| File name: | svhost.exe |
| Full analysis: | https://app.any.run/tasks/4c8df13a-a98e-44c9-b7ff-2c0317bd4596 |
| Verdict: | Malicious activity |
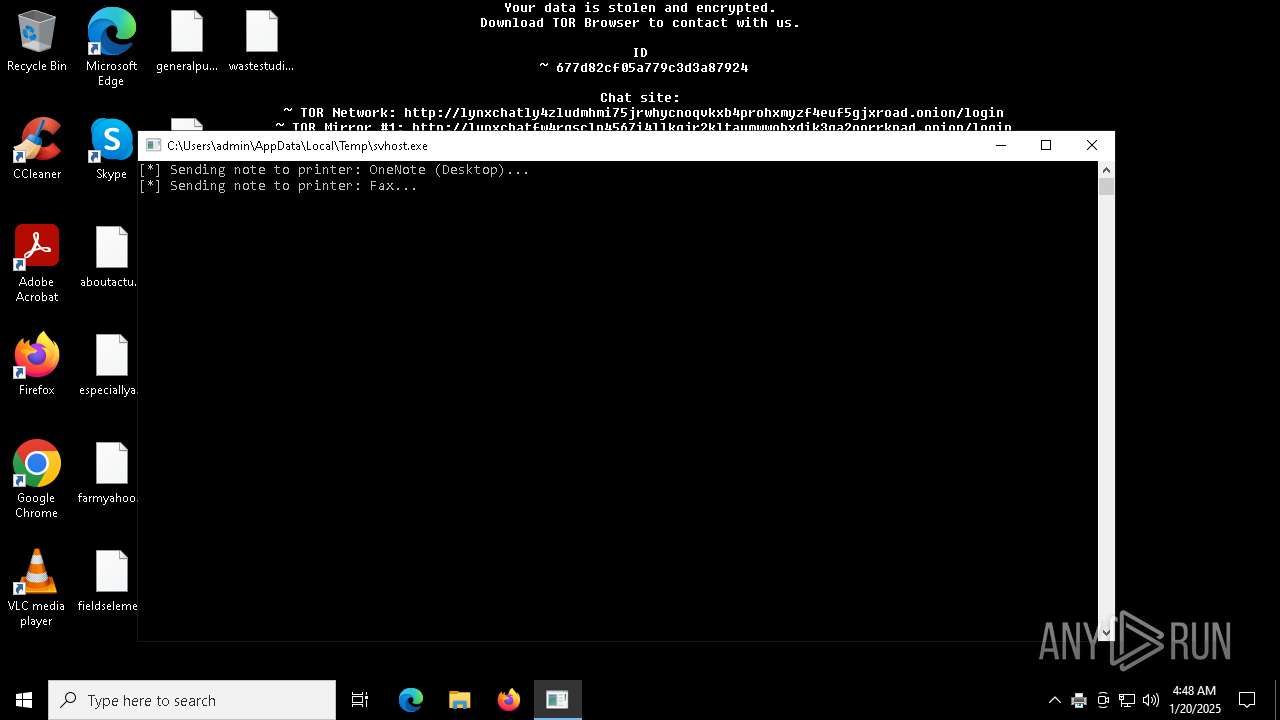
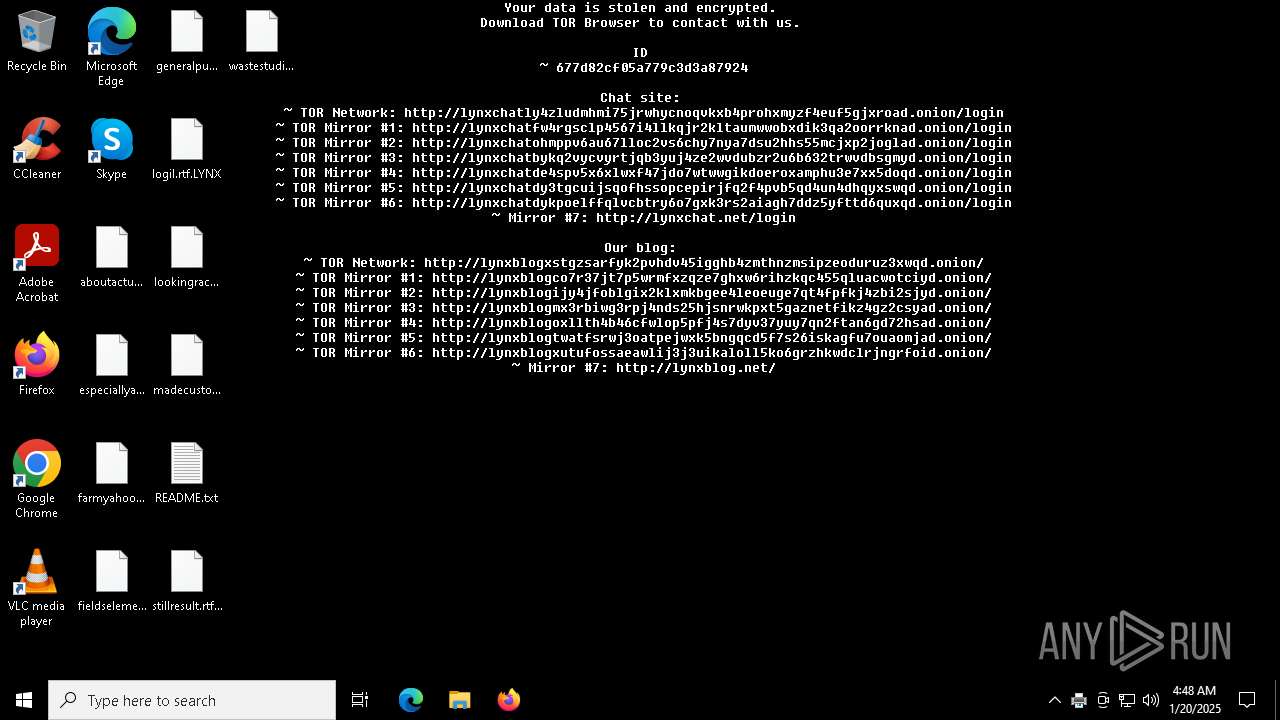
| Threats: | Lynx is a double extortion ransomware: attackers encrypt important and sensitive data and demand a ransom for decryption simultaneously threatening to publish or sell the data. Active since mid-2024. Among techniques are terminating processes and services, privilege escalation, deleting shadow copies. Distribution by phishing, malvertising, exploiting vulnerabilities. |
| Analysis date: | January 20, 2025, 04:47:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 4 sections |
| MD5: | 67A44A38CC36BECD6E2E9C20C27FD9AD |
| SHA1: | 3DD215876039EBEE144E18ECB84D8702697DB94B |
| SHA256: | 80908A51E403EFD47B1D3689C3FB9447D3FB962D691D856B8B97581EEFC0C441 |
| SSDEEP: | 3072:jBBDFFFiZlsEzKbLhbJ3zbFli4YU+kIQu42JB3p+frug1swxtMKzO4XY8PHm3P:ClN+RNVlv+8u42z3p+frdbRG3P |
MALICIOUS
LYNX has been detected
- svhost.exe (PID: 6252)
RANSOMWARE has been detected
- svhost.exe (PID: 6252)
Renames files like ransomware
- svhost.exe (PID: 6252)
SUSPICIOUS
Executable content was dropped or overwritten
- svhost.exe (PID: 6252)
There is functionality for taking screenshot (YARA)
- svhost.exe (PID: 6252)
Executes as Windows Service
- FXSSVC.exe (PID: 6508)
Reads security settings of Internet Explorer
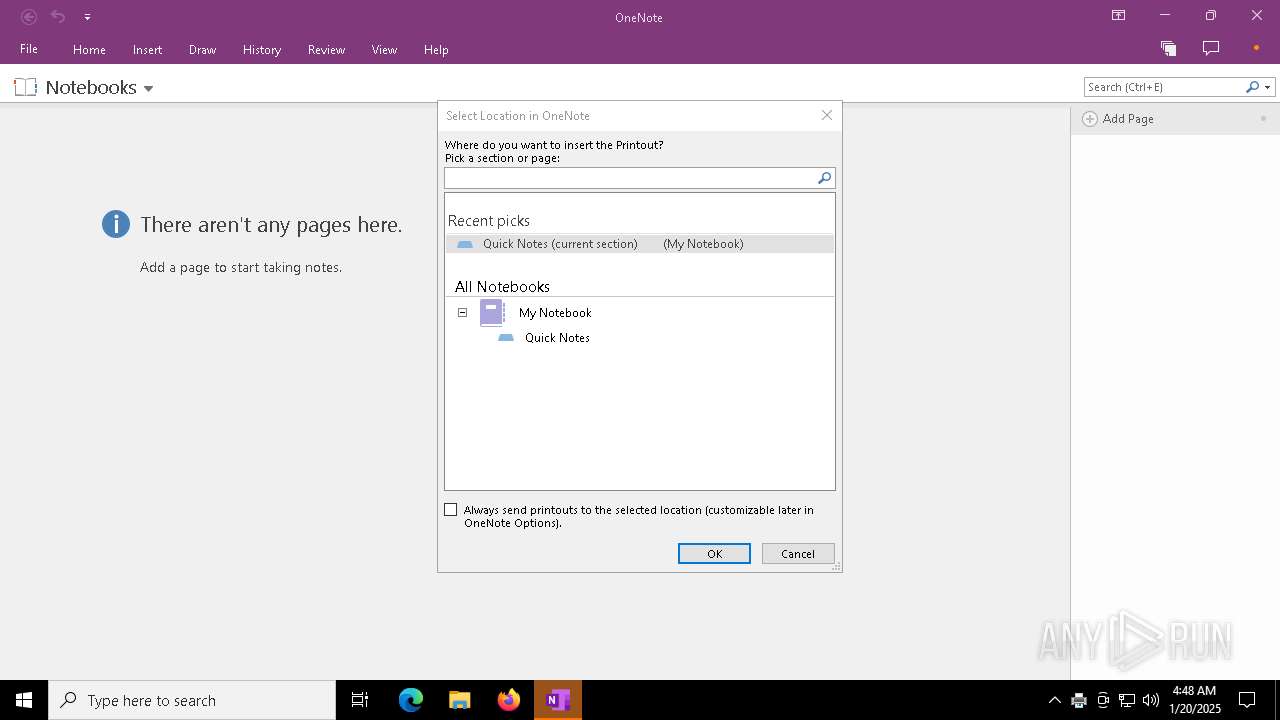
- ONENOTE.EXE (PID: 6540)
Checks Windows Trust Settings
- ONENOTE.EXE (PID: 6540)
Reads the date of Windows installation
- ONENOTE.EXE (PID: 6540)
INFO
Reads the machine GUID from the registry
- svhost.exe (PID: 6252)
- ONENOTE.EXE (PID: 6540)
Creates files in the program directory
- svhost.exe (PID: 6252)
Reads the computer name
- svhost.exe (PID: 6252)
Checks supported languages
- svhost.exe (PID: 6252)
- ONENOTE.EXE (PID: 6540)
Creates files or folders in the user directory
- svhost.exe (PID: 6252)
- printfilterpipelinesvc.exe (PID: 6332)
- ONENOTE.EXE (PID: 6540)
Create files in a temporary directory
- svhost.exe (PID: 6252)
- ONENOTE.EXE (PID: 6540)
Disables trace logs
- FXSSVC.exe (PID: 6508)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 6540)
Reads Environment values
- ONENOTE.EXE (PID: 6540)
Reads product name
- ONENOTE.EXE (PID: 6540)
Reads the software policy settings
- ONENOTE.EXE (PID: 6540)
Checks proxy server information
- ONENOTE.EXE (PID: 6540)
Process checks computer location settings
- ONENOTE.EXE (PID: 6540)
Sends debugging messages
- ONENOTE.EXE (PID: 6540)
Reads CPU info
- ONENOTE.EXE (PID: 6540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:21 11:37:45+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 120832 |
| InitializedDataSize: | 49664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa341 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
137
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6252 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | svhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6332 | C:\WINDOWS\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\System32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6508 | C:\WINDOWS\system32\fxssvc.exe | C:\Windows\System32\FXSSVC.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Fax Service Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6540 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\{658CFE47-B73D-4723-B97F-2A7D73061A87}.xps" 133818221069950000 | C:\Program Files\Microsoft Office\root\Office16\ONENOTE.EXE | printfilterpipelinesvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
11 079
Read events
10 848
Write events
219
Delete events
12
Modification events
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | Server |
Value: | |||
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | From |
Value: | |||
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | User |
Value: | |||
| (PID) Process: | (6252) svhost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp\\background-image.jpg | |||
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax |
| Operation: | write | Name: | RedirectionGuard |
Value: 1 | |||
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | write | Name: | Password |
Value: 00 | |||
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Receipts |
| Operation: | delete value | Name: | Password |
Value: | |||
| (PID) Process: | (6508) FXSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fax\Security |
| Operation: | write | Name: | Descriptor |
Value: 010004805C000000680000000000000014000000020048000300000000001800E7020E000102000000000005200000002002000000001400030002000101000000000001000000000000140027020200010100000000000504000000010100000000000514000000010100000000000514000000 | |||
| (PID) Process: | (6540) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 12 |
Value: 012C19000000001000B24E9A3E02000000000000000200000000000000 | |||
| (PID) Process: | (6540) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\ONENOTE\6540 |
| Operation: | write | Name: | 0 |
Value: 0B0E10B7BE8658CCEDB44F97B207168209259723004690B5D1DFE8DEDAED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC9062E225763446C494E41384C537237784C67357549303451703444396E4730426B415A4C6B6C6361656270562B303D22CA0DC2190000C91003783634C5118C33D2120B6F006E0065006E006F00740065002E00650078006500C51620C517808004C91808323231322D44656300 | |||
Executable files
6
Suspicious files
717
Text files
176
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6252 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\Adobe\Temp\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\Adobe\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\Adobe\ARM\S\388\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\Adobe\ARM\Acrobat_23.001.20093\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\Adobe\ARM\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\AppV\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\Users\admin\AppData\Local\VirtualStore\ProgramData\Microsoft\ClickToRun\MachineData\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\Adobe\ARM\{291AA914-A987-4CE9-BD63-0C0A92D435E5}\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
| 6252 | svhost.exe | C:\ProgramData\README.txt | text | |
MD5:49F0B18C2FB14CA960F7B46FEFEB4688 | SHA256:DB2CDC61651DAC42E9F1305517CFBA42F2BB9AF0193813E8DCE6C95160939C4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
10180 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
10180 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6540 | ONENOTE.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6444 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6540 | ONENOTE.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.21.65.154:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|