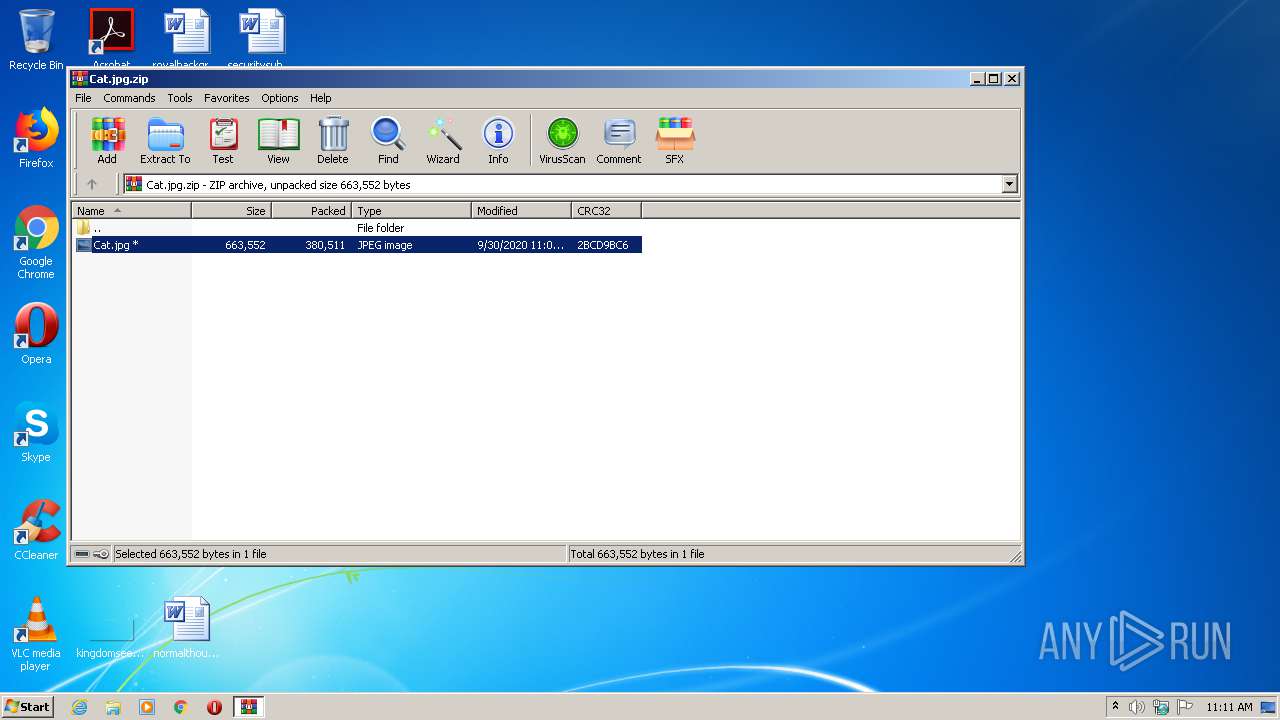
| File name: | Cat.jpg.zip |
| Full analysis: | https://app.any.run/tasks/de259f24-2d65-48d4-8eb6-b08b94b3d8bd |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | September 30, 2020, 10:11:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
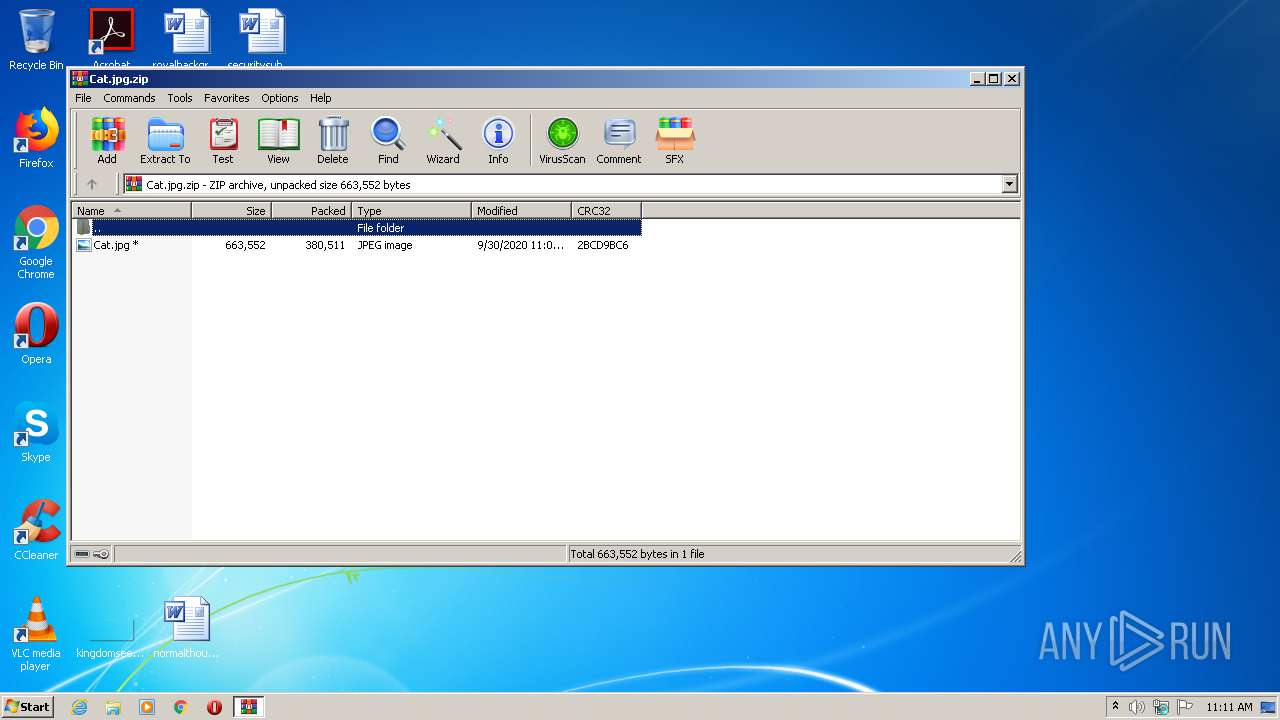
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2C0F9DE7626F5C23FE8F4FB271728CE3 |
| SHA1: | 3D5A11FC836FBD8113D06FA80D8A03F215ADB639 |
| SHA256: | 7FB2335E6267BEC98739BEFFC898A1C2A446798E9AFF044F56ADAB145D201053 |
| SSDEEP: | 6144:niCCtcMgxRsSiqtVxYjwJc3B7AJoB68g7MyP6d32niRM7+9tE6BYPTCUYmKl8N2V:niCCyvsSfVxYjwJcKJ2g7MyPLnYM2E6B |
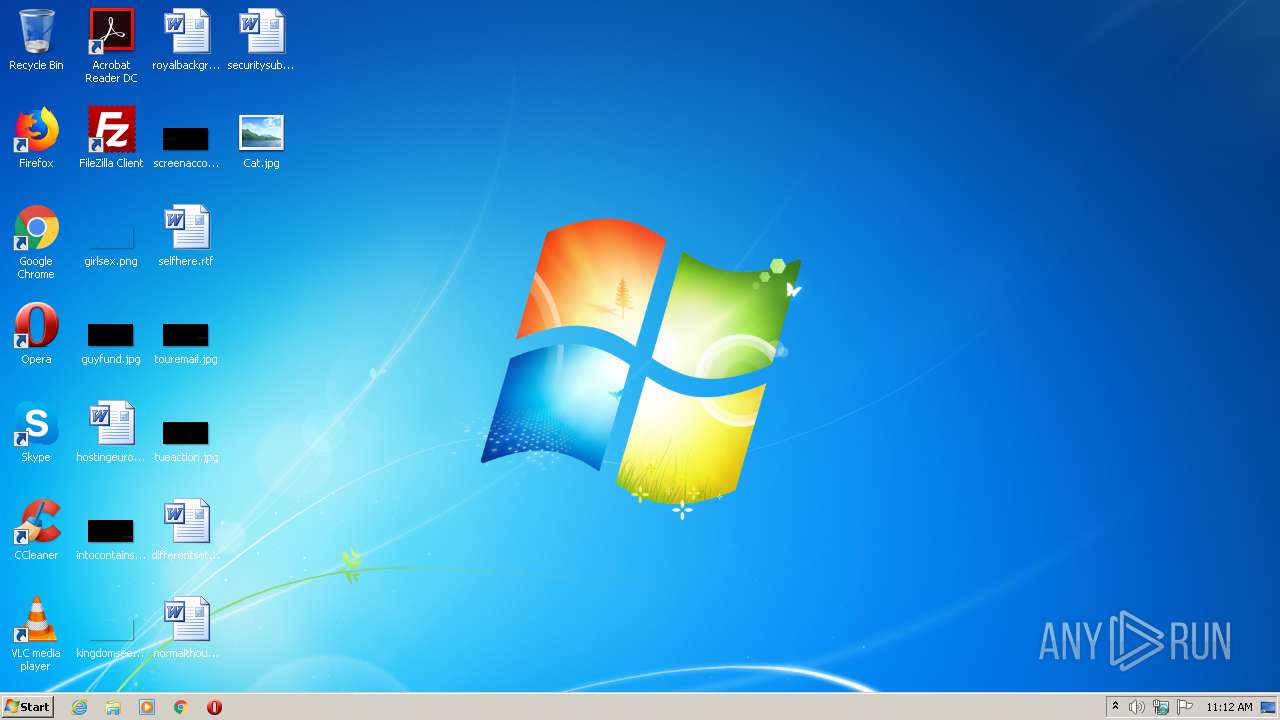
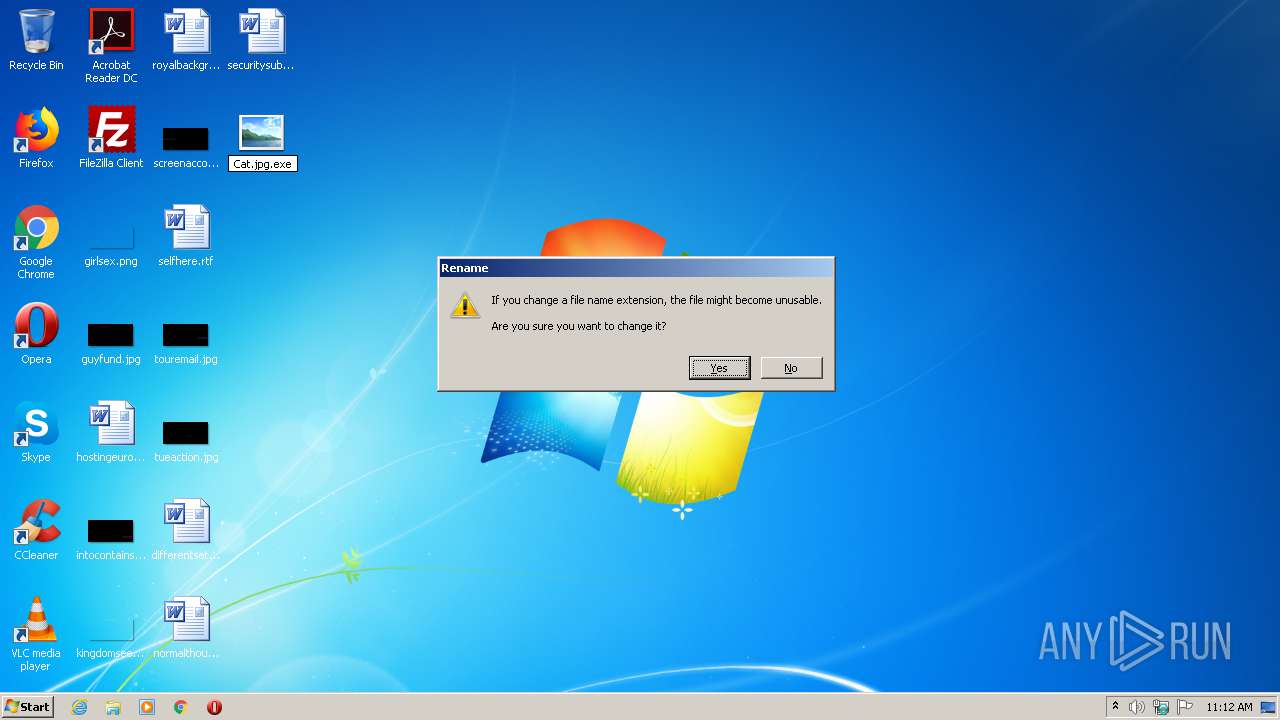
MALICIOUS
Application was dropped or rewritten from another process
- Cat.jpg.exe (PID: 3160)
- $77-WindowsUpdate.exe (PID: 2524)
- Windows.exe (PID: 980)
- $77-WindowsUpdate.exe (PID: 3952)
Changes the autorun value in the registry
- $77-WindowsUpdate.exe (PID: 2524)
- Windows.exe (PID: 980)
QUASAR was detected
- $77-WindowsUpdate.exe (PID: 2524)
- Windows.exe (PID: 980)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2200)
SUSPICIOUS
Starts itself from another location
- $77-WindowsUpdate.exe (PID: 2524)
Creates files in the user directory
- Cat.jpg.exe (PID: 3160)
- $77-WindowsUpdate.exe (PID: 2524)
- Windows.exe (PID: 980)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2452)
- Cat.jpg.exe (PID: 3160)
- $77-WindowsUpdate.exe (PID: 2524)
Executed via COM
- DllHost.exe (PID: 3008)
Starts CMD.EXE for commands execution
- $77-WindowsUpdate.exe (PID: 2524)
Checks for external IP
- $77-WindowsUpdate.exe (PID: 2524)
- Windows.exe (PID: 980)
Starts application with an unusual extension
- cmd.exe (PID: 2200)
INFO
Manual execution by user
- Cat.jpg.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:09:30 10:08:15 |
| ZipCRC: | 0x2bcd9bc6 |
| ZipCompressedSize: | 380511 |
| ZipUncompressedSize: | 663552 |
| ZipFileName: | Cat.jpg |
Total processes
46
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 980 | "C:\Users\admin\AppData\Roaming\Windows\Windows.exe" | C:\Users\admin\AppData\Roaming\Windows\Windows.exe | $77-WindowsUpdate.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 2164 | chcp 65001 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | cmd /c ""C:\Users\admin\AppData\Local\Temp\dtA9D1Ec5TM7.bat" " | C:\Windows\system32\cmd.exe | — | $77-WindowsUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
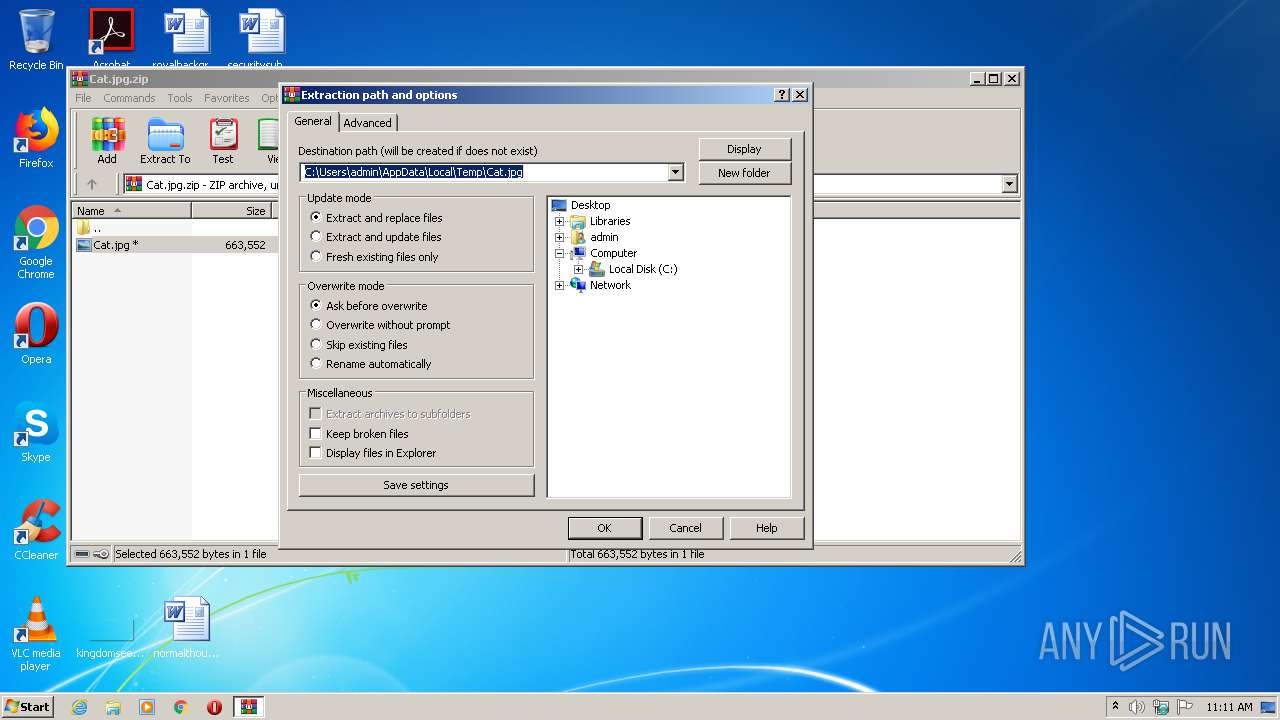
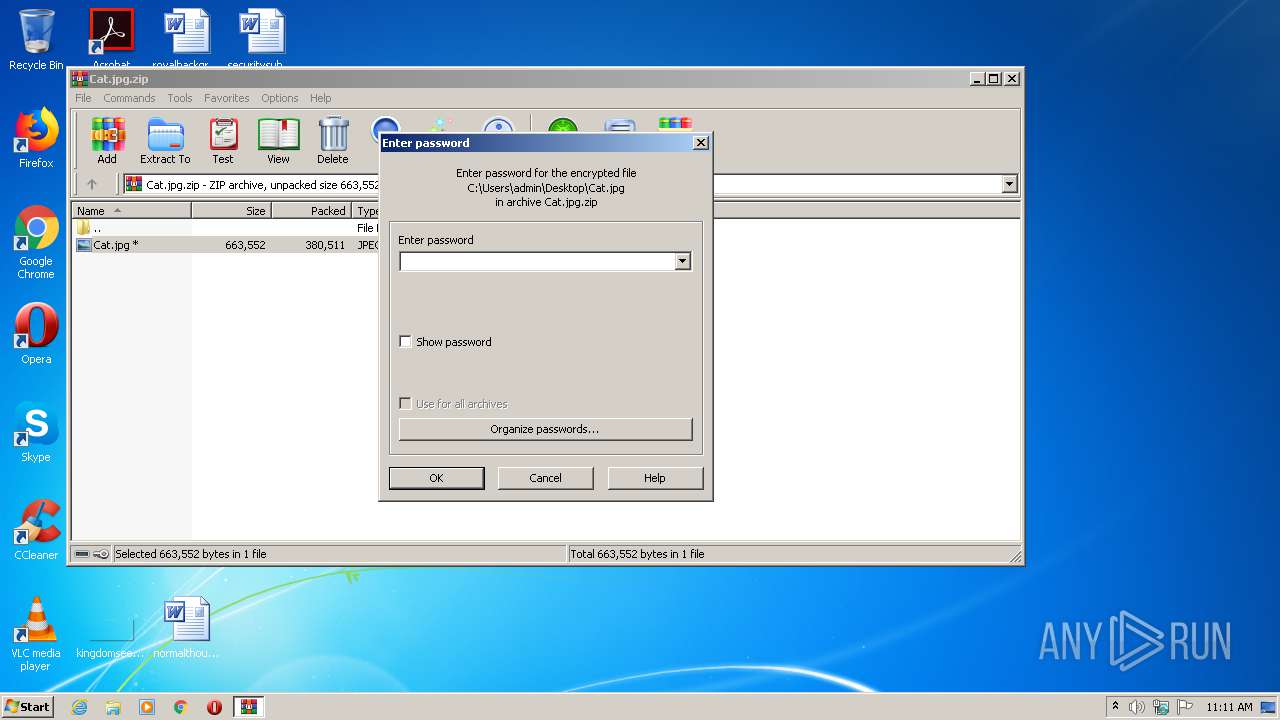
| 2452 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Cat.jpg.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\AppData\Roaming\$77-WindowsUpdate.exe" | C:\Users\admin\AppData\Roaming\$77-WindowsUpdate.exe | Cat.jpg.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 2844 | ping -n 10 localhost | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\Desktop\Cat.jpg.exe" | C:\Users\admin\Desktop\Cat.jpg.exe | explorer.exe | ||||||||||||
User: admin Company: buffer Integrity Level: MEDIUM Description: combatantdisconnect Exit code: 0 Version: 9.27.71.6 Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Roaming\$77-WindowsUpdate.exe" | C:\Users\admin\AppData\Roaming\$77-WindowsUpdate.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
1 669
Read events
1 600
Write events
69
Delete events
0
Modification events
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cat.jpg.zip | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
3
Suspicious files
1
Text files
2
Unknown types
0
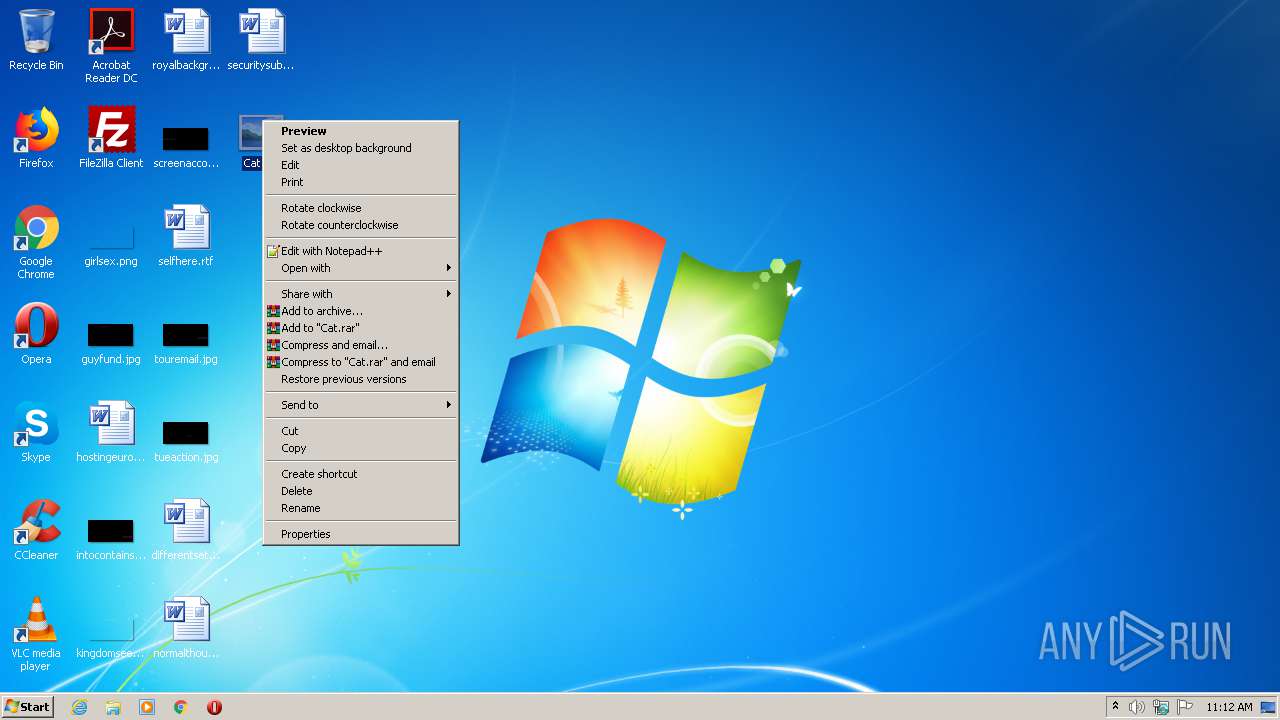
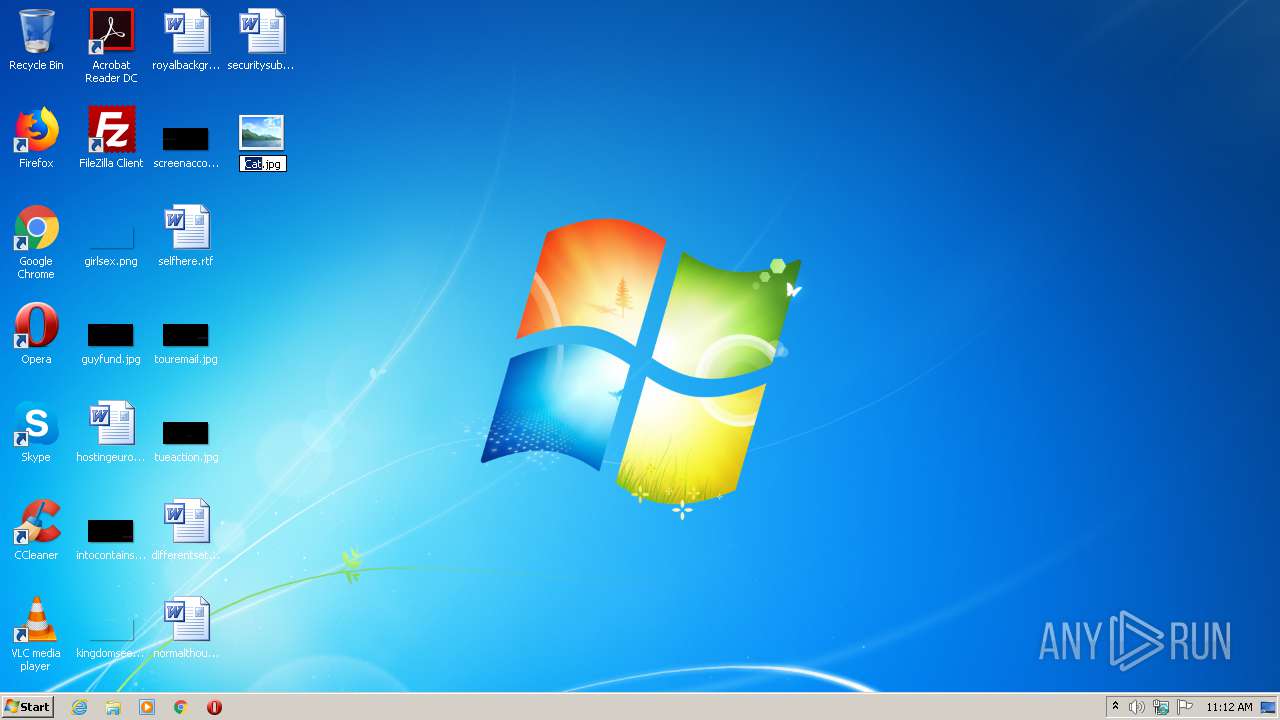
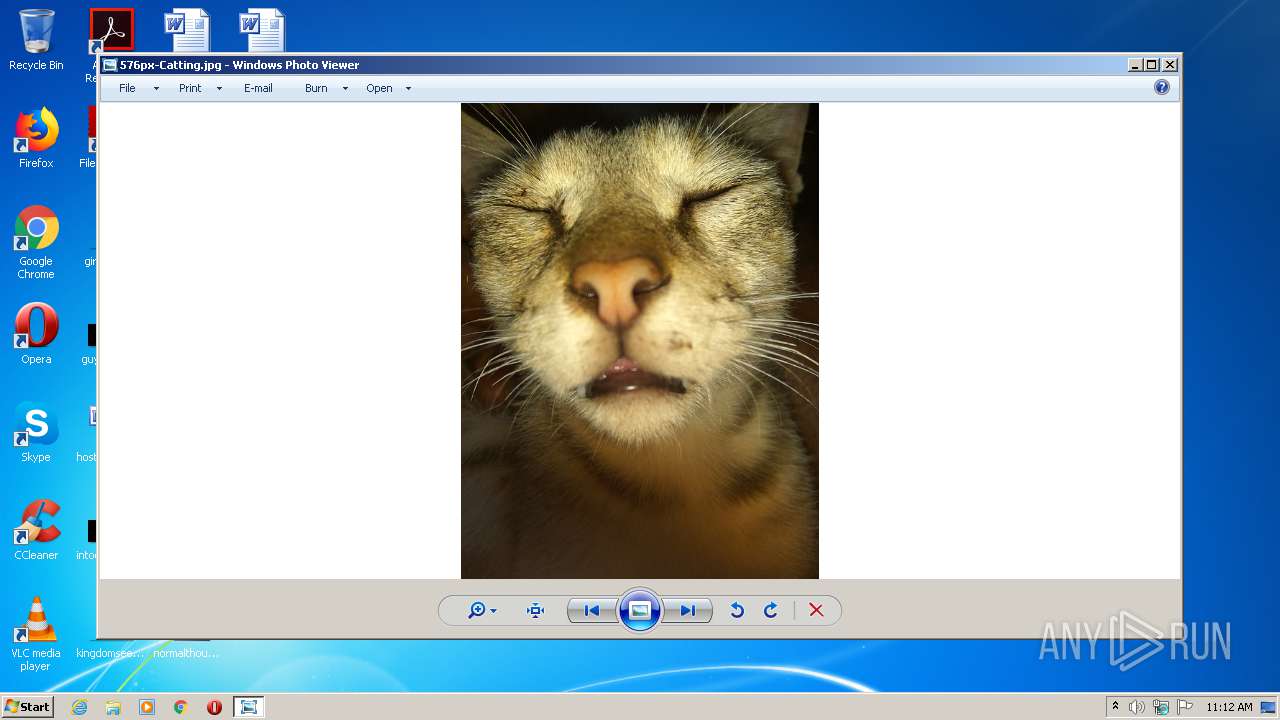
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | Cat.jpg.exe | C:\Users\admin\AppData\Roaming\576px-Catting.jpg | image | |
MD5:— | SHA256:— | |||
| 3160 | Cat.jpg.exe | C:\Users\admin\AppData\Roaming\$77-WindowsUpdate.exe | executable | |
MD5:— | SHA256:— | |||
| 2452 | WinRAR.exe | C:\Users\admin\Desktop\Cat.jpg | executable | |
MD5:— | SHA256:— | |||
| 980 | Windows.exe | C:\Users\admin\AppData\Roaming\Logs\09-30-2020 | binary | |
MD5:— | SHA256:— | |||
| 2524 | $77-WindowsUpdate.exe | C:\Users\admin\AppData\Local\Temp\dtA9D1Ec5TM7.bat | text | |
MD5:— | SHA256:— | |||
| 2524 | $77-WindowsUpdate.exe | C:\Users\admin\AppData\Roaming\Windows\Windows.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
49
DNS requests
2
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
980 | Windows.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 258 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2524 | $77-WindowsUpdate.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
980 | Windows.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
2524 | $77-WindowsUpdate.exe | 145.14.145.179:443 | payloads-poison.000webhostapp.com | Hostinger International Limited | US | shared |
980 | Windows.exe | 193.161.193.99:45152 | — | OOO Bitree Networks | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
payloads-poison.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2524 | $77-WindowsUpdate.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2524 | $77-WindowsUpdate.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2524 | $77-WindowsUpdate.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
2524 | $77-WindowsUpdate.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
980 | Windows.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
980 | Windows.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
980 | Windows.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
980 | Windows.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 404 |
980 | Windows.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 404 |
2 ETPRO signatures available at the full report