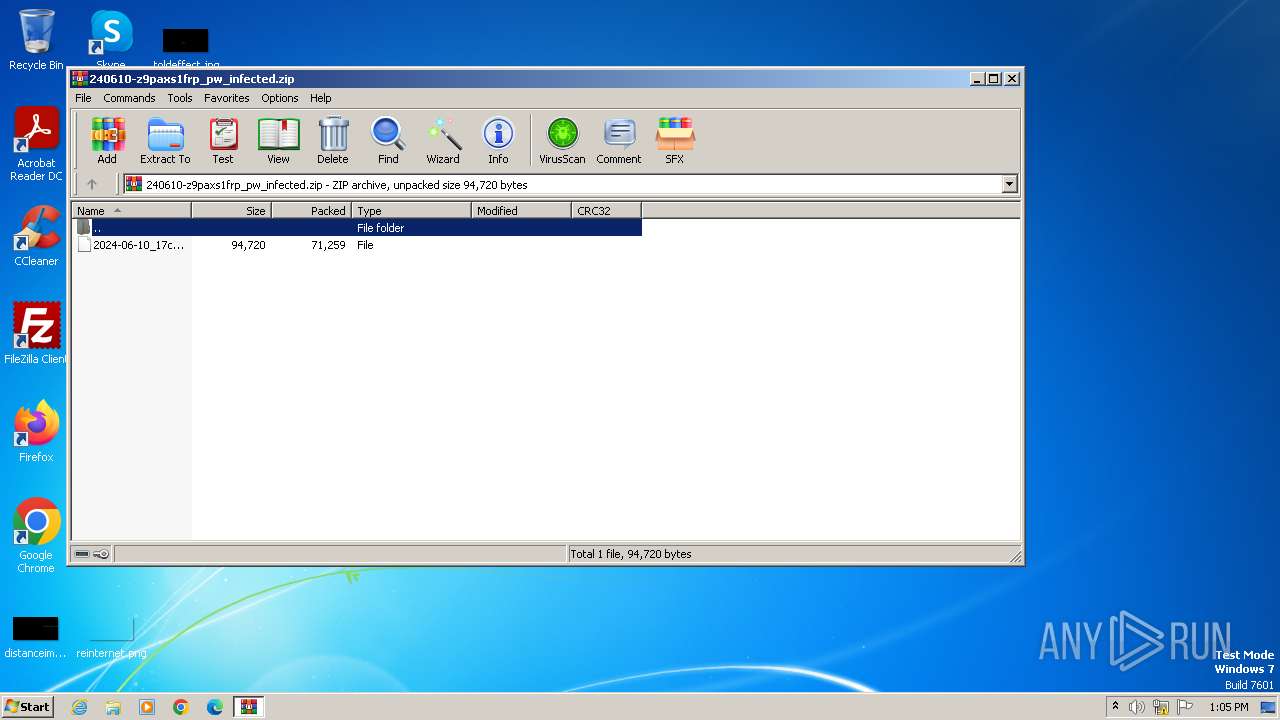
| File name: | 240610-z9paxs1frp_pw_infected.zip |
| Full analysis: | https://app.any.run/tasks/3eefe042-3cf6-4c44-b51d-69fc4ff555ac |
| Verdict: | Malicious activity |
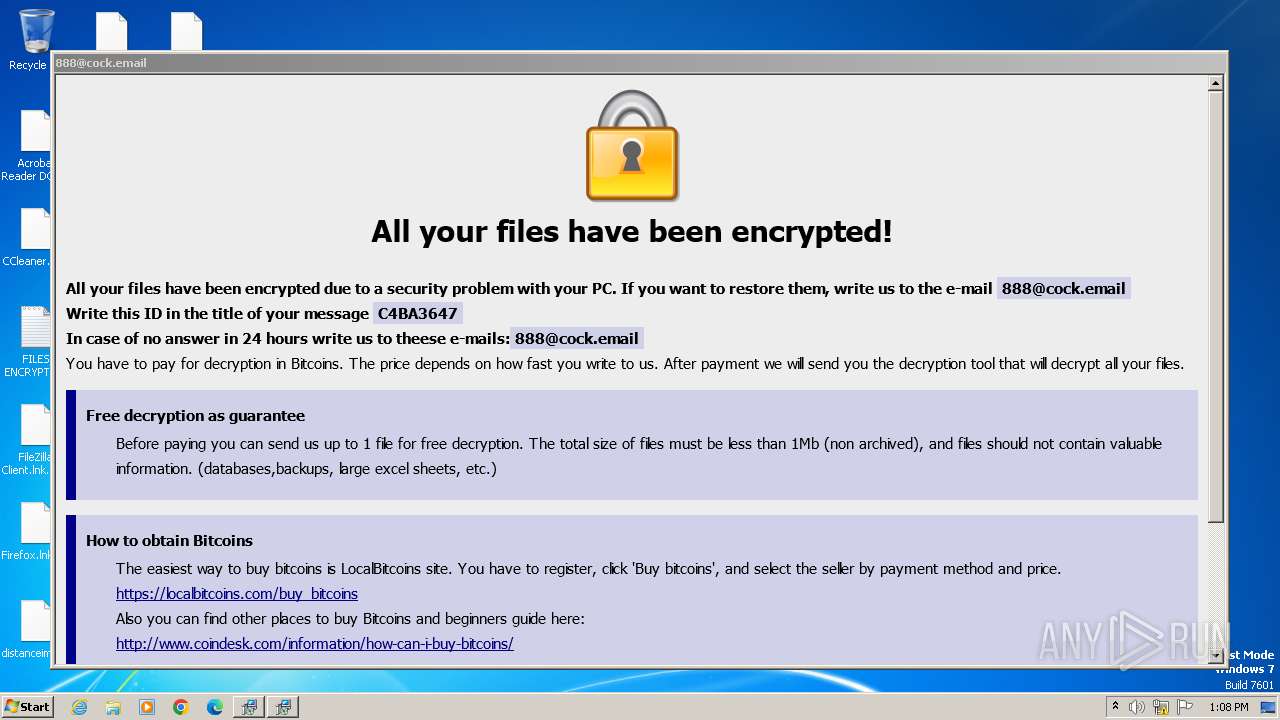
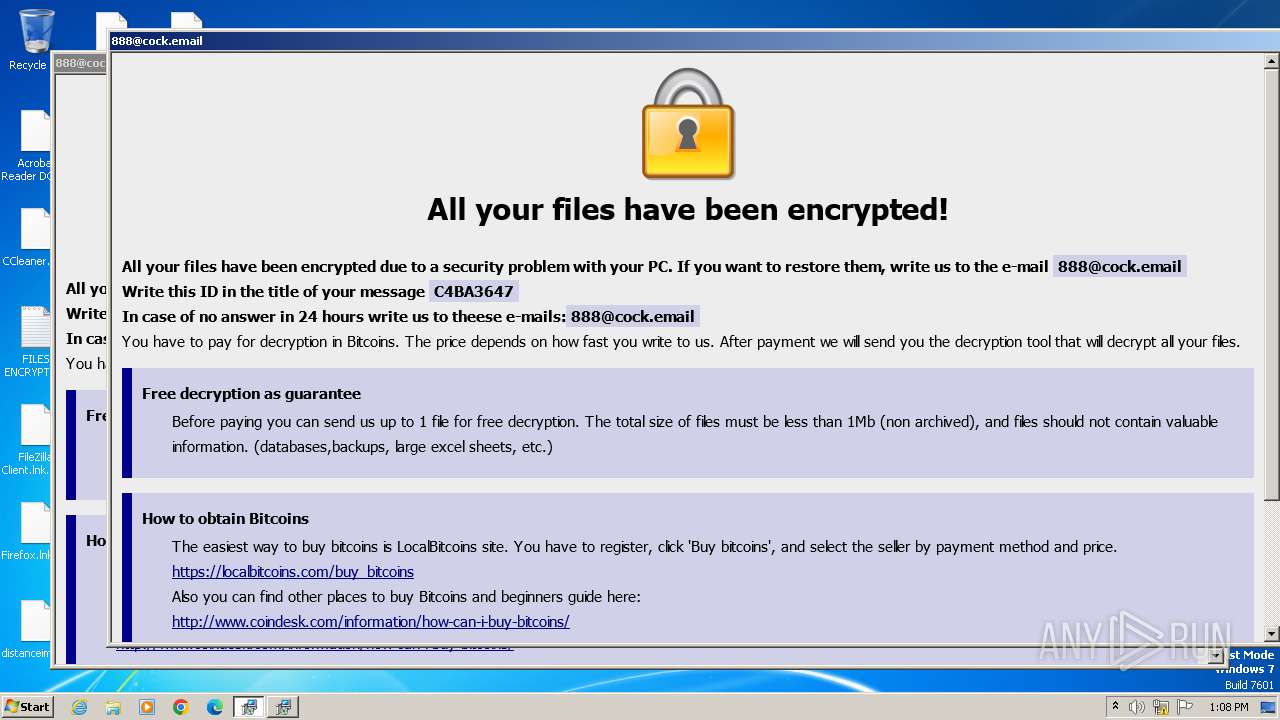
| Threats: | Dharma is advanced ransomware that has been observed in the wild since 2016. It is considered to be the second most profitable RaaS operation by the FBI. The malware targets hospitals and state organizations, encrypts files, and demands a payment to restore access to lost information. |
| Analysis date: | June 11, 2024, 12:05:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 60678B12571D718BF41BD336F23581CE |
| SHA1: | 662ACB22D120DDA089D7E923A94332C46B9CC3C7 |
| SHA256: | 81FA714E1604D4E1045E4C783149046B404ABEFAF539BA5ACFE1C6A4CD19045C |
| SSDEEP: | 3072:qj7VtPRgwrcbJN95Jbm6wnXOtUSa/kzfGxLYvb:qj7zZgwQbPA6wXBSqkyxLYvb |
MALICIOUS
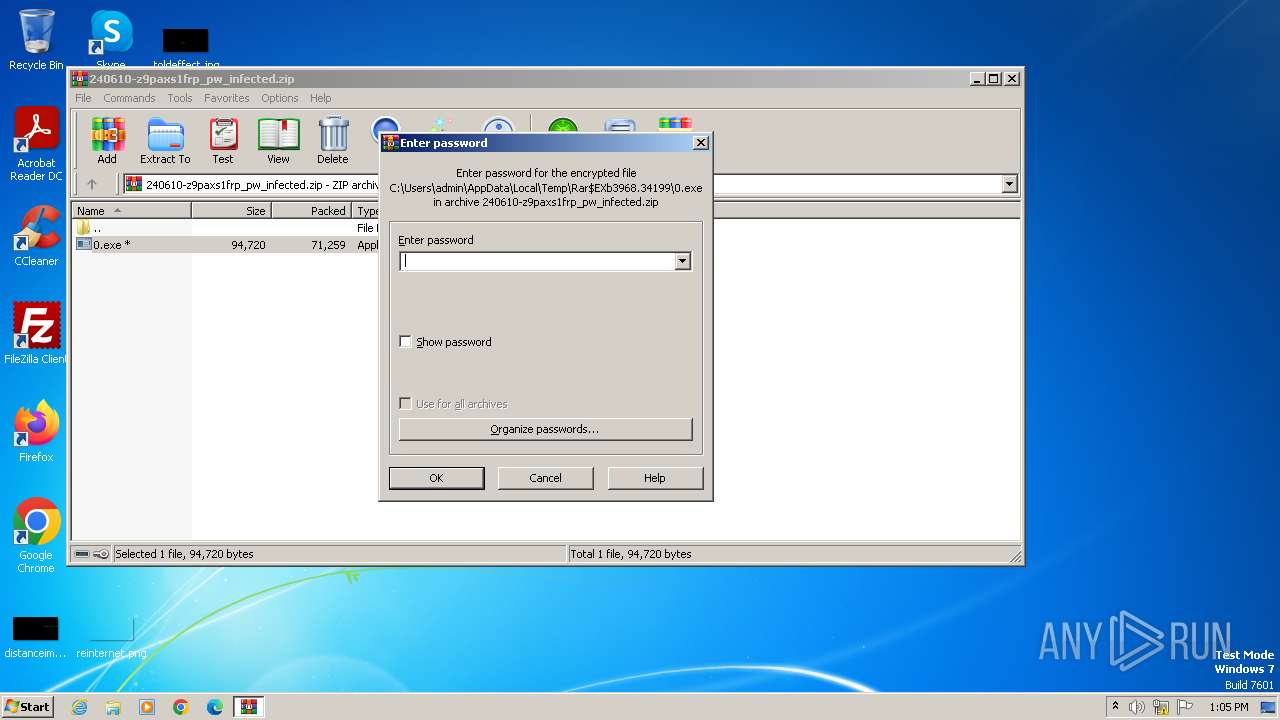
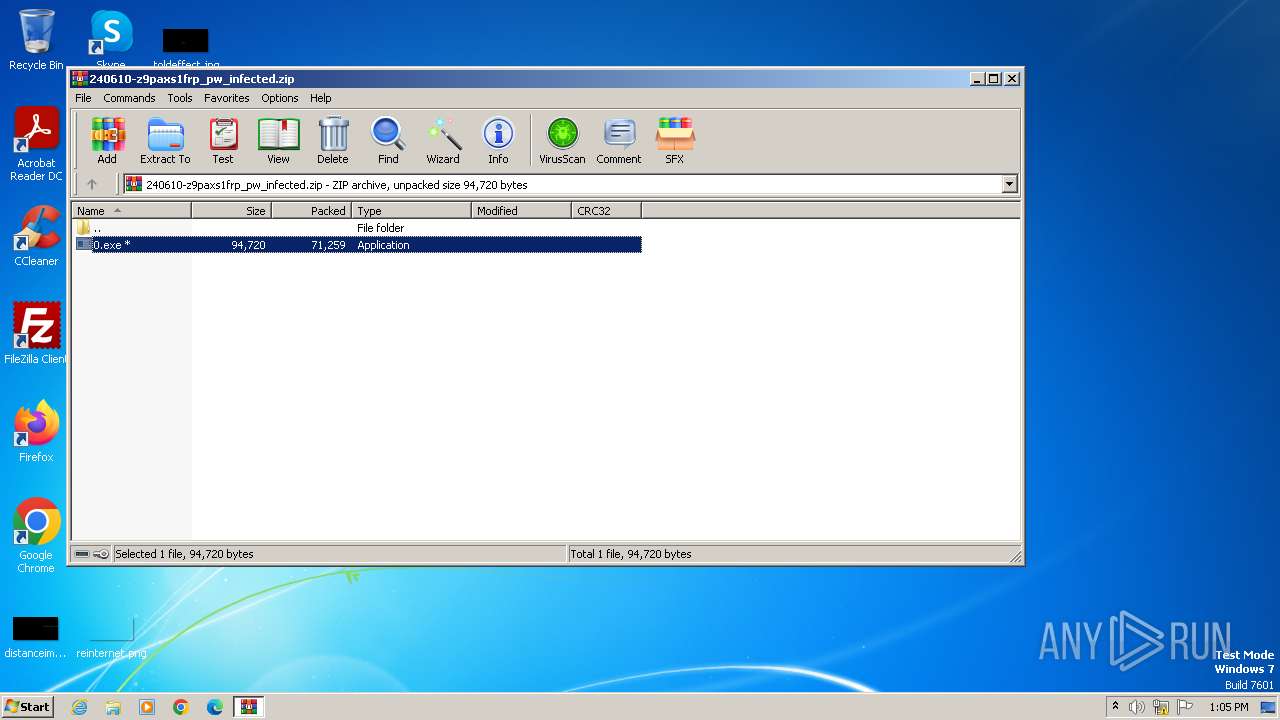
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3968)
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Changes the autorun value in the registry
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Create files in the Startup directory
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
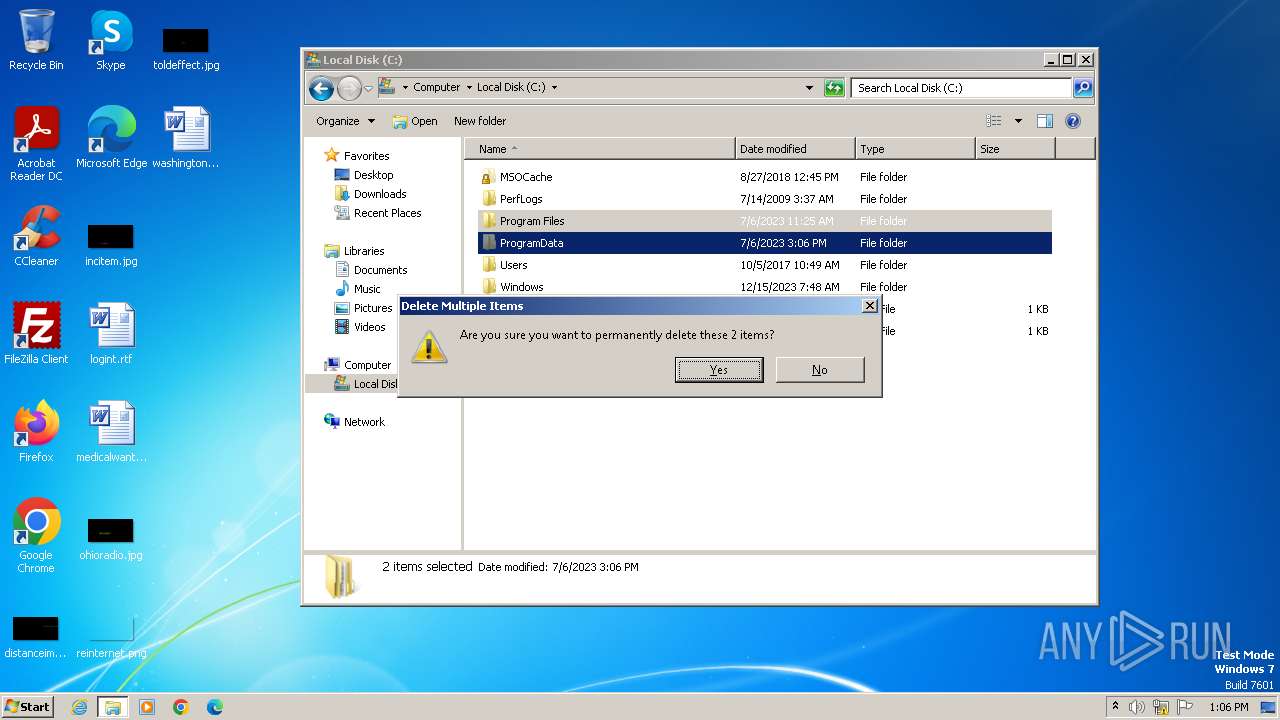
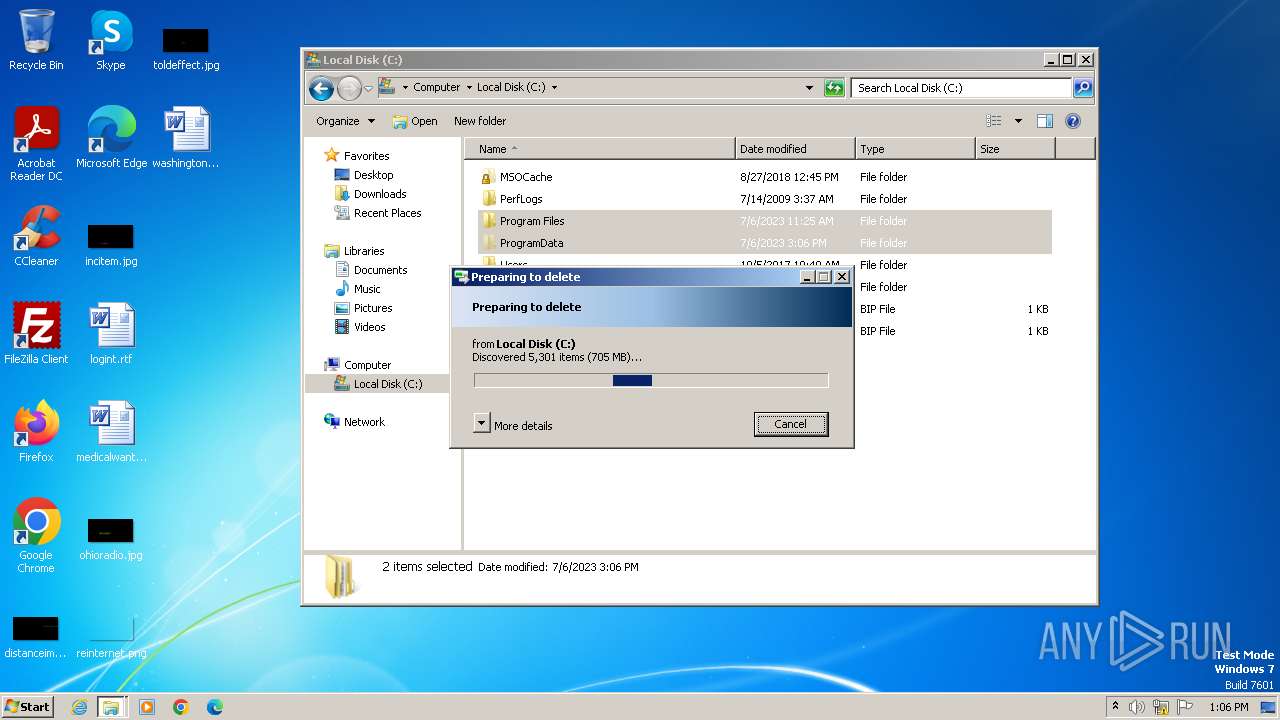
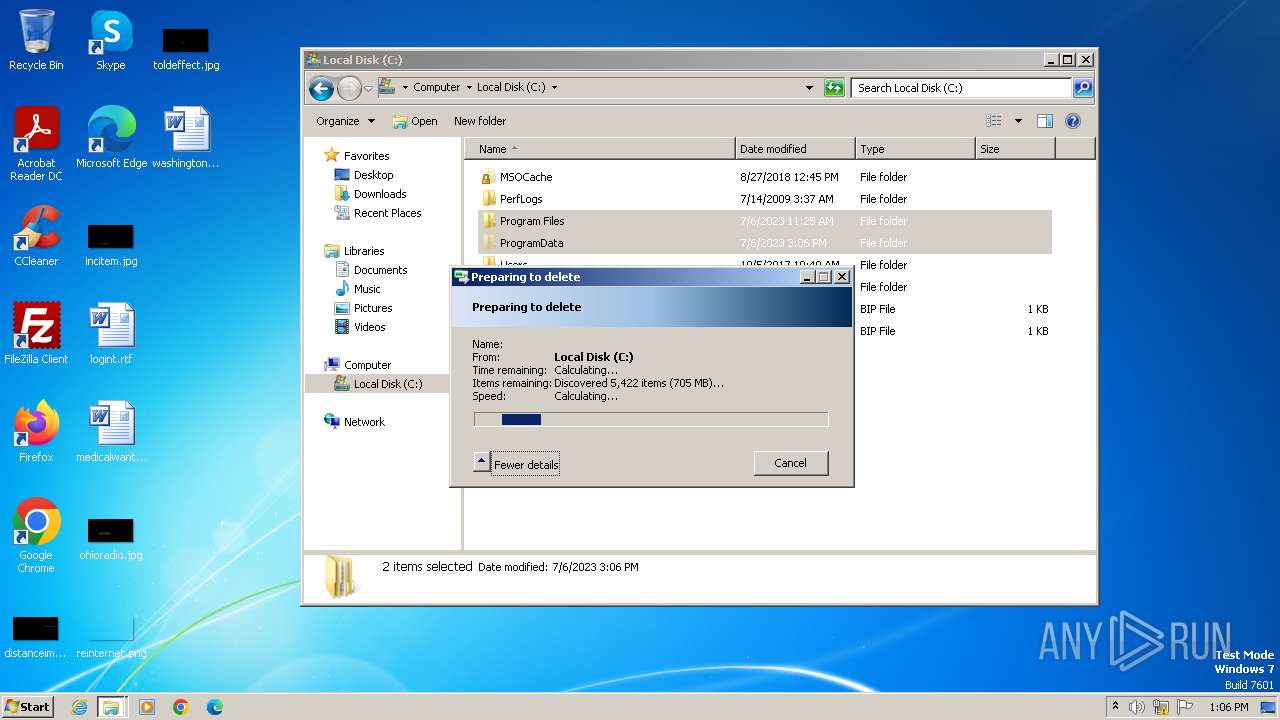
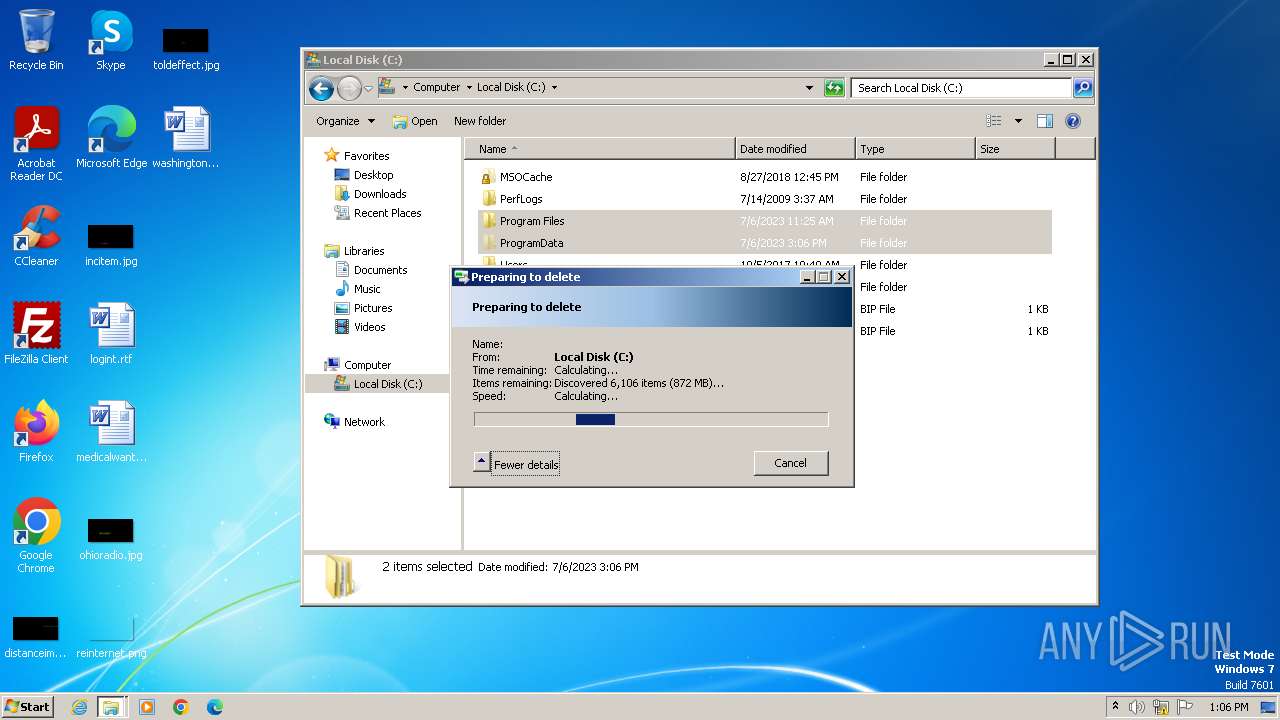
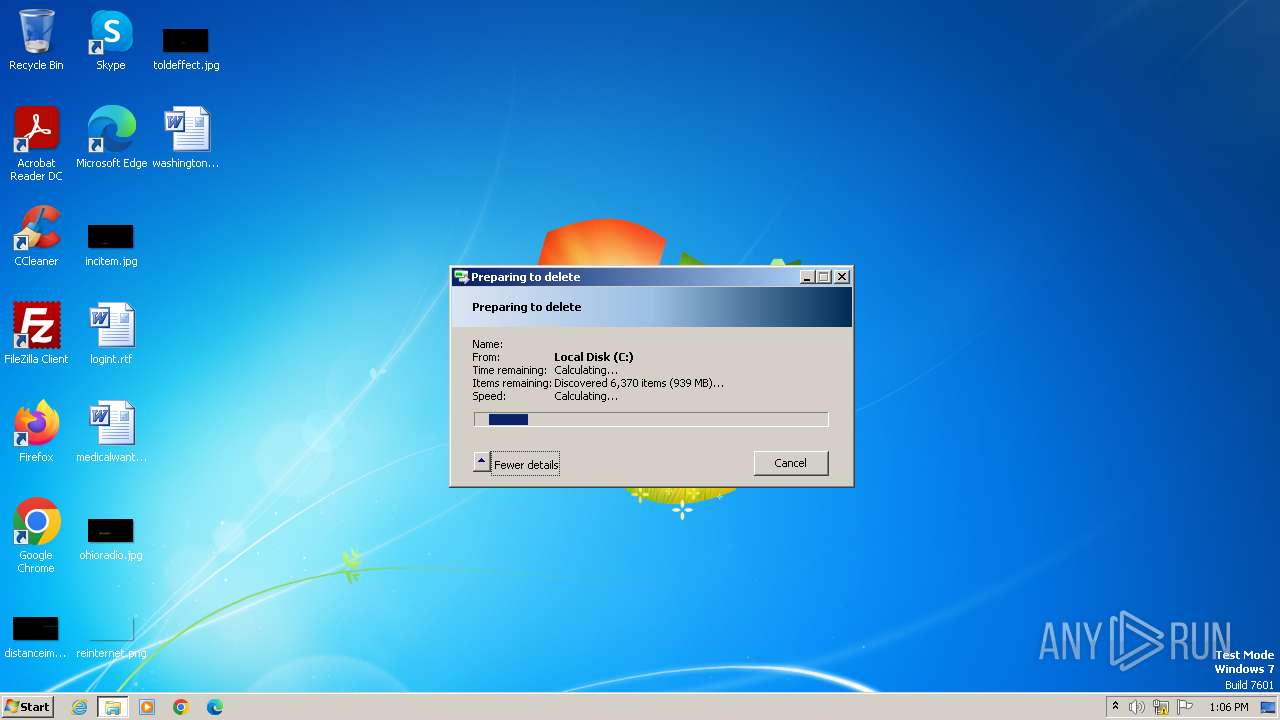
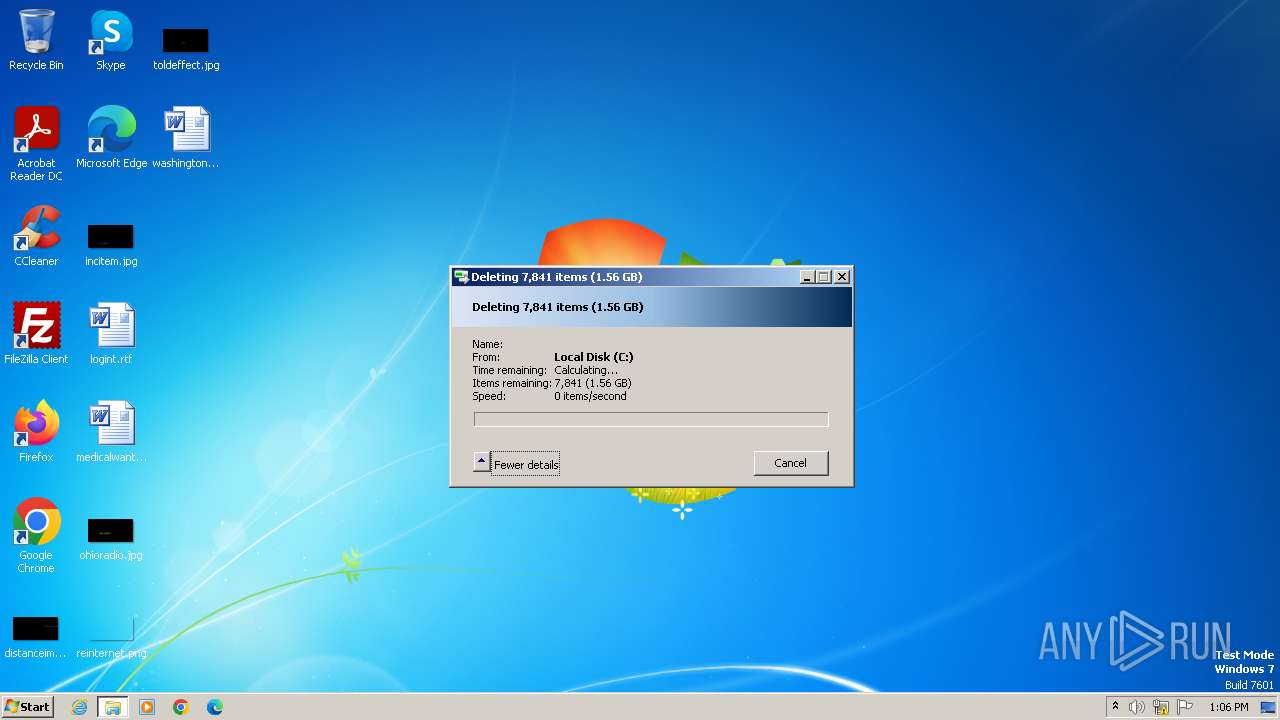
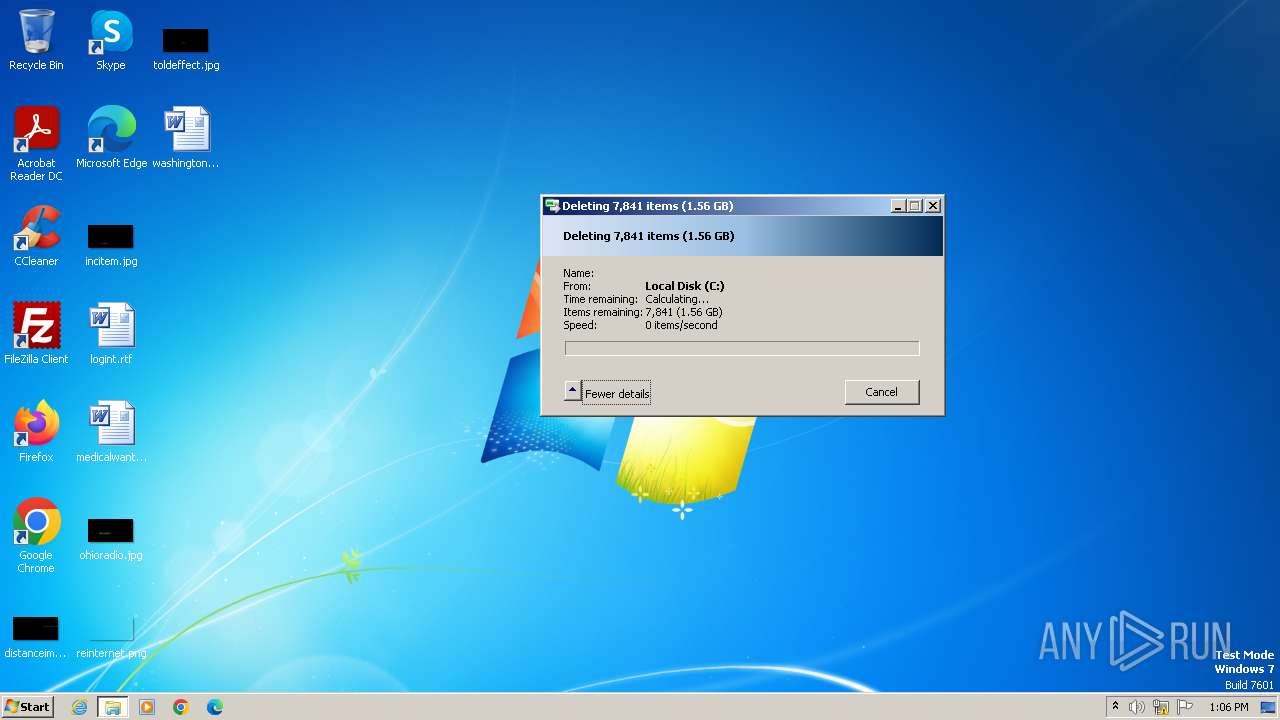
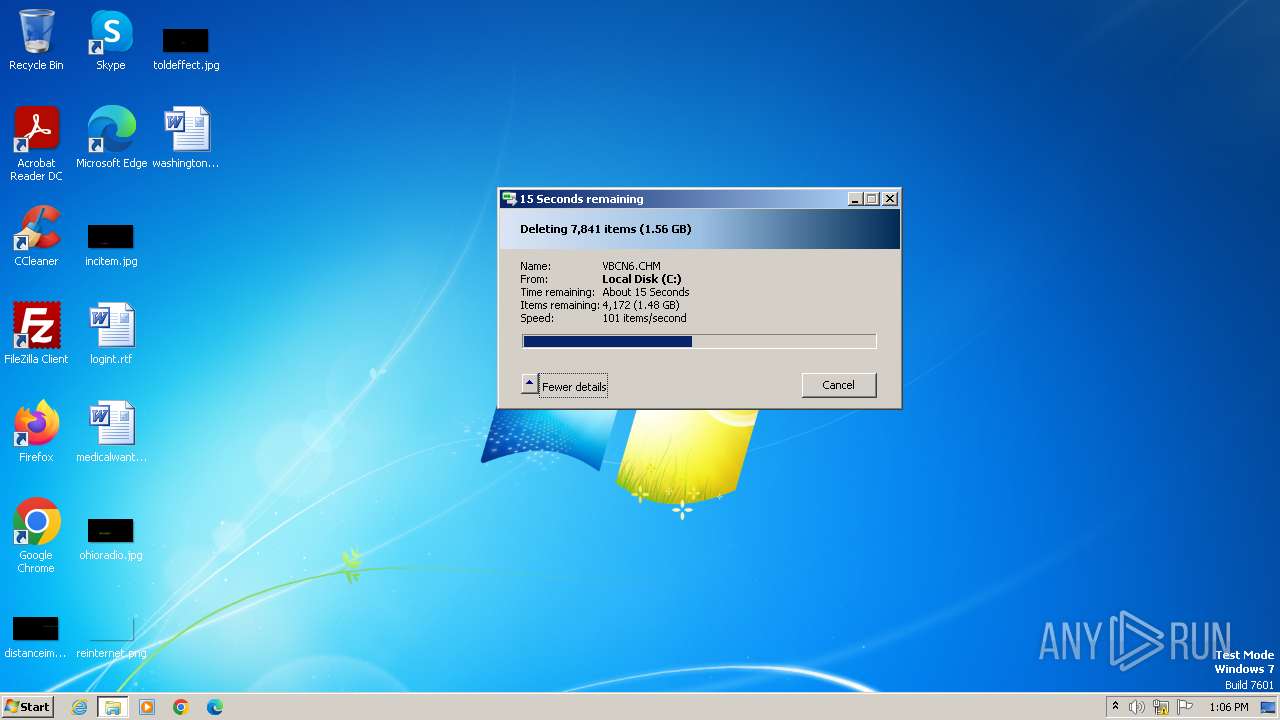
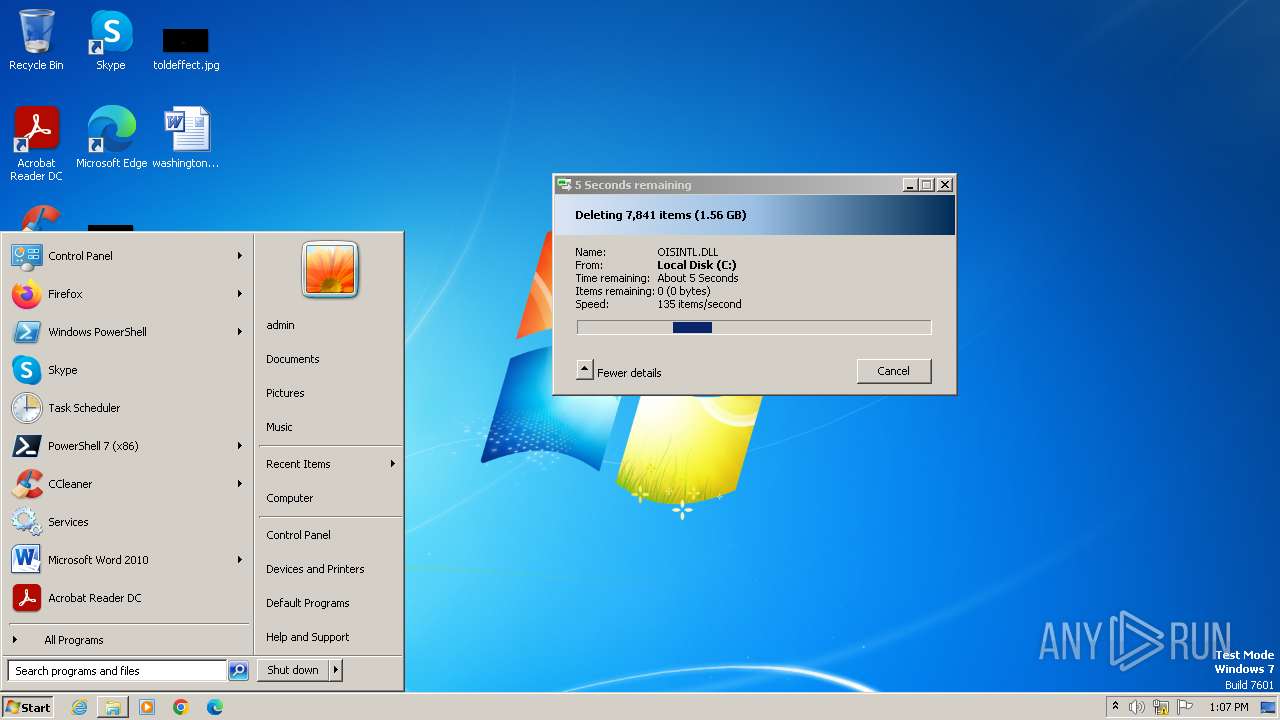
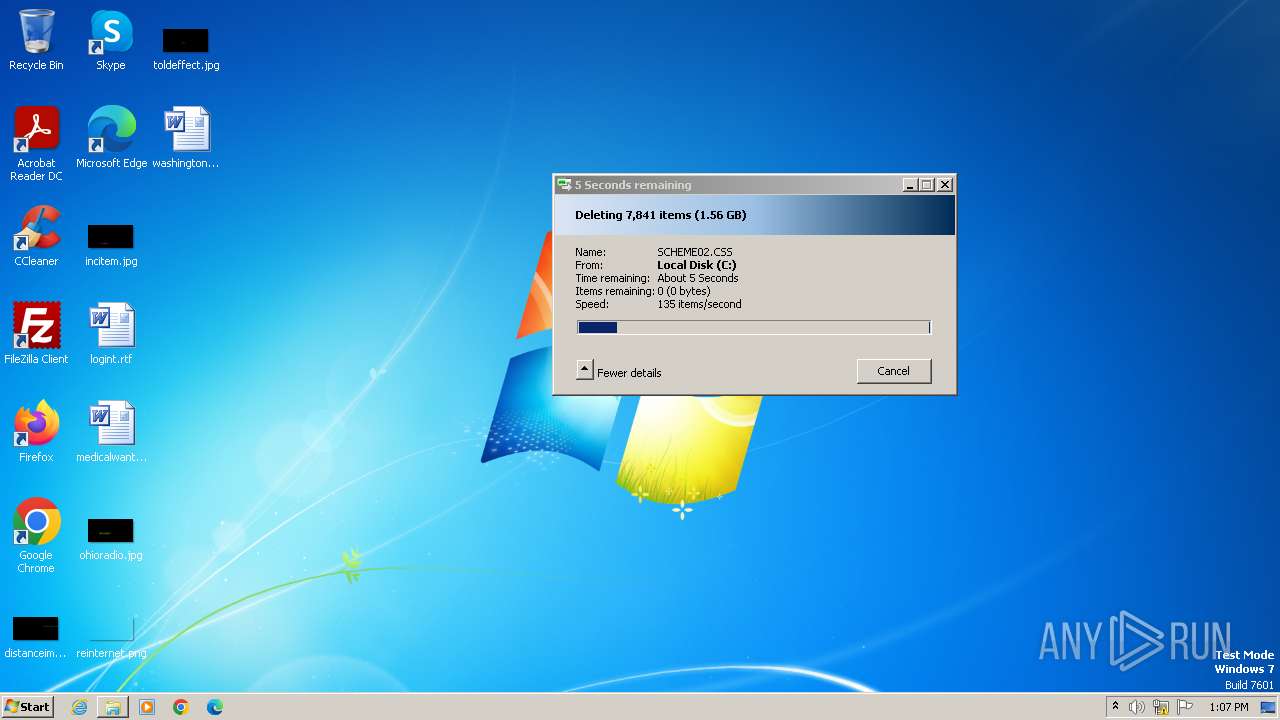
Deletes shadow copies
- cmd.exe (PID: 4020)
- cmd.exe (PID: 312)
- cmd.exe (PID: 1988)
- cmd.exe (PID: 2772)
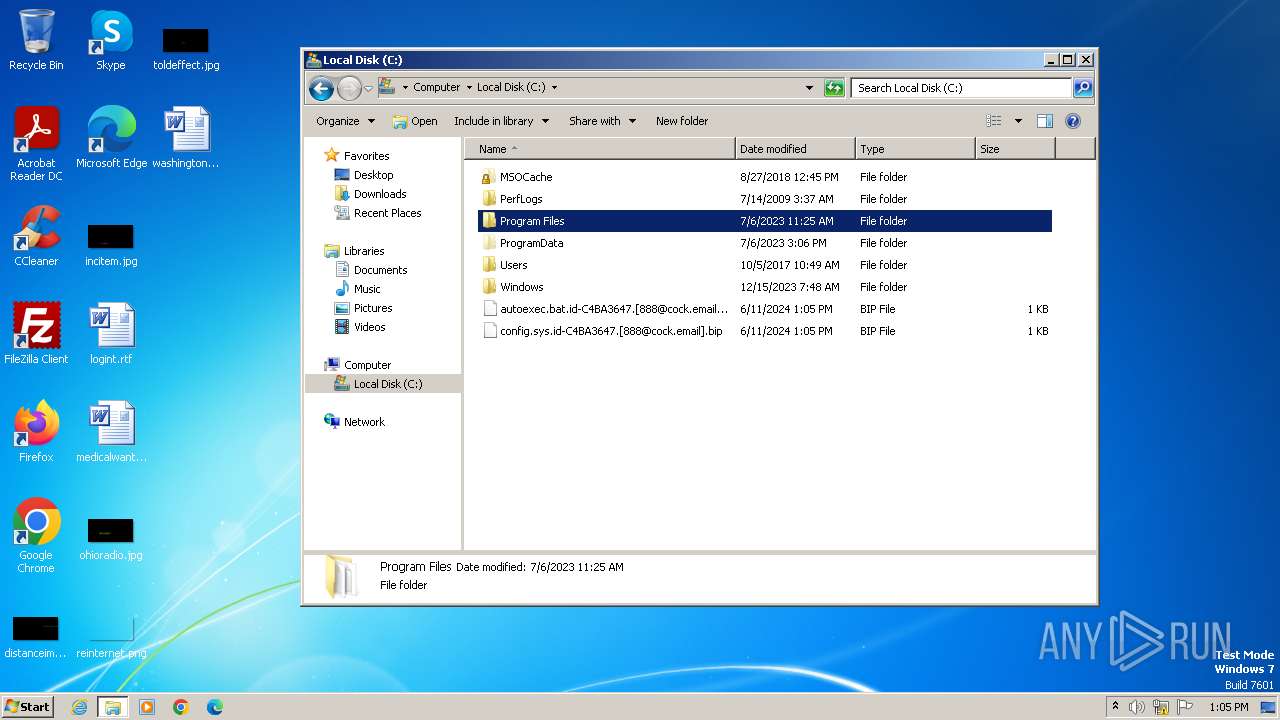
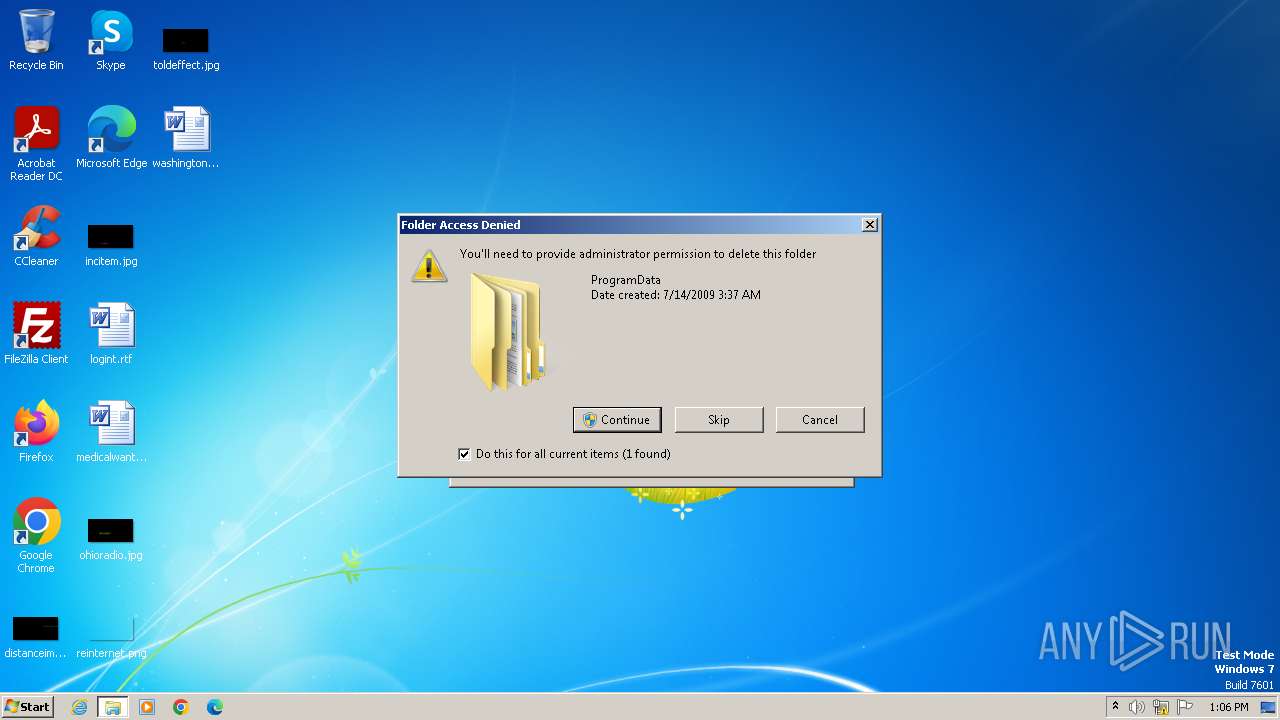
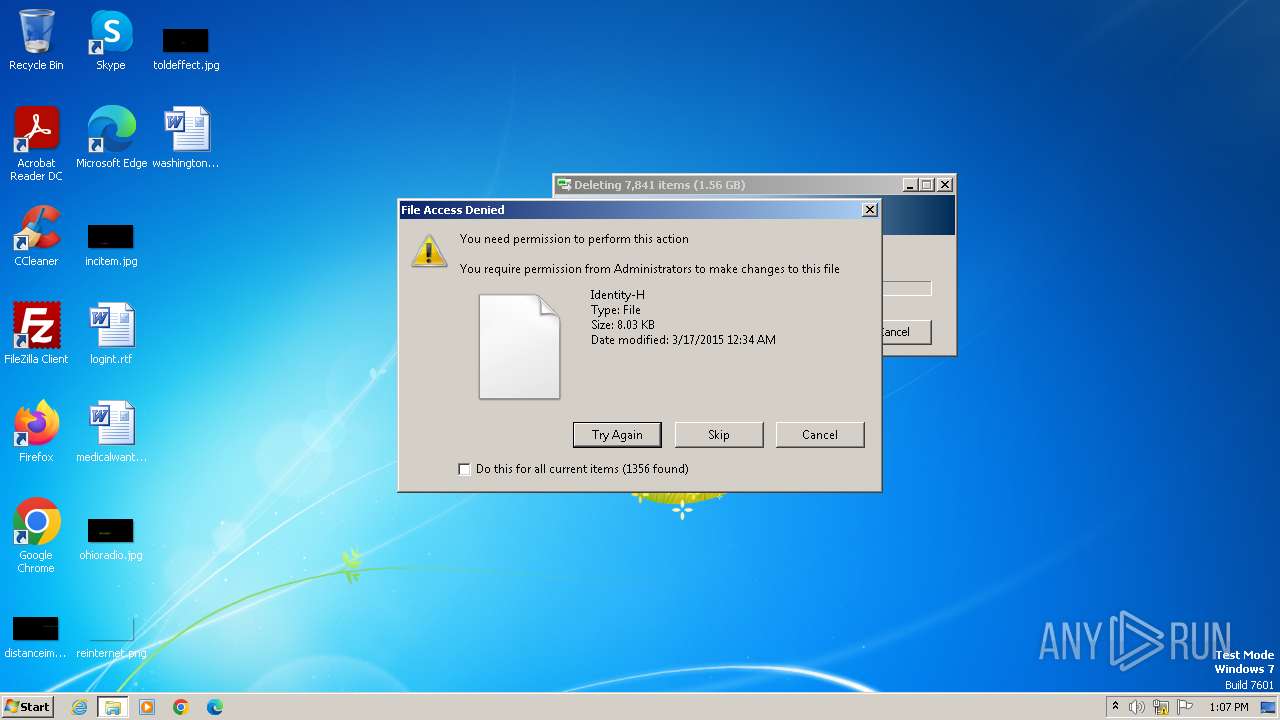
Creates a writable file in the system directory
- 0.exe (PID: 1628)
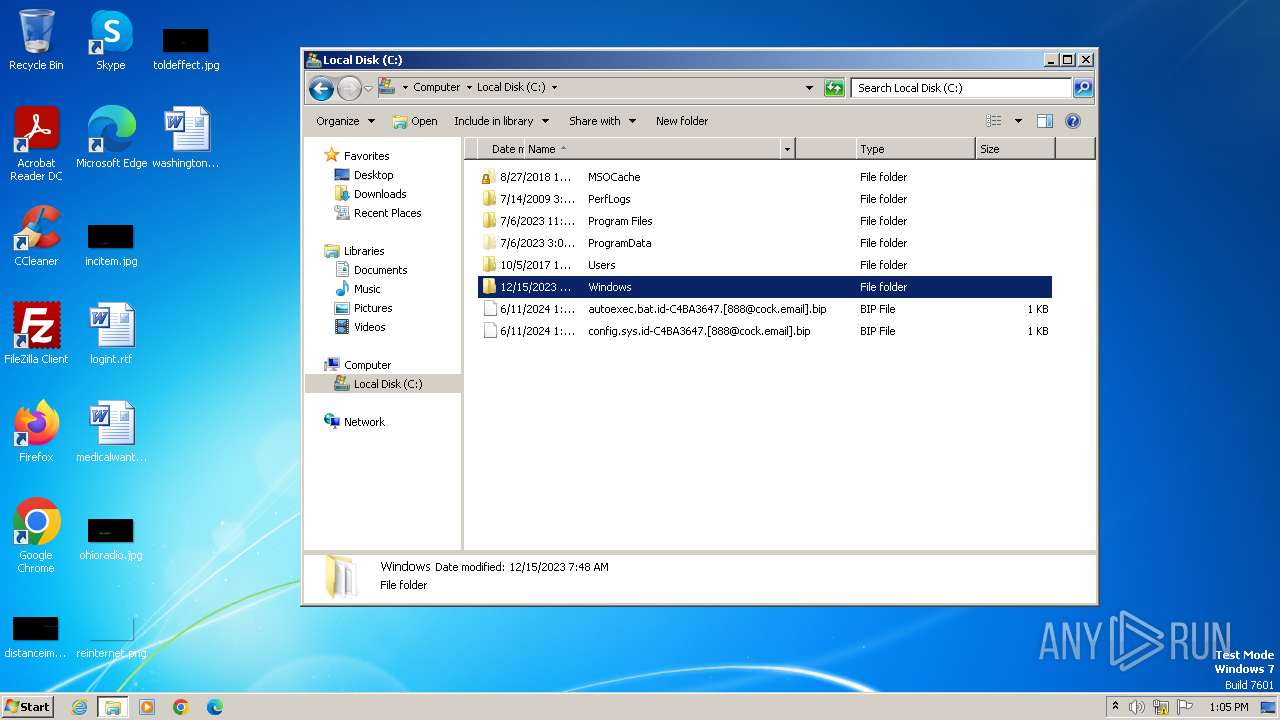
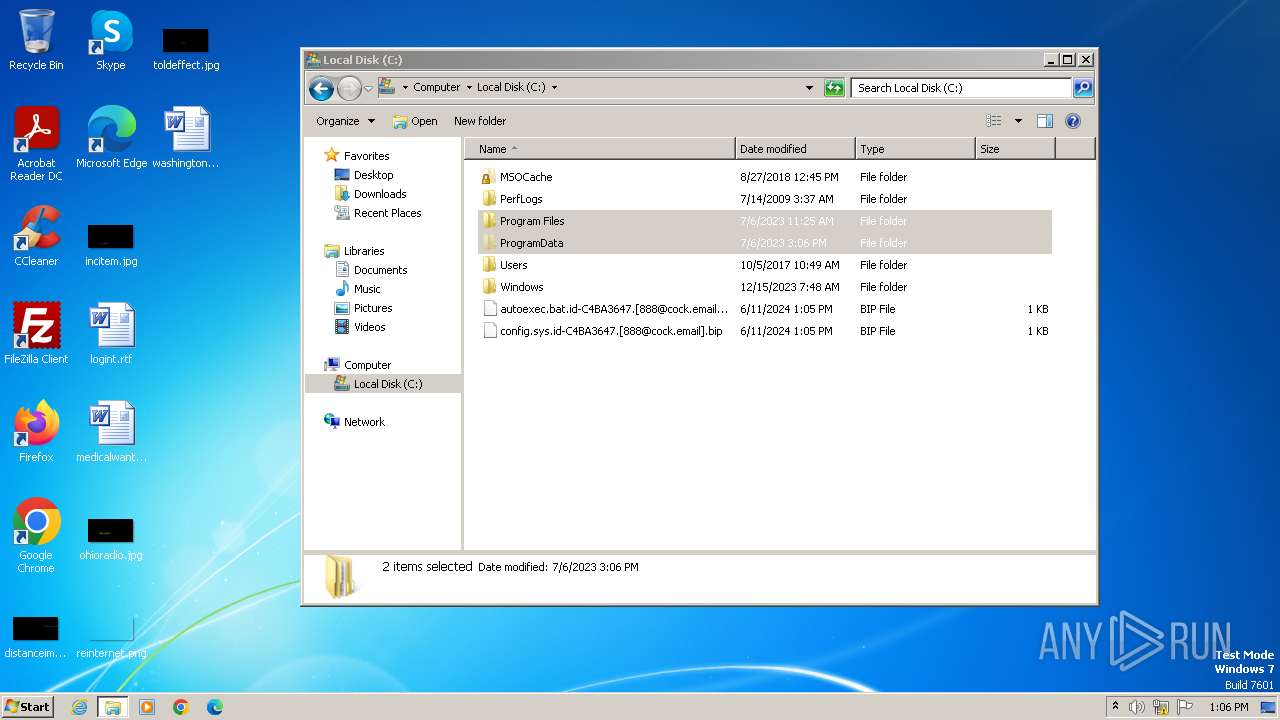
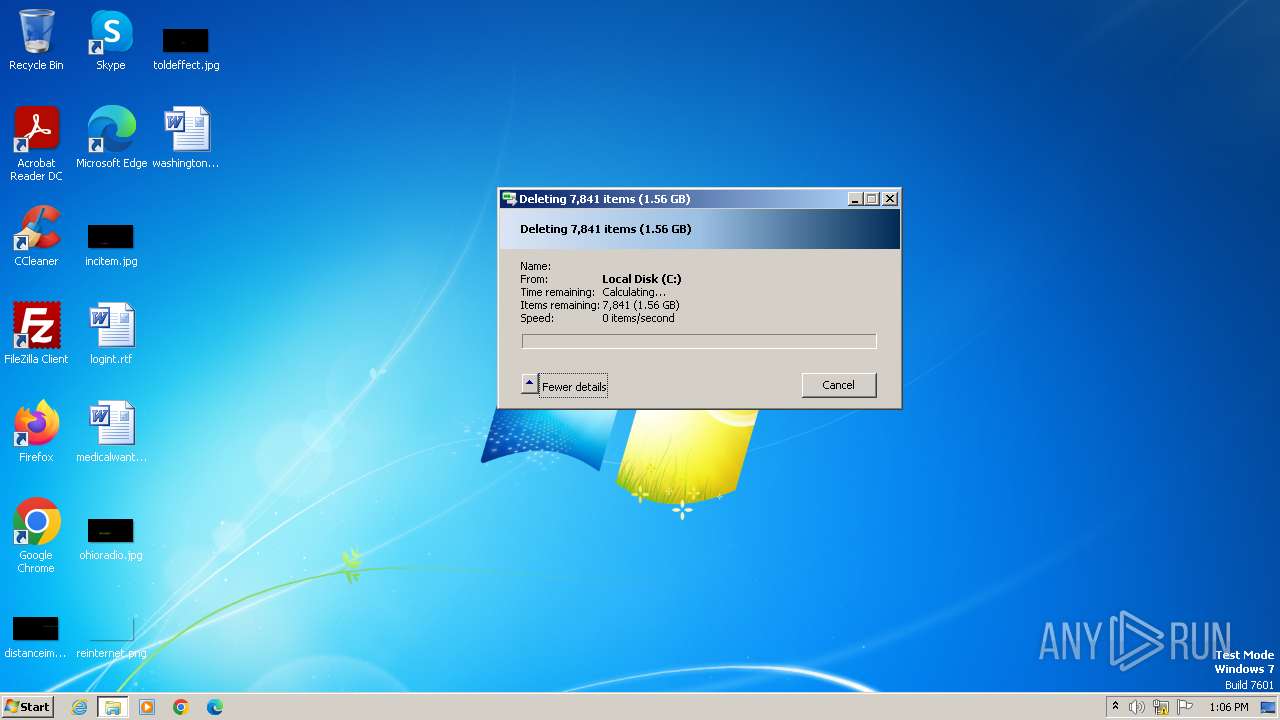
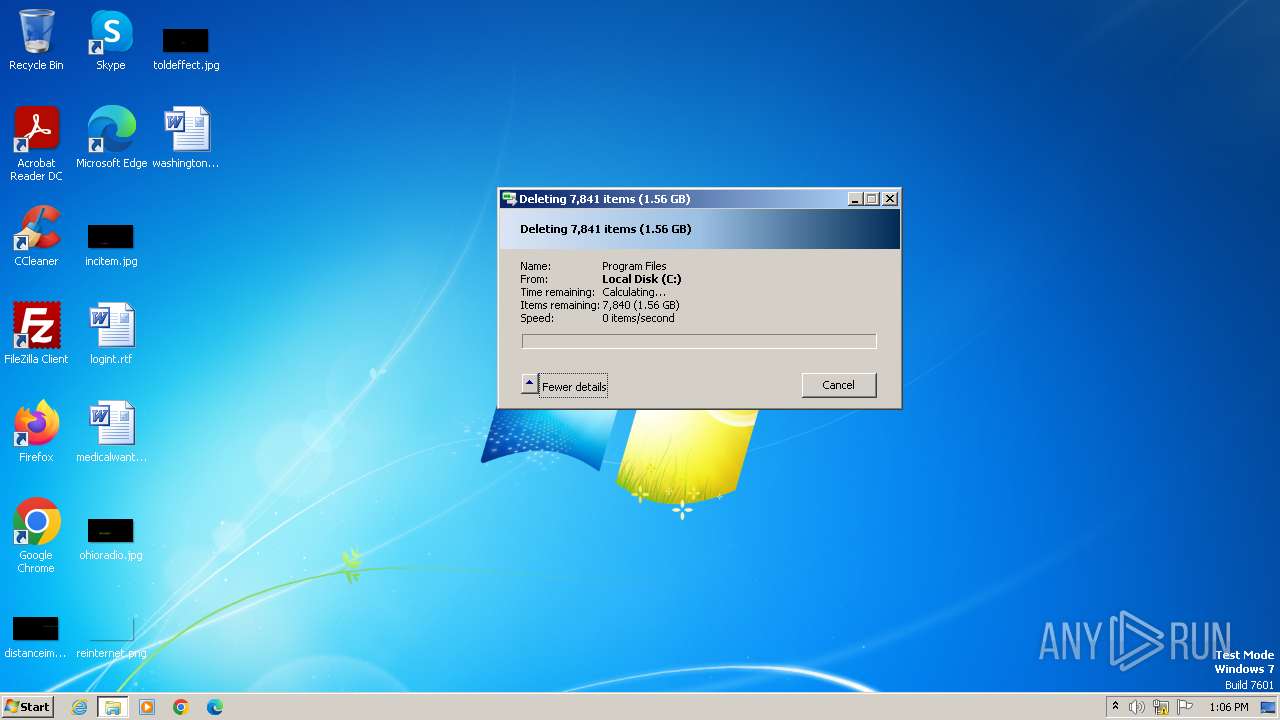
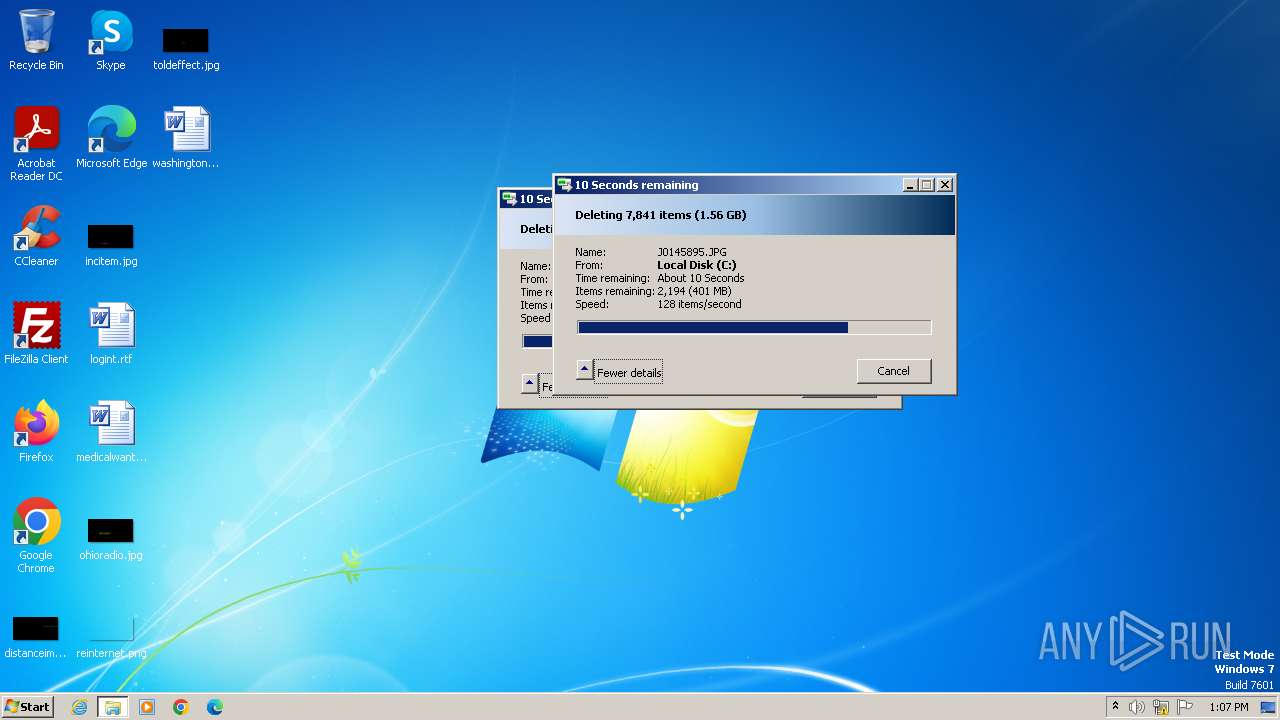
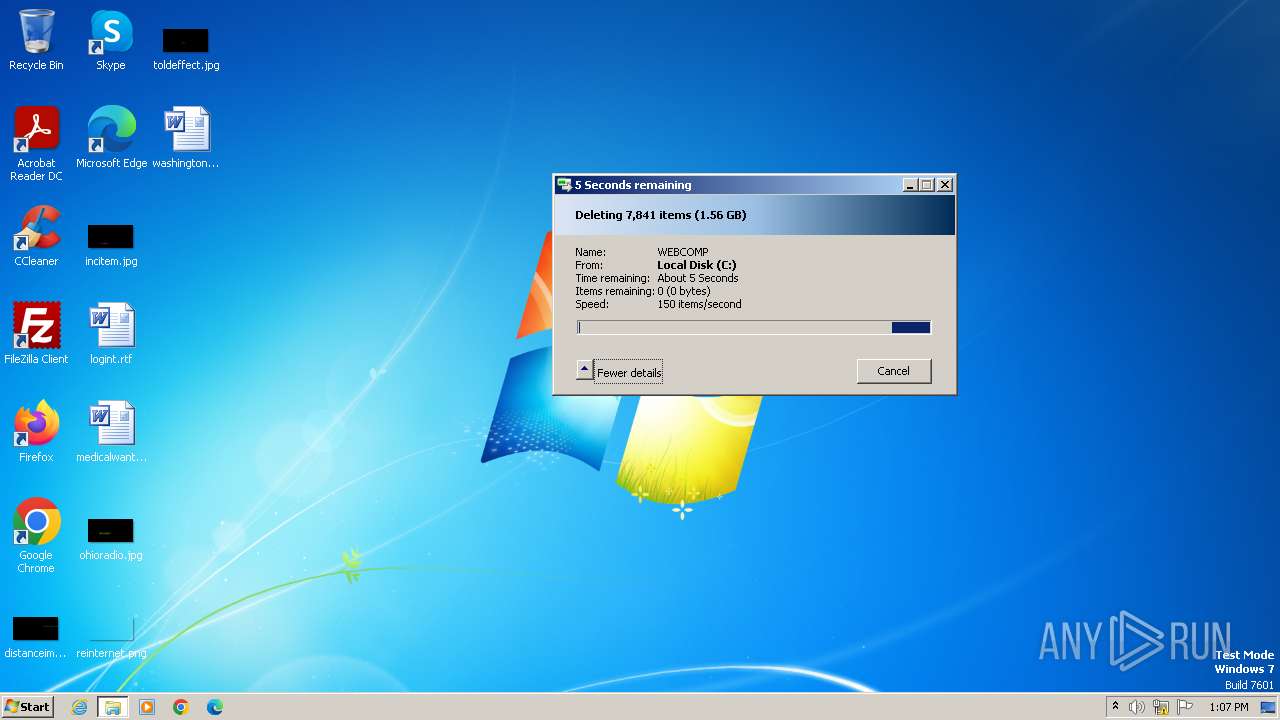
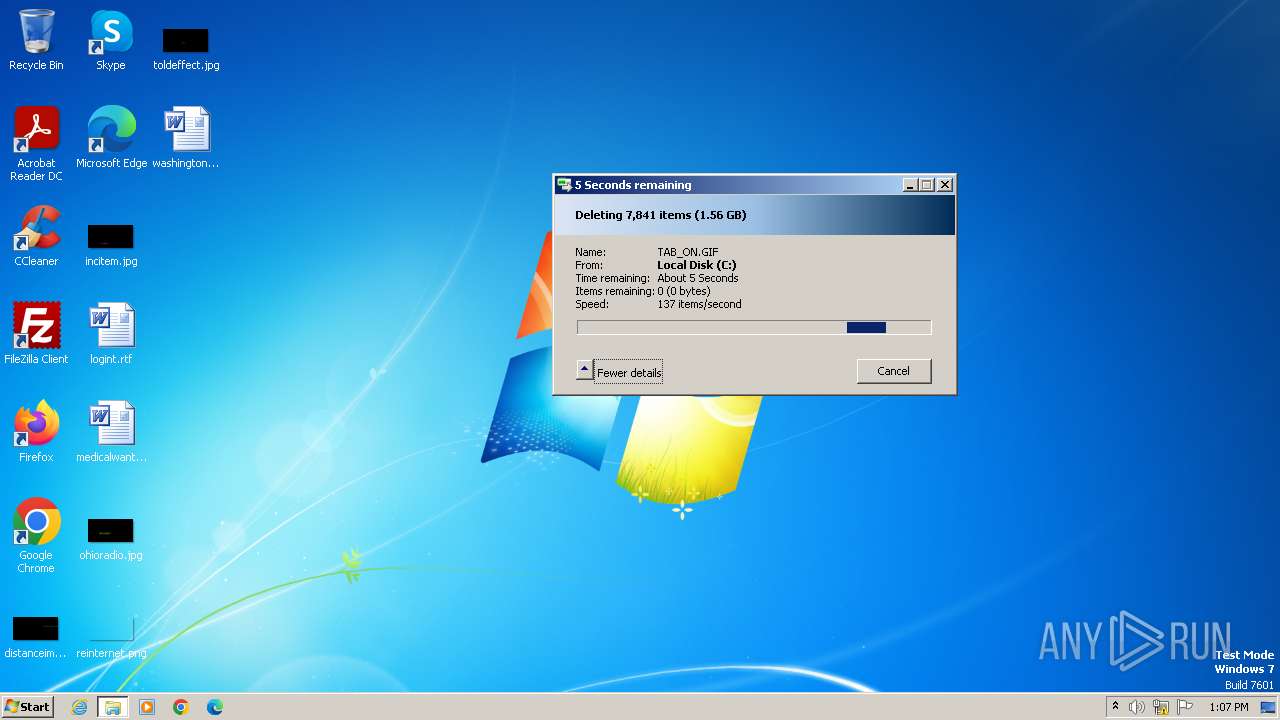
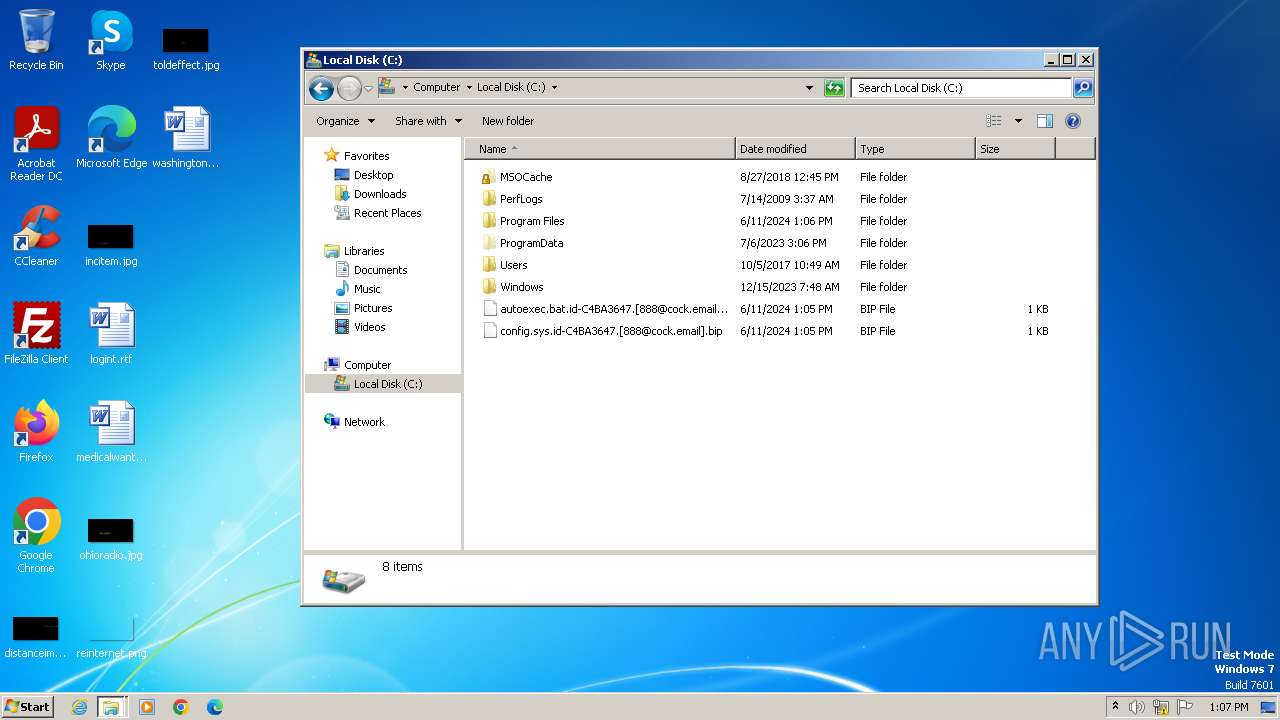
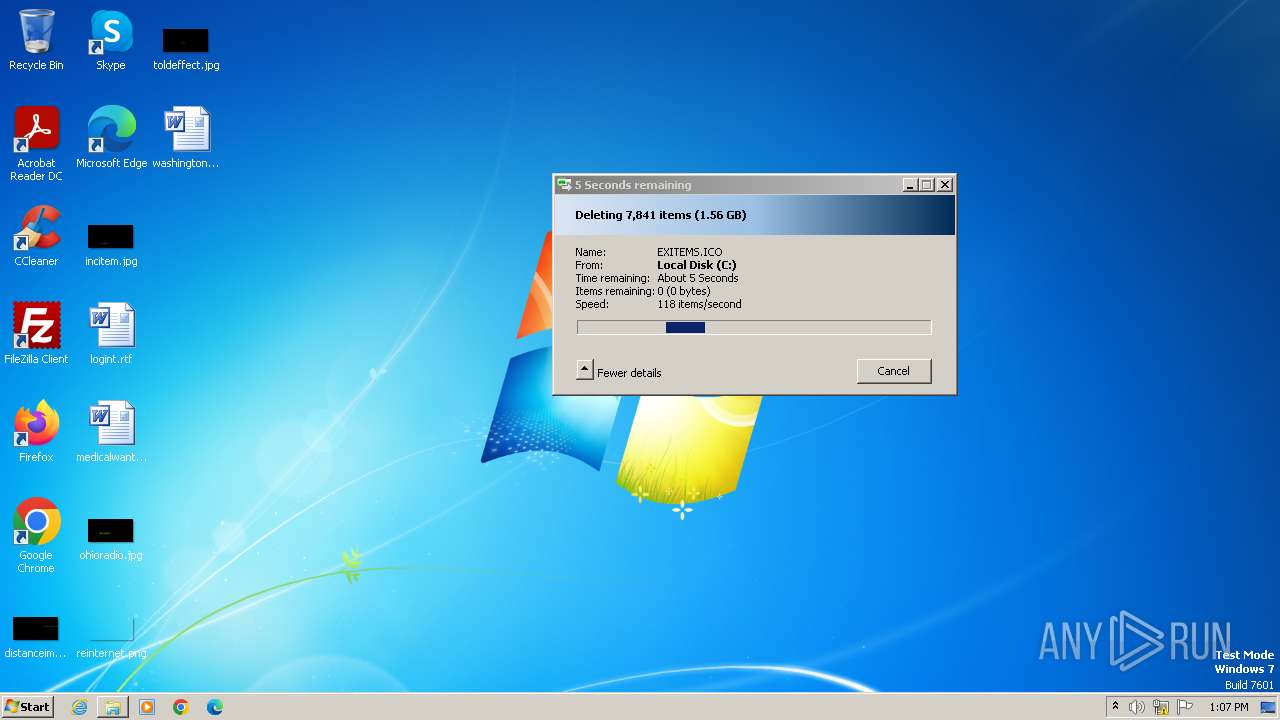
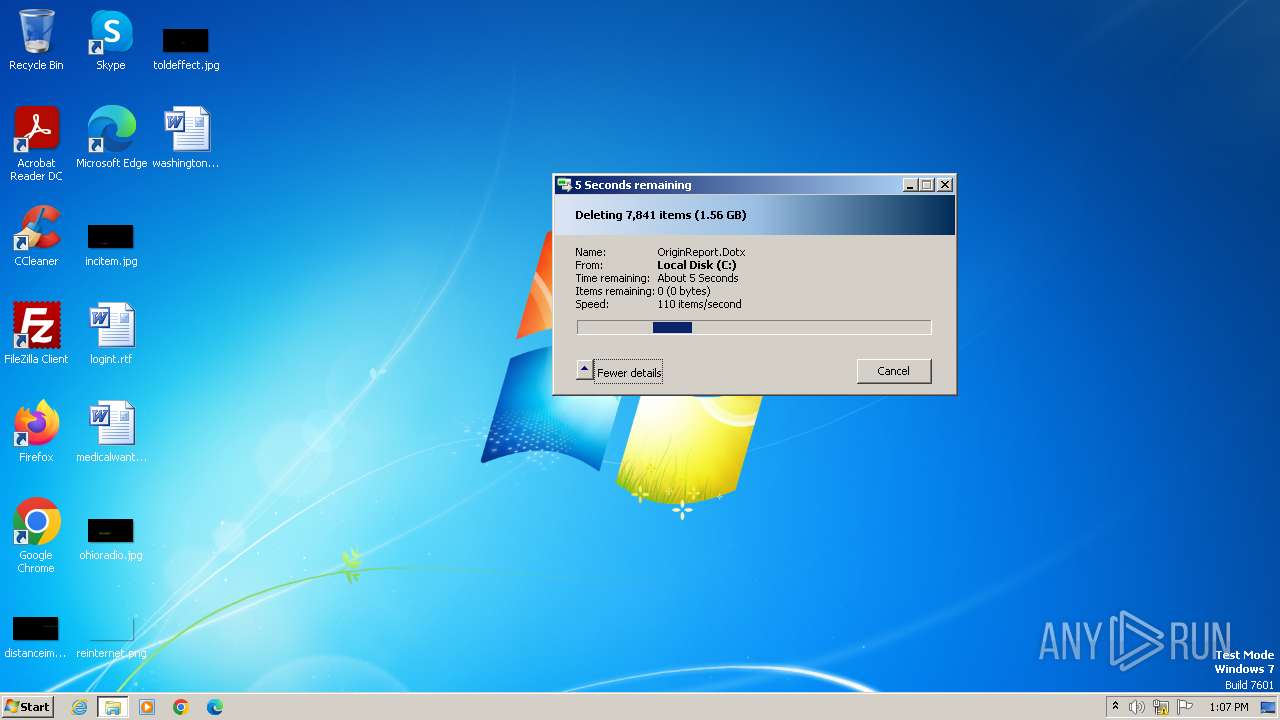
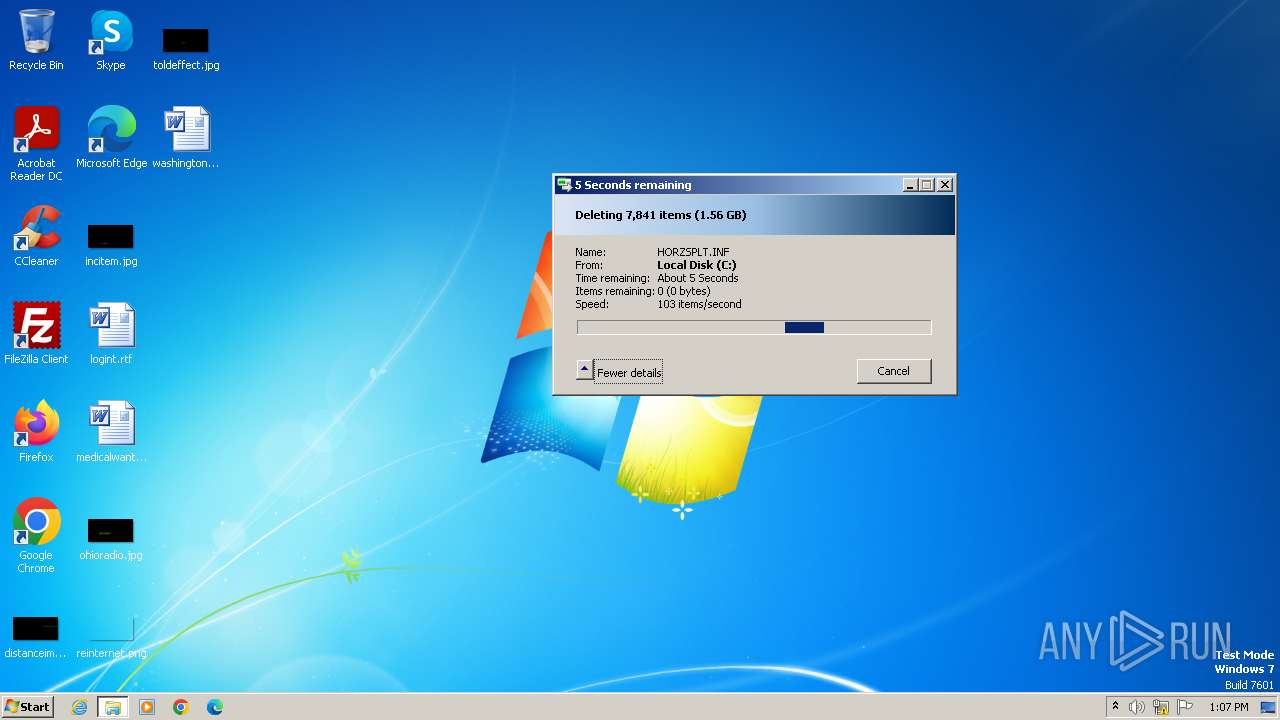
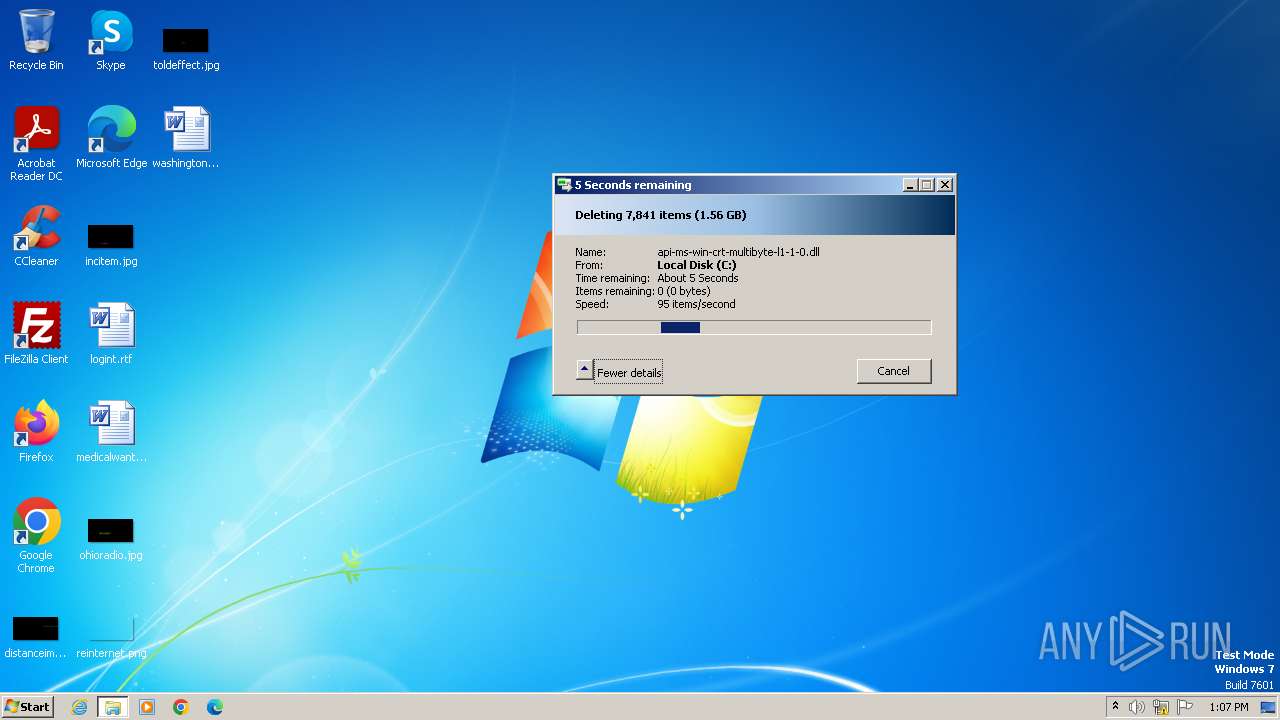
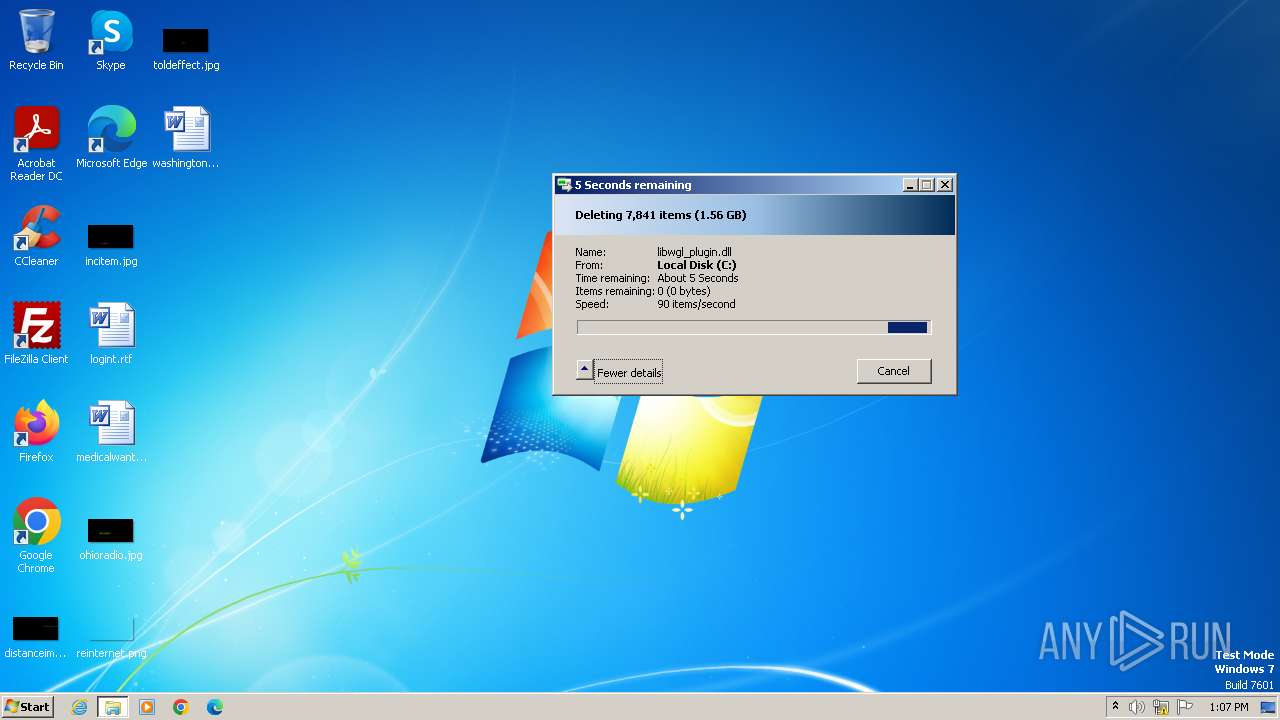
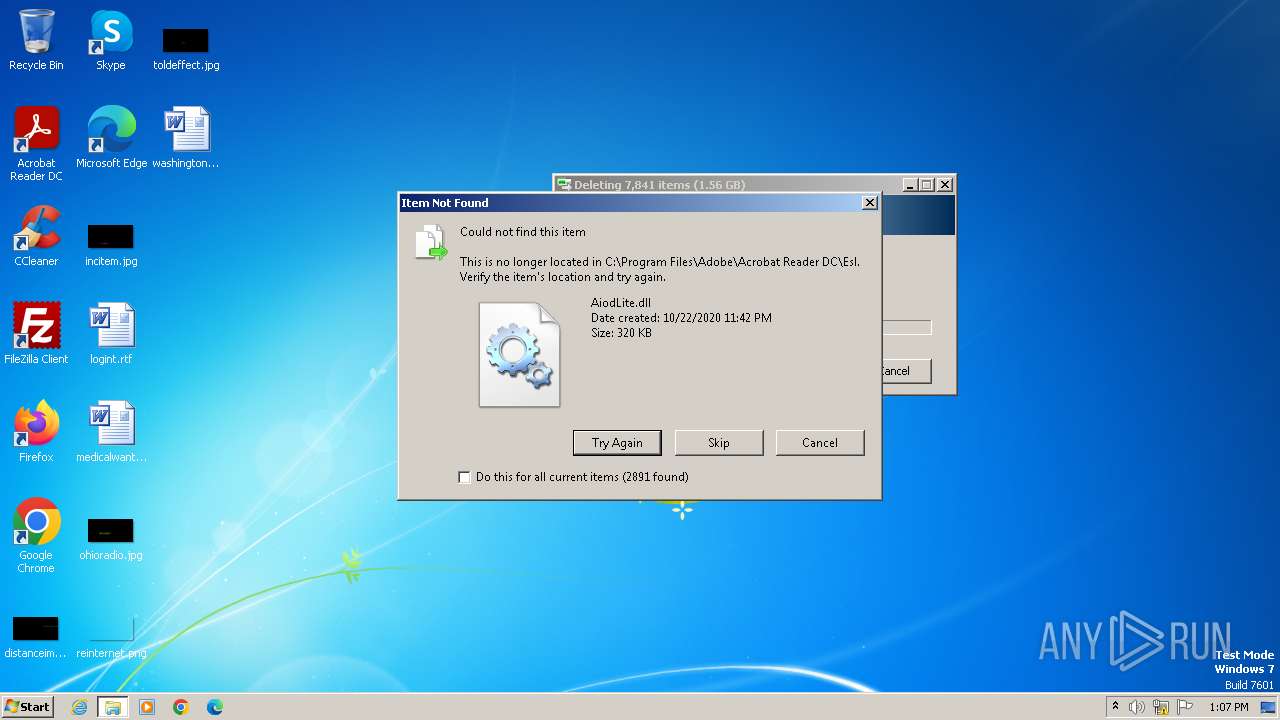
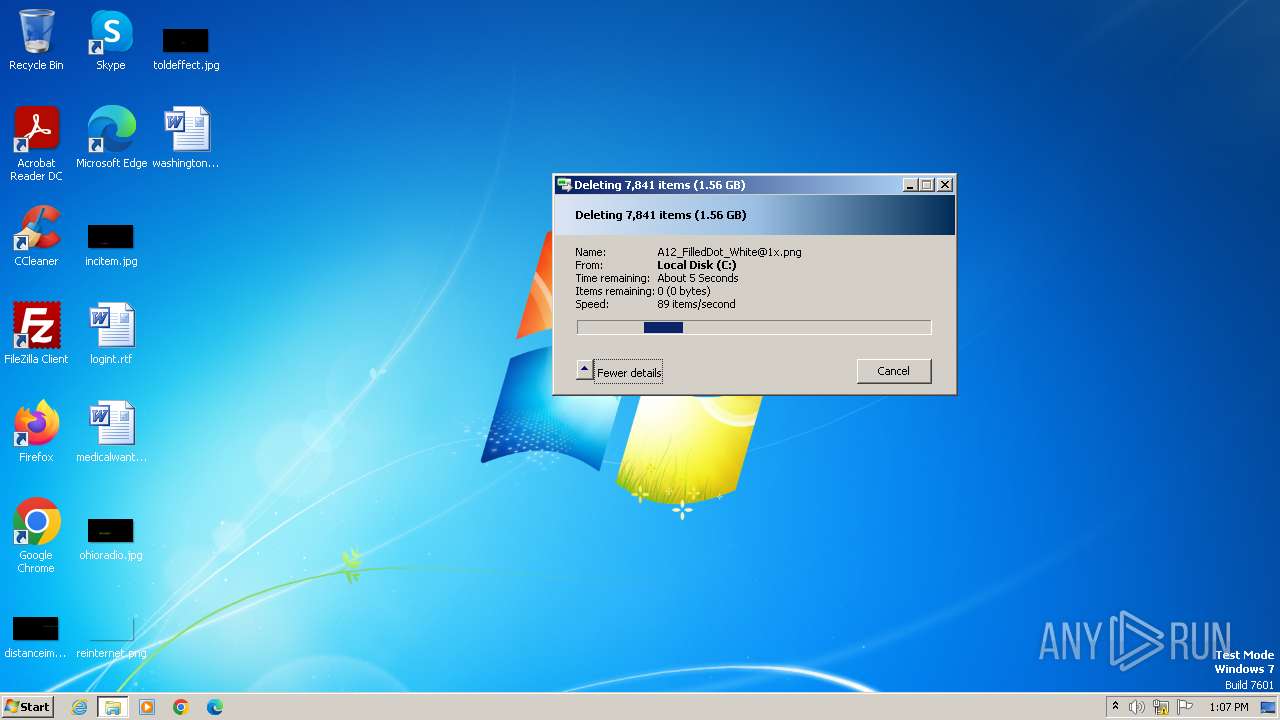
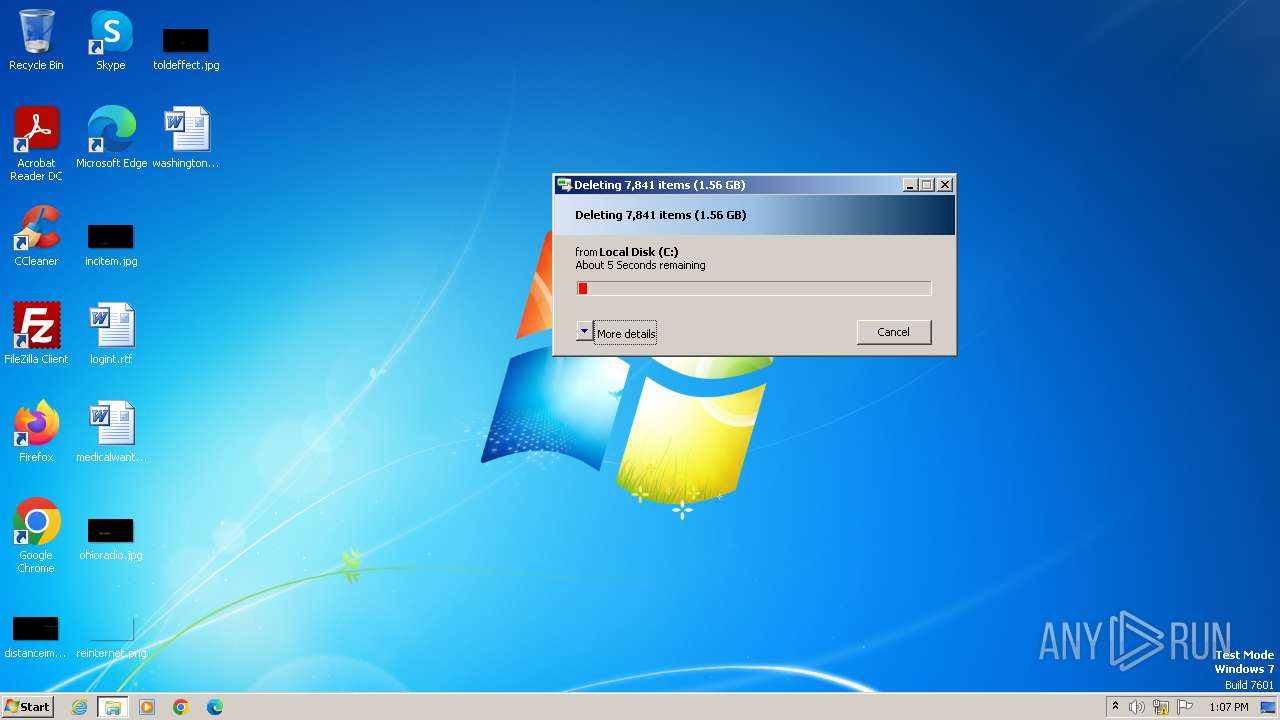
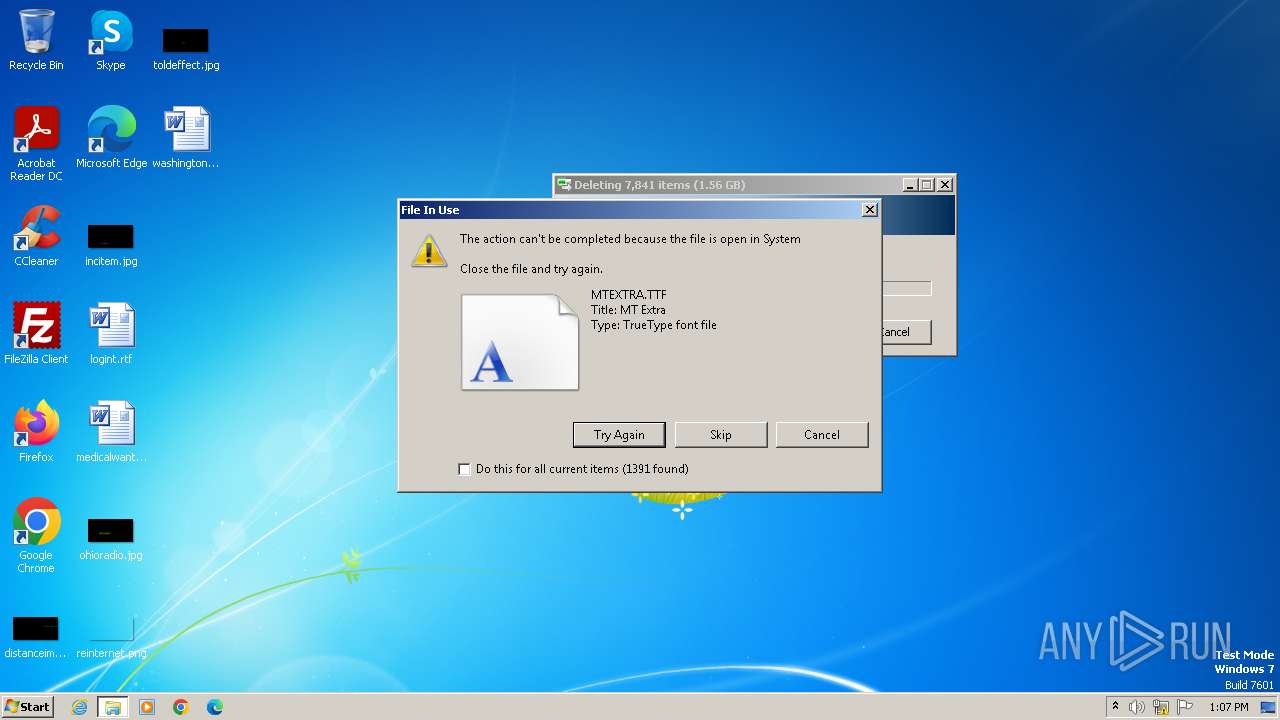
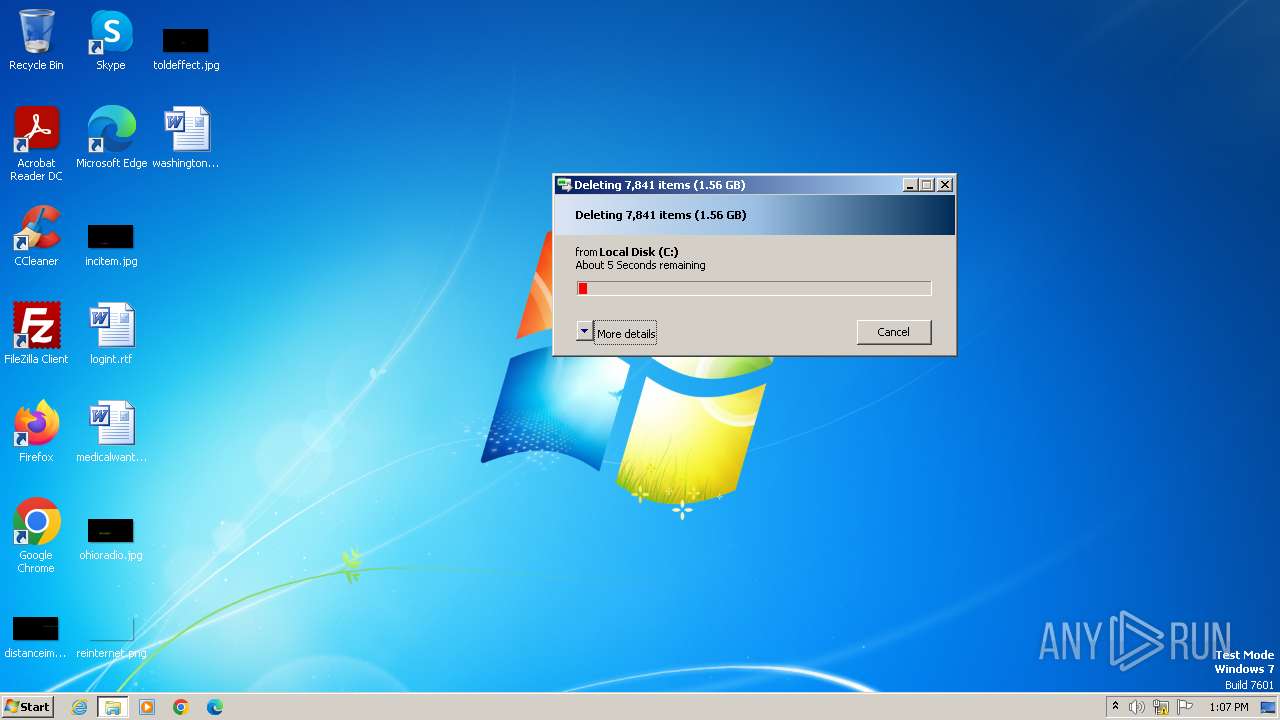
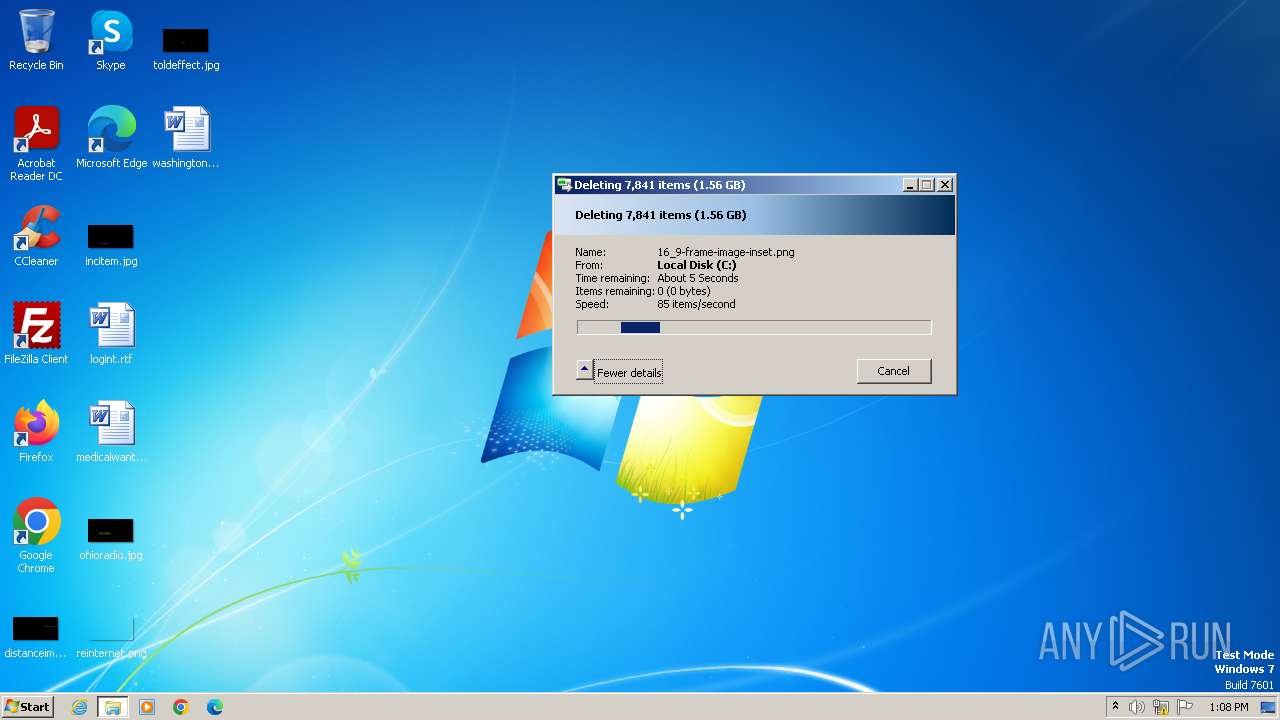
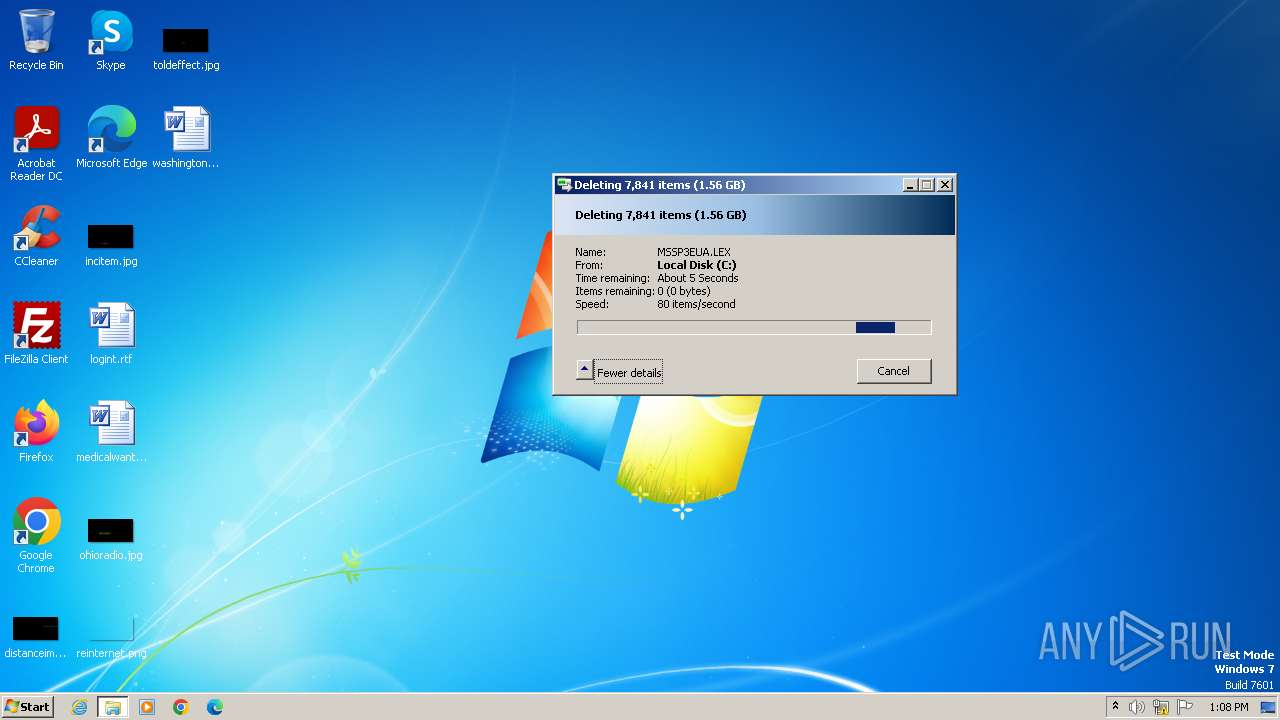
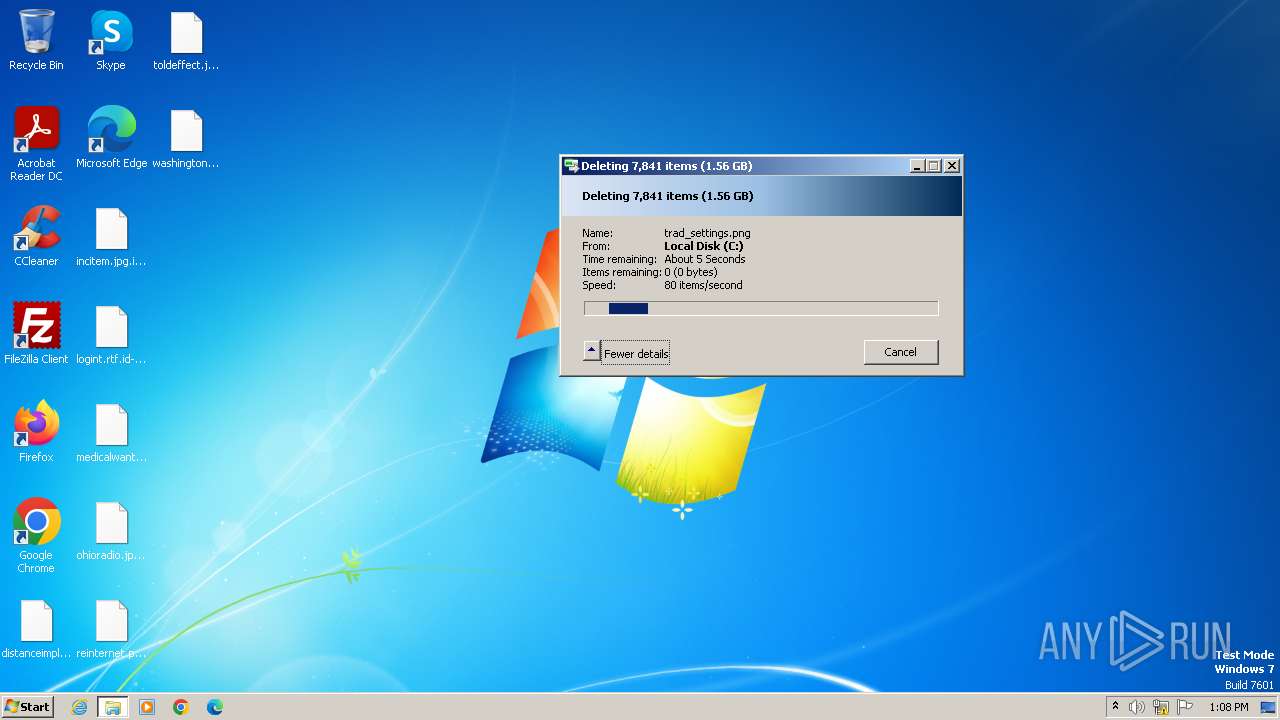
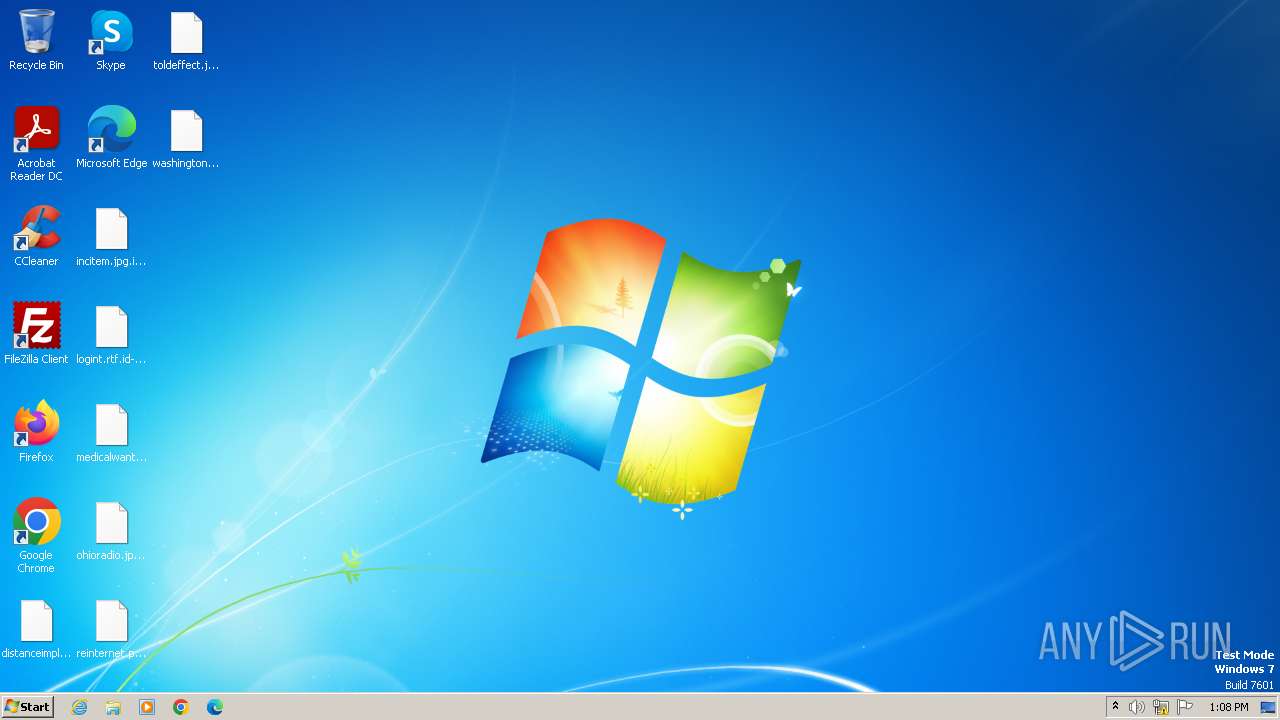
Renames files like ransomware
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
PHOBOS has been detected
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Steals credentials
- 0.exe (PID: 1628)
Dharma/Crysis is detected
- 0.exe (PID: 1628)
Modifies files in the Chrome extension folder
- 0.exe (PID: 1628)
Steals credentials from Web Browsers
- 0.exe (PID: 1628)
Actions looks like stealing of personal data
- 0.exe (PID: 1628)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3968)
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Starts CMD.EXE for commands execution
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Executable content was dropped or overwritten
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Reads the Internet Settings
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
- mshta.exe (PID: 2744)
- mshta.exe (PID: 2720)
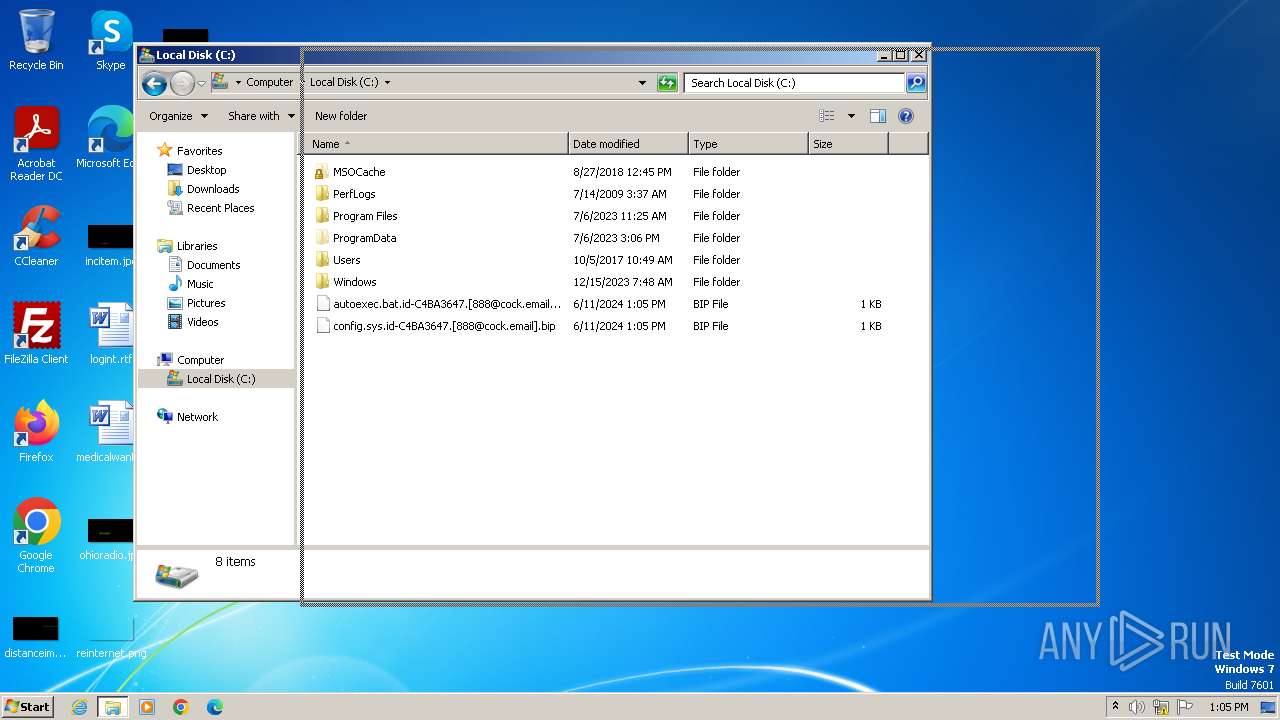
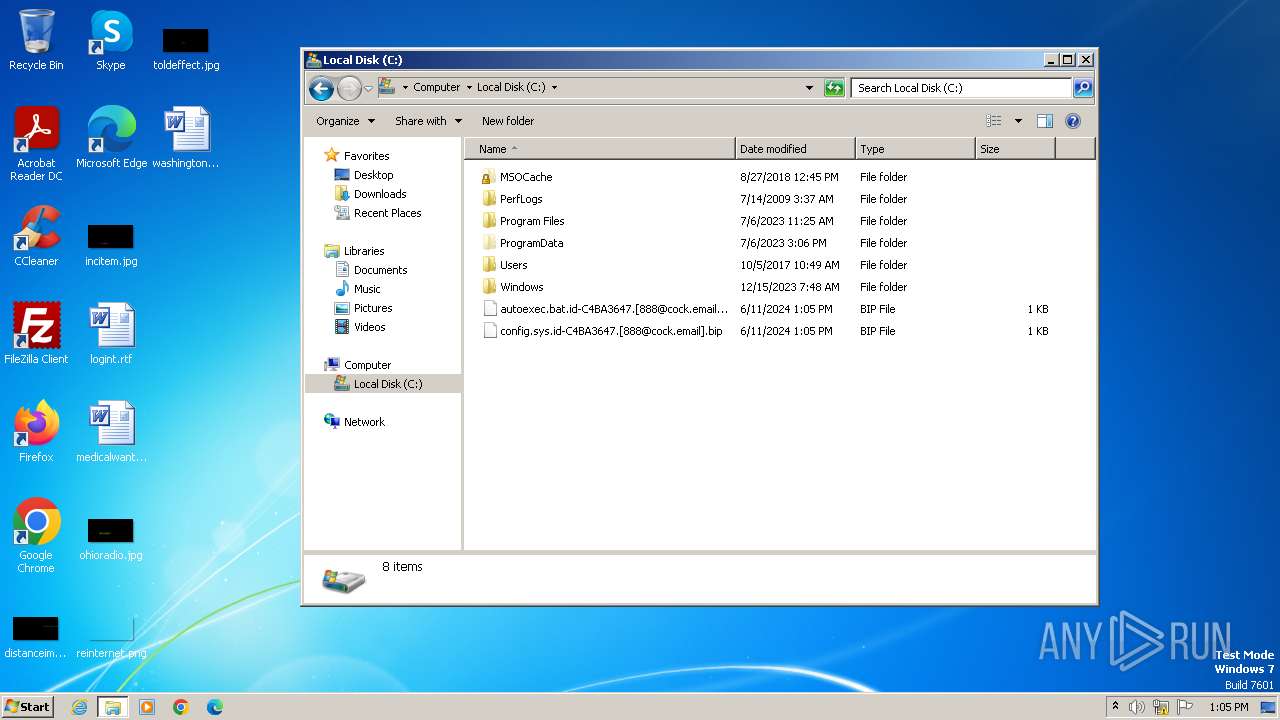
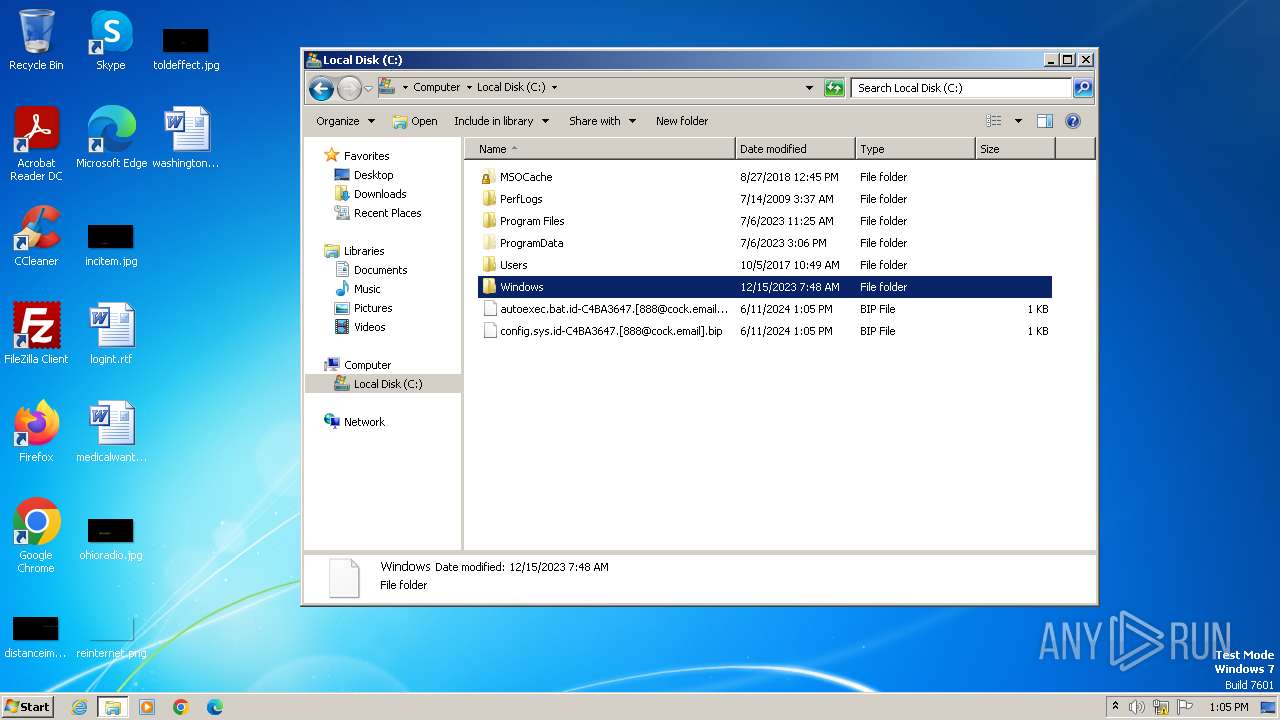
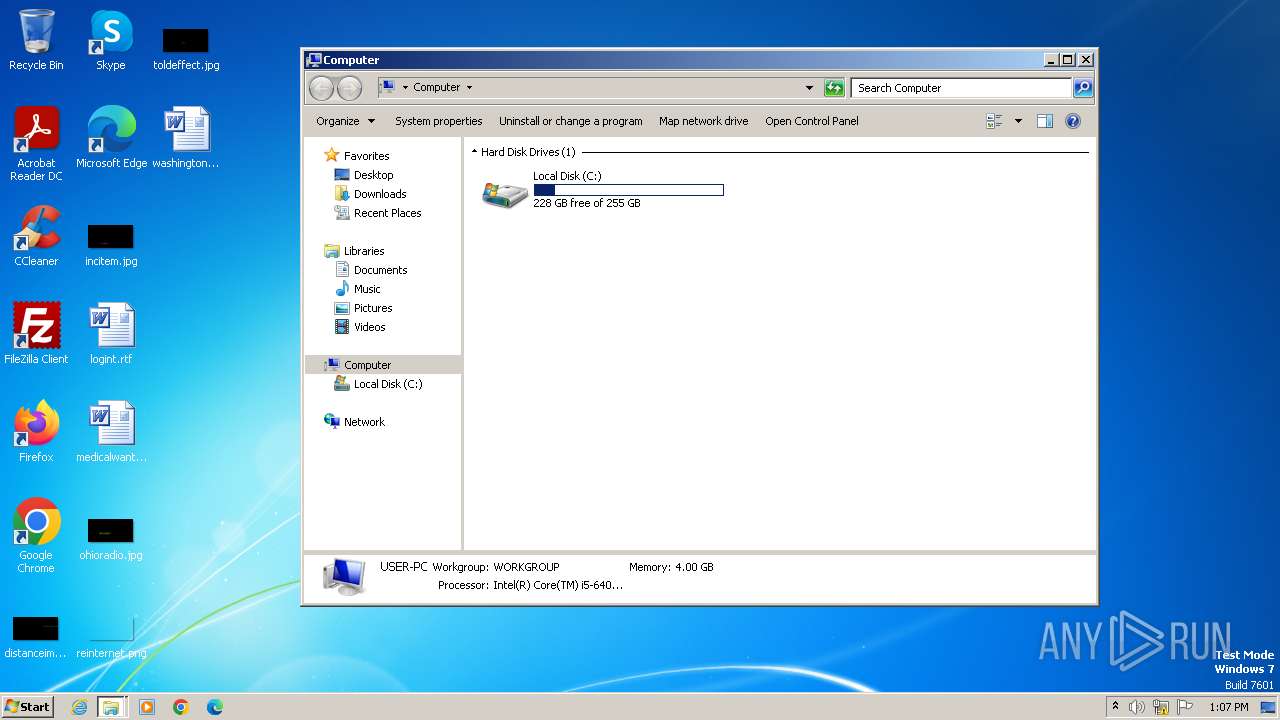
Creates file in the systems drive root
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Process drops legitimate windows executable
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Application launched itself
- 0.exe (PID: 4008)
The process creates files with name similar to system file names
- 0.exe (PID: 1628)
Reads browser cookies
- 0.exe (PID: 1628)
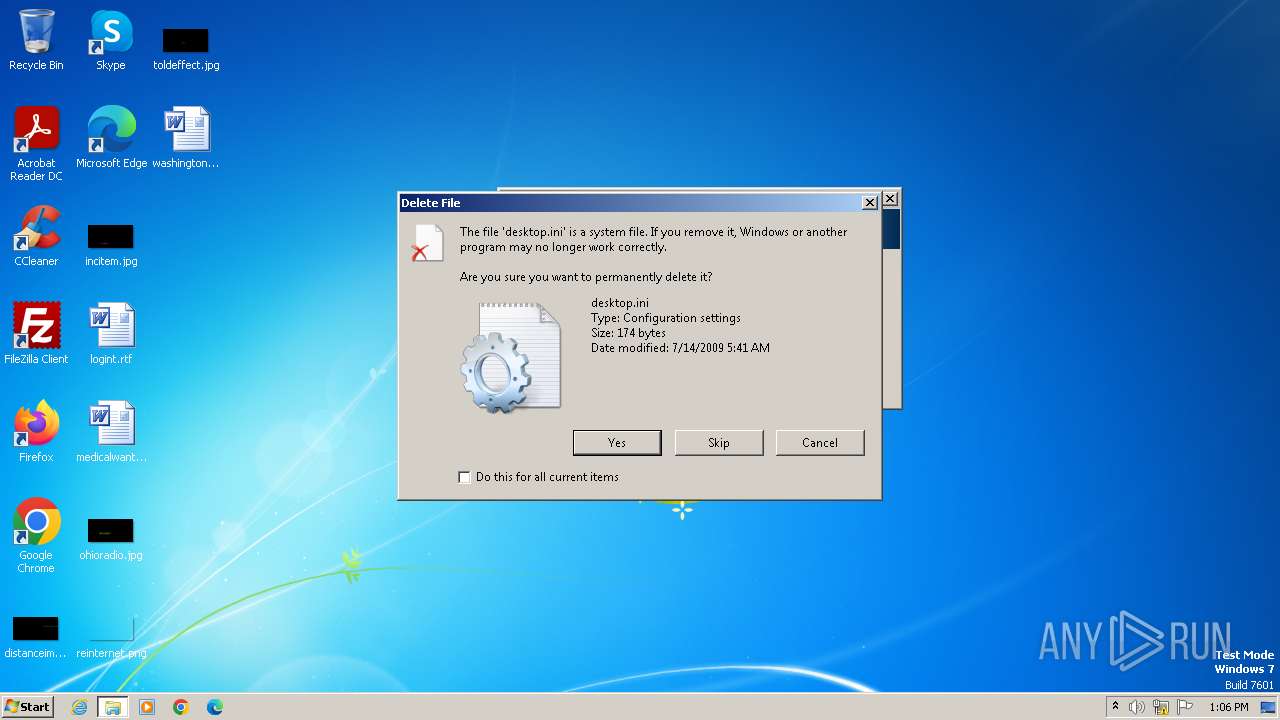
Creates files like ransomware instruction
- 0.exe (PID: 1628)
Executes as Windows Service
- VSSVC.exe (PID: 1284)
INFO
Checks supported languages
- 0.exe (PID: 4008)
- mode.com (PID: 928)
- 0.exe (PID: 1628)
- mode.com (PID: 1604)
- mode.com (PID: 1948)
- mode.com (PID: 3044)
Reads the computer name
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3968)
Creates files or folders in the user directory
- 0.exe (PID: 4008)
- 0.exe (PID: 1628)
Creates files in the program directory
- 0.exe (PID: 1628)
Create files in a temporary directory
- 0.exe (PID: 1628)
Reads Internet Explorer settings
- mshta.exe (PID: 2720)
- mshta.exe (PID: 2744)
Checks proxy server information
- mshta.exe (PID: 2744)
- mshta.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 71259 |
| ZipUncompressedSize: | 94720 |
| ZipFileName: | 2024-06-10_17ce3b6b97f4068d0b7eb0777366c3fe_crysis_dharma |
Total processes
66
Monitored processes
19
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | 0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 752 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | mode con cp select=1251 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1588 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | mode con cp select=1251 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3968.34199\0.exe" -a | C:\Users\admin\AppData\Local\Temp\Rar$EXb3968.34199\0.exe | 0.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1816 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | mode con cp select=1251 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | 0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
14 812
Read events
14 664
Write events
134
Delete events
14
Modification events
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\240610-z9paxs1frp_pw_infected.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
323
Suspicious files
10 652
Text files
41
Unknown types
343
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | 0.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab.id-C4BA3647.[888@cock.email].bip | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab.id-C4BA3647.[888@cock.email].bip | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 4008 | 0.exe | C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |