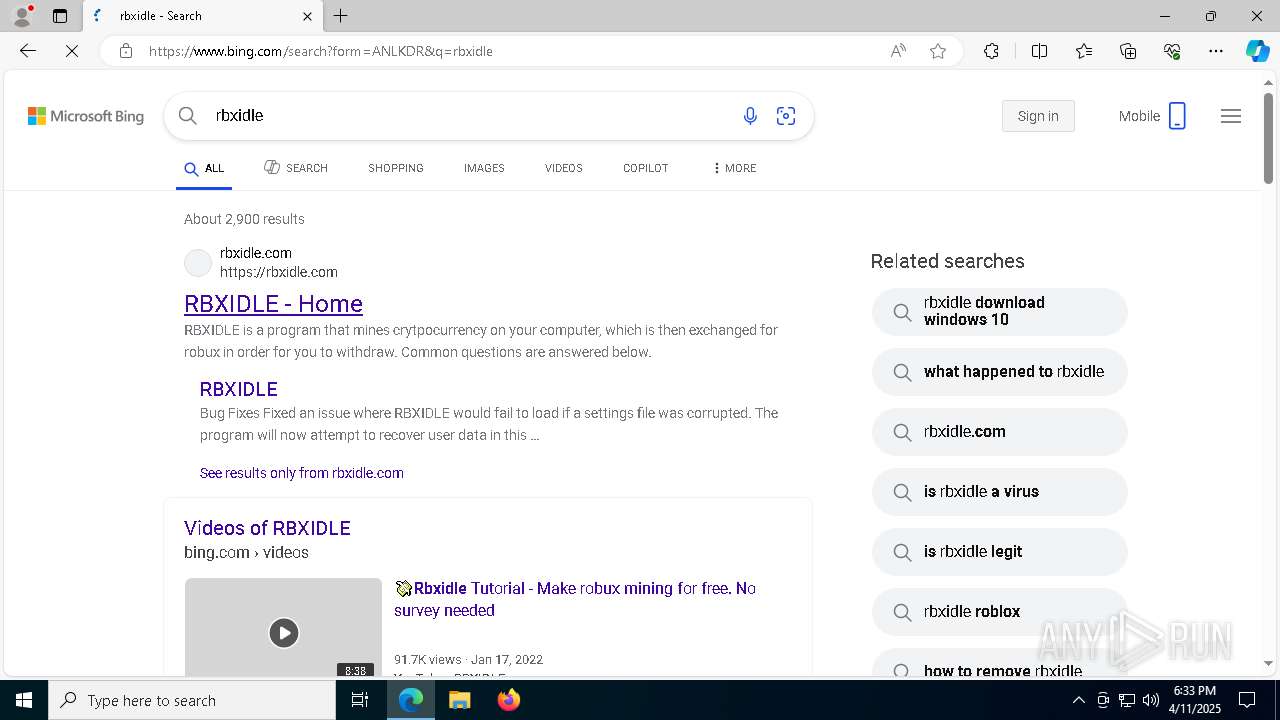
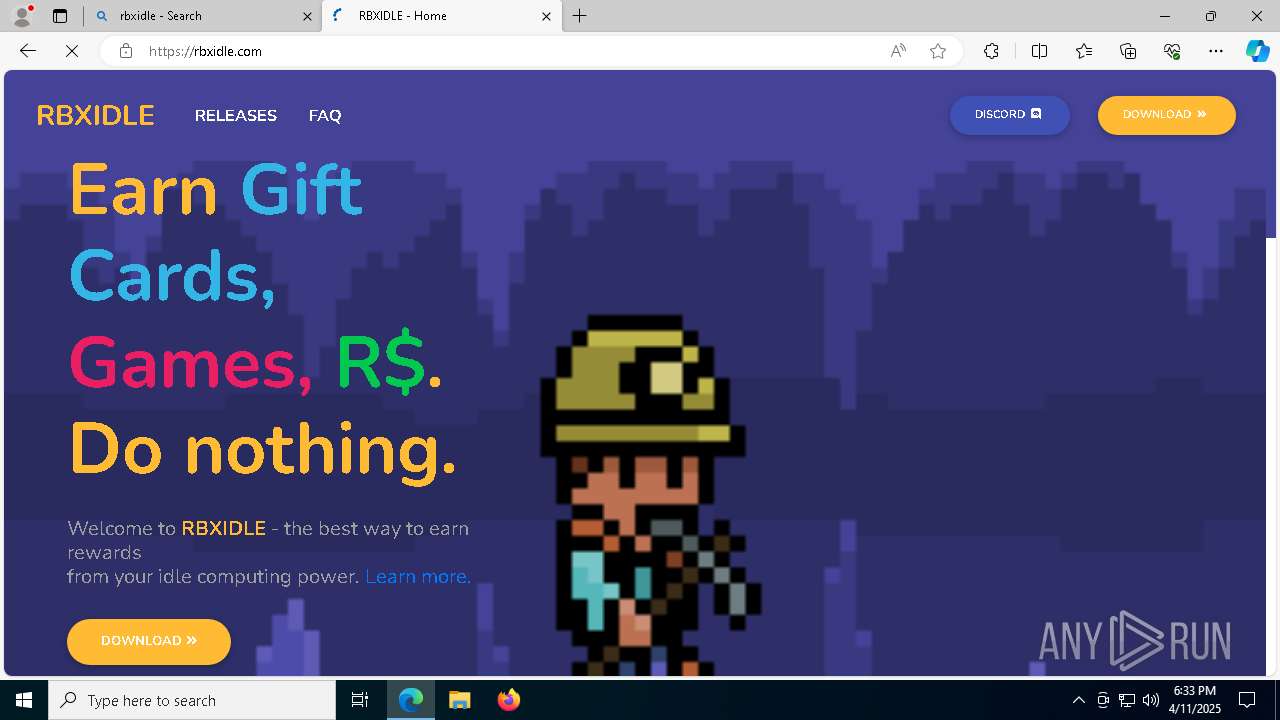
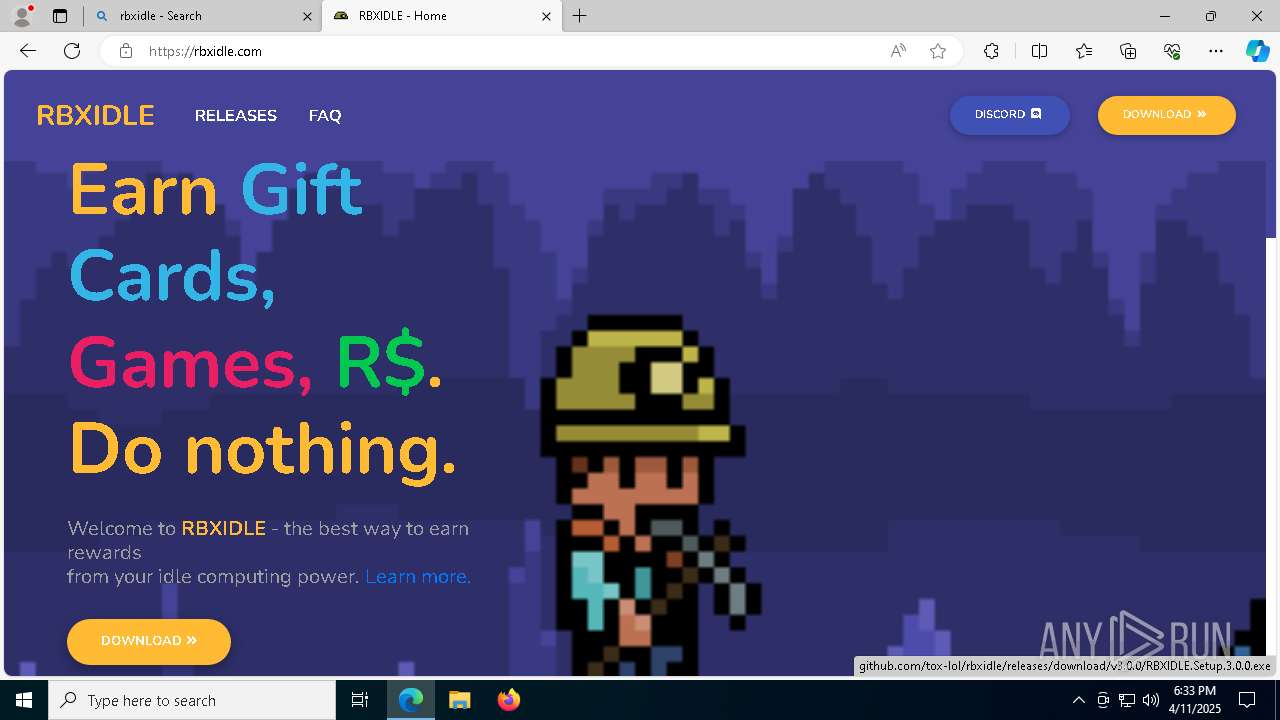
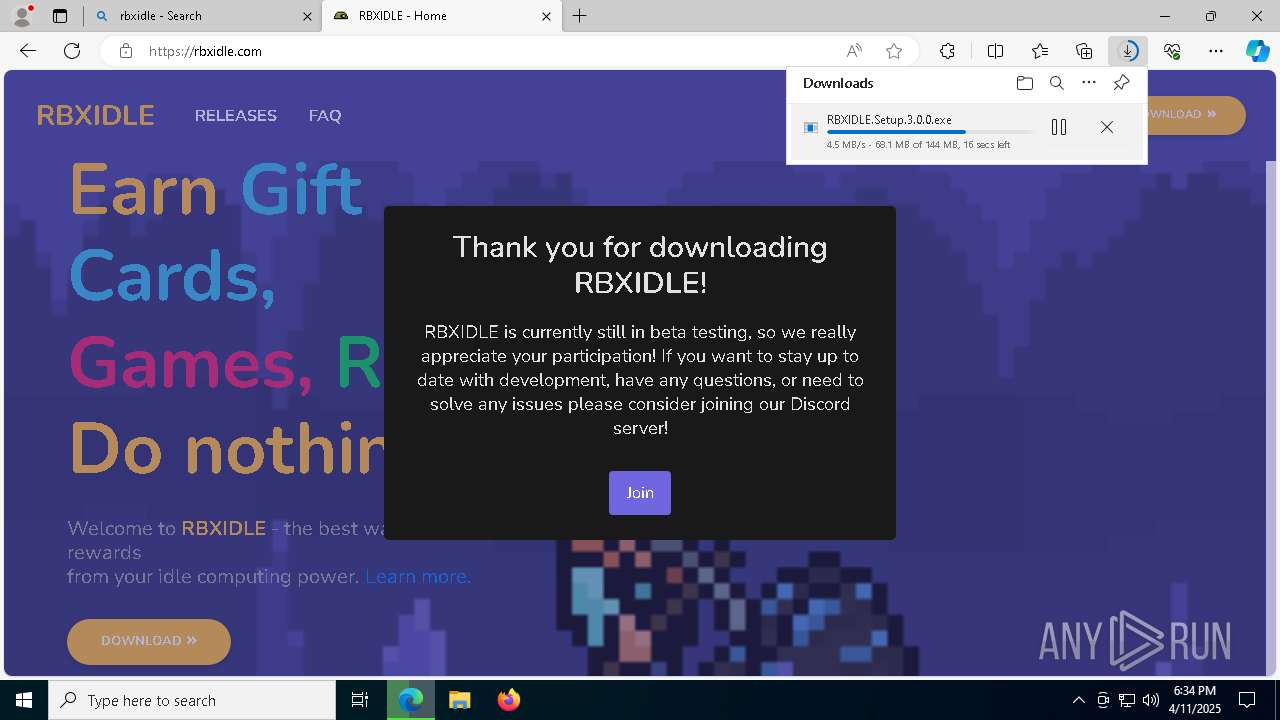
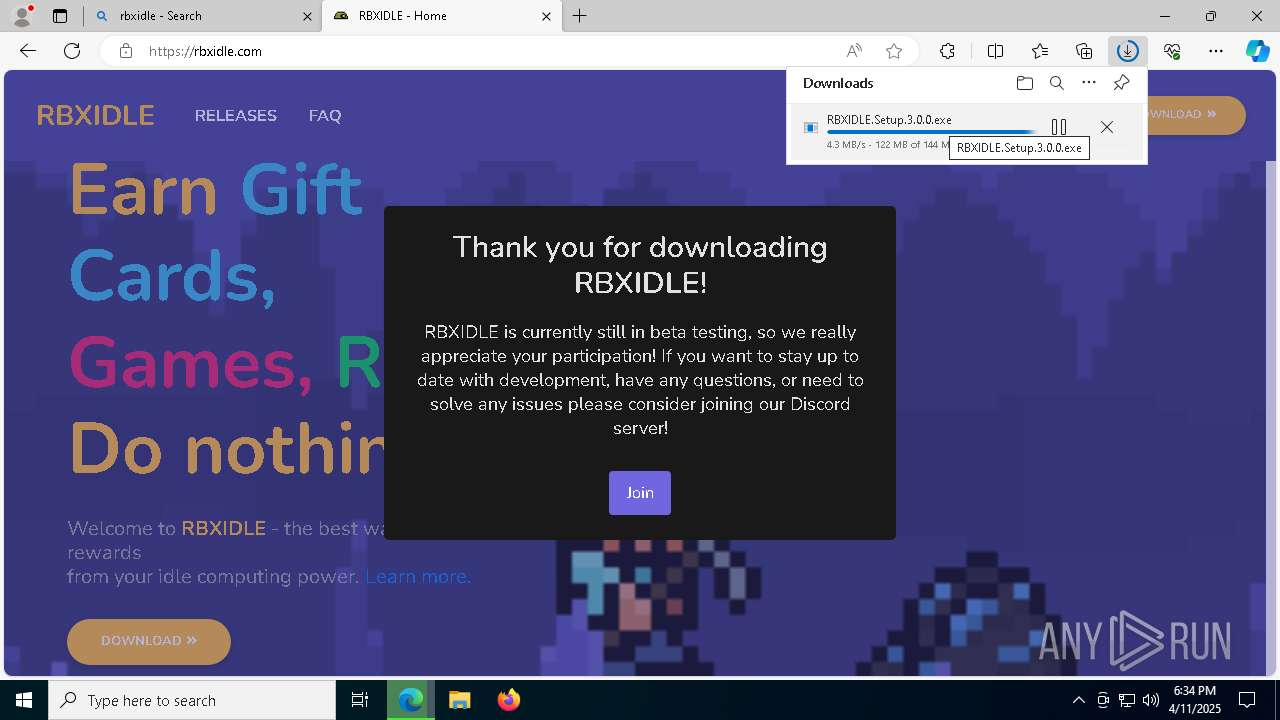
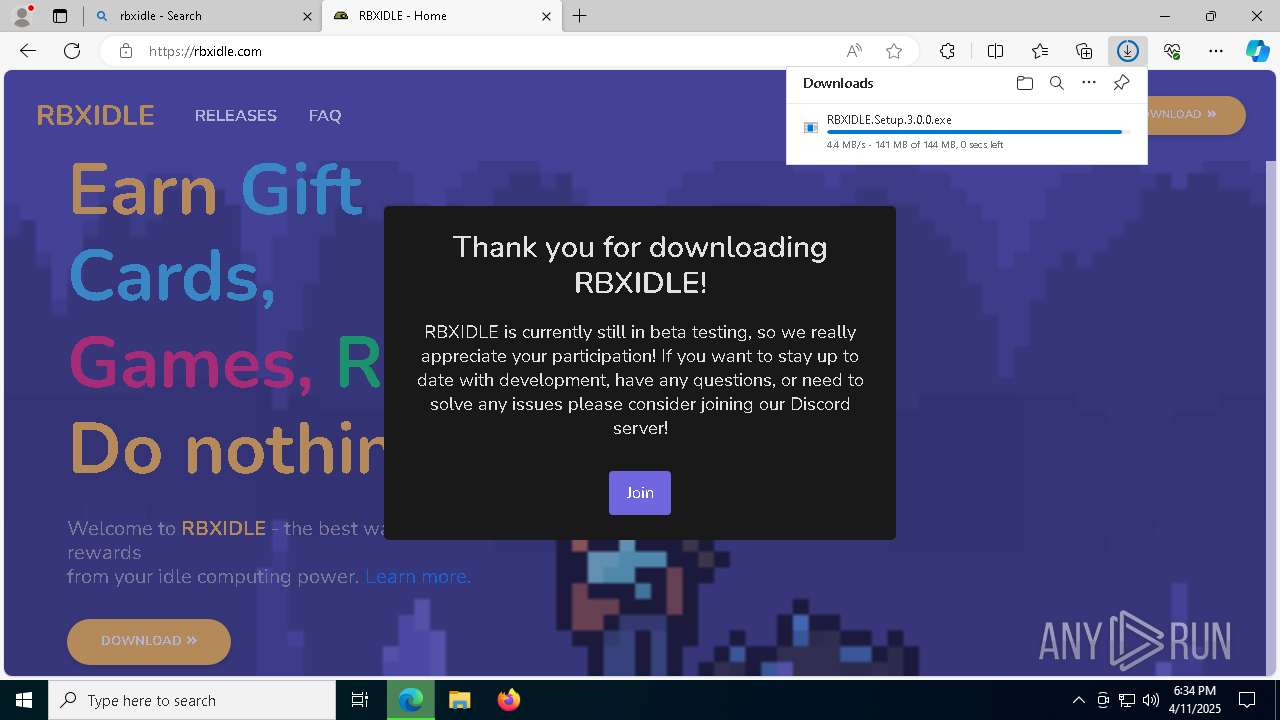
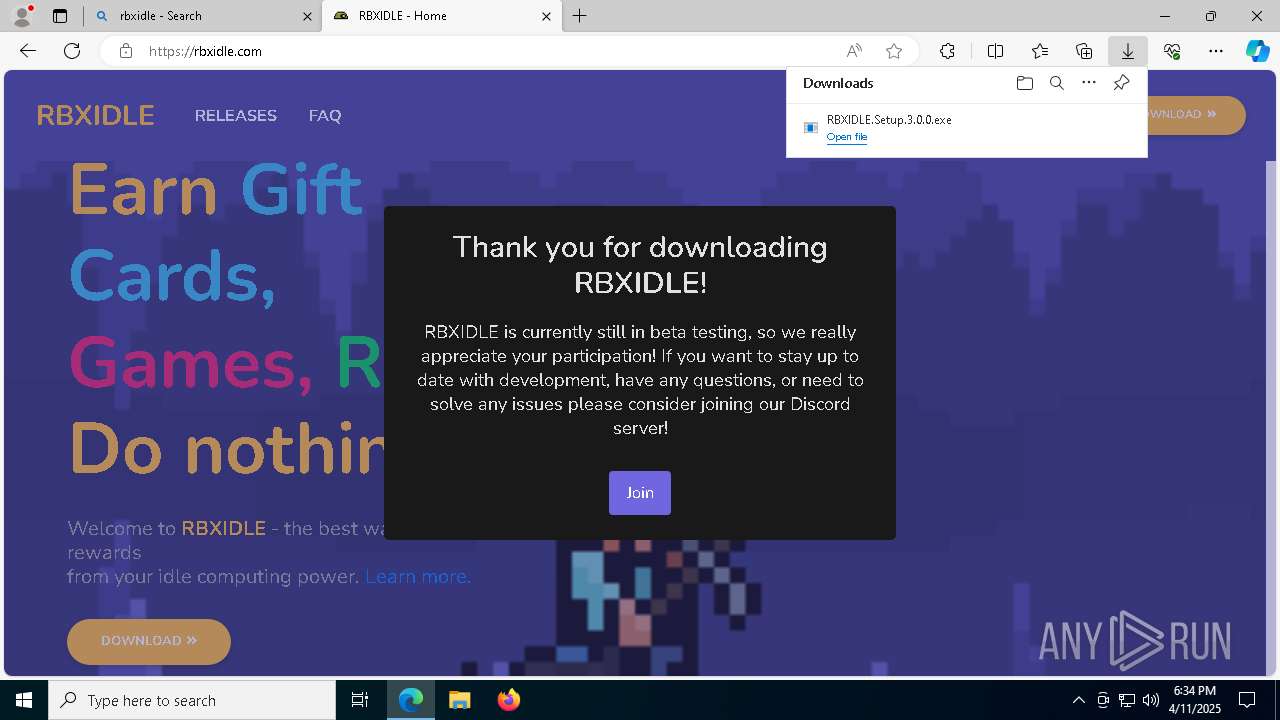
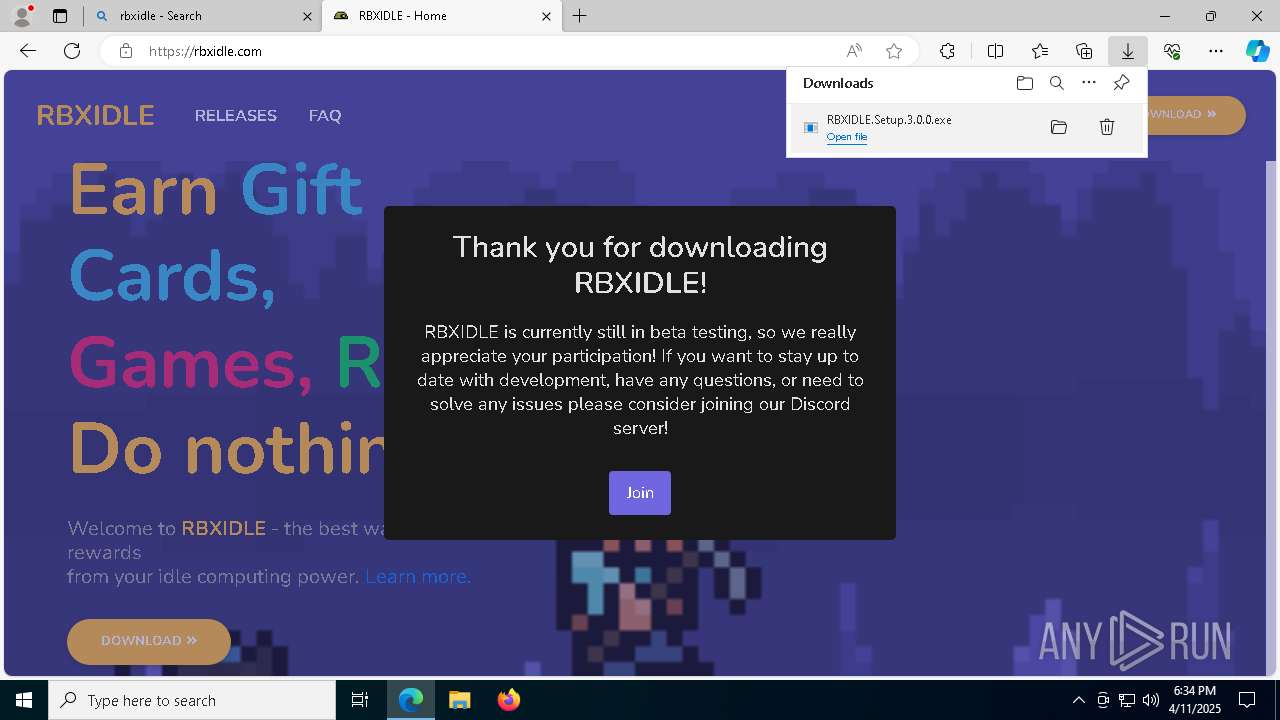
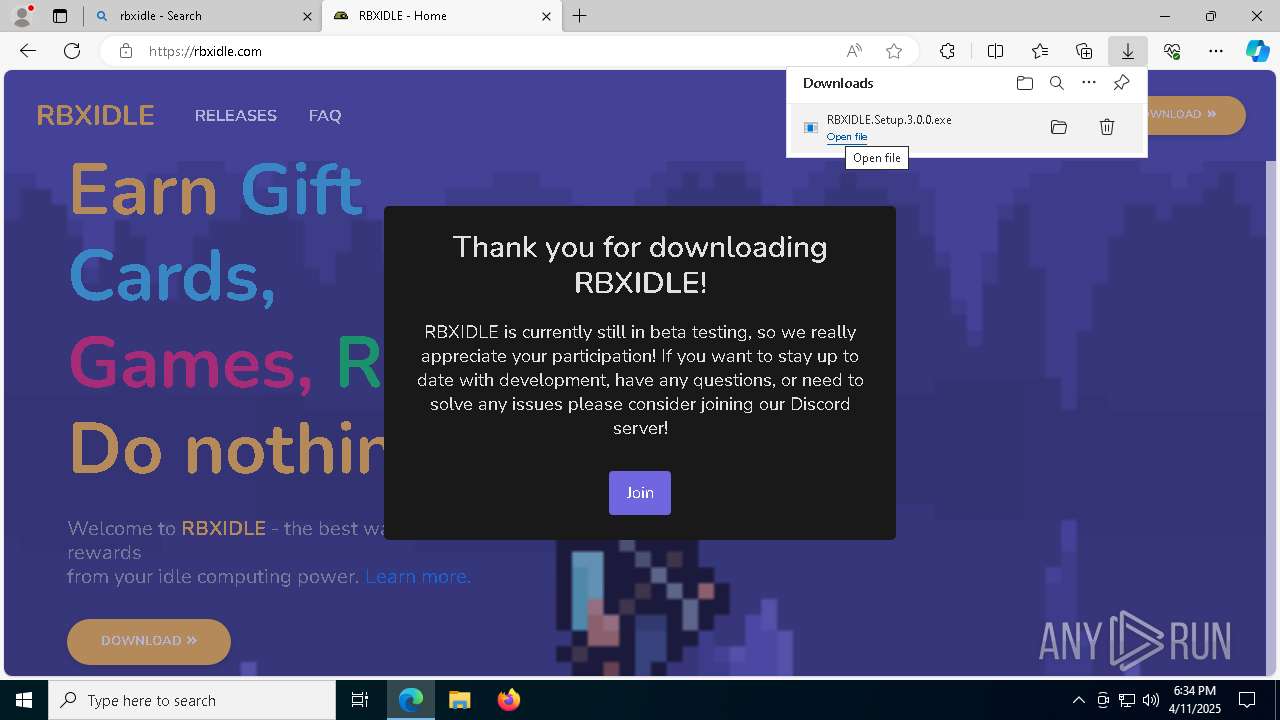
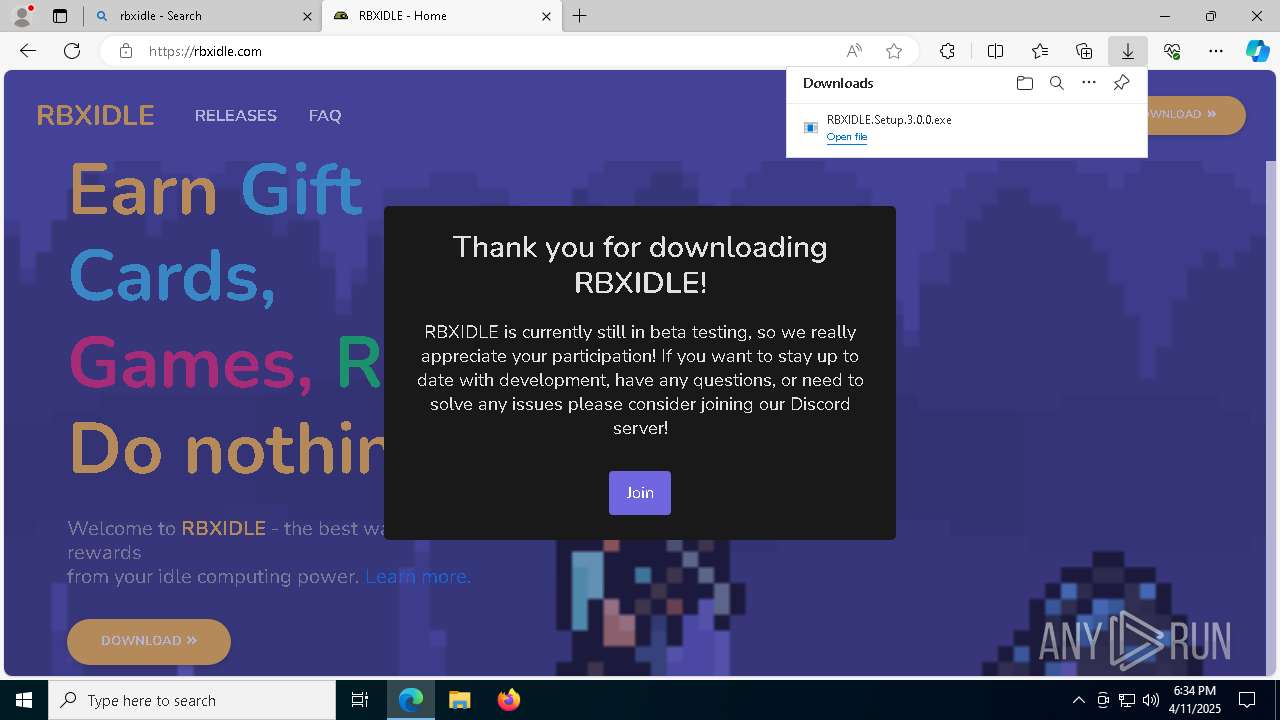
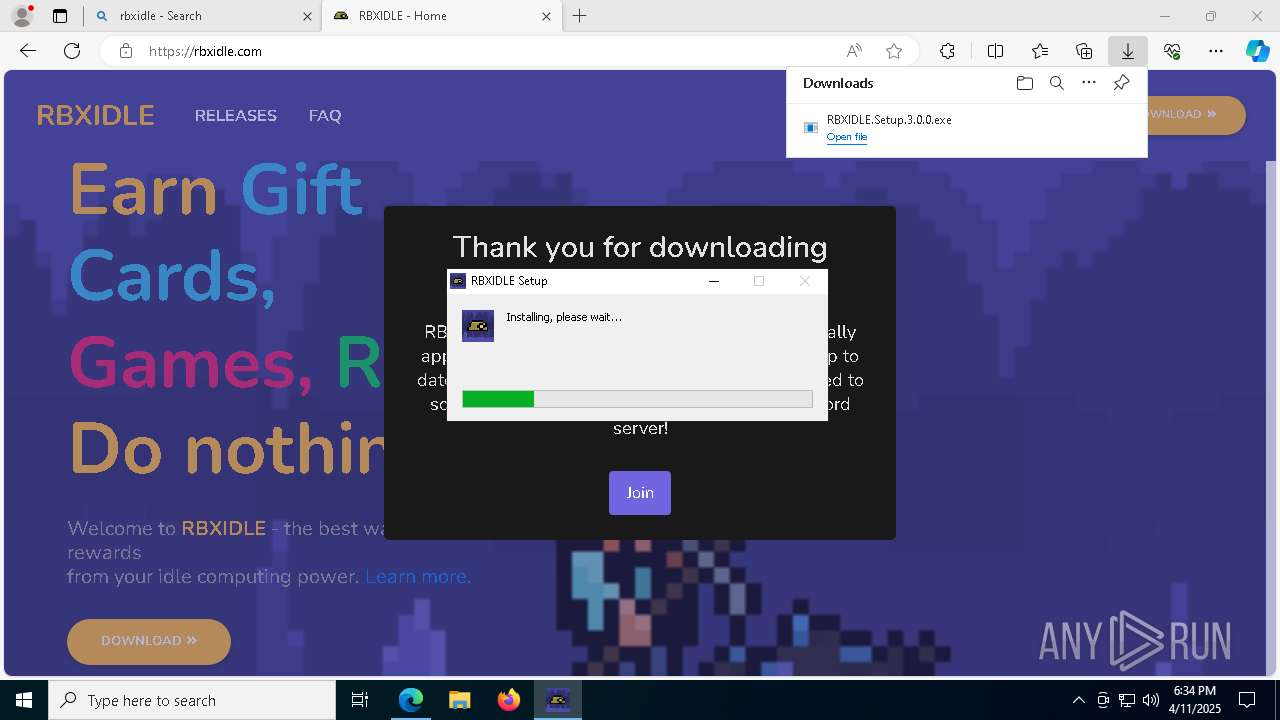
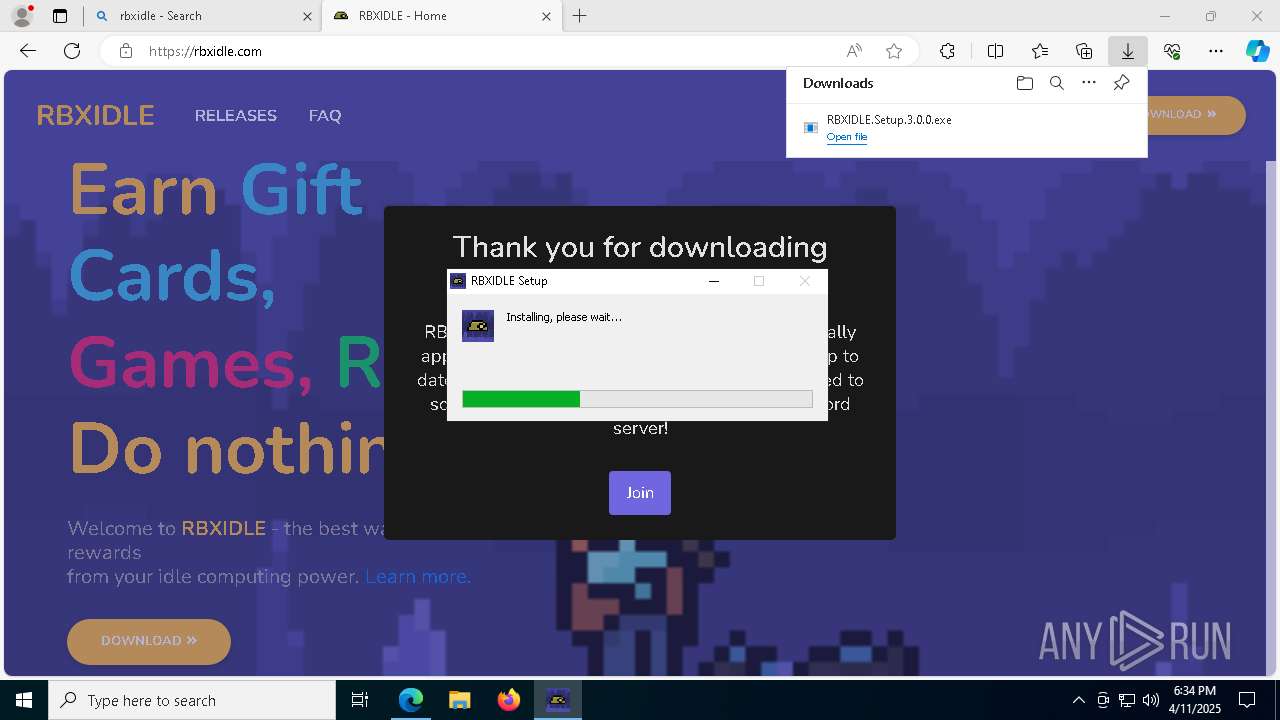
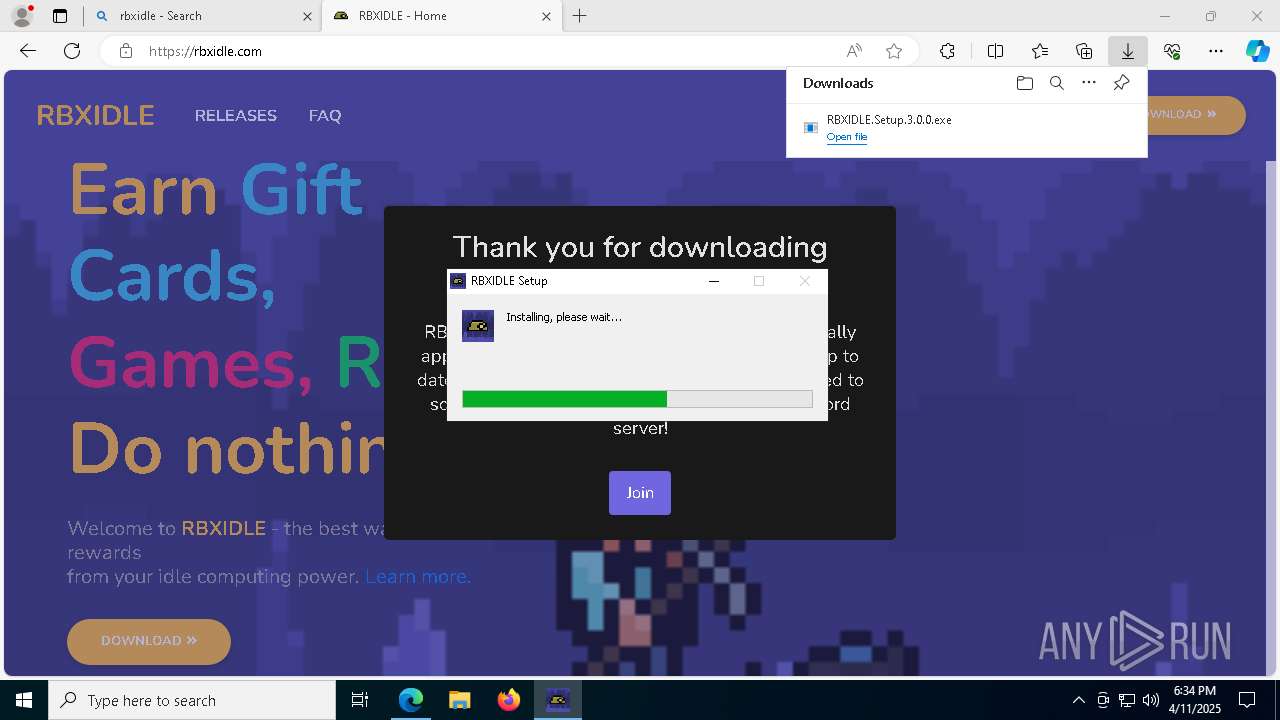
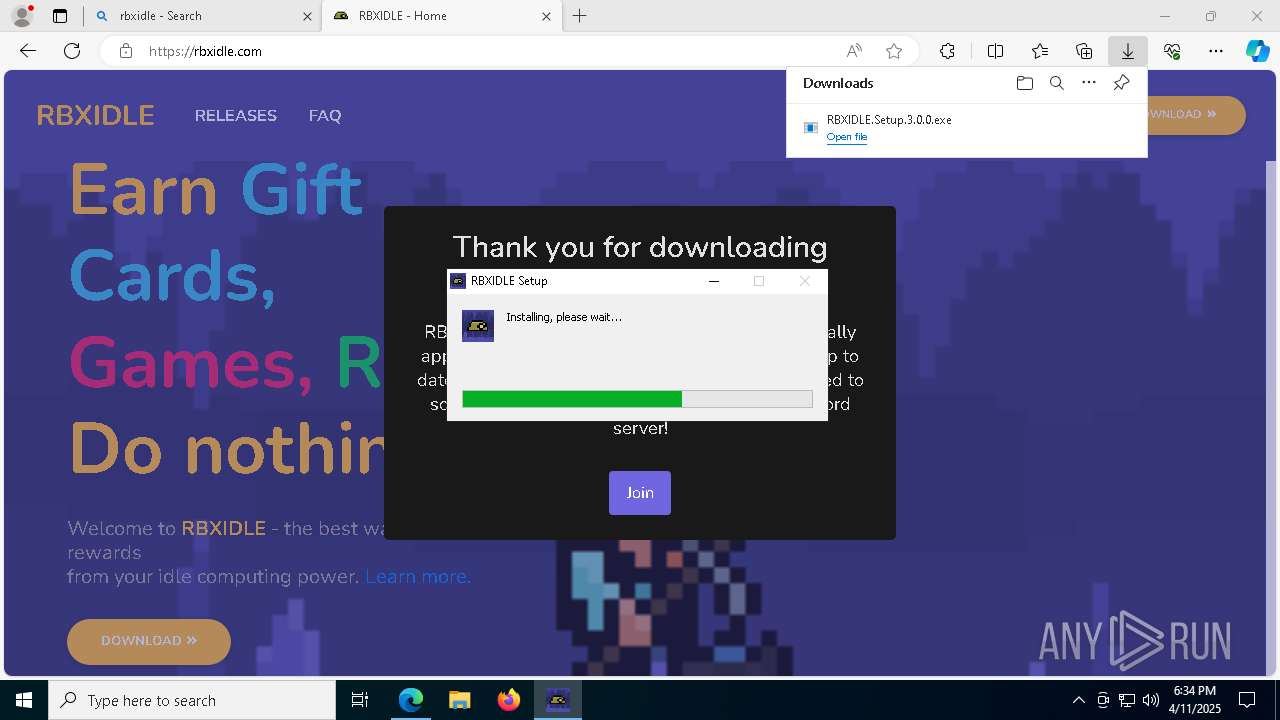
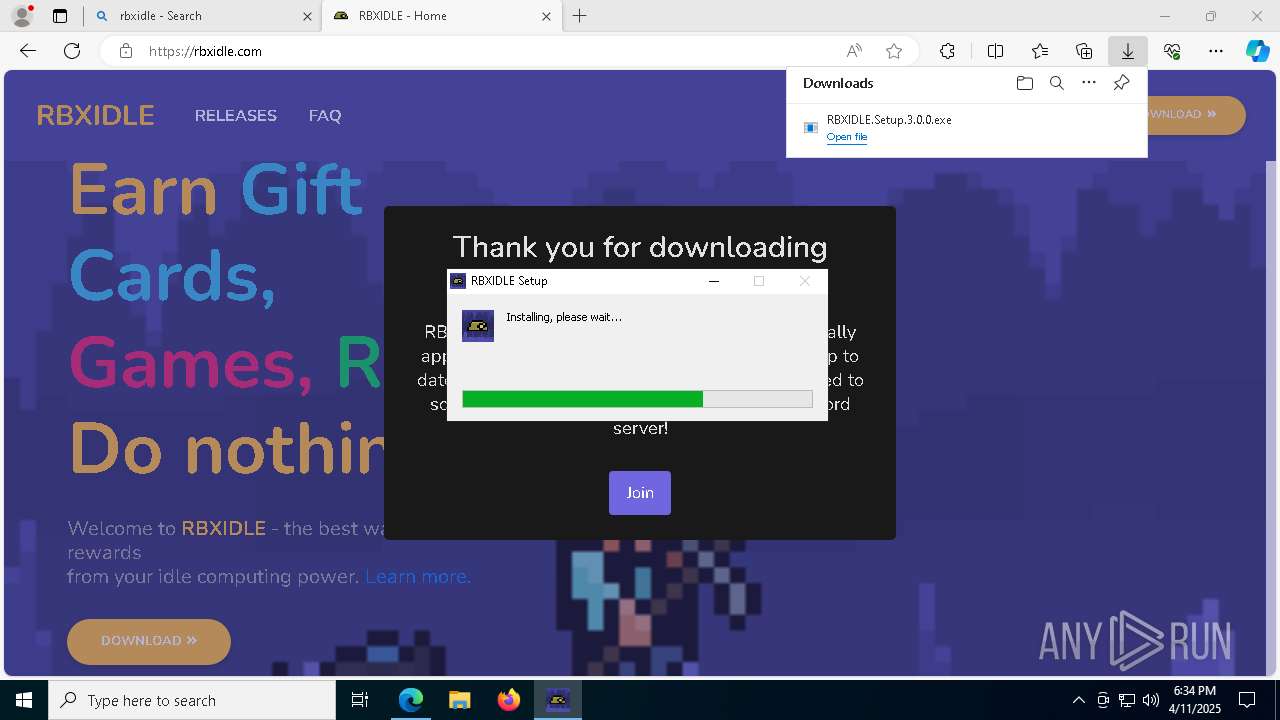
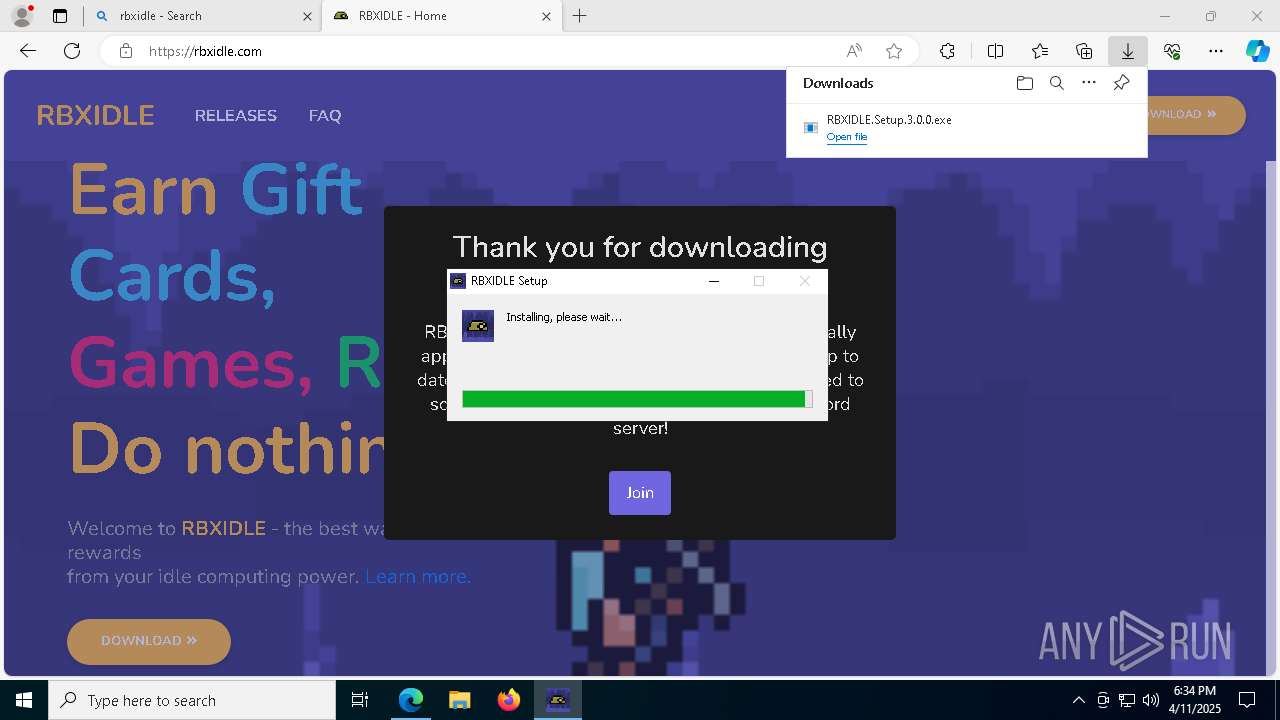
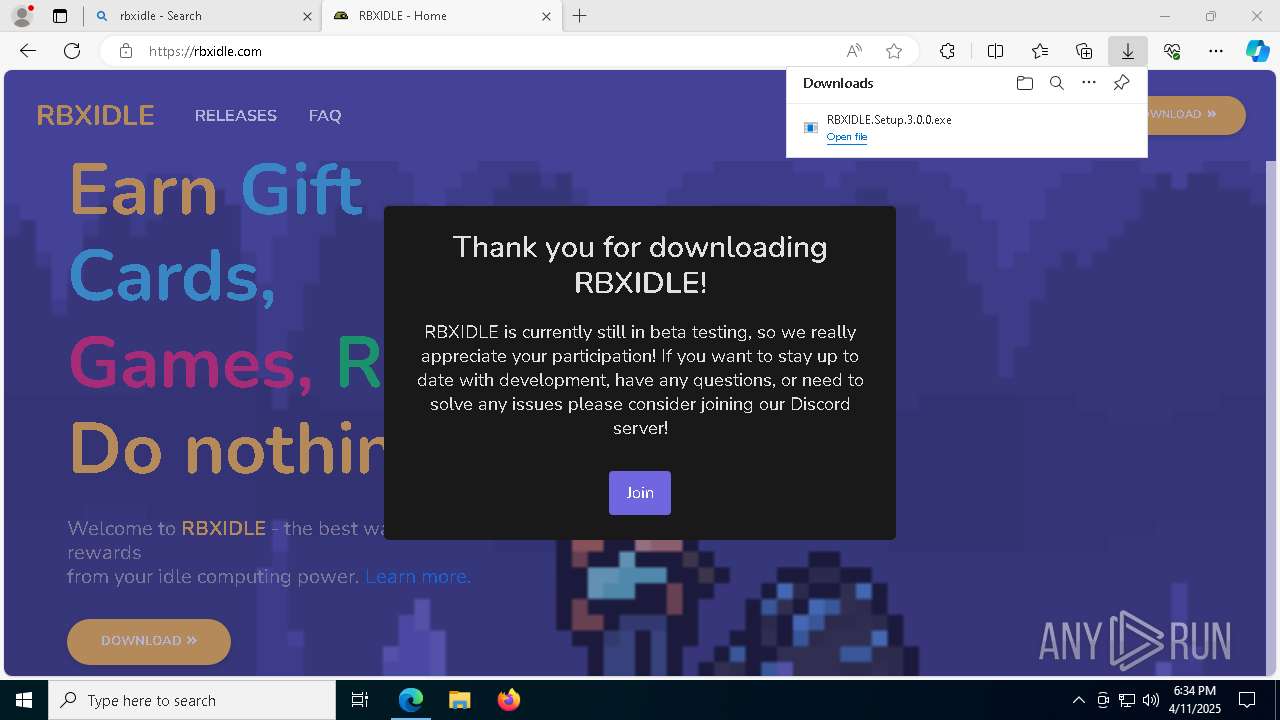
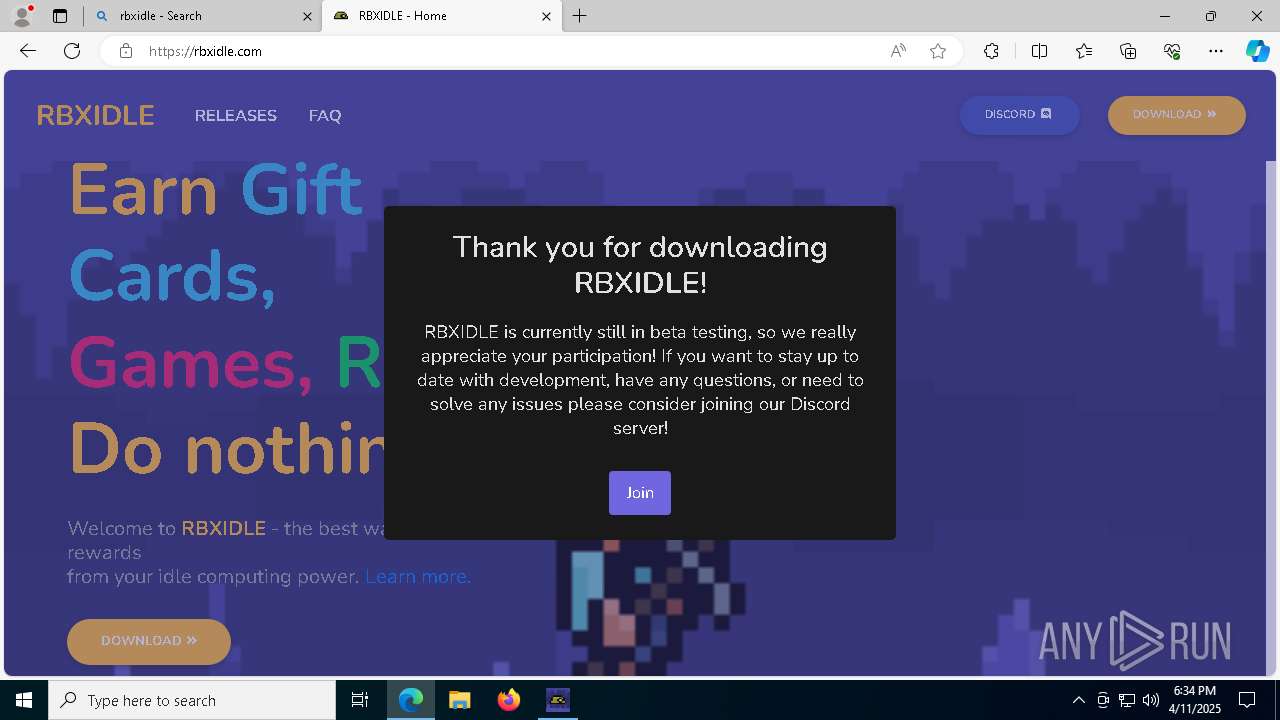
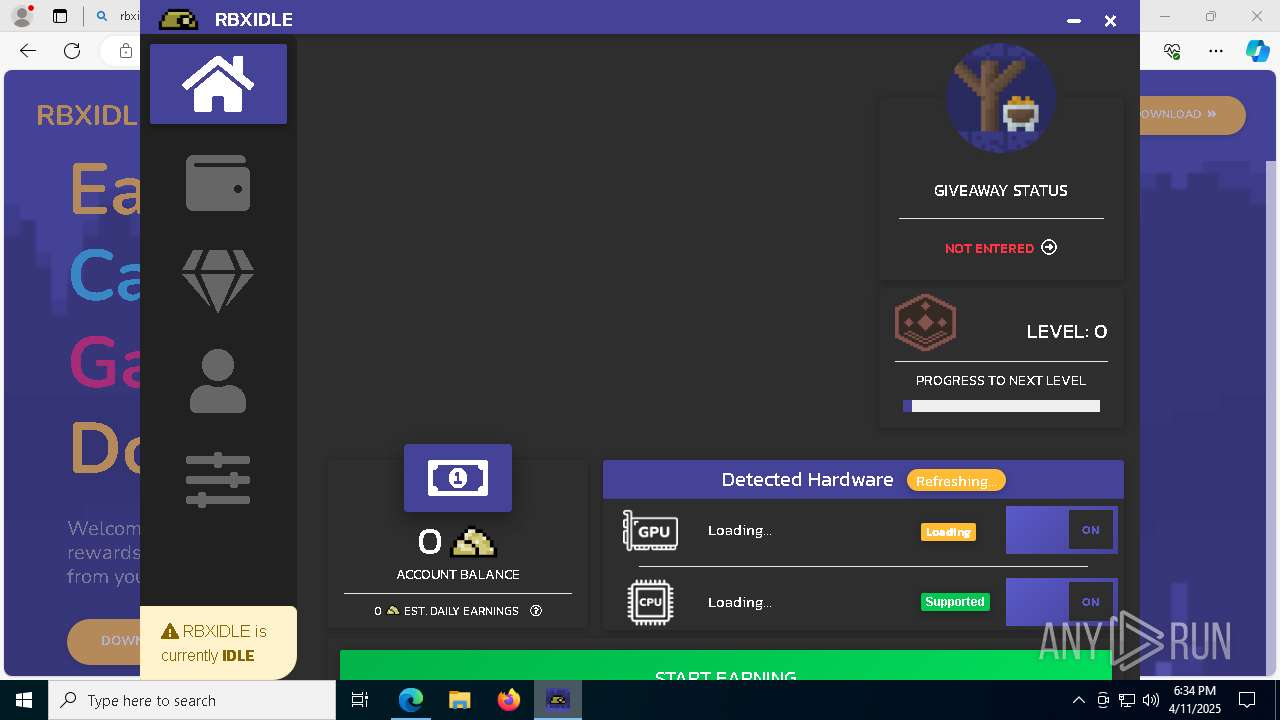
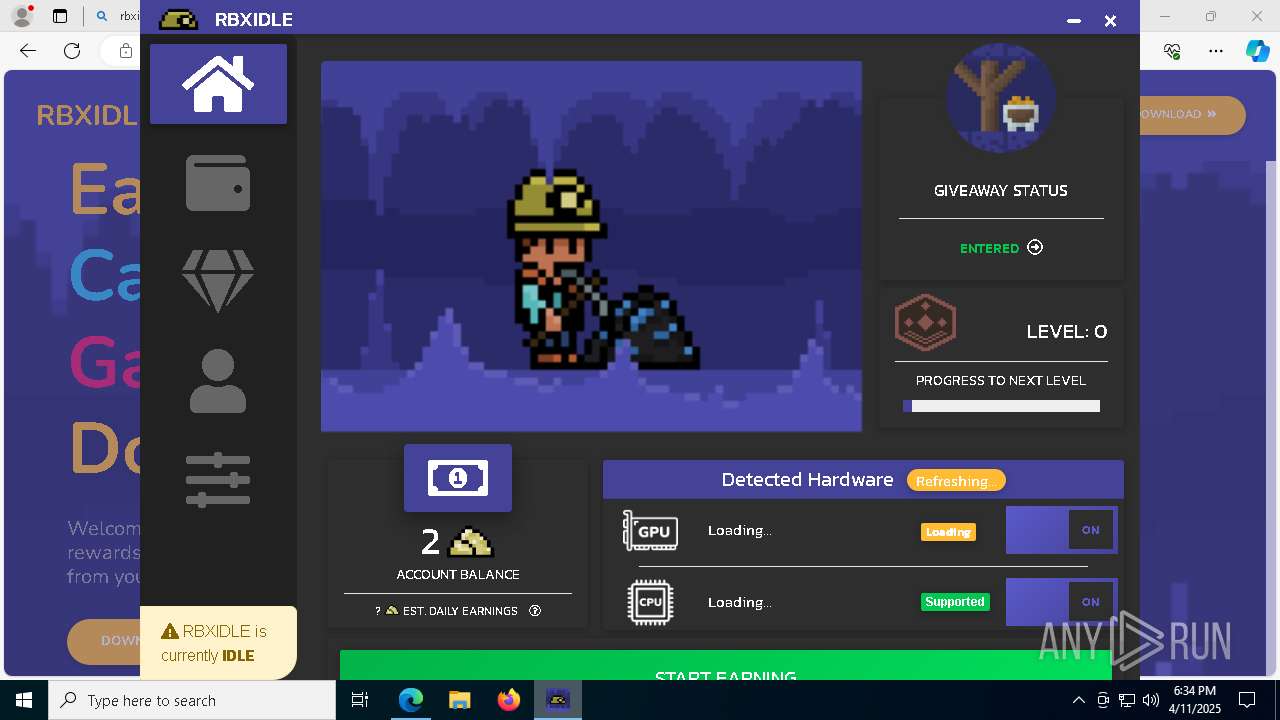
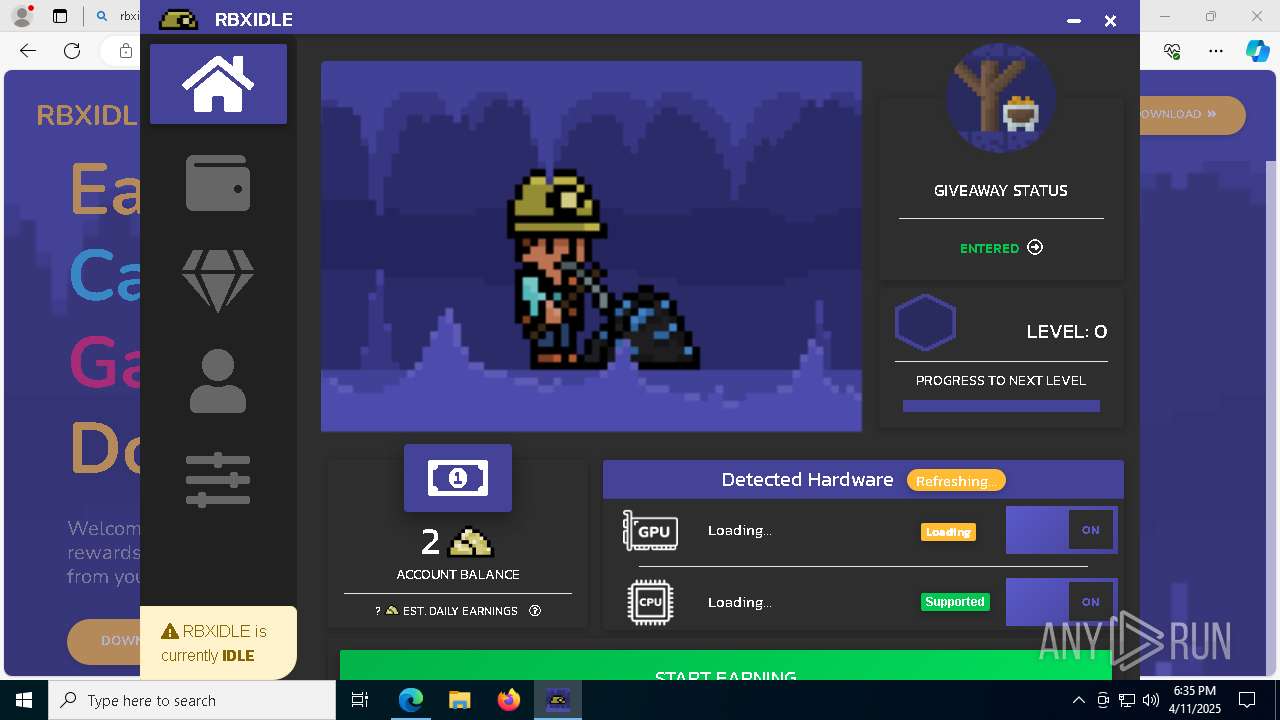
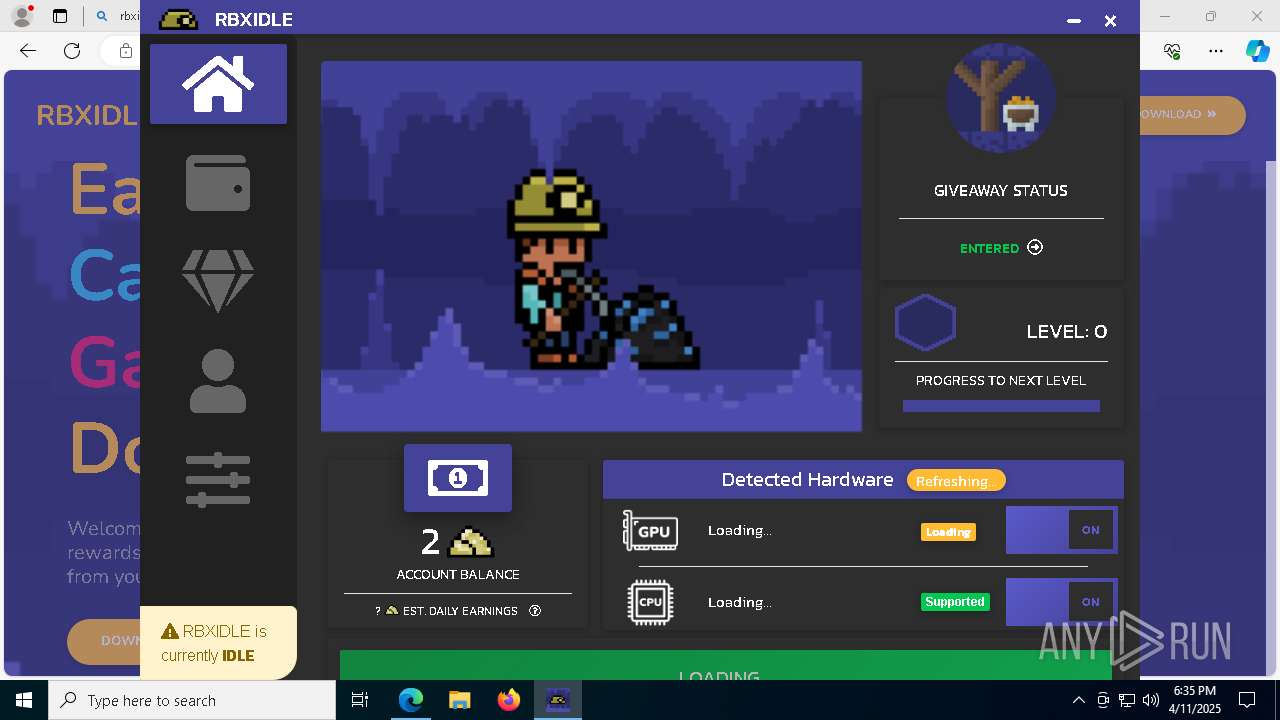
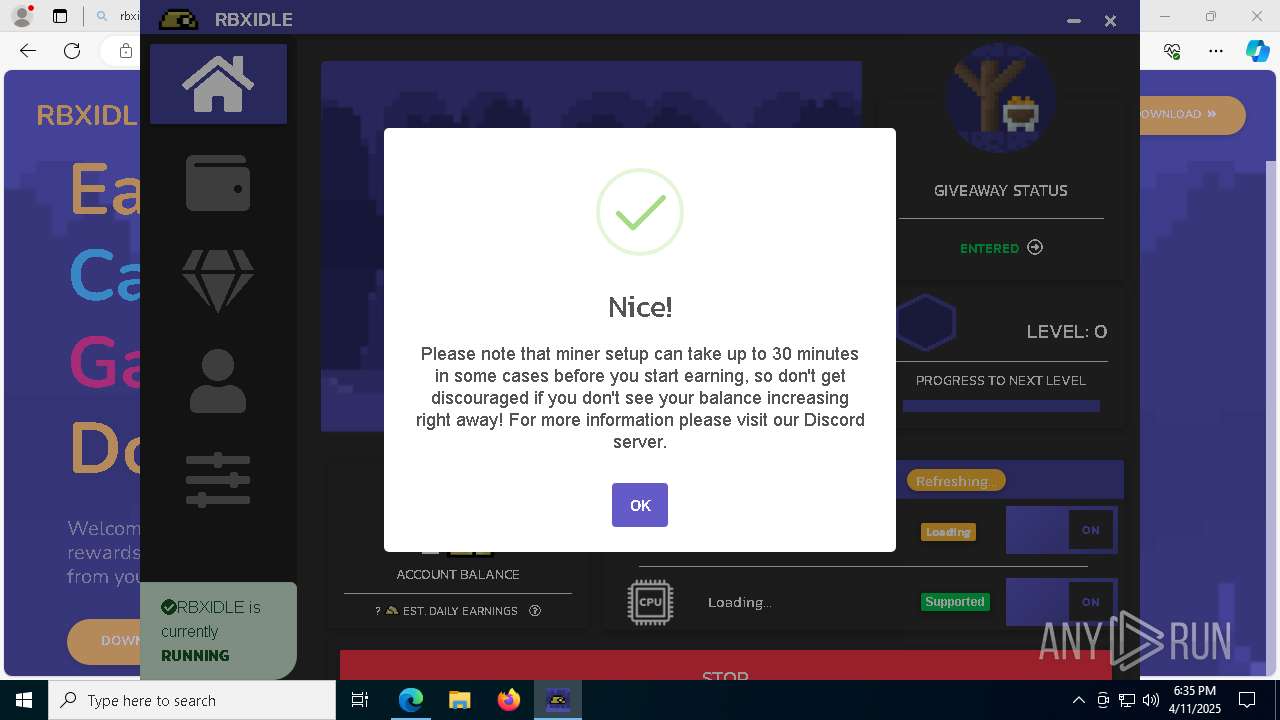
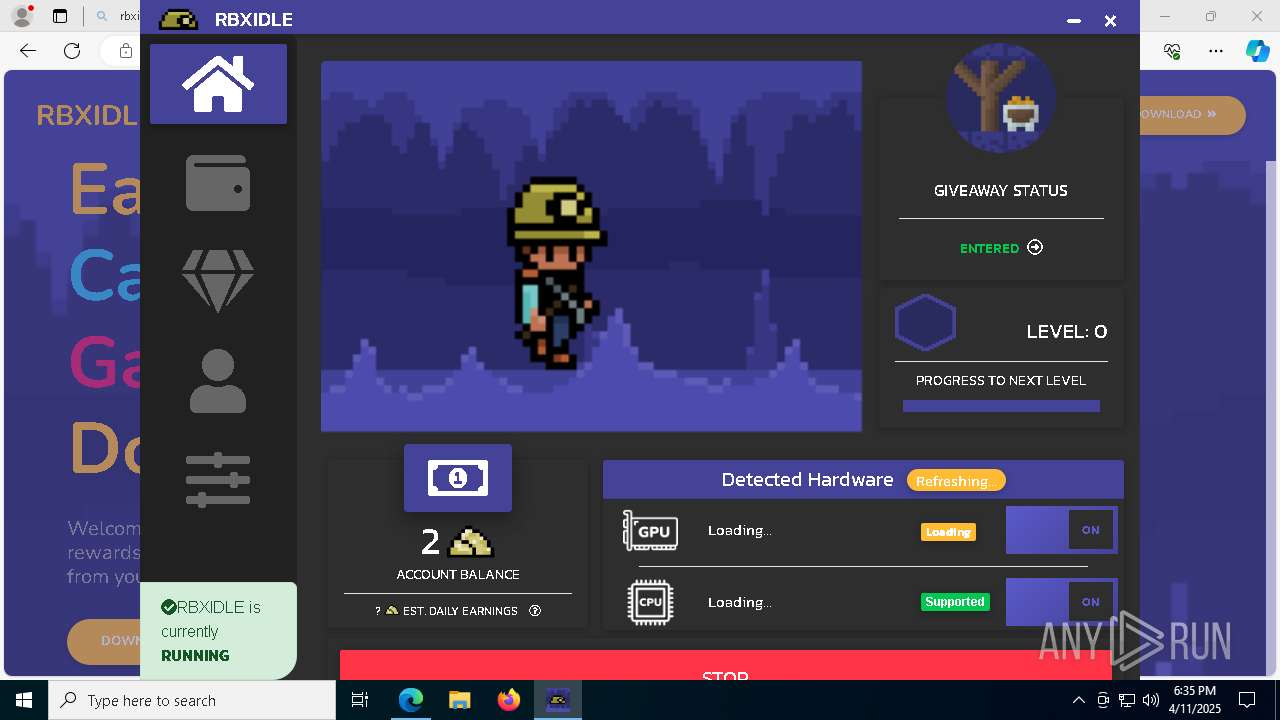
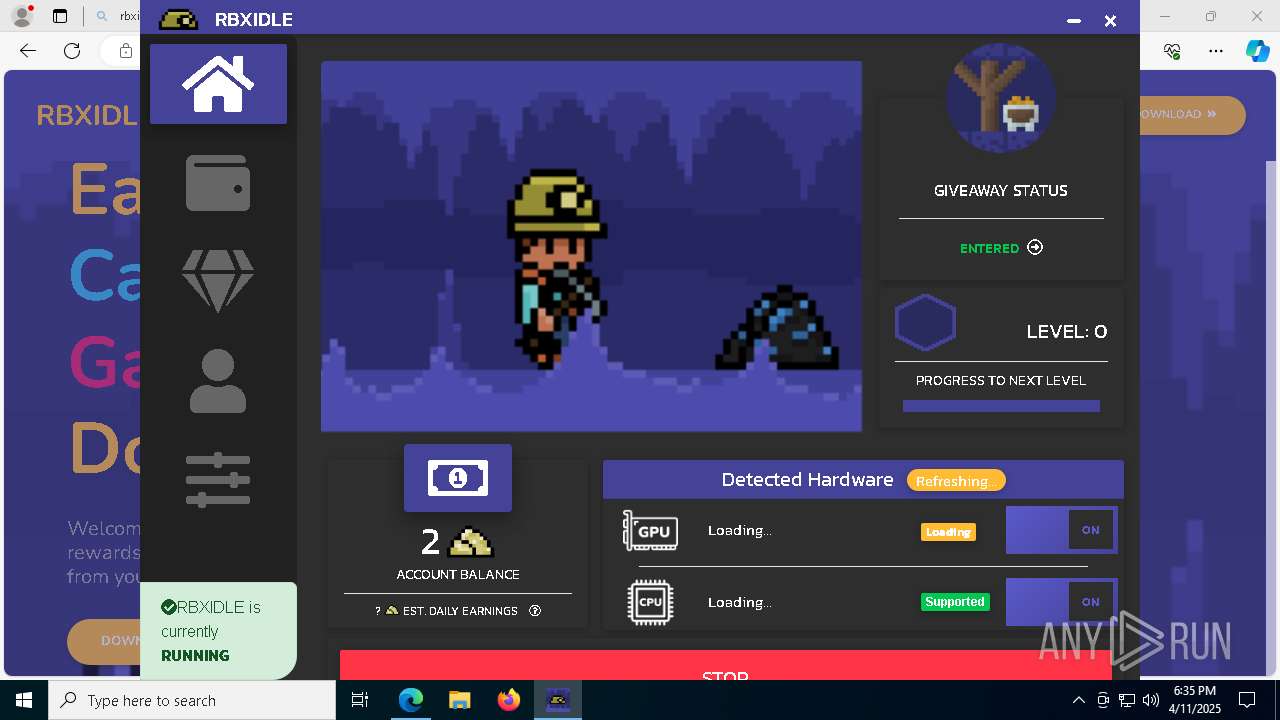
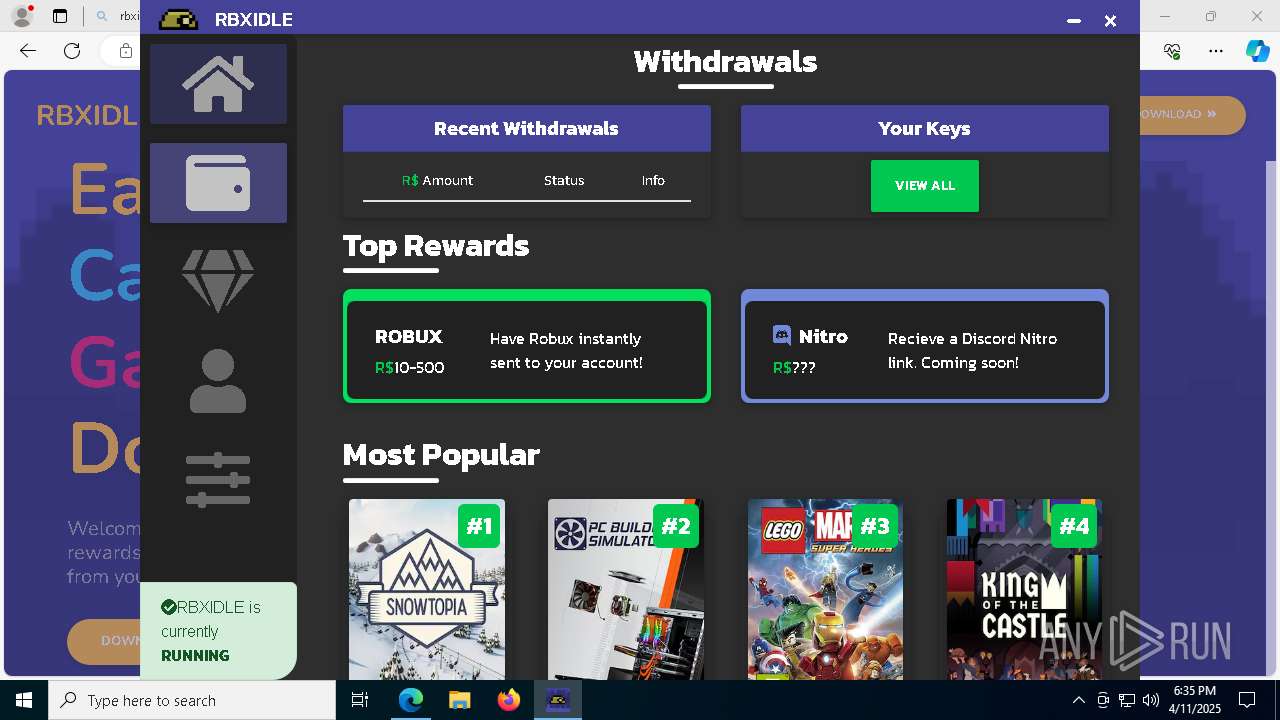
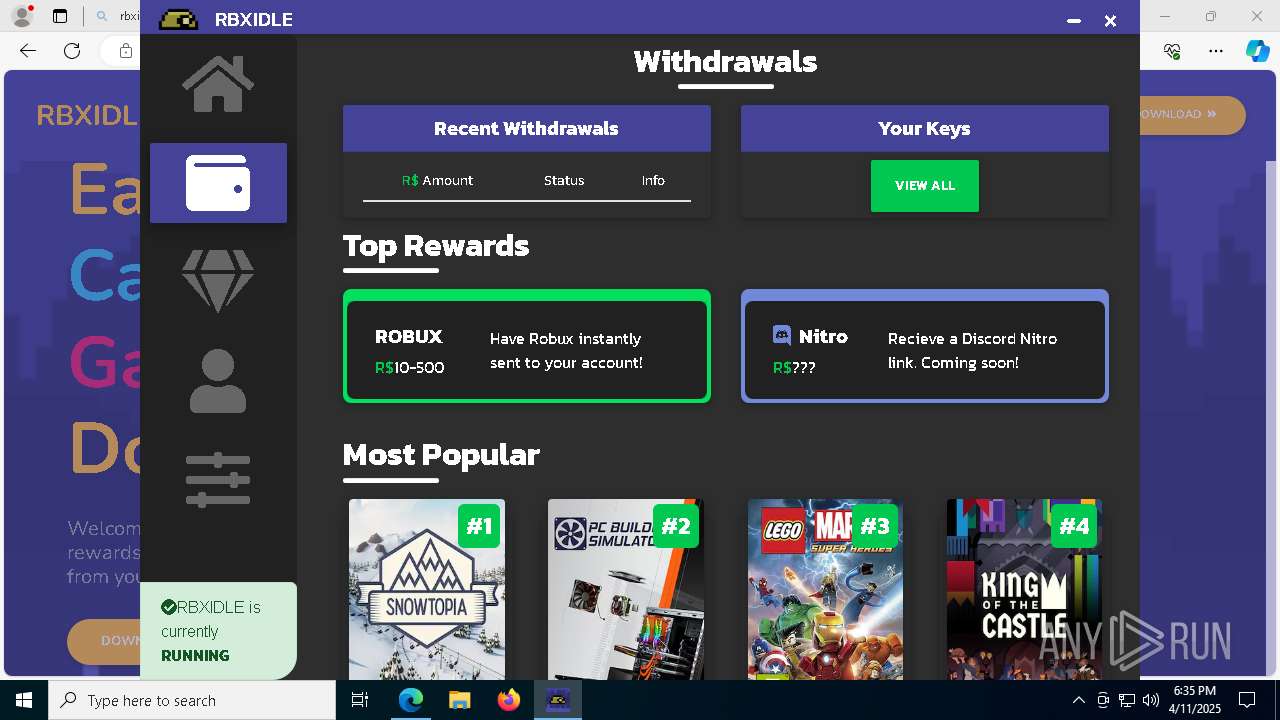
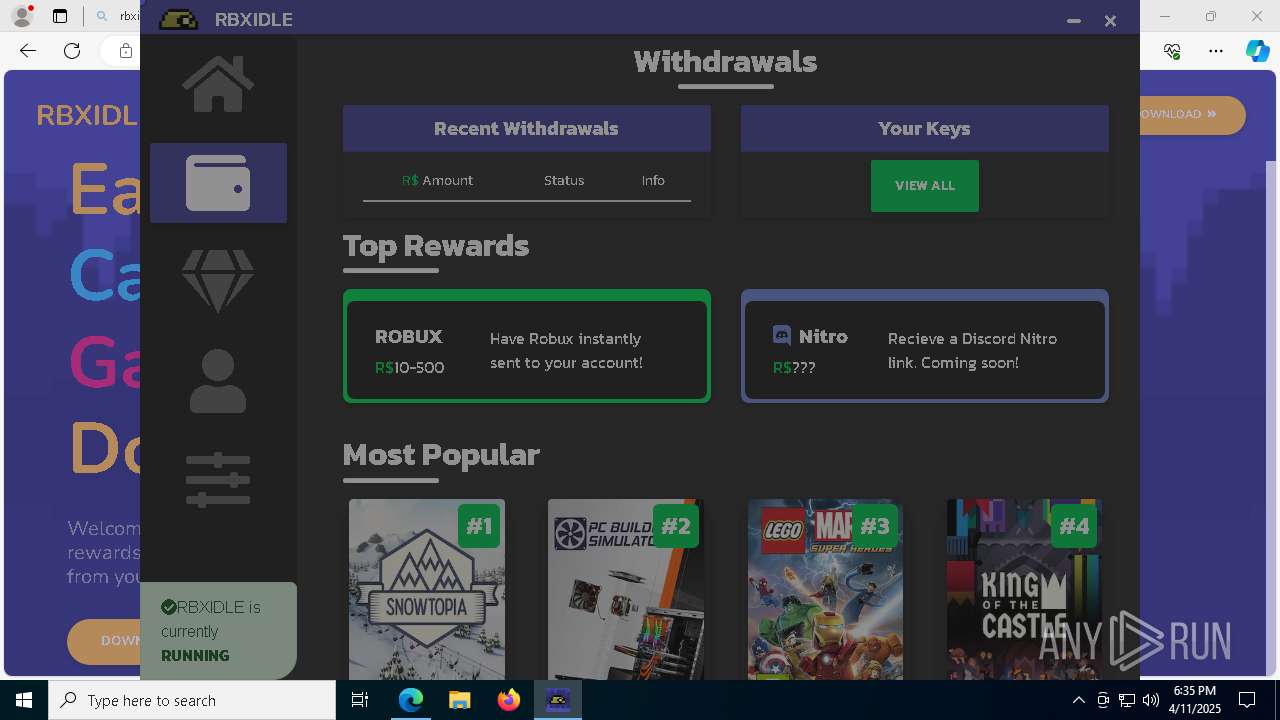
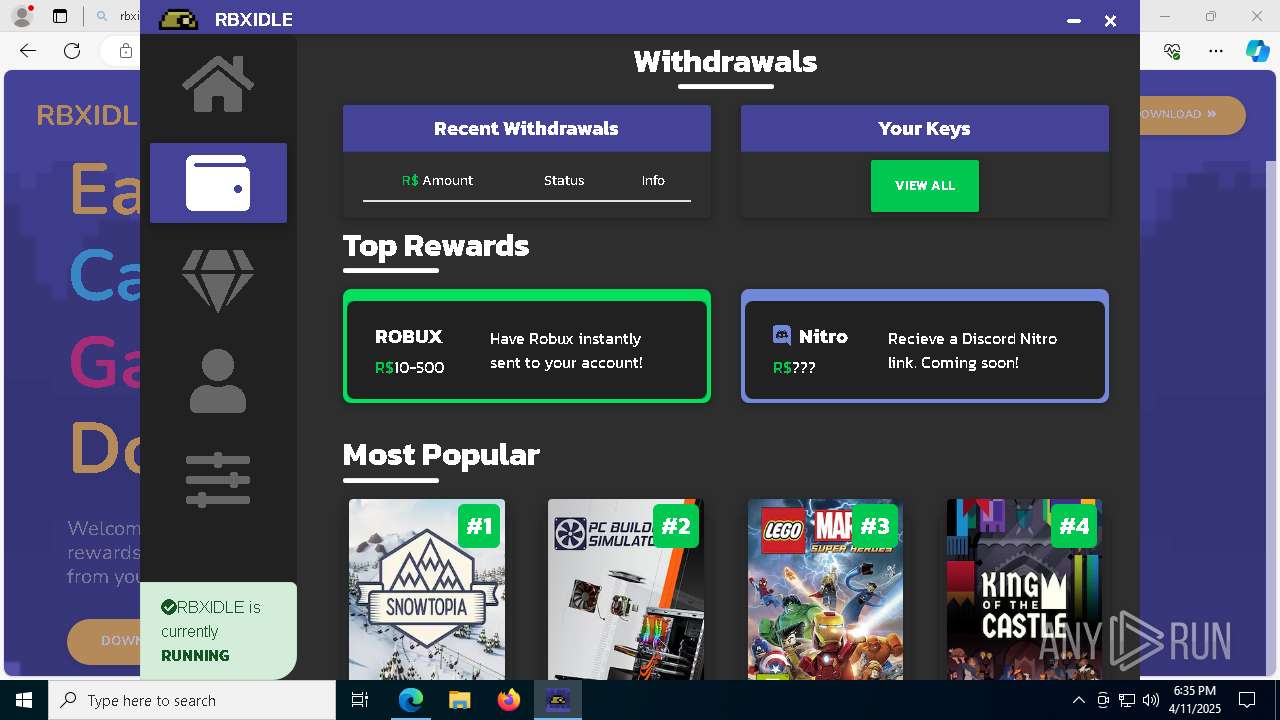
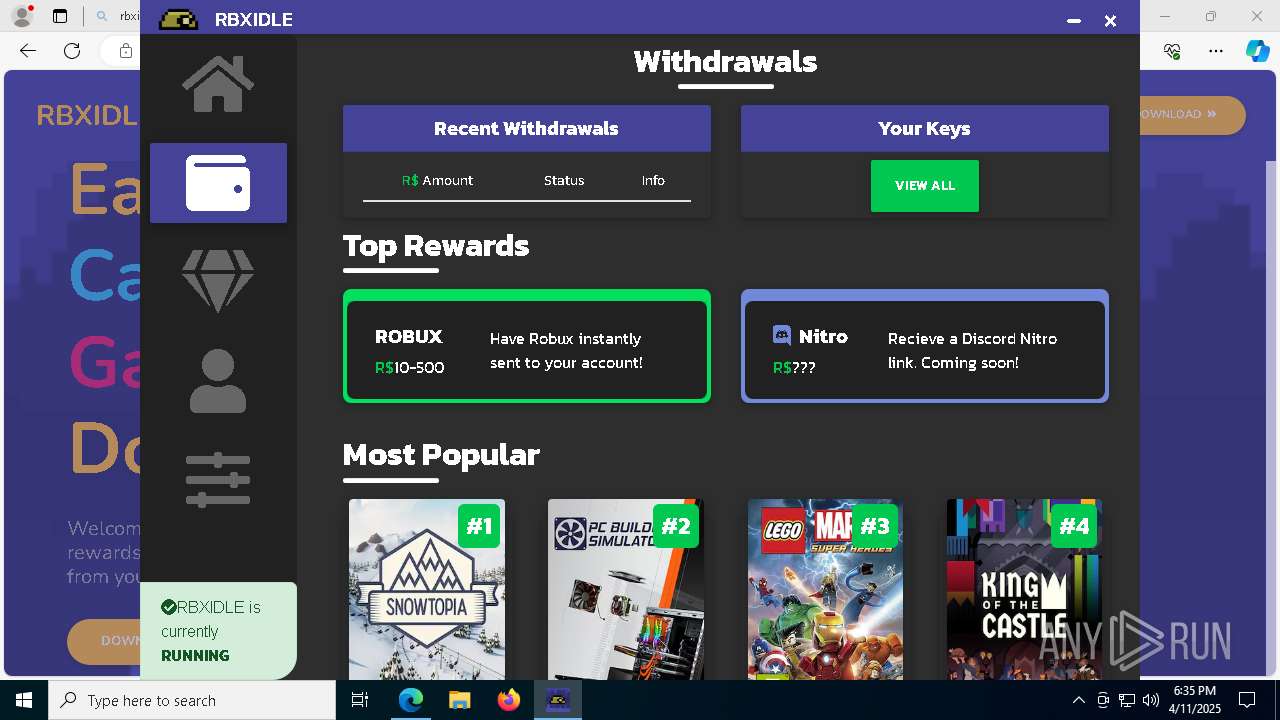
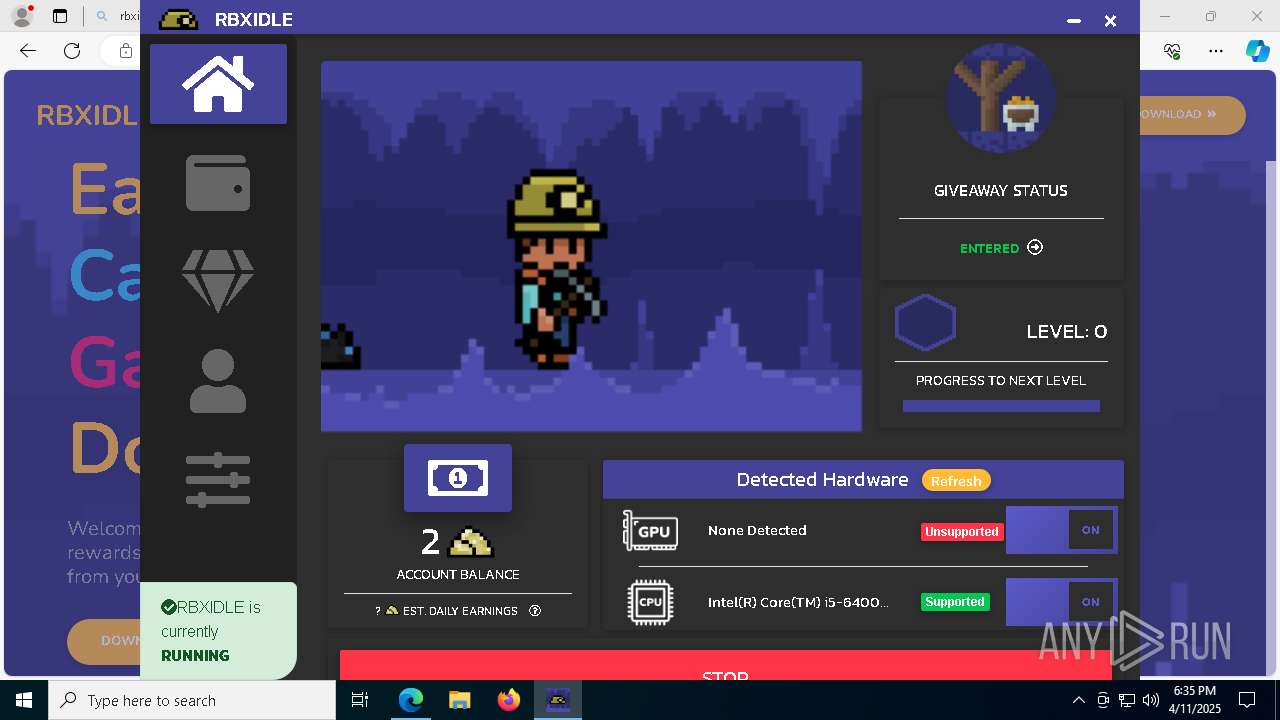
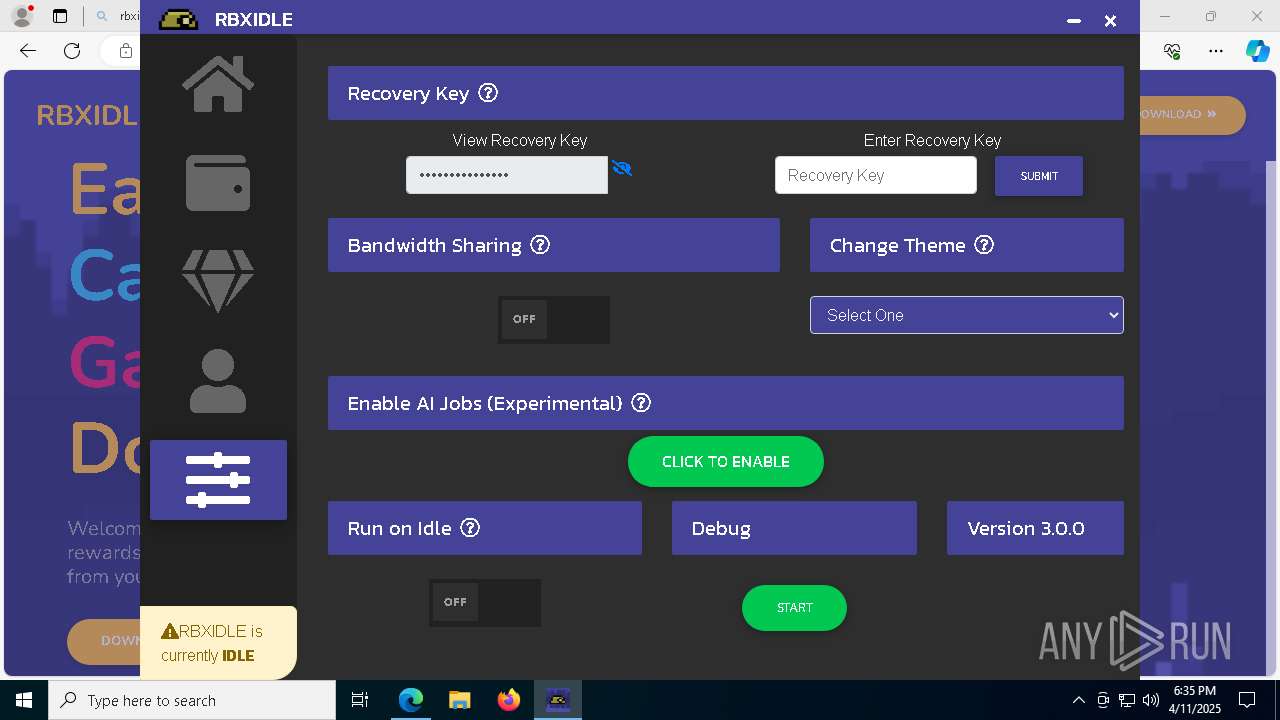
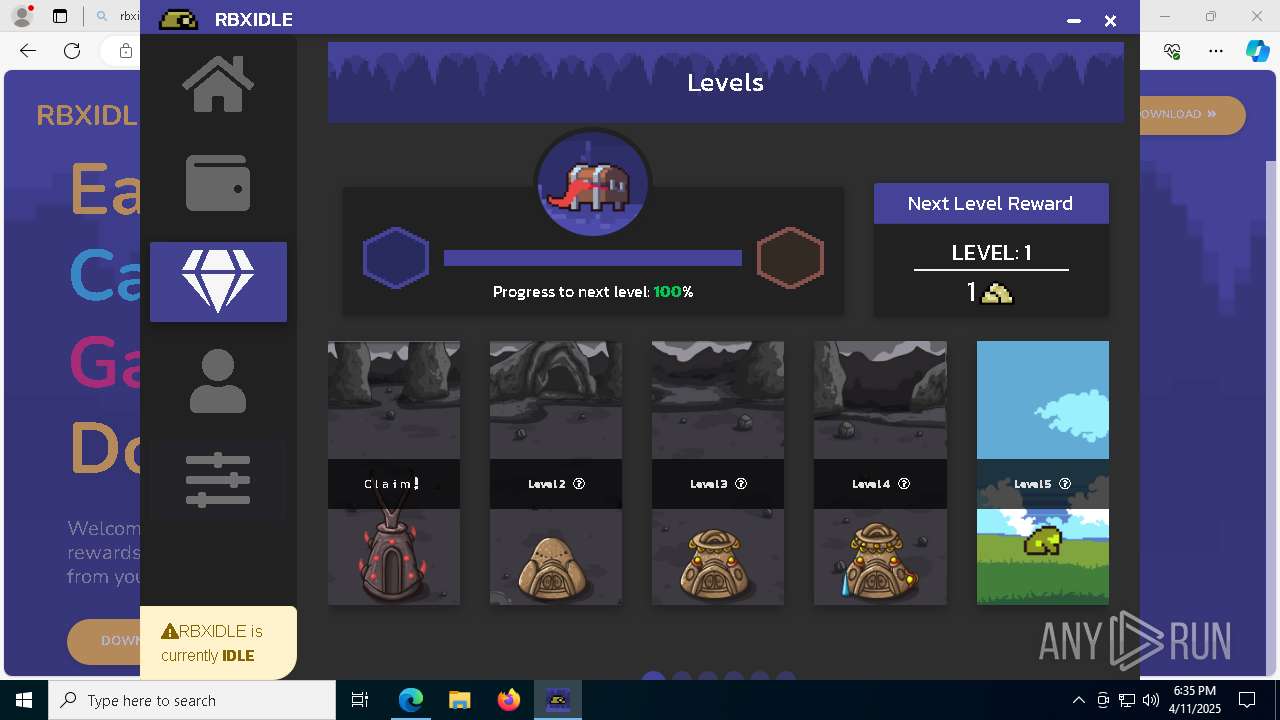
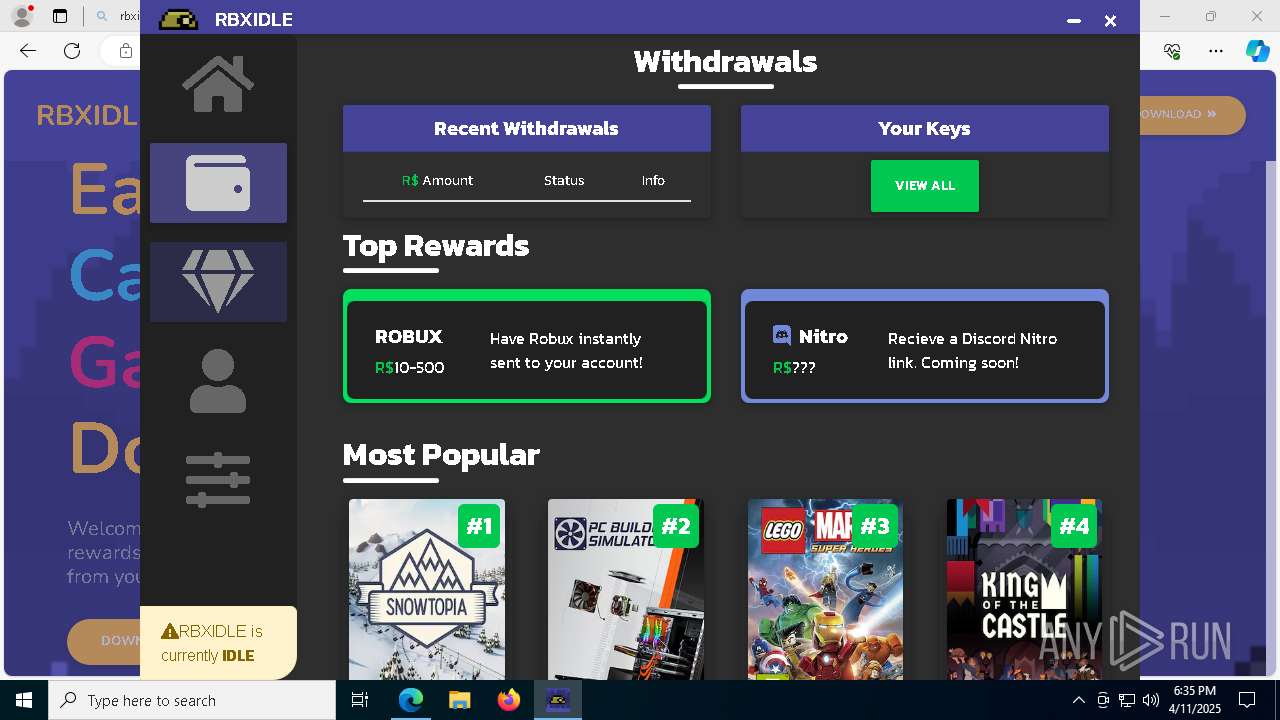
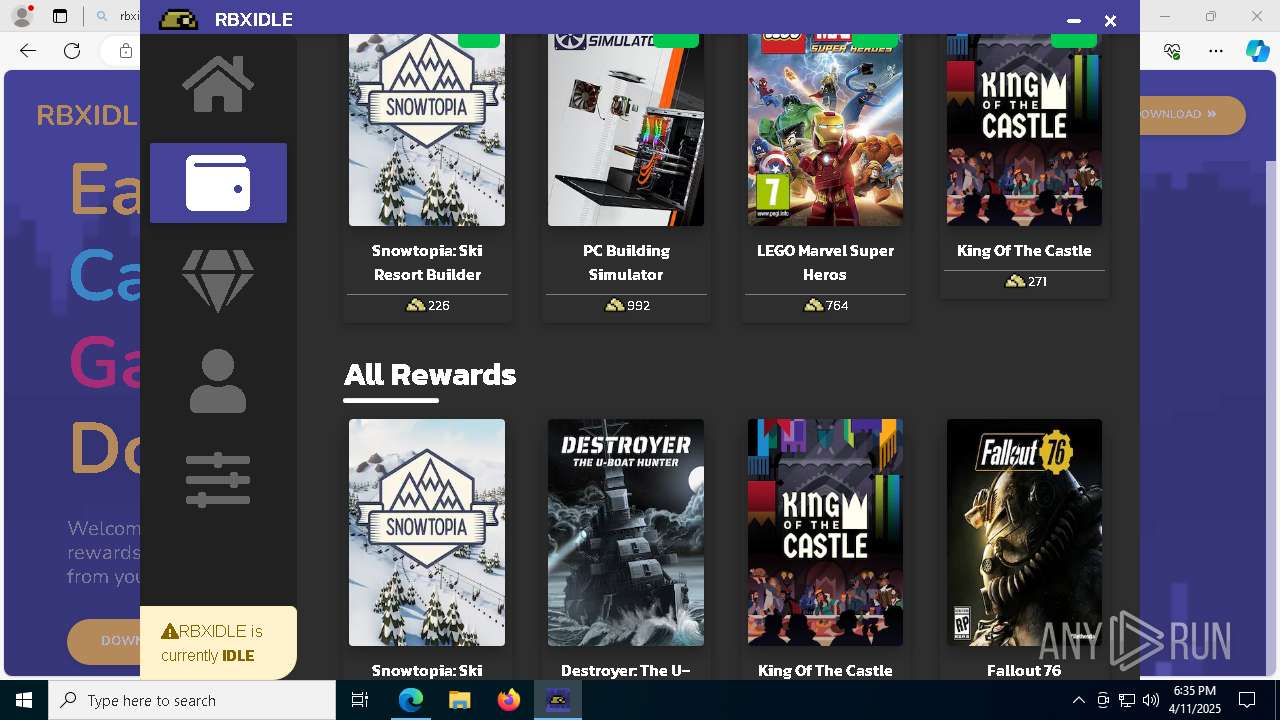
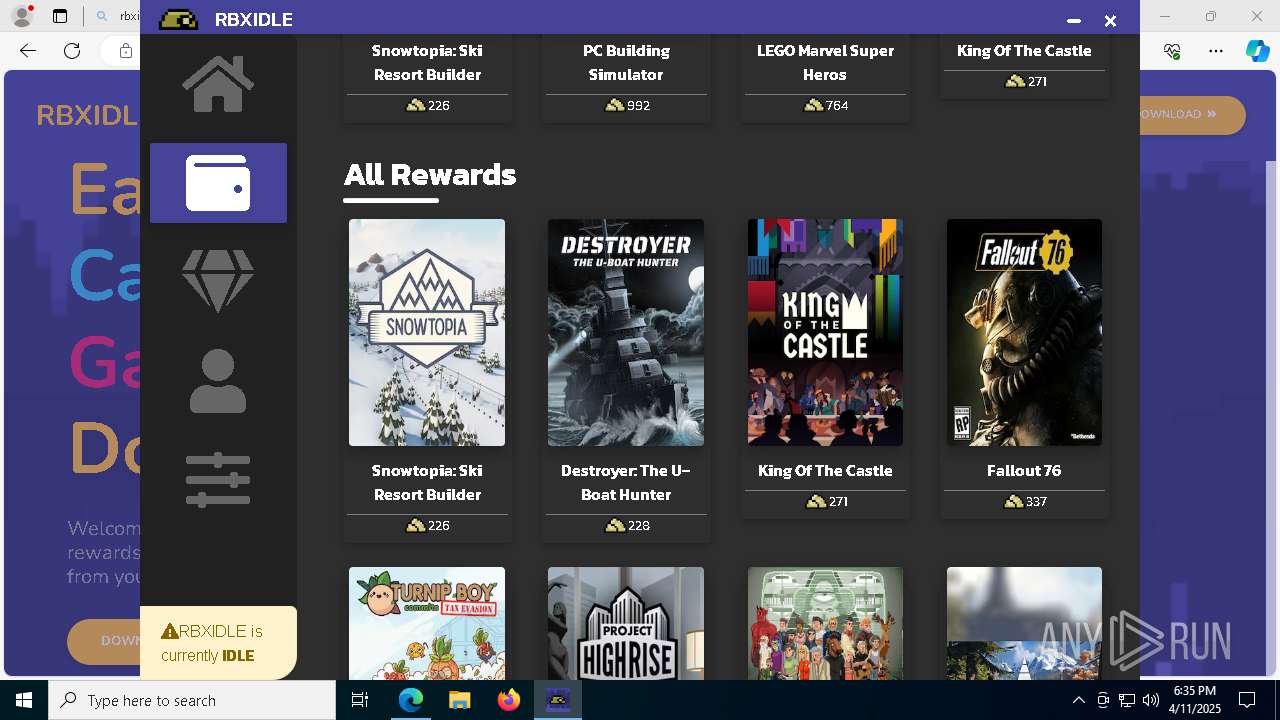
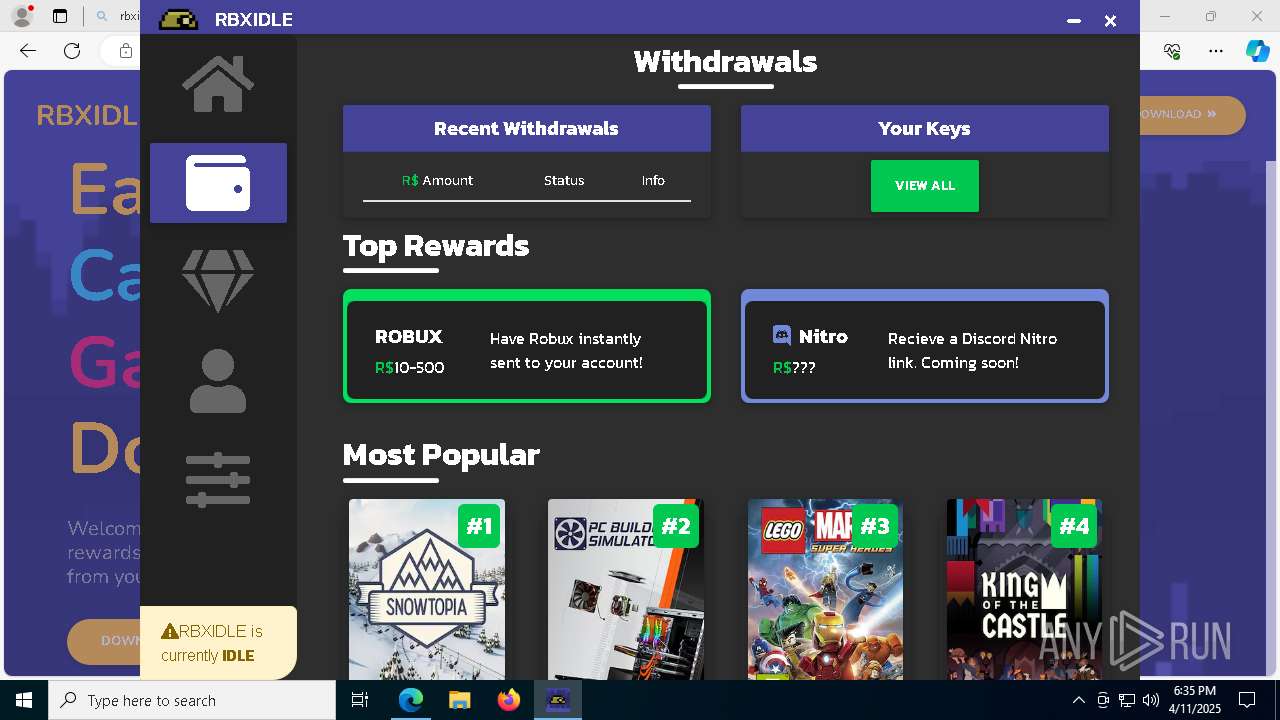
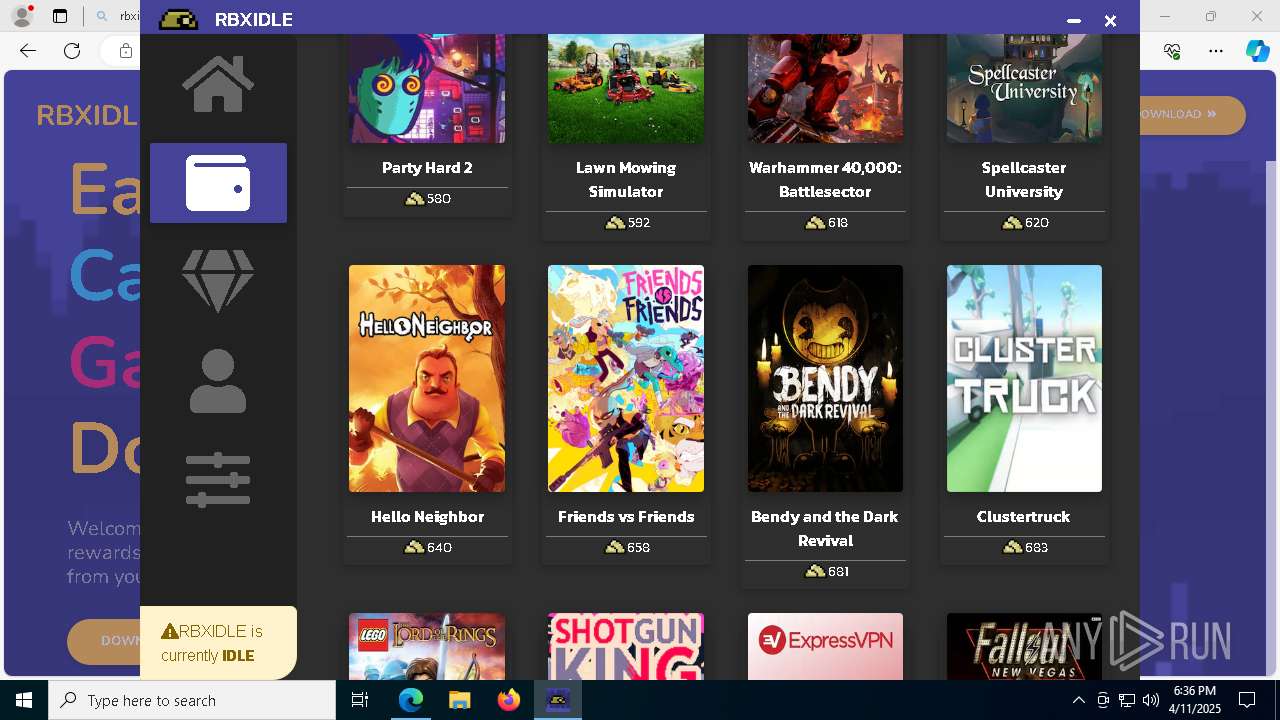
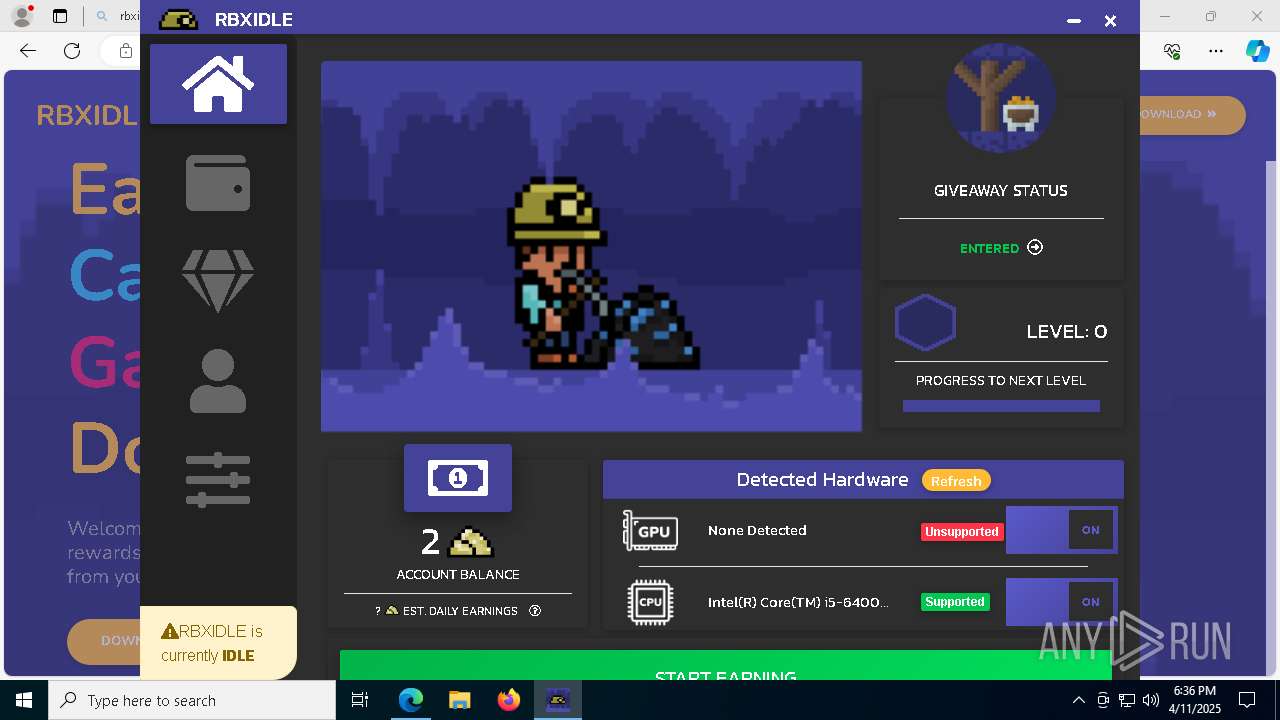
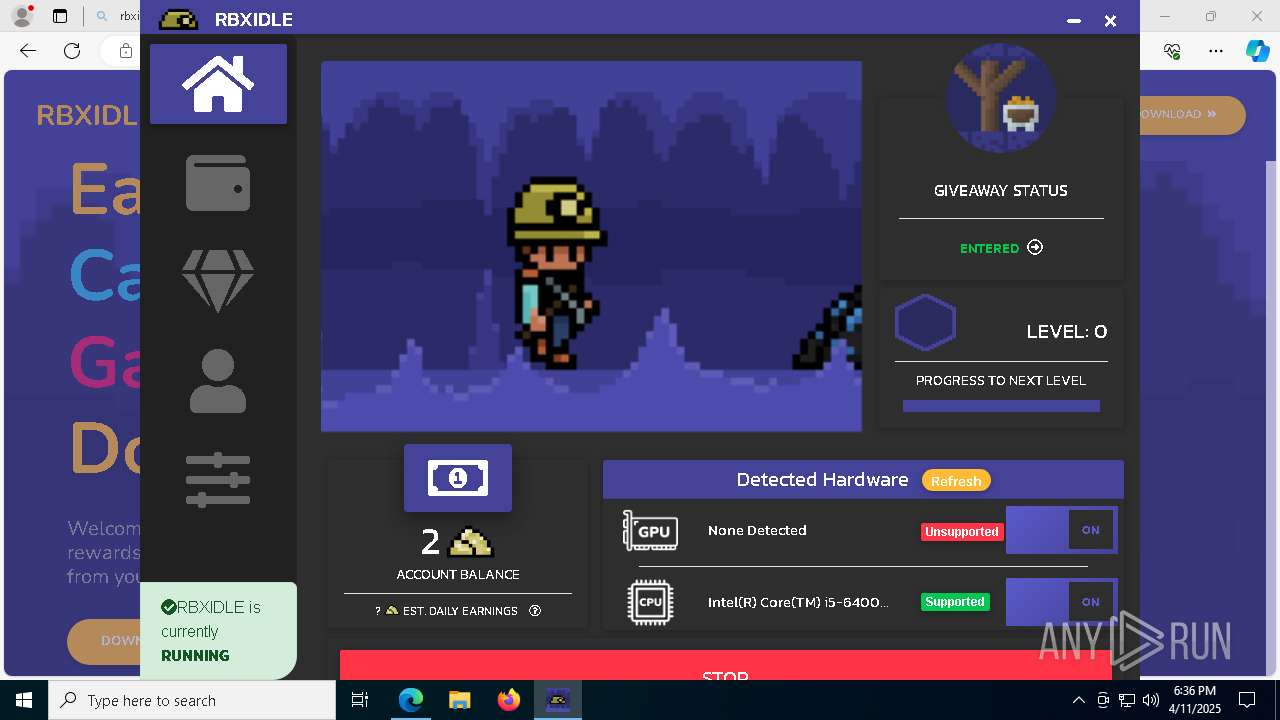
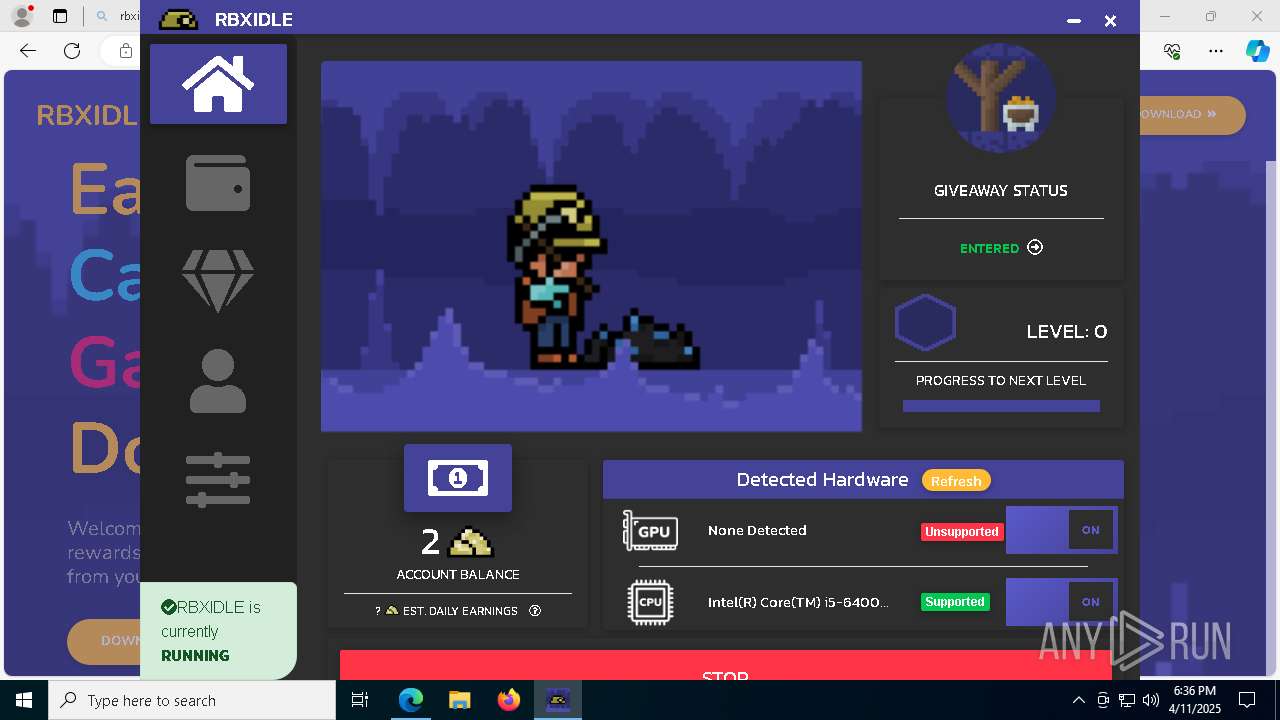
| URL: | www.rbxidle.com |
| Full analysis: | https://app.any.run/tasks/3ed7f383-2dda-4c9f-b171-0a3bcf76229a |
| Verdict: | Malicious activity |
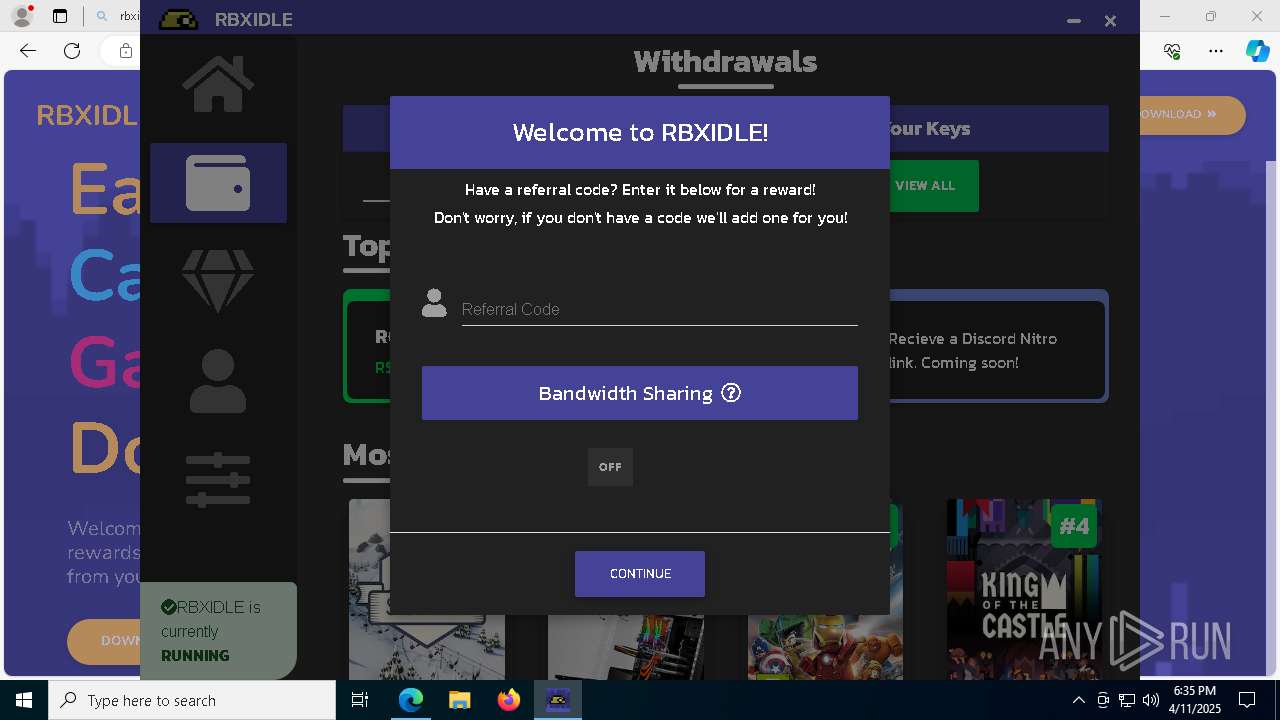
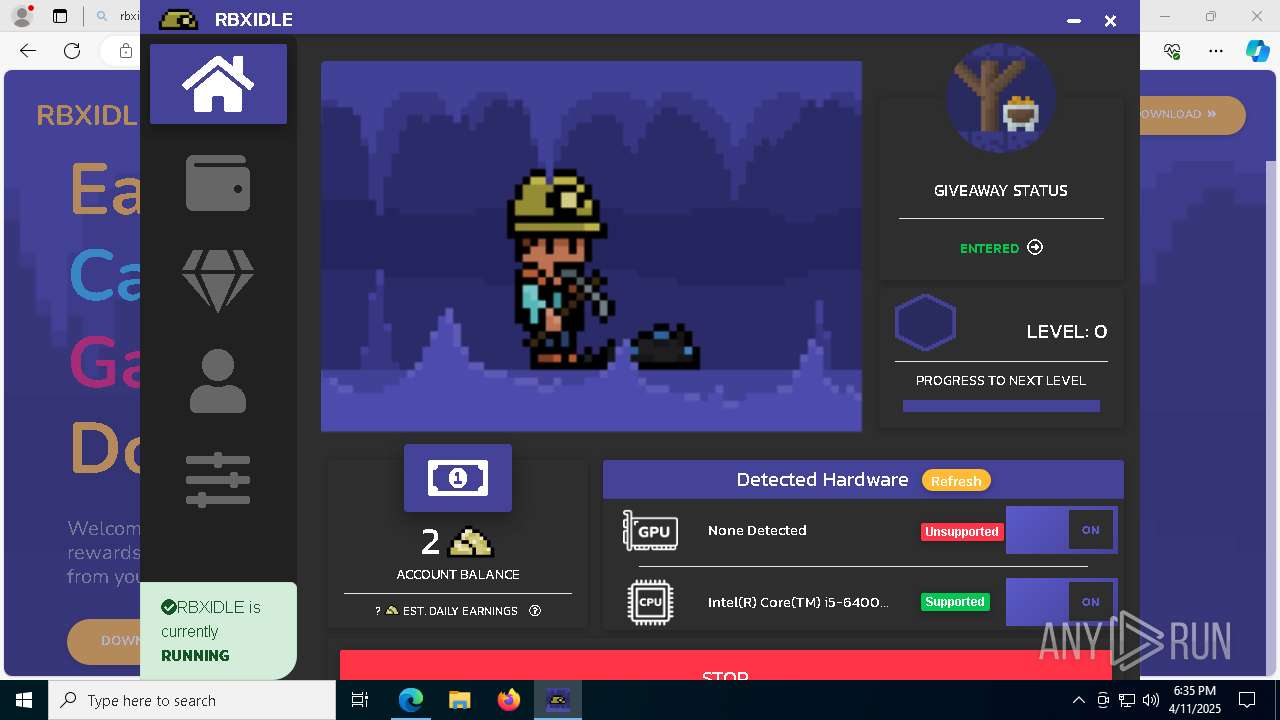
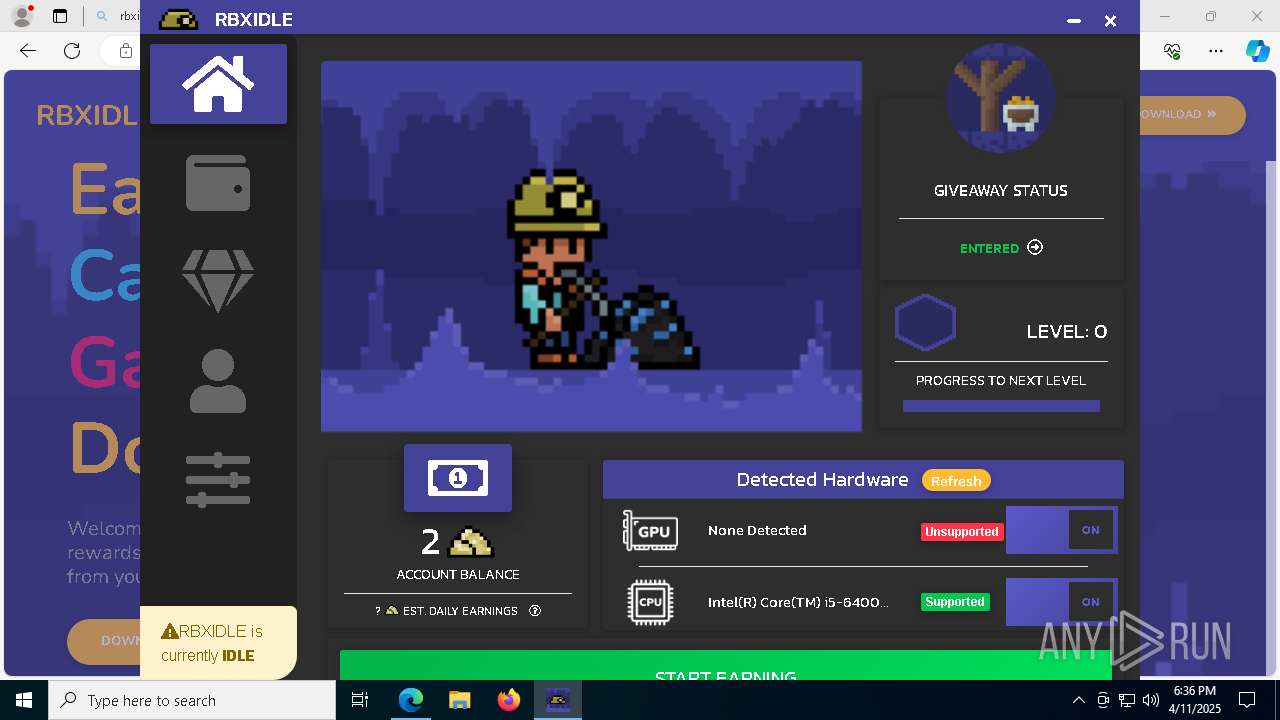
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
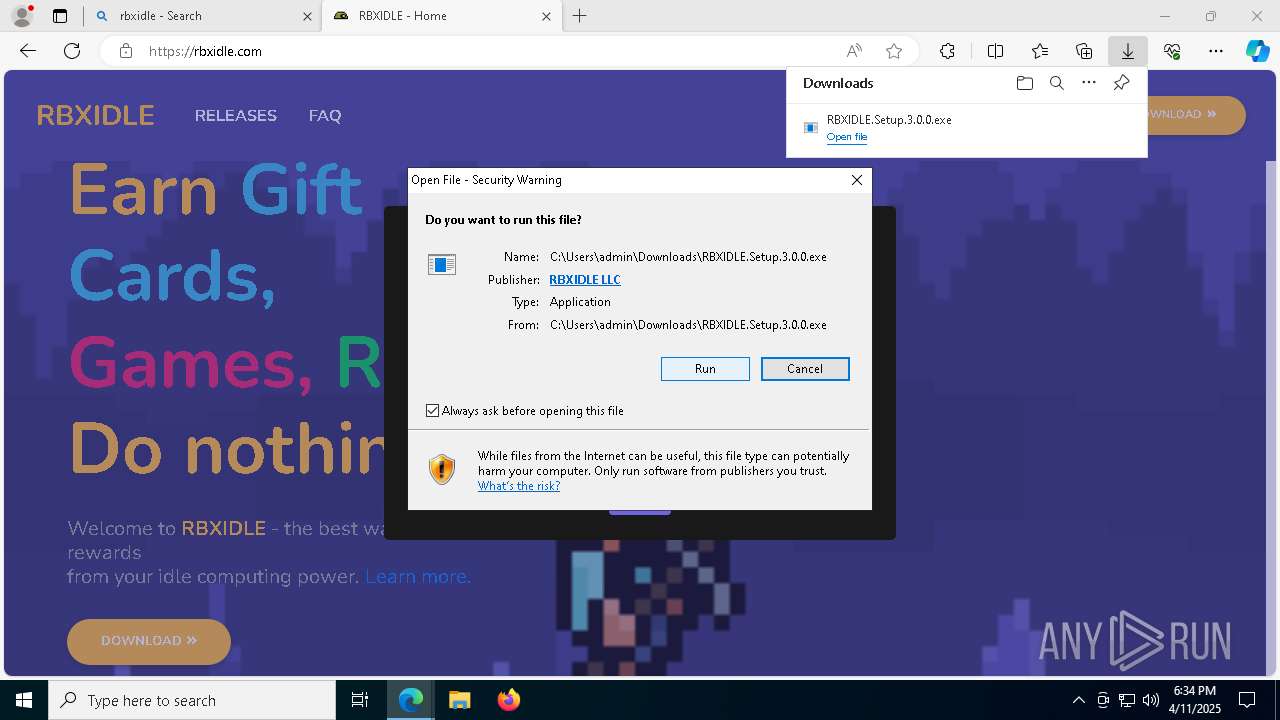
| Analysis date: | April 11, 2025, 18:33:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5F968D6EC30A7B54053960C700C6248D |
| SHA1: | CFC85E2FACF15E36E898AC734FEBD2CD13B05B51 |
| SHA256: | 82A815F7C65EE14D85062D96E4E1D2D8A28CDABCEB00EB9F962F83B9ACBC7CB9 |
| SSDEEP: | 3:E6JKI:UI |
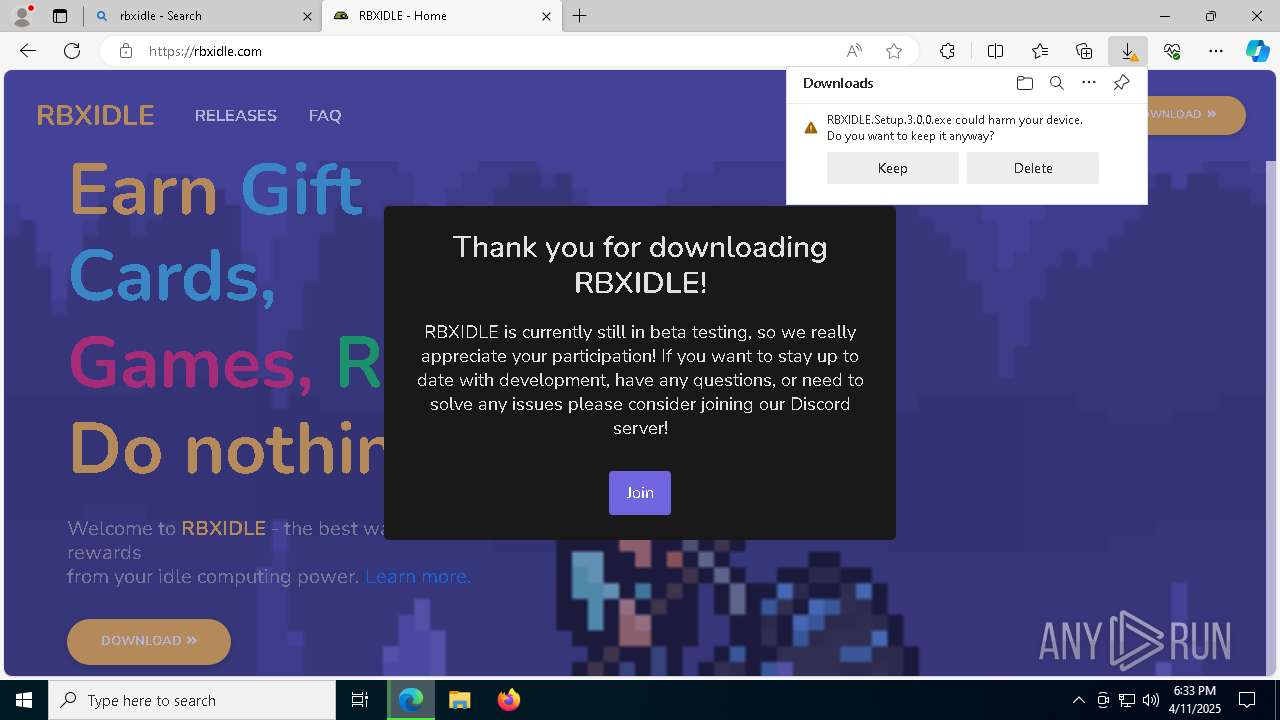
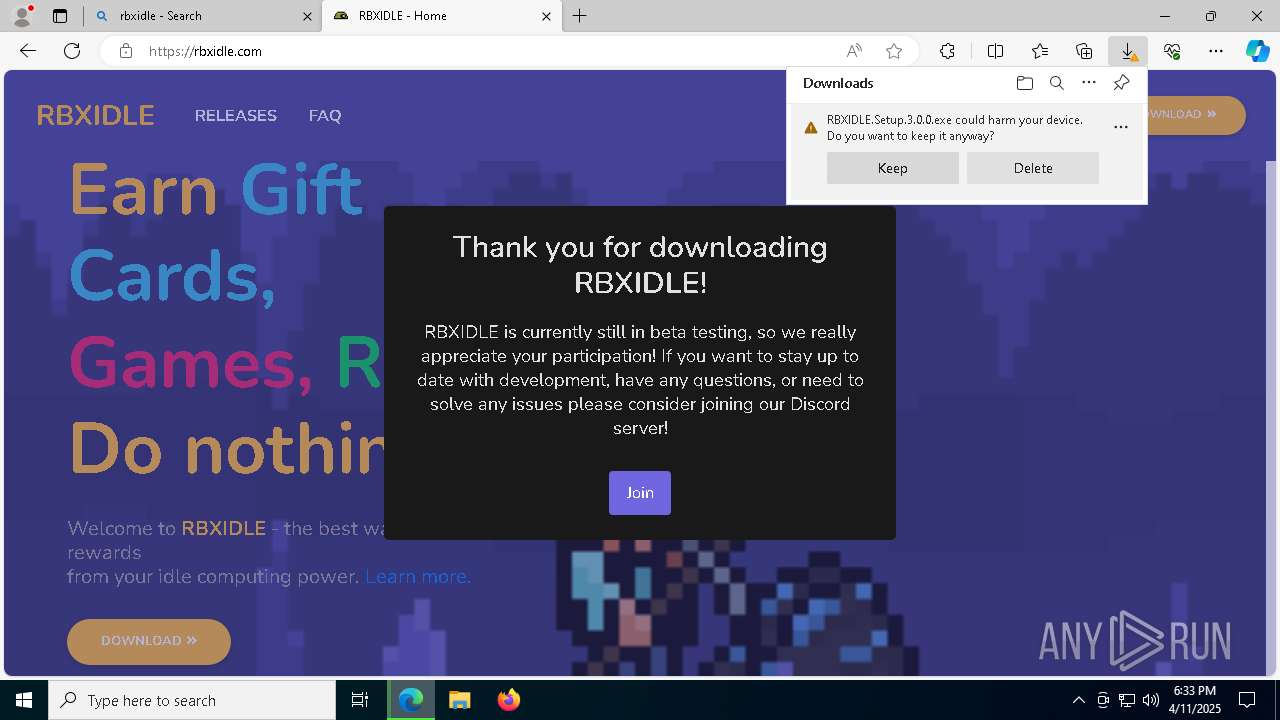
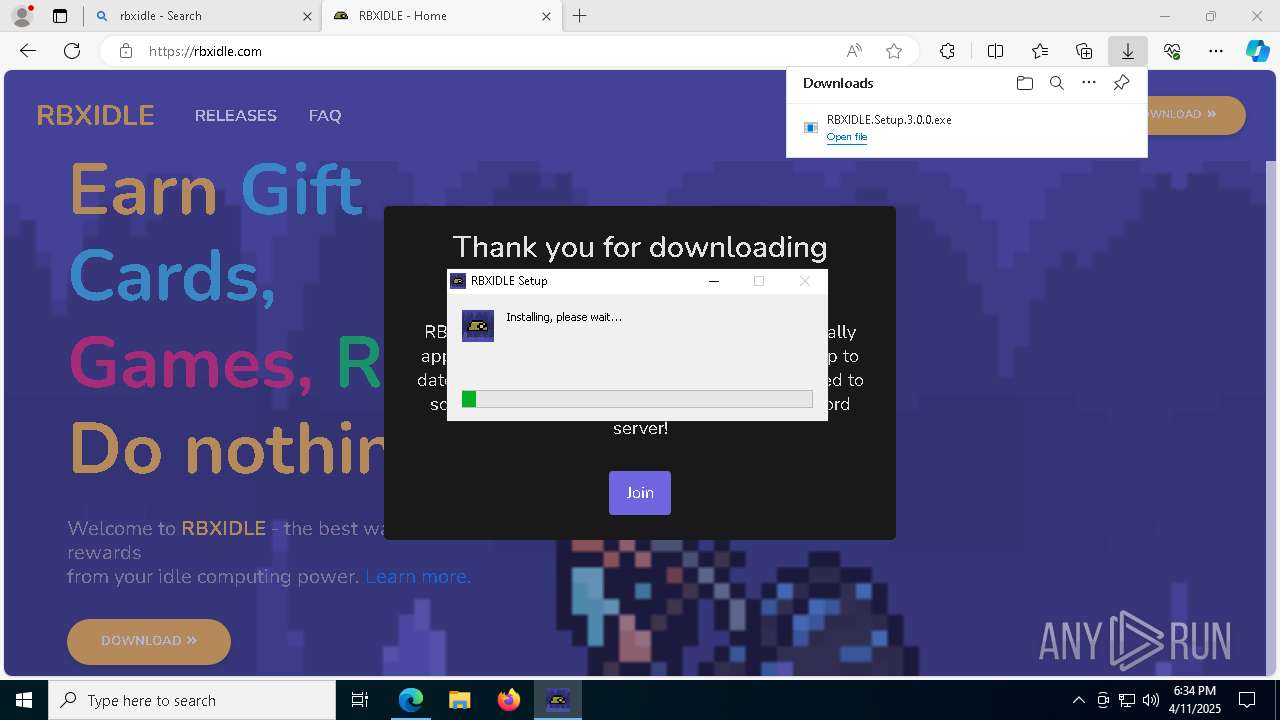
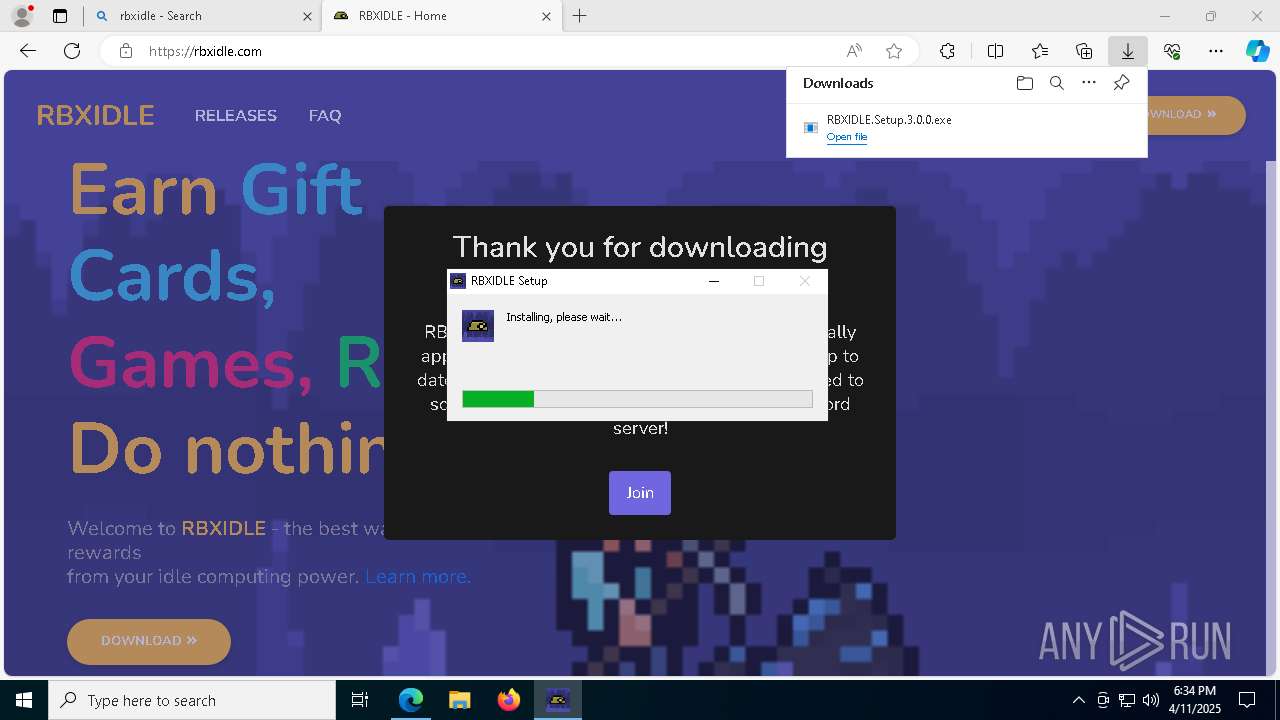
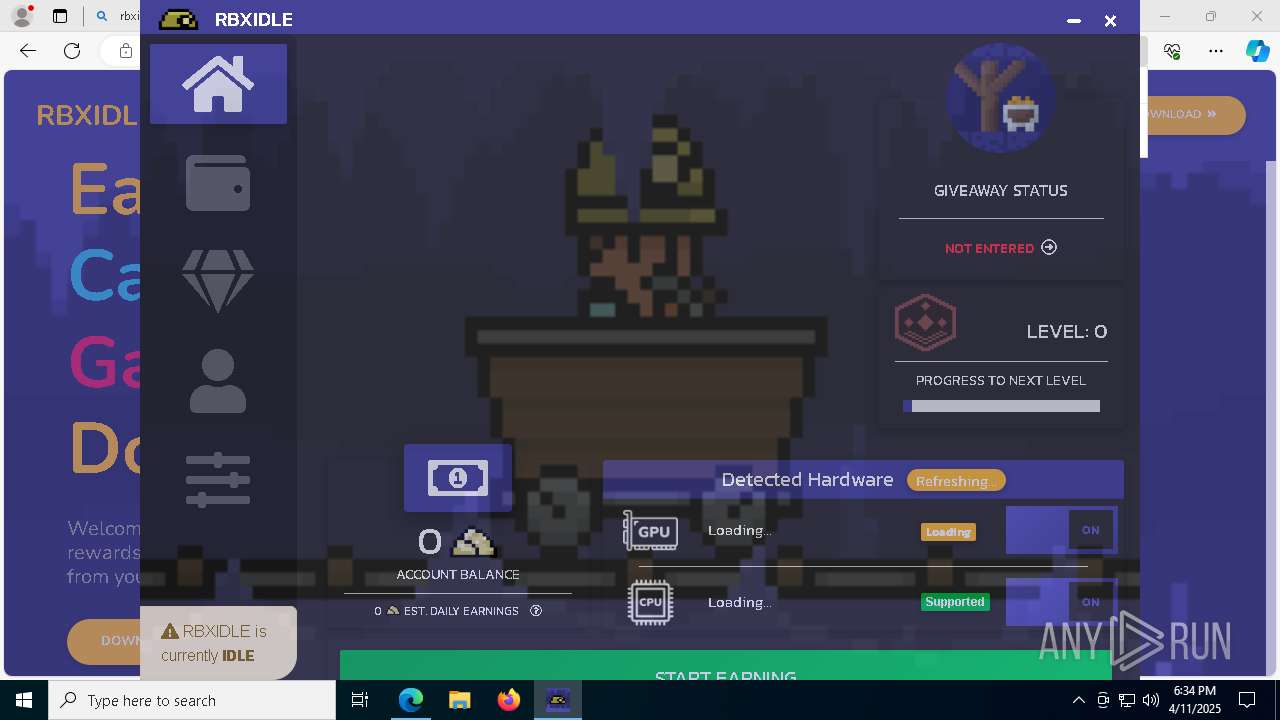
MALICIOUS
Vulnerable driver has been detected
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Changes powershell execution policy (Unrestricted)
- RBXIDLE.exe (PID: 6960)
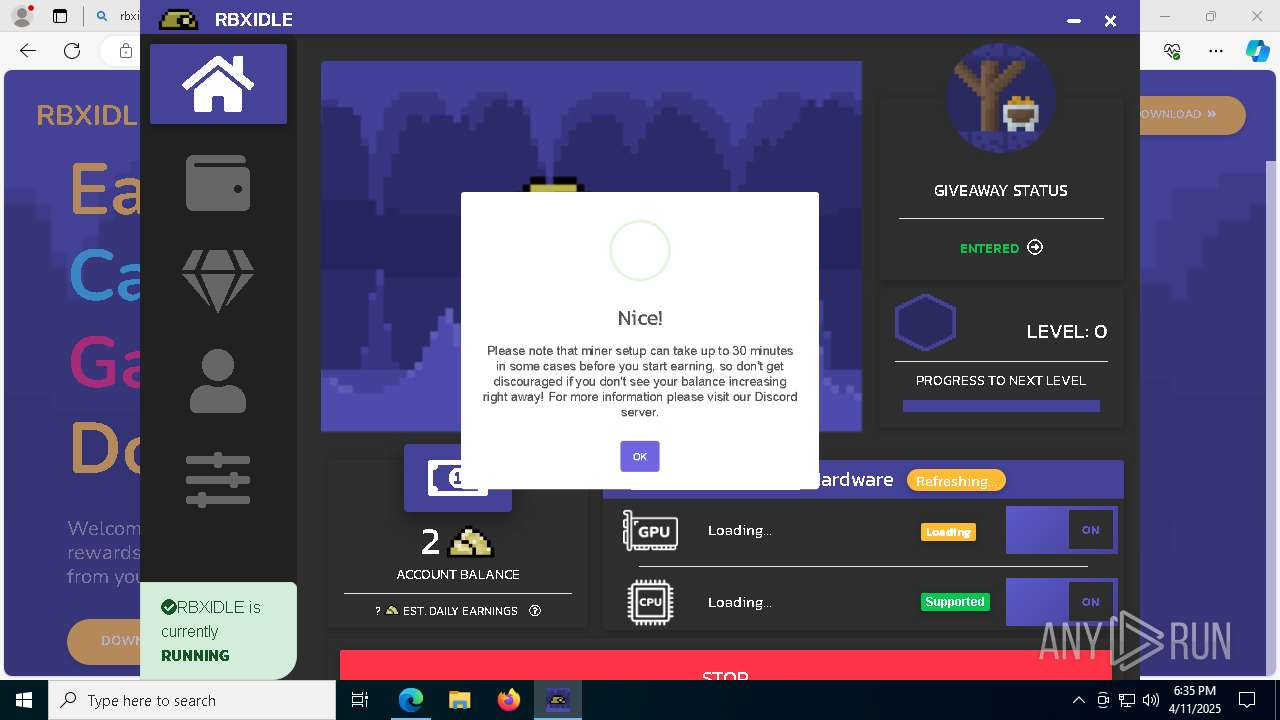
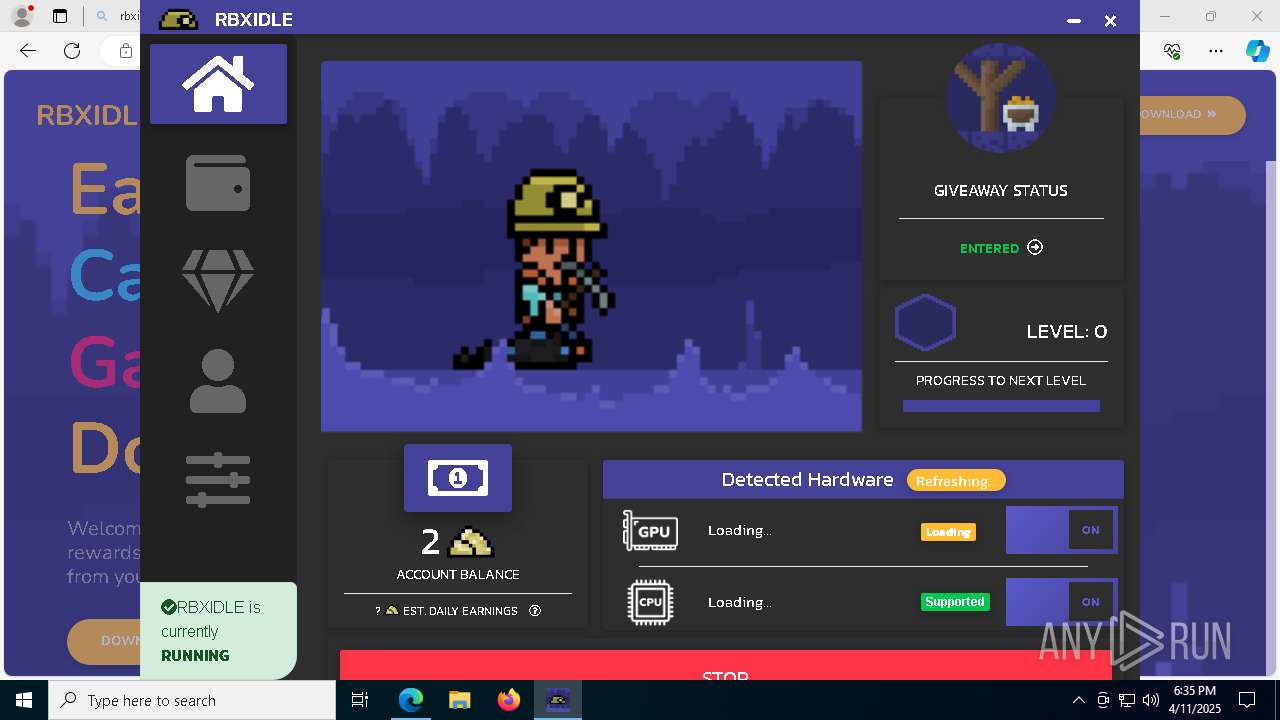
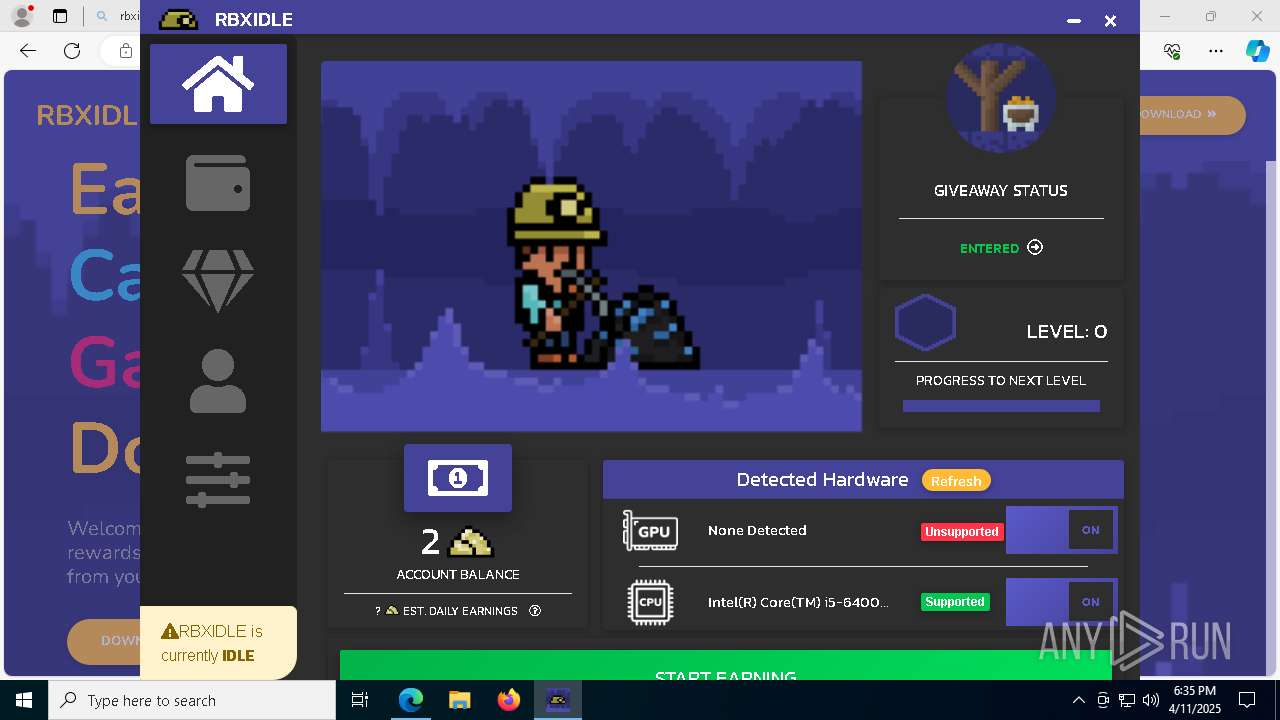
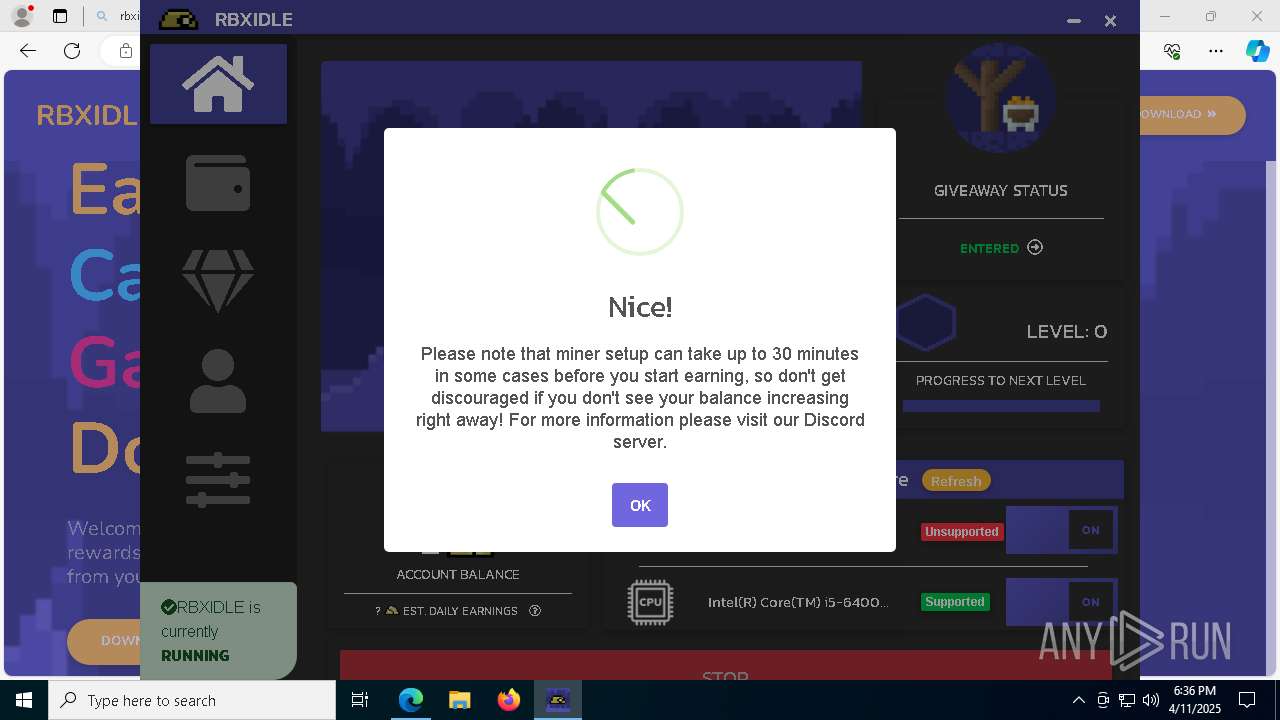
Looks like the application has launched a miner
- RBXIDLE.exe (PID: 6960)
Run PowerShell with an invisible window
- powershell.exe (PID: 5216)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 10180)
Bypass execution policy to execute commands
- powershell.exe (PID: 9896)
- powershell.exe (PID: 8436)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 10180)
Changes Windows Defender settings
- cmd.exe (PID: 10180)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
- xmrig.exe (PID: 2568)
- xmrig.exe (PID: 9096)
Connects to the CnC server
- xmrig.exe (PID: 2568)
- xmrig.exe (PID: 9096)
XMRig has been detected
- xmrig.exe (PID: 2568)
- xmrig.exe (PID: 9096)
SUSPICIOUS
The process creates files with name similar to system file names
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Executable content was dropped or overwritten
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
- RBXIDLE.exe (PID: 6960)
Process drops legitimate windows executable
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Reads security settings of Internet Explorer
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Creates a software uninstall entry
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Malware-specific behavior (creating "System.dll" in Temp)
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Drops 7-zip archiver for unpacking
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Starts CMD.EXE for commands execution
- RBXIDLE.exe (PID: 6960)
- powershell.exe (PID: 5216)
Starts application with an unusual extension
- cmd.exe (PID: 6252)
- cmd.exe (PID: 10180)
There is functionality for taking screenshot (YARA)
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Drops a system driver (possible attempt to evade defenses)
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Application launched itself
- RBXIDLE.exe (PID: 6960)
Adds/modifies Windows certificates
- RBXIDLE.exe (PID: 6960)
The process bypasses the loading of PowerShell profile settings
- RBXIDLE.exe (PID: 6960)
Executing commands from a ".bat" file
- RBXIDLE.exe (PID: 6960)
- powershell.exe (PID: 5216)
Starts process via Powershell
- powershell.exe (PID: 5216)
The process hides Powershell's copyright startup banner
- RBXIDLE.exe (PID: 6960)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7144)
- RBXIDLE.exe (PID: 6960)
- cmd.exe (PID: 10180)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 10180)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
- xmrig.exe (PID: 2568)
- xmrig.exe (PID: 9096)
Connects to unusual port
- xmrig.exe (PID: 2568)
- xmrig.exe (PID: 9096)
Creates/Modifies COM task schedule object
- dxdiag.exe (PID: 904)
- dxdiag.exe (PID: 8828)
The process deletes folder without confirmation
- RBXIDLE.exe (PID: 6960)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2268)
- cmd.exe (PID: 9404)
- cmd.exe (PID: 8720)
INFO
Checks supported languages
- identity_helper.exe (PID: 8032)
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
- chcp.com (PID: 2040)
- RBXIDLE.exe (PID: 4784)
- RBXIDLE.exe (PID: 7272)
- RBXIDLE.exe (PID: 8088)
- RBXIDLE.exe (PID: 6960)
- RBXIDLE.exe (PID: 5384)
- xmrig.exe (PID: 2568)
- chcp.com (PID: 5796)
- xmrig.exe (PID: 9096)
Reads Environment values
- identity_helper.exe (PID: 8032)
- RBXIDLE.exe (PID: 6960)
Application launched itself
- msedge.exe (PID: 7392)
Reads the computer name
- identity_helper.exe (PID: 8032)
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
- RBXIDLE.exe (PID: 4784)
- RBXIDLE.exe (PID: 6960)
- xmrig.exe (PID: 2568)
- RBXIDLE.exe (PID: 8088)
- xmrig.exe (PID: 9096)
Executable content was dropped or overwritten
- msedge.exe (PID: 7392)
- msedge.exe (PID: 9616)
Create files in a temporary directory
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
- RBXIDLE.exe (PID: 6960)
The sample compiled with english language support
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
- msedge.exe (PID: 9616)
Creates files or folders in the user directory
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
- RBXIDLE.exe (PID: 4784)
- RBXIDLE.exe (PID: 6960)
- dxdiag.exe (PID: 904)
- dxdiag.exe (PID: 8828)
Reads the software policy settings
- slui.exe (PID: 8000)
- RBXIDLE.exe (PID: 6960)
- dxdiag.exe (PID: 8828)
- dxdiag.exe (PID: 904)
- slui.exe (PID: 2288)
The sample compiled with japanese language support
- RBXIDLE.Setup.3.0.0.exe (PID: 1244)
Manual execution by a user
- RBXIDLE.exe (PID: 4112)
- RBXIDLE.exe (PID: 6960)
Changes the display of characters in the console
- cmd.exe (PID: 6252)
- cmd.exe (PID: 10180)
Autorun file from Downloads
- msedge.exe (PID: 5744)
Checks proxy server information
- RBXIDLE.exe (PID: 6960)
- dxdiag.exe (PID: 904)
- slui.exe (PID: 2288)
Reads product name
- RBXIDLE.exe (PID: 6960)
Process checks computer location settings
- RBXIDLE.exe (PID: 7272)
- RBXIDLE.exe (PID: 6960)
- RBXIDLE.exe (PID: 5384)
Reads the machine GUID from the registry
- RBXIDLE.exe (PID: 6960)
Reads security settings of Internet Explorer
- explorer.exe (PID: 8208)
- explorer.exe (PID: 8244)
- dxdiag.exe (PID: 904)
- dxdiag.exe (PID: 8828)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8848)
- powershell.exe (PID: 8540)
- powershell.exe (PID: 8816)
- powershell.exe (PID: 8456)
- powershell.exe (PID: 9896)
- powershell.exe (PID: 8436)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 9896)
- powershell.exe (PID: 8436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
273
Monitored processes
132
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7364 --field-trial-handle=2364,i,7899847670317802309,13261009564255719901,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | dxdiag /x C:\Users\admin\AppData\Roaming\RBXIDLE\dx.xml | C:\Windows\System32\dxdiag.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
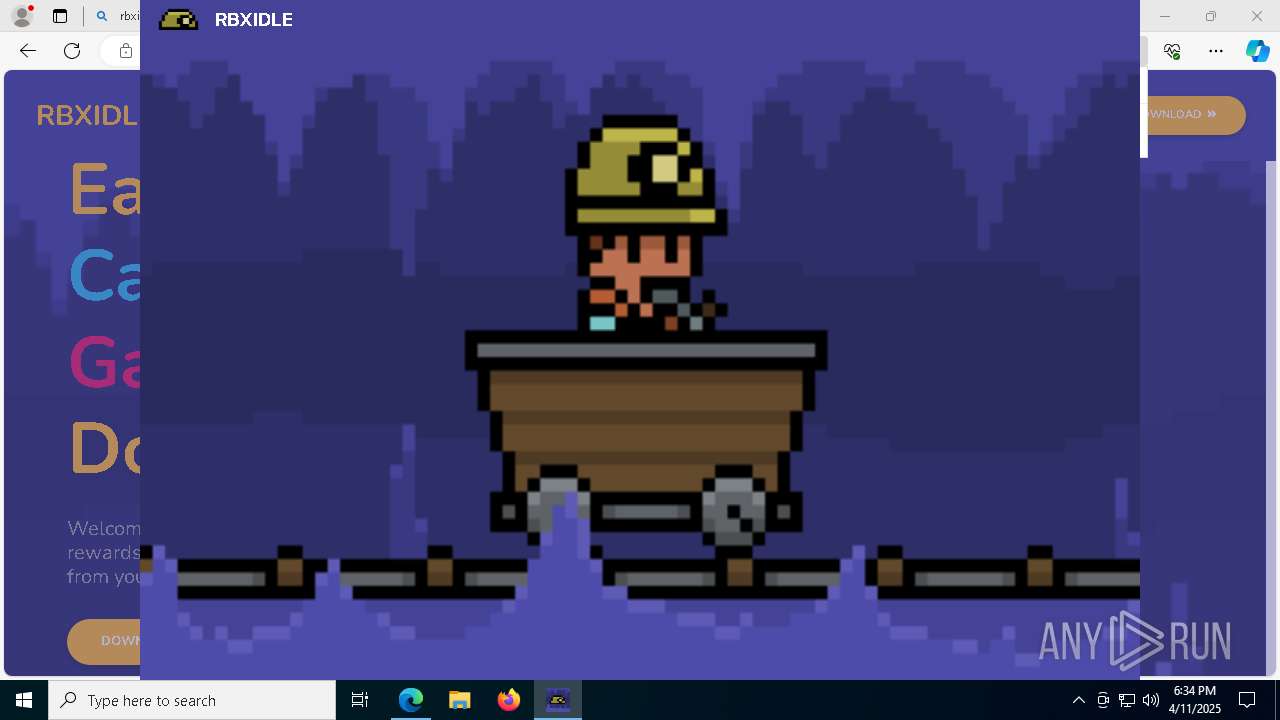
| 1244 | "C:\Users\admin\Downloads\RBXIDLE.Setup.3.0.0.exe" | C:\Users\admin\Downloads\RBXIDLE.Setup.3.0.0.exe | msedge.exe | ||||||||||||
User: admin Company: RBXIDLE LLC Integrity Level: MEDIUM Description: Earn rewards using PC idle power. Exit code: 0 Version: 3.0.0 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6040 --field-trial-handle=2364,i,7899847670317802309,13261009564255719901,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=6316 --field-trial-handle=2364,i,7899847670317802309,13261009564255719901,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | chcp | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3680 --field-trial-handle=2364,i,7899847670317802309,13261009564255719901,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7528 --field-trial-handle=2364,i,7899847670317802309,13261009564255719901,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
121 620
Read events
121 339
Write events
220
Delete events
61
Modification events
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DD8BF0381B912F00 | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0B62F9381B912F00 | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197350 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D8BF63C4-6D6D-4035-B240-87FF986BE57B} | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197350 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EDA91F3F-0D89-48B5-8CCA-DD18B0853BF0} | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197350 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E79D0C37-6F03-4EE1-9202-836028550270} | |||
| (PID) Process: | (7392) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1C5A65391B912F00 | |||
Executable files
250
Suspicious files
524
Text files
214
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b392.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b392.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b392.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b3a2.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b3a2.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
165
DNS requests
152
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.155:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744950980&P2=404&P3=2&P4=Coq4nQ99jHr5mxjsYbfmBsKRzJcx2vjMWgyTmxi88KqQ%2fQvHc%2bxx%2bR%2bx7DZQ96CkdquckeQIev1WwQZApW0iwA%3d%3d | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744950980&P2=404&P3=2&P4=Coq4nQ99jHr5mxjsYbfmBsKRzJcx2vjMWgyTmxi88KqQ%2fQvHc%2bxx%2bR%2bx7DZQ96CkdquckeQIev1WwQZApW0iwA%3d%3d | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744950980&P2=404&P3=2&P4=Coq4nQ99jHr5mxjsYbfmBsKRzJcx2vjMWgyTmxi88KqQ%2fQvHc%2bxx%2bR%2bx7DZQ96CkdquckeQIev1WwQZApW0iwA%3d%3d | unknown | — | — | whitelisted |
5936 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744950980&P2=404&P3=2&P4=Coq4nQ99jHr5mxjsYbfmBsKRzJcx2vjMWgyTmxi88KqQ%2fQvHc%2bxx%2bR%2bx7DZQ96CkdquckeQIev1WwQZApW0iwA%3d%3d | unknown | — | — | whitelisted |
6240 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.155:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7392 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7668 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7668 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7668 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7668 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7668 | msedge.exe | 2.16.10.182:443 | bzib.nelreports.net | Akamai International B.V. | AT | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.rbxidle.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |