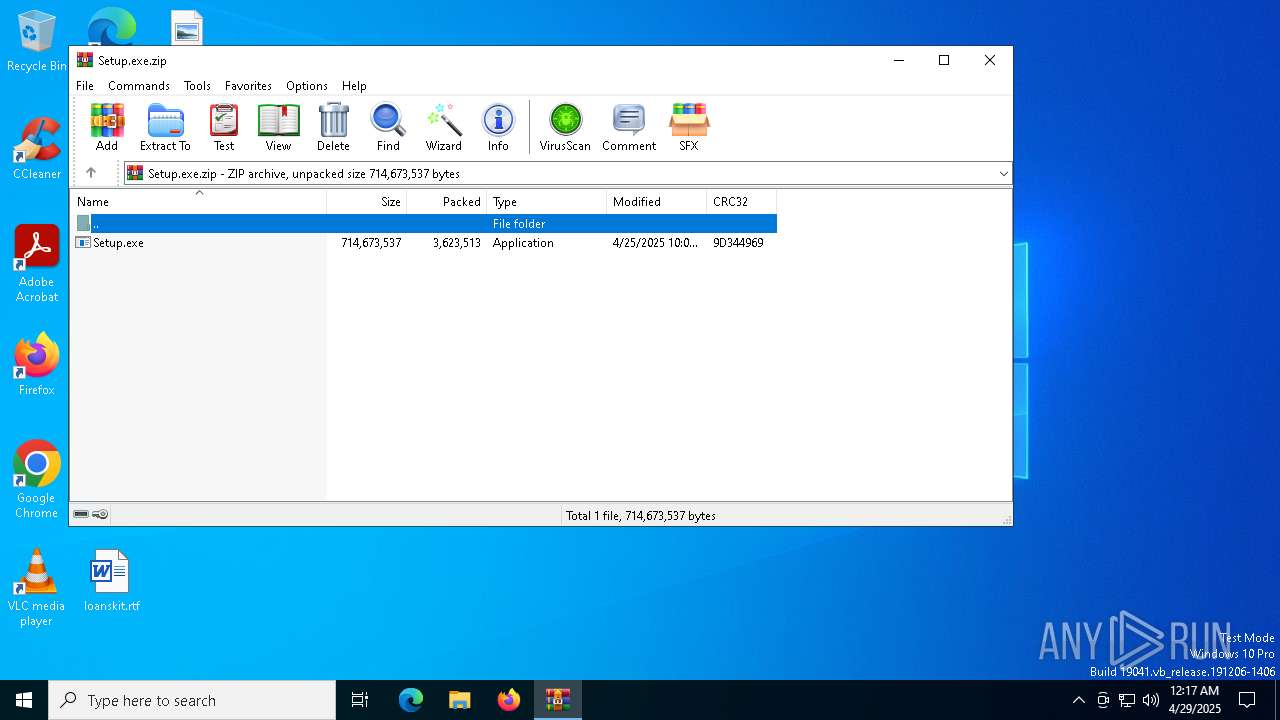
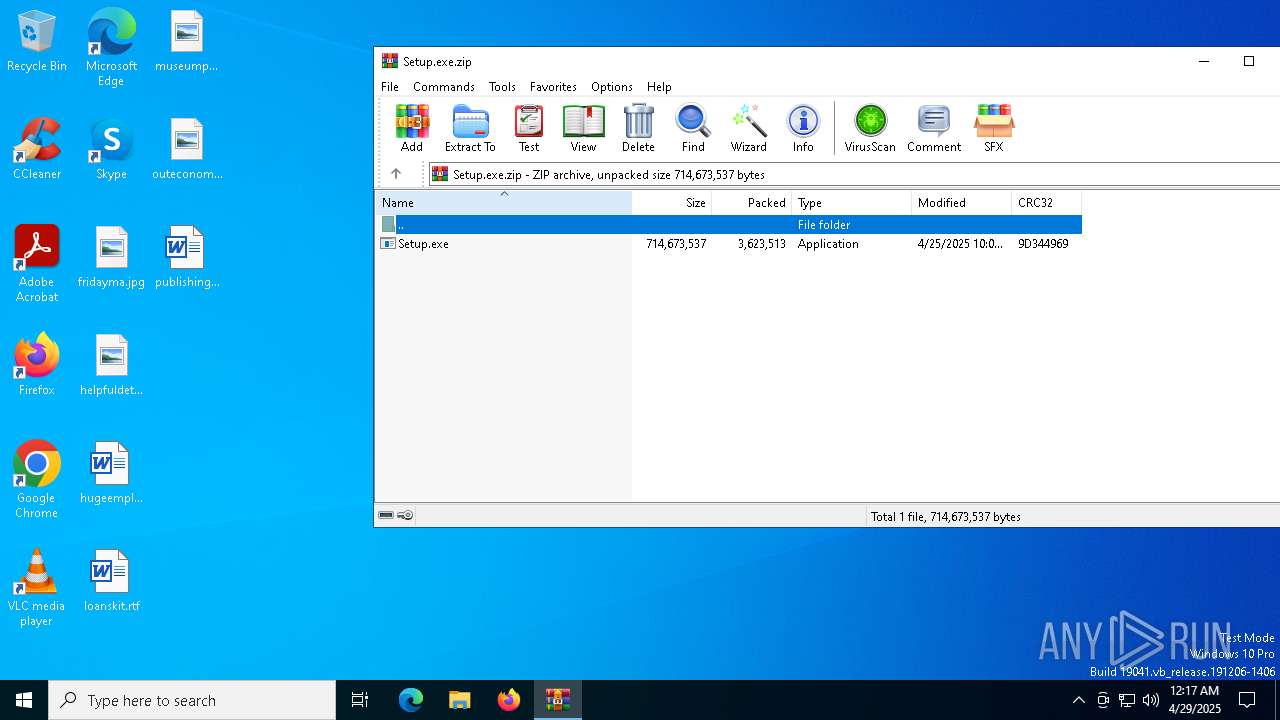
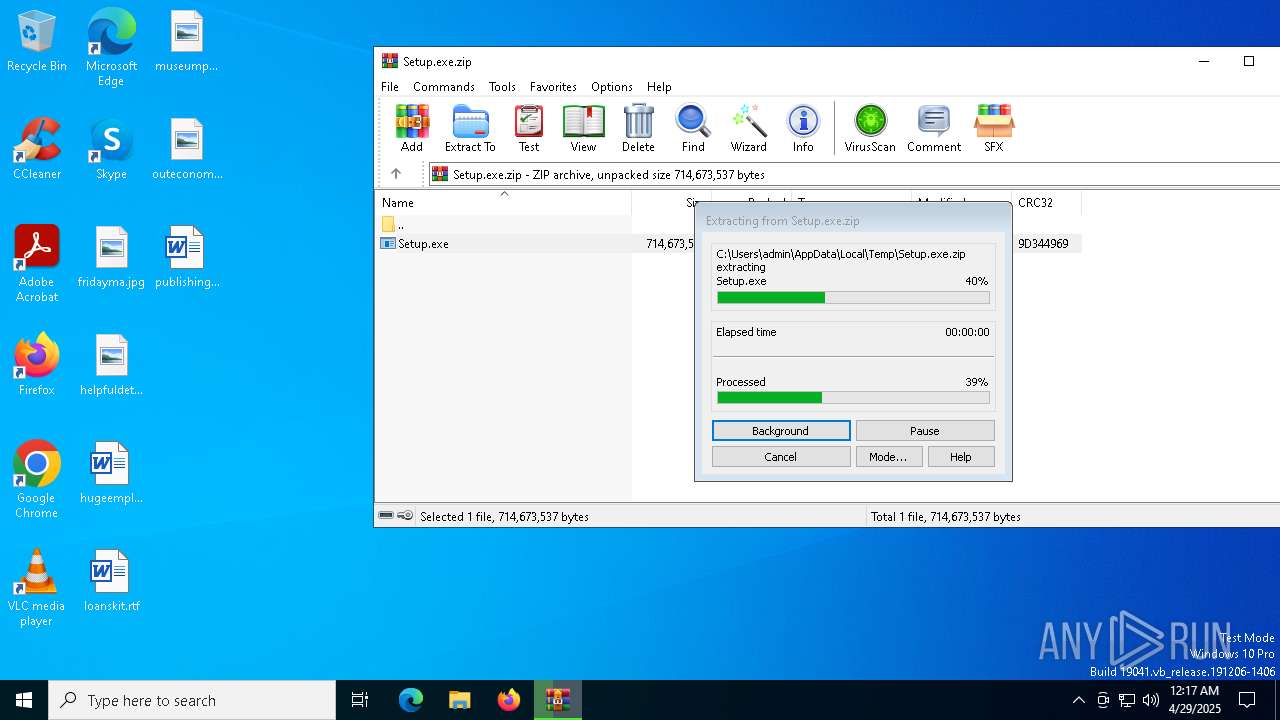
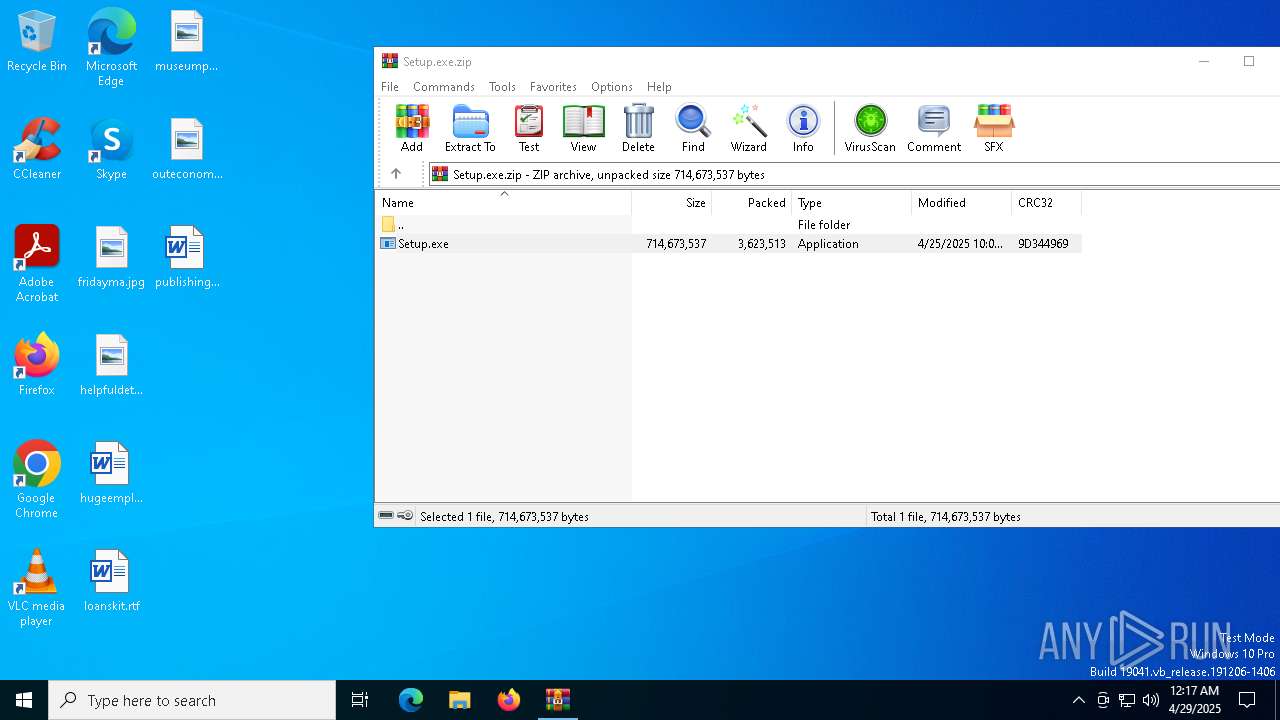
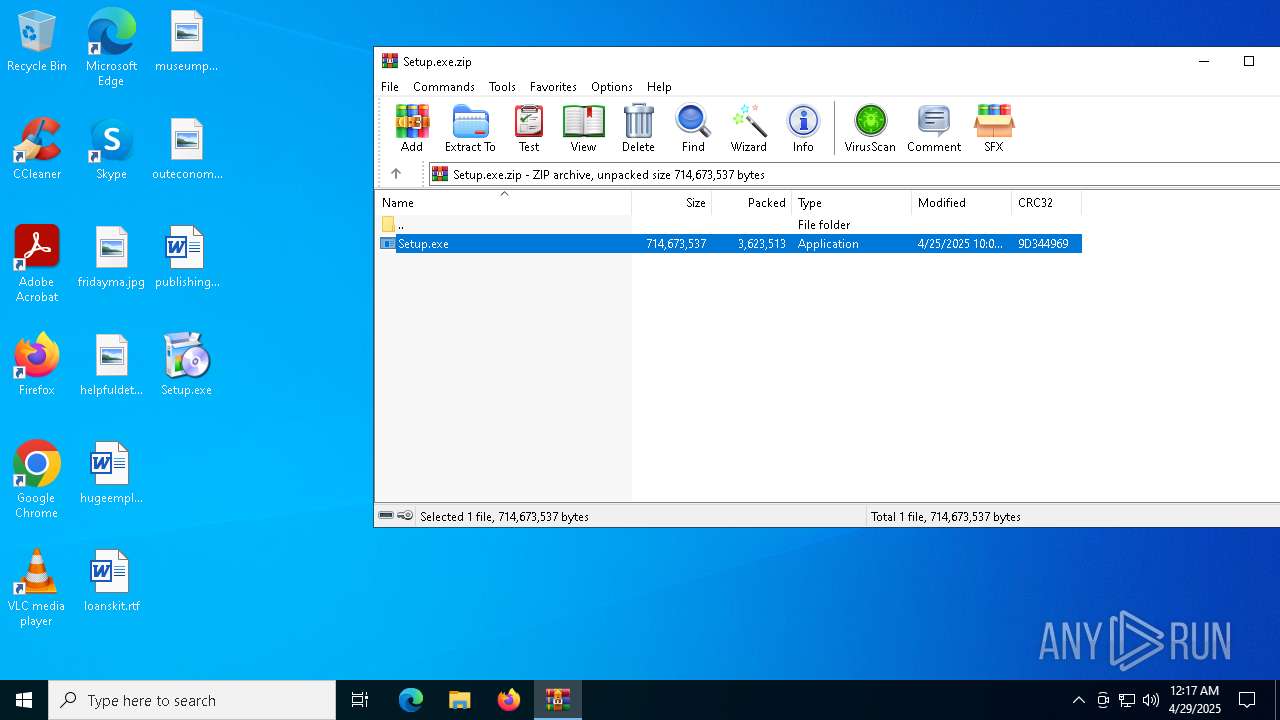
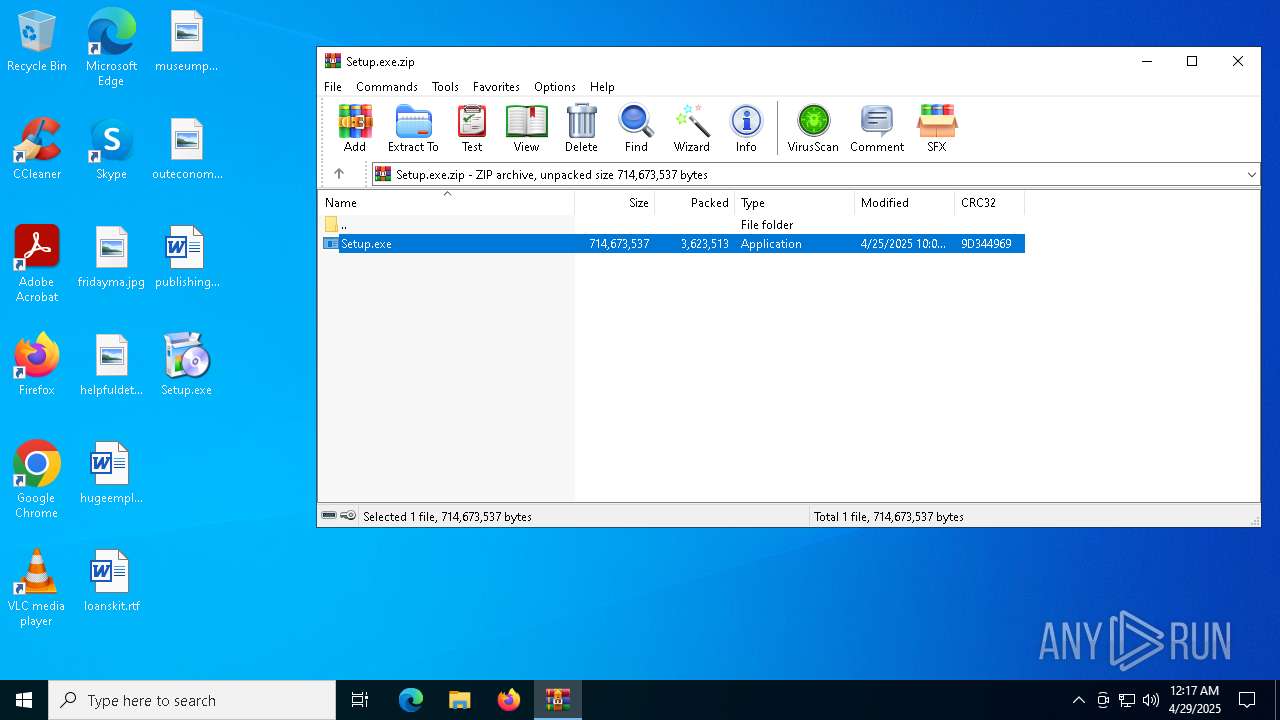
| File name: | Setup.exe.zip |
| Full analysis: | https://app.any.run/tasks/cf412f3f-1b31-472c-90b1-555c6dab704b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 29, 2025, 00:17:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1B44D6BDB341D0E4441D1EF4D7C7058C |
| SHA1: | 6C913BF5DCAF0BF252BFEA02A538611EB6503CF5 |
| SHA256: | 7F35F29CD541E856E0B04E792D7819C87888DA8D03AA4D9F4222F3A6038B5DFE |
| SSDEEP: | 98304:cxBV980+BXgiA/KyZmzxGoBQO0Ly43xHbkdwpnYF4jB54zgw2ZhwFEHPRYg4+Wt2:2H9BxL0M9 |
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 1280)
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- Safari.exe (PID: 6416)
- asus_framework.exe (PID: 6436)
Actions looks like stealing of personal data
- Setup.exe (PID: 1280)
LUMMA mutex has been found
- Setup.exe (PID: 1280)
Known privilege escalation attack
- dllhost.exe (PID: 1040)
Changes the autorun value in the registry
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
- reg.exe (PID: 5048)
HIJACKLOADER has been detected (YARA)
- Clus-Blue.exe (PID: 2040)
AMADEY has been detected (YARA)
- Clus-Blue.exe (PID: 2040)
- ping.com (PID: 2616)
Connects to the CnC server
- ping.com (PID: 2616)
- ping.com (PID: 6740)
AMADEY has been detected (SURICATA)
- ping.com (PID: 2616)
- ping.com (PID: 6740)
SUSPICIOUS
Searches for installed software
- Setup.exe (PID: 1280)
Process drops legitimate windows executable
- Clus-Blue.exe (PID: 4812)
- Setup.exe (PID: 1280)
The process drops C-runtime libraries
- Clus-Blue.exe (PID: 4812)
- Setup.exe (PID: 1280)
Executable content was dropped or overwritten
- Setup.exe (PID: 1280)
- Clus-Blue.exe (PID: 4812)
- Clus-Blue.exe (PID: 6148)
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- Clus-Blue.exe (PID: 2040)
- Clus-Blue.exe (PID: 788)
Starts itself from another location
- Clus-Blue.exe (PID: 4812)
There is functionality for taking screenshot (YARA)
- Clus-Blue.exe (PID: 2040)
- ping.com (PID: 2616)
Starts application with an unusual extension
- Clus-Blue.exe (PID: 2040)
- Clus-Blue.exe (PID: 6588)
Executes application which crashes
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- asus_framework.exe (PID: 6436)
Starts CMD.EXE for commands execution
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- asus_framework.exe (PID: 6436)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1300)
- cmd.exe (PID: 7036)
Adds/modifies Windows certificates
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- asus_framework.exe (PID: 6436)
There is functionality for enable RDP (YARA)
- ping.com (PID: 2616)
The process executes via Task Scheduler
- Clus-Blue.exe (PID: 788)
- PLUGScheduler.exe (PID: 780)
Reads security settings of Internet Explorer
- ping.com (PID: 2616)
Contacting a server suspected of hosting an CnC
- ping.com (PID: 2616)
- ping.com (PID: 6740)
Connects to unusual port
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- asus_framework.exe (PID: 6436)
Connects to the server without a host name
- Safari.exe (PID: 6416)
INFO
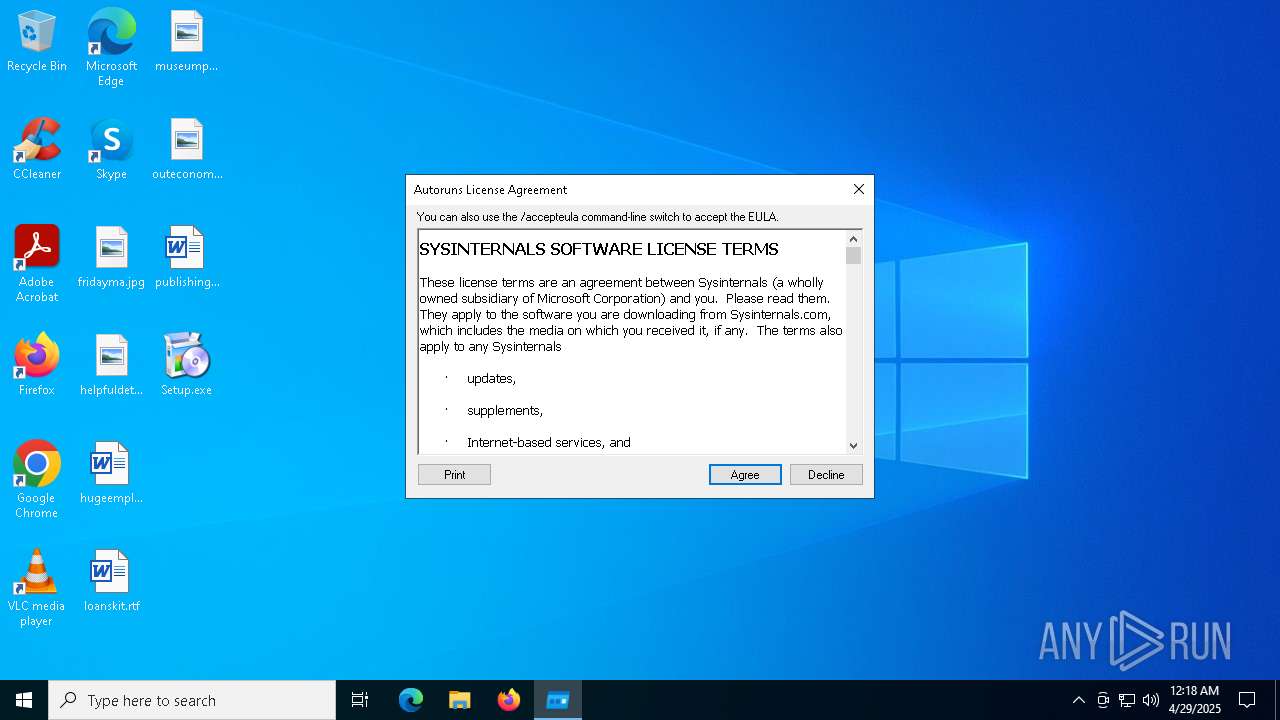
Manual execution by a user
- Setup.exe (PID: 1280)
- asus_framework.exe (PID: 6436)
- Safari.exe (PID: 6416)
Checks supported languages
- Setup.exe (PID: 1280)
- Clus-Blue.exe (PID: 6148)
- Clus-Blue.exe (PID: 4812)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
- 360Tray.exe (PID: 5384)
- Clus-Blue.exe (PID: 2040)
- ping.com (PID: 2616)
- 360Tray.exe (PID: 6068)
Reads the computer name
- Setup.exe (PID: 1280)
- Clus-Blue.exe (PID: 6148)
- Clus-Blue.exe (PID: 4812)
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
- 360Tray.exe (PID: 5384)
- Clus-Blue.exe (PID: 2040)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
- 360Tray.exe (PID: 6068)
- ping.com (PID: 2616)
Detects InnoSetup installer (YARA)
- Setup.exe (PID: 1280)
Compiled with Borland Delphi (YARA)
- Setup.exe (PID: 1280)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
Reads the software policy settings
- Setup.exe (PID: 1280)
- slui.exe (PID: 5960)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
The sample compiled with english language support
- Setup.exe (PID: 1280)
- Clus-Blue.exe (PID: 4812)
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
Creates files in the program directory
- Clus-Blue.exe (PID: 6148)
- Clus-Blue.exe (PID: 4812)
- 57TYHCP43I6HBVGT6O137GQPA5MB6.exe (PID: 1512)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
Create files in a temporary directory
- Setup.exe (PID: 1280)
- Clus-Blue.exe (PID: 2040)
- Clus-Blue.exe (PID: 6148)
The sample compiled with chinese language support
- Clus-Blue.exe (PID: 6148)
- Clus-Blue.exe (PID: 788)
Reads the machine GUID from the registry
- 360Tray.exe (PID: 5384)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 1040)
Drops encrypted JS script (Microsoft Script Encoder)
- CJ2IAAAKW9PDT4VWLRX.exe (PID: 2140)
Checks proxy server information
- ping.com (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:26 06:05:12 |
| ZipCRC: | 0x9d344969 |
| ZipCompressedSize: | 3623513 |
| ZipUncompressedSize: | 714673537 |
| ZipFileName: | Setup.exe |
Total processes
350
Monitored processes
47
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | "C:\ProgramData\Fidl\Clus-Blue.exe" | C:\ProgramData\Fidl\Clus-Blue.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1040 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 1073807364 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1300 | cmd /c "reg add HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce /v asus_framework /t REG_SZ /d C:\ProgramData\asus_framework.exe /f" | C:\Windows\SysWOW64\cmd.exe | — | CJ2IAAAKW9PDT4VWLRX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2140 -s 1476 | C:\Windows\SysWOW64\WerFault.exe | — | CJ2IAAAKW9PDT4VWLRX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Local\Temp\57TYHCP43I6HBVGT6O137GQPA5MB6.exe" | C:\Users\admin\AppData\Local\Temp\57TYHCP43I6HBVGT6O137GQPA5MB6.exe | Setup.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Autostart program viewer Exit code: 1073807364 Version: 14.09 Modules
| |||||||||||||||
| 2040 | "C:\ProgramData\Fidl\Clus-Blue.exe" | C:\ProgramData\Fidl\Clus-Blue.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2084 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2140 -s 732 | C:\Windows\SysWOW64\WerFault.exe | — | CJ2IAAAKW9PDT4VWLRX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 157
Read events
18 084
Write events
49
Delete events
24
Modification events
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Setup.exe.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF350100002E000000F504000017020000 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
33
Suspicious files
58
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4300 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4300.17283\Setup.exe | — | |
MD5:— | SHA256:— | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Qt5Core.dll | executable | |
MD5:5AF1A8D3E720C2ECD7C835510429DA9F | SHA256:45A830C44F93ABA5658E5E9697DE42B3F3EB383BBBF174ADE65A78F9A6C7D8B2 | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\msvcr120.dll | executable | |
MD5:AEB29CCC27E16C4FD223A00189B44524 | SHA256:D28C7AB34842B6149609BD4E6B566DDAB8B891F0D5062480A253EF20A6A2CAAA | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Qt5Xml.dll | executable | |
MD5:EFEE87118A310EDB82A7A6AEEBAEC1C1 | SHA256:0A6D4E2FB47E8DB1D35EA70D66D40097469CBF61979FD10AA2BEB44A6CA06324 | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Qt5Gui.dll | executable | |
MD5:72AC63E9E9F015D6471DDE58297A4FC6 | SHA256:6B8A49B6B37D69213762C8F2C8A9970014364F4055F08A850D27C0343FBE00DE | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Qt5Widgets.dll | executable | |
MD5:2BD07ACEF2FFD5AD8388B714D4F81995 | SHA256:250C3717663E4AB3CE50E4A53BC532BF0C0850D2917773DD7E482E733081A1A1 | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\libcrypto-1_1-x64.dll | executable | |
MD5:CF1DF078FA02C3F20A613FF9FACEEE46 | SHA256:0897F6EF6C7875F64ED82AD83473FD8EA119CFEAA959B0AB2B2F981C1DA7C679 | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Utility.dll | executable | |
MD5:48B0445F21B92190B1E199AD31F89CBC | SHA256:3094FB377E55EF2DEAE50B6C350EA2B6D37FD098D75CD3F874E5AF705A5BB3E8 | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Framework.dll | executable | |
MD5:2207332818329E3CE4E5E020BA1B1F04 | SHA256:C554A0BD610BA0B10D8D92BB588FC86893B59985E4ED9316D340781C482FCAA2 | |||
| 1280 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VQT9BQB43HR3XE24SN6BTT\Qt5Network.dll | executable | |
MD5:D73AA4F8749269D1590541E567387489 | SHA256:7BFDFED166846921DAB87D51CA9B338C1FDD7F96C117E3BA0EDC07ED06DD9CB1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
85
DNS requests
41
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6224 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2616 | ping.com | POST | 200 | 188.114.96.3:80 | http://tackleoutplayed.com/yLC6Ya9ut5bfTA/index.php | unknown | — | — | unknown |
2616 | ping.com | POST | 200 | 188.114.96.3:80 | http://tackleoutplayed.com/yLC6Ya9ut5bfTA/index.php | unknown | — | — | unknown |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6416 | Safari.exe | POST | 502 | 65.108.200.182:80 | http://65.108.200.182/metrika.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5344 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nodepathr.run |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (data-seed-prebsc-2-s1 .binance .org) |
2140 | CJ2IAAAKW9PDT4VWLRX.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (data-seed-prebsc-2-s1 .binance .org in TLS SNI) |
2616 | ping.com | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
2616 | ping.com | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
2616 | ping.com | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
2180 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (data-seed-prebsc-2-s1 .binance .org) |
6436 | asus_framework.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (data-seed-prebsc-2-s1 .binance .org in TLS SNI) |
6740 | ping.com | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6740 | ping.com | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
6740 | ping.com | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |