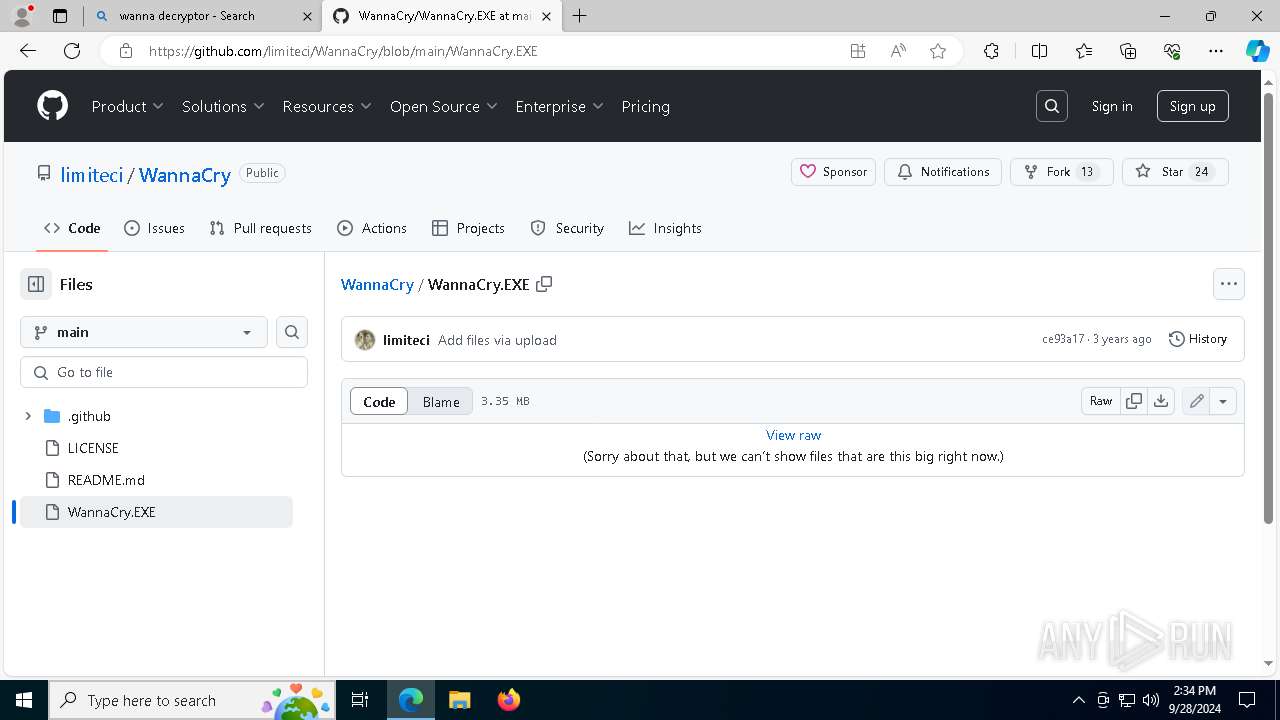
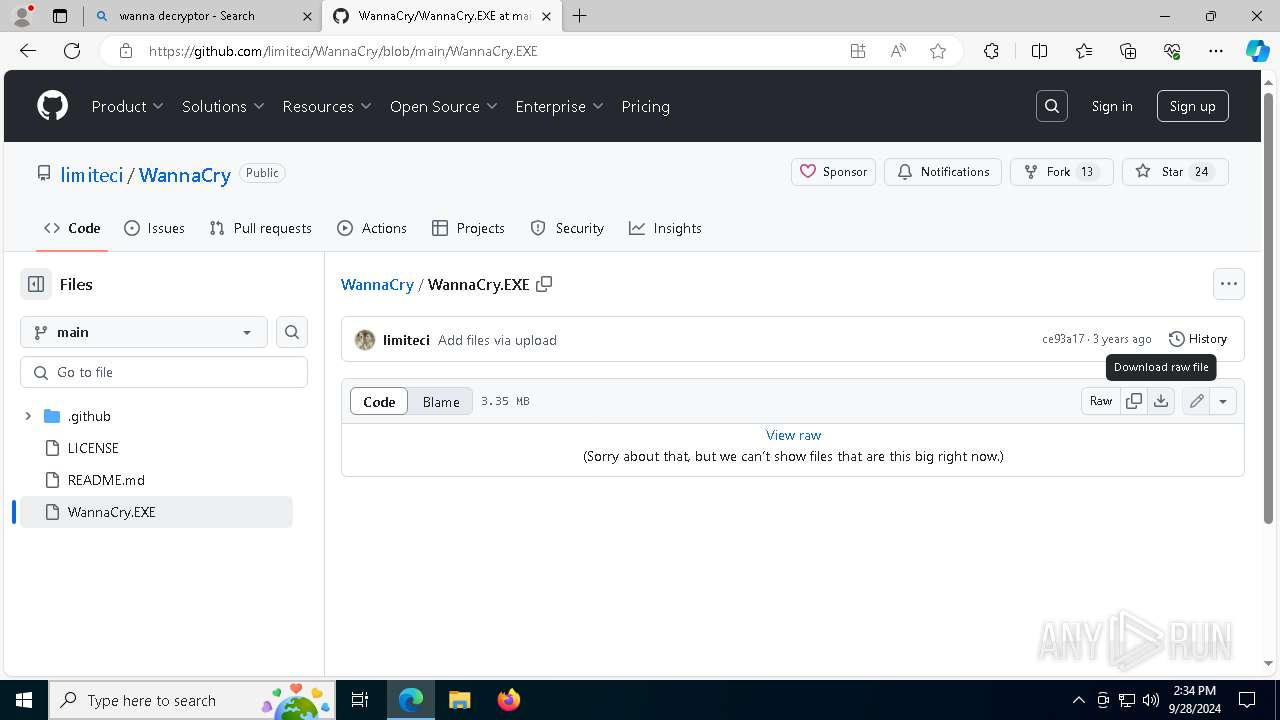
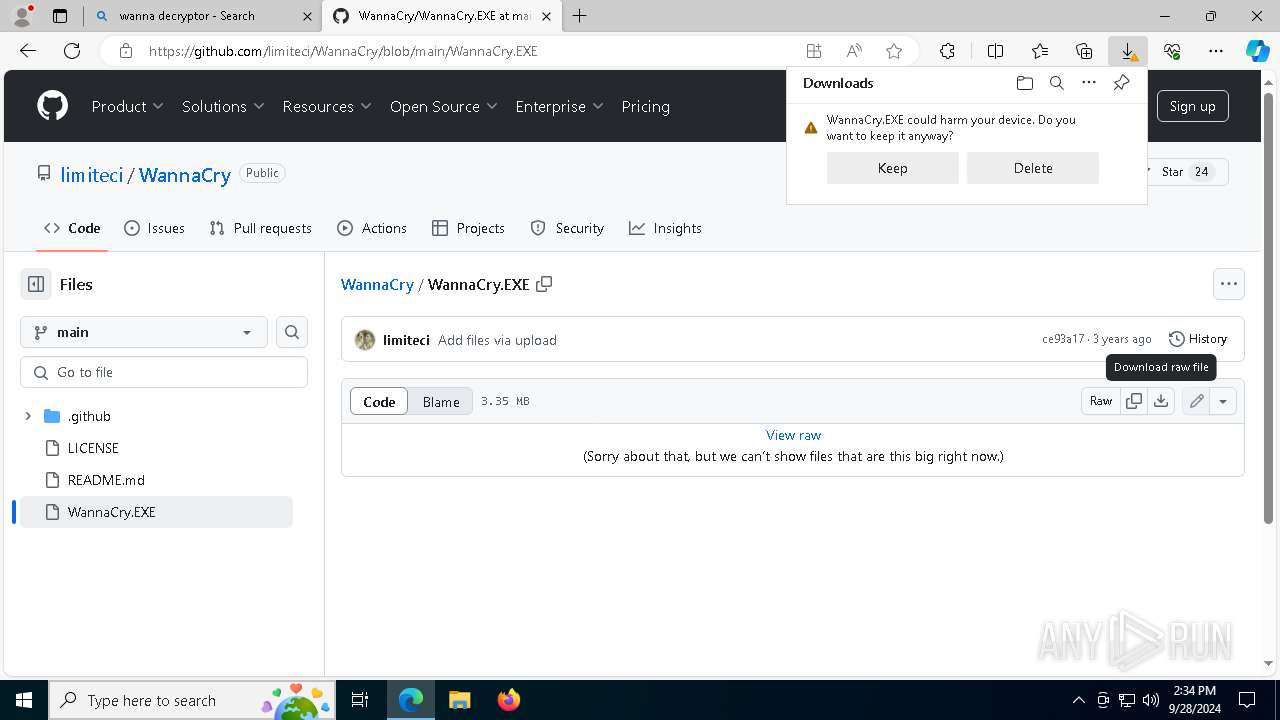
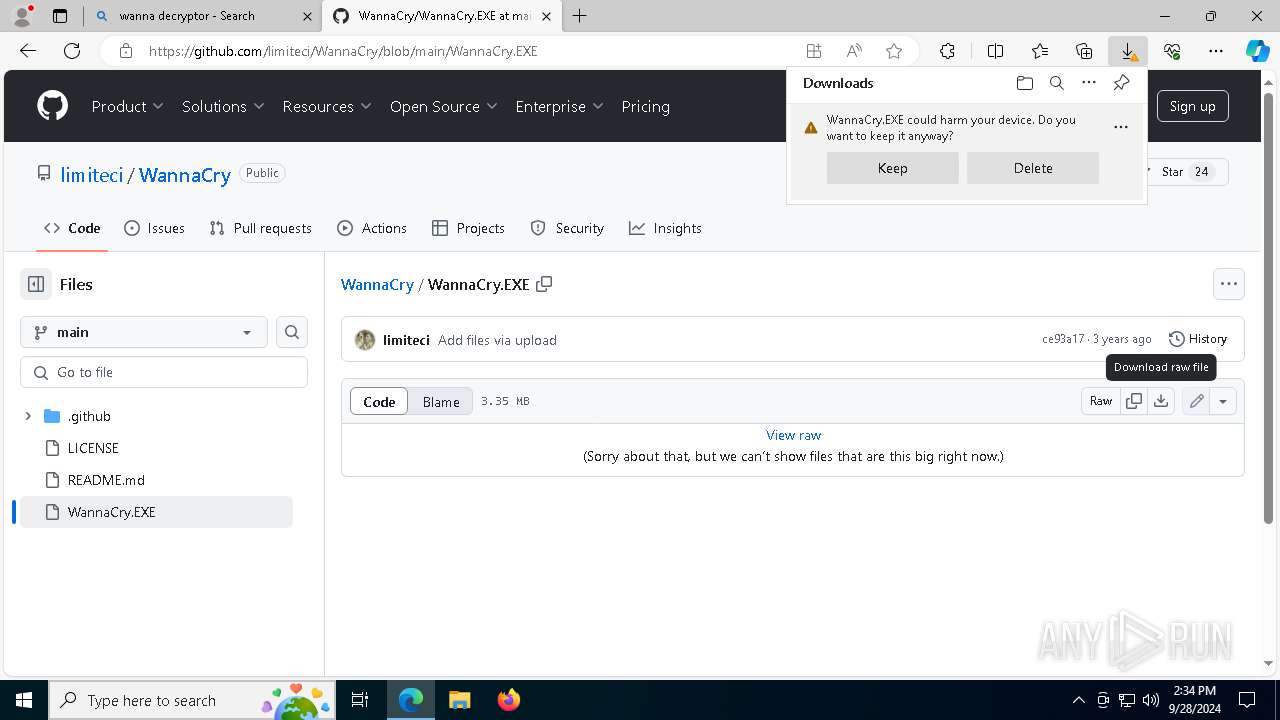
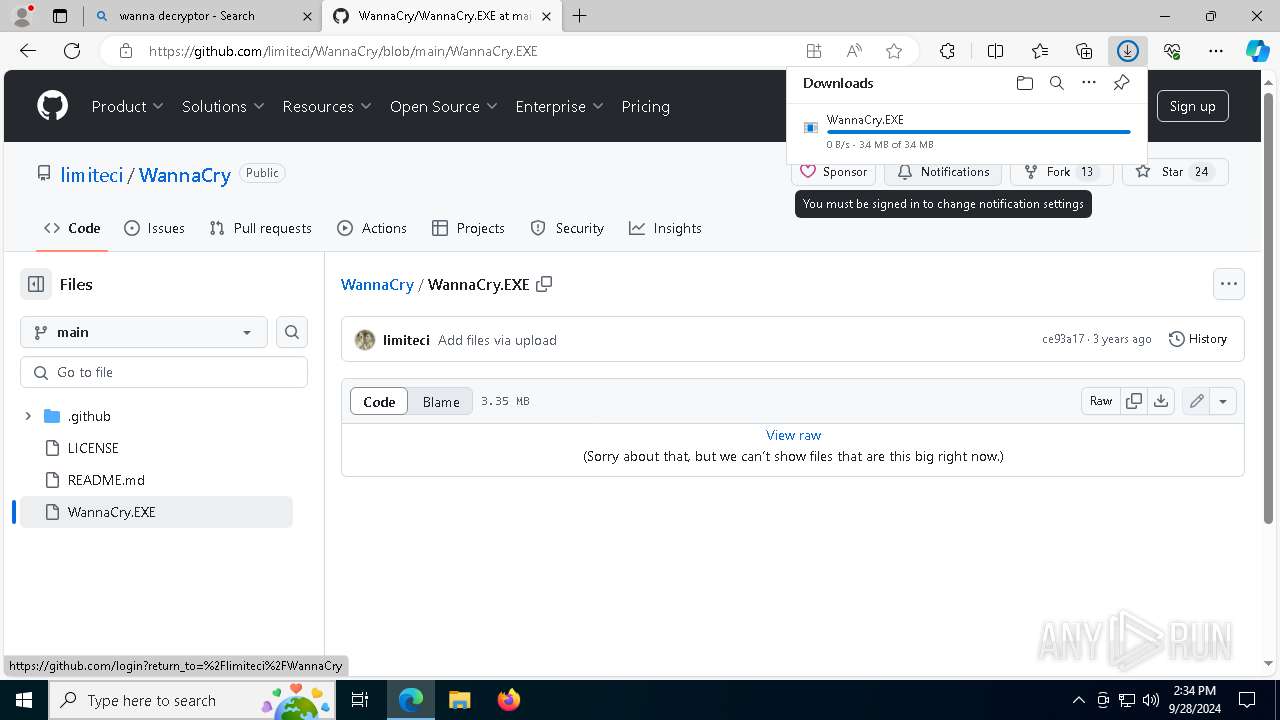
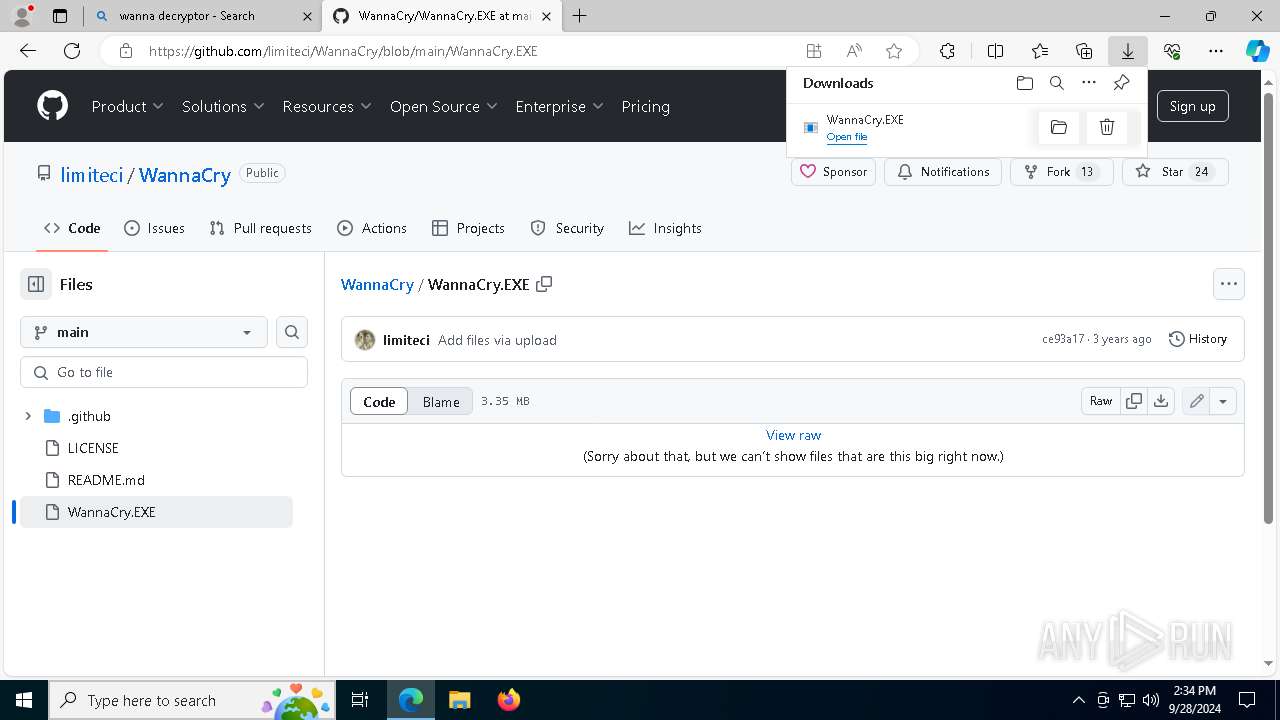
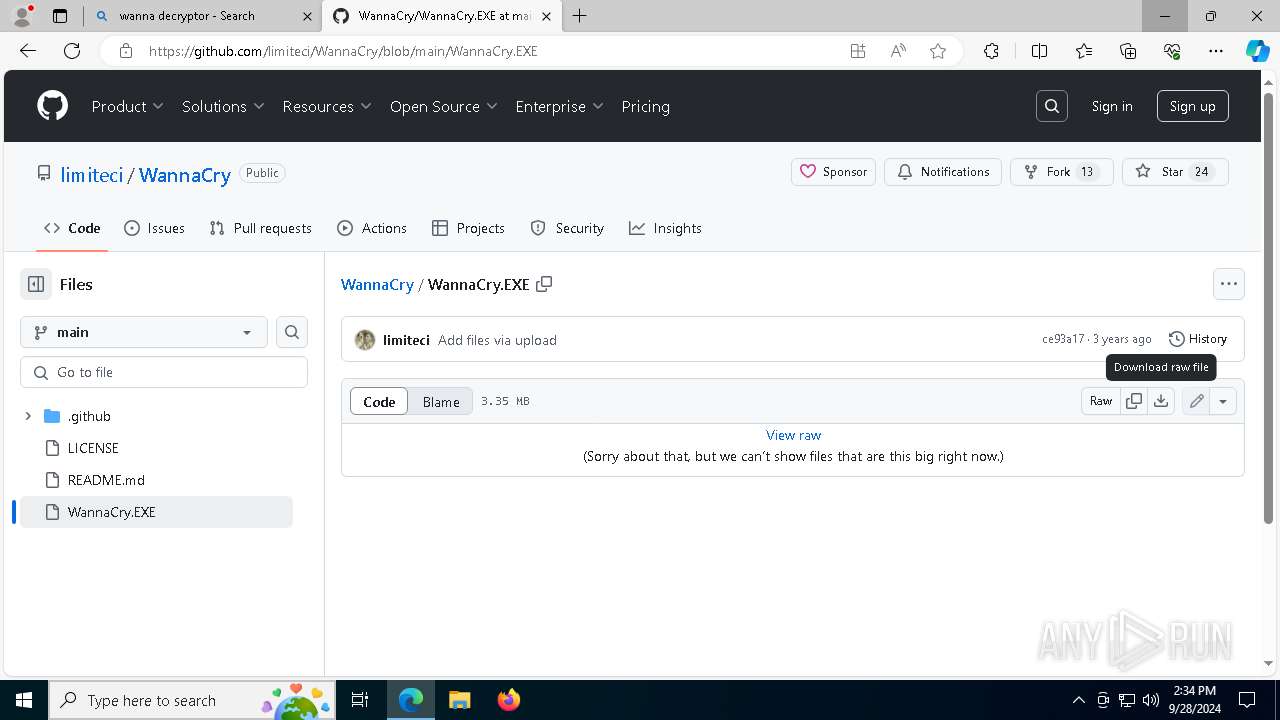
| URL: | https://www.bing.com/search?pglt=41&q=wanna+decryptor&cvid=b9806e8b29a34f54b7b8df3452d80876&gs_lcrp=EgZjaHJvbWUqBggBEAAYQDIGCAAQRRg5MgYIARAAGEAyBggCEAAYQDIGCAMQABhAMgYIBBAAGEAyBggFEAAYQDIGCAYQABhAMgYIBxAAGEAyBggIEAAYQNIBCDM4NzFqMGoxqAIAsAIA&FORM=ANNTA1&ucpdpc=UCPD&PC=ACTS |
| Full analysis: | https://app.any.run/tasks/b54fffc7-d930-4253-9908-b226fe0b5b6c |
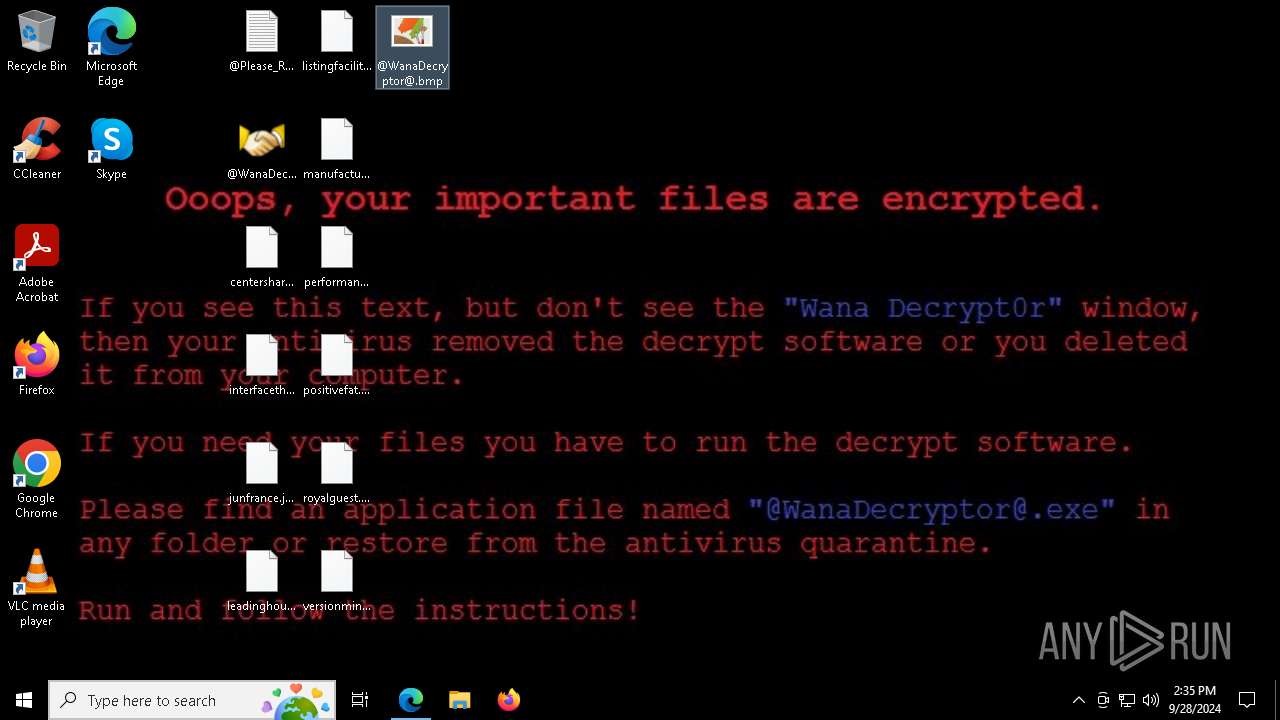
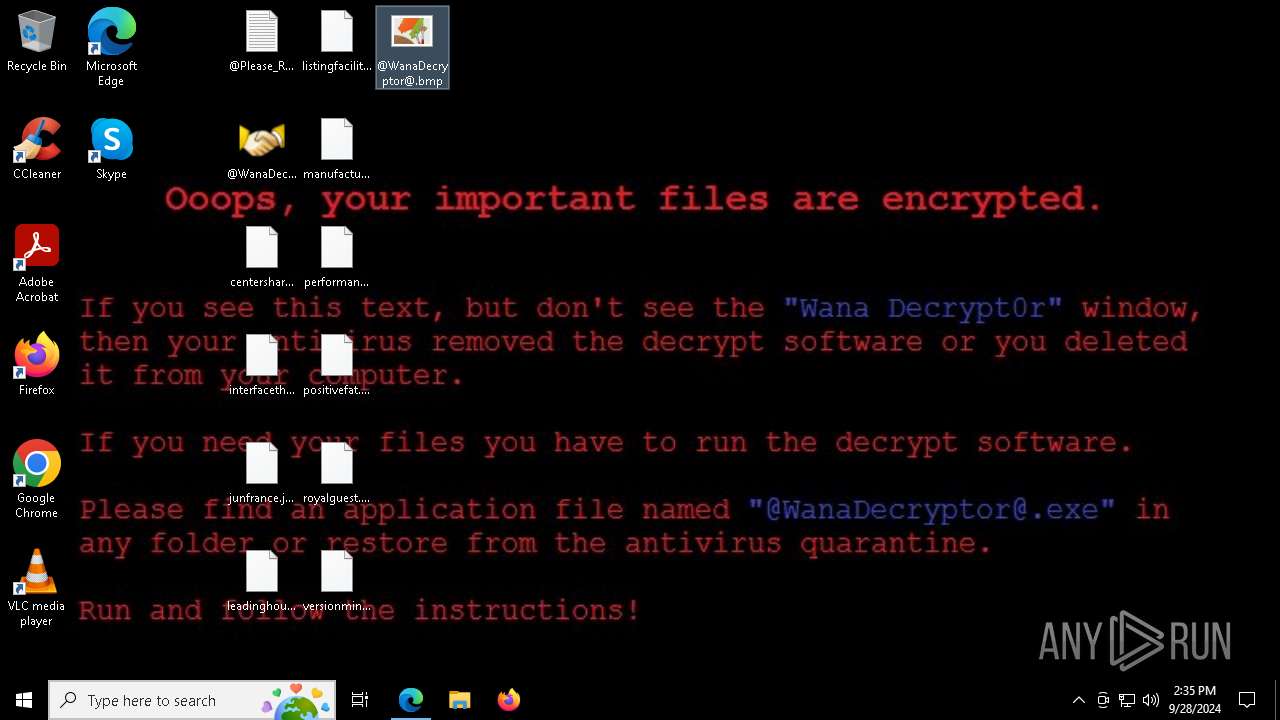
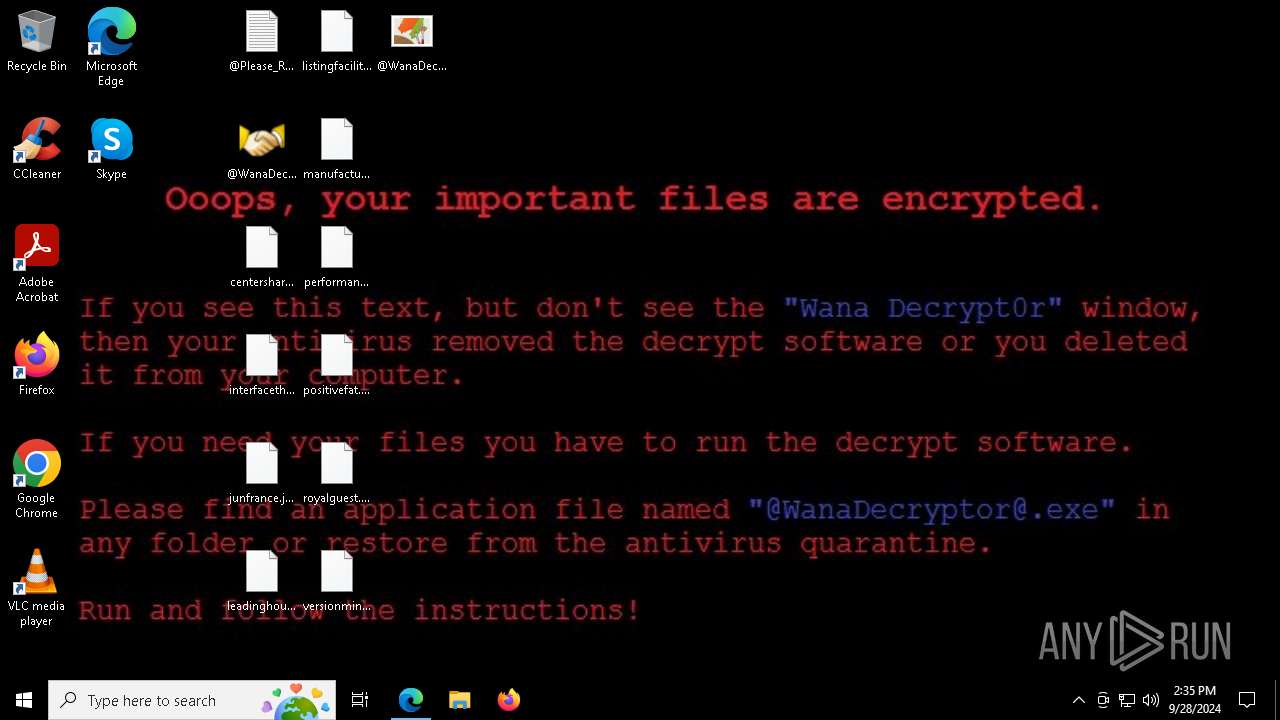
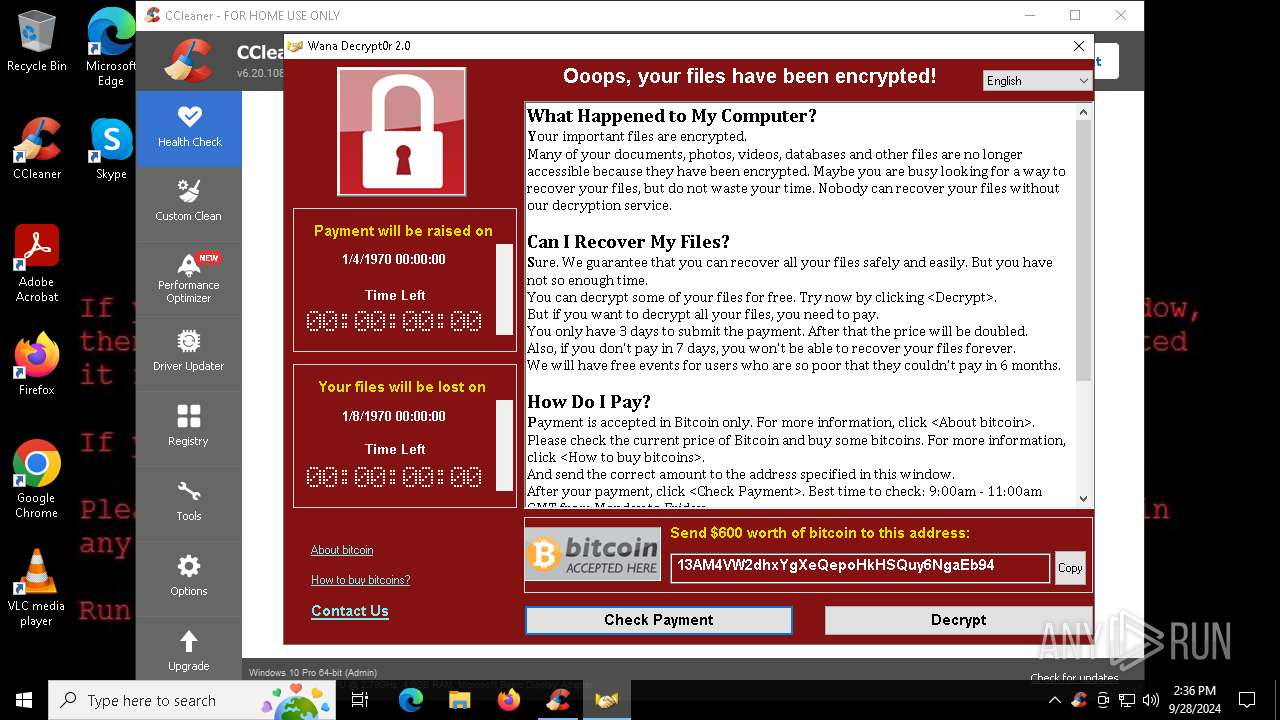
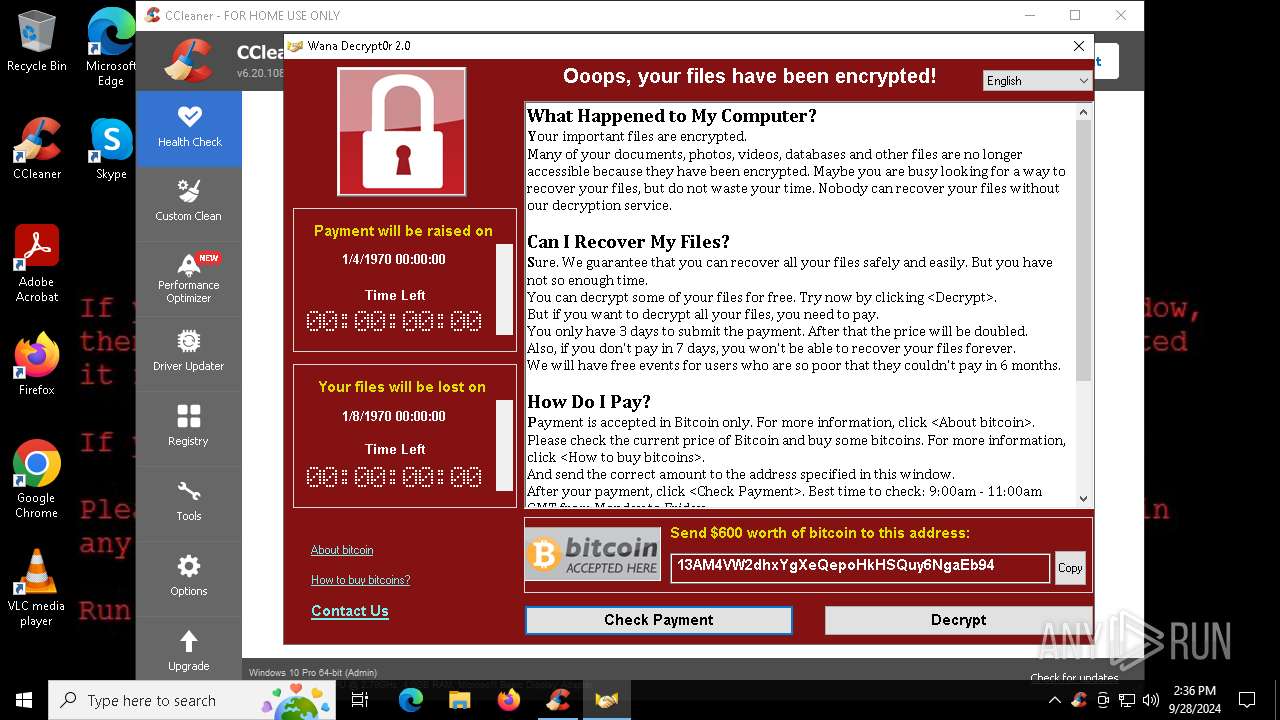
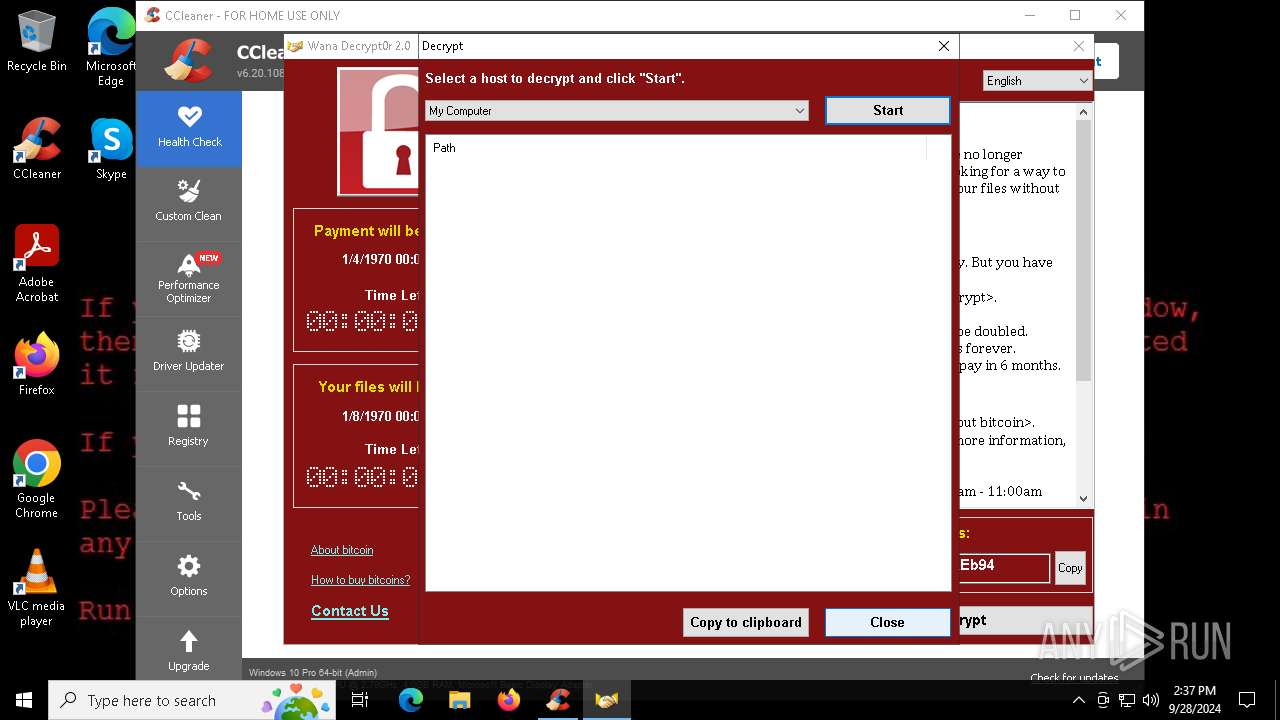
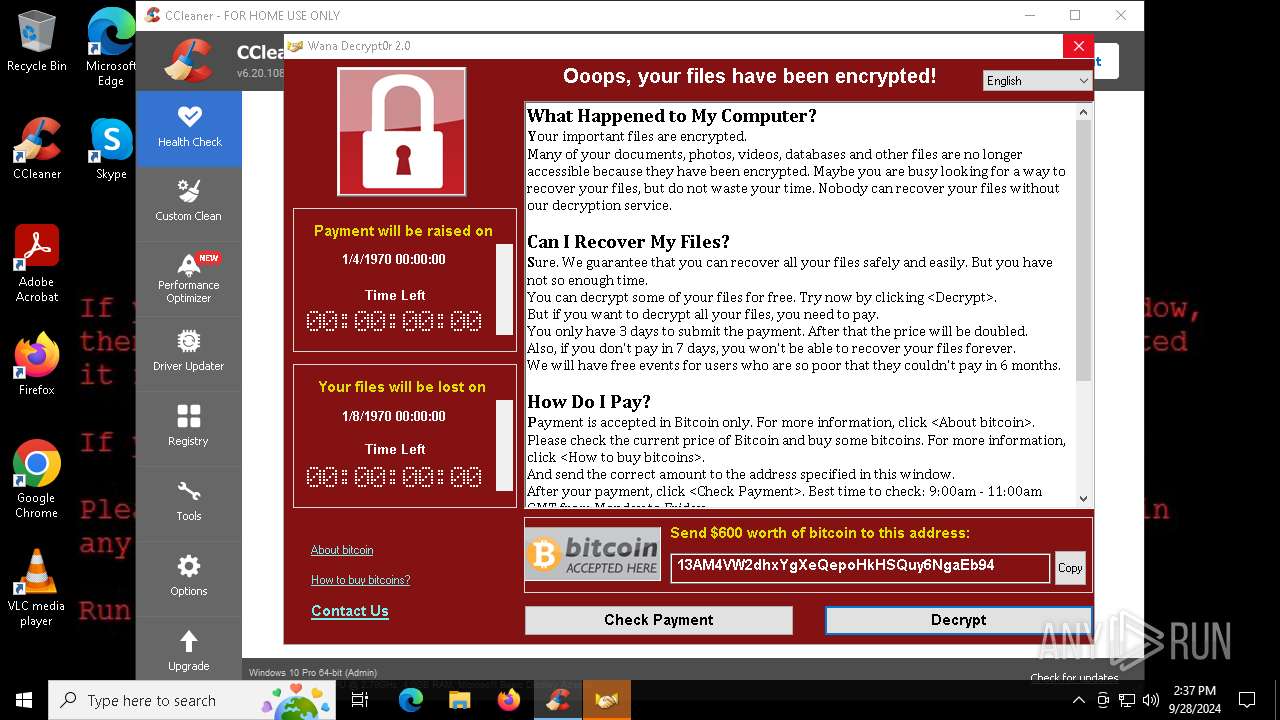
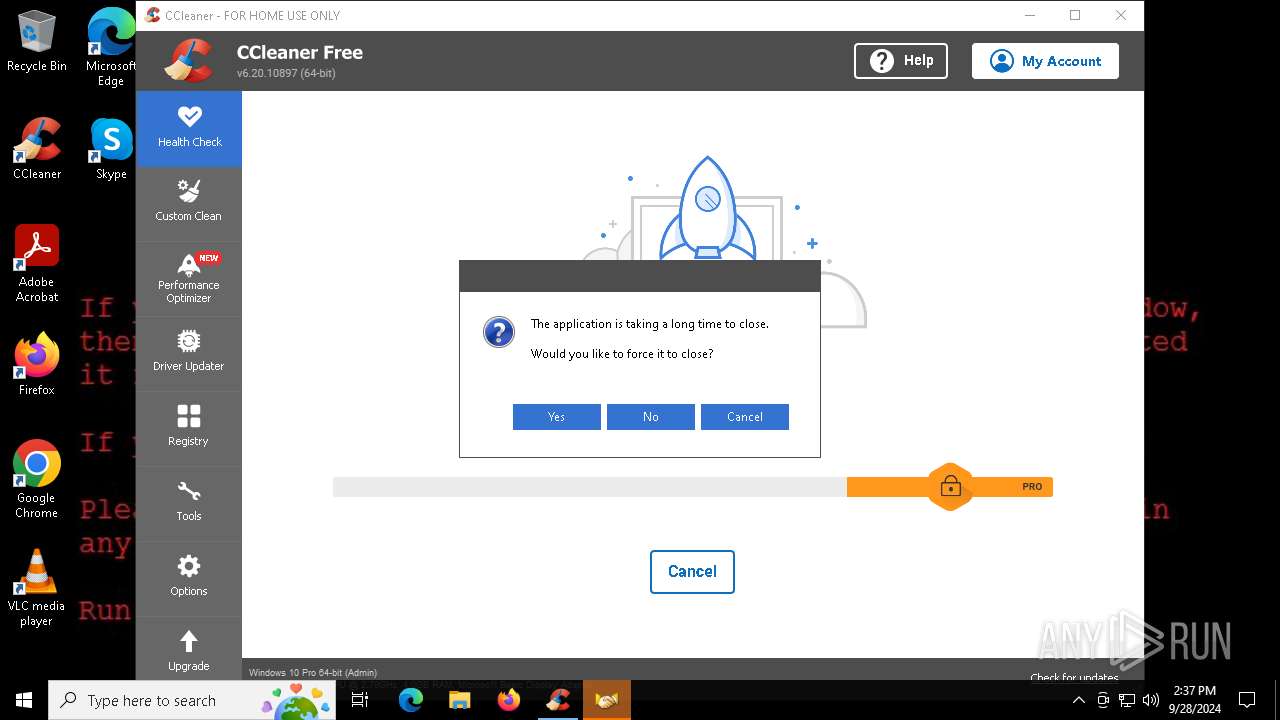
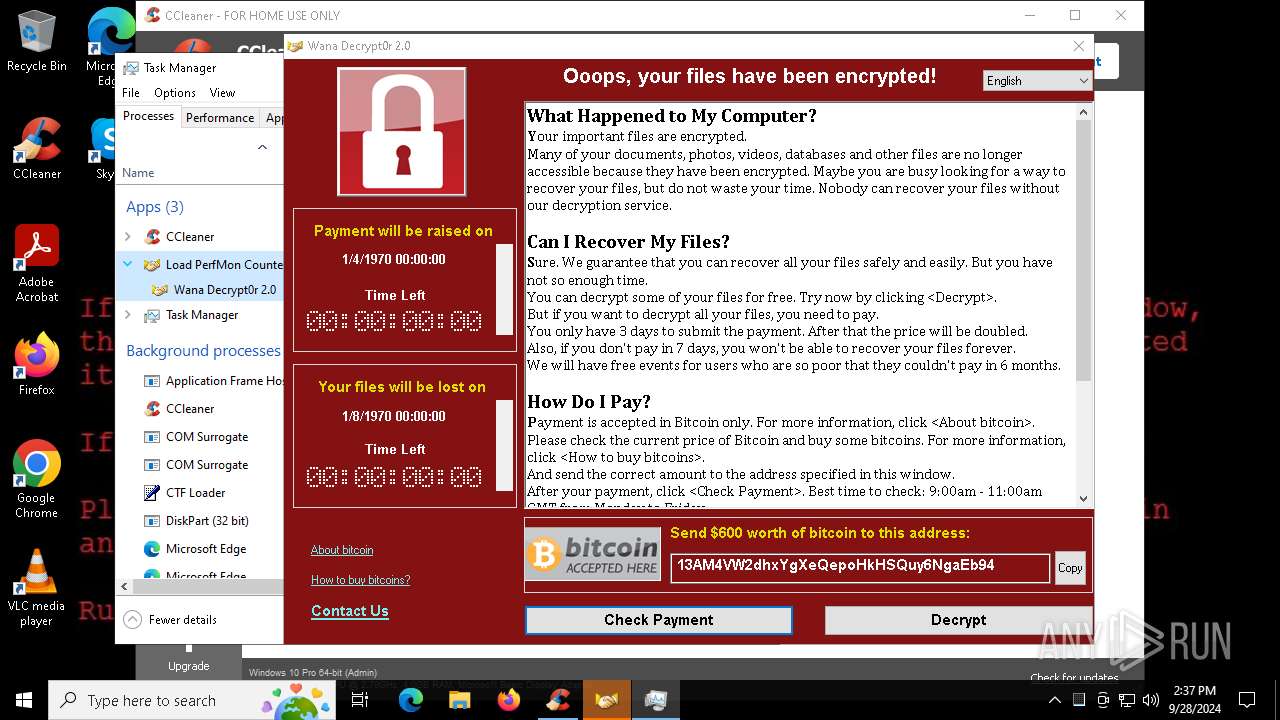
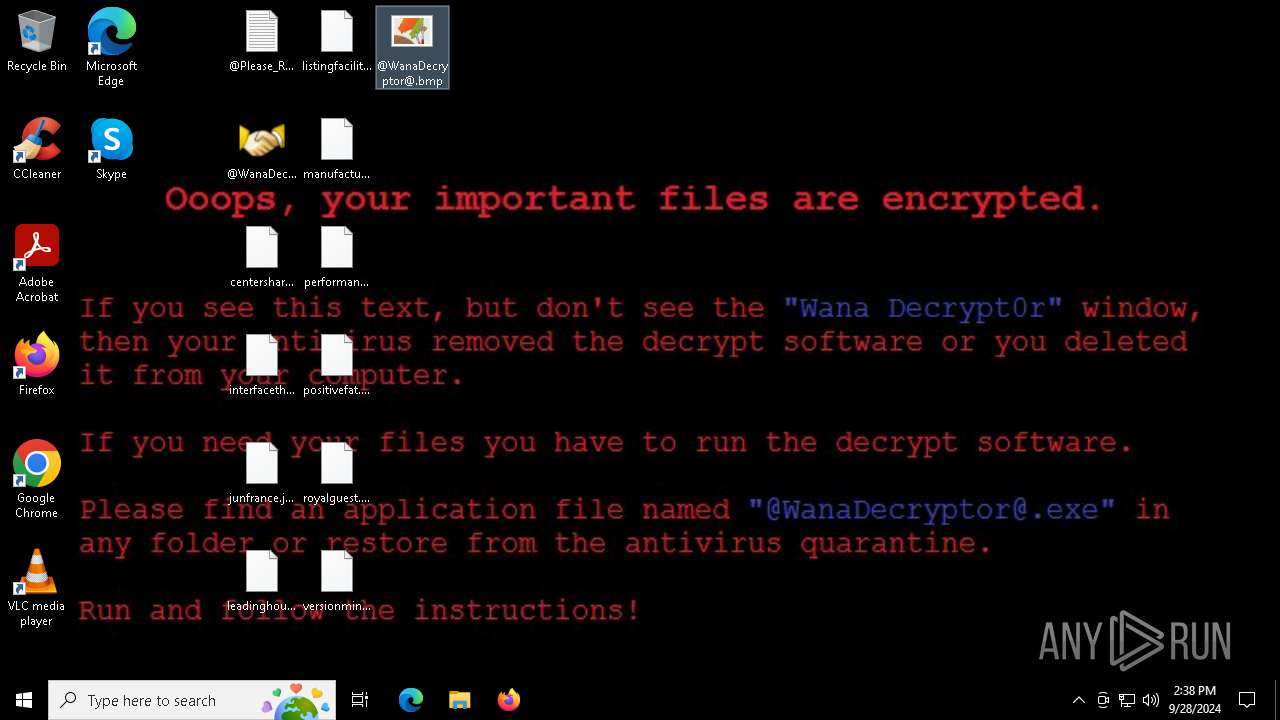
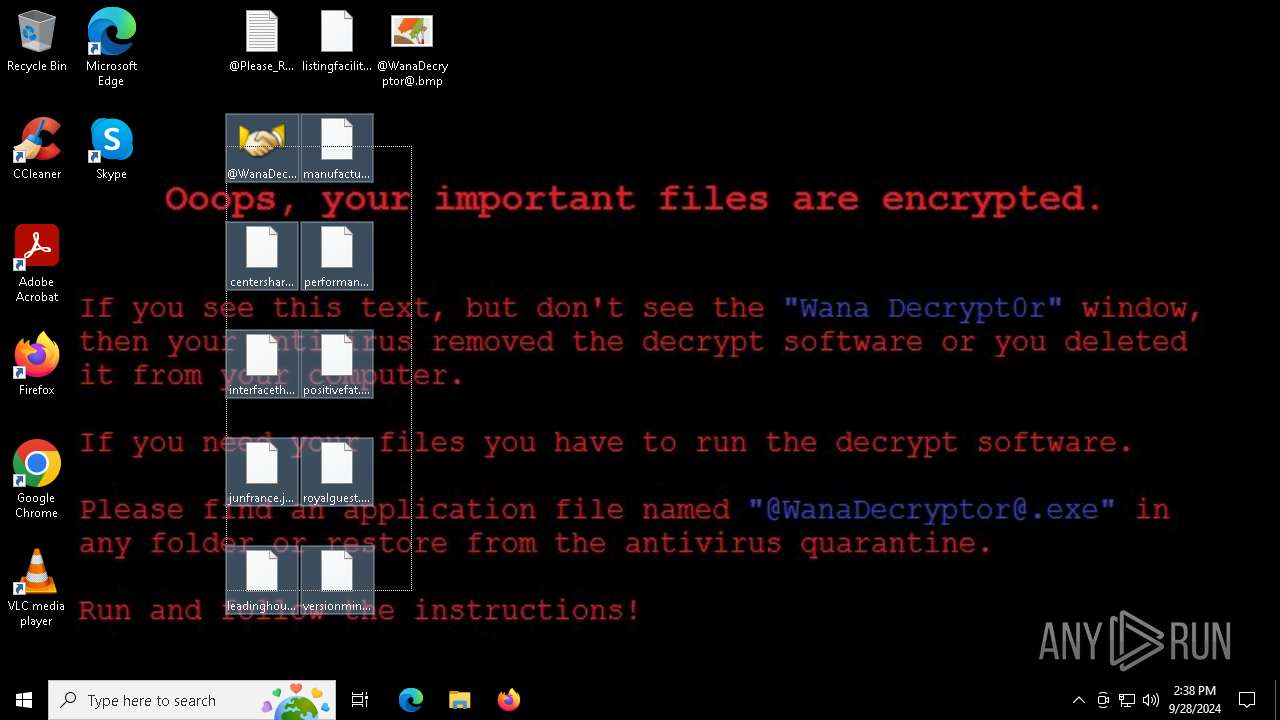
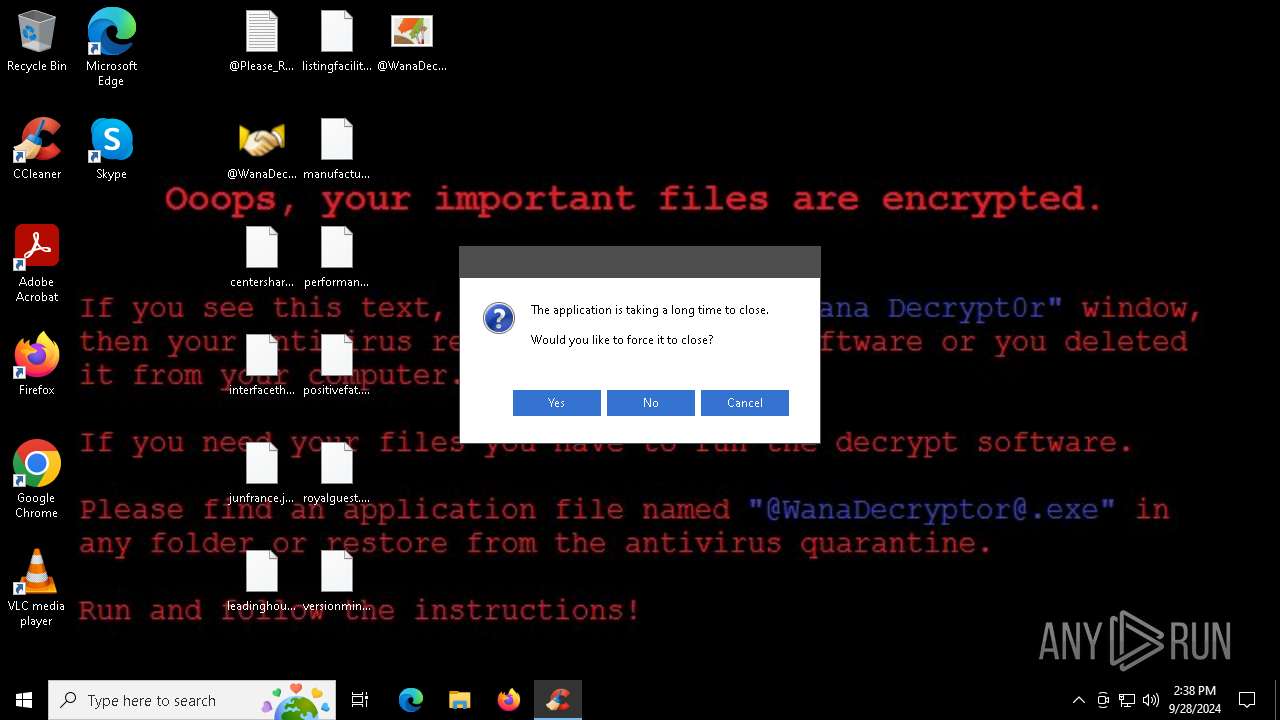
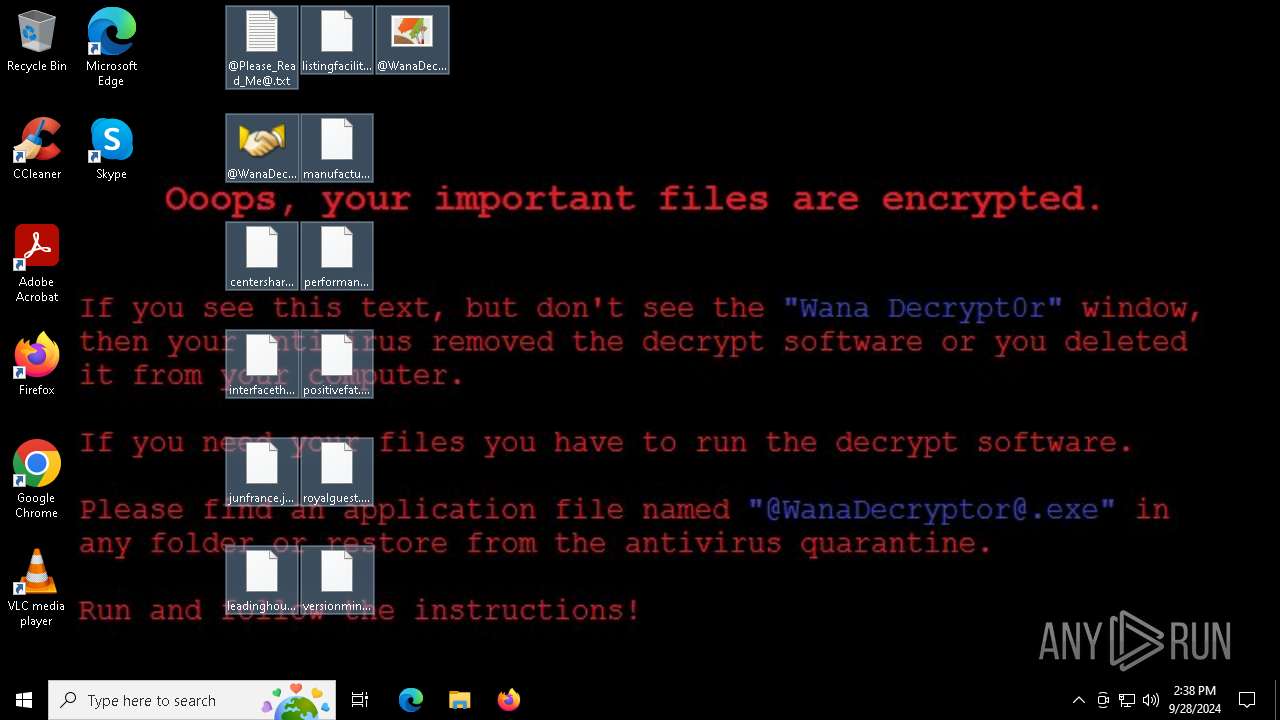
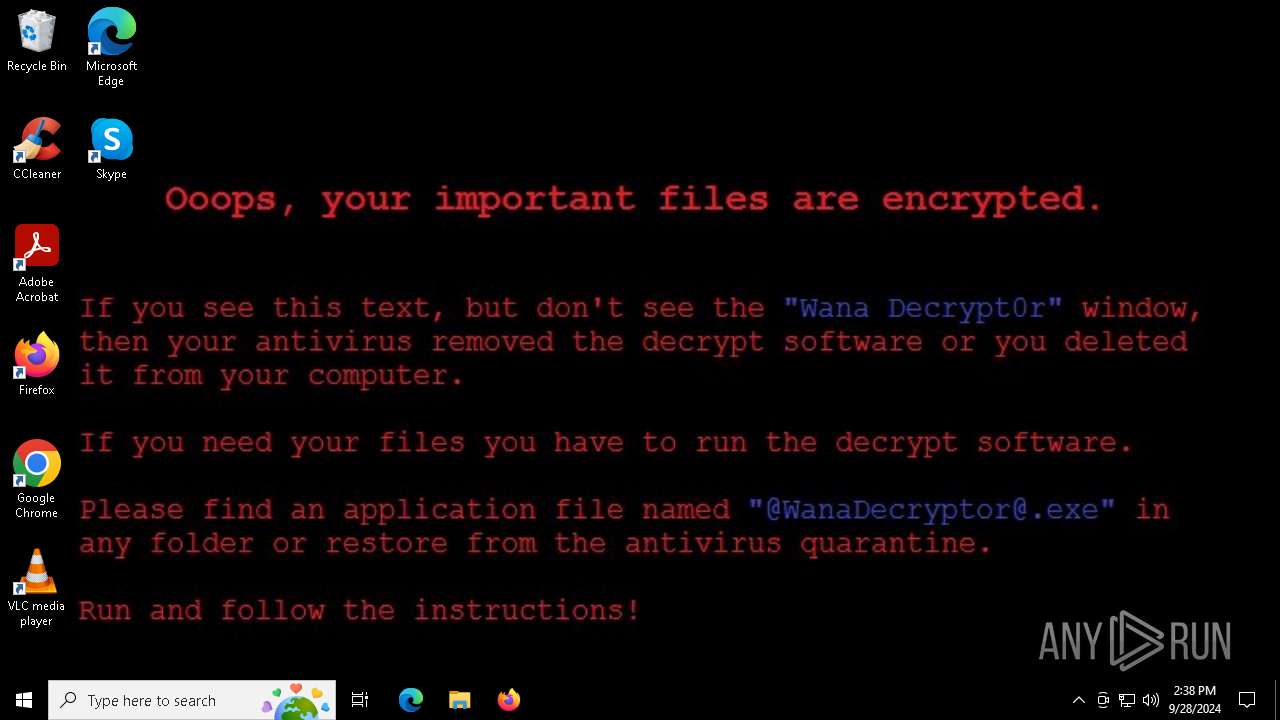
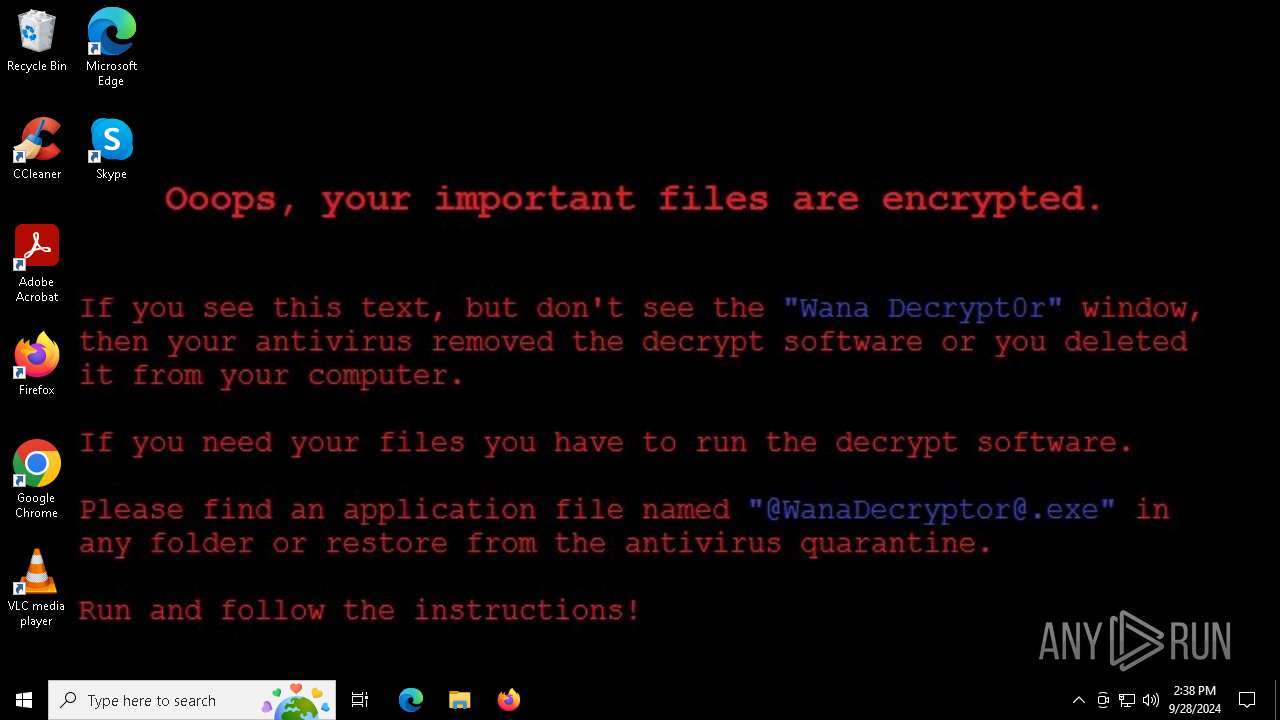
| Verdict: | Malicious activity |
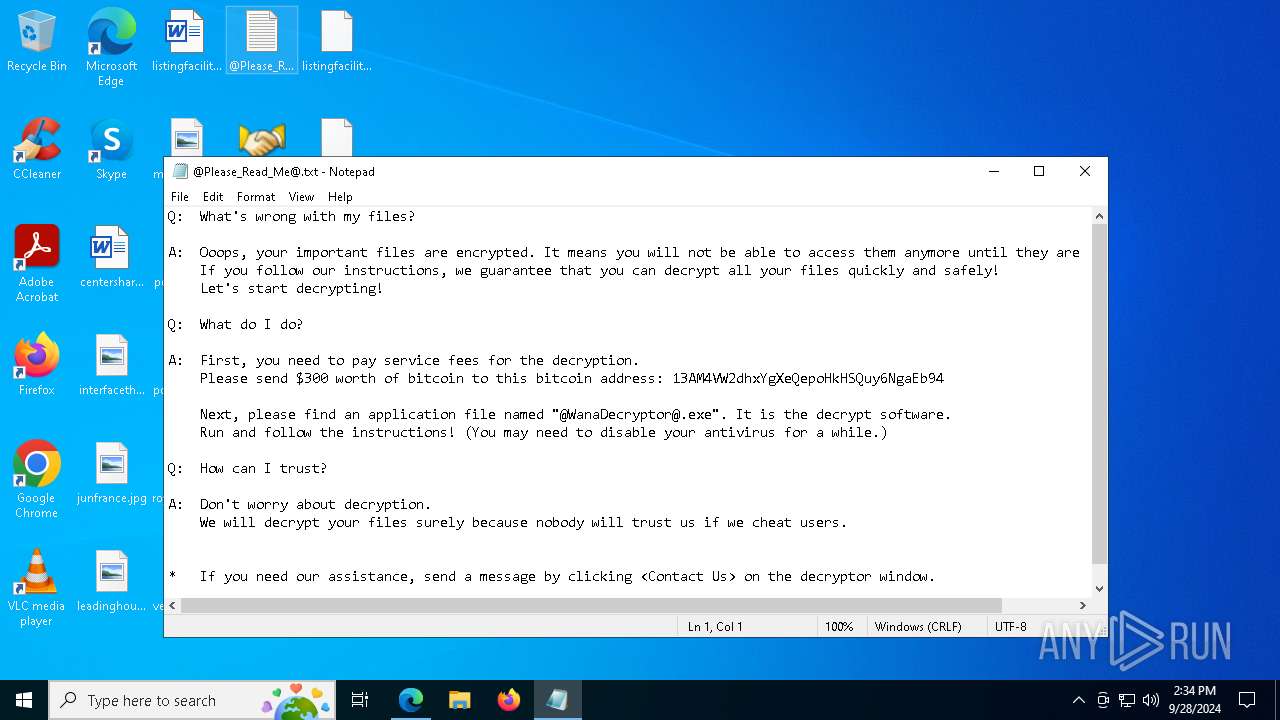
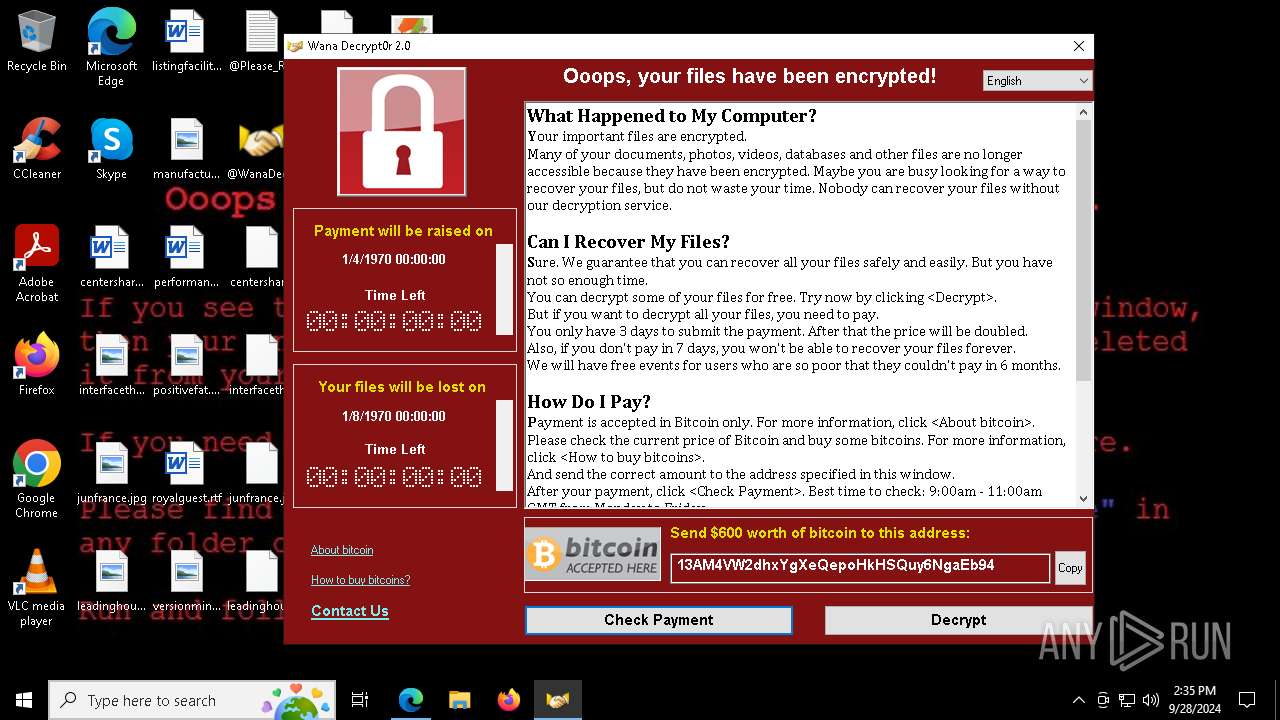
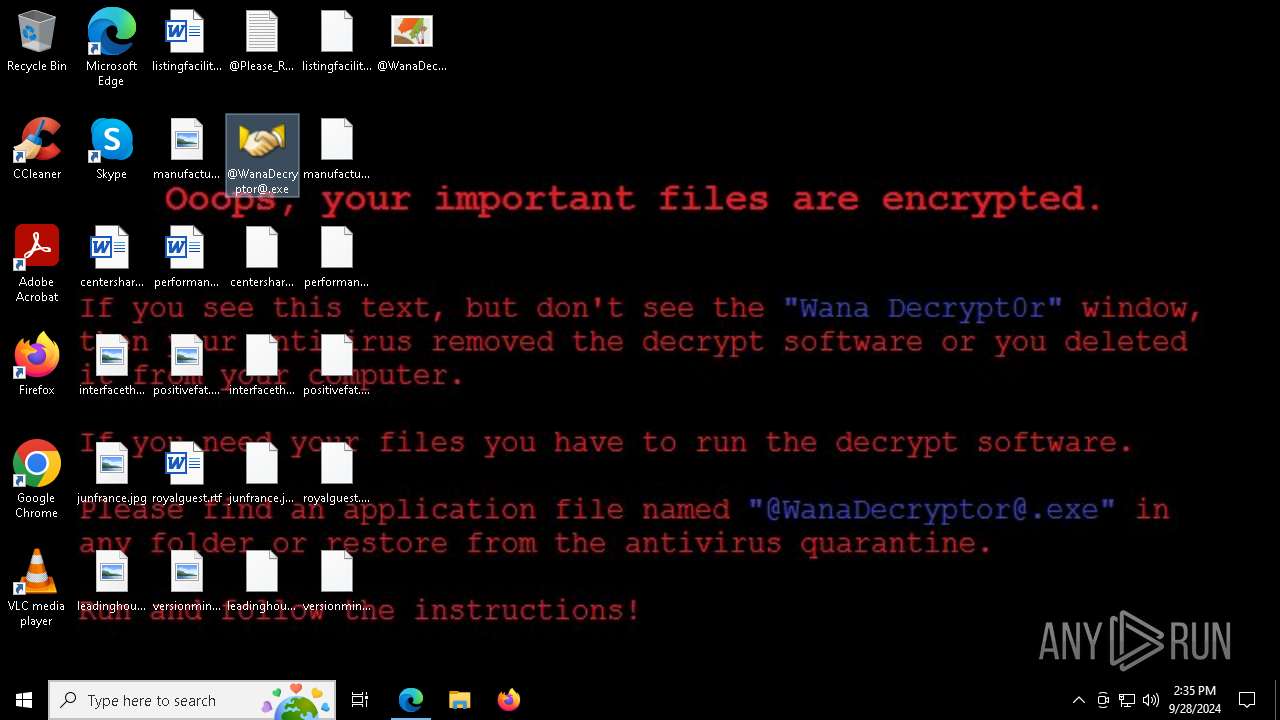
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
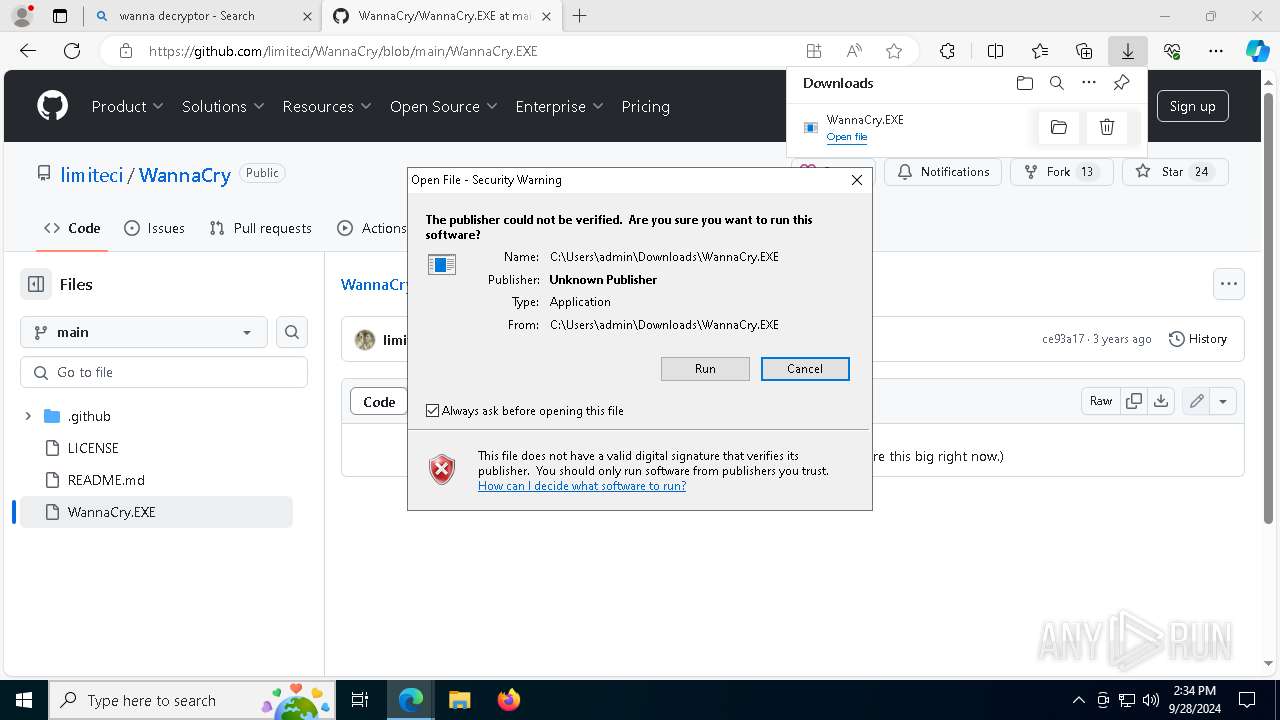
| Analysis date: | September 28, 2024, 14:34:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8FE41F89C88822FFD73579BD1E86CDD1 |
| SHA1: | B1B0CDC01A80A7B461CBD1EDC409A39027019BAC |
| SHA256: | 7F4E2B7890A155E7892BAA48CD51E184EC379970B26AEF754CBD4F1CBEB98FAA |
| SSDEEP: | 6:2OLsBBGoNfohIDs45h+DEdoA3zgk0l+hsMTih4noRTQ8PB3w:23GjhIDsbD8m+l4kuJA |
MALICIOUS
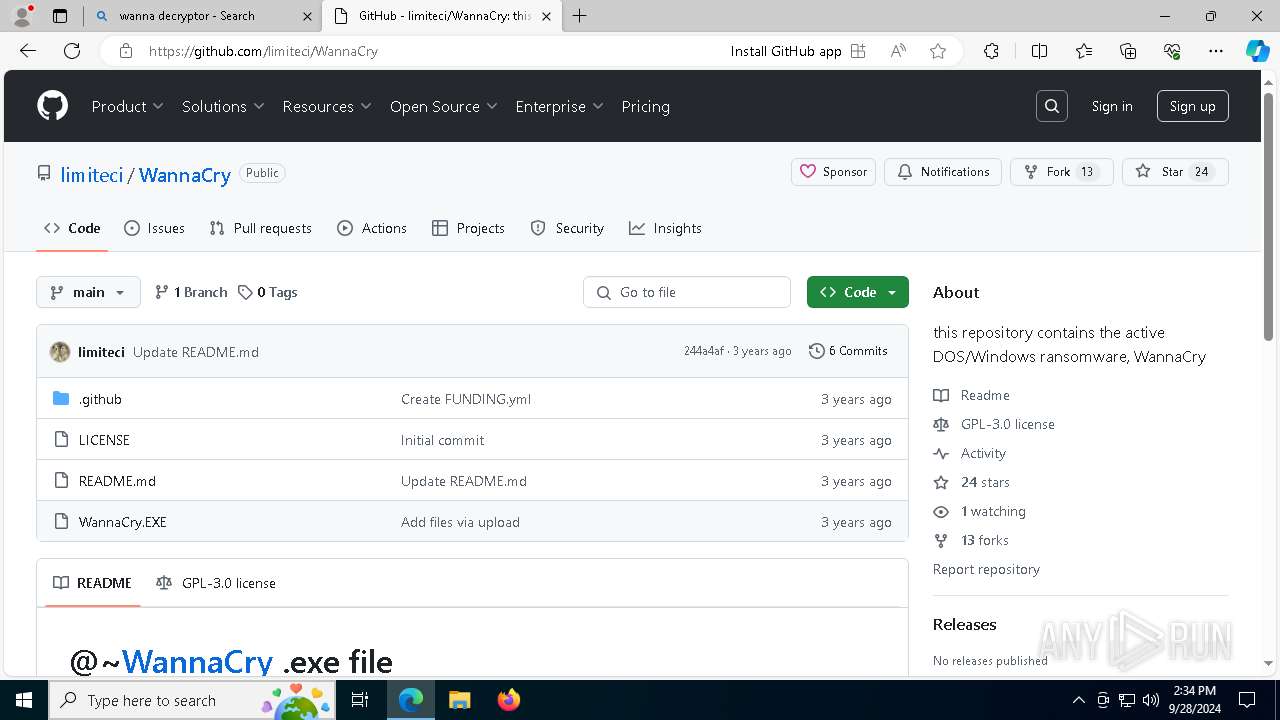
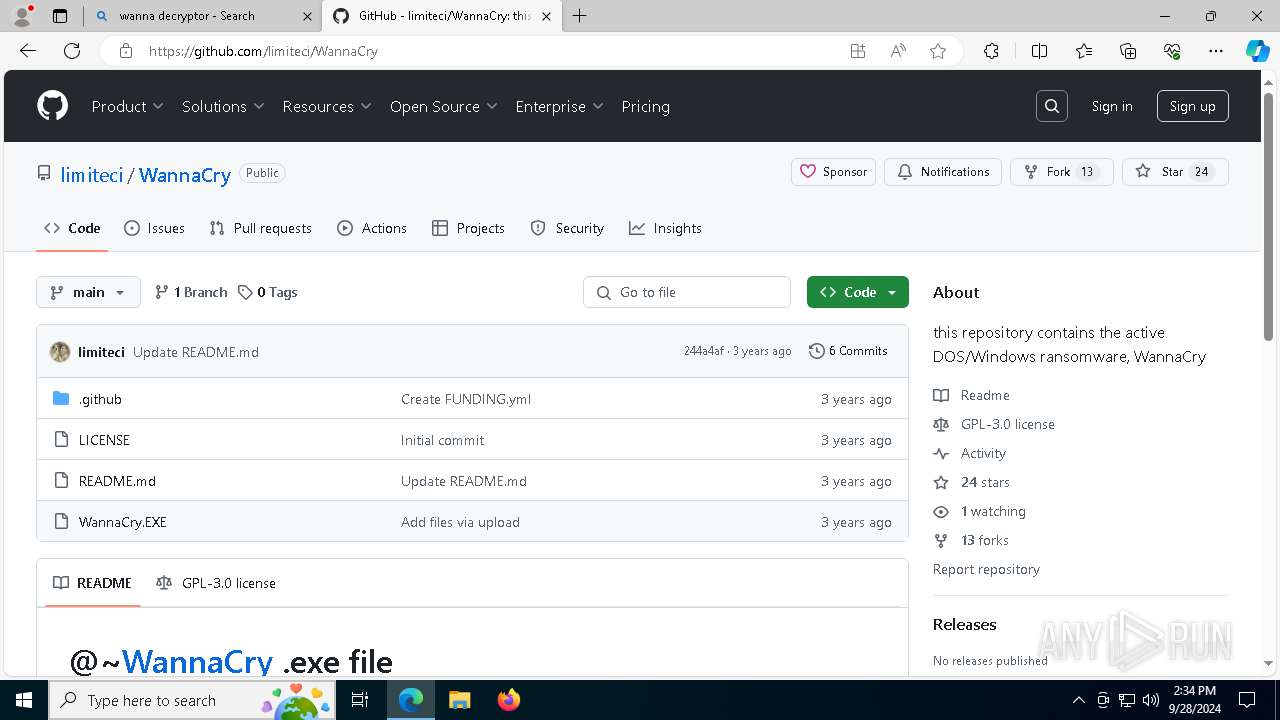
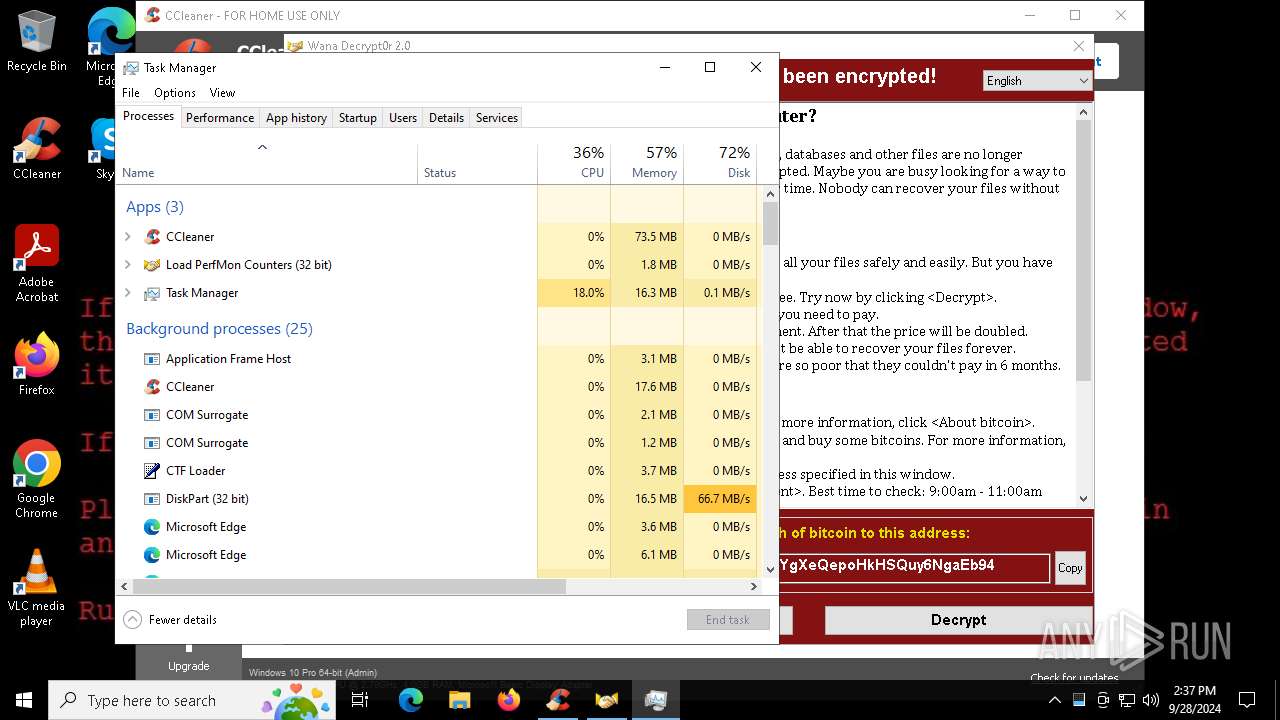
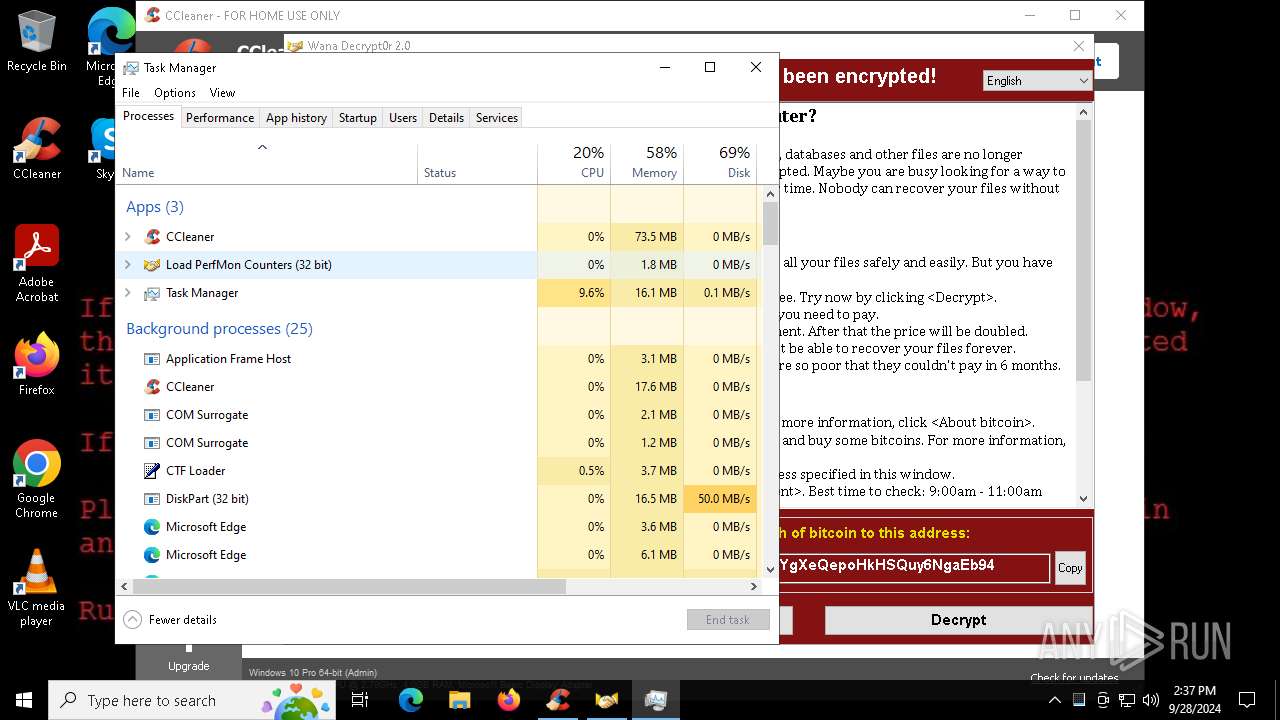
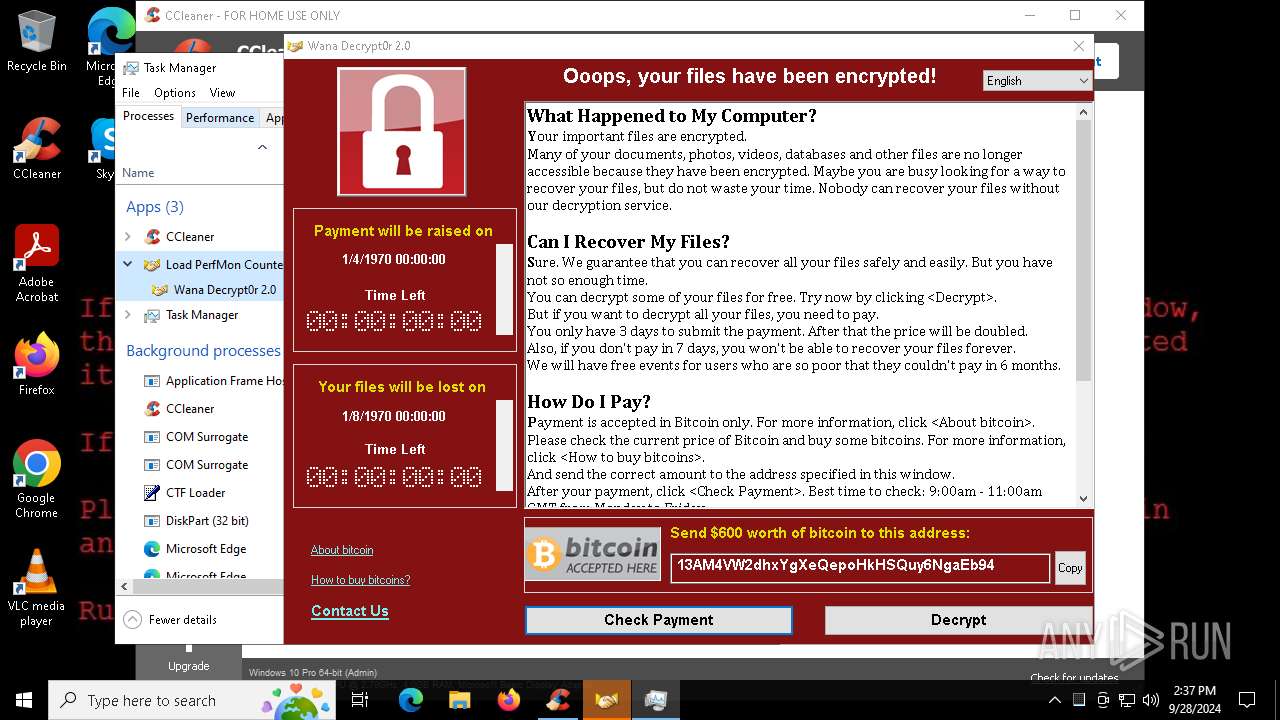
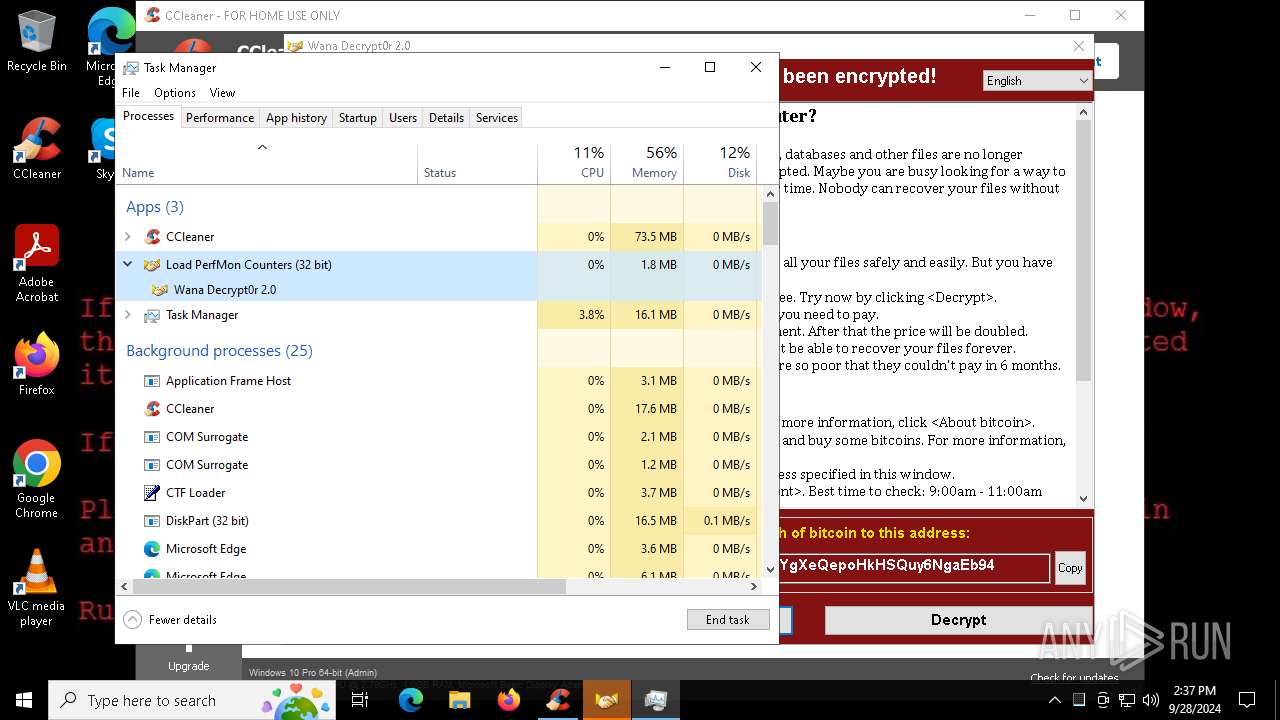
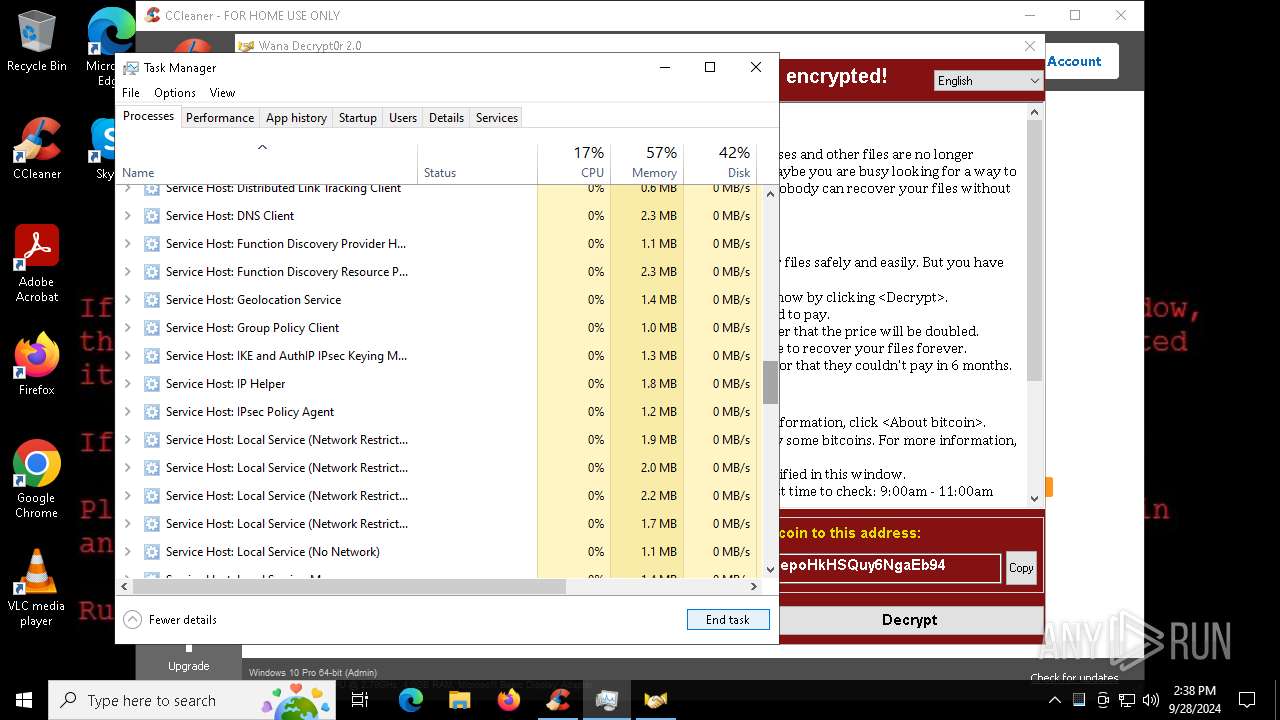
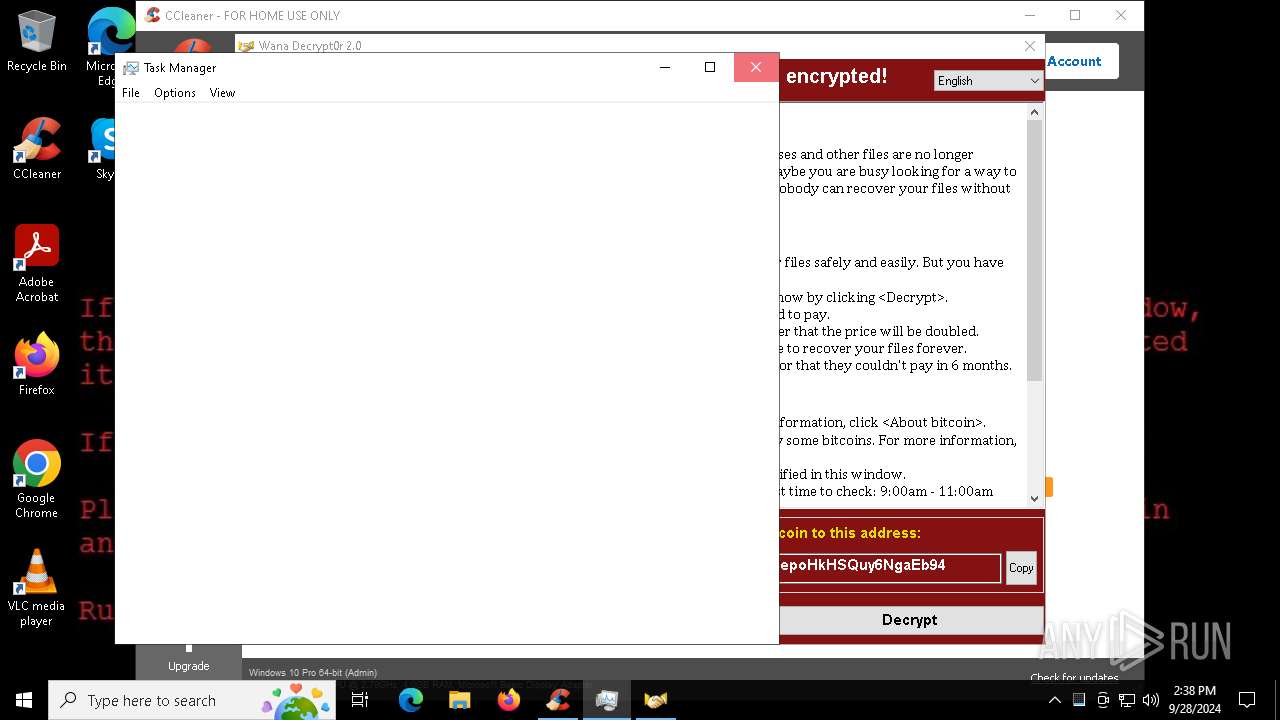
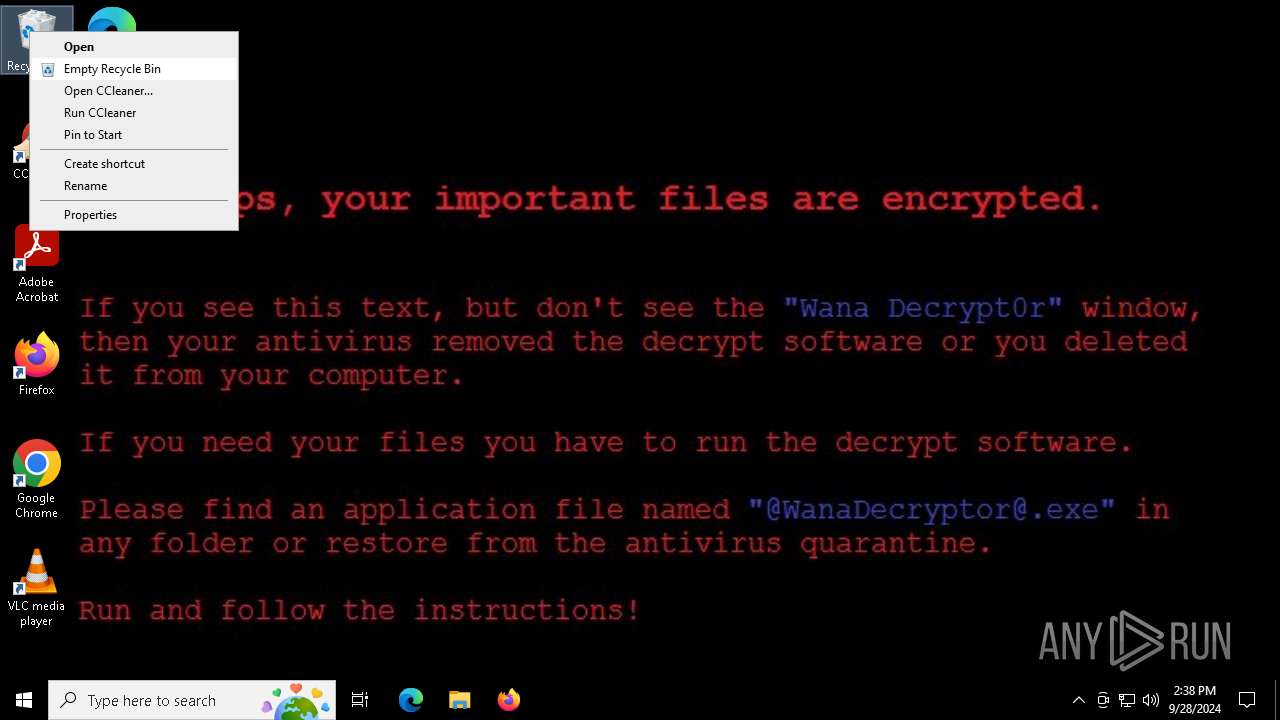
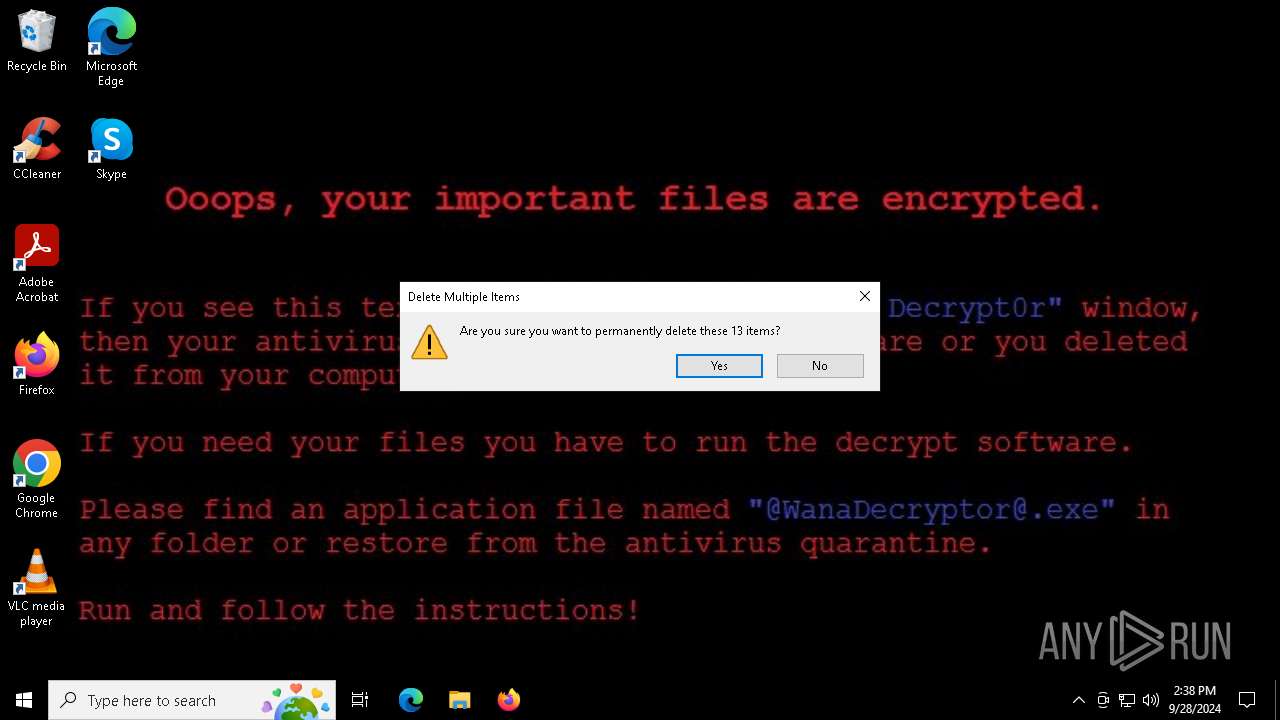
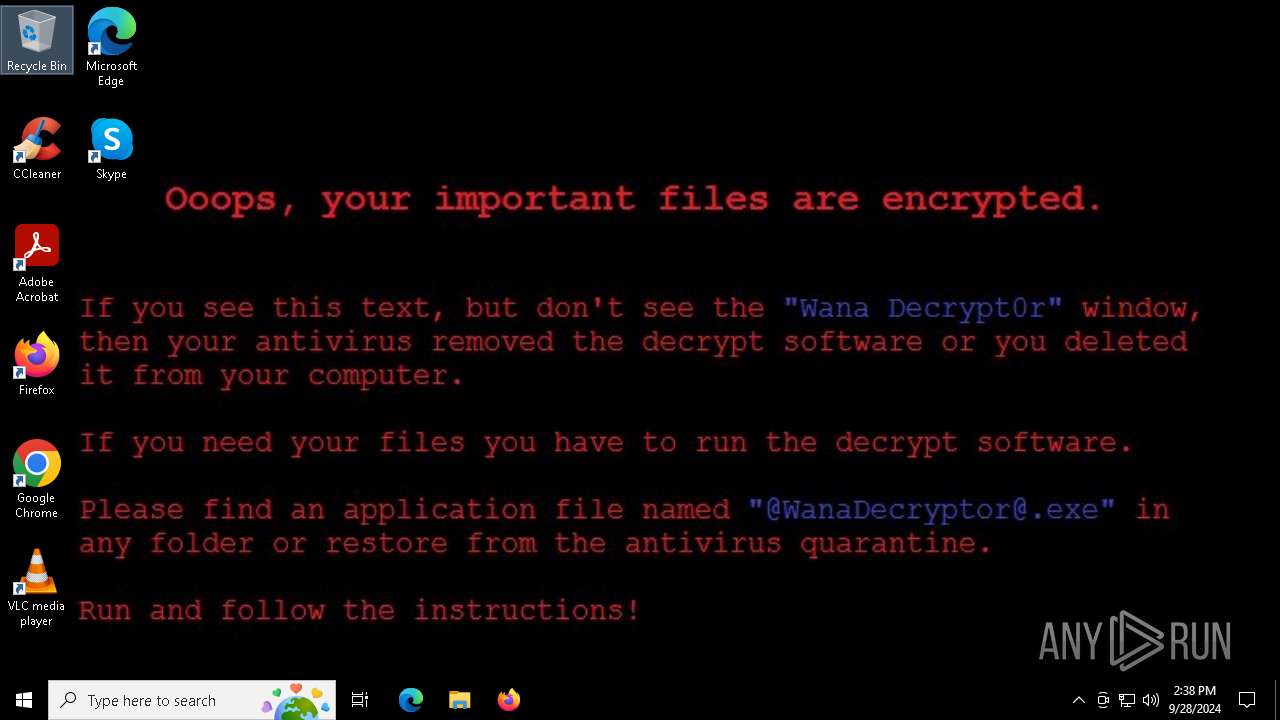
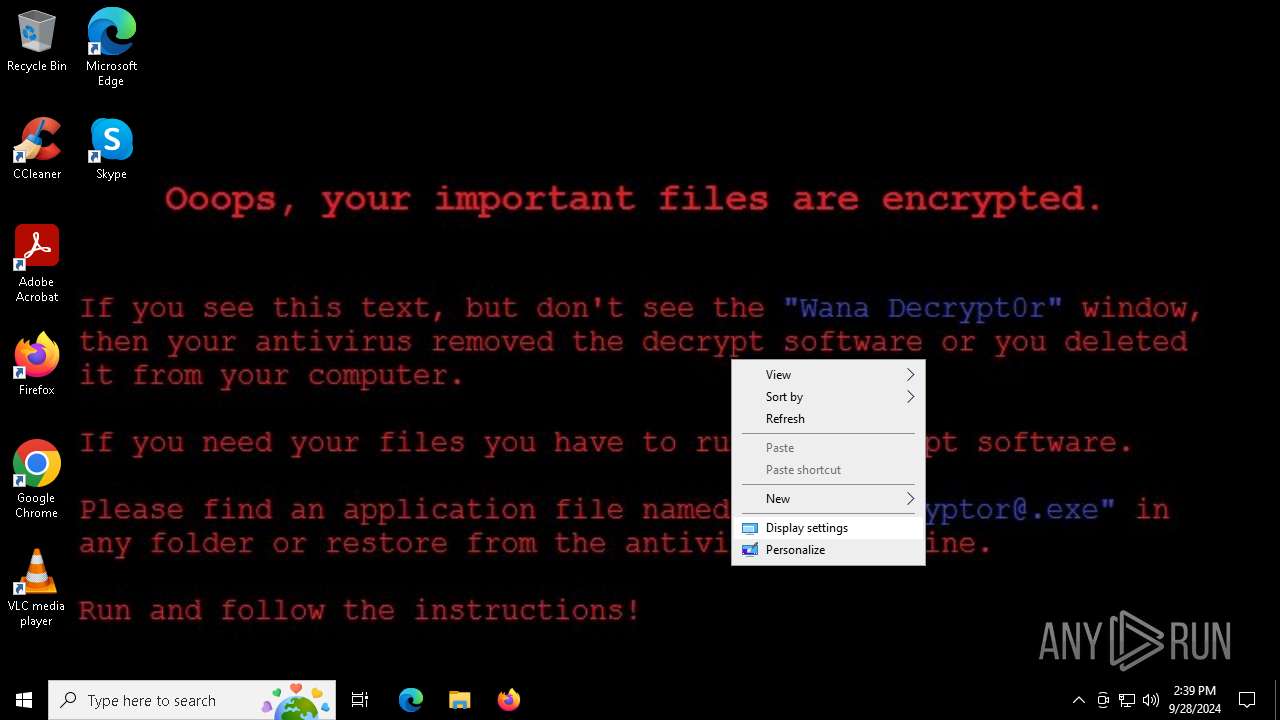
WANNACRY has been detected (YARA)
- WannaCry.EXE (PID: 7608)
Wannacry exe files
- @WanaDecryptor@.exe (PID: 8064)
- @WanaDecryptor@.exe (PID: 8016)
- cmd.exe (PID: 7192)
- @WanaDecryptor@.exe (PID: 3808)
- @WanaDecryptor@.exe (PID: 3880)
- @WanaDecryptor@.exe (PID: 7408)
- @WanaDecryptor@.exe (PID: 8112)
- @WanaDecryptor@.exe (PID: 1884)
WannaCry Ransomware is detected
- WannaCry.EXE (PID: 7608)
- cmd.exe (PID: 7192)
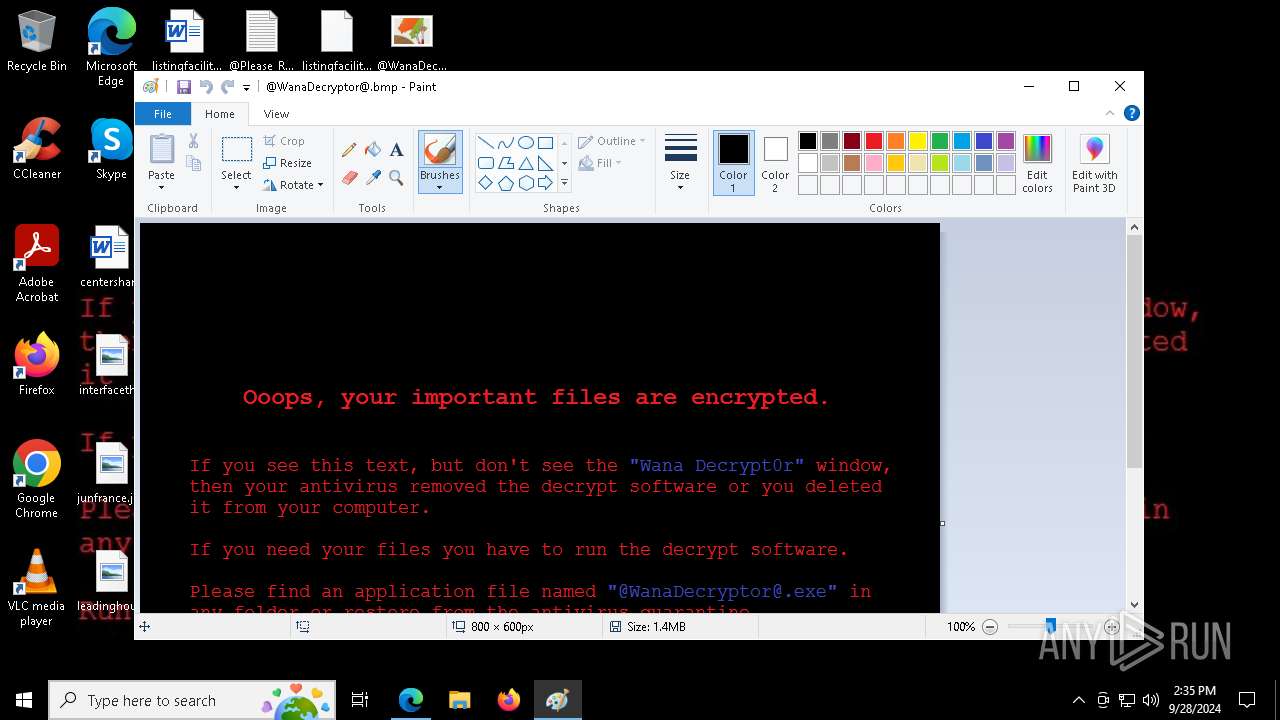
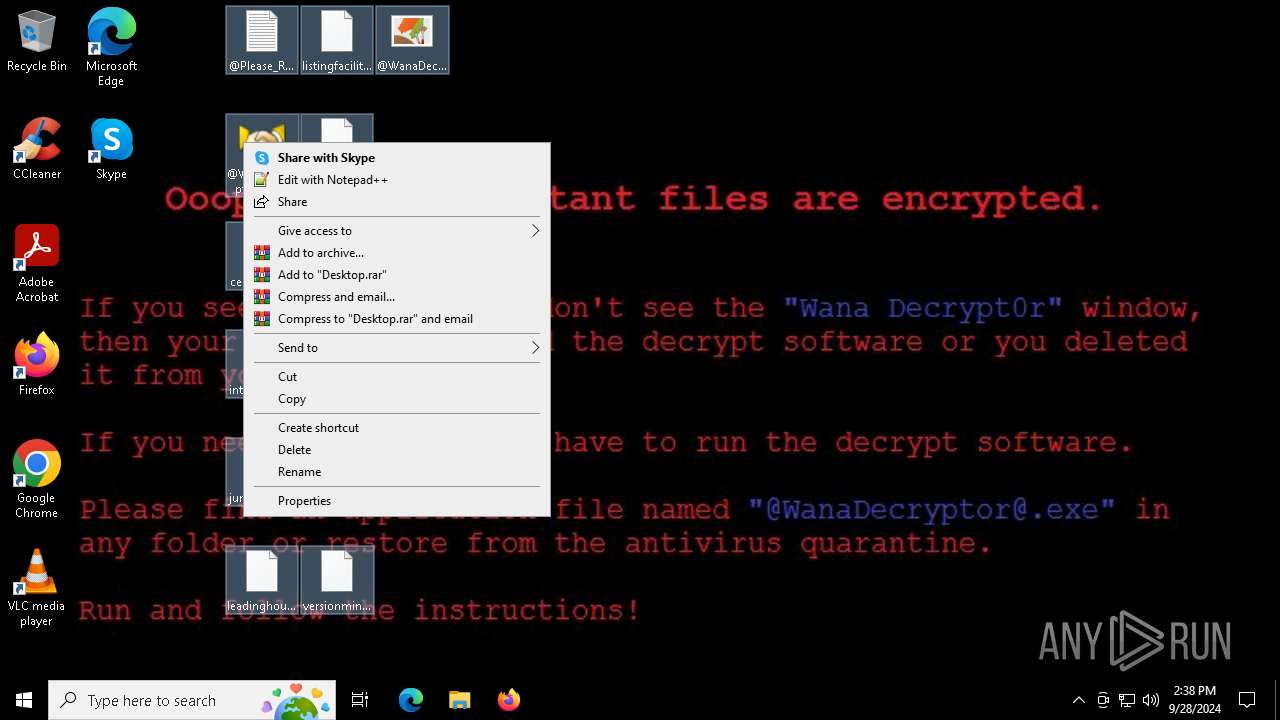
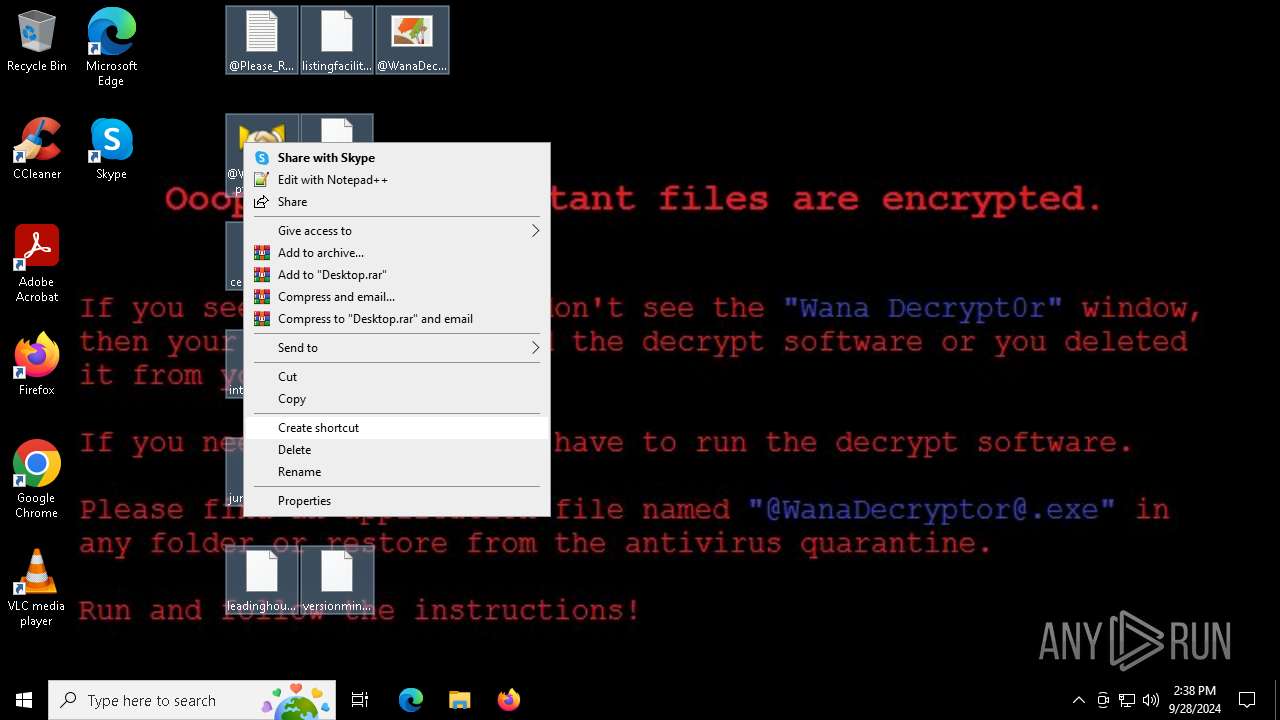
Drops known malicious image
- WannaCry.EXE (PID: 7608)
SUSPICIOUS
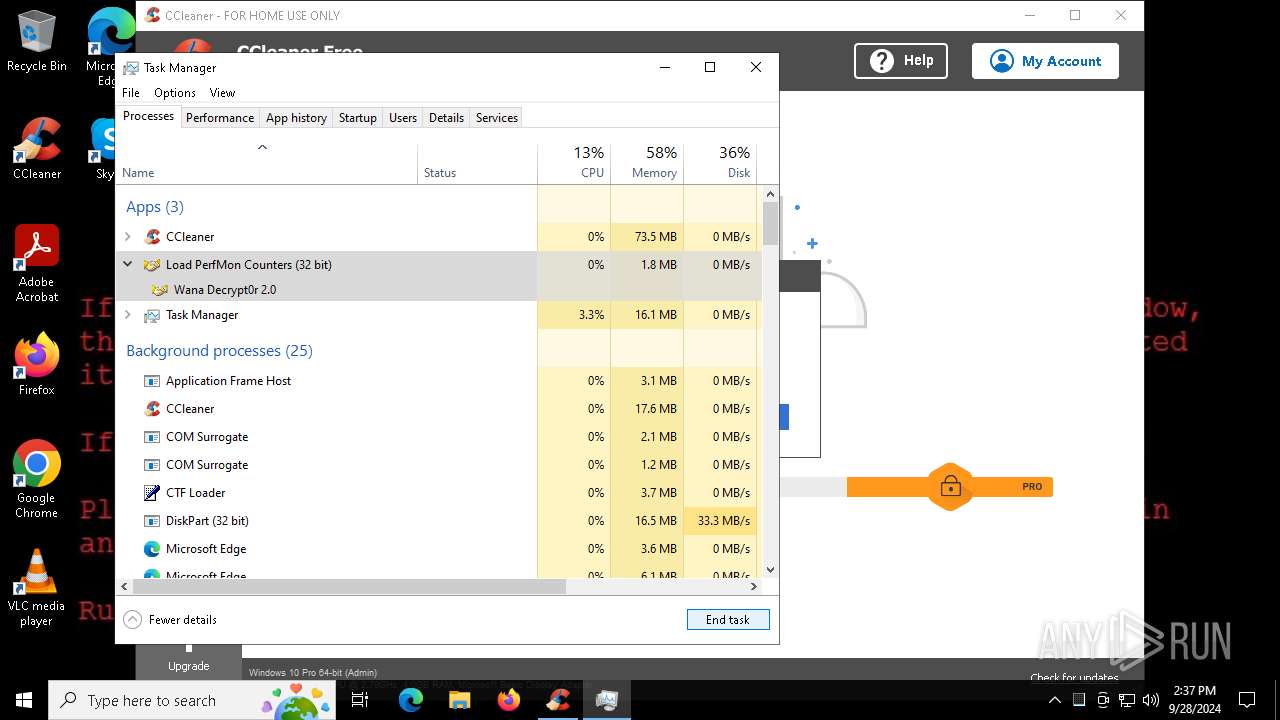
Process drops legitimate windows executable
- msedge.exe (PID: 5960)
- msedge.exe (PID: 2144)
- WannaCry.EXE (PID: 7608)
Executable content was dropped or overwritten
- WannaCry.EXE (PID: 7608)
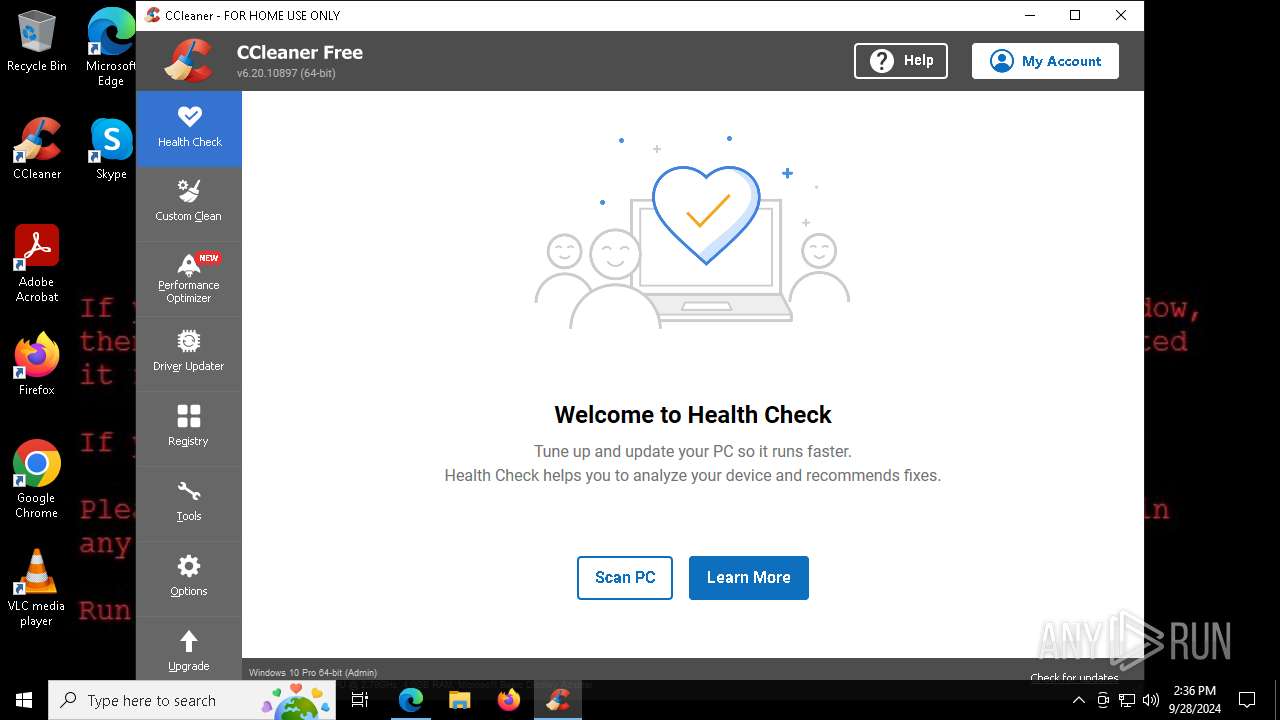
- CCleaner64.exe (PID: 8032)
- CCleaner64.exe (PID: 7552)
Uses ICACLS.EXE to modify access control lists
- WannaCry.EXE (PID: 7608)
Executing commands from a ".bat" file
- WannaCry.EXE (PID: 7608)
Starts CMD.EXE for commands execution
- WannaCry.EXE (PID: 7608)
The process executes VB scripts
- cmd.exe (PID: 6716)
Uses ATTRIB.EXE to modify file attributes
- WannaCry.EXE (PID: 7608)
Starts a Microsoft application from unusual location
- @WanaDecryptor@.exe (PID: 8064)
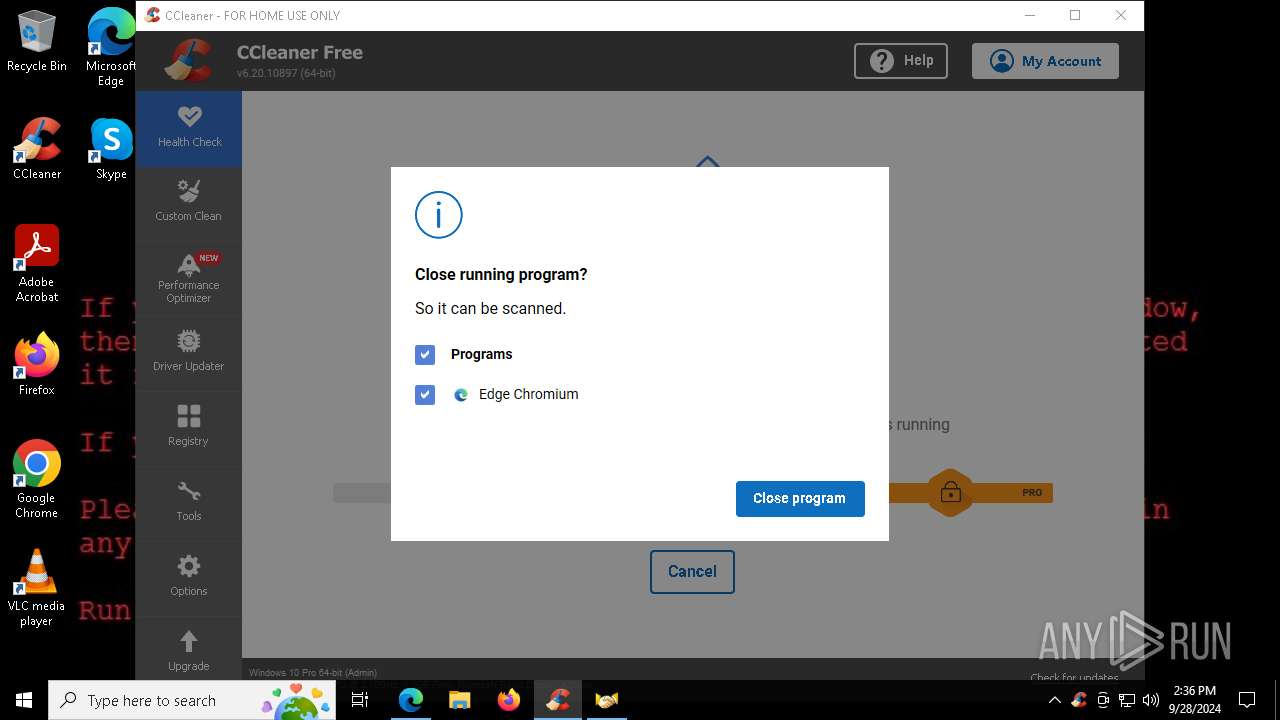
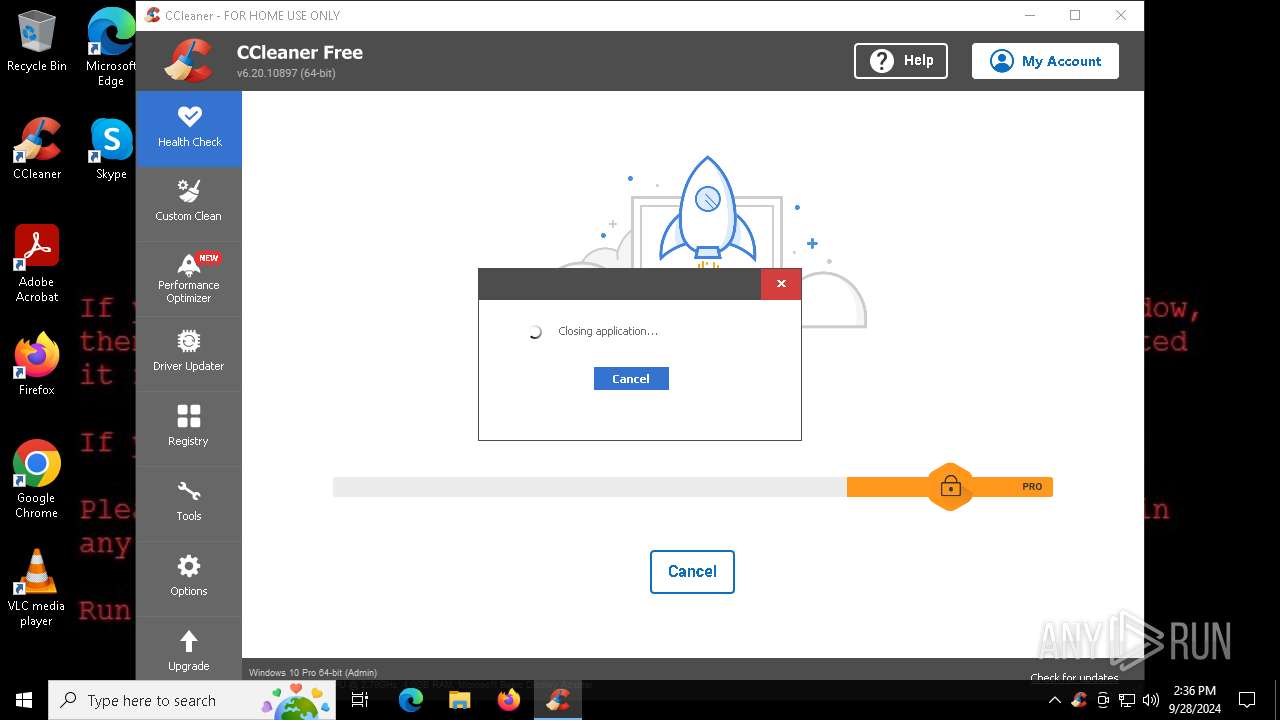
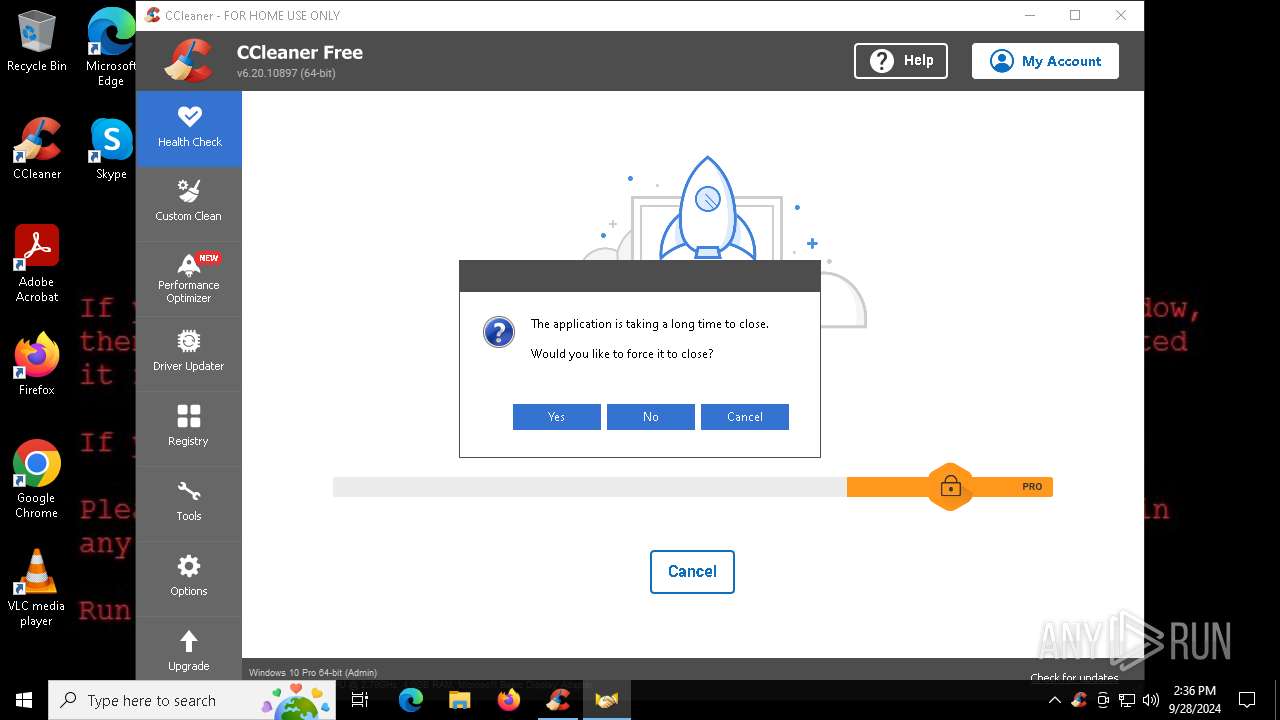
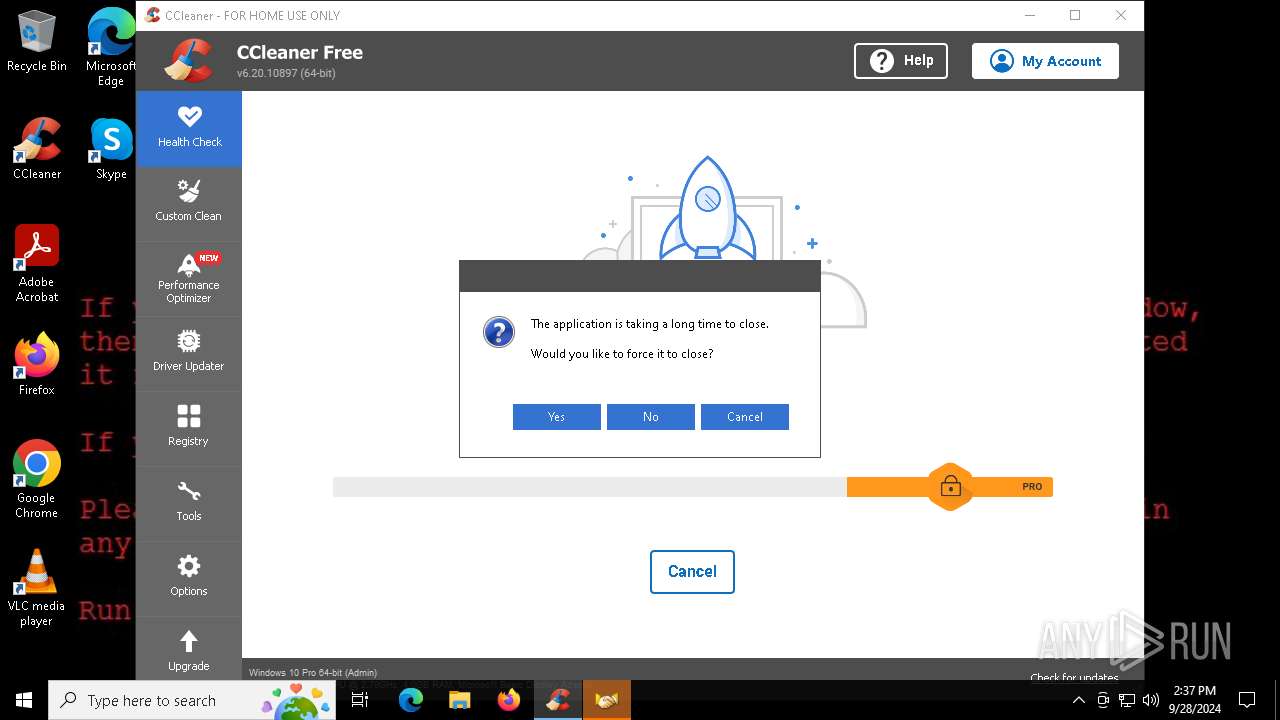
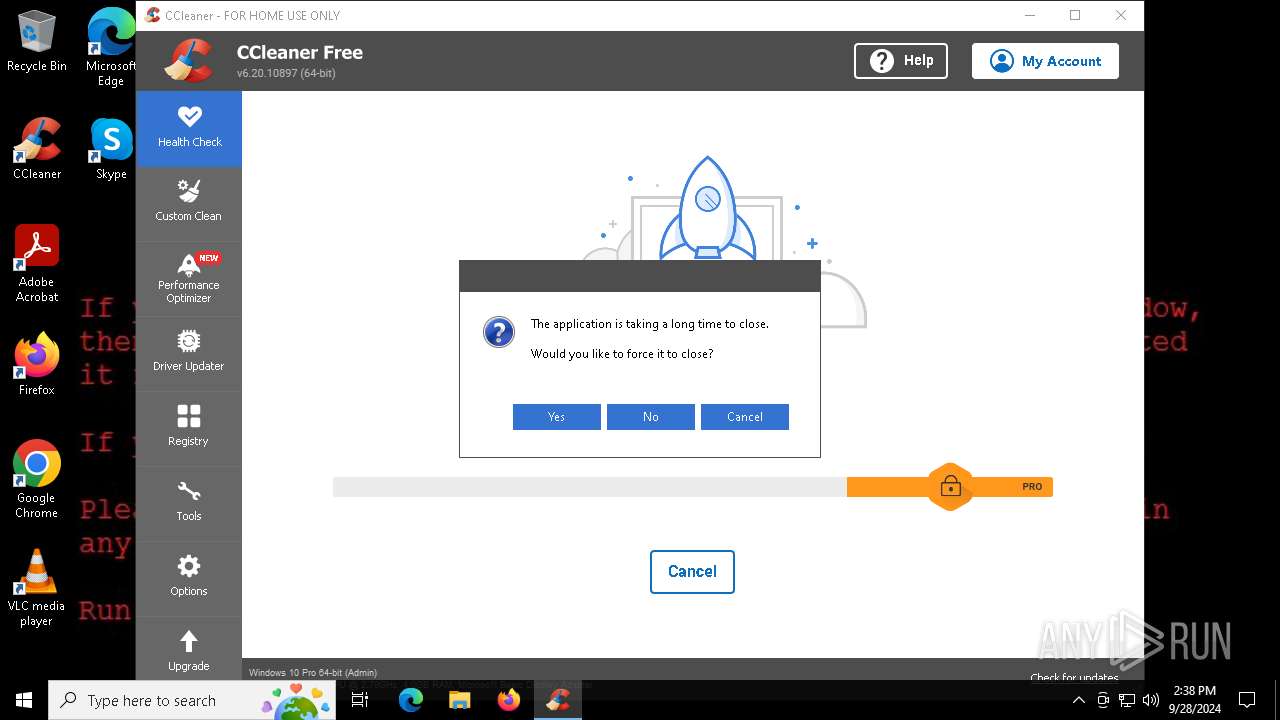
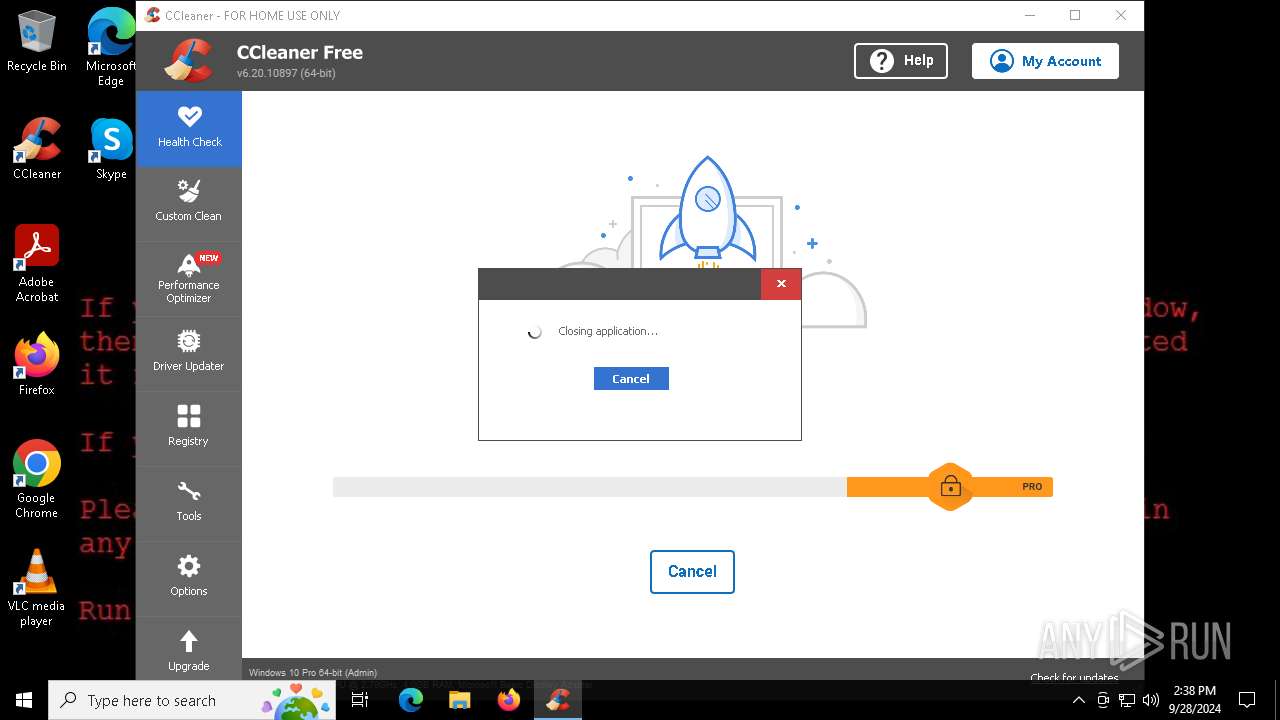
Application launched itself
- CCleaner64.exe (PID: 5084)
- CCleaner64.exe (PID: 8032)
Checks for external IP
- CCleaner64.exe (PID: 8032)
The executable file from the user directory is run by the CMD process
- @WanaDecryptor@.exe (PID: 3880)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5760)
Executes application which crashes
- CCleaner64.exe (PID: 8032)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 2144)
- msedge.exe (PID: 5960)
- msedge.exe (PID: 8008)
Application launched itself
- msedge.exe (PID: 5960)
- msedge.exe (PID: 7380)
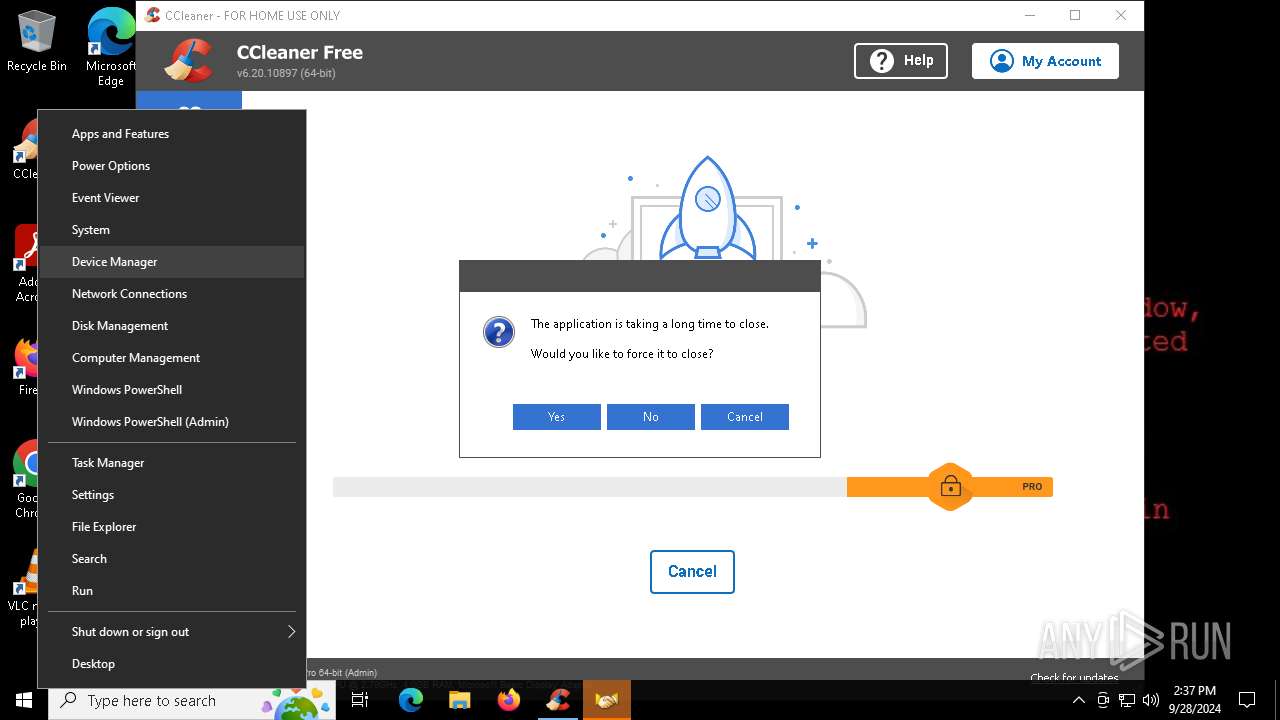
Manual execution by a user
- notepad.exe (PID: 4404)
- @WanaDecryptor@.exe (PID: 8064)
- mspaint.exe (PID: 7560)
- CCleaner64.exe (PID: 5084)
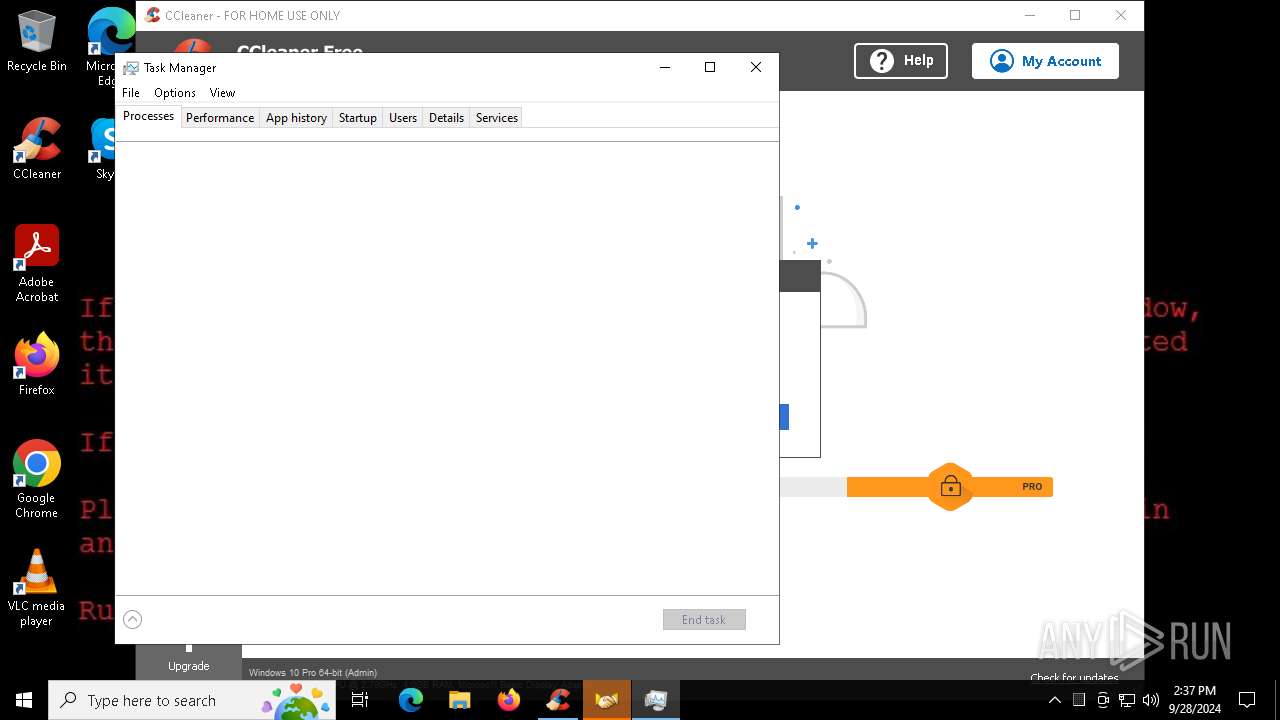
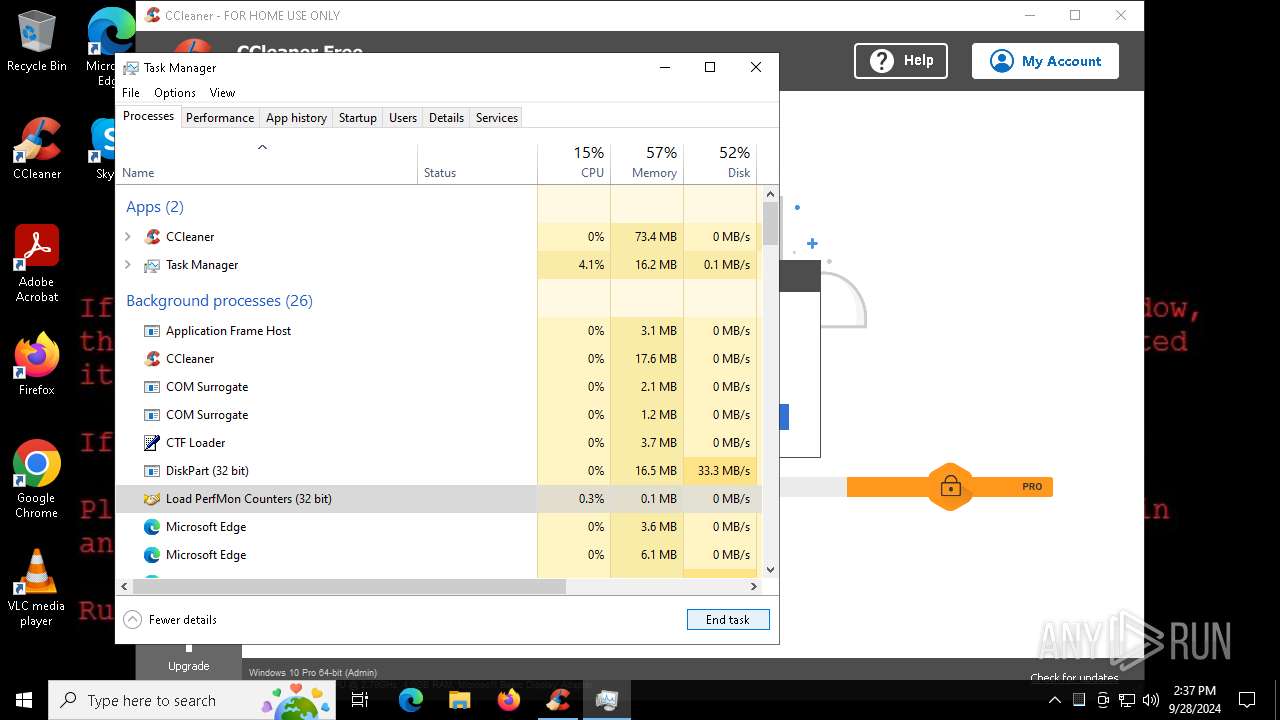
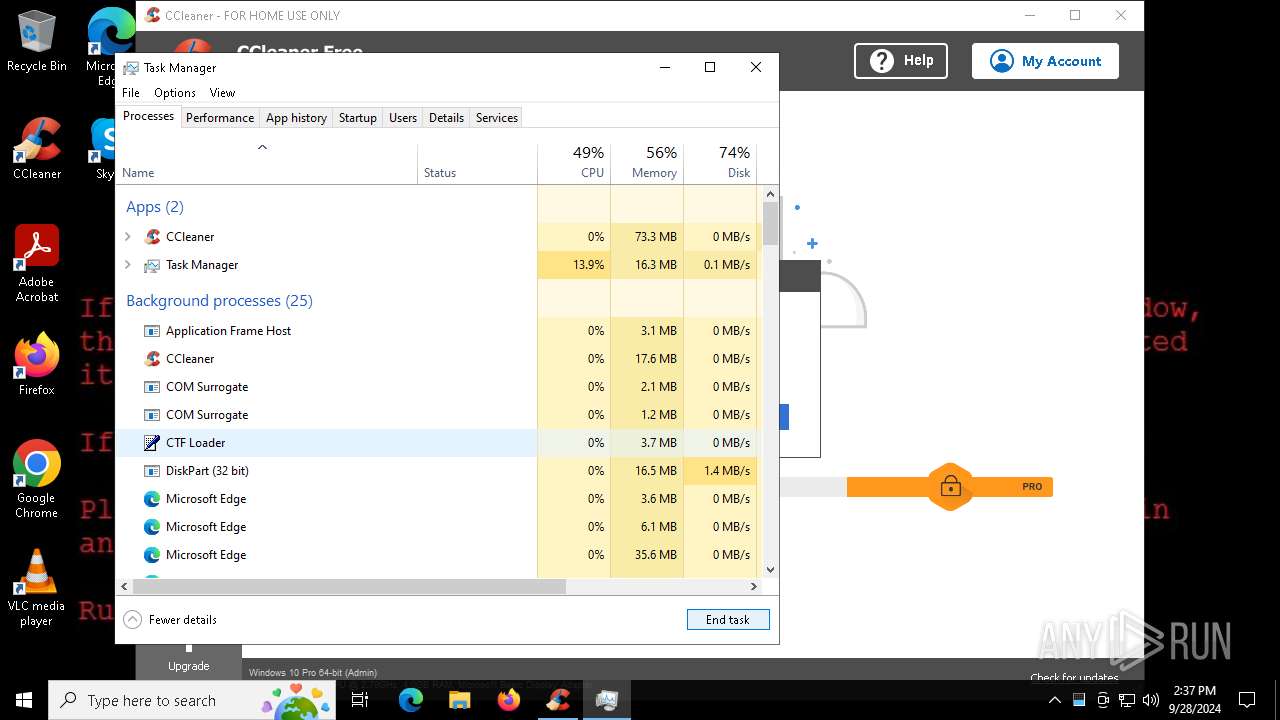
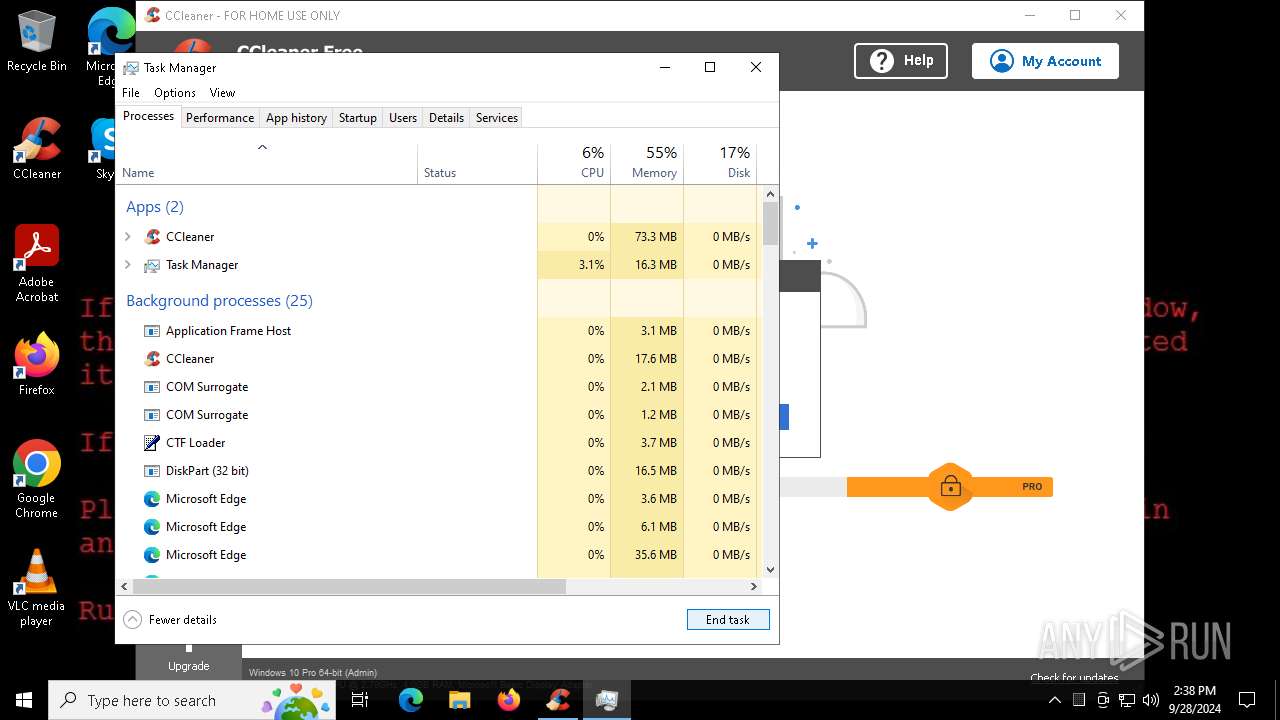
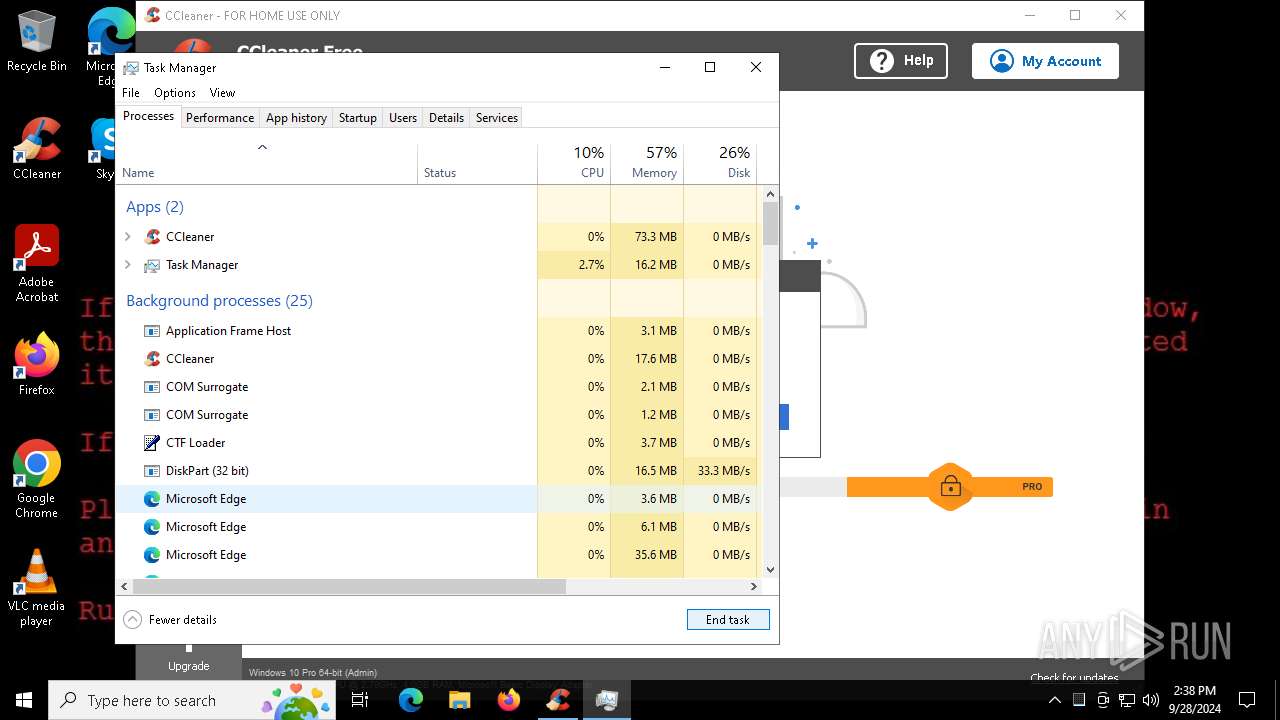
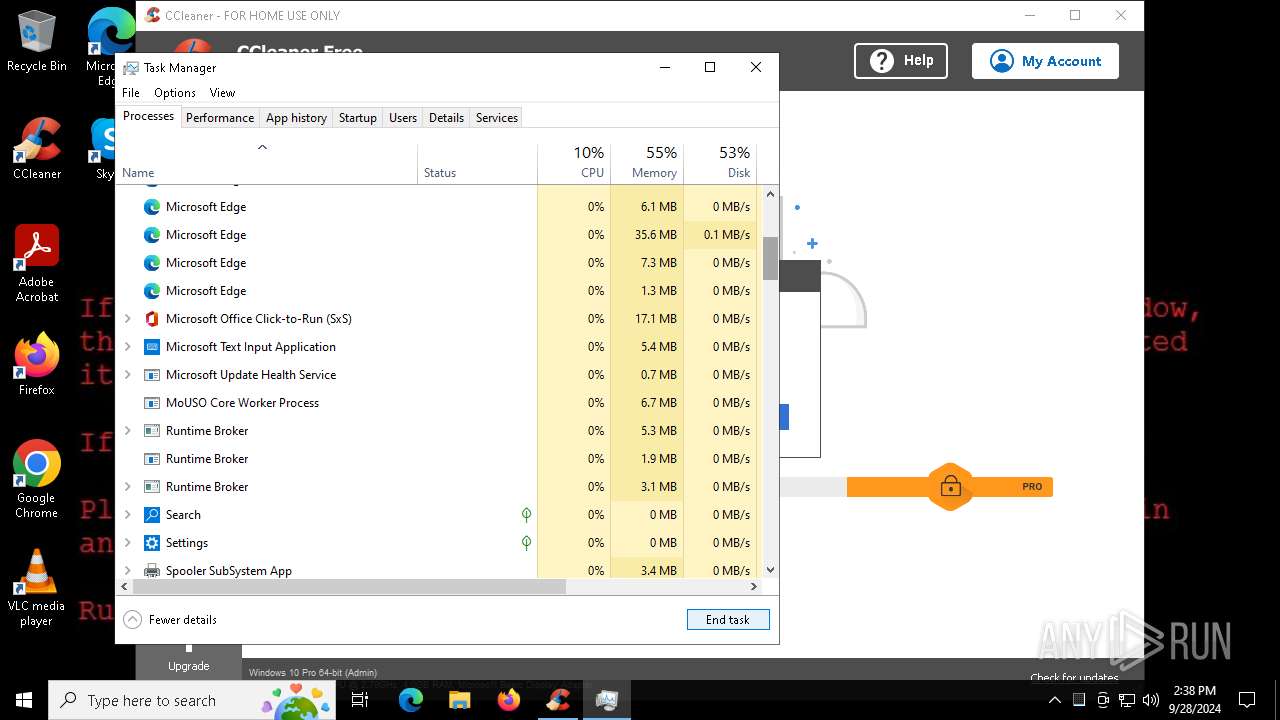
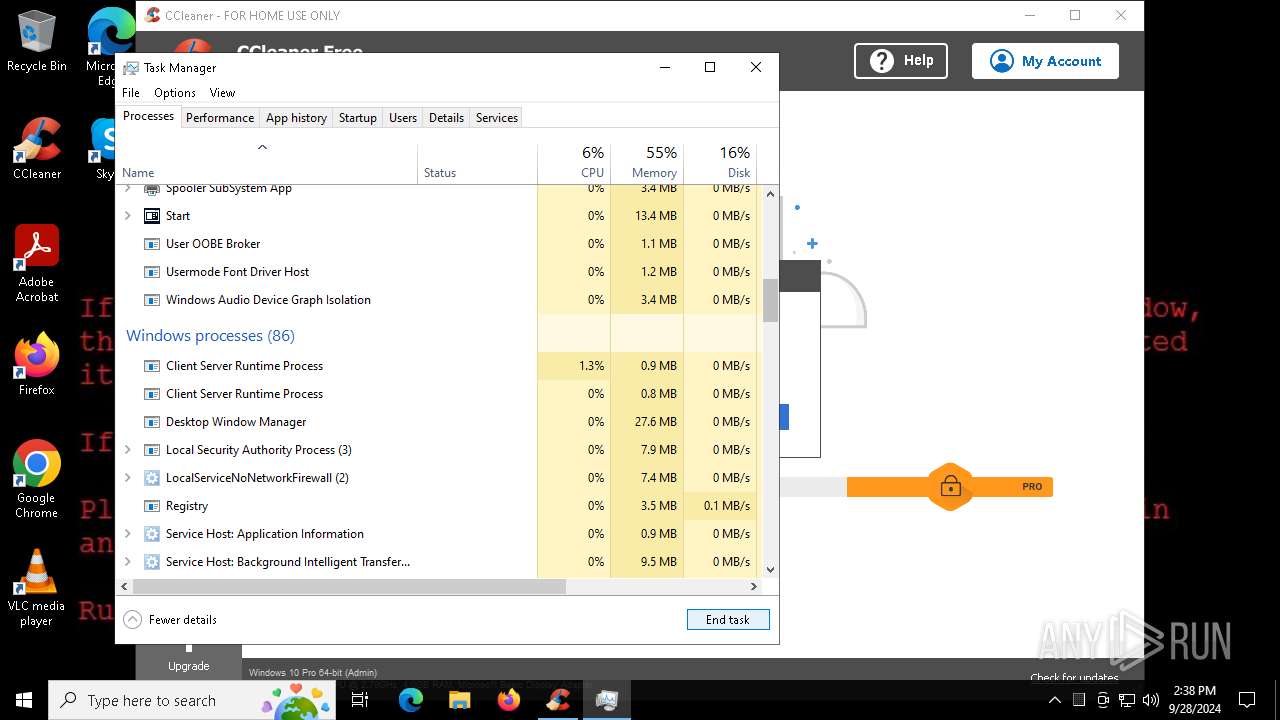
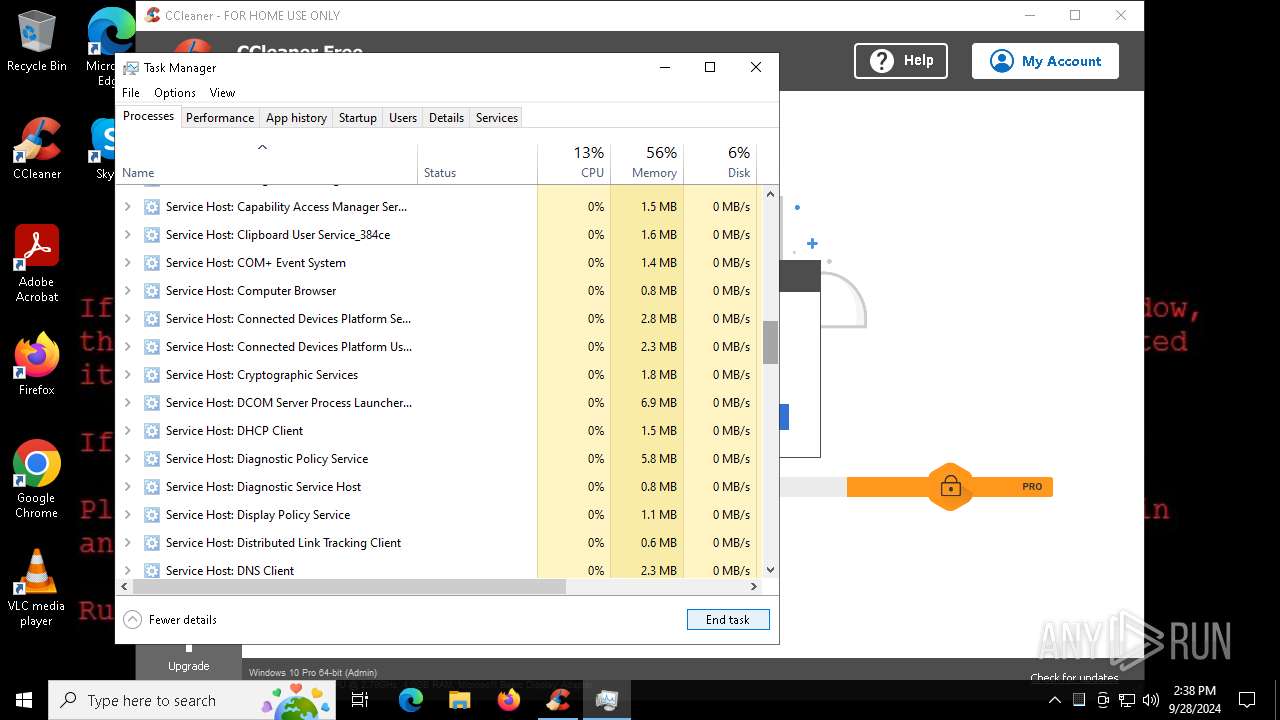
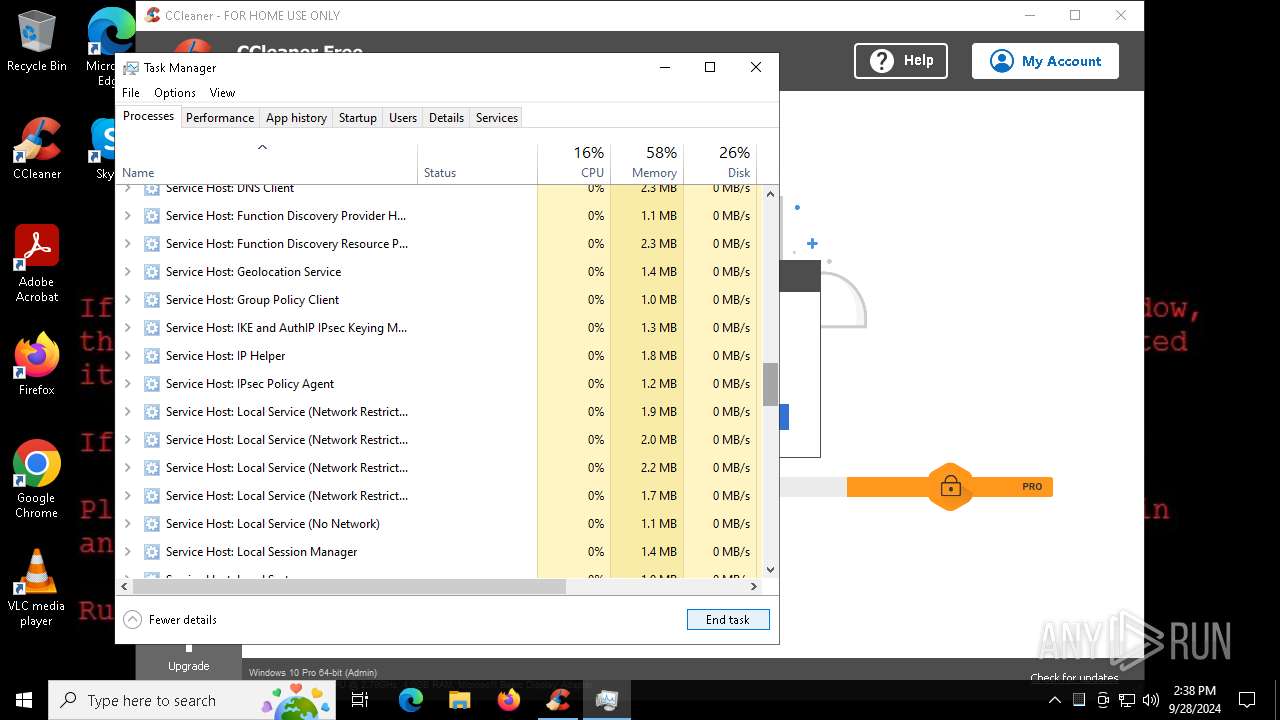
- Taskmgr.exe (PID: 6232)
- Taskmgr.exe (PID: 7384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
273
Monitored processes
122
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | taskdl.exe | C:\Users\admin\Downloads\taskdl.exe | — | WannaCry.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7752 --field-trial-handle=2324,i,1601618492230015595,9626679556289887724,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 652 | attrib +h . | C:\Windows\SysWOW64\attrib.exe | — | WannaCry.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4572 --field-trial-handle=2324,i,1601618492230015595,9626679556289887724,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4432 --field-trial-handle=2024,i,17723752580240824465,10954734953633600806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4064 --field-trial-handle=2324,i,1601618492230015595,9626679556289887724,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1692 | taskdl.exe | C:\Users\admin\Downloads\taskdl.exe | — | WannaCry.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | @WanaDecryptor@.exe | C:\Users\admin\Downloads\@WanaDecryptor@.exe | WannaCry.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2732 --field-trial-handle=2324,i,1601618492230015595,9626679556289887724,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5072 --field-trial-handle=2024,i,17723752580240824465,10954734953633600806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
39 926
Read events
39 659
Write events
192
Delete events
75
Modification events
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7022BF25C5812F00 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CA2FC825C5812F00 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1704780 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F0CF5B7-3D35-46D9-8121-BB02ABD0D6A5} | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1704780 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2F96D1D9-A727-4644-B3BC-493A0191E4C2} | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1704780 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9297EB83-61C1-4BF6-A7AA-7CBBAB17DE12} | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1704780 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {461E54E9-86CE-4282-9F4E-E6077BA9063B} | |||
Executable files
31
Suspicious files
2 108
Text files
762
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF3f6455.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF3f6464.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF3f6464.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF3f64b2.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF3f64c2.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF3f64c2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
176
DNS requests
144
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6364 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7948 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6364 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
1244 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728082871&P2=404&P3=2&P4=ZeL17moRUfGt6nYahnz9siISdD3W4sIX%2fM67TCx%2f5ScHtMOw5fOvDY%2fPdCmAzlGrCr4QPM4ngo9V3BmBQr0t%2fQ%3d%3d | unknown | — | — | whitelisted |
1244 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728082871&P2=404&P3=2&P4=ZeL17moRUfGt6nYahnz9siISdD3W4sIX%2fM67TCx%2f5ScHtMOw5fOvDY%2fPdCmAzlGrCr4QPM4ngo9V3BmBQr0t%2fQ%3d%3d | unknown | — | — | whitelisted |
1244 | svchost.exe | HEAD | 200 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728082871&P2=404&P3=2&P4=ZeL17moRUfGt6nYahnz9siISdD3W4sIX%2fM67TCx%2f5ScHtMOw5fOvDY%2fPdCmAzlGrCr4QPM4ngo9V3BmBQr0t%2fQ%3d%3d | unknown | — | — | whitelisted |
1244 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728082871&P2=404&P3=2&P4=ZeL17moRUfGt6nYahnz9siISdD3W4sIX%2fM67TCx%2f5ScHtMOw5fOvDY%2fPdCmAzlGrCr4QPM4ngo9V3BmBQr0t%2fQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4288 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2144 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5960 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2144 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2144 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
r.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2144 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2144 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
8032 | CCleaner64.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
Process | Message |
|---|---|
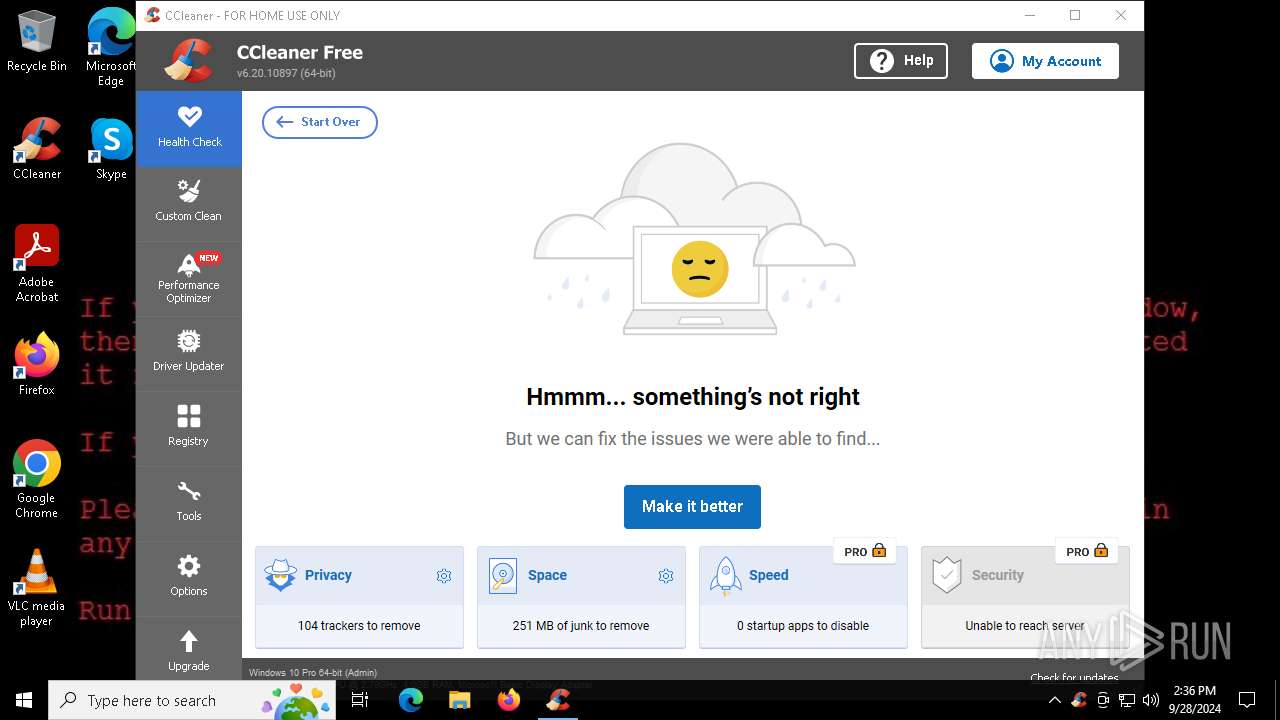
CCleaner64.exe | [2024-09-28 14:36:01.270] [error ] [settings ] [ 8032: 8092] [000000: 0] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner64.exe | [2024-09-28 14:36:01.332] [error ] [ini_access ] [ 8032: 8092] [000000: 0] Incorrect ini_accessor configuration! Fixing relative input path to avoid recursion. Input was: Setup
|
CCleaner64.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner64.exe | OnLanguage - en
|
CCleaner64.exe | [2024-09-28 14:36:02.535] [error ] [settings ] [ 8032: 4492] [D2EC45: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner64.exe | [2024-09-28 14:36:02.550] [error ] [Burger ] [ 8032: 4492] [904E07: 253] [23.2.1118.0] [BurgerReporter.cpp] [253] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner64.exe | [2024-09-28 14:36:02.550] [error ] [Burger ] [ 8032: 4492] [904E07: 253] [23.2.1118.0] [BurgerReporter.cpp] [253] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner64.exe | file:///tis/optimizer.tis(1131) : warning :'await' should be used only inside 'async' or 'event'
|
CCleaner64.exe | file:///tis/optimizer.tis(1288) : warning :'async' does not contain any 'await'
|
CCleaner64.exe | startCheckingLicense()
|