| File name: | 817 |
| Full analysis: | https://app.any.run/tasks/d725e6b1-5b83-479b-8c19-9a1250723b34 |
| Verdict: | Malicious activity |
| Threats: | Ficker Stealer is a malware that steals passwords, files, credit card details, and other types of sensitive information on Windows systems. It is most often distributed via phishing emails and can perform keylogging, process injection, and browser tracking. |
| Analysis date: | August 23, 2021, 05:22:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 724F01298E921F1F7362AF6B1BC31642 |
| SHA1: | E892F38DA2F930133CF67533E592DED56B7D6154 |
| SHA256: | 8174D7D1E9CCF99D8A0164E39DBB7DF725CBD710CF2F611D3CA4F2FDEB434535 |
| SSDEEP: | 196608:PafYtJ9mT5kszFw1d4zZkxaZzDaC0b8LP3gt82xHWPM/SJrUliFGpKERxRE50:SCJ9E5kszq4zZqwzD30biPwzUPZUliFm |
MALICIOUS
Drops executable file immediately after starts
- 817.exe (PID: 3056)
- md9_1sjm.exe (PID: 912)
- Folder.exe (PID: 2400)
- Intere.exe.com (PID: 2364)
- Files.exe (PID: 1692)
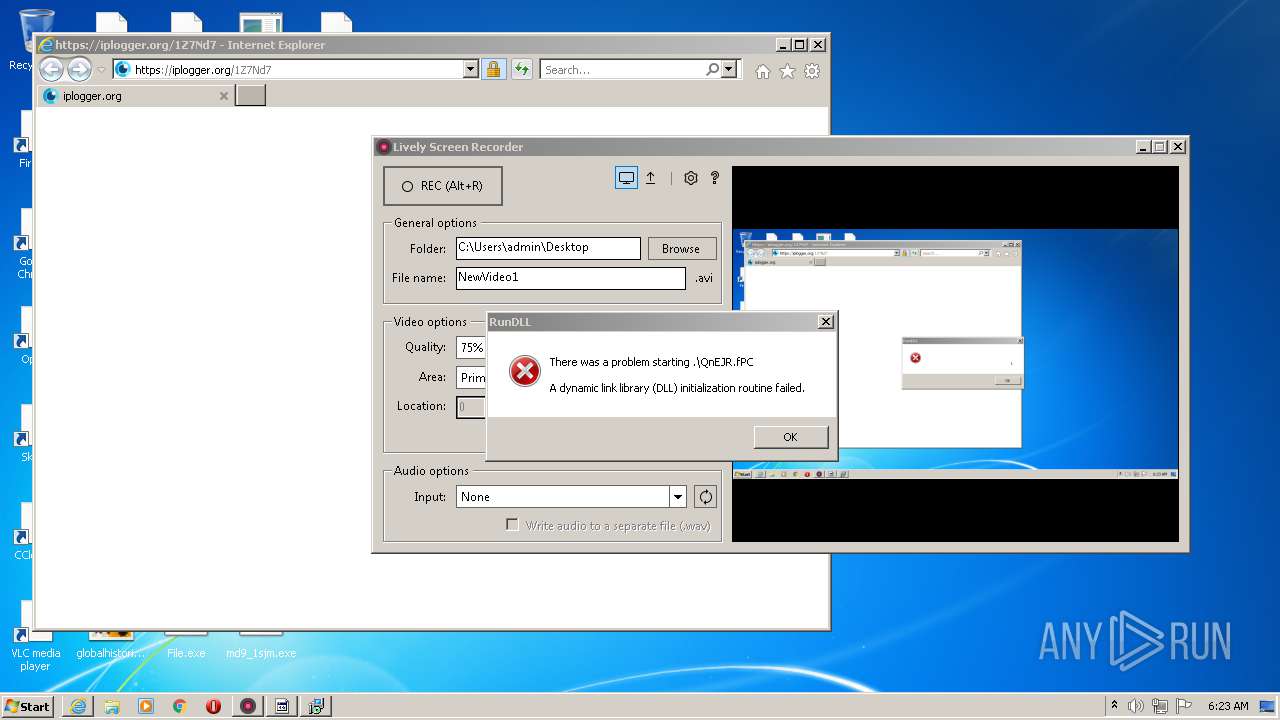
Runs injected code in another process
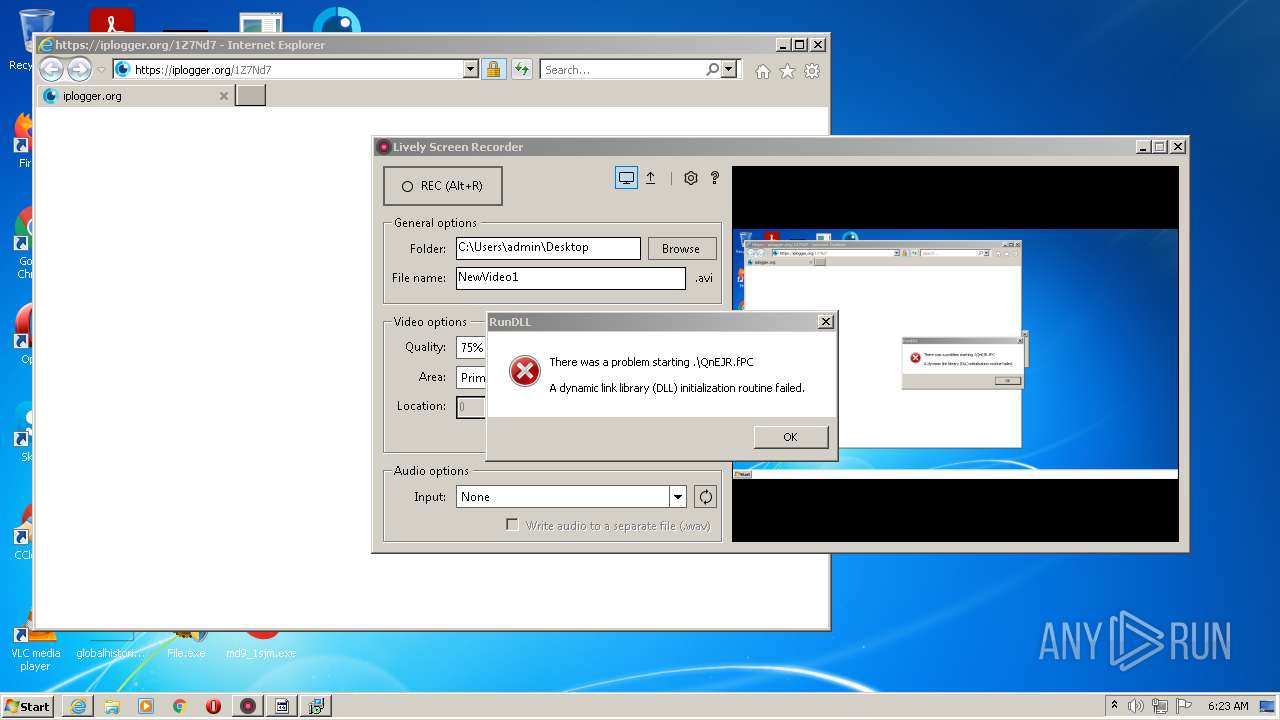
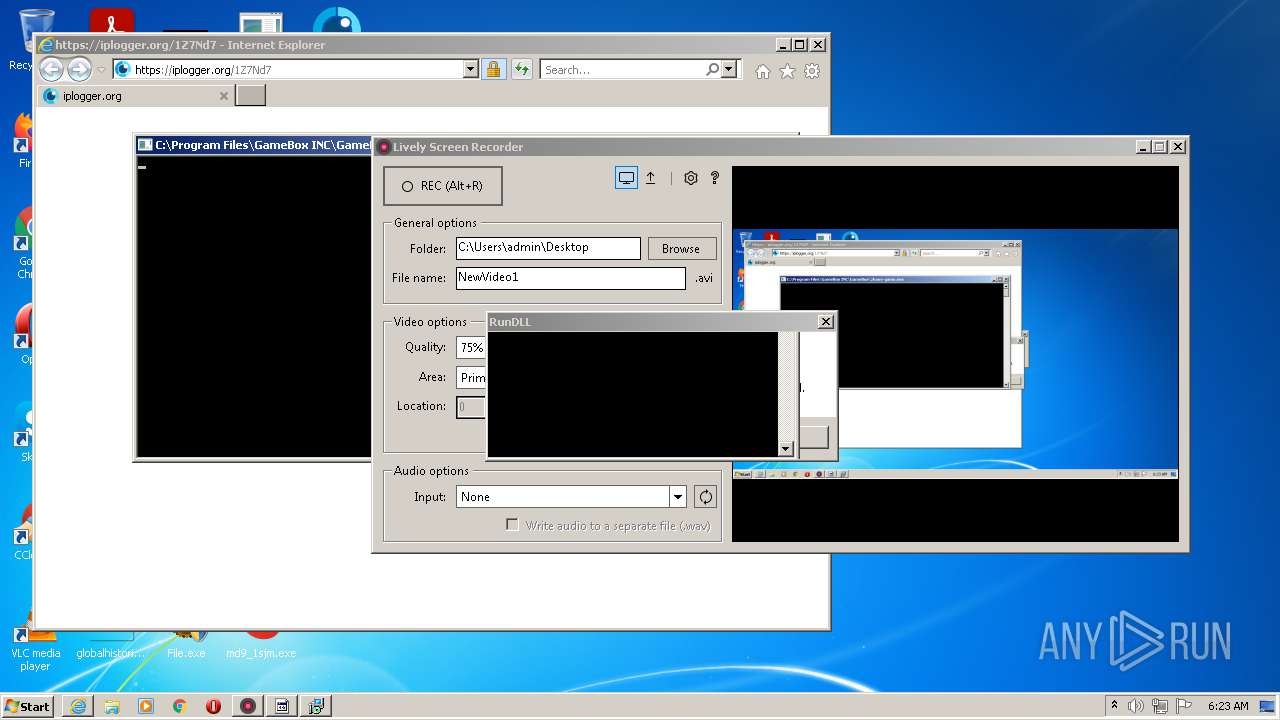
- rUNdlL32.eXe (PID: 2740)
Application was dropped or rewritten from another process
- md9_1sjm.exe (PID: 912)
- Info.exe (PID: 1744)
- File.exe (PID: 3752)
- File.exe (PID: 1236)
- SoCleanInst.exe (PID: 740)
- Folder.exe (PID: 1516)
- Lsr.exe (PID: 952)
- Folder.exe (PID: 2400)
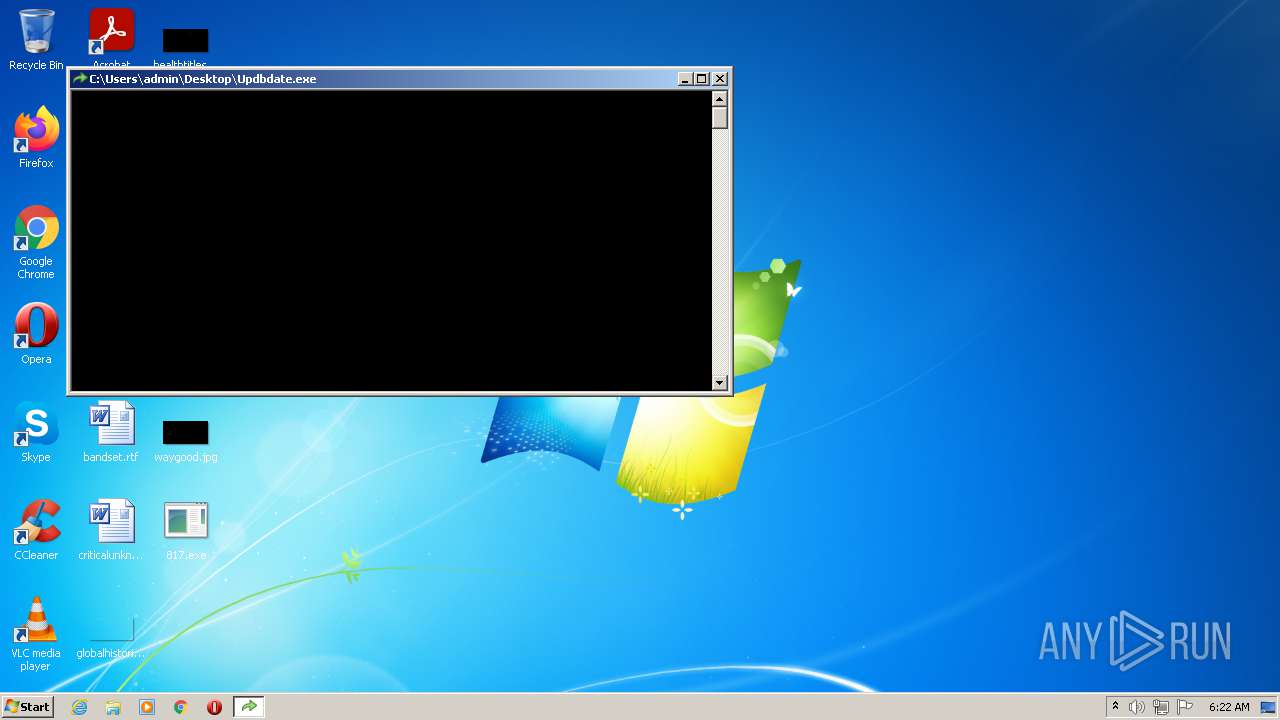
- Updbdate.exe (PID: 2840)
- tmpBCA0_tmp.exe (PID: 2152)
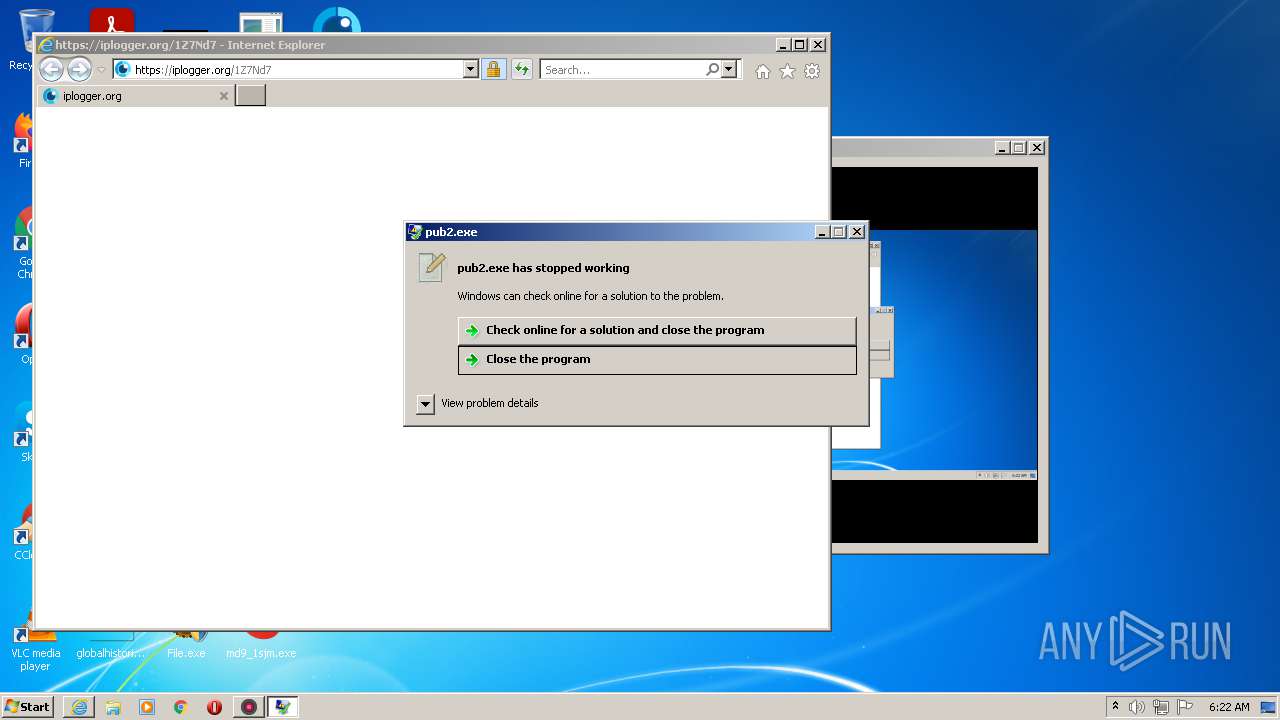
- pub2.exe (PID: 2504)
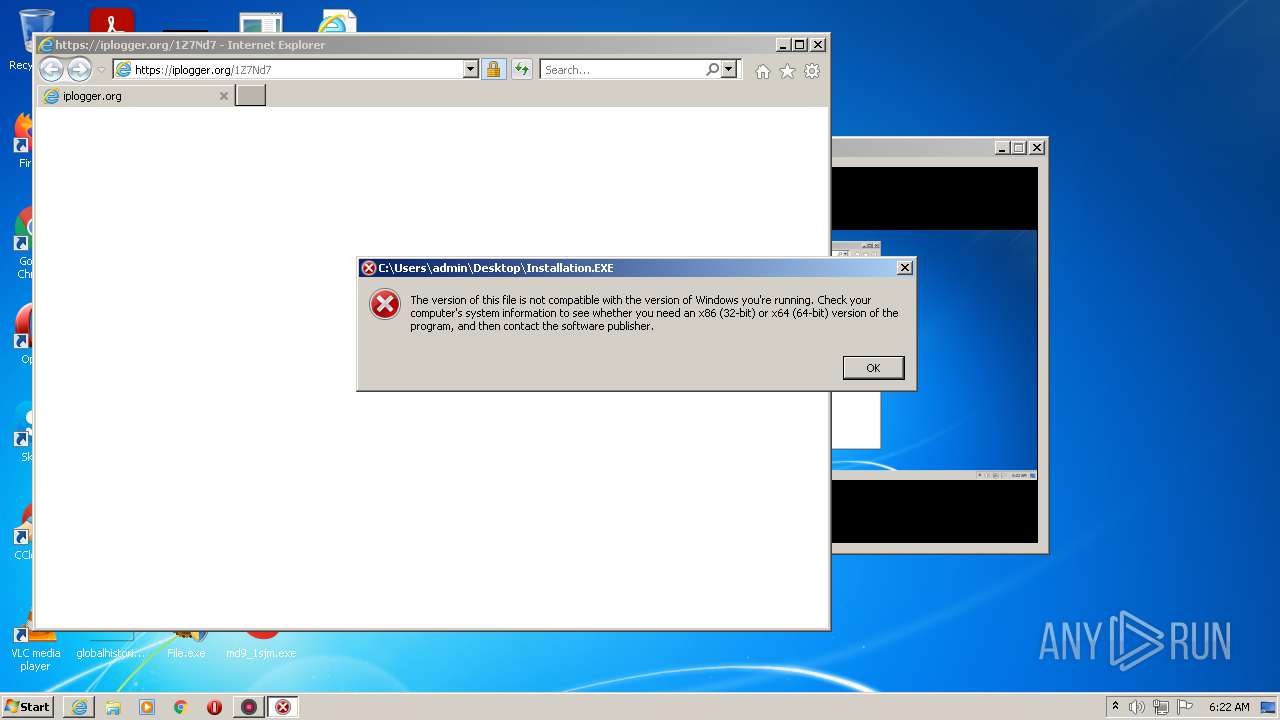
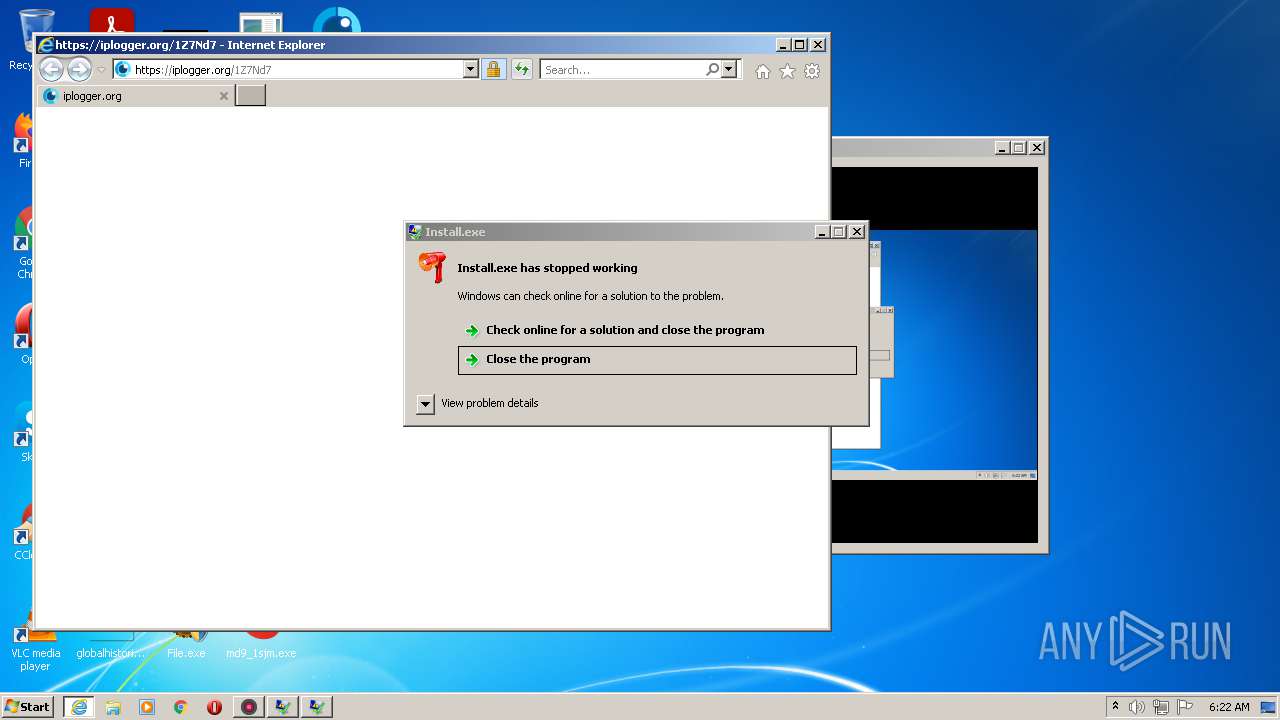
- Install.exe (PID: 2600)
- Files.exe (PID: 2372)
- Files.exe (PID: 1692)
- Install.exe (PID: 2692)
- VEEvoZX2PyYsZaBlNDSH1g50.exe (PID: 1668)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
- VEEvoZX2PyYsZaBlNDSH1g50.exe (PID: 2872)
- Intere.exe.com (PID: 2364)
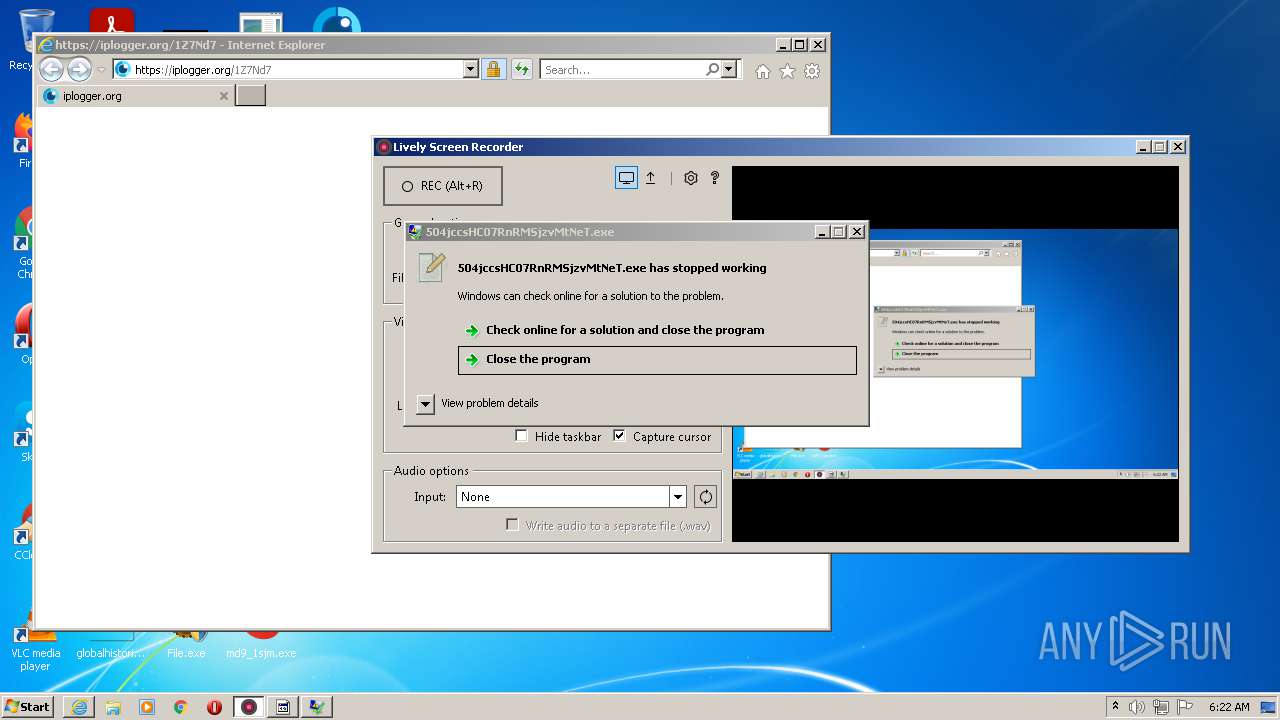
- 504jccsHC07RnRMSjzvMtNeT.exe (PID: 3588)
- jfiag3g_gg.exe (PID: 2428)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 900)
- Intere.exe.com (PID: 2248)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 3296)
- jfiag3g_gg.exe (PID: 1736)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
- efX7rxCXfVYUzI1uXy2HKW4T.exe (PID: 3532)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 2168)
- __WrSzGQXtH88BjDO92QZFob.exe (PID: 2452)
- 28975421242.exe (PID: 3044)
- QrzJinnWMAyQtyHTbSRlHMWq.exe (PID: 2436)
- 28975421242.exe (PID: 2548)
- _t6qKZ1cnUfvraJJk6jkiXIa.exe (PID: 2328)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 2616)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 3760)
- n15lI2QeJcffjWJvEY1l3dve.exe (PID: 1684)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 3000)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 2276)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 3024)
- 58852886416.exe (PID: 4584)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 4880)
- qgx7sz9EiN_cUHDnQbkKeopv.exe (PID: 3452)
- 60232995282.exe (PID: 3728)
- md8_8eus.exe (PID: 3024)
- IIOCze10ia6C3qcHL8WdIoPn.exe (PID: 2904)
- JqbjRAs0RVpnD4odvZCKrxDd.exe (PID: 1736)
- 2spjavkuPys0xLBi9CM9lx28.exe (PID: 4408)
- OQXLIJWMTsY7UIFTrgzFA6q6.exe (PID: 576)
- aLqMv5BypW7rykh2NgSu_9qQ.exe (PID: 6008)
- 2622697.exe (PID: 3844)
Application was injected by another process
- svchost.exe (PID: 1772)
Runs app for hidden code execution
- cmd.exe (PID: 568)
Writes to a start menu file
- Intere.exe.com (PID: 2364)
Changes settings of System certificates
- md9_1sjm.exe (PID: 912)
- Install.exe (PID: 2692)
- File.exe (PID: 1236)
Connects to CnC server
- md9_1sjm.exe (PID: 912)
- Files.exe (PID: 1692)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
Actions looks like stealing of personal data
- md9_1sjm.exe (PID: 912)
- Updbdate.exe (PID: 2840)
- 28975421242.exe (PID: 2548)
- 58852886416.exe (PID: 4584)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
Steals credentials from Web Browsers
- md9_1sjm.exe (PID: 912)
- 28975421242.exe (PID: 2548)
Changes the autorun value in the registry
- Files.exe (PID: 1692)
- 2622697.exe (PID: 3844)
Known privilege escalation attack
- DllHost.exe (PID: 3488)
REDLINE was detected
- Updbdate.exe (PID: 2840)
- IIOCze10ia6C3qcHL8WdIoPn.exe (PID: 2904)
- 2spjavkuPys0xLBi9CM9lx28.exe (PID: 4408)
Loads dropped or rewritten executable
- rUNdlL32.eXe (PID: 2740)
Stealing of credential data
- Updbdate.exe (PID: 2840)
- OQXLIJWMTsY7UIFTrgzFA6q6.exe (PID: 576)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 4880)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 3000)
Disables Windows Defender
- File.exe (PID: 1236)
FICKER was detected
- 28975421242.exe (PID: 2548)
SUSPICIOUS
Reads the computer name
- 817.exe (PID: 3056)
- Lsr.exe (PID: 952)
- SoCleanInst.exe (PID: 740)
- Updbdate.exe (PID: 2840)
- md9_1sjm.exe (PID: 912)
- Folder.exe (PID: 1516)
- Folder.exe (PID: 2400)
- Info.exe (PID: 1744)
- File.exe (PID: 1236)
- tmpBCA0_tmp.exe (PID: 2152)
- Intere.exe.com (PID: 2364)
- IELowutil.exe (PID: 2016)
- Install.exe (PID: 2600)
- Files.exe (PID: 2372)
- jfiag3g_gg.exe (PID: 2428)
- Install.exe (PID: 2692)
- Files.exe (PID: 1692)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 900)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 3296)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 2168)
- __WrSzGQXtH88BjDO92QZFob.exe (PID: 2452)
- 28975421242.exe (PID: 2548)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 2616)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 3000)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 2276)
- JqbjRAs0RVpnD4odvZCKrxDd.exe (PID: 1736)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 3760)
- IIOCze10ia6C3qcHL8WdIoPn.exe (PID: 2904)
- qgx7sz9EiN_cUHDnQbkKeopv.exe (PID: 3452)
- 4542354.exe (PID: 5560)
- 2spjavkuPys0xLBi9CM9lx28.exe (PID: 4408)
- 58852886416.exe (PID: 4584)
- aLqMv5BypW7rykh2NgSu_9qQ.exe (PID: 6008)
- 2622697.exe (PID: 3844)
- OQXLIJWMTsY7UIFTrgzFA6q6.exe (PID: 576)
Drops a file with too old compile date
- 817.exe (PID: 3056)
- File.exe (PID: 1236)
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
Checks supported languages
- Updbdate.exe (PID: 2840)
- 817.exe (PID: 3056)
- Lsr.exe (PID: 952)
- Info.exe (PID: 1744)
- md9_1sjm.exe (PID: 912)
- SoCleanInst.exe (PID: 740)
- Folder.exe (PID: 1516)
- File.exe (PID: 1236)
- Folder.exe (PID: 2400)
- tmpBCA0_tmp.exe (PID: 2152)
- cmd.exe (PID: 568)
- cmd.exe (PID: 2388)
- Intere.exe.com (PID: 2248)
- Intere.exe.com (PID: 2364)
- IELowutil.exe (PID: 2016)
- Files.exe (PID: 2372)
- Install.exe (PID: 2600)
- jfiag3g_gg.exe (PID: 2428)
- pub2.exe (PID: 2504)
- Files.exe (PID: 1692)
- Install.exe (PID: 2692)
- jfiag3g_gg.exe (PID: 1736)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
- efX7rxCXfVYUzI1uXy2HKW4T.exe (PID: 3532)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 900)
- VEEvoZX2PyYsZaBlNDSH1g50.exe (PID: 2872)
- VEEvoZX2PyYsZaBlNDSH1g50.exe (PID: 1668)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 3296)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
- 504jccsHC07RnRMSjzvMtNeT.exe (PID: 3588)
- QrzJinnWMAyQtyHTbSRlHMWq.exe (PID: 2436)
- cmd.exe (PID: 3924)
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
- __WrSzGQXtH88BjDO92QZFob.exe (PID: 2452)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 2168)
- 28975421242.exe (PID: 3044)
- _t6qKZ1cnUfvraJJk6jkiXIa.exe (PID: 2328)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 2616)
- 28975421242.exe (PID: 2548)
- n15lI2QeJcffjWJvEY1l3dve.exe (PID: 1684)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 3000)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 2276)
- qgx7sz9EiN_cUHDnQbkKeopv.exe (PID: 3452)
- JqbjRAs0RVpnD4odvZCKrxDd.exe (PID: 1736)
- IIOCze10ia6C3qcHL8WdIoPn.exe (PID: 2904)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 3760)
- 4542354.exe (PID: 5560)
- OQXLIJWMTsY7UIFTrgzFA6q6.exe (PID: 576)
- cmd.exe (PID: 2644)
- 58852886416.exe (PID: 4584)
- 2spjavkuPys0xLBi9CM9lx28.exe (PID: 4408)
- aLqMv5BypW7rykh2NgSu_9qQ.exe (PID: 6008)
- 2622697.exe (PID: 3844)
- cmd.exe (PID: 4212)
- 60232995282.exe (PID: 3728)
Executable content was dropped or overwritten
- 817.exe (PID: 3056)
- md9_1sjm.exe (PID: 912)
- Folder.exe (PID: 2400)
- Lsr.exe (PID: 952)
- Intere.exe.com (PID: 2364)
- Files.exe (PID: 1692)
- File.exe (PID: 1236)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- JqbjRAs0RVpnD4odvZCKrxDd.exe (PID: 1736)
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
- OQXLIJWMTsY7UIFTrgzFA6q6.exe (PID: 576)
Drops a file that was compiled in debug mode
- 817.exe (PID: 3056)
- Folder.exe (PID: 2400)
- Files.exe (PID: 1692)
- File.exe (PID: 1236)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
- Intere.exe.com (PID: 2364)
- JqbjRAs0RVpnD4odvZCKrxDd.exe (PID: 1736)
- OQXLIJWMTsY7UIFTrgzFA6q6.exe (PID: 576)
Drops a file with a compile date too recent
- 817.exe (PID: 3056)
- md9_1sjm.exe (PID: 912)
- File.exe (PID: 1236)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
Executed via COM
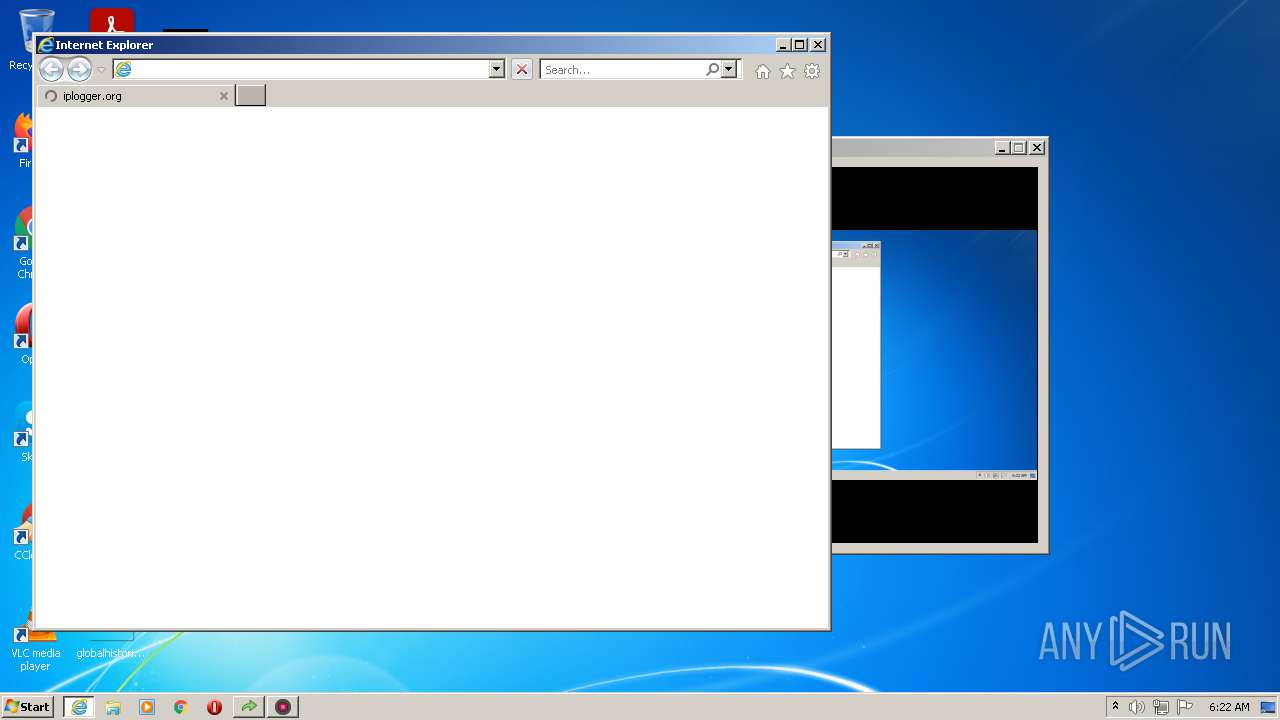
- iexplore.exe (PID: 3040)
- DllHost.exe (PID: 3488)
Reads Environment values
- Lsr.exe (PID: 952)
- SoCleanInst.exe (PID: 740)
- Updbdate.exe (PID: 2840)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 2168)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- __WrSzGQXtH88BjDO92QZFob.exe (PID: 2452)
- IIOCze10ia6C3qcHL8WdIoPn.exe (PID: 2904)
- 2spjavkuPys0xLBi9CM9lx28.exe (PID: 4408)
- 4542354.exe (PID: 5560)
- 28975421242.exe (PID: 2548)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 3000)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2968)
Application launched itself
- Folder.exe (PID: 1516)
- Intere.exe.com (PID: 2248)
- cmd.exe (PID: 568)
- Files.exe (PID: 2372)
- VEEvoZX2PyYsZaBlNDSH1g50.exe (PID: 1668)
- obtD_o3p_iEYTndZ1TNy7hPb.exe (PID: 900)
- 28975421242.exe (PID: 3044)
- KWOuZjIUsBC5m5NxQU5tJRms.exe (PID: 2616)
- KkKG8d5DduZbXt0AbBNJQJNL.exe (PID: 2276)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 2168)
Executed via WMI
- rUNdlL32.eXe (PID: 2740)
Starts CMD.EXE for commands execution
- tmpBCA0_tmp.exe (PID: 2152)
- cmd.exe (PID: 568)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
Starts application with an unusual extension
- Intere.exe.com (PID: 2248)
- cmd.exe (PID: 2388)
Reads mouse settings
- Intere.exe.com (PID: 2364)
- Intere.exe.com (PID: 2248)
Creates files in the user directory
- Intere.exe.com (PID: 2364)
- File.exe (PID: 1236)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- 2622697.exe (PID: 3844)
Reads the cookies of Google Chrome
- md9_1sjm.exe (PID: 912)
Drop AutoIt3 executable file
- Intere.exe.com (PID: 2364)
Adds / modifies Windows certificates
- md9_1sjm.exe (PID: 912)
- Install.exe (PID: 2692)
- File.exe (PID: 1236)
Reads the cookies of Mozilla Firefox
- md9_1sjm.exe (PID: 912)
Searches for installed software
- Updbdate.exe (PID: 2840)
- 28975421242.exe (PID: 2548)
Checks for external IP
- Files.exe (PID: 1692)
- File.exe (PID: 1236)
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
- 28975421242.exe (PID: 2548)
Reads Windows owner or organization settings
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
Reads the Windows organization settings
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
Creates files in the program directory
- 28975421242.exe (PID: 2548)
- aLqMv5BypW7rykh2NgSu_9qQ.exe (PID: 6008)
Reads CPU info
- 58852886416.exe (PID: 4584)
- 28975421242.exe (PID: 2548)
Creates a directory in Program Files
- aLqMv5BypW7rykh2NgSu_9qQ.exe (PID: 6008)
Creates a software uninstall entry
- aLqMv5BypW7rykh2NgSu_9qQ.exe (PID: 6008)
Starts itself from another location
- 2622697.exe (PID: 3844)
INFO
Checks supported languages
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 2968)
- rUNdlL32.eXe (PID: 2740)
- dllhost.exe (PID: 3180)
- findstr.exe (PID: 3244)
- PING.EXE (PID: 1660)
- DllHost.exe (PID: 3488)
Changes internet zones settings
- iexplore.exe (PID: 3040)
Reads the computer name
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 3040)
- rUNdlL32.eXe (PID: 2740)
- PING.EXE (PID: 1660)
- DllHost.exe (PID: 3488)
Application launched itself
- iexplore.exe (PID: 3040)
Reads settings of System Certificates
- Lsr.exe (PID: 952)
- iexplore.exe (PID: 2968)
- SoCleanInst.exe (PID: 740)
- md9_1sjm.exe (PID: 912)
- File.exe (PID: 1236)
- iexplore.exe (PID: 3040)
- Install.exe (PID: 2692)
- Updbdate.exe (PID: 2840)
- Files.exe (PID: 1692)
- QrzJinnWMAyQtyHTbSRlHMWq.tmp (PID: 3172)
- vwxa4WWiZNwIOgD8hgqfZ9xL.exe (PID: 2168)
- pJkWt033jWcTaTCRTe35ziNj.exe (PID: 1404)
- duPQbECLL5fmGlsDVBUJJqIa.exe (PID: 400)
- __WrSzGQXtH88BjDO92QZFob.exe (PID: 2452)
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
Checks Windows Trust Settings
- iexplore.exe (PID: 2968)
- File.exe (PID: 1236)
- iexplore.exe (PID: 3040)
- Install.exe (PID: 2692)
Creates files in the user directory
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 2968)
Changes settings of System certificates
- iexplore.exe (PID: 3040)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3040)
Dropped object may contain Bitcoin addresses
- lbwNHDNb0ZoBXnVzgiOUthaB.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1ec40 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 143360 |
| CodeSize: | 201216 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2020:12:01 19:00:55+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2020 18:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Dec-2020 18:00:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000310EA | 0x00031200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
.rdata | 0x00033000 | 0x0000A612 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22174 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29825 |
.rsrc | 0x00063000 | 0x00015168 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24093 |
.reloc | 0x00079000 | 0x00002268 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55486 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.01704 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.94627 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
138
Monitored processes
70
Malicious processes
30
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | "C:\Users\admin\Documents\duPQbECLL5fmGlsDVBUJJqIa.exe" | C:\Users\admin\Documents\duPQbECLL5fmGlsDVBUJJqIa.exe | File.exe | ||||||||||||
User: admin Company: hfghggfgd Integrity Level: HIGH Description: hfghggfgd Exit code: 0 Version: 1.0.1.1 Modules
| |||||||||||||||
| 568 | "C:\Windows\System32\cmd.exe" /c cmd < Vedo.csv | C:\Windows\System32\cmd.exe | — | tmpBCA0_tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 576 | "C:\Users\admin\Documents\OQXLIJWMTsY7UIFTrgzFA6q6.exe" | C:\Users\admin\Documents\OQXLIJWMTsY7UIFTrgzFA6q6.exe | File.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 740 | "C:\Users\admin\Desktop\SoCleanInst.exe" | C:\Users\admin\Desktop\SoCleanInst.exe | 817.exe | ||||||||||||
User: admin Company: hfghggfgd Integrity Level: MEDIUM Description: hfghggfgd Exit code: 0 Version: 1.0.1.1 Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Documents\obtD_o3p_iEYTndZ1TNy7hPb.exe" | C:\Users\admin\Documents\obtD_o3p_iEYTndZ1TNy7hPb.exe | — | File.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 912 | "C:\Users\admin\Desktop\md9_1sjm.exe" | C:\Users\admin\Desktop\md9_1sjm.exe | 817.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
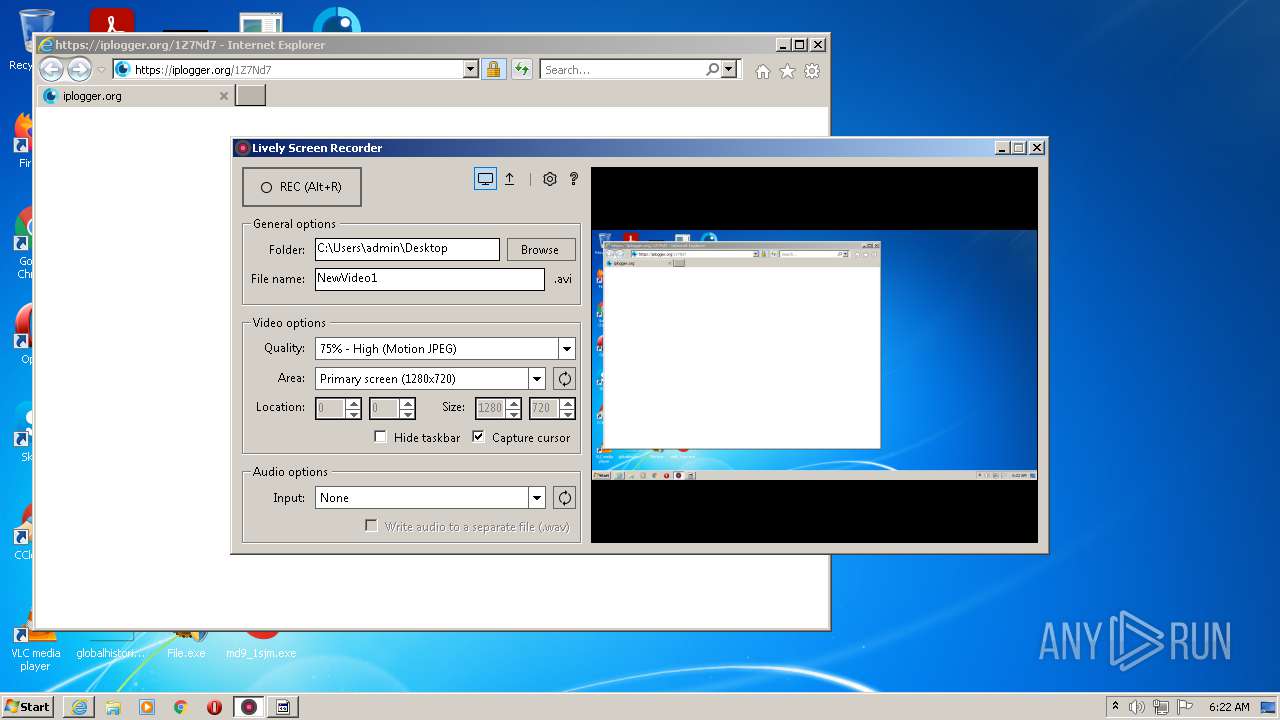
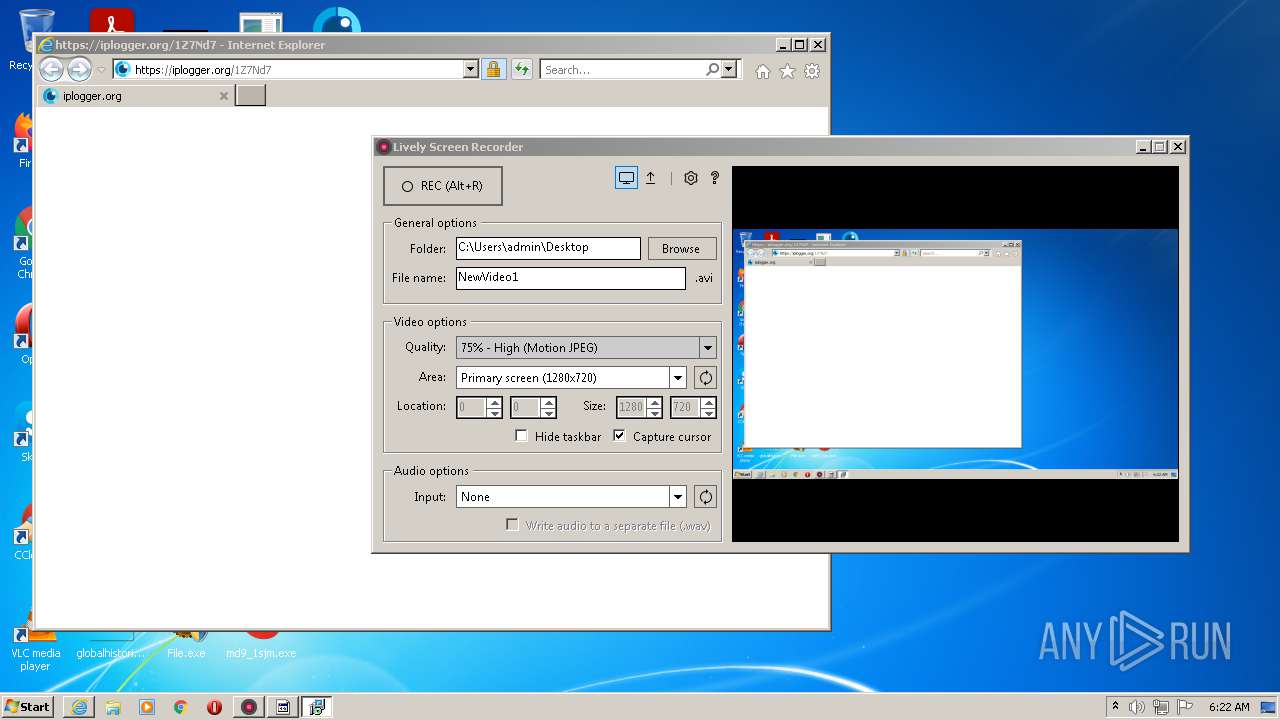
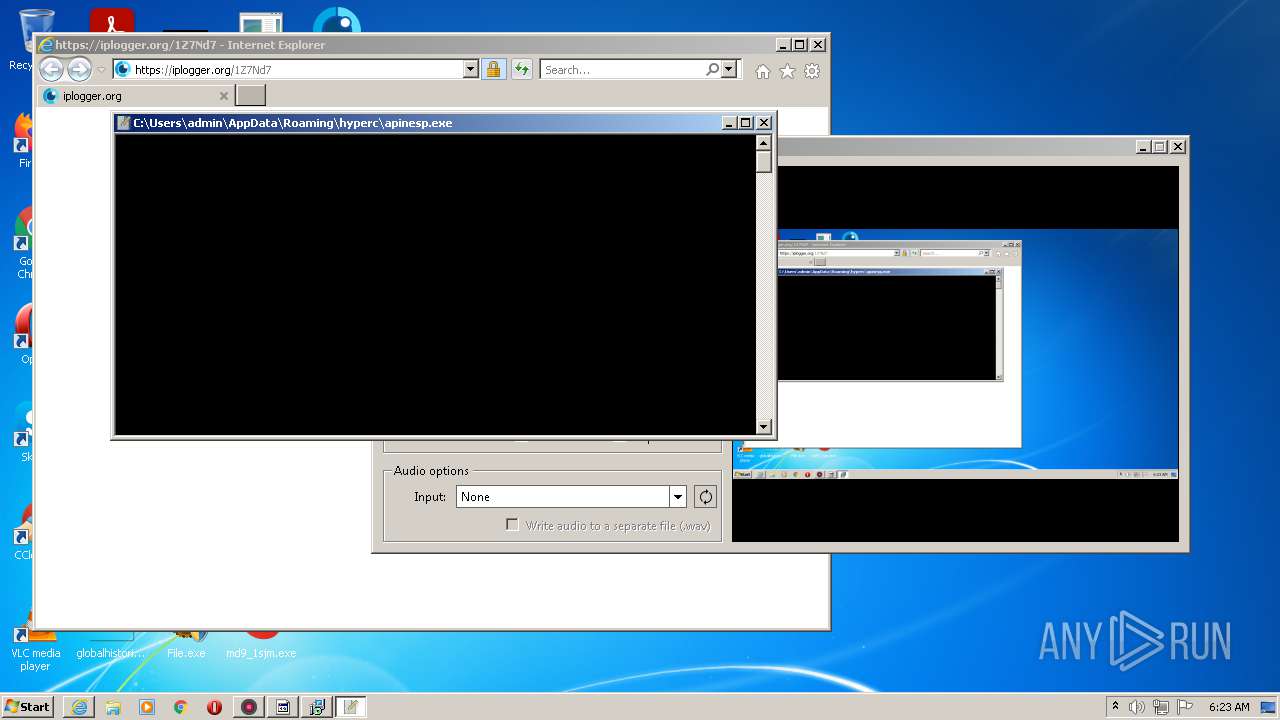
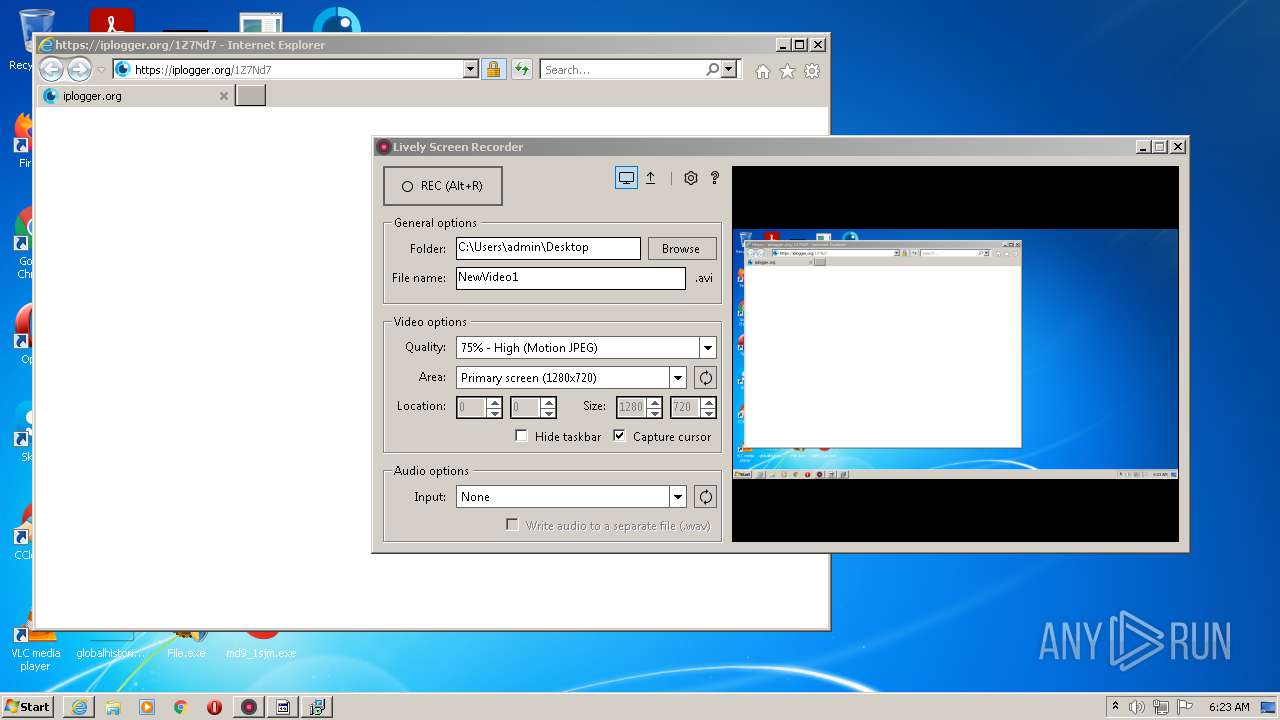
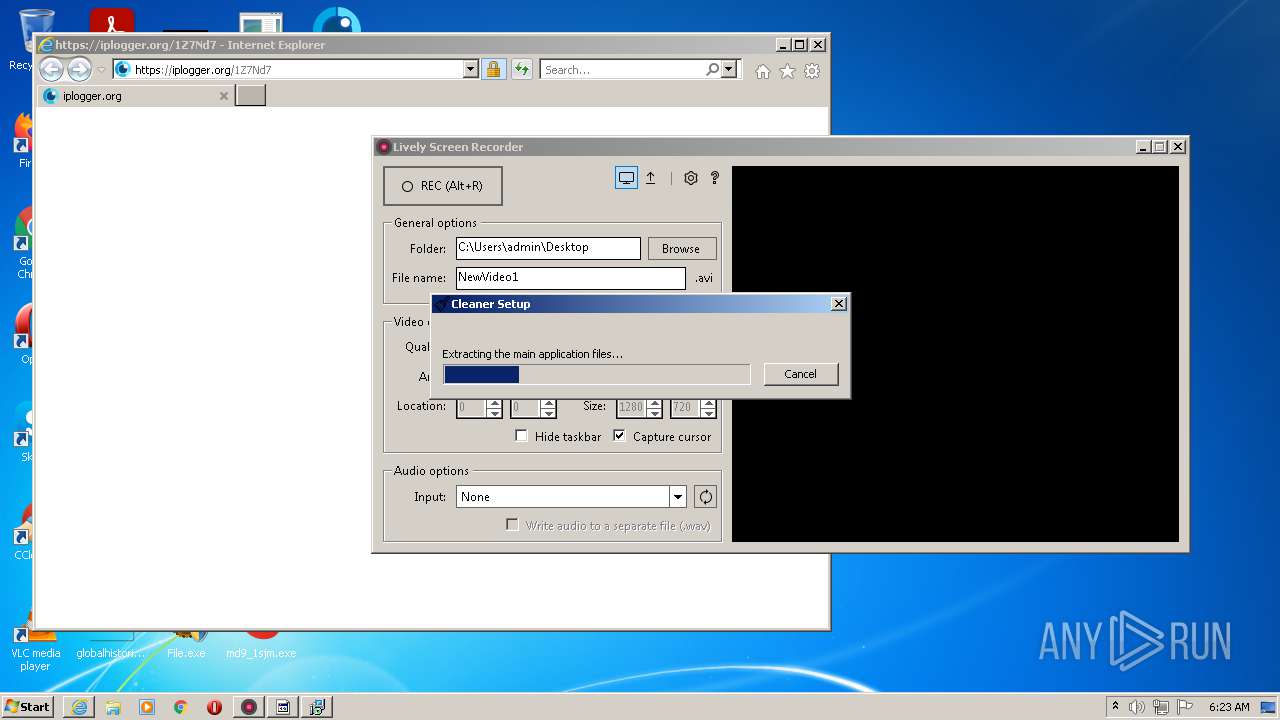
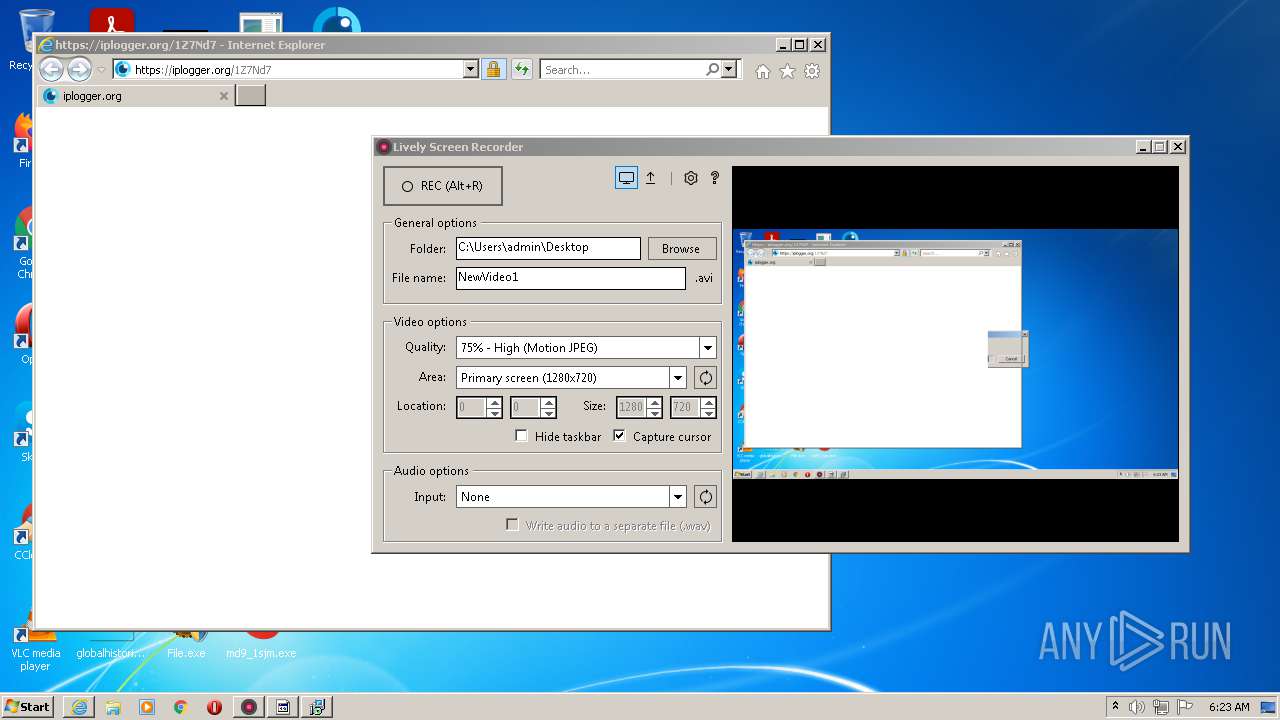
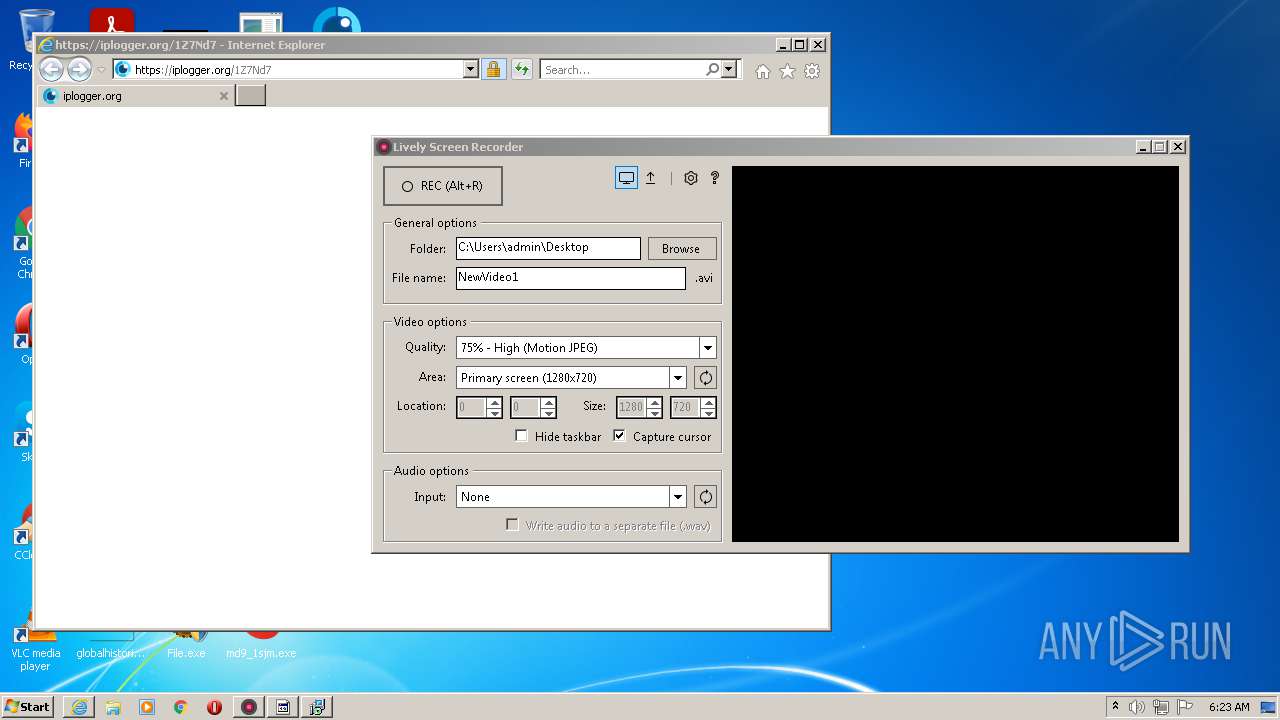
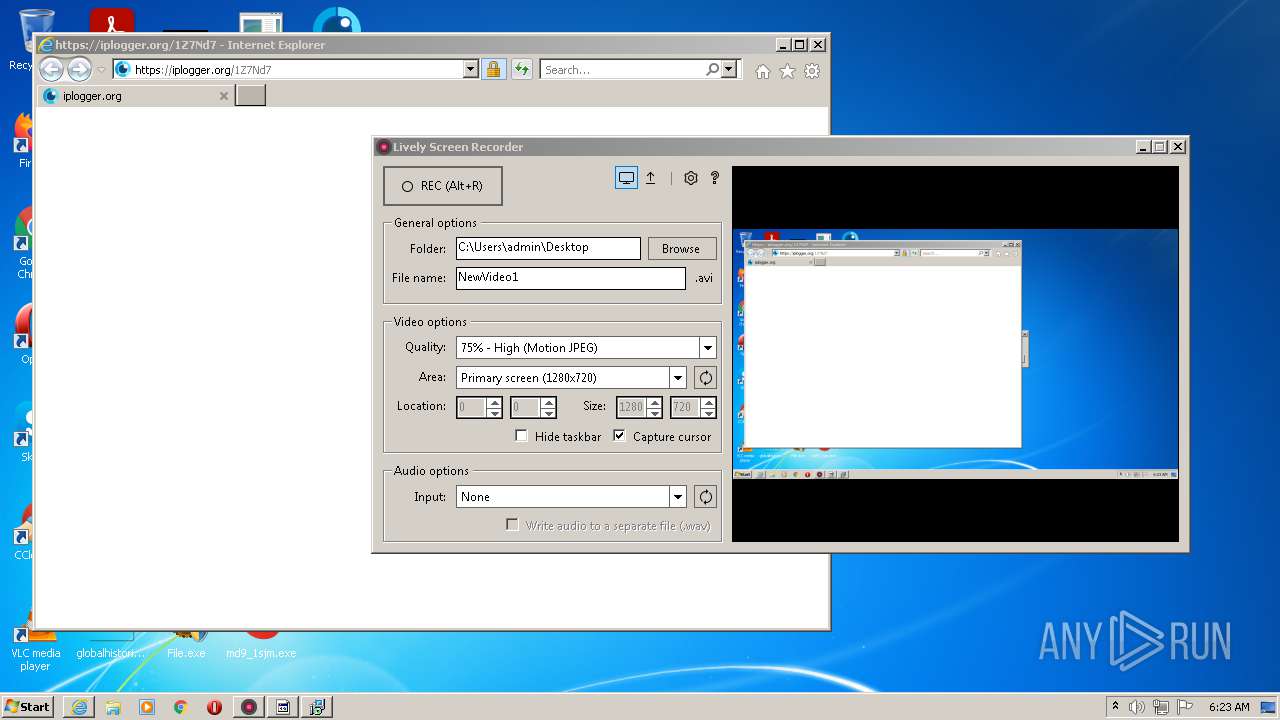
| 952 | "C:\Users\admin\Desktop\Lsr.exe" | C:\Users\admin\Desktop\Lsr.exe | 817.exe | ||||||||||||
User: admin Company: Module Art Integrity Level: MEDIUM Description: Quick Screen Recorder Exit code: 0 Version: 1.2.1 Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\Desktop\File.exe" | C:\Users\admin\Desktop\File.exe | 817.exe | ||||||||||||
User: admin Company: MMSample Disk Integrity Level: HIGH Description: MMSample Disk Exit code: 0 Version: 2.1.1.3 Modules
| |||||||||||||||
| 1404 | "C:\Users\admin\Documents\pJkWt033jWcTaTCRTe35ziNj.exe" | C:\Users\admin\Documents\pJkWt033jWcTaTCRTe35ziNj.exe | File.exe | ||||||||||||
User: admin Company: Microsoft� Visual Studio� Integrity Level: HIGH Description: VsJITDebugger.exe Exit code: 0 Version: 16.0.100.0 Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\Desktop\Folder.exe" | C:\Users\admin\Desktop\Folder.exe | — | 817.exe | |||||||||||
User: admin Company: RealVNC Ltd Integrity Level: MEDIUM Description: VNC� Viewer Exit code: 0 Version: 6.21.406 (r44671) Modules
| |||||||||||||||
Total events
192 406
Read events
191 683
Write events
709
Delete events
14
Modification events
| (PID) Process: | (3056) 817.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3056) 817.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3056) 817.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3056) 817.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3056) 817.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FBF23B40-E3F0-101B-8488-00AA003E56F8} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000791B4CDBDE97D701 | |||
| (PID) Process: | (952) Lsr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (952) Lsr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (952) Lsr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (952) Lsr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
Executable files
96
Suspicious files
30
Text files
48
Unknown types
143
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3056 | 817.exe | C:\Users\admin\Desktop\pkts.url | text | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\md9_1sjm.exe | executable | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\SoCleanInst.exe | executable | |
MD5:— | SHA256:— | |||
| 1772 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\Updbdate.exe | executable | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\Lsr.exe | executable | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\File.exe | executable | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\Info.exe | executable | |
MD5:— | SHA256:— | |||
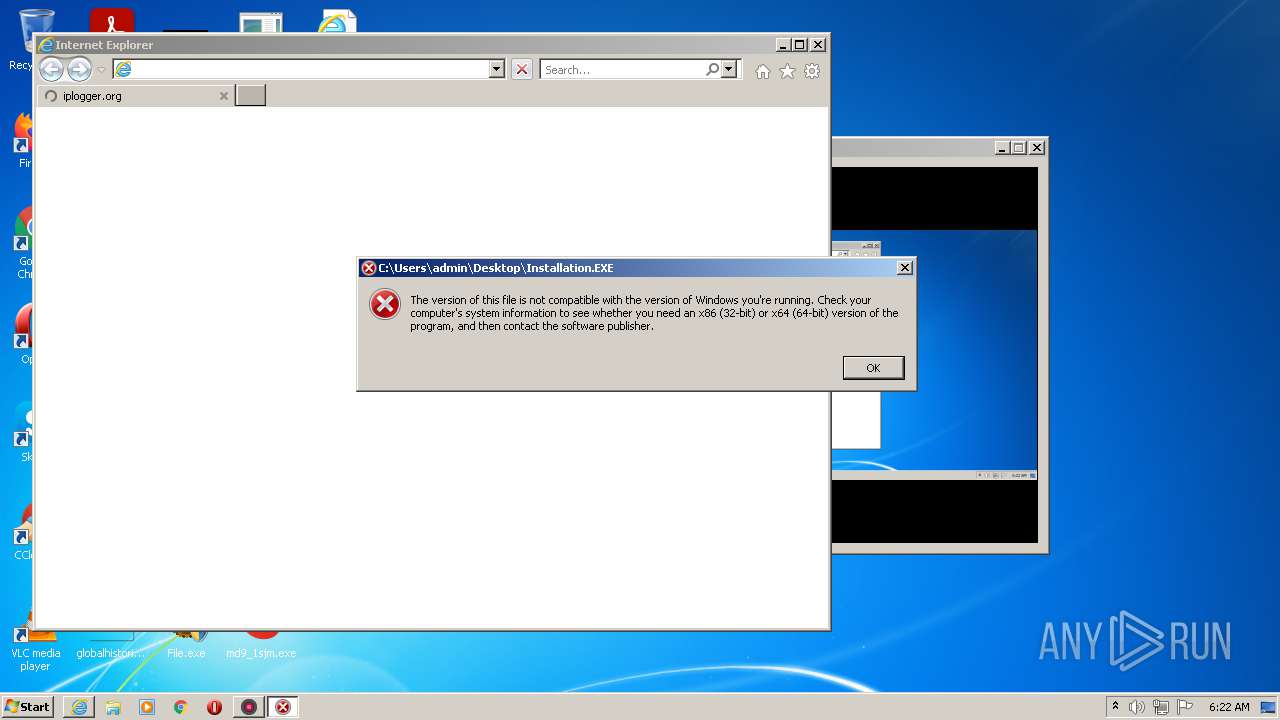
| 3056 | 817.exe | C:\Users\admin\Desktop\Installation.EXE | executable | |
MD5:— | SHA256:— | |||
| 3056 | 817.exe | C:\Users\admin\Desktop\pub2.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
166
TCP/UDP connections
307
DNS requests
65
Threats
361
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | iexplore.exe | GET | 304 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4e9655a668f5dedb | US | — | — | whitelisted |
3040 | iexplore.exe | GET | 304 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8fb906d5c3f15d29 | US | — | — | whitelisted |
1236 | File.exe | GET | 200 | 37.0.10.214:80 | http://37.0.10.214/proxies.txt | NL | text | 2.45 Kb | malicious |
1236 | File.exe | GET | 200 | 37.0.10.237:80 | http://37.0.10.237/base/api/statistics.php | NL | binary | 96 b | suspicious |
2968 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
912 | md9_1sjm.exe | GET | 200 | 186.2.171.3:80 | http://186.2.171.3/seemorebty/il.php?e=md9_1sjm | RU | text | 26 b | malicious |
2968 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2692 | Install.exe | GET | 200 | 93.184.220.29:80 | http://statuse.digitalcertvalidation.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJrF0xYA49jC3D83fgDGesaUkzIQQUf9OZ86BHDjEAVlYijrfMnt3KAYoCEAYJR5FkG19ljPHMaGsuvmc%3D | US | der | 471 b | whitelisted |
1692 | Files.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 280 b | malicious |
2692 | Install.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAWAJn8G8pVTNI4cGFpe7i4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1236 | File.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
952 | Lsr.exe | 95.142.37.102:80 | activityhike.com | Servers.com, Inc. | RU | suspicious |
952 | Lsr.exe | 95.142.37.102:443 | activityhike.com | Servers.com, Inc. | RU | suspicious |
2968 | iexplore.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
912 | md9_1sjm.exe | 186.2.171.3:80 | — | DANCOM LTD | RU | malicious |
2968 | iexplore.exe | 67.27.159.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
740 | SoCleanInst.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
740 | SoCleanInst.exe | 172.67.192.184:443 | webboutiquestudio.xyz | — | US | malicious |
2840 | Updbdate.exe | 193.56.146.78:54955 | — | — | — | malicious |
1236 | File.exe | 37.0.10.214:80 | — | — | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activityhike.com |
| malicious |
iplogger.org |
| shared |
your-info-services.xyz |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
webboutiquestudio.xyz |
| malicious |
google.vrthcobj.com |
| whitelisted |
2no.co |
| whitelisted |
cdn.discordapp.com |
| shared |
VNEHmoQrfRTi.VNEHmoQrfRTi |
| unknown |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
952 | Lsr.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
1236 | File.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
912 | md9_1sjm.exe | A Network Trojan was detected | AV TROJAN Win32/Masson CnC Activity |
1236 | File.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
1692 | Files.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1692 | Files.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1888 | svchost.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Reserved Bit Set |
2840 | Updbdate.exe | A Network Trojan was detected | AV TROJAN RedLine Stealer Config Download |
1236 | File.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
1236 | File.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
88 ETPRO signatures available at the full report