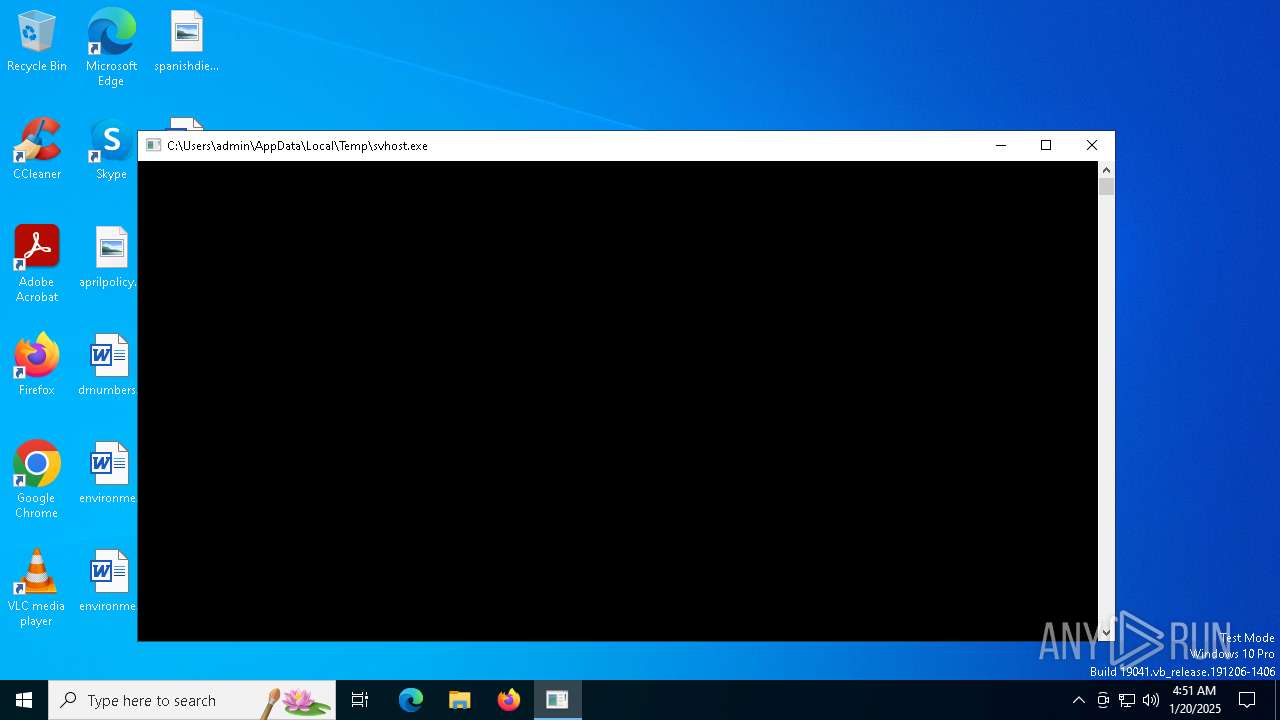
| File name: | svhost.exe |
| Full analysis: | https://app.any.run/tasks/4ede3e17-cefa-4393-942e-7681583d513f |
| Verdict: | Malicious activity |
| Threats: | Lynx is a double extortion ransomware: attackers encrypt important and sensitive data and demand a ransom for decryption simultaneously threatening to publish or sell the data. Active since mid-2024. Among techniques are terminating processes and services, privilege escalation, deleting shadow copies. Distribution by phishing, malvertising, exploiting vulnerabilities. |
| Analysis date: | January 20, 2025, 04:51:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 4 sections |
| MD5: | 67A44A38CC36BECD6E2E9C20C27FD9AD |
| SHA1: | 3DD215876039EBEE144E18ECB84D8702697DB94B |
| SHA256: | 80908A51E403EFD47B1D3689C3FB9447D3FB962D691D856B8B97581EEFC0C441 |
| SSDEEP: | 3072:jBBDFFFiZlsEzKbLhbJ3zbFli4YU+kIQu42JB3p+frug1swxtMKzO4XY8PHm3P:ClN+RNVlv+8u42z3p+frdbRG3P |
MALICIOUS
LYNX has been detected
- svhost.exe (PID: 188)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- svhost.exe (PID: 188)
INFO
Reads the computer name
- svhost.exe (PID: 188)
Checks supported languages
- svhost.exe (PID: 188)
Creates files in the program directory
- svhost.exe (PID: 188)
Creates files or folders in the user directory
- svhost.exe (PID: 188)
Reads the machine GUID from the registry
- svhost.exe (PID: 188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:21 11:37:45+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 120832 |
| InitializedDataSize: | 49664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa341 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
129
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | svhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 769
Read events
1 769
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
192
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 188 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\ProgramData\Adobe\ARM\Acrobat_23.001.20093\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\ProgramData\Adobe\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\ProgramData\Adobe\ARM\S\388\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\ProgramData\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\ClickToRun\DeploymentConfig.1.xml | binary | |
MD5:FA97C4C4247B4E42F54619F461EDDED6 | SHA256:6BC3BACBFC10E07FA3BB9E9B1877FB80282641E6B6DD572C06E01BCB8A9A7B0D | |||
| 188 | svhost.exe | C:\ProgramData\Adobe\ARM\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 188 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\ClickToRun\DeploymentConfig.2.xml | binary | |
MD5:991F1BA3BFB64D3C3F8DF93D93F458EE | SHA256:E41CB1A9585EAD5F875B29D47E5E892938337DCFA9B670548374BF7A024E723D | |||
| 188 | svhost.exe | C:\ProgramData\Microsoft\ClickToRun\DeploymentConfig.2.xml.LYNX | binary | |
MD5:991F1BA3BFB64D3C3F8DF93D93F458EE | SHA256:E41CB1A9585EAD5F875B29D47E5E892938337DCFA9B670548374BF7A024E723D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
25
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4444 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4444 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.136:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.30.18.9:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |