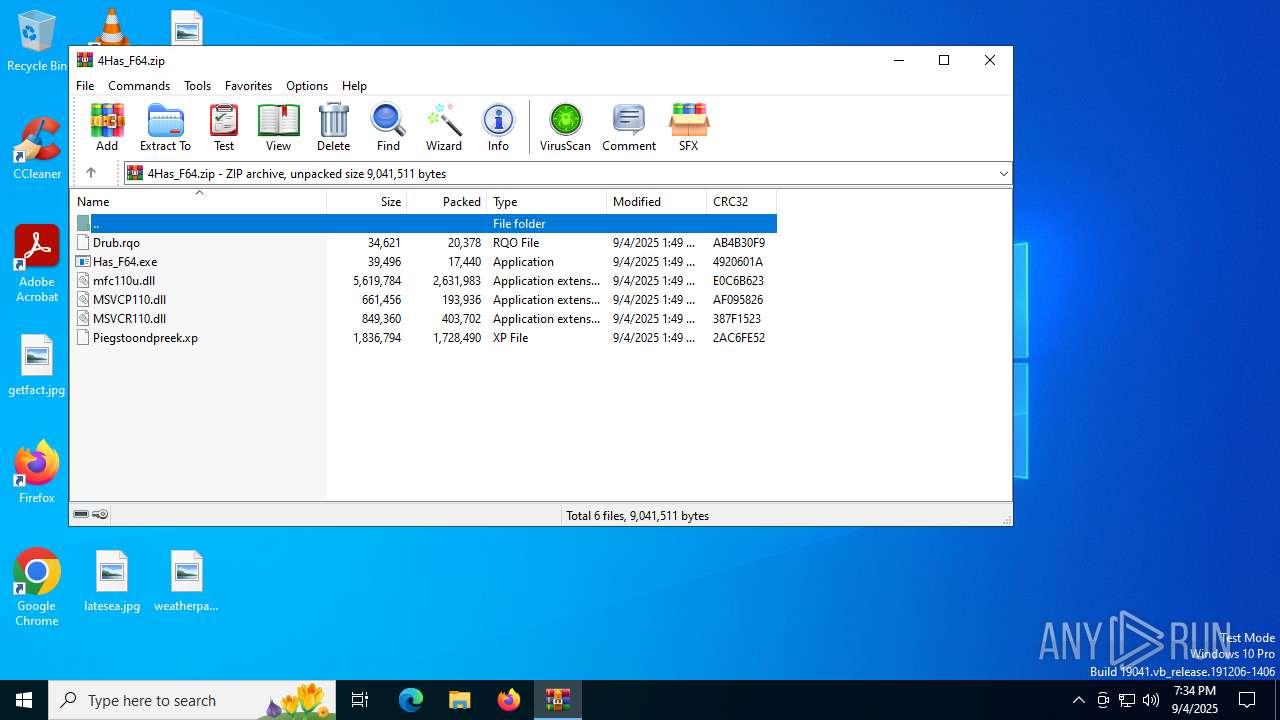
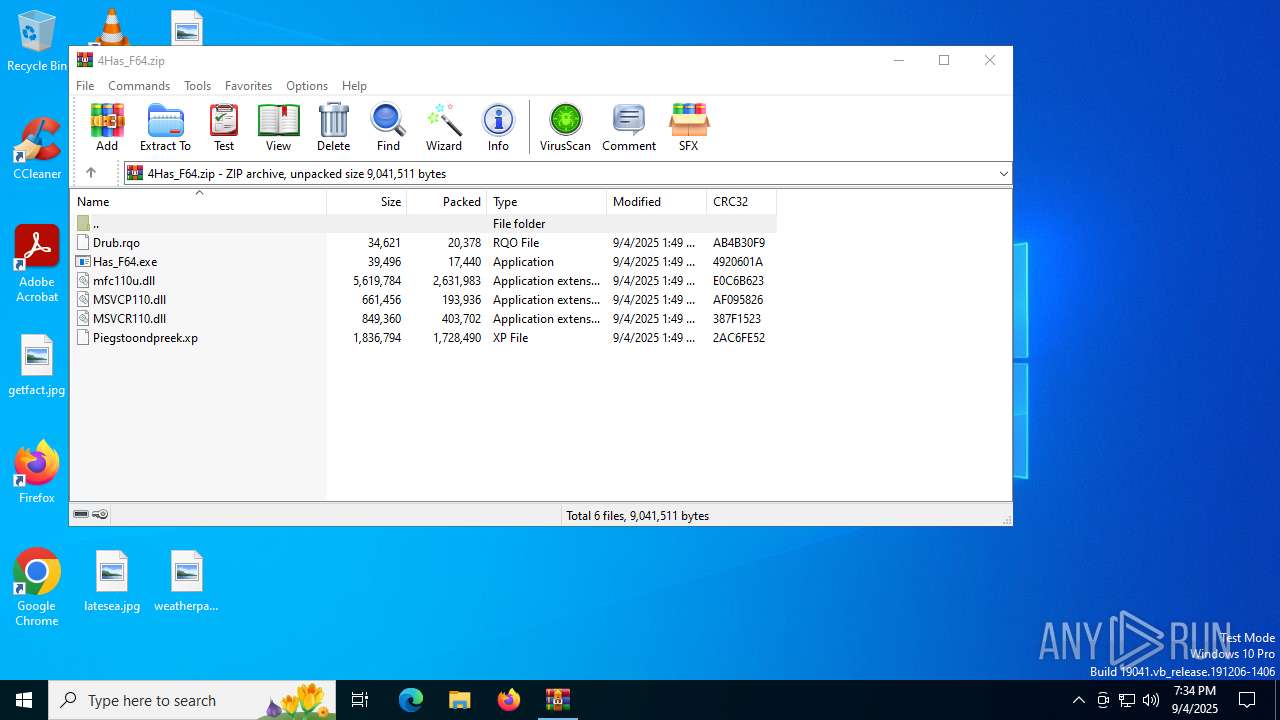
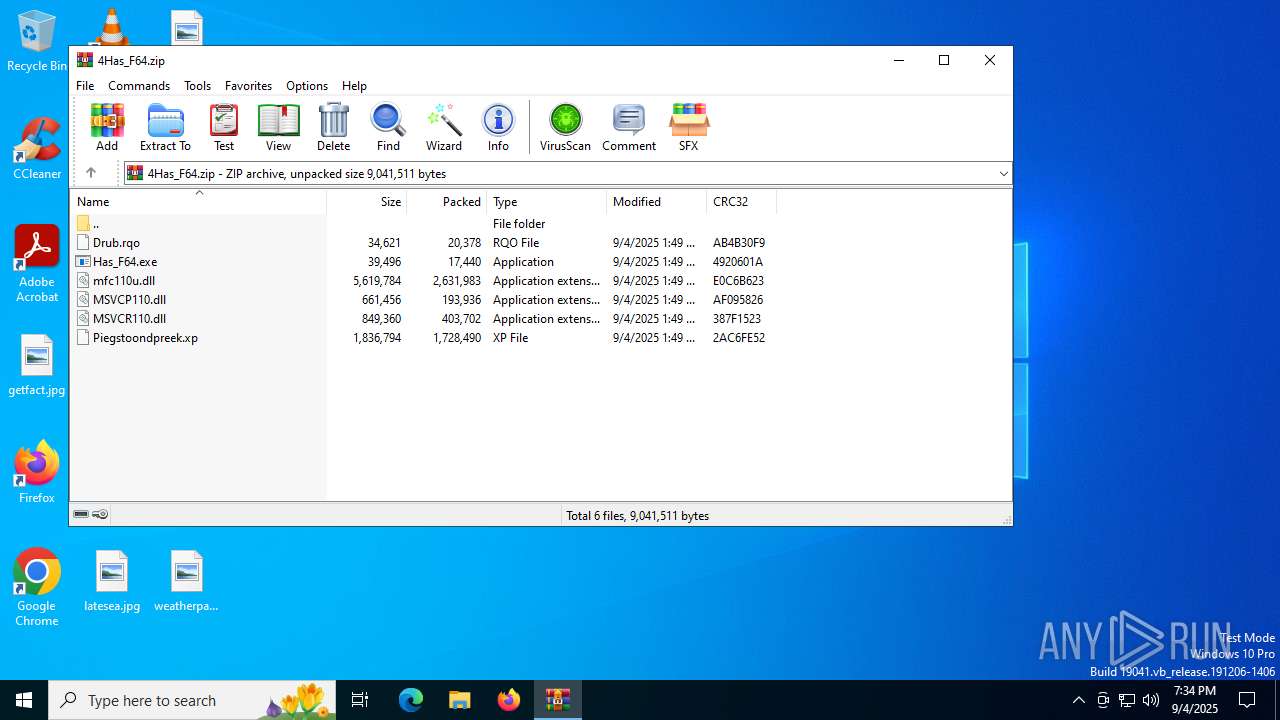
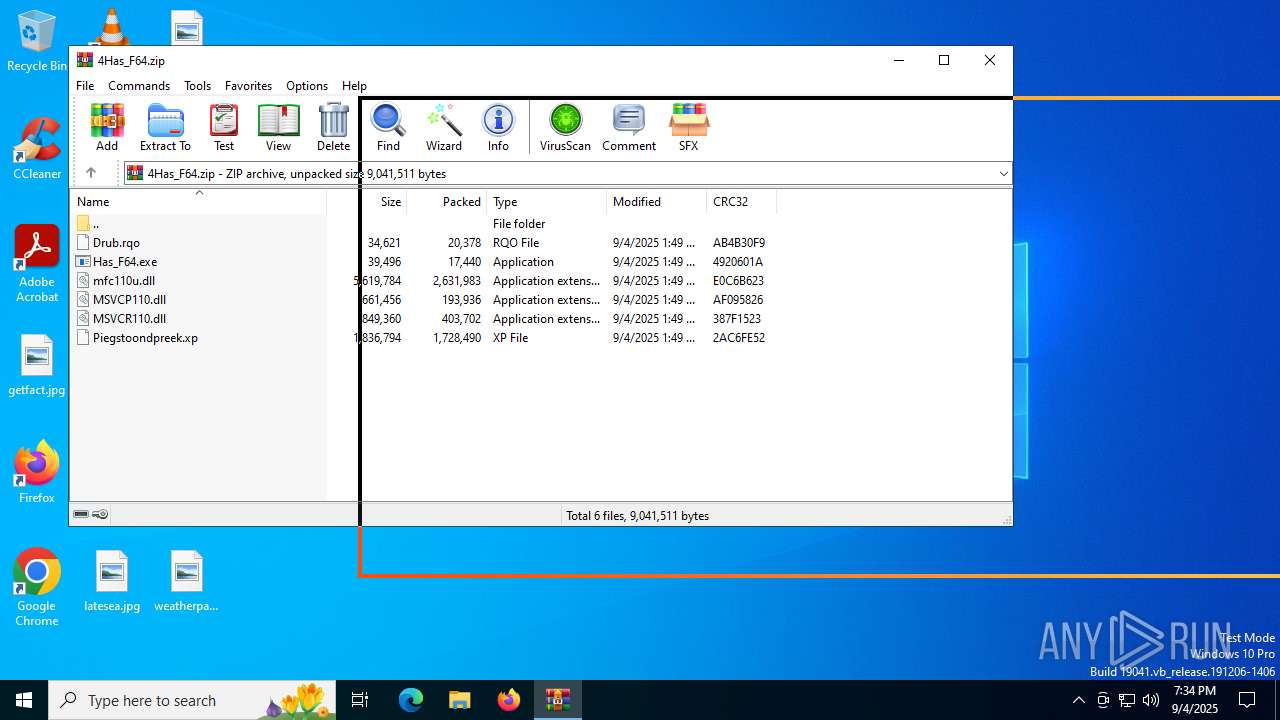
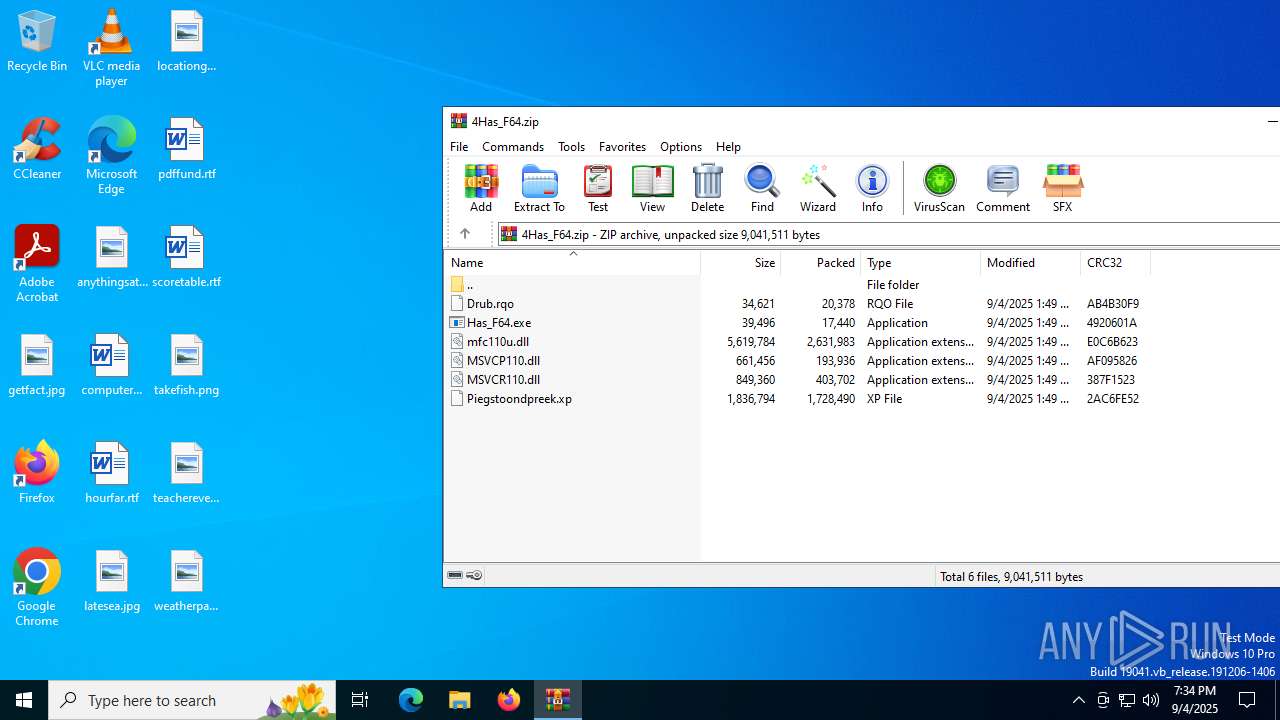
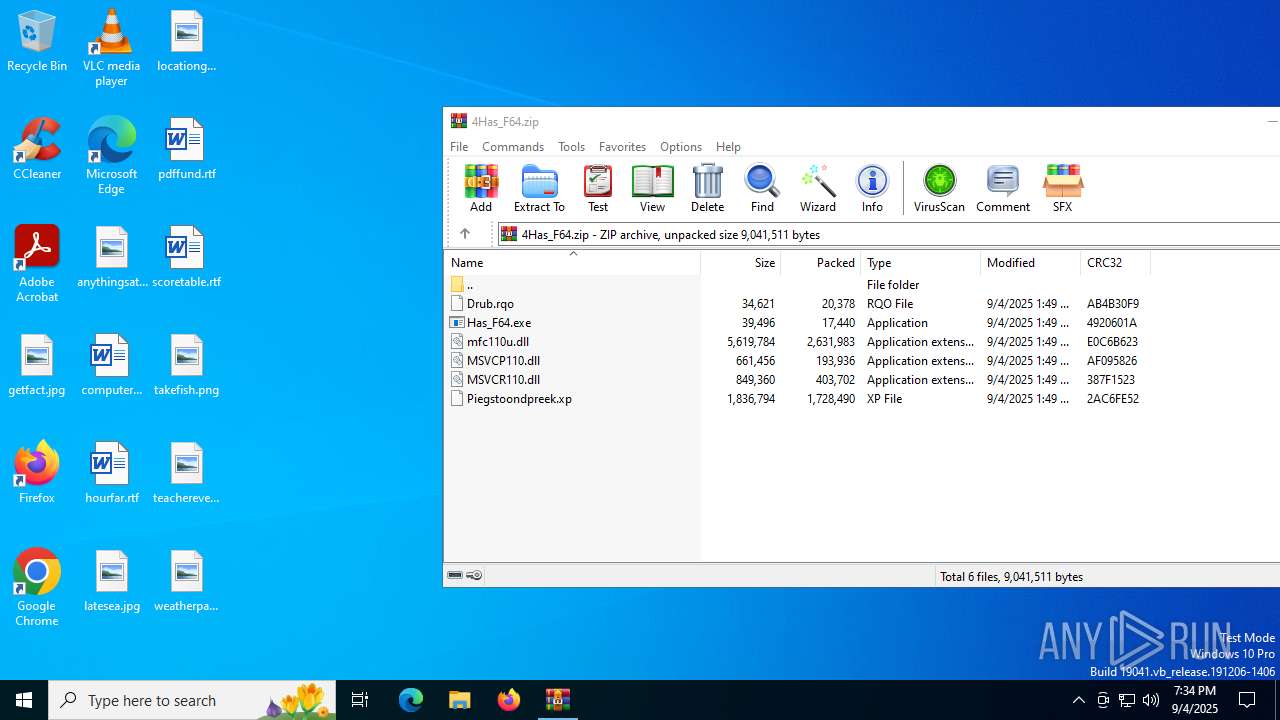
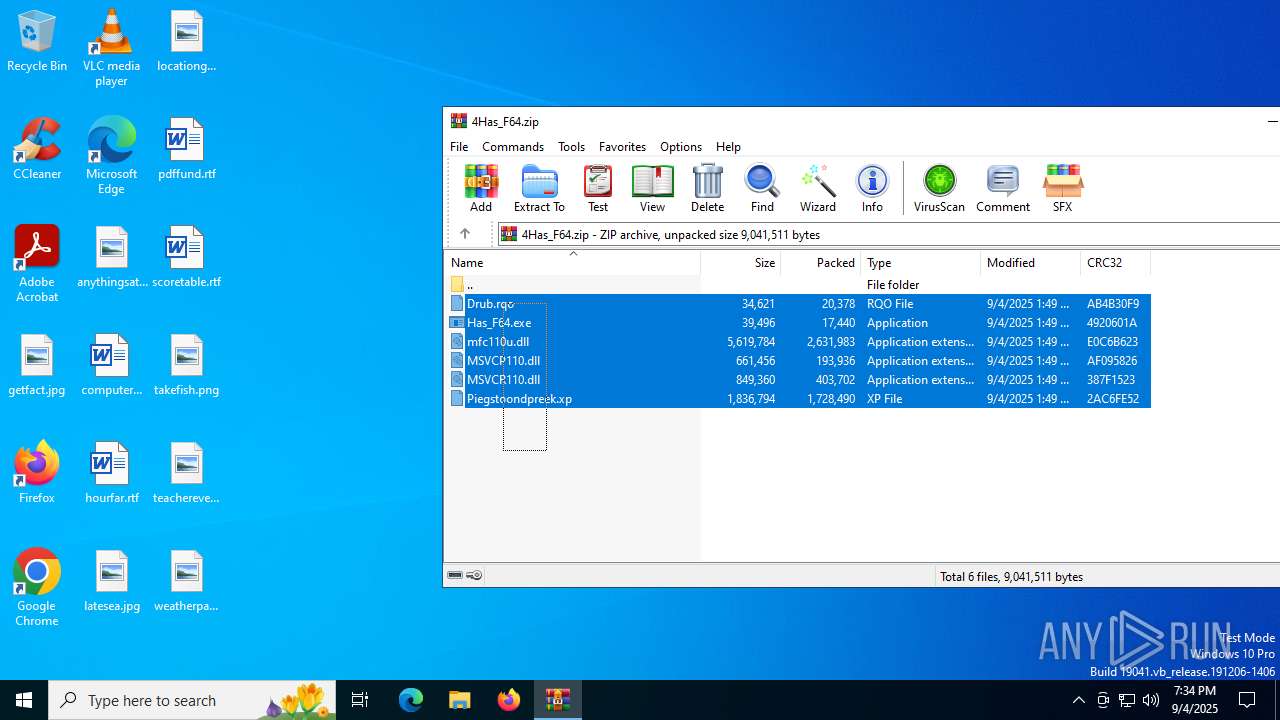
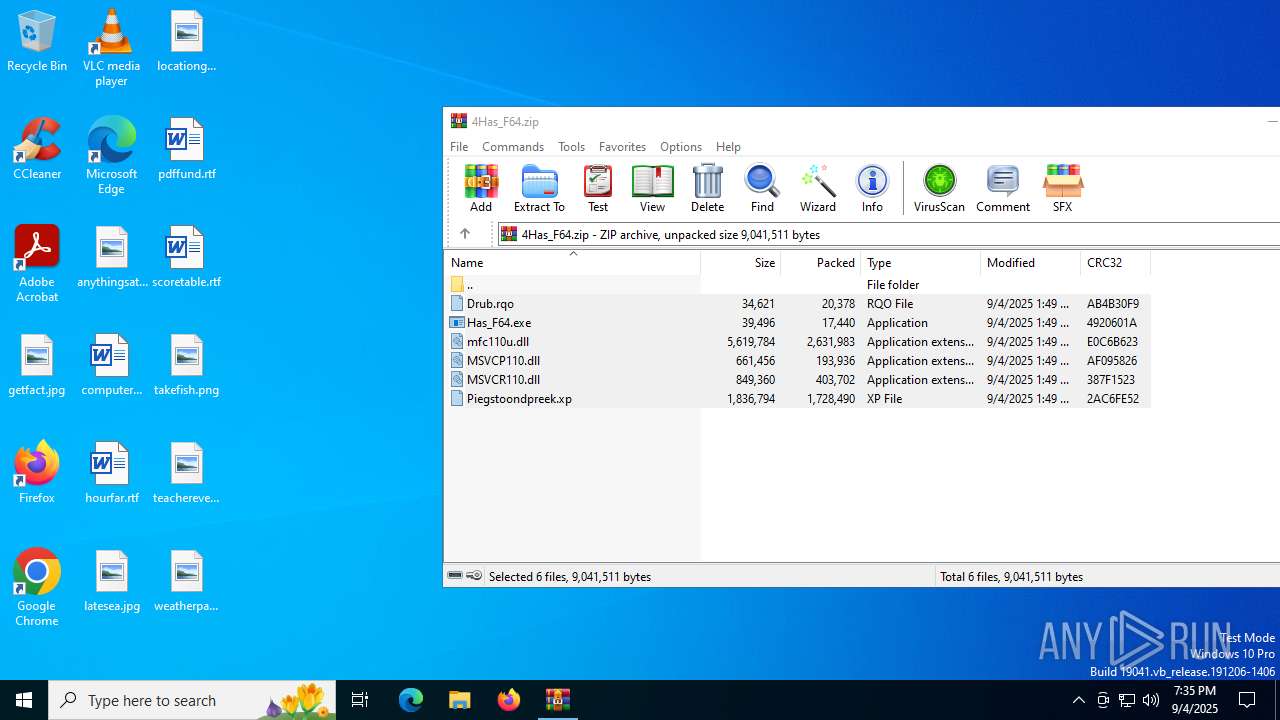
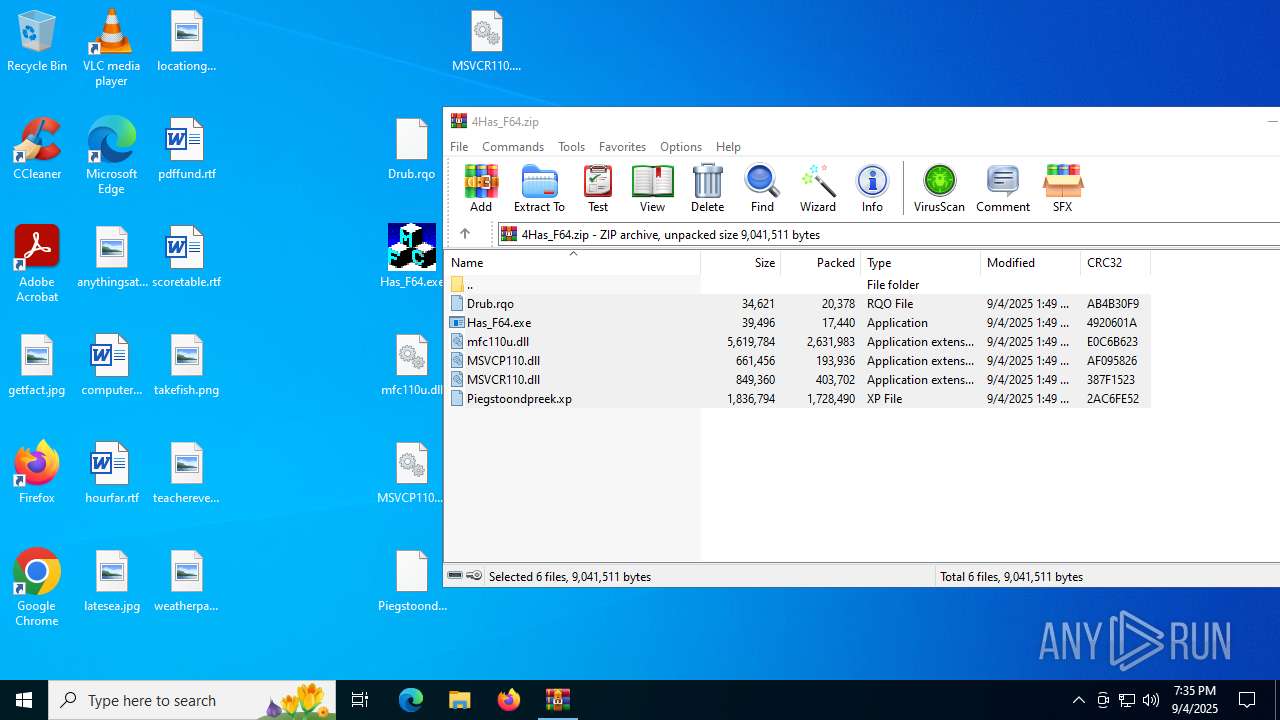
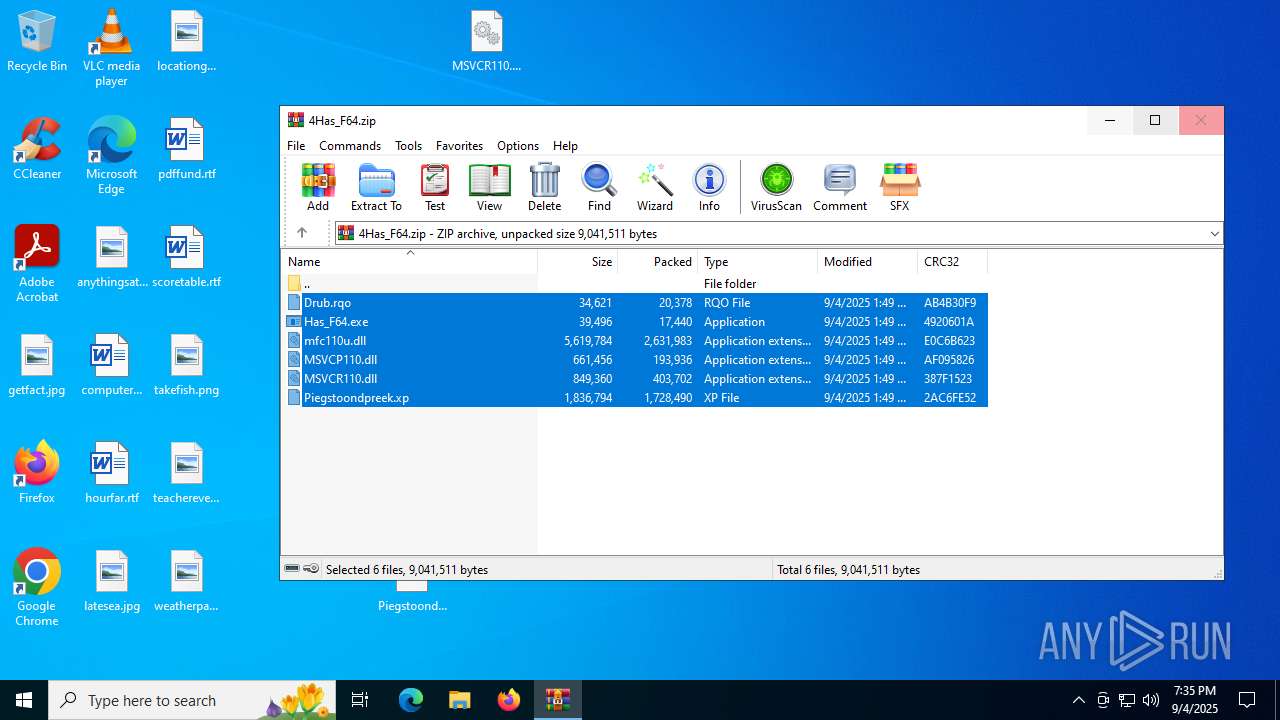
| File name: | 4Has_F64.zip |
| Full analysis: | https://app.any.run/tasks/b963874a-b415-4a81-8f5a-24ec83d7b0ca |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | September 04, 2025, 19:34:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 4A87CFC91192E90C075E2E7A0B4FC6FE |
| SHA1: | 9059F7BC168304BB53F3AB118C5376E105582B06 |
| SHA256: | 7F3F01810868C1761DEB55178F41373F6075F8A5F12AC0CEF014973CCF948A1F |
| SSDEEP: | 98304:X5VdISidItypzM2vWdLM8tlBQdCfkkGJbHrgow4/Nc1iwdK7THmUYdlLGe/nEB3V:a7QCp/ |
MALICIOUS
Executing a file with an untrusted certificate
- Has_F64.exe (PID: 4680)
- Has_F64.exe (PID: 6236)
- Has_F64.exe (PID: 1352)
- Has_F64.exe (PID: 3964)
Generic archive extractor
- WinRAR.exe (PID: 4744)
HIJACKLOADER has been detected (YARA)
- Has_F64.exe (PID: 6236)
- Has_F64.exe (PID: 3964)
DCRAT mutex has been found
- StreamVa.exe (PID: 3896)
ASYNCRAT has been detected (SURICATA)
- StreamVa.exe (PID: 3896)
SUSPICIOUS
Starts itself from another location
- Has_F64.exe (PID: 4680)
- Has_F64.exe (PID: 1352)
Executable content was dropped or overwritten
- Has_F64.exe (PID: 4680)
- Has_F64.exe (PID: 6236)
Process drops legitimate windows executable
- Has_F64.exe (PID: 4680)
- WinRAR.exe (PID: 4744)
The process drops C-runtime libraries
- Has_F64.exe (PID: 4680)
Connects to unusual port
- StreamVa.exe (PID: 3896)
There is functionality for taking screenshot (YARA)
- StreamVa.exe (PID: 3896)
- StreamVa.exe (PID: 6292)
Contacting a server suspected of hosting an CnC
- StreamVa.exe (PID: 3896)
Possibly patching Antimalware Scan Interface function (YARA)
- StreamVa.exe (PID: 6292)
INFO
Checks supported languages
- Has_F64.exe (PID: 6236)
- Has_F64.exe (PID: 4680)
- Has_F64.exe (PID: 1352)
- Has_F64.exe (PID: 3964)
- StreamVa.exe (PID: 6292)
- Chime.exe (PID: 5564)
- Chime.exe (PID: 5904)
- StreamVa.exe (PID: 3896)
The sample compiled with english language support
- Has_F64.exe (PID: 4680)
- WinRAR.exe (PID: 4744)
- Has_F64.exe (PID: 6236)
Reads the computer name
- Has_F64.exe (PID: 4680)
- Has_F64.exe (PID: 6236)
- Has_F64.exe (PID: 1352)
- Has_F64.exe (PID: 3964)
- Chime.exe (PID: 5564)
- Chime.exe (PID: 5904)
- StreamVa.exe (PID: 6292)
- StreamVa.exe (PID: 3896)
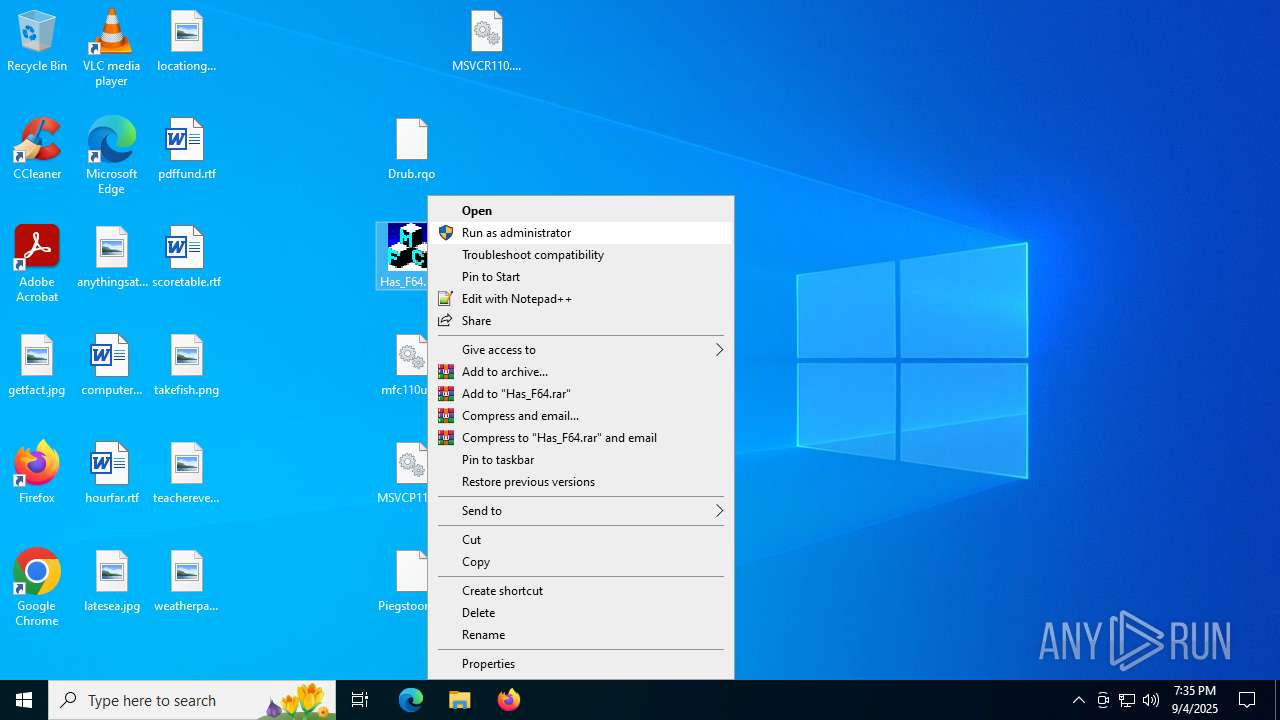
Manual execution by a user
- Has_F64.exe (PID: 4680)
- Has_F64.exe (PID: 1352)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4744)
Creates files in the program directory
- Has_F64.exe (PID: 4680)
Creates files or folders in the user directory
- Has_F64.exe (PID: 6236)
Create files in a temporary directory
- Has_F64.exe (PID: 3964)
- Has_F64.exe (PID: 6236)
Reads the machine GUID from the registry
- StreamVa.exe (PID: 3896)
Reads the software policy settings
- StreamVa.exe (PID: 3896)
- slui.exe (PID: 7140)
The sample compiled with chinese language support
- Has_F64.exe (PID: 6236)
Checks proxy server information
- slui.exe (PID: 7140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:09:04 08:49:36 |
| ZipCRC: | 0x2ac6fe52 |
| ZipCompressedSize: | 1728490 |
| ZipUncompressedSize: | 1836794 |
| ZipFileName: | Piegstoondpreek.xp |
Total processes
146
Monitored processes
11
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Users\admin\Desktop\Has_F64.exe" | C:\Users\admin\Desktop\Has_F64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: RegLibs MFC Application Exit code: 0 Version: 1, 0, 0, 23 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | C:\Users\admin\StreamVa.exe | C:\Users\admin\StreamVa.exe | Has_F64.exe | ||||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: SysCleanPro Application Version: 1.0.0.1101 Modules
| |||||||||||||||
| 3964 | C:\ProgramData\SyStreamv2\Has_F64.exe | C:\ProgramData\SyStreamv2\Has_F64.exe | Has_F64.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: RegLibs MFC Application Exit code: 0 Version: 1, 0, 0, 23 Modules
| |||||||||||||||
| 4680 | "C:\Users\admin\Desktop\Has_F64.exe" | C:\Users\admin\Desktop\Has_F64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RegLibs MFC Application Exit code: 0 Version: 1, 0, 0, 23 Modules
| |||||||||||||||
| 4744 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\4Has_F64.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5564 | C:\Users\admin\AppData\Local\SyStreamv2\Chime.exe | C:\Users\admin\AppData\Local\SyStreamv2\Chime.exe | — | Has_F64.exe | |||||||||||
User: admin Company: Amazon.com Services LLC Integrity Level: MEDIUM Description: Amazon Chime Exit code: 0 Version: 5.23.32022 Modules
| |||||||||||||||
| 5904 | C:\Users\admin\AppData\Local\SyStreamv2\Chime.exe | C:\Users\admin\AppData\Local\SyStreamv2\Chime.exe | — | Has_F64.exe | |||||||||||
User: admin Company: Amazon.com Services LLC Integrity Level: HIGH Description: Amazon Chime Exit code: 0 Version: 5.23.32022 Modules
| |||||||||||||||
| 6236 | C:\ProgramData\SyStreamv2\Has_F64.exe | C:\ProgramData\SyStreamv2\Has_F64.exe | Has_F64.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RegLibs MFC Application Exit code: 0 Version: 1, 0, 0, 23 Modules
| |||||||||||||||
| 6292 | C:\Users\admin\StreamVa.exe | C:\Users\admin\StreamVa.exe | — | Has_F64.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: SysCleanPro Application Exit code: 0 Version: 1.0.0.1101 Modules
| |||||||||||||||
Total events
7 962
Read events
7 942
Write events
20
Delete events
0
Modification events
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4Has_F64.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
10
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6236 | Has_F64.exe | C:\Users\admin\AppData\Local\Temp\60A37FF.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | Has_F64.exe | C:\Users\admin\AppData\Local\Temp\658916A.tmp | — | |
MD5:— | SHA256:— | |||
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4744.13903\Drub.rqo | binary | |
MD5:AF34F45183EB84CAD53DC027B701F78A | SHA256:F2B6507ABC5F504B33DCCDC8573244D62B6079A863B1EFB066AB9518061C48E4 | |||
| 4680 | Has_F64.exe | C:\ProgramData\SyStreamv2\mfc110u.dll | executable | |
MD5:6E6E60BA389FCDE9FD2E3F9A6619A9A8 | SHA256:047376677433E527287F4455D89A86AE0D42285F9C8A86ED71E321E2A83BF54A | |||
| 4680 | Has_F64.exe | C:\ProgramData\SyStreamv2\MSVCP110.dll | executable | |
MD5:7CAA1B97A3311EB5A695E3C9028616E7 | SHA256:27F394AE01D12F851F1DEE3632DEE3C5AFA1D267F7A96321D35FD43105B035AD | |||
| 6236 | Has_F64.exe | C:\Users\admin\AppData\Local\Temp\5FD28EB.tmp | binary | |
MD5:00350CF5806FA1EA20B0A206DBEA2DF0 | SHA256:C476D7B3DDA5B66AC2D4EA6FC709FCE80AF55BDB4B946ADD13EAE3EBE0E5FC8F | |||
| 3964 | Has_F64.exe | C:\Users\admin\AppData\Local\Temp\64F86F9.tmp | binary | |
MD5:256C3BBA67B16DD03A8431715633A75C | SHA256:89CD50E61DCA4FD043DDF716D80ADC6765FB712906806C583765D70D989EB4EF | |||
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4744.13903\Has_F64.exe | executable | |
MD5:285AF5DF9E15CD1467966E50E4A933F8 | SHA256:C2A2846F3775E641218CE24189E795ACBAC3562D7B2F0F27A4E08F43173898C1 | |||
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4744.13903\Piegstoondpreek.xp | binary | |
MD5:F7F3F81AA8A508E11376EE54BD426B8C | SHA256:37BCCF63C3EAB48298A6F9E9E84D931DA21BF0FB20667AB5431E69AD07005109 | |||
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4744.13903\MSVCP110.dll | executable | |
MD5:7CAA1B97A3311EB5A695E3C9028616E7 | SHA256:27F394AE01D12F851F1DEE3632DEE3C5AFA1D267F7A96321D35FD43105B035AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
19
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2940 | svchost.exe | GET | 200 | 23.3.109.48:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
4892 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6748 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6748 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1948 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4892 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.dynuddns .net Domain |
3896 | StreamVa.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
3896 | StreamVa.exe | A Network Trojan was detected | ET MALWARE Observed Malicious SSL Cert (Various RAT) |
3896 | StreamVa.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
3896 | StreamVa.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |