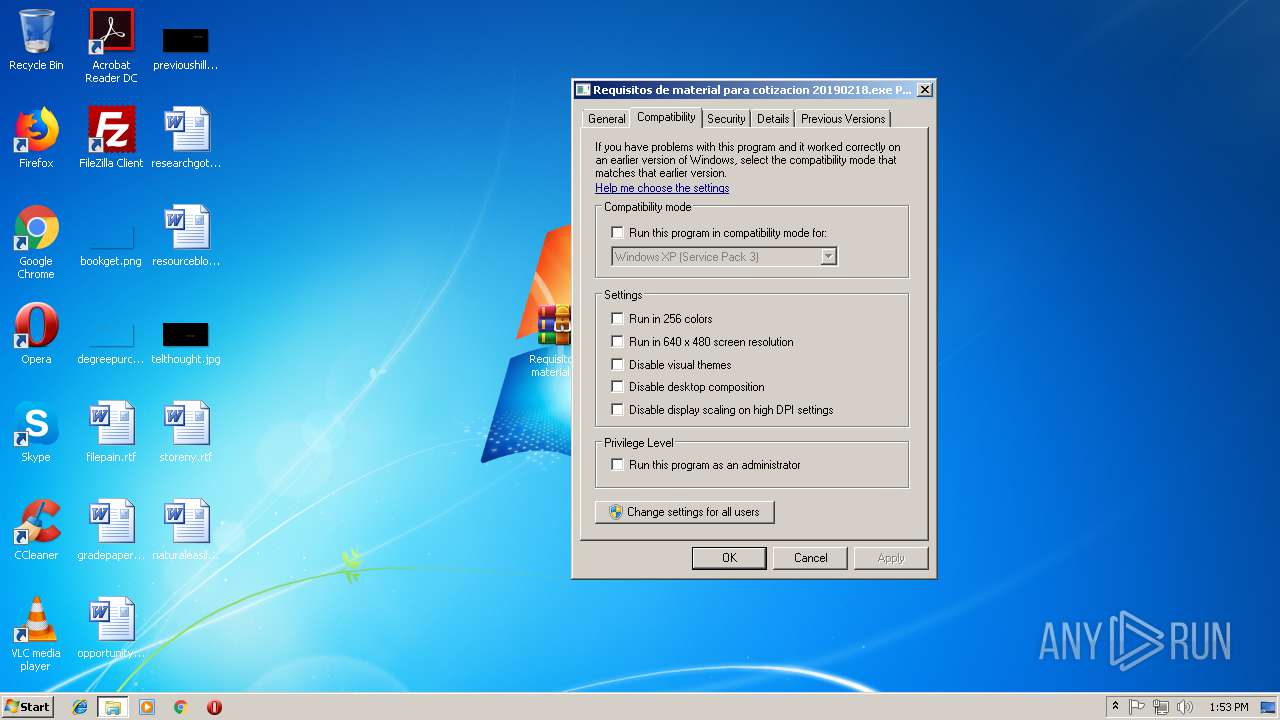
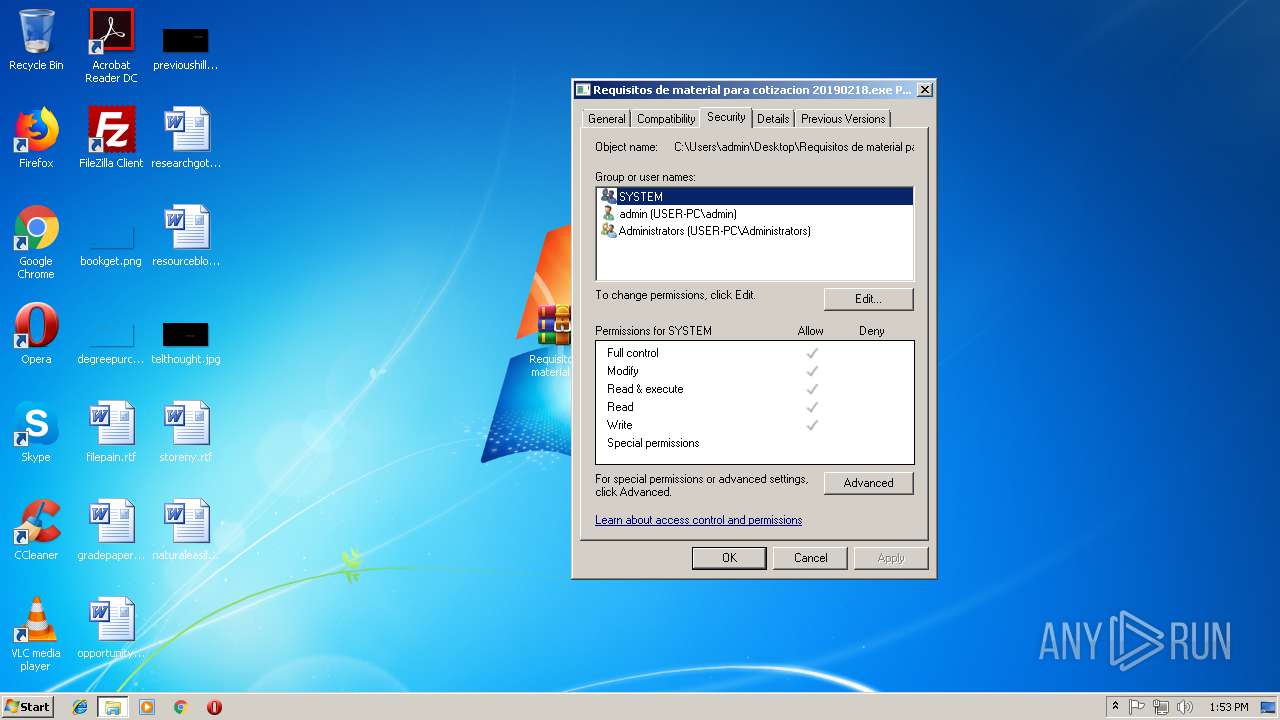
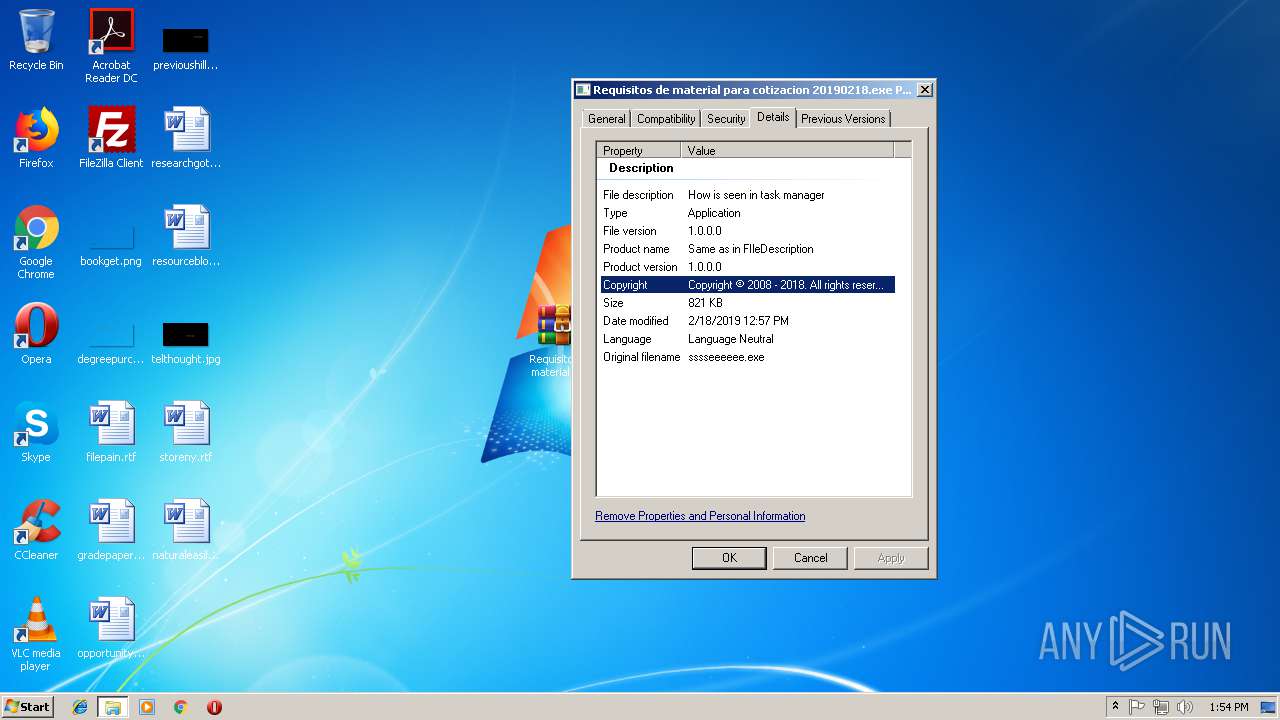
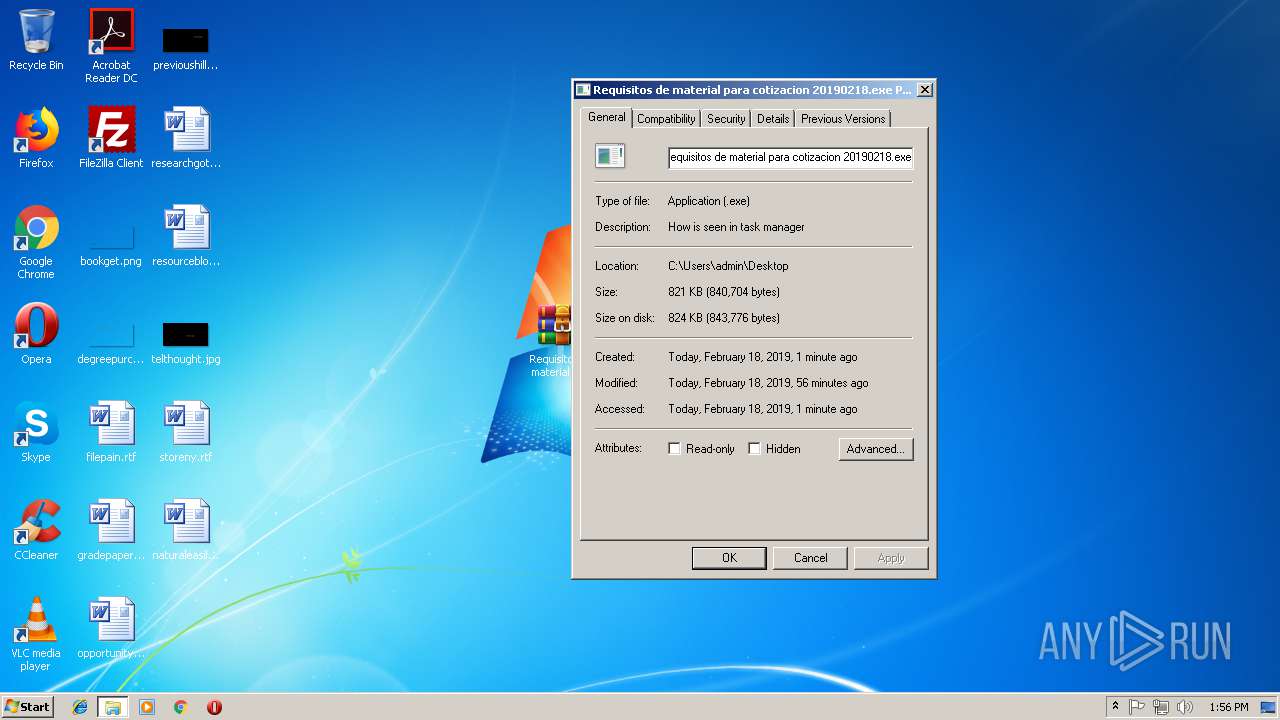
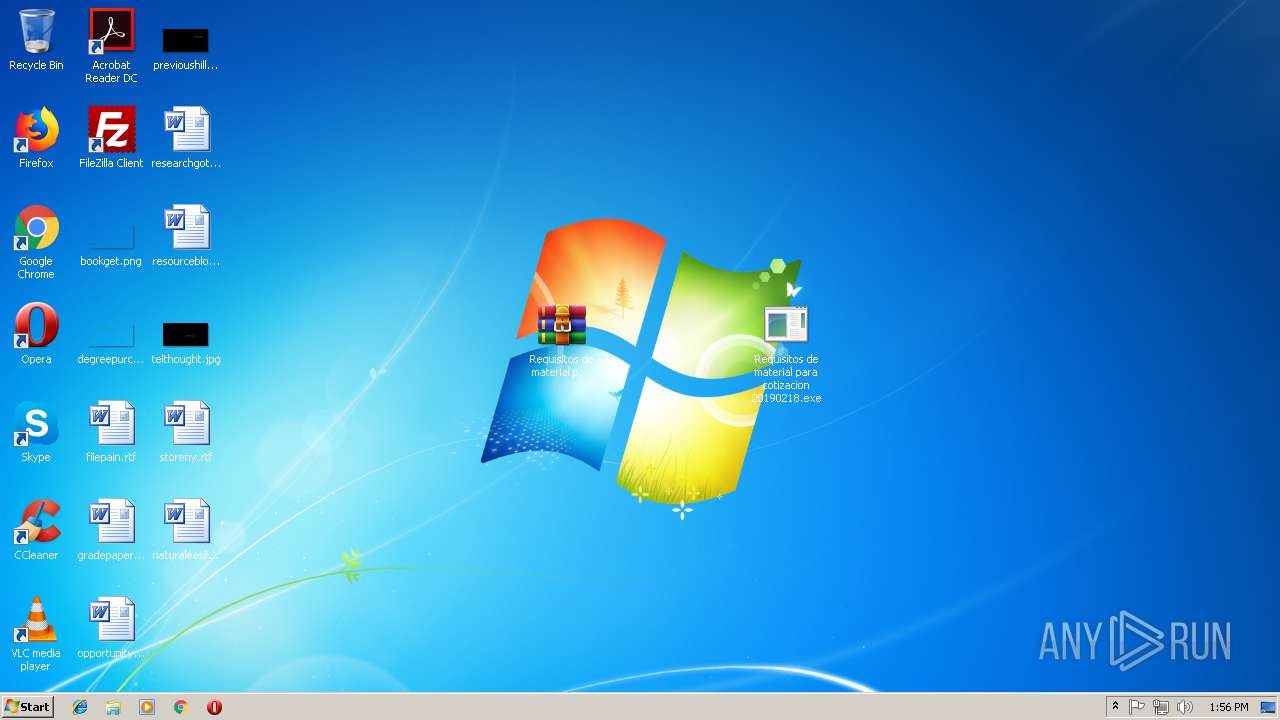
| 252 | "C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe" | C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe | — | explorer.exe | |||||||||||
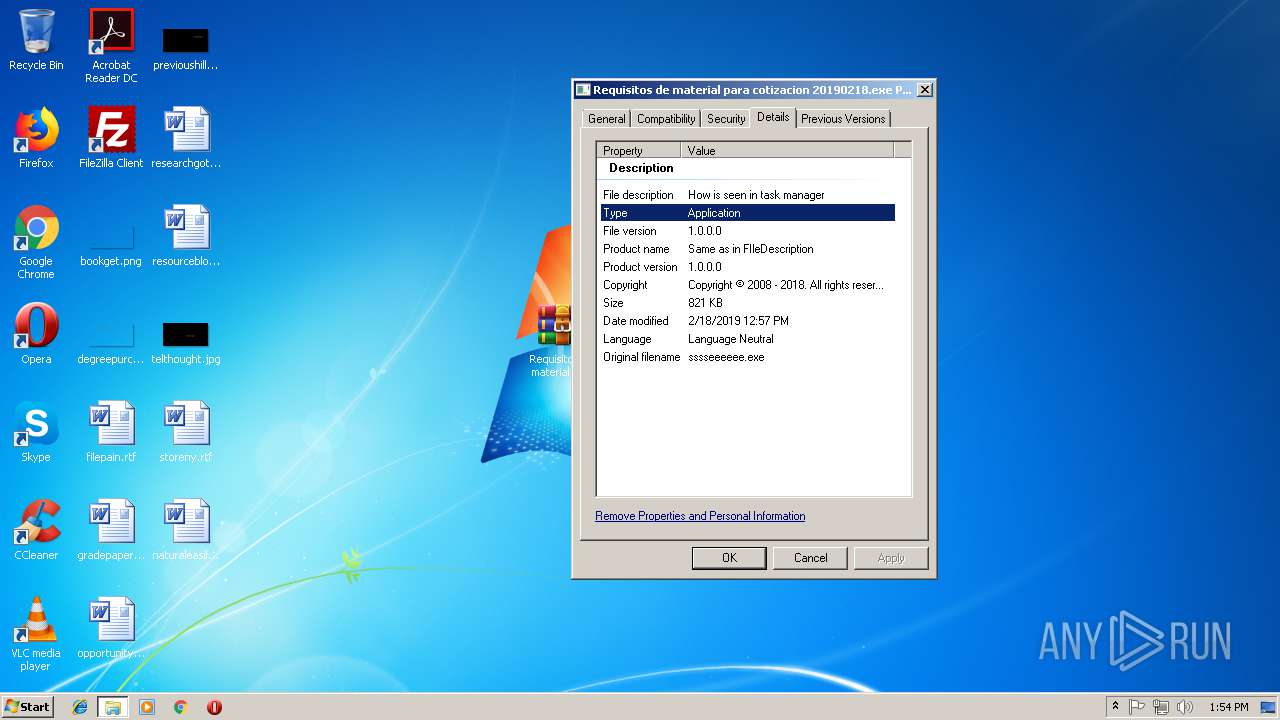
User: admin Company: Company name Integrity Level: MEDIUM Description: How is seen in task manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 824 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp4A52.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Requisitos de material para cotizacion 20190218.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2328 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp4E4A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Requisitos de material para cotizacion 20190218.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe" | C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe | Requisitos de material para cotizacion 20190218.exe | ||||||||||||
User: admin Company: Company name Integrity Level: MEDIUM Description: How is seen in task manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
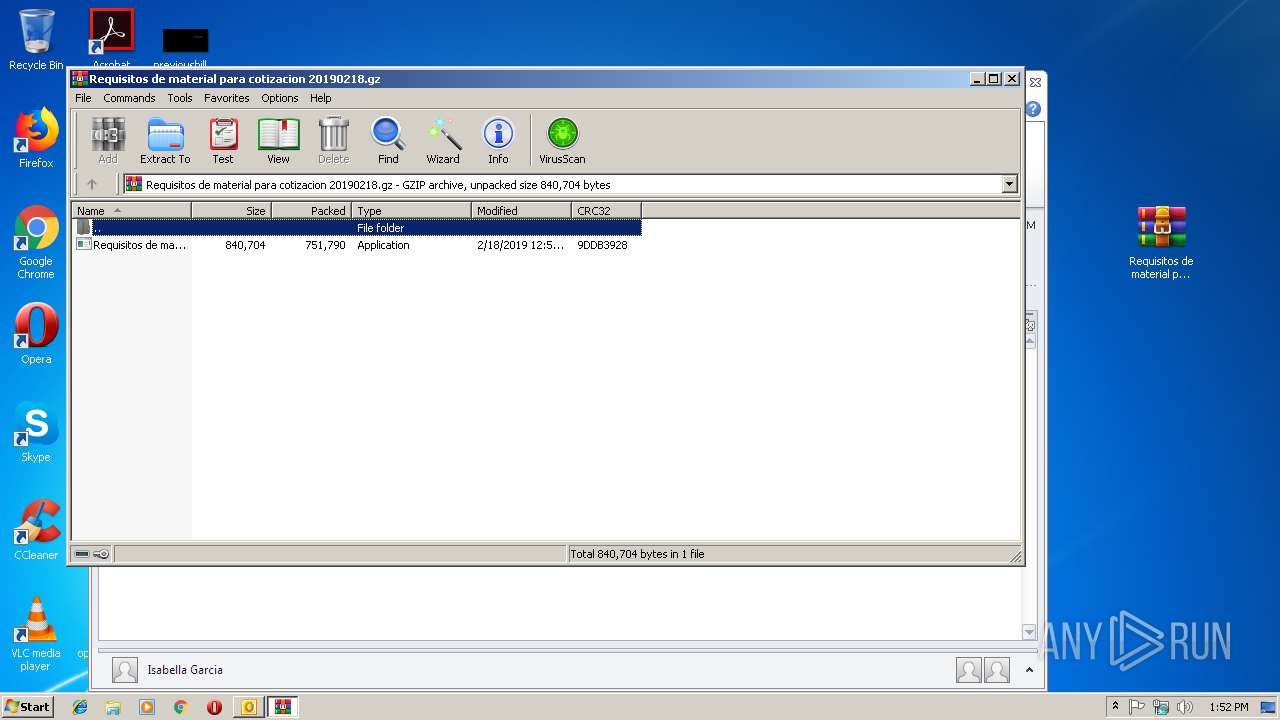
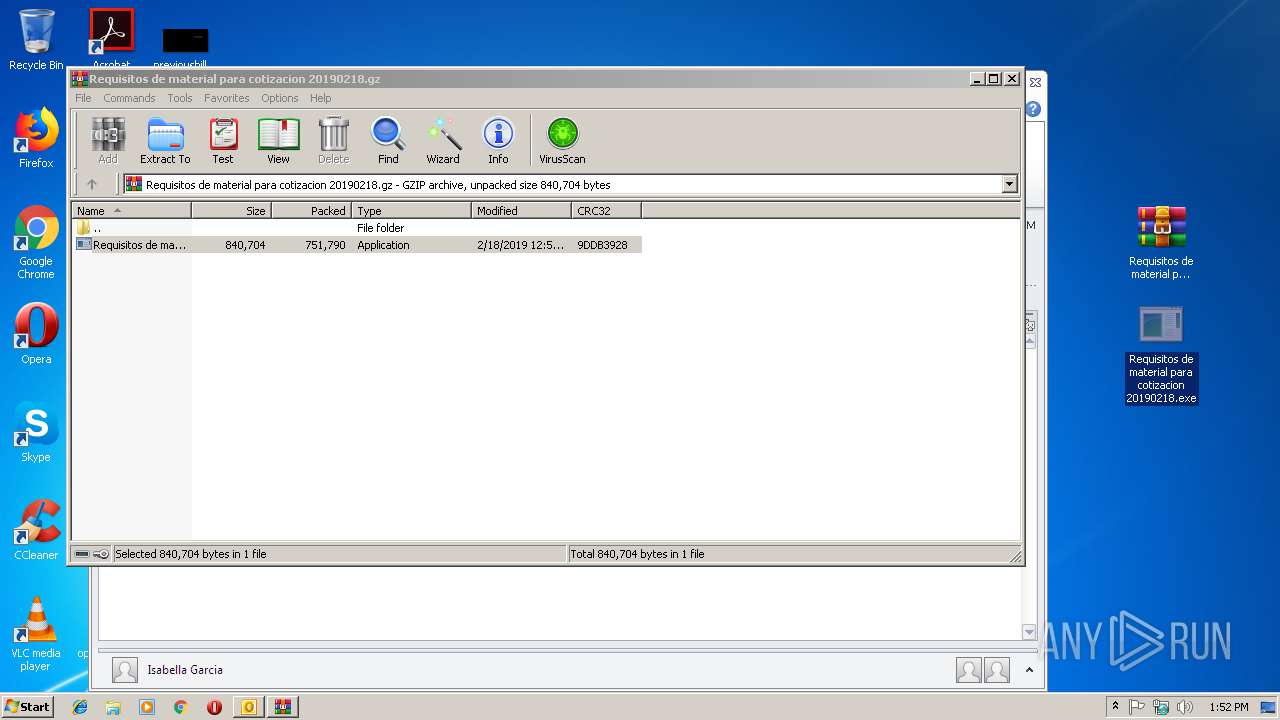
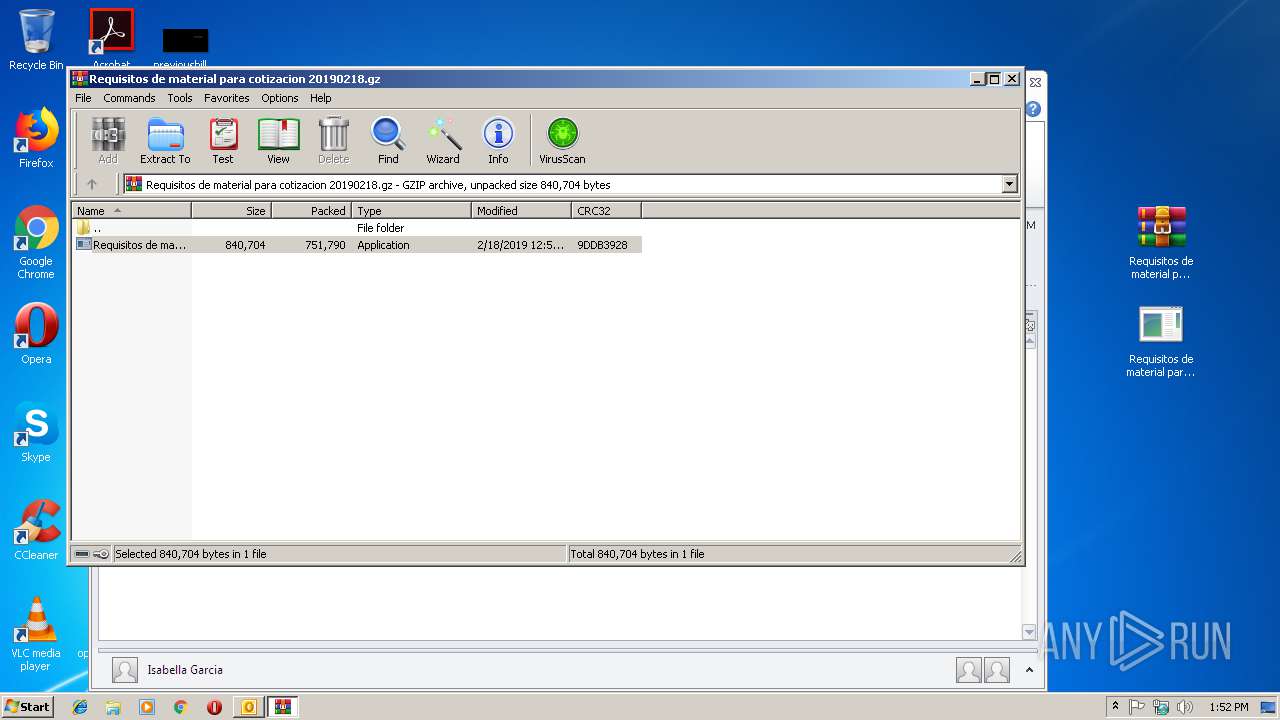
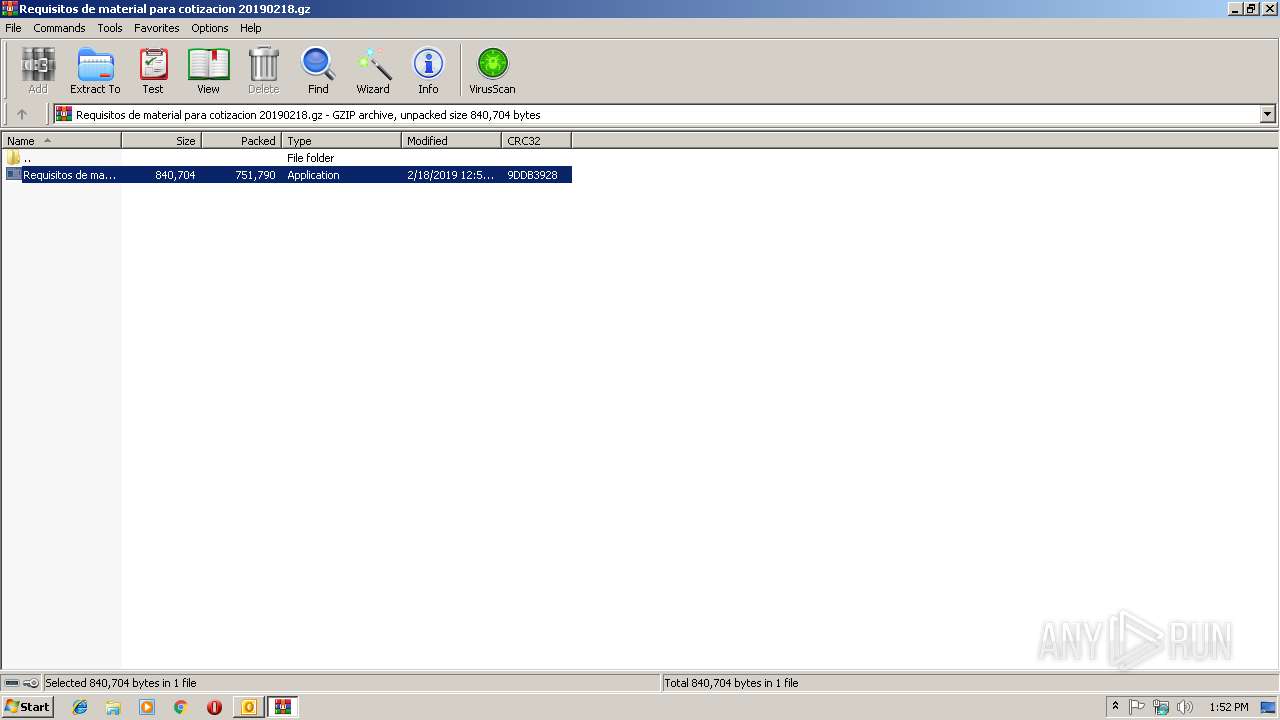
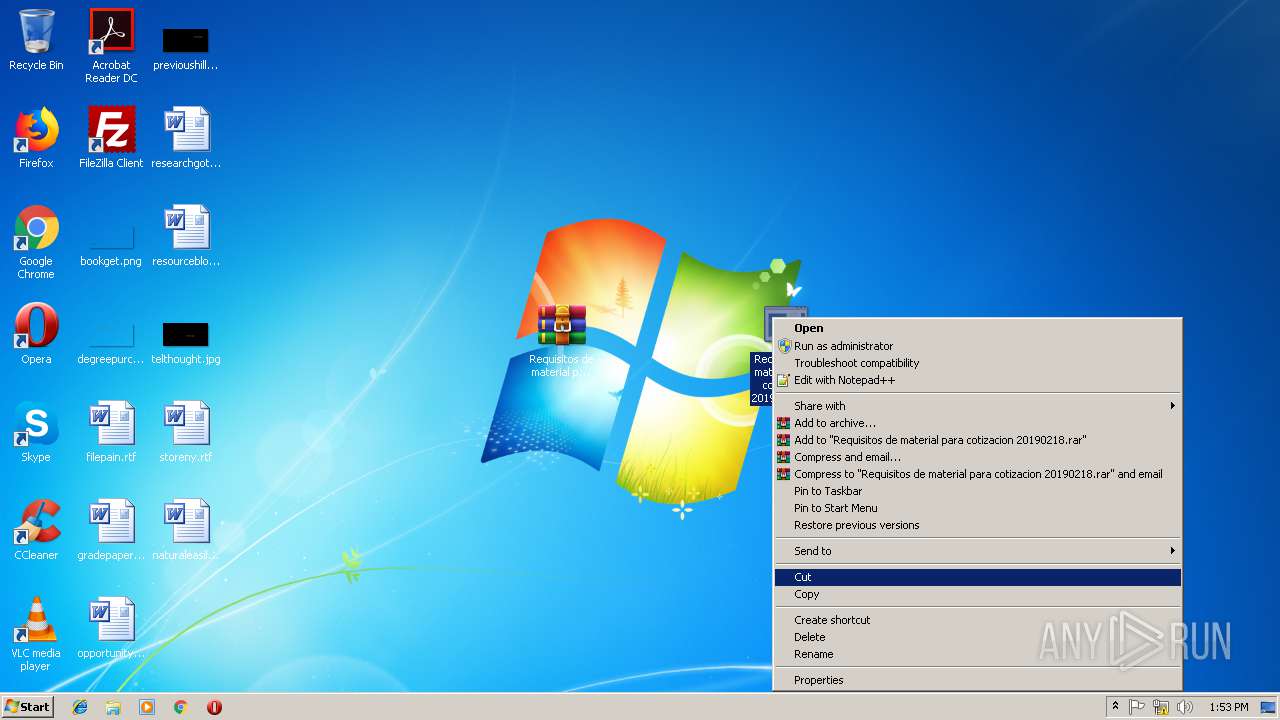
| 2596 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.gz" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2808 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp219D.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Requisitos de material para cotizacion 20190218.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3028 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Vir.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3284 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpB35.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Requisitos de material para cotizacion 20190218.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe" | C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe | — | explorer.exe | |||||||||||
User: admin Company: Company name Integrity Level: MEDIUM Description: How is seen in task manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe" | C:\Users\admin\Desktop\Requisitos de material para cotizacion 20190218.exe | Requisitos de material para cotizacion 20190218.exe | ||||||||||||
User: admin Company: Company name Integrity Level: MEDIUM Description: How is seen in task manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 810
Read events
1 357
Write events
433
Delete events
20
Modification events
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | }`, |
Value: 7D602C00D40B0000010000000000000000000000 | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: D40B0000D8F9A82891C7D40100000000 | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219915360 | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3028) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1313996821 | |||
Executable files
0
Suspicious files
2
Text files
29
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE8DD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpEA84.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2596.45650\Requisitos de material para cotizacion 20190218.exe | — | |
MD5:— | SHA256:— | |||
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFA102C800C22B8147.TMP | — | |
MD5:— | SHA256:— | |||
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFAF76B8FF09CF96E8.TMP | — | |
MD5:— | SHA256:— | |||
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3BB45DD0-BAE2-4C54-BECF-06381A0D9060}.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4008 | Requisitos de material para cotizacion 20190218.exe | C:\Users\admin\AppData\Local\Temp\25291068-43af-3e16-50f6-5889d9ce7904 | text | |
MD5:— | SHA256:— | |||
| 3284 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpB35.tmp | text | |
MD5:— | SHA256:— | |||
| 3028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\UWOCFGNP\Requisitos de material para cotizacion 20190218.gz | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4008 | Requisitos de material para cotizacion 20190218.exe | 103.28.12.136:50160 | ftp.sanpacsinergi.co.id | PT Qwords Company International | ID | malicious |
2508 | Requisitos de material para cotizacion 20190218.exe | 103.28.12.136:21 | ftp.sanpacsinergi.co.id | PT Qwords Company International | ID | malicious |
2508 | Requisitos de material para cotizacion 20190218.exe | 103.28.12.136:50800 | ftp.sanpacsinergi.co.id | PT Qwords Company International | ID | malicious |
4008 | Requisitos de material para cotizacion 20190218.exe | 103.28.12.136:21 | ftp.sanpacsinergi.co.id | PT Qwords Company International | ID | malicious |
3028 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
ftp.sanpacsinergi.co.id |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4008 | Requisitos de material para cotizacion 20190218.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2508 | Requisitos de material para cotizacion 20190218.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |