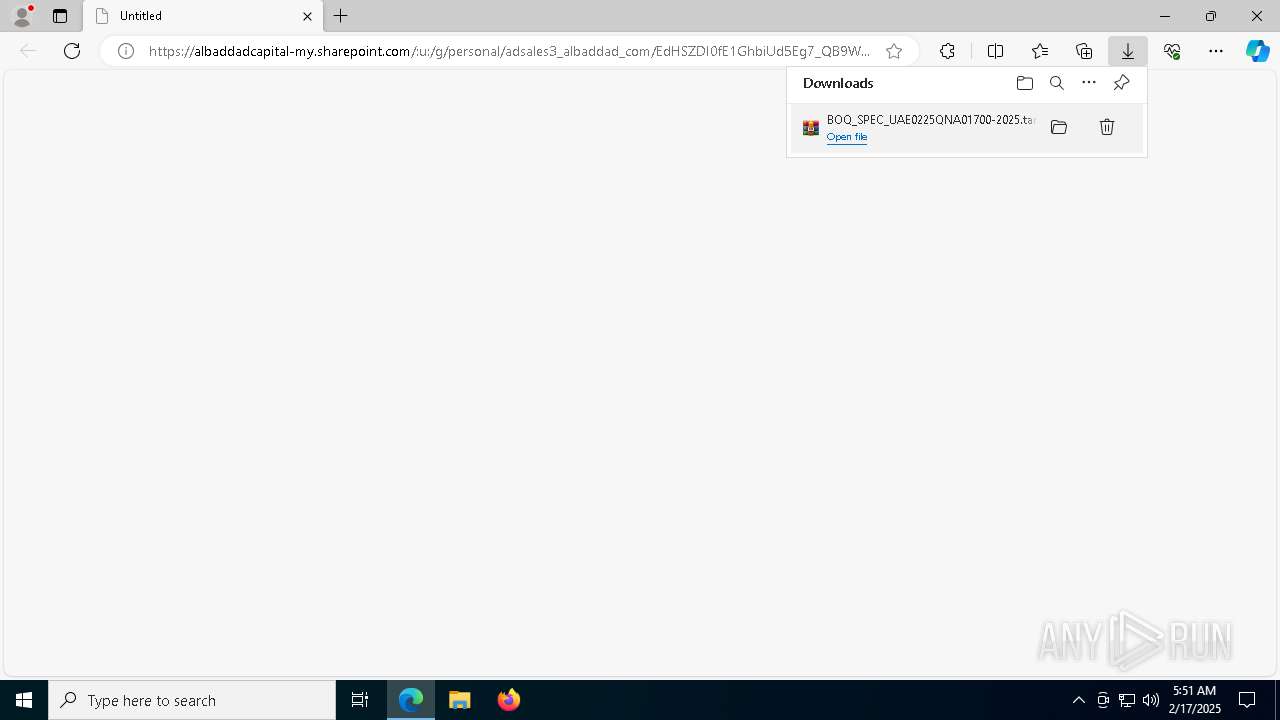
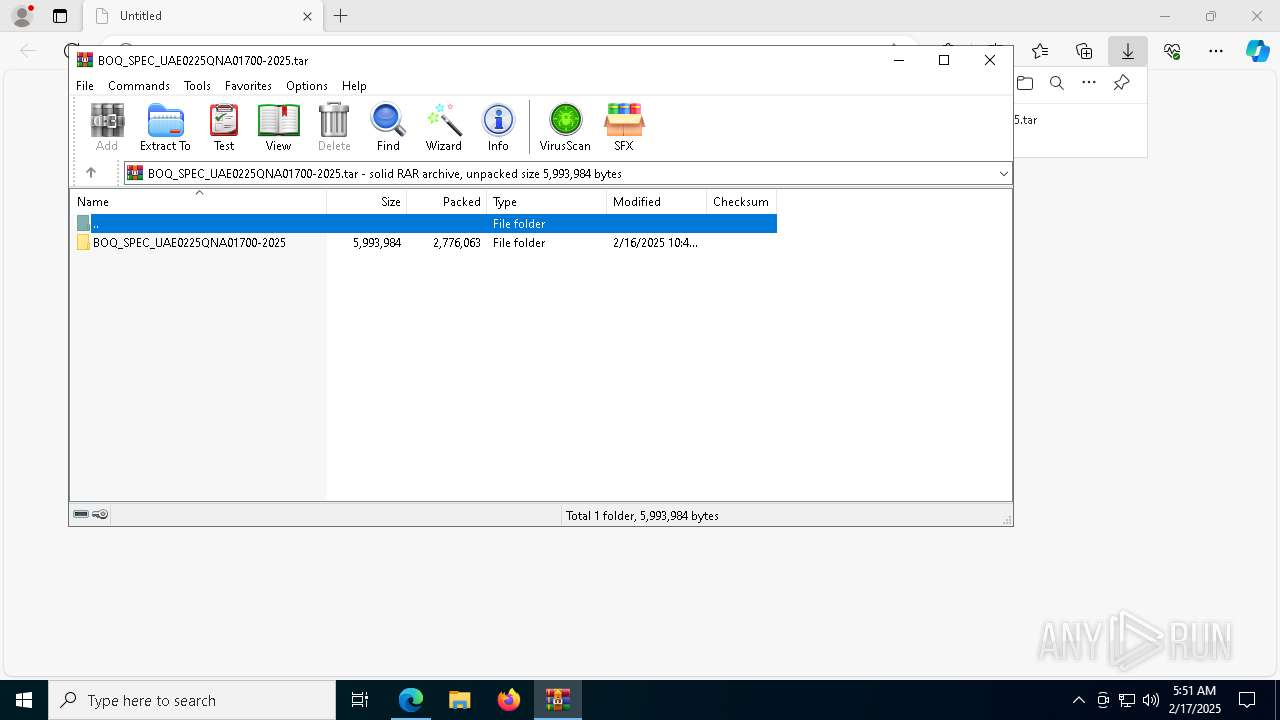
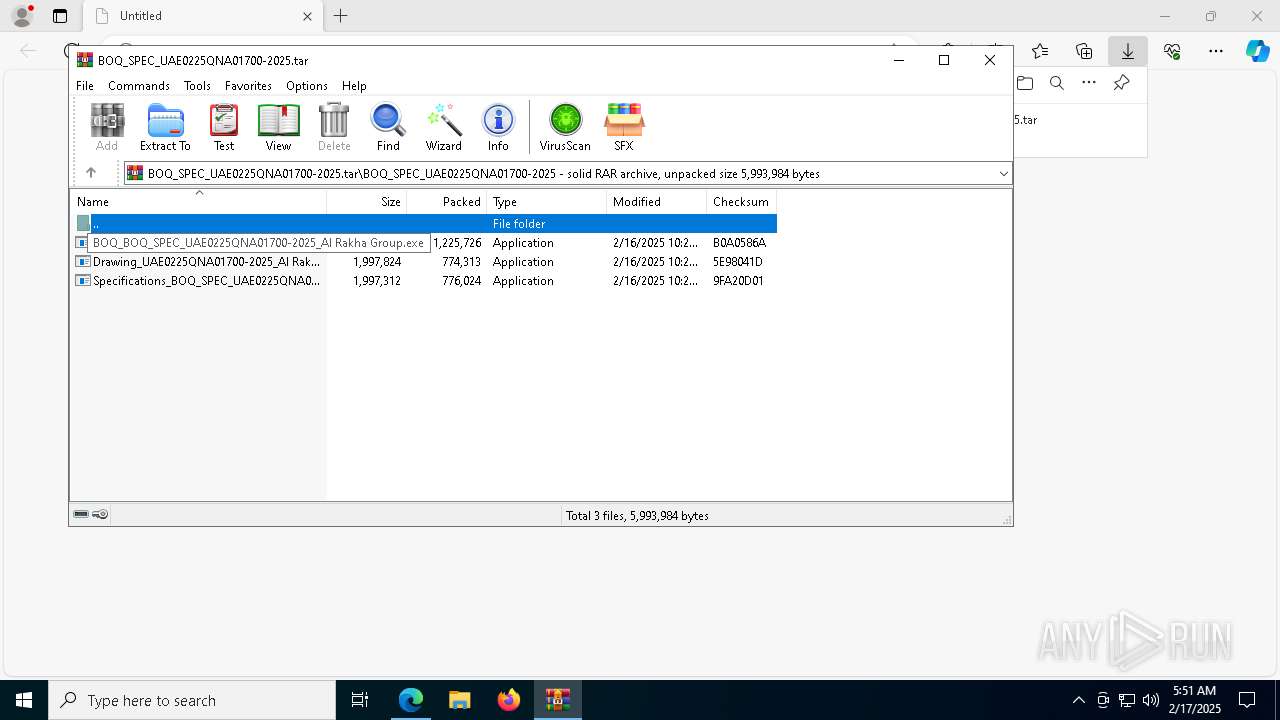
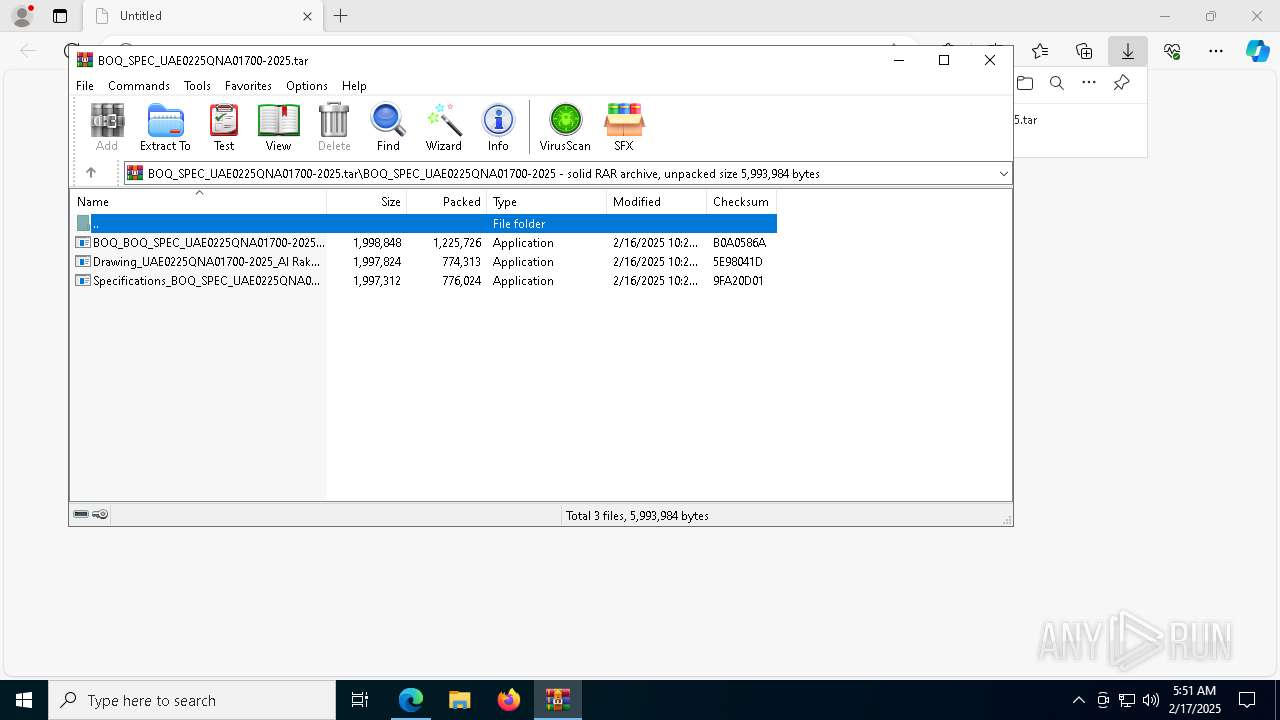
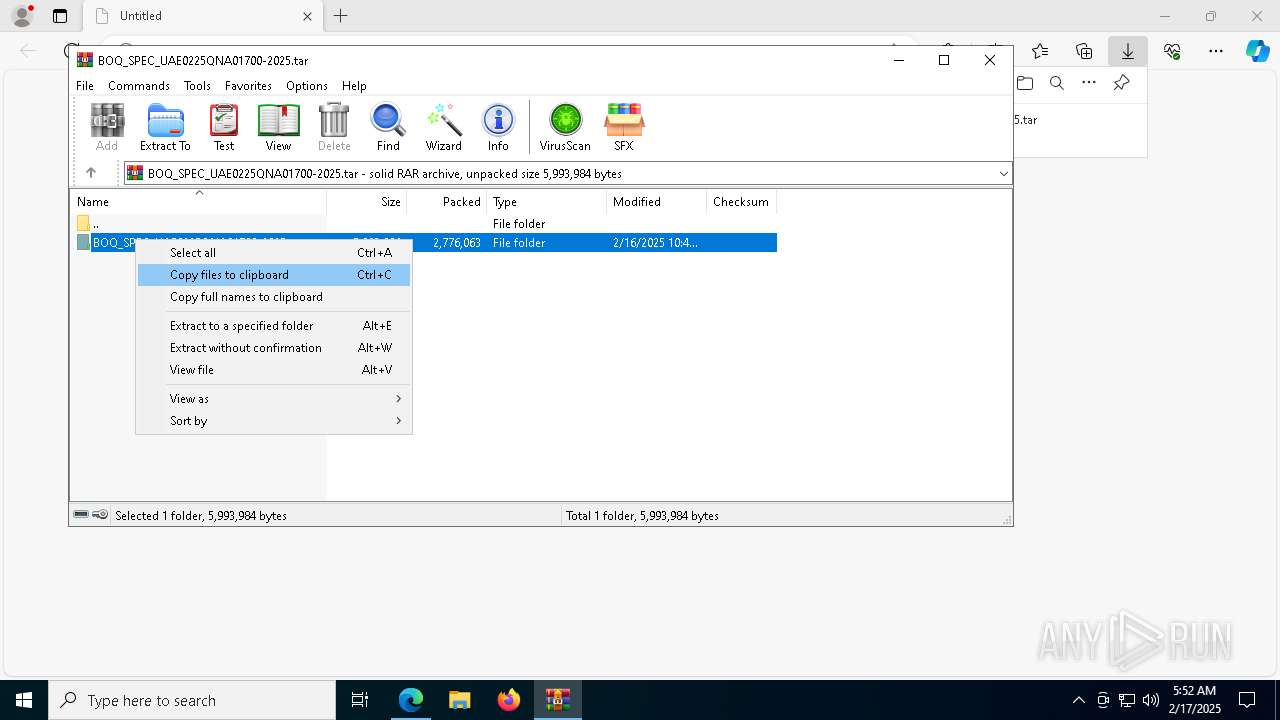
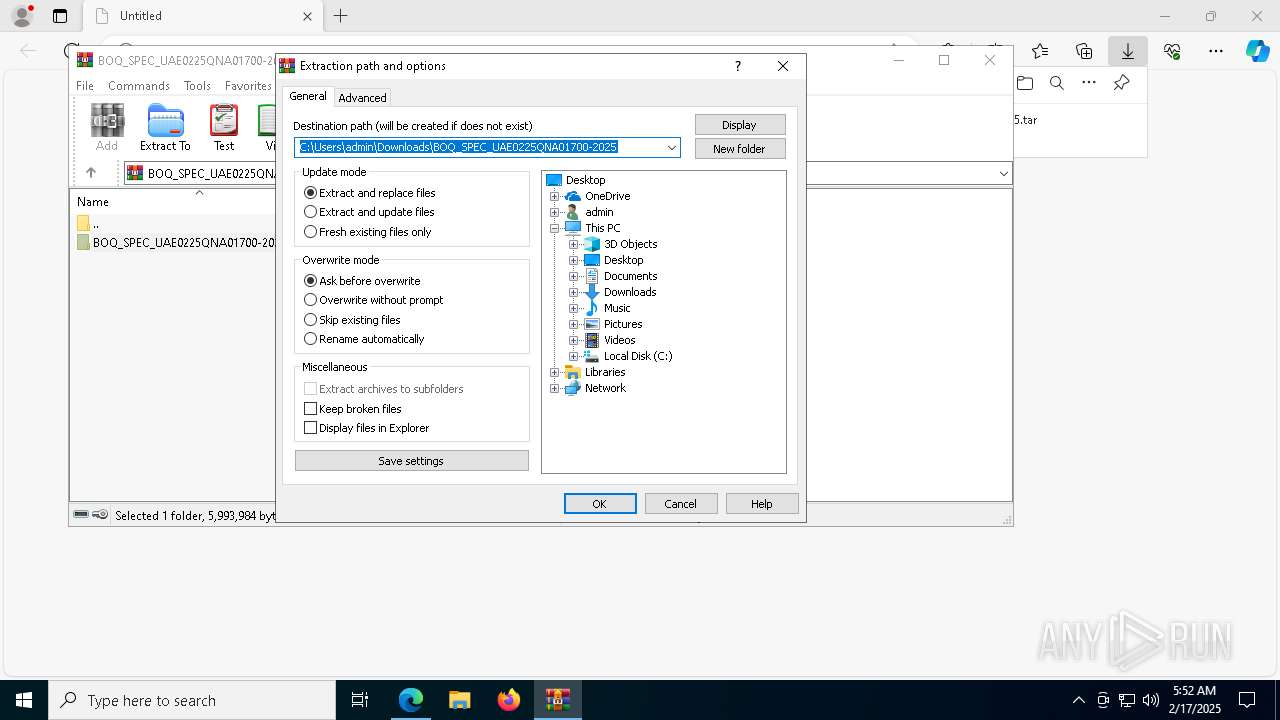
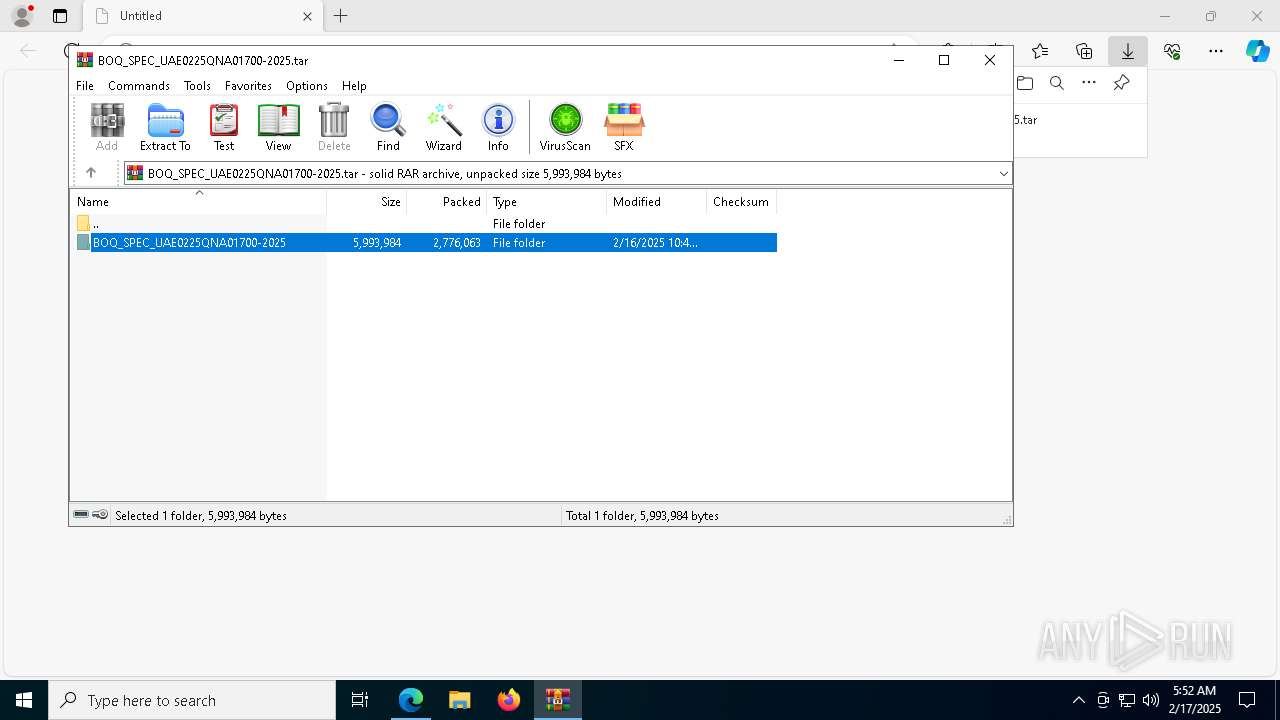
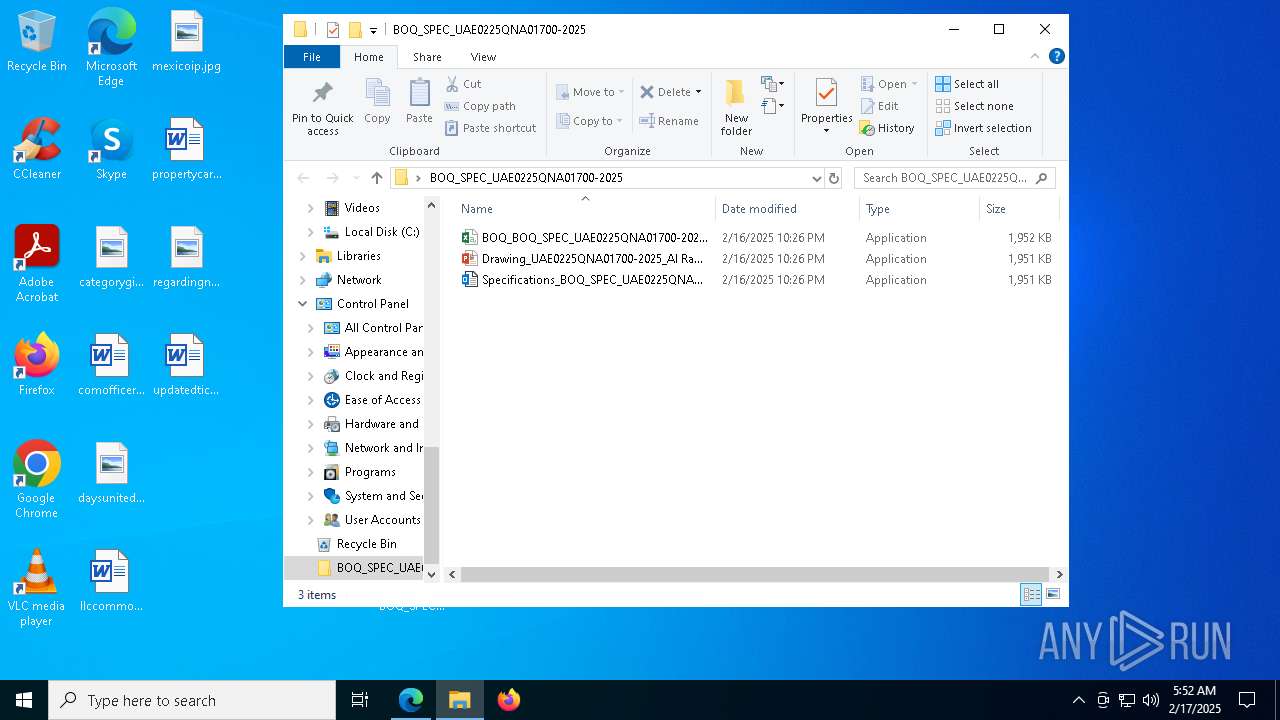
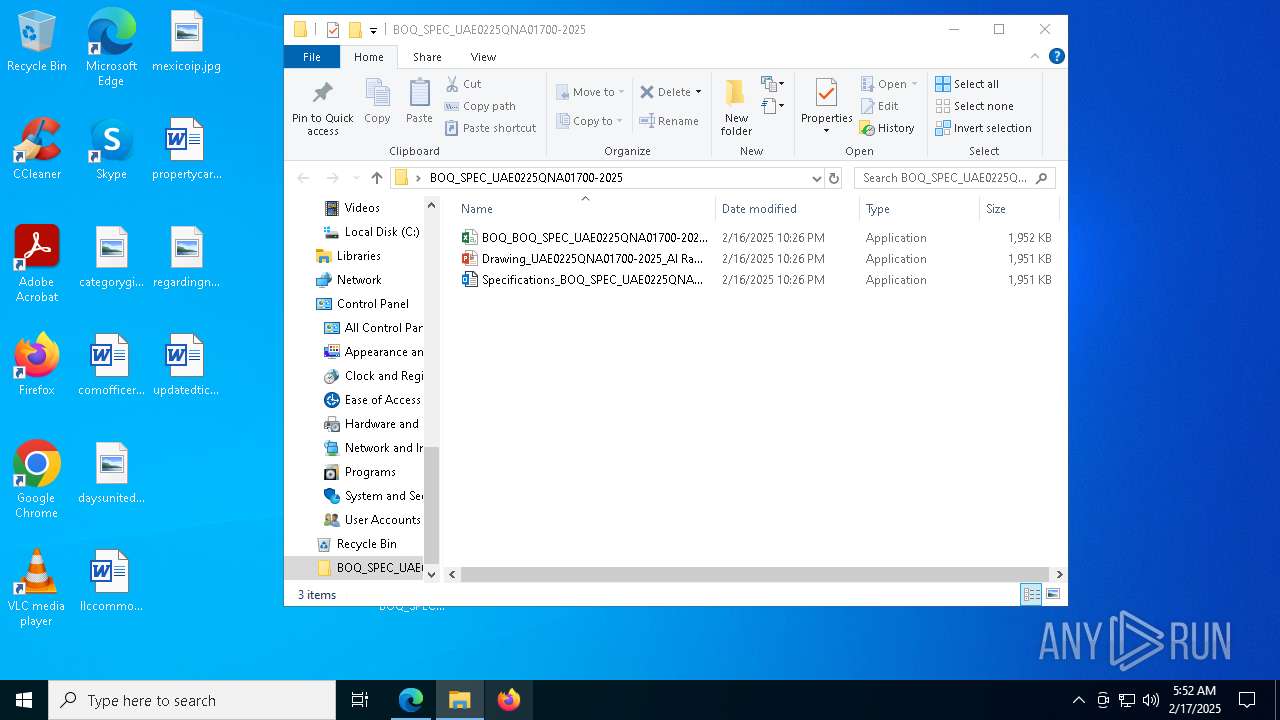
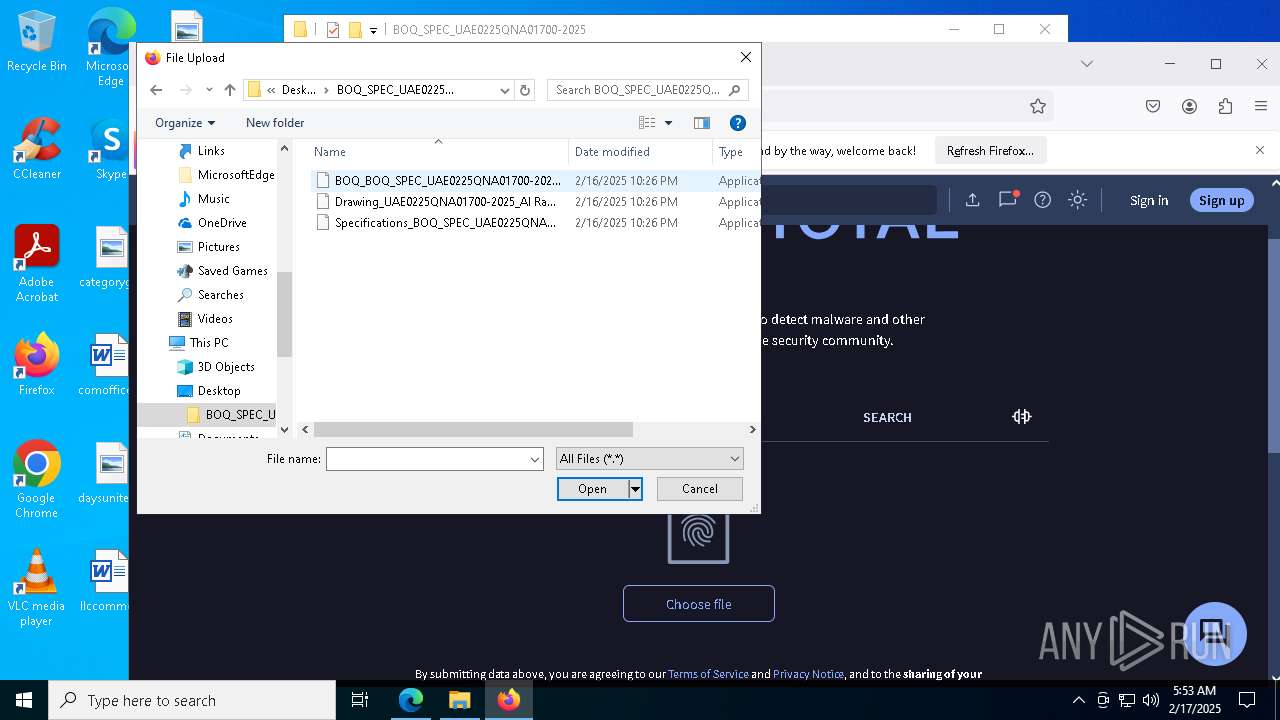
| URL: | https://albaddadcapital-my.sharepoint.com/:u:/g/personal/adsales3_albaddad_com/EdHSZDI0fE1GhbiUd5Eg7_QB9WDezp87-a79QhG1t2wviQ?e=Ee4bsy&download=1 |
| Full analysis: | https://app.any.run/tasks/16be8e6b-eae8-45a2-aaea-5adeea1794fb |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | February 17, 2025, 05:51:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7218AC4A0A4A42C906D896BCF5040467 |
| SHA1: | 163010F15120538B956D7D961F748D29345070E3 |
| SHA256: | 81E7DF73237451A18A910AC90EC7B6029B5838964673AD499C493B167EB89C56 |
| SSDEEP: | 3:N8U1wxdWN+ArL5kKVFSE/iJVMWOxVi/3FhRC8AYrj92Un:2UCdK+AfzQJFOx8/Zrj9zn |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5836)
- alpha.pif (PID: 7568)
- cmd.exe (PID: 6876)
- alpha.pif (PID: 7724)
Starts PowerShell from an unusual location
- alpha.pif (PID: 7568)
- alpha.pif (PID: 7724)
Changes the autorun value in the registry
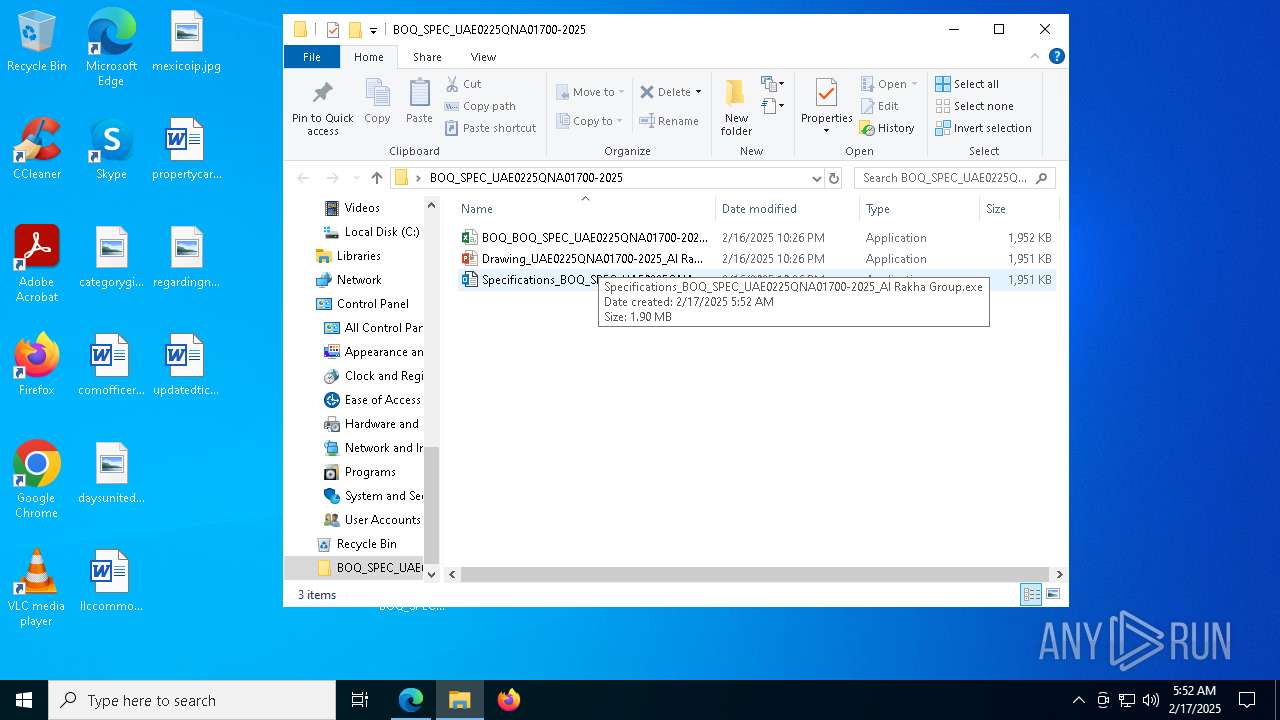
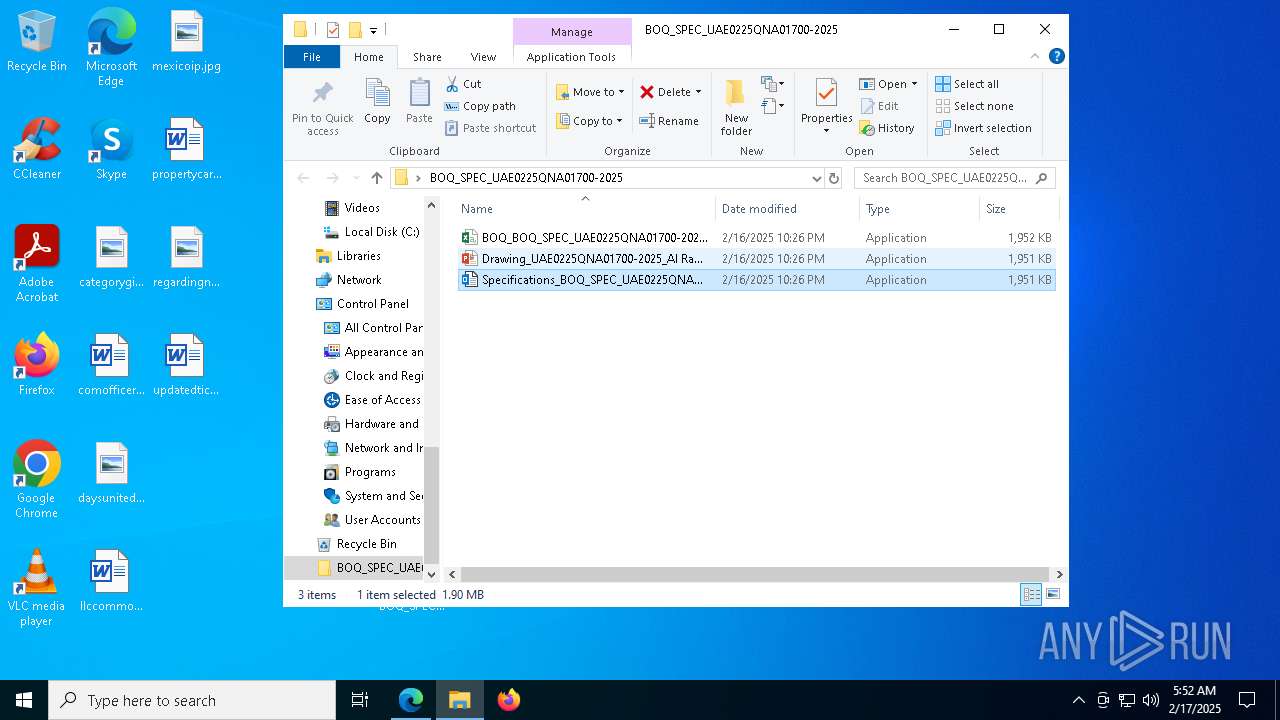
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
REMCOS has been detected (SURICATA)
- SndVol.exe (PID: 5580)
Actions looks like stealing of personal data
- SndVol.exe (PID: 7624)
- SndVol.exe (PID: 5112)
- SndVol.exe (PID: 6648)
- SndVol.exe (PID: 5536)
Steals credentials from Web Browsers
- SndVol.exe (PID: 5112)
SUSPICIOUS
Drops a file with a rarely used extension (PIF)
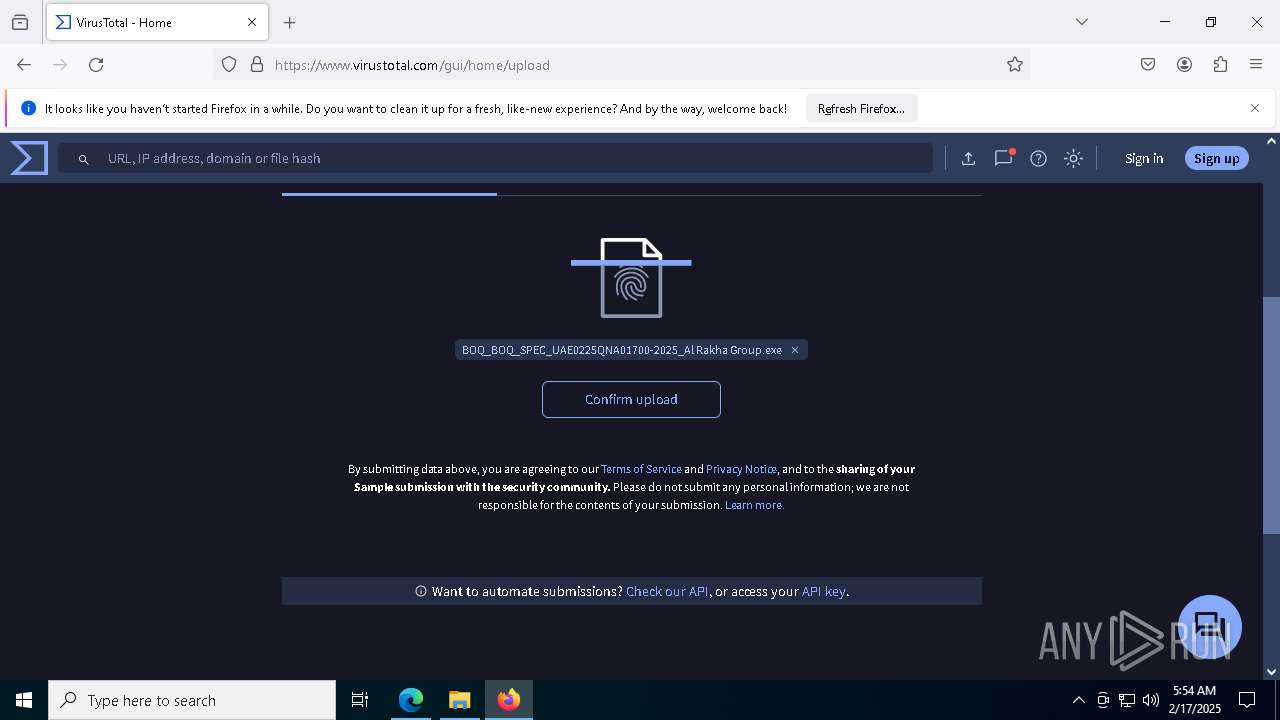
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- extrac32.exe (PID: 5208)
- extrac32.exe (PID: 7480)
- extrac32.exe (PID: 7520)
- extrac32.exe (PID: 7572)
- extrac32.exe (PID: 7060)
- extrac32.exe (PID: 7056)
Executing commands from ".cmd" file
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- svchost.pif (PID: 5112)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- svchost.pif (PID: 7692)
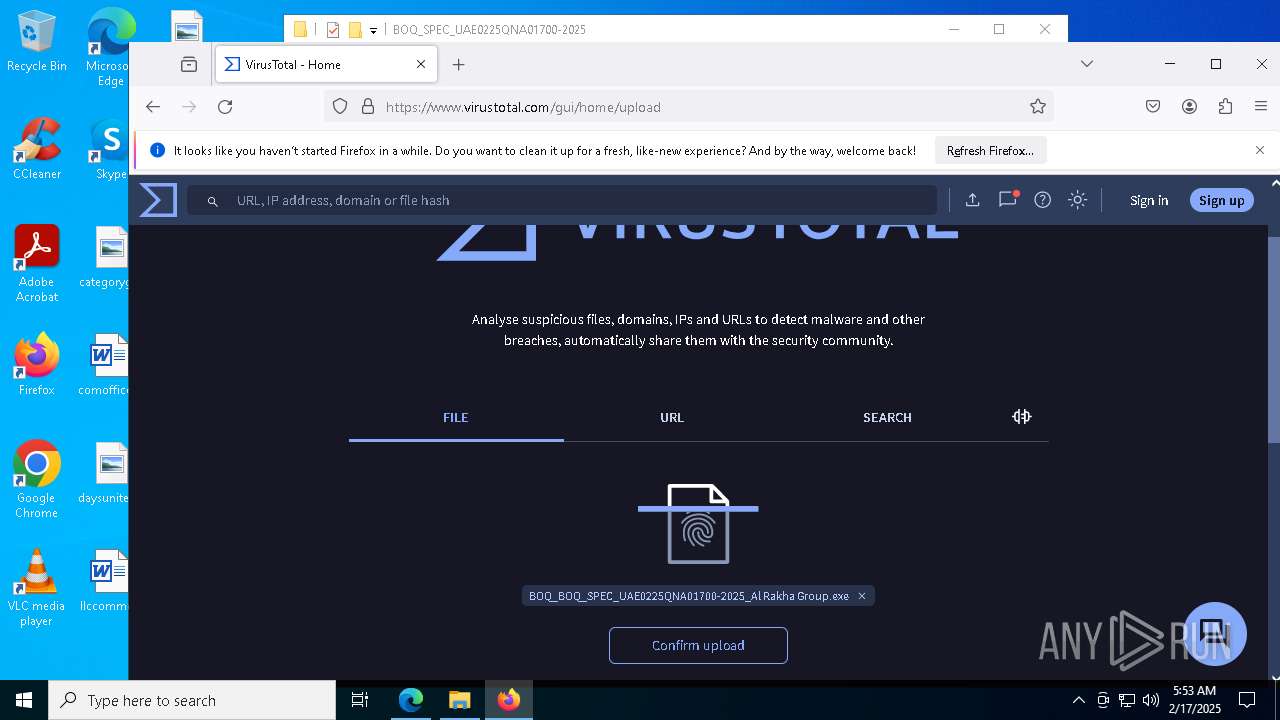
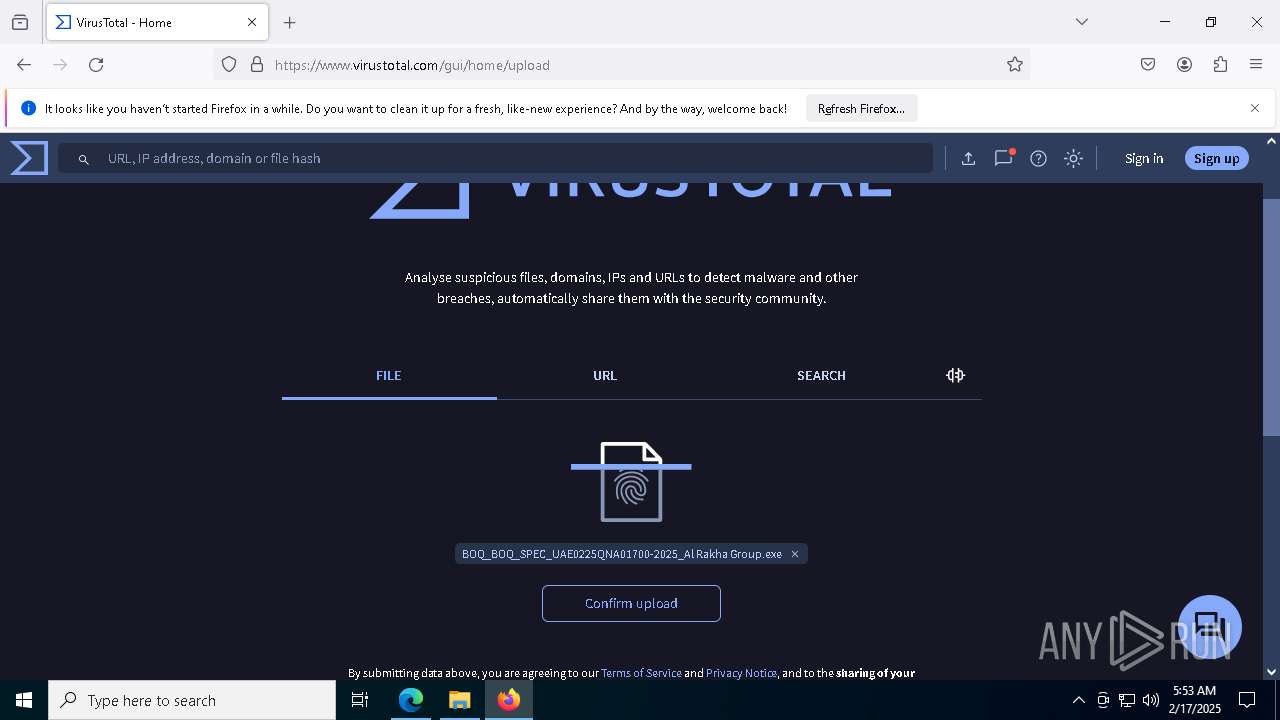
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- svchost.pif (PID: 7140)
Reads security settings of Internet Explorer
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- ndpha.pif (PID: 4520)
- aken.pif (PID: 7596)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- ndpha.pif (PID: 1556)
- aken.pif (PID: 6916)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- ndpha.pif (PID: 1476)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 4640)
- cmd.exe (PID: 5876)
- extrac32.exe (PID: 5208)
- ndpha.pif (PID: 4520)
- cmd.exe (PID: 5836)
- extrac32.exe (PID: 7480)
- extrac32.exe (PID: 7520)
- alpha.pif (PID: 7568)
- aken.pif (PID: 7596)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 1856)
- extrac32.exe (PID: 7572)
- extrac32.exe (PID: 7060)
- ndpha.pif (PID: 1556)
- cmd.exe (PID: 6876)
- extrac32.exe (PID: 6860)
- extrac32.exe (PID: 7076)
- alpha.pif (PID: 7724)
- extrac32.exe (PID: 3532)
- aken.pif (PID: 6916)
- cmd.exe (PID: 1888)
- cmd.exe (PID: 7620)
- extrac32.exe (PID: 7056)
- ndpha.pif (PID: 1476)
- cmd.exe (PID: 2736)
Starts CMD.EXE for commands execution
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- svchost.pif (PID: 5112)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- svchost.pif (PID: 7692)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- svchost.pif (PID: 7140)
Process drops legitimate windows executable
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- extrac32.exe (PID: 5208)
- extrac32.exe (PID: 7480)
- extrac32.exe (PID: 7520)
- extrac32.exe (PID: 7572)
- extrac32.exe (PID: 7060)
- extrac32.exe (PID: 7056)
Executable content was dropped or overwritten
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- extrac32.exe (PID: 5208)
- extrac32.exe (PID: 7480)
- extrac32.exe (PID: 7520)
- extrac32.exe (PID: 7572)
- extrac32.exe (PID: 7060)
- extrac32.exe (PID: 7056)
Starts application with an unusual extension
- cmd.exe (PID: 5876)
- ndpha.pif (PID: 4520)
- cmd.exe (PID: 5836)
- cmd.exe (PID: 1856)
- ndpha.pif (PID: 1556)
- cmd.exe (PID: 6876)
- alpha.pif (PID: 7724)
- cmd.exe (PID: 7620)
- ndpha.pif (PID: 1476)
- alpha.pif (PID: 7568)
Starts a Microsoft application from unusual location
- ndpha.pif (PID: 4520)
- alpha.pif (PID: 7568)
- aken.pif (PID: 7596)
- ndpha.pif (PID: 1556)
- alpha.pif (PID: 7724)
- aken.pif (PID: 6916)
- ndpha.pif (PID: 1476)
There is functionality for taking screenshot (YARA)
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- SndVol.exe (PID: 5580)
Access to SharePoint Content
- msedge.exe (PID: 4740)
Starts itself from another location
- cmd.exe (PID: 5836)
- cmd.exe (PID: 6876)
Checks Windows Trust Settings
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
Contacting a server suspected of hosting an CnC
- SndVol.exe (PID: 5580)
Application launched itself
- SndVol.exe (PID: 5580)
Connects to unusual port
- SndVol.exe (PID: 5580)
INFO
Checks supported languages
- identity_helper.exe (PID: 6248)
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- extrac32.exe (PID: 5208)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- extrac32.exe (PID: 7480)
- svchost.pif (PID: 5112)
- extrac32.exe (PID: 7520)
- ndpha.pif (PID: 4520)
- extrac32.exe (PID: 7572)
- alpha.pif (PID: 7568)
- aken.pif (PID: 7596)
- ndpha.pif (PID: 1556)
- extrac32.exe (PID: 6860)
- svchost.pif (PID: 7692)
- extrac32.exe (PID: 7076)
- extrac32.exe (PID: 3532)
- alpha.pif (PID: 7724)
- aken.pif (PID: 6916)
- extrac32.exe (PID: 7056)
- ndpha.pif (PID: 1476)
- svchost.pif (PID: 7140)
- extrac32.exe (PID: 7060)
Reads the computer name
- identity_helper.exe (PID: 6248)
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- extrac32.exe (PID: 5208)
- ndpha.pif (PID: 4520)
- extrac32.exe (PID: 7480)
- extrac32.exe (PID: 7520)
- extrac32.exe (PID: 7572)
- aken.pif (PID: 7596)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- extrac32.exe (PID: 7060)
- extrac32.exe (PID: 6860)
- ndpha.pif (PID: 1556)
- extrac32.exe (PID: 7076)
- extrac32.exe (PID: 3532)
- aken.pif (PID: 6916)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- extrac32.exe (PID: 7056)
- ndpha.pif (PID: 1476)
Reads Environment values
- identity_helper.exe (PID: 6248)
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
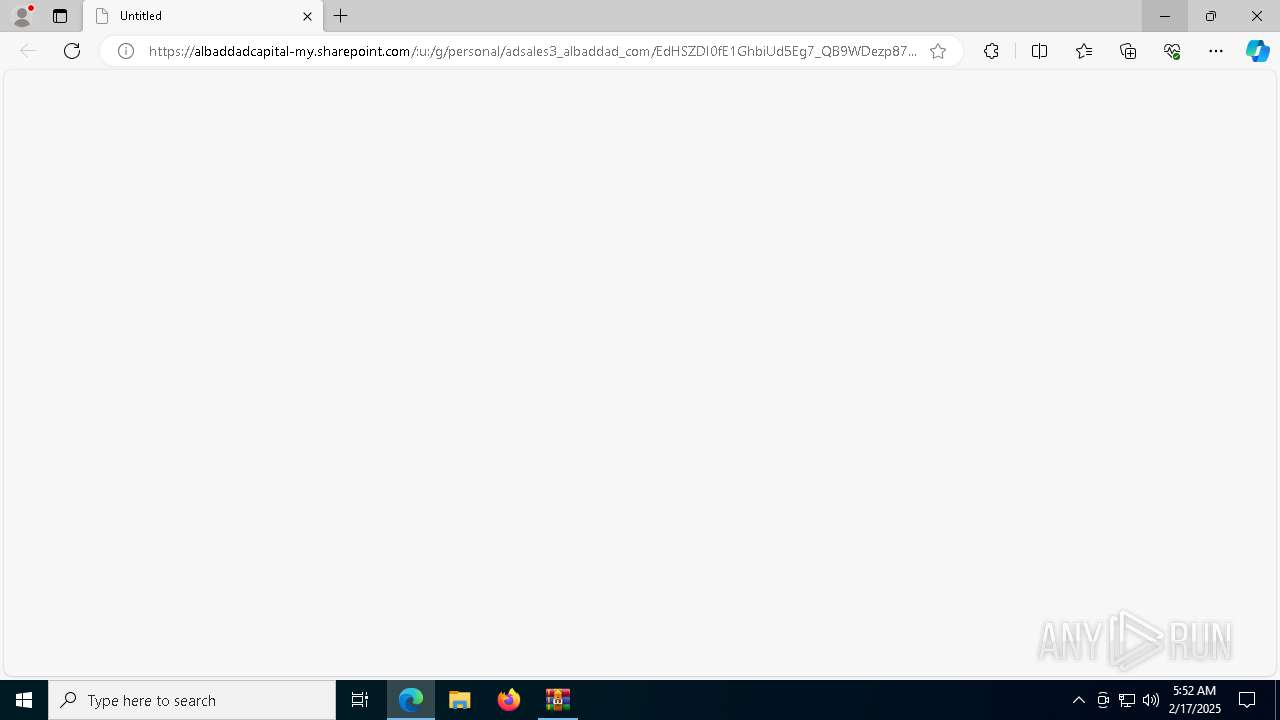
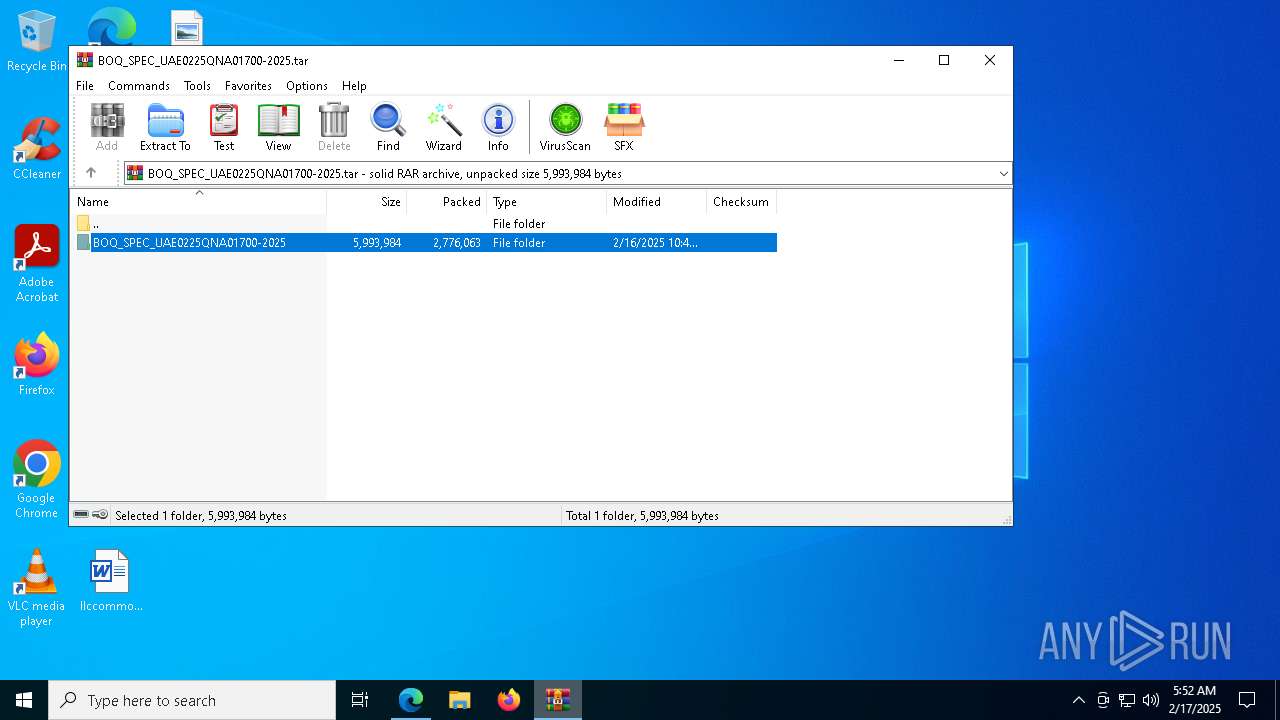
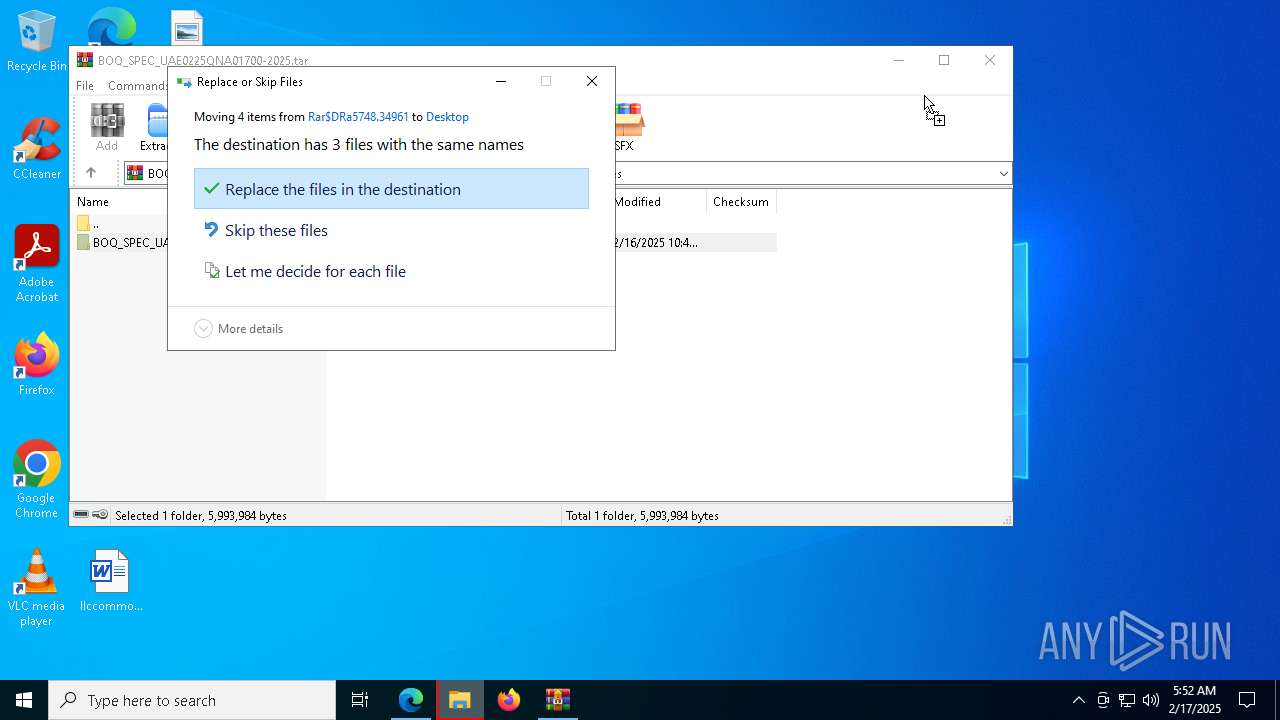
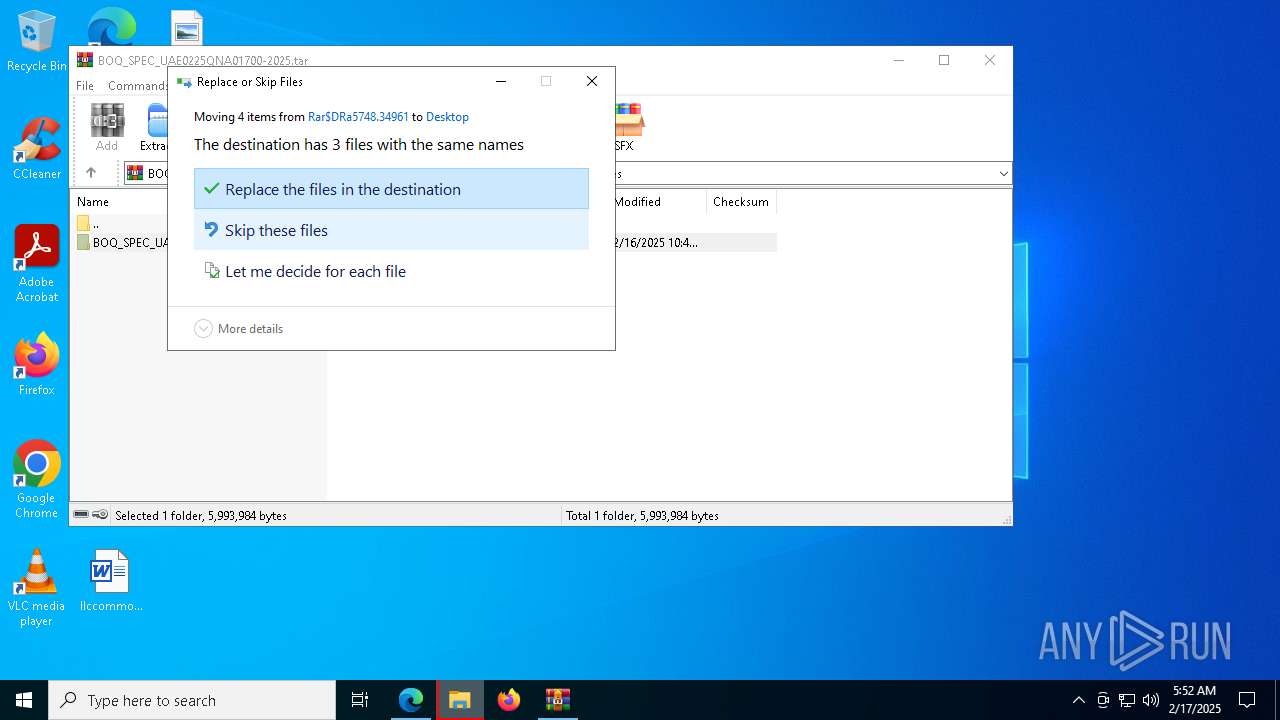
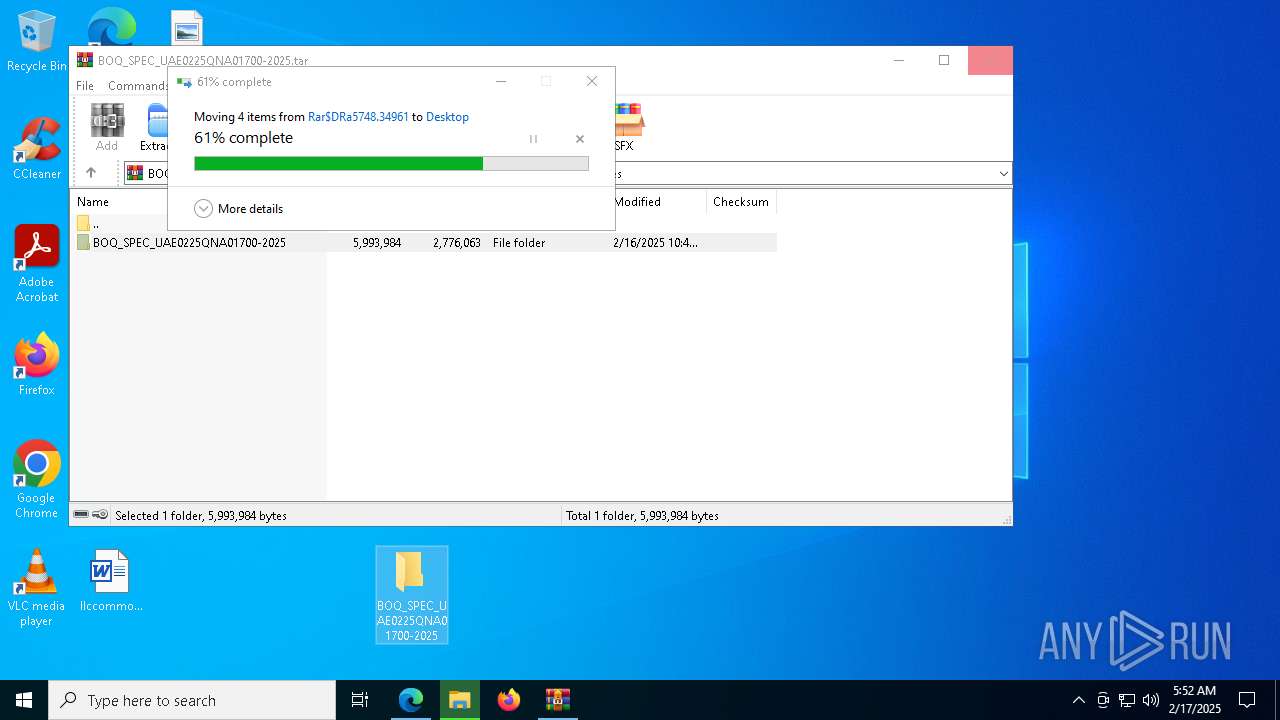
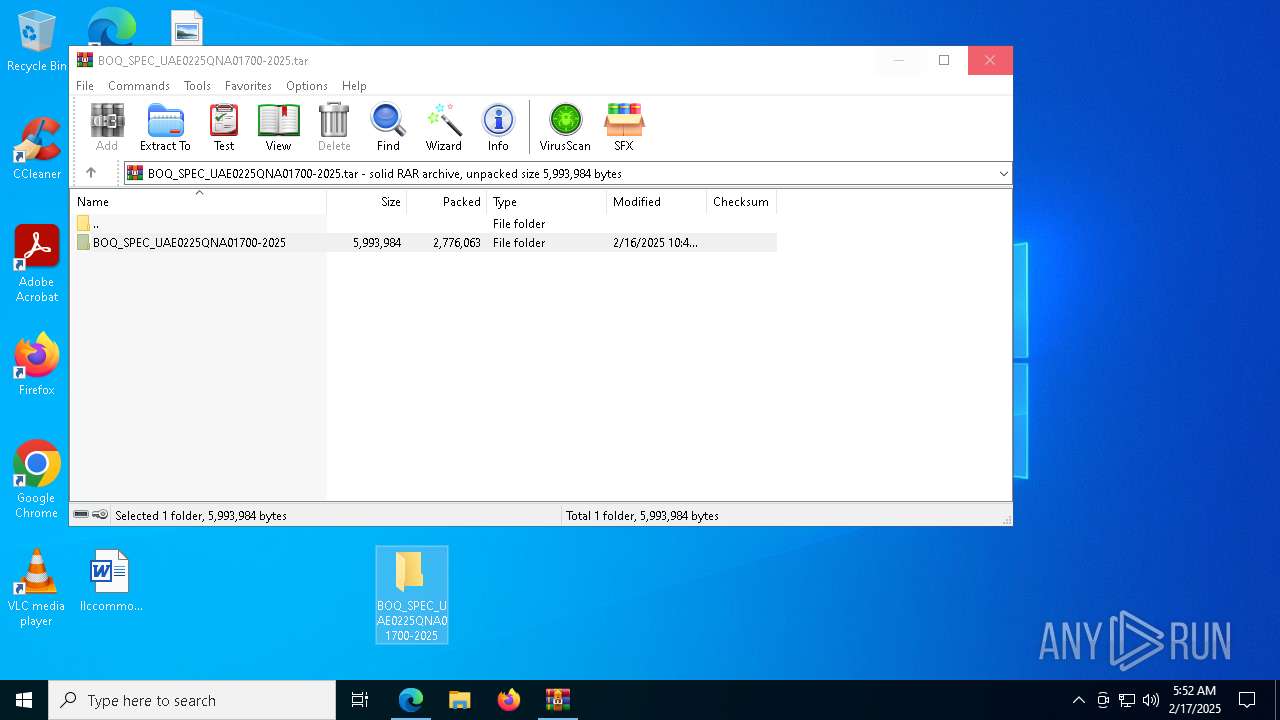
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5748)
- msedge.exe (PID: 1864)
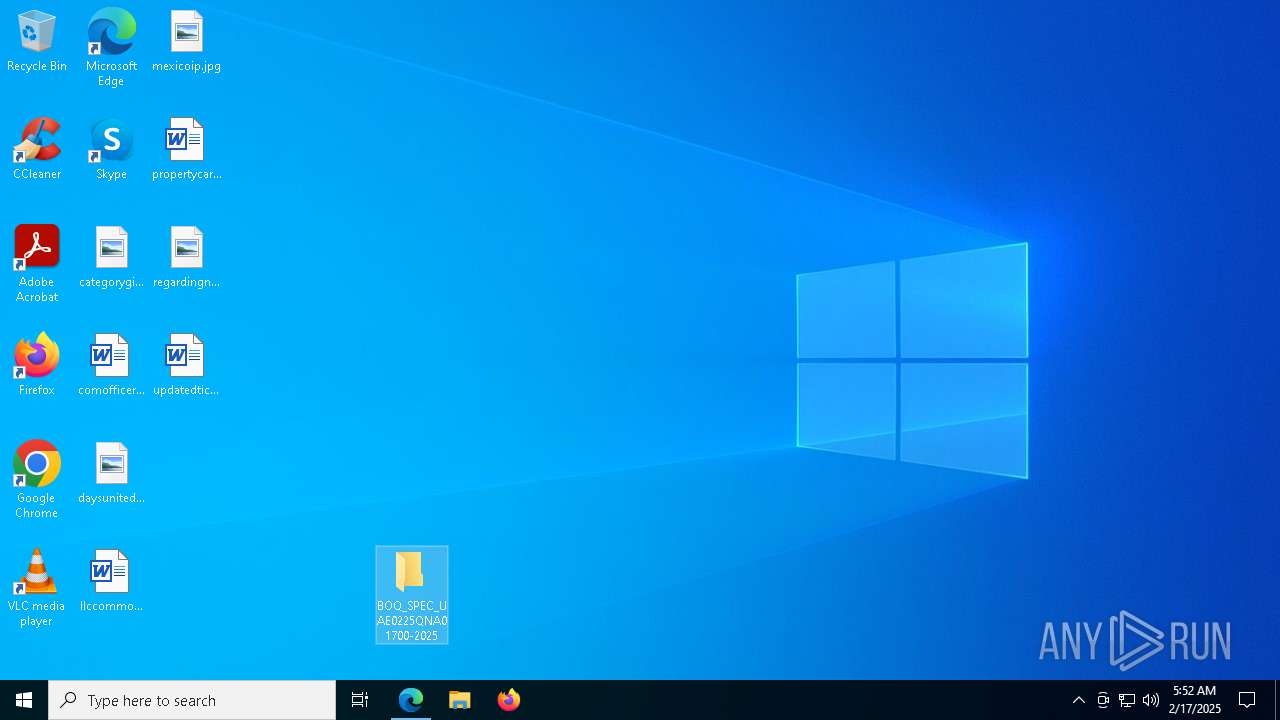
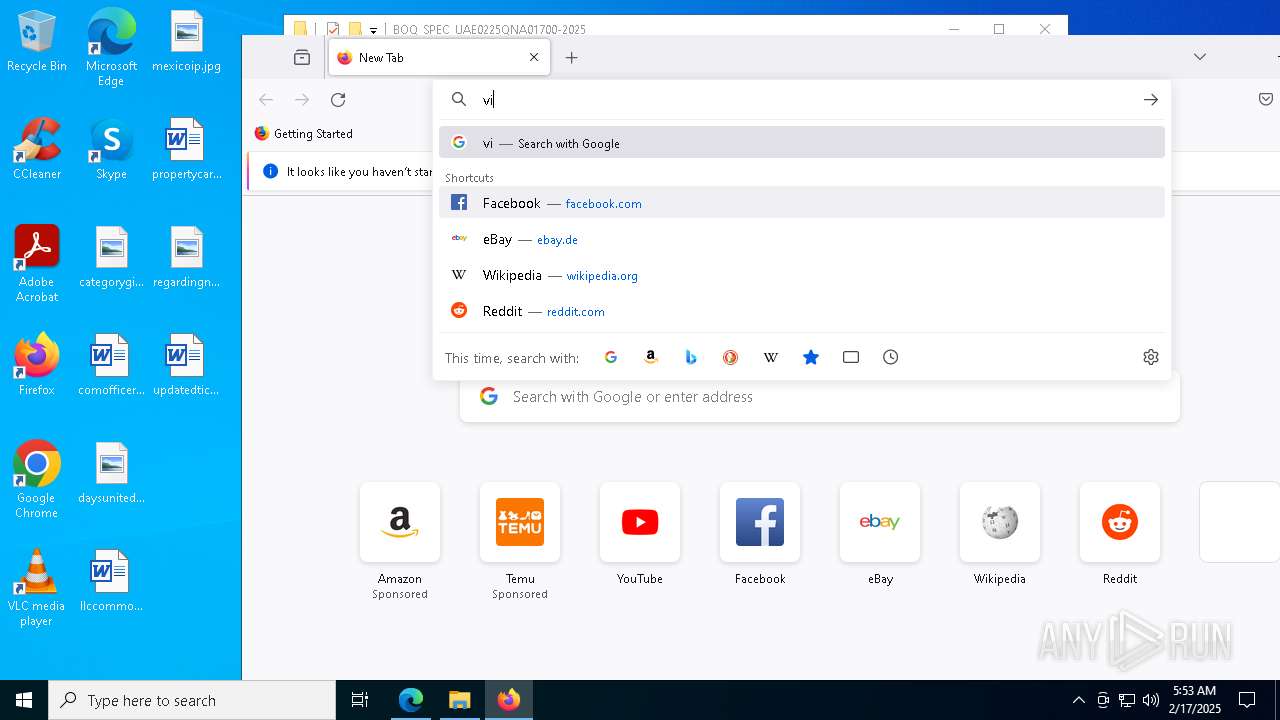
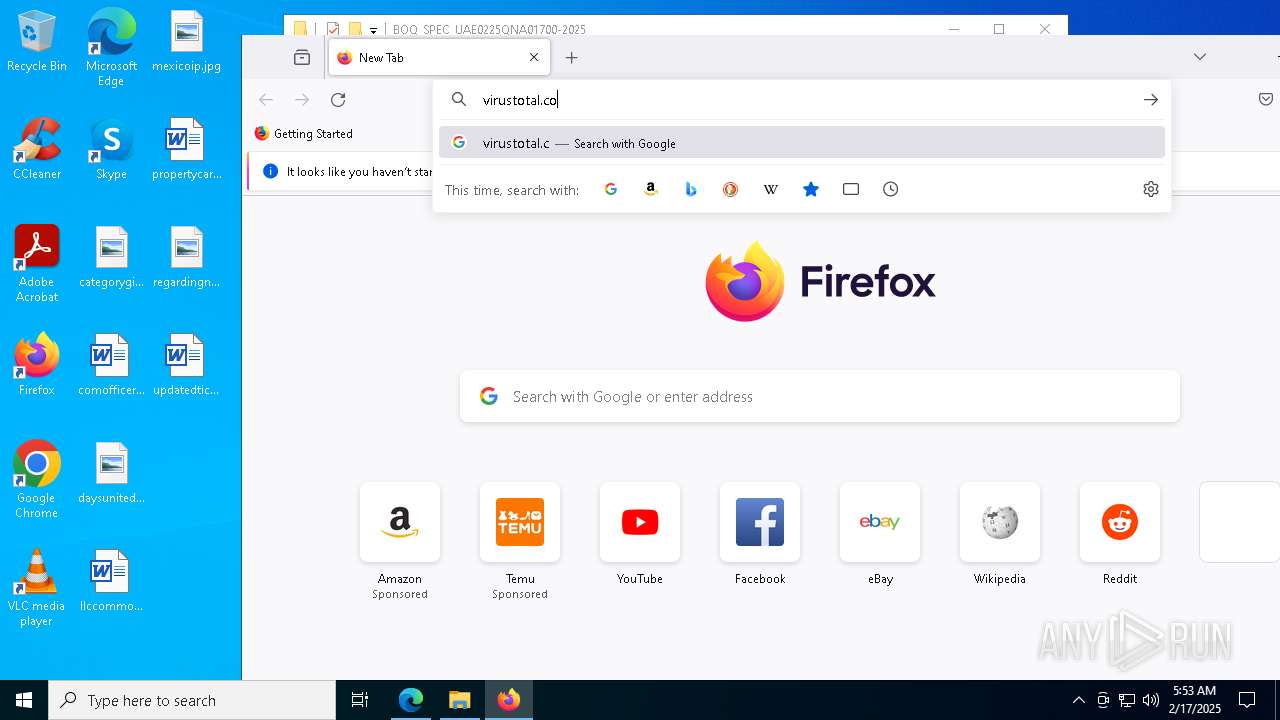
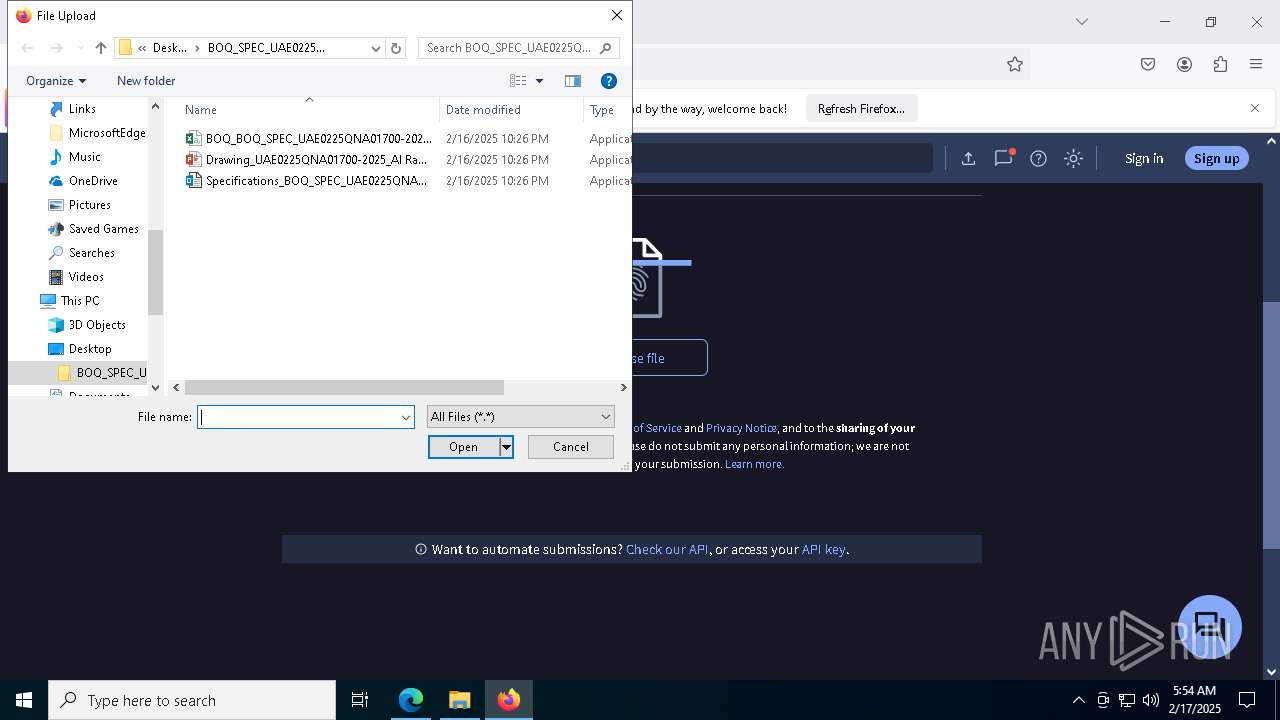
Manual execution by a user
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- firefox.exe (PID: 7808)
Compiled with Borland Delphi (YARA)
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
Application launched itself
- msedge.exe (PID: 4740)
- firefox.exe (PID: 7808)
- firefox.exe (PID: 7788)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4740)
Checks proxy server information
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- SndVol.exe (PID: 5580)
The sample compiled with english language support
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- extrac32.exe (PID: 5208)
- extrac32.exe (PID: 7480)
- extrac32.exe (PID: 7572)
- extrac32.exe (PID: 7520)
- extrac32.exe (PID: 7060)
- extrac32.exe (PID: 7056)
- msedge.exe (PID: 1864)
Process checks computer location settings
- ndpha.pif (PID: 4520)
- ndpha.pif (PID: 1556)
- ndpha.pif (PID: 1476)
Process checks Powershell version
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
Reads the software policy settings
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
Reads the machine GUID from the registry
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
- Specifications_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7852)
- BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 3564)
- Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe (PID: 7896)
Create files in a temporary directory
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
- SndVol.exe (PID: 7624)
- SndVol.exe (PID: 6648)
- SndVol.exe (PID: 5112)
Checks if a key exists in the options dictionary (POWERSHELL)
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
Script raised an exception (POWERSHELL)
- aken.pif (PID: 7596)
- aken.pif (PID: 6916)
Reads security settings of Internet Explorer
- SndVol.exe (PID: 5580)
Creates files or folders in the user directory
- SndVol.exe (PID: 5580)
Mpress packer has been detected
- SndVol.exe (PID: 5580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
245
Monitored processes
113
Malicious processes
14
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7064 -childID 9 -isForBrowser -prefsHandle 5836 -prefMapHandle 6992 -prefsLen 32108 -prefMapSize 244583 -jsInitHandle 1488 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {118ec7ba-d130-4e90-b693-fdafc5639374} 7788 "\\.\pipe\gecko-crash-server-pipe.7788" 264924fea10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 732 | "C:\Windows \SysWOW64\svchost.pif" | C:\Windows \SysWOW64\svchost.pif | — | ndpha.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Exchange ActiveSync Invoker Exit code: 3221226540 Version: 10.0.22621.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6792 --field-trial-handle=2400,i,10491848237813873826,7667278564200486402,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1200 | C:\Windows\System32\colorcpl.exe | C:\Windows\SysWOW64\colorcpl.exe | — | BOQ_BOQ_SPEC_UAE0225QNA01700-2025_Al Rakha Group.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | "C:\Windows \SysWOW64\svchost.pif" | C:\Windows \SysWOW64\svchost.pif | — | ndpha.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Exchange ActiveSync Invoker Exit code: 3221226540 Version: 10.0.22621.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | C:\\Users\\Public\\ndpha.pif zipfldr.dll,RouteTheCall C:\Windows \SysWOW64\svchost.pif | C:\Users\Public\ndpha.pif | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | C:\\Users\\Public\\ndpha.pif zipfldr.dll,RouteTheCall C:\Windows \SysWOW64\svchost.pif | C:\Users\Public\ndpha.pif | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x308,0x30c,0x310,0x304,0x314,0x7ff820fe5fd8,0x7ff820fe5fe4,0x7ff820fe5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\Libraries\\Zhpymxci12.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | Drawing_UAE0225QNA01700-2025_Al Rakha Group.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5564 --field-trial-handle=2400,i,10491848237813873826,7667278564200486402,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
43 650
Read events
43 488
Write events
145
Delete events
17
Modification events
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2E14B166E68C2F00 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 376CC166E68C2F00 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DFF2072E-D400-47DE-ADA1-868DC05B3DDC} | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {99A3838A-DA16-4EC5-92B8-B3F42A86B444} | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B318D566E68C2F00 | |||
| (PID) Process: | (4740) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
30
Suspicious files
742
Text files
128
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134b35.TMP | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134b35.TMP | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134b35.TMP | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134b54.TMP | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF134b64.TMP | — | |
MD5:— | SHA256:— | |||
| 4740 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
161
DNS requests
191
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
628 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7976 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739806675&P2=404&P3=2&P4=E77quK4VD7l4xjeVu%2fB23sXxX3yknHJ9llMK%2f0%2bKh4s1Rr3VjkNl%2fiVvD8Zewt3Z1M88tTRR8f9Ph4ZHwrxbVQ%3d%3d | unknown | — | — | whitelisted |
3508 | svchost.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7976 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739806675&P2=404&P3=2&P4=E77quK4VD7l4xjeVu%2fB23sXxX3yknHJ9llMK%2f0%2bKh4s1Rr3VjkNl%2fiVvD8Zewt3Z1M88tTRR8f9Ph4ZHwrxbVQ%3d%3d | unknown | — | — | whitelisted |
7976 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739806675&P2=404&P3=2&P4=E77quK4VD7l4xjeVu%2fB23sXxX3yknHJ9llMK%2f0%2bKh4s1Rr3VjkNl%2fiVvD8Zewt3Z1M88tTRR8f9Ph4ZHwrxbVQ%3d%3d | unknown | — | — | whitelisted |
7976 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739806675&P2=404&P3=2&P4=E77quK4VD7l4xjeVu%2fB23sXxX3yknHJ9llMK%2f0%2bKh4s1Rr3VjkNl%2fiVvD8Zewt3Z1M88tTRR8f9Ph4ZHwrxbVQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3508 | svchost.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.222.10.99:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3508 | svchost.exe | 23.222.10.99:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3568 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4740 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6368 | msedge.exe | 13.107.136.10:443 | albaddadcapital-my.sharepoint.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6368 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
albaddadcapital-my.sharepoint.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing DNS (.sharepoint .com) |
6368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing TLS SNI (.sharepoint .com) |
6368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing DNS (.sharepoint .com) |
6368 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6368 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6368 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Accessing SharePoint content without a legitimate Microsoft Sign-In |
5580 | SndVol.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
5580 | SndVol.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
5580 | SndVol.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
5580 | SndVol.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |