| File name: | 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe |
| Full analysis: | https://app.any.run/tasks/fe0eb04b-f1a4-43a9-bc56-2cfba34e28a9 |
| Verdict: | Malicious activity |
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | May 11, 2024, 11:37:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 585D78B9FFC988D345E7A2A0EE119111 |
| SHA1: | 65B5C6A6C72A845D5610D82CA2AA9A301A907E43 |
| SHA256: | 82AE530EB29E0C64986DBD019F86CAC5EFF3DAF3C1FB861757A60252EB1E4661 |
| SSDEEP: | 196608:ubGf4Jsi1RkqfMgfezrtqKWZHYa5KnoUHihyM9mo03lq3xdxJv3X0NLMKO:949/fUrt8HYCKo9y1omM3zxp0NLMKO |
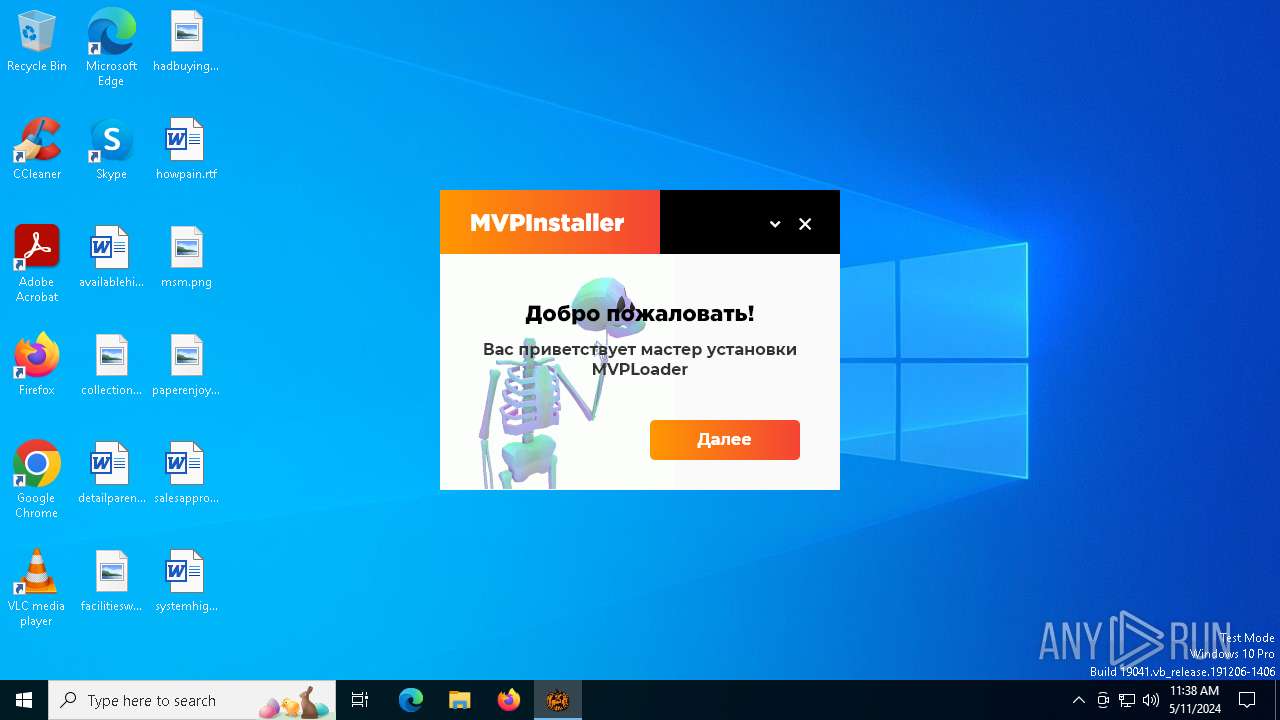
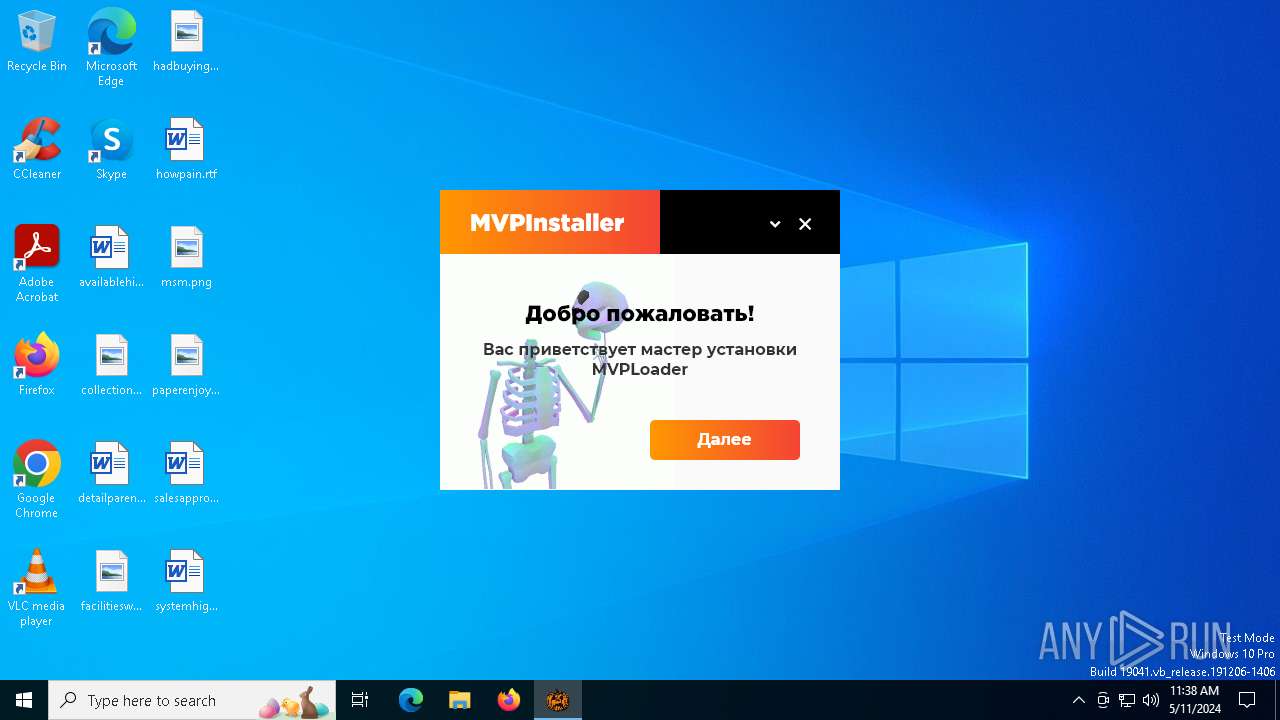
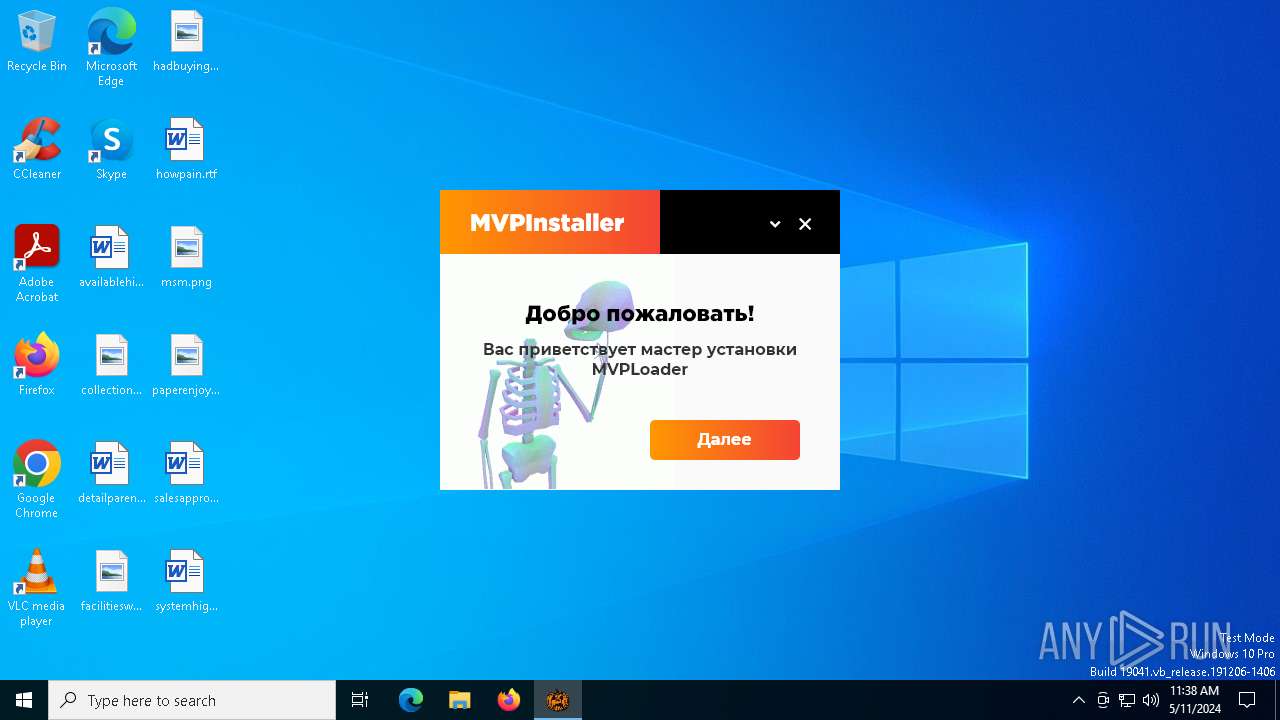
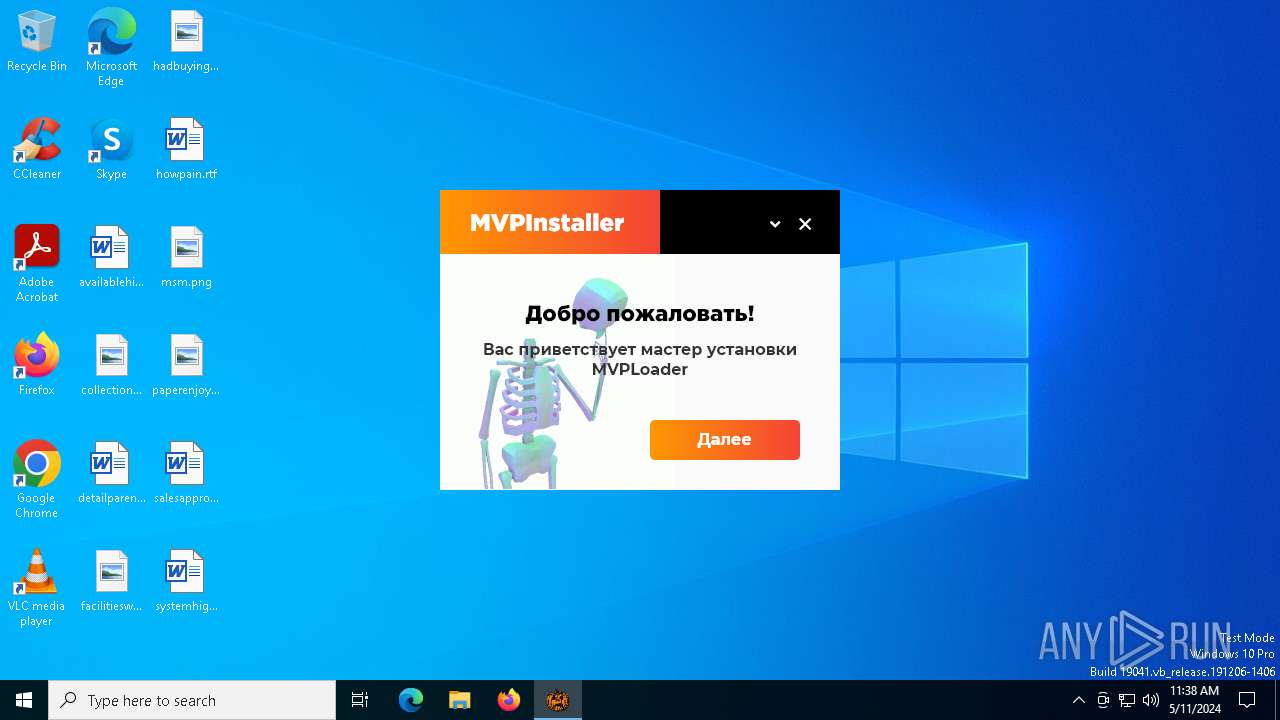
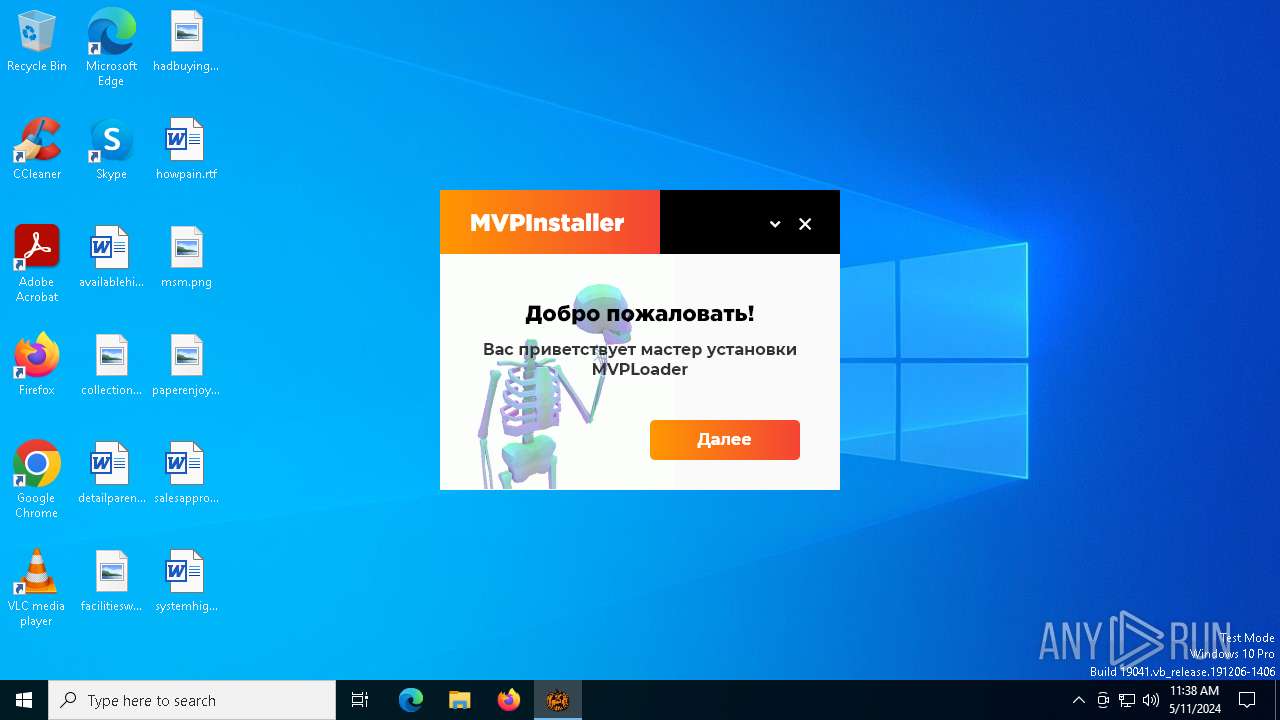
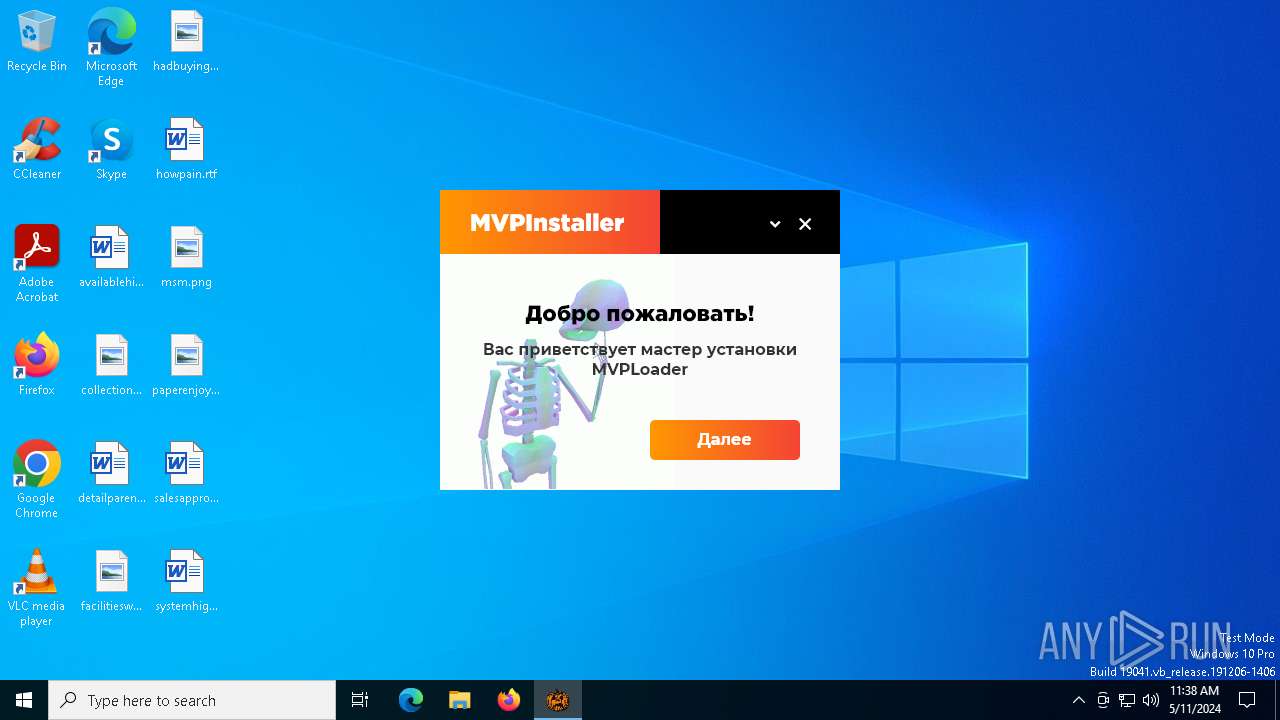
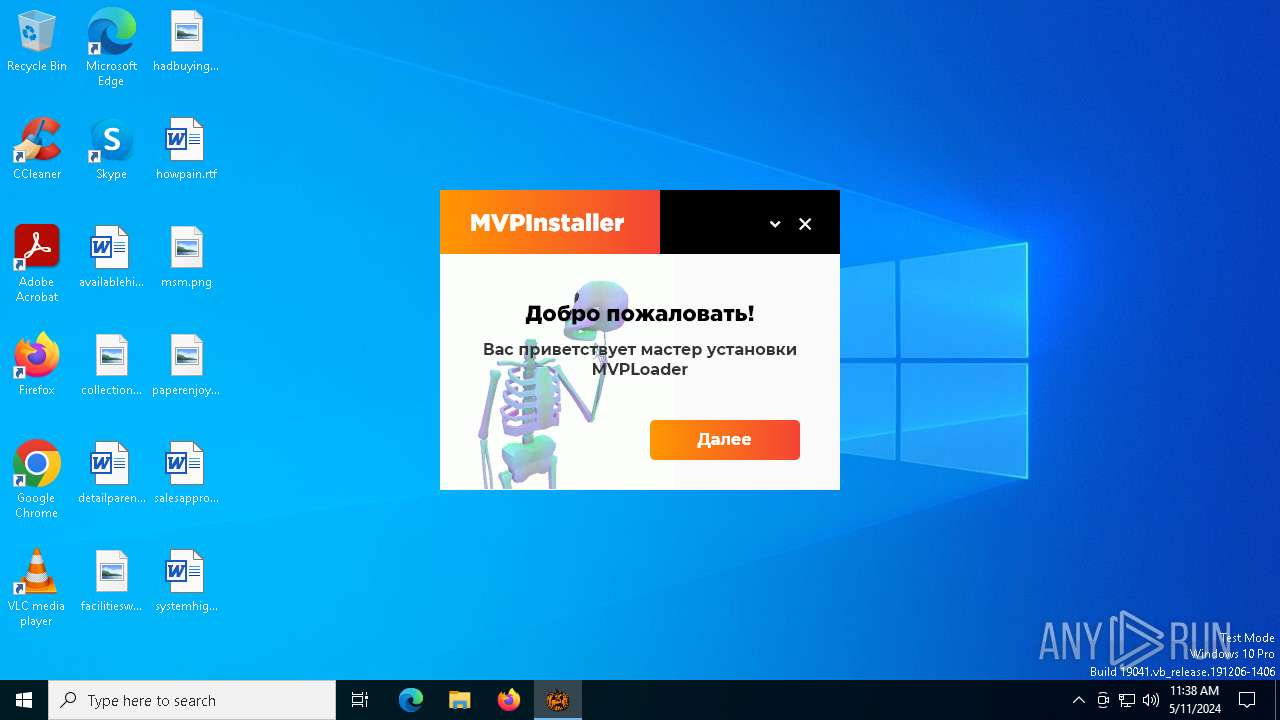
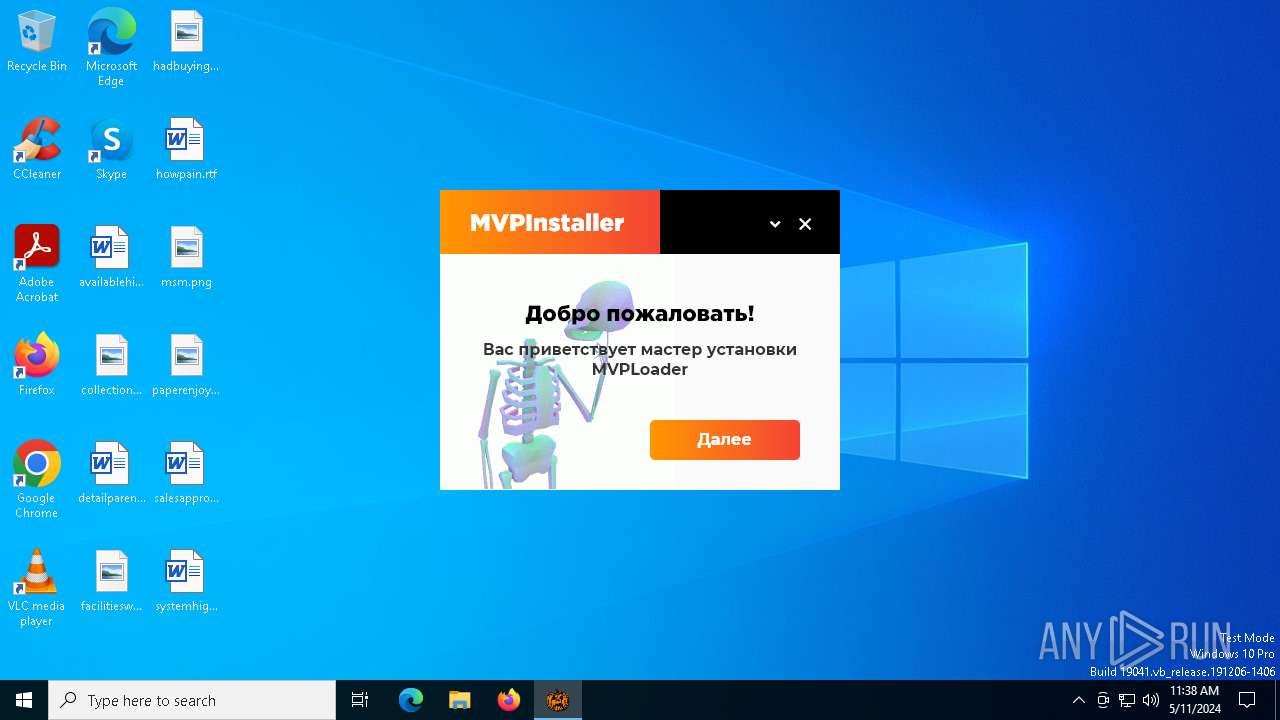
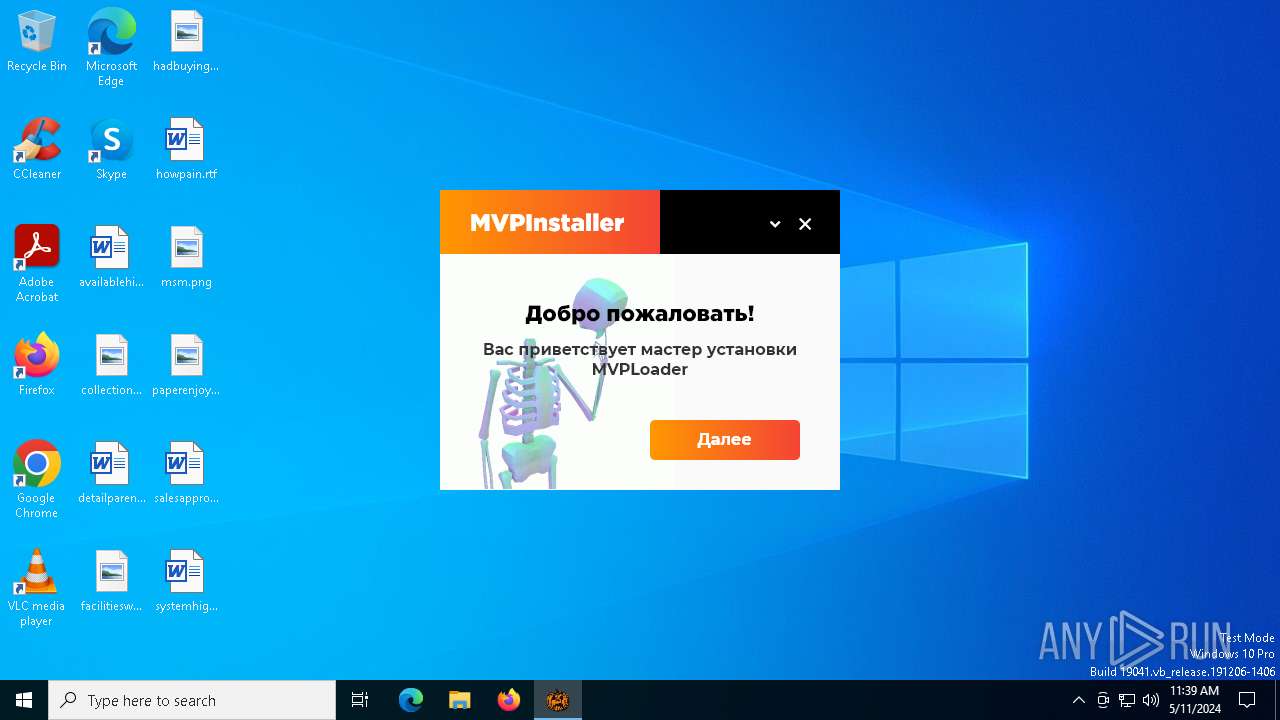
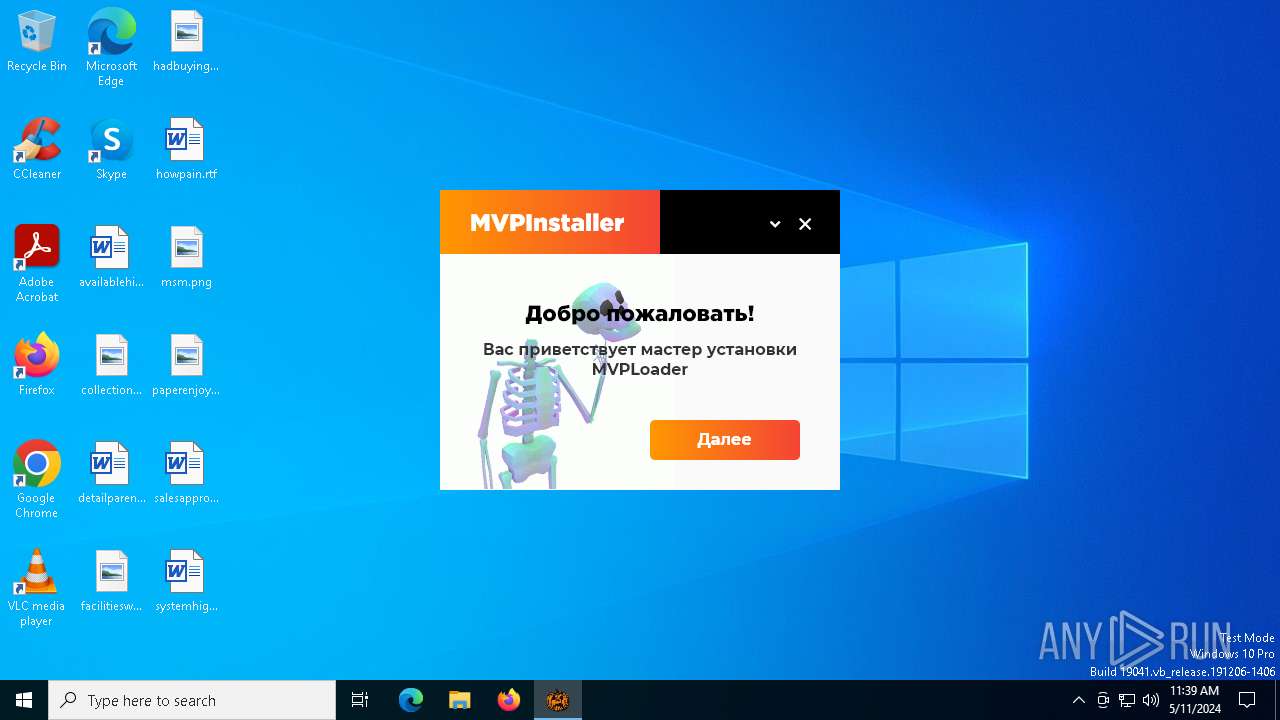
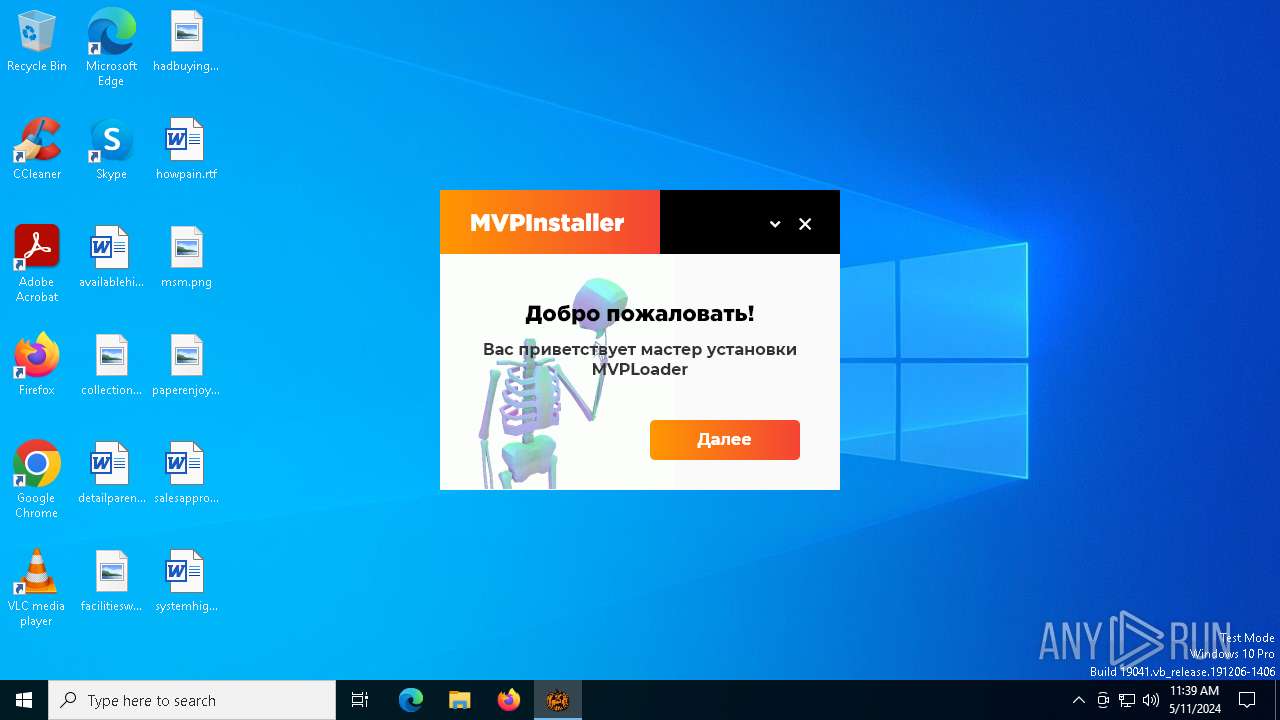
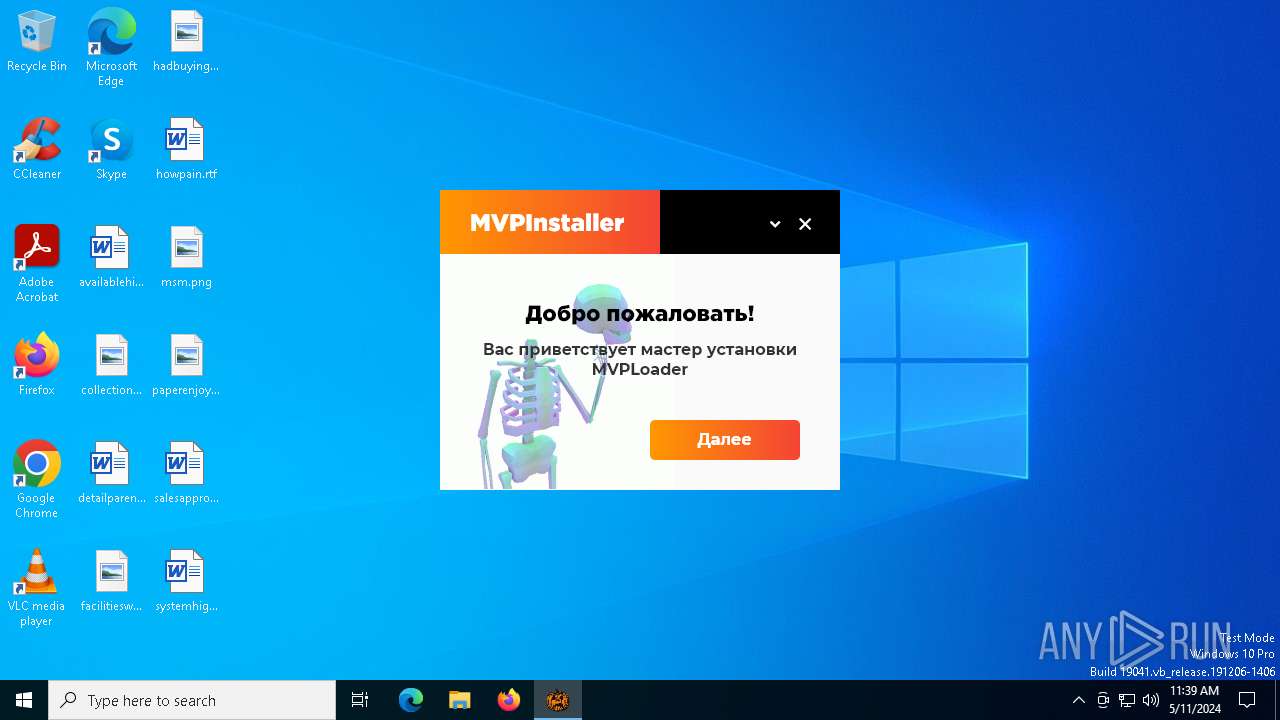
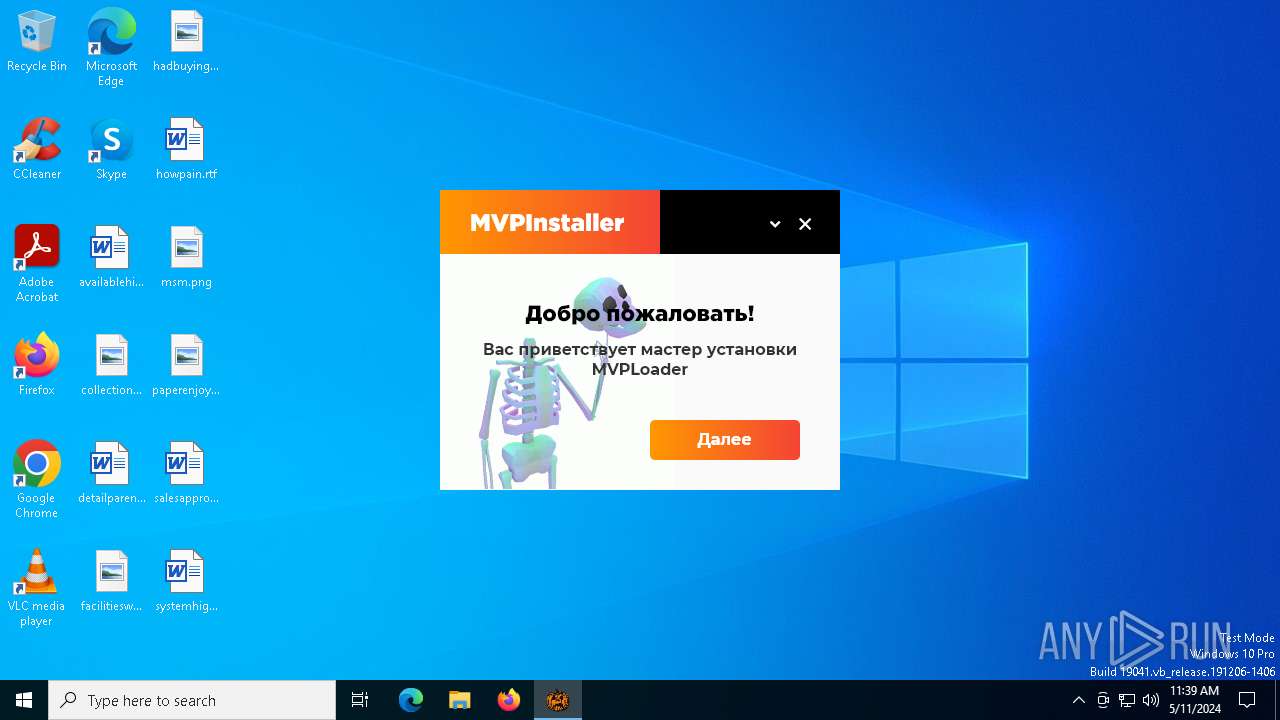
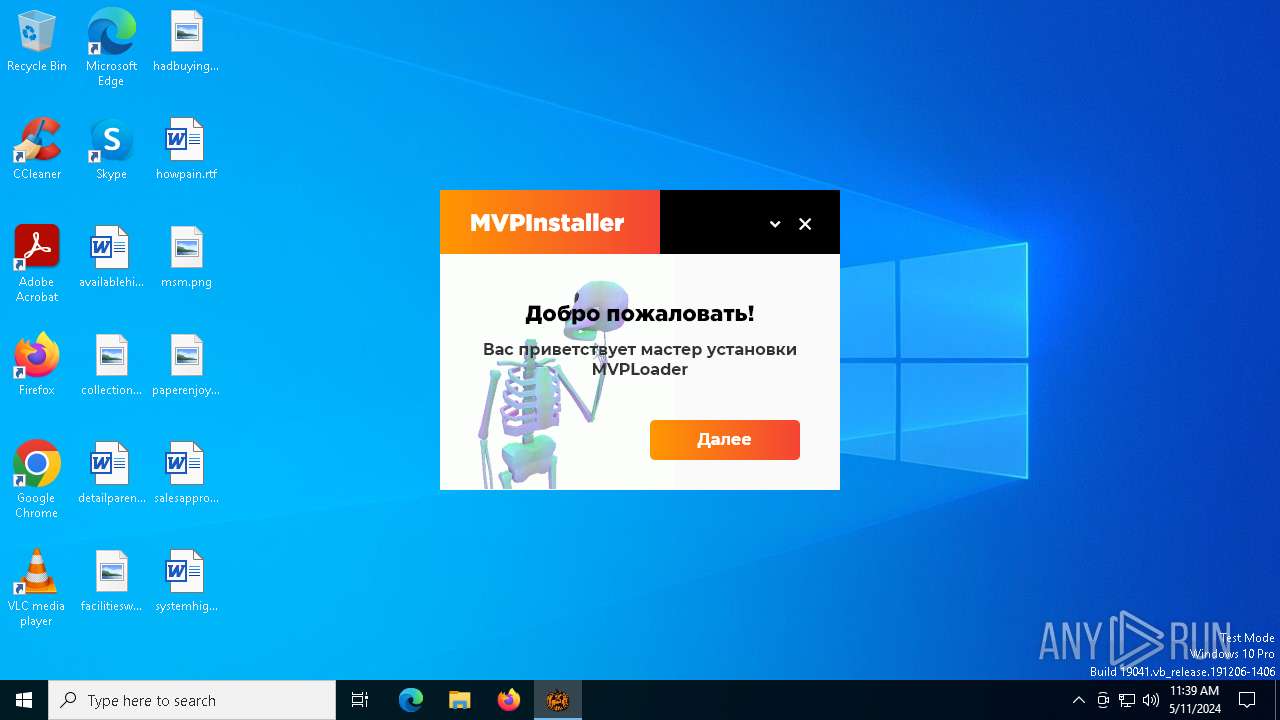
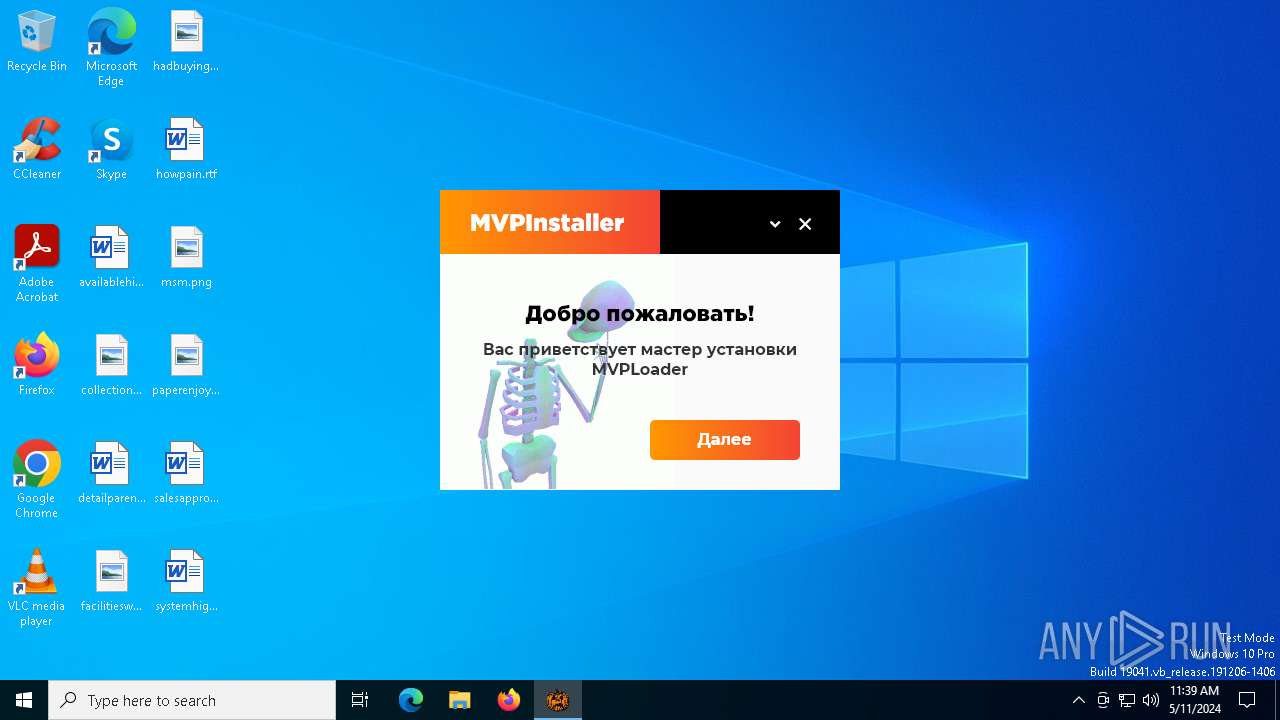
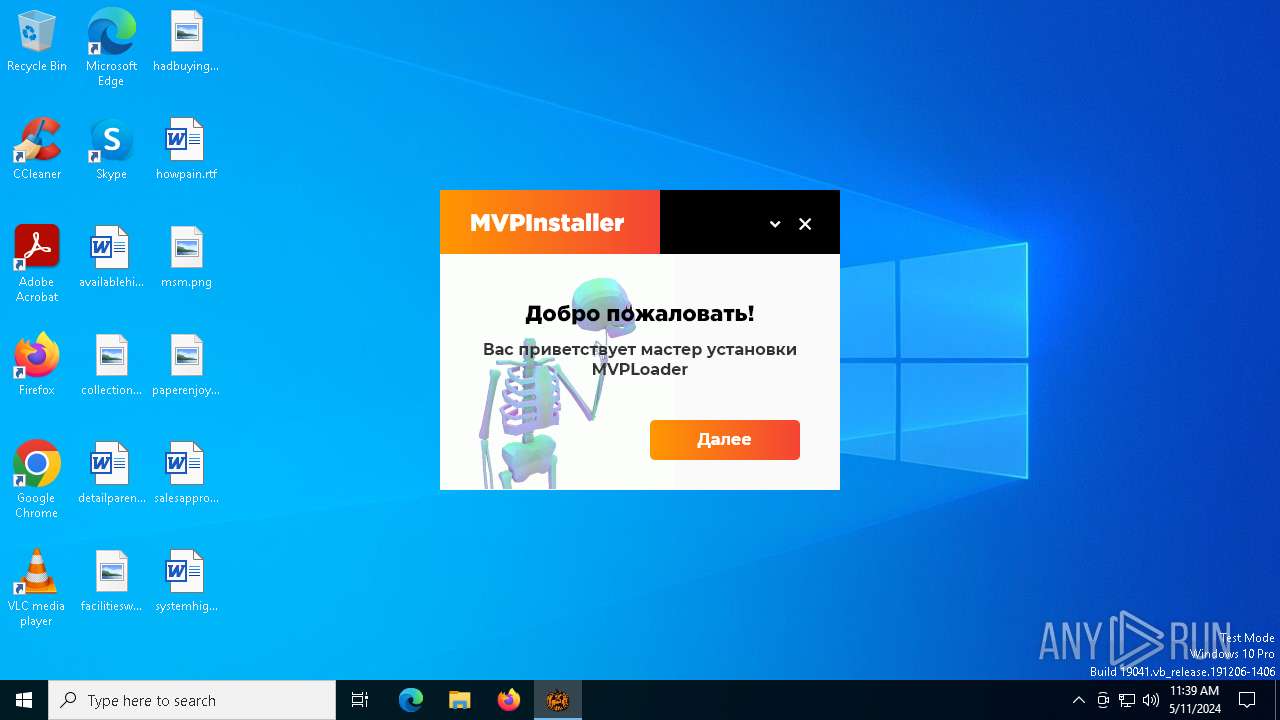
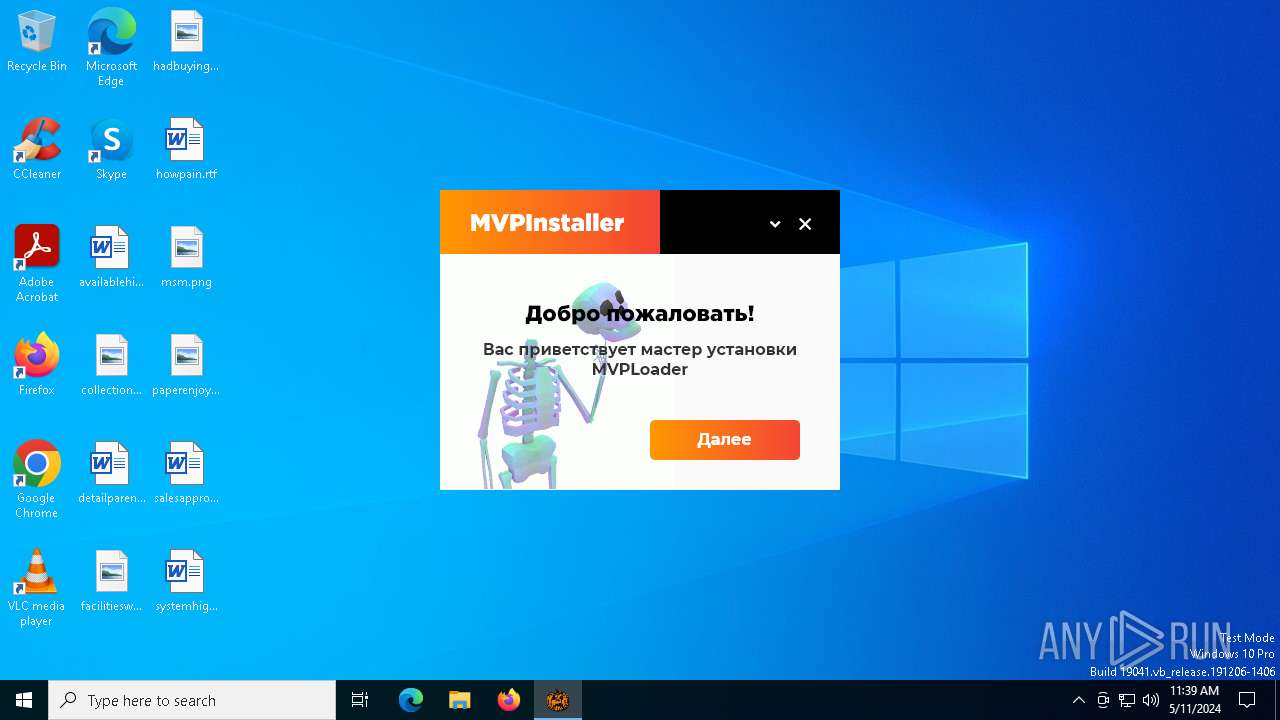
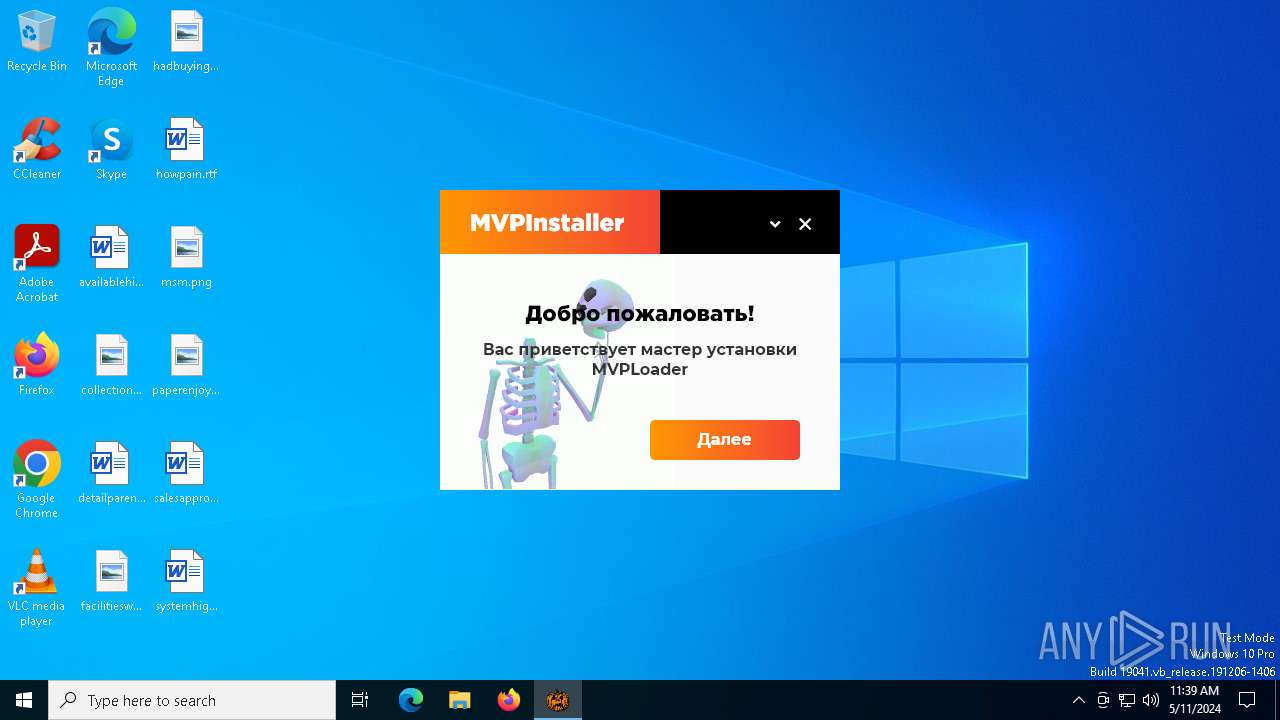
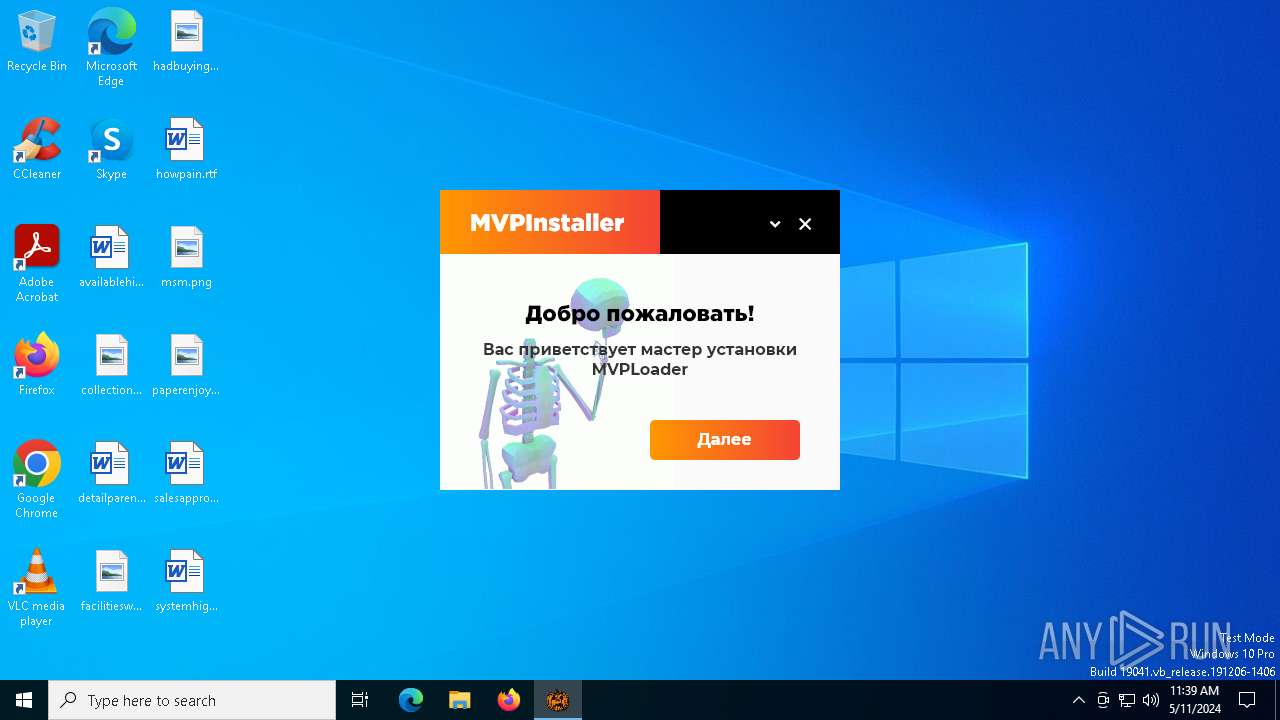
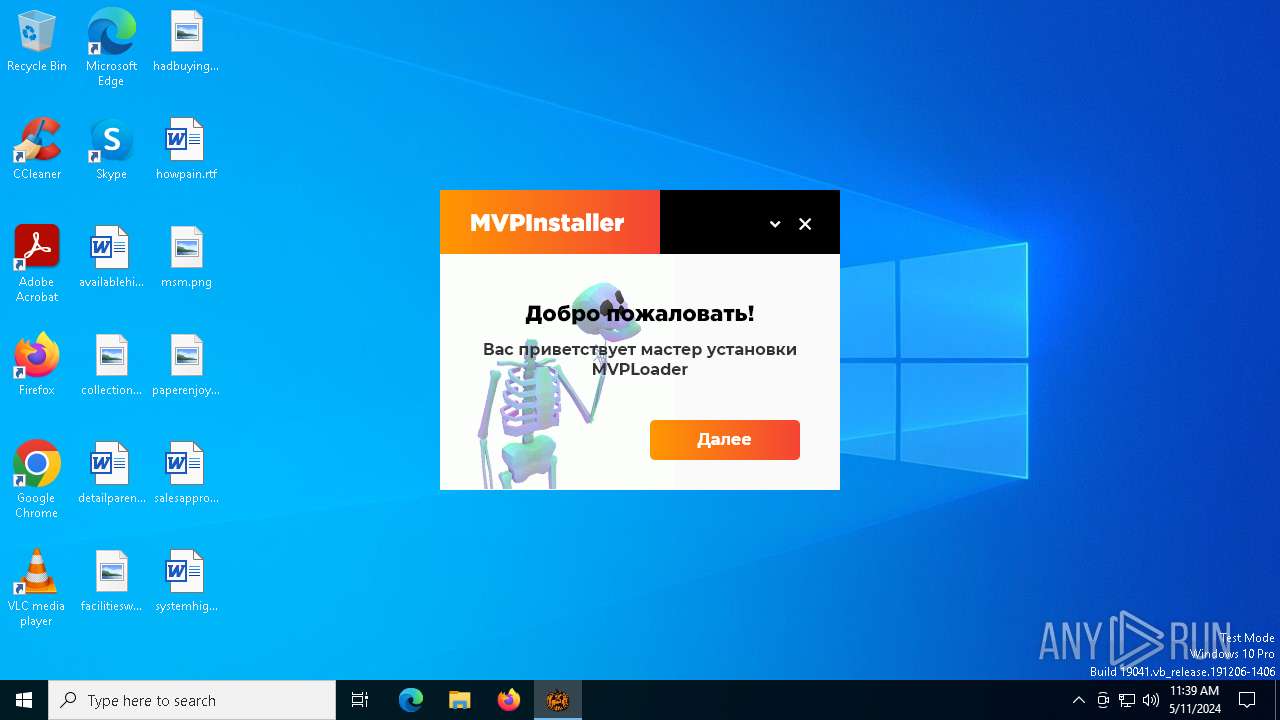
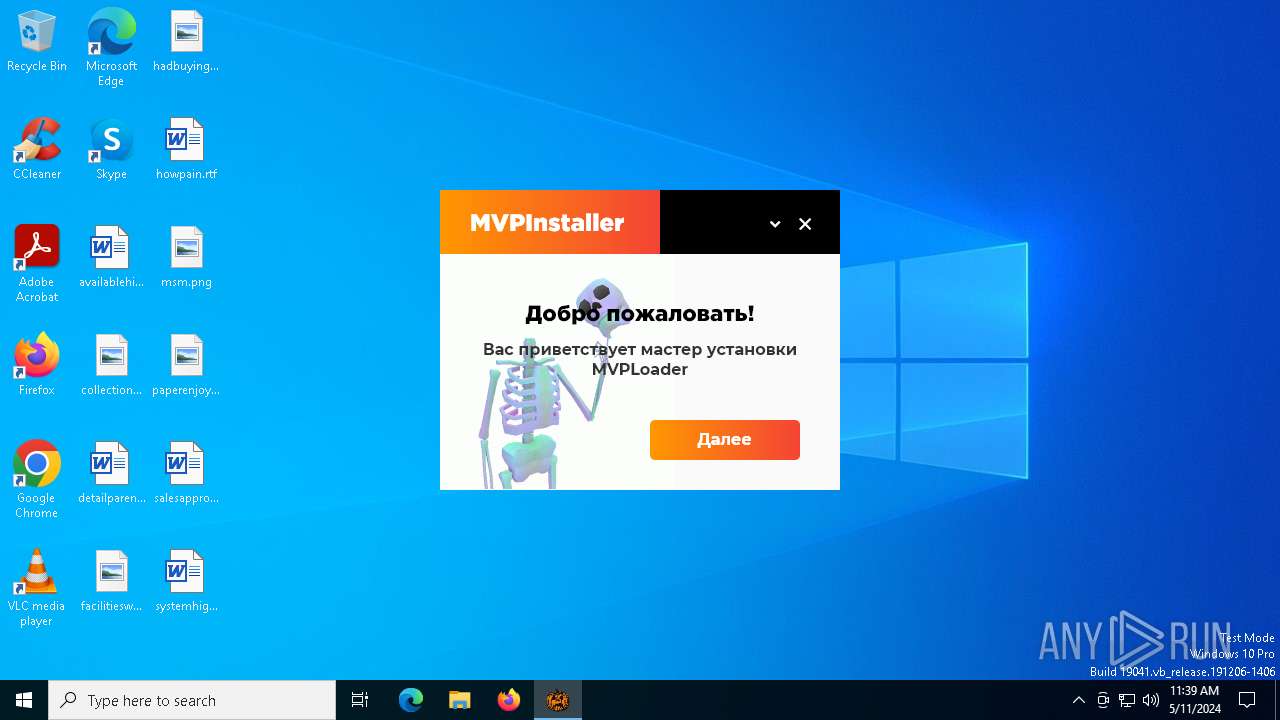
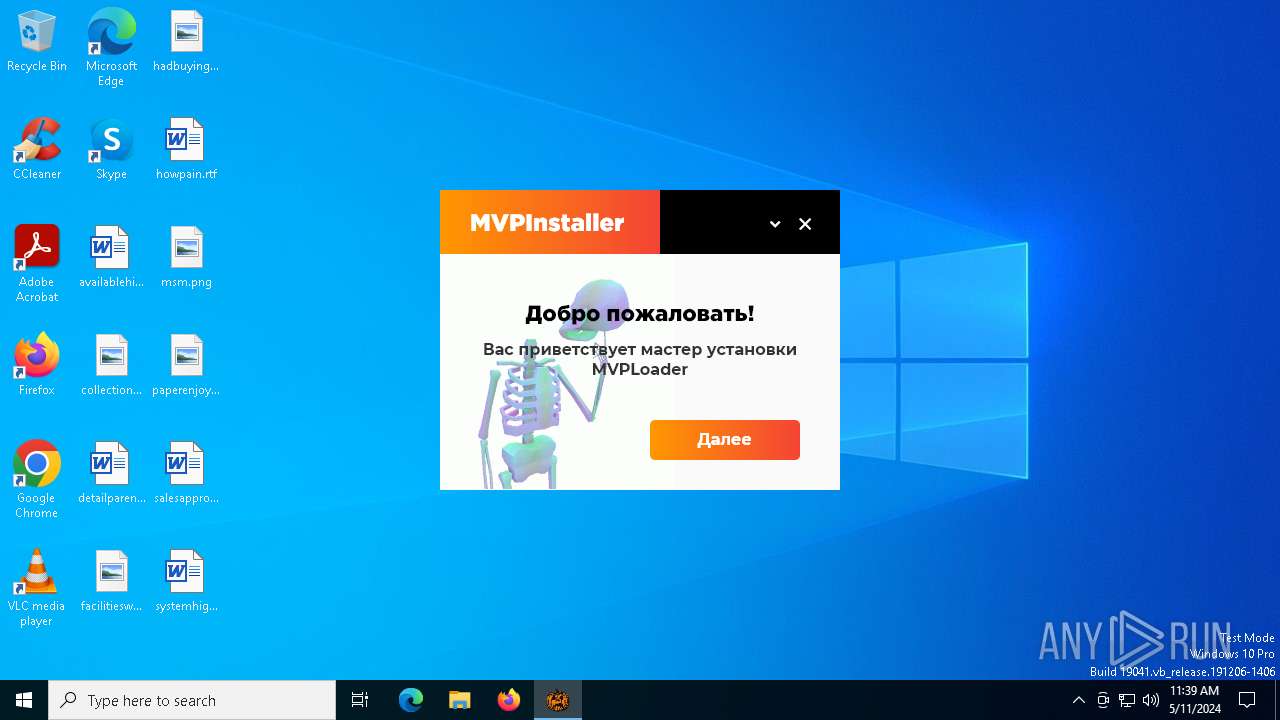
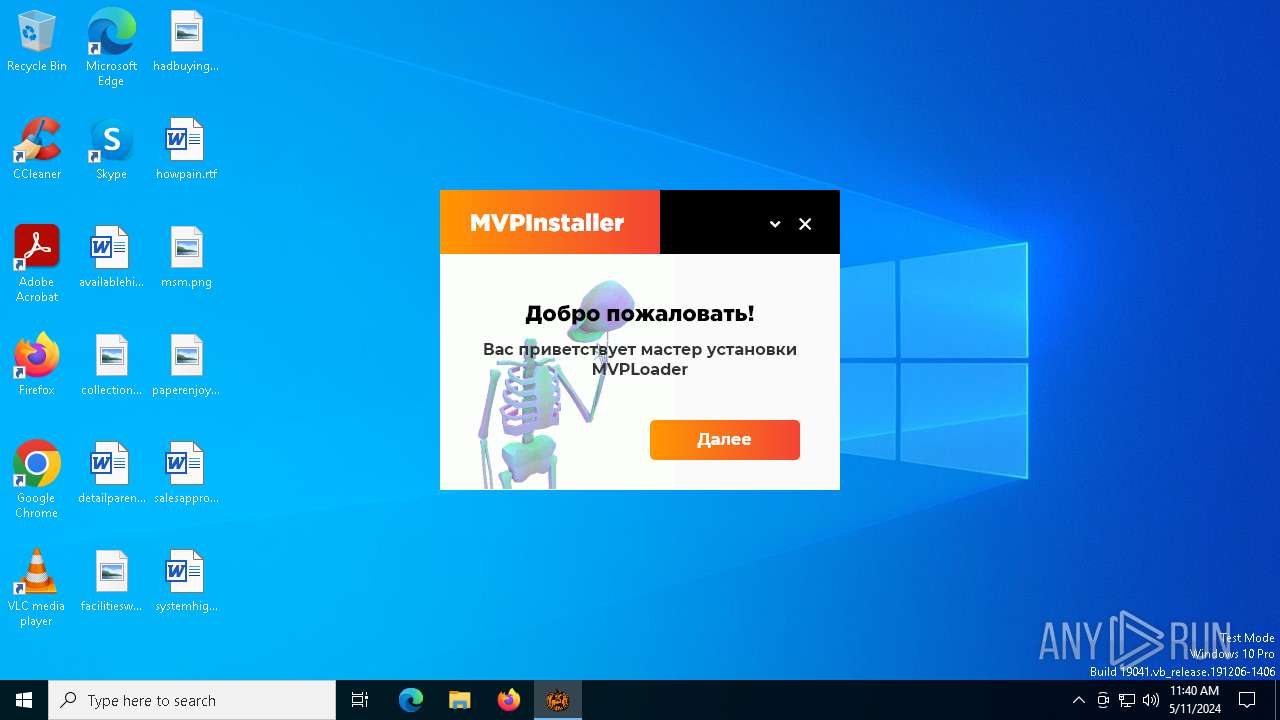
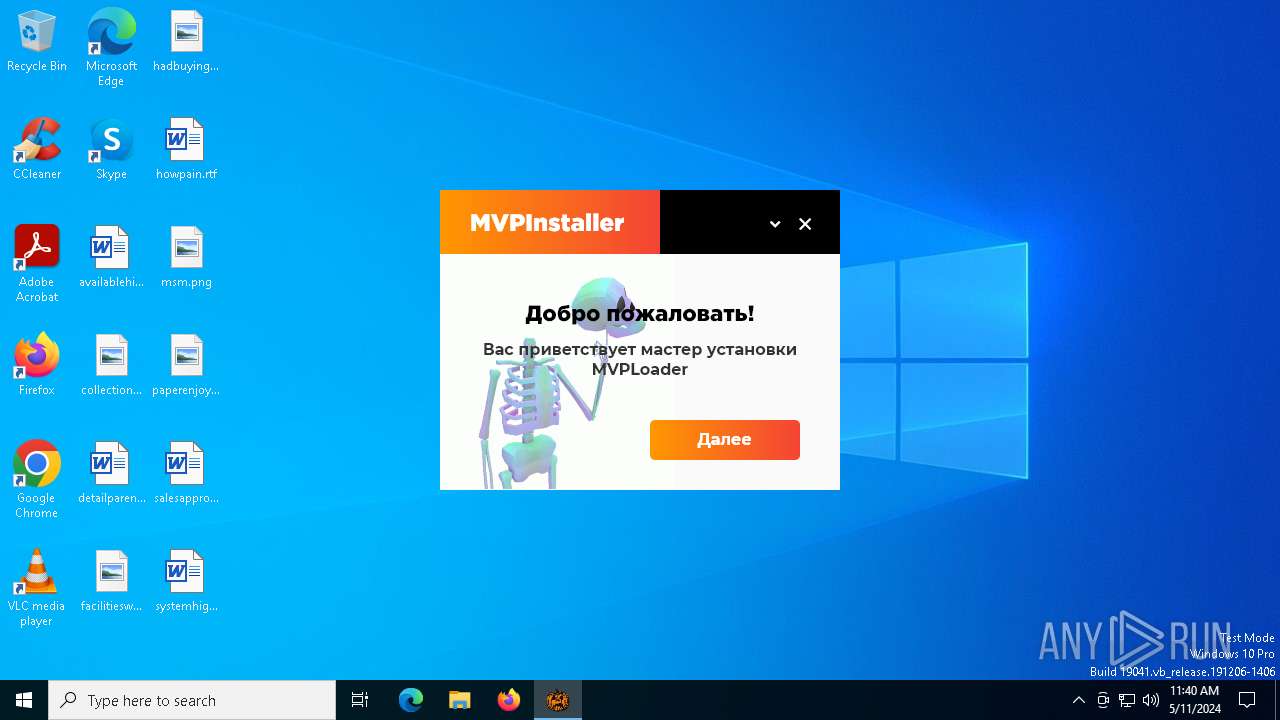
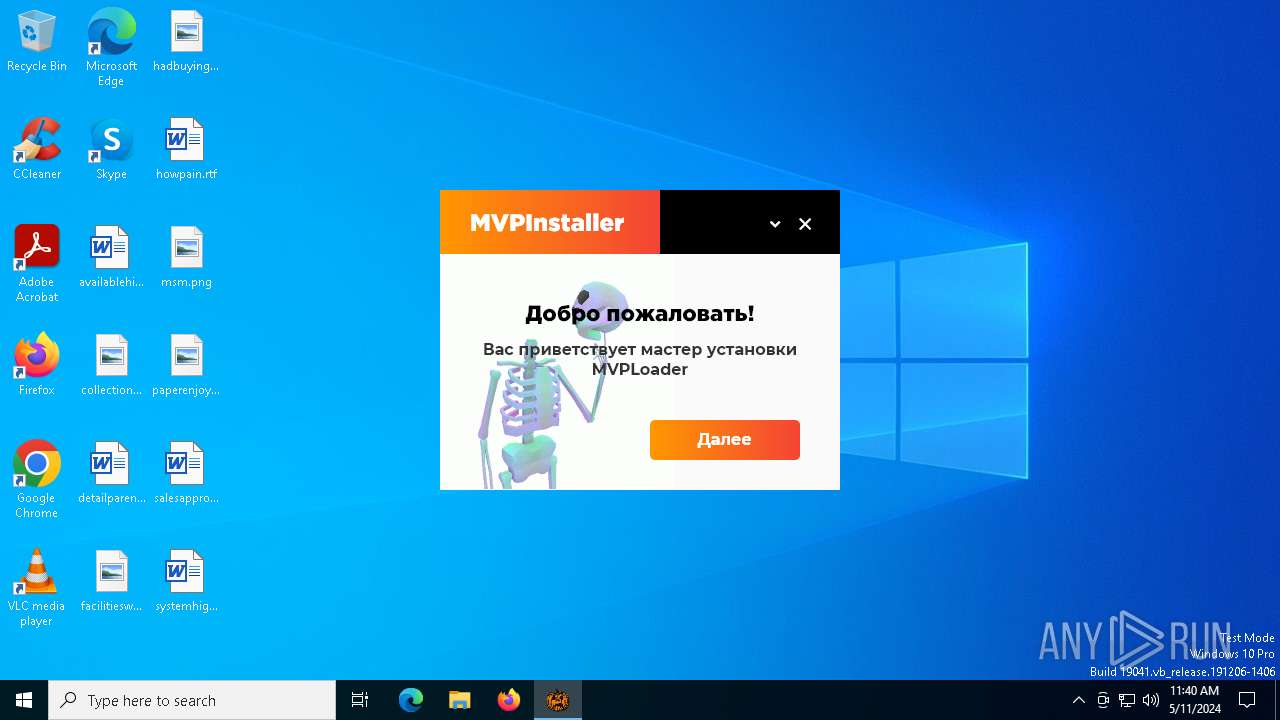
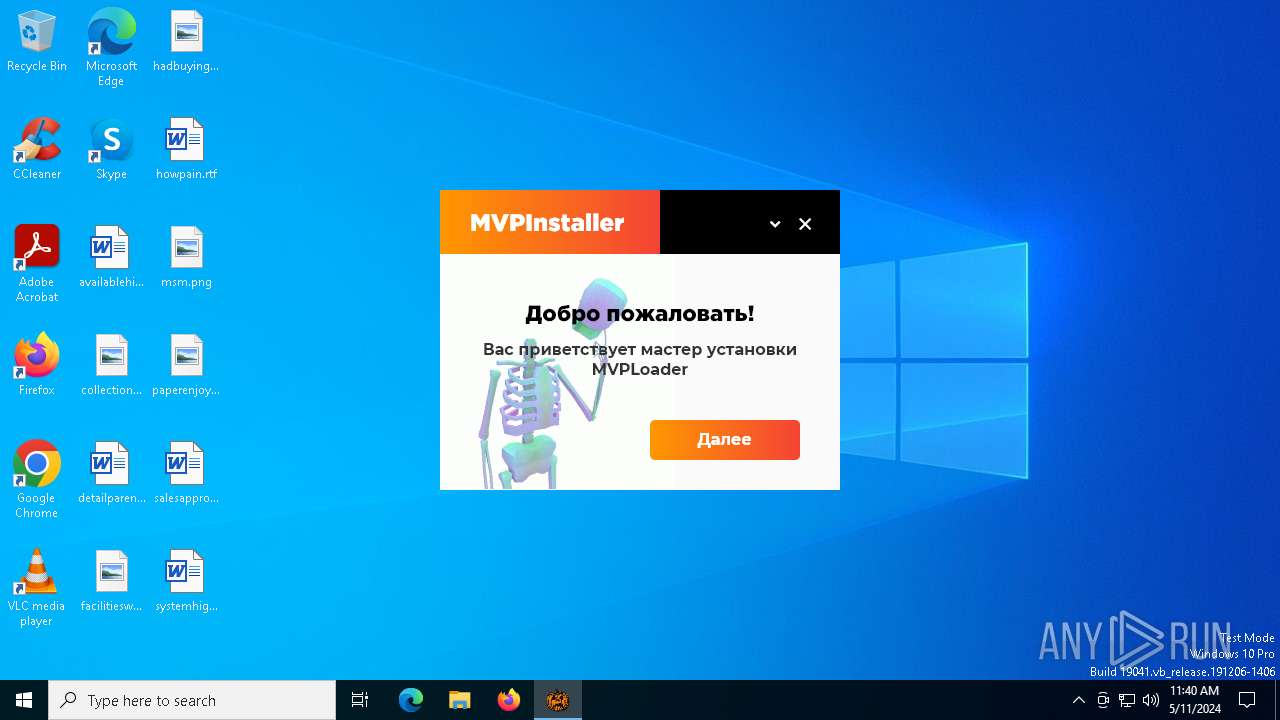
MALICIOUS
Drops the executable file immediately after the start
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- MVPInstaller.exe (PID: 6440)
- DCRatBuild.exe (PID: 6380)
- MVPInstaller.exe (PID: 6564)
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6540)
Adds extension to the Windows Defender exclusion list
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Steals credentials from Web Browsers
- 323.exe (PID: 6388)
Modifies hosts file to block updates
- build.exe (PID: 6356)
Application was injected by another process
- lsass.exe (PID: 748)
- winlogon.exe (PID: 668)
- dwm.exe (PID: 504)
- svchost.exe (PID: 488)
- svchost.exe (PID: 1420)
- svchost.exe (PID: 1156)
- svchost.exe (PID: 1064)
- svchost.exe (PID: 1292)
- svchost.exe (PID: 1472)
- svchost.exe (PID: 1520)
- svchost.exe (PID: 1664)
- svchost.exe (PID: 1800)
- svchost.exe (PID: 1400)
- svchost.exe (PID: 1656)
- svchost.exe (PID: 1548)
- svchost.exe (PID: 1696)
- svchost.exe (PID: 1836)
- svchost.exe (PID: 1908)
- svchost.exe (PID: 784)
- svchost.exe (PID: 1032)
- svchost.exe (PID: 1164)
- svchost.exe (PID: 1348)
- svchost.exe (PID: 2016)
- svchost.exe (PID: 1916)
- svchost.exe (PID: 2184)
- svchost.exe (PID: 2368)
- svchost.exe (PID: 2376)
- svchost.exe (PID: 2076)
- svchost.exe (PID: 2888)
- svchost.exe (PID: 2828)
- svchost.exe (PID: 2432)
- svchost.exe (PID: 2268)
- svchost.exe (PID: 2356)
- spoolsv.exe (PID: 2660)
- svchost.exe (PID: 2720)
- OfficeClickToRun.exe (PID: 2908)
- svchost.exe (PID: 2924)
- svchost.exe (PID: 3056)
- svchost.exe (PID: 2944)
- svchost.exe (PID: 3032)
- svchost.exe (PID: 2900)
- svchost.exe (PID: 2972)
- svchost.exe (PID: 2964)
- svchost.exe (PID: 3160)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 3632)
- dasHost.exe (PID: 4056)
- svchost.exe (PID: 3936)
- svchost.exe (PID: 3716)
- svchost.exe (PID: 3876)
- svchost.exe (PID: 4168)
- svchost.exe (PID: 2984)
- explorer.exe (PID: 4472)
- sihost.exe (PID: 1560)
- ctfmon.exe (PID: 4252)
- svchost.exe (PID: 4364)
- svchost.exe (PID: 4176)
- svchost.exe (PID: 4404)
- svchost.exe (PID: 3352)
- svchost.exe (PID: 3152)
- svchost.exe (PID: 3968)
- RuntimeBroker.exe (PID: 5888)
- dllhost.exe (PID: 6000)
- UserOOBEBroker.exe (PID: 5760)
- ApplicationFrameHost.exe (PID: 5544)
- svchost.exe (PID: 5456)
- svchost.exe (PID: 2760)
- MoUsoCoreWorker.exe (PID: 5140)
- svchost.exe (PID: 1784)
- svchost.exe (PID: 544)
- svchost.exe (PID: 2732)
- svchost.exe (PID: 3368)
- uhssvc.exe (PID: 1716)
- svchost.exe (PID: 2408)
- svchost.exe (PID: 4732)
- RuntimeBroker.exe (PID: 5048)
- RuntimeBroker.exe (PID: 5212)
- dllhost.exe (PID: 5408)
- RuntimeBroker.exe (PID: 2876)
- svchost.exe (PID: 2508)
- svchost.exe (PID: 6340)
- WmiPrvSE.exe (PID: 708)
- WmiPrvSE.exe (PID: 1744)
- taskhostw.exe (PID: 4936)
- svchost.exe (PID: 4716)
Runs injected code in another process
- dialer.exe (PID: 6384)
- dialer.exe (PID: 6396)
Actions looks like stealing of personal data
- 323.exe (PID: 6388)
METASTEALER has been detected (SURICATA)
- 323.exe (PID: 6388)
Creates a writable file in the system directory
- powershell.exe (PID: 1604)
SUSPICIOUS
Reads the date of Windows installation
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- DCRatBuild.exe (PID: 6380)
- MVPInstaller.exe (PID: 6564)
Reads security settings of Internet Explorer
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- MVPInstaller.exe (PID: 6564)
- DCRatBuild.exe (PID: 6380)
- TextInputHost.exe (PID: 6892)
- OfficeClickToRun.exe (PID: 2908)
Executable content was dropped or overwritten
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- MVPInstaller.exe (PID: 6440)
- DCRatBuild.exe (PID: 6380)
- MVPInstaller.exe (PID: 6564)
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Reads the Windows owner or organization settings
- MVPInstaller.exe (PID: 6440)
Starts CMD.EXE for commands execution
- MVPInstaller.exe (PID: 6440)
- wscript.exe (PID: 6540)
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Executing commands from a ".bat" file
- MVPInstaller.exe (PID: 6440)
- wscript.exe (PID: 6540)
Process drops legitimate windows executable
- MVPInstaller.exe (PID: 6564)
- svchost.exe (PID: 2732)
The process drops C-runtime libraries
- MVPInstaller.exe (PID: 6564)
Script adds exclusion path to Windows Defender
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Script adds exclusion extension to Windows Defender
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Starts POWERSHELL.EXE for commands execution
- build.exe (PID: 6356)
- WinUpdater.exe (PID: 5032)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6540)
Searches for installed software
- 323.exe (PID: 6388)
Process uninstalls Windows update
- wusa.exe (PID: 6660)
- wusa.exe (PID: 2480)
Starts SC.EXE for service management
- build.exe (PID: 6356)
Executes as Windows Service
- WinUpdater.exe (PID: 5032)
Connects to unusual port
- 323.exe (PID: 6388)
- dialer.exe (PID: 3728)
Drops a system driver (possible attempt to evade defenses)
- WinUpdater.exe (PID: 5032)
Checks Windows Trust Settings
- OfficeClickToRun.exe (PID: 2908)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4472)
- RuntimeBroker.exe (PID: 2876)
Checks supported languages
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- build.exe (PID: 6356)
- DCRatBuild.exe (PID: 6380)
- 323.exe (PID: 6388)
- MVPInstaller.exe (PID: 6440)
- MVPInstaller.exe (PID: 6564)
- TextInputHost.exe (PID: 6892)
- WindowsUpdate.exe (PID: 2312)
- MVPInstaller.exe (PID: 6716)
- WinUpdater.exe (PID: 5032)
Reads the computer name
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- DCRatBuild.exe (PID: 6380)
- MVPInstaller.exe (PID: 6440)
- 323.exe (PID: 6388)
- MVPInstaller.exe (PID: 6564)
- MVPInstaller.exe (PID: 6716)
- TextInputHost.exe (PID: 6892)
- WindowsUpdate.exe (PID: 2312)
Process checks computer location settings
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- DCRatBuild.exe (PID: 6380)
- MVPInstaller.exe (PID: 6564)
Create files in a temporary directory
- 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe (PID: 6276)
- MVPInstaller.exe (PID: 6440)
- MVPInstaller.exe (PID: 6564)
Reads the software policy settings
- lsass.exe (PID: 748)
- OfficeClickToRun.exe (PID: 2908)
Creates files or folders in the user directory
- MVPInstaller.exe (PID: 6440)
- dllhost.exe (PID: 5408)
- lsass.exe (PID: 748)
Creates files in the program directory
- MVPInstaller.exe (PID: 6440)
- MoUsoCoreWorker.exe (PID: 5140)
- build.exe (PID: 6356)
- svchost.exe (PID: 1032)
Reads the machine GUID from the registry
- 323.exe (PID: 6388)
- WindowsUpdate.exe (PID: 2312)
- OfficeClickToRun.exe (PID: 2908)
Reads Environment values
- WindowsUpdate.exe (PID: 2312)
- 323.exe (PID: 6388)
Reads Windows Product ID
- WmiPrvSE.exe (PID: 708)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2908)
Reads the time zone
- WmiPrvSE.exe (PID: 708)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6992)
- powershell.exe (PID: 1604)
Drops the executable file immediately after the start
- svchost.exe (PID: 2732)
Creates a writable file in the system directory
- svchost.exe (PID: 2924)
- lsass.exe (PID: 748)
- OfficeClickToRun.exe (PID: 2908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 5120 |
| InitializedDataSize: | 25021952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20cc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
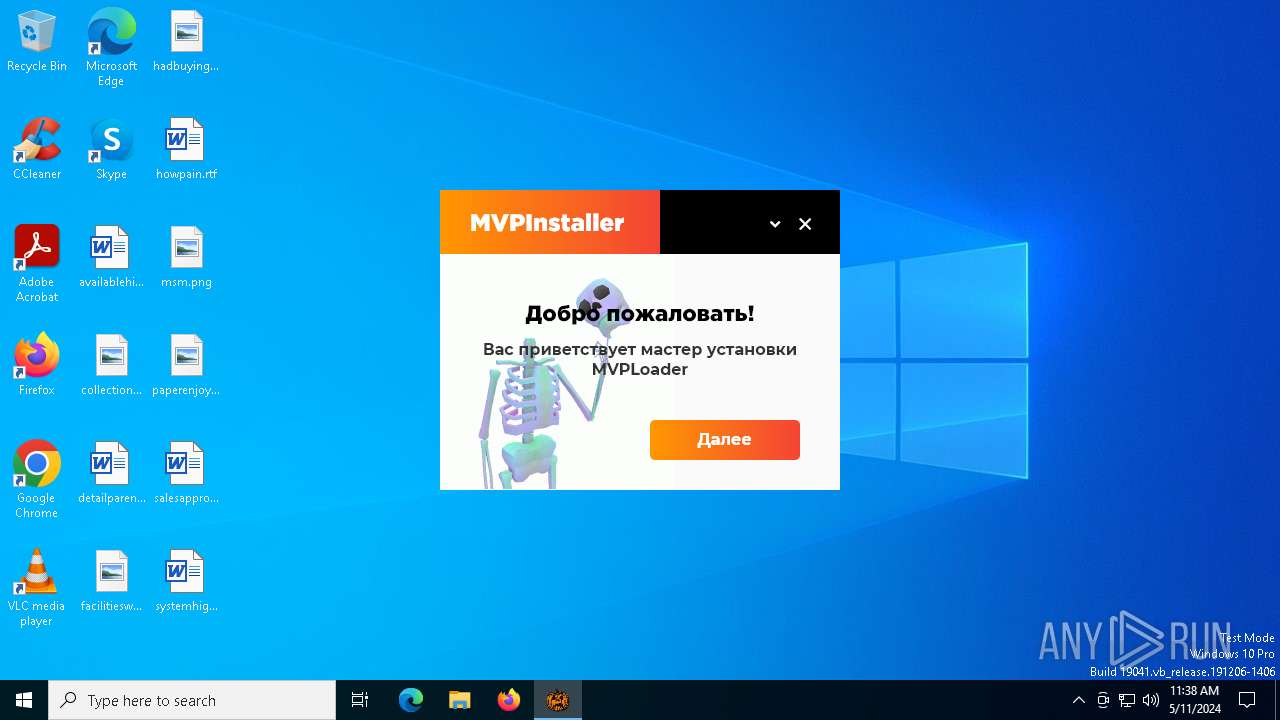
| CompanyName: | MVPLoader LLC |
| FileDescription: | MVPInstaller Setup |
| FileVersion: | 2 |
| InternalName: | MVPInstaller |
| LegalCopyright: | Copyright © 2024 MVPLoader LLC |
| LegalTrademarks: | - |
| OriginalFileName: | MVPInstaller.exe |
| PrivateBuild: | - |
| ProductName: | MVPInstaller |
| ProductVersion: | 2 |
| SpecialBuild: | - |
Total processes
165
Monitored processes
127
Malicious processes
95
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | "dwm.exe" | C:\Windows\System32\dwm.exe | winlogon.exe | ||||||||||||
User: DWM-1 Company: Microsoft Corporation Integrity Level: SYSTEM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | C:\WINDOWS\System32\svchost.exe -k netsvcs -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 708 | C:\WINDOWS\system32\wbem\wmiprvse.exe -secured -Embedding | C:\Windows\System32\wbem\WmiPrvSE.exe | svchost.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Provider Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 748 | C:\WINDOWS\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\WINDOWS\system32\dialer.exe | C:\Windows\System32\dialer.exe | — | WinUpdater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Phone Dialer Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s gpsvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1032 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s DsmSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1064 | C:\WINDOWS\System32\svchost.exe -k LocalServiceNetworkRestricted -p -s lmhosts | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
79 205
Read events
78 334
Write events
592
Delete events
279
Modification events
| (PID) Process: | (4472) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000044000000 | |||
| (PID) Process: | (748) lsass.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\W32Time\SecureTimeLimits |
| Operation: | write | Name: | SecureTimeHigh |
Value: 5E3432F6CE6FDA01 | |||
| (PID) Process: | (748) lsass.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\W32Time\SecureTimeLimits |
| Operation: | write | Name: | SecureTimeEstimated |
Value: 5ECC6D94C66FDA01 | |||
| (PID) Process: | (748) lsass.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\W32Time\SecureTimeLimits |
| Operation: | write | Name: | SecureTimeLow |
Value: 5E64A932BE6FDA01 | |||
| (PID) Process: | (748) lsass.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\W32Time\SecureTimeLimits\RunTime |
| Operation: | write | Name: | SecureTimeTickCount |
Value: 465C110000000000 | |||
| (PID) Process: | (748) lsass.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\W32Time\SecureTimeLimits\RunTime |
| Operation: | write | Name: | SecureTimeConfidence |
Value: 0 | |||
| (PID) Process: | (6276) 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6276) 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6276) 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6276) 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
27
Suspicious files
100
Text files
23
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6276 | 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe | C:\Users\admin\AppData\Local\Temp\DCRatBuild.exe | executable | |
MD5:CADDB11F9014C4B6BD7F79306211899F | SHA256:5BE33A975FB052C1A4338ED8DECA2641F5A9FA52F2CF3C6FD71B420FFF462440 | |||
| 6564 | MVPInstaller.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\data\app.so | — | |
MD5:— | SHA256:— | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\SVCHOST.EXE-0C2D202C.pf | binary | |
MD5:462462C0EE5E4C7DC19F27C5F0855970 | SHA256:96D4ACBFCA738F70EA3AA9874BFA6BE281F38C0AF29C98B065D4A759CC5A6C33 | |||
| 6440 | MVPInstaller.exe | C:\Users\admin\AppData\Local\Temp\genteert.dll | executable | |
MD5:6CE814FD1AD7AE07A9E462C26B3A0F69 | SHA256:54C0DA1735BB1CB02B60C321DE938488345F8D1D26BF389C8CB2ACAD5D01B831 | |||
| 6276 | 82ae530eb29e0c64986dbd019f86cac5eff3daf3c1fb861757a60252eb1e4661.exe | C:\Users\admin\AppData\Local\Temp\323.exe | executable | |
MD5:53C1D38049F4318E577C3AB1BCC6E38F | SHA256:AD6BAED534549A8EB75F44C05807581E0EB5FDE56A8B3A64A741853BCB19A863 | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\82AE530EB29E0C64986DBD019F86C-785B32DF.pf | binary | |
MD5:22B07320906C064A3C75E8154520543F | SHA256:CF0D5FD2262135EECDD8DD4A4AEA8B3AFA02797A2EA71F658876A9466C4679CC | |||
| 4472 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 6380 | DCRatBuild.exe | C:\WindowsUpdate\2UpMr4oh.bat | text | |
MD5:ECECCB4DAB2899A896F6727230DDB26A | SHA256:F7F7150AE59104004CC4BDD36110807333EF0A27C0CE0A08FD0AE2646159F73C | |||
| 6440 | MVPInstaller.exe | C:\Users\admin\AppData\Local\Temp\gentee65\guig.dll | executable | |
MD5:D3F8C0334C19198A109E44D074DAC5FD | SHA256:005C251C21D6A5BA1C3281E7B9F3B4F684D007E0C3486B34A545BB370D8420AA | |||
| 1664 | svchost.exe | C:\Windows\Prefetch\UPFC.EXE-BDDF79D6.pf | binary | |
MD5:675F0AEA5D25CA5817F98AFCA5D60C6B | SHA256:A60A9491F07BD9D5E3EC25C528850C9B10B2DA503250C74330F40E5A6CAAAF69 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
54
DNS requests
26
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4264 | svchost.exe | GET | 200 | 2.16.164.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
4264 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4680 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
2508 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
7116 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
7116 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
6172 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
2908 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4708 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4264 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4264 | svchost.exe | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
4264 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
6388 | 323.exe | 176.123.161.158:1337 | — | OOO MediaSeti | RU | malicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5140 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
xmr.2miners.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6388 | 323.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
6388 | 323.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer/MetaStealer Family Related (MC-NMF Authorization) |
6388 | 323.exe | A Network Trojan was detected | ET MALWARE Redline Stealer/MetaStealer Family Activity (Response) |
2184 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER Observed DNS Query to Cryptocurrency Mining Pool Domain (xmr .2miners .com) |