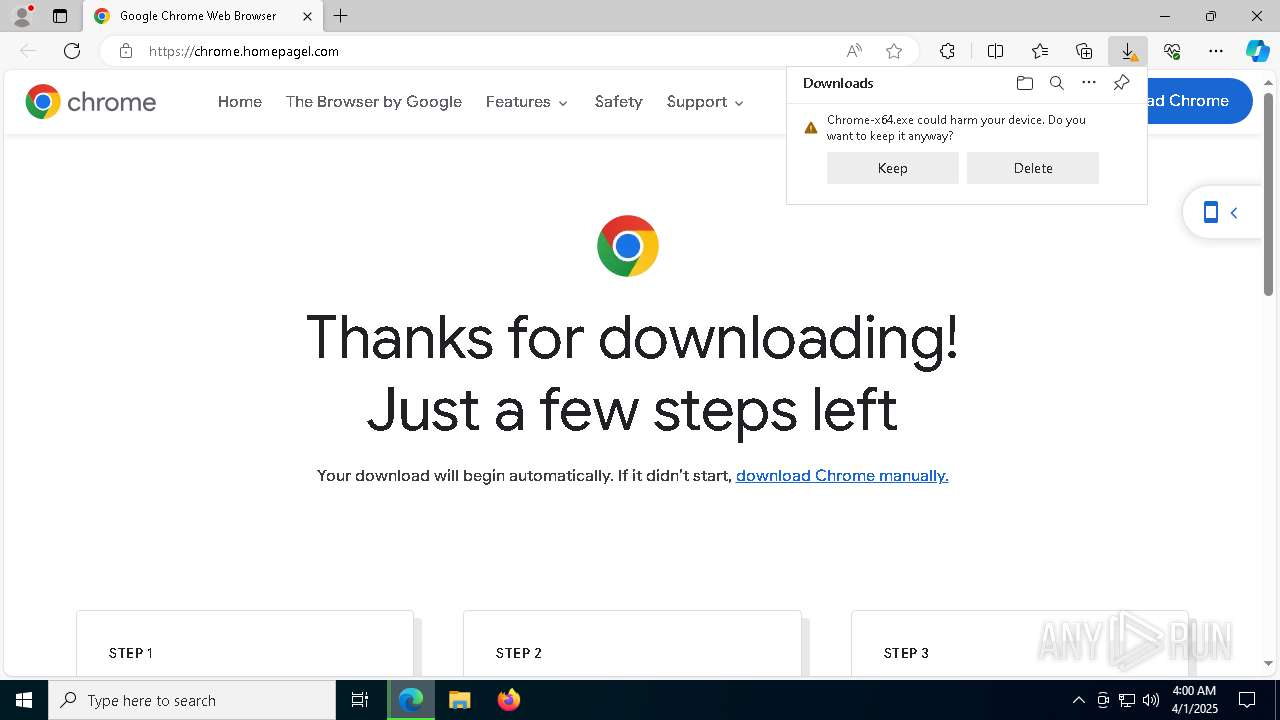
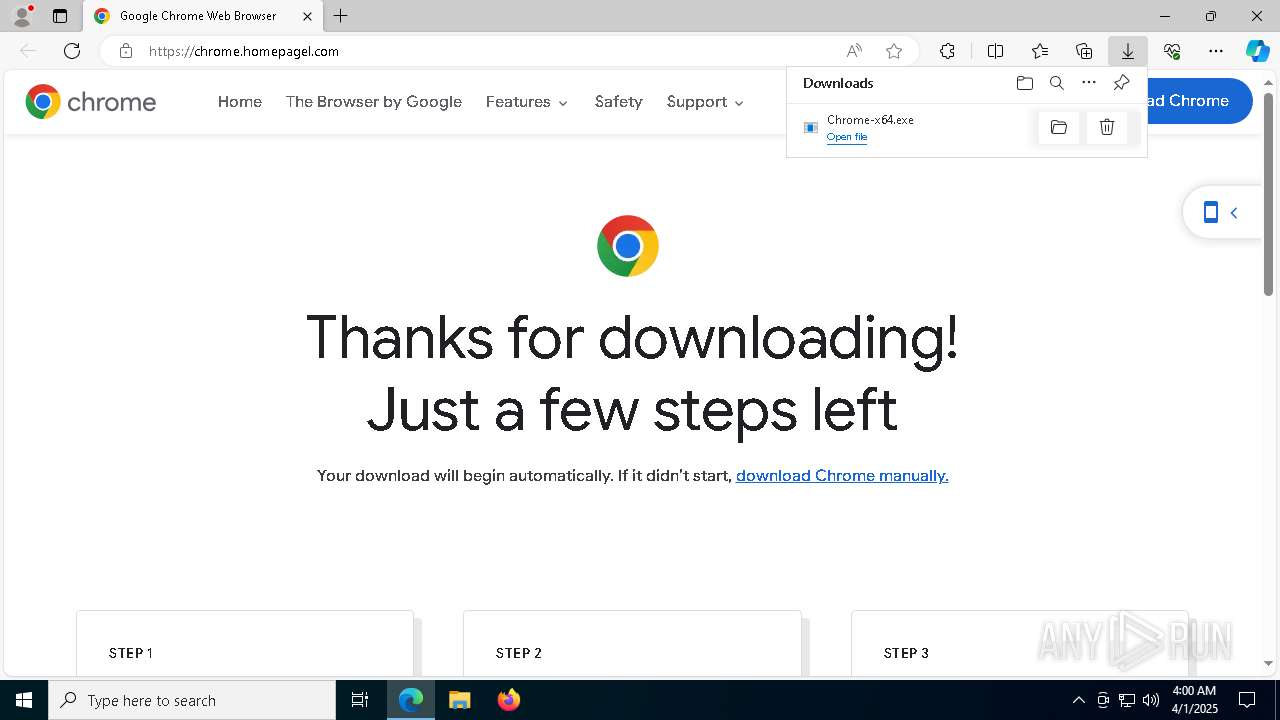
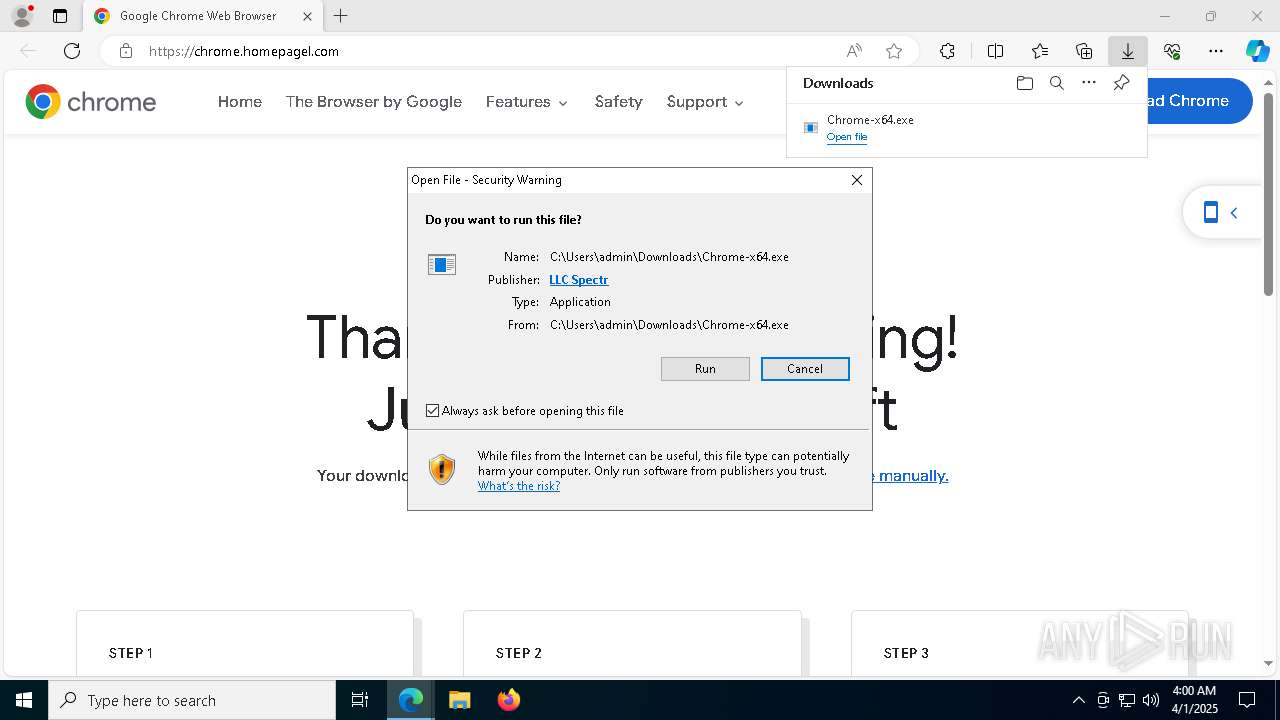
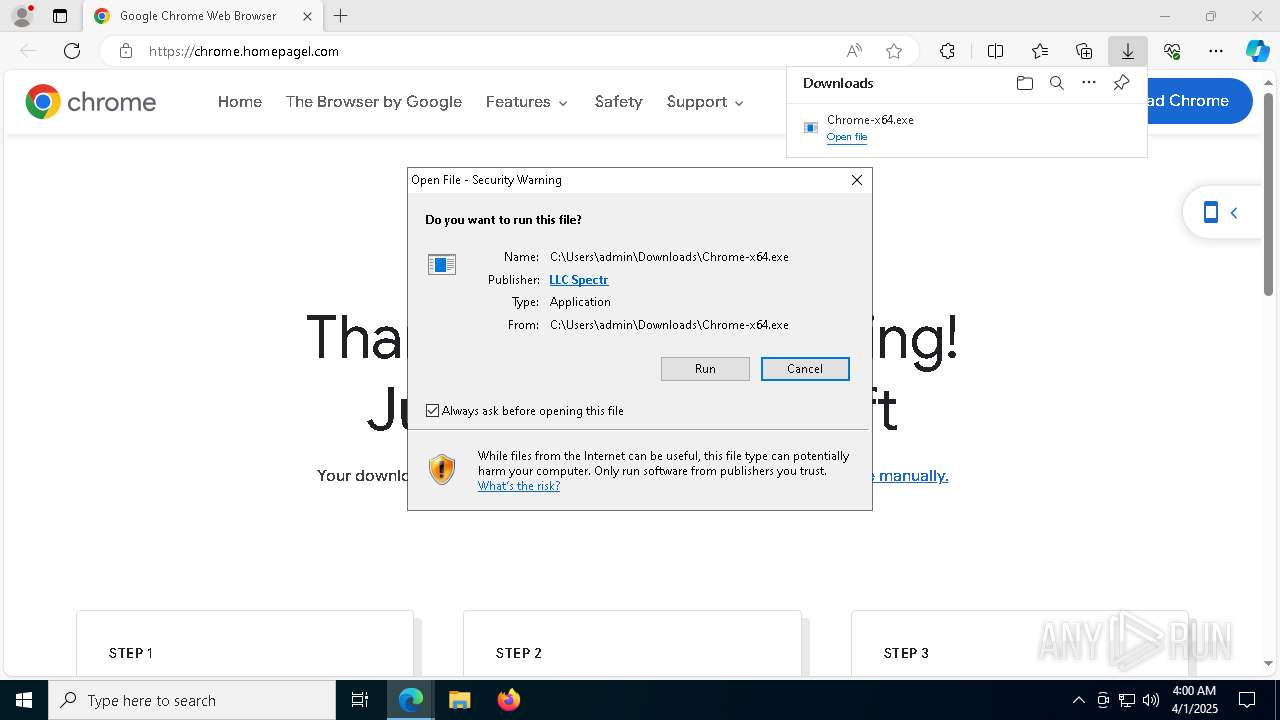
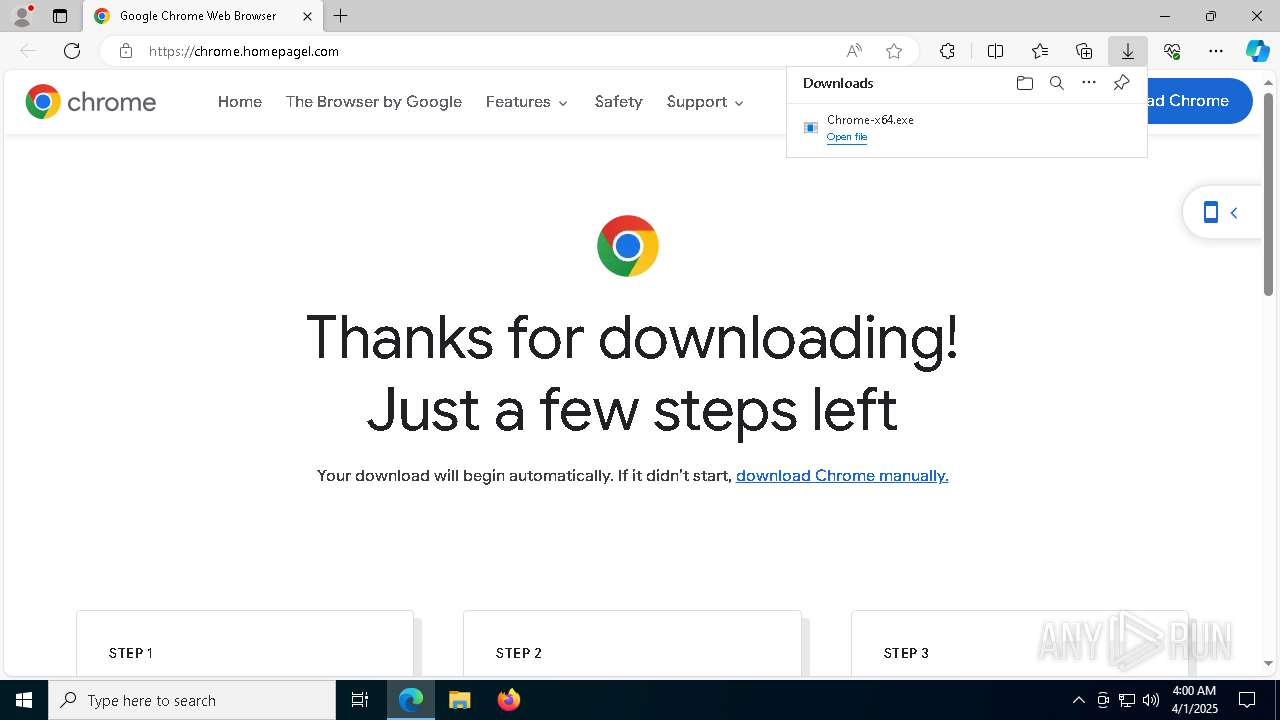
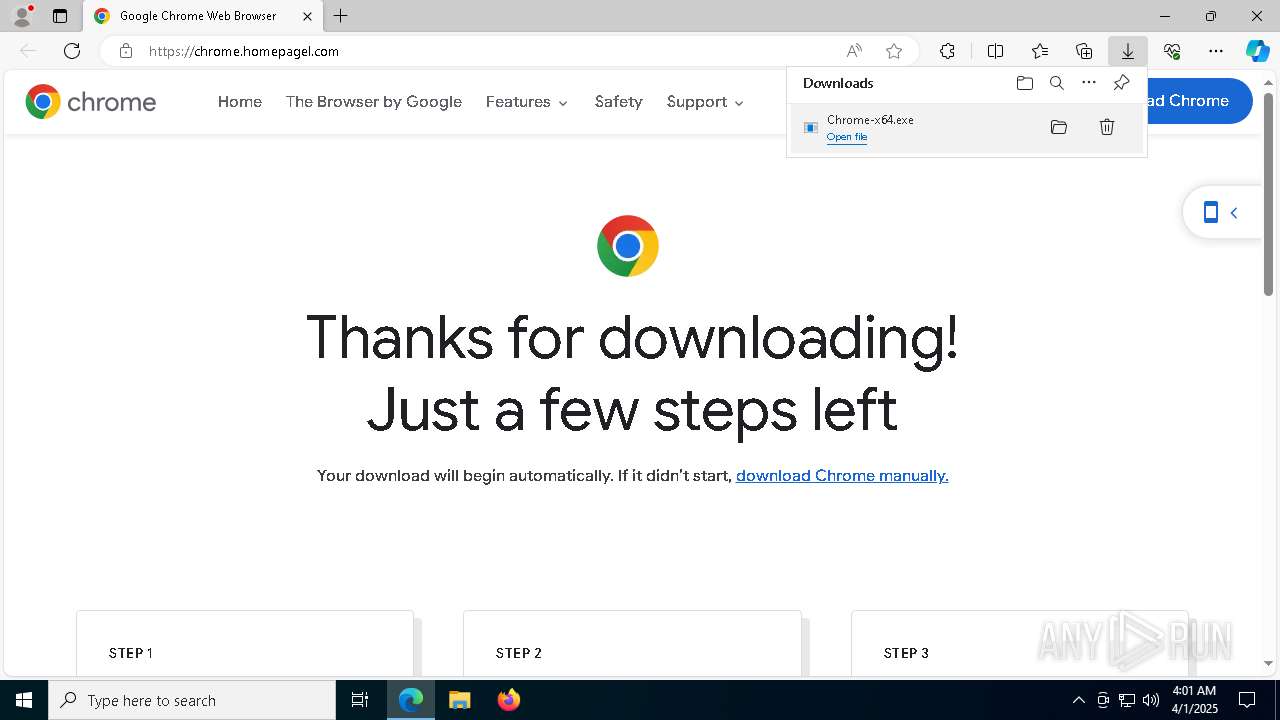
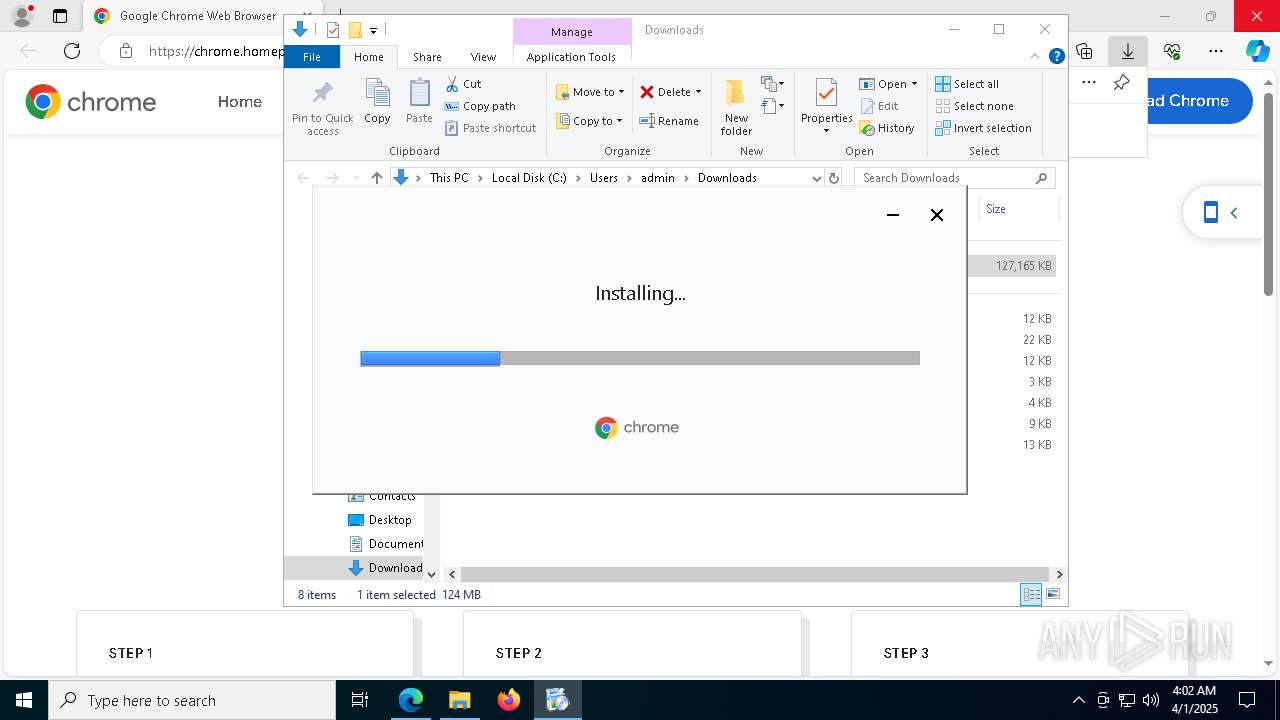
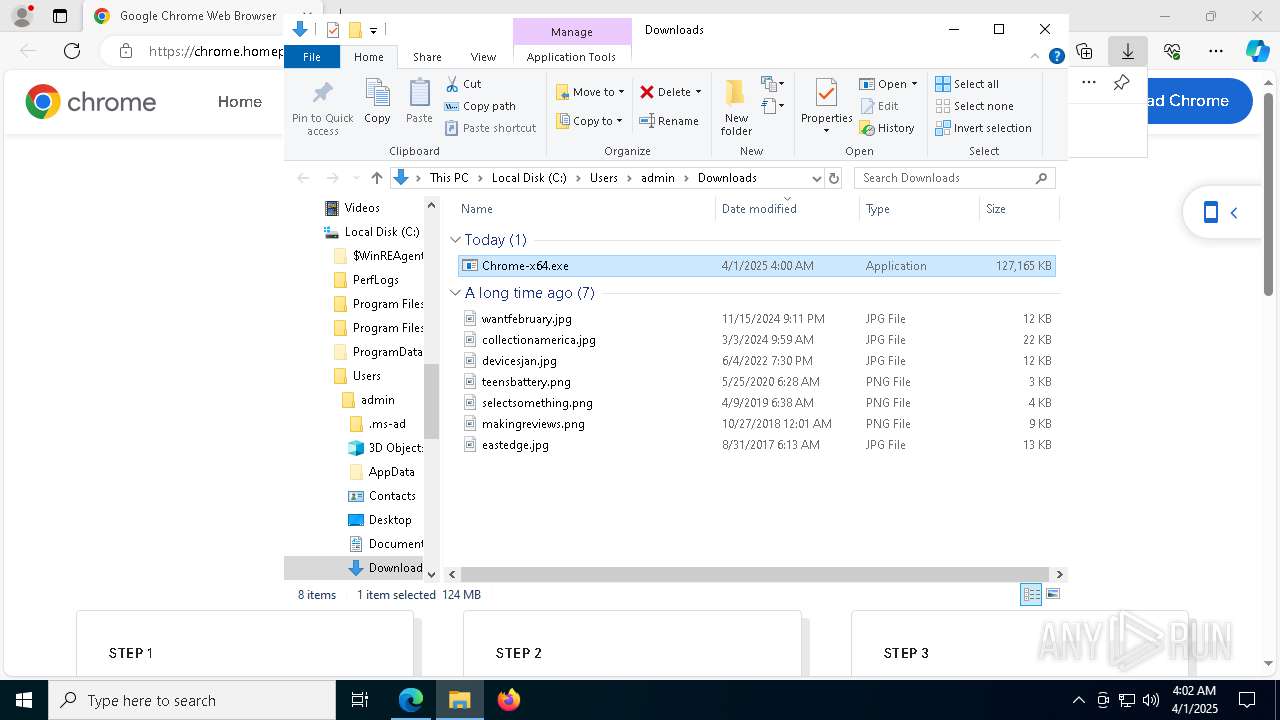
| URL: | chrome.homepagel.com |
| Full analysis: | https://app.any.run/tasks/bb3d5bd2-1ba6-4731-9ccd-bca2efb221d9 |
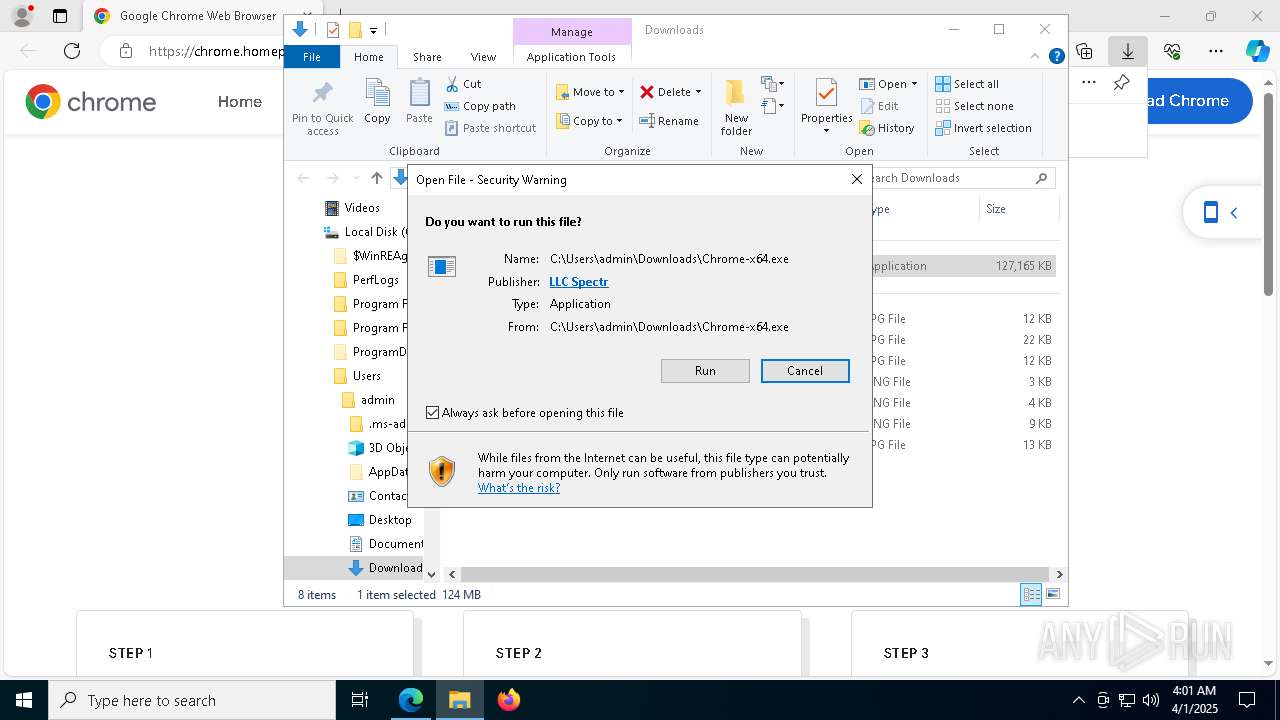
| Verdict: | Malicious activity |
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
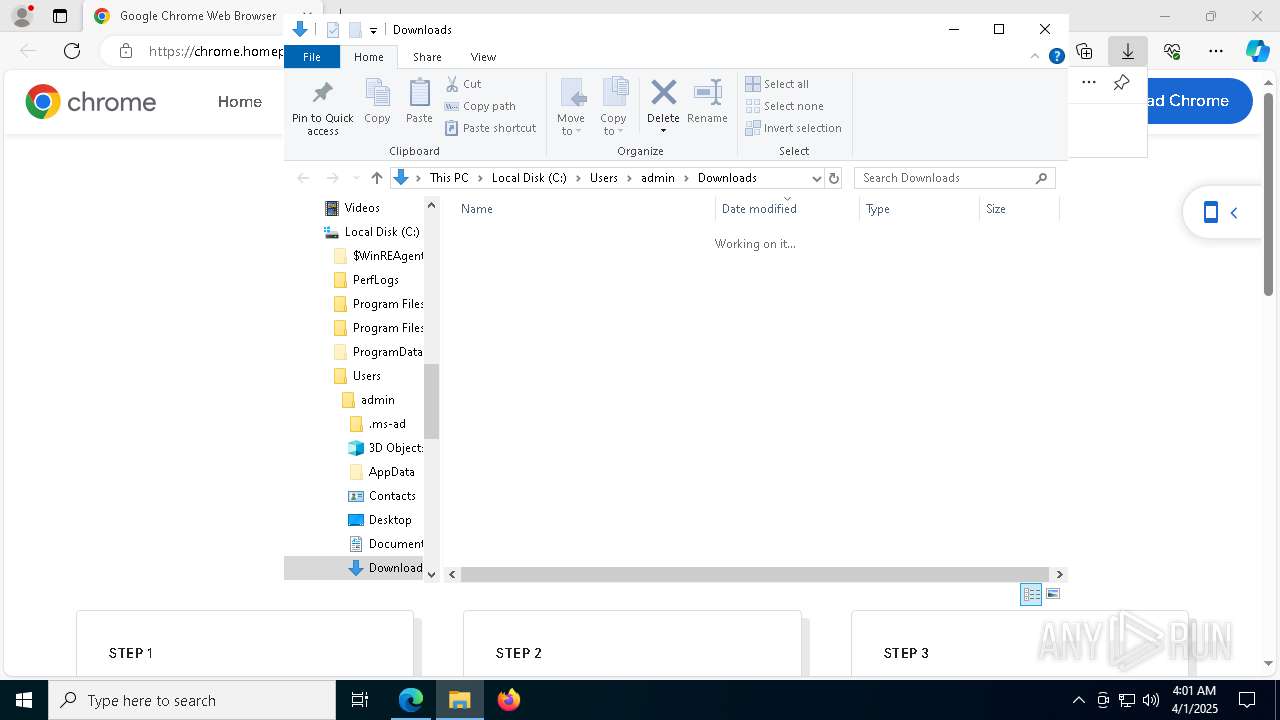
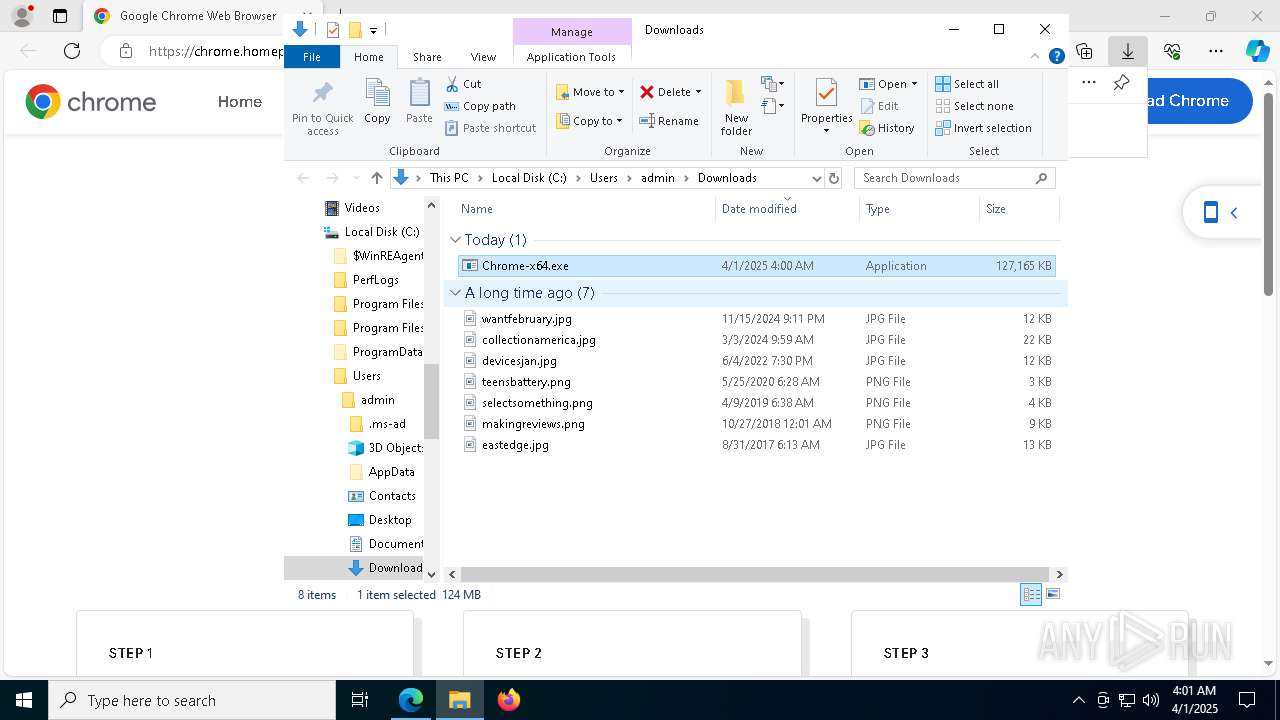
| Analysis date: | April 01, 2025, 04:00:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2B103D9E83B909271F444D5E17F34D80 |
| SHA1: | B085B080CC7C89412D2855BAEF0009A4D59927AD |
| SHA256: | 8115B48184464A5C46AF51DE01449BE88B6EE85B326AA43F7C120A3F22F658AA |
| SSDEEP: | 3:S3roI:SkI |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 4300)
- Chrome-x64.exe (PID: 6724)
- Chrome-x64.exe (PID: 4452)
- cmd.exe (PID: 6660)
Changes Windows Defender settings
- cmd.exe (PID: 4300)
- cmd.exe (PID: 6660)
GENERIC has been found (auto)
- Chrome-x64.exe (PID: 6724)
ARECHCLIENT2 has been detected (SURICATA)
- cmd.exe (PID: 6040)
Actions looks like stealing of personal data
- cmd.exe (PID: 6040)
Changes the autorun value in the registry
- setup.exe (PID: 2236)
SUSPICIOUS
Process drops legitimate windows executable
- Chrome-x64.exe (PID: 6108)
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 4976)
Executable content was dropped or overwritten
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 6724)
- decrypted.exe (PID: 7860)
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 4976)
- updater.exe (PID: 5756)
- updater.exe (PID: 7844)
- 134.0.6998.178_chrome_installer.exe (PID: 4784)
- setup.exe (PID: 2236)
The process creates files with name similar to system file names
- Chrome-x64.exe (PID: 6108)
Reads security settings of Internet Explorer
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 6724)
- updater.exe (PID: 5756)
- Chrome-x64.exe (PID: 4452)
- Chrome-x64.exe (PID: 7152)
Starts CMD.EXE for commands execution
- Chrome-x64.exe (PID: 6724)
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 7152)
- ABUsbTips.exe (PID: 2616)
- Chrome-x64.exe (PID: 4452)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4300)
- cmd.exe (PID: 6660)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 4300)
- cmd.exe (PID: 6660)
Starts itself from another location
- decrypted.exe (PID: 7860)
- ABUsbTips.exe (PID: 4976)
The process drops C-runtime libraries
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 4976)
Application launched itself
- updater.exe (PID: 5756)
- updater.exe (PID: 7844)
- updater.exe (PID: 5892)
- setup.exe (PID: 2236)
- setup.exe (PID: 1164)
- updater.exe (PID: 8720)
The executable file from the user directory is run by the CMD process
- Chrome-x64.exe (PID: 6724)
- Chrome-x64.exe (PID: 4452)
Executes as Windows Service
- updater.exe (PID: 7844)
- updater.exe (PID: 5892)
- updater.exe (PID: 8720)
Connects to unusual port
- cmd.exe (PID: 6040)
Executes application which crashes
- decrypted.exe (PID: 1184)
Creates a software uninstall entry
- setup.exe (PID: 2236)
- chrome.exe (PID: 7732)
Searches for installed software
- setup.exe (PID: 2236)
INFO
Application launched itself
- msedge.exe (PID: 5256)
- chrome.exe (PID: 7732)
Executable content was dropped or overwritten
- msedge.exe (PID: 5256)
- msedge.exe (PID: 6768)
Reads Environment values
- identity_helper.exe (PID: 4200)
Reads the computer name
- identity_helper.exe (PID: 4200)
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 6724)
- decrypted.exe (PID: 7860)
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 4976)
- ABUsbTips.exe (PID: 2616)
- Chrome-x64.exe (PID: 7152)
- ChromeSetup.exe (PID: 4488)
- updater.exe (PID: 5756)
- updater.exe (PID: 7844)
- updater.exe (PID: 5892)
- Chrome-x64.exe (PID: 4452)
- 134.0.6998.178_chrome_installer.exe (PID: 4784)
- setup.exe (PID: 2236)
- setup.exe (PID: 1164)
- elevation_service.exe (PID: 4016)
- updater.exe (PID: 8720)
Autorun file from Downloads
- msedge.exe (PID: 4040)
Checks supported languages
- Chrome-x64.exe (PID: 6108)
- identity_helper.exe (PID: 4200)
- decrypted.exe (PID: 7860)
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 4976)
- ABUsbTips.exe (PID: 2616)
- Chrome-x64.exe (PID: 7152)
- ChromeSetup.exe (PID: 4488)
- updater.exe (PID: 5756)
- updater.exe (PID: 6700)
- updater.exe (PID: 7636)
- updater.exe (PID: 7844)
- Chrome-x64.exe (PID: 6724)
- updater.exe (PID: 2340)
- updater.exe (PID: 5892)
- Chrome-x64.exe (PID: 4452)
- 134.0.6998.178_chrome_installer.exe (PID: 4784)
- setup.exe (PID: 2236)
- setup.exe (PID: 516)
- setup.exe (PID: 3828)
- elevation_service.exe (PID: 4016)
- setup.exe (PID: 1164)
- updater.exe (PID: 8664)
- updater.exe (PID: 8720)
Create files in a temporary directory
- Chrome-x64.exe (PID: 6108)
- decrypted.exe (PID: 7860)
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 2616)
- updater.exe (PID: 5756)
Creates files in the program directory
- Chrome-x64.exe (PID: 6108)
- ChromeSetup.exe (PID: 4488)
- updater.exe (PID: 6700)
- updater.exe (PID: 5756)
- updater.exe (PID: 7844)
- updater.exe (PID: 5892)
- setup.exe (PID: 1164)
- setup.exe (PID: 2236)
- updater.exe (PID: 8720)
Checks proxy server information
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 6724)
- updater.exe (PID: 5756)
- Chrome-x64.exe (PID: 7152)
- Chrome-x64.exe (PID: 4452)
- cmd.exe (PID: 6040)
- slui.exe (PID: 8108)
Reads the software policy settings
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 6724)
- slui.exe (PID: 7596)
- updater.exe (PID: 5756)
- updater.exe (PID: 5892)
- Chrome-x64.exe (PID: 4452)
- Chrome-x64.exe (PID: 7152)
- slui.exe (PID: 8108)
- updater.exe (PID: 8720)
Process checks computer location settings
- Chrome-x64.exe (PID: 6108)
- Chrome-x64.exe (PID: 6724)
- Chrome-x64.exe (PID: 4452)
- Chrome-x64.exe (PID: 7152)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 3676)
Creates files or folders in the user directory
- Chrome-x64.exe (PID: 6724)
- ABUsbTips.exe (PID: 4976)
- updater.exe (PID: 5756)
- WerFault.exe (PID: 920)
The sample compiled with english language support
- Chrome-x64.exe (PID: 6724)
- decrypted.exe (PID: 7860)
- decrypted.exe (PID: 1184)
- ABUsbTips.exe (PID: 4976)
- updater.exe (PID: 5756)
- updater.exe (PID: 7844)
- 134.0.6998.178_chrome_installer.exe (PID: 4784)
- setup.exe (PID: 2236)
- msedge.exe (PID: 6768)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2516)
- powershell.exe (PID: 3676)
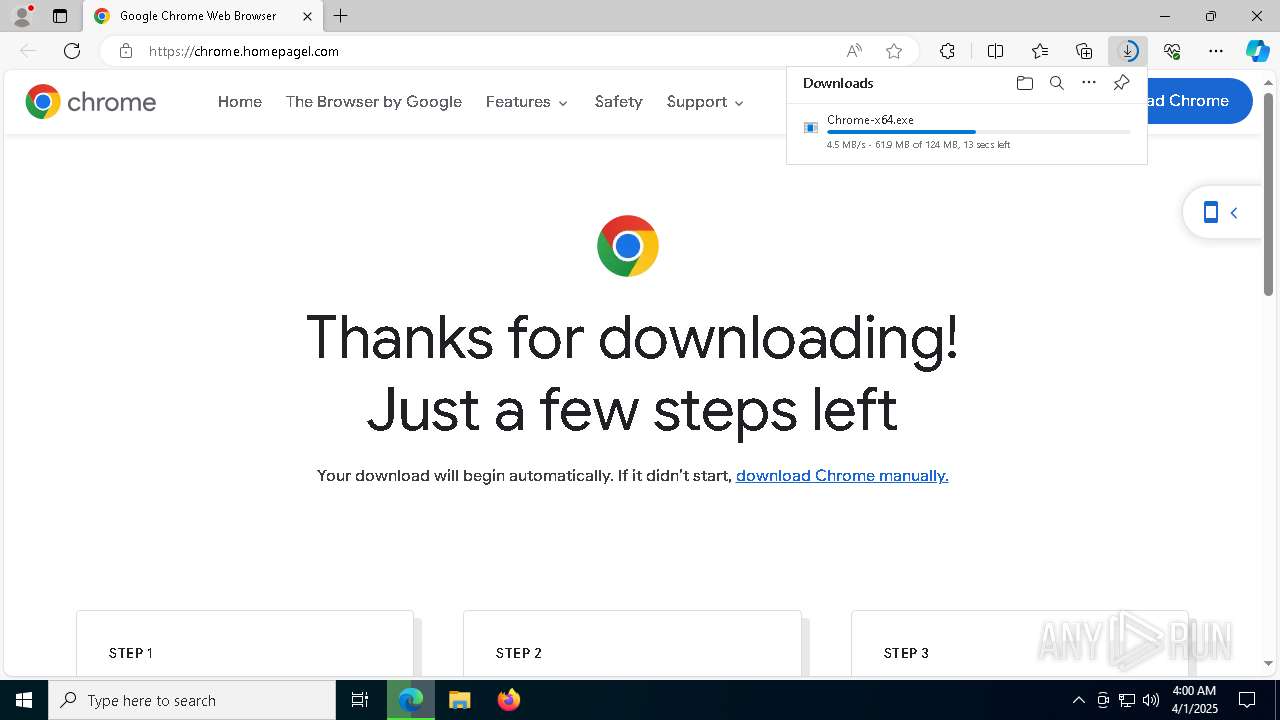
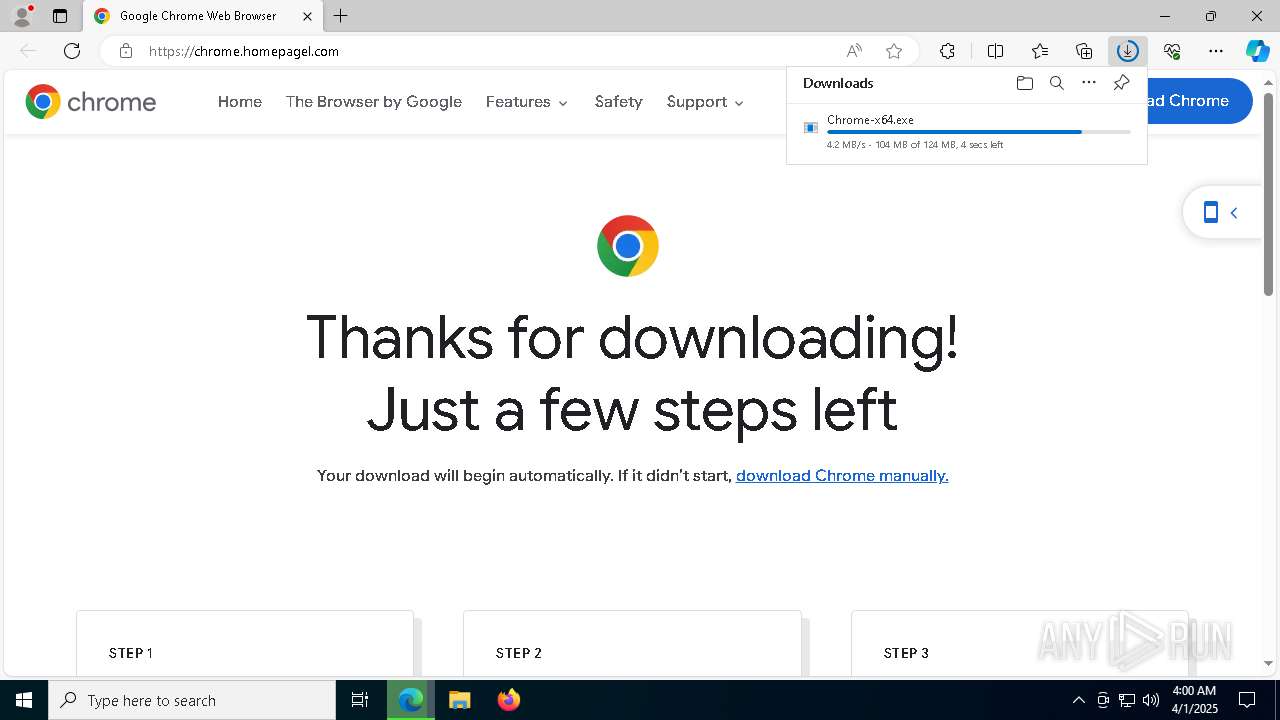
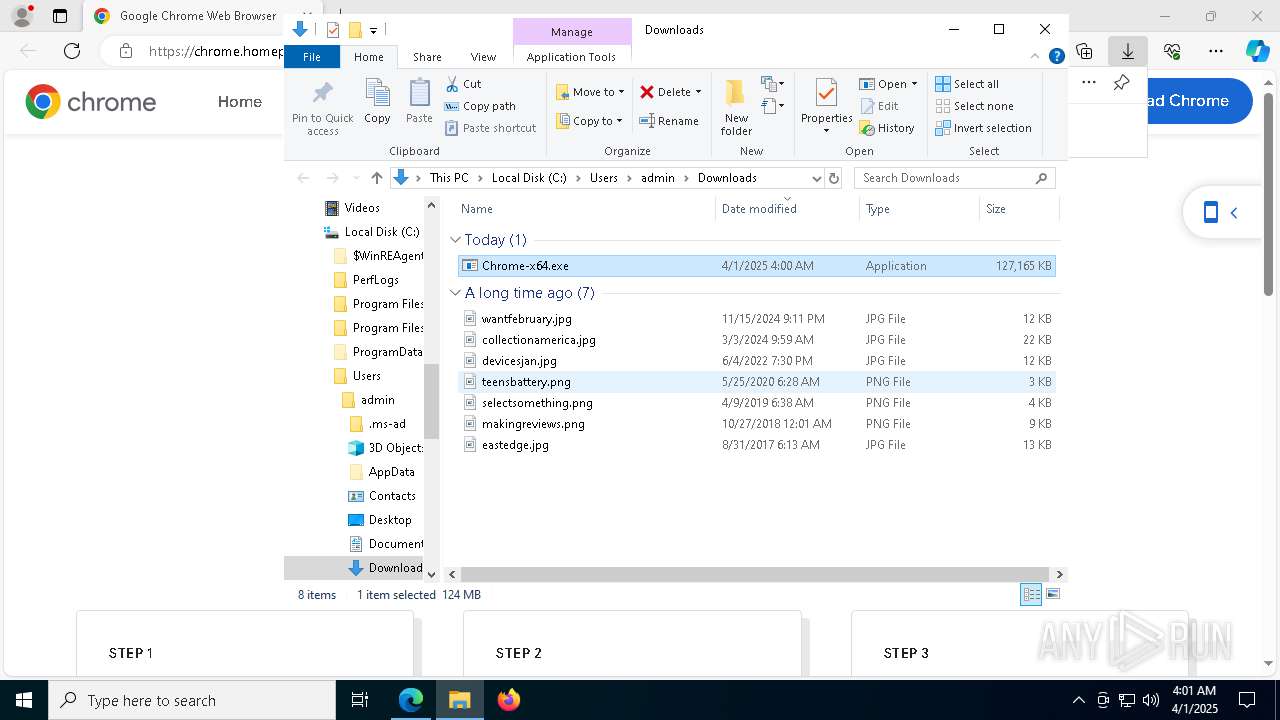
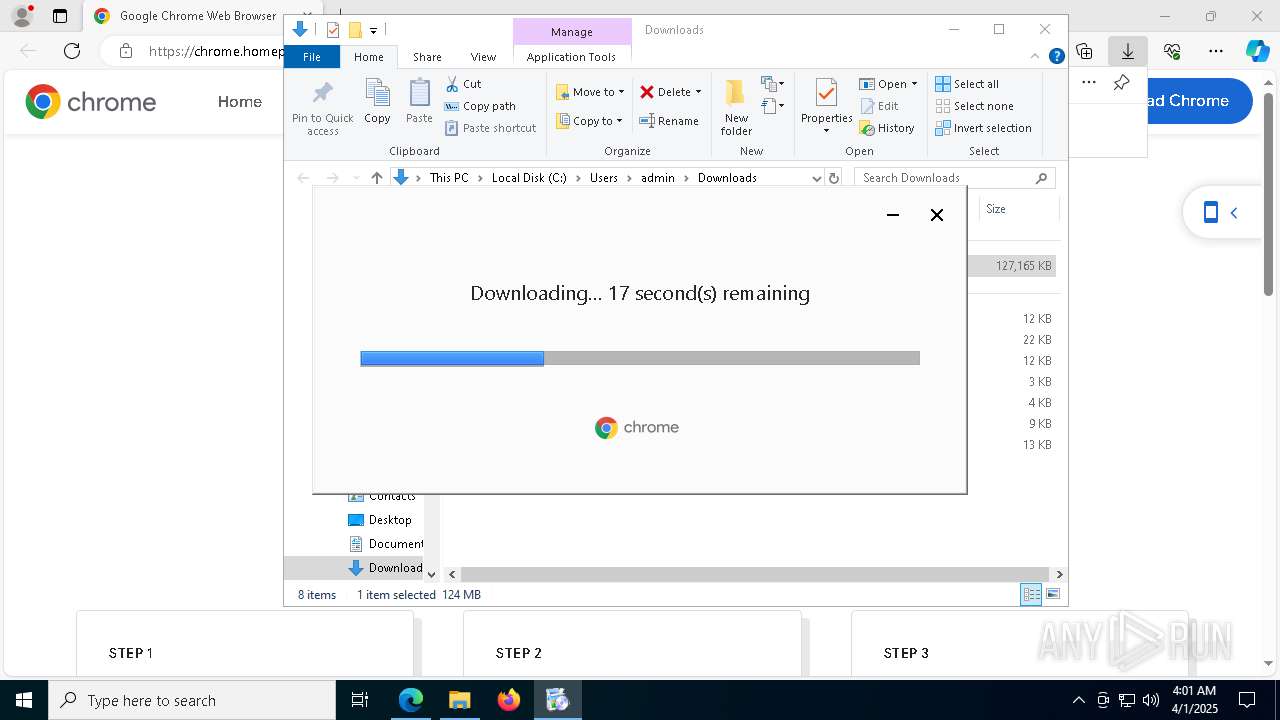
Manual execution by a user
- Chrome-x64.exe (PID: 7152)
- chrome.exe (PID: 7732)
Process checks whether UAC notifications are on
- updater.exe (PID: 5756)
- updater.exe (PID: 7844)
- updater.exe (PID: 5892)
- updater.exe (PID: 8720)
Reads the machine GUID from the registry
- updater.exe (PID: 5756)
Disables trace logs
- cmd.exe (PID: 6040)
Executes as Windows Service
- elevation_service.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
266
Monitored processes
125
Malicious processes
16
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping5892_1543319119\CR_58347.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\WINDOWS\SystemTemp\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=134.0.6998.178 --initial-client-data=0x2b0,0x2b4,0x2b8,0x28c,0x2bc,0x7ff7a32d9ed8,0x7ff7a32d9ee4,0x7ff7a32d9ef0 | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping5892_1543319119\CR_58347.tmp\setup.exe | — | setup.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Chrome Installer Exit code: 0 Version: 134.0.6998.178 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --field-trial-handle=1980,i,8306243105219885676,7688763217155772416,262144 --variations-seed-version --mojo-platform-channel-handle=3520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 134.0.6998.178 Modules
| |||||||||||||||
| 680 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6880 --field-trial-handle=2316,i,12184058912780312870,10016333443819078436,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --field-trial-handle=1980,i,8306243105219885676,7688763217155772416,262144 --variations-seed-version --mojo-platform-channel-handle=5300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 134.0.6998.178 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7364 --field-trial-handle=2316,i,12184058912780312870,10016333443819078436,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\WerFault.exe -u -p 1184 -s 700 | C:\Windows\System32\WerFault.exe | — | decrypted.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=1980,i,8306243105219885676,7688763217155772416,262144 --variations-seed-version --mojo-platform-channel-handle=4164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 134.0.6998.178 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7256 --field-trial-handle=2316,i,12184058912780312870,10016333443819078436,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping5892_1543319119\CR_58347.tmp\setup.exe" --channel=stable --system-level --verbose-logging --create-shortcuts=2 --install-level=1 | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping5892_1543319119\CR_58347.tmp\setup.exe | — | setup.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Chrome Installer Exit code: 73 Version: 134.0.6998.178 Modules
| |||||||||||||||
Total events
44 198
Read events
43 890
Write events
275
Delete events
33
Modification events
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 563CA6DB45902F00 | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CFFD92DB45902F00 | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262912 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {824E062E-0148-4BA9-A5B6-C43E3AB9128B} | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262912 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D7E4333D-4A4C-4CC8-9611-28038D595148} | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262912 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {297EE804-5EF9-4E85-A59D-6B8389A0786C} | |||
| (PID) Process: | (5256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262912 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F71251EC-7041-4FCB-99D2-587413C6BECB} | |||
Executable files
263
Suspicious files
416
Text files
145
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10cb60.TMP | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10cb70.TMP | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10cb7f.TMP | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10cbce.TMP | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10cc3b.TMP | — | |
MD5:— | SHA256:— | |||
| 5256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
88
DNS requests
100
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5256 | msedge.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
1328 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5256 | msedge.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDCHrGioOtg%2F16UjkBw%3D%3D | unknown | — | — | whitelisted |
8084 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744039858&P2=404&P3=2&P4=Vu0HAGBaywTh5x7IglfFpgtt7JbeyYIyQACoaA1BxYE4zfLPjDT4YVzJCNEFllpohw1dlaUNKrZClfimbKSDdw%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744039858&P2=404&P3=2&P4=Vu0HAGBaywTh5x7IglfFpgtt7JbeyYIyQACoaA1BxYE4zfLPjDT4YVzJCNEFllpohw1dlaUNKrZClfimbKSDdw%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744039858&P2=404&P3=2&P4=Vu0HAGBaywTh5x7IglfFpgtt7JbeyYIyQACoaA1BxYE4zfLPjDT4YVzJCNEFllpohw1dlaUNKrZClfimbKSDdw%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744039858&P2=404&P3=2&P4=Vu0HAGBaywTh5x7IglfFpgtt7JbeyYIyQACoaA1BxYE4zfLPjDT4YVzJCNEFllpohw1dlaUNKrZClfimbKSDdw%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744039858&P2=404&P3=2&P4=Vu0HAGBaywTh5x7IglfFpgtt7JbeyYIyQACoaA1BxYE4zfLPjDT4YVzJCNEFllpohw1dlaUNKrZClfimbKSDdw%3d%3d | unknown | — | — | whitelisted |
5756 | updater.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
5756 | updater.exe | GET | 200 | 142.250.185.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEG%2BorlfPZWf5CeqNw%2Flf3jE%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.10.31.115:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5256 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7324 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 2.17.22.48:443 | www.bing.com | AKAMAI-AS | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
chrome.homepagel.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6040 | cmd.exe | A Network Trojan was detected | ET MALWARE Arechclient2 Backdoor/SecTopRAT Related Activity M3 (GET) |
6040 | cmd.exe | A Network Trojan was detected | ET MALWARE Arechclient2 Backdoor/SecTopRAT Related Activity M2 (GET) |