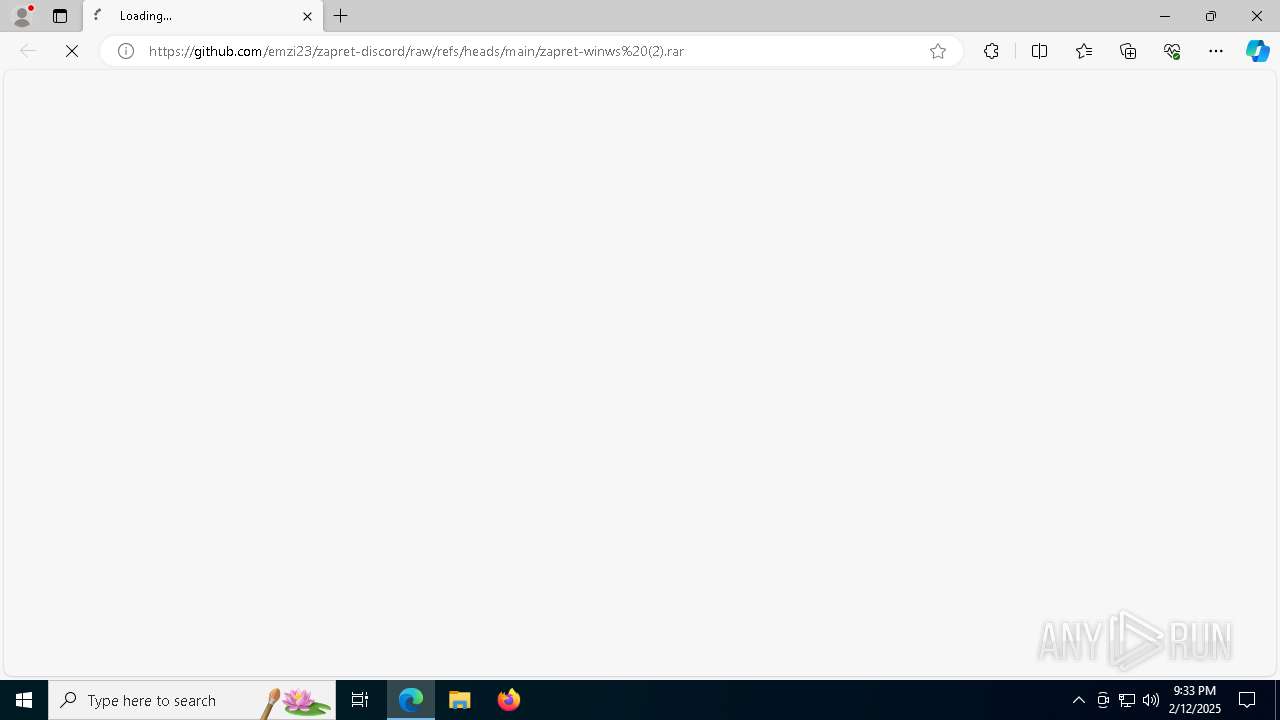
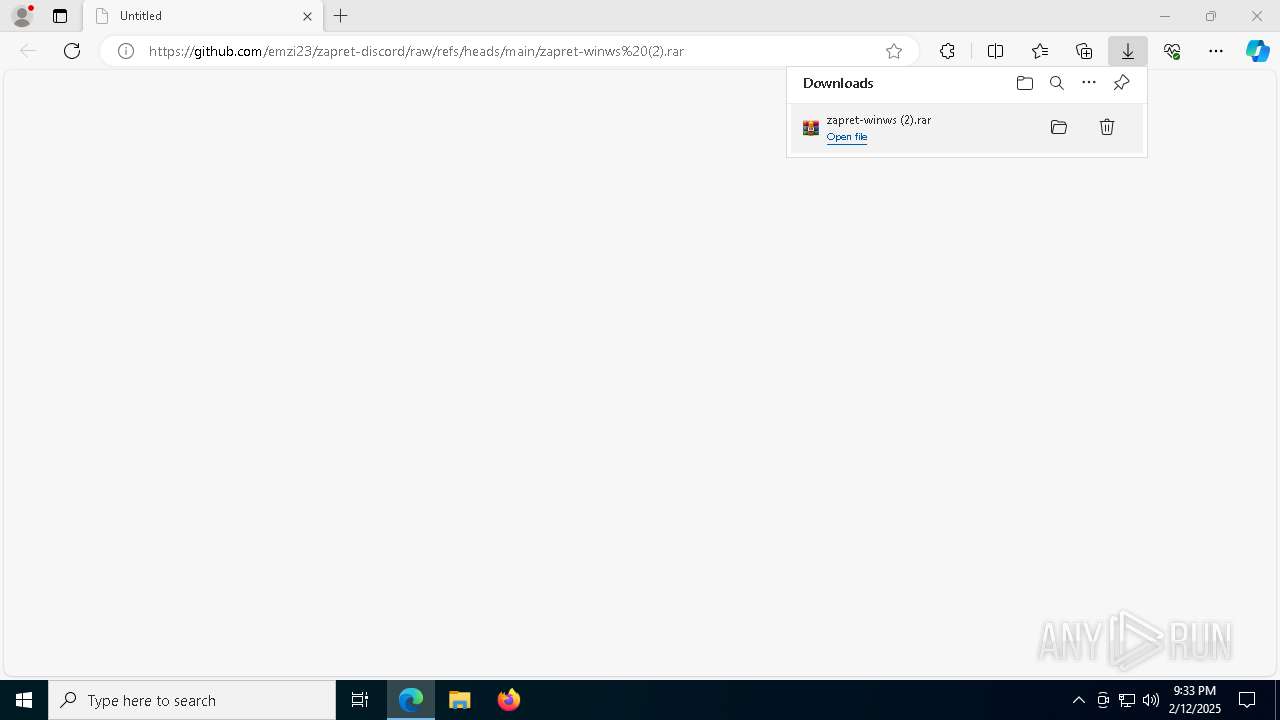
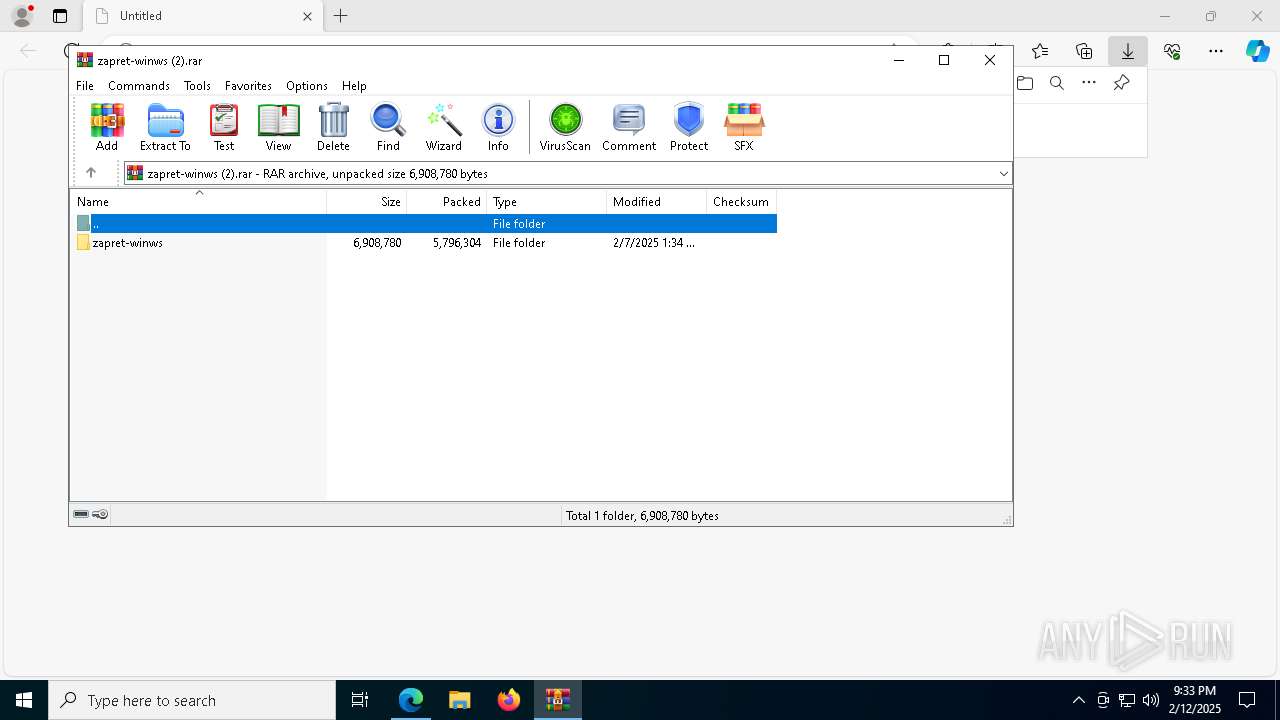
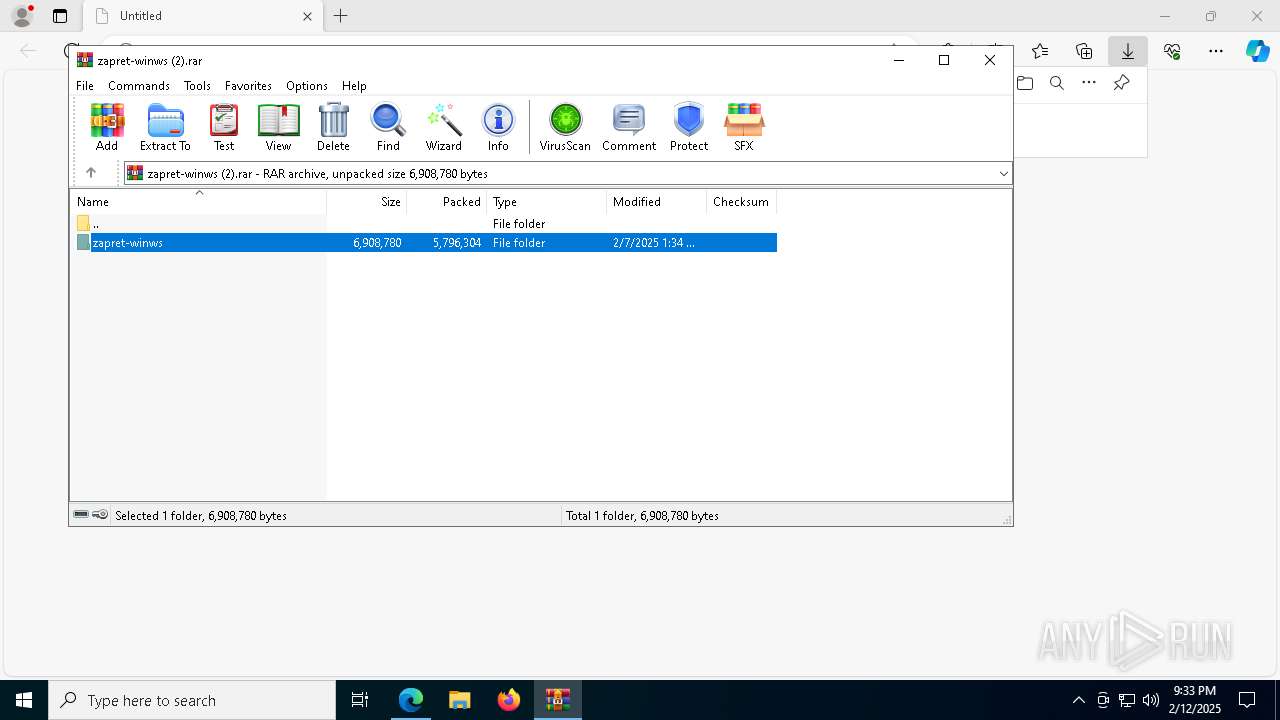
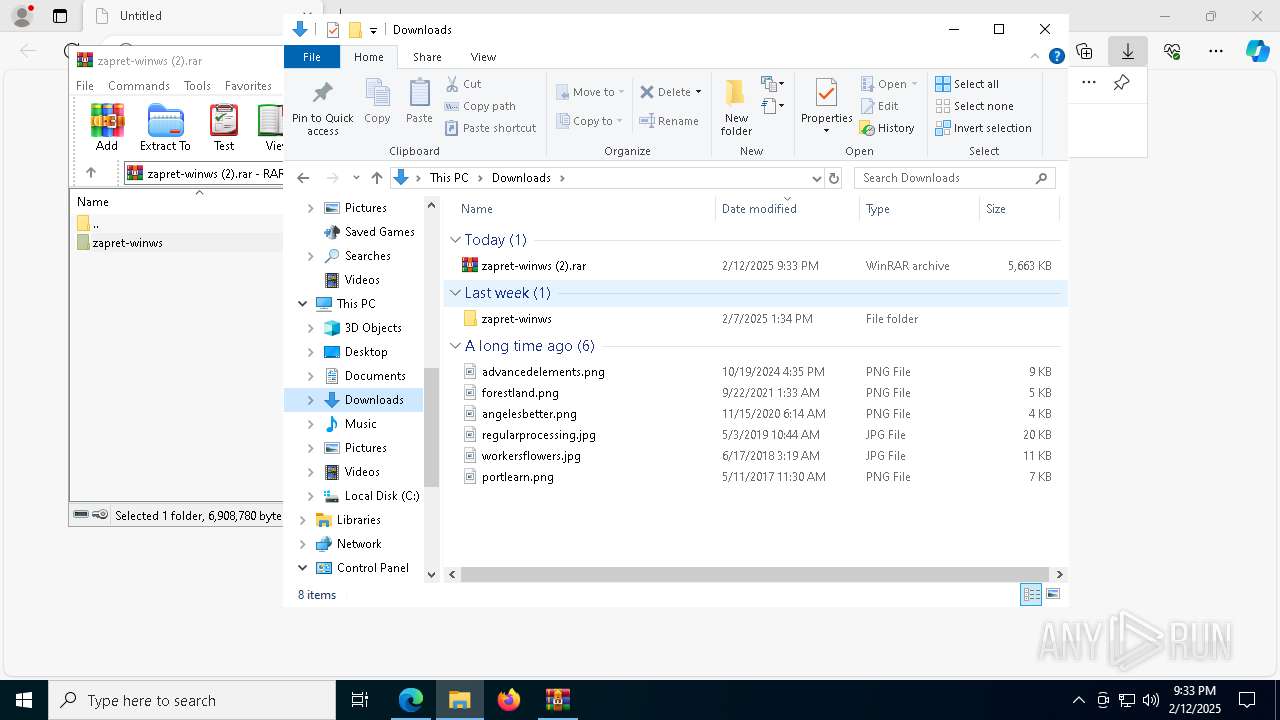
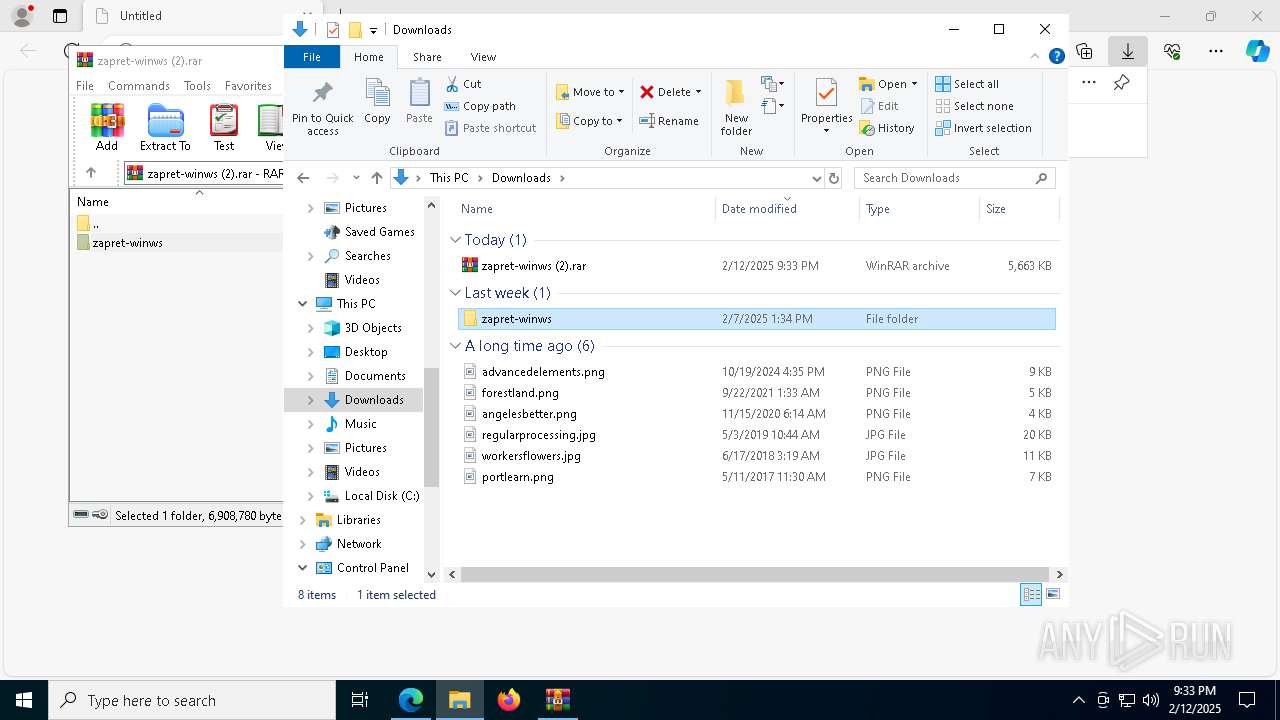
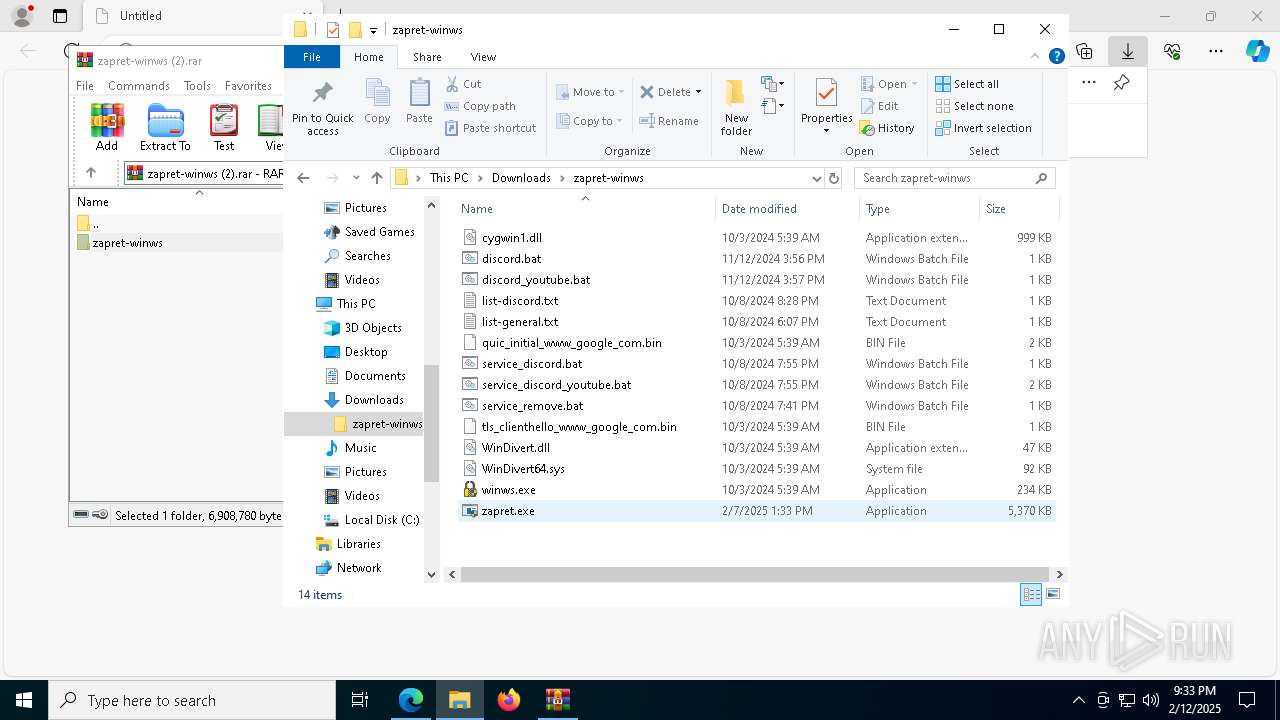
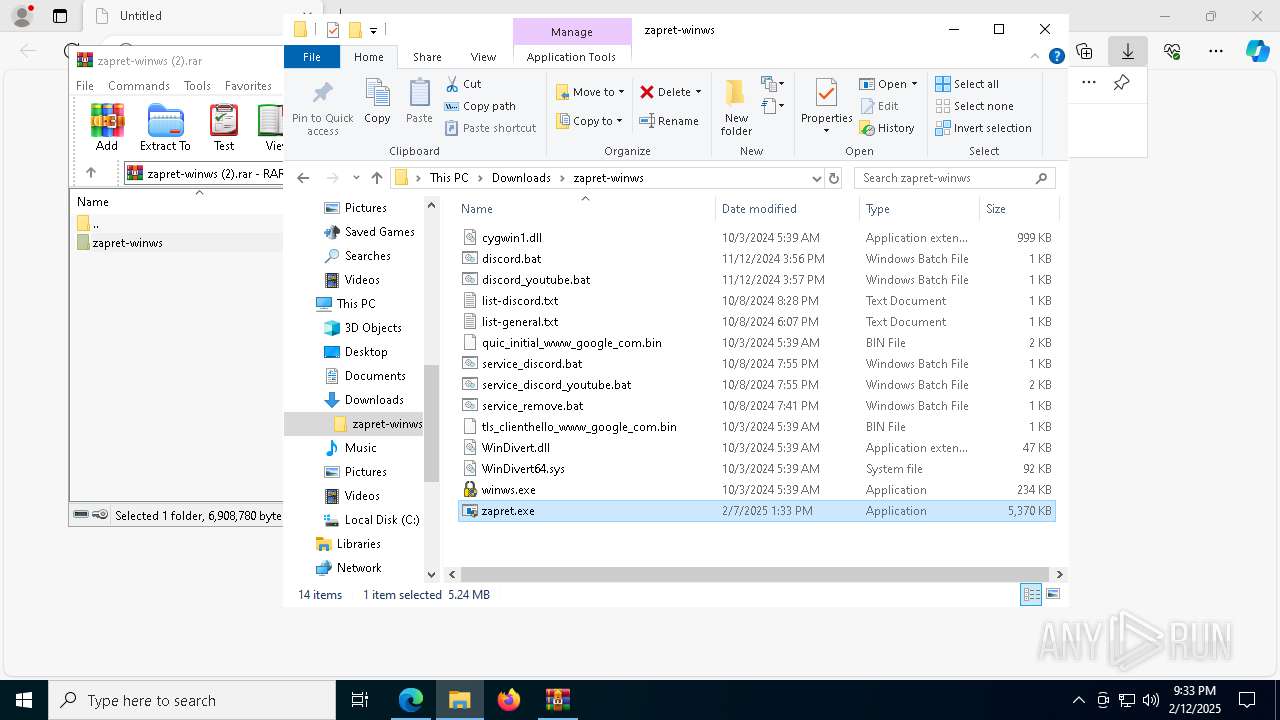
| URL: | https://github.com/emzi23/zapret-discord/raw/refs/heads/main/zapret-winws%20(2).rar |
| Full analysis: | https://app.any.run/tasks/708356e7-8ee7-4de3-adf4-bc904fde083c |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
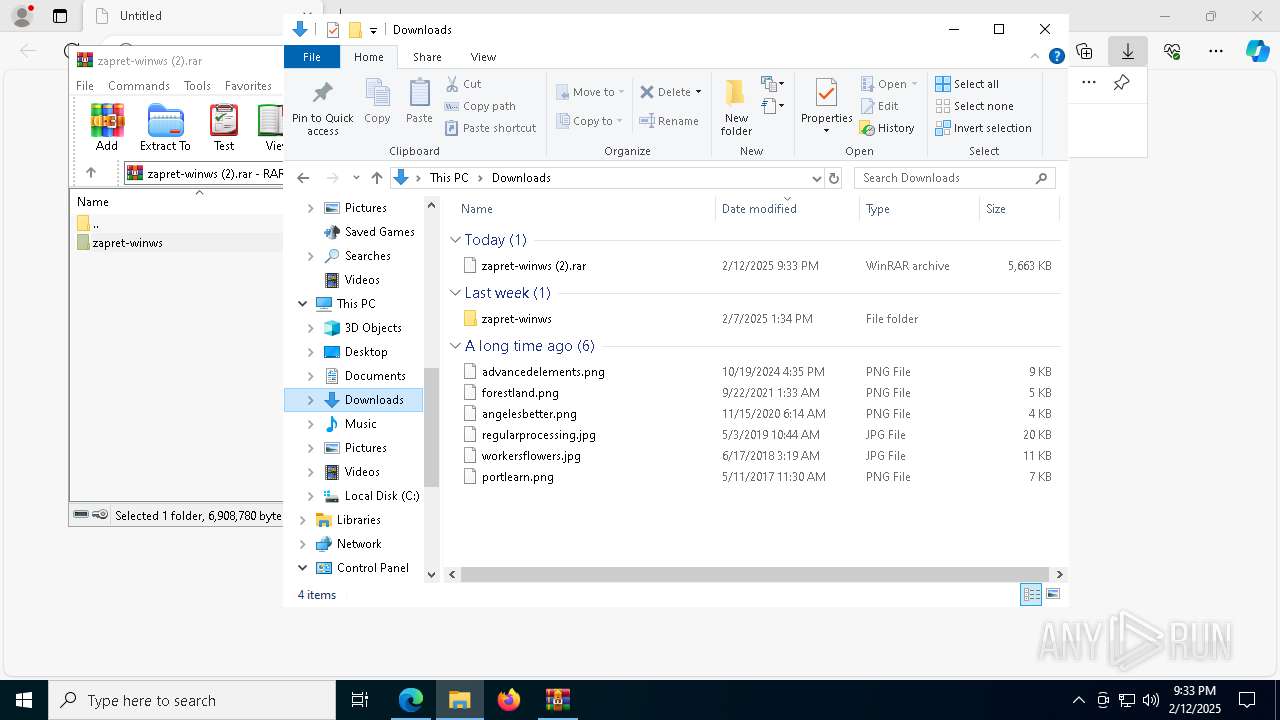
| Analysis date: | February 12, 2025, 21:33:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6A774EF382BBA767FED9D05CD409CFBD |
| SHA1: | CB4E4FB29005DD336B2A159027870B80E1E28F5C |
| SHA256: | 7E6EF57D63B9287193DA2ED28EB4EC4B6BB9E22BF11B8C07BF1F13F6181107E7 |
| SSDEEP: | 3:N8tEdwuX0d8tRLNKsyULa38EXn:2umM0daRLNKpSatn |
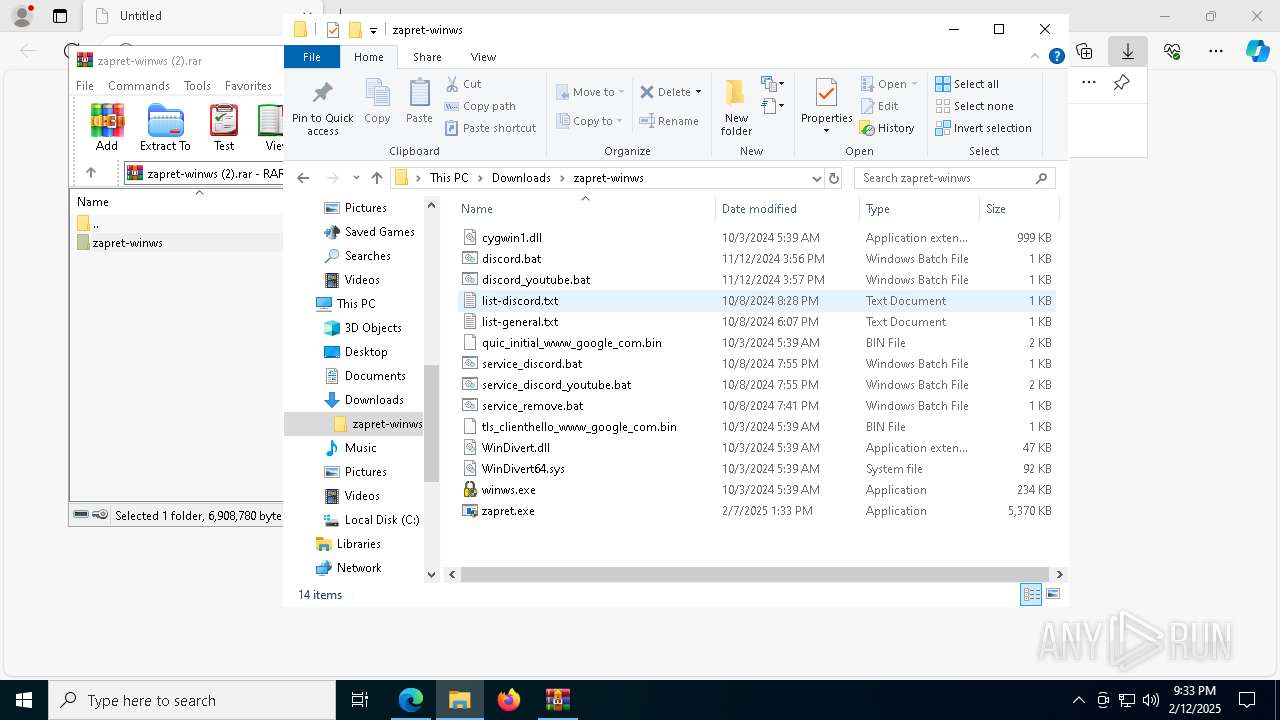
MALICIOUS
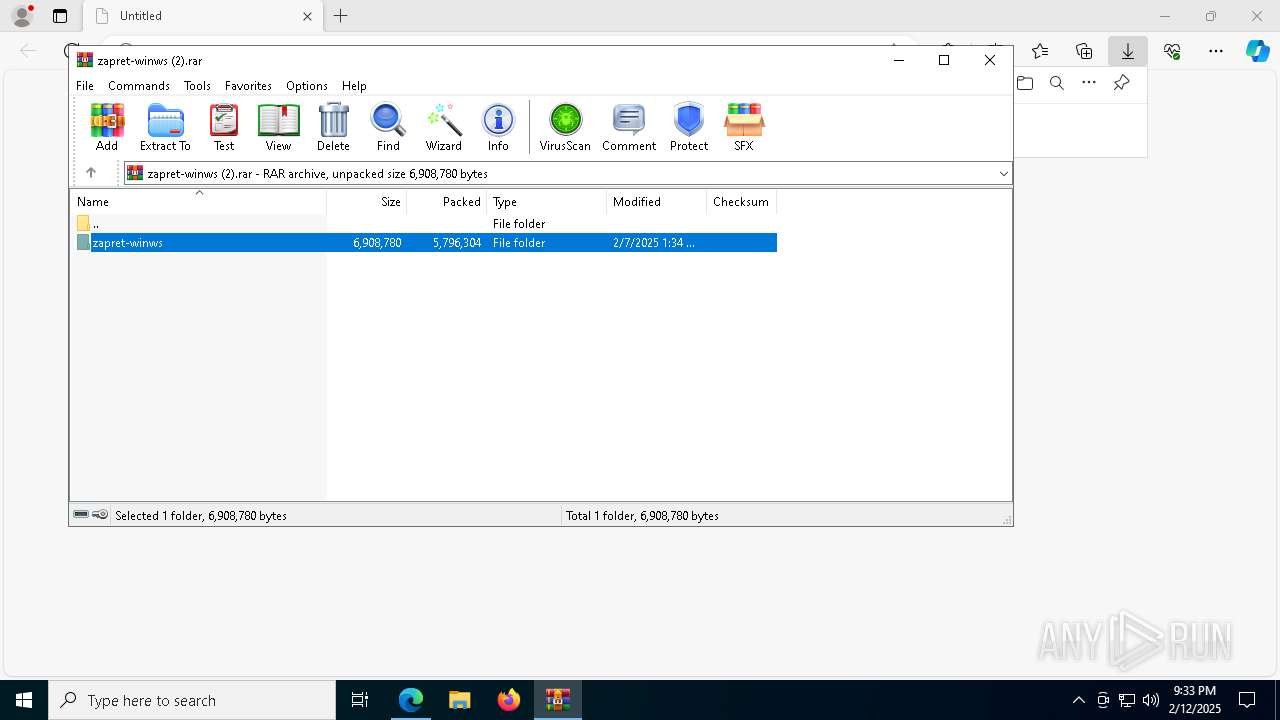
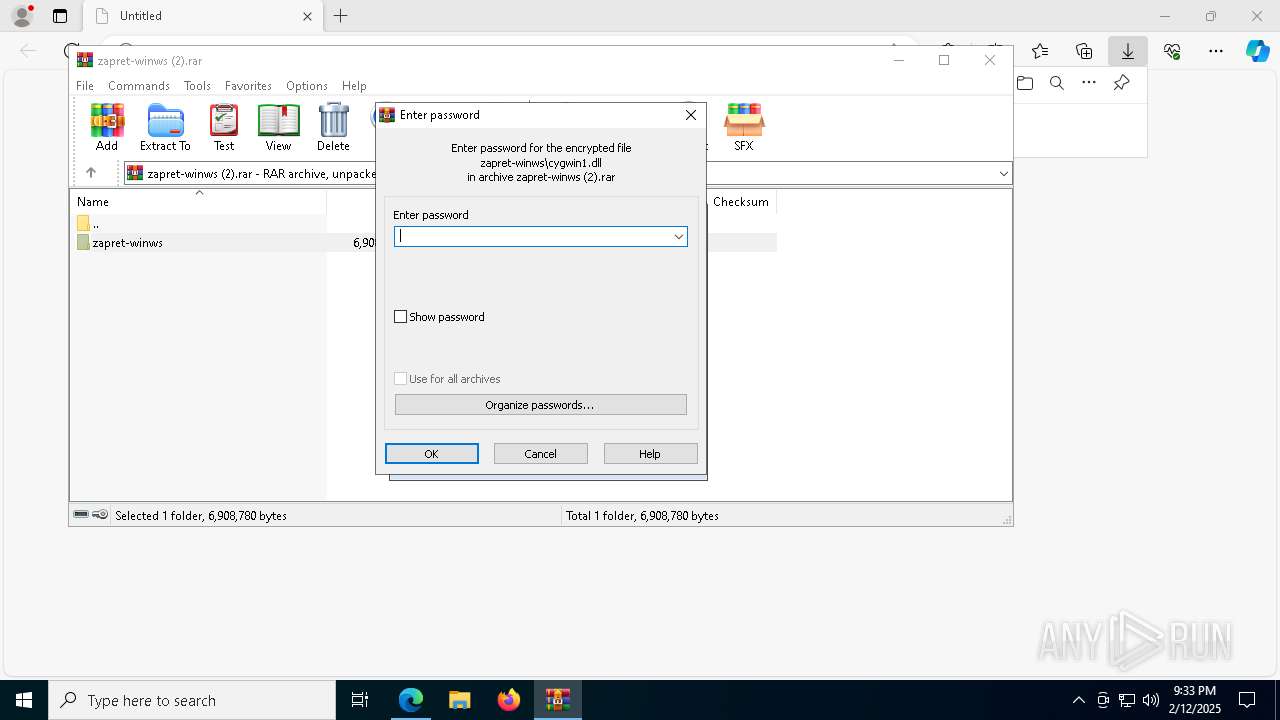
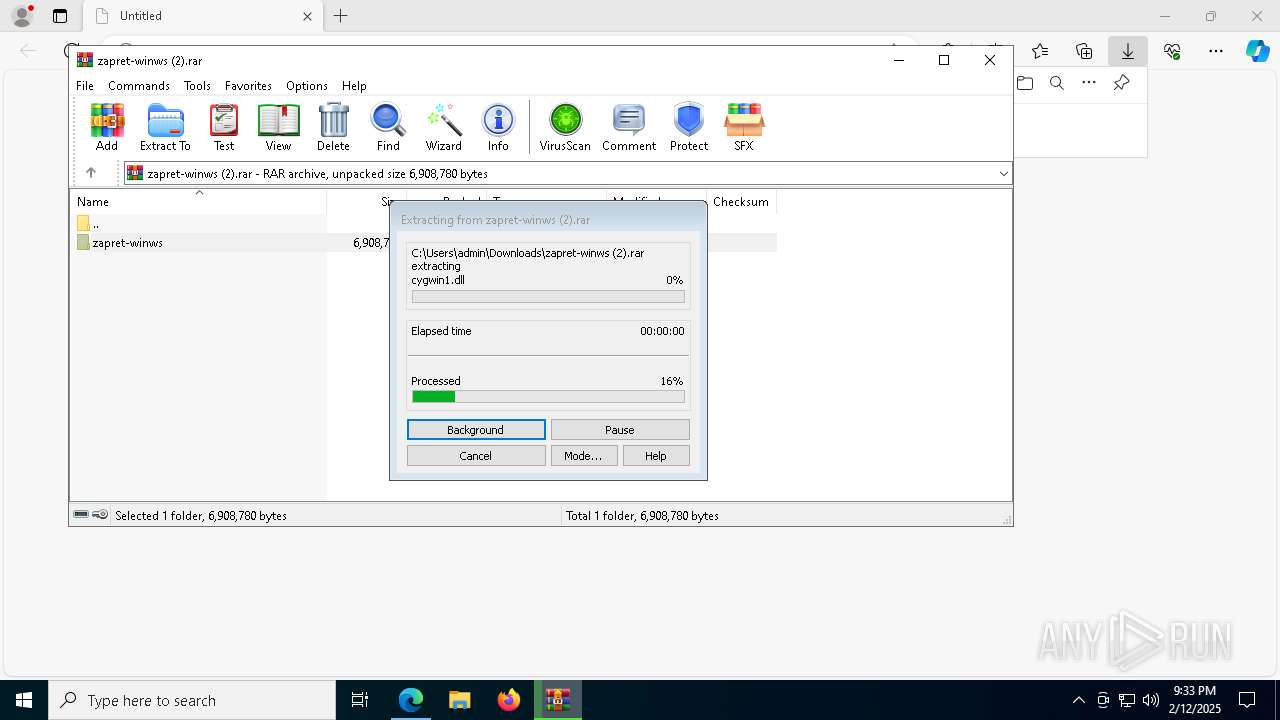
Detects Cygwin installation
- WinRAR.exe (PID: 7984)
Executing a file with an untrusted certificate
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- updater.exe (PID: 3568)
Adds extension to the Windows Defender exclusion list
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- dialer.exe (PID: 6192)
- updater.exe (PID: 3568)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 1296)
- cmd.exe (PID: 7500)
Application was injected by another process
- svchost.exe (PID: 1068)
- winlogon.exe (PID: 684)
- lsass.exe (PID: 760)
- svchost.exe (PID: 320)
- svchost.exe (PID: 1260)
- svchost.exe (PID: 1276)
- svchost.exe (PID: 1268)
- svchost.exe (PID: 1452)
- svchost.exe (PID: 1316)
- svchost.exe (PID: 1776)
- svchost.exe (PID: 1364)
- svchost.exe (PID: 1424)
- svchost.exe (PID: 1500)
- svchost.exe (PID: 1768)
- svchost.exe (PID: 1660)
- svchost.exe (PID: 1564)
- svchost.exe (PID: 1784)
- svchost.exe (PID: 1908)
- svchost.exe (PID: 1880)
- dwm.exe (PID: 912)
- svchost.exe (PID: 1972)
- svchost.exe (PID: 2360)
- svchost.exe (PID: 2272)
- svchost.exe (PID: 1980)
- svchost.exe (PID: 2364)
- svchost.exe (PID: 2192)
- svchost.exe (PID: 2340)
- svchost.exe (PID: 2372)
- svchost.exe (PID: 2500)
- spoolsv.exe (PID: 2652)
- svchost.exe (PID: 2748)
- svchost.exe (PID: 2852)
- OfficeClickToRun.exe (PID: 2884)
- svchost.exe (PID: 2816)
- svchost.exe (PID: 2892)
- svchost.exe (PID: 3016)
- svchost.exe (PID: 2064)
- svchost.exe (PID: 2944)
- svchost.exe (PID: 2288)
- svchost.exe (PID: 2660)
- svchost.exe (PID: 3592)
- svchost.exe (PID: 3164)
- svchost.exe (PID: 3600)
- sihost.exe (PID: 1712)
- svchost.exe (PID: 3160)
- svchost.exe (PID: 2920)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 3704)
- svchost.exe (PID: 4436)
- svchost.exe (PID: 3824)
- dasHost.exe (PID: 3896)
- svchost.exe (PID: 4000)
- RuntimeBroker.exe (PID: 4676)
- RuntimeBroker.exe (PID: 4960)
- dllhost.exe (PID: 5904)
- RuntimeBroker.exe (PID: 5820)
- ApplicationFrameHost.exe (PID: 6108)
- UserOOBEBroker.exe (PID: 3004)
- svchost.exe (PID: 2952)
- svchost.exe (PID: 4176)
- explorer.exe (PID: 4488)
- ctfmon.exe (PID: 4268)
- svchost.exe (PID: 4168)
- svchost.exe (PID: 3668)
- svchost.exe (PID: 4696)
- dllhost.exe (PID: 5164)
- svchost.exe (PID: 3976)
- svchost.exe (PID: 4456)
- svchost.exe (PID: 1340)
- uhssvc.exe (PID: 2908)
- svchost.exe (PID: 3056)
- svchost.exe (PID: 812)
- svchost.exe (PID: 2148)
- dllhost.exe (PID: 1816)
- WmiPrvSE.exe (PID: 8140)
- svchost.exe (PID: 376)
- WmiPrvSE.exe (PID: 5472)
- svchost.exe (PID: 1176)
- svchost.exe (PID: 1764)
- svchost.exe (PID: 3052)
- svchost.exe (PID: 1020)
- RuntimeBroker.exe (PID: 2624)
- MoUsoCoreWorker.exe (PID: 4712)
- svchost.exe (PID: 4200)
- svchost.exe (PID: 6088)
- WerFault.exe (PID: 4228)
- svchost.exe (PID: 7152)
Runs injected code in another process
- dialer.exe (PID: 2800)
- dialer.exe (PID: 5652)
- dialer.exe (PID: 7584)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 7984)
- updater.exe (PID: 2976)
Reads security settings of Internet Explorer
- zapret.exe (PID: 7276)
BASE64 encoded PowerShell command has been detected
- zapret.exe (PID: 7276)
Base64-obfuscated command line is found
- zapret.exe (PID: 7276)
Starts POWERSHELL.EXE for commands execution
- zapret.exe (PID: 7276)
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- updater.exe (PID: 3568)
- dialer.exe (PID: 6192)
Executable content was dropped or overwritten
- zapret.exe (PID: 7276)
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- svchost.exe (PID: 1340)
Manipulates environment variables
- powershell.exe (PID: 7576)
- powershell.exe (PID: 2448)
- powershell.exe (PID: 4864)
- powershell.exe (PID: 5236)
Script adds exclusion path to Windows Defender
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- dialer.exe (PID: 6192)
- updater.exe (PID: 3568)
Script adds exclusion extension to Windows Defender
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- dialer.exe (PID: 6192)
- updater.exe (PID: 3568)
Starts CMD.EXE for commands execution
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- updater.exe (PID: 3568)
Process uninstalls Windows update
- wusa.exe (PID: 7588)
- wusa.exe (PID: 7696)
- wusa.exe (PID: 6176)
Starts SC.EXE for service management
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- updater.exe (PID: 3568)
Stops a currently running service
- sc.exe (PID: 1356)
- sc.exe (PID: 5252)
- sc.exe (PID: 5788)
- sc.exe (PID: 5576)
- sc.exe (PID: 3568)
- sc.exe (PID: 6364)
- sc.exe (PID: 3172)
- sc.exe (PID: 4388)
- sc.exe (PID: 2292)
- sc.exe (PID: 8172)
- sc.exe (PID: 6500)
- sc.exe (PID: 3488)
- sc.exe (PID: 3820)
- sc.exe (PID: 7212)
- sc.exe (PID: 5392)
- sc.exe (PID: 4604)
Creates a new Windows service
- sc.exe (PID: 7044)
Uses powercfg.exe to modify the power settings
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- updater.exe (PID: 3568)
Windows service management via SC.EXE
- sc.exe (PID: 2292)
- sc.exe (PID: 8188)
Executes as Windows Service
- updater.exe (PID: 2976)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2192)
Executes application which crashes
- updater.exe (PID: 2976)
INFO
Application launched itself
- msedge.exe (PID: 6220)
Reads the computer name
- identity_helper.exe (PID: 7920)
- zapret.exe (PID: 7276)
Reads the software policy settings
- lsass.exe (PID: 760)
- WerFault.exe (PID: 1792)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6220)
- OfficeClickToRun.exe (PID: 2884)
Reads security settings of Internet Explorer
- RuntimeBroker.exe (PID: 2624)
- explorer.exe (PID: 4488)
Reads Environment values
- identity_helper.exe (PID: 7920)
Checks supported languages
- identity_helper.exe (PID: 7920)
- zapret.exe (PID: 7276)
- zapret.exe (PID: 7456)
- updater.exe (PID: 2976)
- updater.exe (PID: 3568)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7984)
- msedge.exe (PID: 4520)
The sample compiled with english language support
- WinRAR.exe (PID: 7984)
- svchost.exe (PID: 1340)
- msedge.exe (PID: 4520)
Reads the time zone
- WmiPrvSE.exe (PID: 5472)
- svchost.exe (PID: 2816)
Manual execution by a user
- zapret.exe (PID: 1576)
- zapret.exe (PID: 7276)
Process checks computer location settings
- zapret.exe (PID: 7276)
Create files in a temporary directory
- zapret.exe (PID: 7276)
- svchost.exe (PID: 6088)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7452)
- powershell.exe (PID: 7576)
- powershell.exe (PID: 2448)
- powershell.exe (PID: 4864)
- powershell.exe (PID: 5236)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7452)
- powershell.exe (PID: 7576)
- powershell.exe (PID: 2448)
- powershell.exe (PID: 4864)
- powershell.exe (PID: 5236)
Creates files in the program directory
- zapret.exe (PID: 7456)
- MoUsoCoreWorker.exe (PID: 4712)
- svchost.exe (PID: 7152)
The sample compiled with japanese language support
- updater.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
276
Monitored processes
230
Malicious processes
94
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s WdiSystemHost | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | C:\WINDOWS\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s StorSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7948 --field-trial-handle=2412,i,3683013539102897493,12532276450882733451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 912 | "dwm.exe" | C:\Windows\System32\dwm.exe | winlogon.exe | ||||||||||||
User: DWM-1 Company: Microsoft Corporation Integrity Level: SYSTEM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5356 --field-trial-handle=2412,i,3683013539102897493,12532276450882733451,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
74 336
Read events
73 664
Write events
442
Delete events
230
Modification events
| (PID) Process: | (6220) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6220) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6220) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6220) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3976) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\Orchestrator |
| Operation: | write | Name: | Preshutdown |
Value: 0 | |||
| (PID) Process: | (6220) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 597C82F88E8C2F00 | |||
| (PID) Process: | (4712) MoUsoCoreWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsUpdate\Orchestrator |
| Operation: | delete value | Name: | EnhancedShutdownEnabled |
Value: | |||
| (PID) Process: | (4712) MoUsoCoreWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsUpdate\Orchestrator |
| Operation: | write | Name: | ShutdownFlyoutOptions |
Value: 0 | |||
| (PID) Process: | (4712) MoUsoCoreWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Wosc\Client\Persistent\ClientState\FCON |
| Operation: | write | Name: | ETag |
Value: "39929200:054BDF00DCCFDEBE87A180CAB84F81397E68843F417F30B0CA27C37AB3A7B392CA185DEDEDC8247B0A79ABFE4BB43B27875DCB4BA978EAFA89BDD333A41CBA448E3320B5CCC79838565926C25C7F9965AD6330E1D187A45720A18082A44C5394E18E8340D5CD6B5C8463739004FAB91B7ACF082E923DA3D48648F0C81B0285664985791894C6C9D6BB3863252B08A6DA768B54F7DE18108551FEA8853B905C5F2A73A08C89879833B2D0DAEF6B0718CD706FF5DDF0CDD59D2B2198858D89C6D1CFE975B95D98D161C8A46E37DE6D6D6E0576EC467D56A5A1:2F20687AEE" | |||
| (PID) Process: | (4712) MoUsoCoreWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Wosc\Client\Persistent\ClientState\FCON |
| Operation: | delete value | Name: | ETagBackup |
Value: | |||
Executable files
28
Suspicious files
593
Text files
116
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136cf6.TMP | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136d05.TMP | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:C7E2197BAE099B13BBB3ADEB1433487D | SHA256:3460EEAF45D581DD43A6E4E17AF8102DDAFF5AEAA88B10099527CF85211629E9 | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136d44.TMP | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:1AF1D1ED27A40F9FDA977B6C353EC48B | SHA256:01B66ED195749BF7909E0B655A6C4C6AFDECD665D7304653D09CD538191CC50A | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136d53.TMP | — | |
MD5:— | SHA256:— | |||
| 6220 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
69
DNS requests
58
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.50:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3984 | svchost.exe | GET | 200 | 23.48.23.50:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.85.144.229:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3984 | svchost.exe | GET | 200 | 184.85.144.229:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3688 | SIHClient.exe | GET | 200 | 184.85.144.229:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3688 | SIHClient.exe | GET | 200 | 184.85.144.229:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.56.216:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6088 | svchost.exe | HEAD | 200 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739810277&P2=404&P3=2&P4=gVw%2fGiQHQK4IN0OgDt6TFREEcmKF5Ev%2f%2fDfFc9%2fLCVtvWFjg6LMlfIUIAgYdw2Vrkymwb6H1nkjWVGN4u1KwbA%3d%3d | unknown | — | — | whitelisted |
7652 | backgroundTaskHost.exe | GET | 200 | 23.52.56.216:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739810277&P2=404&P3=2&P4=gVw%2fGiQHQK4IN0OgDt6TFREEcmKF5Ev%2f%2fDfFc9%2fLCVtvWFjg6LMlfIUIAgYdw2Vrkymwb6H1nkjWVGN4u1KwbA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 184.86.251.10:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.50:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3984 | svchost.exe | 23.48.23.50:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.85.144.229:80 | www.microsoft.com | AKAMAI-AS | FI | whitelisted |
3984 | svchost.exe | 184.85.144.229:80 | www.microsoft.com | AKAMAI-AS | FI | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2632 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6220 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6616 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |