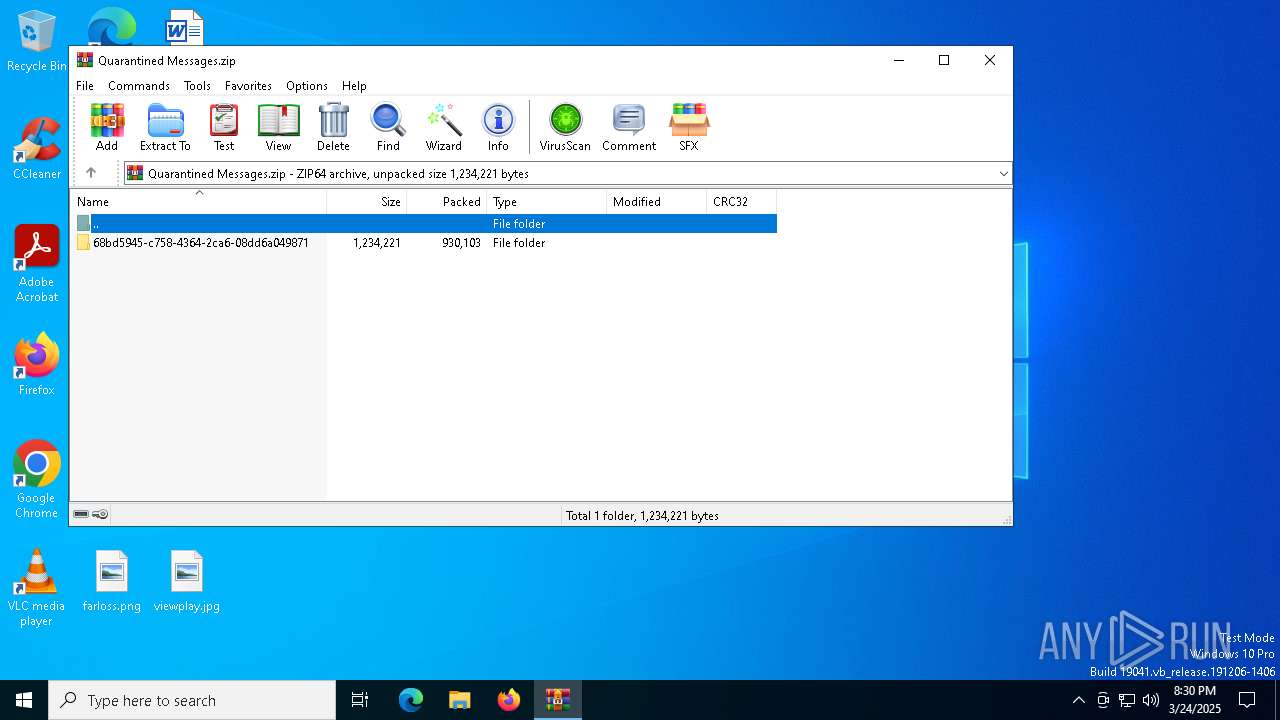
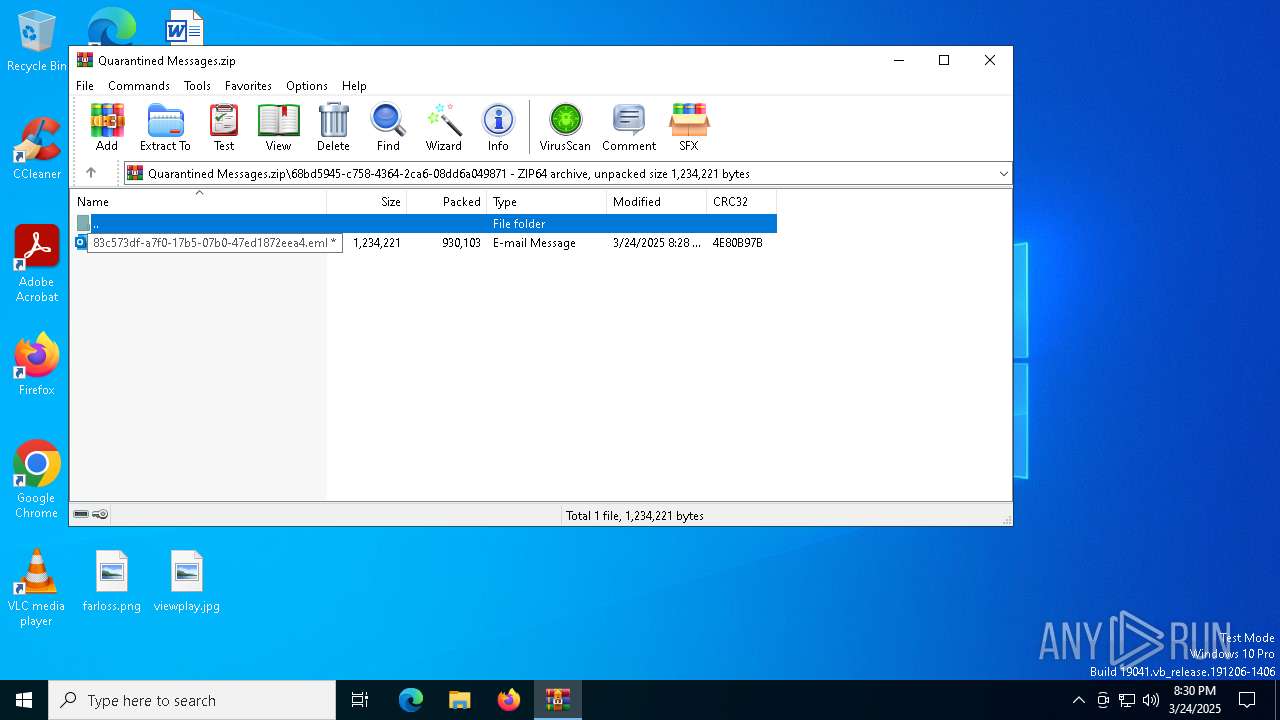
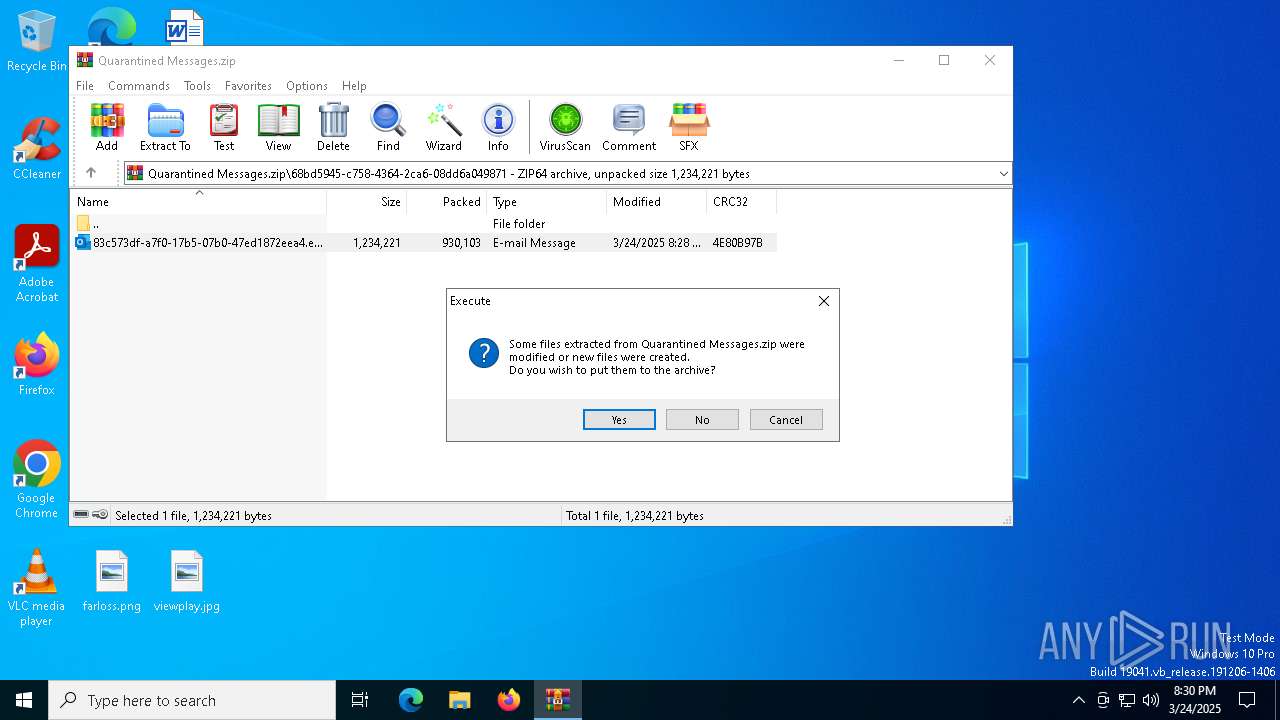
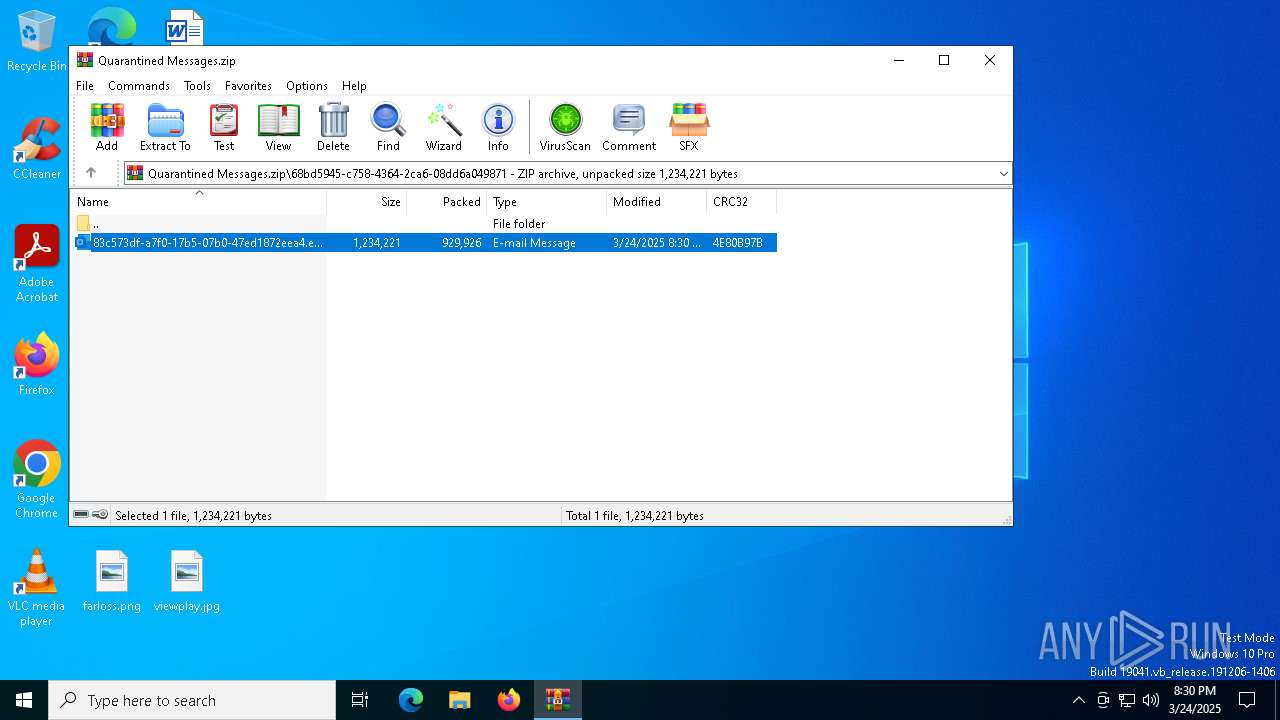
| File name: | Quarantined Messages.zip |
| Full analysis: | https://app.any.run/tasks/09277304-8f24-42f0-a0c8-7af0564266d1 |
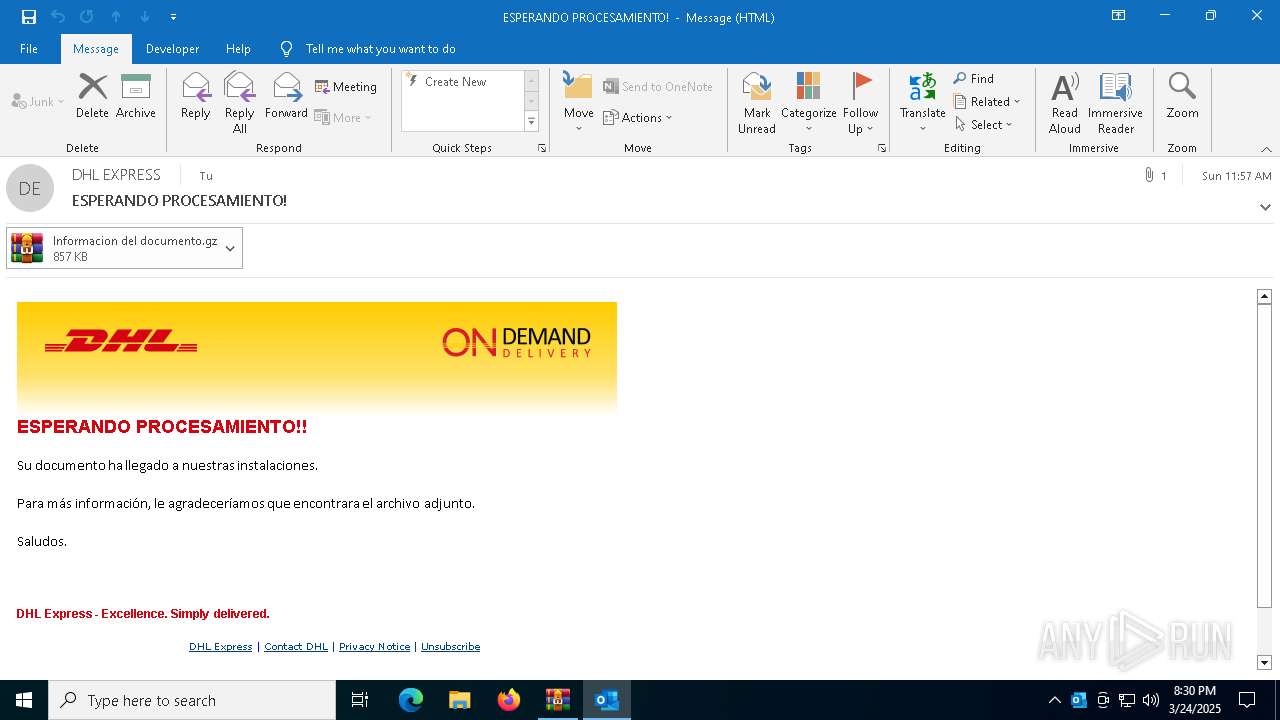
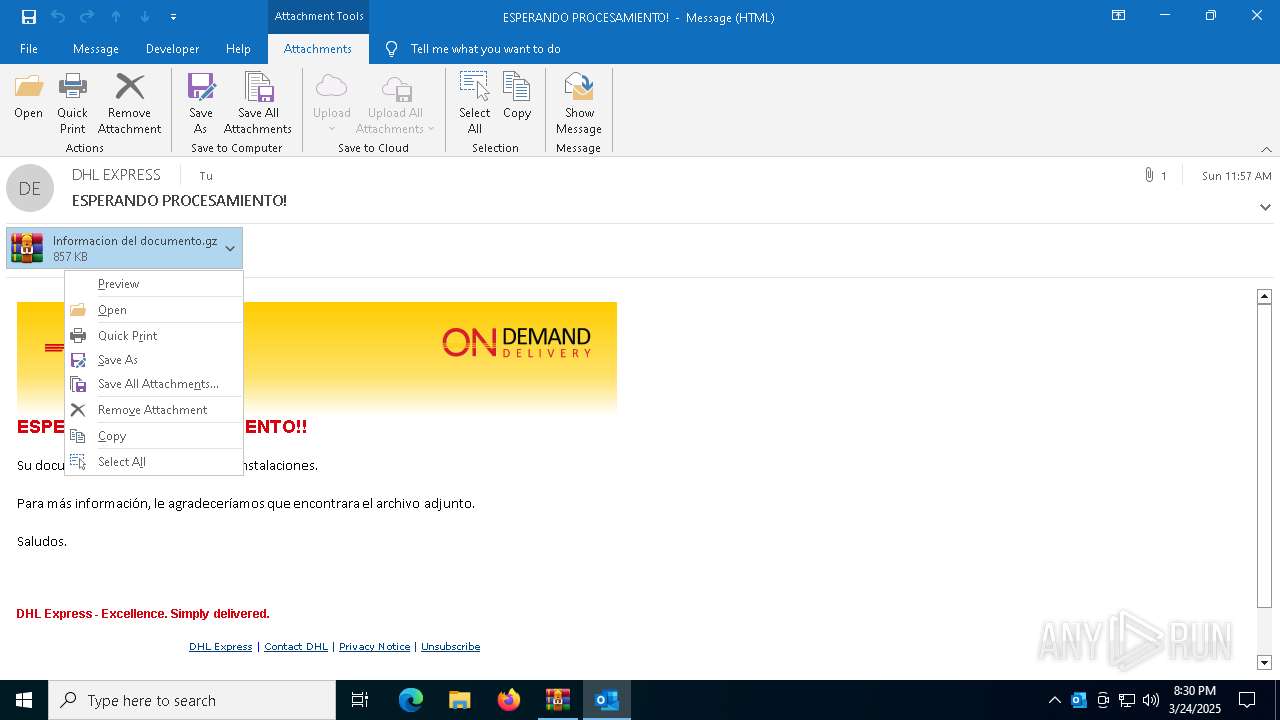
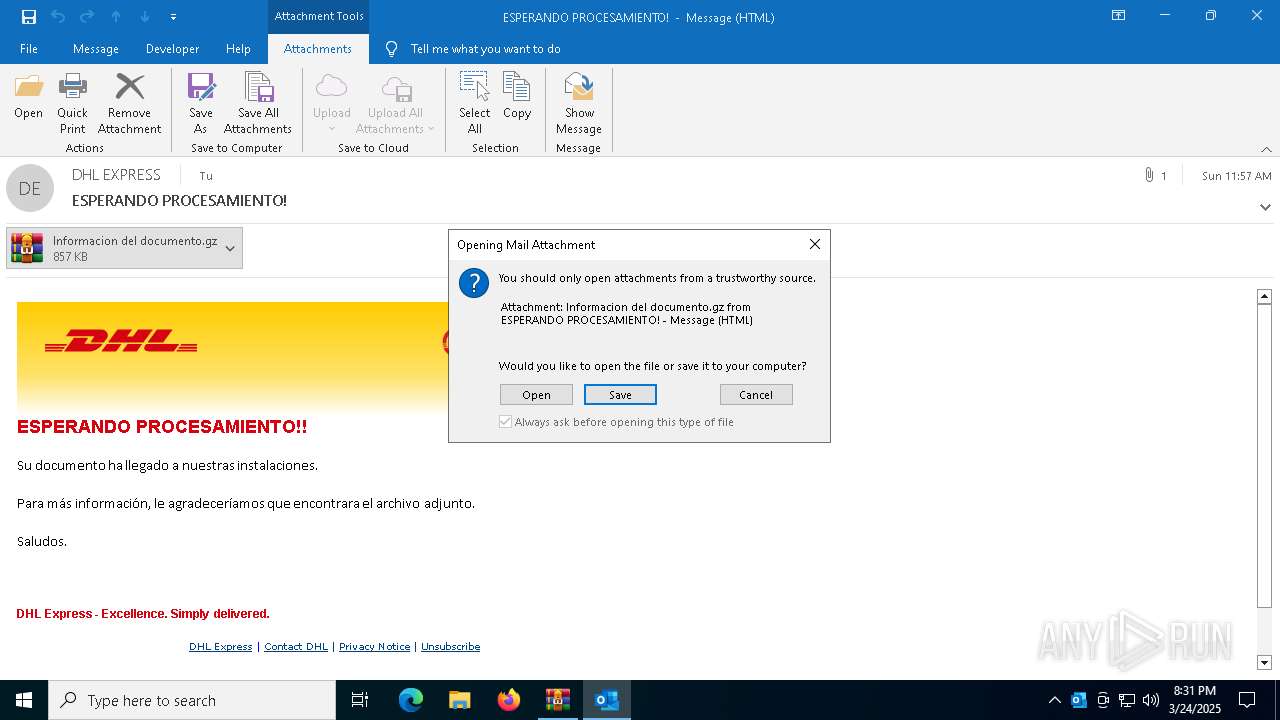
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | March 24, 2025, 20:30:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
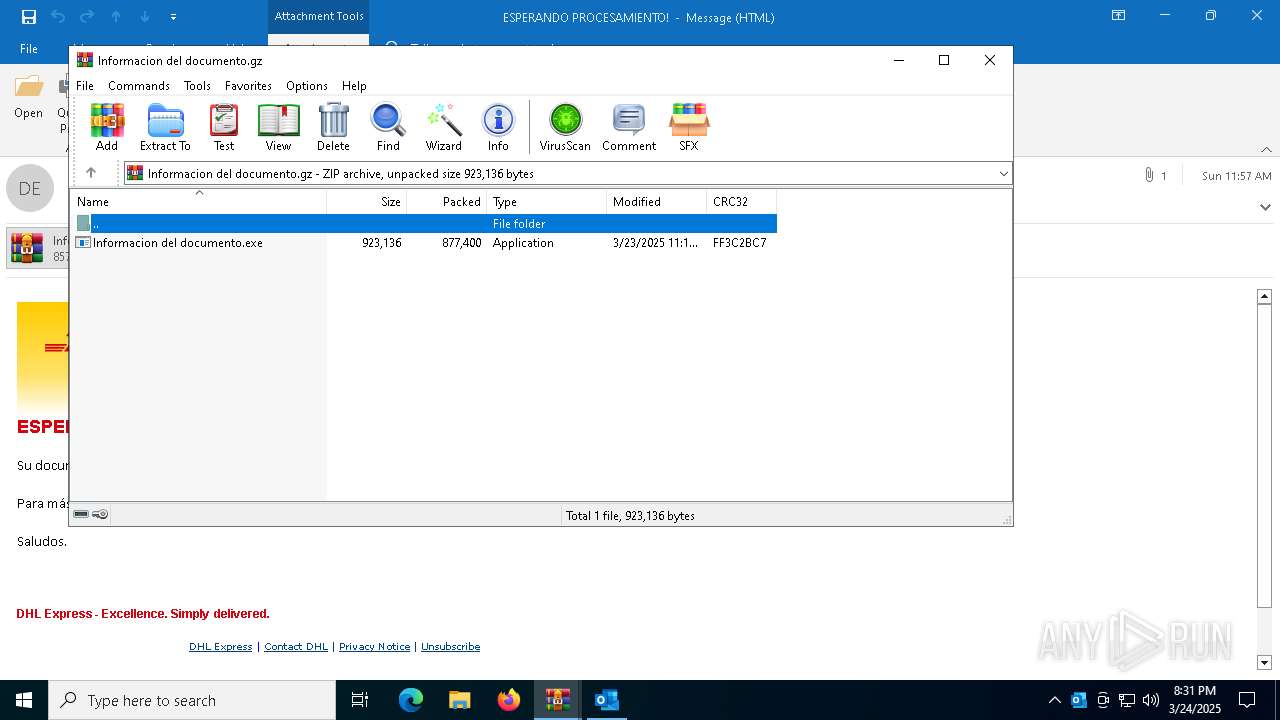
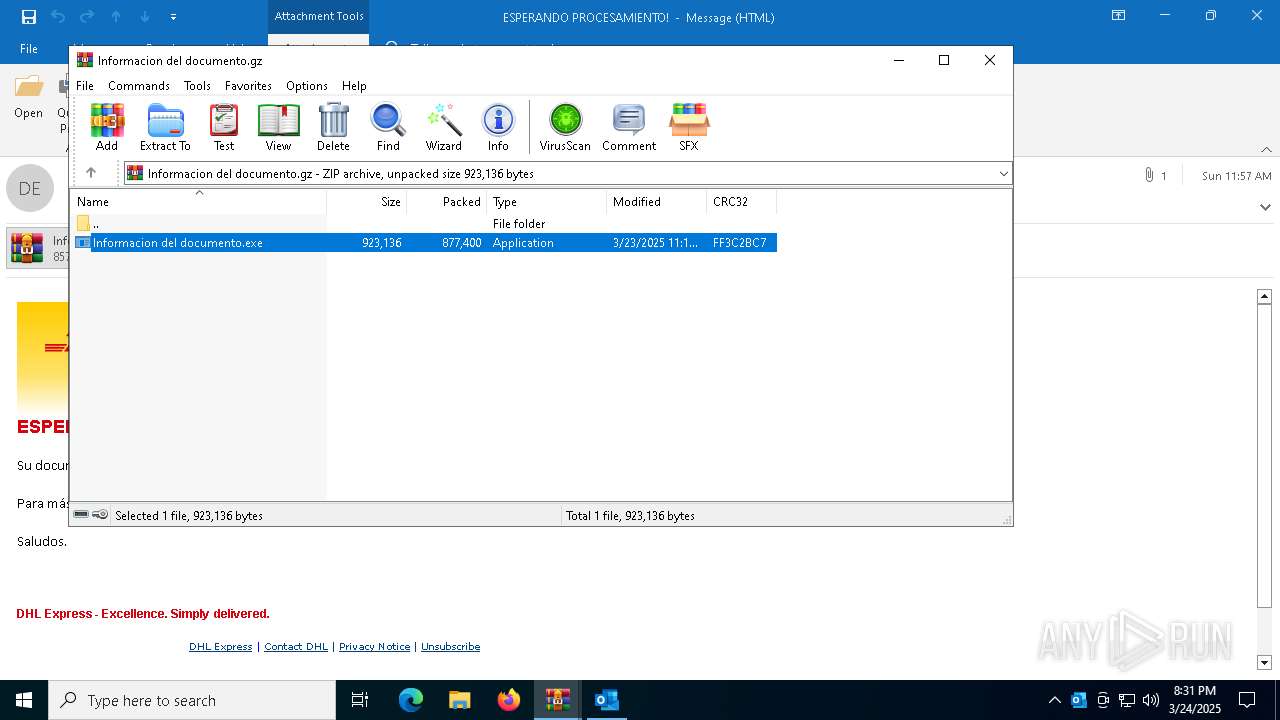
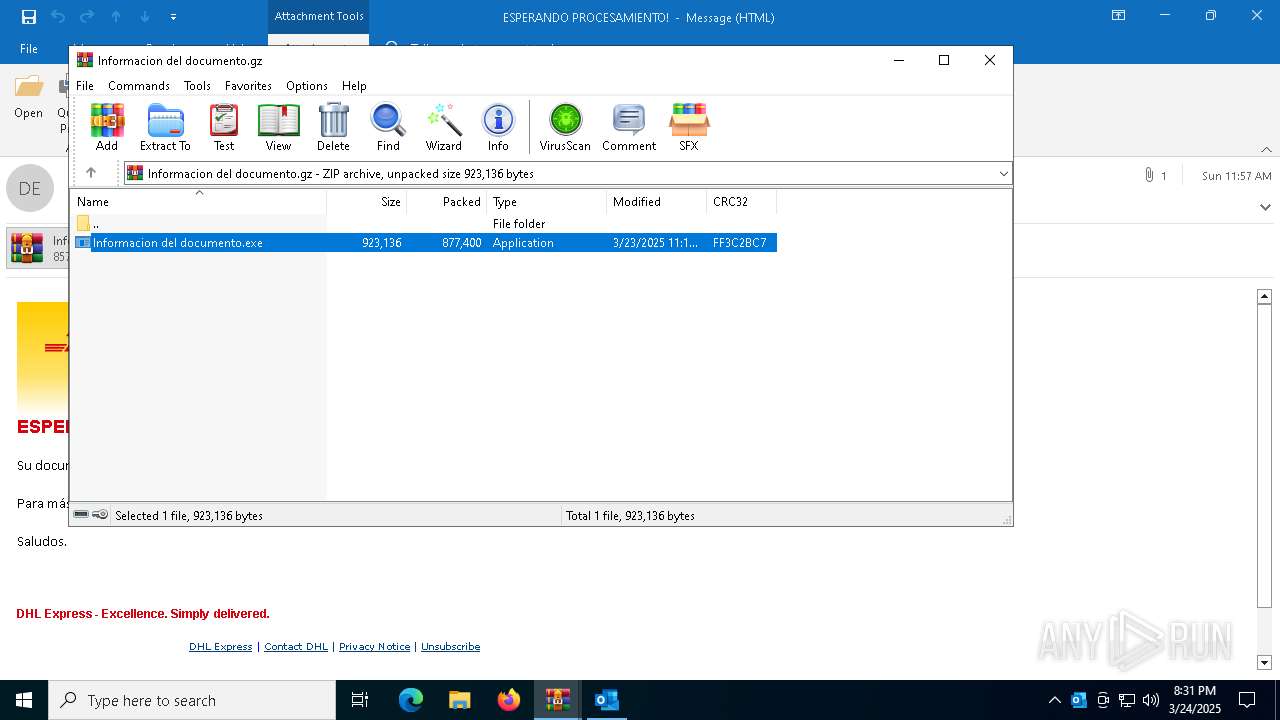
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 9E9F45F5EE755EAAC037C58A3759BDEF |
| SHA1: | 1F071E5EE40A005C3918C363AA8D8E07B9A521D9 |
| SHA256: | 81EACA07F2D2C3714AFE4F27353FB9958A9CE41489CF8A64335B041FF297BC05 |
| SSDEEP: | 49152:k+W2NgvuuUinLGvuri/Zvnfe57WTwom6PXS4s7m8sfNzD1twsG9IiUgpOJKjXDsP:KIOlLlrYZvq7WfpvSX7m8sVzDnPWIiLi |
MALICIOUS
Changes the autorun value in the registry
- Informacion del documento.exe (PID: 7476)
- updates.exe (PID: 7856)
QUASAR has been detected (YARA)
- updates.exe (PID: 7856)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 7012)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7012)
- WinRAR.exe (PID: 1244)
- ShellExperienceHost.exe (PID: 1748)
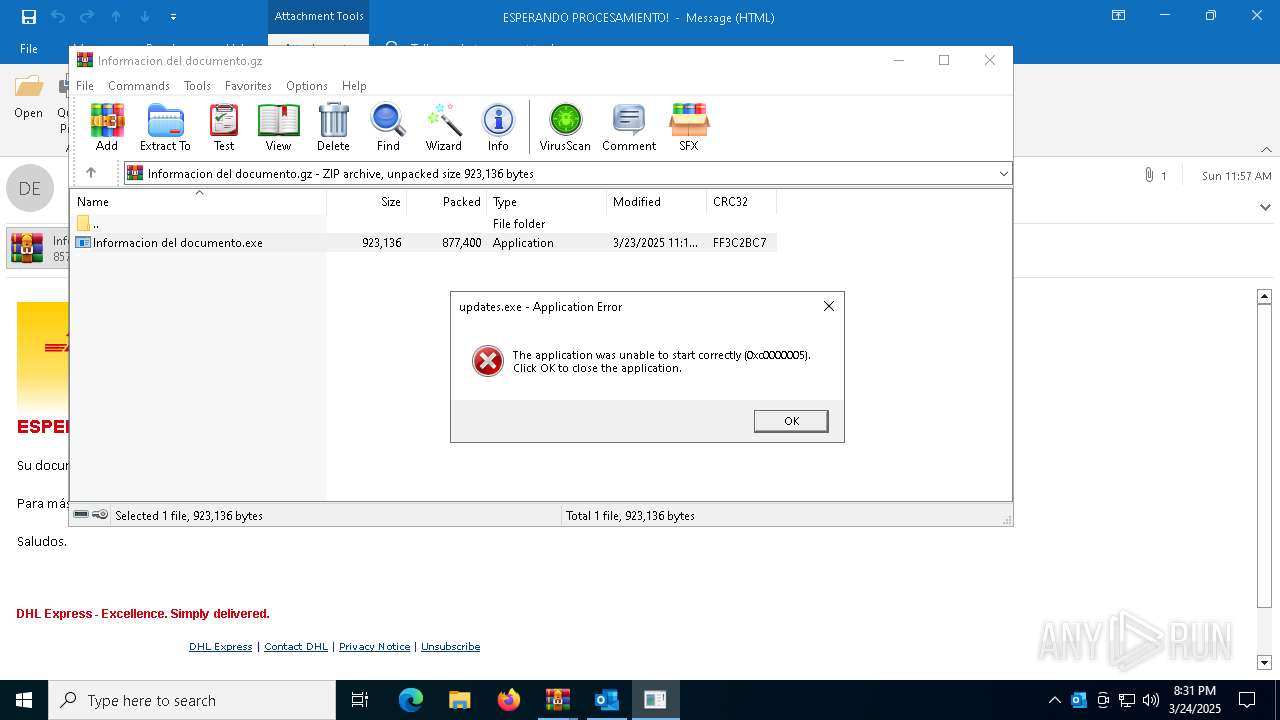
Application launched itself
- Informacion del documento.exe (PID: 7568)
- updates.exe (PID: 7256)
- Informacion del documento.exe (PID: 660)
- Informacion del documento.exe (PID: 7656)
Checks for external IP
- svchost.exe (PID: 2196)
- Informacion del documento.exe (PID: 7476)
- updates.exe (PID: 7856)
Executable content was dropped or overwritten
- Informacion del documento.exe (PID: 7476)
Starts itself from another location
- Informacion del documento.exe (PID: 7476)
Executes application which crashes
- updates.exe (PID: 7860)
There is functionality for taking screenshot (YARA)
- updates.exe (PID: 7856)
Connects to unusual port
- updates.exe (PID: 7856)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8044)
- BackgroundTransferHost.exe (PID: 516)
- BackgroundTransferHost.exe (PID: 7328)
- BackgroundTransferHost.exe (PID: 6080)
- BackgroundTransferHost.exe (PID: 7840)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7012)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7328)
- Informacion del documento.exe (PID: 7476)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7328)
- Informacion del documento.exe (PID: 7476)
- updates.exe (PID: 7856)
- slui.exe (PID: 5512)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7328)
- slui.exe (PID: 7268)
- slui.exe (PID: 5512)
Checks supported languages
- Informacion del documento.exe (PID: 7568)
- Informacion del documento.exe (PID: 7476)
- Informacion del documento.exe (PID: 7464)
- updates.exe (PID: 7256)
- updates.exe (PID: 7856)
- Informacion del documento.exe (PID: 660)
- Informacion del documento.exe (PID: 6036)
- Informacion del documento.exe (PID: 2852)
- Informacion del documento.exe (PID: 7500)
- ShellExperienceHost.exe (PID: 1748)
- Informacion del documento.exe (PID: 7656)
- Informacion del documento.exe (PID: 6584)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1244)
Reads the machine GUID from the registry
- Informacion del documento.exe (PID: 7568)
- Informacion del documento.exe (PID: 7476)
- Informacion del documento.exe (PID: 7464)
- updates.exe (PID: 7256)
- Informacion del documento.exe (PID: 660)
- Informacion del documento.exe (PID: 2852)
- Informacion del documento.exe (PID: 6036)
- updates.exe (PID: 7856)
- Informacion del documento.exe (PID: 7500)
- Informacion del documento.exe (PID: 6584)
- Informacion del documento.exe (PID: 7656)
Reads the computer name
- Informacion del documento.exe (PID: 7568)
- Informacion del documento.exe (PID: 7476)
- Informacion del documento.exe (PID: 7464)
- updates.exe (PID: 7256)
- updates.exe (PID: 7856)
- Informacion del documento.exe (PID: 660)
- Informacion del documento.exe (PID: 2852)
- Informacion del documento.exe (PID: 6036)
- ShellExperienceHost.exe (PID: 1748)
- Informacion del documento.exe (PID: 7500)
- Informacion del documento.exe (PID: 6584)
- Informacion del documento.exe (PID: 7656)
Disables trace logs
- Informacion del documento.exe (PID: 7476)
- updates.exe (PID: 7856)
Confuser has been detected (YARA)
- updates.exe (PID: 7856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(7856) updates.exe
Version1.3.0.0
C2 (4)fortyfive5.ydns.eu:61539
seventyfive75.ydns.eu:61539
fortyfivev.crabdance.com:61540
Sub_Dirwindows
Install_Nameupdates.exe
MutexQSR_MUTEX_5Kh4llnQQz8E6x39sb
Startupwindows espdater
TagStroy8
LogDirLogs
Signature
Certificate
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 20:28:34 |
| ZipCRC: | 0x4e80b97b |
| ZipCompressedSize: | 4294967295 |
| ZipUncompressedSize: | 4294967295 |
| ZipFileName: | 68bd5945-c758-4364-2ca6-08dd6a049871/83c573df-a7f0-17b5-07b0-47ed1872eea4.eml |
Total processes
172
Monitored processes
27
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1244.8884\Informacion del documento.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1244.8884\Informacion del documento.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Edge update Integrity Level: MEDIUM Description: Edge update Exit code: 0 Version: 2.3.6.6 Modules
| |||||||||||||||
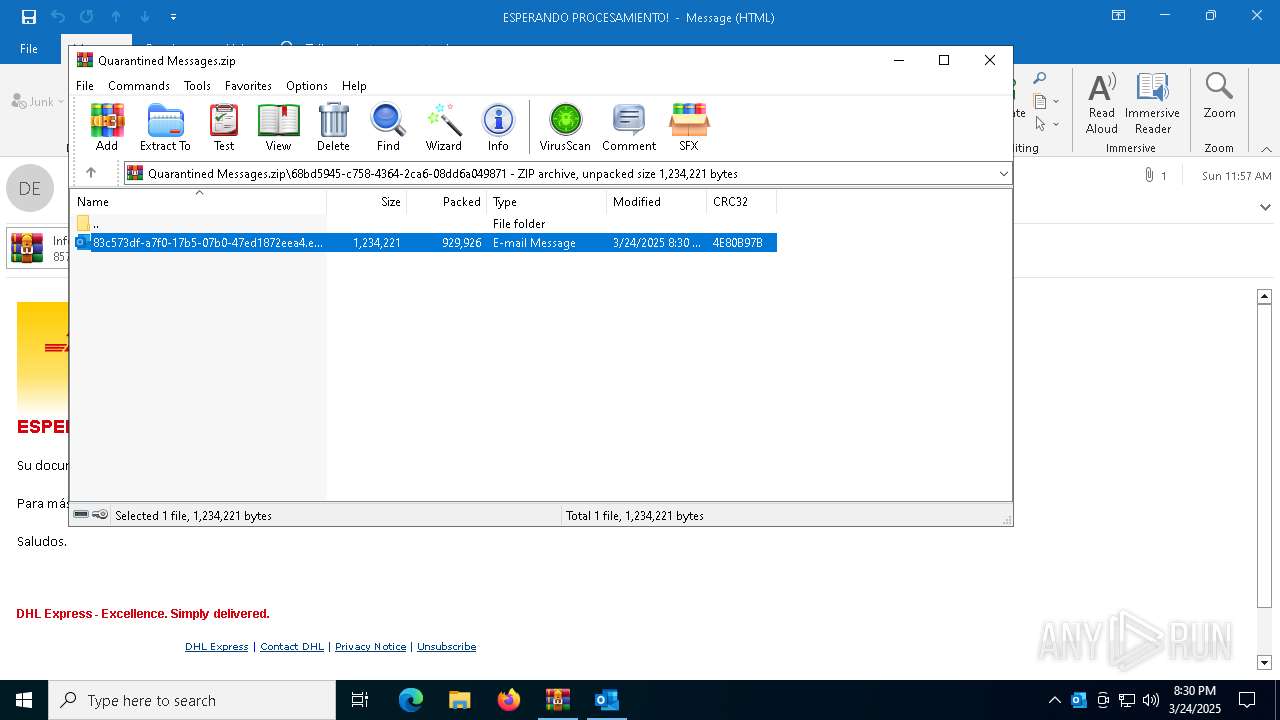
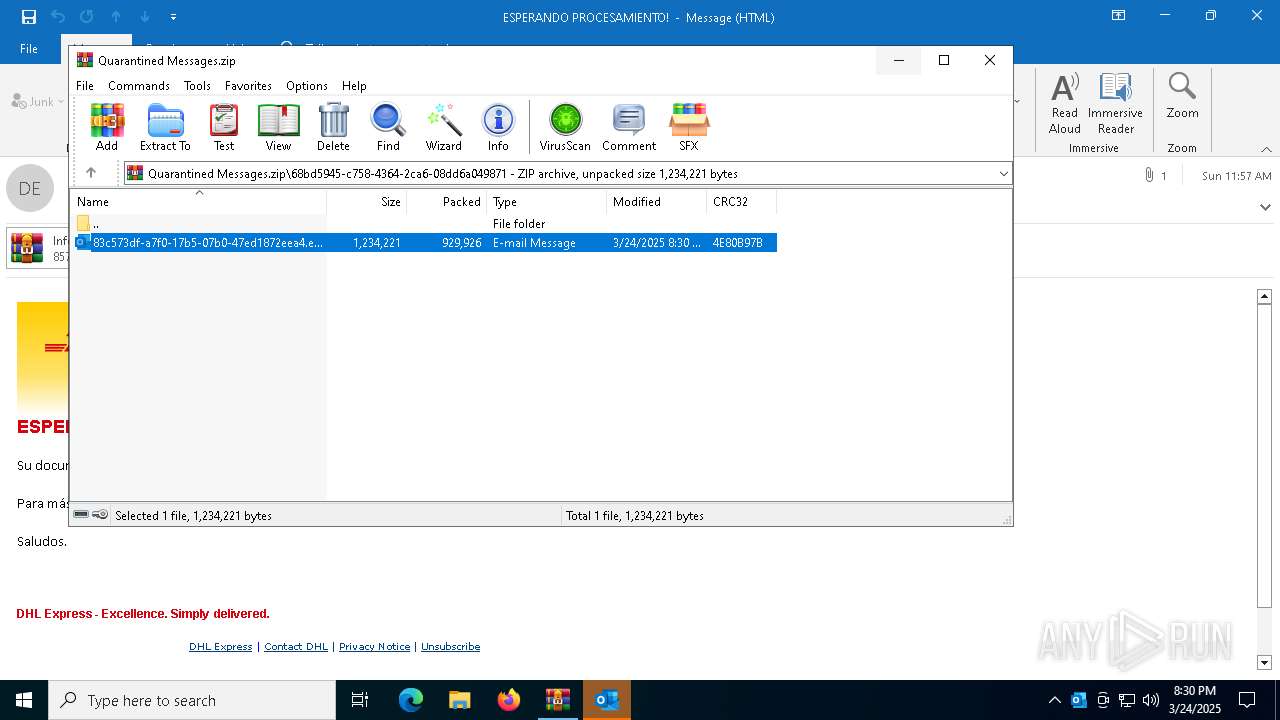
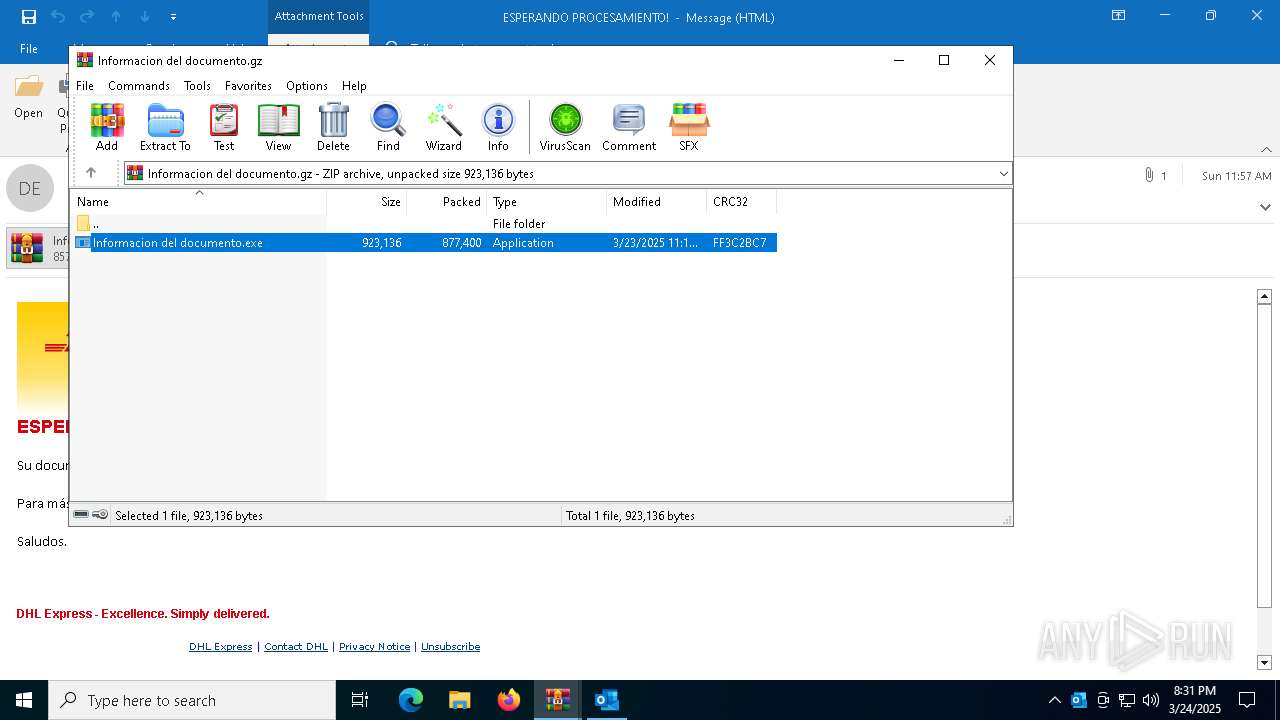
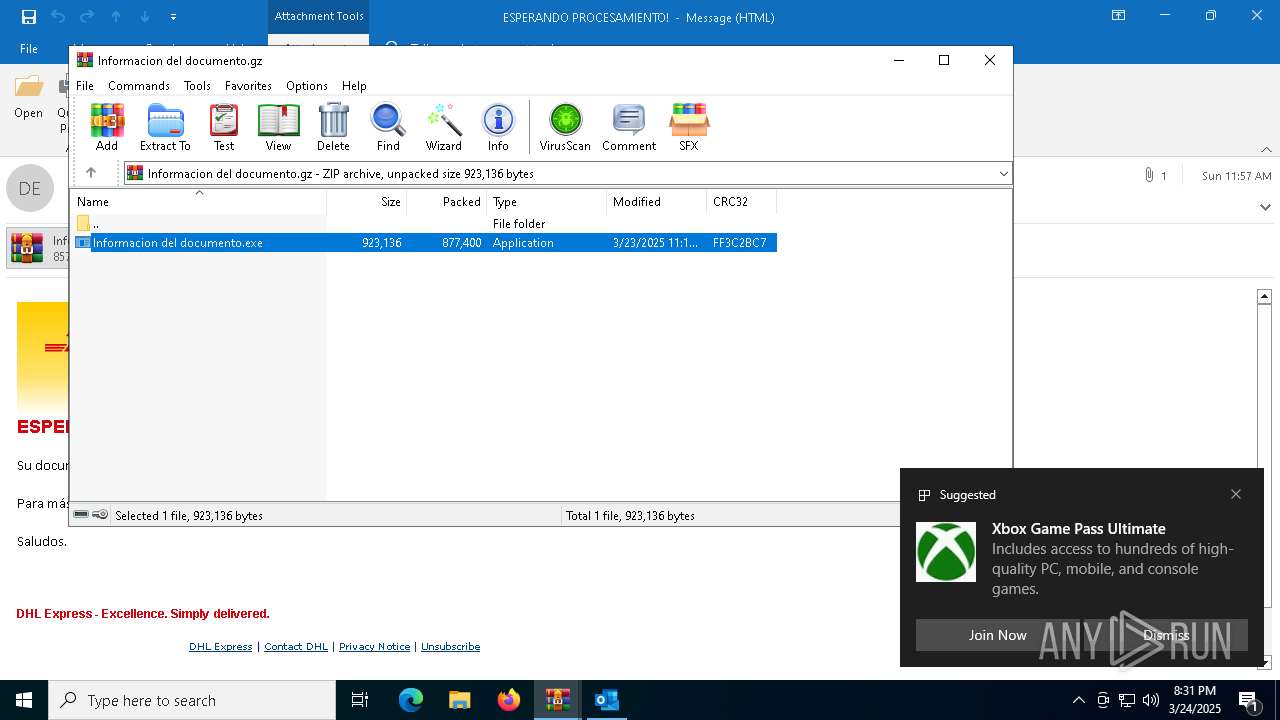
| 1244 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\F5EOXEGQ\Informacion del documento.gz" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1244.8884\Informacion del documento.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1244.8884\Informacion del documento.exe | — | Informacion del documento.exe | |||||||||||
User: admin Company: Edge update Integrity Level: MEDIUM Description: Edge update Exit code: 0 Version: 2.3.6.6 Modules
| |||||||||||||||
| 5384 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "D235E3AB-DF36-487C-A295-636F37D212A6" "75838F26-6324-4E4A-85E7-0D95241F52C4" "7980" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 5512 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6036 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1244.8884\Informacion del documento.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1244.8884\Informacion del documento.exe | — | Informacion del documento.exe | |||||||||||
User: admin Company: Edge update Integrity Level: MEDIUM Description: Edge update Exit code: 0 Version: 2.3.6.6 Modules
| |||||||||||||||
| 6080 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 063
Read events
24 747
Write events
1 160
Delete events
156
Modification events
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Quarantined Messages.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
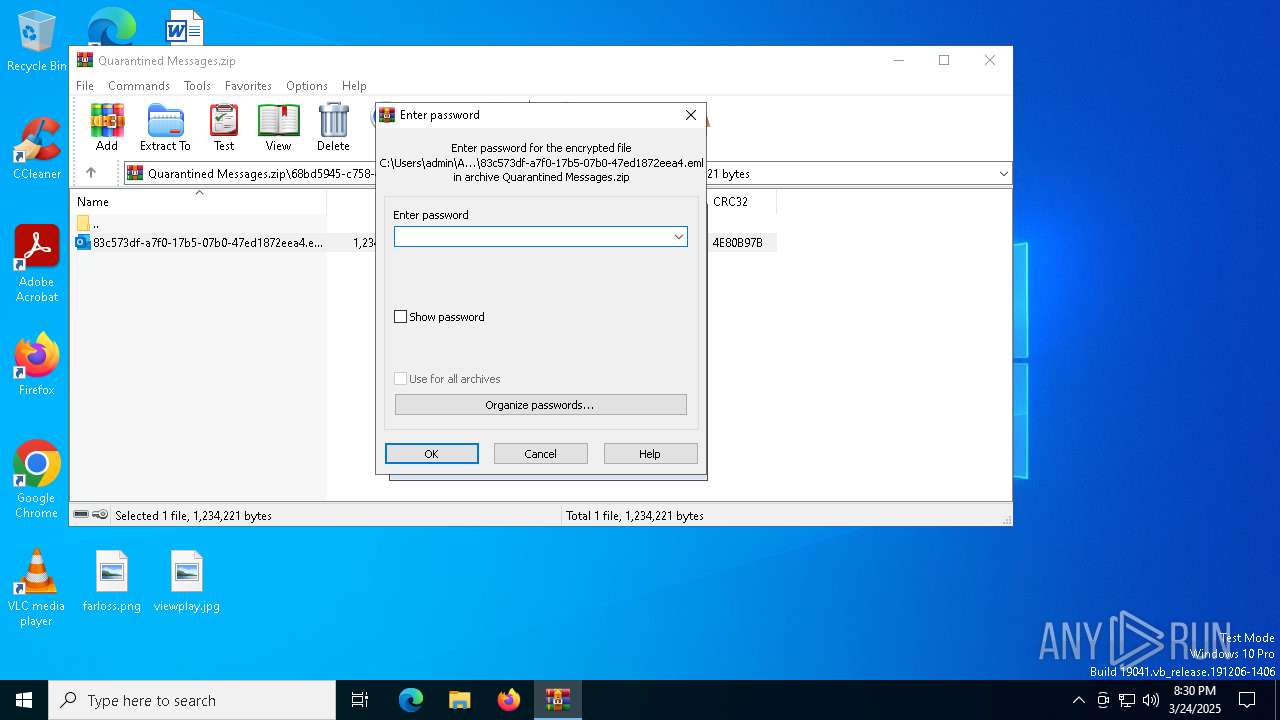
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
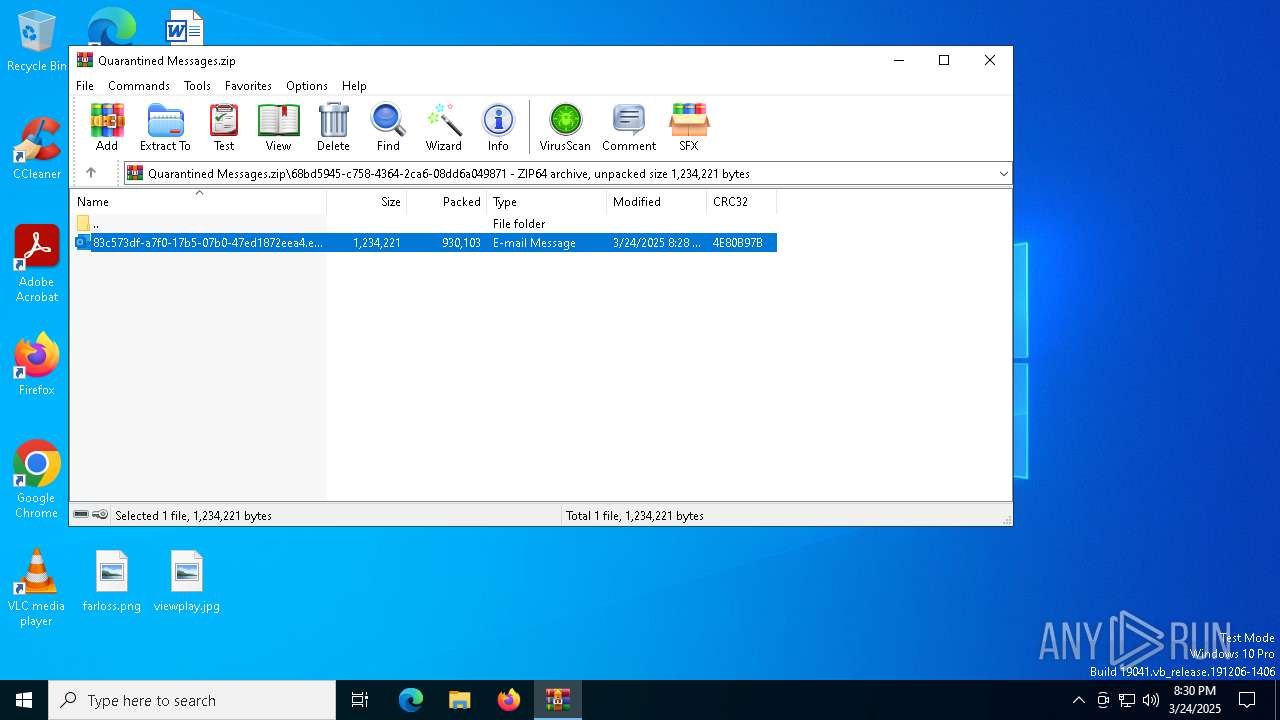
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
Executable files
4
Suspicious files
19
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7980 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f2d78b61-79ff-4241-a09f-c9ba7c663e0f.down_data | — | |
MD5:— | SHA256:— | |||
| 7980 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:C5A5E4398E677138D454617351946C35 | SHA256:9649ACA150E59E584924E0AF2E9D753523A4C112B7047FA5C03D54D3371ABBA5 | |||
| 7980 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olkF743.tmp | binary | |
MD5:9FC6294072F49C2046F88DDB669FB6D9 | SHA256:F1243E77B0E8BDA957D63485B9A6544B02E48B8885CA4EC8039B0F8C117720EF | |||
| 7980 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:FC7CE799BB9D6DBD09514CBDCF9823EA | SHA256:AF84F34F2819460B1924067971FB4818F5895F0F2335B86C983CD01133D4B05E | |||
| 7012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Quarantined Messages.zip | compressed | |
MD5:F6313ACC7BD90040B3BCD57B54D0E842 | SHA256:873CBB94C787D38917D5BD3D7890175B1D4709E7A3C44AACF313C73CC333AF73 | |||
| 7980 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\3468850E-D86C-4D8C-8A52-DC8EF9A8FCFA | xml | |
MD5:A130C9F13047005099C64E845D8B247B | SHA256:8E5C26099AD0654E0C5846E56D500B8B49F34C15224991153E4759B233CF30A5 | |||
| 7012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7012.4537\83c573df-a7f0-17b5-07b0-47ed1872eea4.eml:OECustomProperty | binary | |
MD5:2C3AB378DE7F21640A5252433F067B3C | SHA256:B064787ADF734160C6D15F72B96E8A1DDF4B93FC9DE90B8299E4C8BA7191E14F | |||
| 7012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7012.4537\83c573df-a7f0-17b5-07b0-47ed1872eea4.eml | binary | |
MD5:556EA9D3C86BB849E9F0CF9D75ED3E3F | SHA256:53B823F0ADBD5E113F3DA25C9361E8DC2E1DBC5EBCD3789C8ADE6C1469DD02A9 | |||
| 7980 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\7846CAC3.dat | image | |
MD5:177C95AF18F2A426E0190D1526923FA5 | SHA256:9B5363F08DBF741CFD712D4663E730293D3F852FD0D17E02C1EDDA7506CED76A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
241
DNS requests
30
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.159:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7456 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7328 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7980 | OUTLOOK.EXE | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7512 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7512 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7980 | OUTLOOK.EXE | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7476 | Informacion del documento.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
7856 | updates.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.159:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7456 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7456 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7476 | Informacion del documento.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7476 | Informacion del documento.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
7856 | updates.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
7856 | updates.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Dynamic DNS Service (ydns .eu) |
— | — | Misc activity | INFO [ANY.RUN] Dynamic DNS Service (ydns .eu) |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.crabdance .com Domain |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain ( .crabdance .com) |