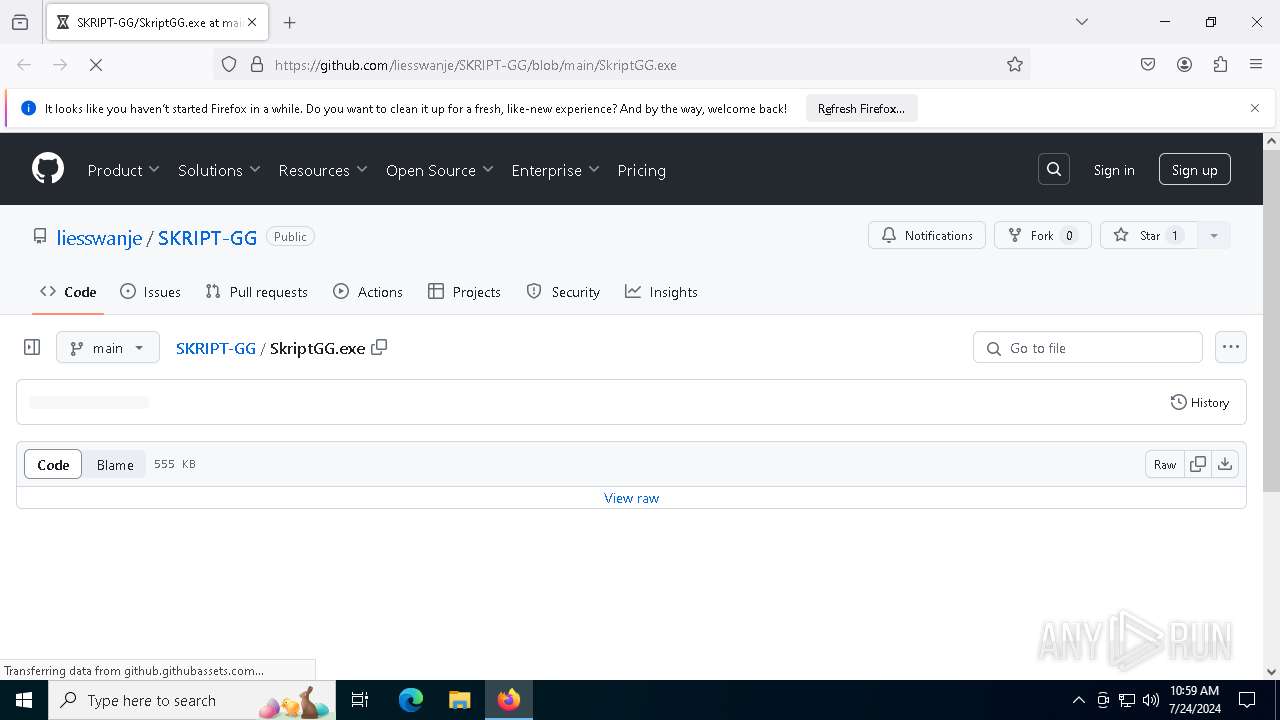
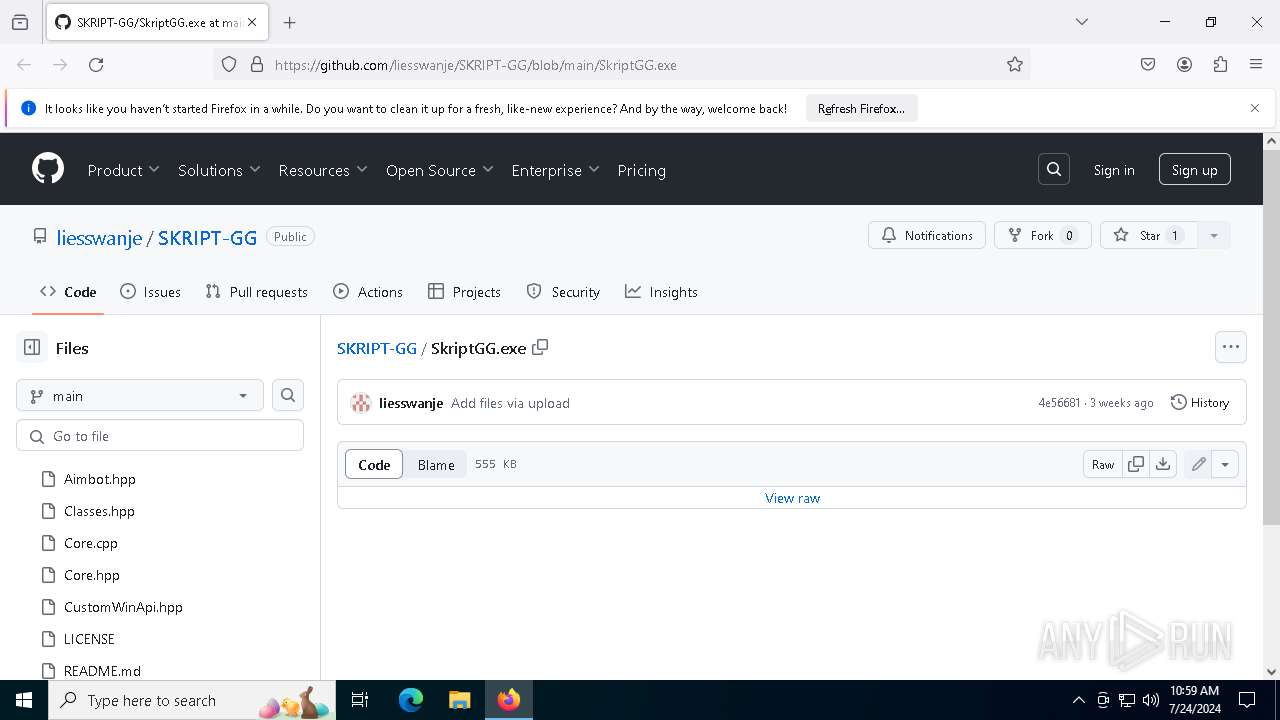
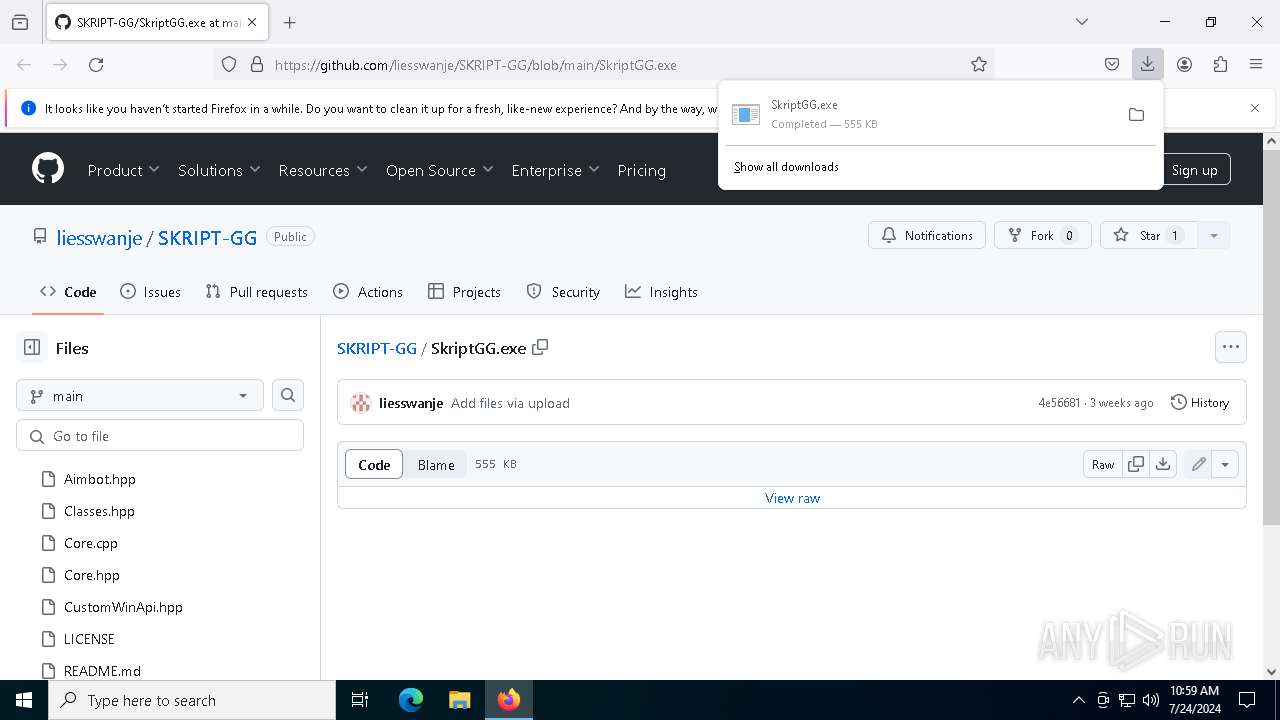
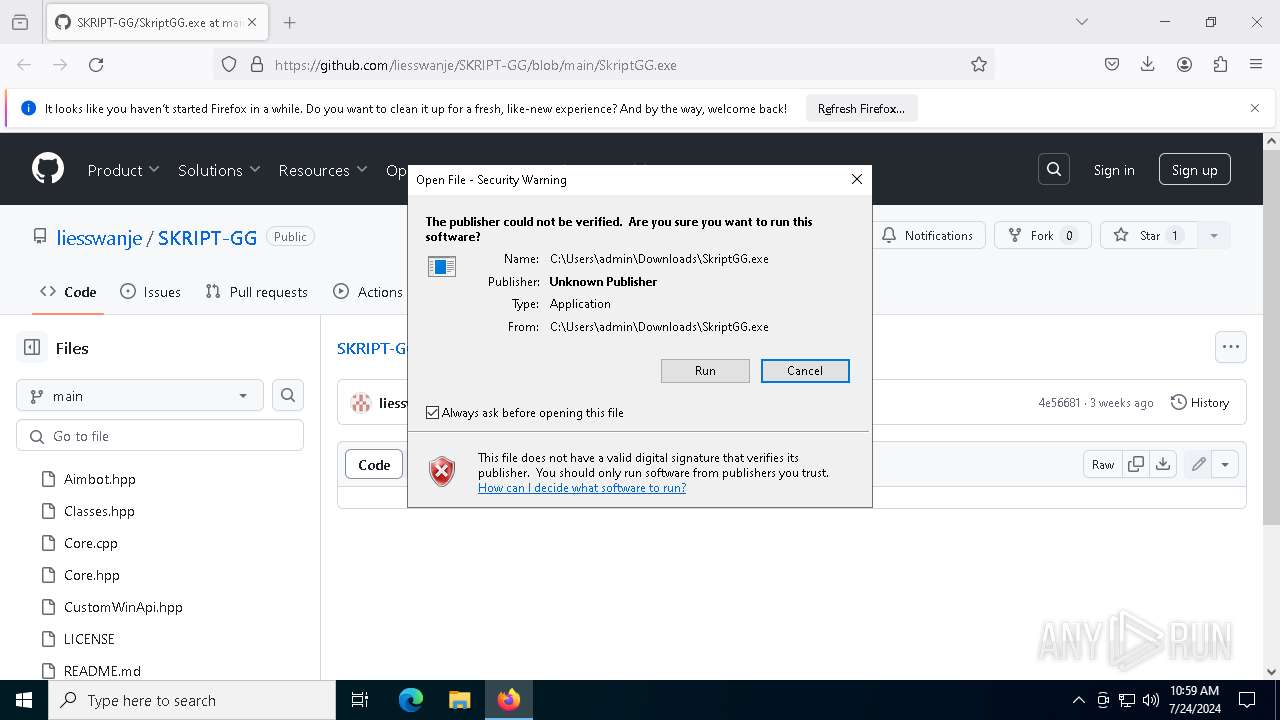
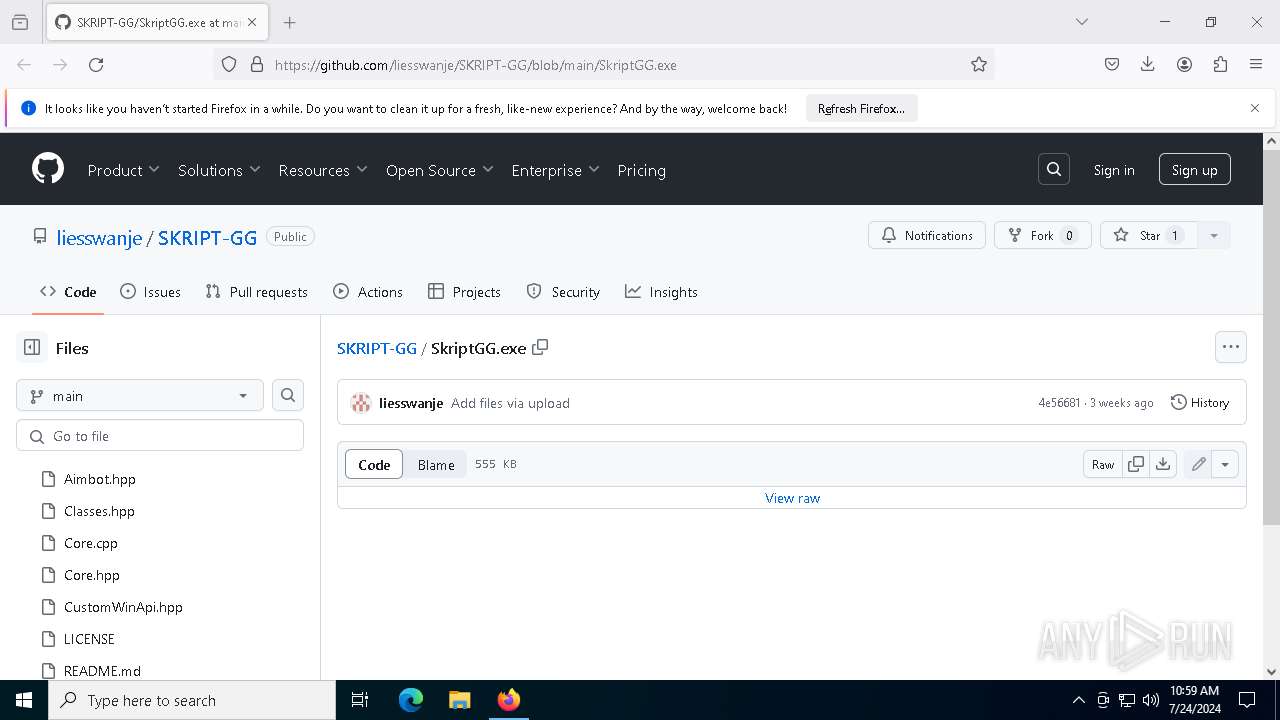
| URL: | https://github.com/liesswanje/SKRIPT-GG/blob/main/SkriptGG.exe |
| Full analysis: | https://app.any.run/tasks/f81e9b25-3b31-4081-9a3a-29d76eee775d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 24, 2024, 10:58:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 58C8E187F213588F71A0ABB158DFC0F4 |
| SHA1: | 3B2EEB8F9EDBC307EB7ECDD1E730570827A1ACEF |
| SHA256: | 7F438D5EDF2980E09C53A1FFCEB22F74DCDBC2AF89BC3EDCABAB4394E132F8ED |
| SSDEEP: | 3:N8tEd5Mz62alzERSL:2uUz62alzsC |
MALICIOUS
Drops the executable file immediately after the start
- SkriptGG.exe (PID: 7948)
Stealers network behavior
- aspnet_regiis.exe (PID: 8044)
LUMMA has been detected (SURICATA)
- aspnet_regiis.exe (PID: 8044)
Actions looks like stealing of personal data
- aspnet_regiis.exe (PID: 8044)
SUSPICIOUS
Executable content was dropped or overwritten
- SkriptGG.exe (PID: 7948)
Searches for installed software
- aspnet_regiis.exe (PID: 8044)
INFO
Application launched itself
- firefox.exe (PID: 6220)
- firefox.exe (PID: 3888)
Checks proxy server information
- slui.exe (PID: 2232)
The process uses the downloaded file
- firefox.exe (PID: 3888)
Reads the software policy settings
- slui.exe (PID: 2232)
- aspnet_regiis.exe (PID: 8044)
Reads the computer name
- SkriptGG.exe (PID: 7948)
- aspnet_regiis.exe (PID: 8044)
Checks supported languages
- SkriptGG.exe (PID: 7948)
- aspnet_regiis.exe (PID: 8044)
Creates files or folders in the user directory
- SkriptGG.exe (PID: 7948)
Reads Microsoft Office registry keys
- firefox.exe (PID: 3888)
Drops the executable file immediately after the start
- firefox.exe (PID: 3888)
Executable content was dropped or overwritten
- firefox.exe (PID: 3888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
159
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2212 -parentBuildID 20240213221259 -prefsHandle 2200 -prefMapHandle 2188 -prefsLen 30537 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f96516c8-cf40-485e-8ded-a64d3d1bb356} 3888 "\\.\pipe\gecko-crash-server-pipe.3888" 23388380b10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 | |||||||||||||||
| 704 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4488 -childID 2 -isForBrowser -prefsHandle 4480 -prefMapHandle 4476 -prefsLen 36263 -prefMapSize 244343 -jsInitHandle 1212 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {039c1348-3628-48b4-92b5-ece8e39c6392} 3888 "\\.\pipe\gecko-crash-server-pipe.3888" 23399f9f850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 | |||||||||||||||
| 916 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5128 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5204 -prefMapHandle 5200 -prefsLen 36339 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {41c254fb-200d-4030-8786-c083a584c2a0} 3888 "\\.\pipe\gecko-crash-server-pipe.3888" 2339bb82710 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 | |||||||||||||||
| 1812 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5780 -childID 4 -isForBrowser -prefsHandle 5016 -prefMapHandle 5776 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1212 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {015ba8e3-2da4-4b13-8224-a7348d75f2dc} 3888 "\\.\pipe\gecko-crash-server-pipe.3888" 2339e0b6d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5968 -childID 5 -isForBrowser -prefsHandle 5972 -prefMapHandle 5976 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1212 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d41815f9-683a-40b5-976b-778a8d46695c} 3888 "\\.\pipe\gecko-crash-server-pipe.3888" 2339e0b6f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 | |||||||||||||||
| 2232 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3384 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3888 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/liesswanje/SKRIPT-GG/blob/main/SkriptGG.exe | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 4364 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 | |||||||||||||||
Total events
759
Read events
759
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
169
Text files
40
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:4190F5A40EAF6D57FFD4EEFBD040A784 | SHA256:03BD049D82D05C8C50A37B703A4791469149612B407ABD104CA9C99459A0AEBB | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:04376FDEB670785966CFF083BA15A3B2 | SHA256:6731D5A6ACFC9BD49C22D8DE2246EBDFBE21888B01AD2EDA5C88B3EA743C53DB | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:B521EAE7B0C92E6A0A7E51D5FC2FE456 | SHA256:6D48A81FC9A0BB32F496D76B1162C61B789FE10F19ADFEBBF5020FCAD3B1801D | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | sqlite | |
MD5:1BECEACBE77F1FBDC07DBC3154493FF6 | SHA256:9D079B1B3048192B6CA404C5BE8BFD7B8BFE65CAD05745F5E6FC356123543408 | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:4006DDC2918B16C7EF5516C58373842B | SHA256:269EA23B77EDE0874628BD8611BCC5A3E87E0C44CA8A821C0D028B929D4F468F | |||
| 3888 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:DFC685CA828833FE9AA7299785B26B0A | SHA256:3F5D76B68463D9325A6FA8AA0F99BC91D77489F34141671816C261DDE8056BA7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
132
DNS requests
142
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3888 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
3888 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
3888 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
3888 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3656 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4360 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 92.123.104.33:443 | — | Akamai International B.V. | DE | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4204 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
7124 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3888 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
3888 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
8044 | aspnet_regiis.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |