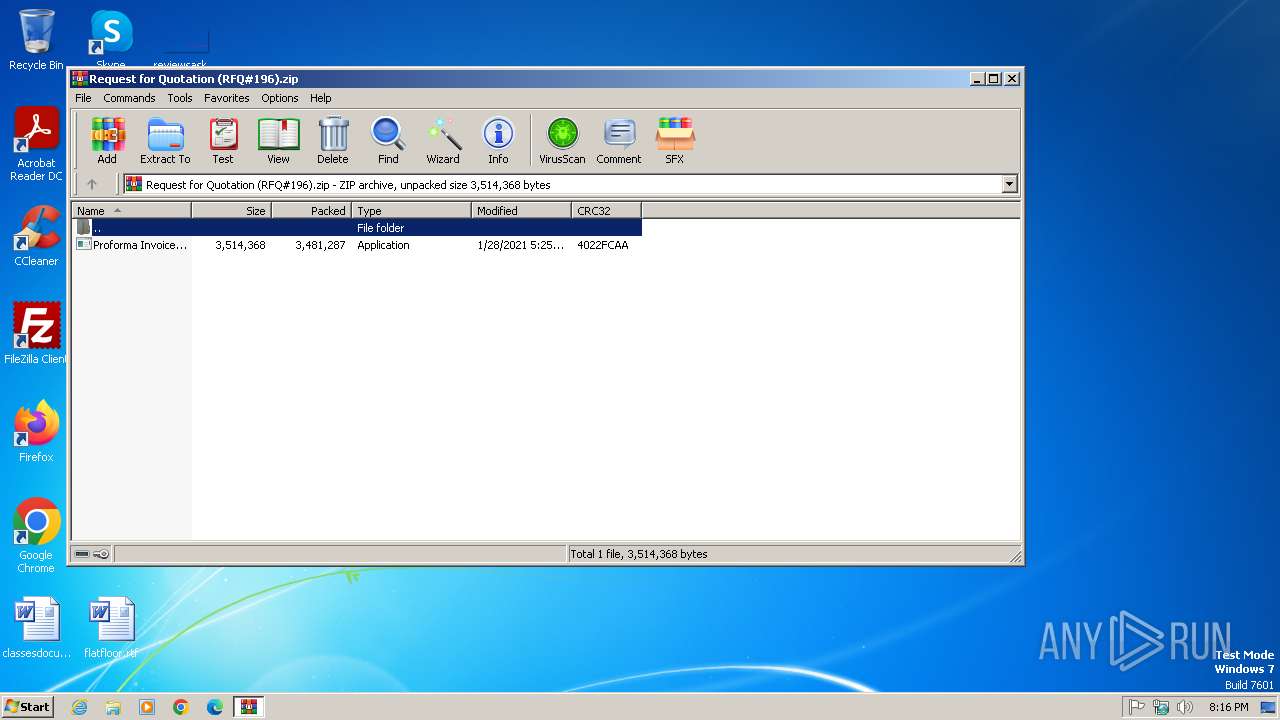
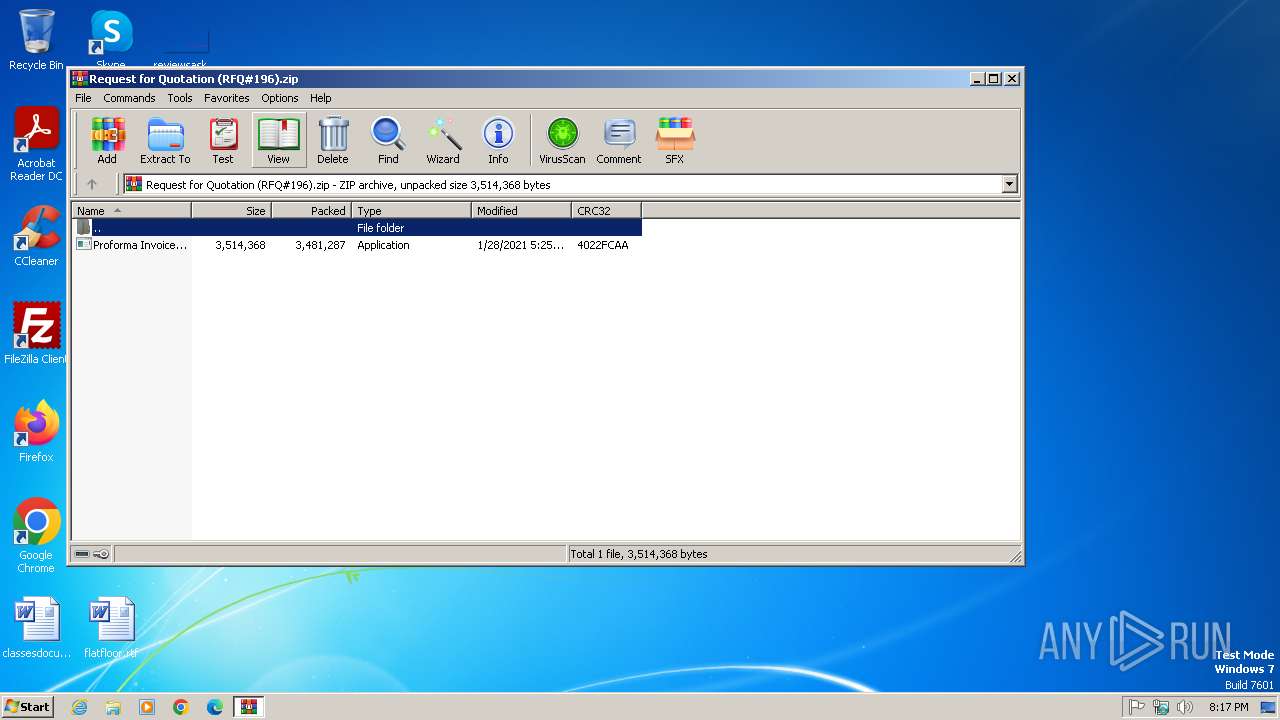
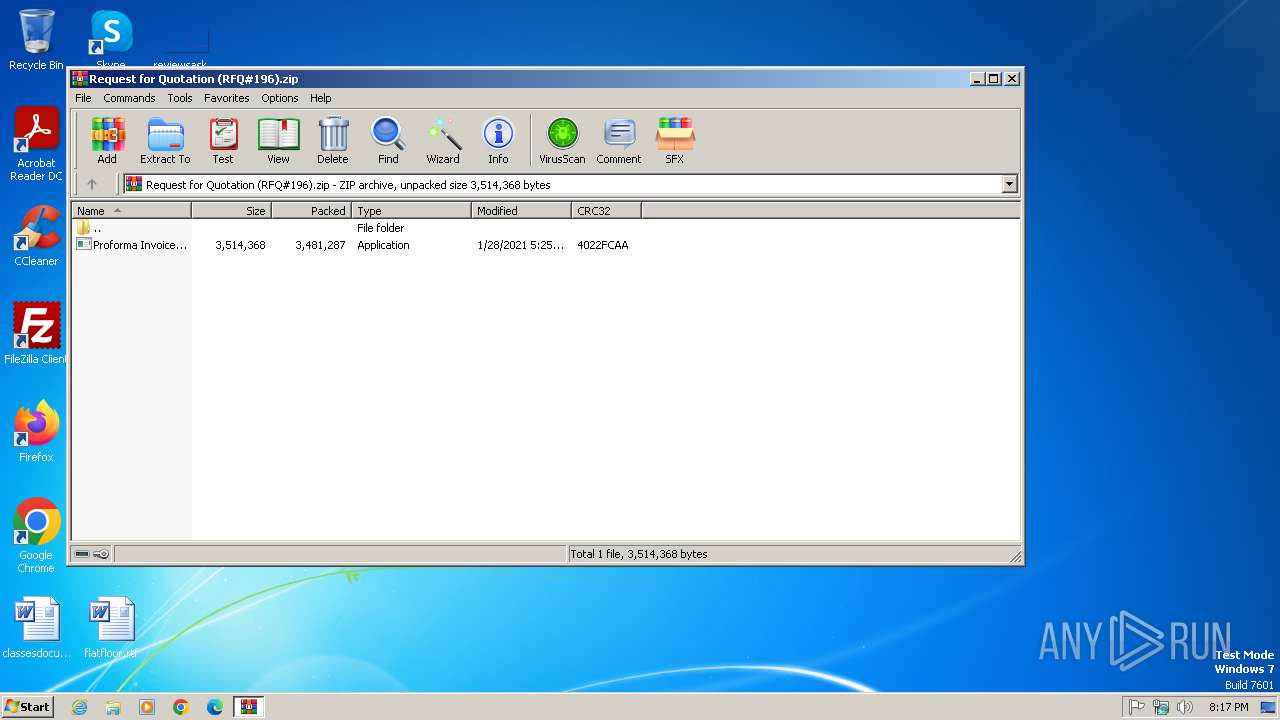
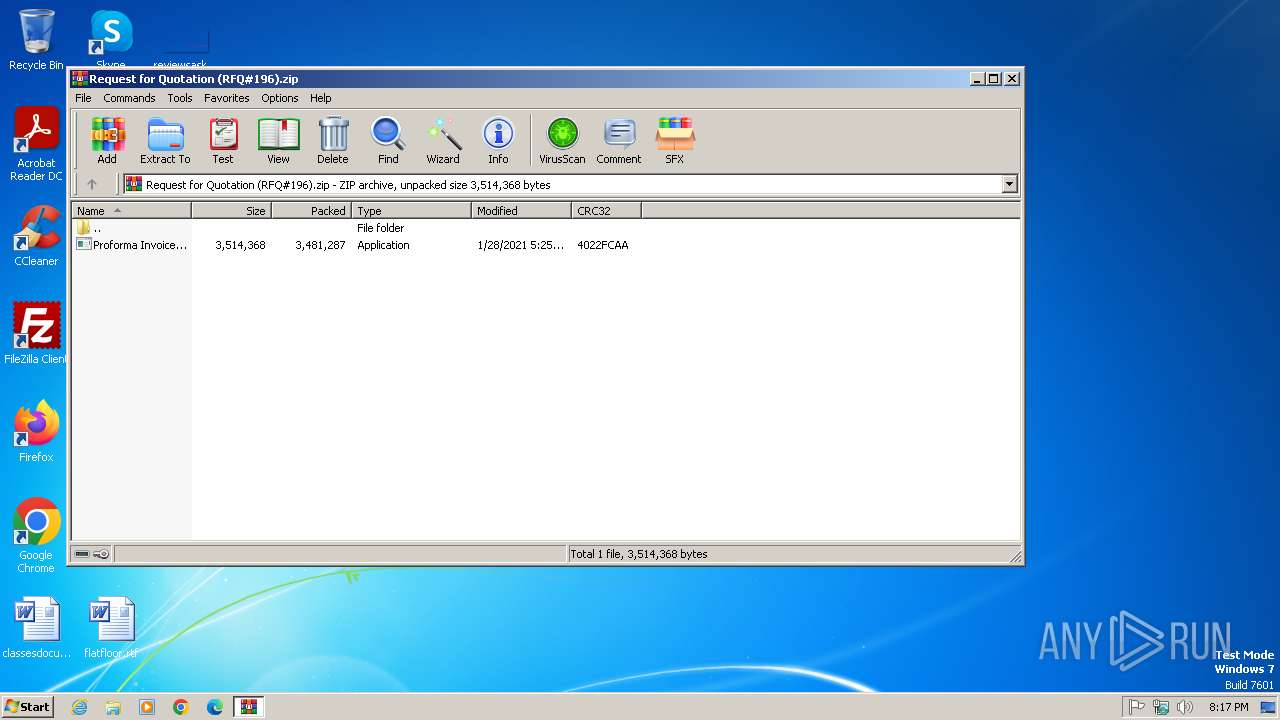
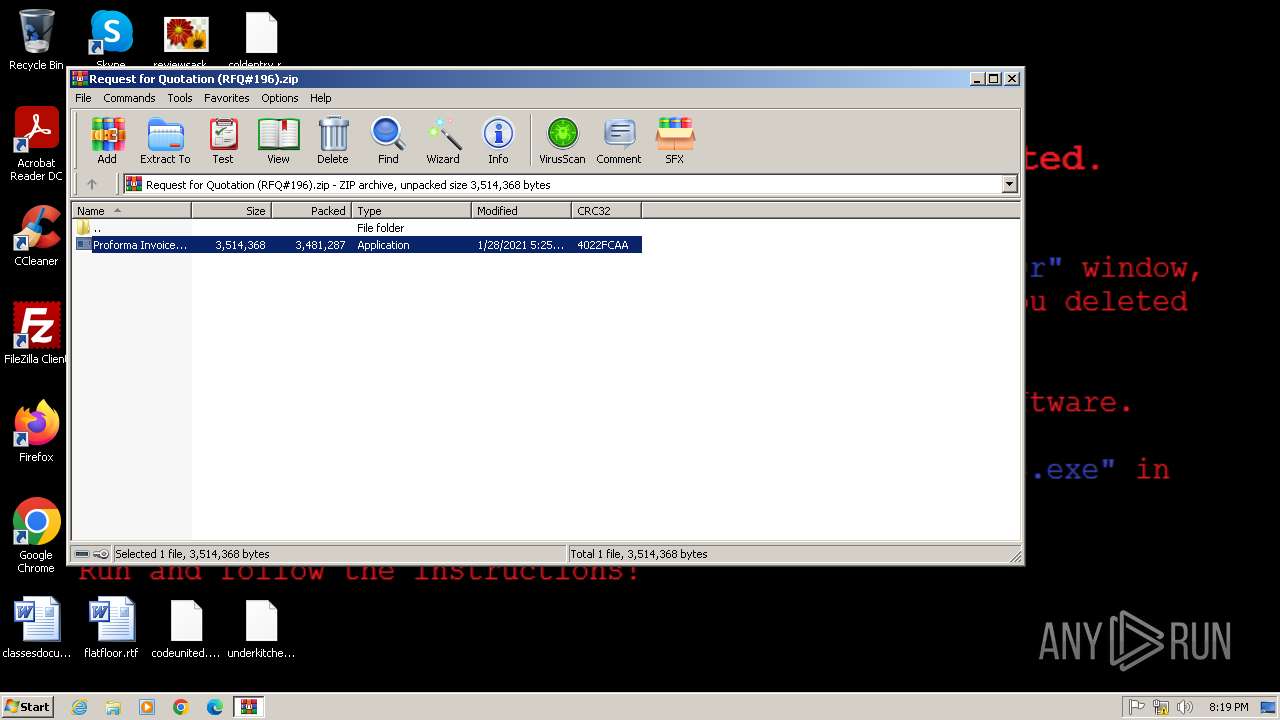
| File name: | Request for Quotation (RFQ#196).zip |
| Full analysis: | https://app.any.run/tasks/ddd25d6c-1d67-4c30-bbcc-3004a726db5e |
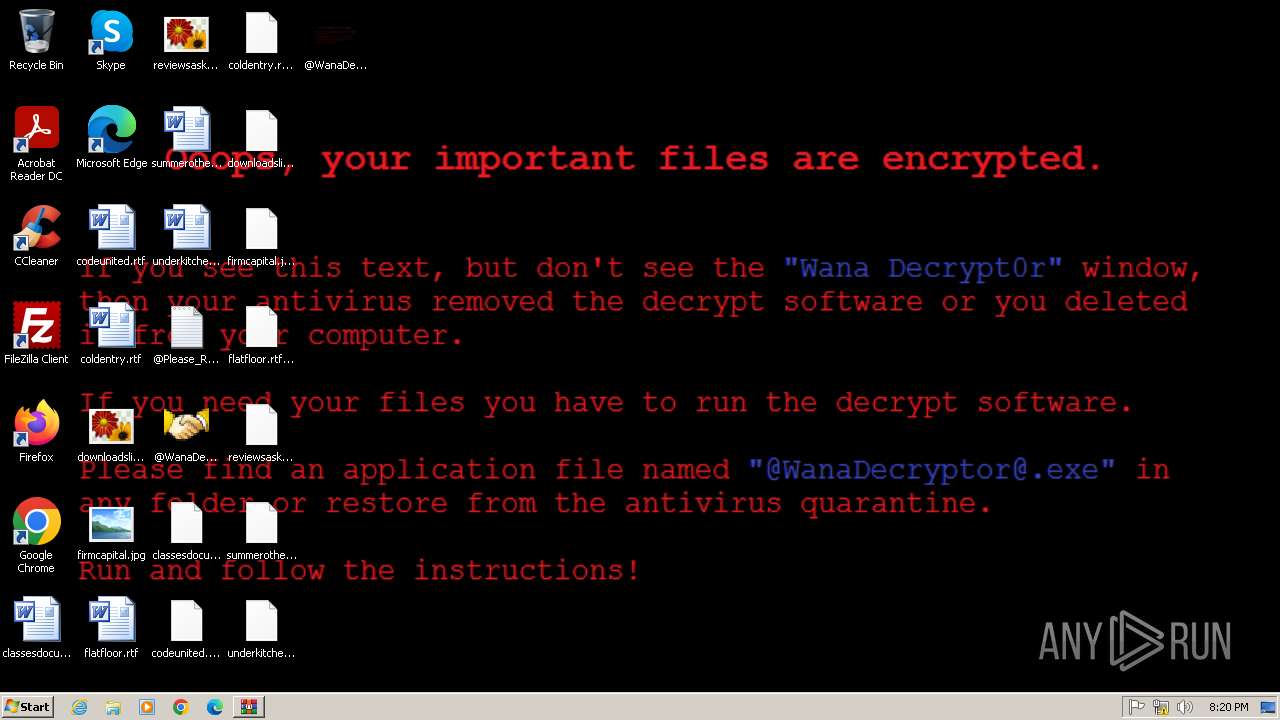
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | April 14, 2025, 19:16:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
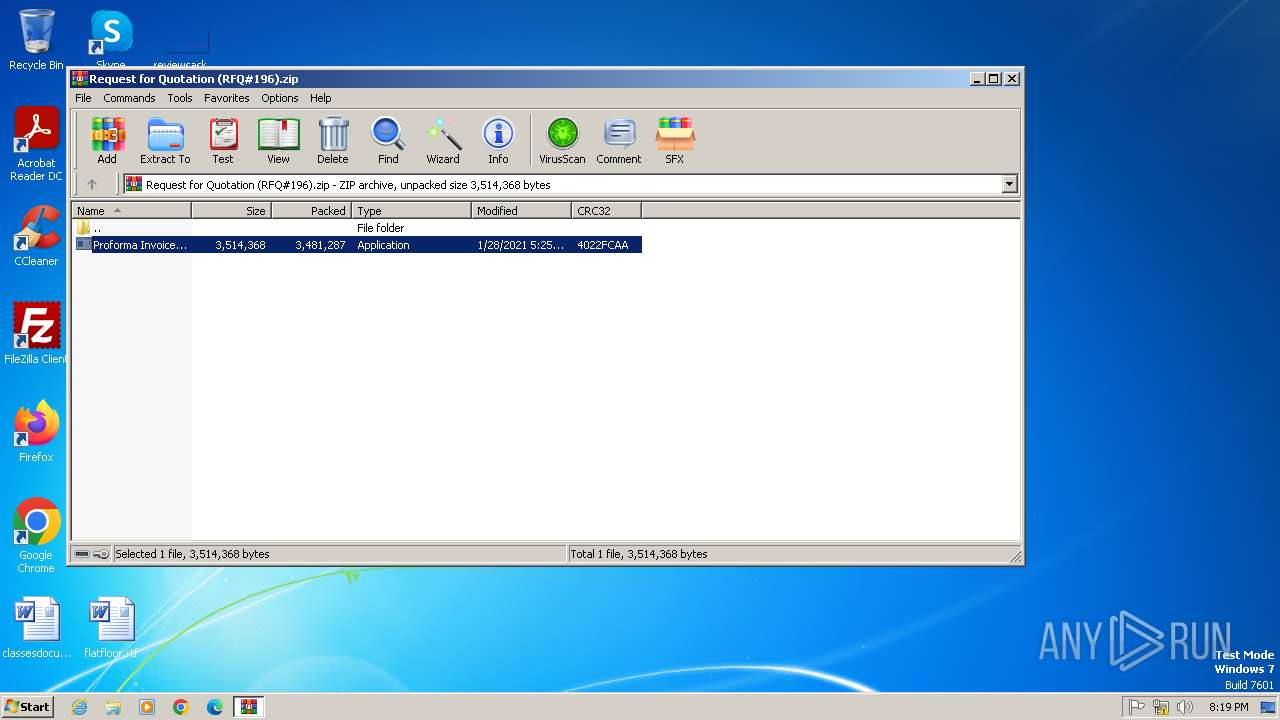
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D69DC6569B385C0467185D002E252D89 |
| SHA1: | 25938A66CCE0078C76A15F351CBD19C8FCC2B081 |
| SHA256: | 80239619C4CA44380C6269873A5B6B695585CCFCF278E0F2C72698658A3A6FD8 |
| SSDEEP: | 49152:pZL1zufKjTpcSPBeJJTXAlSr1/2ueI1HEafmKIDBsuN3FcTuYx/uEjF5RX:/RzvjTCVAlet2XmHxfmKIPNYx/RX |
MALICIOUS
WANNACRY has been detected
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- @WanaDecryptor@.exe (PID: 3328)
- @WanaDecryptor@.exe (PID: 2728)
- @WanaDecryptor@.exe (PID: 3068)
WANNACRY mutex has been found
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
WANNACRY has been detected (YARA)
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- @WanaDecryptor@.exe (PID: 2728)
- @WanaDecryptor@.exe (PID: 3068)
Actions looks like stealing of personal data
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Writes a file to the Word startup folder
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Modifies files in the Chrome extension folder
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
WannaCry Ransomware is detected
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- cmd.exe (PID: 2544)
Wannacry exe files
- cmd.exe (PID: 2544)
- @WanaDecryptor@.exe (PID: 2728)
- @WanaDecryptor@.exe (PID: 3328)
- @WanaDecryptor@.exe (PID: 3068)
- @WanaDecryptor@.exe (PID: 1332)
- @WanaDecryptor@.exe (PID: 548)
- @WanaDecryptor@.exe (PID: 1588)
Deletes shadow copies
- cmd.exe (PID: 3196)
Changes the autorun value in the registry
- reg.exe (PID: 3172)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 3196)
SUSPICIOUS
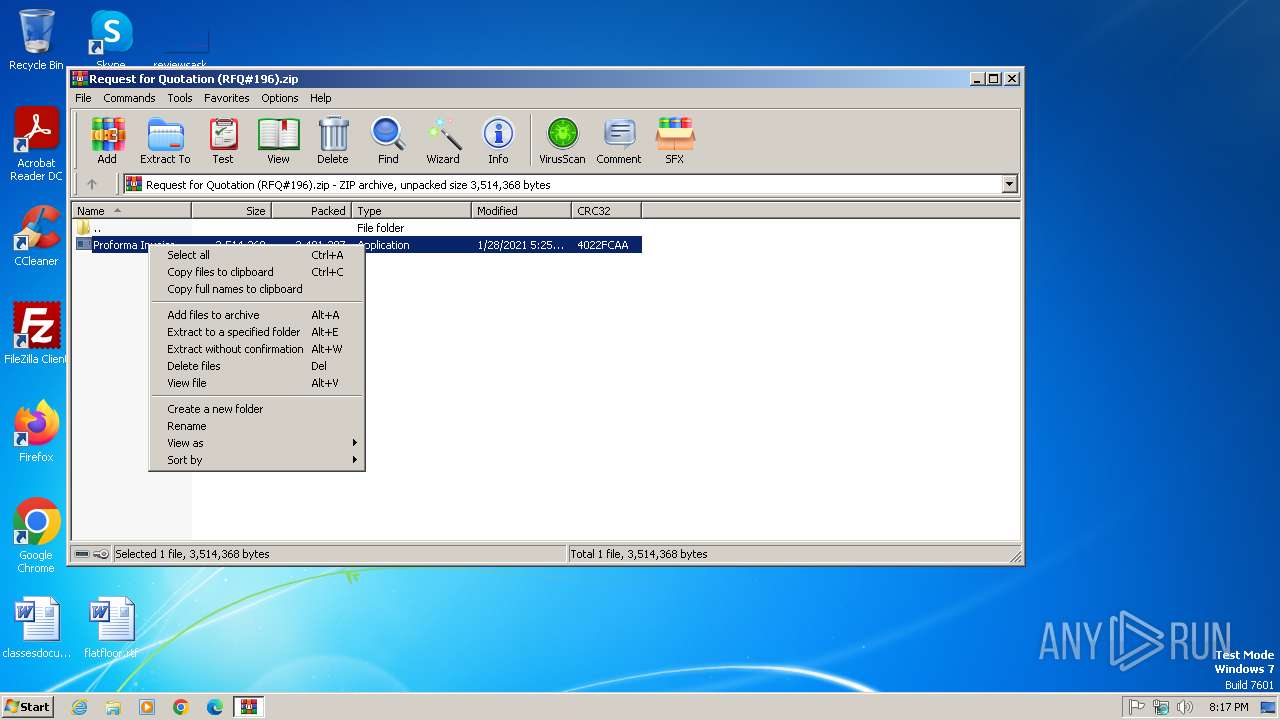
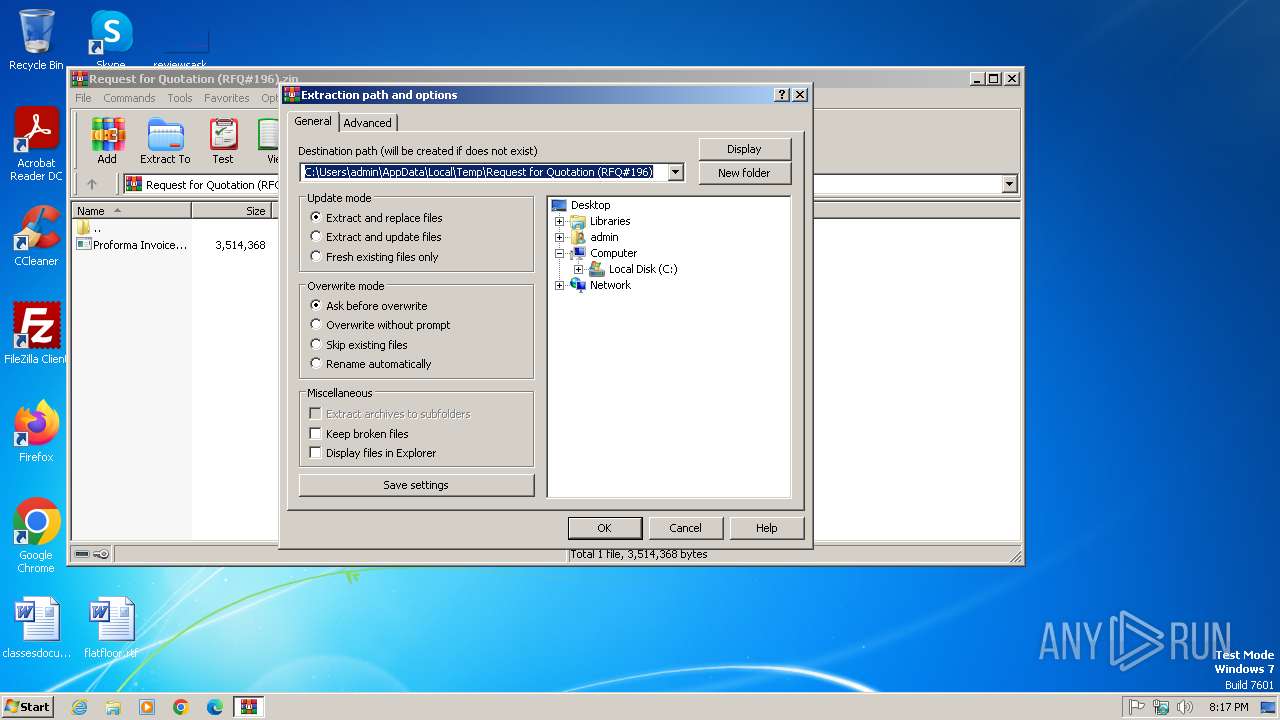
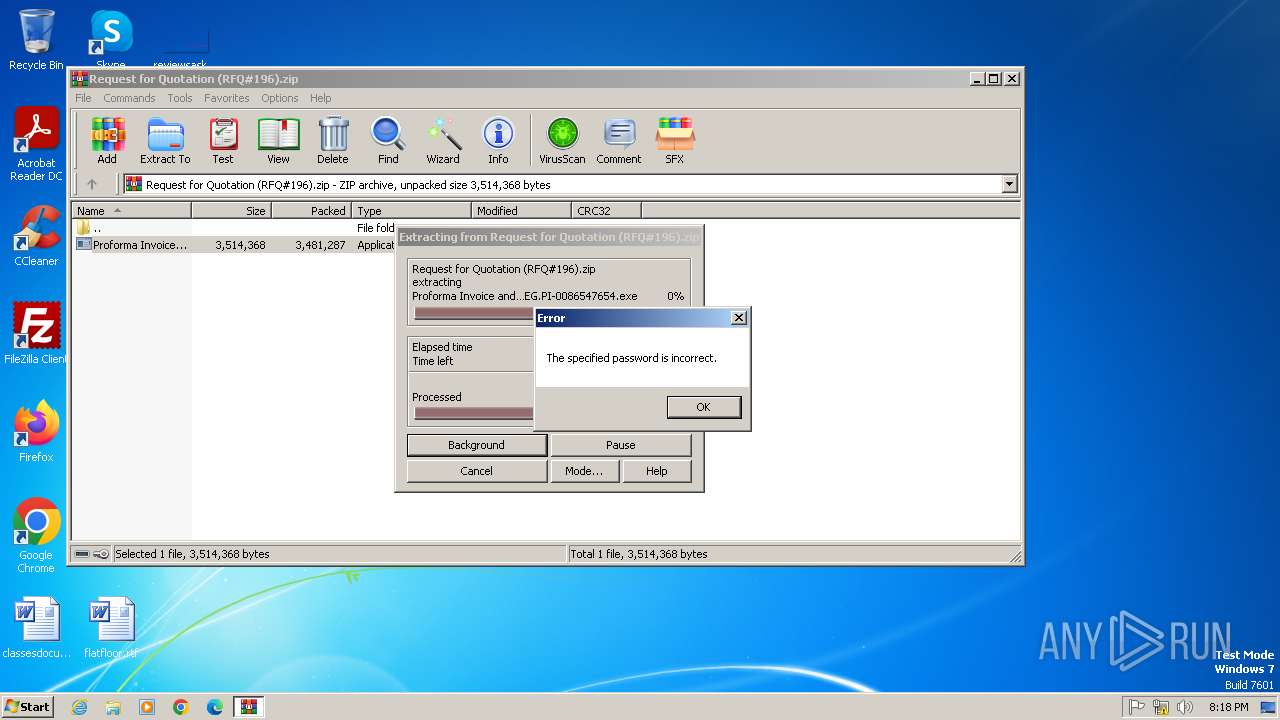
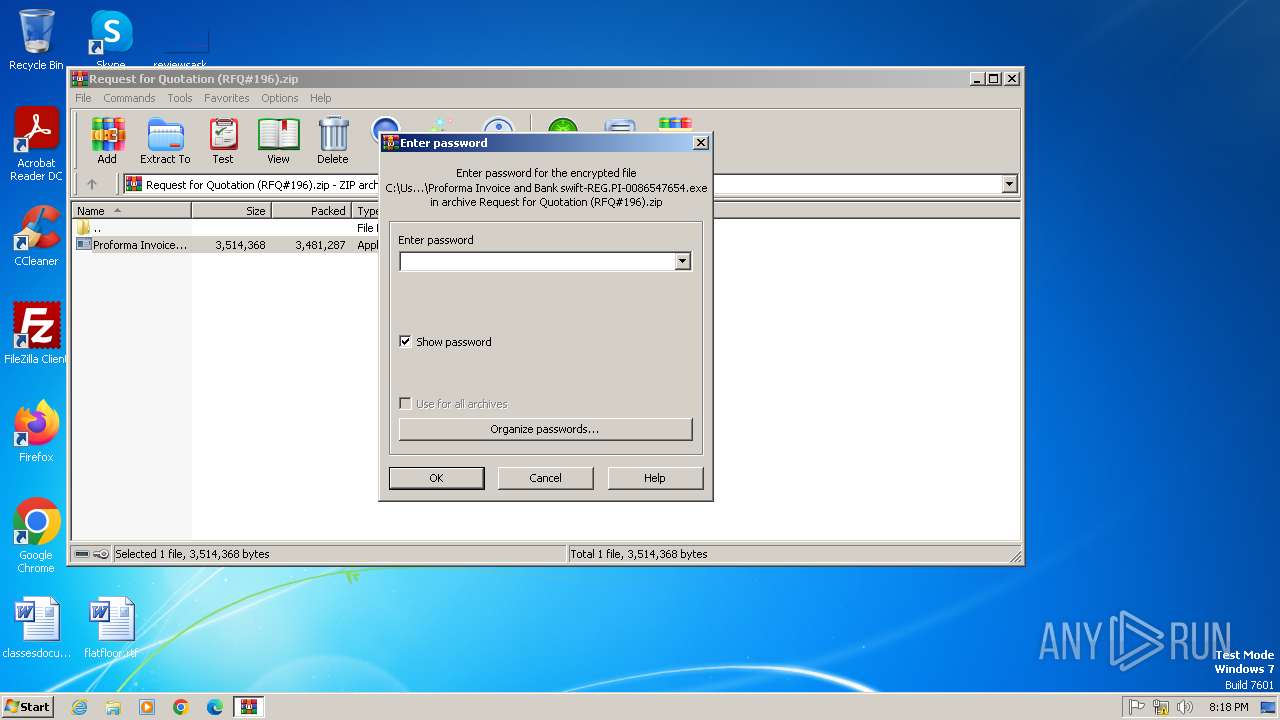
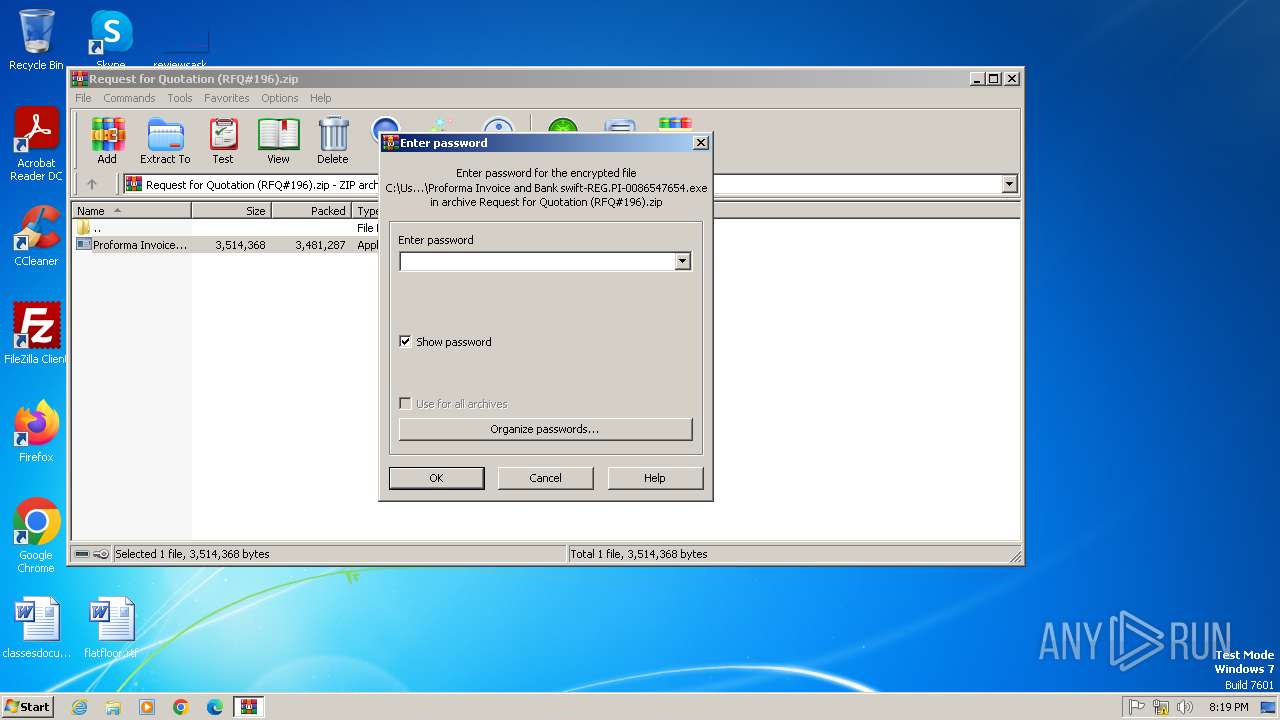
Process drops legitimate windows executable
- WinRAR.exe (PID: 2848)
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Starts a Microsoft application from unusual location
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- taskdl.exe (PID: 2056)
- taskdl.exe (PID: 2420)
- @WanaDecryptor@.exe (PID: 2728)
- @WanaDecryptor@.exe (PID: 3328)
- @WanaDecryptor@.exe (PID: 3068)
- taskdl.exe (PID: 604)
- @WanaDecryptor@.exe (PID: 1332)
- @WanaDecryptor@.exe (PID: 548)
- taskdl.exe (PID: 1092)
- taskdl.exe (PID: 1924)
- @WanaDecryptor@.exe (PID: 1588)
- taskdl.exe (PID: 3036)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2848)
- @WanaDecryptor@.exe (PID: 3328)
Executable content was dropped or overwritten
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- @WanaDecryptor@.exe (PID: 2728)
Uses ATTRIB.EXE to modify file attributes
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Uses ICACLS.EXE to modify access control lists
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Executing commands from a ".bat" file
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Starts CMD.EXE for commands execution
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- @WanaDecryptor@.exe (PID: 3328)
The process executes VB scripts
- cmd.exe (PID: 3856)
Connects to unusual port
- taskhsvc.exe (PID: 3552)
Reads the Internet Settings
- @WanaDecryptor@.exe (PID: 3328)
- WMIC.exe (PID: 1076)
The executable file from the user directory is run by the CMD process
- @WanaDecryptor@.exe (PID: 3328)
Executes as Windows Service
- VSSVC.exe (PID: 3236)
- wbengine.exe (PID: 1020)
- vds.exe (PID: 1196)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3364)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2848)
The sample compiled with english language support
- WinRAR.exe (PID: 2848)
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- @WanaDecryptor@.exe (PID: 2728)
Create files in a temporary directory
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- cscript.exe (PID: 3124)
- @WanaDecryptor@.exe (PID: 2728)
Reads the computer name
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- taskhsvc.exe (PID: 3552)
- @WanaDecryptor@.exe (PID: 3328)
Checks supported languages
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- taskdl.exe (PID: 2420)
- taskdl.exe (PID: 2056)
- @WanaDecryptor@.exe (PID: 3328)
- @WanaDecryptor@.exe (PID: 2728)
- taskhsvc.exe (PID: 3552)
- taskdl.exe (PID: 3036)
- @WanaDecryptor@.exe (PID: 3068)
- taskdl.exe (PID: 604)
- @WanaDecryptor@.exe (PID: 1332)
- taskdl.exe (PID: 1092)
- @WanaDecryptor@.exe (PID: 1588)
- taskdl.exe (PID: 1924)
- @WanaDecryptor@.exe (PID: 548)
Reads the machine GUID from the registry
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- taskhsvc.exe (PID: 3552)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3124)
Creates files or folders in the user directory
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
- taskhsvc.exe (PID: 3552)
Creates files in the program directory
- Proforma Invoice and Bank swift-REG.PI-0086547654.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:01:28 09:25:36 |
| ZipCRC: | 0x4022fcaa |
| ZipCompressedSize: | 3481287 |
| ZipUncompressedSize: | 3514368 |
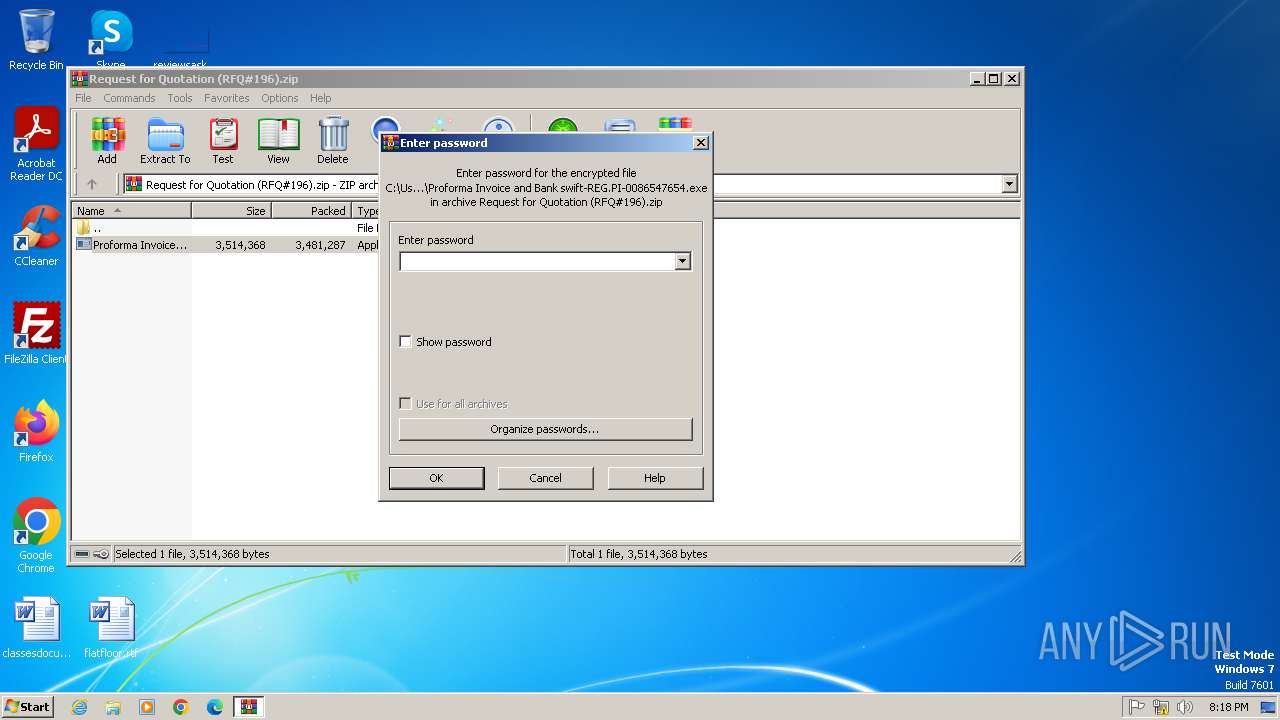
| ZipFileName: | Proforma Invoice and Bank swift-REG.PI-0086547654.exe |
Total processes
80
Monitored processes
32
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | @WanaDecryptor@.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\@WanaDecryptor@.exe | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | taskdl.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\taskdl.exe | — | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 628 | attrib +h . | C:\Windows\System32\attrib.exe | — | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1020 | "C:\Windows\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | wmic shadowcopy delete | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | taskdl.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\taskdl.exe | — | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1196 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | @WanaDecryptor@.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\@WanaDecryptor@.exe | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1588 | @WanaDecryptor@.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\@WanaDecryptor@.exe | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 913
Read events
5 879
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Request for Quotation (RFQ#196).zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
19
Suspicious files
1 082
Text files
476
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_chinese (simplified).wnry | text | |
MD5:0252D45CA21C8E43C9742285C48E91AD | SHA256:845D0E178AEEBD6C7E2A2E9697B2BF6CF02028C50C288B3BA88FE2918EA2834A | |||
| 2848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\Proforma Invoice and Bank swift-REG.PI-0086547654.exe | executable | |
MD5:84C82835A5D21BBCF75A61706D8AB549 | SHA256:ED01EBFBC9EB5BBEA545AF4D01BF5F1071661840480439C6E5BABE8E080E41AA | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\b.wnry | image | |
MD5:C17170262312F3BE7027BC2CA825BF0C | SHA256:D5E0E8694DDC0548D8E6B87C83D50F4AB85C1DEBADB106D6A6A794C3E746F4FA | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_croatian.wnry | text | |
MD5:17194003FA70CE477326CE2F6DEEB270 | SHA256:3F33734B2D34CCE83936CE99C3494CD845F1D2C02D7F6DA31D42DFC1CA15A171 | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_filipino.wnry | text | |
MD5:08B9E69B57E4C9B966664F8E1C27AB09 | SHA256:D8489F8C16318E524B45DE8B35D7E2C3CD8ED4821C136F12F5EF3C9FC3321324 | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_danish.wnry | text | |
MD5:2C5A3B81D5C4715B7BEA01033367FCB5 | SHA256:A75BB44284B9DB8D702692F84909A7E23F21141866ADF3DB888042E9109A1CB6 | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_korean.wnry | text | |
MD5:6735CB43FE44832B061EEB3F5956B099 | SHA256:552AA0F82F37C9601114974228D4FC54F7434FE3AE7A276EF1AE98A0F608F1D0 | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_german.wnry | text | |
MD5:3D59BBB5553FE03A89F817819540F469 | SHA256:2ADC900FAFA9938D85CE53CB793271F37AF40CF499BCC454F44975DB533F0B61 | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_finnish.wnry | text | |
MD5:35C2F97EEA8819B1CAEBD23FEE732D8F | SHA256:1ADFEE058B98206CB4FBE1A46D3ED62A11E1DEE2C7FF521C1EEF7C706E6A700E | |||
| 1824 | Proforma Invoice and Bank swift-REG.PI-0086547654.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2848.10669\msg\m_dutch.wnry | text | |
MD5:7A8D499407C6A647C03C4471A67EAAD7 | SHA256:2C95BEF914DA6C50D7BDEDEC601E589FBB4FDA24C4863A7260F4F72BD025799C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
1
Threats
7
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
3552 | taskhsvc.exe | 171.25.193.9:80 | — | Foreningen for digitala fri- och rattigheter | SE | unknown |
3552 | taskhsvc.exe | 85.10.202.87:9001 | — | Hetzner Online GmbH | DE | unknown |
3552 | taskhsvc.exe | 176.65.149.209:8080 | — | — | DE | unknown |
3552 | taskhsvc.exe | 185.11.180.67:9001 | — | Administrator Systems AS | NO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3552 | taskhsvc.exe | Misc activity | ET INFO TLS possible TOR SSL traffic |
3552 | taskhsvc.exe | Unknown Traffic | ET JA3 Hash - Possible Malware - Malspam |
3552 | taskhsvc.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 241 |
3552 | taskhsvc.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
3552 | taskhsvc.exe | Misc activity | ET INFO TLS possible TOR SSL traffic |
3552 | taskhsvc.exe | Unknown Traffic | ET JA3 Hash - Possible Malware - Malspam |
3552 | taskhsvc.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 241 |