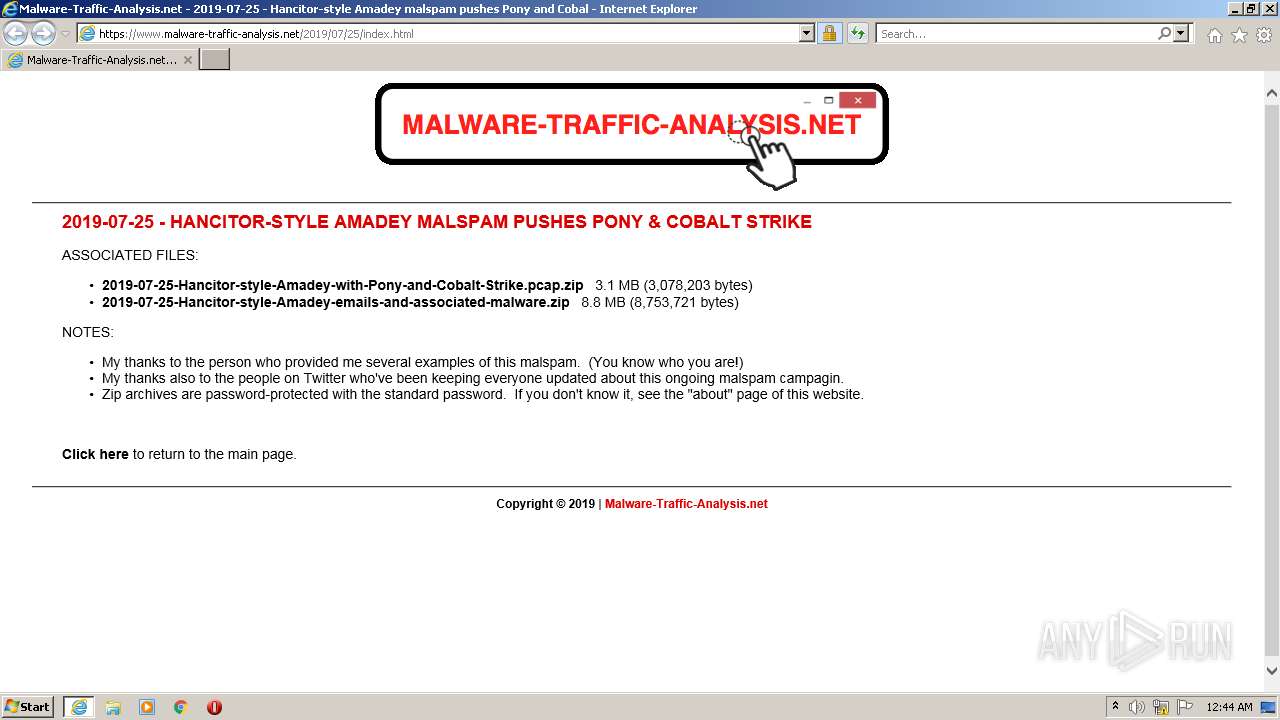
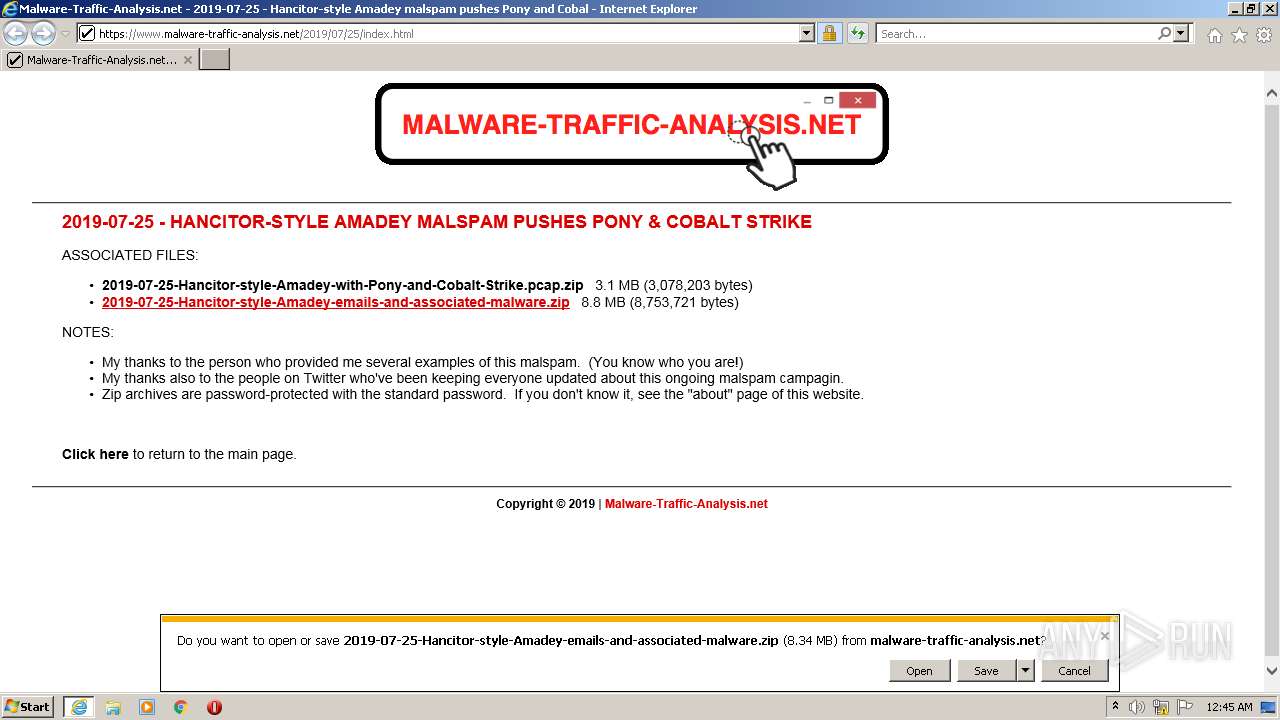
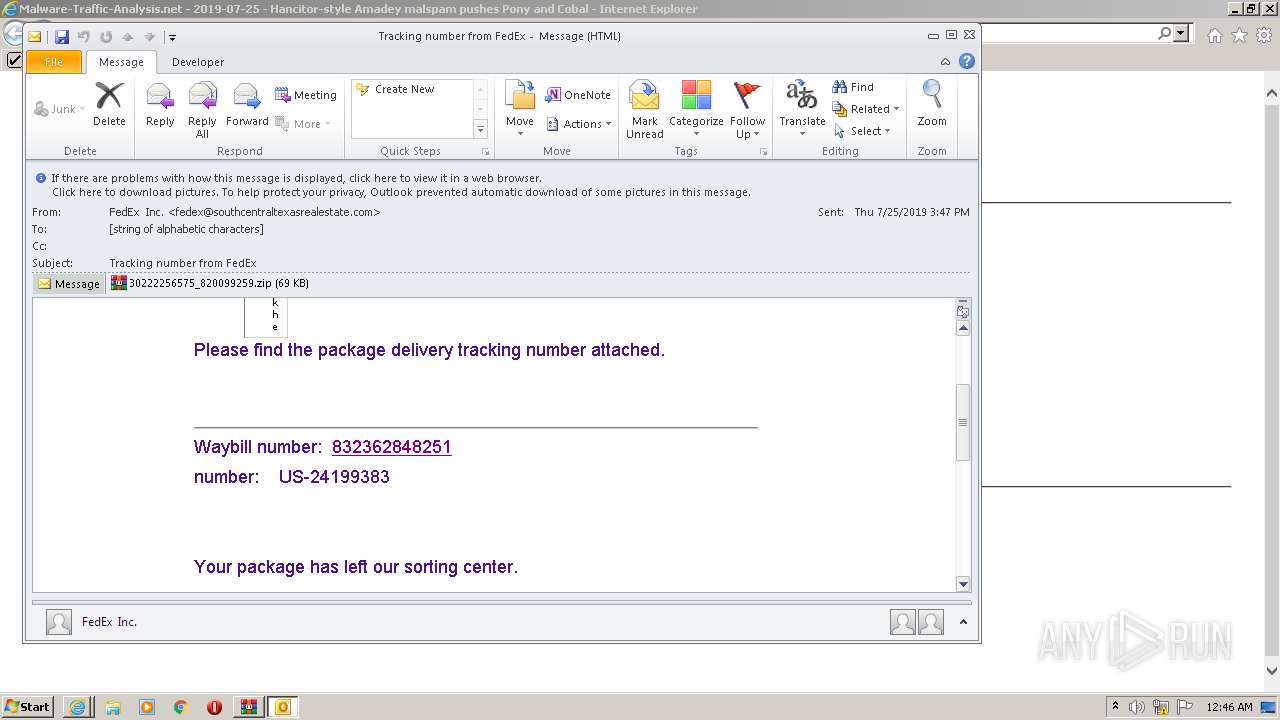
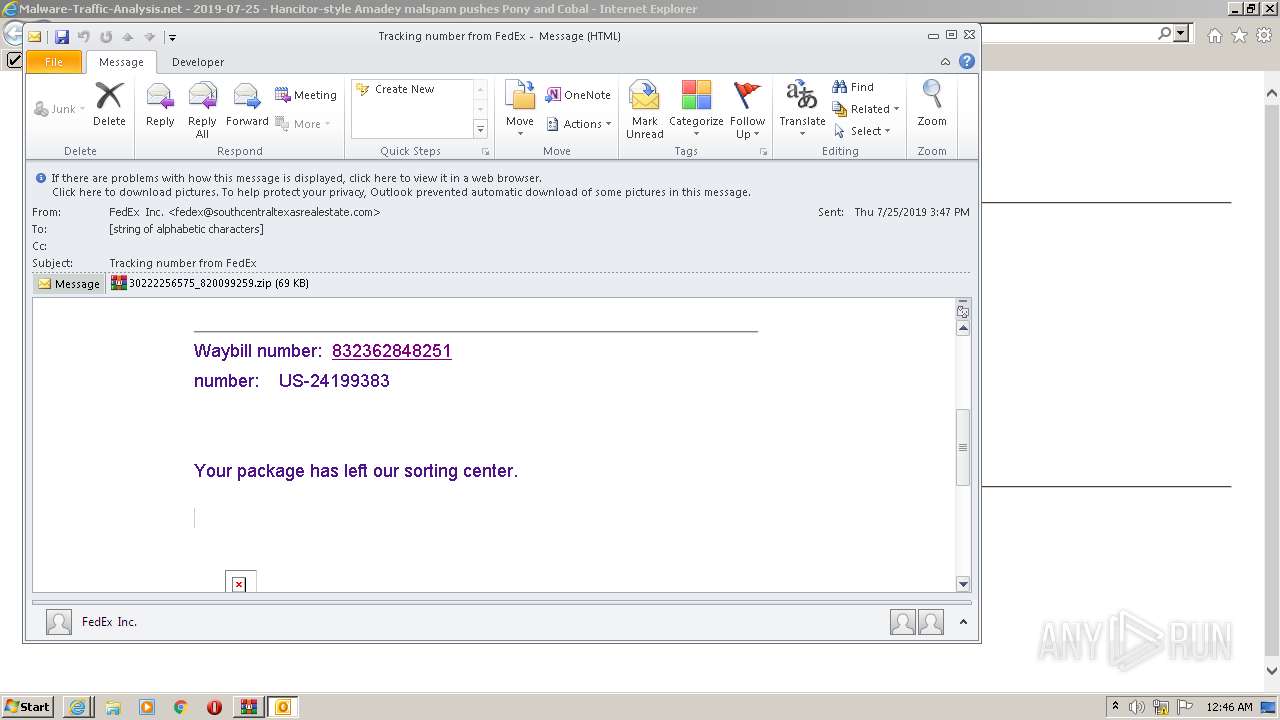
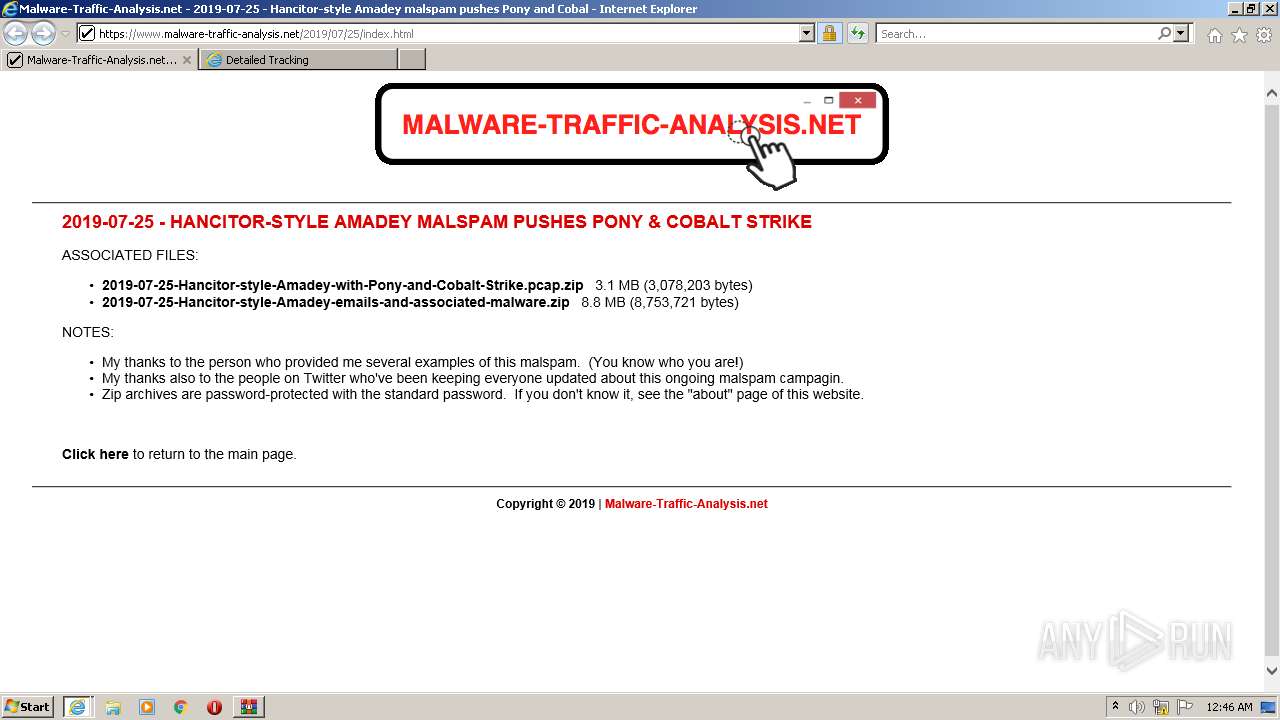
| URL: | https://www.malware-traffic-analysis.net/2019/07/25/index.html |
| Full analysis: | https://app.any.run/tasks/605450af-86c3-4beb-803e-66fee7559738 |
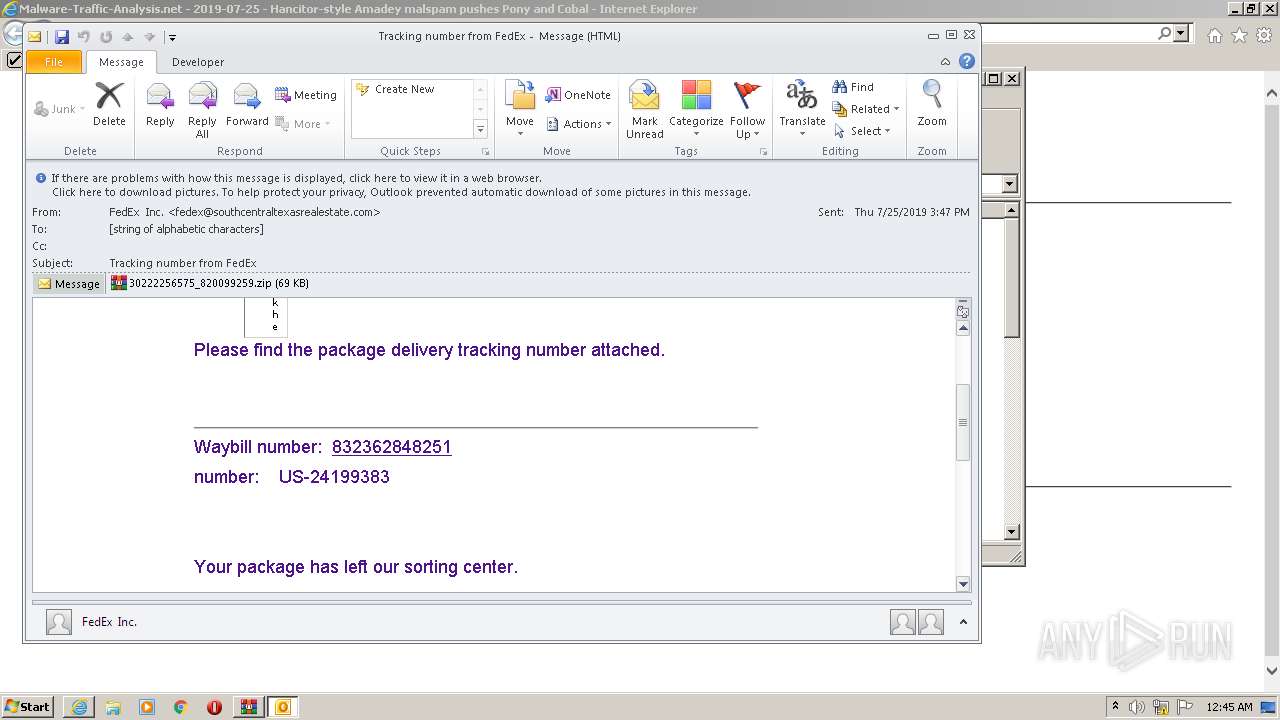
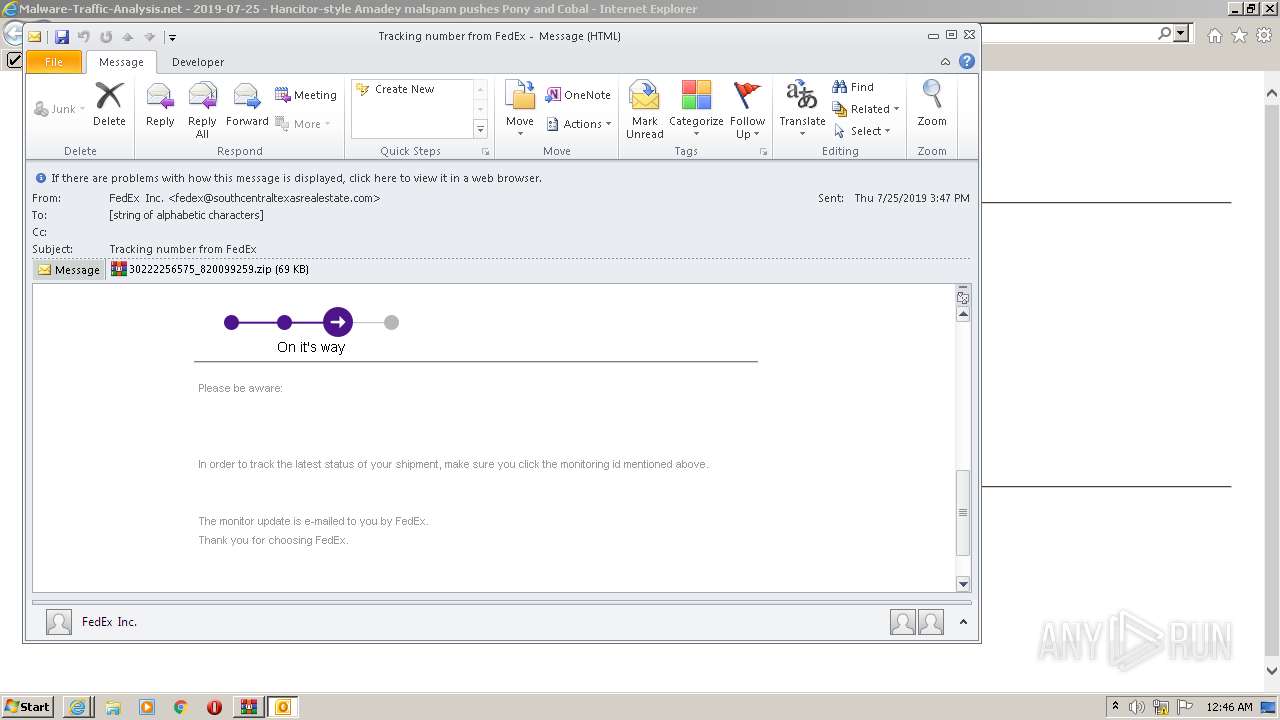
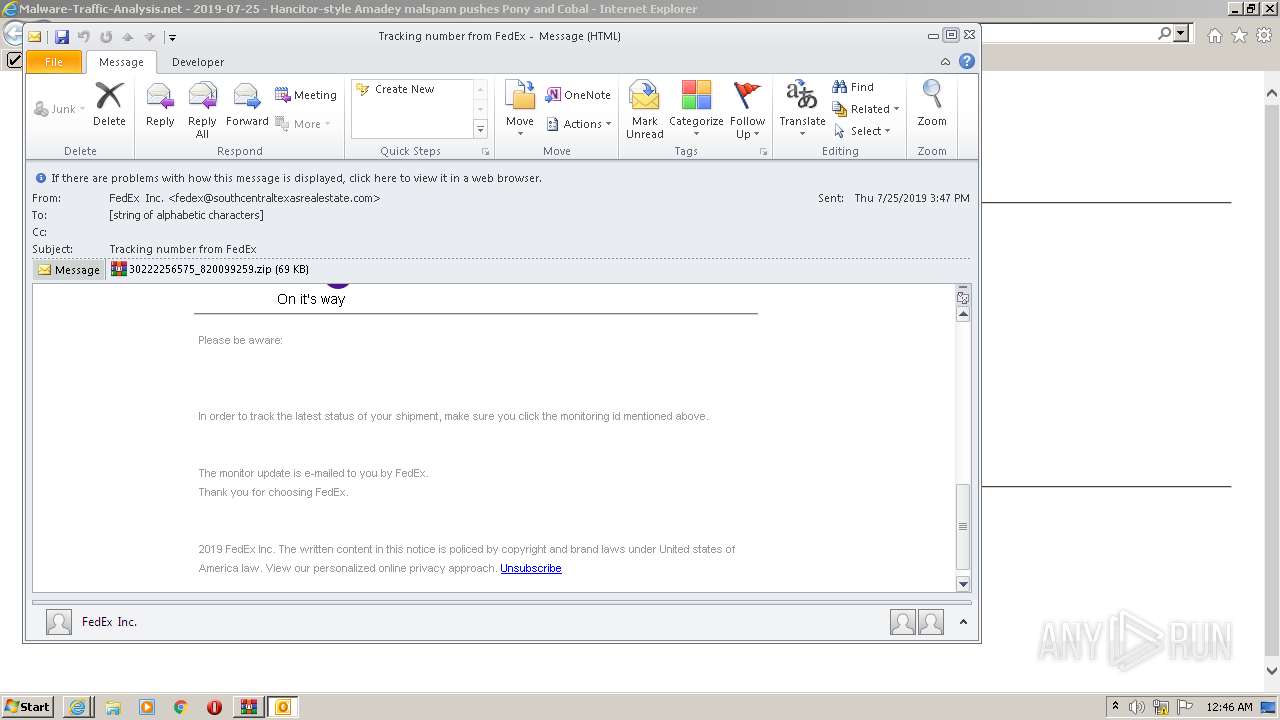
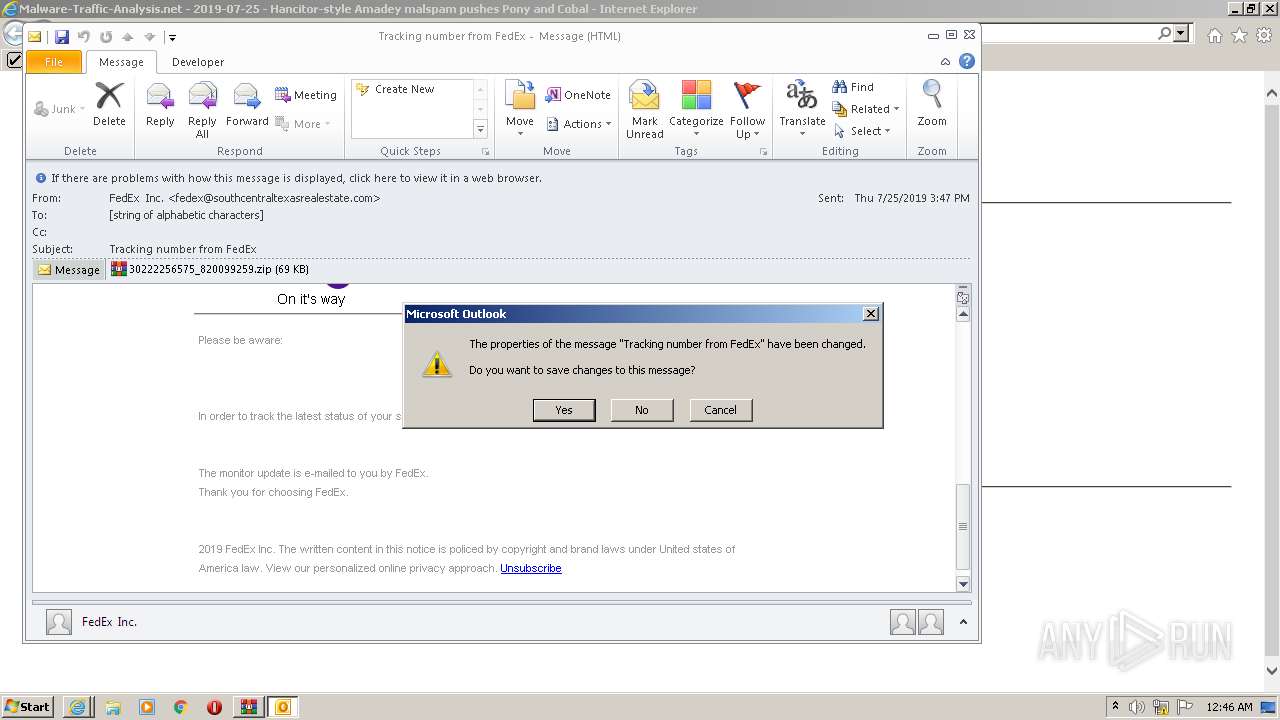
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 20, 2022, 23:44:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1673053A13F4B442EA718BACF47D6418 |
| SHA1: | 2D76416AA5C6CB180E6B410DE3FC7B616FA495BF |
| SHA256: | 7ECEFA55F3DA3742646BD054EA05B6938BDF9CED5FDEE38251223CE5FB98D785 |
| SSDEEP: | 3:N8DSLHXWQfigcWMMLA2BKAXG5G:2OLHpJY0X8G |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 968)
- WScript.exe (PID: 668)
- XLYHZCq.exe (PID: 3364)
Application was dropped or rewritten from another process
- 2019-07-25-Cobalt-Strike-EXE-retrieved-by-Amadey-infected-host-art.exe (PID: 3324)
- XLYHZCq.exe (PID: 3364)
- kntd.exe (PID: 3616)
AMADEY was detected
- XLYHZCq.exe (PID: 3364)
Changes the Startup folder
- REG.exe (PID: 3572)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 968)
- OUTLOOK.EXE (PID: 2324)
- 2019-07-25-Cobalt-Strike-EXE-retrieved-by-Amadey-infected-host-art.exe (PID: 3324)
- WScript.exe (PID: 668)
- XLYHZCq.exe (PID: 3364)
- kntd.exe (PID: 3616)
- WinRAR.exe (PID: 2152)
Reads the computer name
- WinRAR.exe (PID: 968)
- OUTLOOK.EXE (PID: 2324)
- 2019-07-25-Cobalt-Strike-EXE-retrieved-by-Amadey-infected-host-art.exe (PID: 3324)
- WScript.exe (PID: 668)
- kntd.exe (PID: 3616)
- WinRAR.exe (PID: 2152)
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 968)
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 3340)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2324)
Searches for installed software
- OUTLOOK.EXE (PID: 2324)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 968)
- WScript.exe (PID: 668)
- XLYHZCq.exe (PID: 3364)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 968)
- WScript.exe (PID: 668)
- XLYHZCq.exe (PID: 3364)
Executes scripts
- WinRAR.exe (PID: 968)
Starts itself from another location
- XLYHZCq.exe (PID: 3364)
Creates files in the program directory
- XLYHZCq.exe (PID: 3364)
Uses REG.EXE to modify Windows registry
- kntd.exe (PID: 3616)
Application launched itself
- WinRAR.exe (PID: 968)
Executed via WMI
- XLYHZCq.exe (PID: 3364)
INFO
Checks supported languages
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3040)
- REG.exe (PID: 3572)
Reads the computer name
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3040)
Reads settings of System Certificates
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3040)
Changes internet zones settings
- iexplore.exe (PID: 2840)
Application launched itself
- iexplore.exe (PID: 2840)
Checks Windows Trust Settings
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3040)
- WScript.exe (PID: 668)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3040)
Changes settings of System certificates
- iexplore.exe (PID: 2840)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2840)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2840)
Creates files in the user directory
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3040)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3040)
- WinRAR.exe (PID: 968)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
11
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
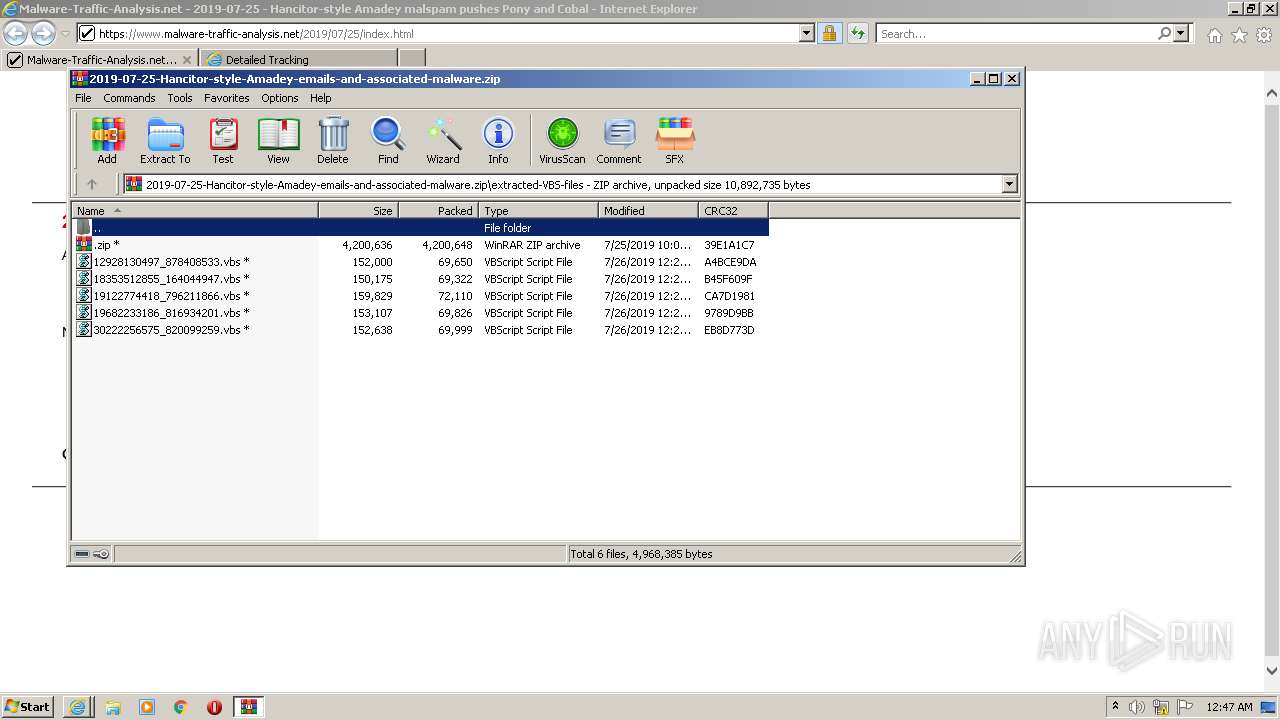
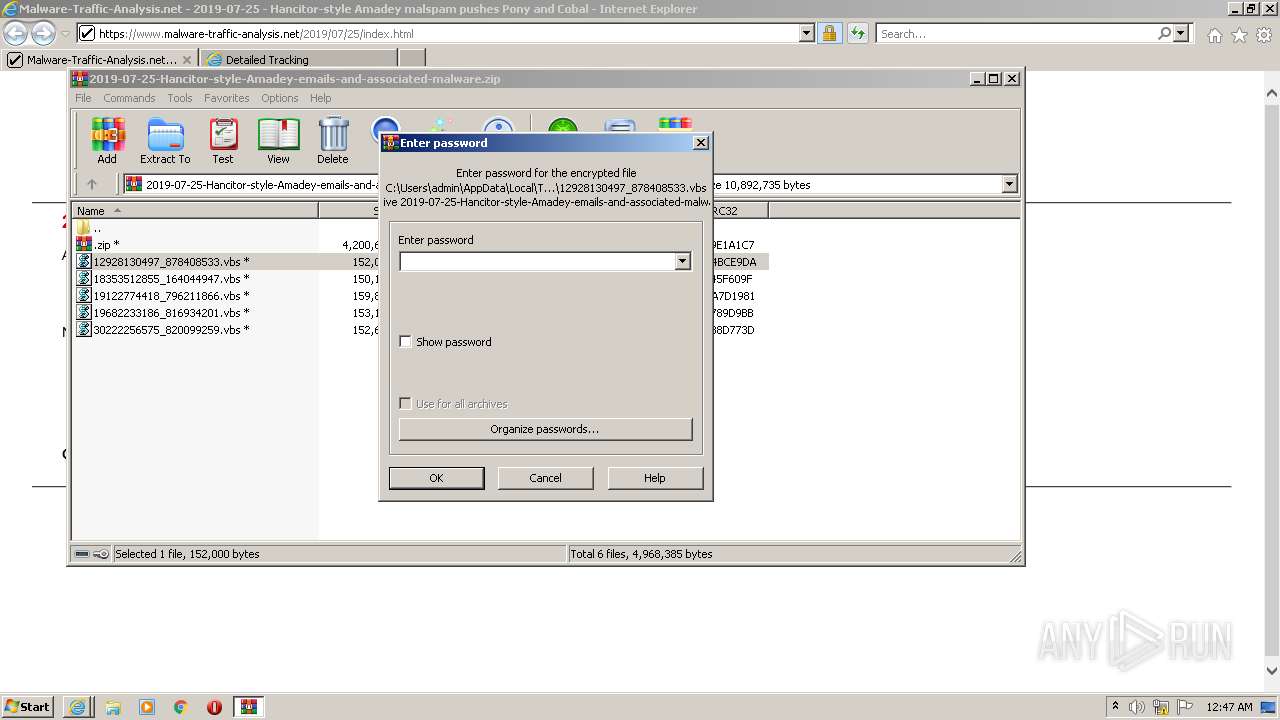
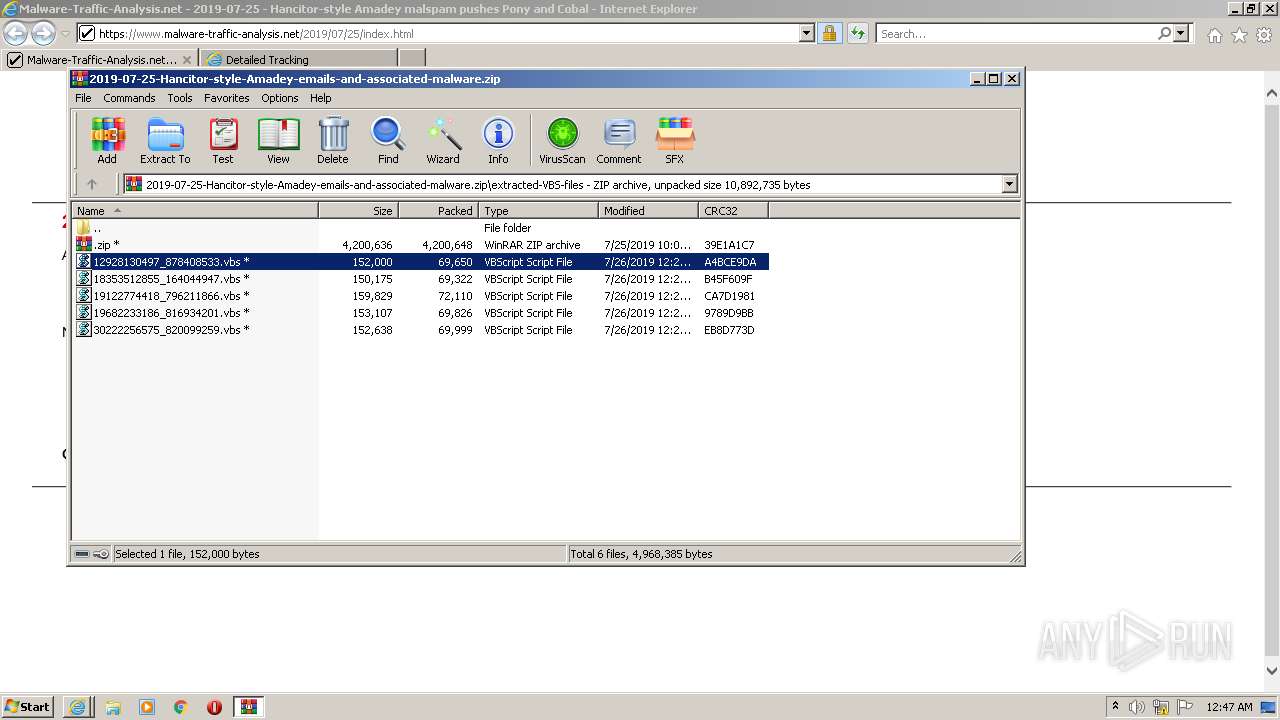
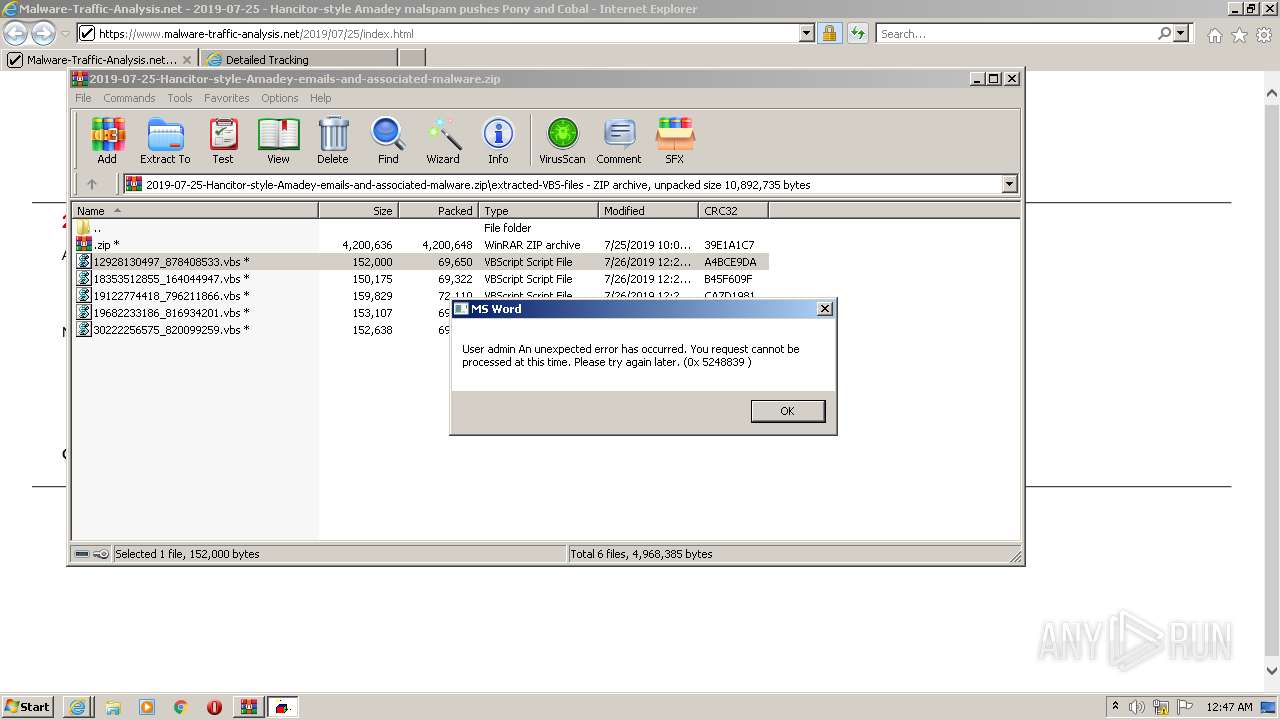
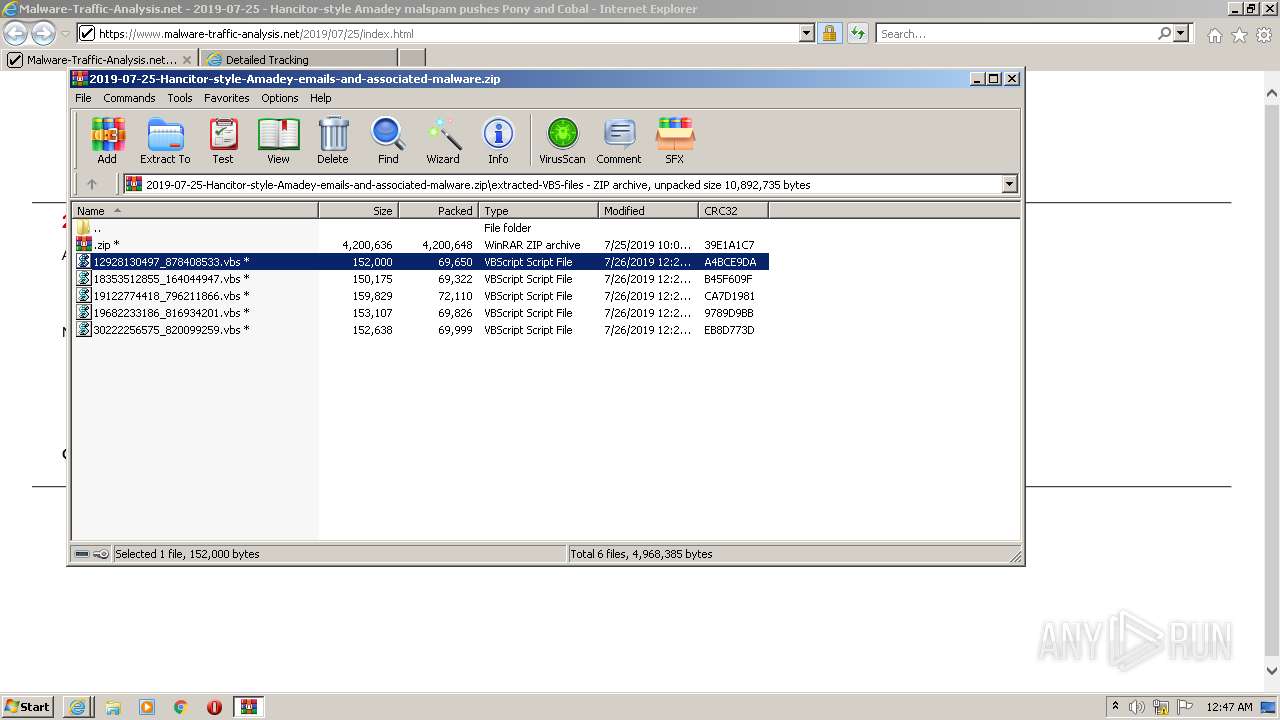
| 668 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb968.10392\12928130497_878408533.vbs" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
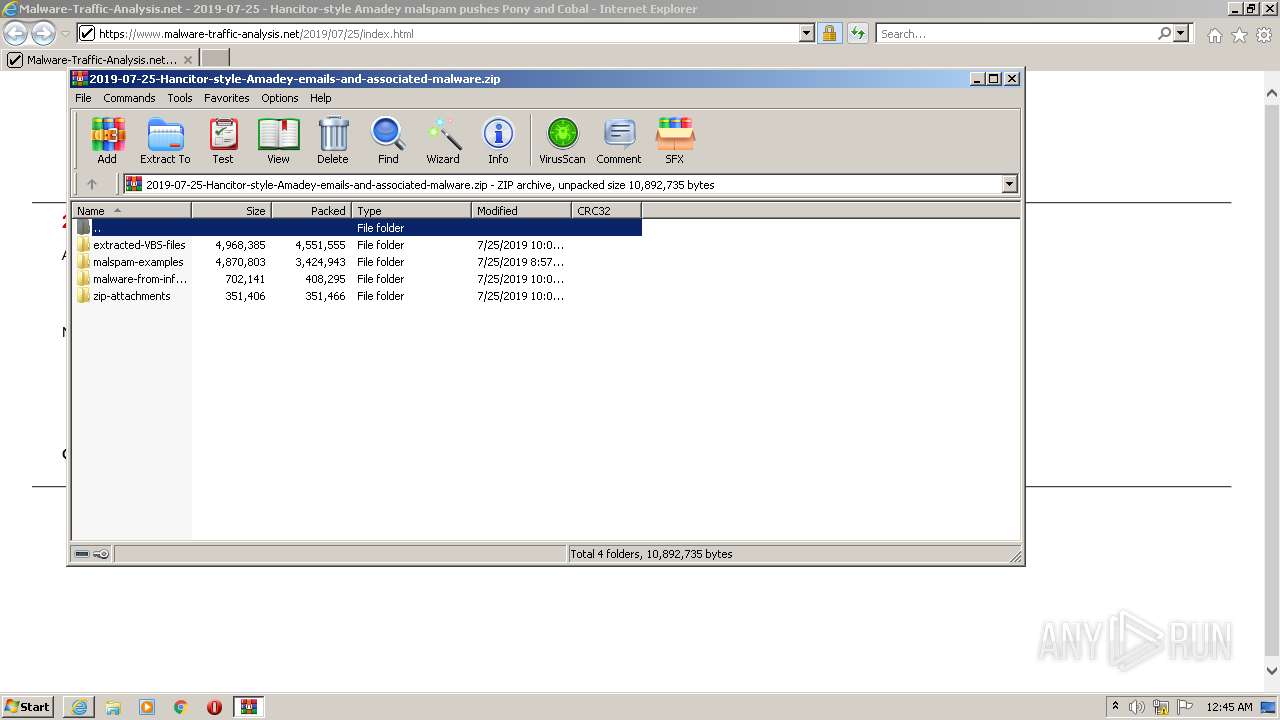
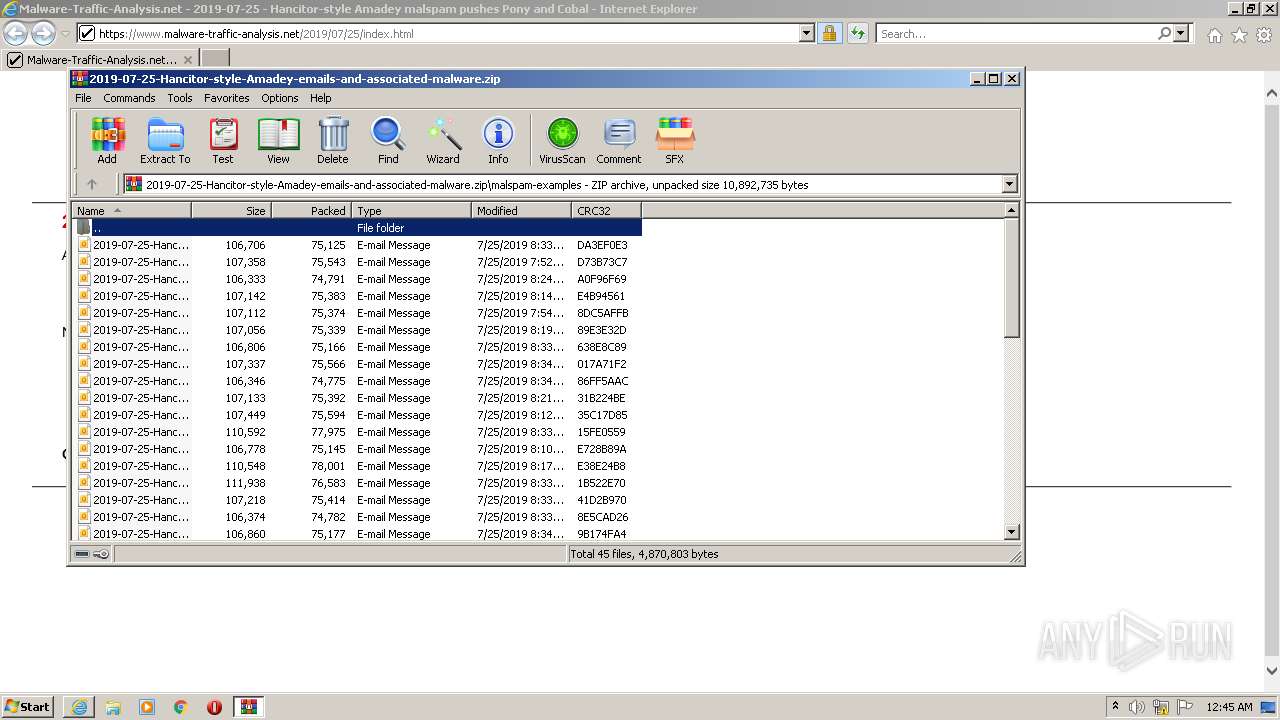
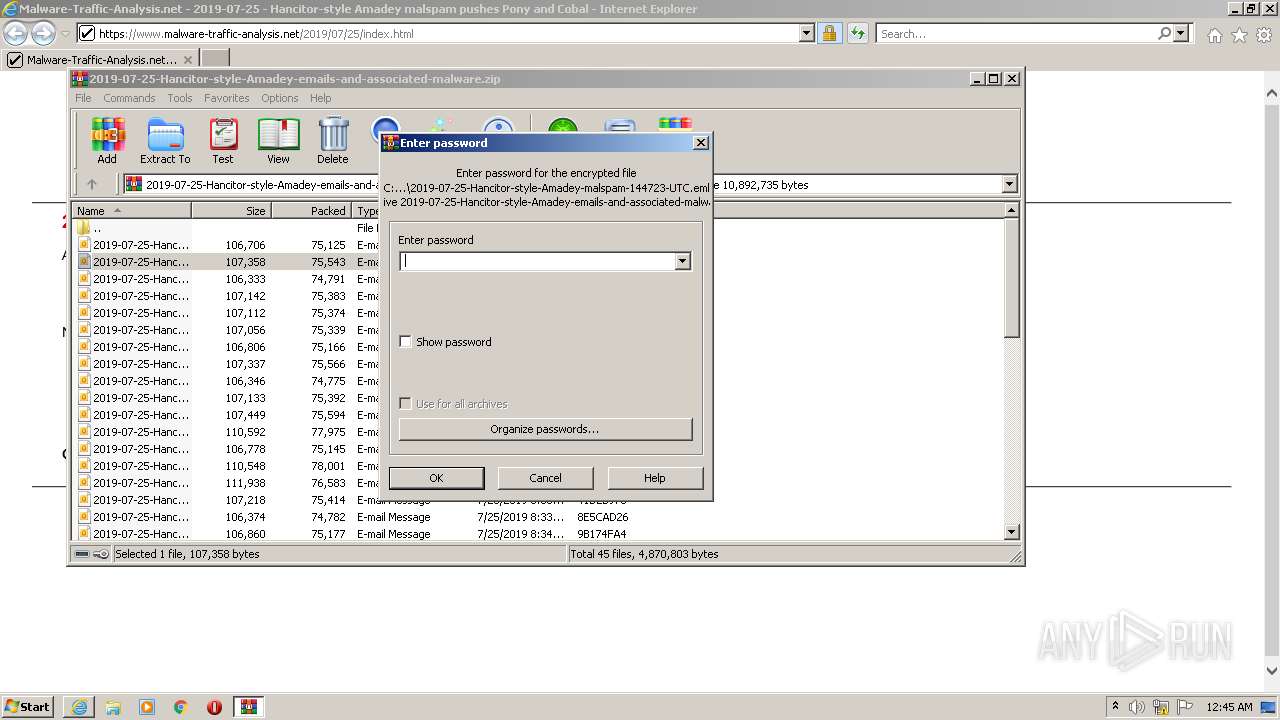
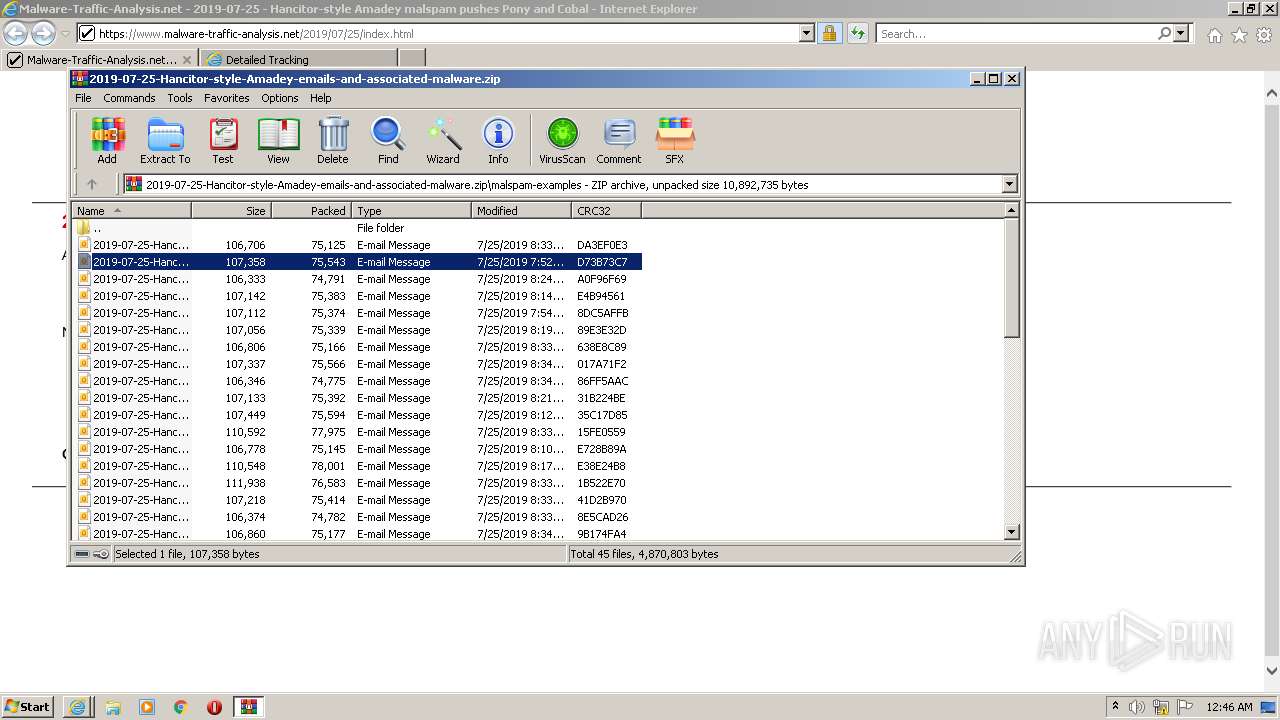
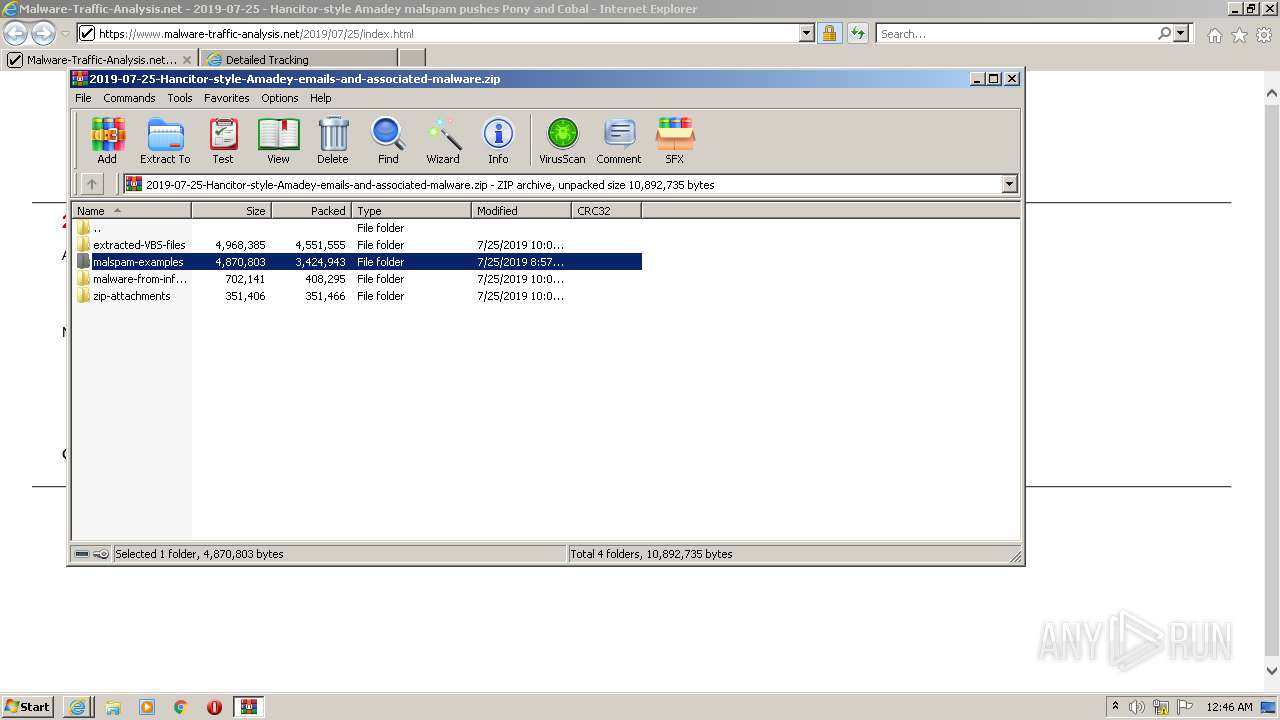
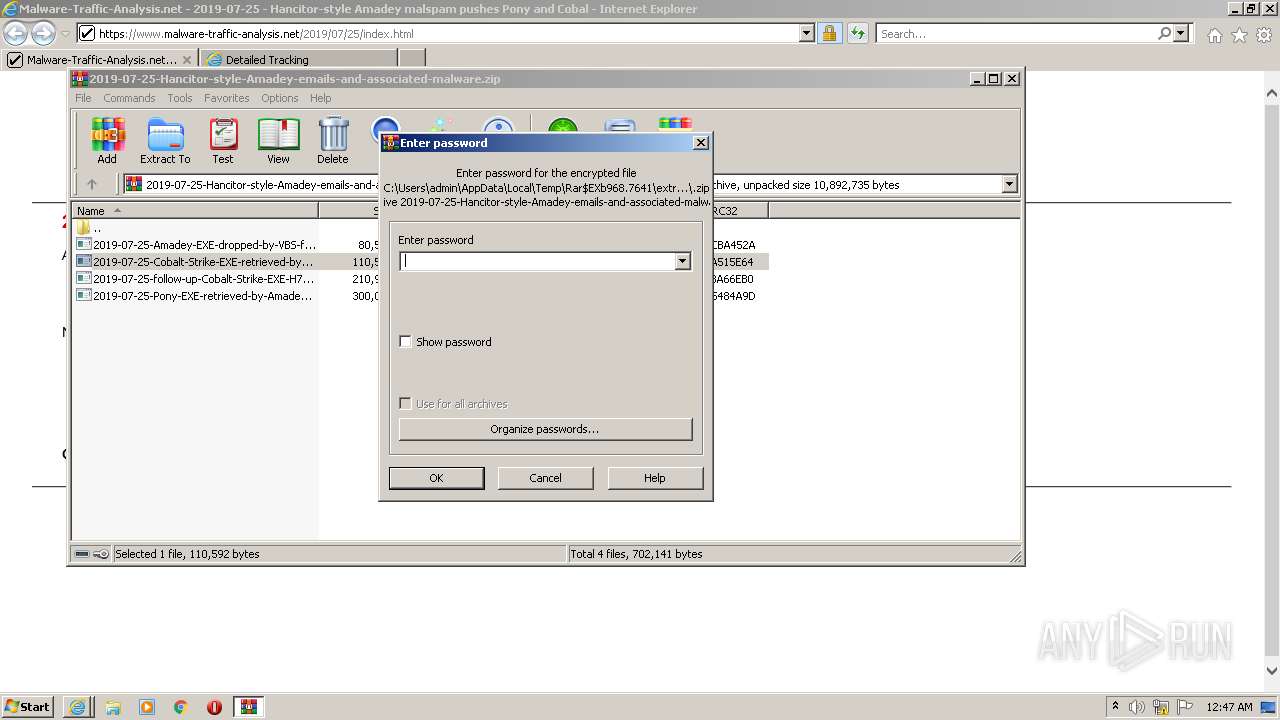
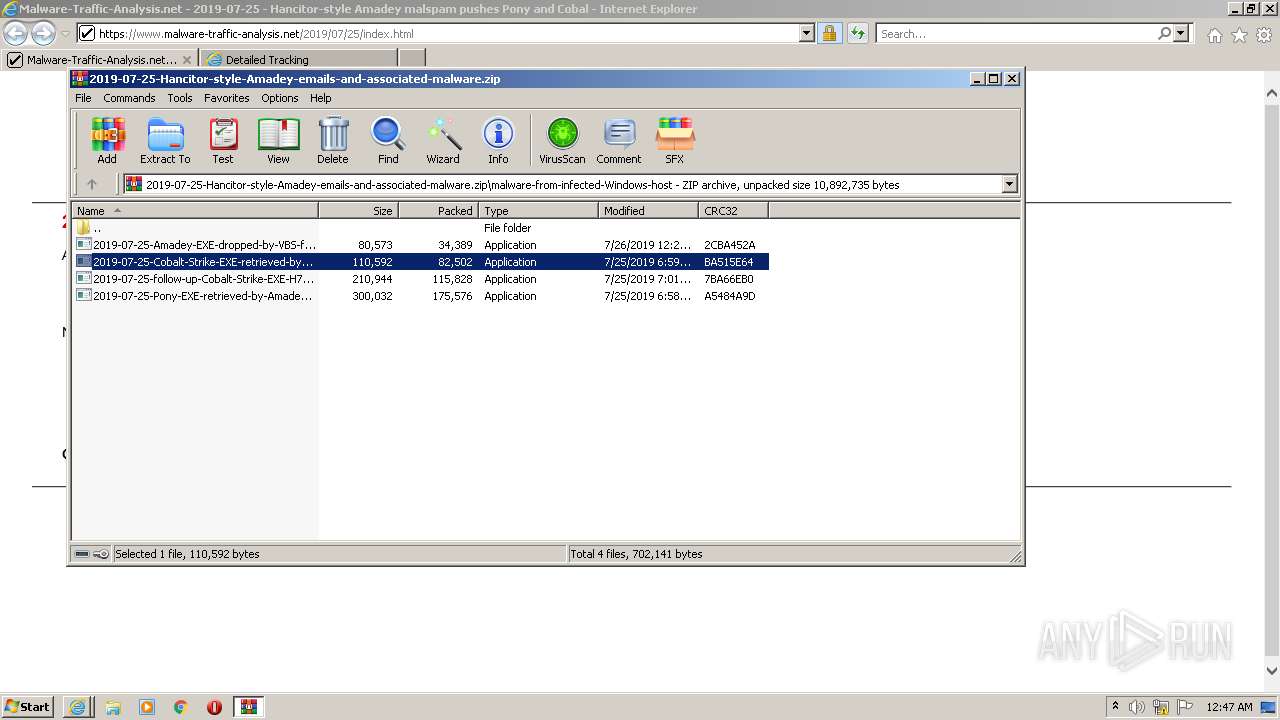
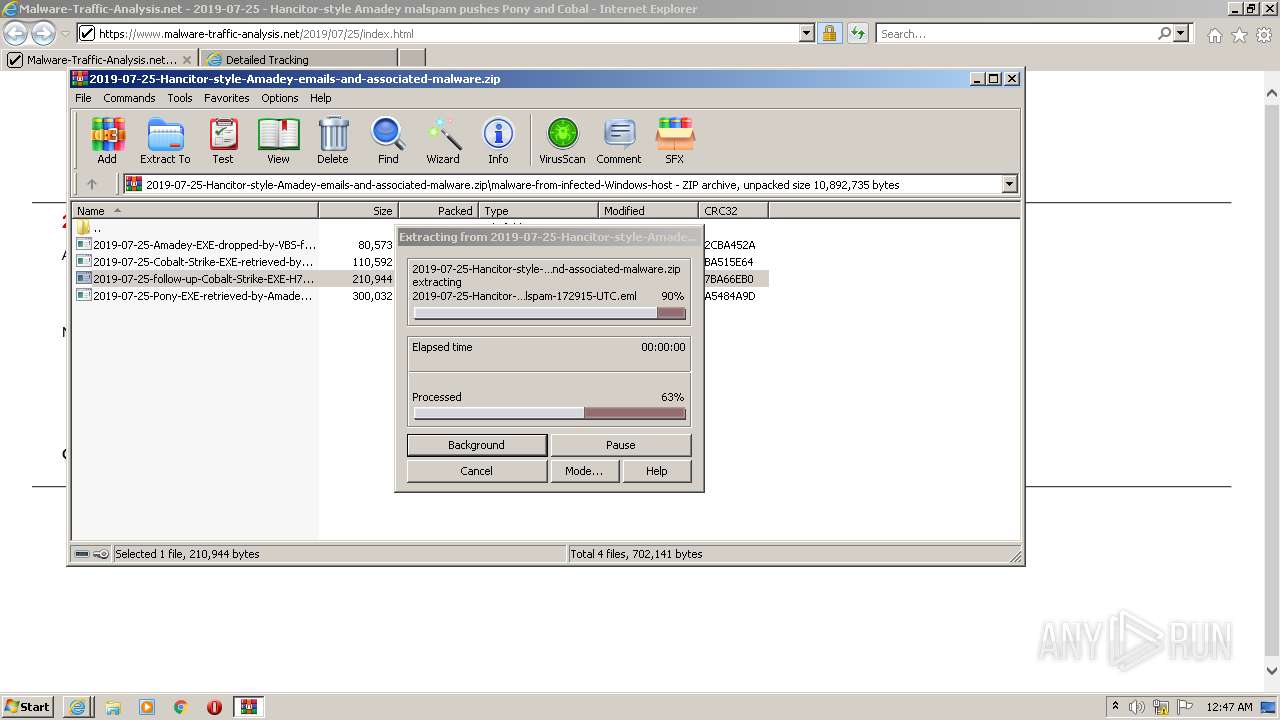
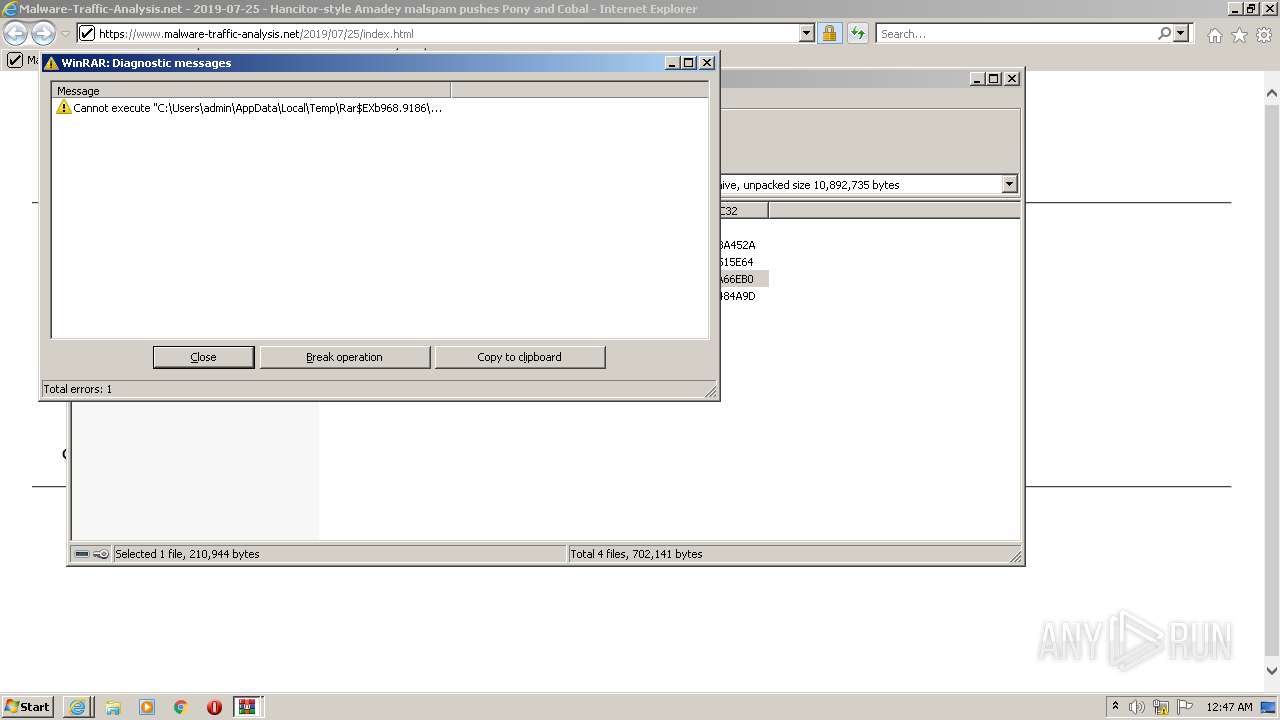
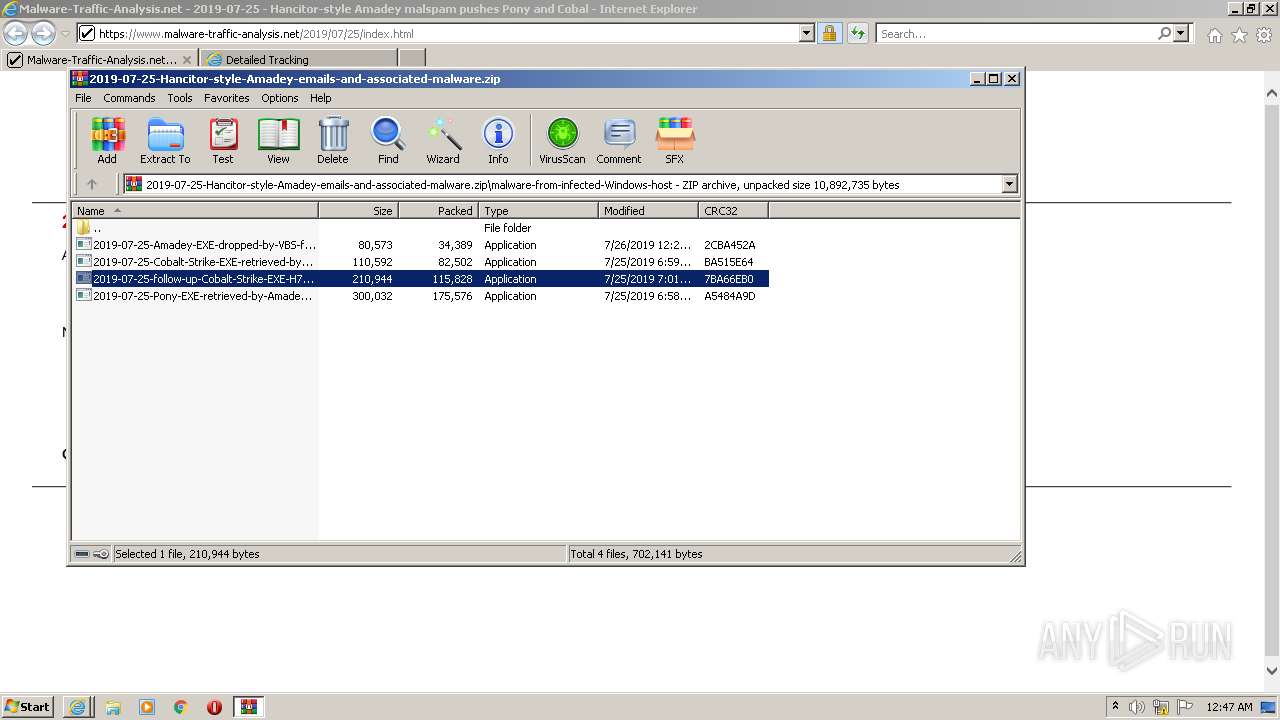
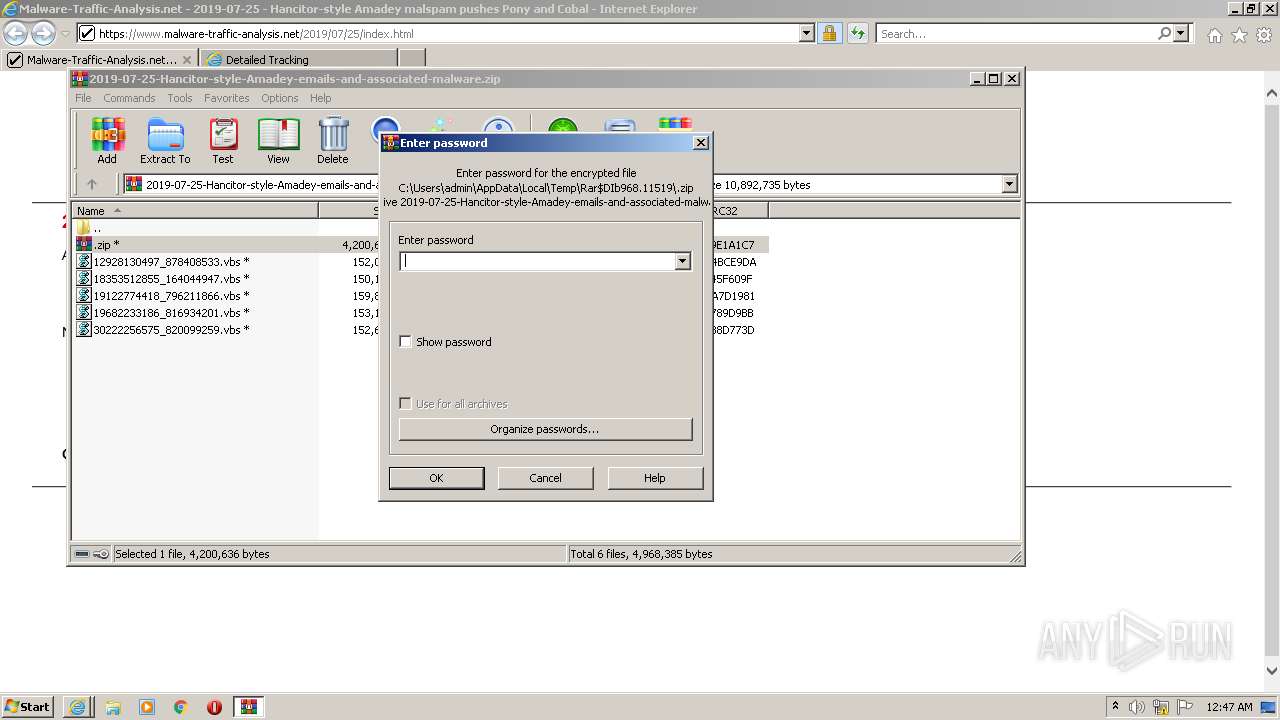
| 968 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\2019-07-25-Hancitor-style-Amadey-emails-and-associated-malware.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
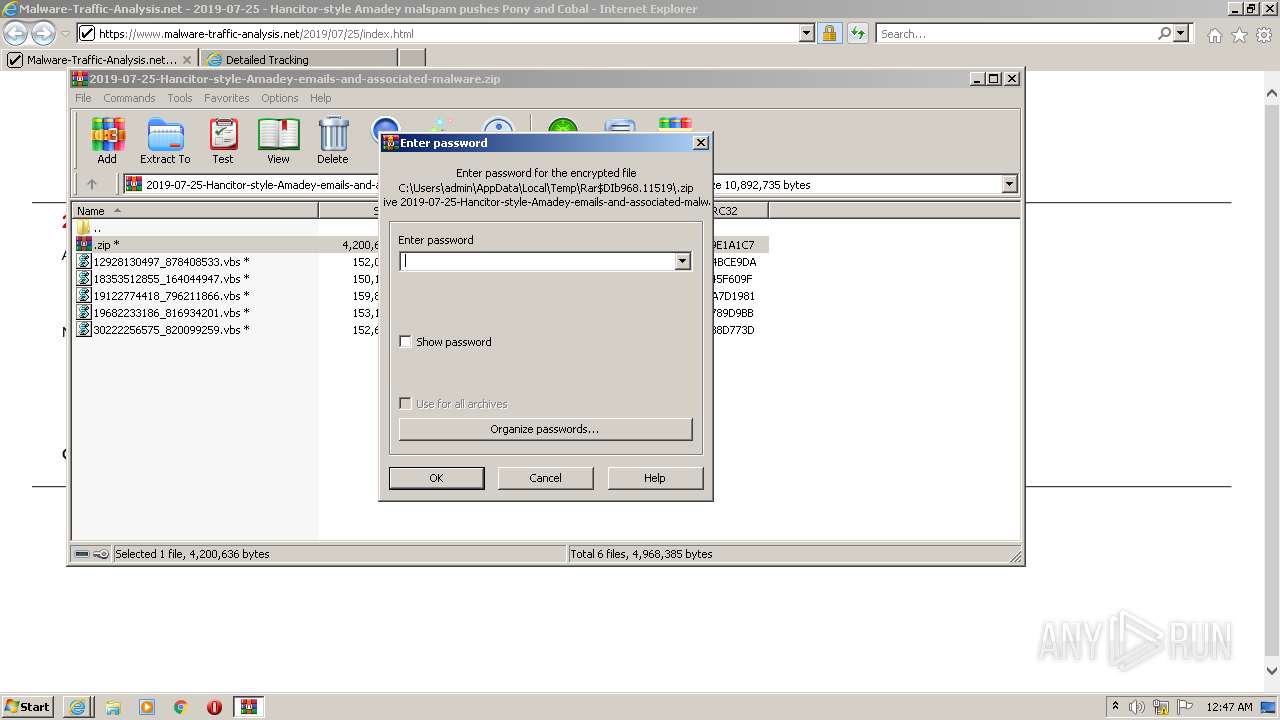
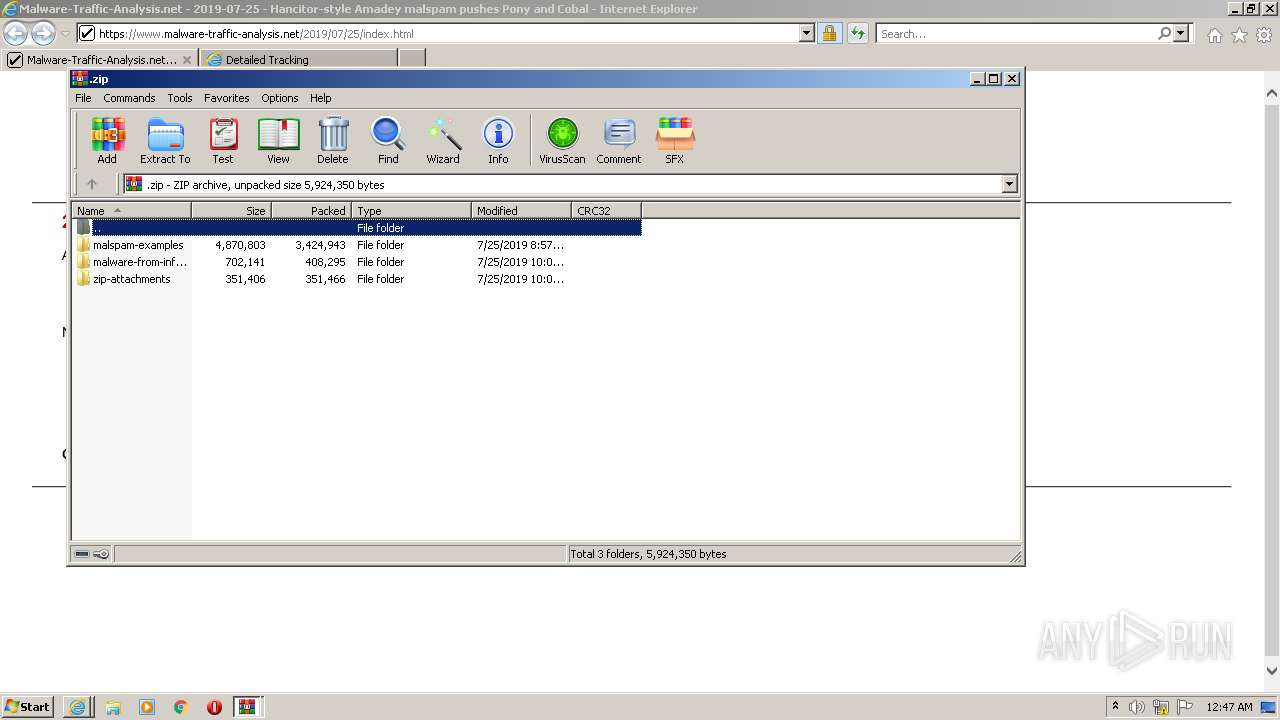
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb968.11519\.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
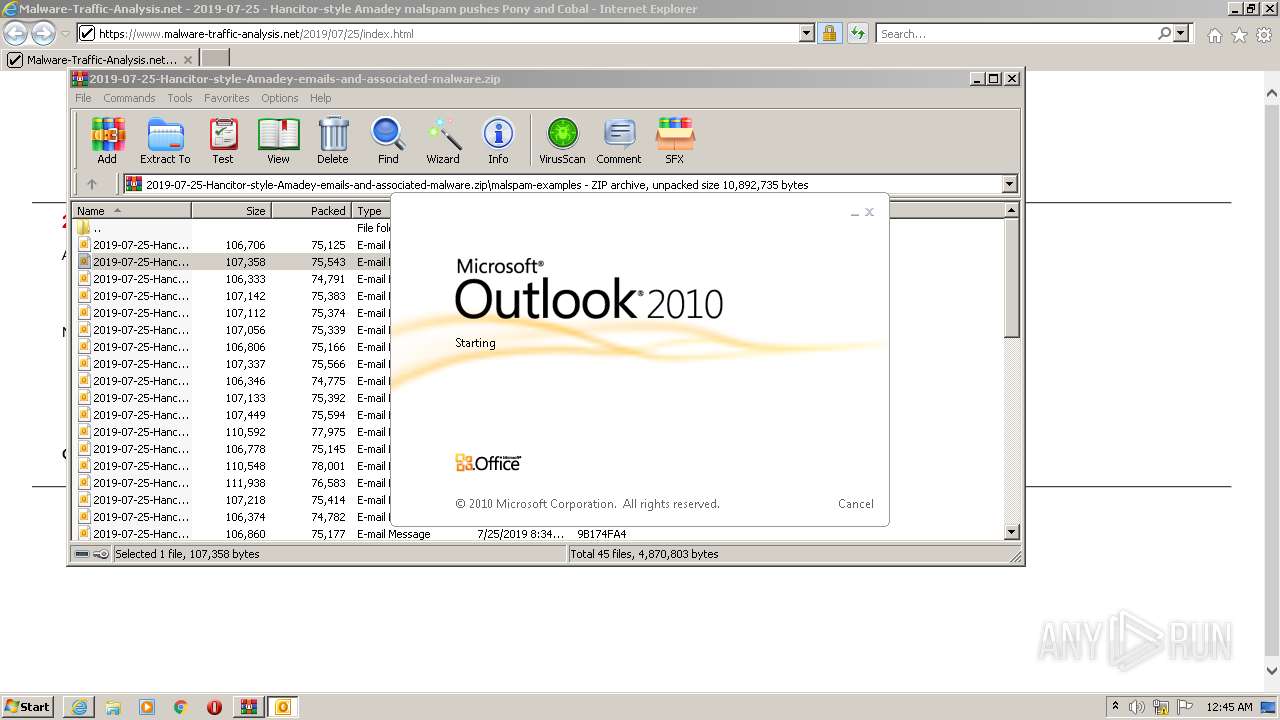
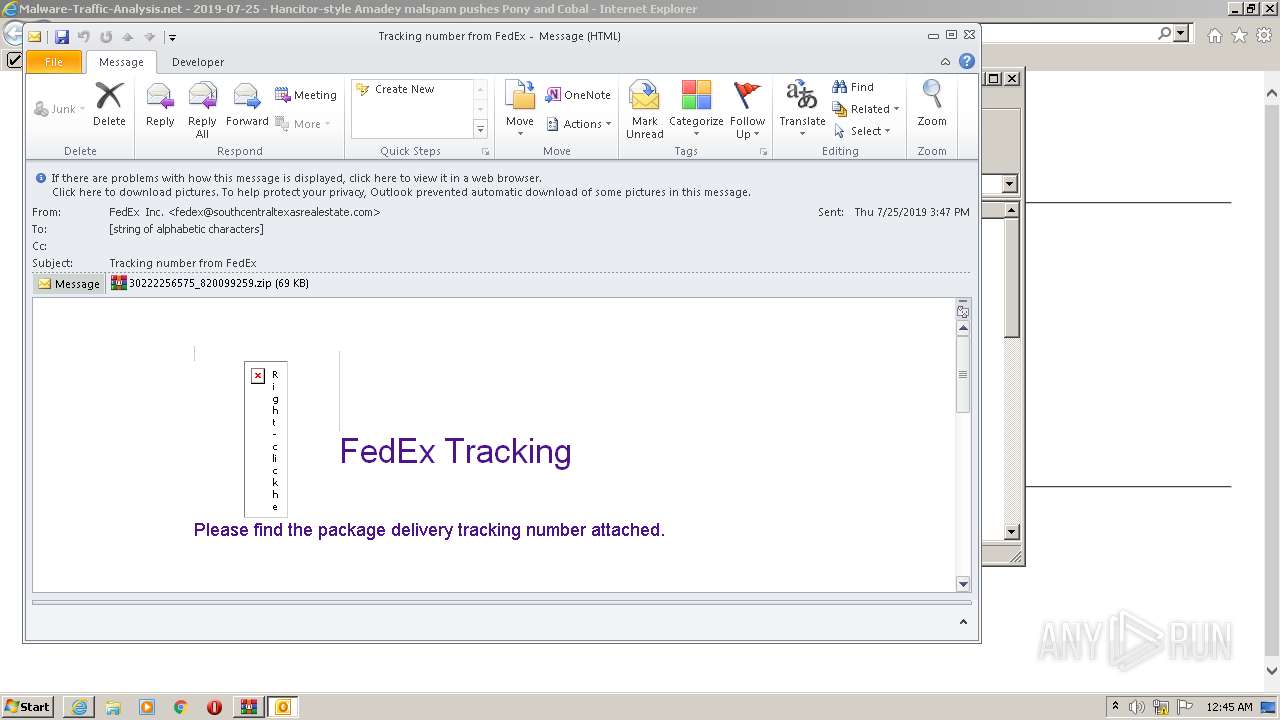
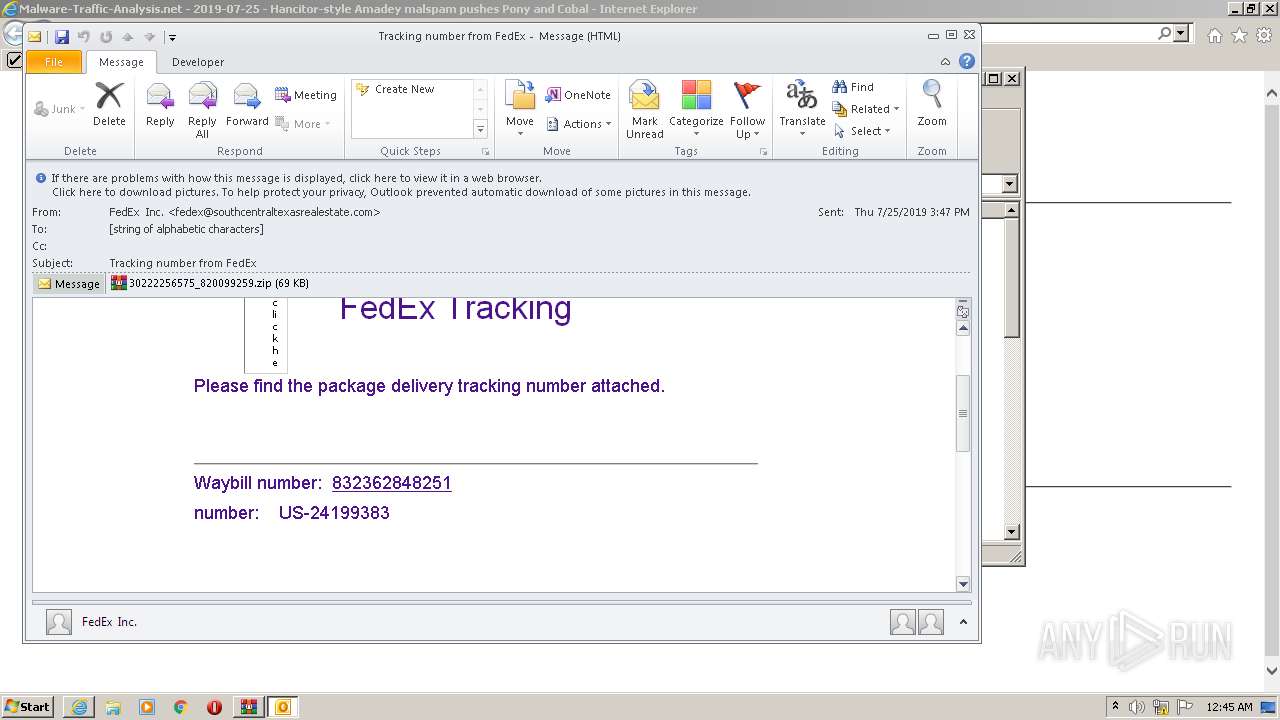
| 2324 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIb968.49466\2019-07-25-Hancitor-style-Amadey-malspam-144723-UTC.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.malware-traffic-analysis.net/2019/07/25/index.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:1643795 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
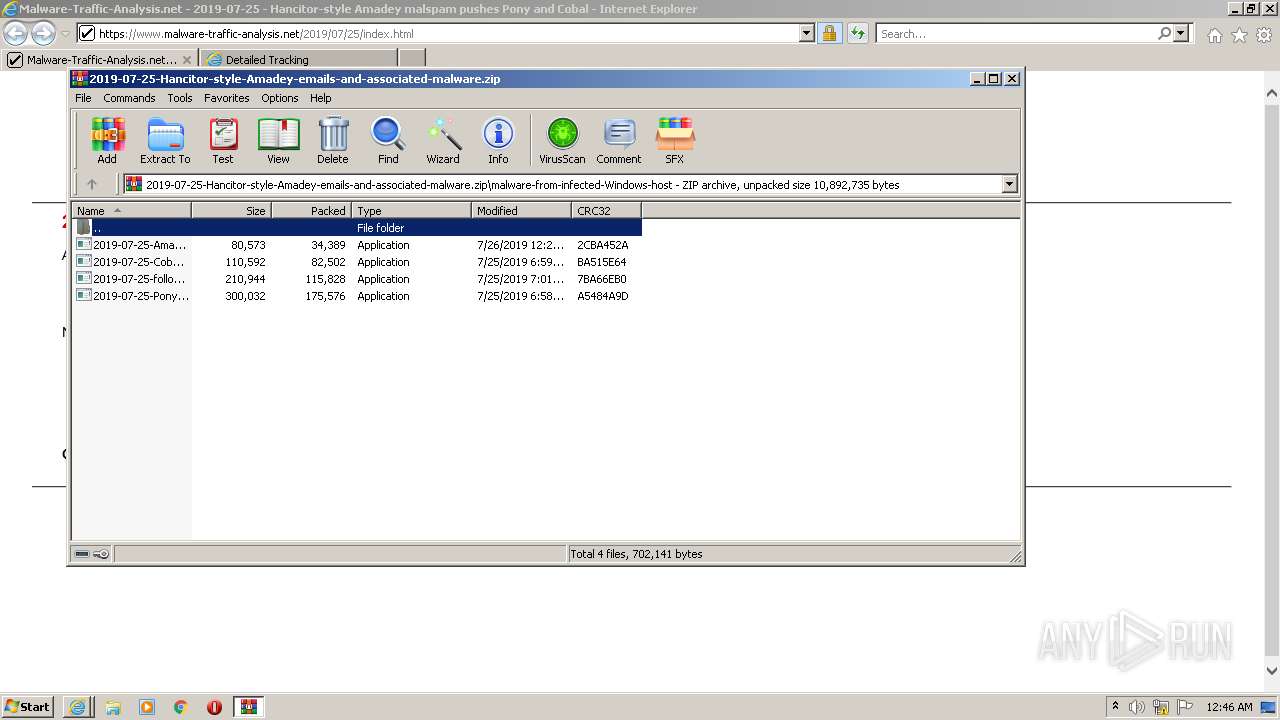
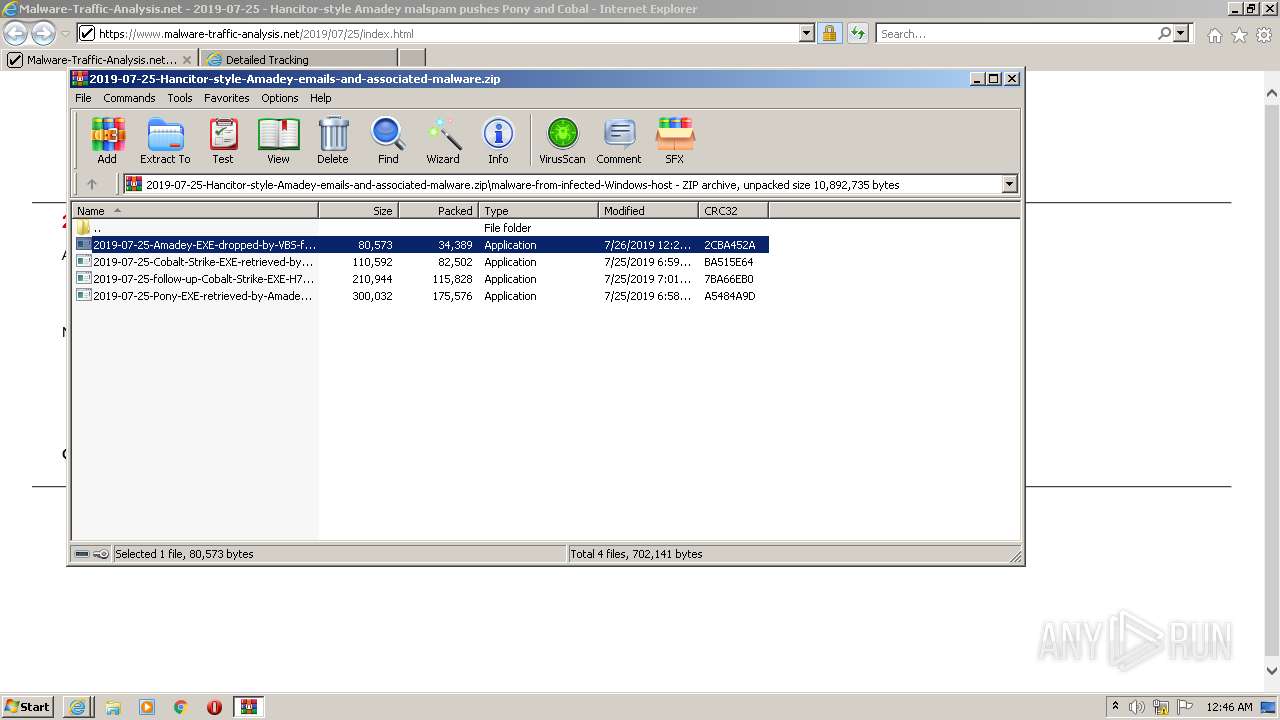
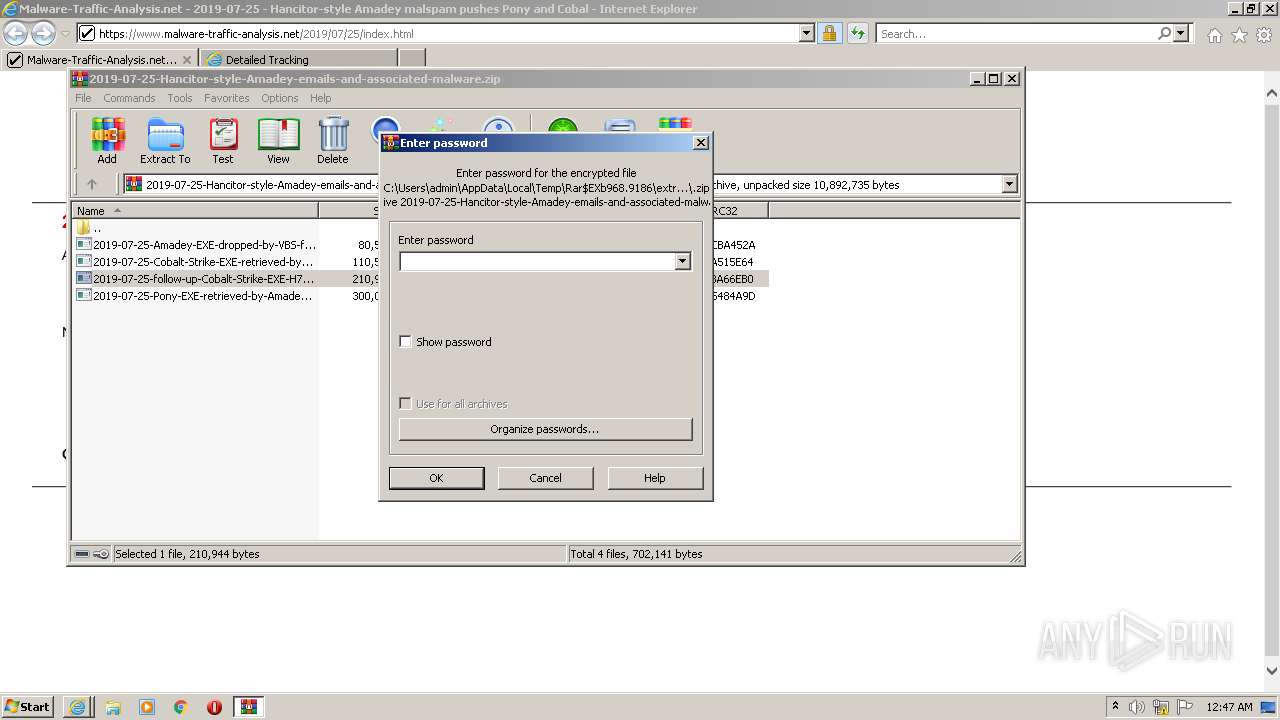
| 3324 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb968.7641\malware-from-infected-Windows-host\2019-07-25-Cobalt-Strike-EXE-retrieved-by-Amadey-infected-host-art.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb968.7641\malware-from-infected-Windows-host\2019-07-25-Cobalt-Strike-EXE-retrieved-by-Amadey-infected-host-art.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1768843639 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3364 | C:\Users\admin\AppData\Local\Temp\XLYHZCq.exe | C:\Users\admin\AppData\Local\Temp\XLYHZCq.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Creative Technology Limited Integrity Level: MEDIUM Description: ReadReg MFC Application Exit code: 0 Version: 2, 0, 0, 2 Modules
| |||||||||||||||
| 3572 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\d409470c6b | C:\Windows\system32\REG.exe | kntd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30 866
Read events
29 916
Write events
922
Delete events
28
Modification events
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960803 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960803 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
10
Suspicious files
49
Text files
122
Unknown types
120
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2A249A8EAE5FF8B677AA8B178688CF94 | der | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2A249A8EAE5FF8B677AA8B178688CF94 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
76
DNS requests
33
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2324 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3340 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3340 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECECrsM%2B7Sq5MOuq8mZpDVUKY%3D | US | der | 471 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3340 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2840 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2840 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b751281f24805fcb | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3340 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2840 | iexplore.exe | 199.201.110.204:443 | www.malware-traffic-analysis.net | Namecheap, Inc. | US | suspicious |
2840 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2840 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3340 | iexplore.exe | 199.201.110.204:443 | www.malware-traffic-analysis.net | Namecheap, Inc. | US | suspicious |
2840 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3040 | iexplore.exe | 95.101.22.144:443 | www.fedex.com | Akamai International B.V. | — | suspicious |
— | — | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3040 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3040 | iexplore.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.malware-traffic-analysis.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3040 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3040 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
2019-07-25-Cobalt-Strike-EXE-retrieved-by-Amadey-infected-host-art.exe | G8xv |
XLYHZCq.exe | zI |
kntd.exe | zI |