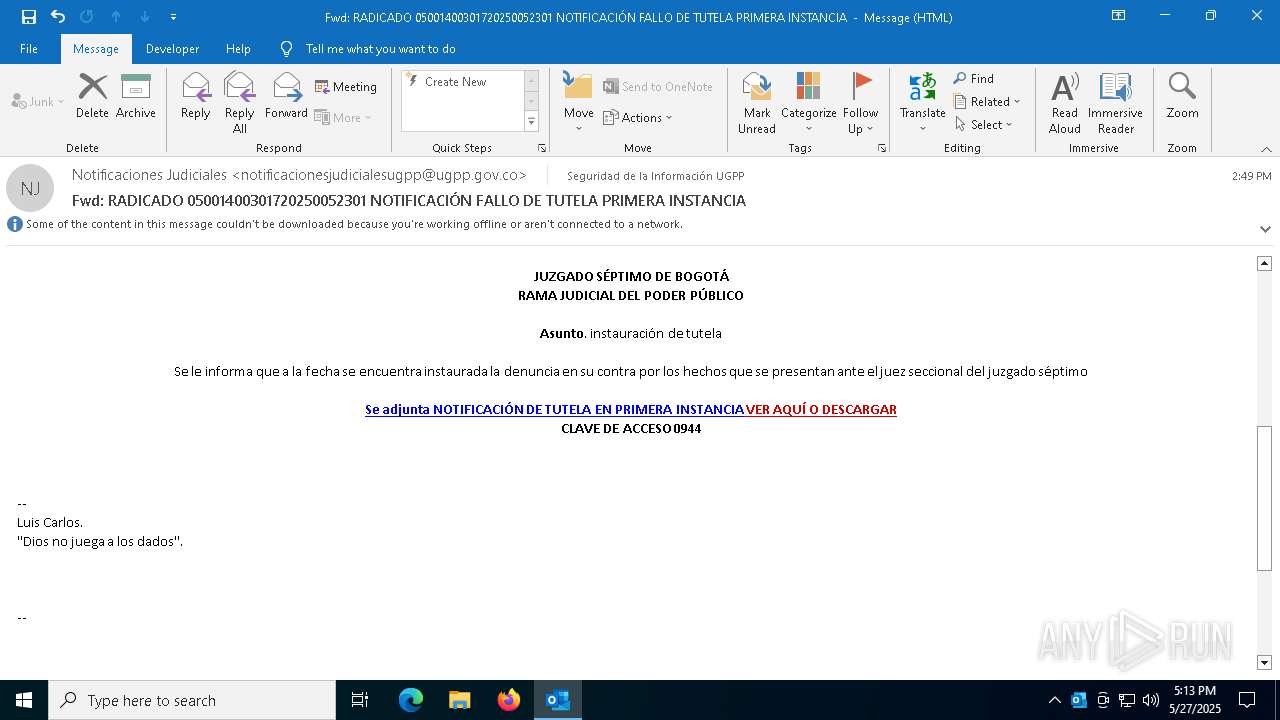
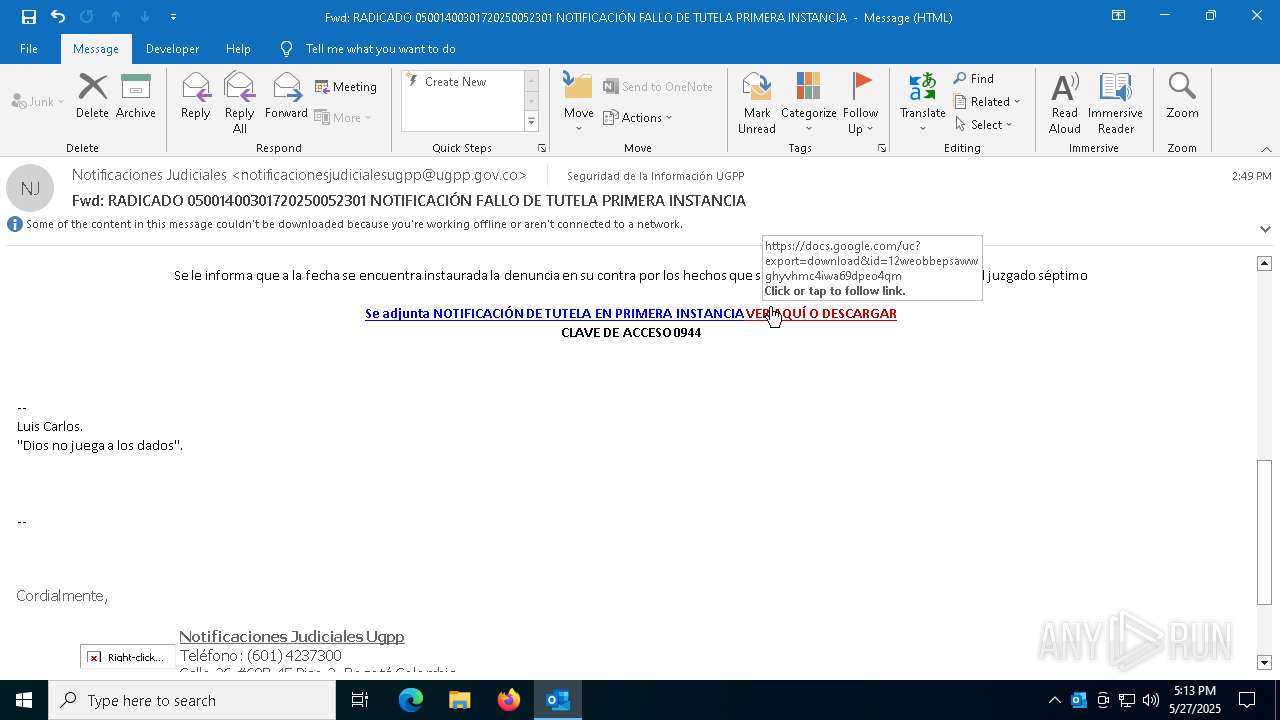
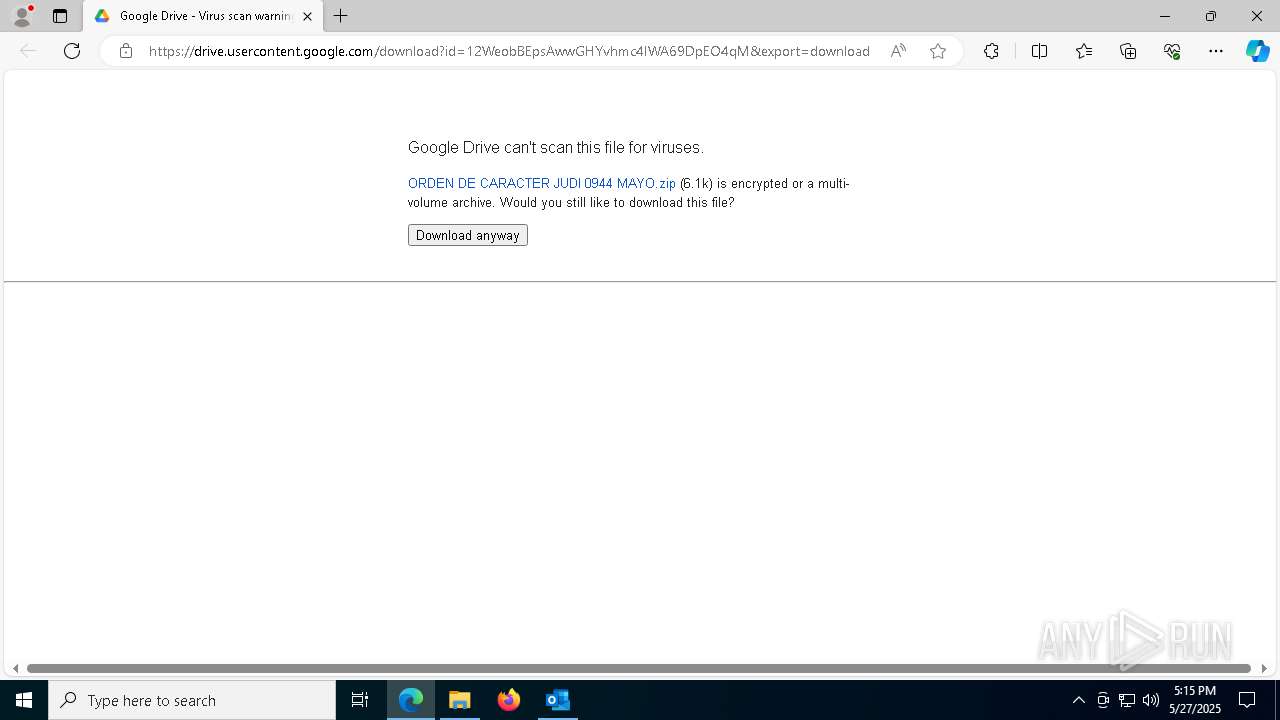
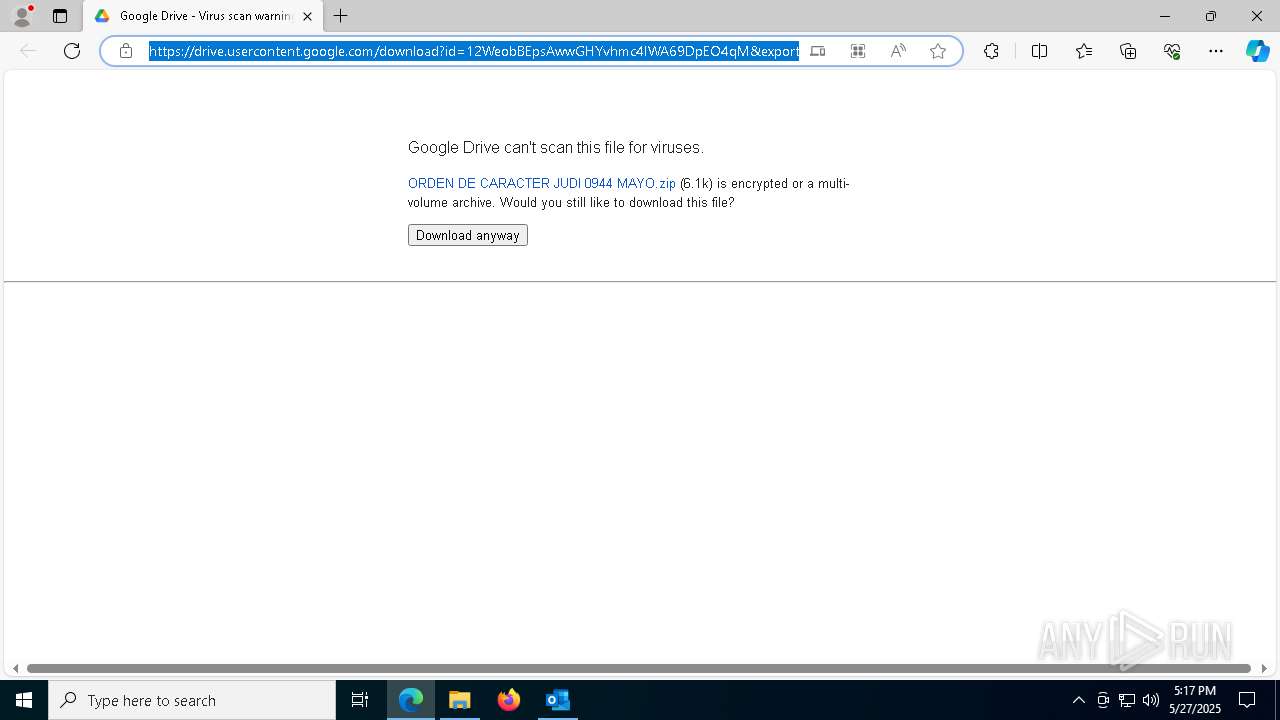
| File name: | RADICADO 05001400301720250052301 NOTIFICACIÓN FALLO DE TUTELA PRIMERA INSTANCIA.eml |
| Full analysis: | https://app.any.run/tasks/93e6151b-bb1a-4255-bdfb-9bf11738222b |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 27, 2025, 17:13:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text, with CRLF line terminators |
| MD5: | 26B98E3E18B7AEF9ED6D02B87EB9D055 |
| SHA1: | 756E7624E45B9D5E8ED743491589C076B81F45D1 |
| SHA256: | 7EC75804356C63D574DF140D8B4854FB355D8F1D7514B8D83D2A8E820D569E34 |
| SSDEEP: | 768:RnEcTD0EcTrE5OK0cb7jE59MEUeYT9q8QErtKhaW1v1bPy4QhDNKL4OJMqNyz:RrD8EnMWxTQDh1v1OxKLZJMqNyz |
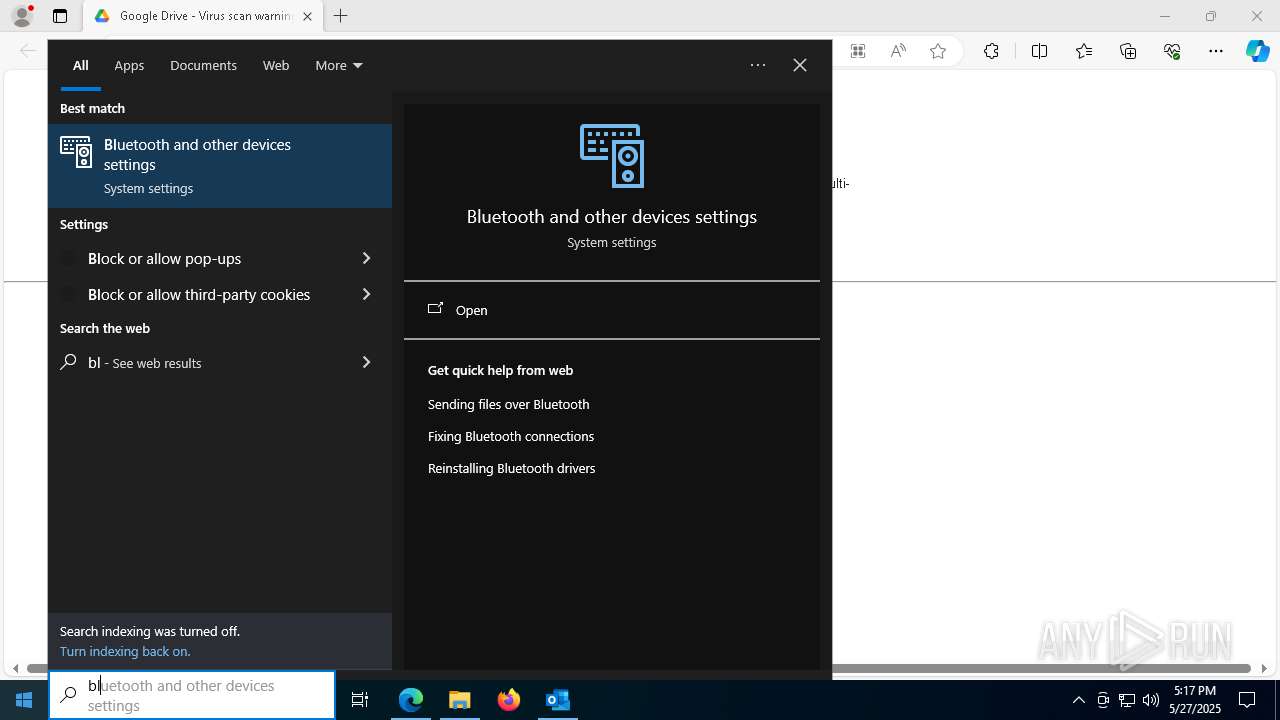
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3968)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6488)
- powershell.exe (PID: 6708)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 6760)
Changes powershell execution policy
- wscript.exe (PID: 6920)
- powershell.exe (PID: 3968)
- wscript.exe (PID: 7436)
- cscript.exe (PID: 1132)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6760)
STEGOCAMPAIGN has been detected
- powershell.exe (PID: 5968)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 5172)
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 6760)
- RegAsm.exe (PID: 2772)
ASYNCRAT has been detected (YARA)
- RegAsm.exe (PID: 2772)
SUSPICIOUS
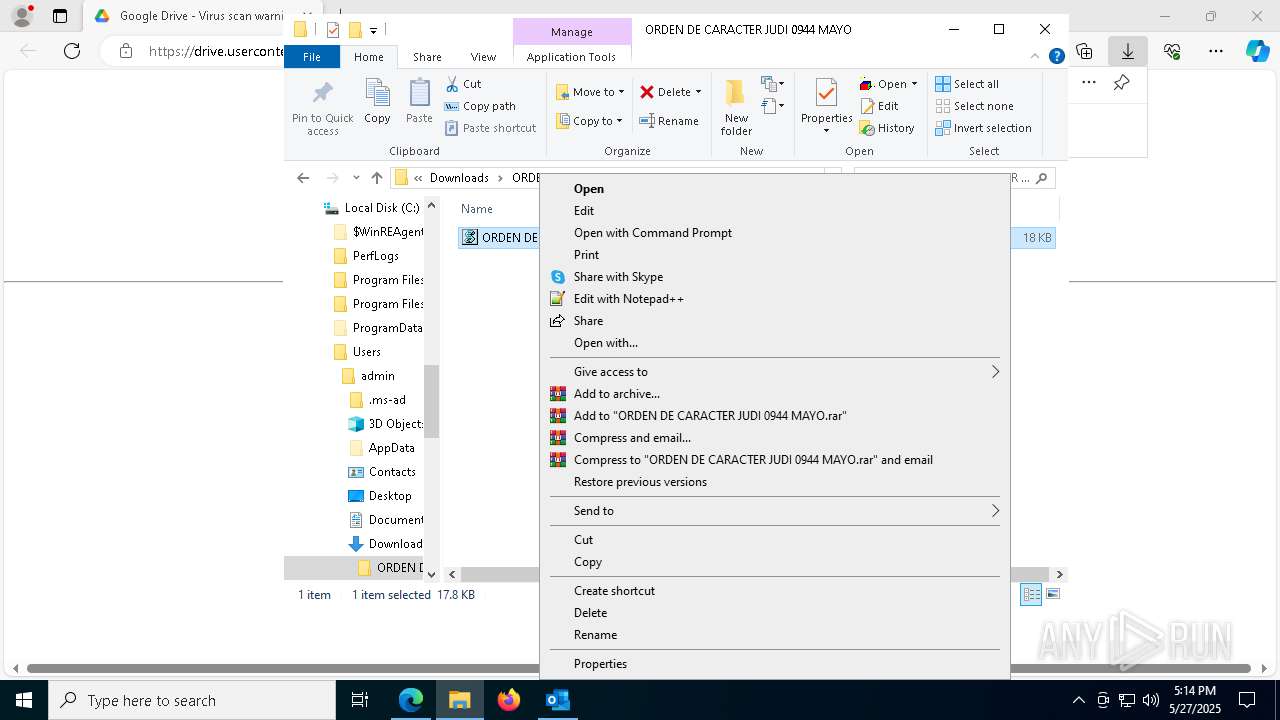
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 6920)
- wscript.exe (PID: 7436)
- cscript.exe (PID: 1132)
Get information on the list of running processes
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6760)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6920)
- powershell.exe (PID: 3968)
- wscript.exe (PID: 7436)
- powershell.exe (PID: 5968)
- cscript.exe (PID: 1132)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6760)
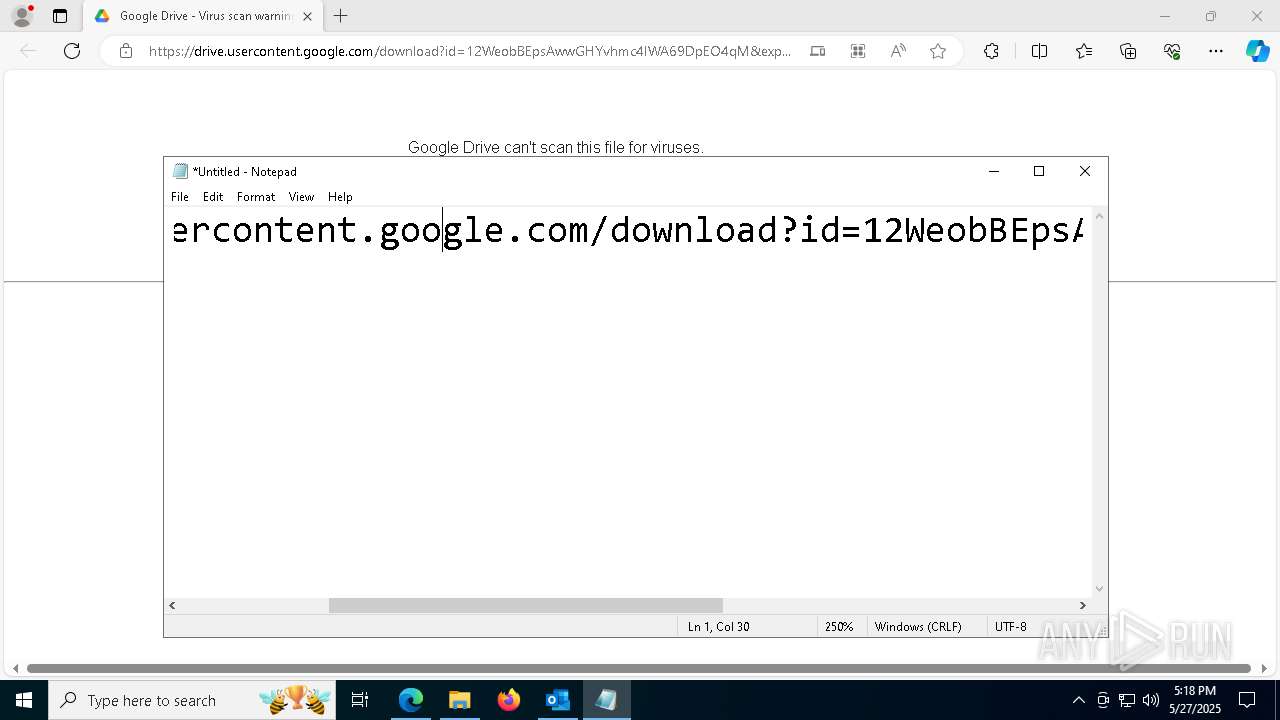
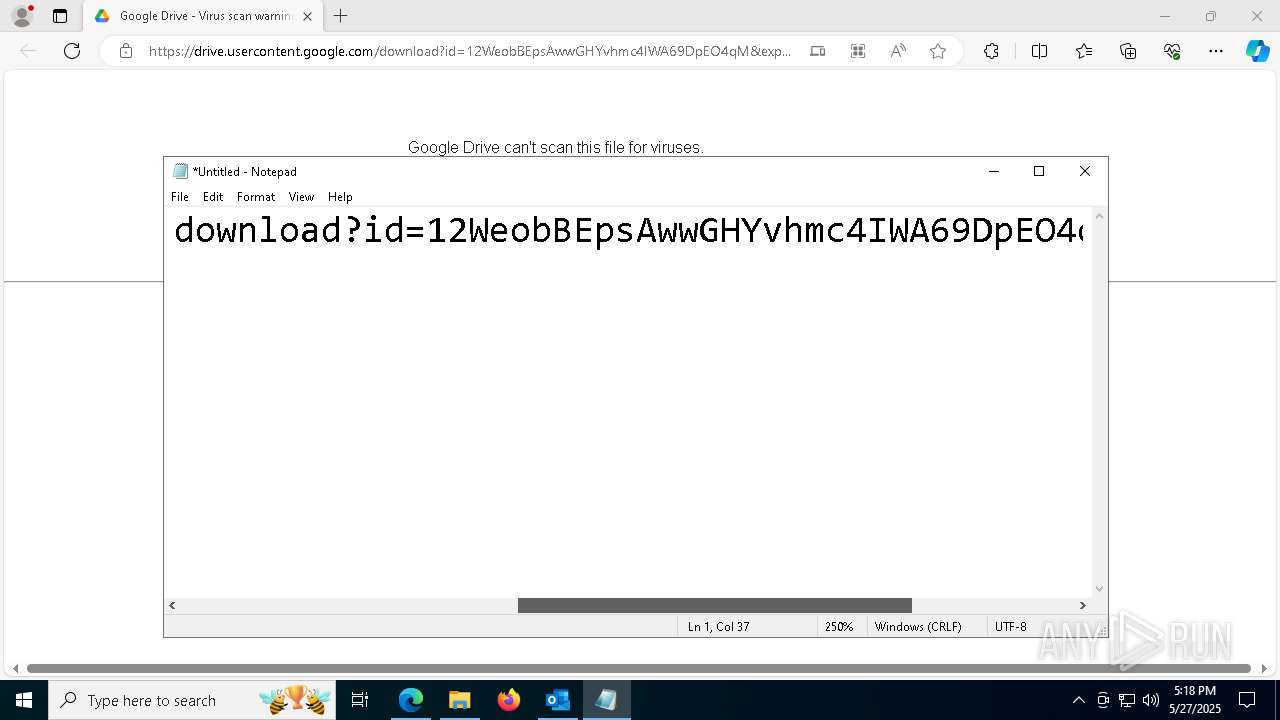
Probably download files using WebClient
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6760)
Application launched itself
- powershell.exe (PID: 3968)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 6132)
- powershell.exe (PID: 6760)
Starts process via Powershell
- powershell.exe (PID: 6488)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 6708)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6488)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6184)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 6760)
- RegAsm.exe (PID: 2772)
Connects to unusual port
- RegAsm.exe (PID: 6760)
- RegAsm.exe (PID: 2772)
INFO
Checks supported languages
- identity_helper.exe (PID: 8108)
Application launched itself
- msedge.exe (PID: 7448)
Reads Environment values
- identity_helper.exe (PID: 8108)
Reads the computer name
- identity_helper.exe (PID: 8108)
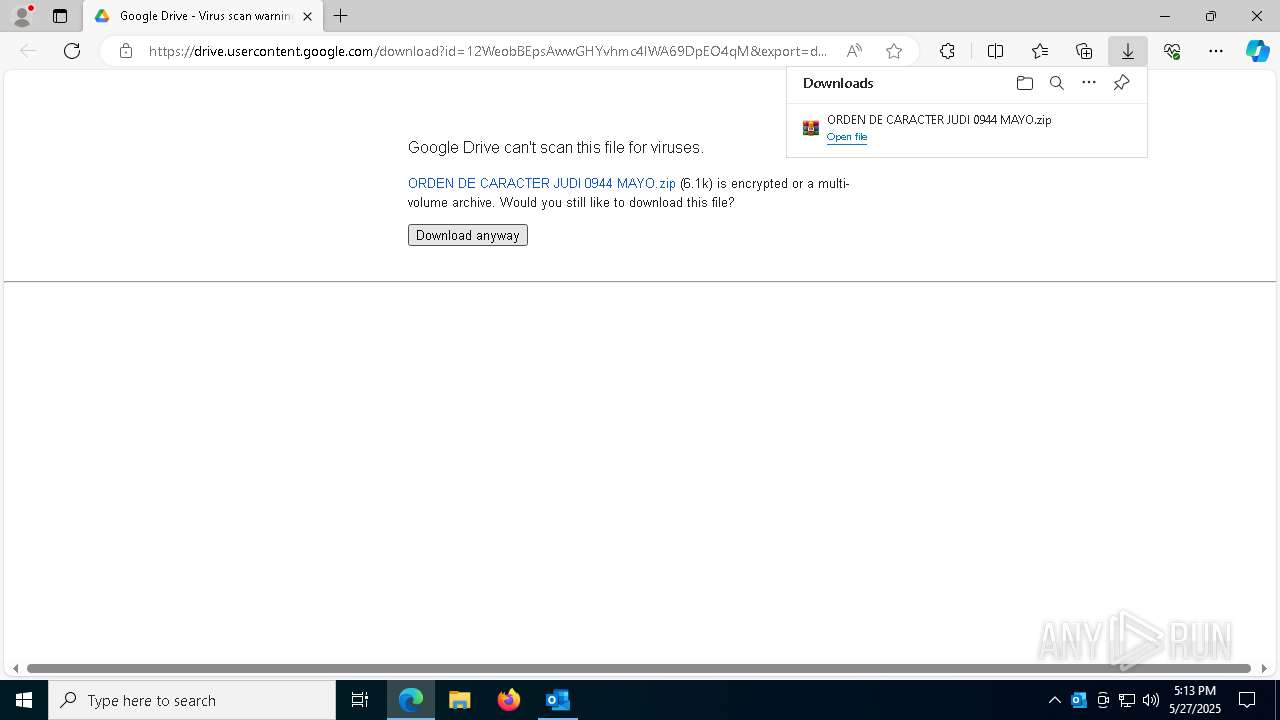
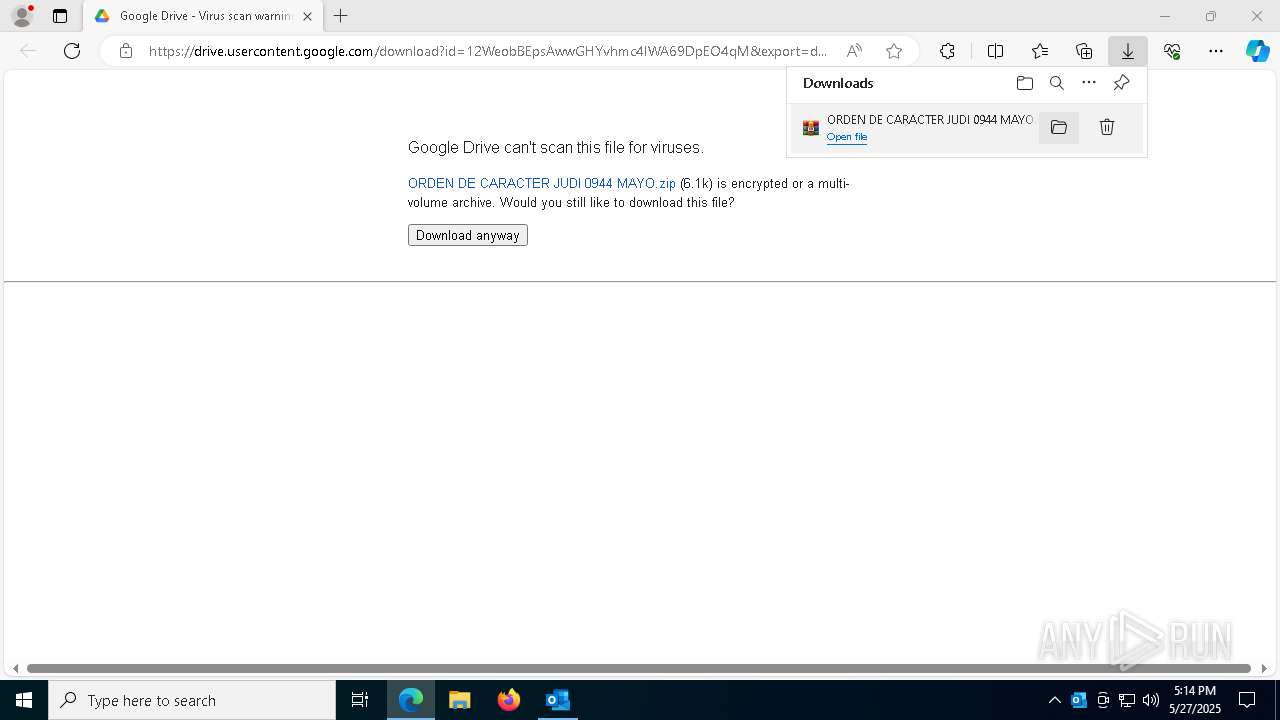
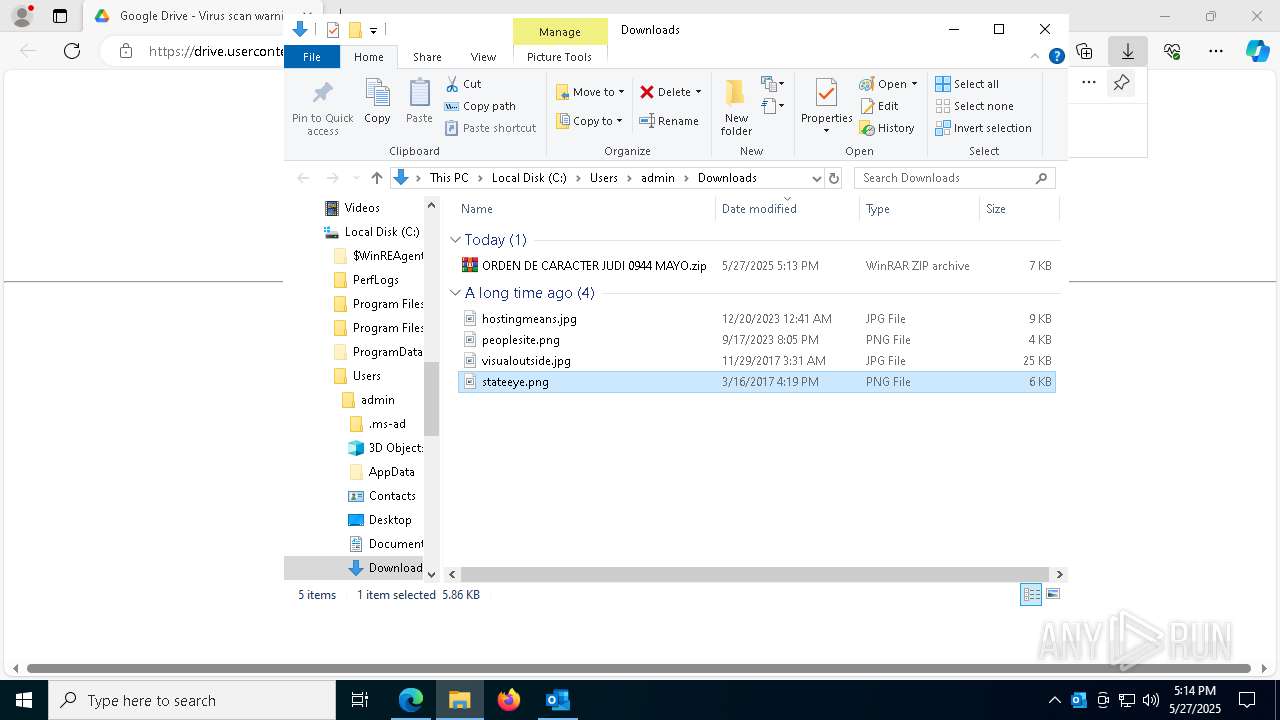
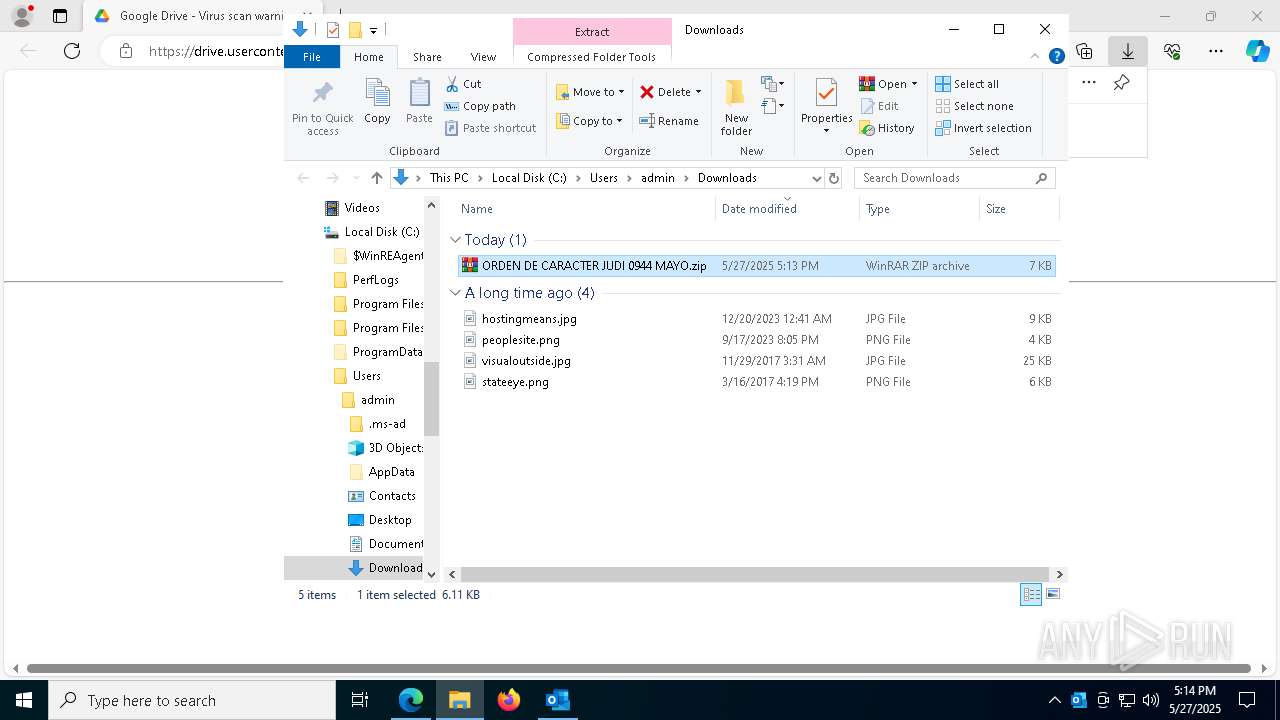
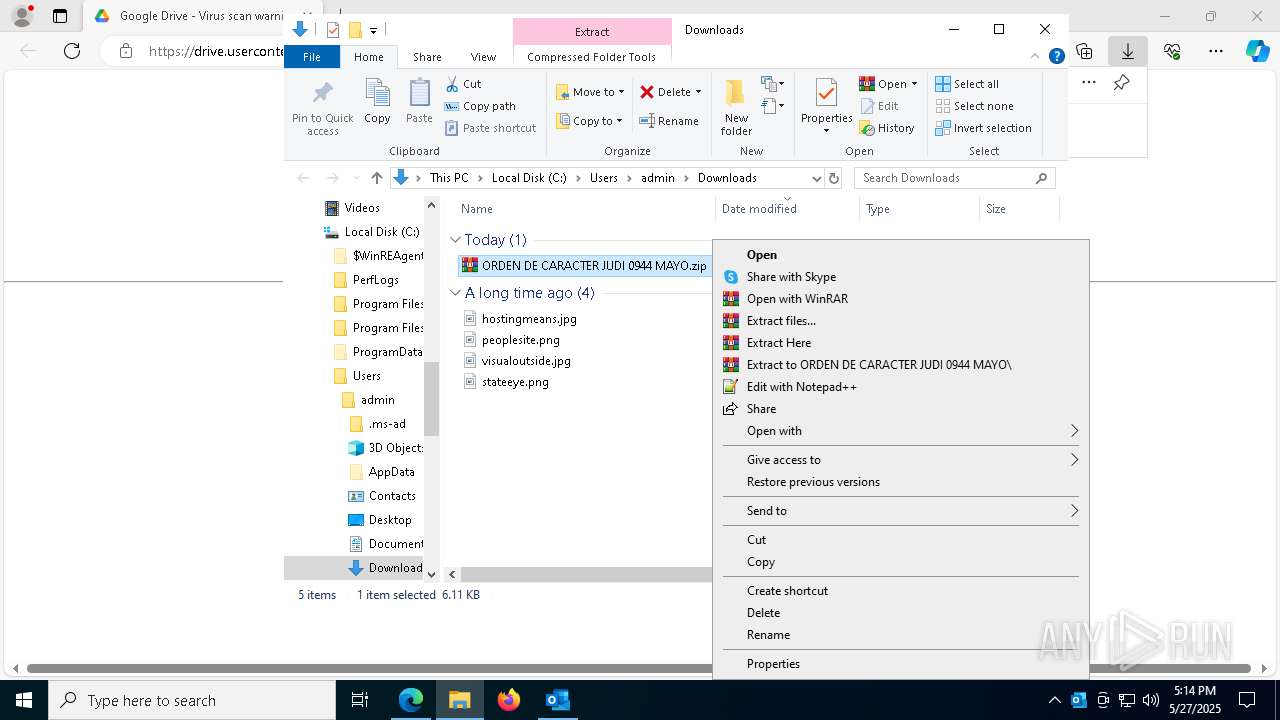
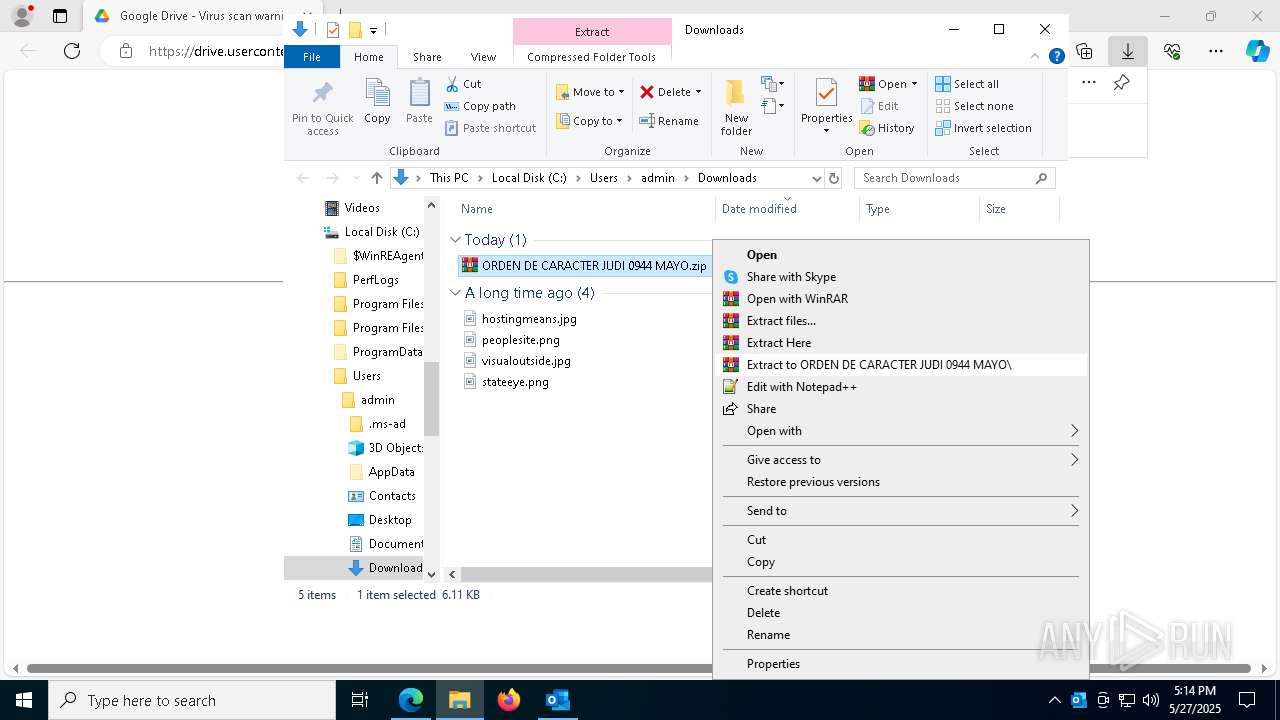
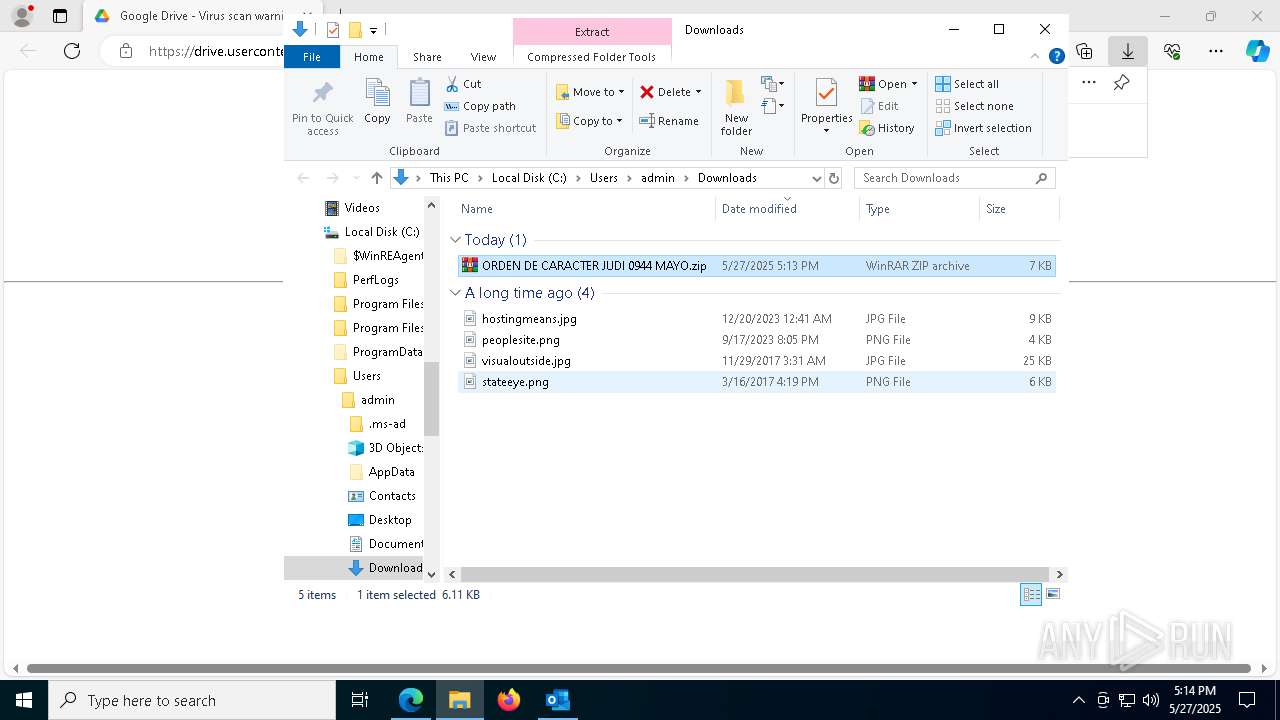
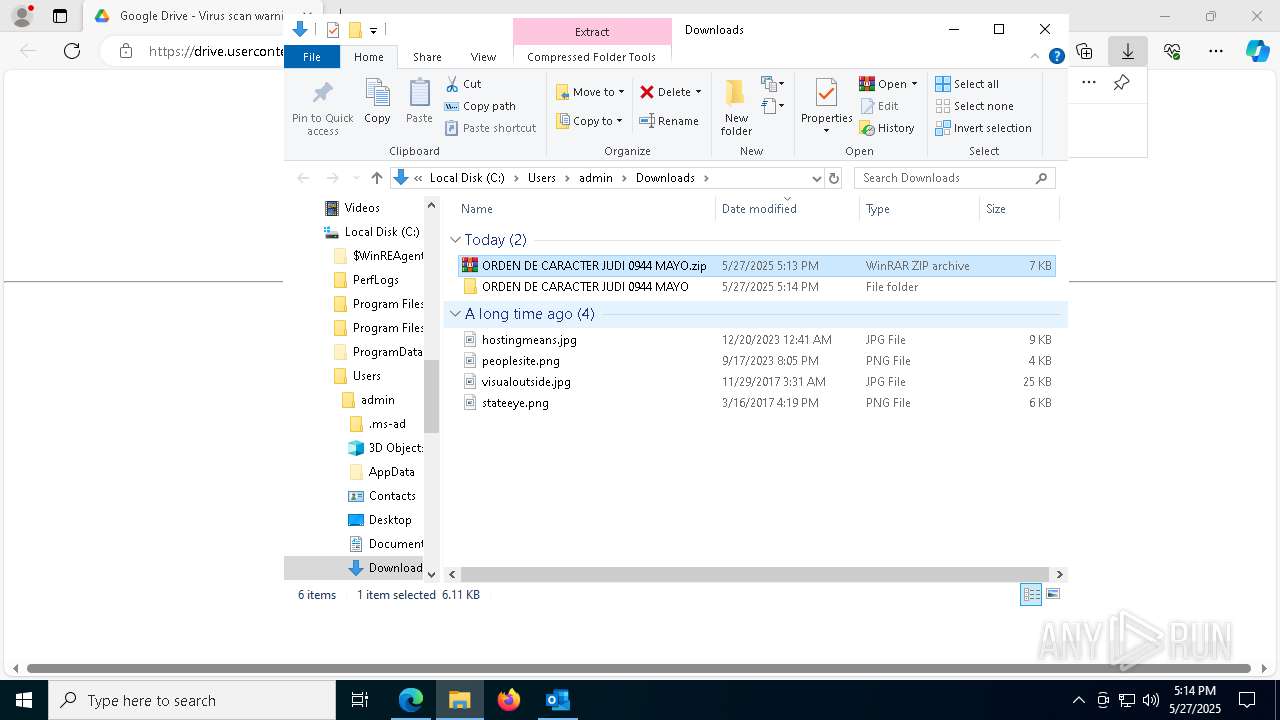
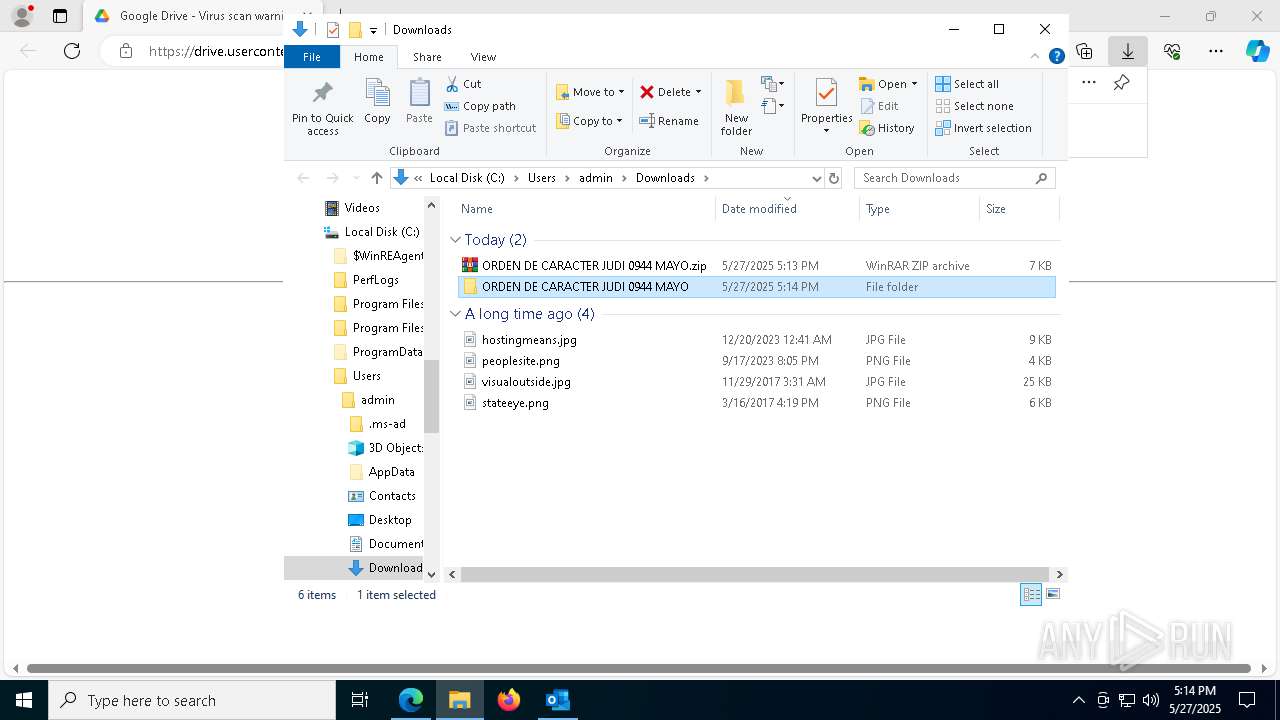
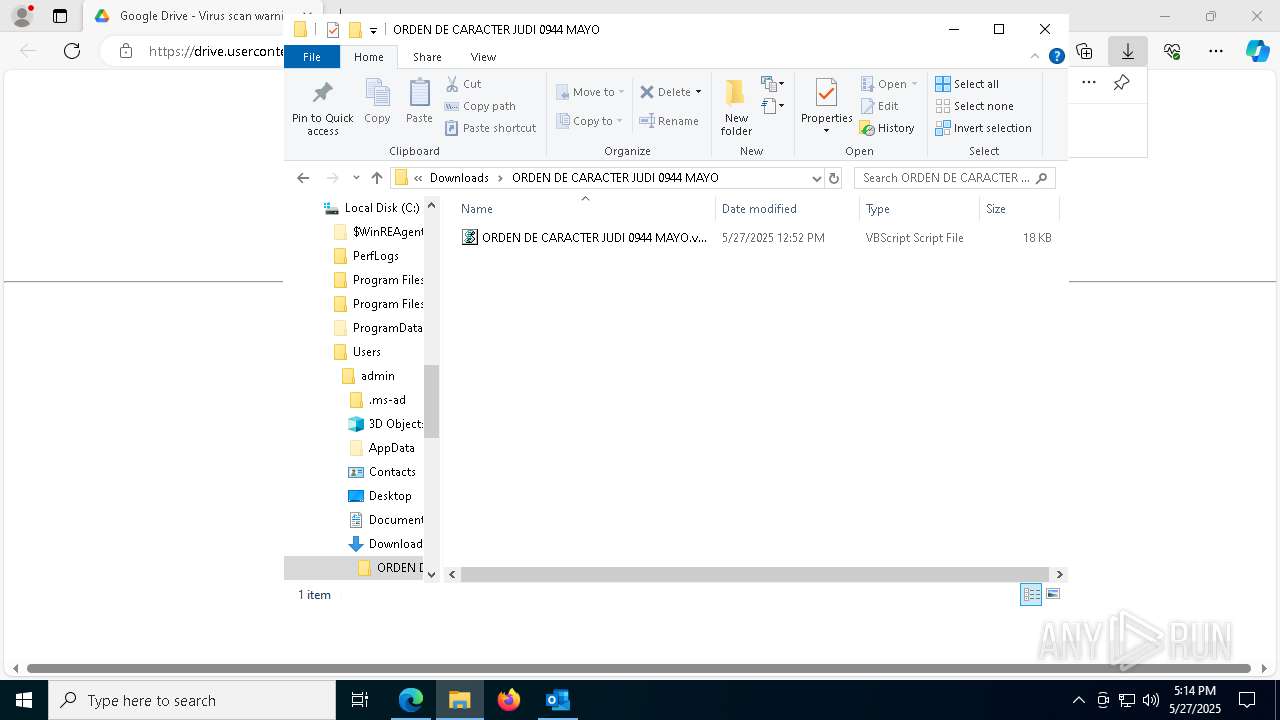
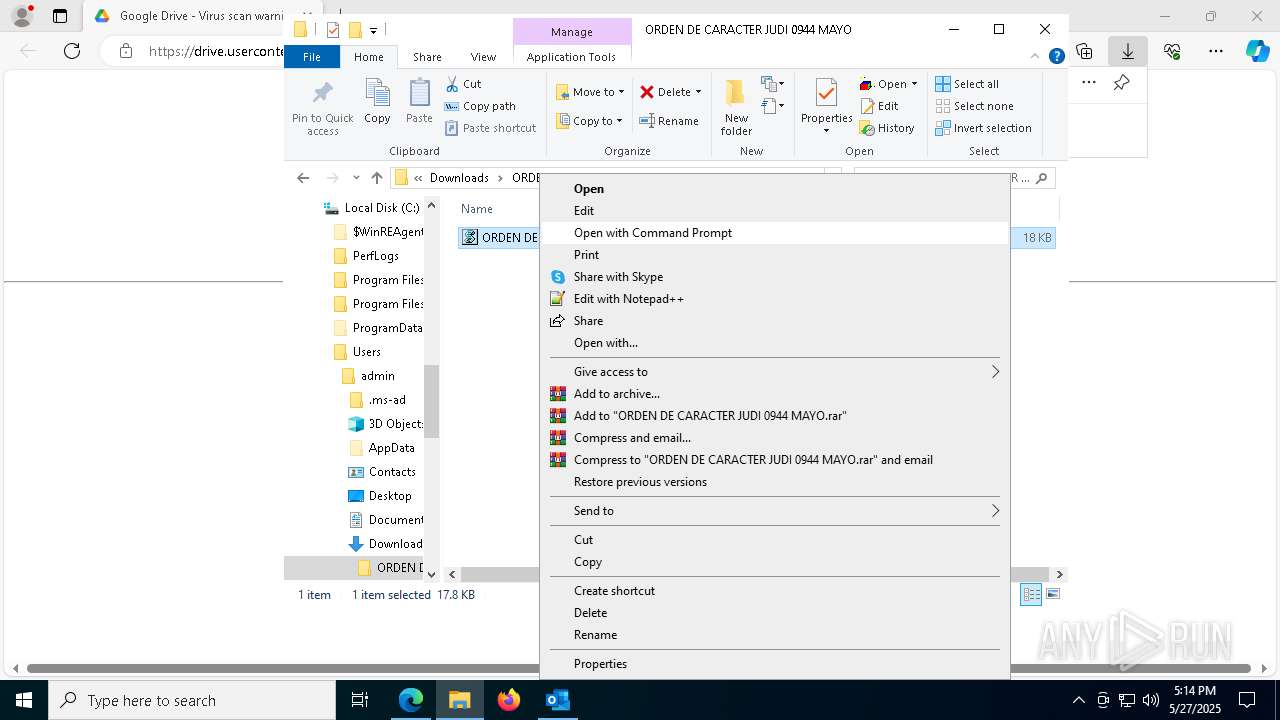
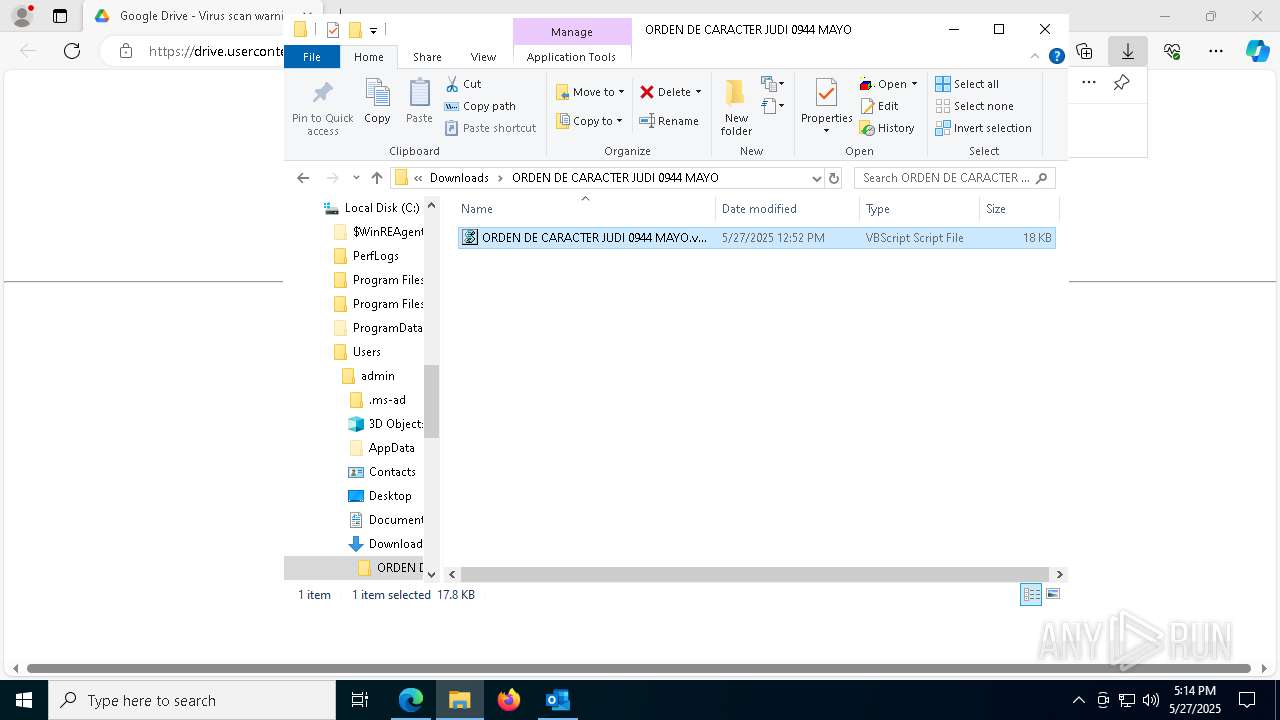
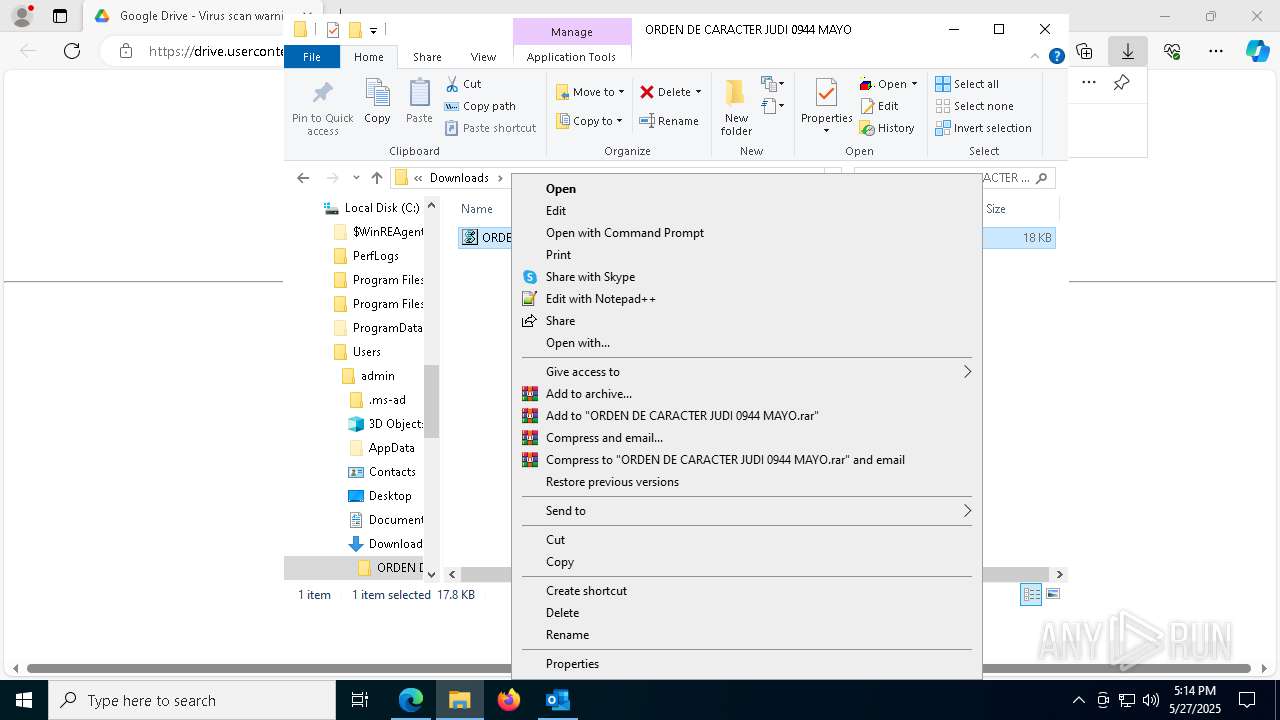
Launch of the file from Downloads directory
- msedge.exe (PID: 7448)
- msedge.exe (PID: 1240)
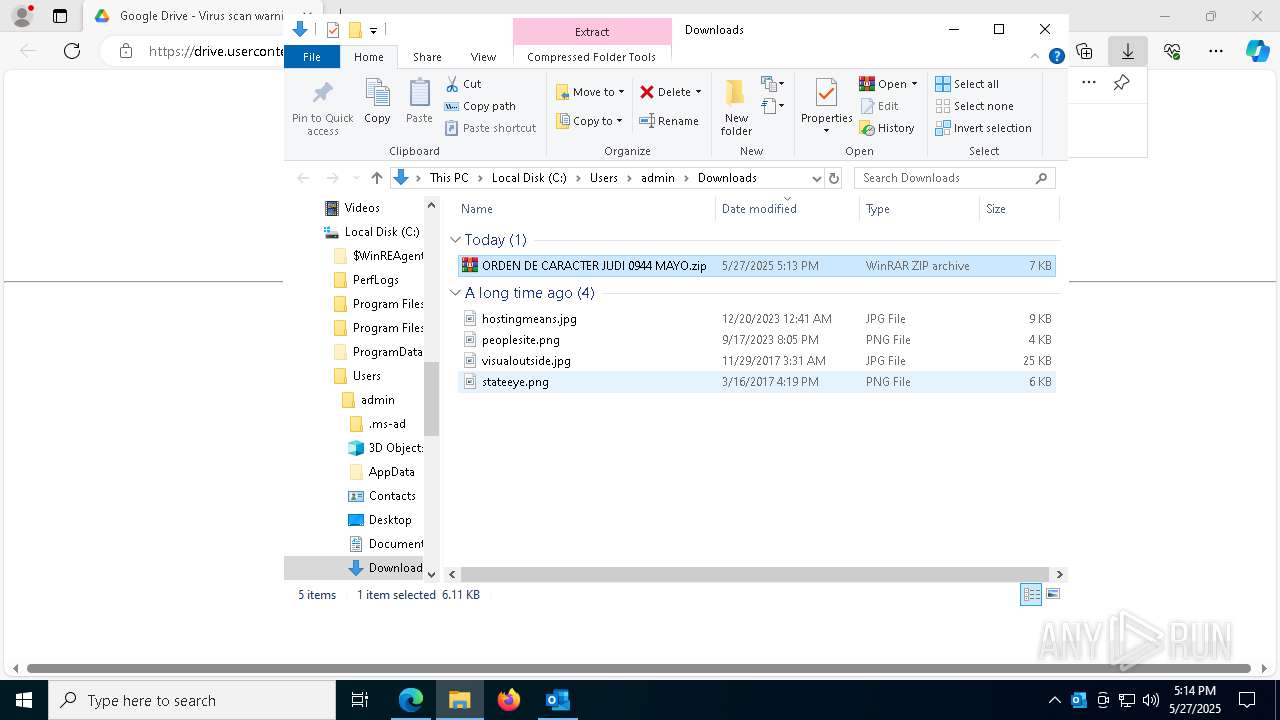
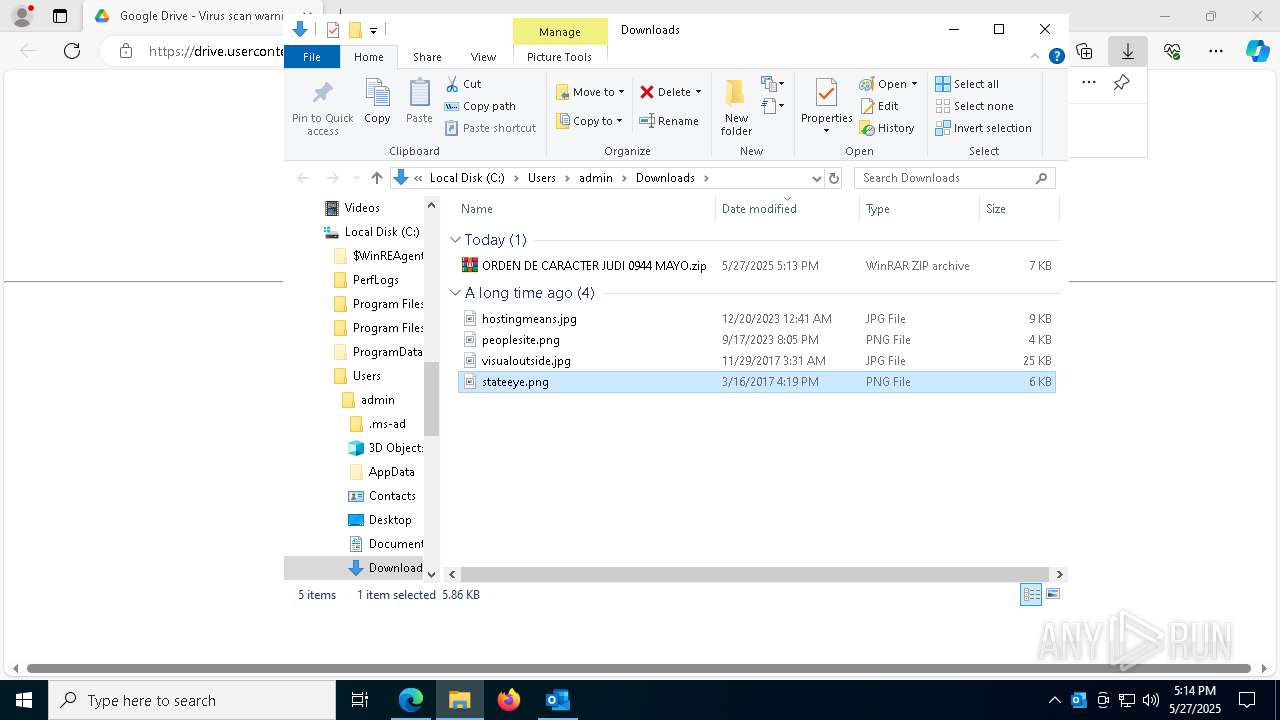
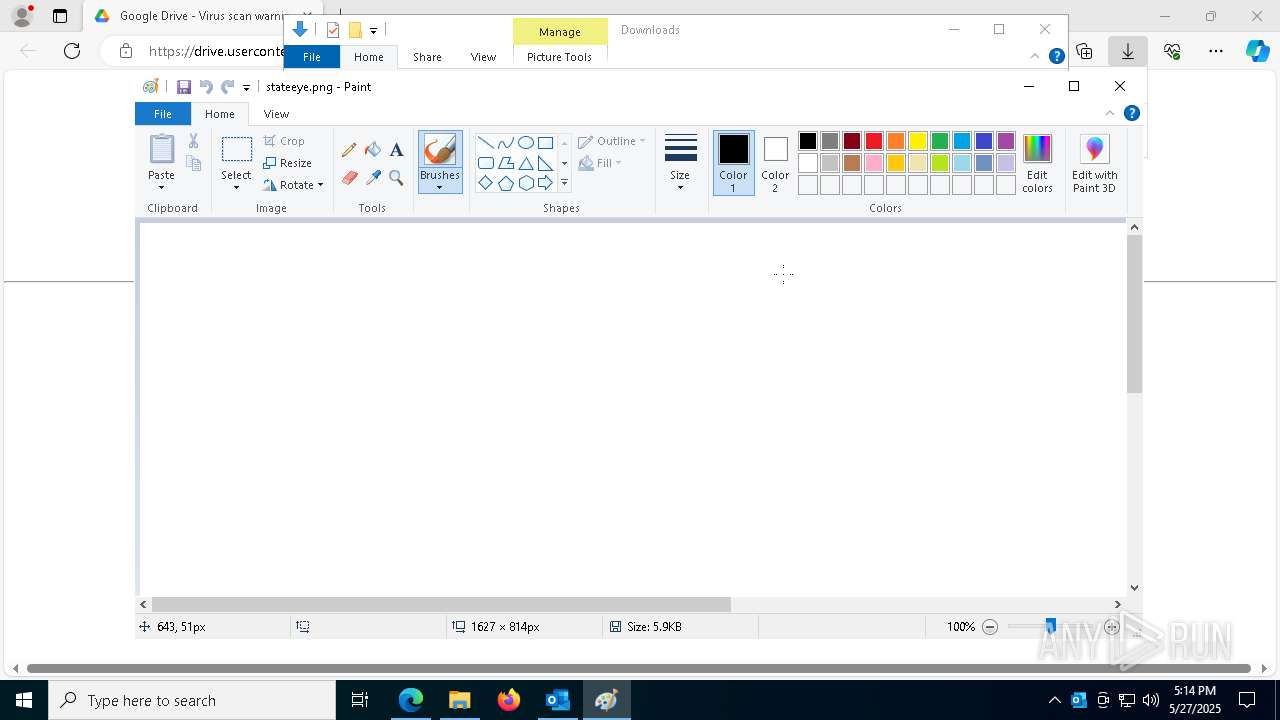
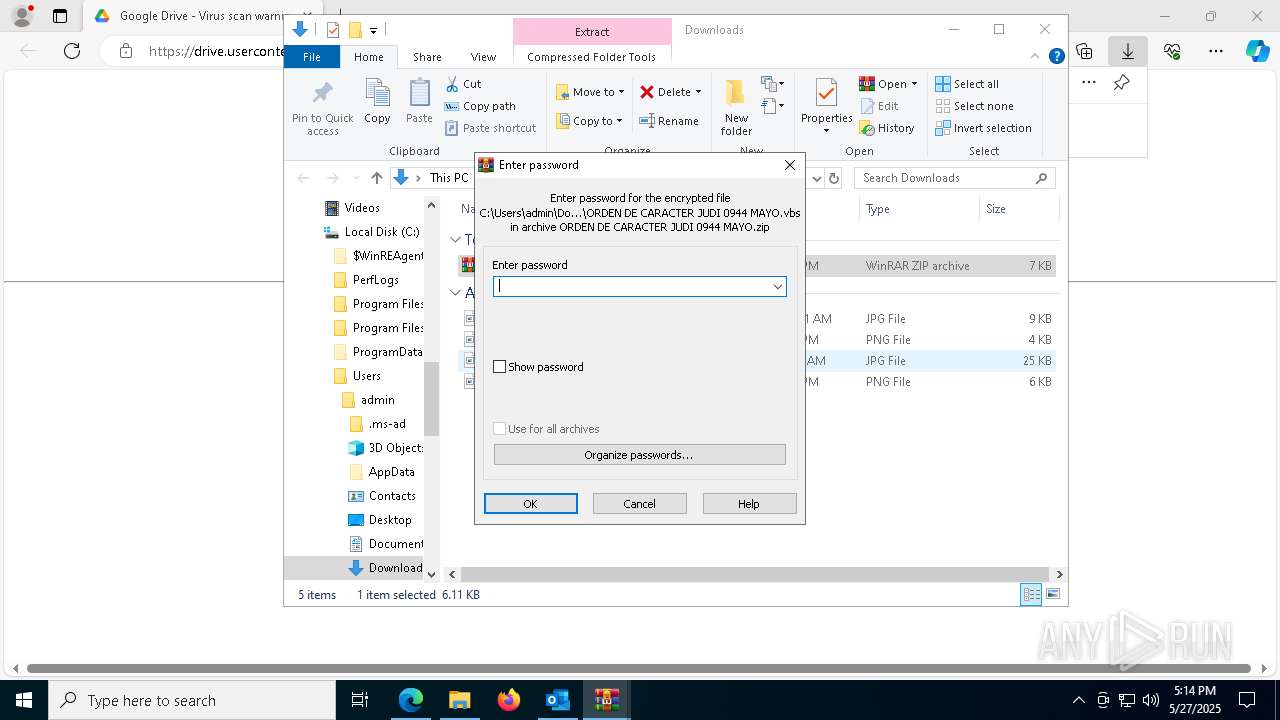
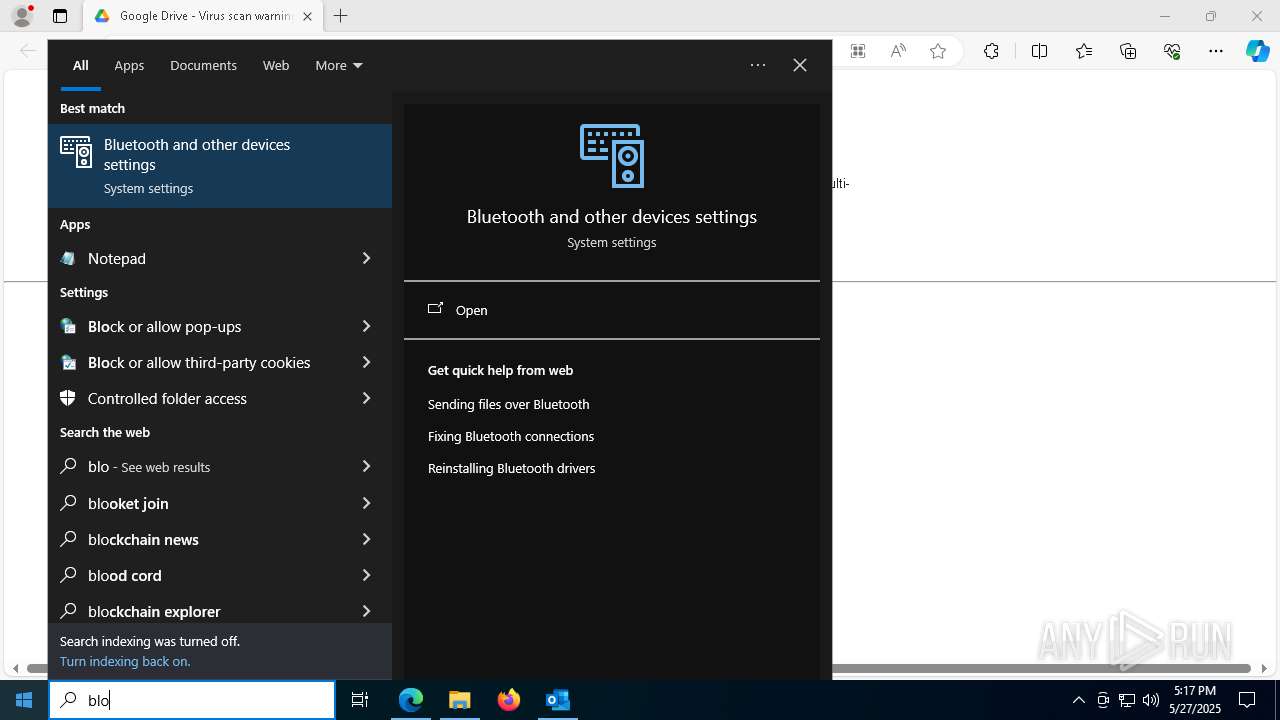
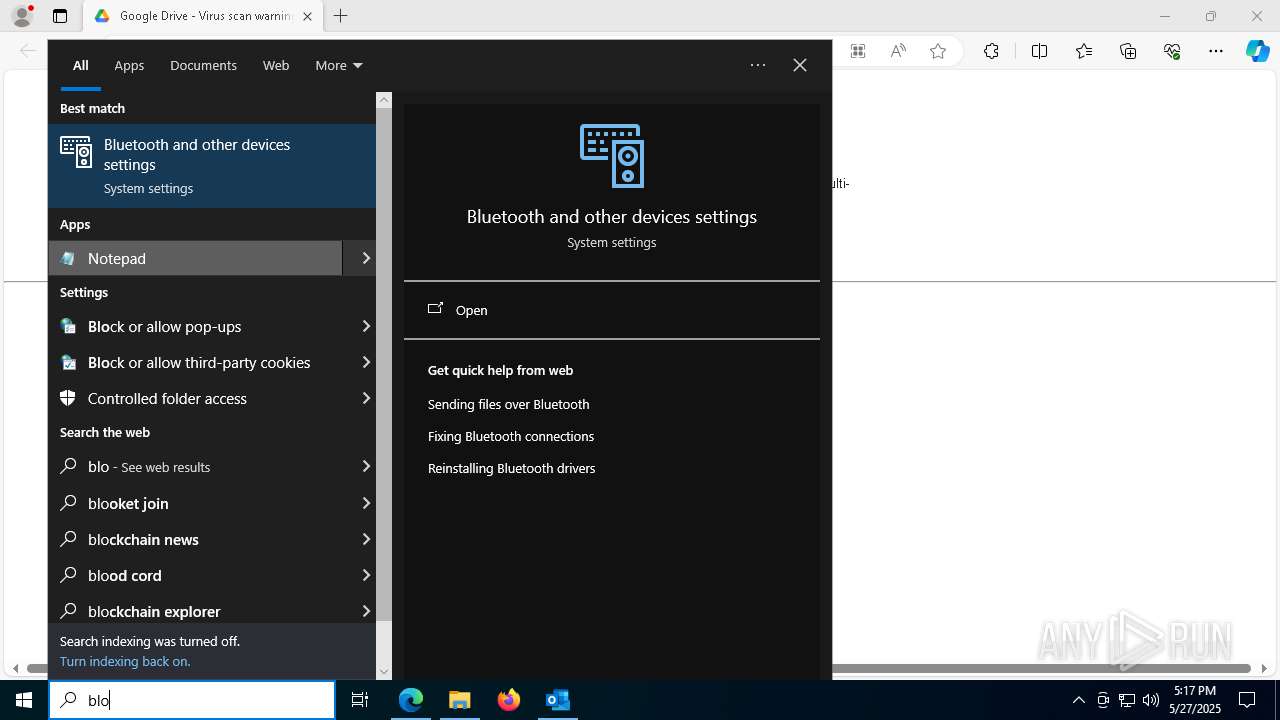
Manual execution by a user
- mspaint.exe (PID: 3100)
- WinRAR.exe (PID: 7280)
- wscript.exe (PID: 6920)
- wscript.exe (PID: 7436)
- cscript.exe (PID: 1132)
- notepad.exe (PID: 3008)
Returns hidden items found within a container (POWERSHELL)
- powershell.exe (PID: 6708)
- conhost.exe (PID: 856)
- conhost.exe (PID: 1616)
- conhost.exe (PID: 7244)
- conhost.exe (PID: 4896)
Found Base64 encoded access to processes via PowerShell (YARA)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6760)
Found Base64 encoded network access via PowerShell (YARA)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6760)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6760)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6760)
The sample compiled with english language support
- msedge.exe (PID: 8088)
Executable content was dropped or overwritten
- msedge.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 7) (100) |
|---|
Total processes
230
Monitored processes
86
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | taskkill /IM RegAsm.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5184 --field-trial-handle=2376,i,4927018449746030862,9764000787597638735,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
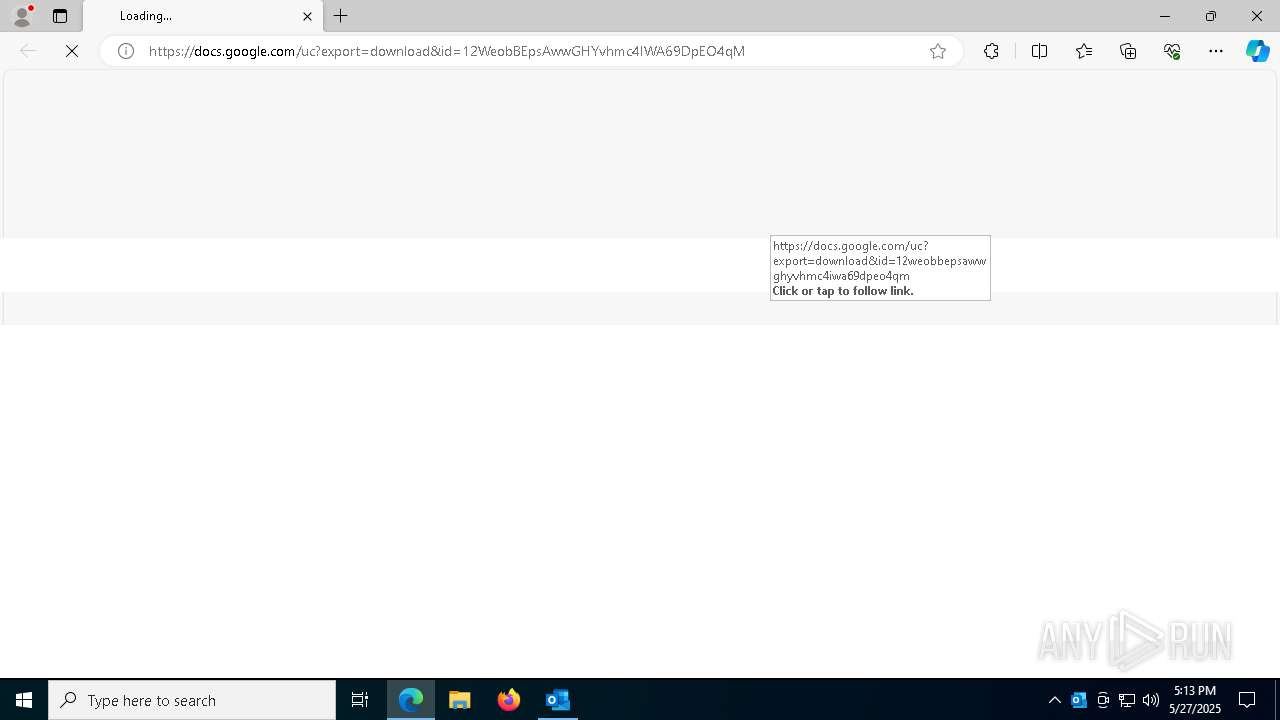
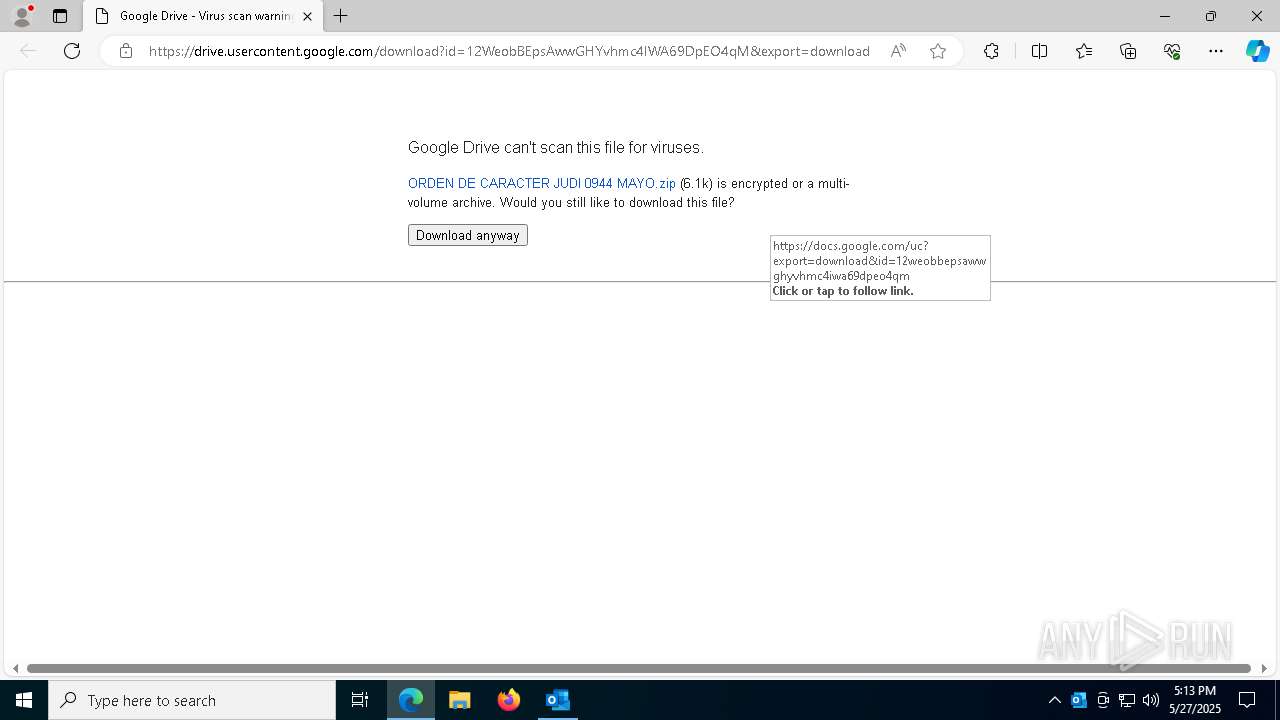
| 1132 | "C:\WINDOWS\System32\CScript.exe" "C:\Users\admin\Downloads\ORDEN DE CARACTER JUDI 0944 MAYO\ORDEN DE CARACTER JUDI 0944 MAYO.vbs" | C:\Windows\System32\cscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4720 --field-trial-handle=2376,i,4927018449746030862,9764000787597638735,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 | |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4572 --field-trial-handle=2376,i,4927018449746030862,9764000787597638735,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
66 767
Read events
66 199
Write events
473
Delete events
95
Modification events
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsData |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | write | Name: | OutlookBootFlag |
Value: 1 | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (1812) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
Executable files
1
Suspicious files
716
Text files
209
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10f88b.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10f89a.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1812 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:5E1F0DB954C9B4D0B64E04B074244B29 | SHA256:AA037044CBA9E987528D43AD3514030FE801D07D2246A6E536046F8D298FF7D1 | |||
| 1812 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_31BDBEC48939F54E87C0D12E36B6B694.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
| 1812 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:556C1E568AE3E9BD1395FF4ECF31C21A | SHA256:3FBB05C2A85A9470B4F5A159AB5041F04C678E689F30B1297B30A64072E3F178 | |||
| 7448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10f8c9.TMP | — | |
MD5:— | SHA256:— | |||
| 7448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
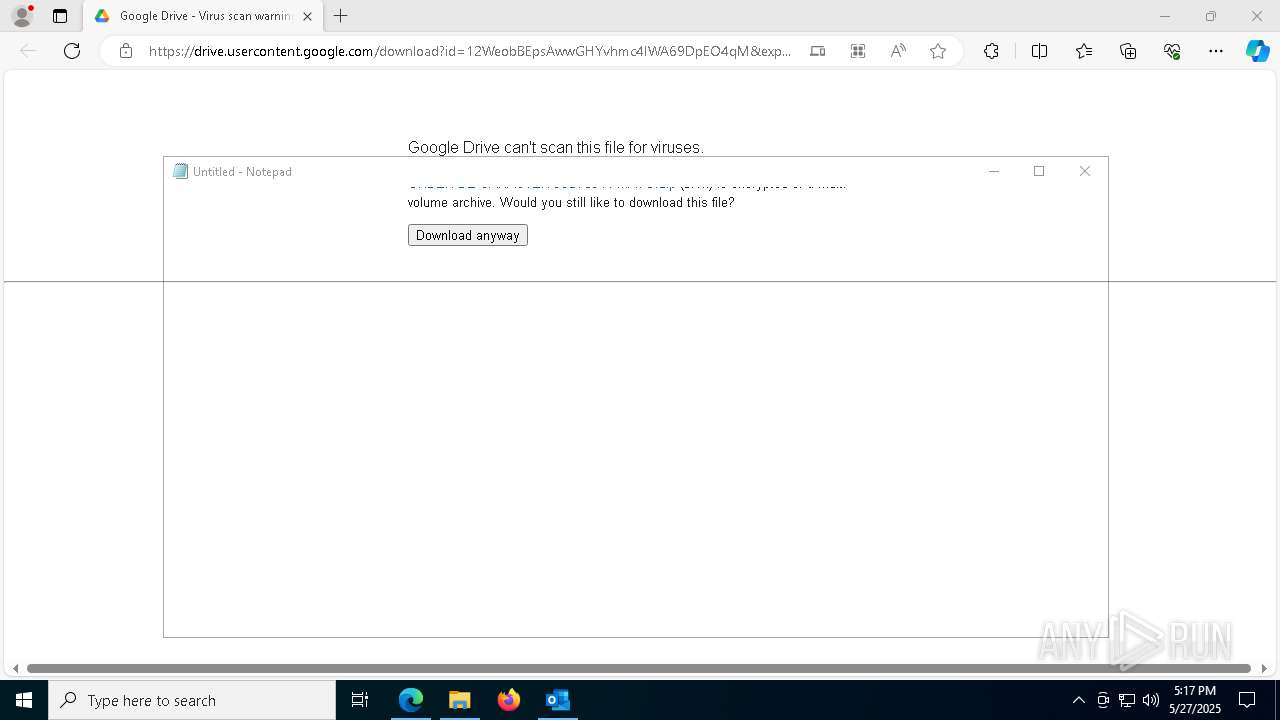
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
113
DNS requests
120
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6392 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
1812 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5596 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6512 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748964861&P2=404&P3=2&P4=Y6xchWzJu6Ik7sOwzlZAjWVSvapSeO1uxXtX9RRcotkysi7ZsSO2SLAa8I09wz88yOXIoOrvO1CdHOPDCFflYA%3d%3d | unknown | — | — | whitelisted |
5596 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6512 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748964861&P2=404&P3=2&P4=Y6xchWzJu6Ik7sOwzlZAjWVSvapSeO1uxXtX9RRcotkysi7ZsSO2SLAa8I09wz88yOXIoOrvO1CdHOPDCFflYA%3d%3d | unknown | — | — | whitelisted |
6512 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748964861&P2=404&P3=2&P4=Y6xchWzJu6Ik7sOwzlZAjWVSvapSeO1uxXtX9RRcotkysi7ZsSO2SLAa8I09wz88yOXIoOrvO1CdHOPDCFflYA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4268 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1812 | OUTLOOK.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1812 | OUTLOOK.EXE | 2.16.168.101:443 | omex.cdn.office.net | Akamai International B.V. | RU | whitelisted |
1812 | OUTLOOK.EXE | 52.111.236.4:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6760 | RegAsm.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6760 | RegAsm.exe | A Network Trojan was detected | ET MALWARE Observed Malicious SSL Cert (Various RAT) |
6760 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
2772 | RegAsm.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2772 | RegAsm.exe | A Network Trojan was detected | ET MALWARE Observed Malicious SSL Cert (Various RAT) |
2772 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
2772 | RegAsm.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
7684 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7684 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7684 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
1 ETPRO signatures available at the full report