| File name: | Sample_5f6b5cda69480900164d7b49.bin |
| Full analysis: | https://app.any.run/tasks/2cab28c7-5a52-4108-ac9f-7c247e7f5c95 |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
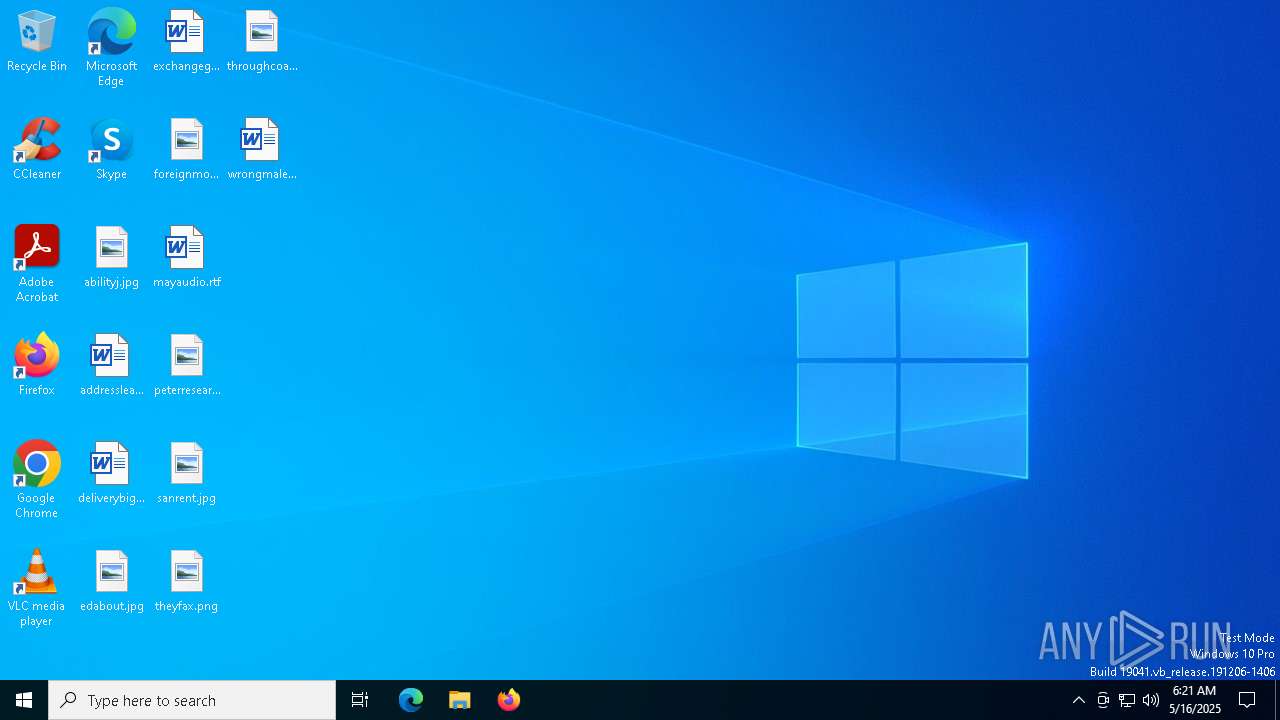
| Analysis date: | May 16, 2025, 06:21:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 17492F7B9906B807CFFD30E8A0EDD993 |
| SHA1: | AC0724C724F8D6E2A54B41B86D99AA189E40DC81 |
| SHA256: | 7E8C547FCC86E26B973E4C974DA8EE2C4CFE84846E2CDFCD7F265929D27602F9 |
| SSDEEP: | 12288:QyeWT96x+MN2N4Bou8Bw1bFswwGFGvyLOE8uQnUK5bA:QyeAEwN4BuYFswwsGz1uFCc |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 7000)
Disables Windows Defender
- ееЕаАххВОеЕао.exe (PID: 5544)
- ееЕаАххВОеЕао.exe (PID: 8584)
Starts SC.EXE for service management
- cmd.exe (PID: 5008)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 8644)
Changes Windows Defender settings
- cmd.exe (PID: 6388)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 8660)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 8972)
- cmd.exe (PID: 8948)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 8780)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8868)
- cmd.exe (PID: 9072)
Changes settings for real-time protection
- powershell.exe (PID: 4920)
- powershell.exe (PID: 8824)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 4040)
- powershell.exe (PID: 4812)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 6512)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7492)
- powershell.exe (PID: 7228)
TRICKBOT mutex has been found
- svchost.exe (PID: 7912)
SUSPICIOUS
Starts itself from another location
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
Reads security settings of Internet Explorer
- ееЕаАххВОеЕао.exe (PID: 5544)
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
- ееЕаАххВОеЕао.exe (PID: 8584)
Executable content was dropped or overwritten
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
- svchost.exe (PID: 7912)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6388)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 8660)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 8948)
- cmd.exe (PID: 8972)
- cmd.exe (PID: 8780)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8868)
- cmd.exe (PID: 9072)
Starts CMD.EXE for commands execution
- ееЕаАххВОеЕао.exe (PID: 5544)
- ееЕаАххВОеЕао.exe (PID: 8584)
Windows service management via SC.EXE
- sc.exe (PID: 6516)
- sc.exe (PID: 8852)
Script disables Windows Defender's behavior monitoring
- cmd.exe (PID: 6388)
- cmd.exe (PID: 8676)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 5380)
- cmd.exe (PID: 8660)
Script disables Windows Defender's IPS
- cmd.exe (PID: 1012)
- cmd.exe (PID: 8908)
Stops a currently running service
- sc.exe (PID: 5720)
- sc.exe (PID: 8808)
The process executes via Task Scheduler
- ееЕаАххВОеЕао.exe (PID: 8584)
There is functionality for taking screenshot (YARA)
- ееЕаАххВОеЕао.exe (PID: 4880)
INFO
Reads the machine GUID from the registry
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
- ееЕаАххВОеЕао.exe (PID: 4880)
- ееЕаАххВОеЕао.exe (PID: 5544)
- ееЕаАххВОеЕао.exe (PID: 8584)
Reads the computer name
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
- ееЕаАххВОеЕао.exe (PID: 4880)
- ееЕаАххВОеЕао.exe (PID: 5544)
- ееЕаАххВОеЕао.exe (PID: 8584)
Checks supported languages
- ееЕаАххВОеЕао.exe (PID: 5544)
- ееЕаАххВОеЕао.exe (PID: 4880)
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
- ееЕаАххВОеЕао.exe (PID: 8584)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 7000)
Process checks computer location settings
- ееЕаАххВОеЕао.exe (PID: 5544)
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
Creates files in the program directory
- Sample_5f6b5cda69480900164d7b49.bin.exe (PID: 4692)
- ееЕаАххВОеЕао.exe (PID: 8584)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7412)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 4040)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 7396)
- powershell.exe (PID: 7404)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7404)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 7396)
- powershell.exe (PID: 7412)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 5892)
Reads the software policy settings
- slui.exe (PID: 720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:18 08:09:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 61440 |
| InitializedDataSize: | 339968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4570 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
210
Monitored processes
82
Malicious processes
14
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableIntrusionPreventionSystem $true | C:\Windows\System32\cmd.exe | — | ееЕаАххВОеЕао.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -LowThreatDefaultAction 6 | C:\Windows\System32\cmd.exe | — | ееЕаАххВОеЕао.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
112 234
Read events
112 223
Write events
11
Delete events
0
Modification events
| (PID) Process: | (5544) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (5544) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (5544) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (5544) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (5544) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (7000) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8584) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (8584) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (8584) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (8584) ееЕаАххВОеЕао.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
Executable files
3
Suspicious files
4
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rzn0nn1k.fjp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xd4ecpnn.nw3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4692 | Sample_5f6b5cda69480900164d7b49.bin.exe | C:\ProgramData\ееЕаАххВОеЕао.exe | executable | |
MD5:17492F7B9906B807CFFD30E8A0EDD993 | SHA256:7E8C547FCC86E26B973E4C974DA8EE2C4CFE84846E2CDFCD7F265929D27602F9 | |||
| 7020 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mnjwq14q.bsn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dtu1ektx.vbc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1rmzj2q2.53a.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bf1tdagt.kly.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cko4e4qs.xhr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7492 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_o3pae2wi.bvp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_svgcodfd.fwo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
8184 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |