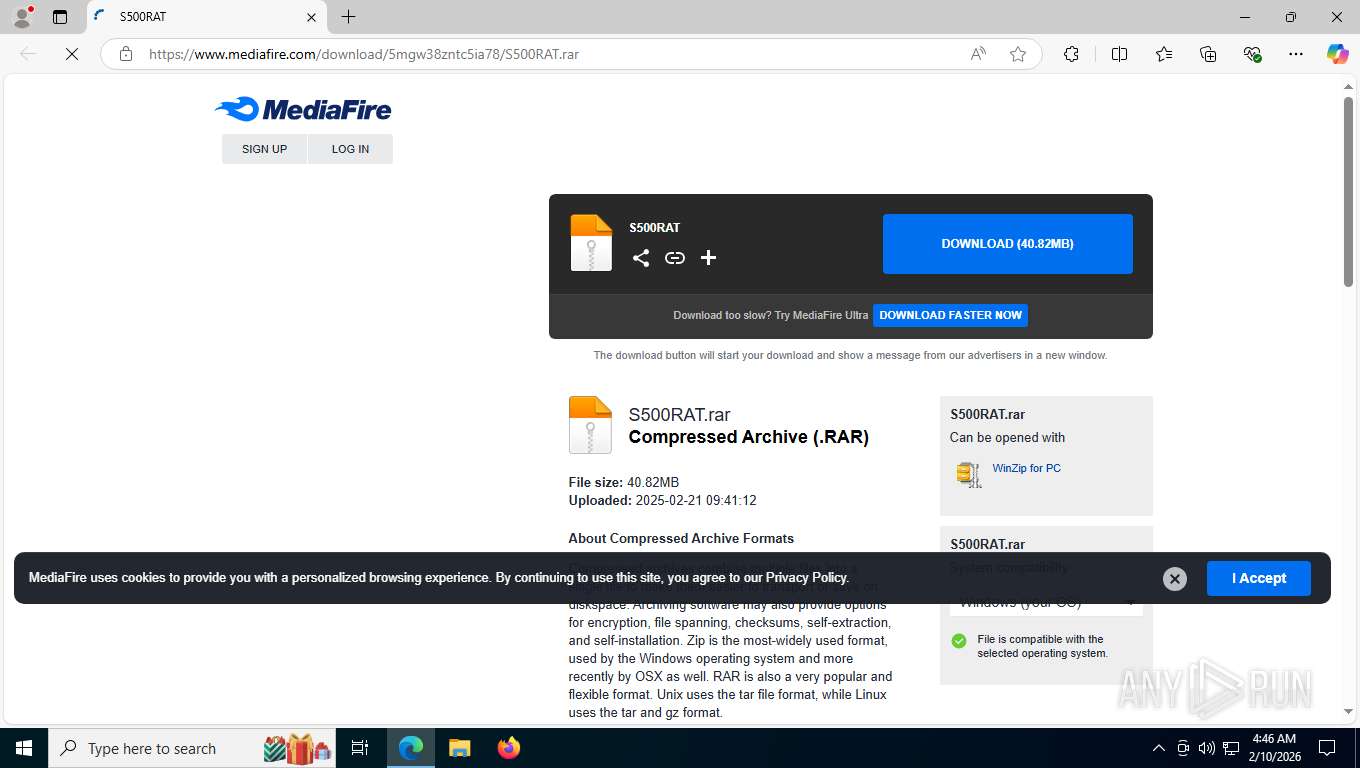
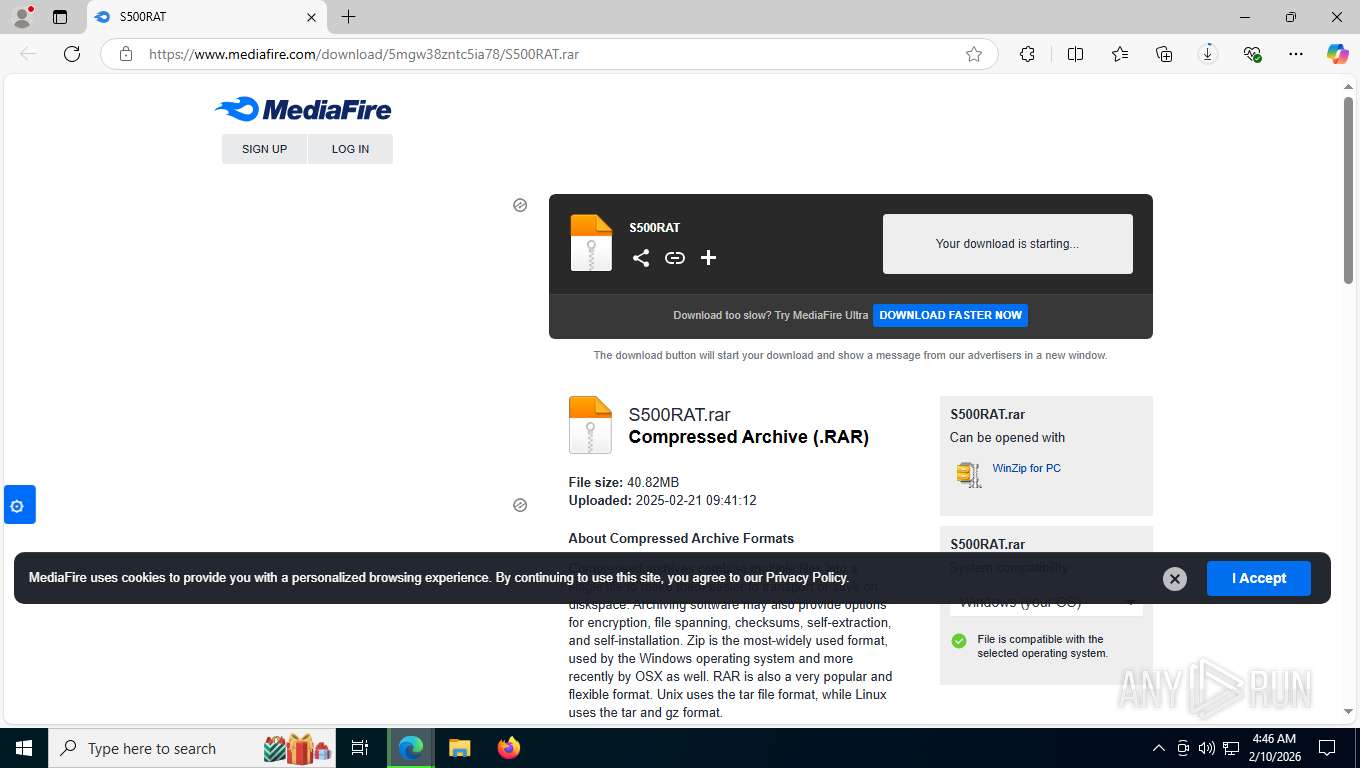
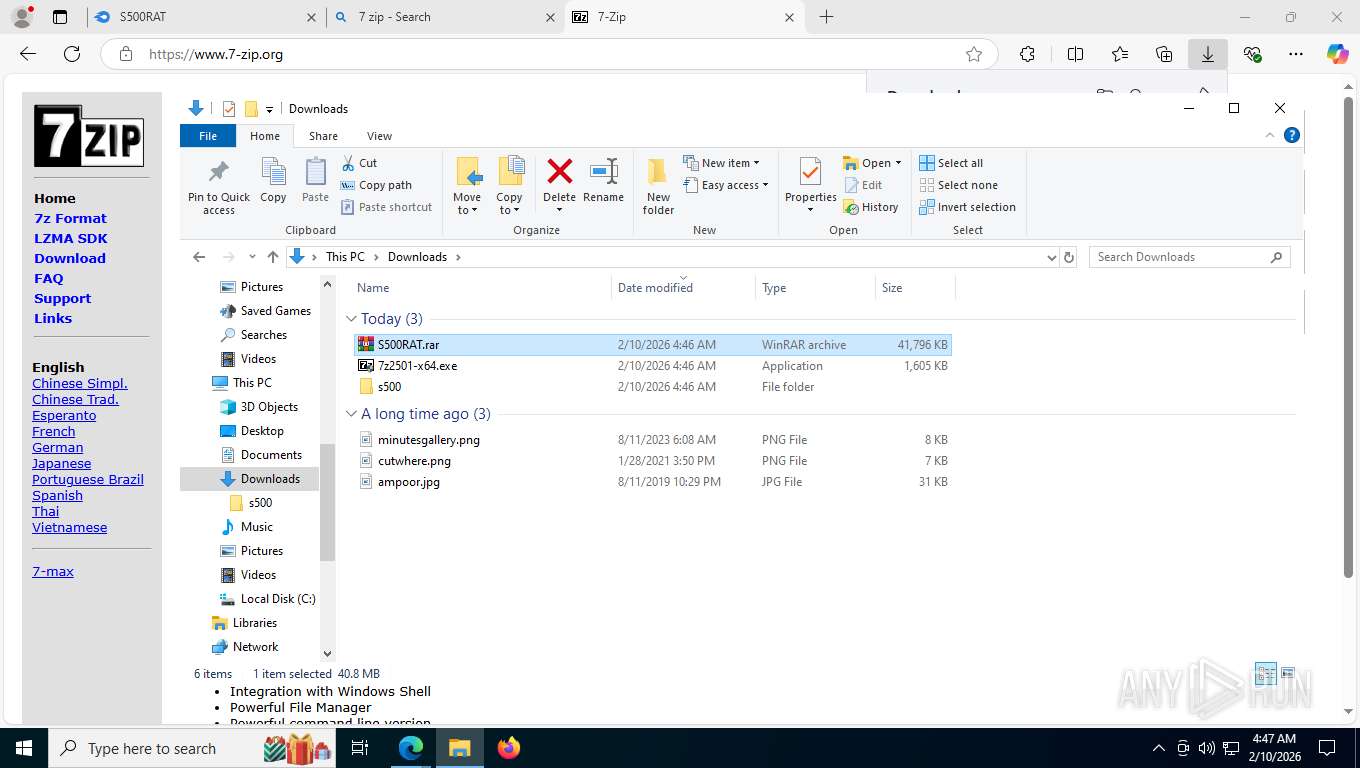
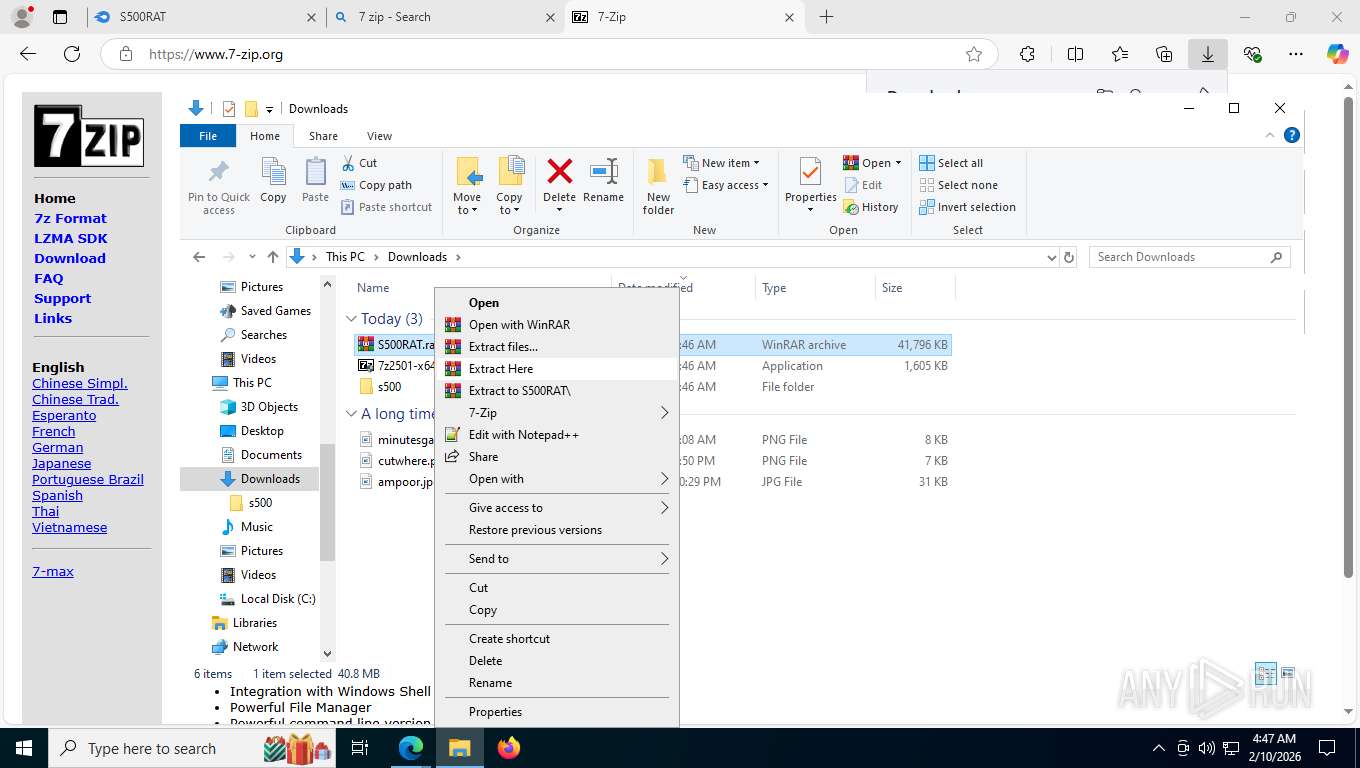
| URL: | https://www.mediafire.com/download/5mgw38zntc5ia78/S500RAT.rar |
| Full analysis: | https://app.any.run/tasks/1ebb26bd-5a65-4e41-9efa-93335047356a |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | February 10, 2026, 09:46:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1ECF0544BC9C7EC7D682DA94A338F713 |
| SHA1: | 607FA3DAC16291E58FF0EFEE716758736A94E00C |
| SHA256: | 7E89F95AC74E4C240305538D65D754979955326A77766BB7D2FE7D286E9DB1AC |
| SSDEEP: | 3:N8DSLw3eGWKLQaafa7dtQVVo4X:2OLw3eGNkaaSdiVVRX |
MALICIOUS
Reads a specific registry key of the VM
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
Known privilege escalation attack
- dllhost.exe (PID: 7652)
Changes powershell execution policy (Bypass)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- cmd.exe (PID: 9400)
- svchost.exe (PID: 2336)
Changes Windows Defender settings
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 3164)
- svchost.exe (PID: 2336)
Adds path to the Windows Defender exclusion list
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- dllhost.exe (PID: 3988)
- cmd.exe (PID: 3092)
- svchost.exe (PID: 2336)
Changes the autorun value in the registry
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
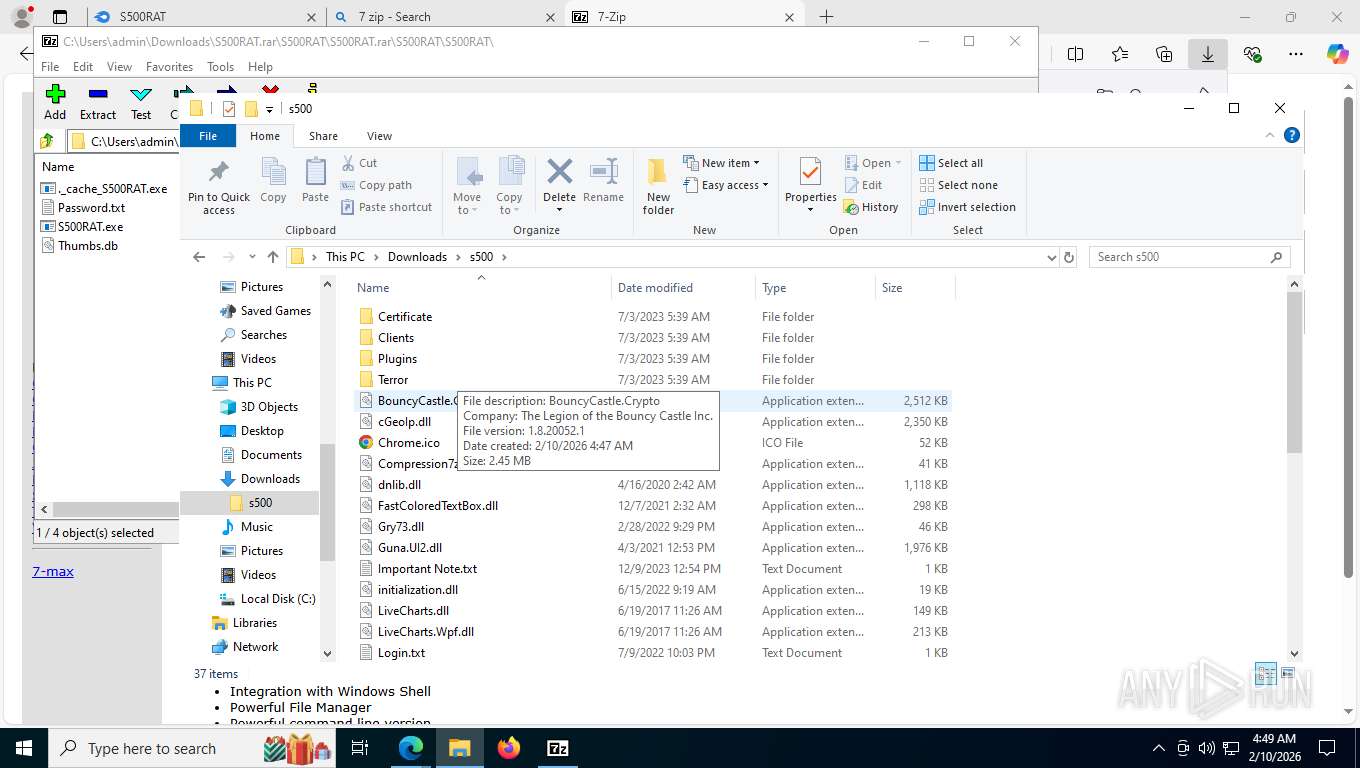
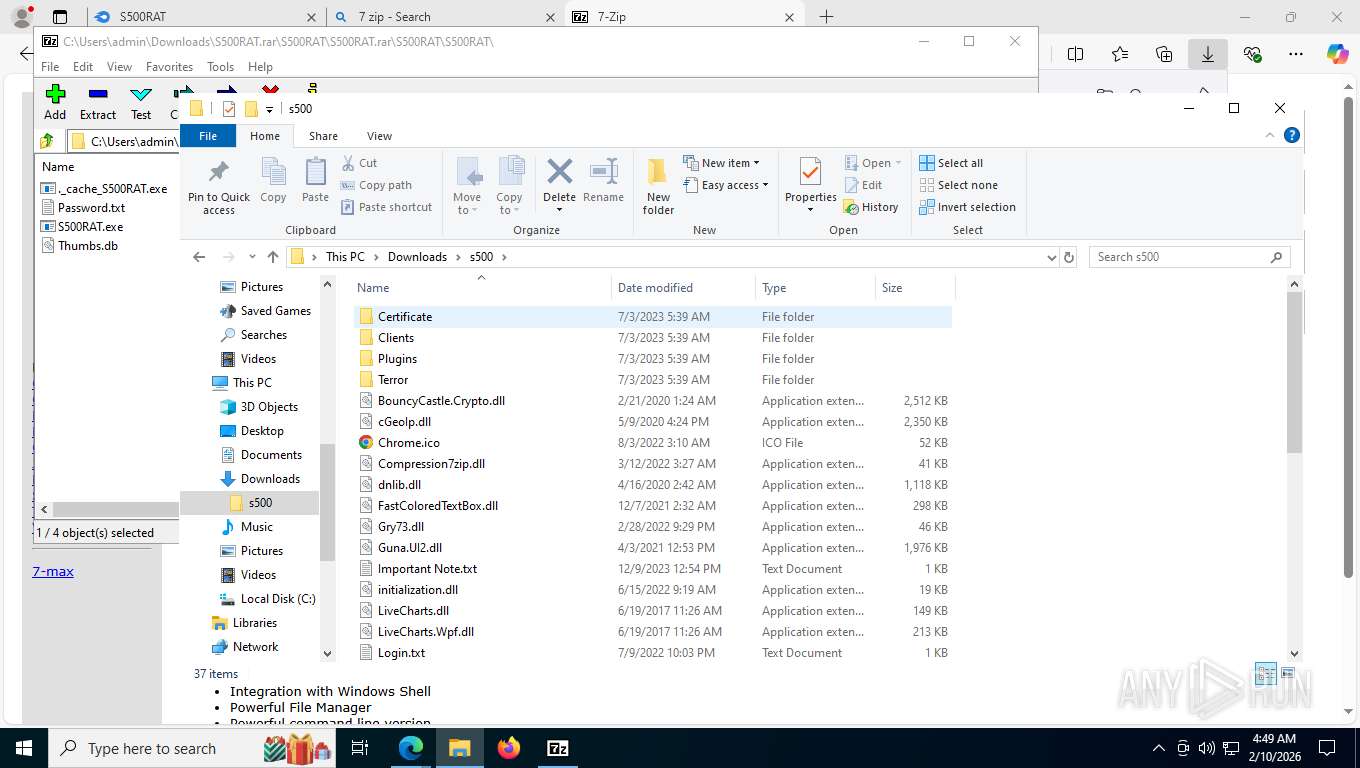
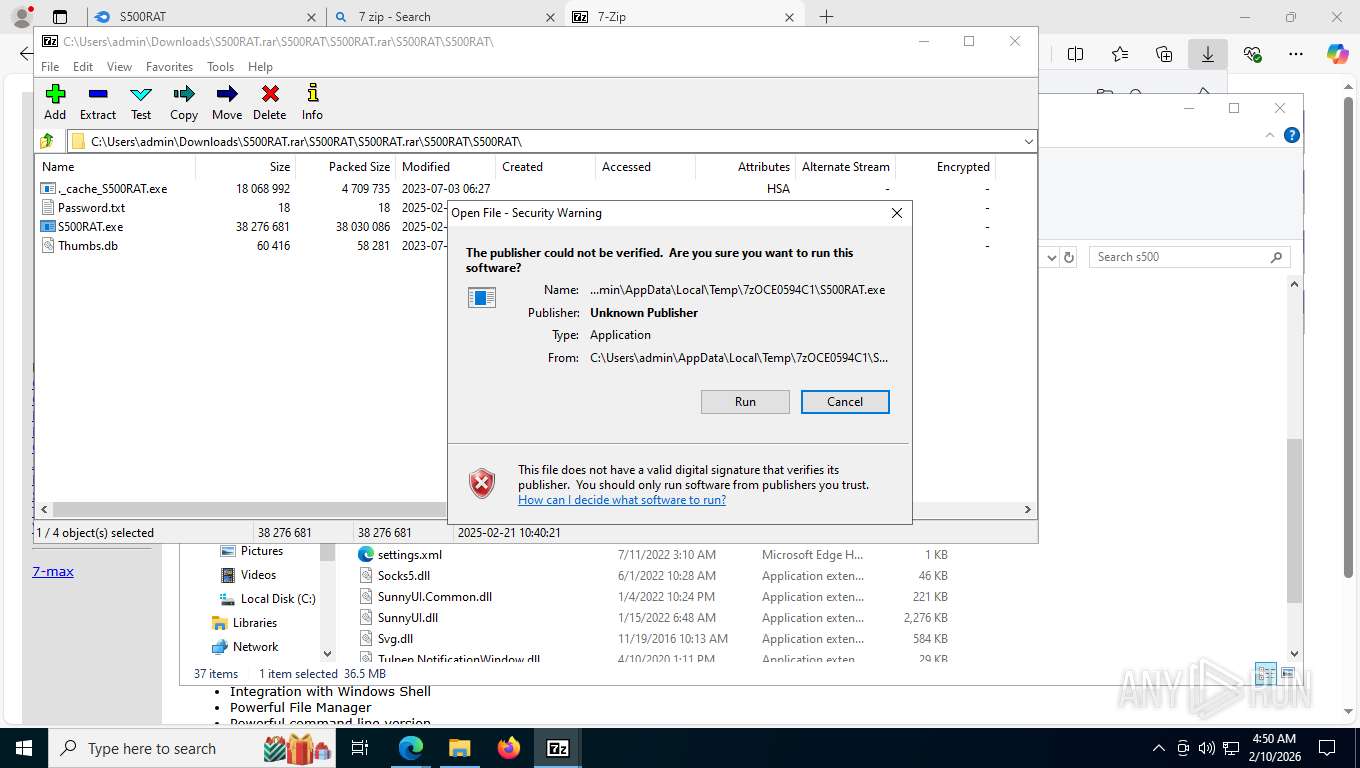
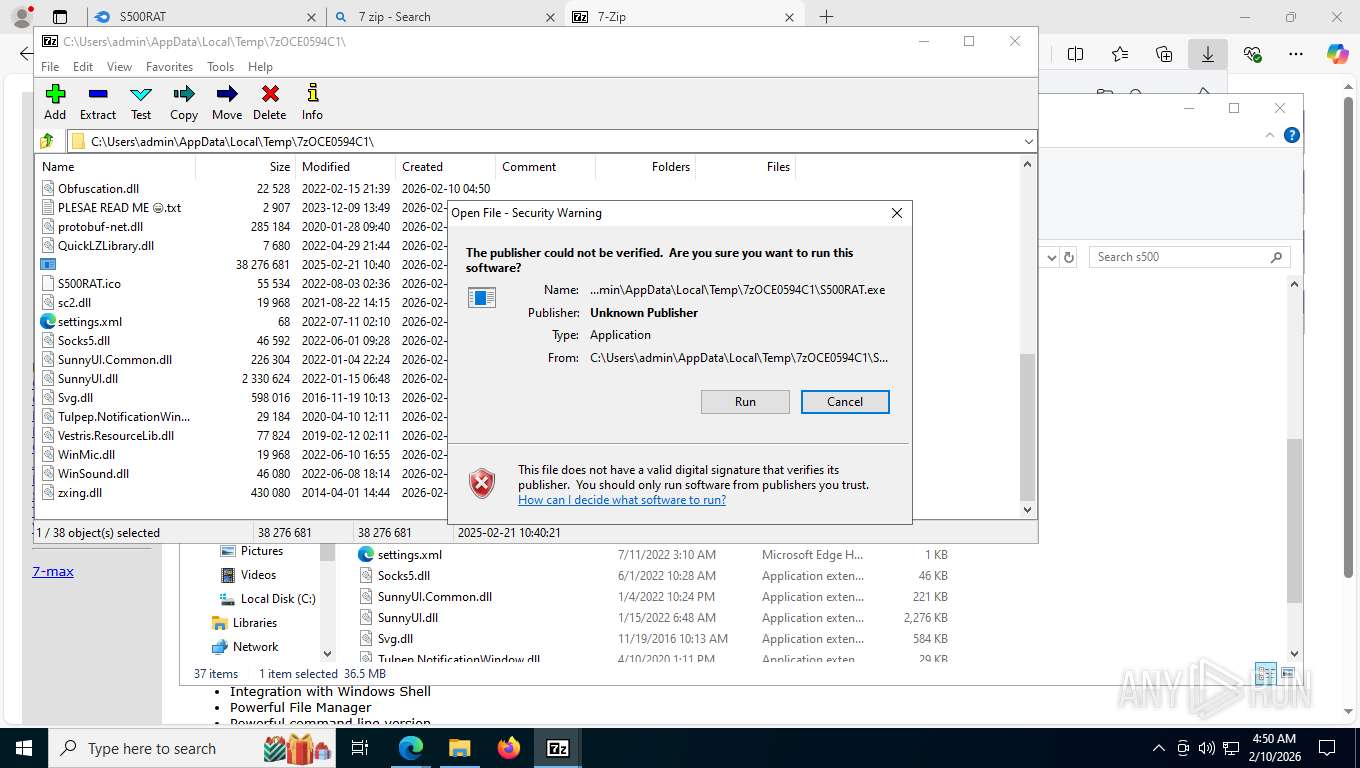
Executing a file with an untrusted certificate
- dllhost.exe (PID: 9020)
- dllhost.exe (PID: 3988)
BlankGrabber has been detected
- dllhost.exe (PID: 9020)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 3164)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 4828)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 4828)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 4828)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 4828)
Changes settings for real-time protection
- powershell.exe (PID: 4828)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 4828)
Changes Controlled Folder Access settings
- powershell.exe (PID: 4828)
Actions looks like stealing of personal data
- dllhost.exe (PID: 3988)
Steals credentials from Web Browsers
- dllhost.exe (PID: 3988)
AGENTTESLA has been detected
- powershell.exe (PID: 1692)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 9392)
Adds process to the Windows Defender exclusion list
- svchost.exe (PID: 2336)
BLANKGRABBER has been detected (SURICATA)
- dllhost.exe (PID: 3988)
Uses Task Scheduler to run other applications
- svchost.exe (PID: 2336)
XWORM has been detected
- svchost.exe (PID: 2336)
Create files in the Startup directory
- svchost.exe (PID: 2336)
SUSPICIOUS
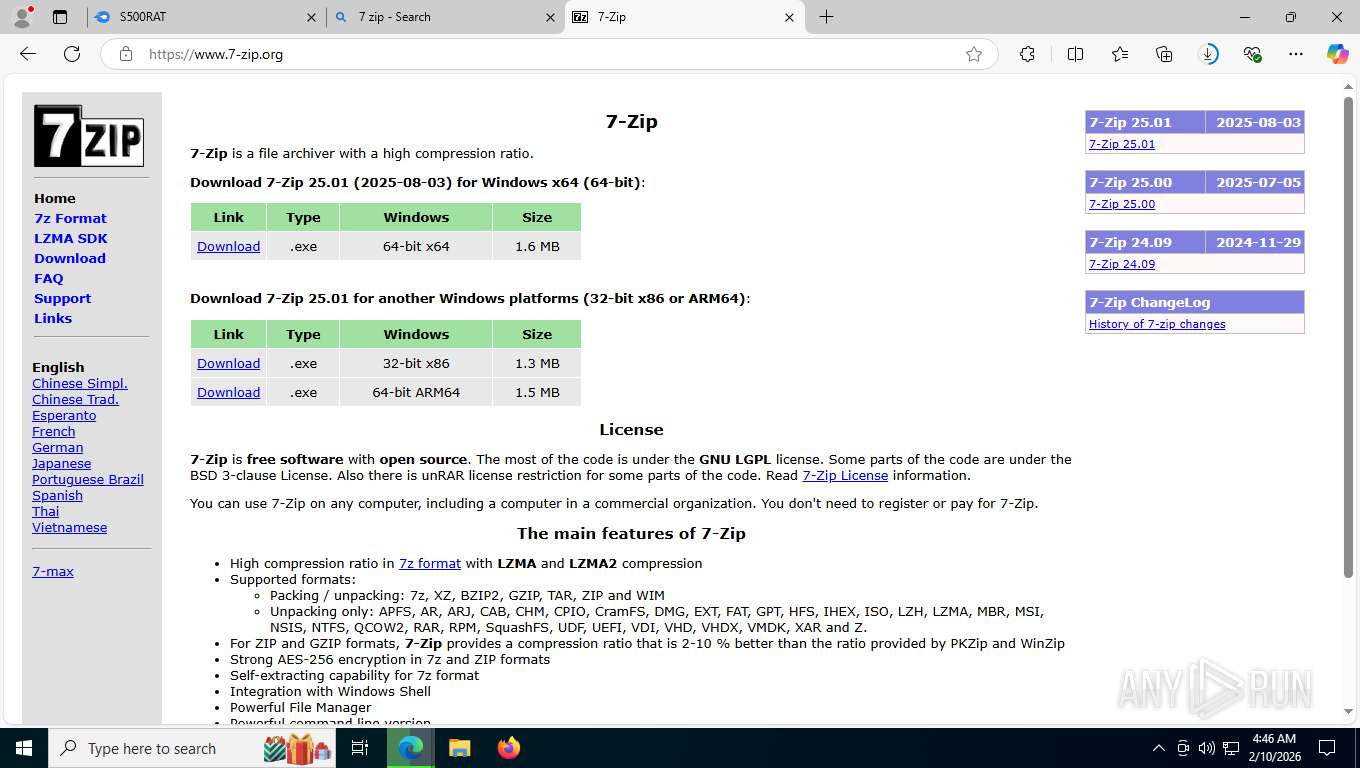
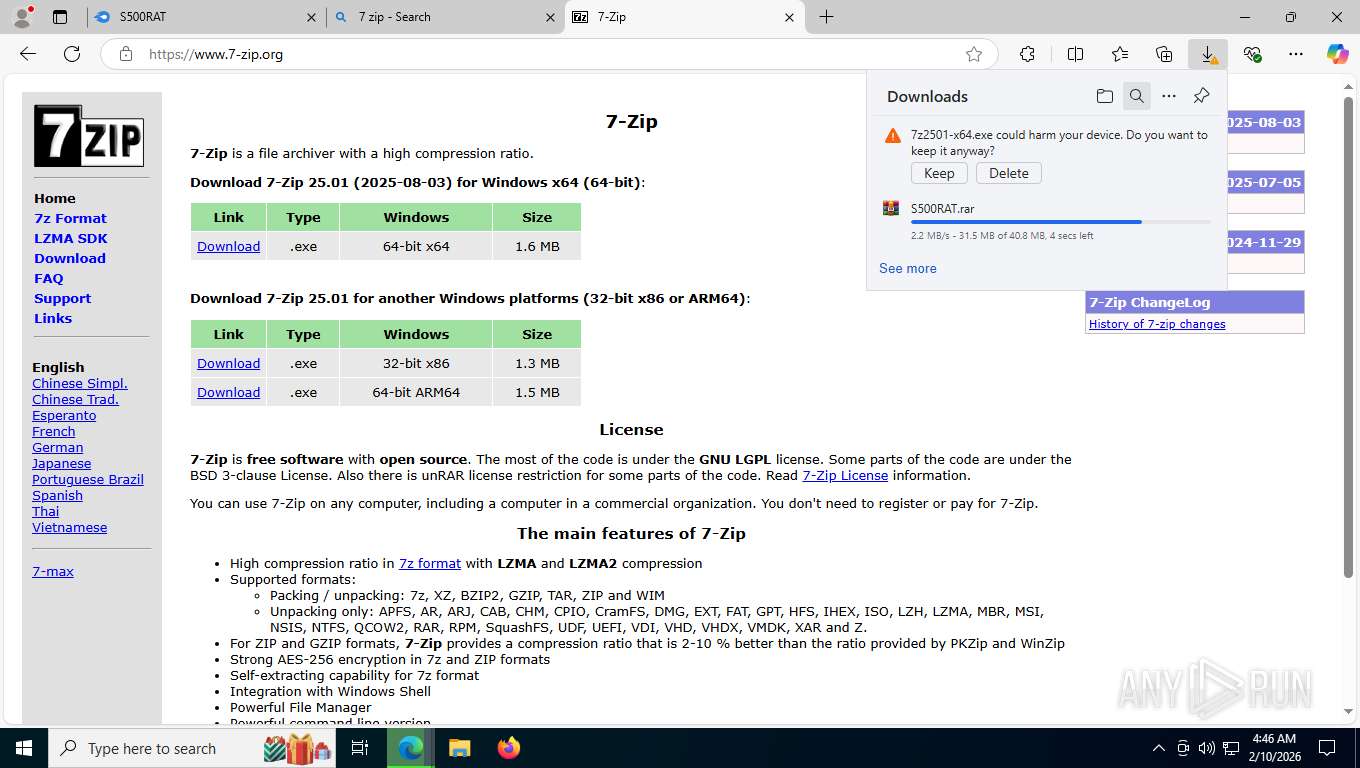
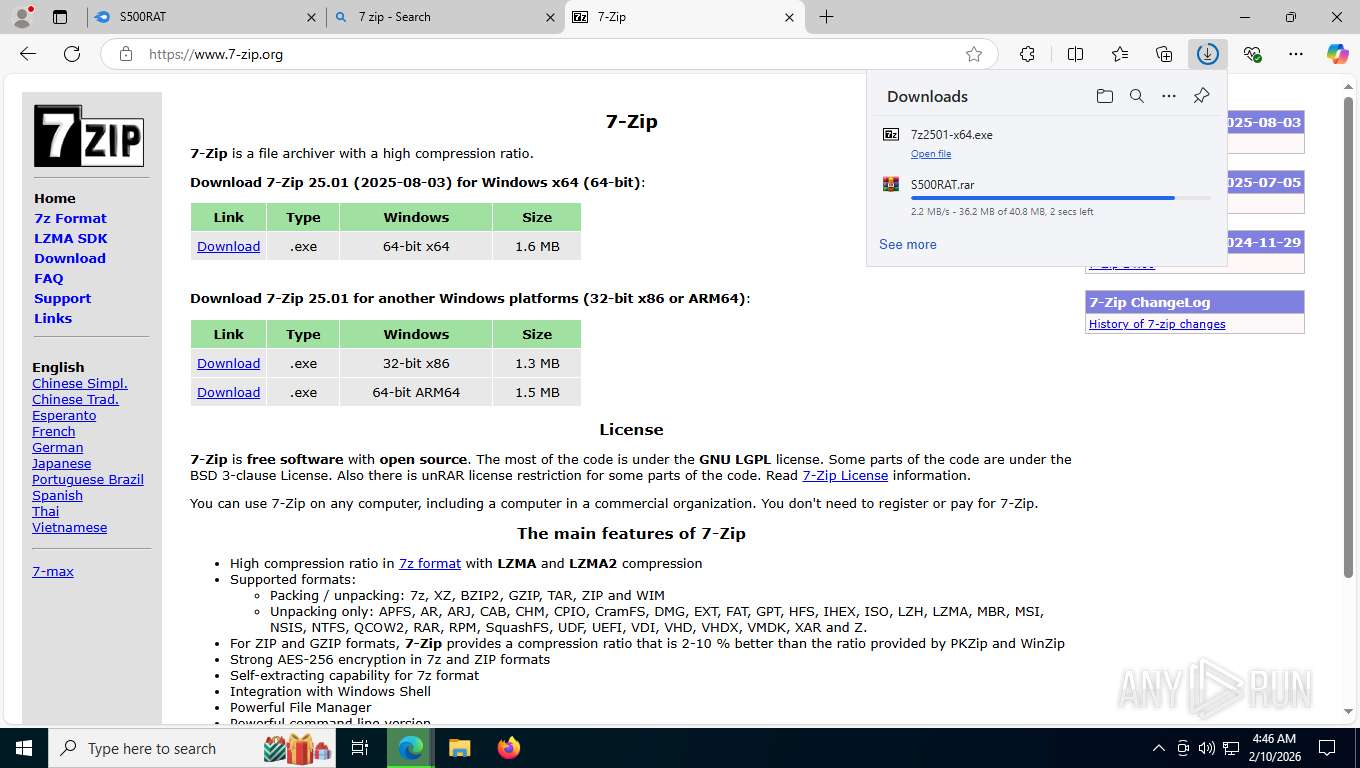
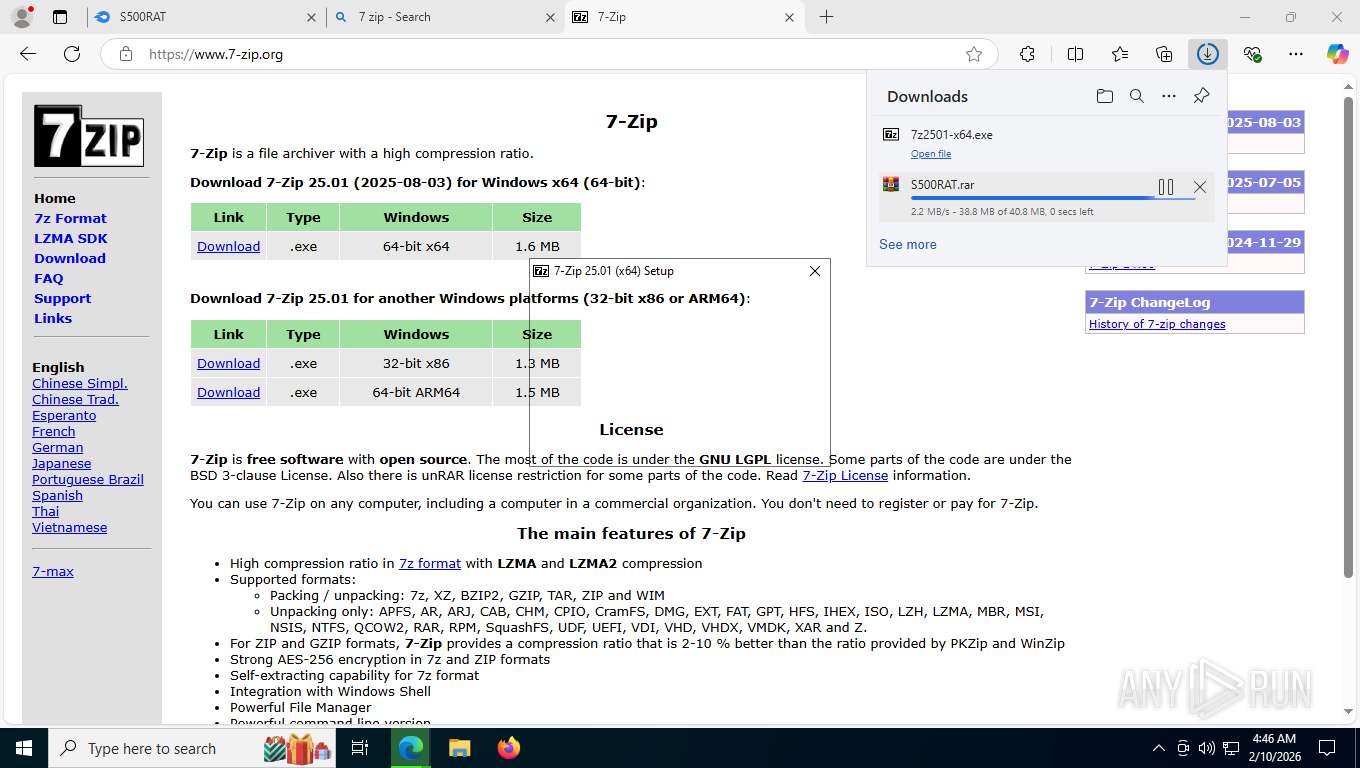
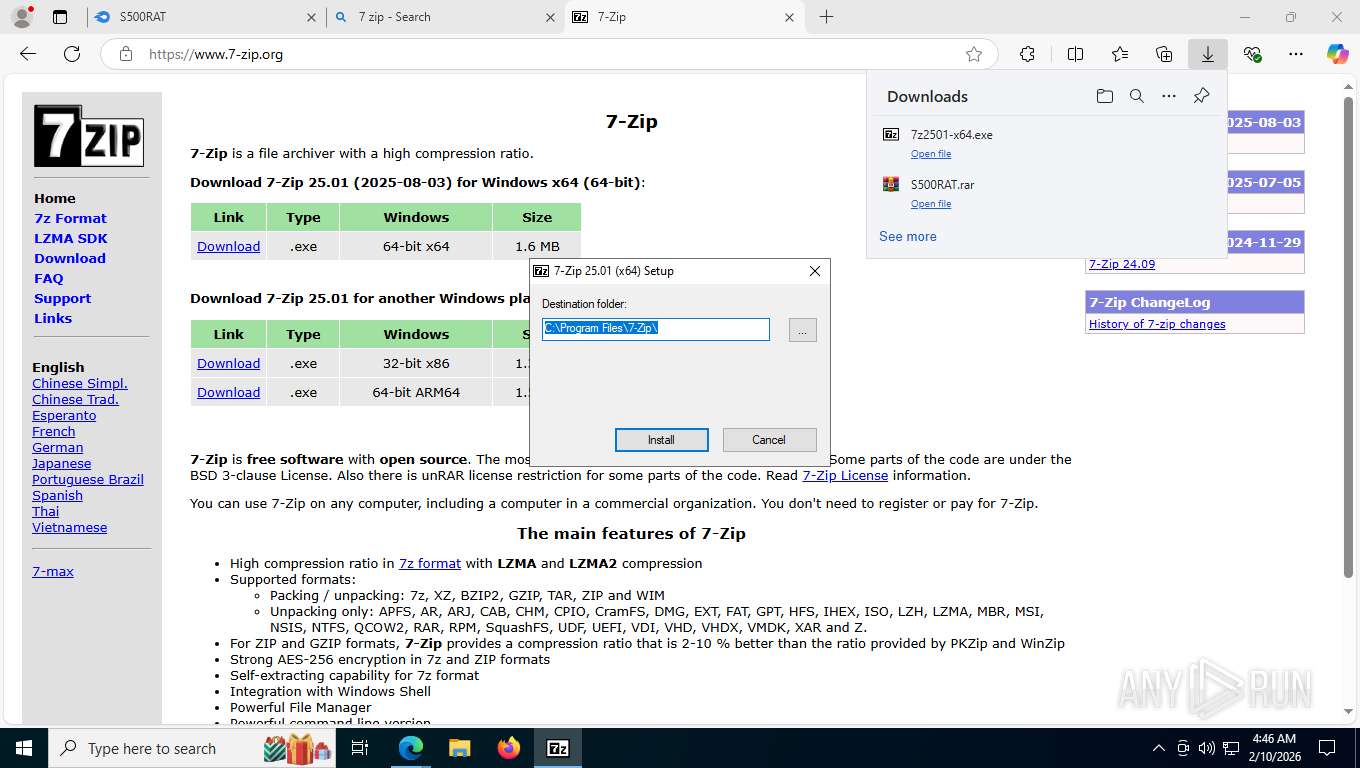
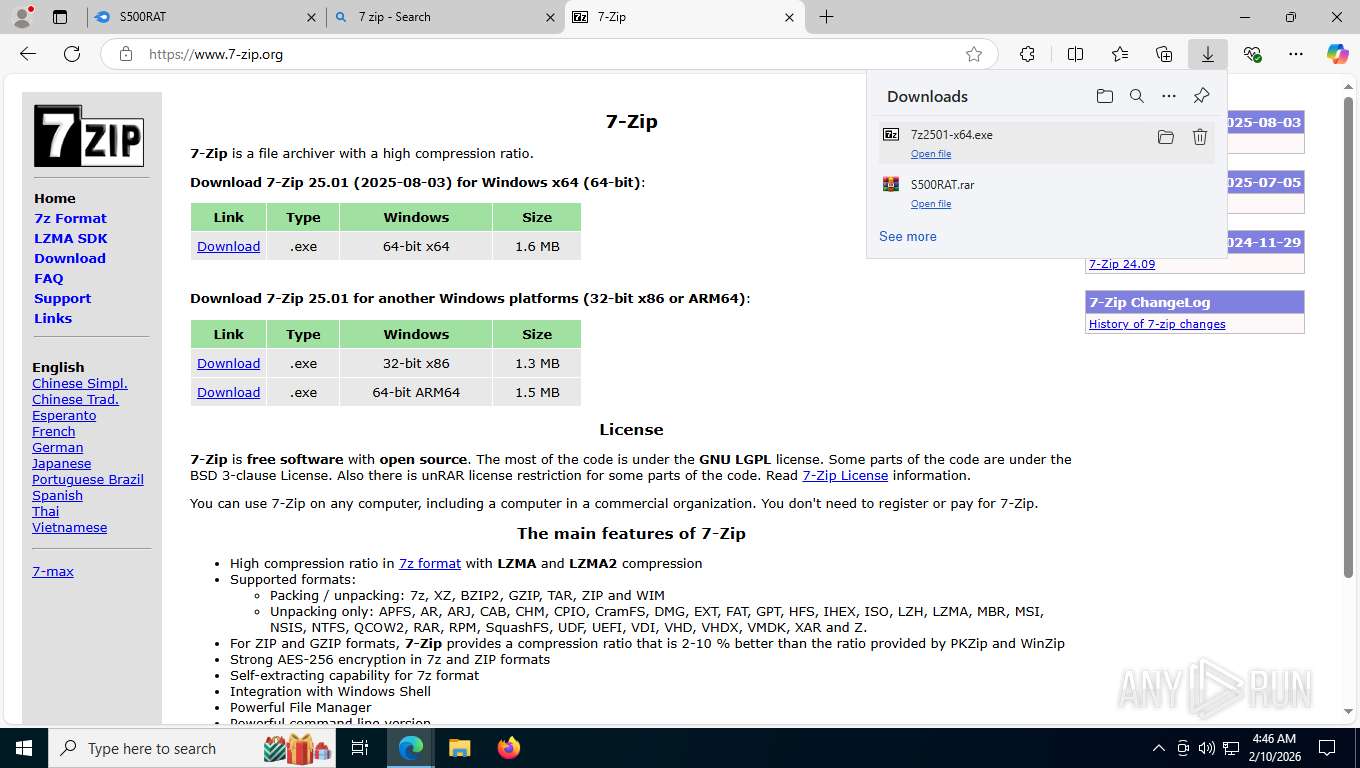
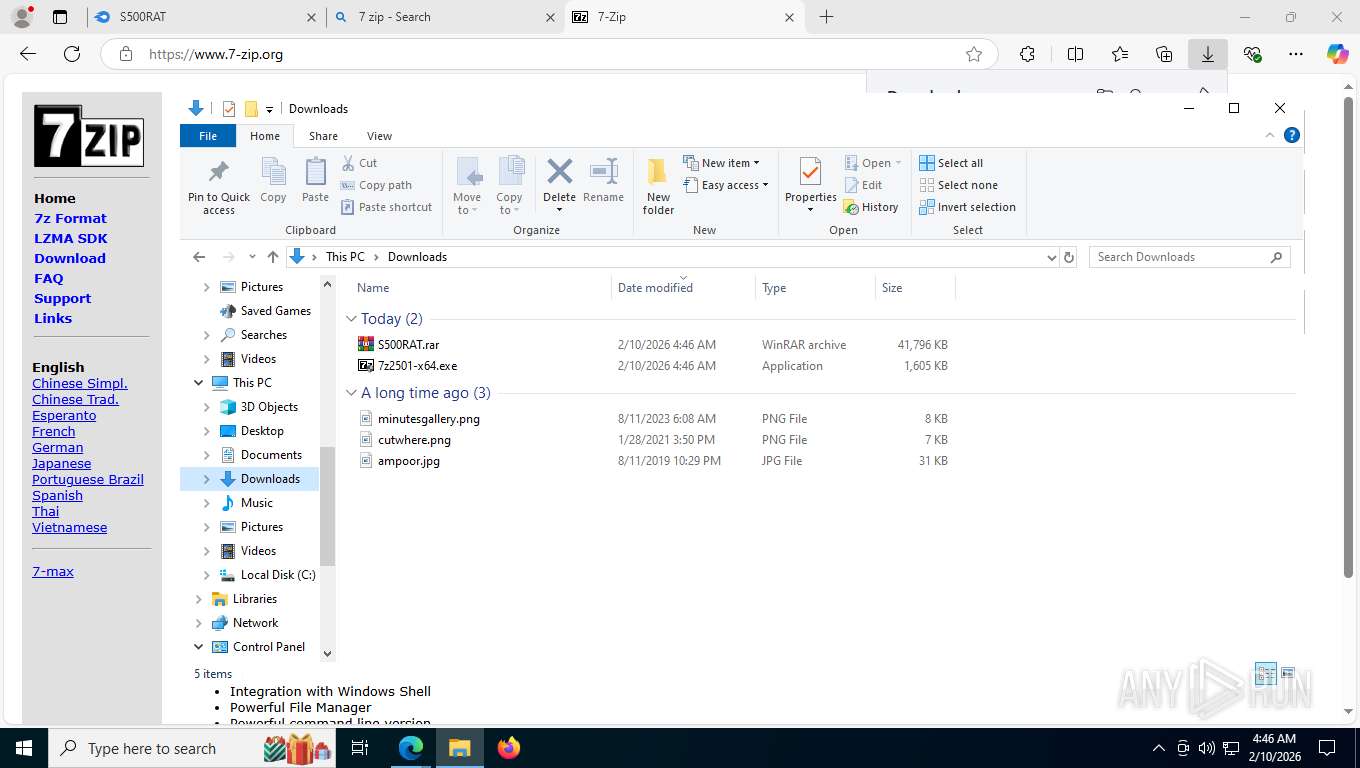
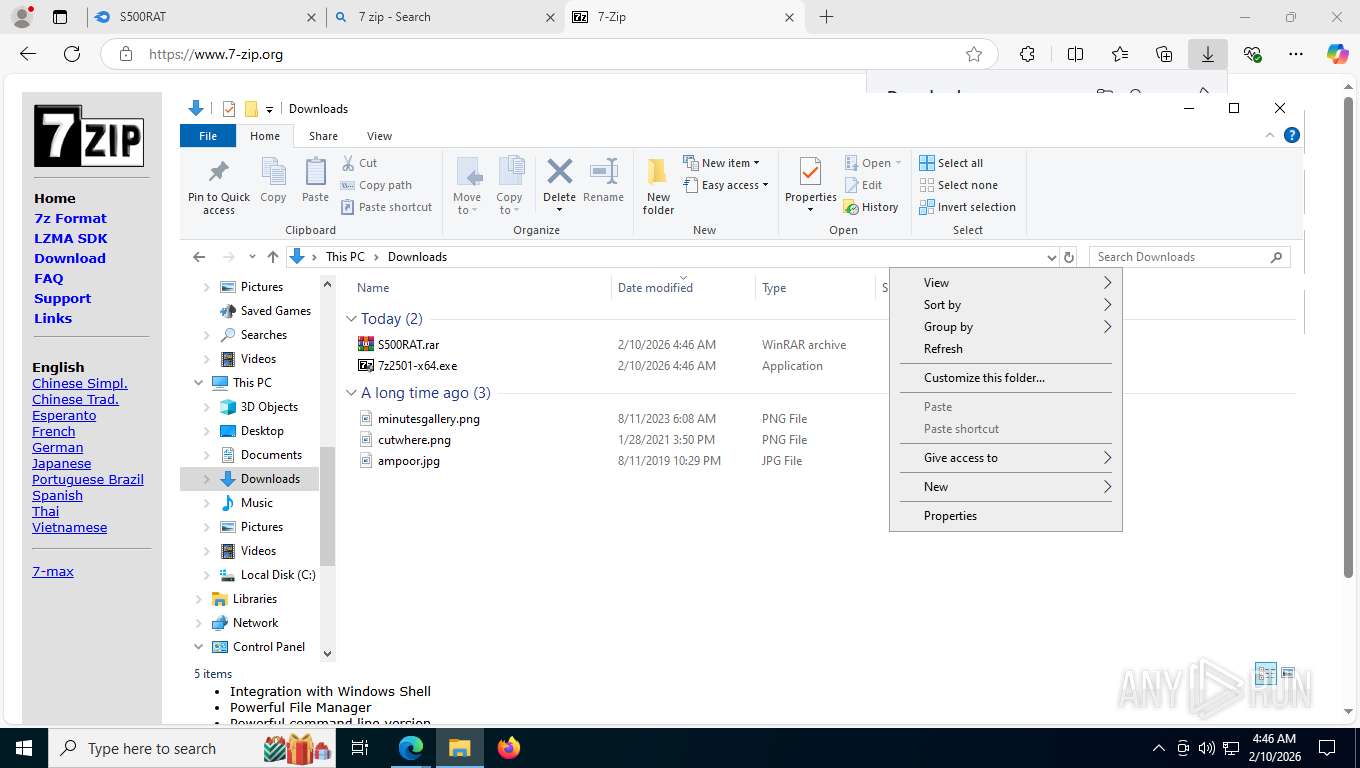
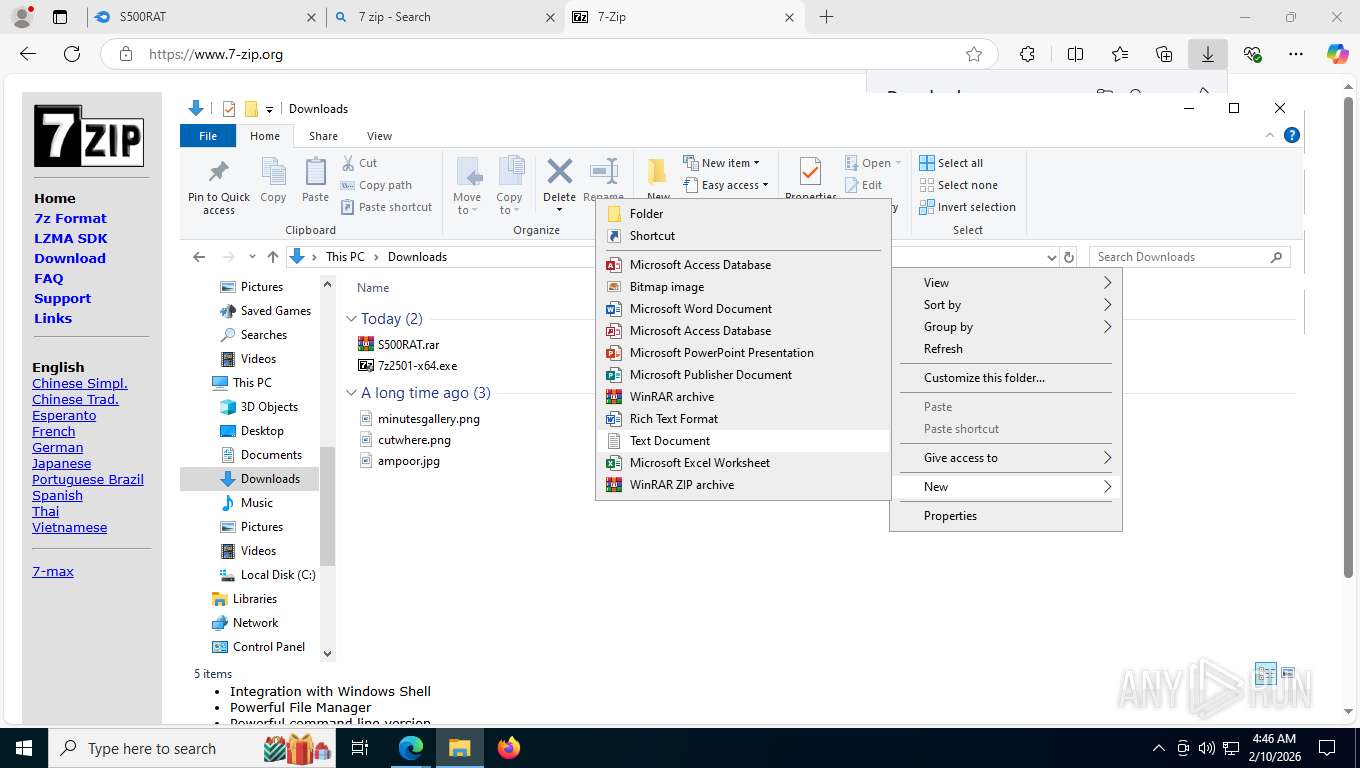
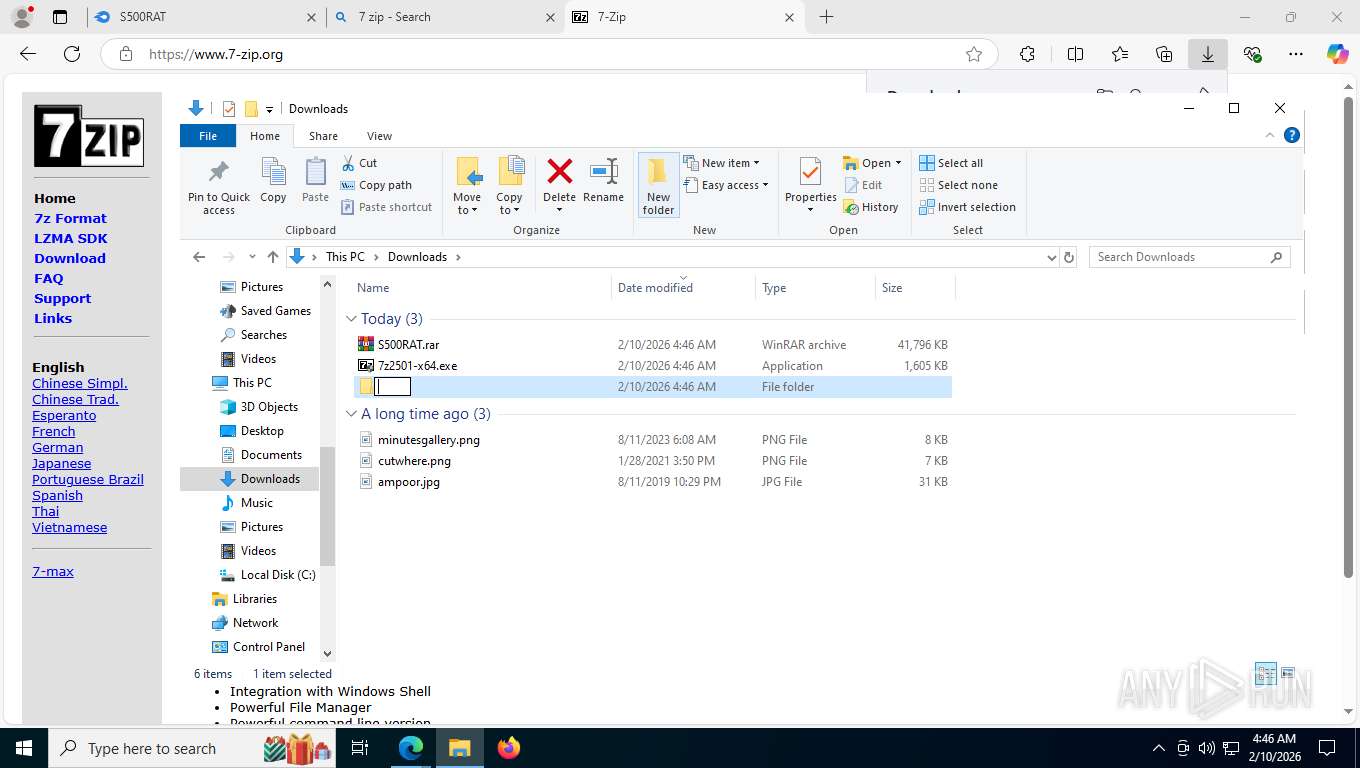
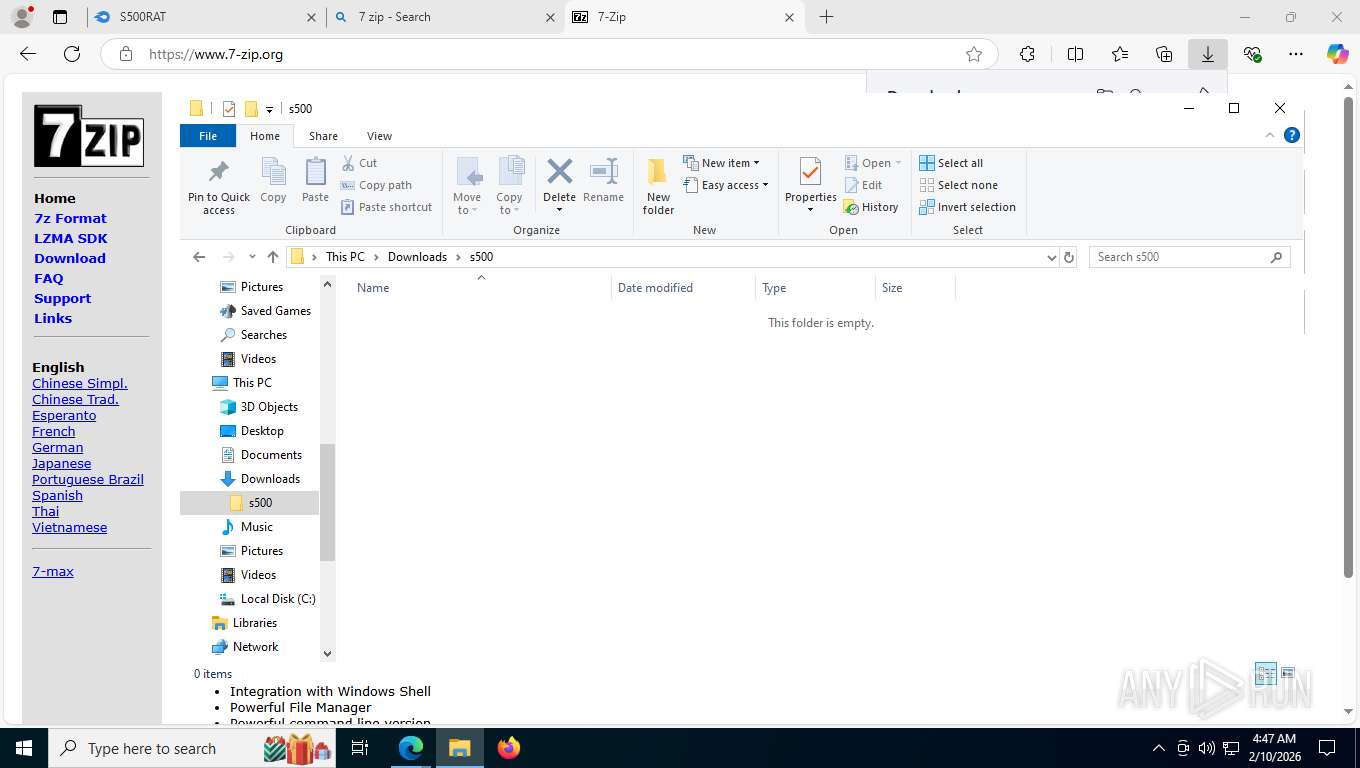
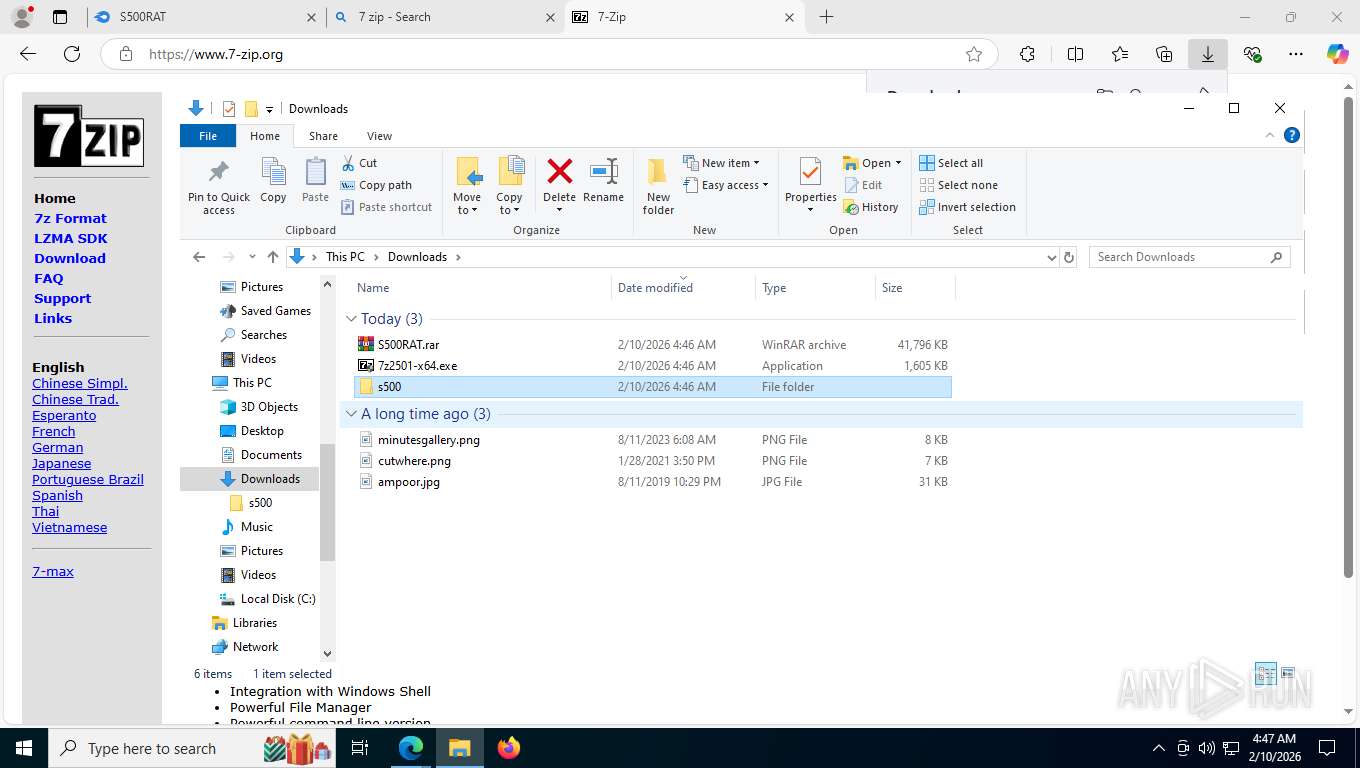
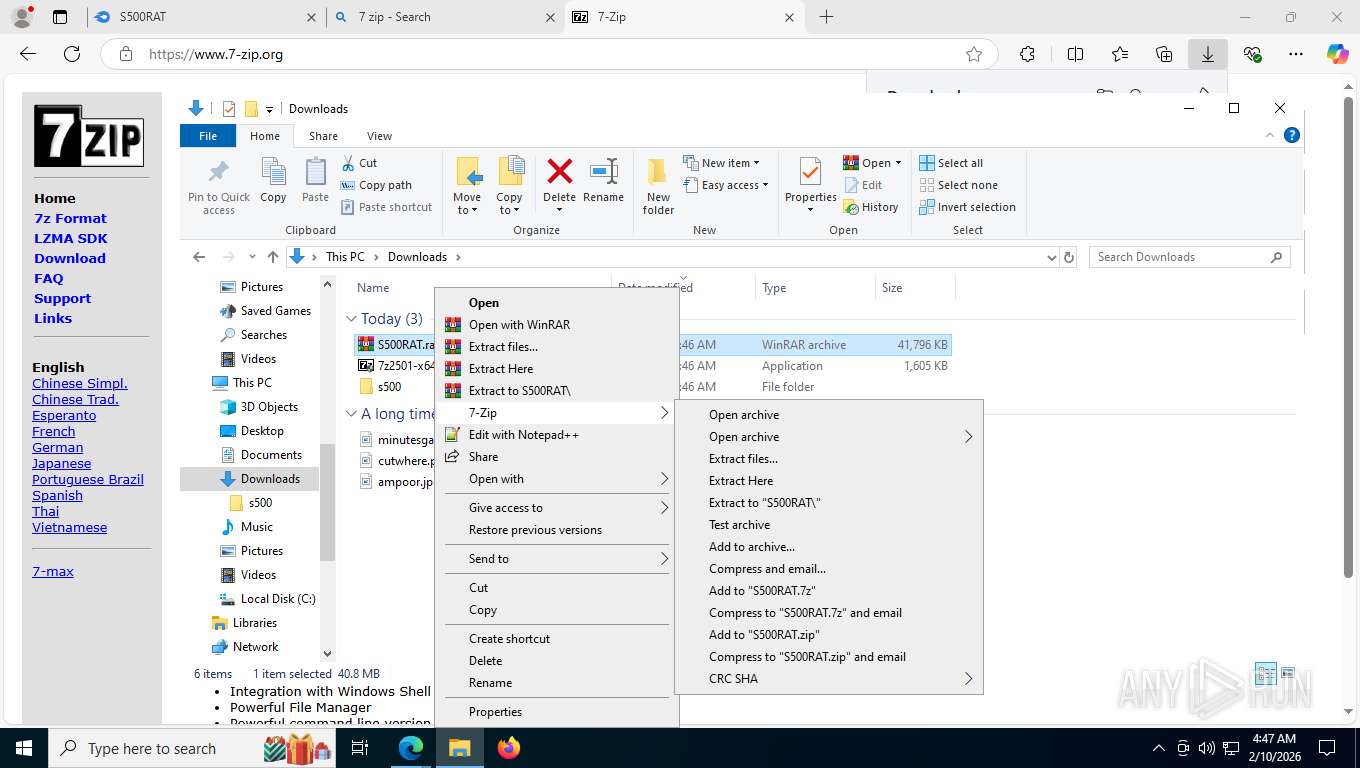
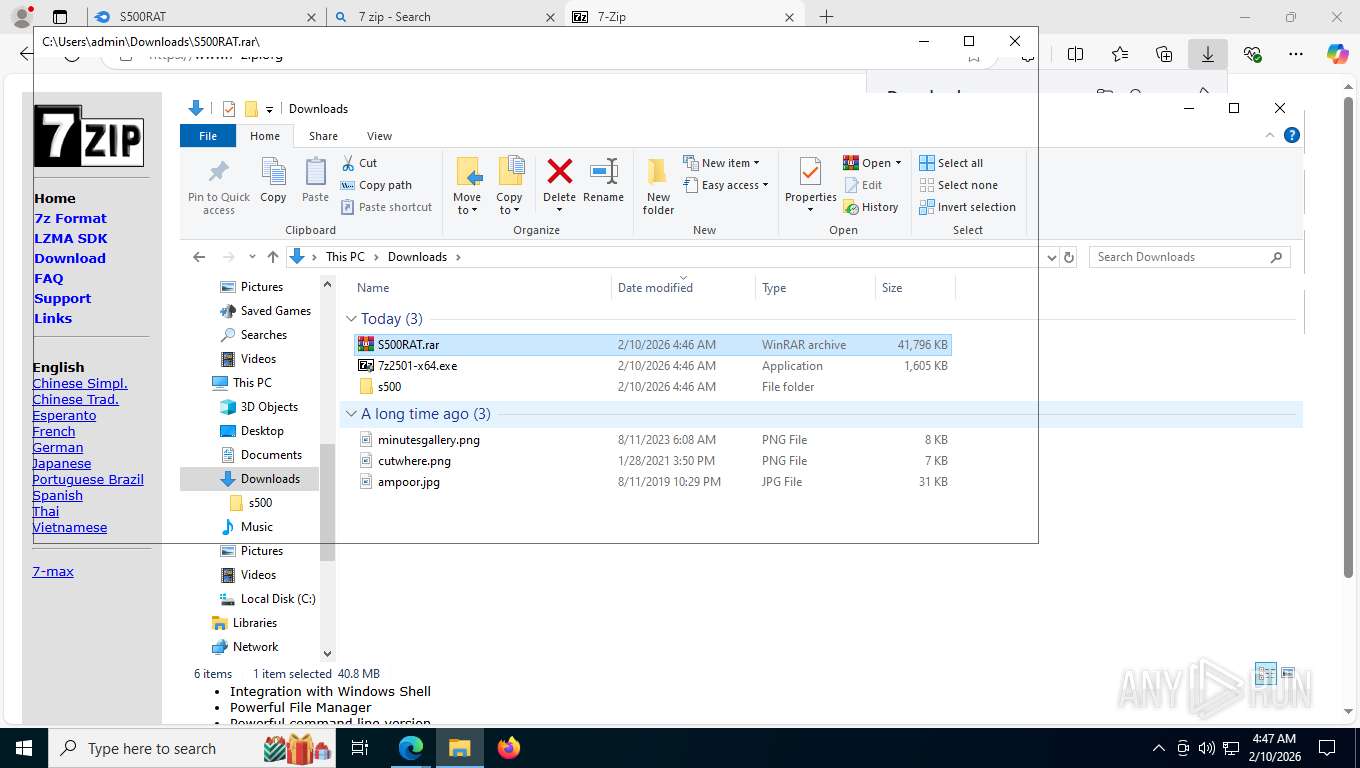
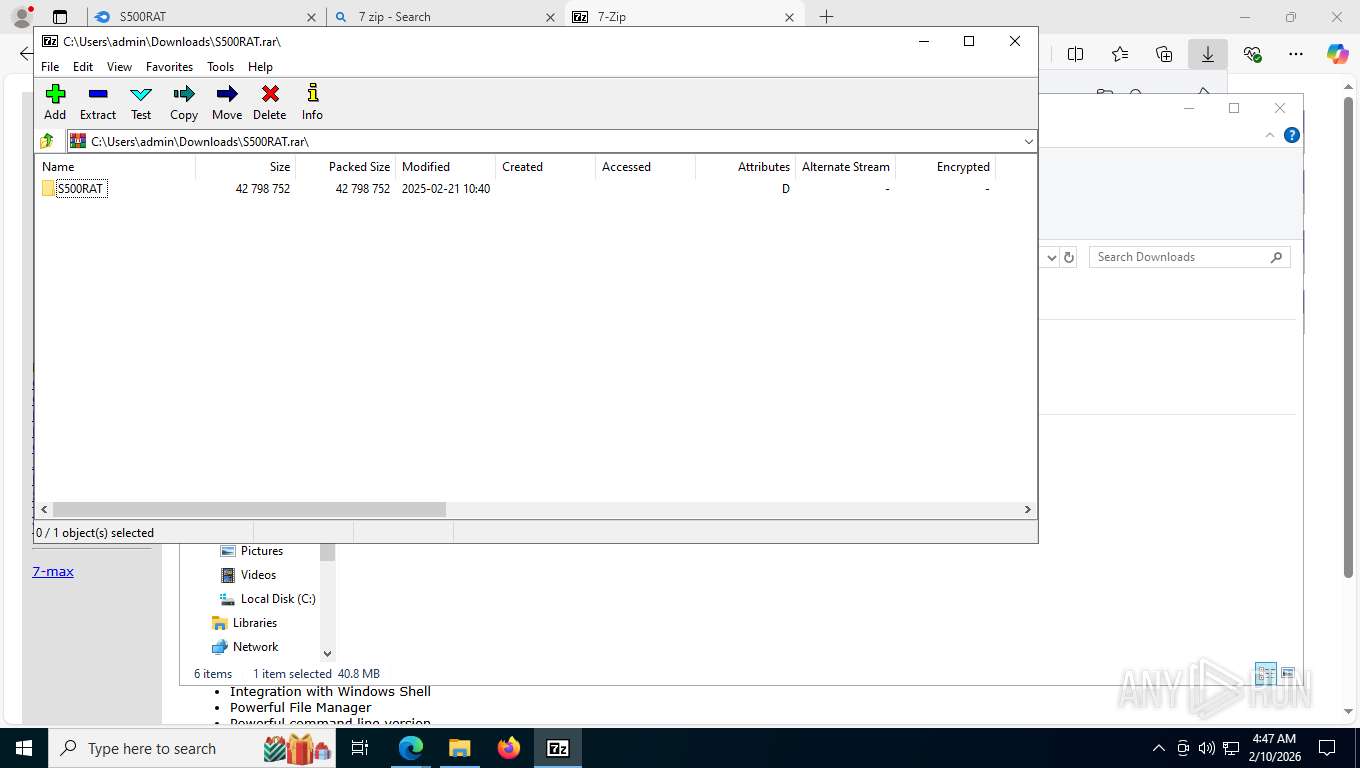
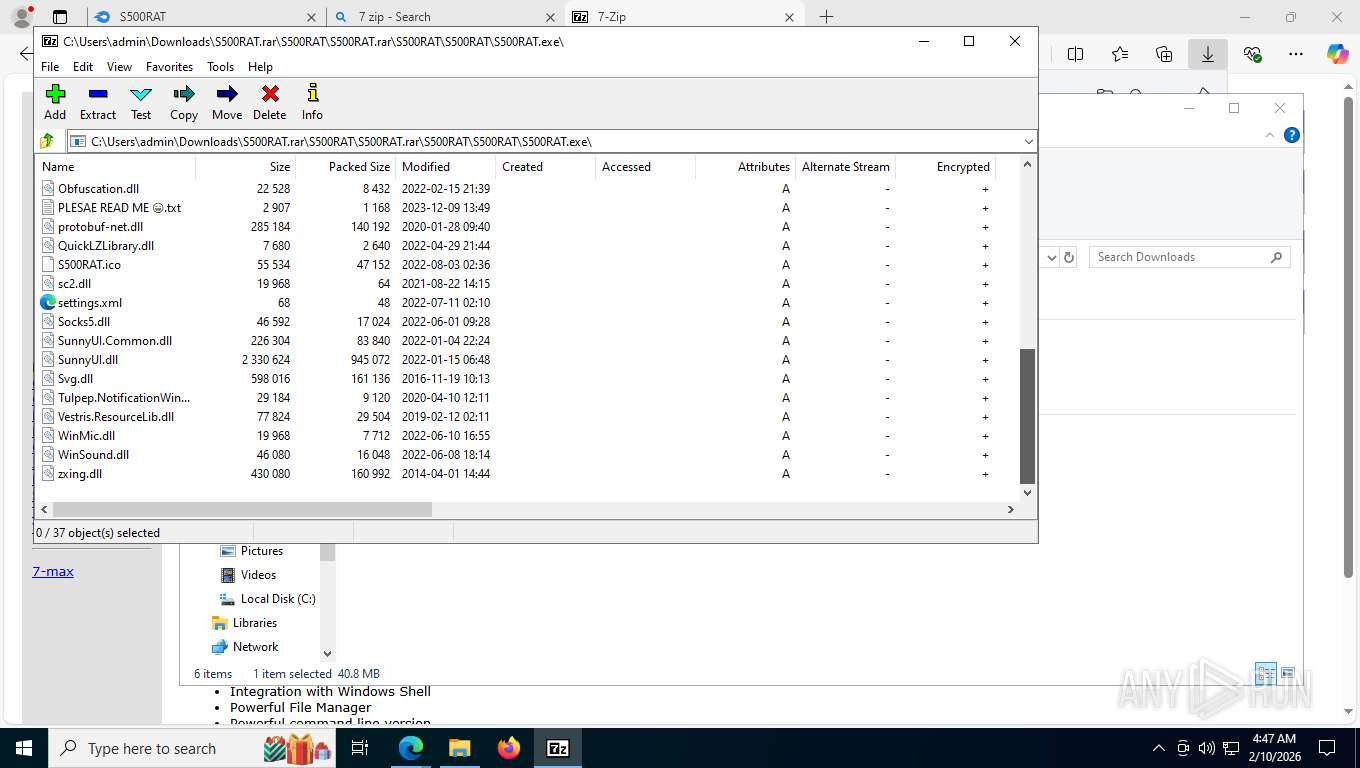
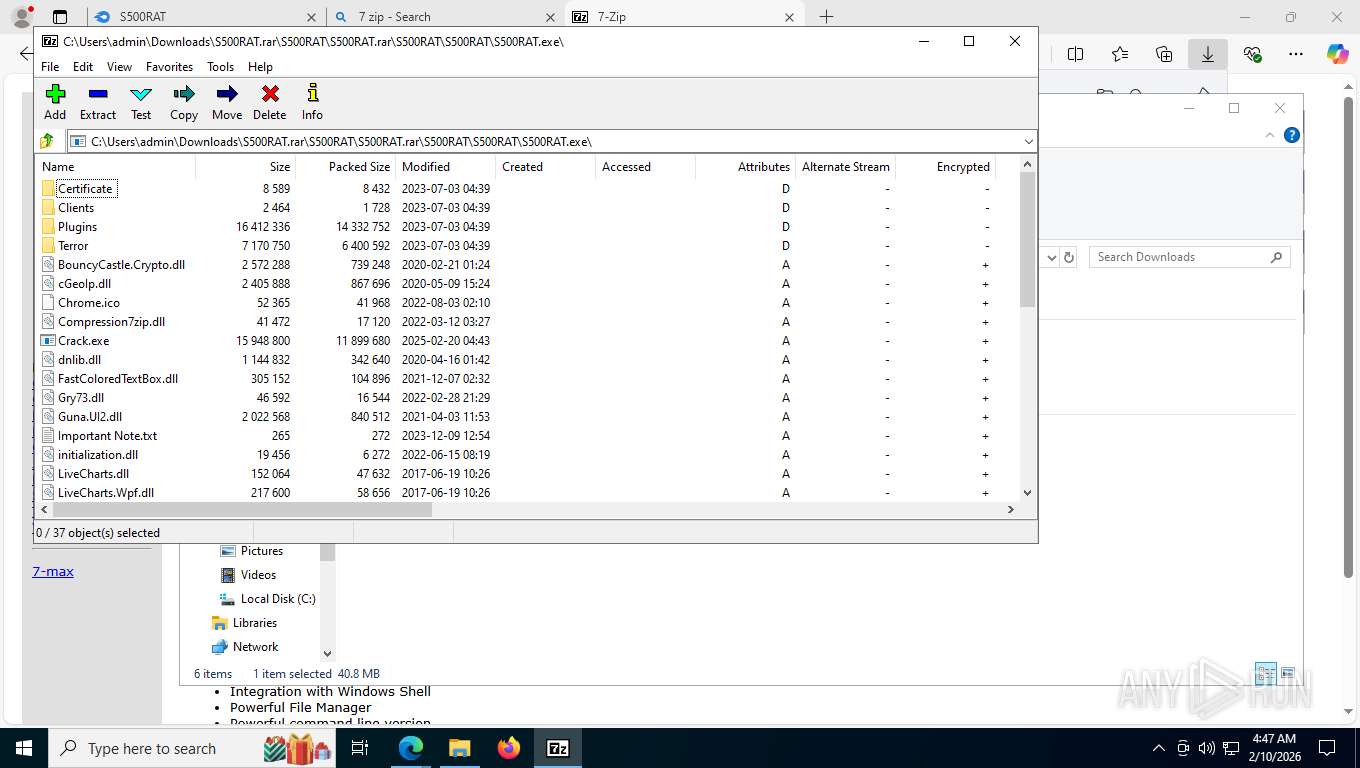
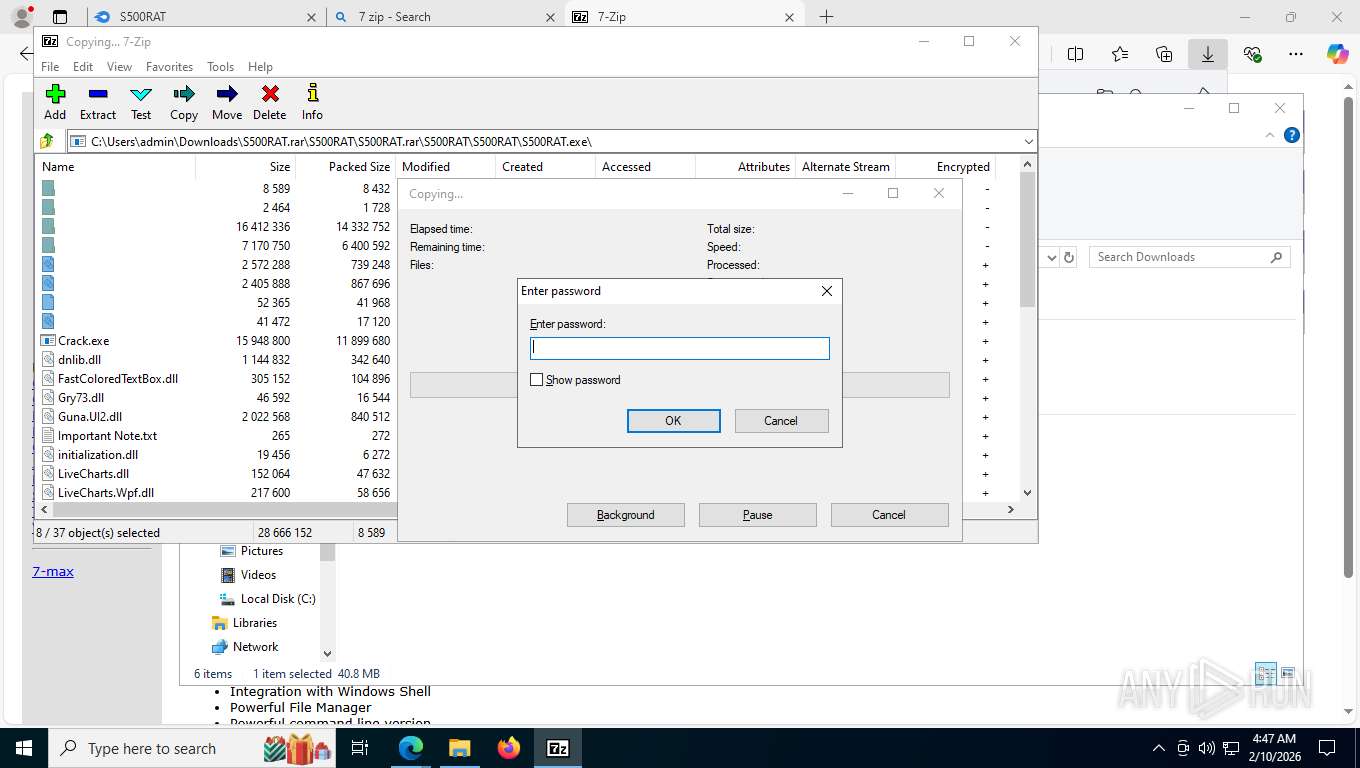
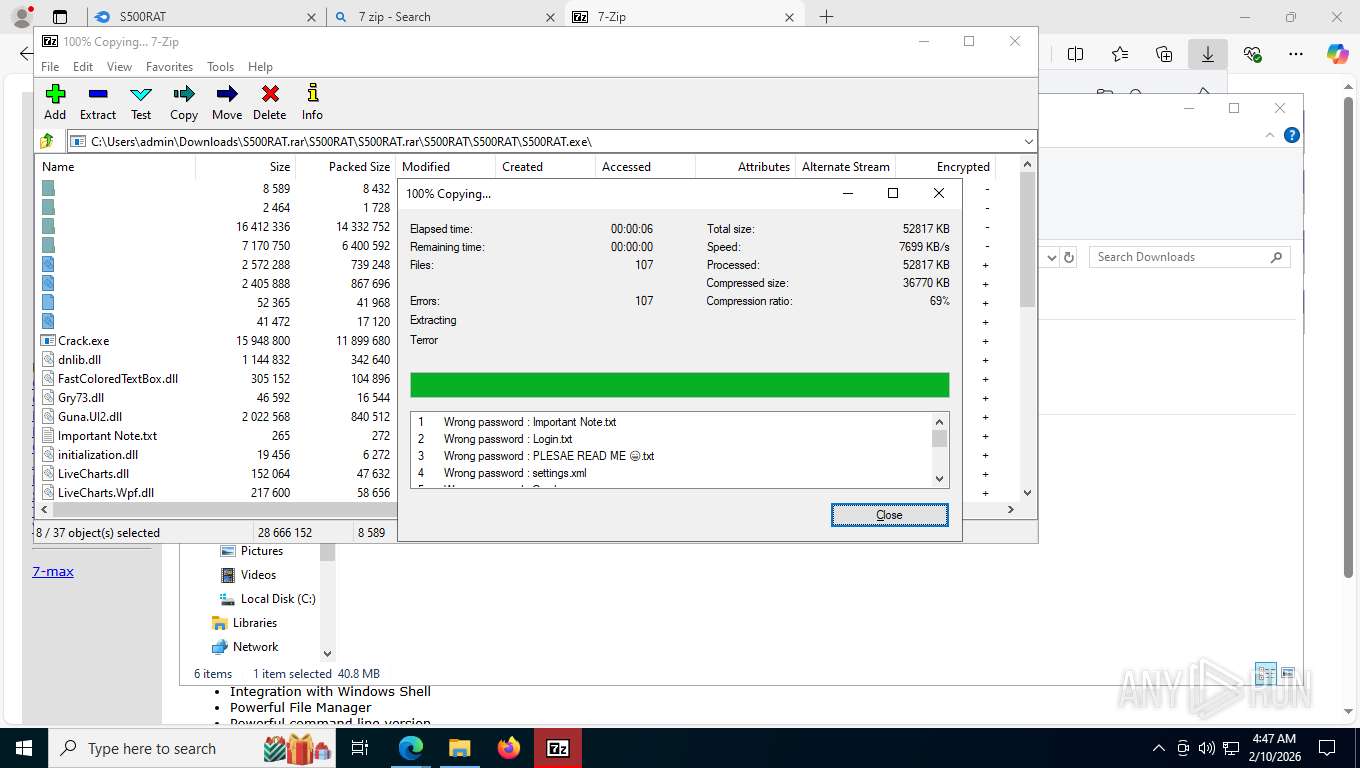
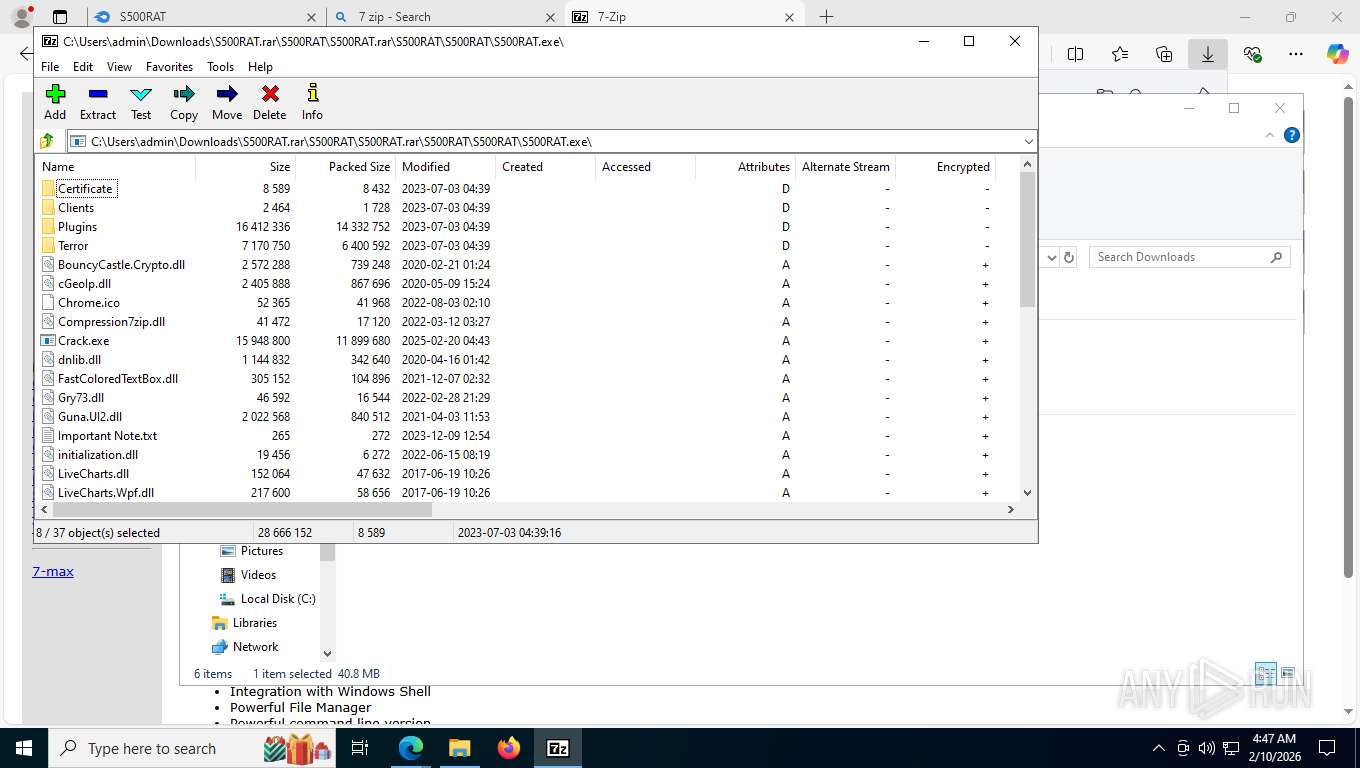
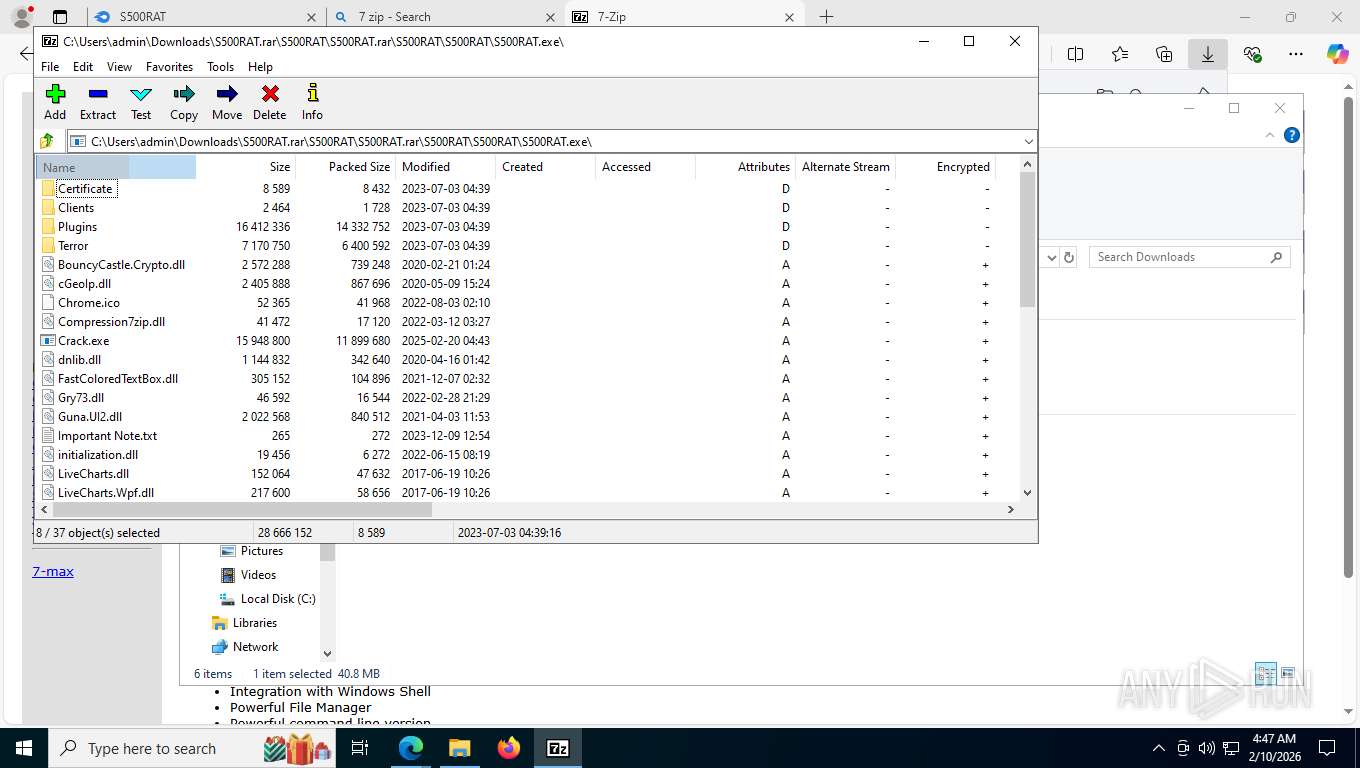
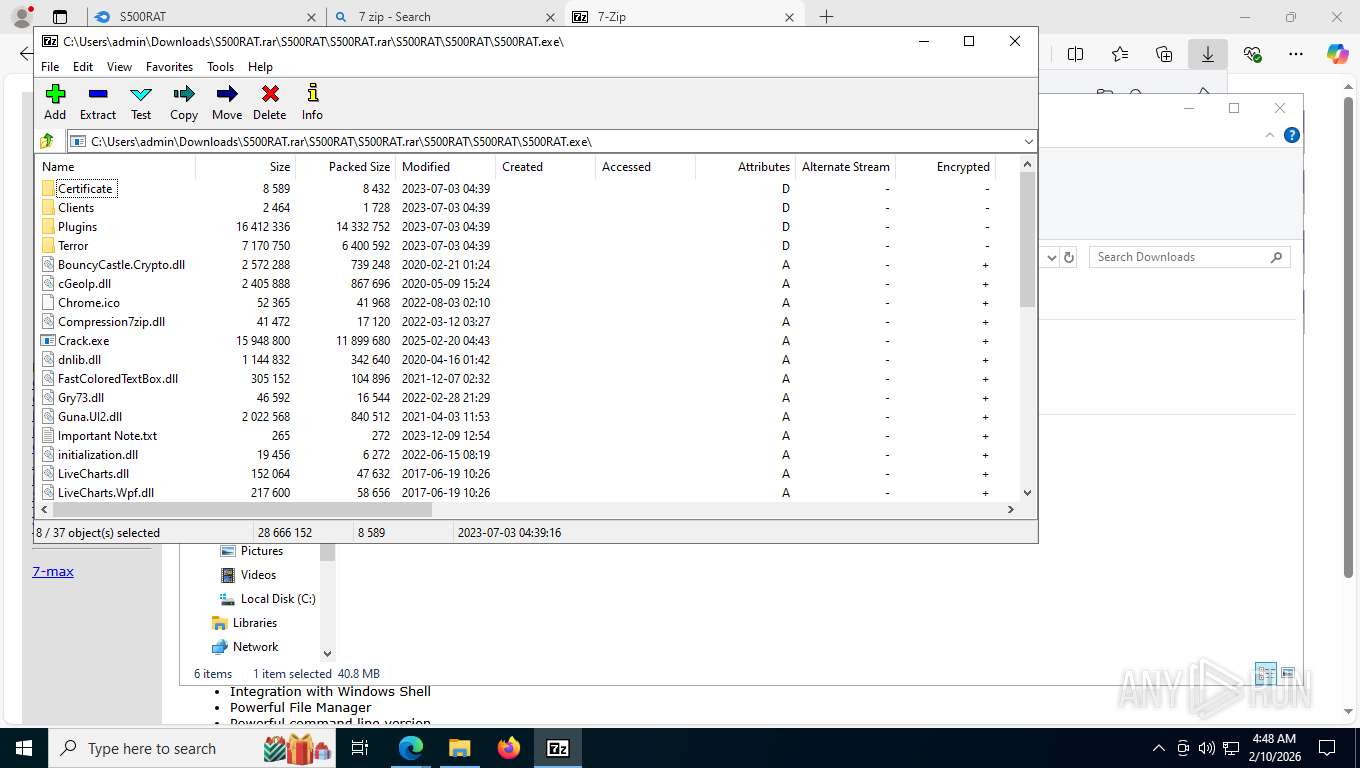
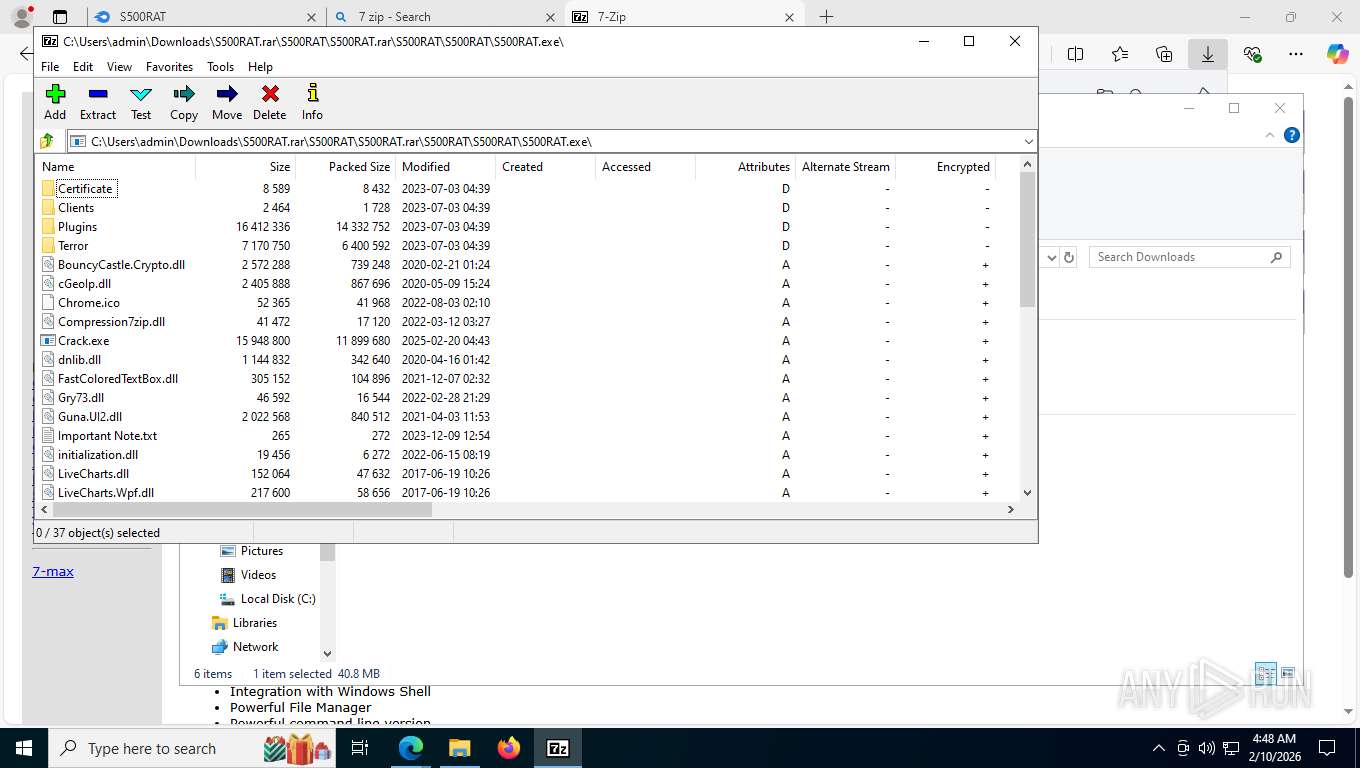
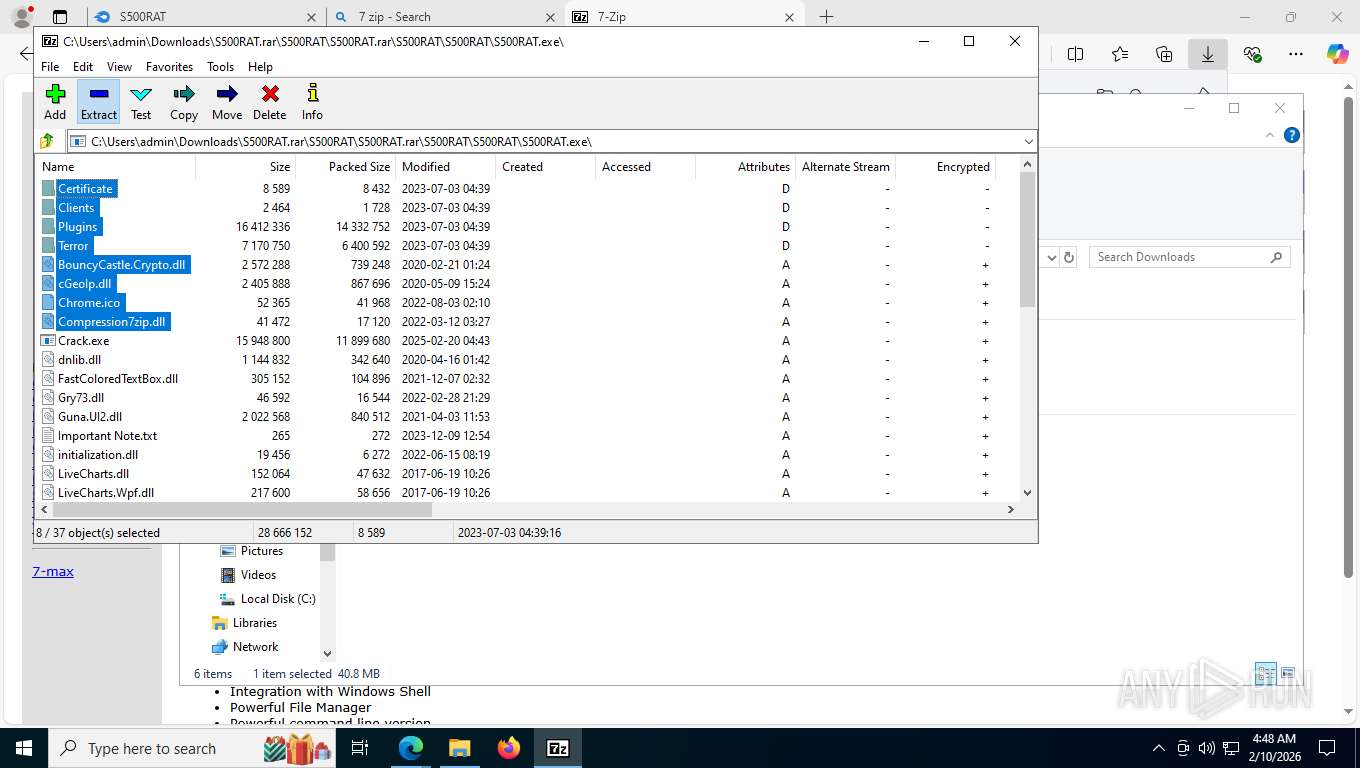
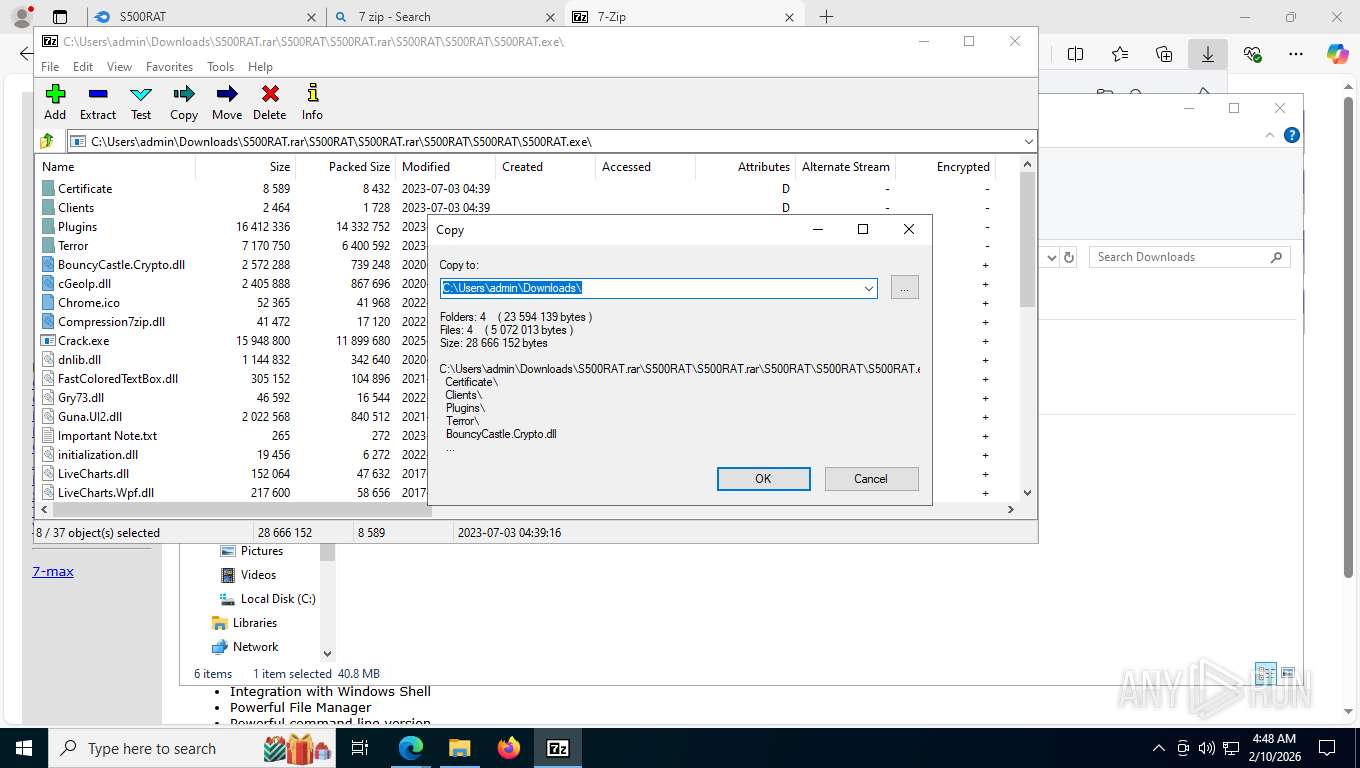
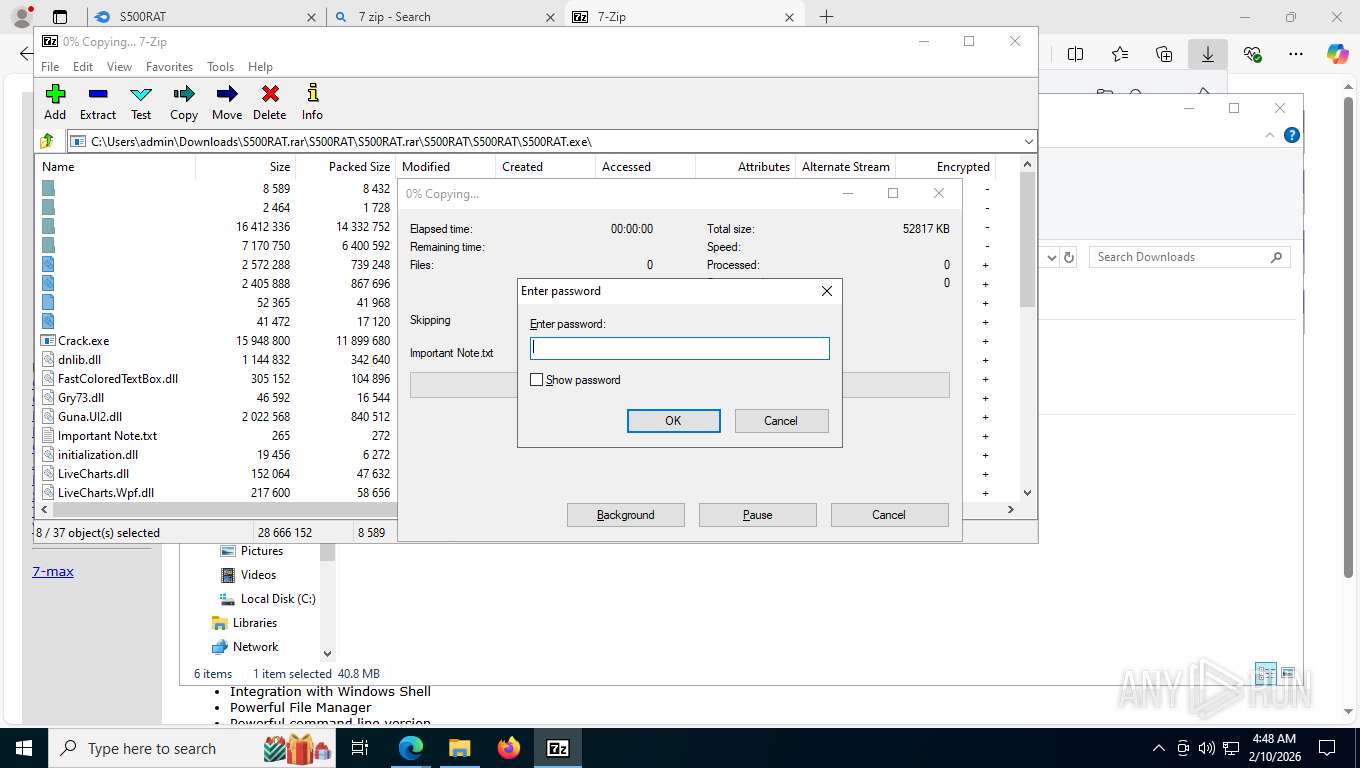
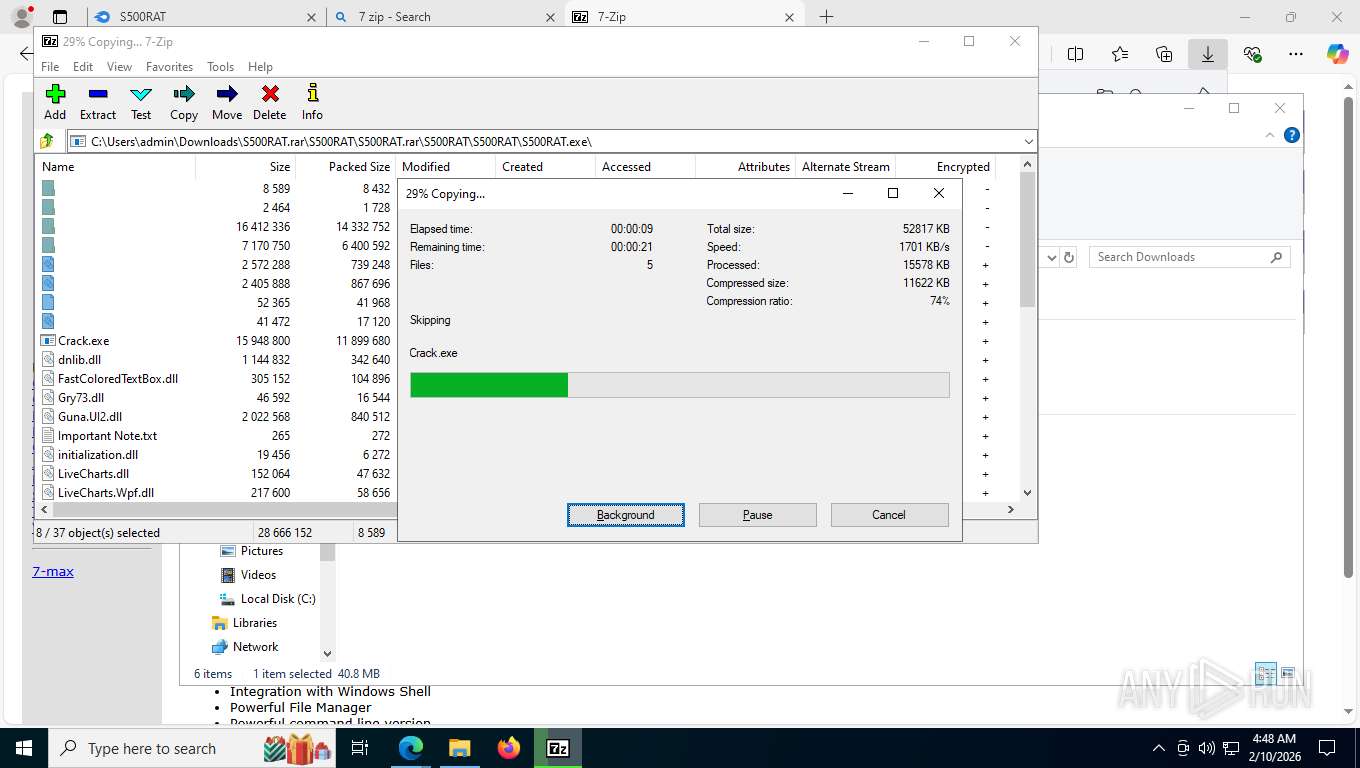
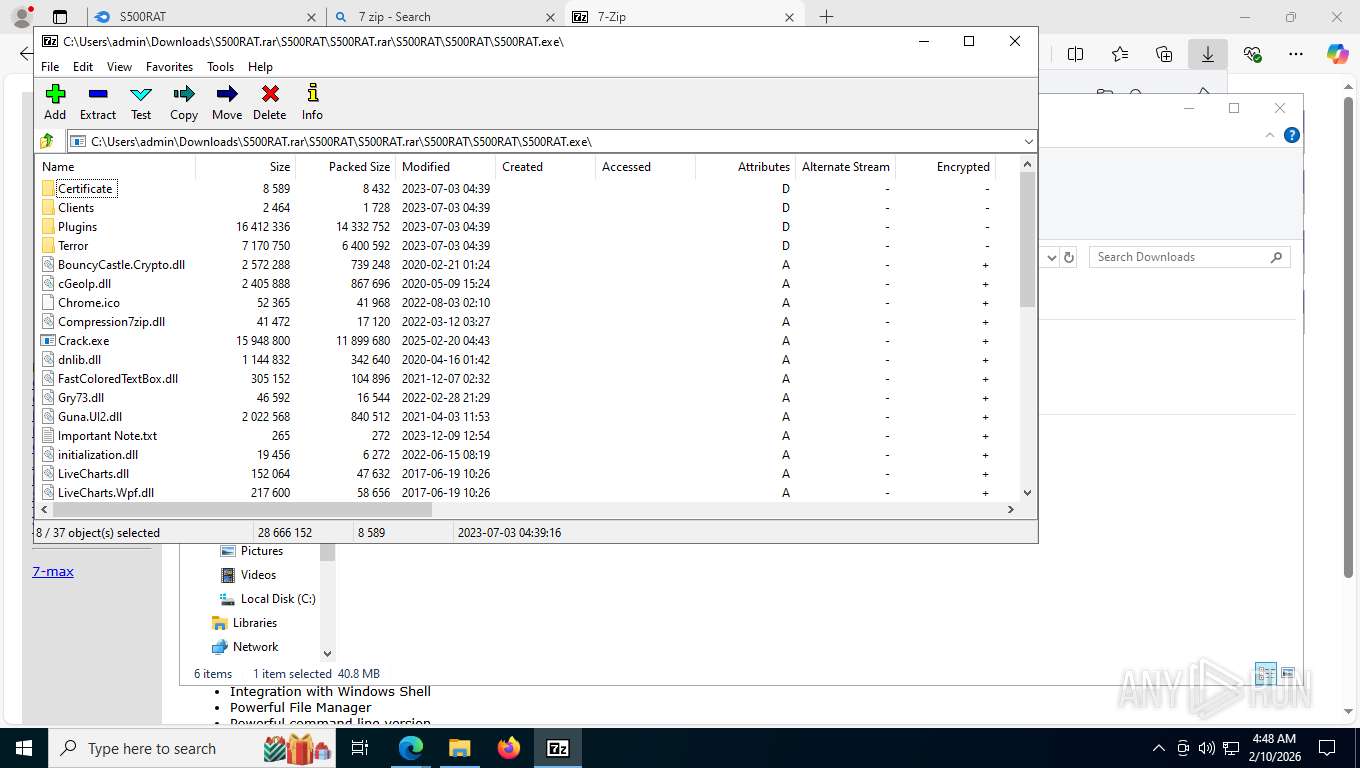
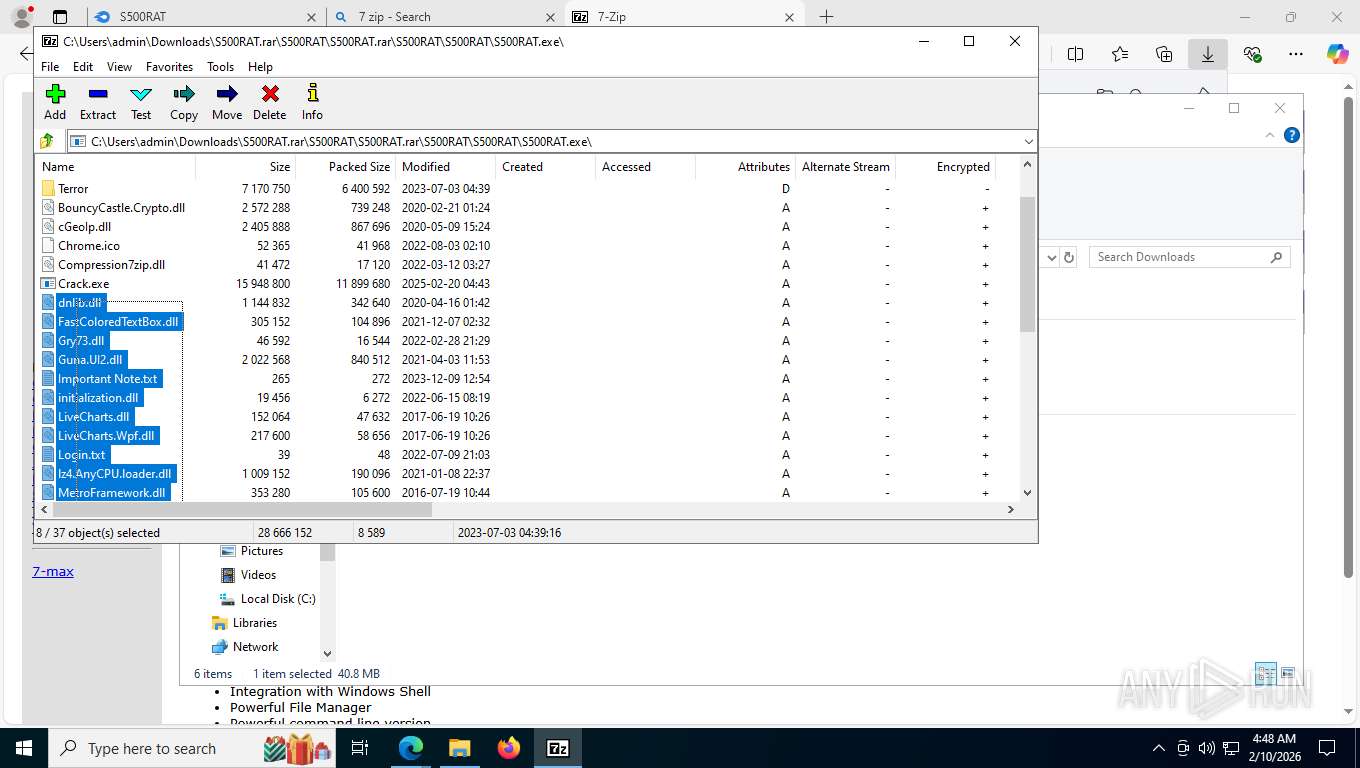
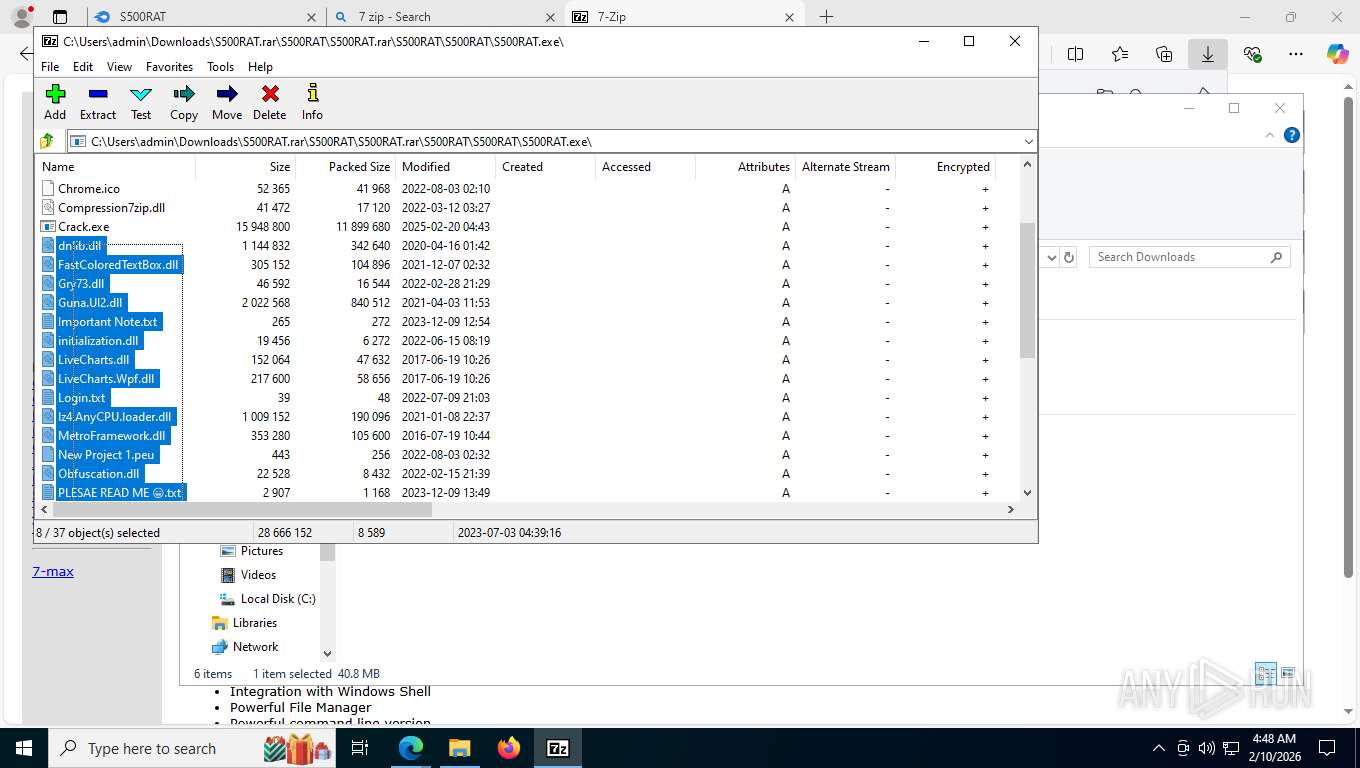
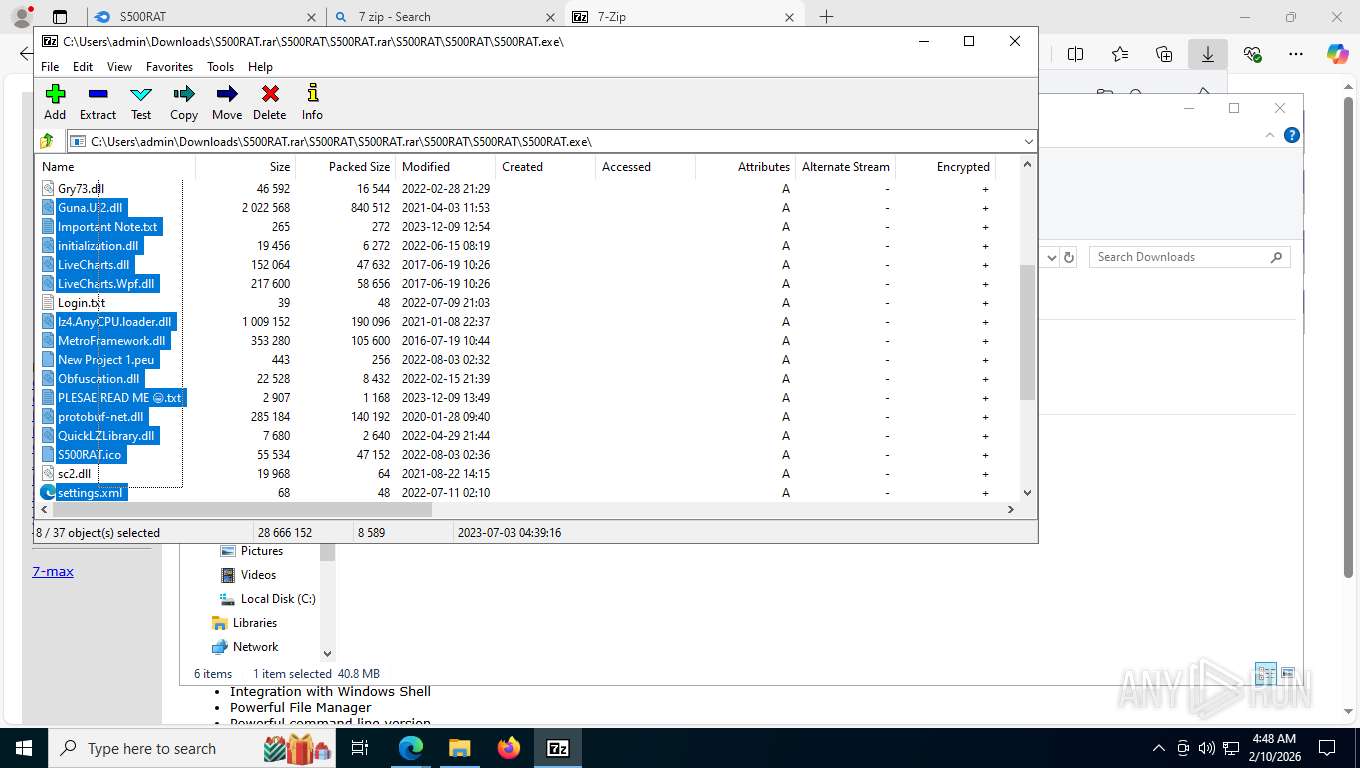
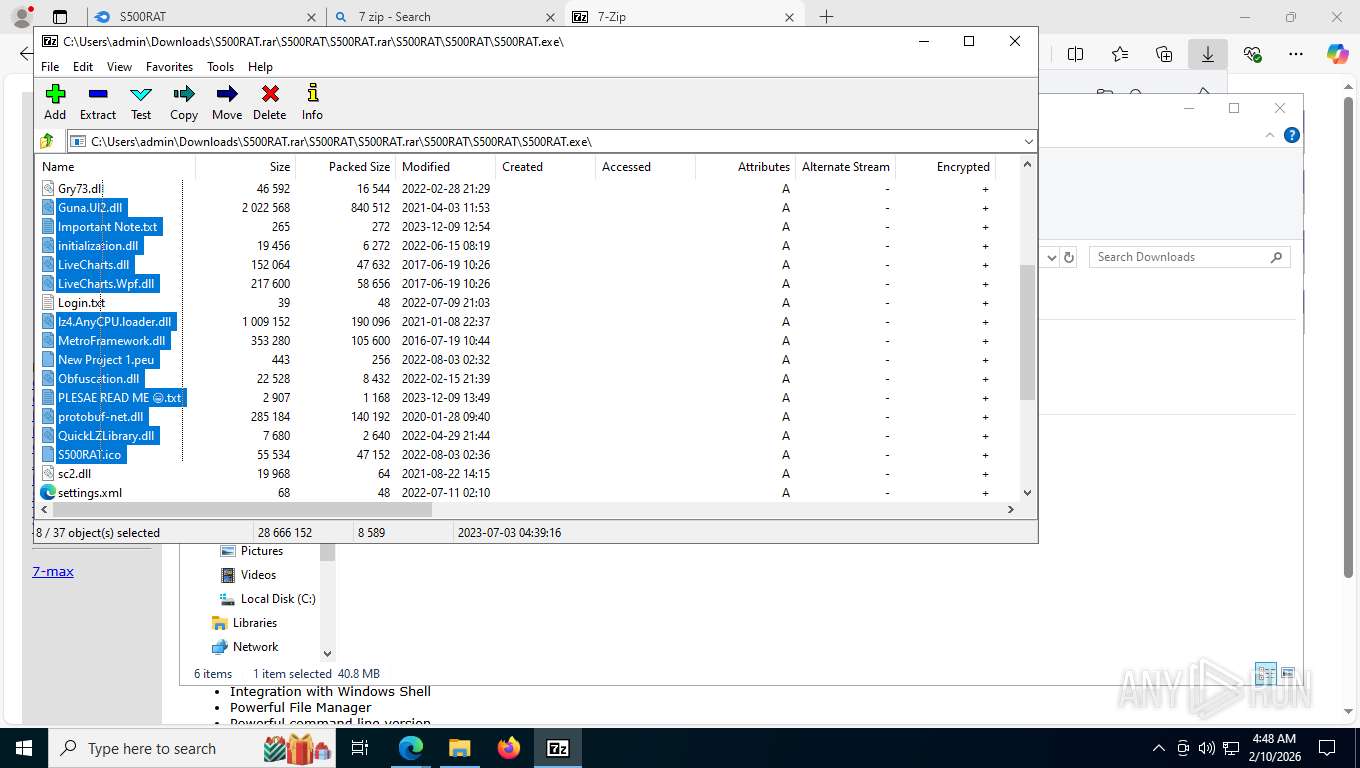
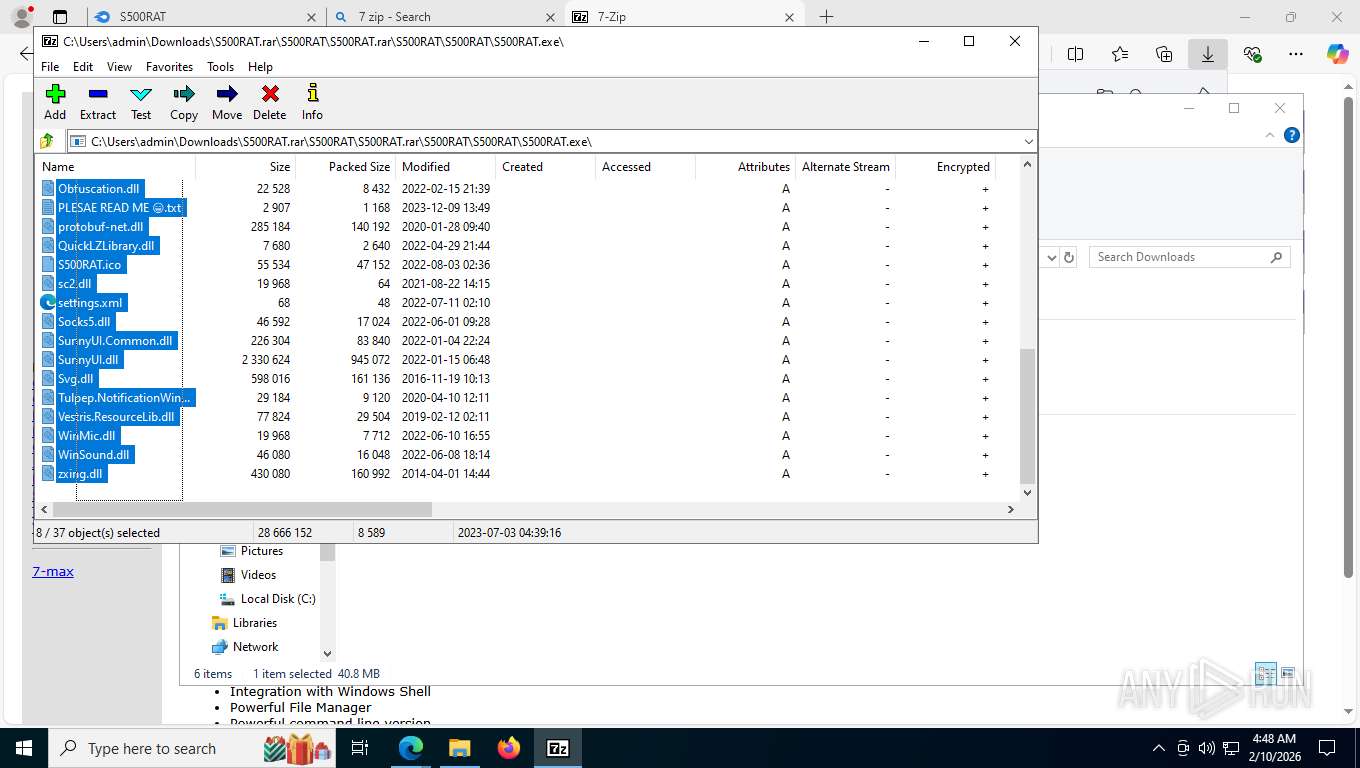
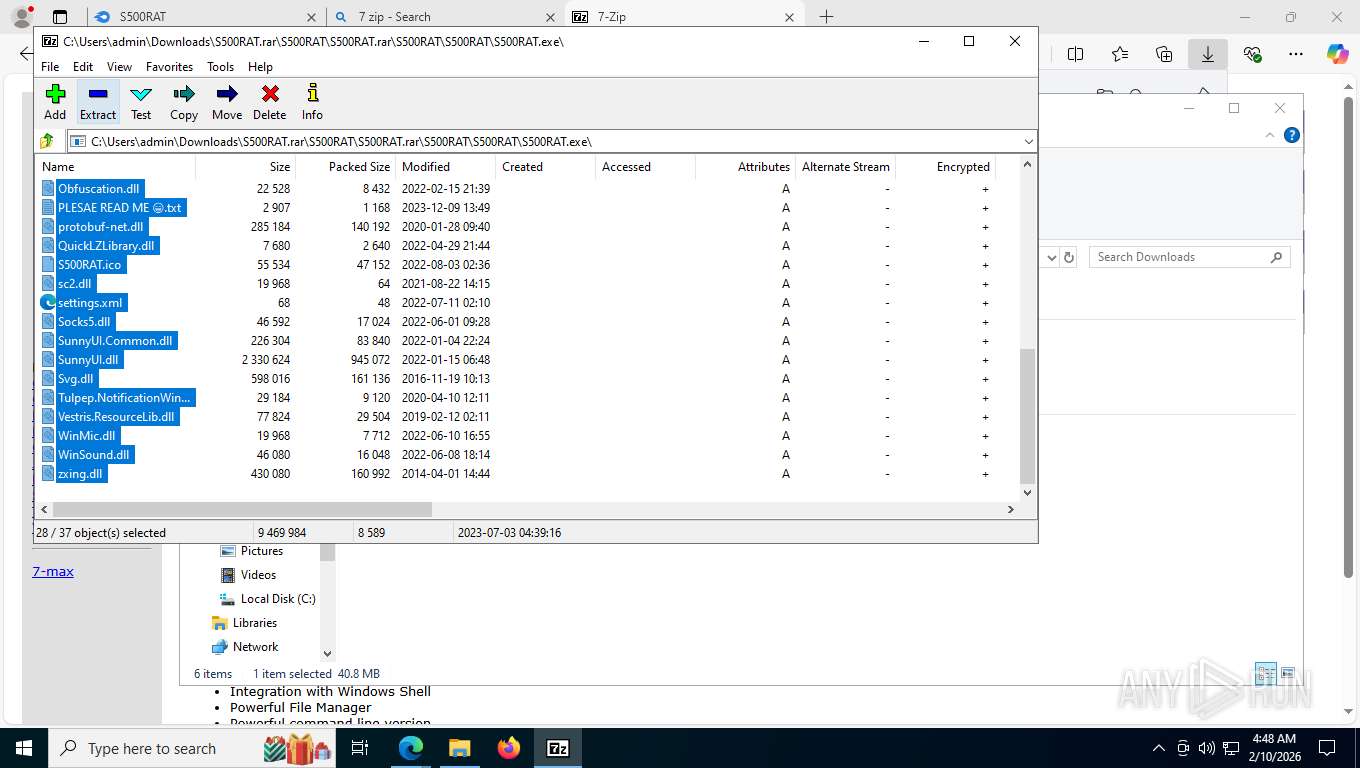
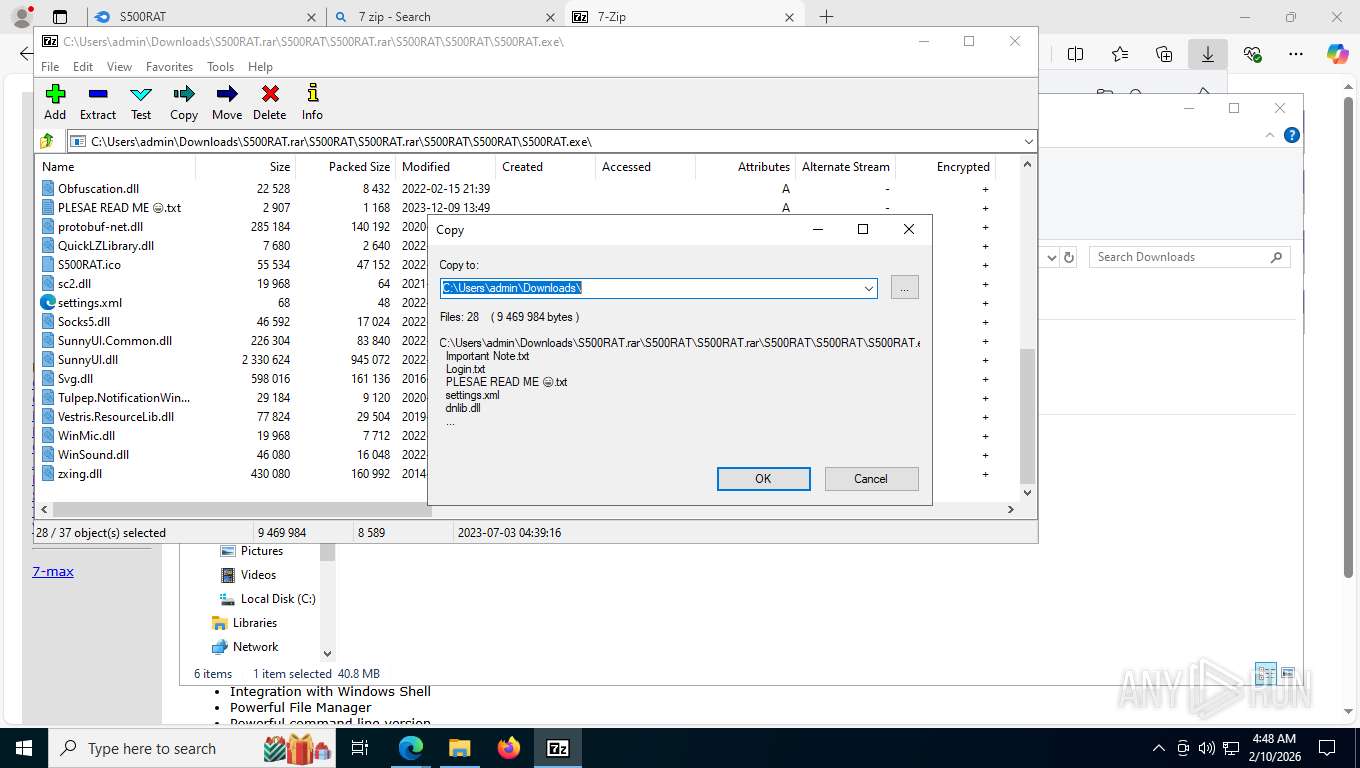
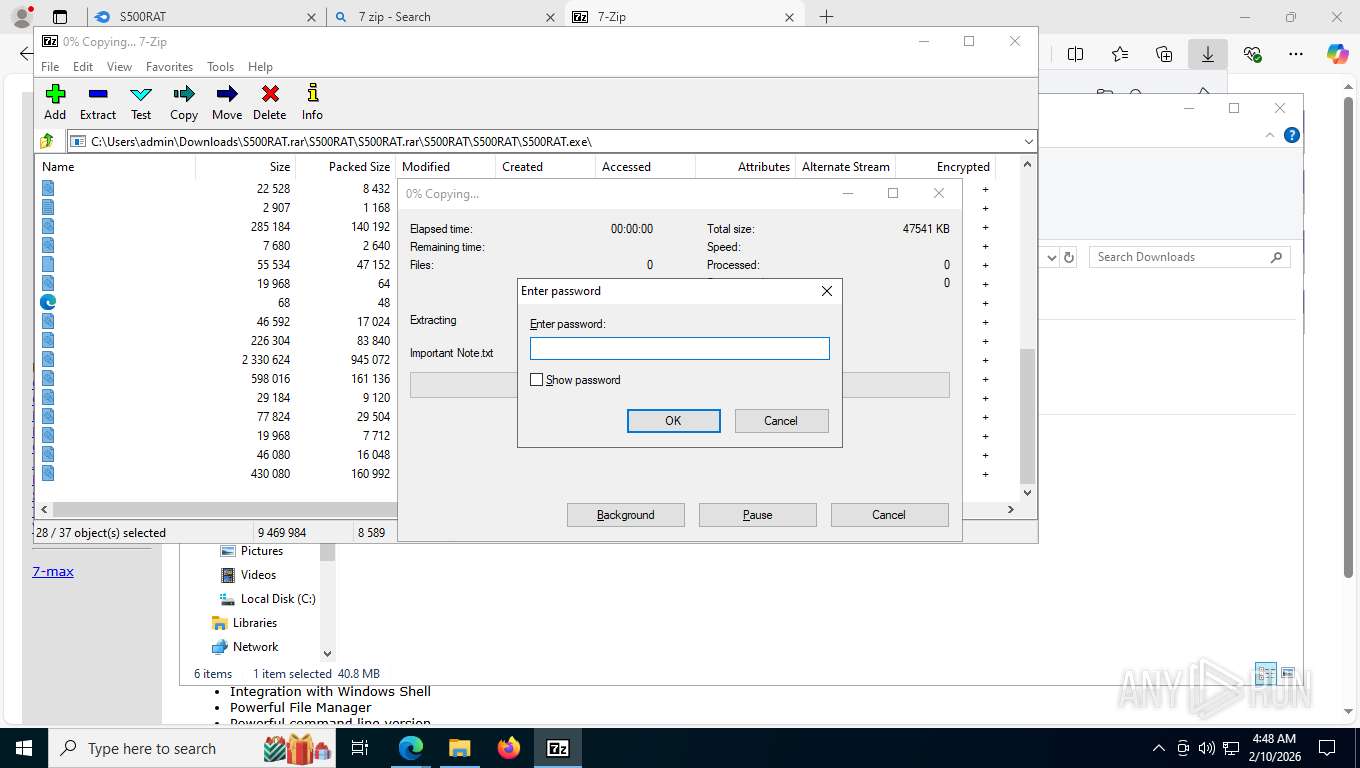
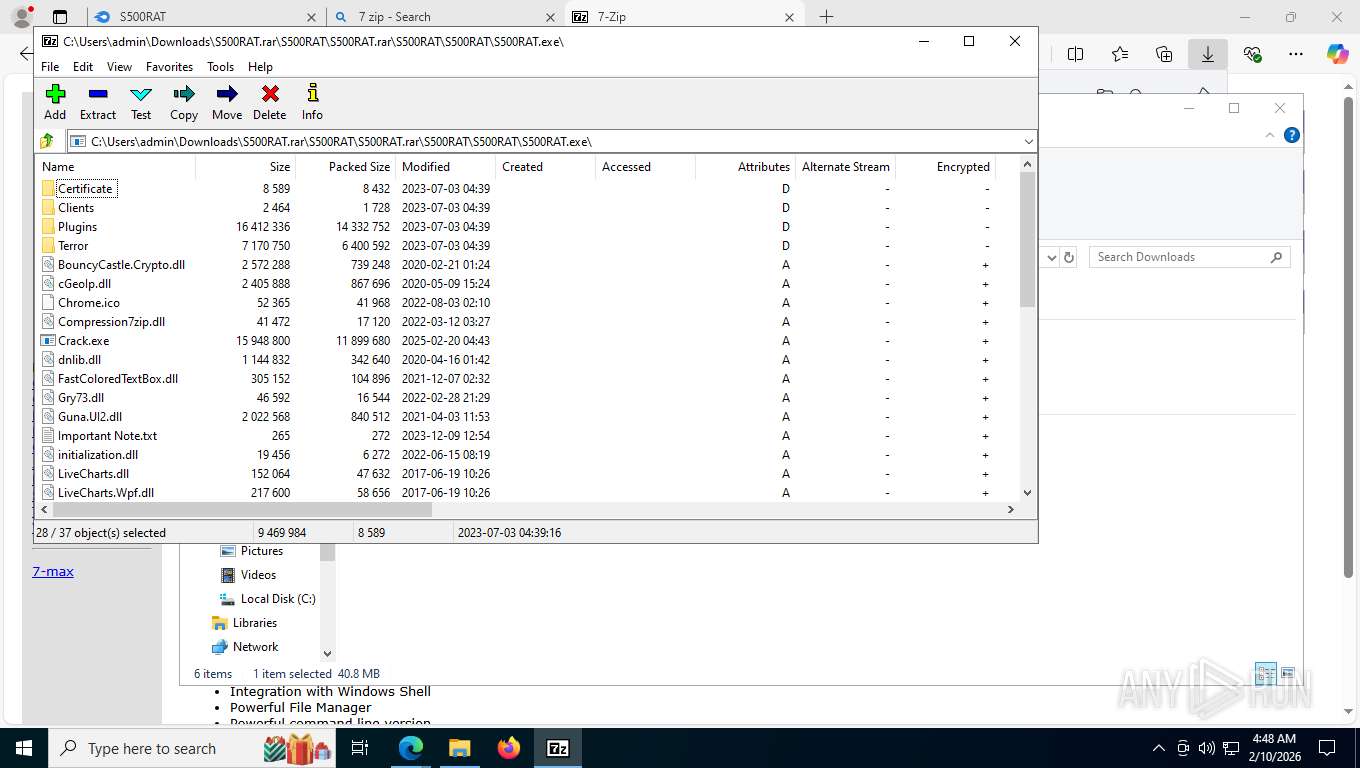
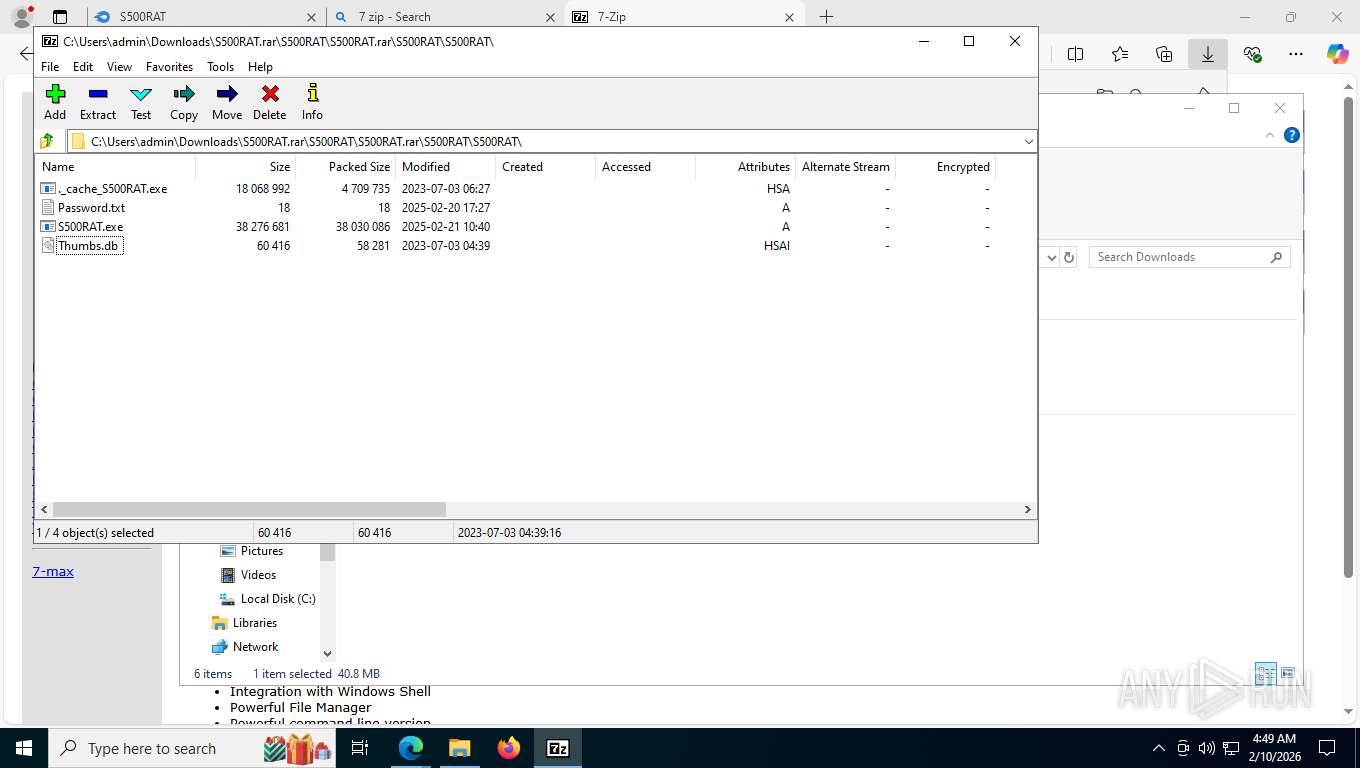
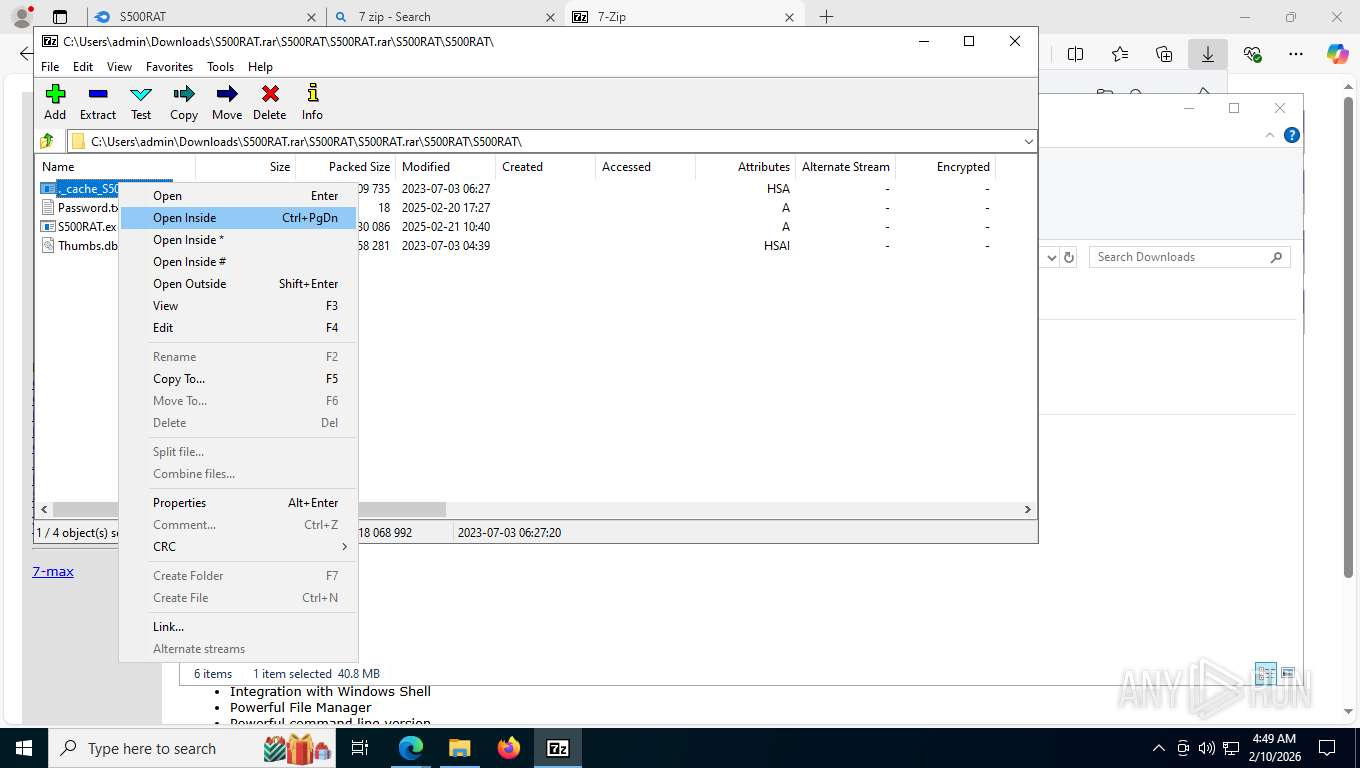
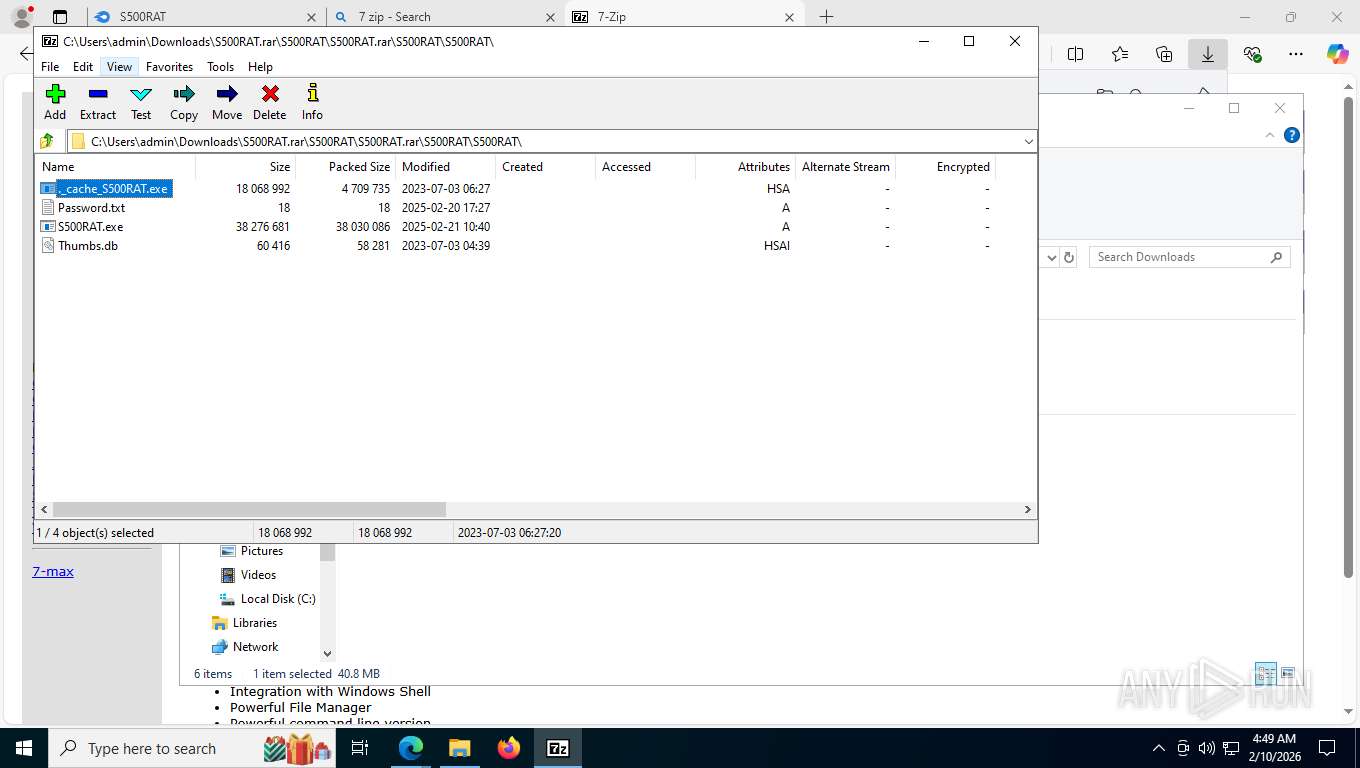
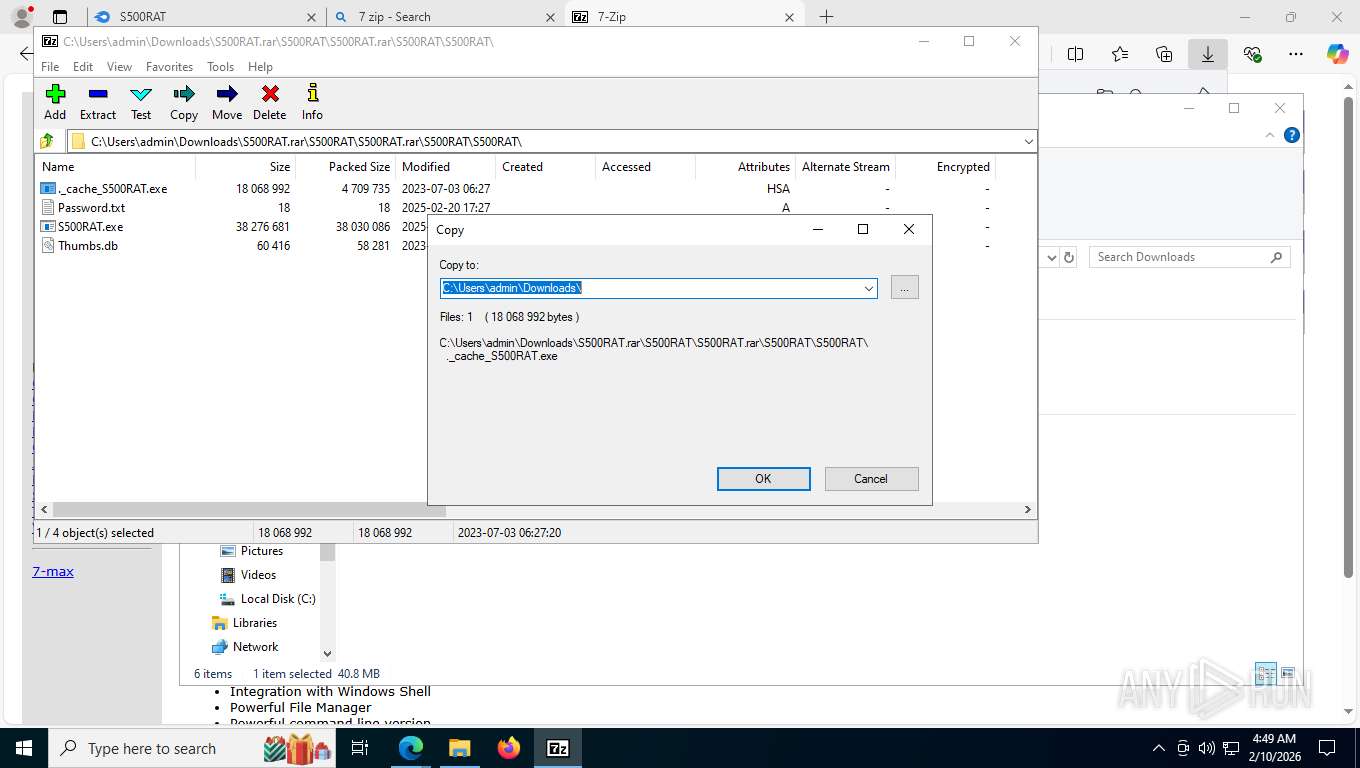
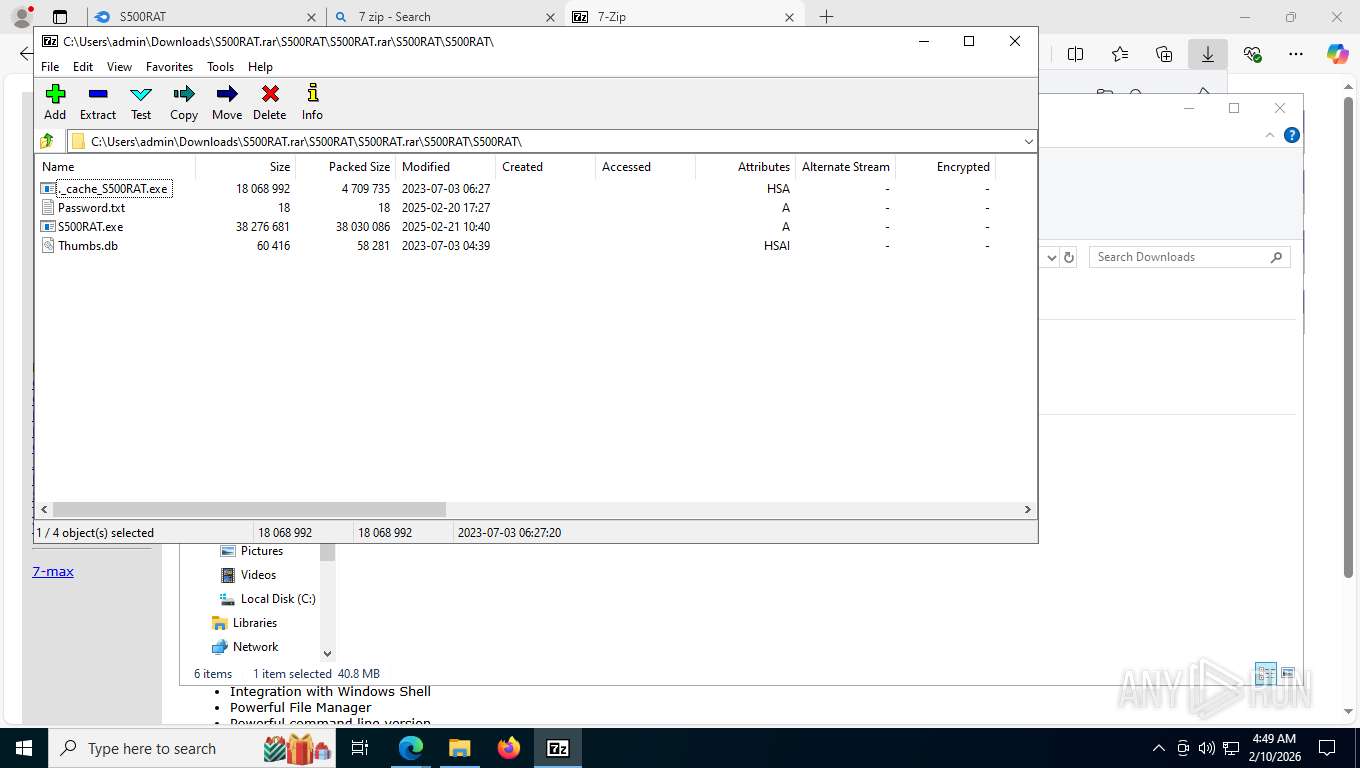
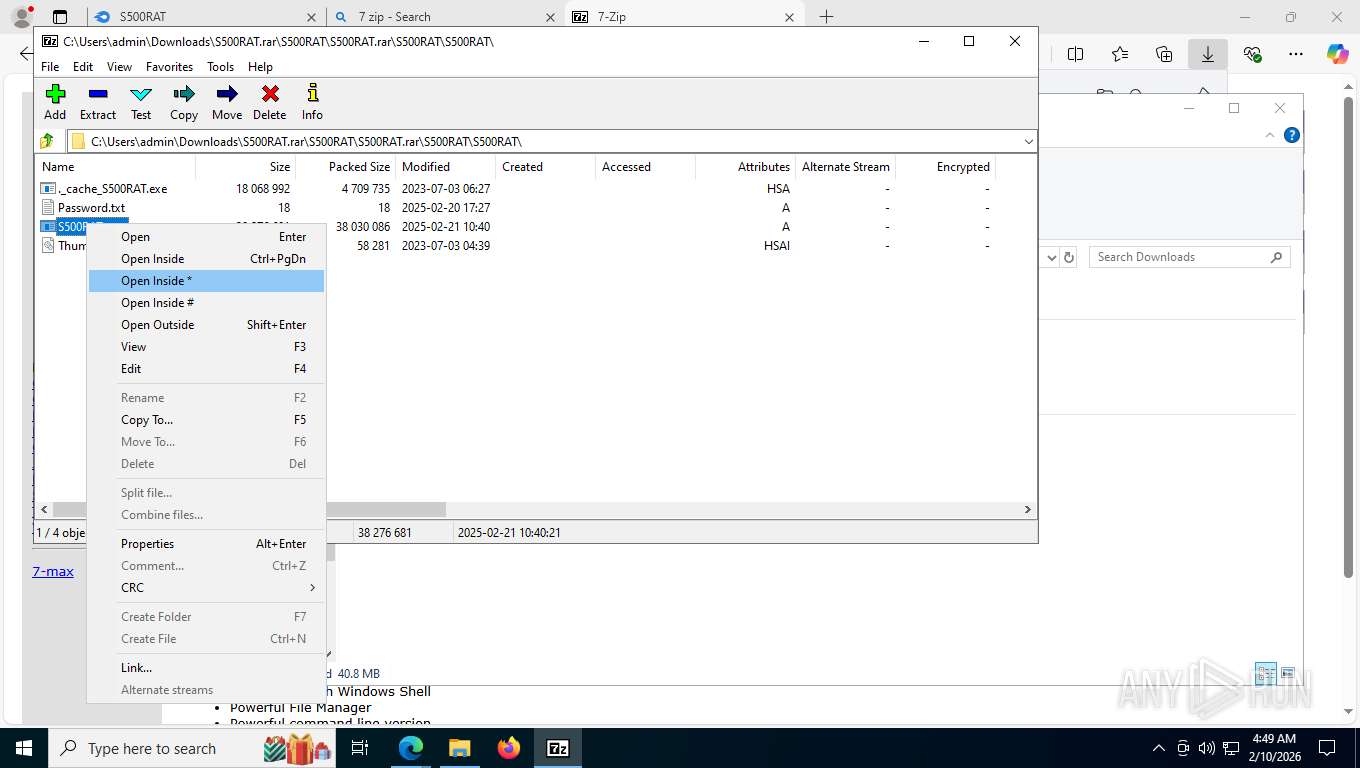
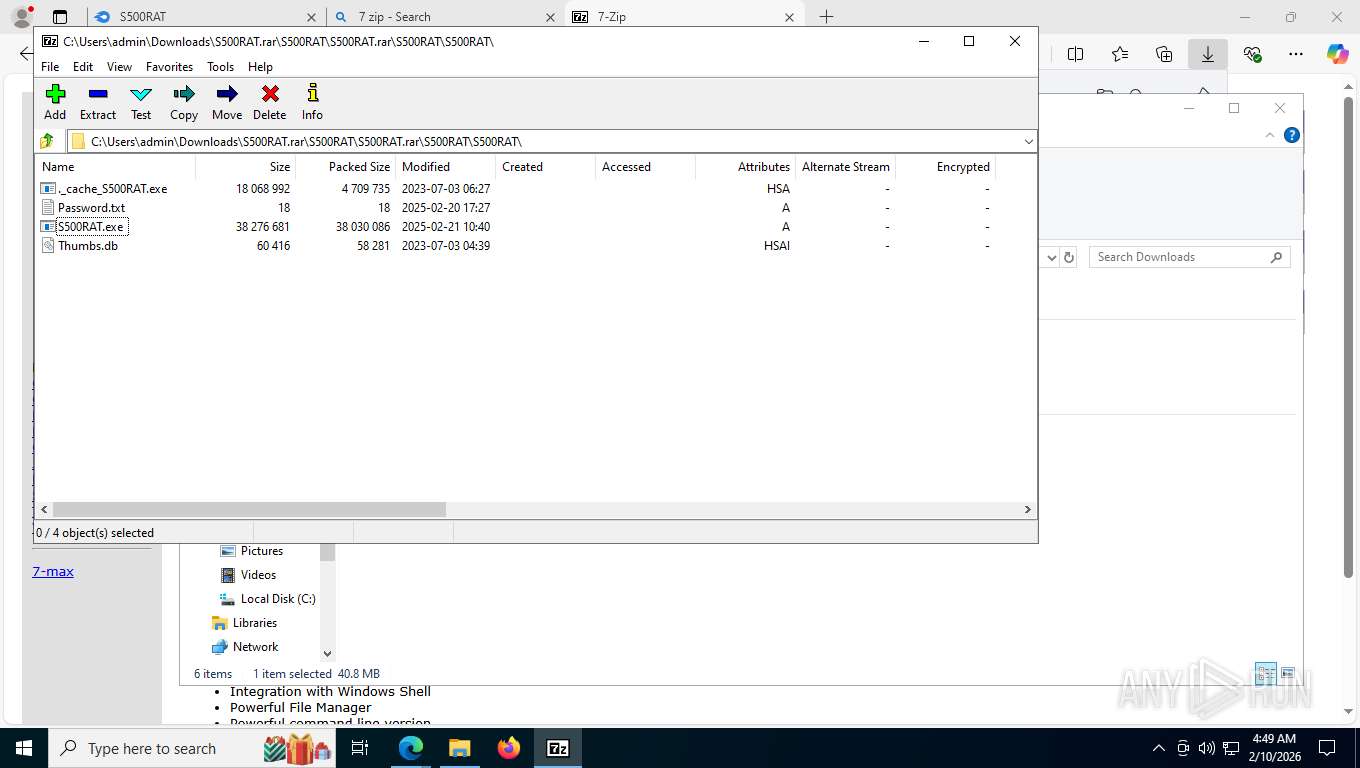
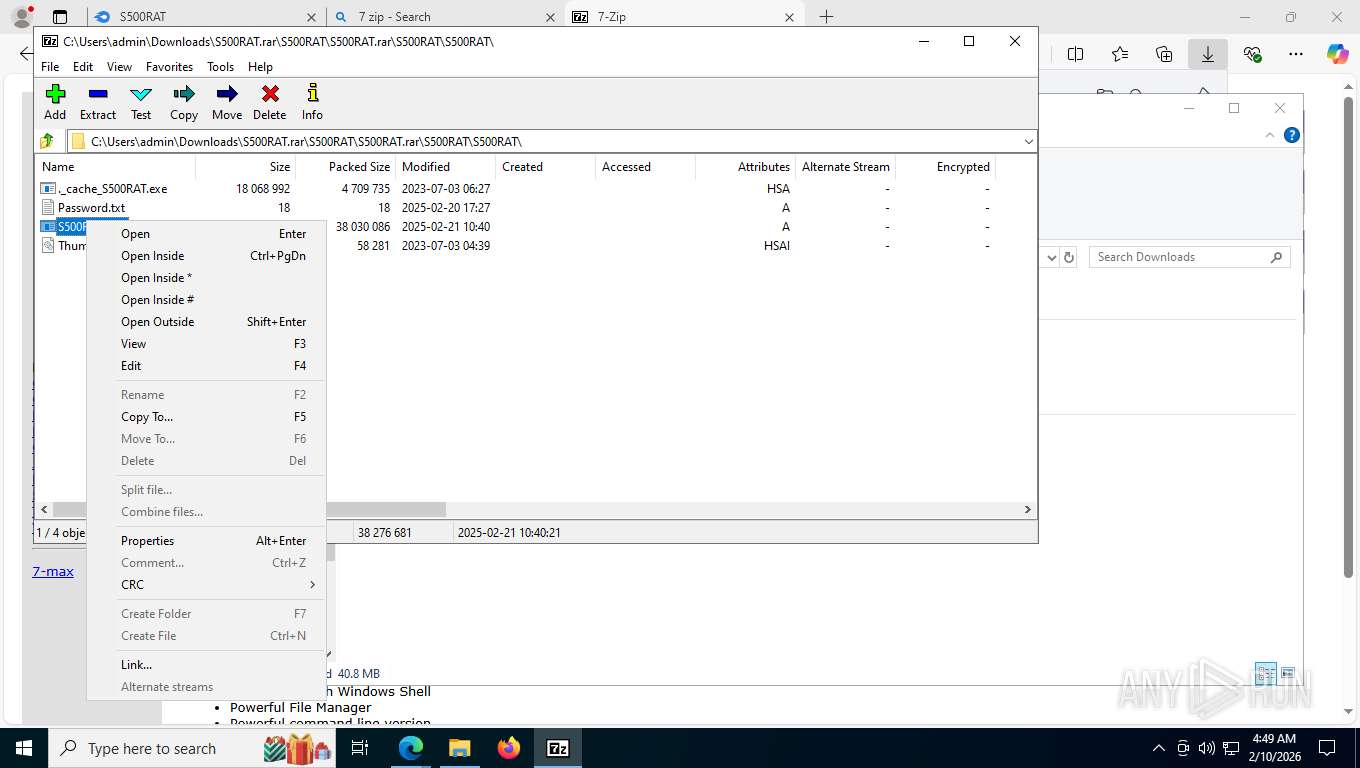
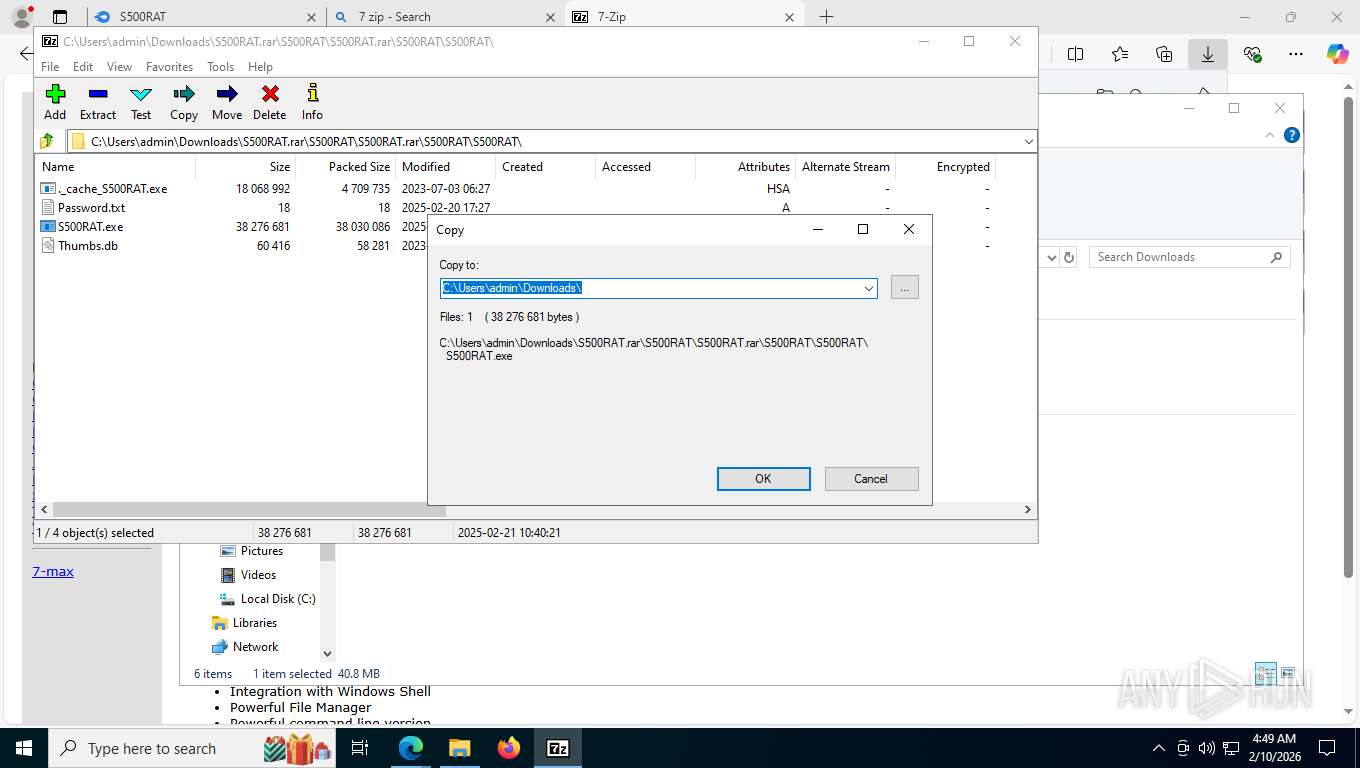
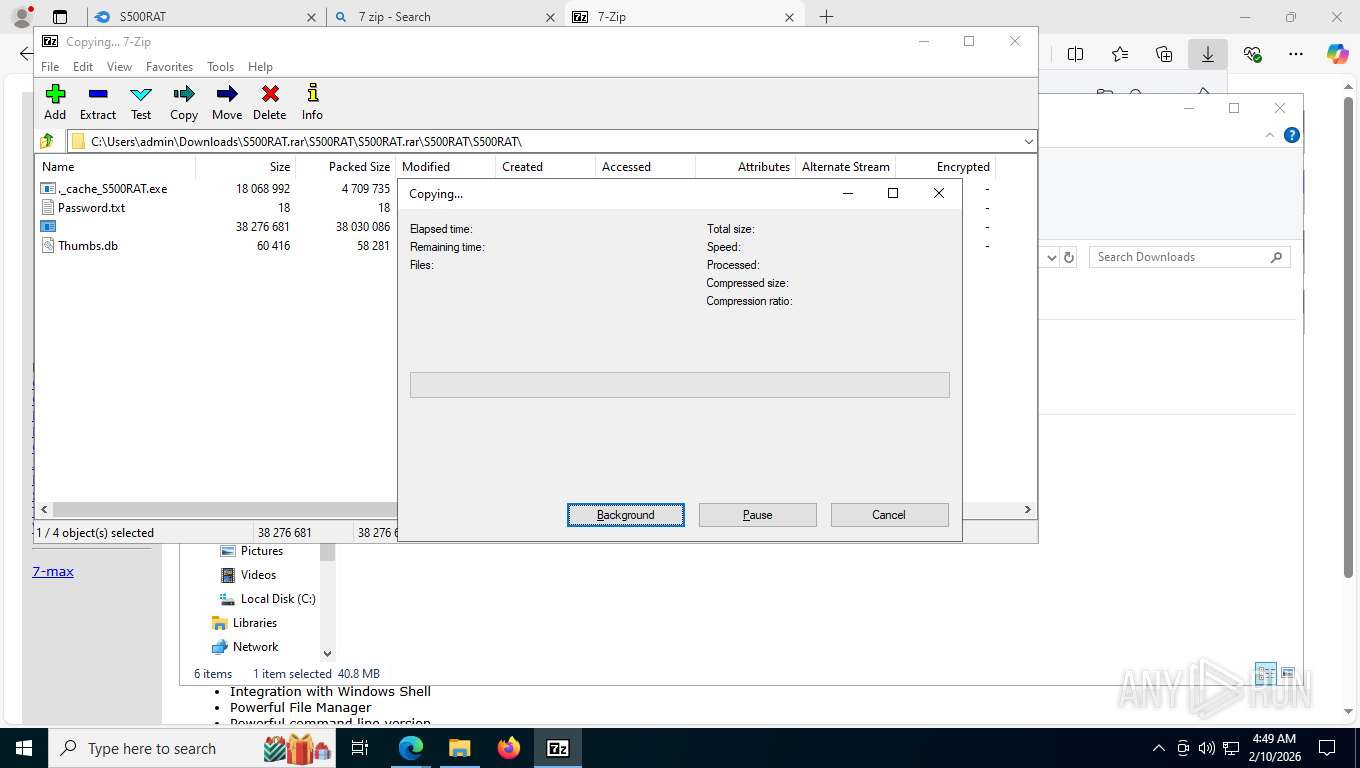
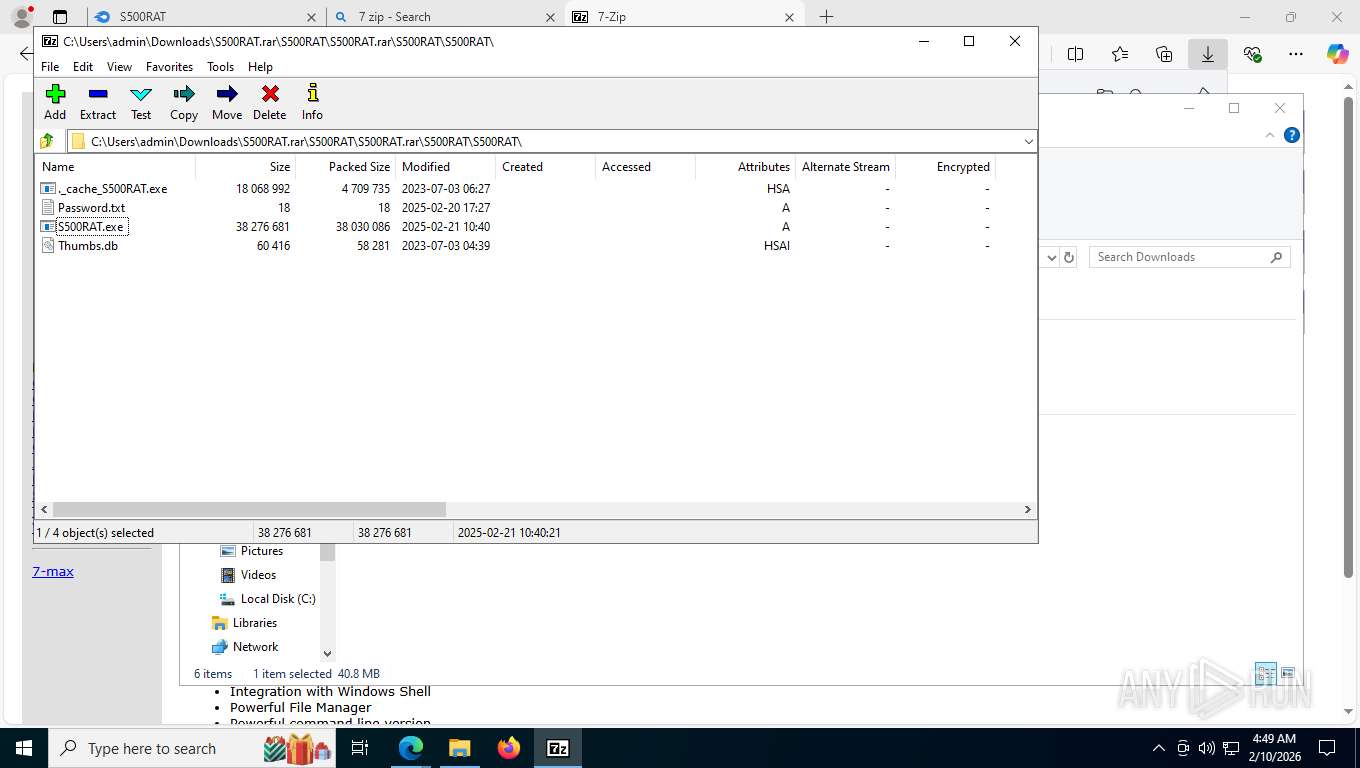
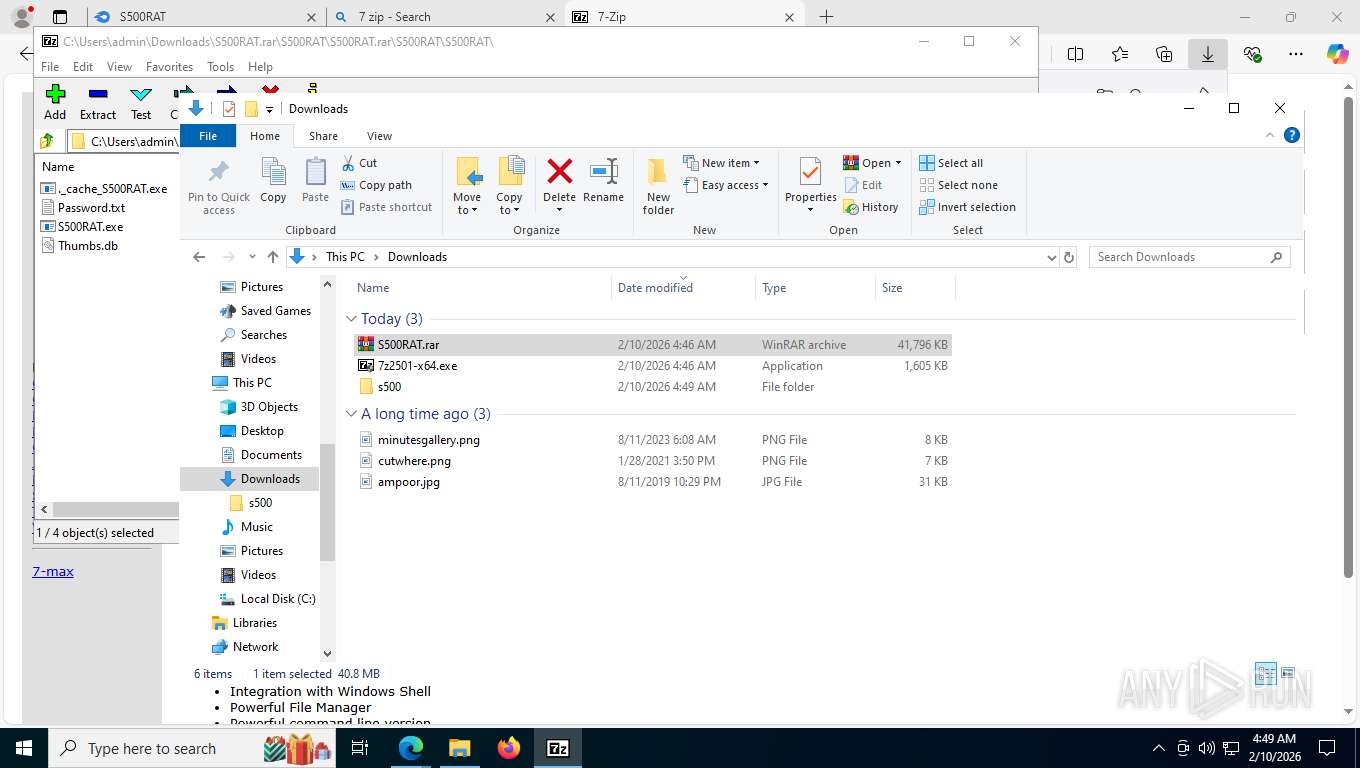
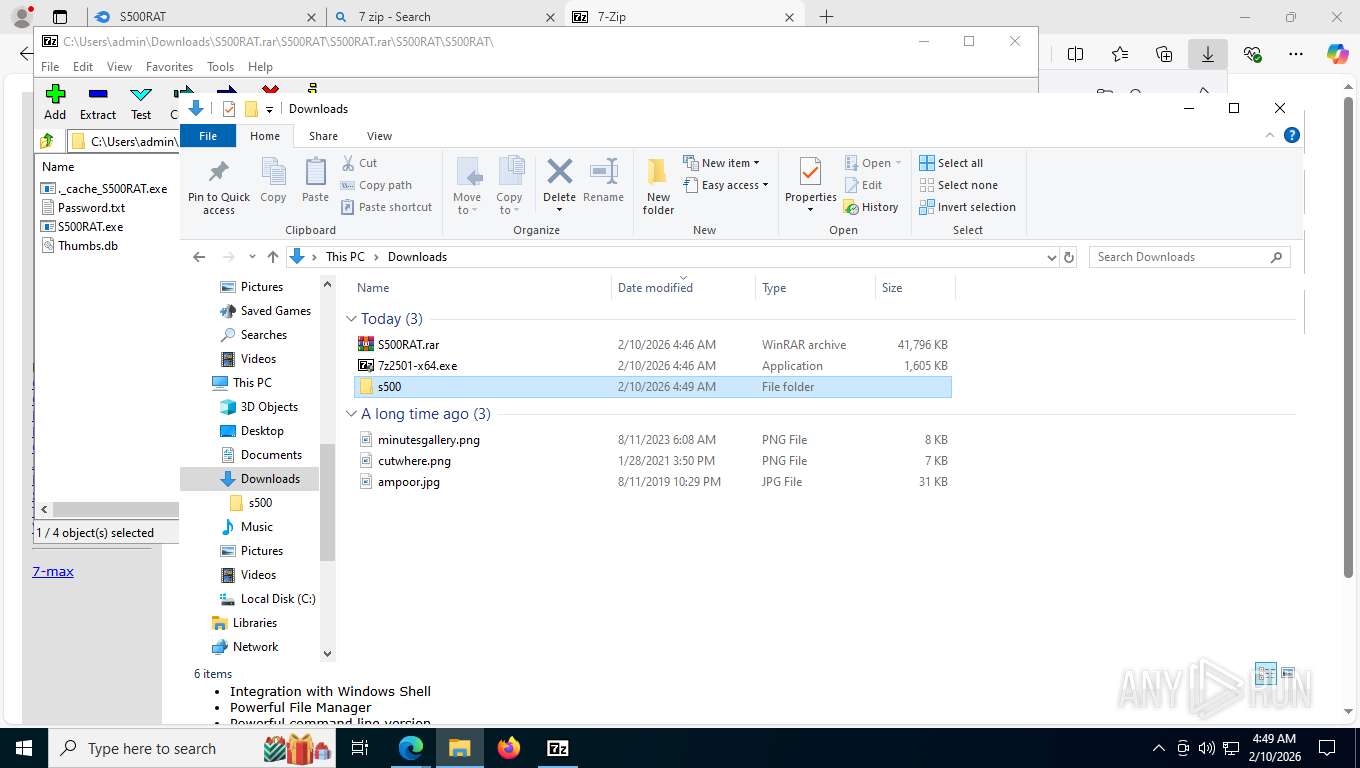
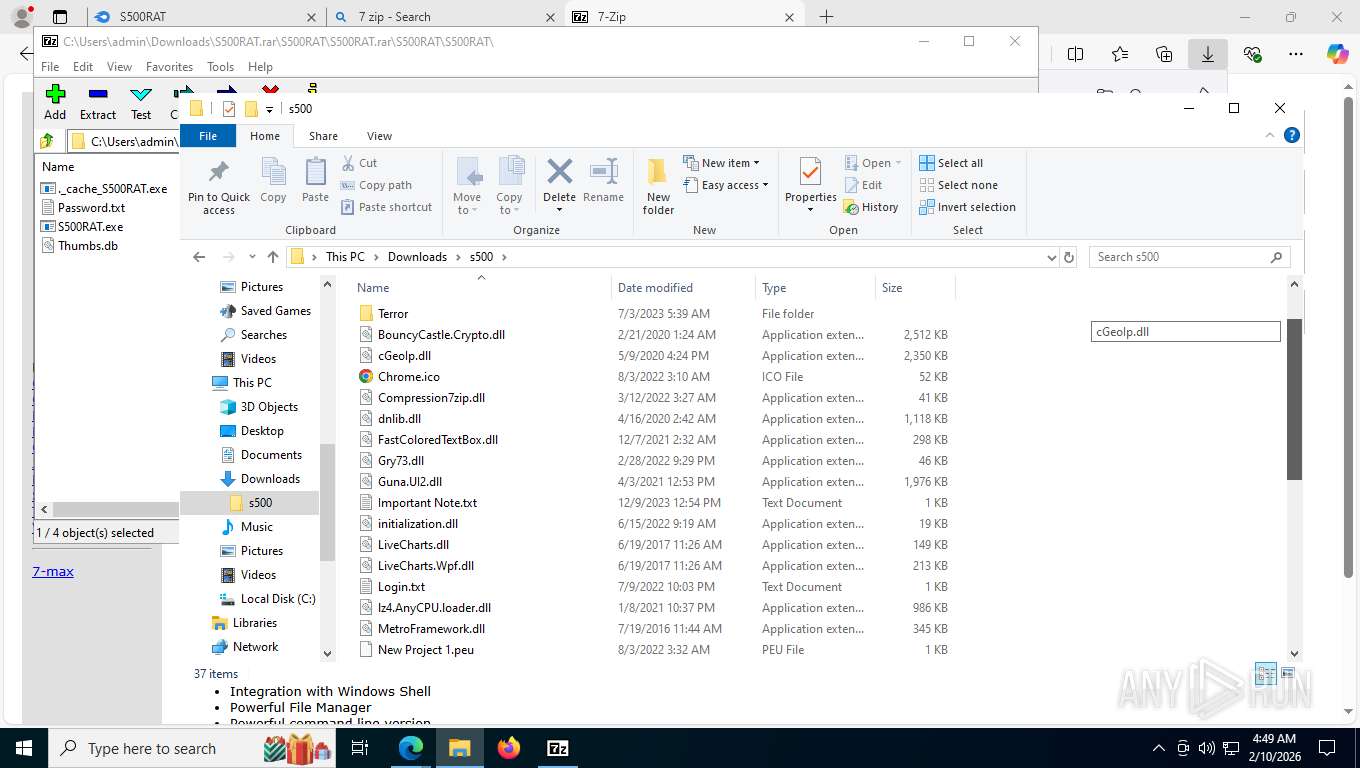
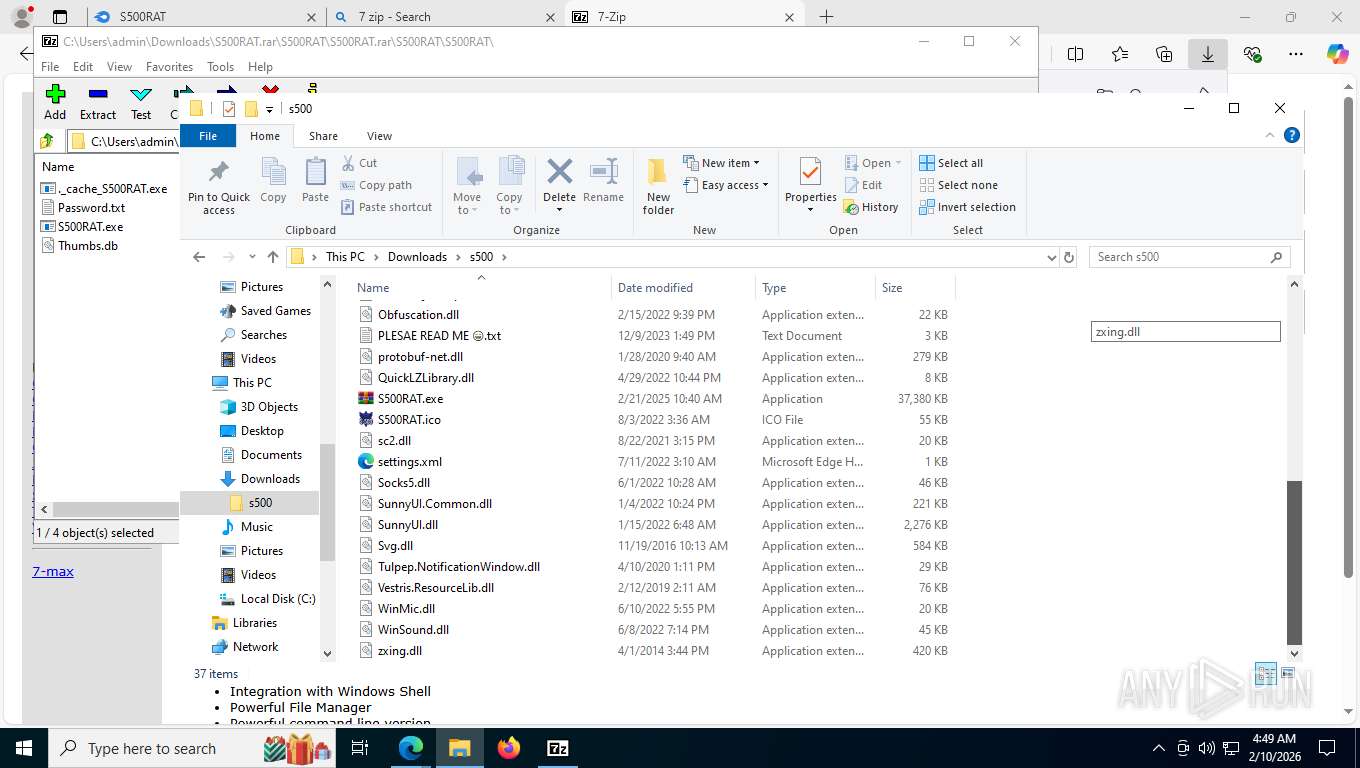
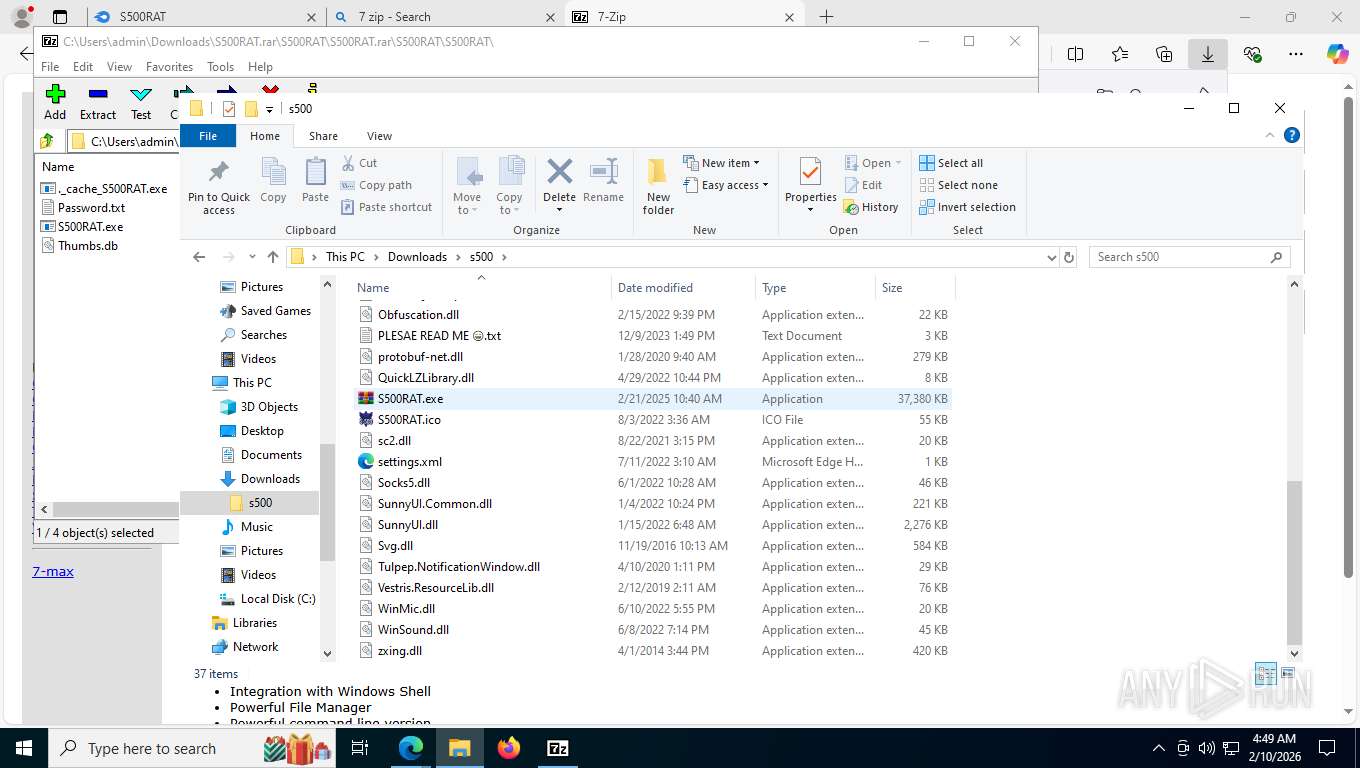
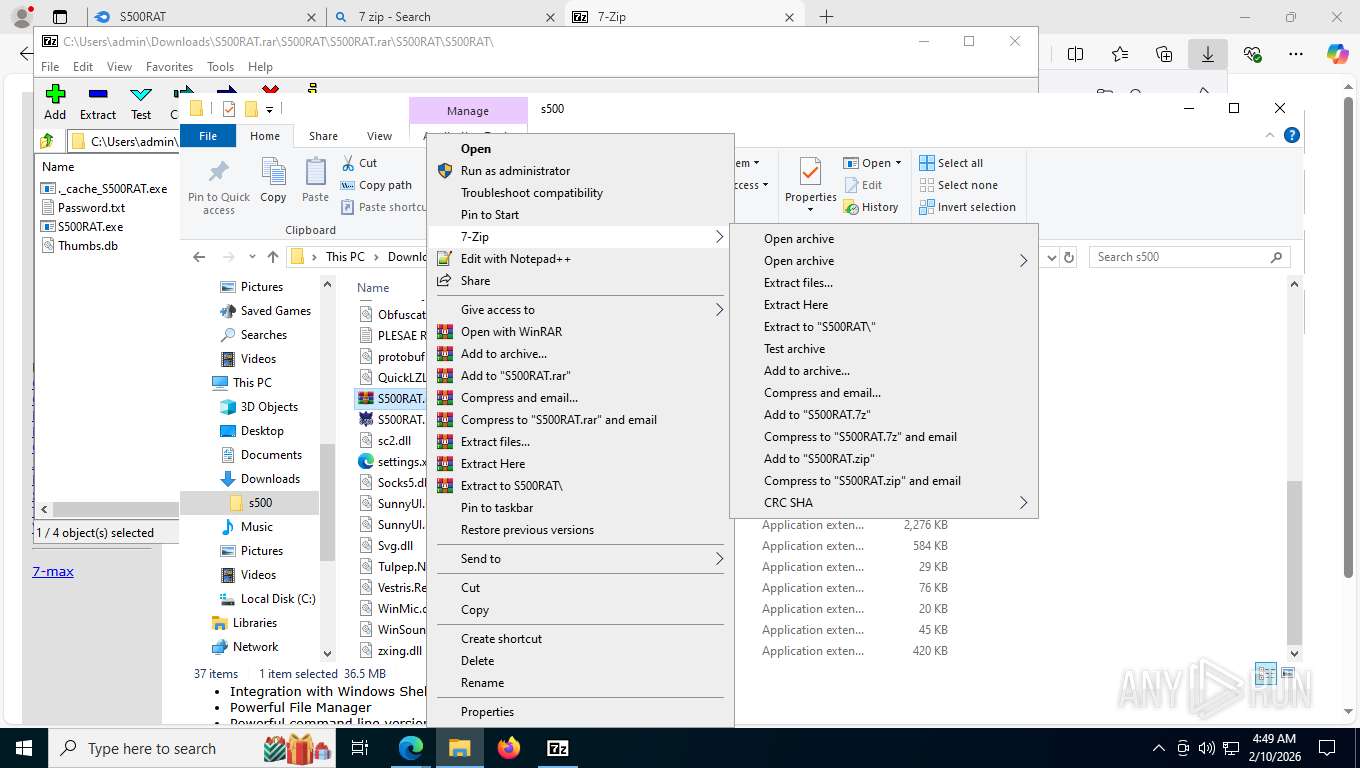
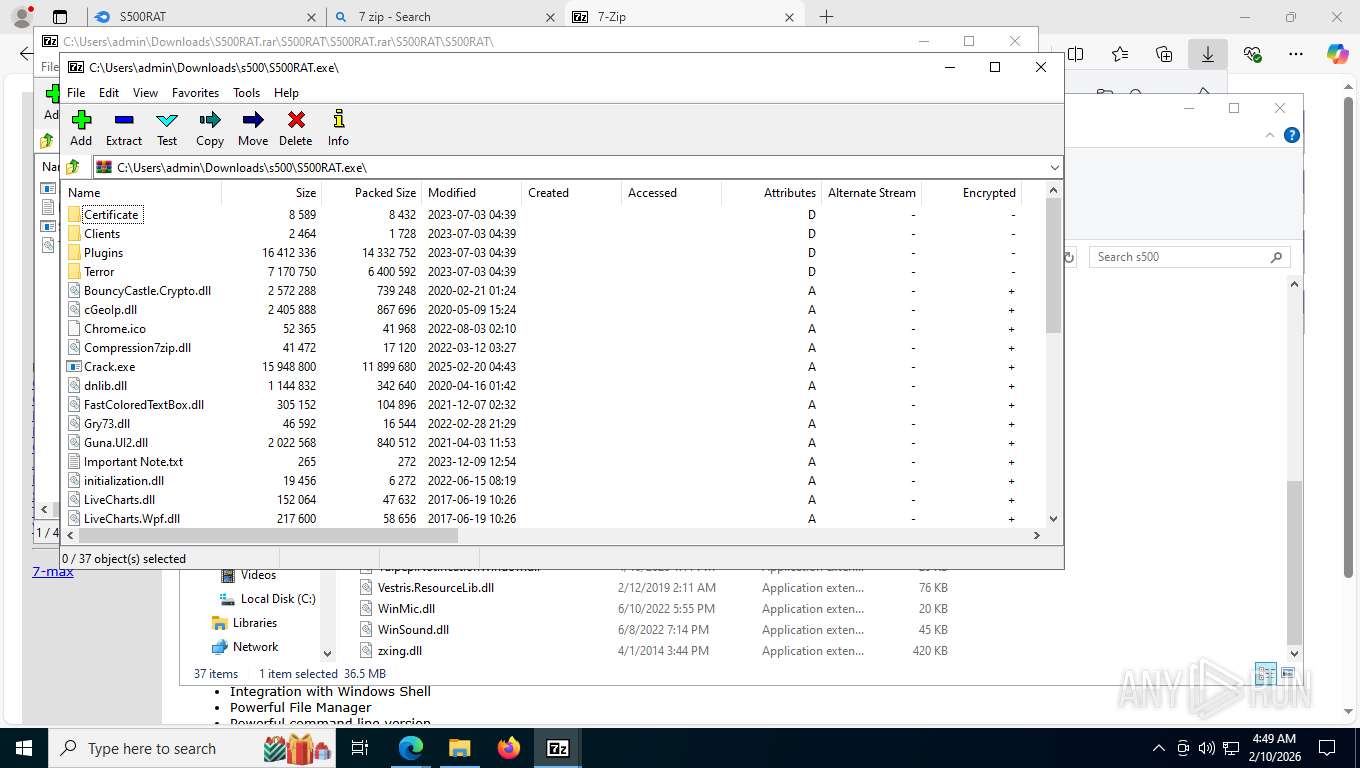
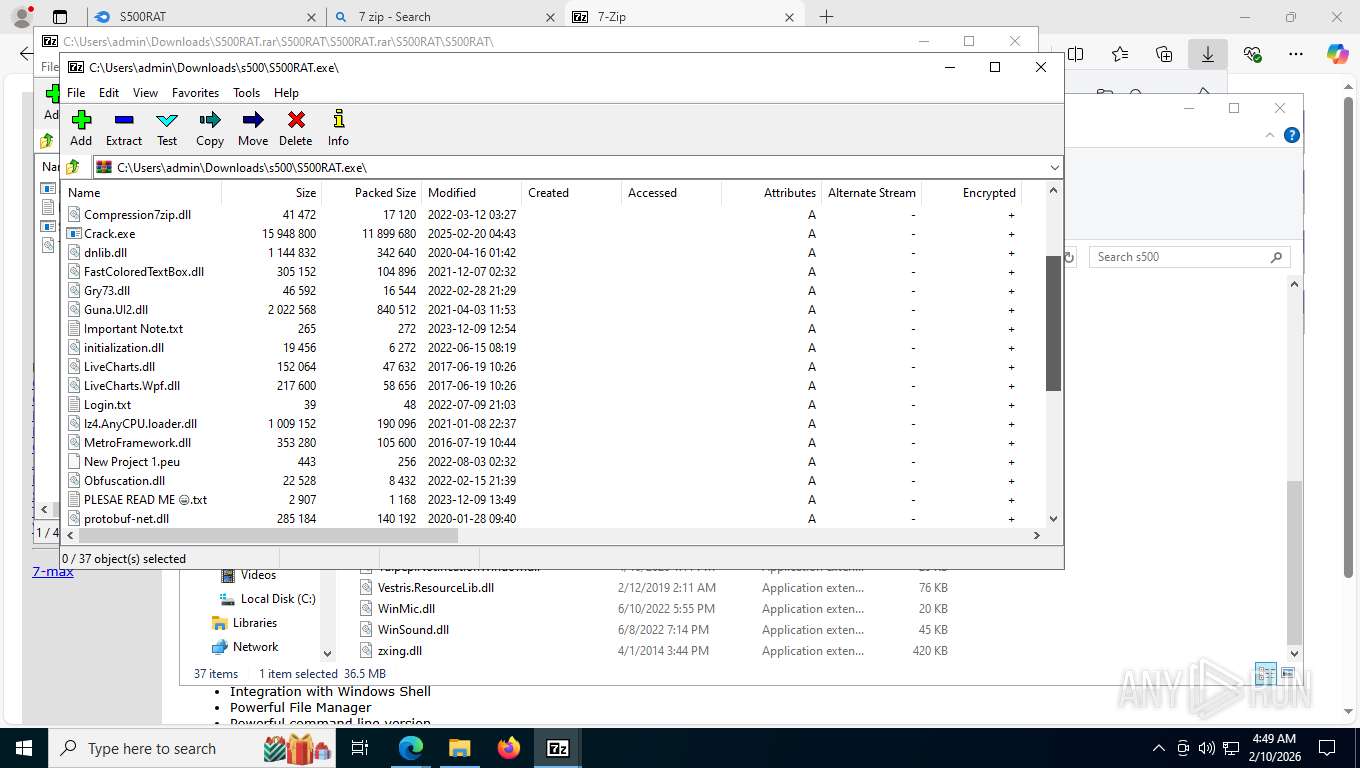
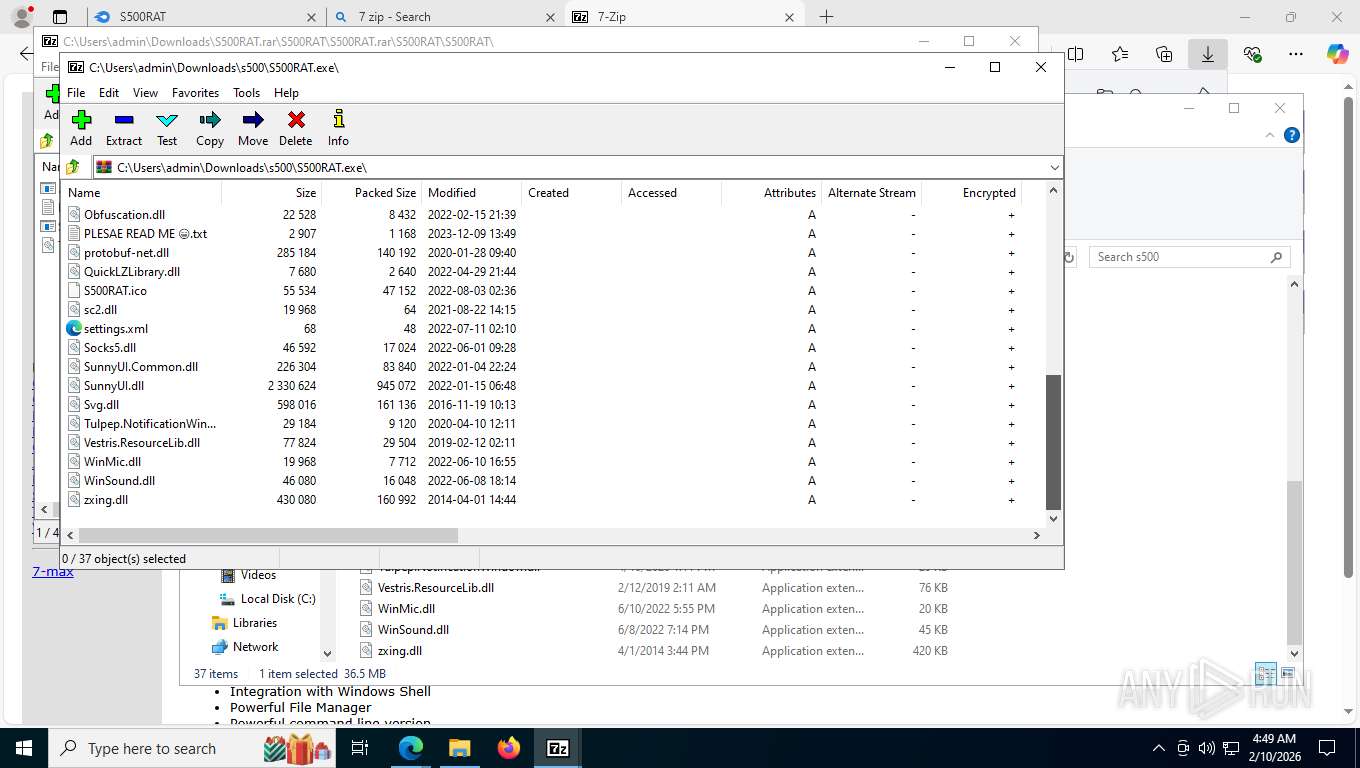
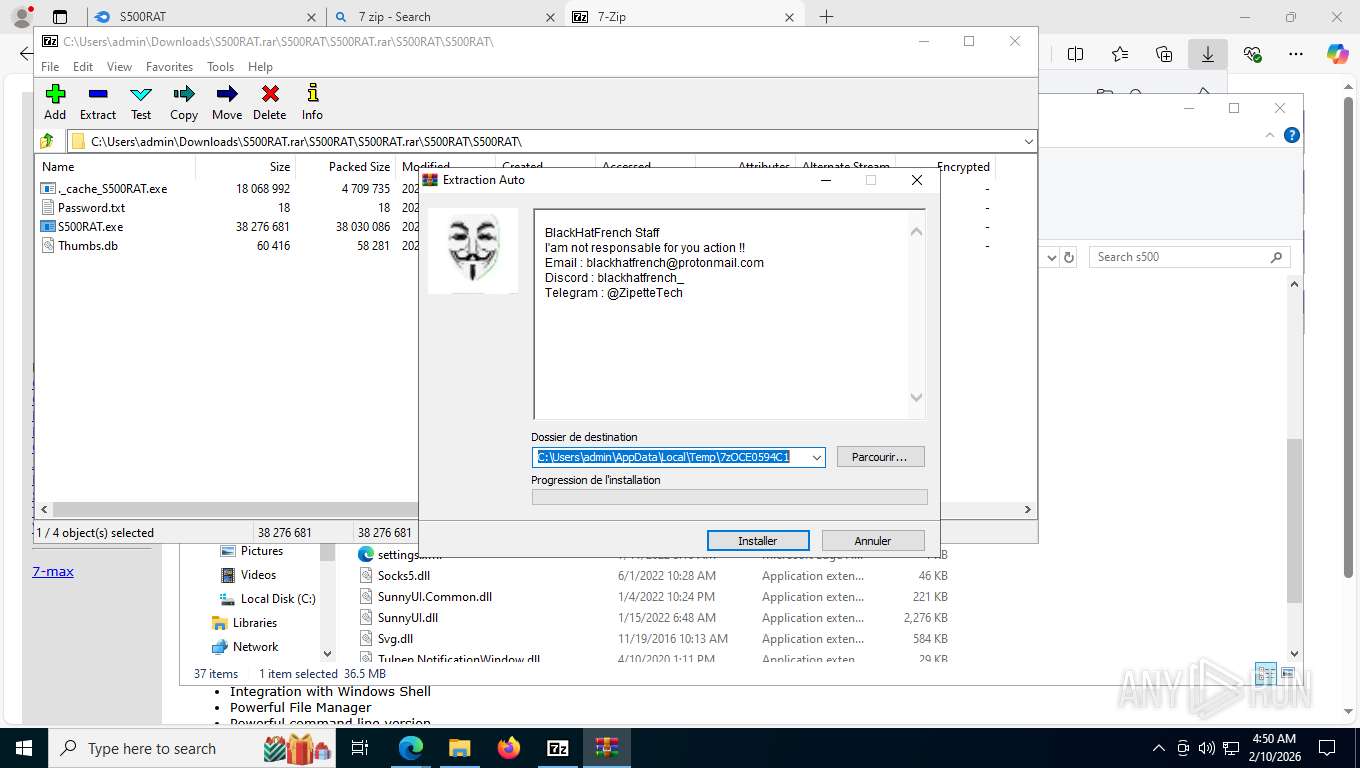
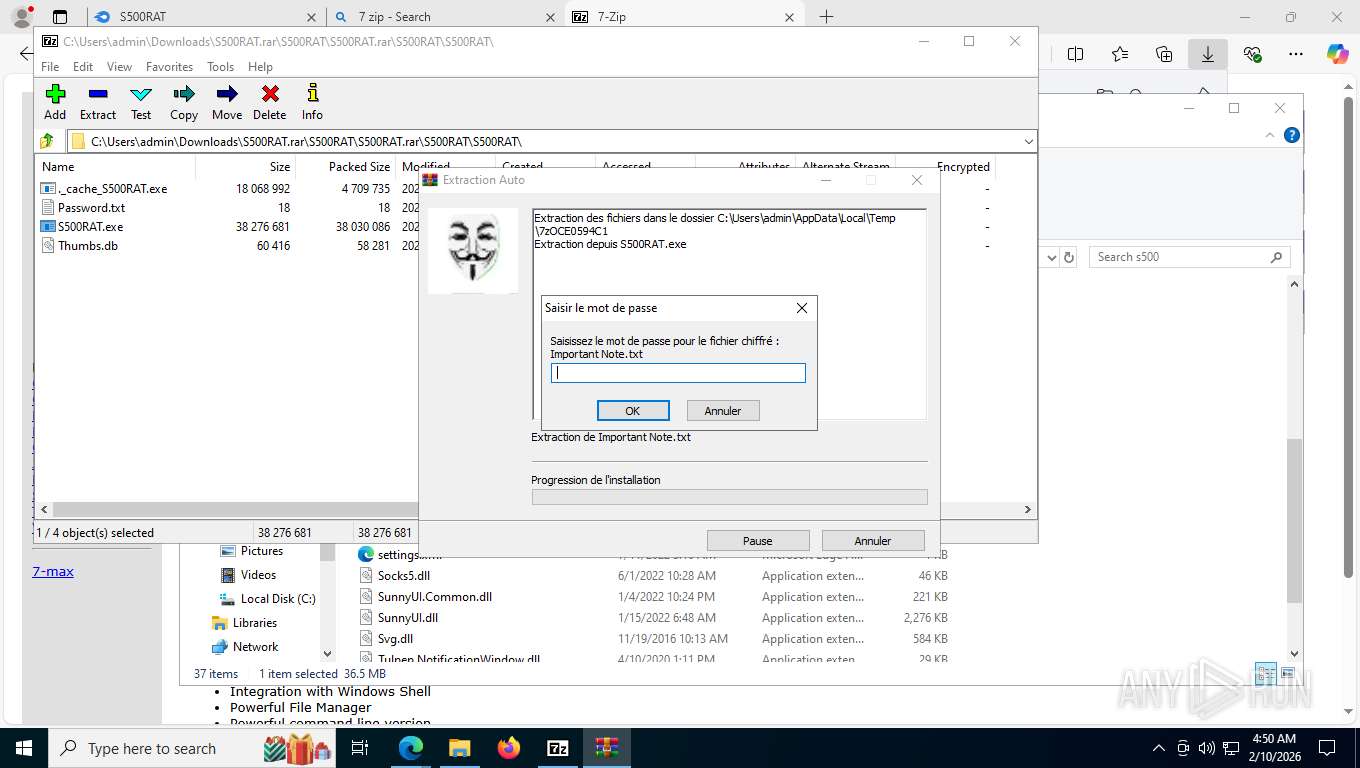
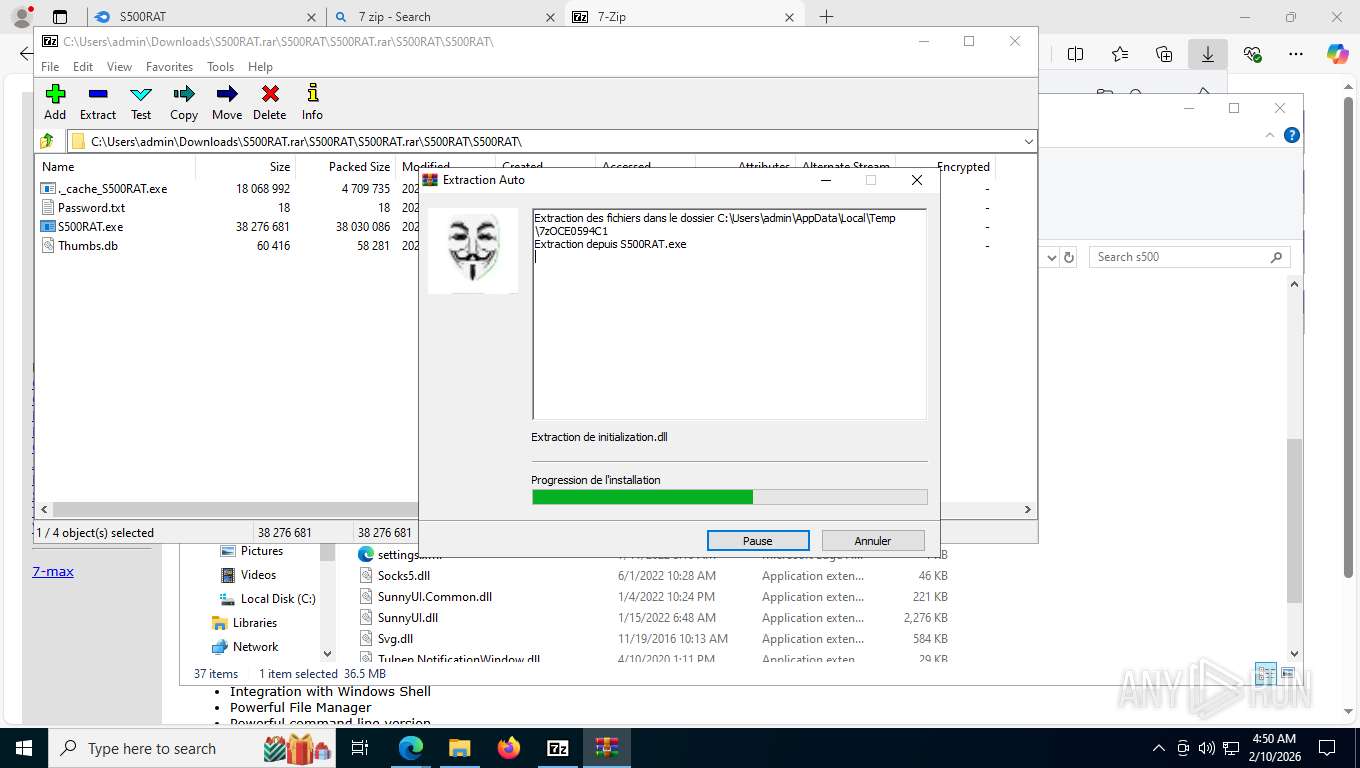
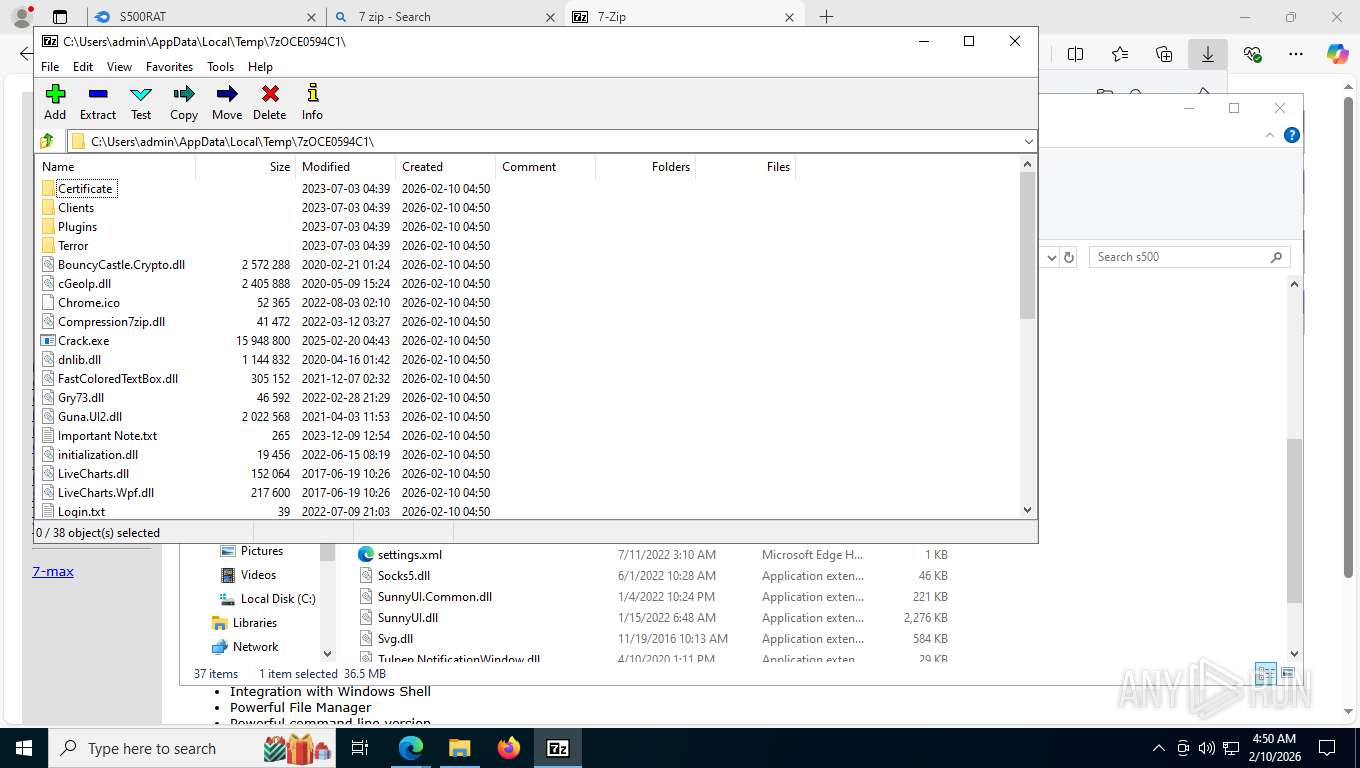
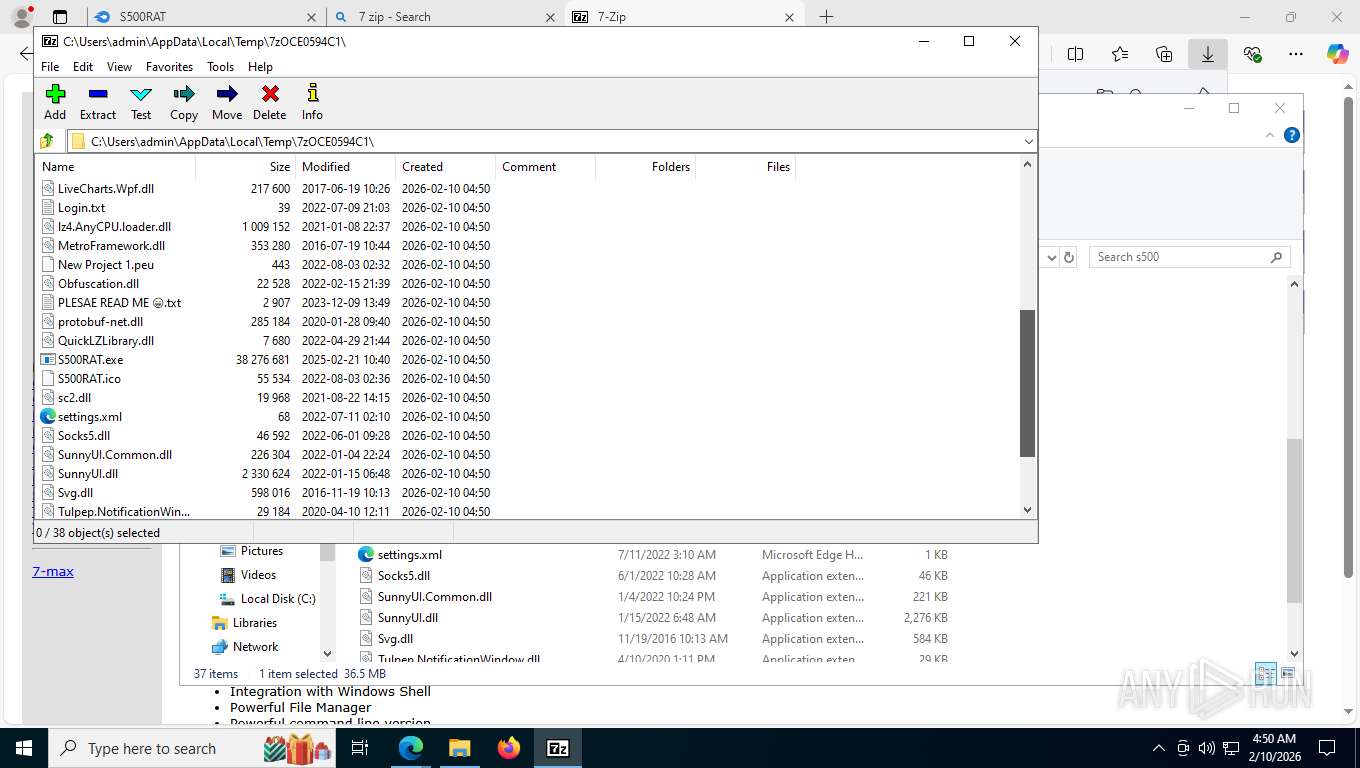
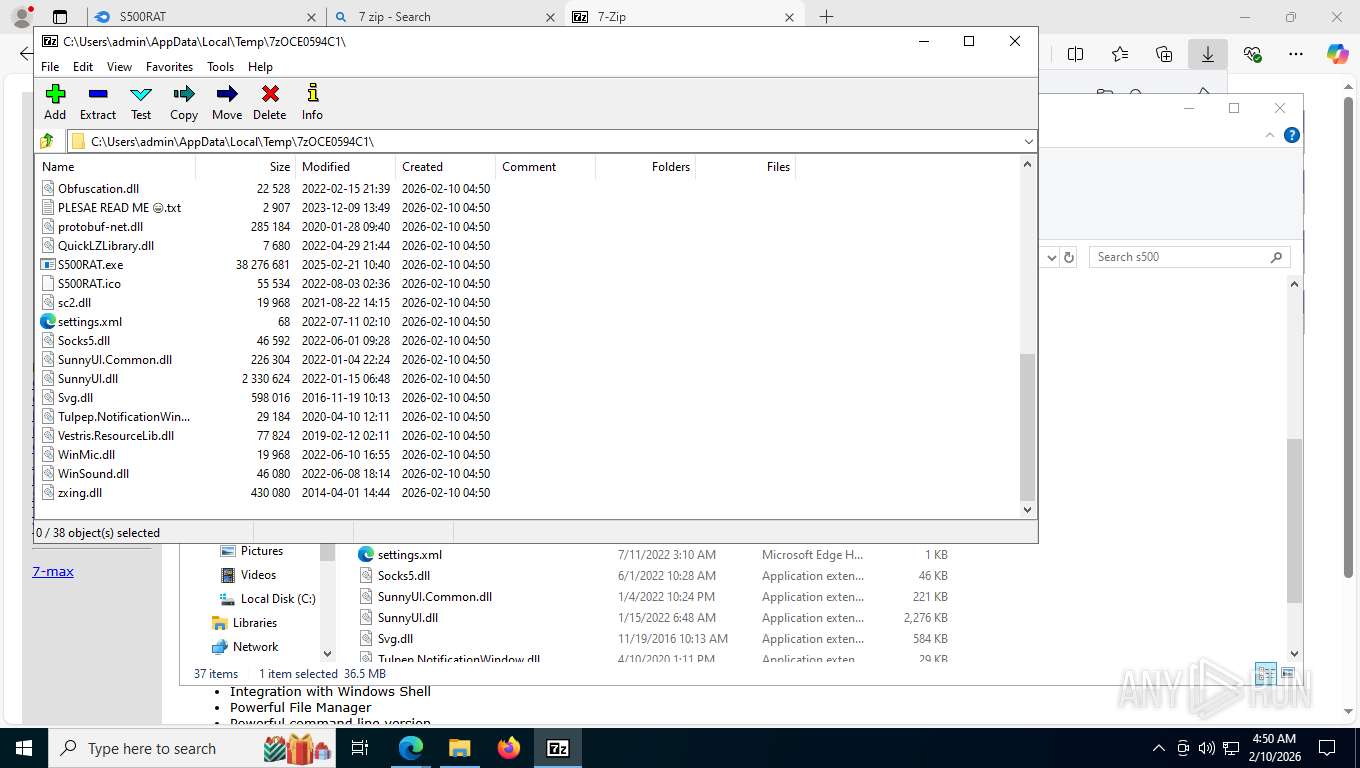
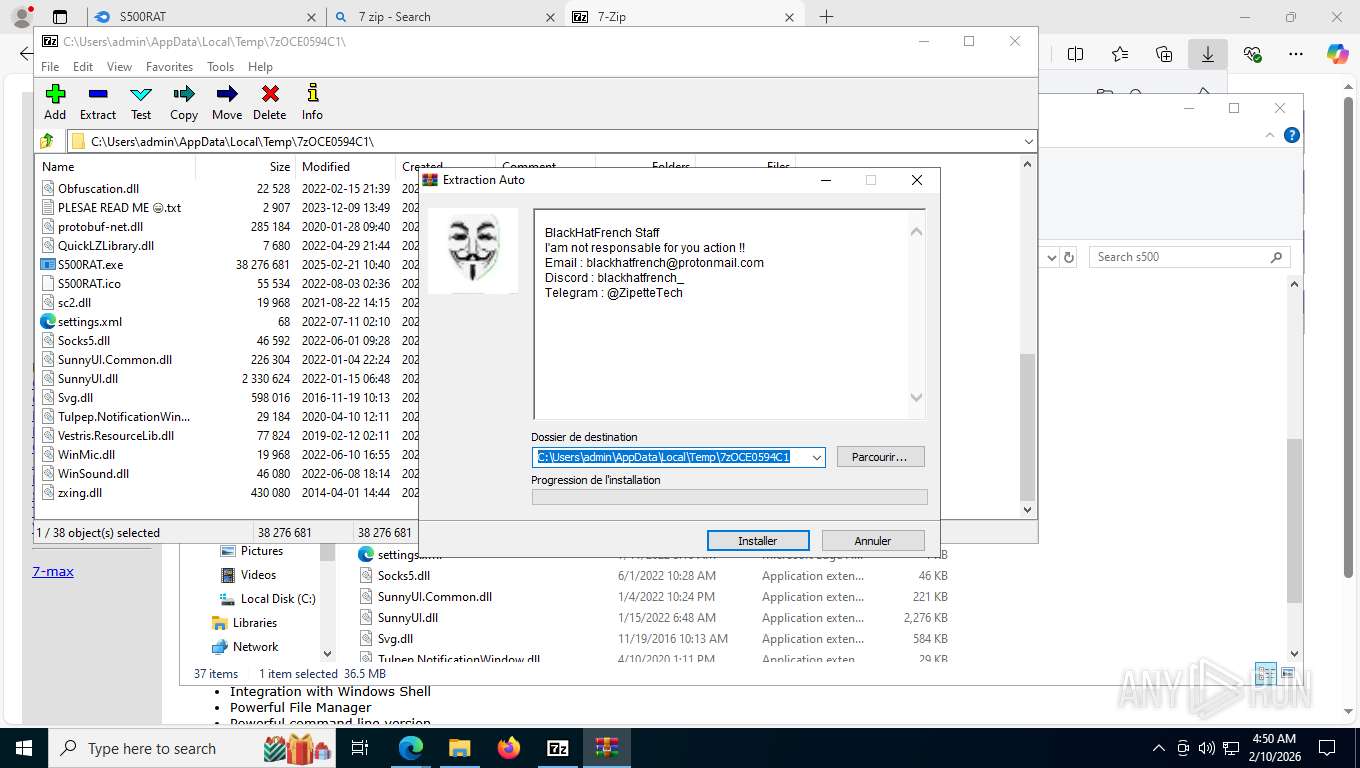
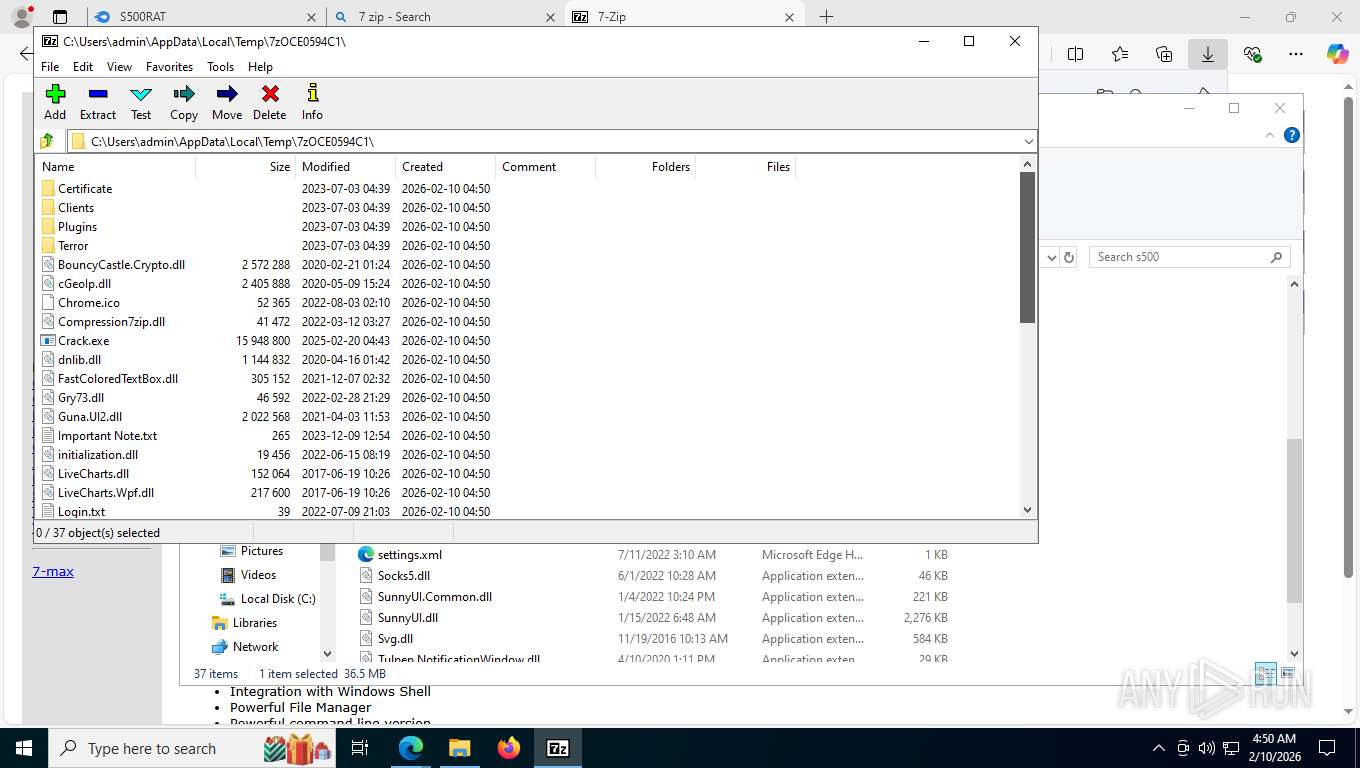
Drops 7-zip archiver for unpacking
- msedge.exe (PID: 7788)
- 7z2501-x64.exe (PID: 6332)
- msedge.exe (PID: 8412)
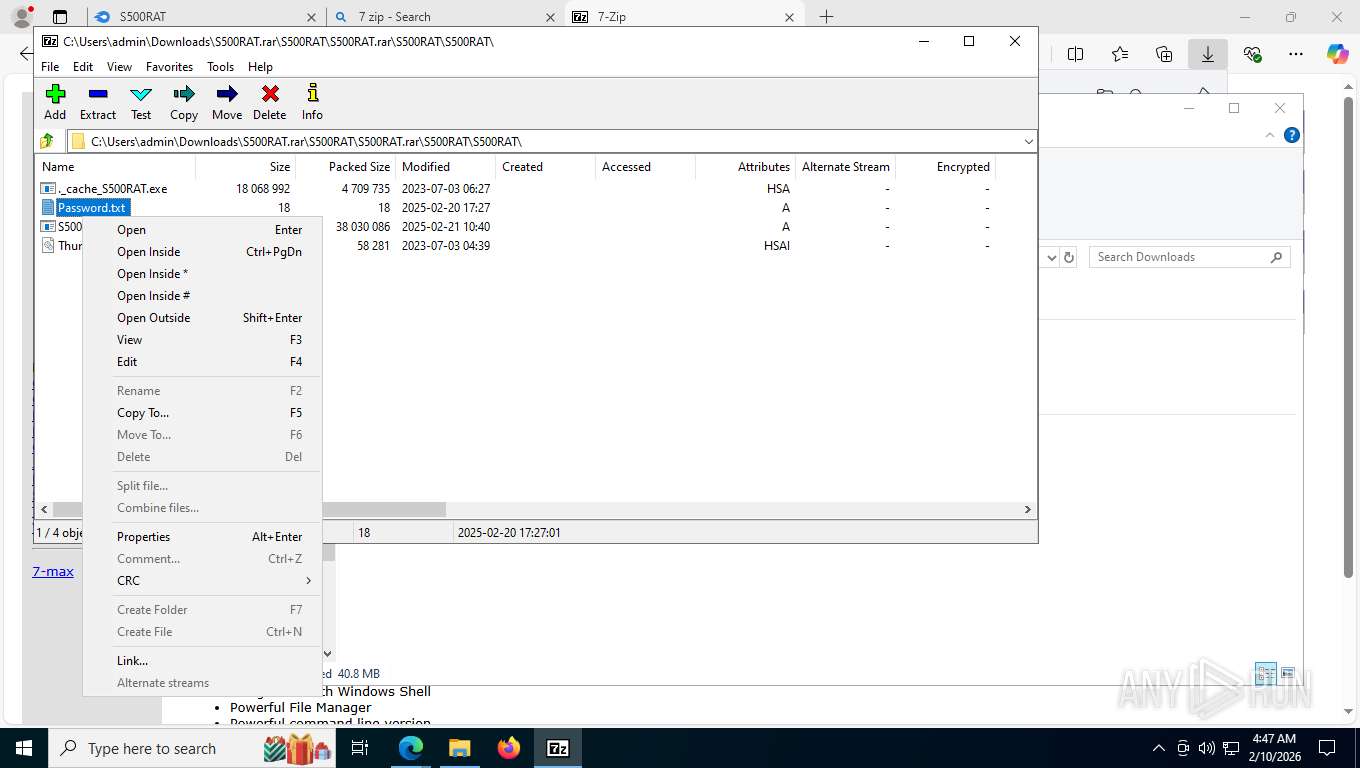
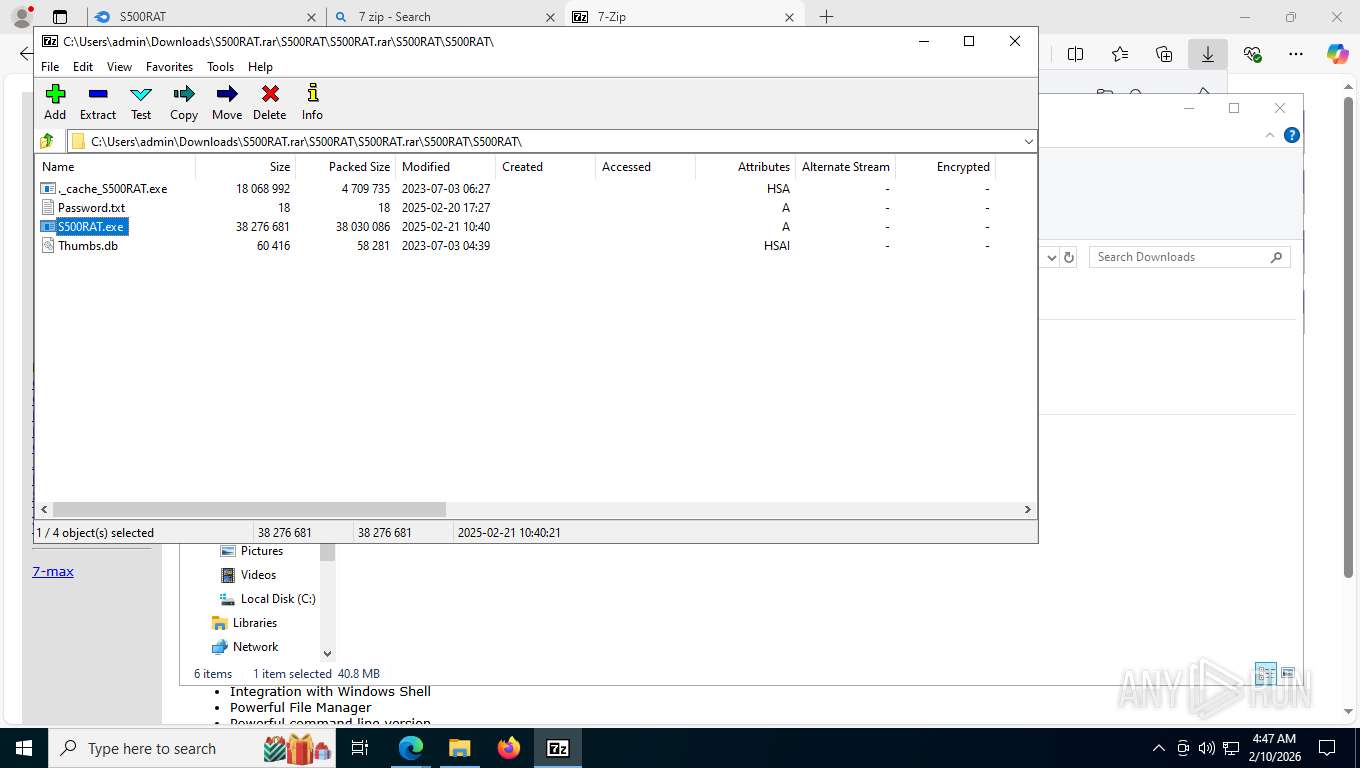
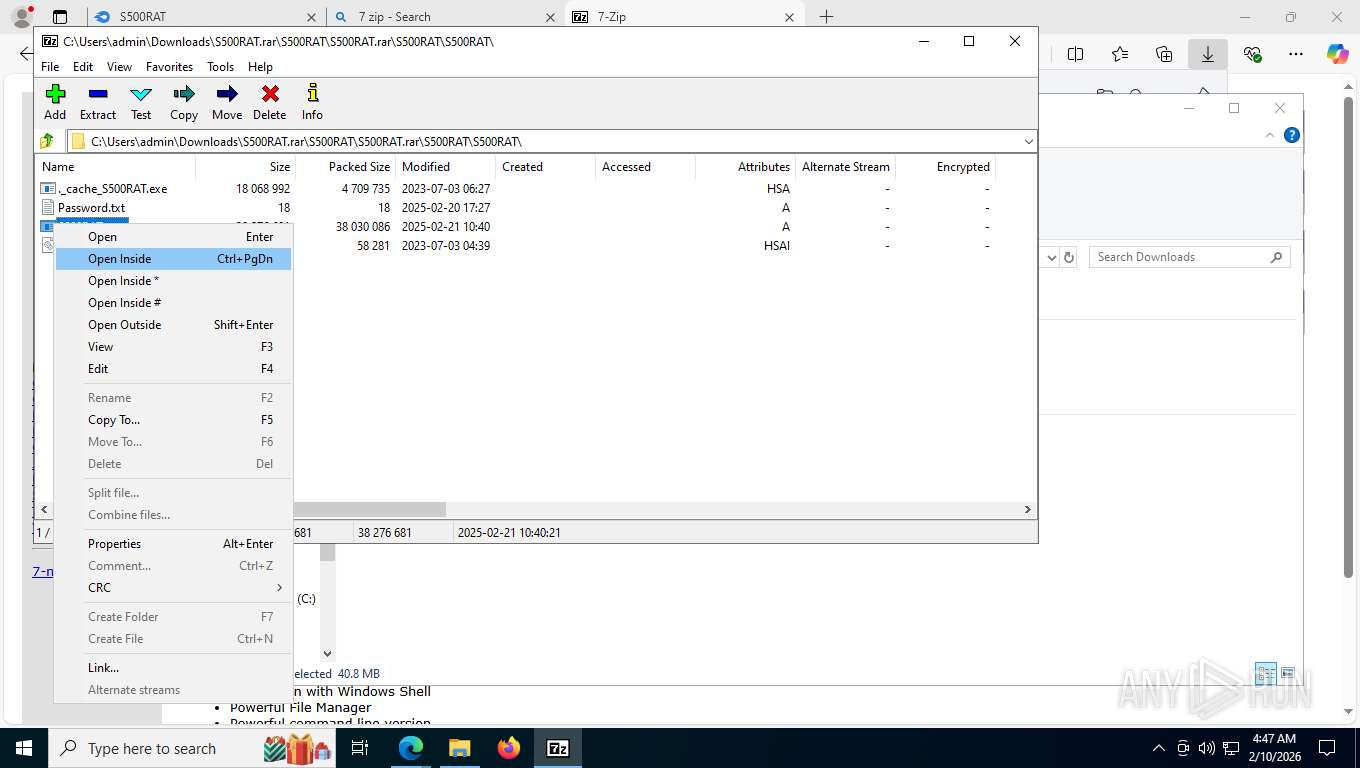
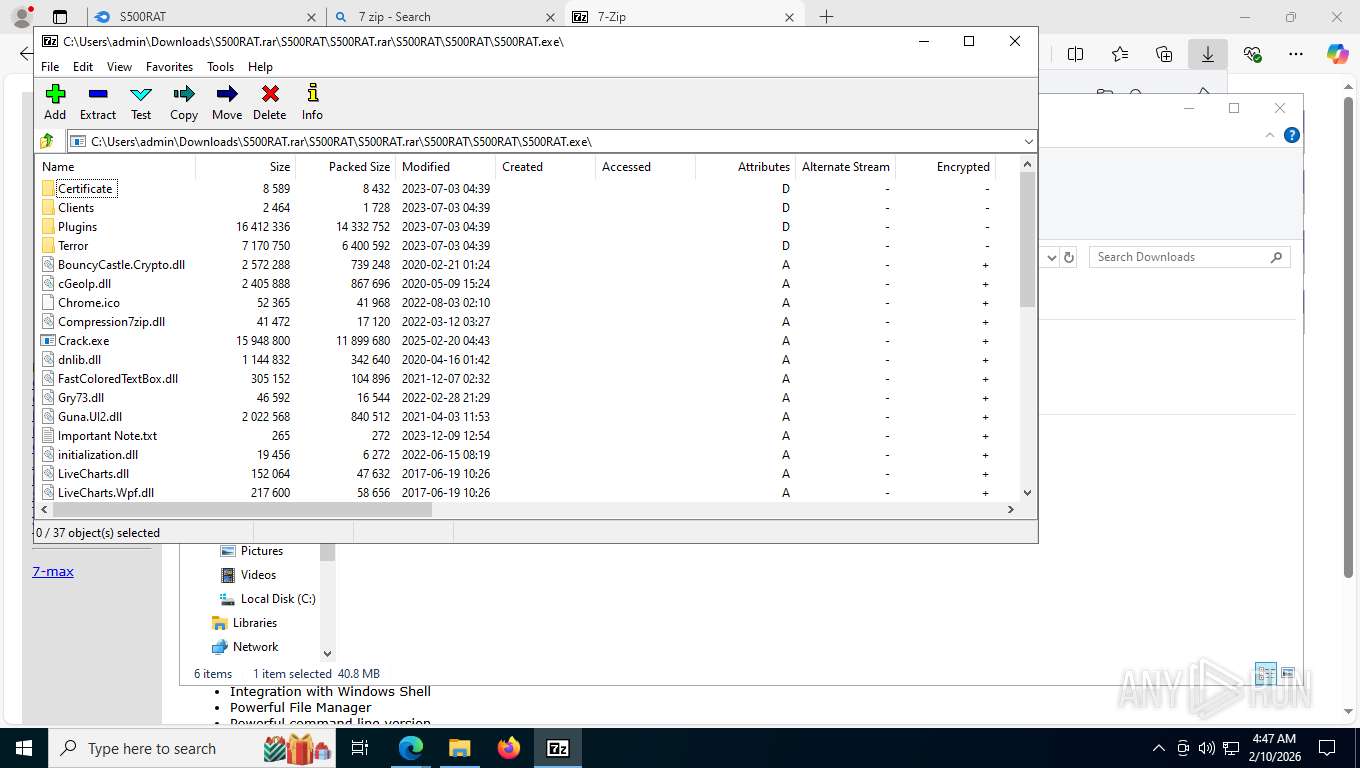
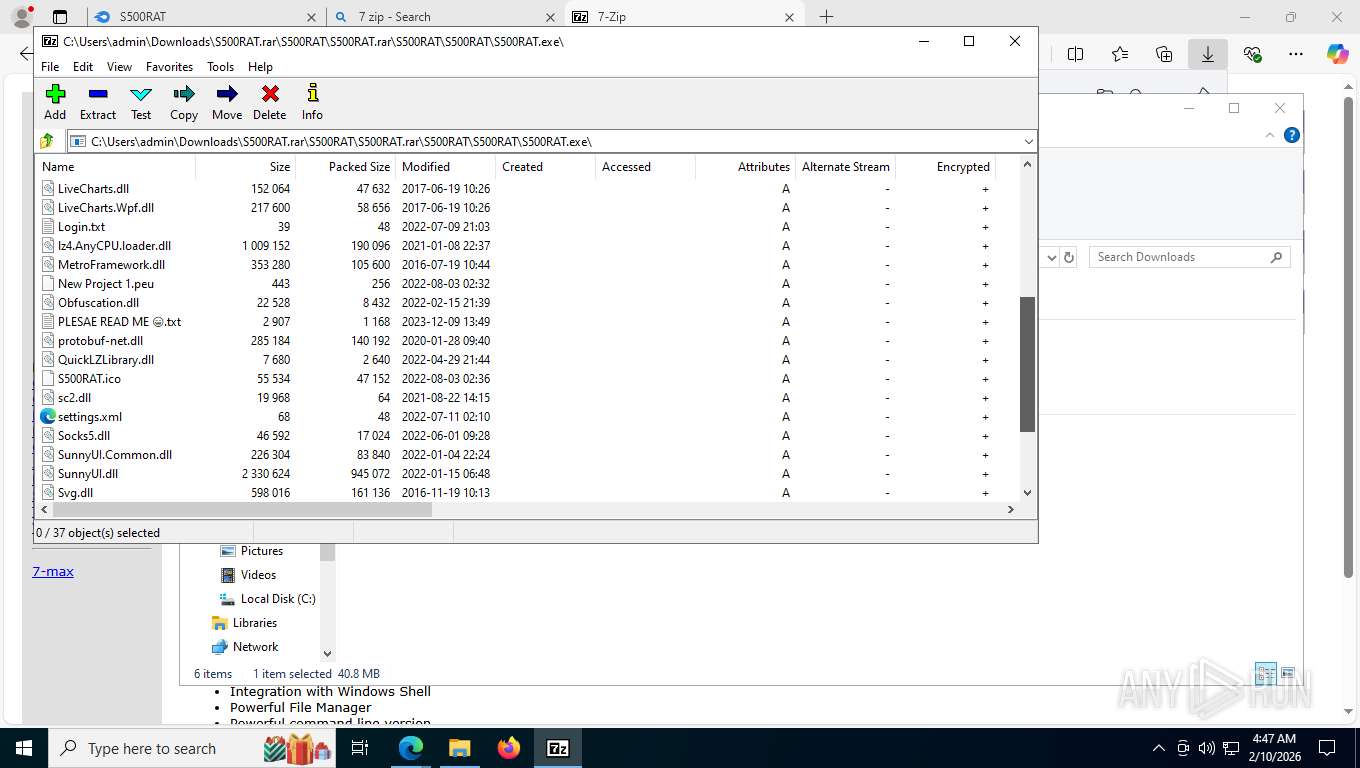
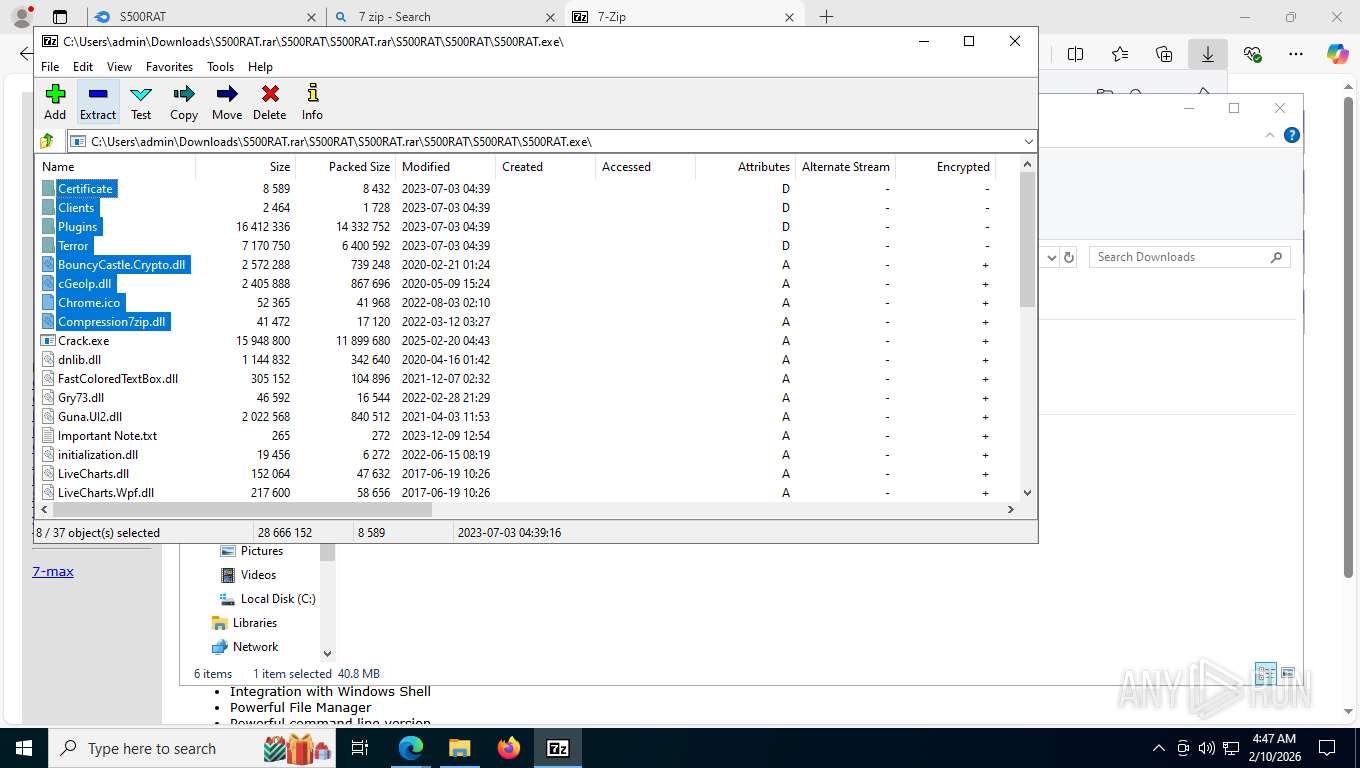
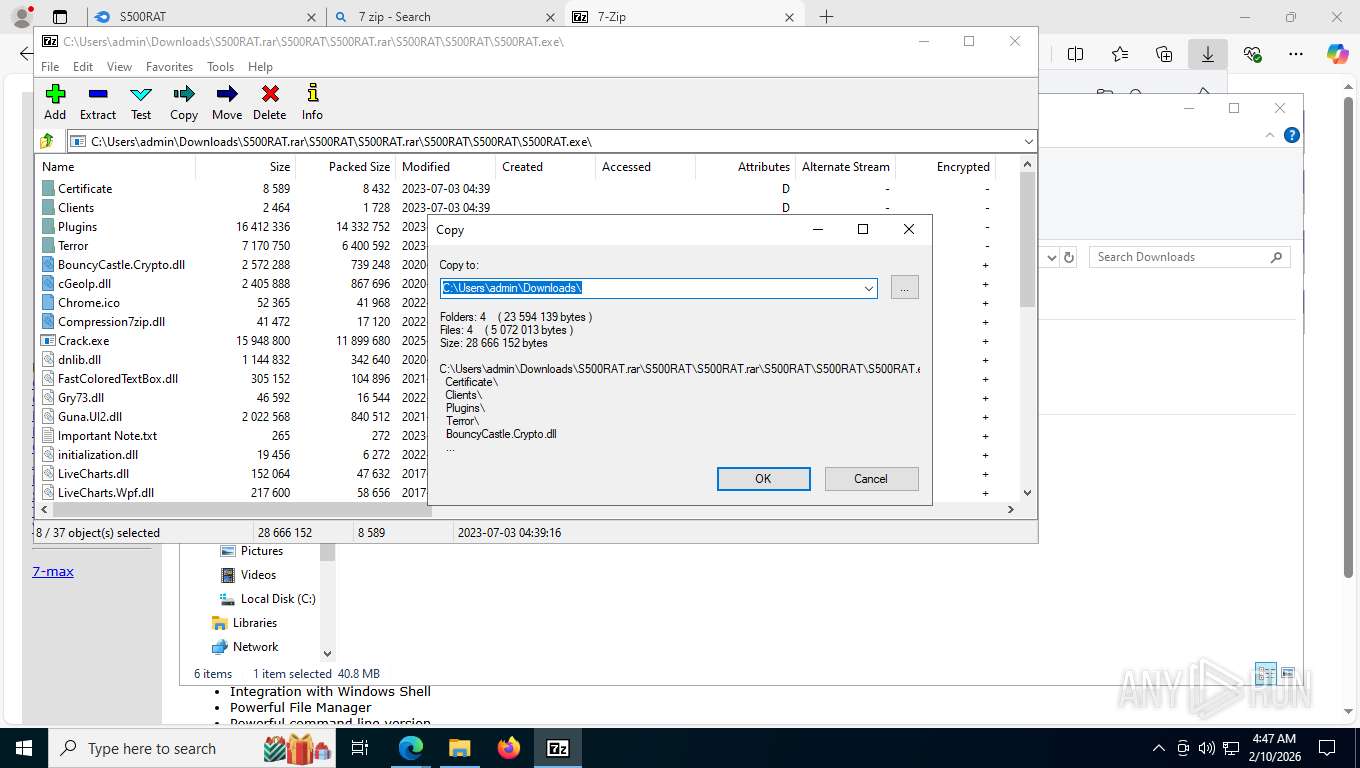
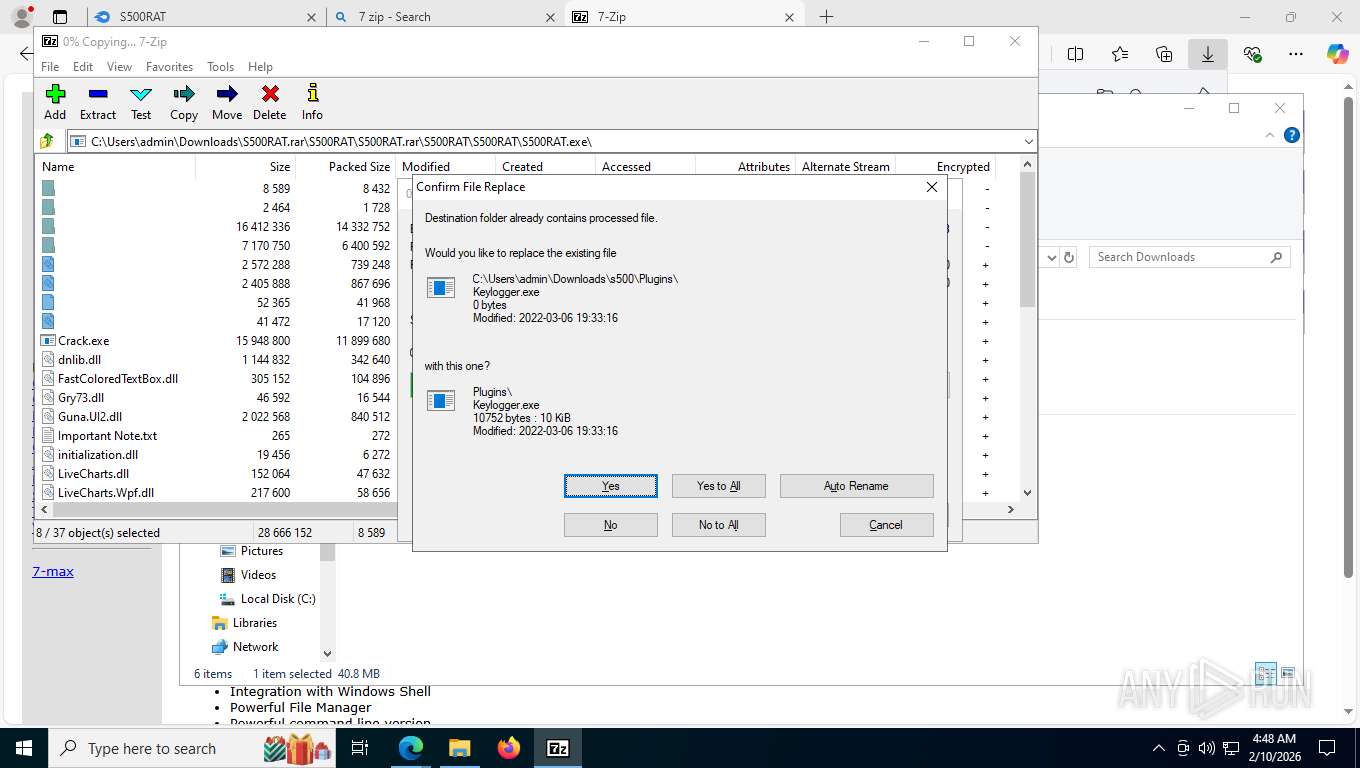
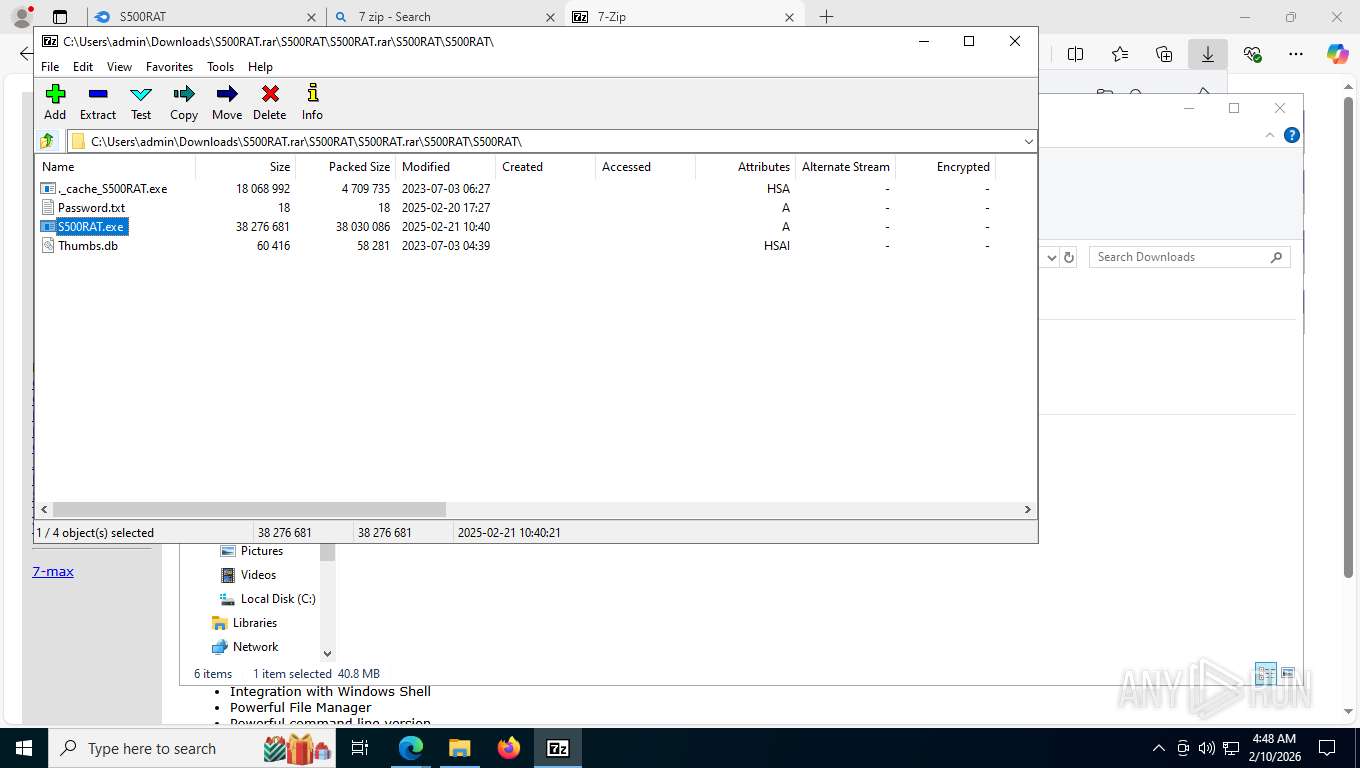
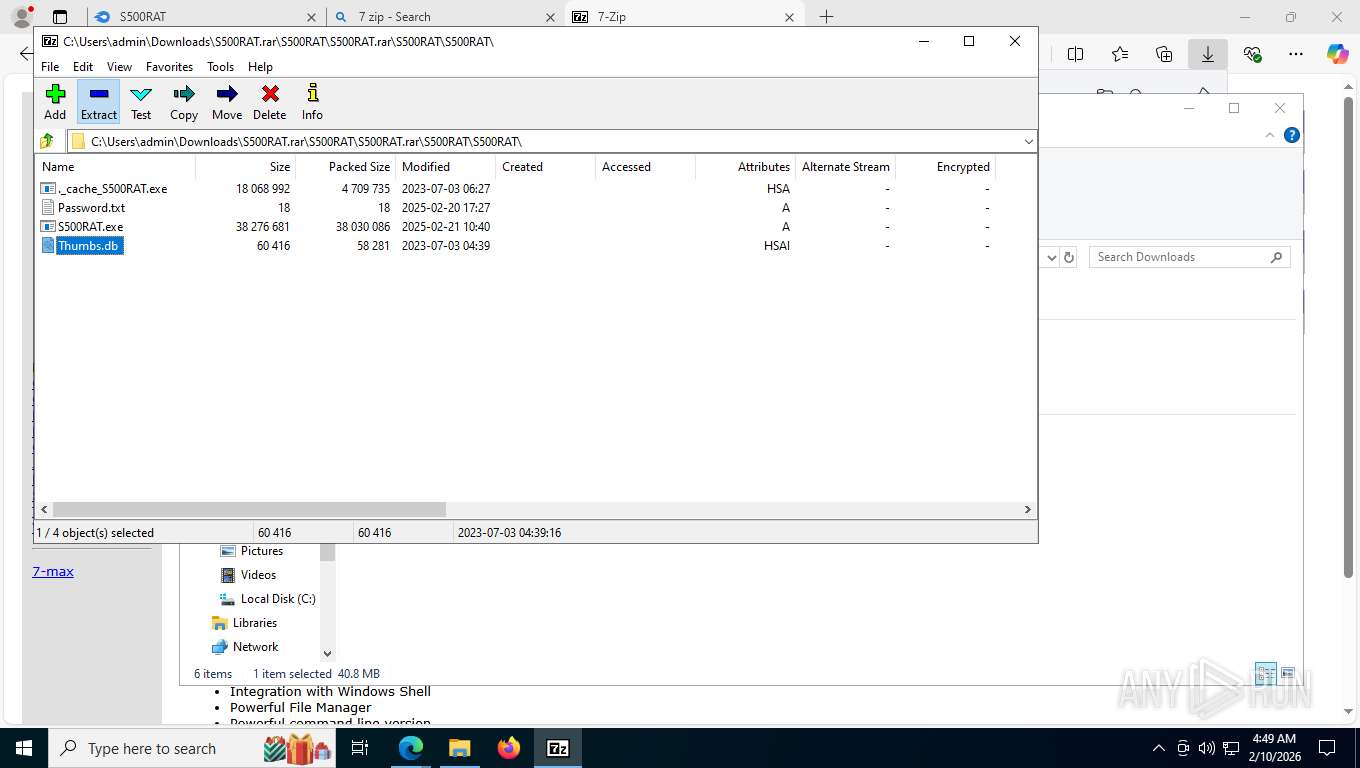
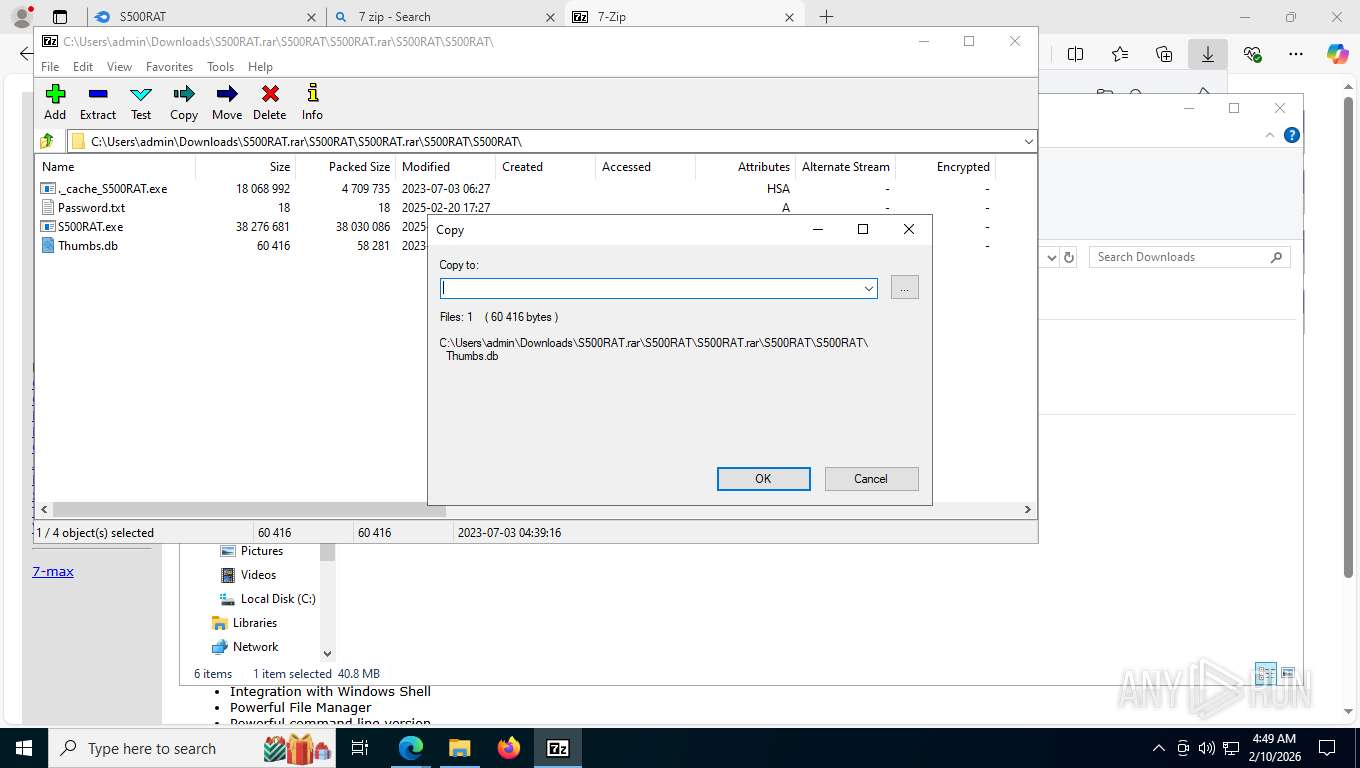
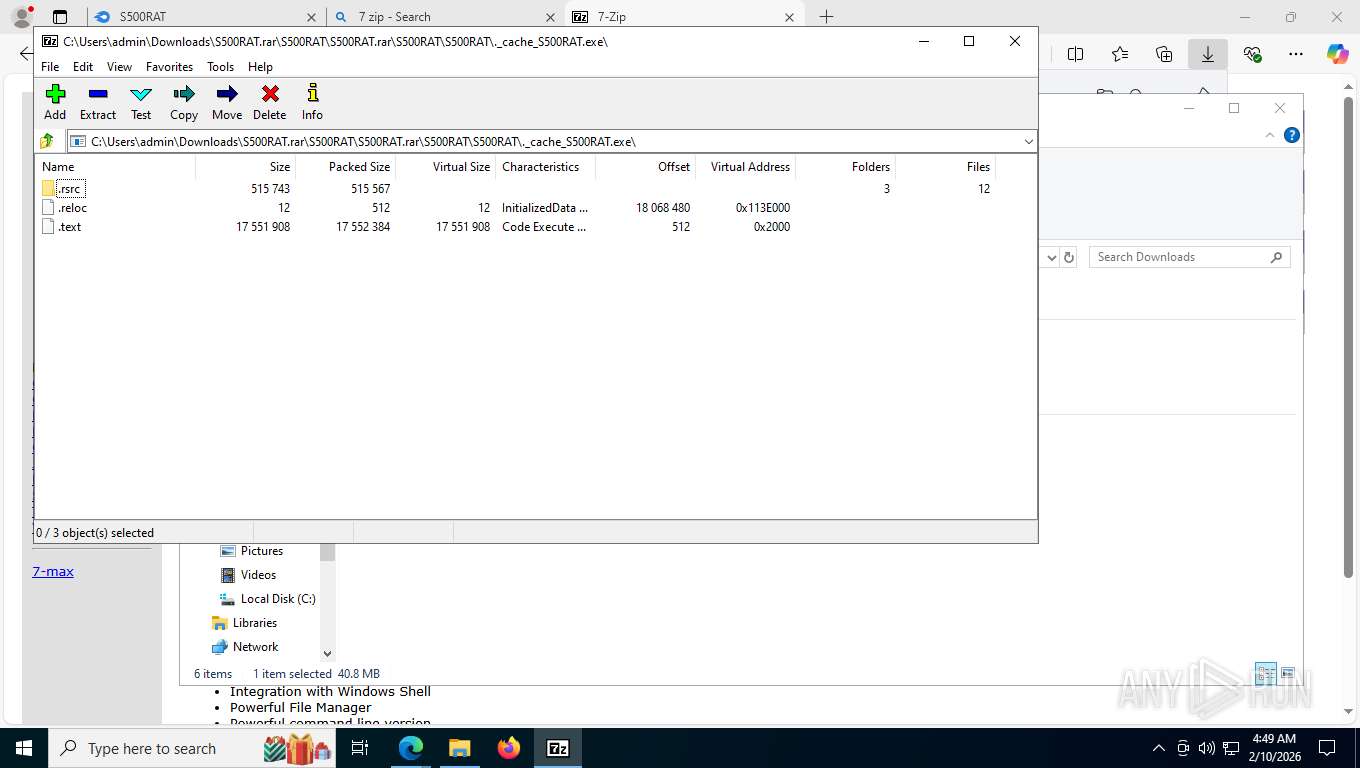
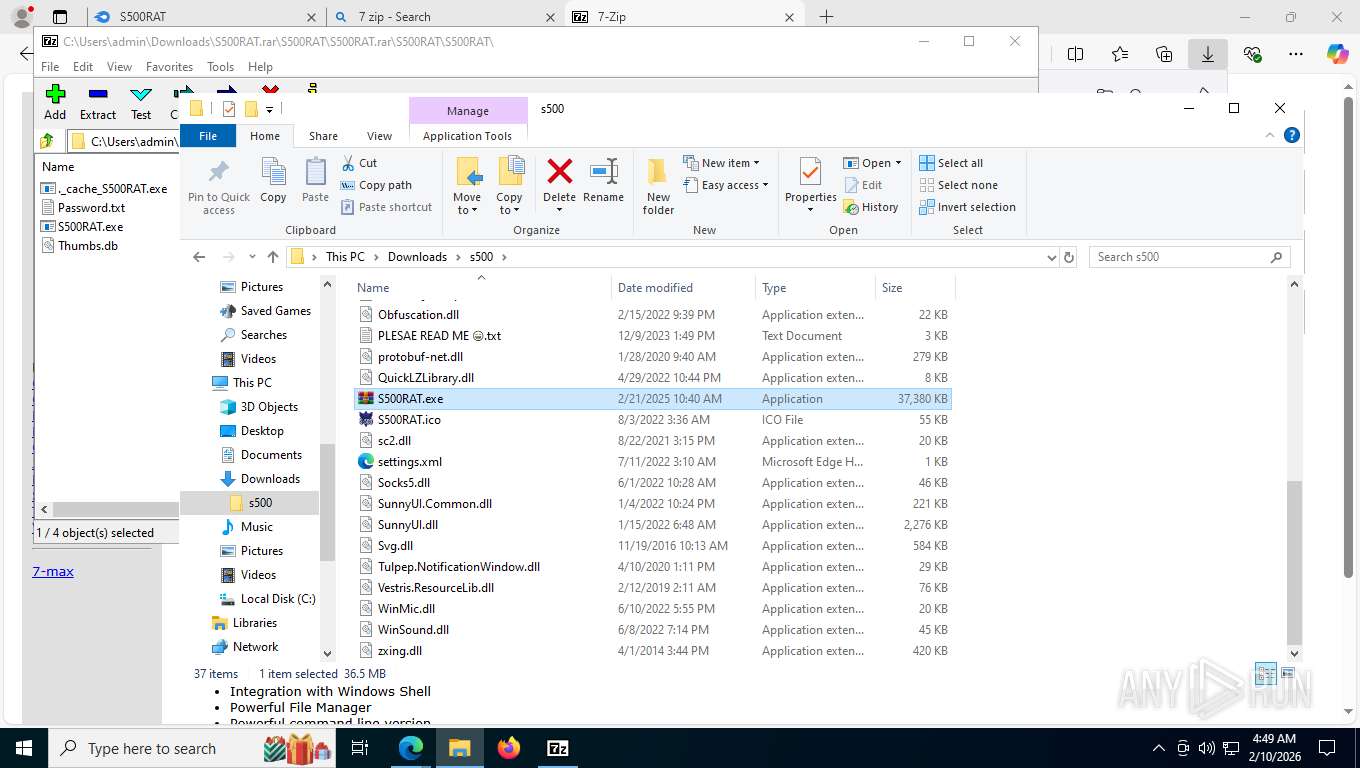
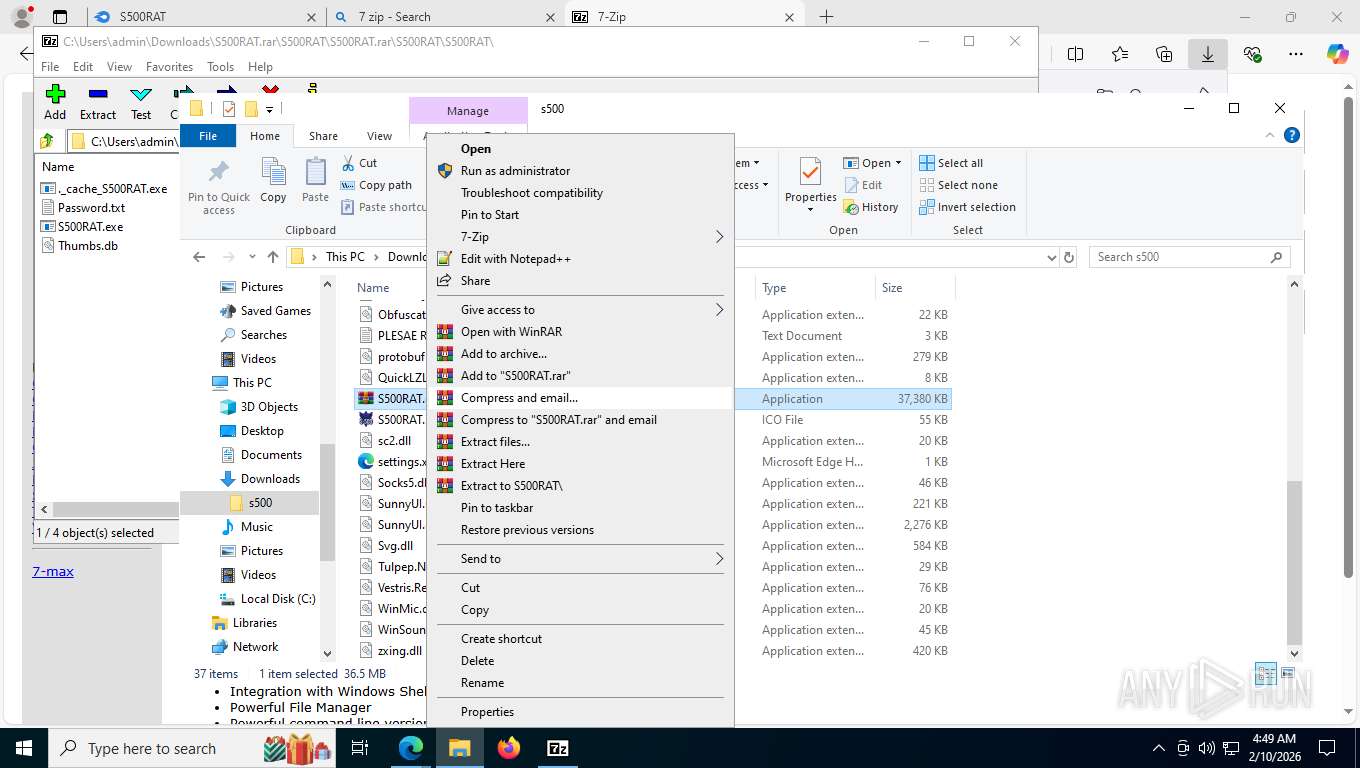
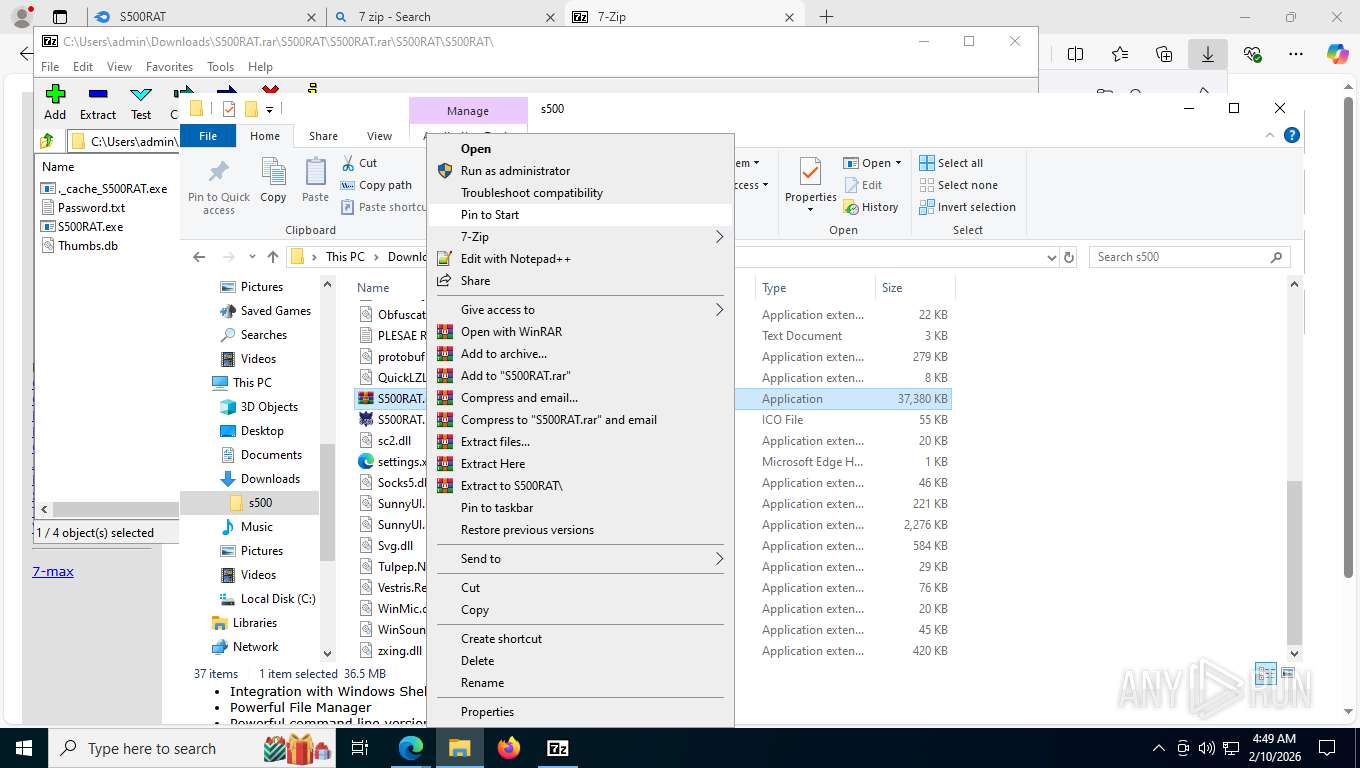
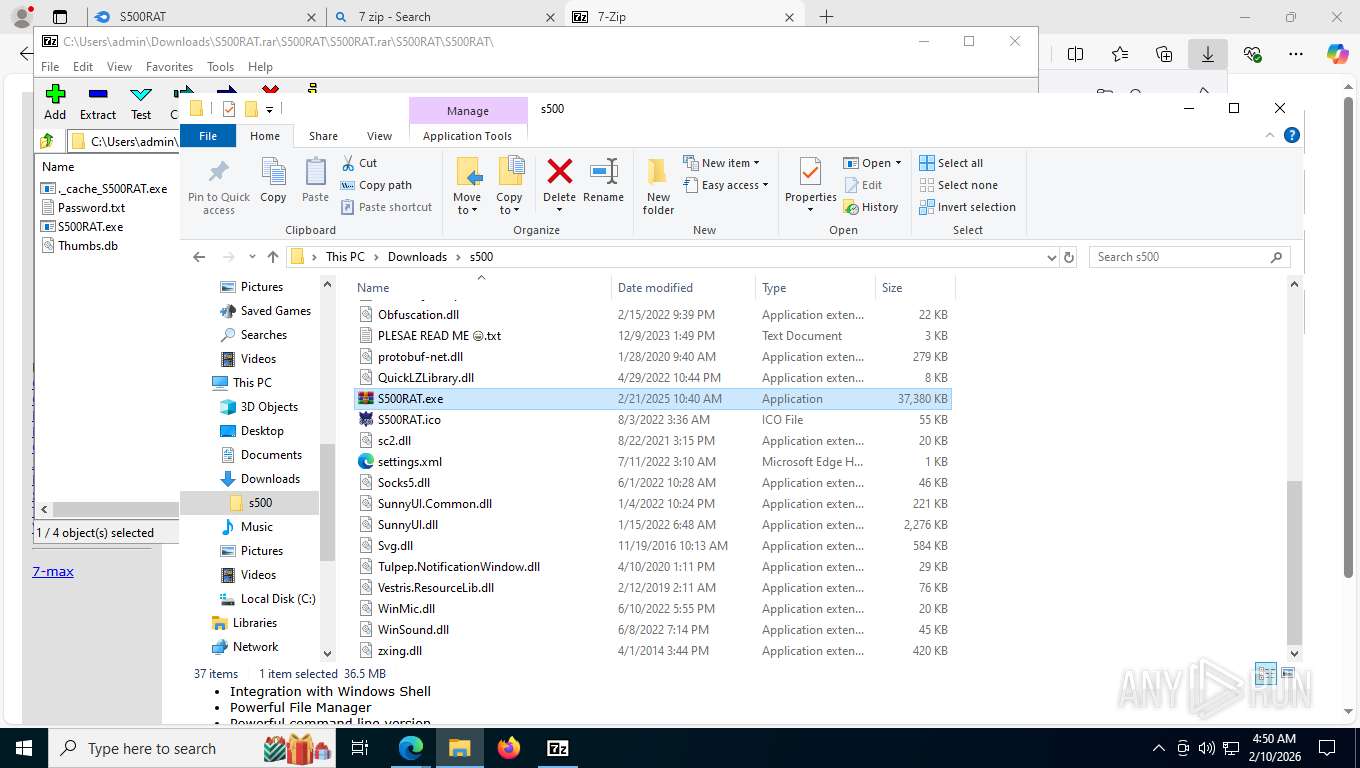
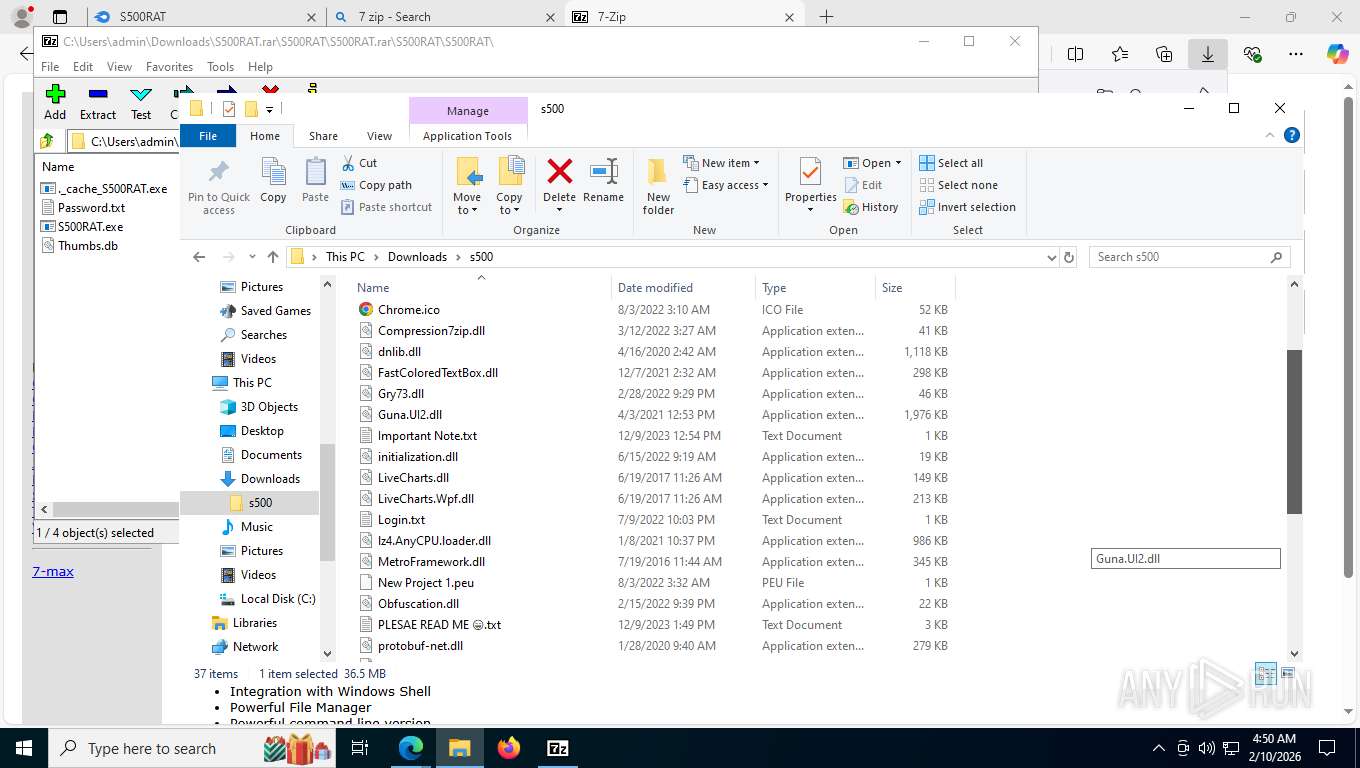
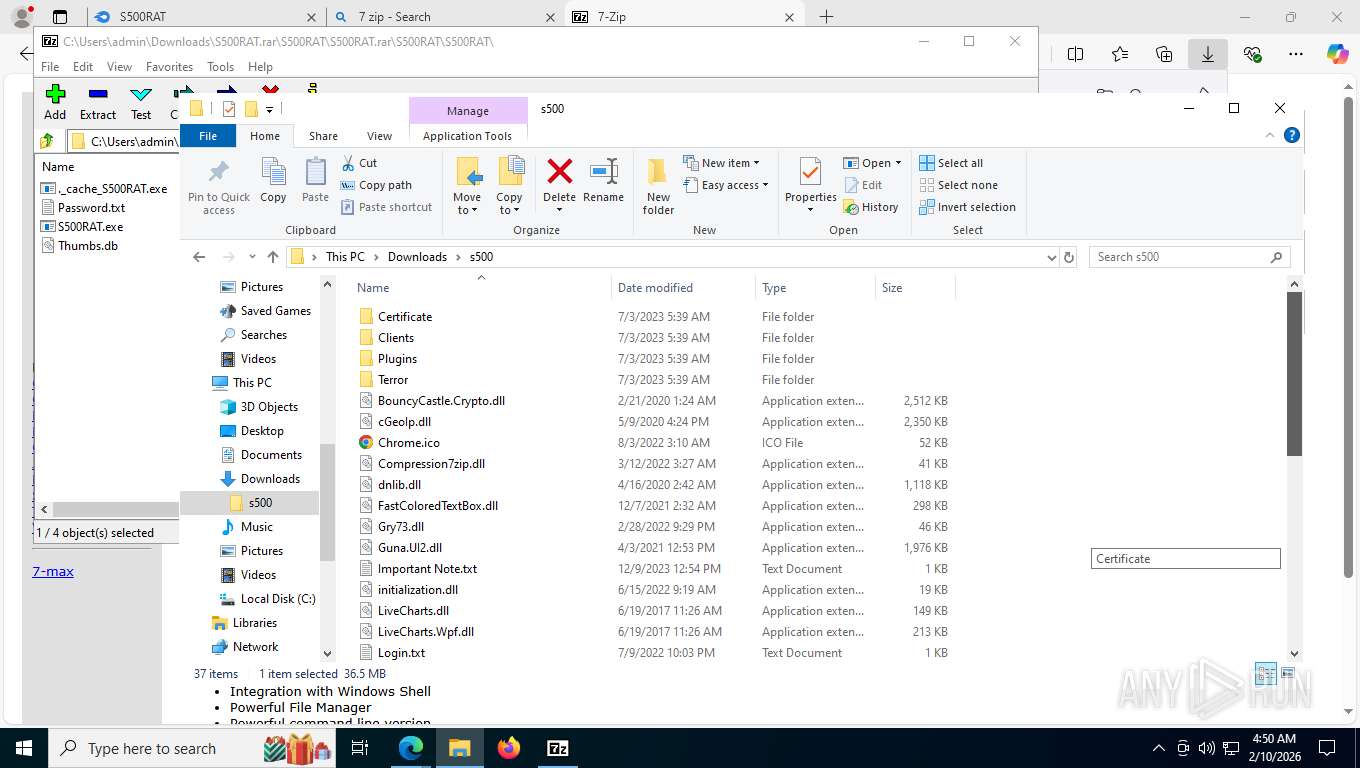
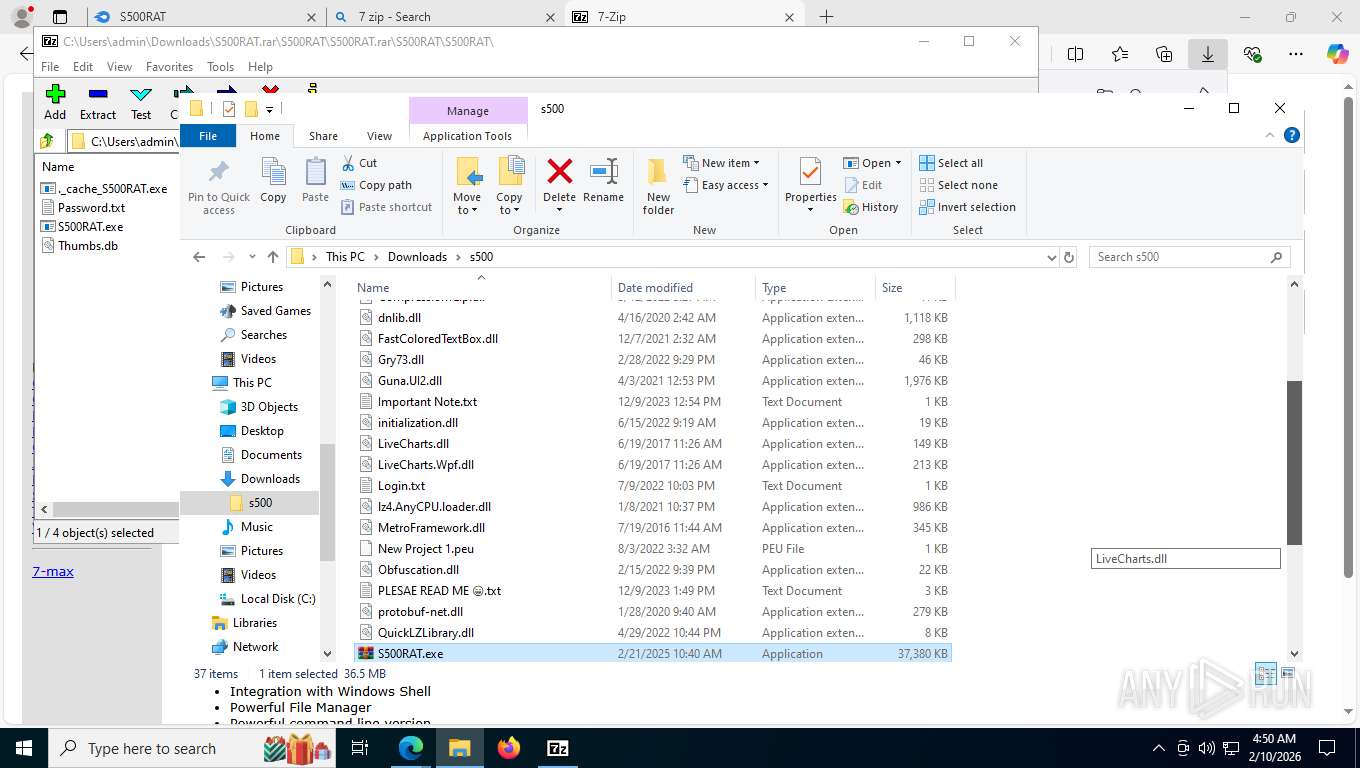
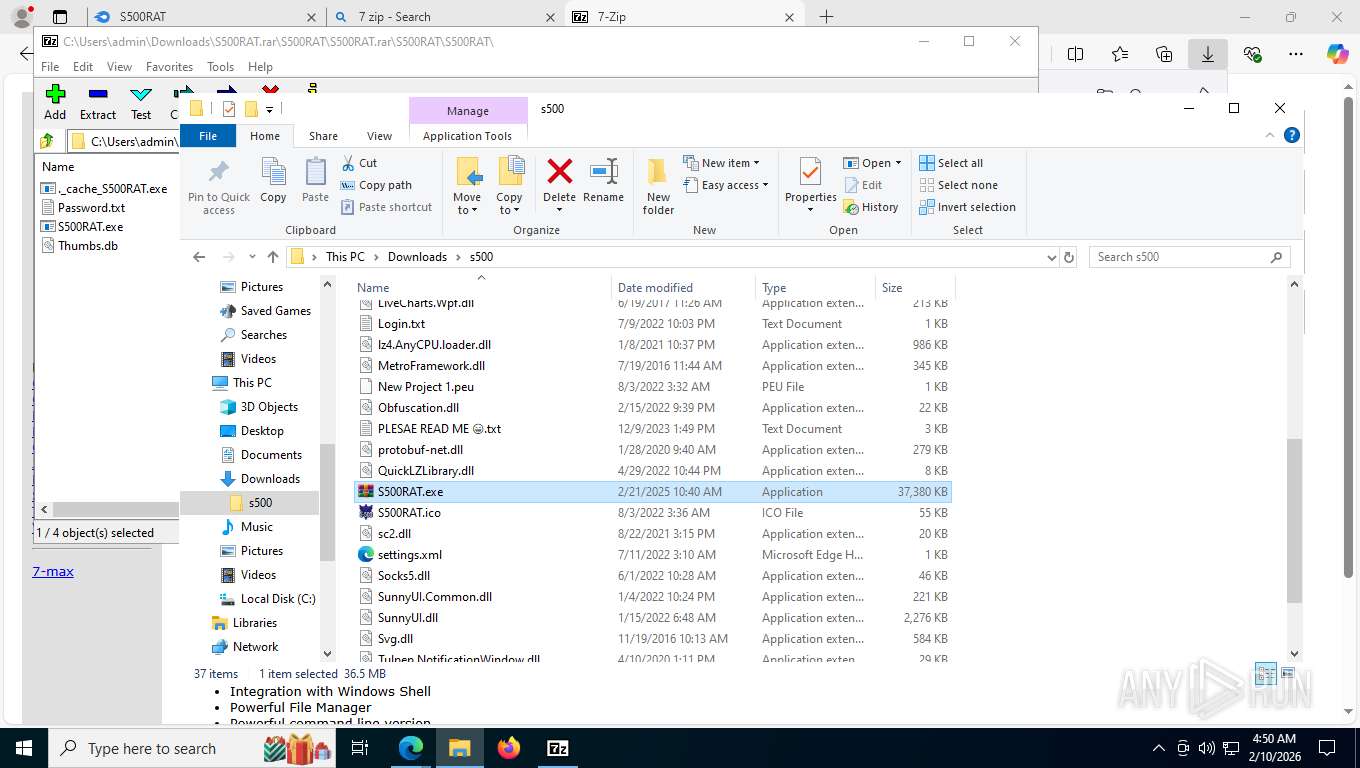
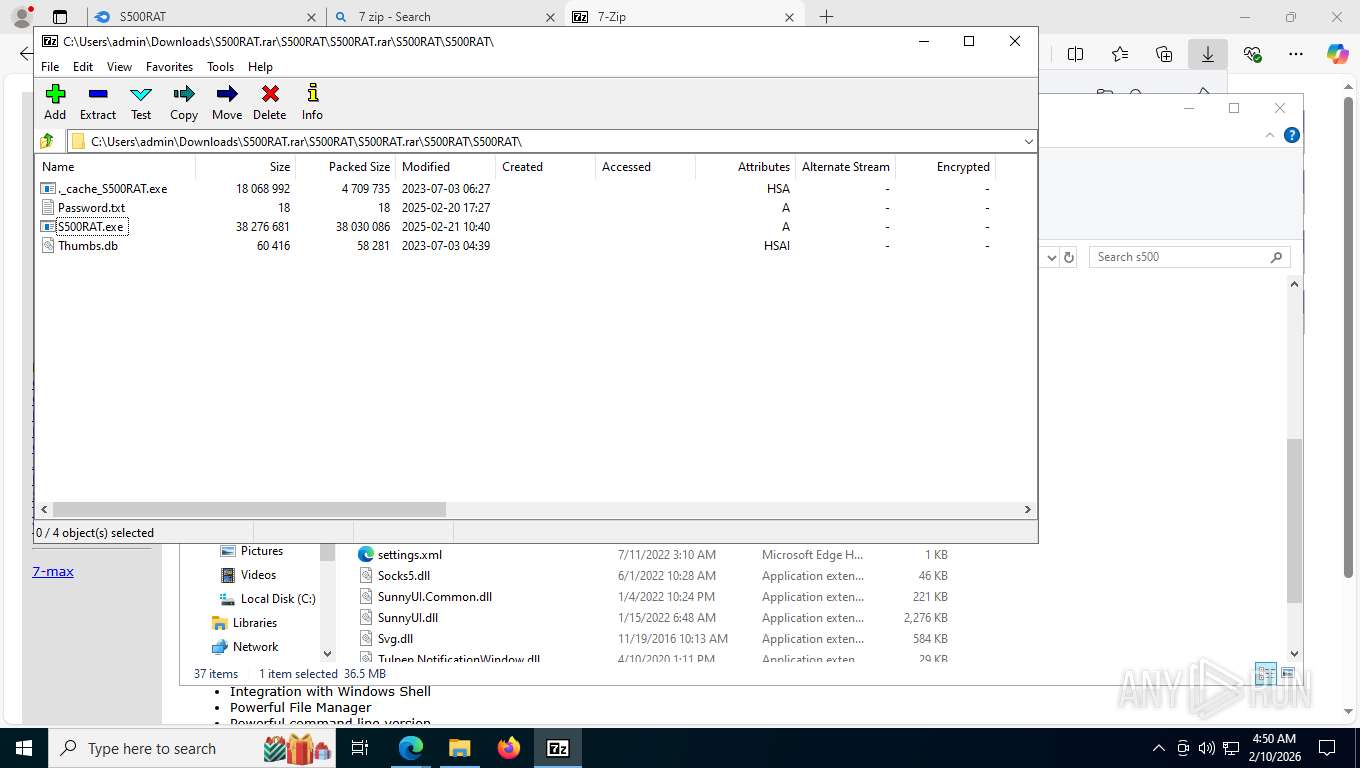
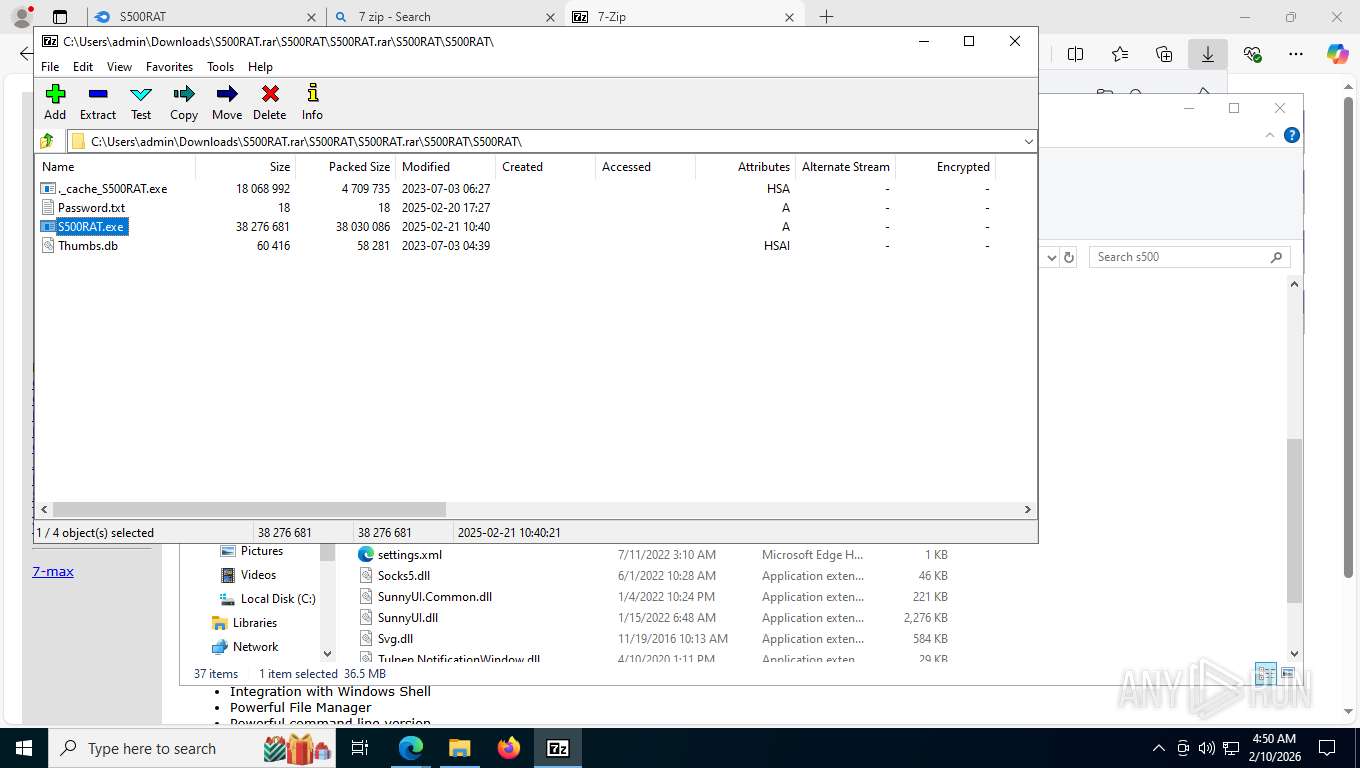
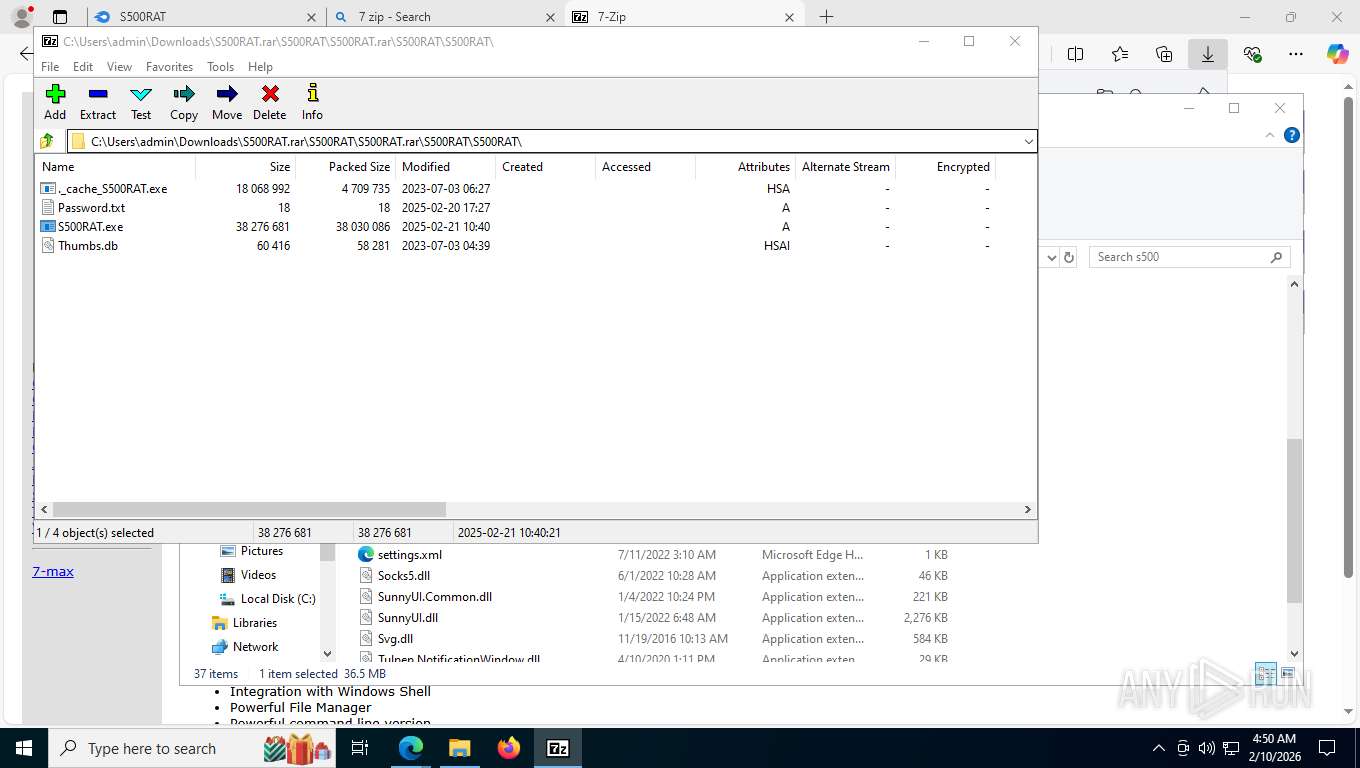
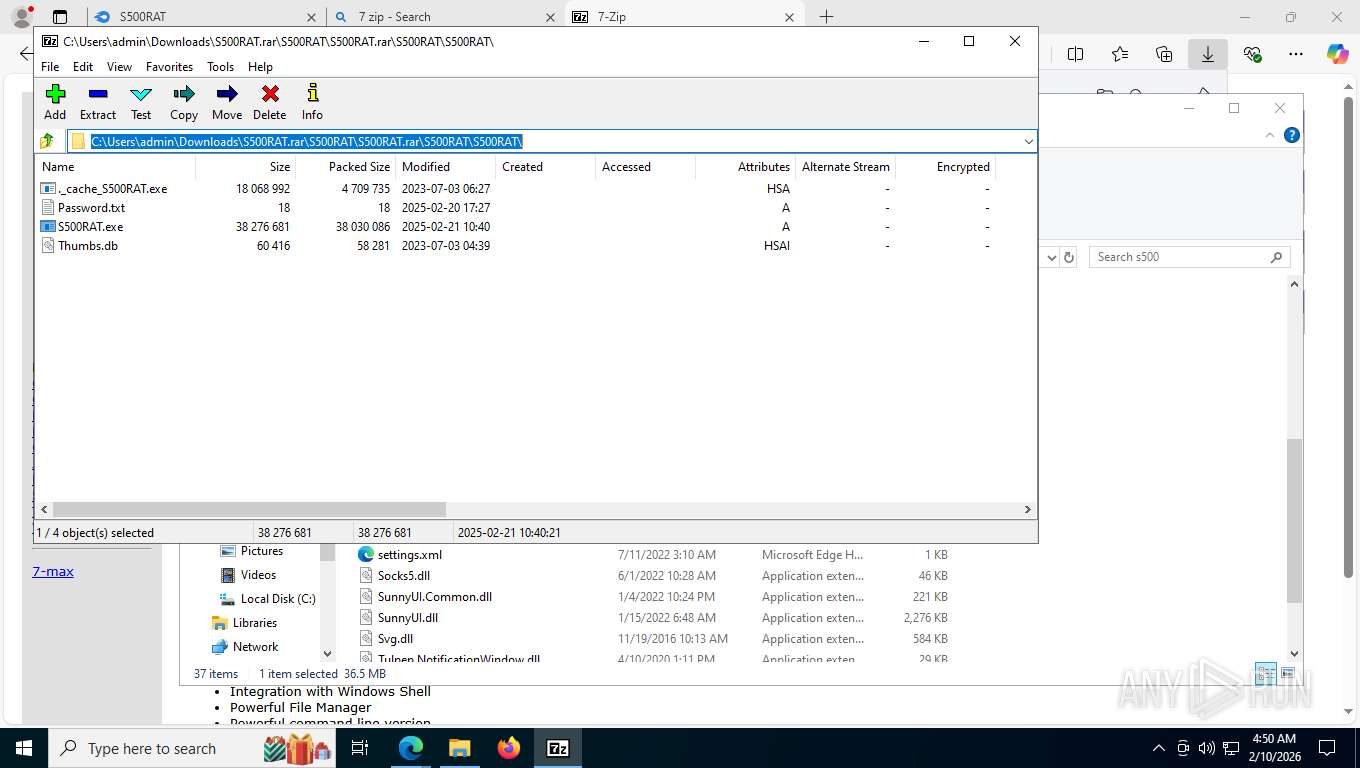
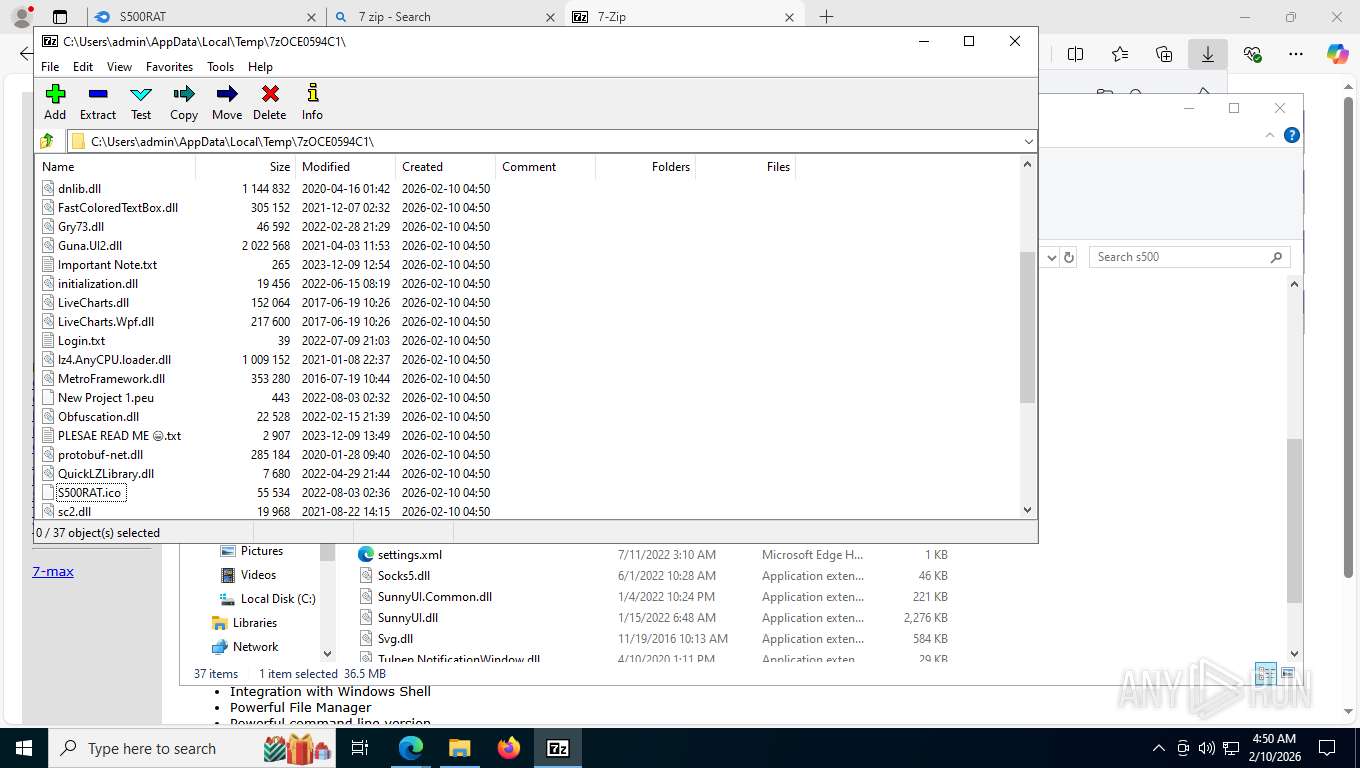
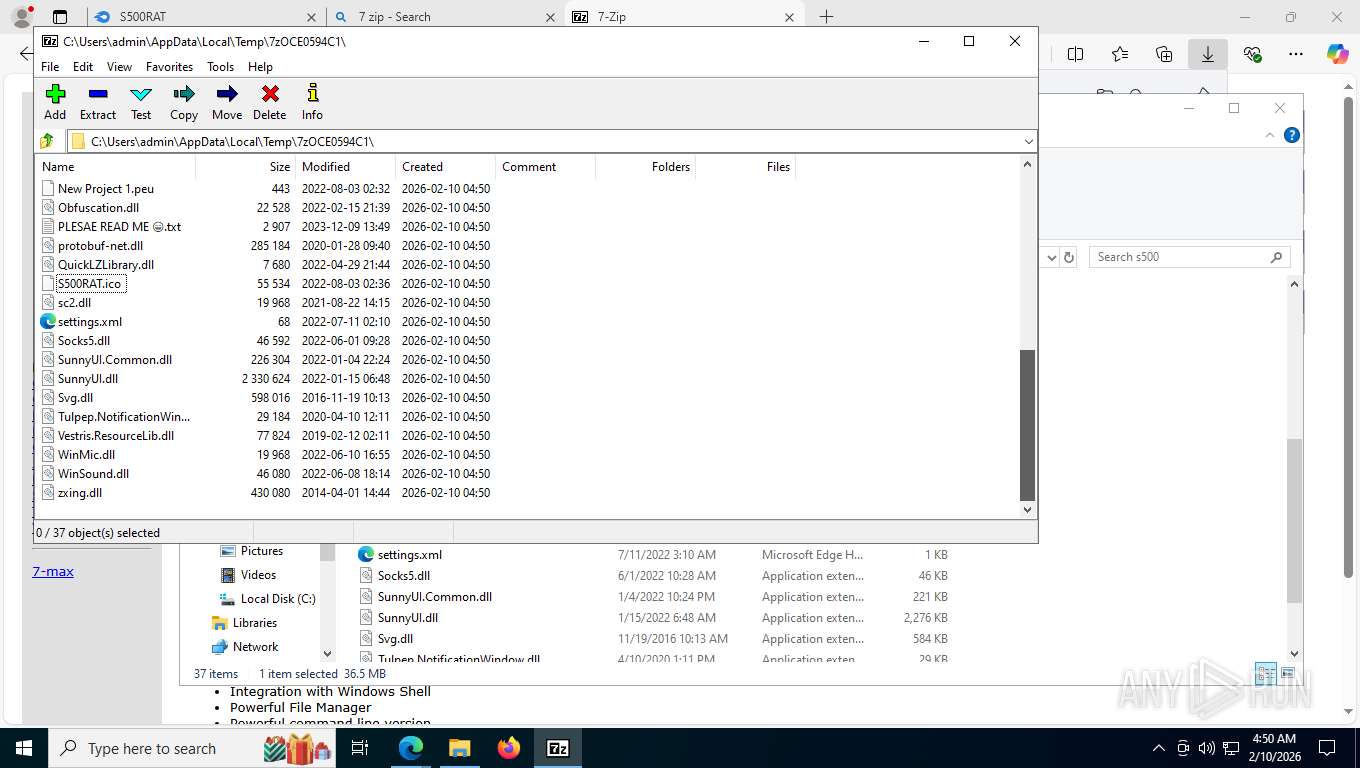
Executable content was dropped or overwritten
- 7z2501-x64.exe (PID: 6332)
- 7zFM.exe (PID: 8428)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 5516)
- dllhost.exe (PID: 9020)
- csc.exe (PID: 9296)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Creates/Modifies COM task schedule object
- 7z2501-x64.exe (PID: 6332)
The process creates files with name similar to system file names
- 7zFM.exe (PID: 8428)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
Reads Microsoft Outlook installation path
- S500RAT.exe (PID: 5808)
- S500RAT.exe (PID: 1824)
Reads the date of Windows installation
- 7zFM.exe (PID: 8428)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Reads Internet Explorer settings
- S500RAT.exe (PID: 5808)
- S500RAT.exe (PID: 1824)
Reads the BIOS version
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
The process checks if it is being run in the virtual environment
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
Read disk information to detect sandboxing environments
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
Checks for external IP
- svchost.exe (PID: 2292)
- Crack.exe (PID: 5516)
- Crack.exe (PID: 2912)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- Crack.exe (PID: 2912)
Used cmstp for execute code hidden within an inf file
- Crack.exe (PID: 2912)
Script adds exclusion path to Windows Defender
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- cmd.exe (PID: 3092)
- svchost.exe (PID: 2336)
Bypass execution policy to execute commands
- powershell.exe (PID: 9020)
- powershell.exe (PID: 3404)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 3096)
- powershell.exe (PID: 1692)
- powershell.exe (PID: 9704)
- powershell.exe (PID: 9316)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 8488)
- powershell.exe (PID: 2684)
Starts POWERSHELL.EXE for commands execution
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- cmd.exe (PID: 3092)
- cmd.exe (PID: 3164)
- cmd.exe (PID: 10096)
- cmd.exe (PID: 9400)
- cmd.exe (PID: 2740)
- svchost.exe (PID: 2336)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 9376)
- cmd.exe (PID: 412)
Process drops legitimate windows executable
- Crack.exe (PID: 5516)
- dllhost.exe (PID: 9020)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
The process drops C-runtime libraries
- dllhost.exe (PID: 9020)
Process drops python dynamic module
- dllhost.exe (PID: 9020)
Starts MSHTA.EXE for opening HTA or HTMLS files
- dllhost.exe (PID: 7652)
Application launched itself
- dllhost.exe (PID: 9020)
Found strings related to reading or modifying Windows Defender settings
- dllhost.exe (PID: 3988)
Starts CMD.EXE for commands execution
- dllhost.exe (PID: 3988)
Get information on the list of running processes
- cmd.exe (PID: 2312)
- dllhost.exe (PID: 3988)
- cmd.exe (PID: 9832)
- cmd.exe (PID: 10108)
- cmd.exe (PID: 9860)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 3164)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1844)
- cmd.exe (PID: 10060)
- cmd.exe (PID: 1512)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8176)
- WMIC.exe (PID: 7448)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 9532)
- cmd.exe (PID: 9636)
- cmd.exe (PID: 9852)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 9588)
- WMIC.exe (PID: 9712)
- WMIC.exe (PID: 3092)
Possible stealing from crypto wallets
- dllhost.exe (PID: 3988)
Get Clipboard Data (POWERSHELL)
- cmd.exe (PID: 10096)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 10220)
Script disables Windows Defender's IPS
- cmd.exe (PID: 3164)
Starts application with an unusual extension
- cmd.exe (PID: 4424)
- cmd.exe (PID: 10204)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 9888)
- cmd.exe (PID: 8400)
- cmd.exe (PID: 9112)
Base64-obfuscated command line is found
- cmd.exe (PID: 9400)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 2912)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 9400)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 4516)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 9400)
CSC.EXE is used to compile C# code
- csc.exe (PID: 9296)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6756)
- cmd.exe (PID: 9852)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 4124)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 10012)
- cmd.exe (PID: 10164)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 1368)
- mshta.exe (PID: 8996)
- cmd.exe (PID: 9320)
- cmd.exe (PID: 6992)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 9856)
- cmd.exe (PID: 9896)
- cmd.exe (PID: 9904)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 10044)
- cmd.exe (PID: 10112)
- cmd.exe (PID: 10196)
- cmd.exe (PID: 10156)
- cmd.exe (PID: 9136)
Runs shell command (SCRIPT)
- mshta.exe (PID: 8996)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 1692)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 8088)
Executable started from TEMP via cmd.exe
- cmd.exe (PID: 5896)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 6900)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4624)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8068)
Script adds exclusion process to Windows Defender
- svchost.exe (PID: 2336)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 8044)
INFO
Application launched itself
- msedge.exe (PID: 7788)
Drops script file
- msedge.exe (PID: 7788)
- msedge.exe (PID: 3152)
- msedge.exe (PID: 8412)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 3404)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 3096)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 4828)
- powershell.exe (PID: 1692)
- powershell.exe (PID: 9704)
- dllhost.exe (PID: 3988)
- powershell.exe (PID: 9244)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 9316)
- powershell.exe (PID: 9208)
- powershell.exe (PID: 1320)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 8488)
- powershell.exe (PID: 2684)
The sample compiled with english language support
- msedge.exe (PID: 7788)
- msedge.exe (PID: 8412)
- 7z2501-x64.exe (PID: 6332)
- Crack.exe (PID: 5516)
- dllhost.exe (PID: 9020)
Reads the computer name
- identity_helper.exe (PID: 2052)
- 7z2501-x64.exe (PID: 6332)
- 7zFM.exe (PID: 8428)
- 7zFM.exe (PID: 7368)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 2912)
- S500RAT.exe (PID: 1824)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- dllhost.exe (PID: 9020)
- dllhost.exe (PID: 3988)
- MpCmdRun.exe (PID: 9392)
- svchost.exe (PID: 2336)
Checks supported languages
- 7z2501-x64.exe (PID: 6332)
- identity_helper.exe (PID: 2052)
- 7zFM.exe (PID: 8428)
- 7zFM.exe (PID: 7368)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- S500RAT.exe (PID: 1824)
- WUDFHo.exe (PID: 5260)
- dllhost.exe (PID: 9020)
- dllhost.exe (PID: 3988)
- tree.com (PID: 9544)
- tree.com (PID: 10068)
- tree.com (PID: 9520)
- tree.com (PID: 2872)
- tree.com (PID: 9112)
- tree.com (PID: 9388)
- MpCmdRun.exe (PID: 9392)
- csc.exe (PID: 9296)
- cvtres.exe (PID: 8292)
- svchost.exe (PID: 2336)
- rar.exe (PID: 8088)
Executable content was dropped or overwritten
- msedge.exe (PID: 8412)
- msedge.exe (PID: 7788)
Reads Environment values
- identity_helper.exe (PID: 2052)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
The sample compiled with russian language support
- 7z2501-x64.exe (PID: 6332)
Manual execution by a user
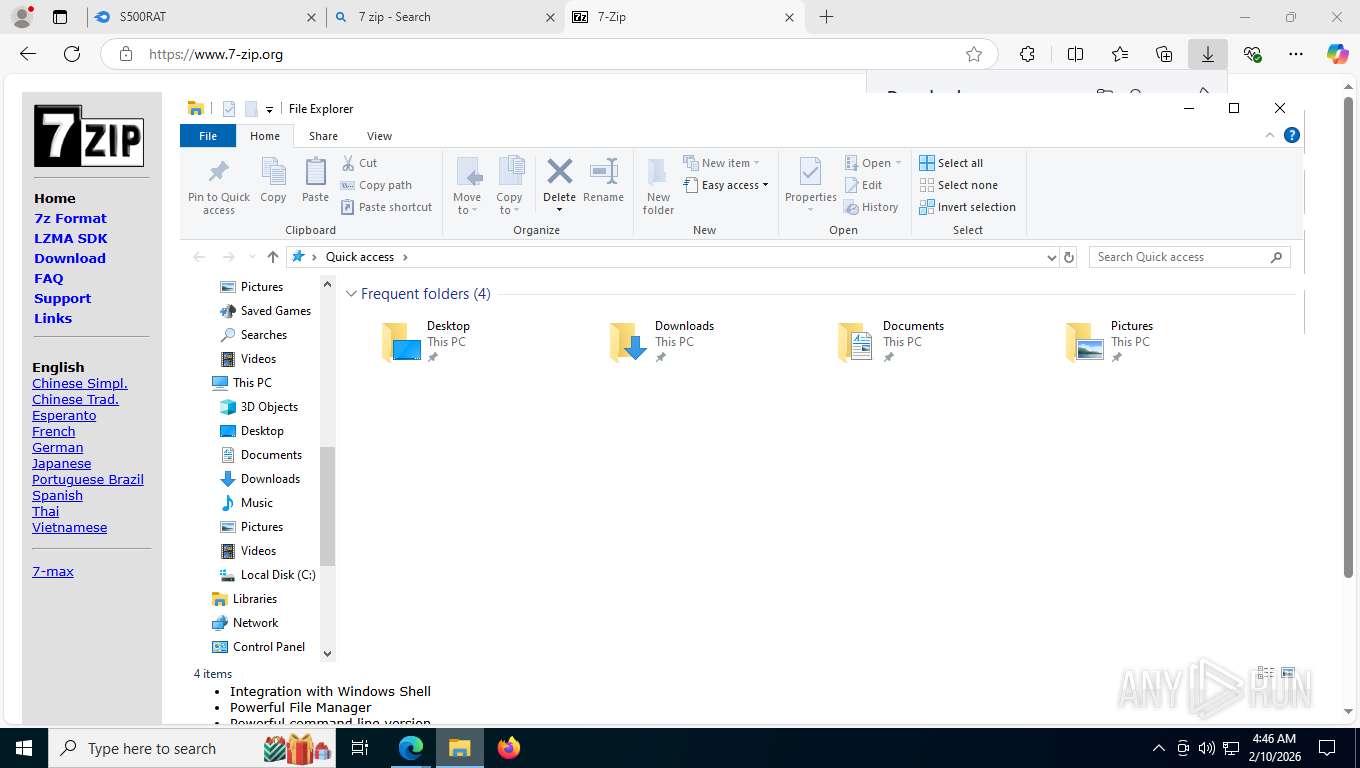
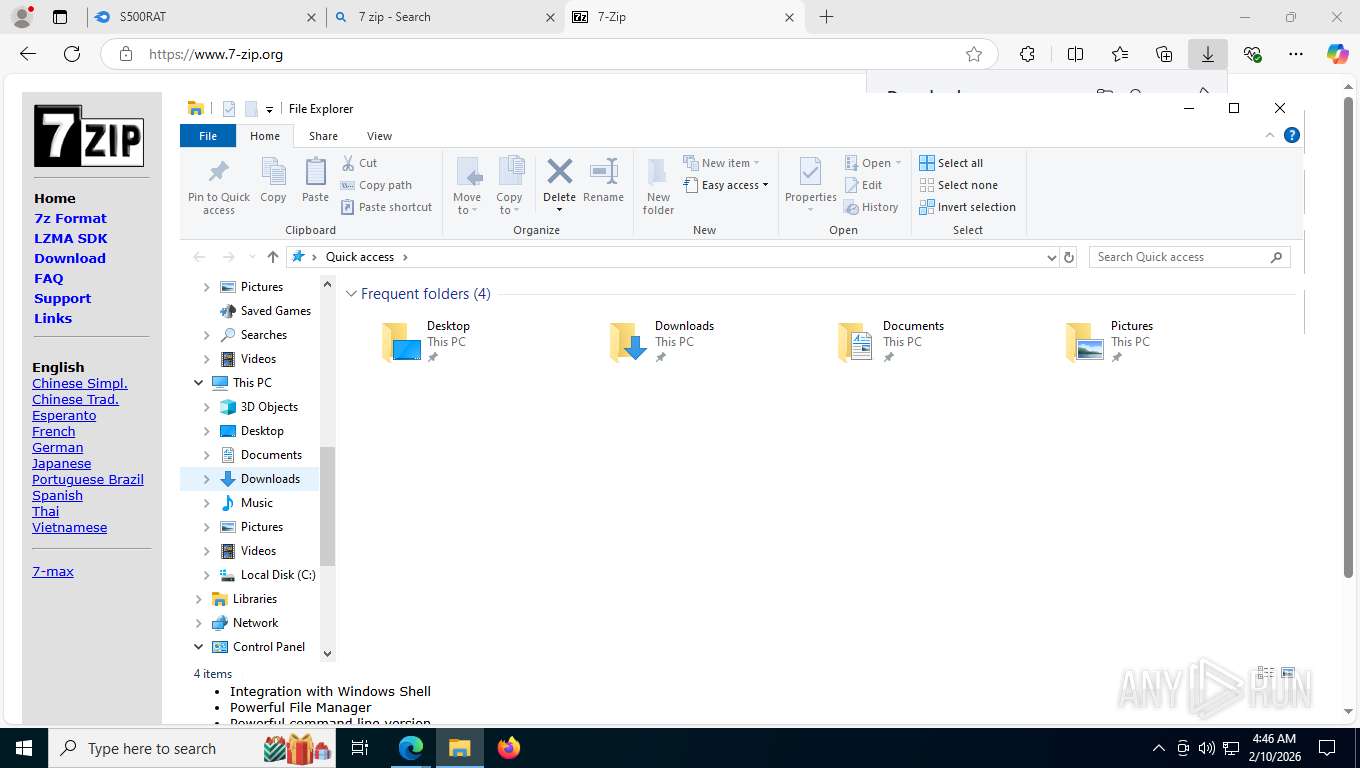
- 7zFM.exe (PID: 8428)
- 7zFM.exe (PID: 7368)
Creates a software uninstall entry
- 7z2501-x64.exe (PID: 6332)
Create files in a temporary directory
- 7zFM.exe (PID: 8428)
- S500RAT.exe (PID: 5808)
- dllhost.exe (PID: 9020)
- dllhost.exe (PID: 3988)
- MpCmdRun.exe (PID: 9392)
- csc.exe (PID: 9296)
- cvtres.exe (PID: 8292)
- rar.exe (PID: 8088)
Checks proxy server information
- slui.exe (PID: 1600)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- S500RAT.exe (PID: 1824)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Reads security settings of Internet Explorer
- 7zFM.exe (PID: 8428)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- S500RAT.exe (PID: 1824)
- WUDFHo.exe (PID: 5260)
- WMIC.exe (PID: 9588)
- WMIC.exe (PID: 8176)
- WMIC.exe (PID: 9712)
- WMIC.exe (PID: 10220)
- svchost.exe (PID: 2336)
- WMIC.exe (PID: 6900)
- WMIC.exe (PID: 8512)
- WMIC.exe (PID: 3092)
- WMIC.exe (PID: 7448)
Process checks computer location settings
- 7zFM.exe (PID: 8428)
- S500RAT.exe (PID: 5808)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Reads the machine GUID from the registry
- 7zFM.exe (PID: 8428)
- Crack.exe (PID: 2912)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- csc.exe (PID: 9296)
- svchost.exe (PID: 2336)
- rar.exe (PID: 8088)
Launching a file from the Downloads directory
- msedge.exe (PID: 7788)
Creates files in the program directory
- 7z2501-x64.exe (PID: 6332)
- dllhost.exe (PID: 7652)
There is functionality for taking screenshot (YARA)
- S500RAT.exe (PID: 5808)
Disables trace logs
- Crack.exe (PID: 2912)
- cmstp.exe (PID: 8552)
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 8552)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 3404)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 3096)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 4828)
- powershell.exe (PID: 9704)
- powershell.exe (PID: 9316)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 8488)
- powershell.exe (PID: 2684)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 3404)
- powershell.exe (PID: 3552)
- powershell.exe (PID: 3096)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 4828)
- powershell.exe (PID: 9704)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 9208)
- powershell.exe (PID: 9316)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 8488)
- powershell.exe (PID: 2684)
Creates files or folders in the user directory
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Launching a file from a Registry key
- Crack.exe (PID: 5516)
- WUDFHo.exe (PID: 5260)
- svchost.exe (PID: 2336)
Reads Internet Explorer settings
- mshta.exe (PID: 8996)
Search a value from a registry key
- cmd.exe (PID: 9428)
- reg.exe (PID: 9632)
The Powershell gets current clipboard
- powershell.exe (PID: 9244)
Checks the directory tree
- tree.com (PID: 9544)
- tree.com (PID: 10068)
- tree.com (PID: 2872)
- tree.com (PID: 9520)
- tree.com (PID: 9112)
- tree.com (PID: 9388)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 9364)
Launching a file from the Startup directory
- svchost.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
428
Monitored processes
267
Malicious processes
17
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=16 --always-read-main-dll --field-trial-handle=6448,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6464 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3628,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 412 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-ItemPropertyValue -Path 'HKLM:SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform' -Name BackupProductKeyDefault" | C:\Windows\System32\cmd.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=10064,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=10040 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=9640,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=8700,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7656 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=9432,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=9904 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7308,i,15715711659173336276,10101492031935264947,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7460 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1040 | powershell Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
136 043
Read events
135 946
Write events
93
Delete events
4
Modification events
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path64 |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path64 |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {23170F69-40C1-278A-1000-000100020000} |
Value: 7-Zip Shell Extension | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {23170F69-40C1-278A-1000-000100020000} |
Value: 7-Zip Shell Extension | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\7zFM.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (6332) 7z2501-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7-Zip |
| Operation: | write | Name: | DisplayName |
Value: 7-Zip 25.01 (x64) | |||
Executable files
182
Suspicious files
828
Text files
607
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5002.TMP | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5002.TMP | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5002.TMP | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5012.TMP | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5012.TMP | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e5012.TMP | — | |
MD5:— | SHA256:— | |||
| 7788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 226
TCP/UDP connections
333
DNS requests
422
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8412 | msedge.exe | GET | 302 | 104.17.147.83:443 | https://www.mediafire.com/cdn-cgi/challenge-platform/scripts/jsd/main.js | US | — | — | unknown |
8412 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:0N__MuD-dd8vrQ6wMBejMy7qkUuAWq39EoFq31LldIU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
8412 | msedge.exe | GET | 200 | 52.123.224.66:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.47 Kb | whitelisted |
8412 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
8412 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
8412 | msedge.exe | GET | 200 | 104.17.147.83:443 | https://www.mediafire.com/download/5mgw38zntc5ia78/S500RAT.rar | US | html | 325 Kb | unknown |
8412 | msedge.exe | GET | 200 | 104.21.42.32:443 | https://cmp.gatekeeperconsent.com/min.js | US | text | 1.03 Kb | unknown |
8412 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
8412 | msedge.exe | GET | 200 | 172.67.199.186:443 | https://the.gatekeeperconsent.com/cmp.min.js | US | text | 7.71 Kb | unknown |
8412 | msedge.exe | GET | 200 | 142.251.127.97:443 | https://www.googletagmanager.com/gtag/js?id=UA-829541-1 | US | text | 295 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7428 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5520 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8412 | msedge.exe | 52.123.224.66:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8412 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8412 | msedge.exe | 104.17.147.83:443 | www.mediafire.com | CLOUDFLARENET | US | whitelisted |
8412 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8412 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cmp.gatekeeperconsent.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8412 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
8412 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
8412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
8412 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |