| File name: | PO for the month of November 2018.pdf.exe |
| Full analysis: | https://app.any.run/tasks/bf70901c-5c05-4c32-ac6e-1b9d490dfb10 |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | November 14, 2018, 10:34:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 24234DE13BA466D46059393275E35C7F |
| SHA1: | 3006D9AB14026536A4EA6DA6A3DA5628728BC1CF |
| SHA256: | 80F7C9C8D4630145CC85C56A13504F2367F8601E626CB6EC391D89EB46AF9A85 |
| SSDEEP: | 12288:4wTefHonIcjH7SZQEWOlziZgi6BNazePXzbLDbMNkq1GbkZy:3etcGQOOT6BUIXzbLMr1Gb9 |
MALICIOUS
Connects to CnC server
- PO for the month of November 2018.pdf.exe (PID: 272)
Detected Pony/Fareit Trojan
- PO for the month of November 2018.pdf.exe (PID: 272)
Actions looks like stealing of personal data
- PO for the month of November 2018.pdf.exe (PID: 272)
SUSPICIOUS
Reads Internet Cache Settings
- PO for the month of November 2018.pdf.exe (PID: 272)
Application launched itself
- PO for the month of November 2018.pdf.exe (PID: 3128)
Starts CMD.EXE for commands execution
- PO for the month of November 2018.pdf.exe (PID: 272)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2716)
Creates files in the user directory
- WINWORD.EXE (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:03:26 03:01:22+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 351744 |
| InitializedDataSize: | 240128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x56bc0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Mar-1992 02:01:22 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 26-Mar-1992 02:01:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00055C08 | 0x00055E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53014 |
DATA | 0x00057000 | 0x0000F670 | 0x0000F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.4815 |
BSS | 0x00067000 | 0x00000BE5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00068000 | 0x00002050 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88426 |
.tls | 0x0006B000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0006C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x0006D000 | 0x000062DC | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.65011 |
.rsrc | 0x00074000 | 0x0002296C | 0x00022A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.95792 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.79909 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
427 | 7.03519 | 2537 | Latin 1 / Western European | English - United States | RT_CURSOR |
428 | 7.27384 | 2537 | Latin 1 / Western European | English - United States | RT_CURSOR |
429 | 7.25152 | 2537 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
version.dll |
winmm.dll |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\AppData\Local\Temp\PO for the month of November 2018.pdf.exe" | C:\Users\admin\AppData\Local\Temp\PO for the month of November 2018.pdf.exe | PO for the month of November 2018.pdf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
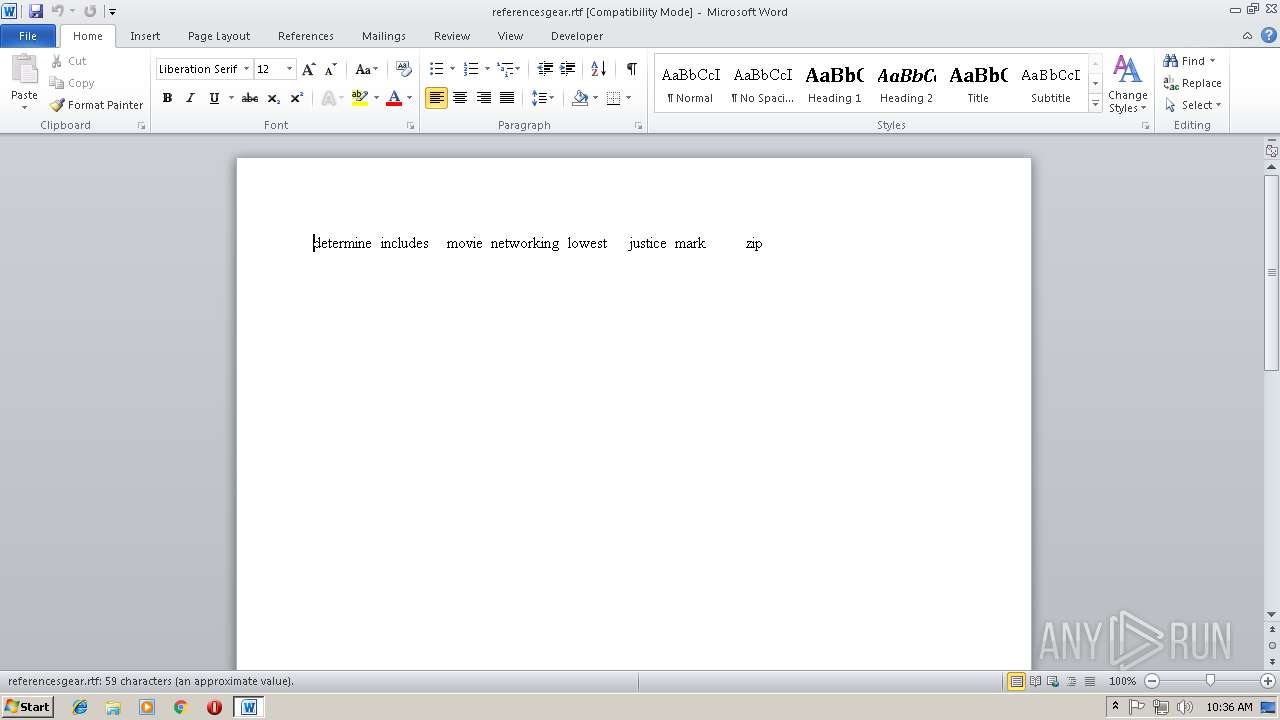
| 2716 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\referencesgear.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3128 | "C:\Users\admin\AppData\Local\Temp\PO for the month of November 2018.pdf.exe" | C:\Users\admin\AppData\Local\Temp\PO for the month of November 2018.pdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3412 | cmd /c ""C:\Users\admin\AppData\Local\Temp\6197015.bat" "C:\Users\admin\AppData\Local\Temp\PO for the month of November 2018.pdf.exe" " | C:\Windows\system32\cmd.exe | — | PO for the month of November 2018.pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
864
Read events
818
Write events
35
Delete events
11
Modification events
| (PID) Process: | (272) PO for the month of November 2018.pdf.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | HWID |
Value: 7B32353635433246312D373134352D343030342D423939352D3246303030313341453832307D | |||
| (PID) Process: | (272) PO for the month of November 2018.pdf.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | Client Hash |
Value: 1D1C30B733D527D717D1FC1DEB35FDCE | |||
| (PID) Process: | (272) PO for the month of November 2018.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (272) PO for the month of November 2018.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | cl |
Value: 20636C009C0A0000010000000000000000000000 | |||
| (PID) Process: | (2716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2716) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2716) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054608 | |||
| (PID) Process: | (2716) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (2716) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF790.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{87F7D266-CEB9-4771-9520-548E95DFC175}.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{1ACB7307-024A-4FFE-8D4F-1A0630E22FAF}.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 272 | PO for the month of November 2018.pdf.exe | C:\Users\admin\AppData\Local\Temp\6197015.bat | text | |
MD5:3880EEB1C736D853EB13B44898B718AB | SHA256:936D9411D5226B7C5A150ECAF422987590A8870C8E095E1CAA072273041A86E7 | |||
| 2716 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2716 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\referencesgear.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2716 | WINWORD.EXE | C:\Users\admin\Desktop\~$ferencesgear.rtf | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
272 | PO for the month of November 2018.pdf.exe | GET | 404 | 108.170.57.53:80 | http://toolplus-cn.com/panel/shit.exe | US | html | 331 b | malicious |
272 | PO for the month of November 2018.pdf.exe | POST | — | 108.170.57.53:80 | http://toolplus-cn.com/panel/gate.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
272 | PO for the month of November 2018.pdf.exe | 108.170.57.53:80 | toolplus-cn.com | SECURED SERVERS LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
toolplus-cn.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
272 | PO for the month of November 2018.pdf.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
272 | PO for the month of November 2018.pdf.exe | Potentially Bad Traffic | ET TROJAN Generic -POST To gate.php w/Extended ASCII Characters (Likely Zeus Derivative) |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony CnC Server stdResponse |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 3 |
272 | PO for the month of November 2018.pdf.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
272 | PO for the month of November 2018.pdf.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious downloader - 404 Not Found for .exe |
1 ETPRO signatures available at the full report