| File name: | SET_UP.exe |
| Full analysis: | https://app.any.run/tasks/10439d73-7986-416e-9758-90033d8bc81a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
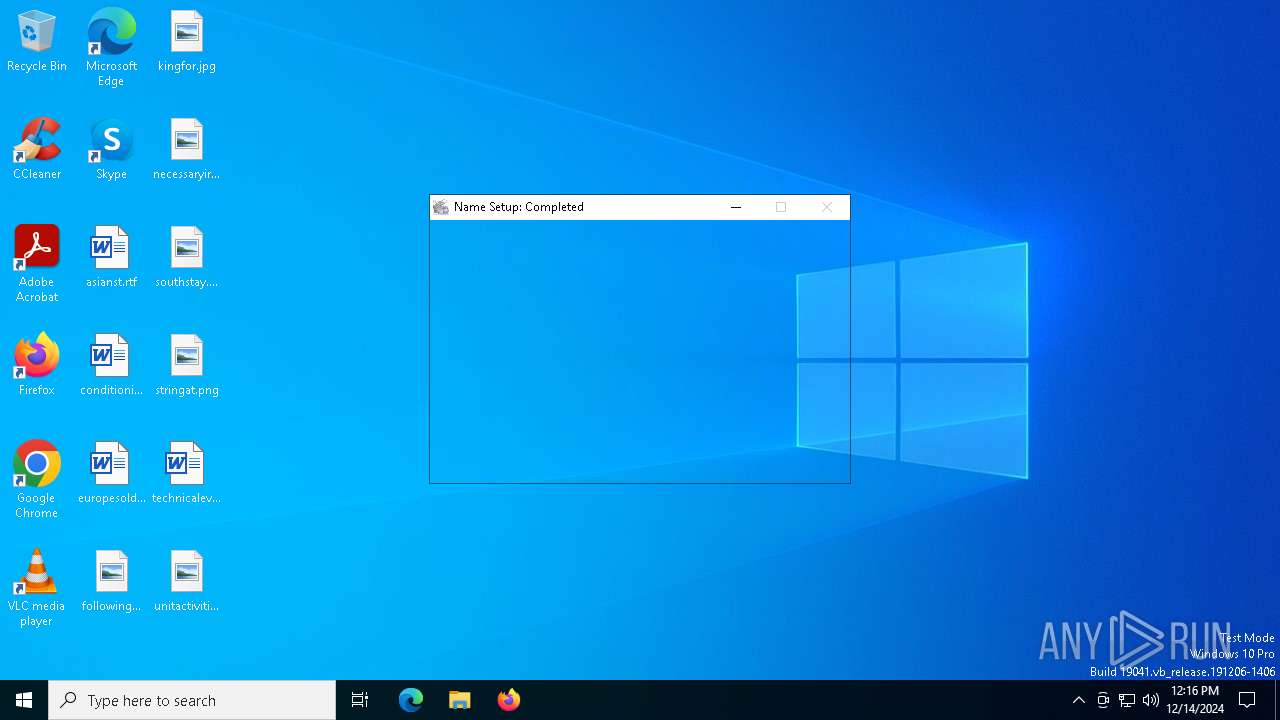
| Analysis date: | December 14, 2024, 12:16:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 3D7985D235DDDD50133C9CB4D05E93CF |
| SHA1: | F4760735FAC36EE4453905208EE47589526A30C7 |
| SHA256: | 7FEB04DD3086C567C461E43A682DD1BFDF1CDE3C8F37338A87656FC81A23BA5D |
| SSDEEP: | 98304:4W0JMnH6lSPaAny7ahqeITAUa/TsEnLz5hxBBDgS8BQX/N5qjtGm5IcDP:QMjX1mlP |
MALICIOUS
Executing a file with an untrusted certificate
- SET_UP.exe (PID: 6548)
Actions looks like stealing of personal data
- Stored.com (PID: 6916)
AutoIt loader has been detected (YARA)
- Stored.com (PID: 6916)
Steals credentials from Web Browsers
- Stored.com (PID: 6916)
LUMMA mutex has been found
- Stored.com (PID: 6916)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
SUSPICIOUS
Starts CMD.EXE for commands execution
- SET_UP.exe (PID: 6548)
- cmd.exe (PID: 6608)
Get information on the list of running processes
- cmd.exe (PID: 6608)
Executing commands from ".cmd" file
- SET_UP.exe (PID: 6548)
Application launched itself
- cmd.exe (PID: 6608)
Reads security settings of Internet Explorer
- SET_UP.exe (PID: 6548)
Executable content was dropped or overwritten
- cmd.exe (PID: 6608)
Starts the AutoIt3 executable file
- cmd.exe (PID: 6608)
The executable file from the user directory is run by the CMD process
- Stored.com (PID: 6916)
Starts application with an unusual extension
- cmd.exe (PID: 6608)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6608)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
INFO
Create files in a temporary directory
- SET_UP.exe (PID: 6548)
The process uses the downloaded file
- SET_UP.exe (PID: 6548)
Process checks computer location settings
- SET_UP.exe (PID: 6548)
Reads the computer name
- SET_UP.exe (PID: 6548)
- Stored.com (PID: 6916)
Creates a new folder
- cmd.exe (PID: 6852)
Checks supported languages
- SET_UP.exe (PID: 6548)
- Stored.com (PID: 6916)
Reads mouse settings
- Stored.com (PID: 6916)
Reads the software policy settings
- Stored.com (PID: 6916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:20:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 511488 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
131
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6548 | "C:\Users\admin\AppData\Local\Temp\SET_UP.exe" | C:\Users\admin\AppData\Local\Temp\SET_UP.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6608 | "C:\Windows\System32\cmd.exe" /c copy Figured Figured.cmd && Figured.cmd | C:\Windows\SysWOW64\cmd.exe | SET_UP.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6680 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6692 | findstr /I "wrsa opssvc" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6792 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6800 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6852 | cmd /c md 516983 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6872 | findstr /V "ProposedKellyChampionCouldMinistryPhotographersNotFruit" Permitted | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 095
Read events
1 095
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
16
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Locator | binary | |
MD5:85E9FAB9AB9A2CE1935F980078995C7B | SHA256:0392E54997947D4E6AC2A5A919F18699DB82524DA641AA913B9E360BB2A1D7DF | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Transport | binary | |
MD5:29310511E646A9DB8EC20112F750205A | SHA256:92572FF759F59420EB6EF712DC8DB8469C63425F0B2AB5798EBB19370FFB61E1 | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Suicide | binary | |
MD5:1EE9DAEEF21C43336AE8626E9335BEB5 | SHA256:DAB4963BCAFDA1A1E3FCEE0678F1B77B8440DA6E6F04A3CB858AD37101ABFE3D | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Returns | gpg | |
MD5:299474AEFC18F21A899289DA0E9C20A5 | SHA256:8C6FA7CD083A01B4A76F96188BE63E1E80657C45F0D85418B342C2580A45472C | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Quest | binary | |
MD5:05C707C8F33E056405D5138D7CBAC25B | SHA256:0815C0EFAB440E5298F28FE5D266AD8DEA60EADB3A82DB46C95ADBE2B6EEADB0 | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Figured | text | |
MD5:21350FCCD60418B01CF83AC826AA31E9 | SHA256:BE21F7CA2001511FBC3E0E43312F8649E83037EBF098682D5FA1D290E62BF470 | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Hdtv | binary | |
MD5:287E05D580B456477FD557F23109E172 | SHA256:55CD25CC9644F9015C6996048C072AC40173284E80DEEB745E4C4DF37DD00A6F | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Joel | binary | |
MD5:FED092A988D0DB96E611A27280DD05B7 | SHA256:8CD6962716B0B9BF77F28D1A37238CBDCB09FDB97F0761FF224B78201227CCB3 | |||
| 6608 | cmd.exe | C:\Users\admin\AppData\Local\Temp\516983\Stored.com | executable | |
MD5:3DEC208B512C5ADCD445D7FD80F11B8A | SHA256:8CA3A132A9B953C94813C736CC7A911D5C7792E19126E37DEC064BAD1B1454A7 | |||
| 6548 | SET_UP.exe | C:\Users\admin\AppData\Local\Temp\Ghana | binary | |
MD5:3AB94BB43E76A8079D9A89259A3A49A4 | SHA256:1627A89C2D801544C1020462EFB4D6C7D615A6407BC6097B7F7423FE79C383D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1380 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1380 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2940 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2548 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2548 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1380 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1380 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
trxBhEXoOi.trxBhEXoOi |
| unknown |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (klipcatepiu0 .shop) |