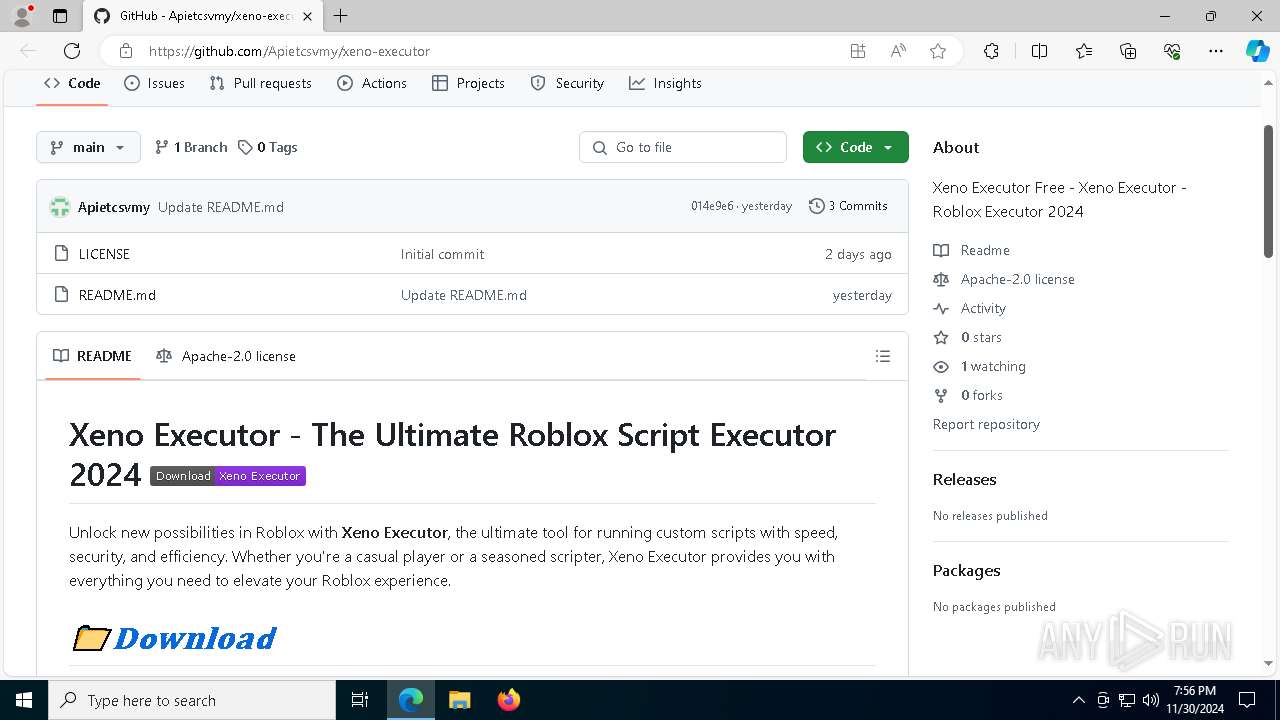
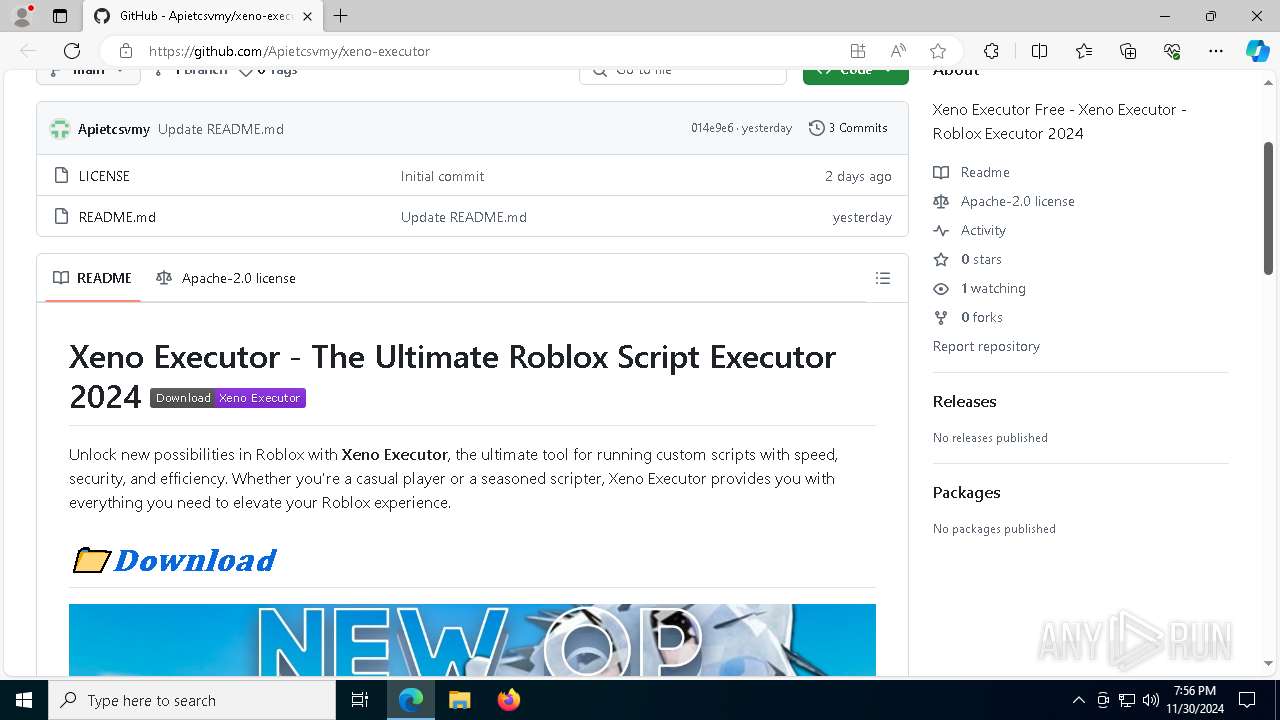
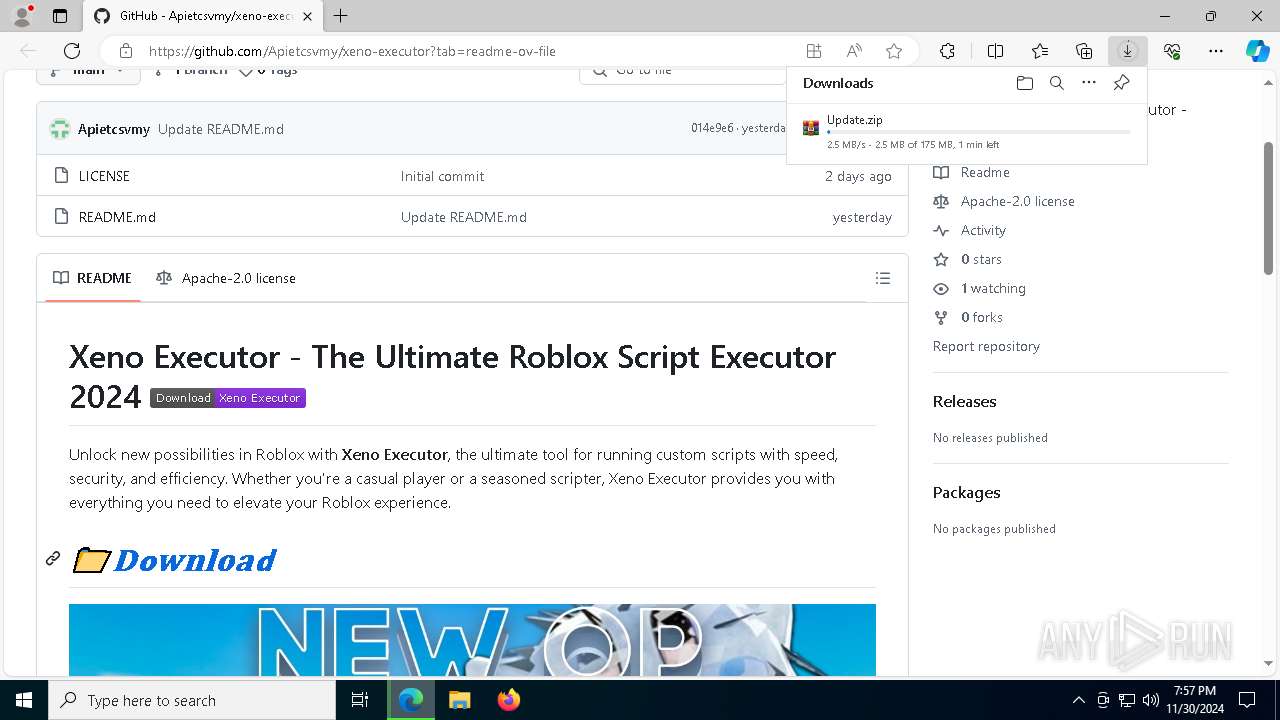
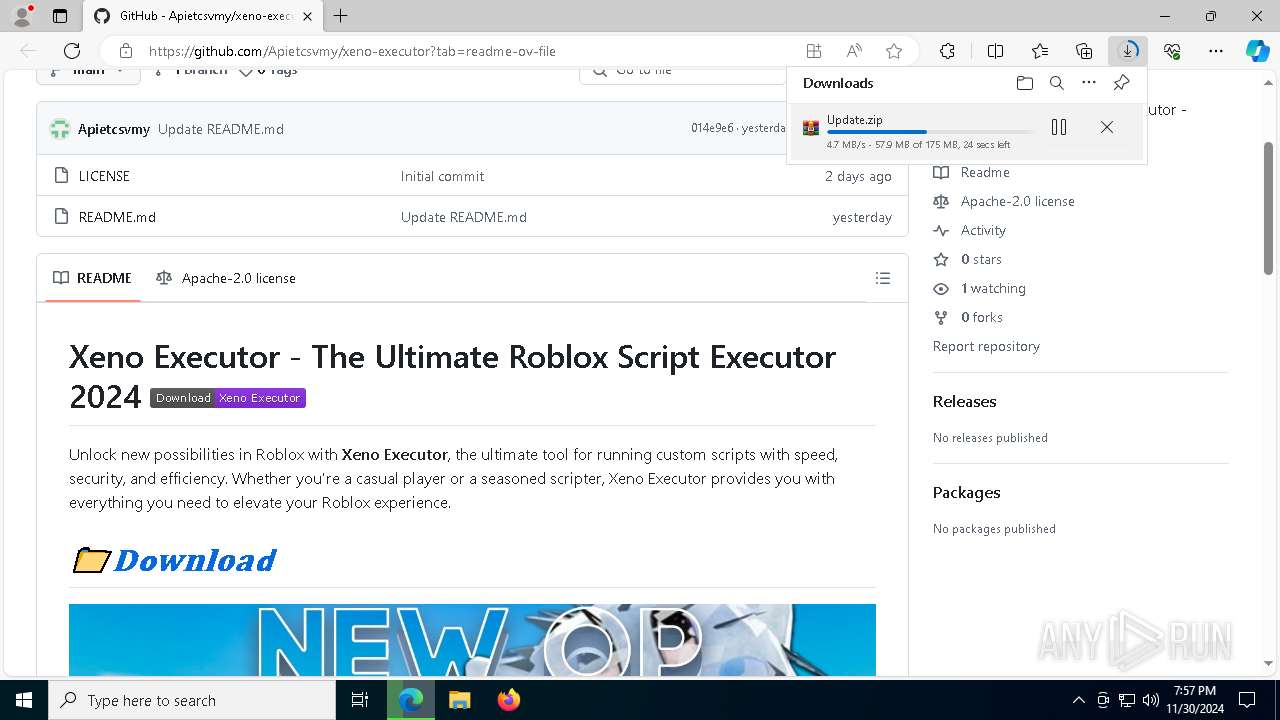
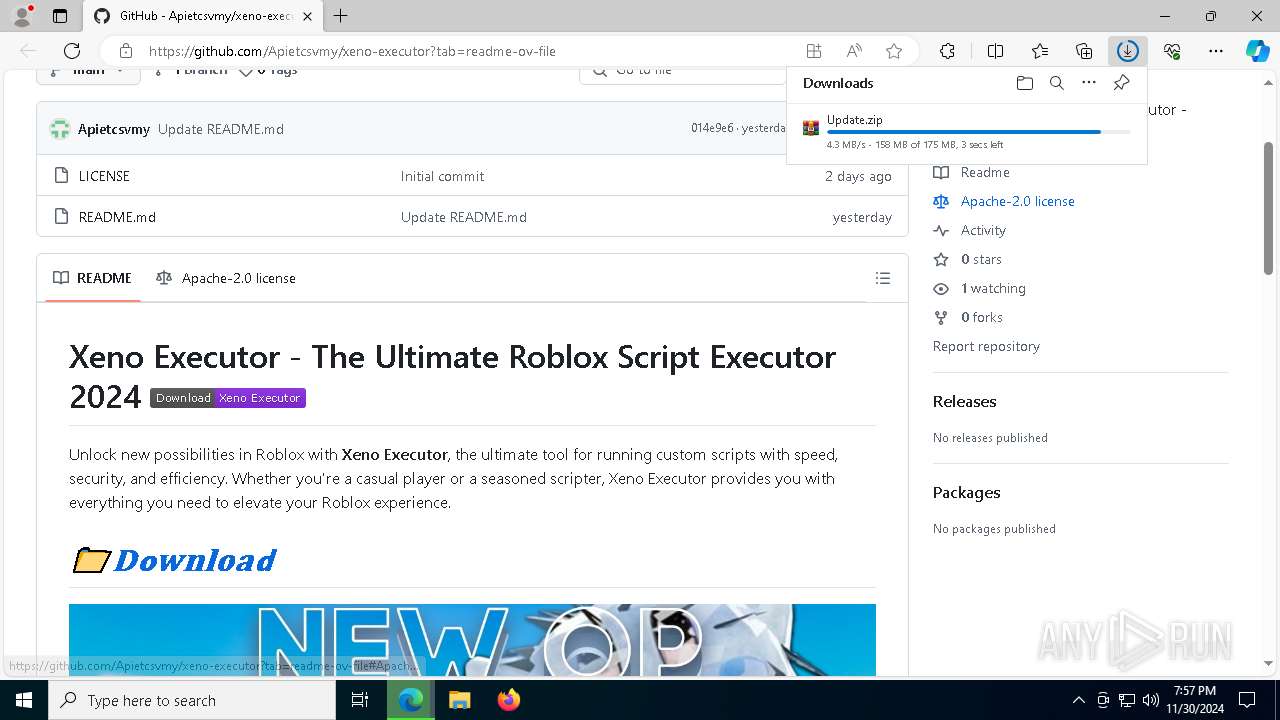
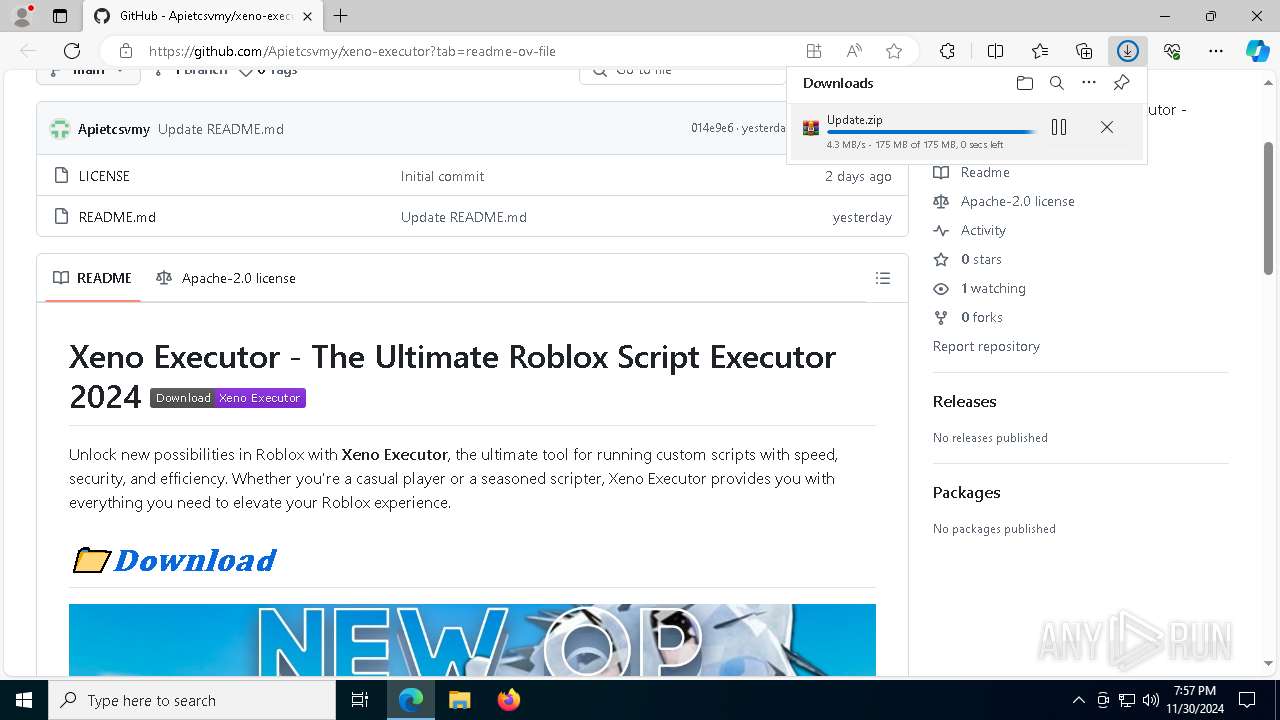
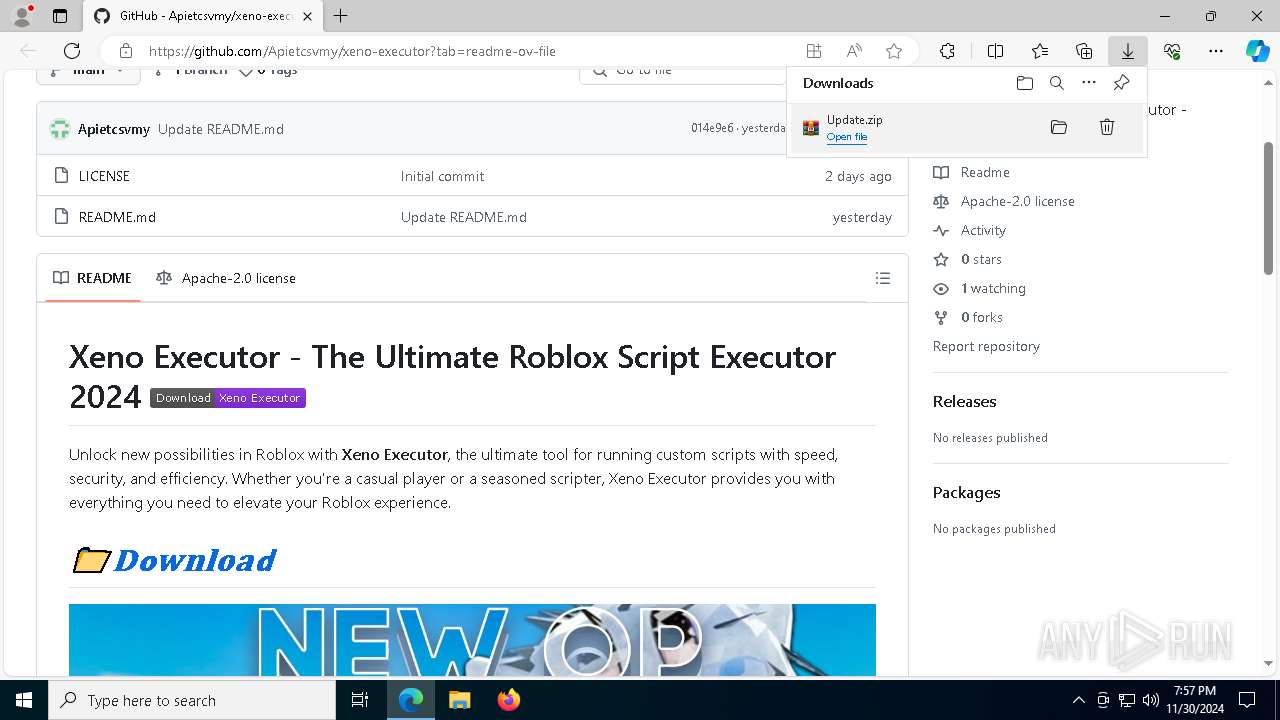
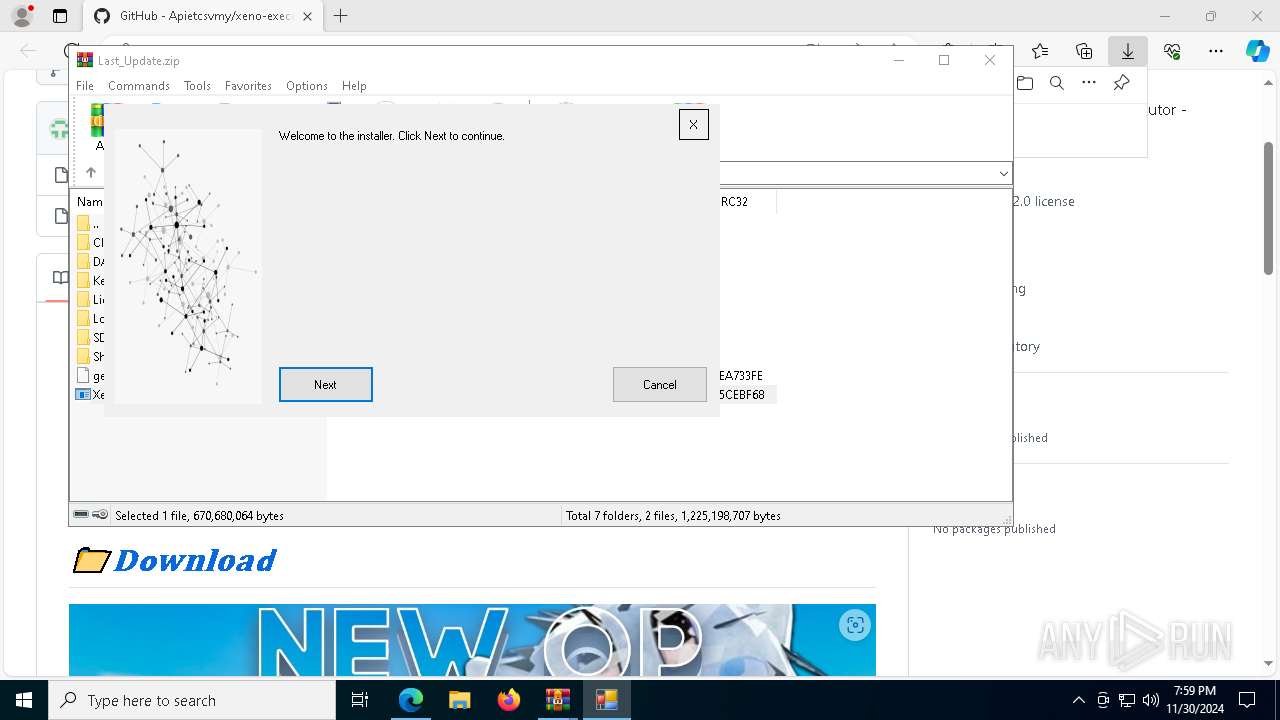
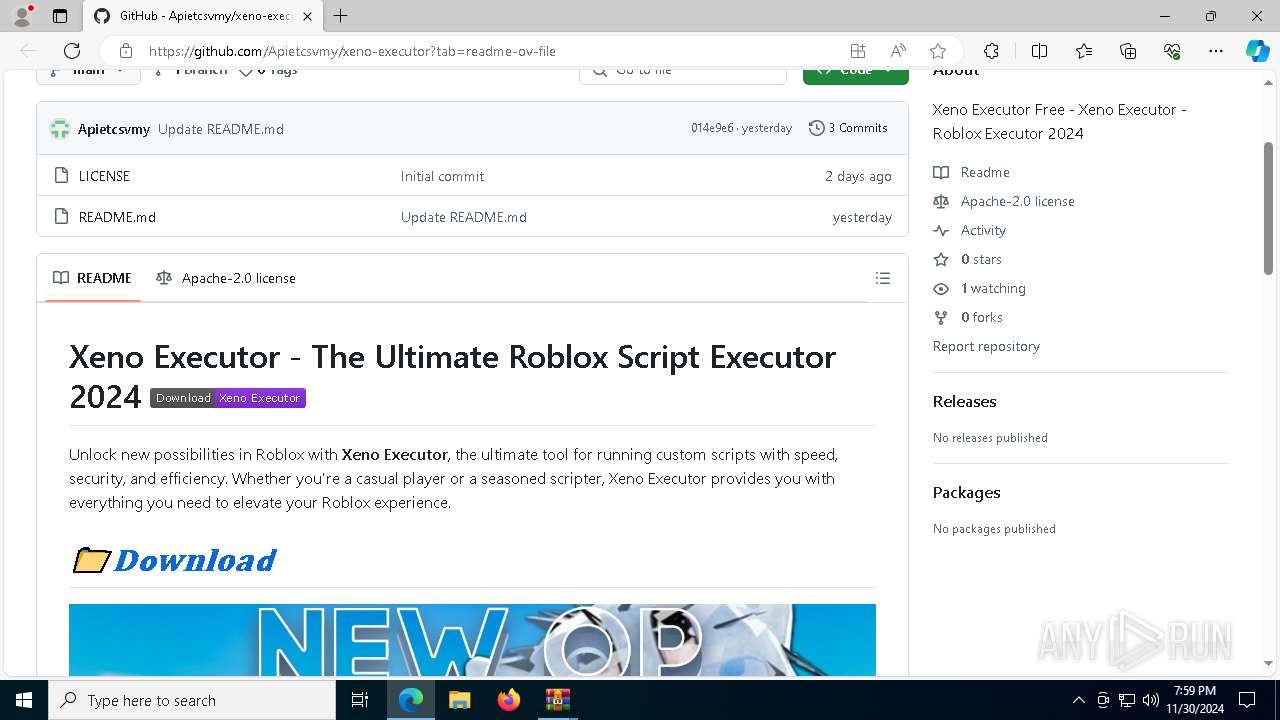
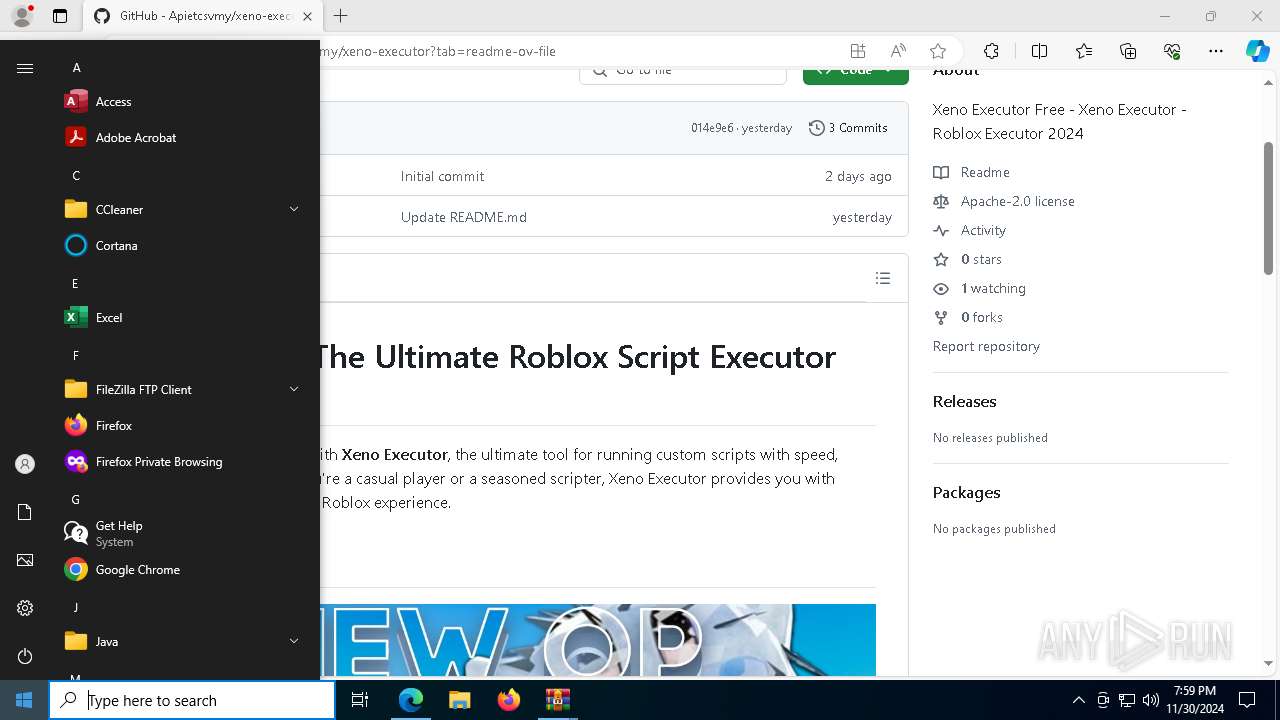
| URL: | https://github.com/Apietcsvmy/xeno-executor |
| Full analysis: | https://app.any.run/tasks/ee443c27-309b-48bd-b3bf-4c3c5ad8ae85 |
| Verdict: | Malicious activity |
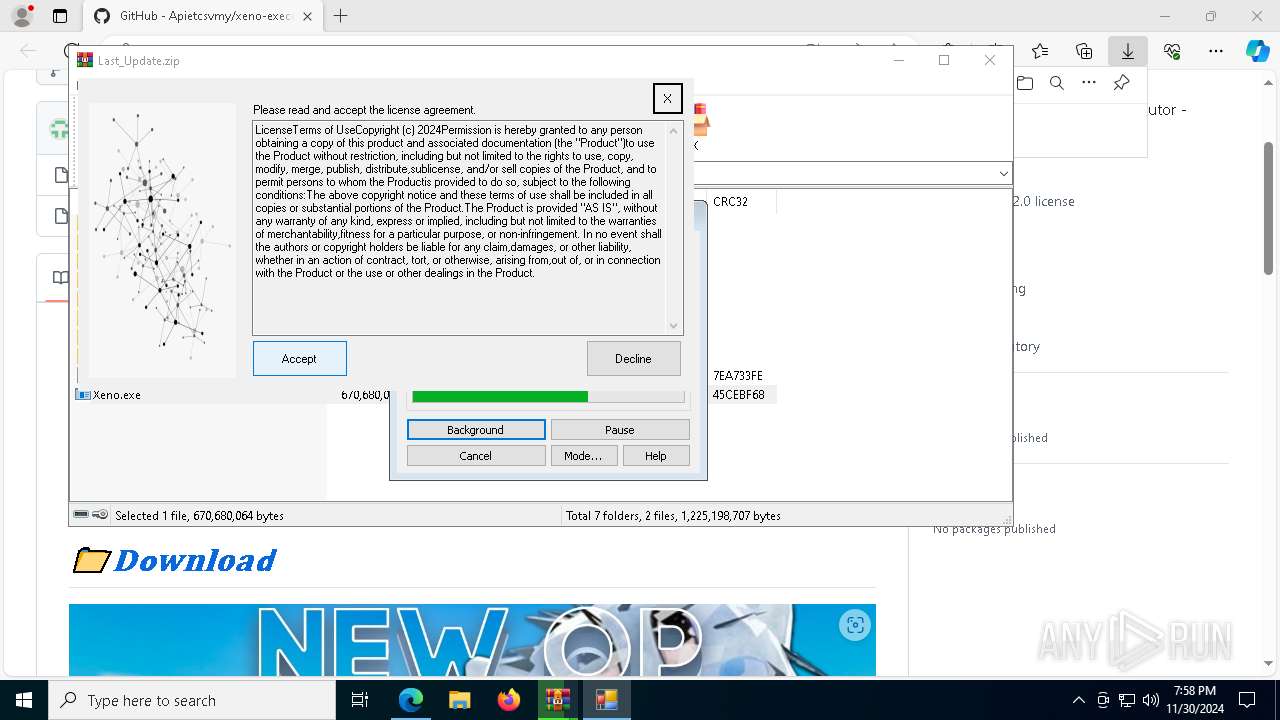
| Threats: | Meduza Stealer is an information-stealing malware primarily targeting Windows systems, designed to harvest sensitive data such as login credentials, browsing histories, cookies, cryptocurrency wallets, and password manager data. It has advanced anti-detection mechanisms, allowing it to evade many antivirus programs. The malware is distributed through various means, including phishing emails and malicious links. It’s marketed on underground forums and Telegram channels. |
| Analysis date: | November 30, 2024, 19:56:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C5217B10833C4AEA924E7CAE19345AC1 |
| SHA1: | EF2254F400B4E22A2F4462CA249D6739A228901B |
| SHA256: | 831BE9BA02A167F9C7DA8CFB62FF59F28D4621FE18B7055F5C8E7FBF1AF129E4 |
| SSDEEP: | 3:N8tEdSfIZucAGQRM:2utZucsRM |
MALICIOUS
Steals credentials from Web Browsers
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Actions looks like stealing of personal data
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
MEDUZASTEALER has been detected (SURICATA)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Starts CMD.EXE for self-deleting
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
SUSPICIOUS
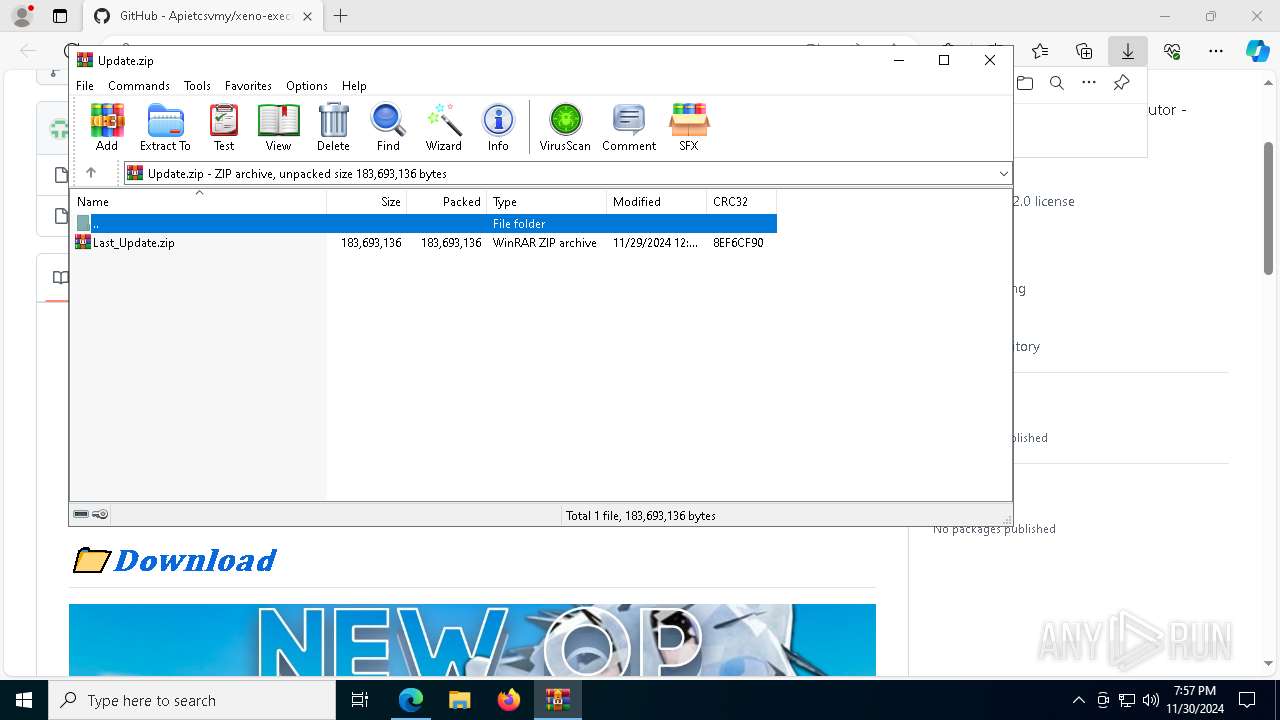
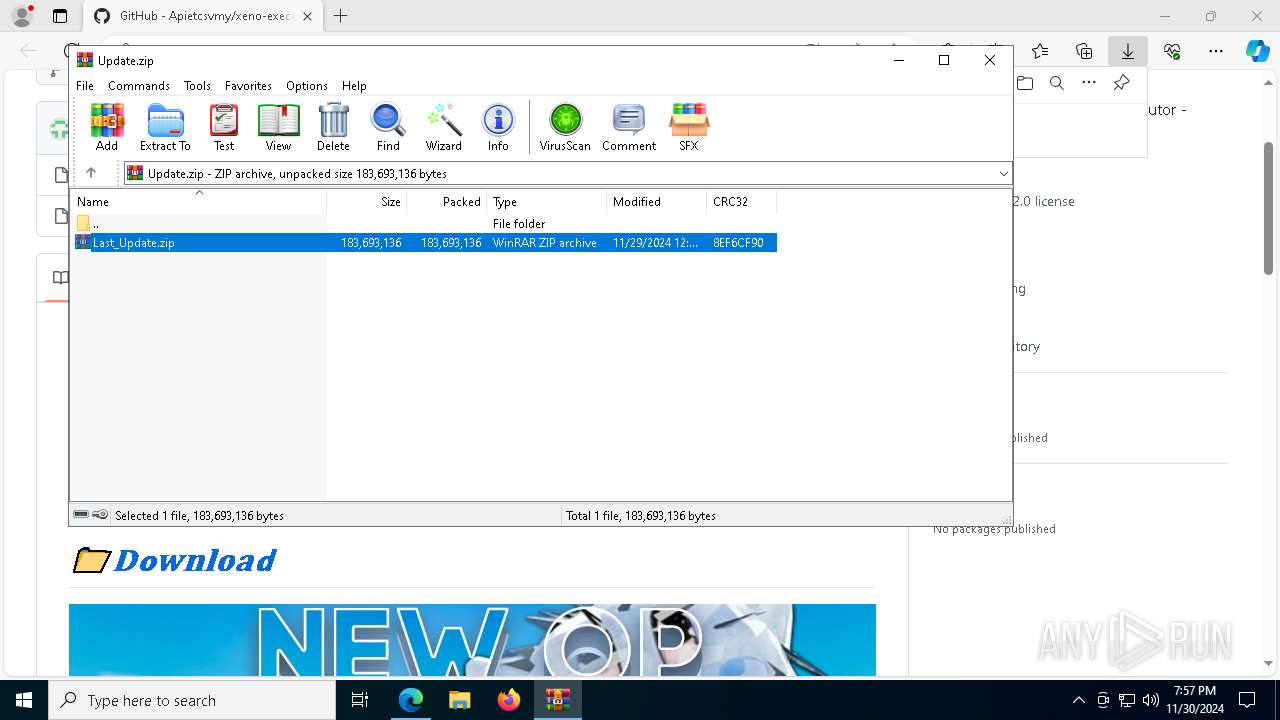
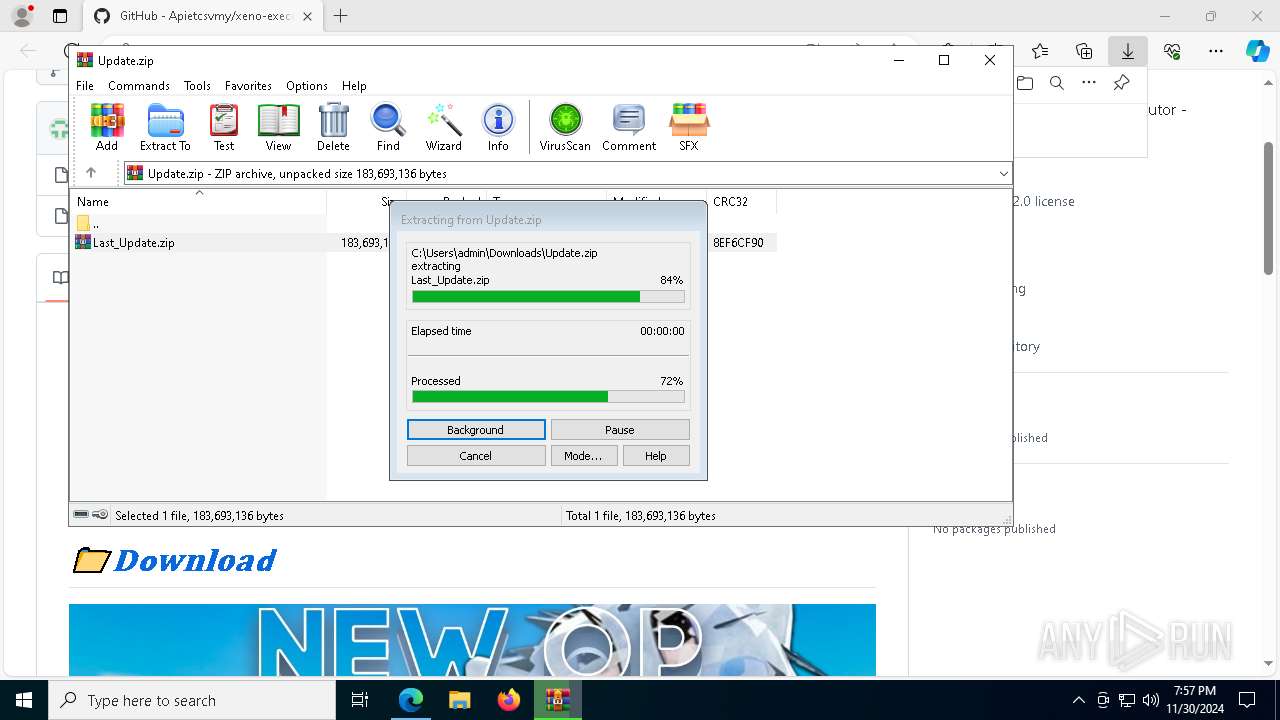
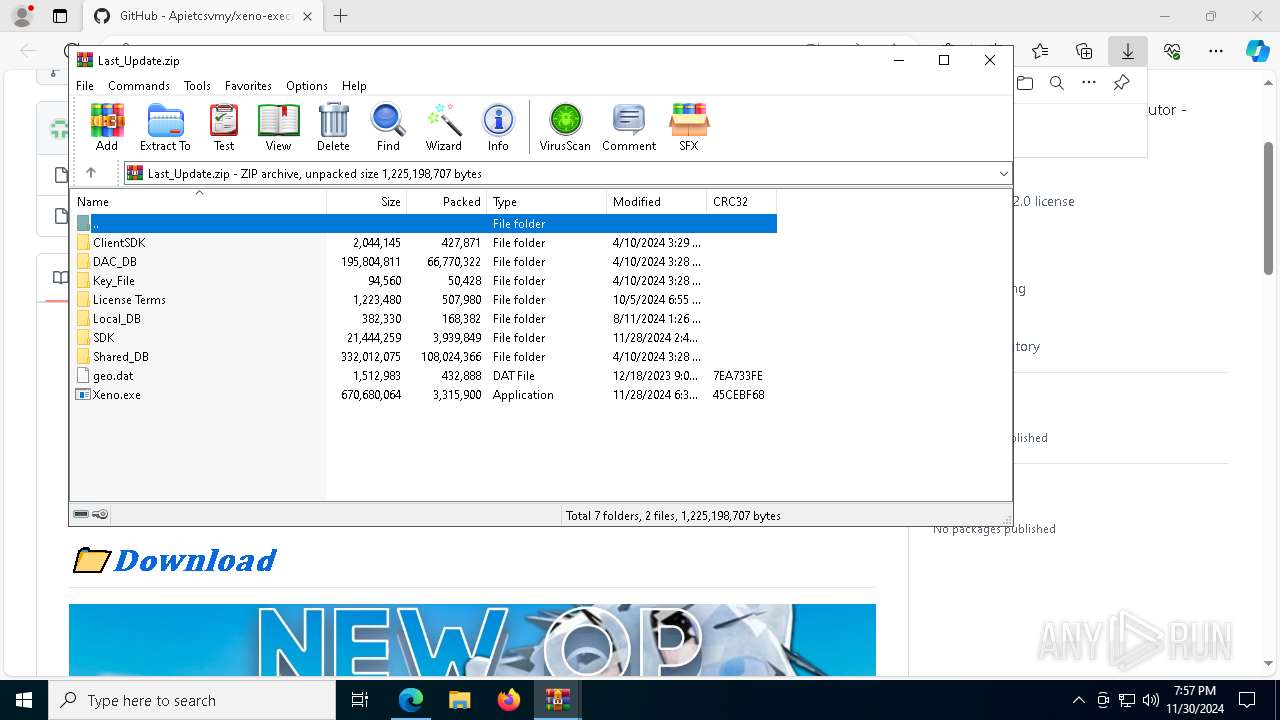
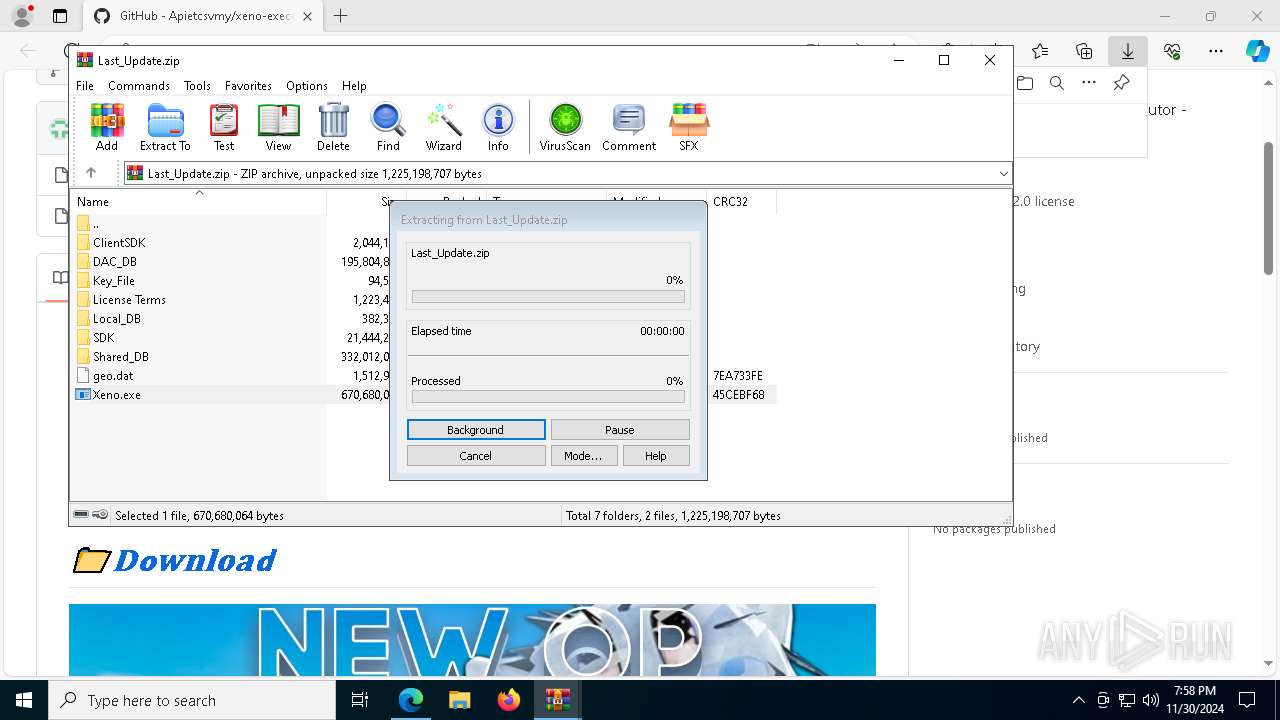
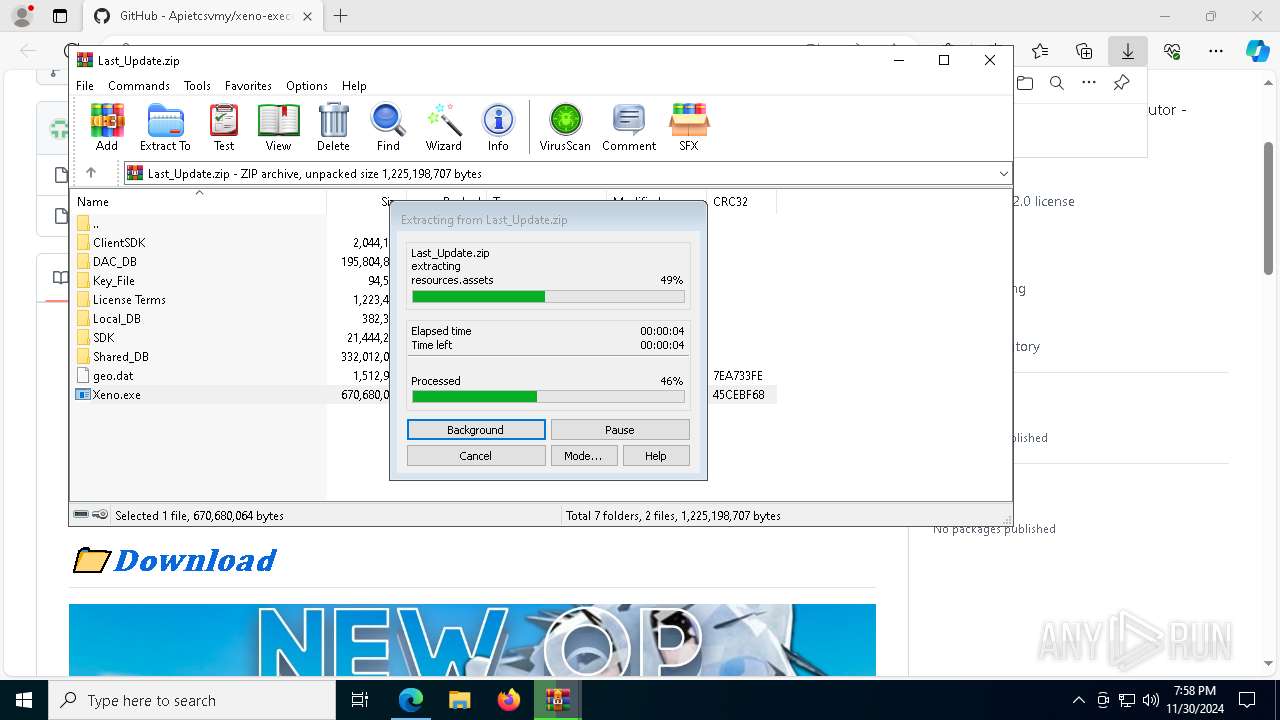
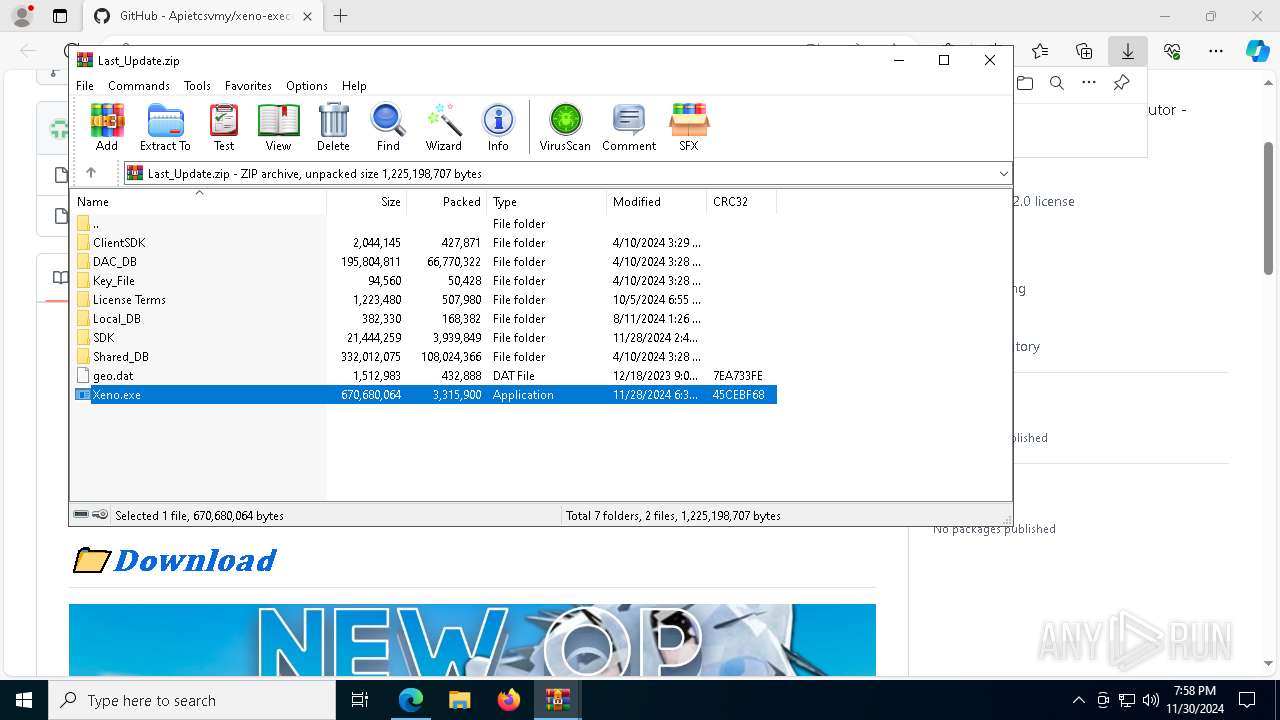
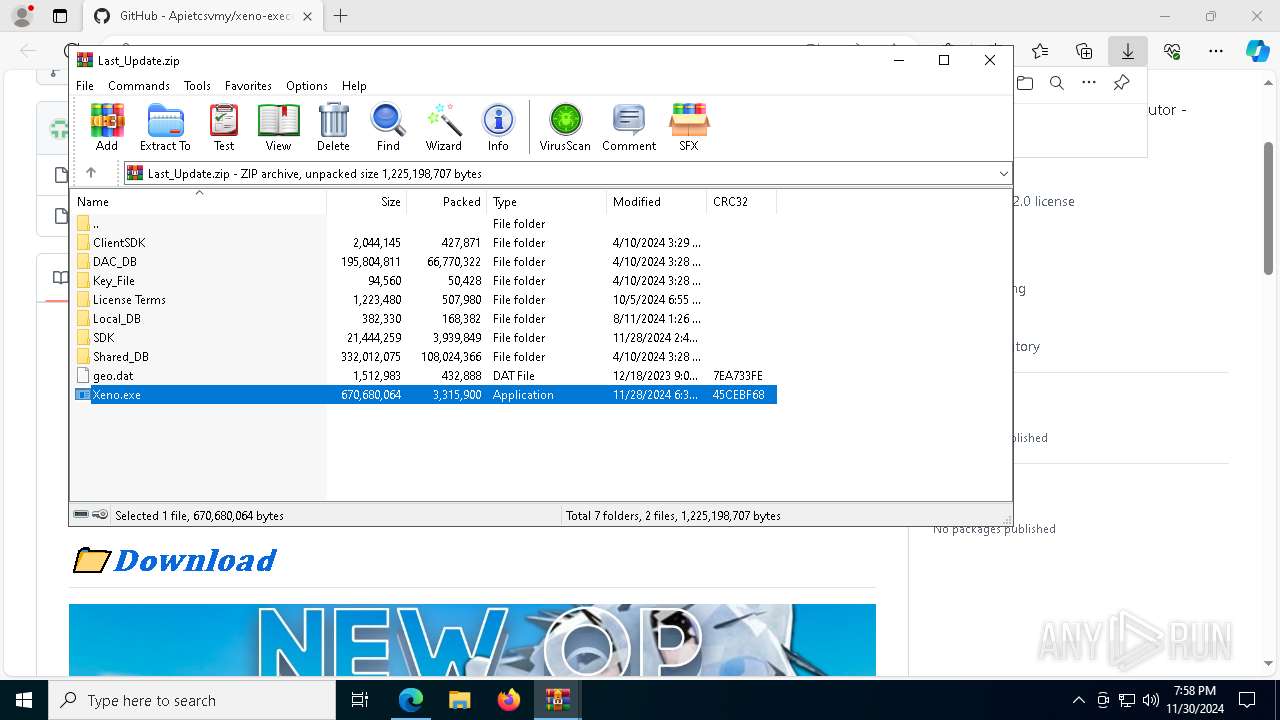
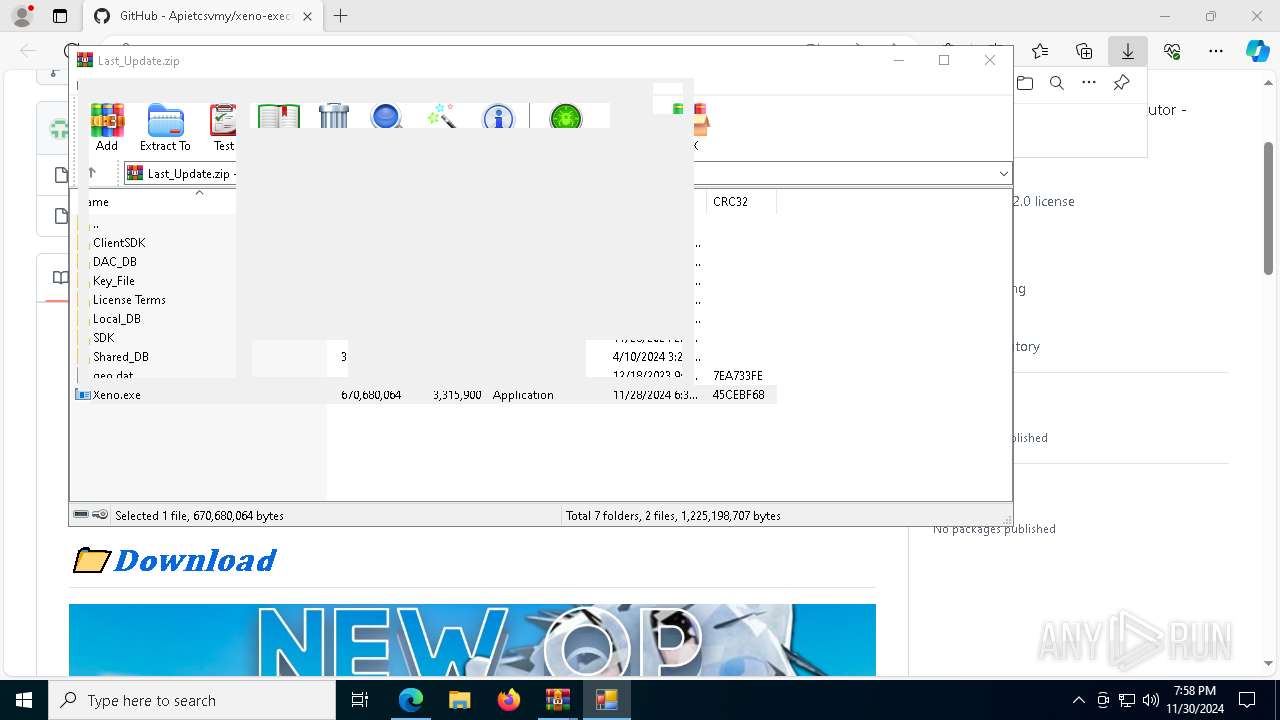
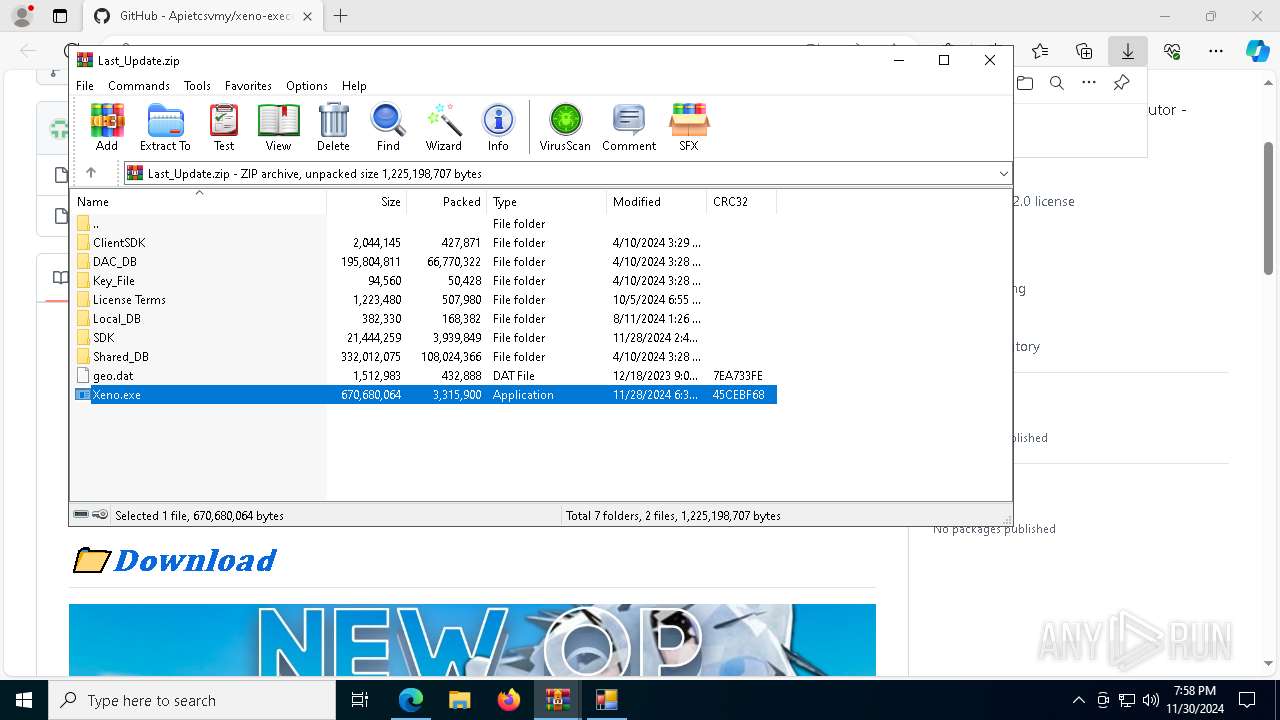
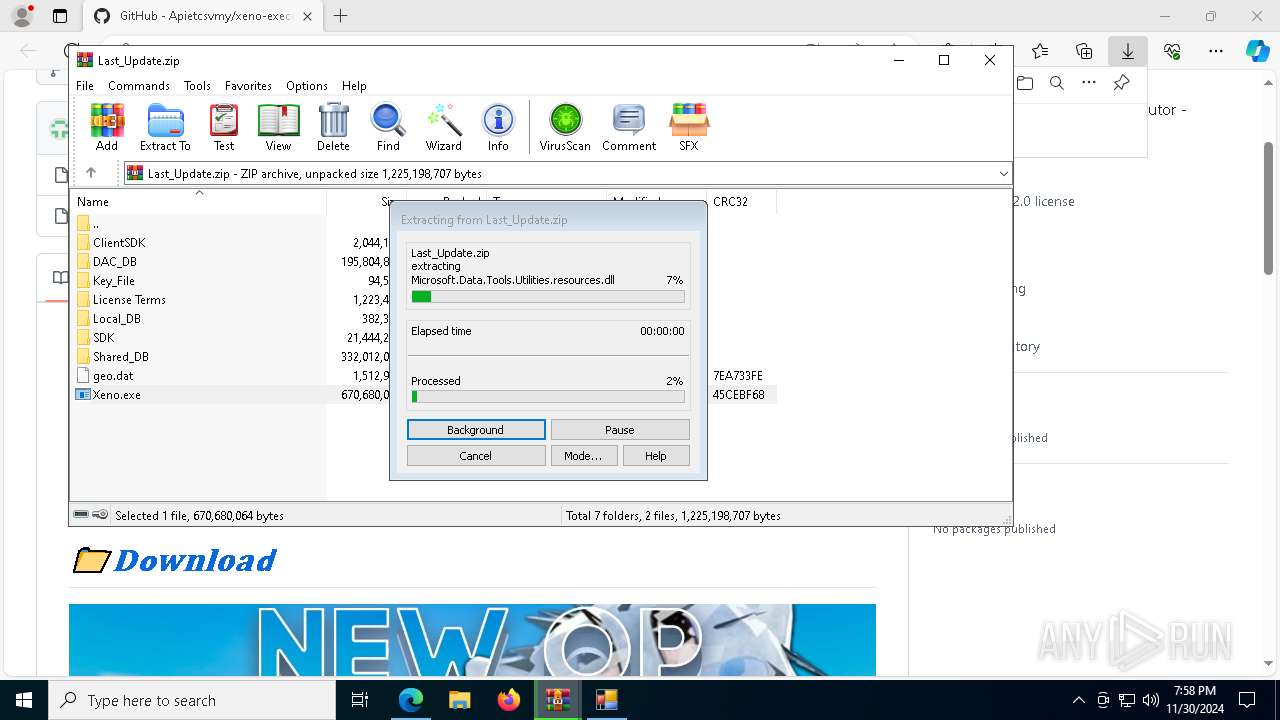
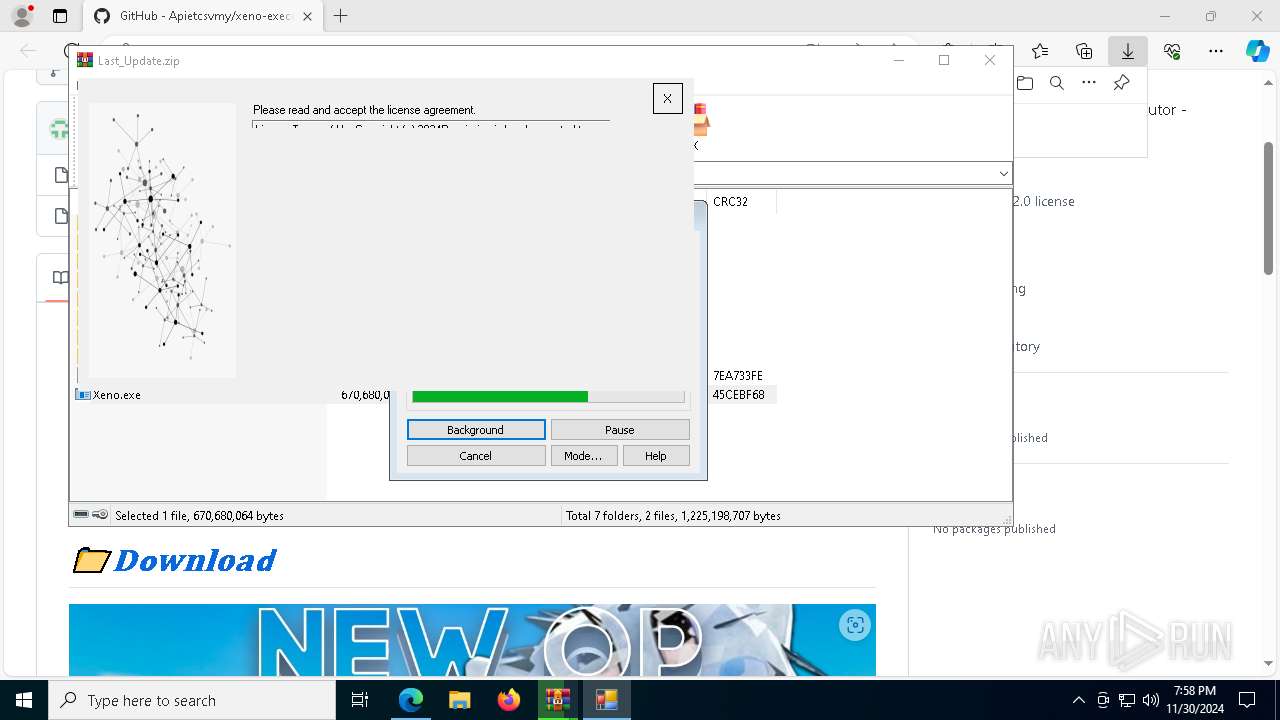
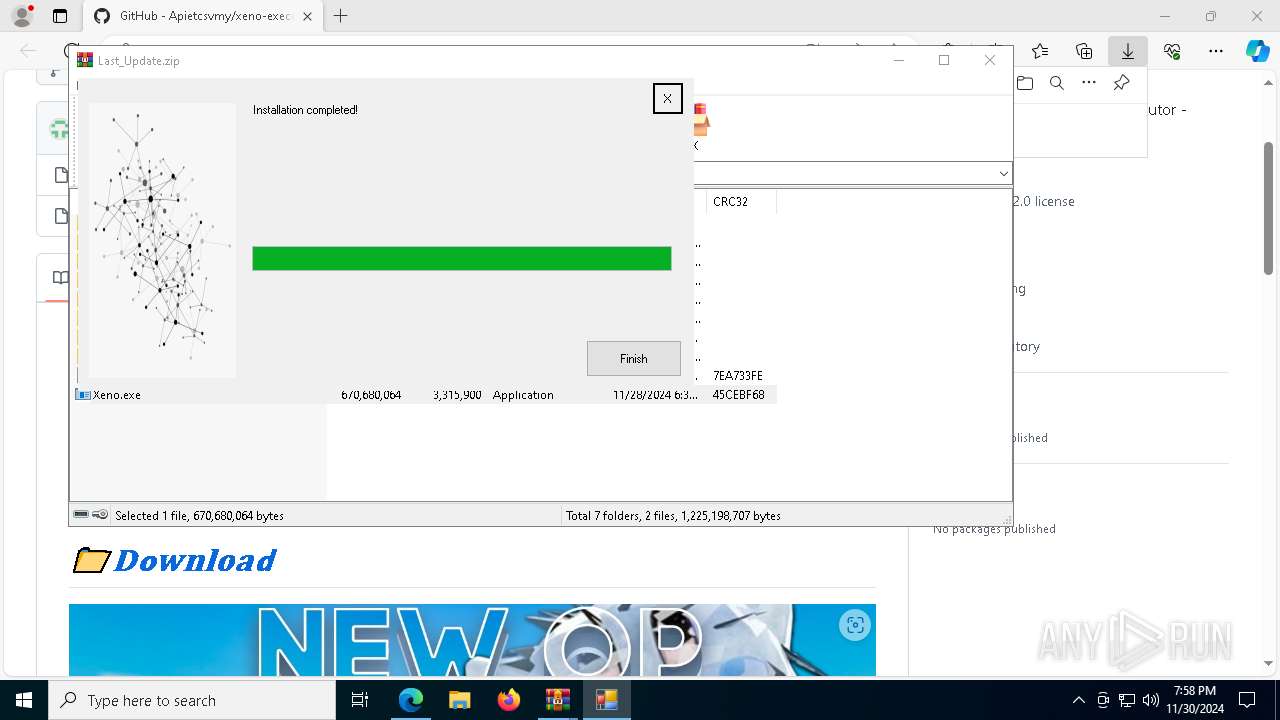
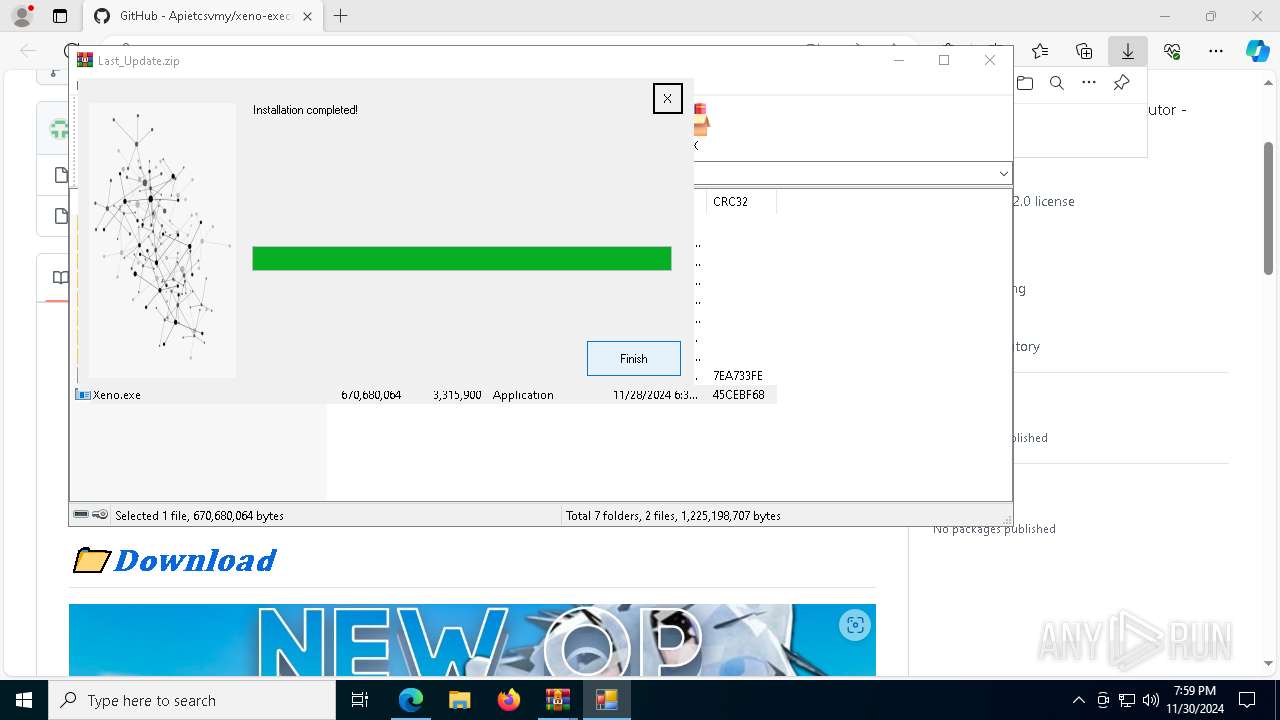
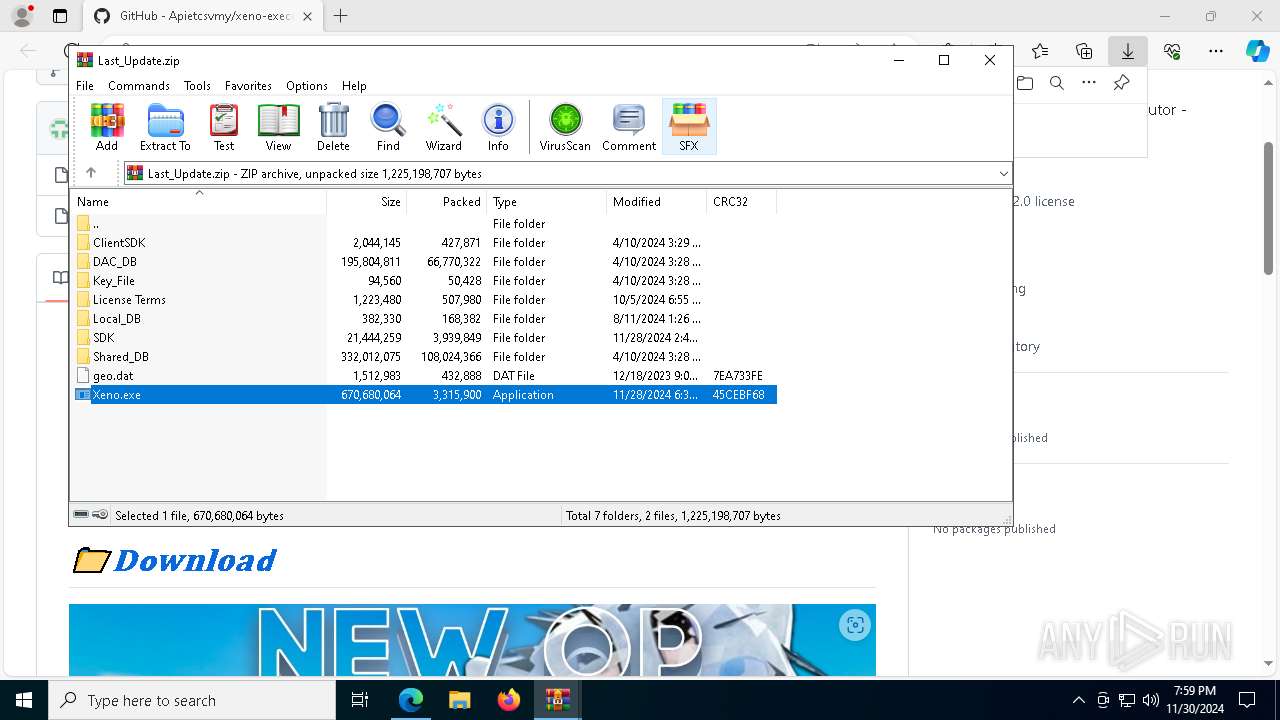
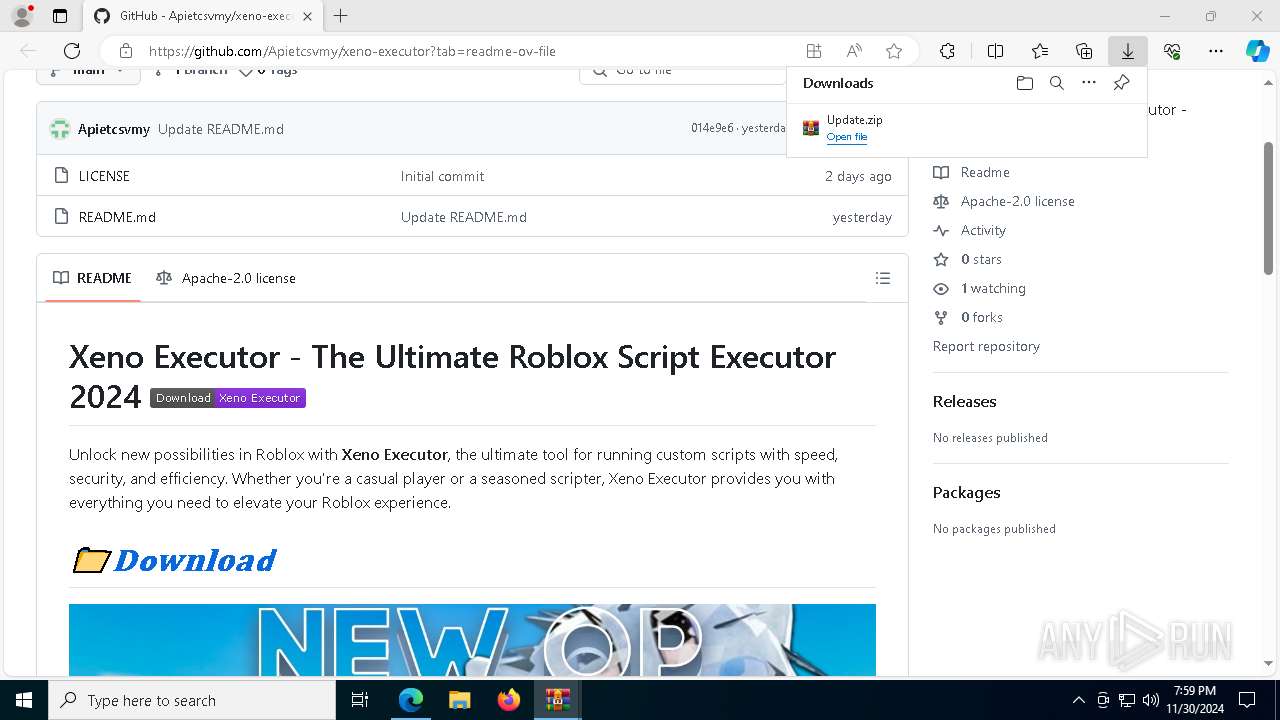
Application launched itself
- WinRAR.exe (PID: 5684)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7652)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5684)
- WinRAR.exe (PID: 7652)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
- Xeno.exe (PID: 2224)
Executable content was dropped or overwritten
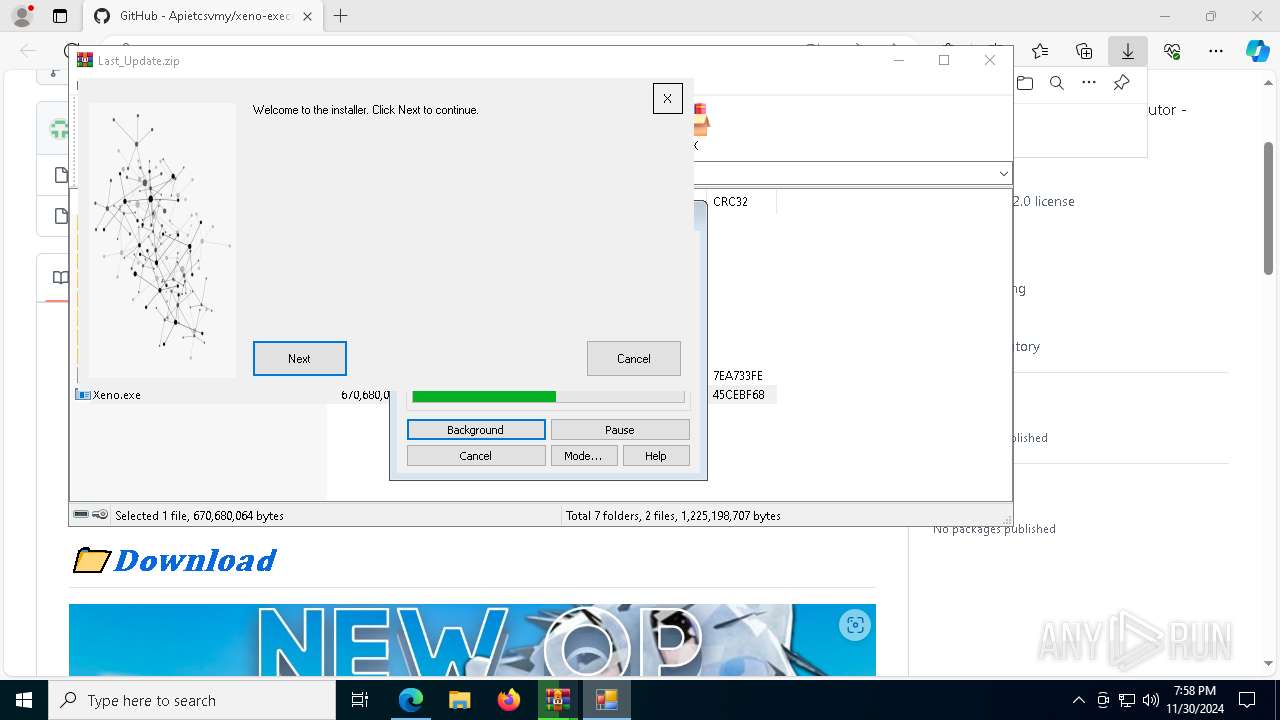
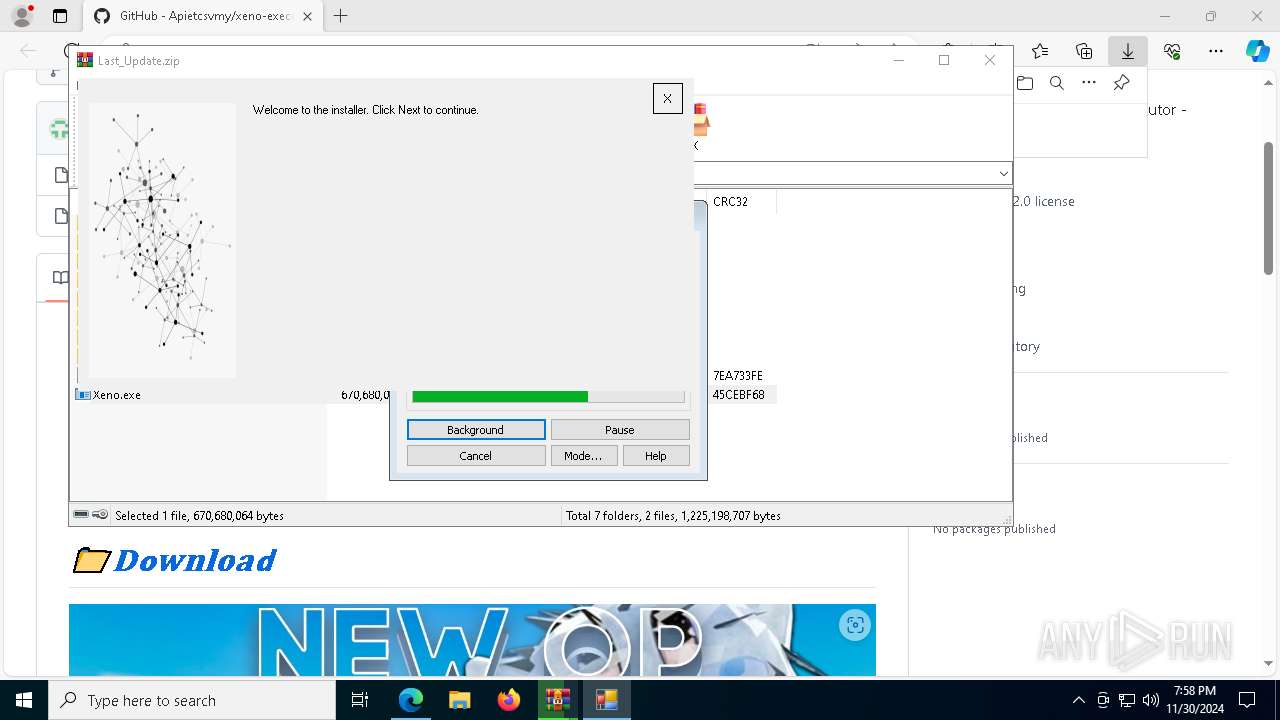
- Xeno.exe (PID: 2224)
Checks Windows Trust Settings
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Checks for external IP
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Connects to unusual port
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Searches for installed software
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Reads the date of Windows installation
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
The process connected to a server suspected of theft
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Starts CMD.EXE for commands execution
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Hides command output
- cmd.exe (PID: 7868)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7868)
INFO
Application launched itself
- msedge.exe (PID: 6364)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6364)
Reads Environment values
- identity_helper.exe (PID: 7548)
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
The process uses the downloaded file
- msedge.exe (PID: 6364)
- msedge.exe (PID: 3364)
- WinRAR.exe (PID: 5684)
- Xeno.exe (PID: 2224)
- WinRAR.exe (PID: 7652)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Reads the machine GUID from the registry
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
- Xeno.exe (PID: 440)
Disables trace logs
- Xeno.exe (PID: 2224)
Reads the computer name
- Xeno.exe (PID: 2224)
- identity_helper.exe (PID: 7548)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
- Xeno.exe (PID: 440)
Checks proxy server information
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7652)
- msedge.exe (PID: 8104)
Checks supported languages
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
- identity_helper.exe (PID: 7548)
- Xeno.exe (PID: 440)
Reads the software policy settings
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Process checks computer location settings
- Xeno.exe (PID: 2224)
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Create files in a temporary directory
- Xeno.exe (PID: 2224)
Reads product name
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Creates files or folders in the user directory
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Reads the time zone
- 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe (PID: 4764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
57
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7652.2382\Xeno.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7652.2382\Xeno.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PixelPlay Version: 3.3.1.0 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5980 --field-trial-handle=2324,i,13594271177879225184,17260300421799166439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6760 --field-trial-handle=2324,i,13594271177879225184,17260300421799166439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7652.49366\Xeno.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7652.49366\Xeno.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PixelPlay Exit code: 3221226540 Version: 3.3.1.0 Modules
| |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1540 --field-trial-handle=2324,i,13594271177879225184,17260300421799166439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1540 | ping 1.1.1.1 -n 1 -w 3000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5032 --field-trial-handle=2324,i,13594271177879225184,17260300421799166439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4476 --field-trial-handle=2324,i,13594271177879225184,17260300421799166439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7652.49366\Xeno.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7652.49366\Xeno.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PixelPlay Exit code: 0 Version: 3.3.1.0 Modules
| |||||||||||||||
| 2632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4056 --field-trial-handle=2324,i,13594271177879225184,17260300421799166439,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
9 748
Read events
9 701
Write events
47
Delete events
0
Modification events
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82768D60-4239-4D03-876D-61ED81312DBE} | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5F9E2C00BD862F00 | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (6364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {383085B5-003E-4E8B-A0F4-69908B0974FA} | |||
Executable files
296
Suspicious files
508
Text files
169
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13545d.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13545d.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13545d.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13546c.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13546c.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
98
DNS requests
105
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2632 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4764 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7128 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4764 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7964 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1733063839&P2=404&P3=2&P4=bUq01MUYxkPD7AHVTqOWo3SxTTIqeFHH3%2fq9z8%2fzAt1RP%2bwIwe5v%2fRuh%2bcM%2fDUrMoVhcoldfSjwX%2bWjW10iErQ%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1733063839&P2=404&P3=2&P4=bUq01MUYxkPD7AHVTqOWo3SxTTIqeFHH3%2fq9z8%2fzAt1RP%2bwIwe5v%2fRuh%2bcM%2fDUrMoVhcoldfSjwX%2bWjW10iErQ%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1733060240&P2=404&P3=2&P4=M1%2b7p%2f3%2bv25S6fVxWxVu4zANIha6qAbRSgiRrSE4T6Lz7fNkTr3POdcHUQN01OBLNqMN0pjvilhFv3nnINYLAw%3d%3d | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1733060240&P2=404&P3=2&P4=M1%2b7p%2f3%2bv25S6fVxWxVu4zANIha6qAbRSgiRrSE4T6Lz7fNkTr3POdcHUQN01OBLNqMN0pjvilhFv3nnINYLAw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2632 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2632 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| shared |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Meduza Stealer |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Meduza Stealer Exfiltration M1 |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Meduza Stealer Exfiltration M1 |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Meduza Stealer |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
4764 | 099fbb00-cd7a-4835-82f9-b199f71b55d5.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |