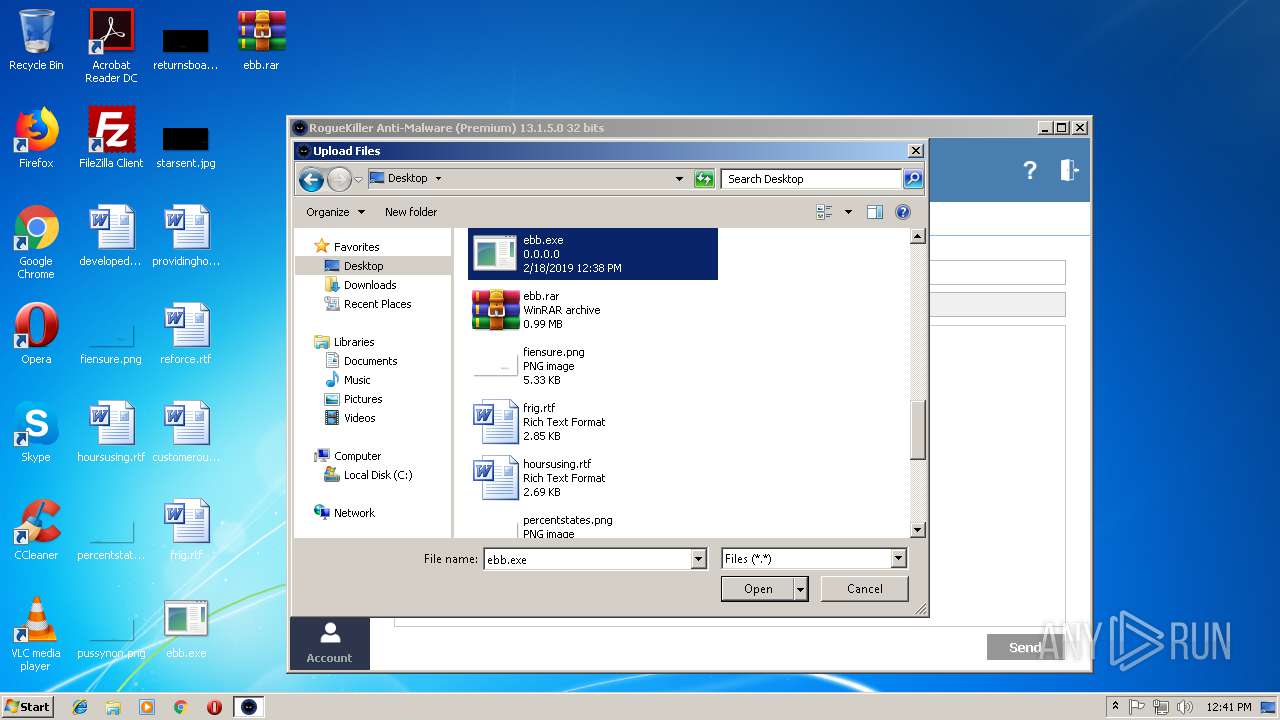
| File name: | ebb.exe |
| Full analysis: | https://app.any.run/tasks/7e98ce97-ca5c-49fc-846b-004d942e57af |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | February 18, 2019, 12:37:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 050CE2A3AD62A87D9D92B3DAD4CB4ED9 |
| SHA1: | BBE54668C71F43D322D66AC779EBE5AE7724B400 |
| SHA256: | 7E34D90D55B98E8CA75DC8B6CA7ED397CDDAF8BE71141A3697AA724328934D14 |
| SSDEEP: | 24576:/AHnh+eWsN3skA4RV1Hom2KXMmHamY0/UO85lIXmnx+6XSQ01kU+VEv5:ih+ZkldoPK8Yamf |
MALICIOUS
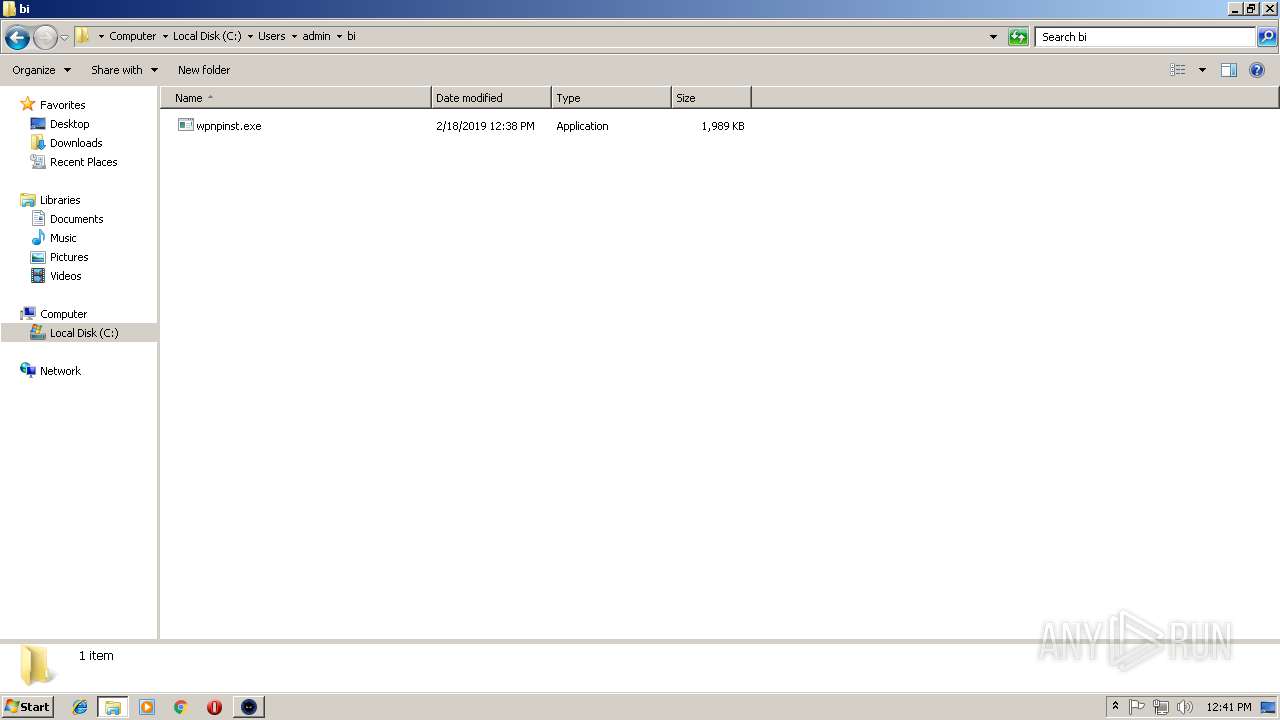
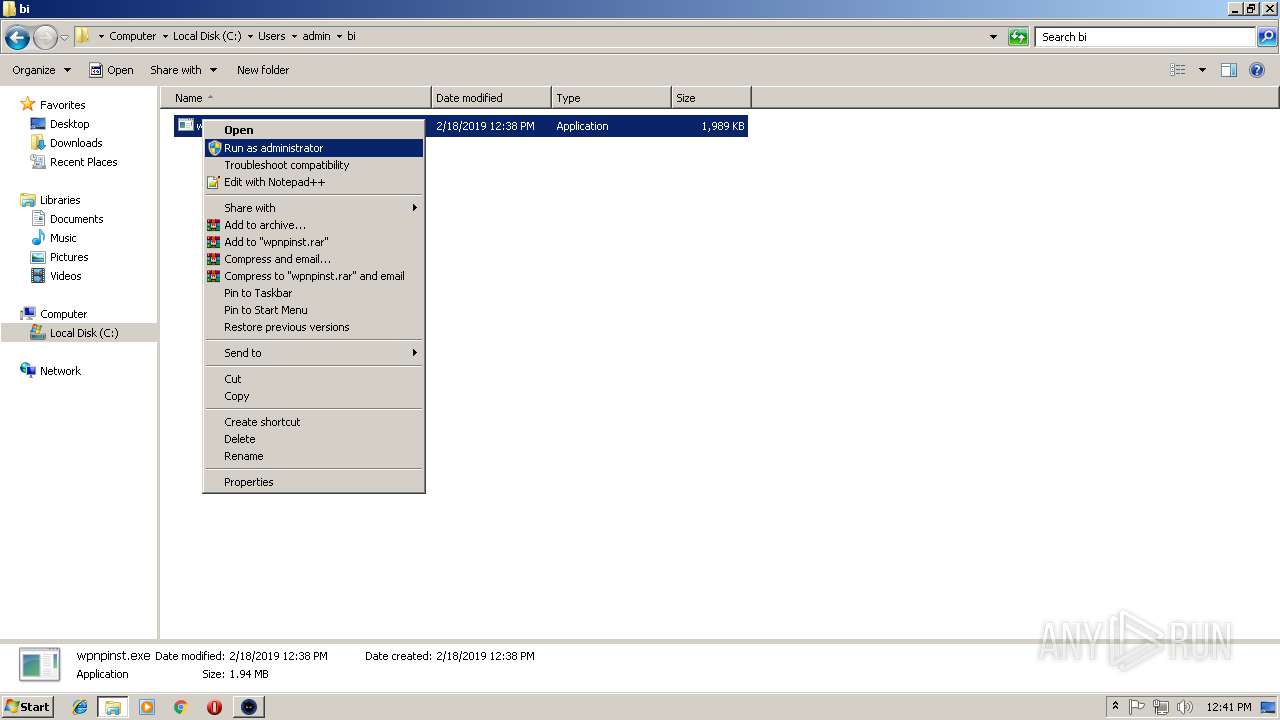
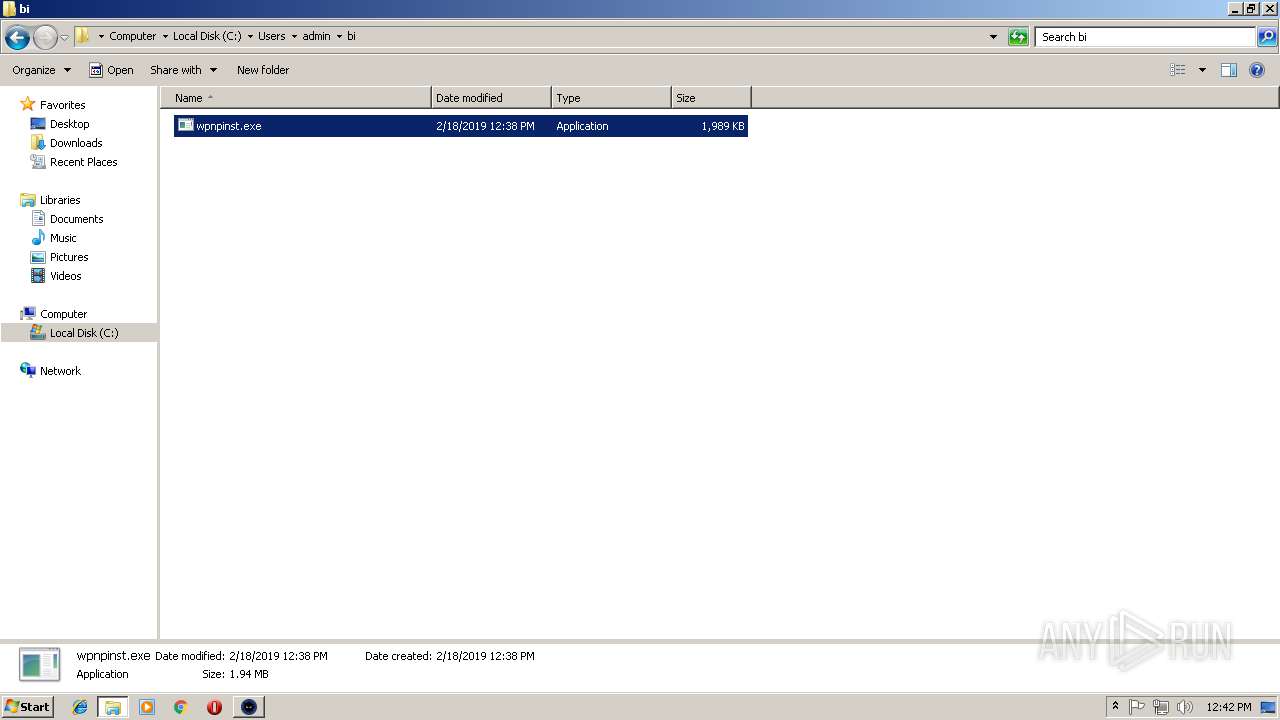
Uses Task Scheduler to run other applications
- ebb.exe (PID: 3680)
- wpnpinst.exe (PID: 3436)
- wpnpinst.exe (PID: 2056)
- wpnpinst.exe (PID: 2820)
- wpnpinst.exe (PID: 2580)
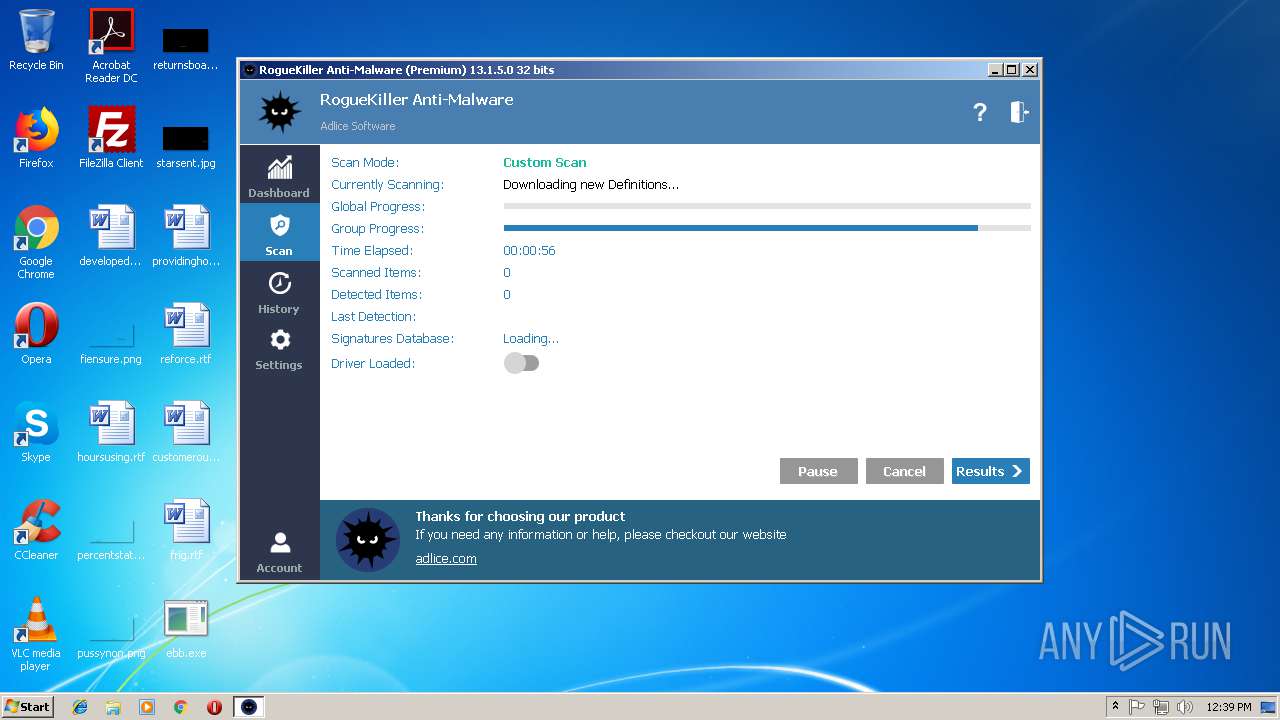
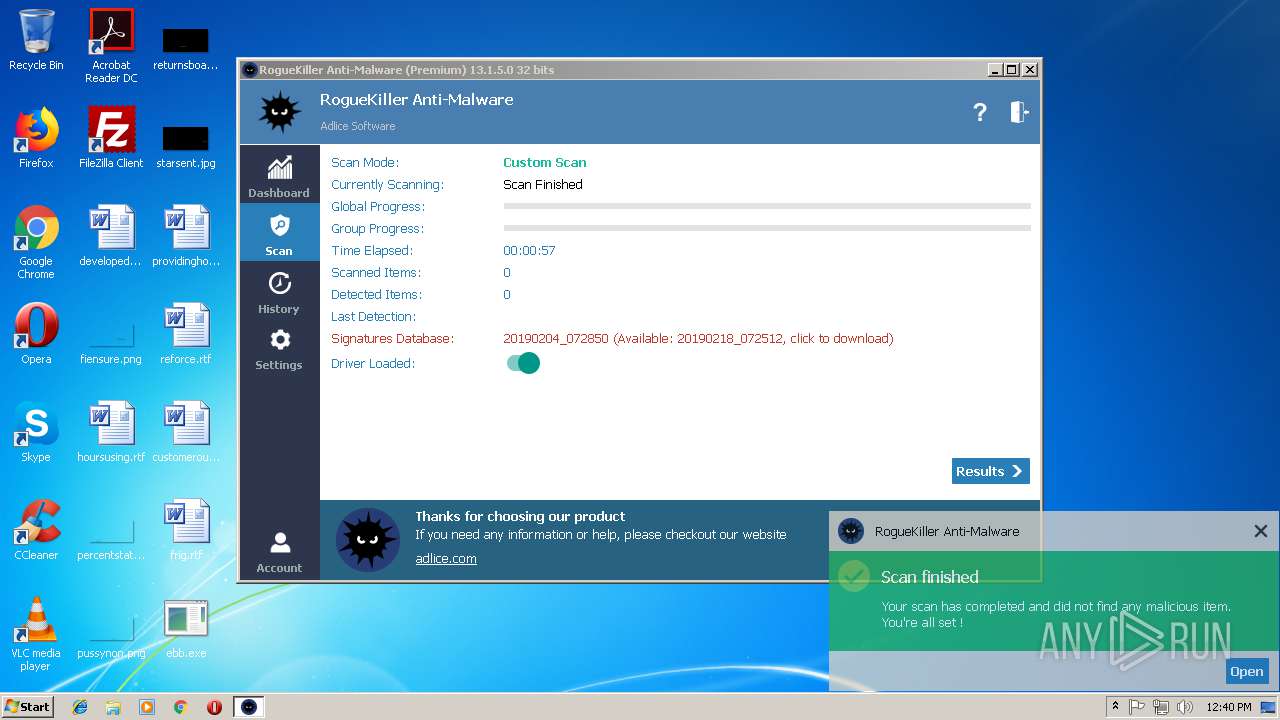
Loads the Task Scheduler COM API
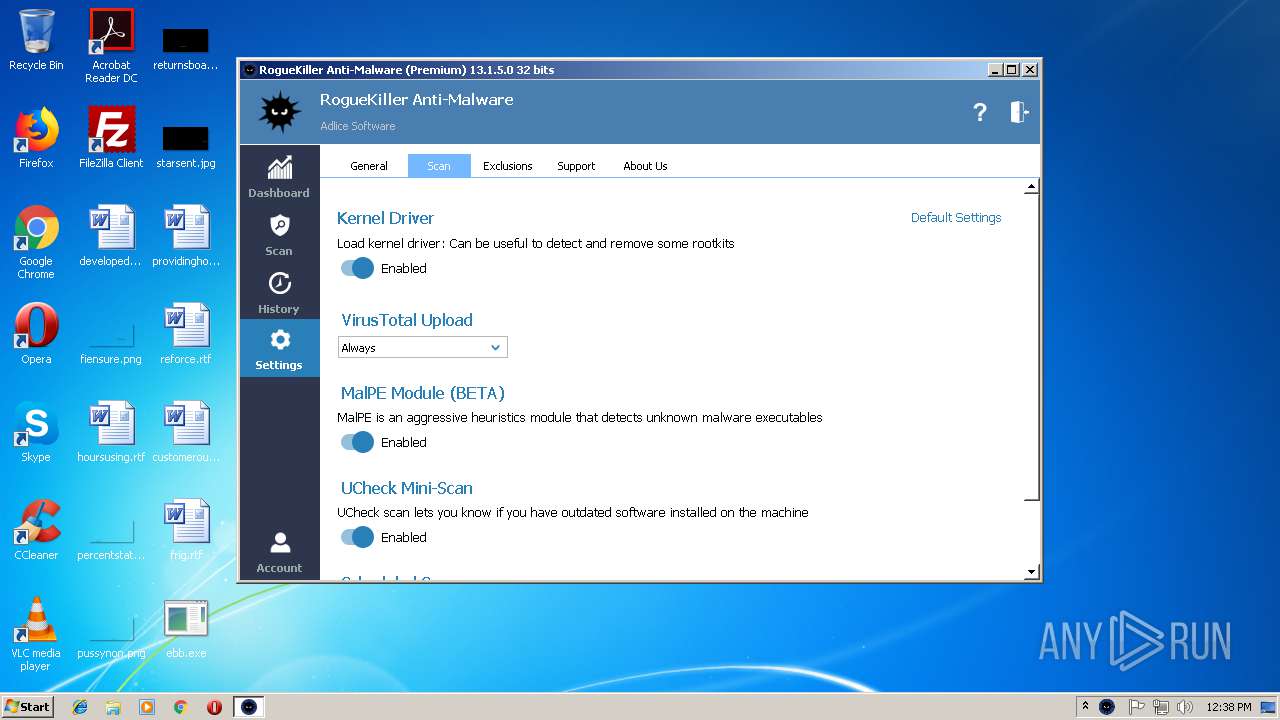
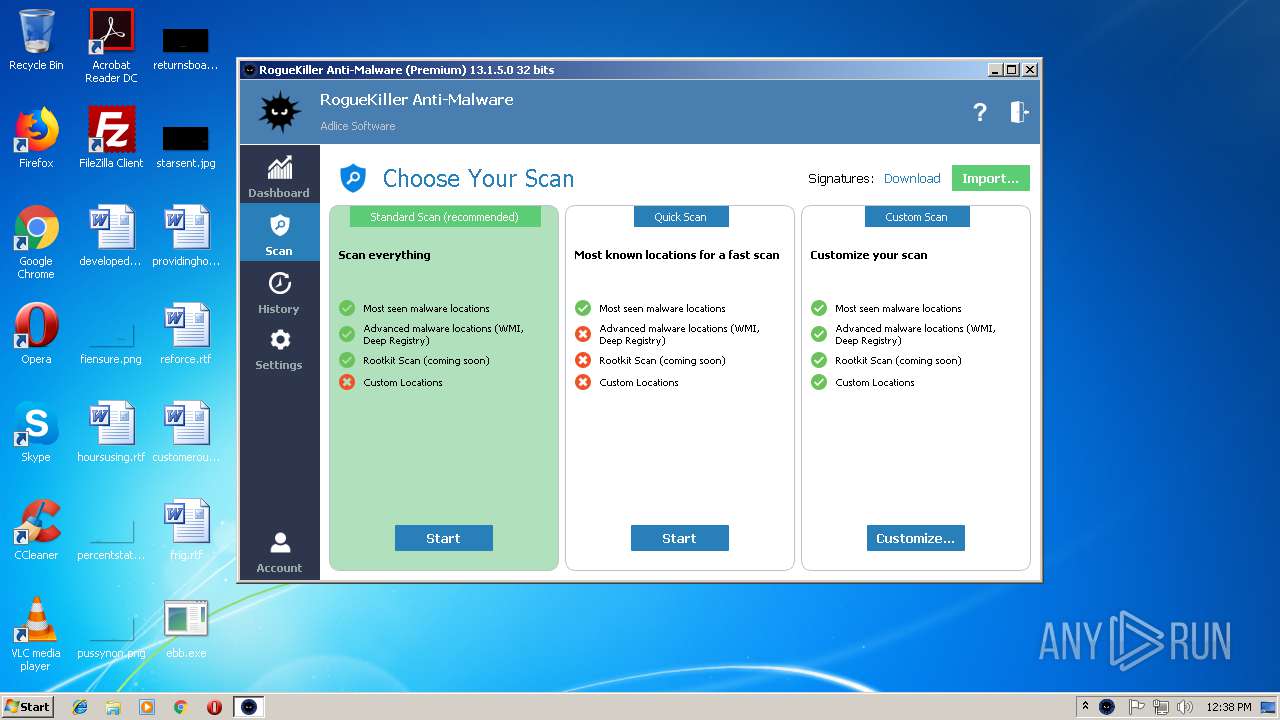
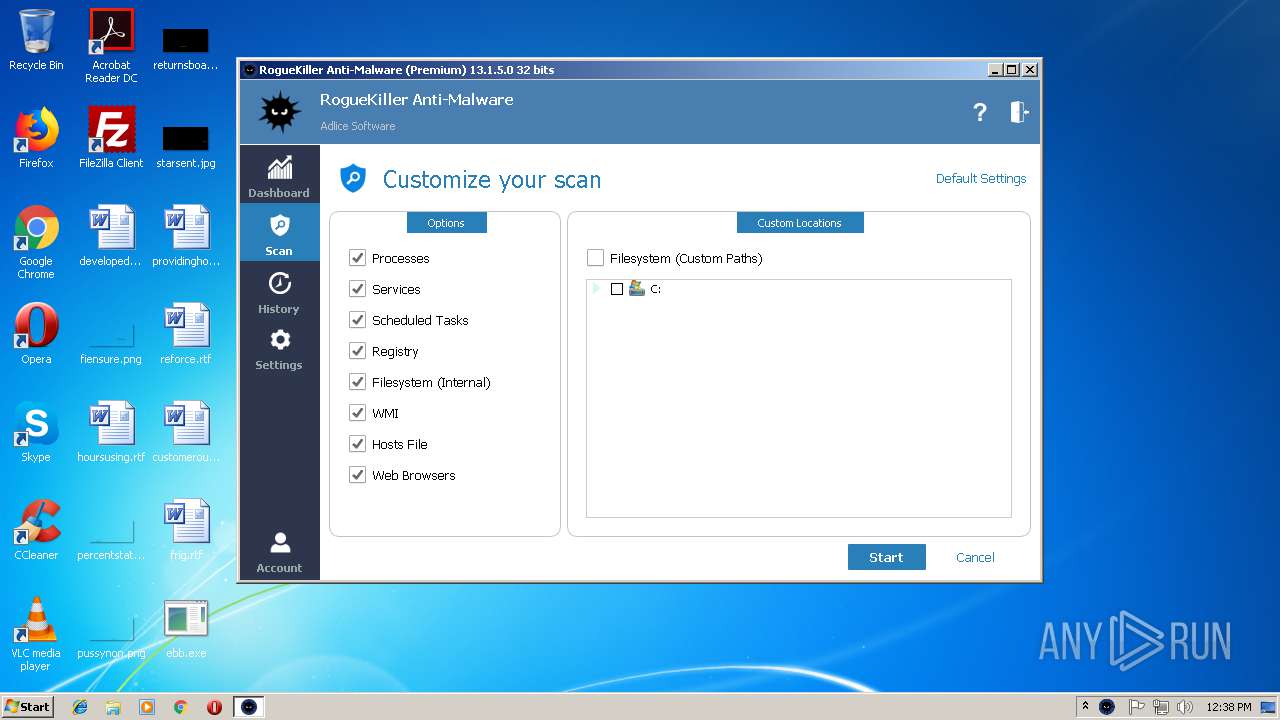
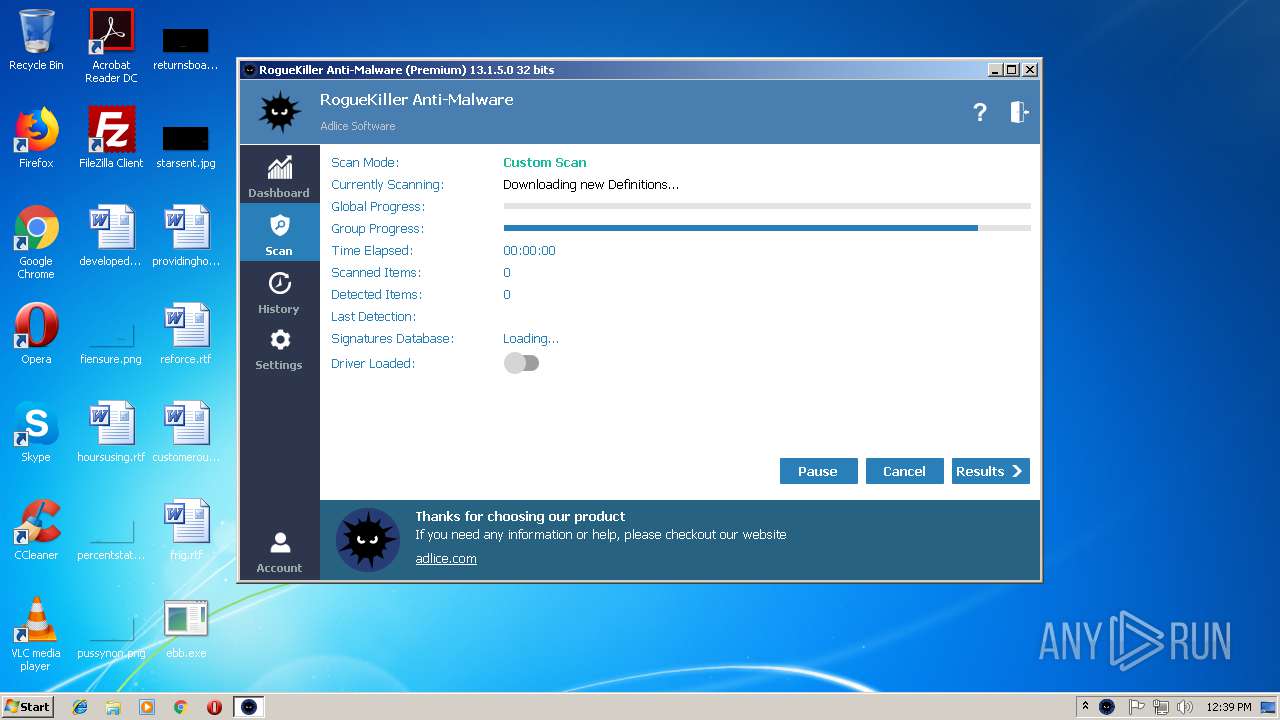
- schtasks.exe (PID: 2476)
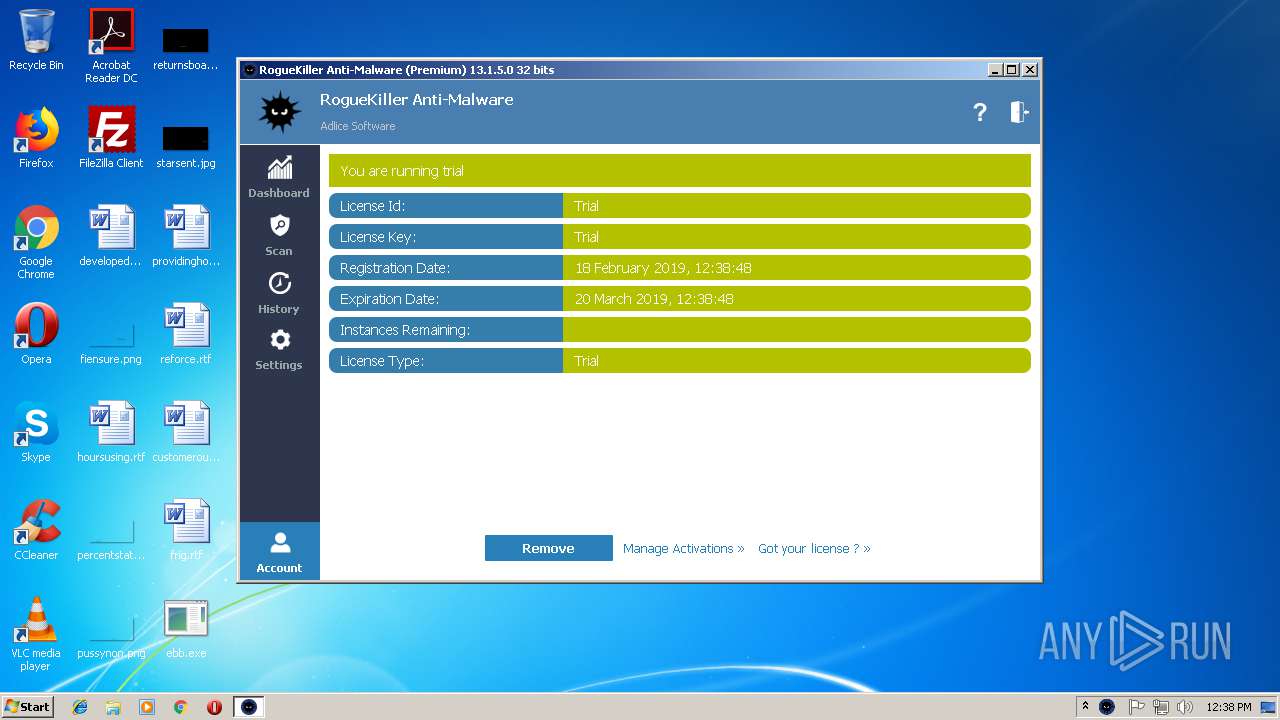
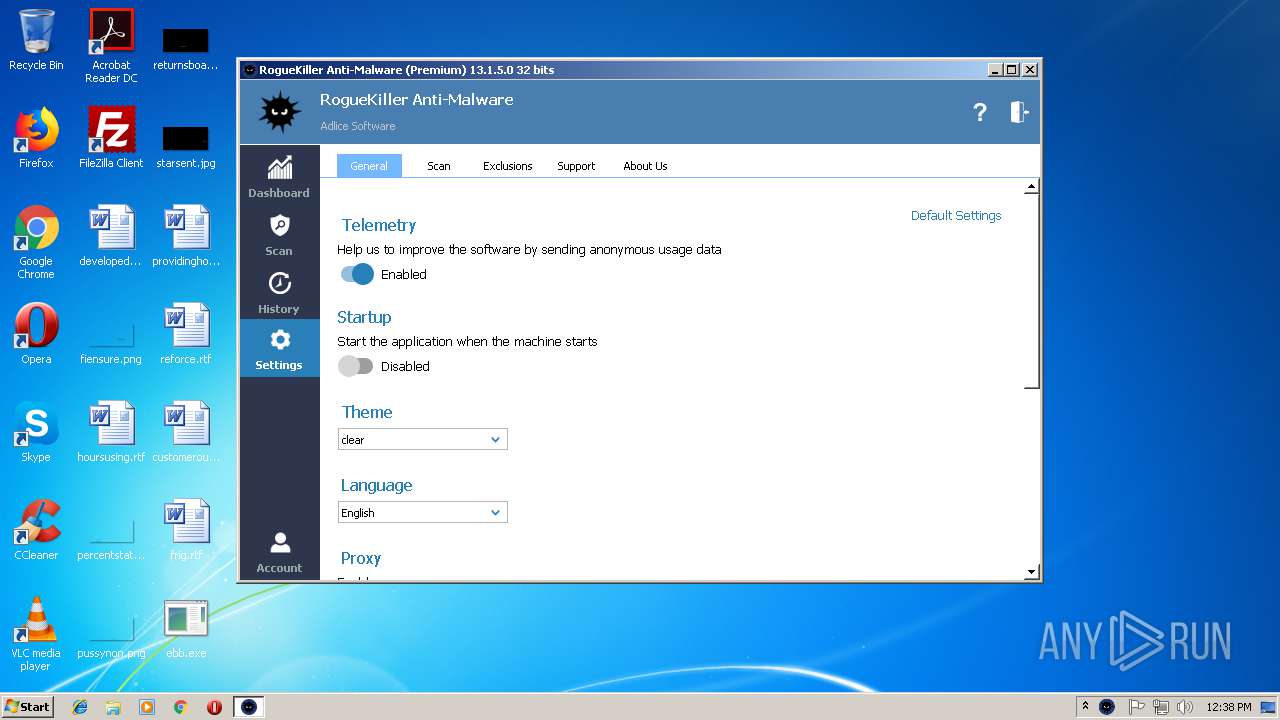
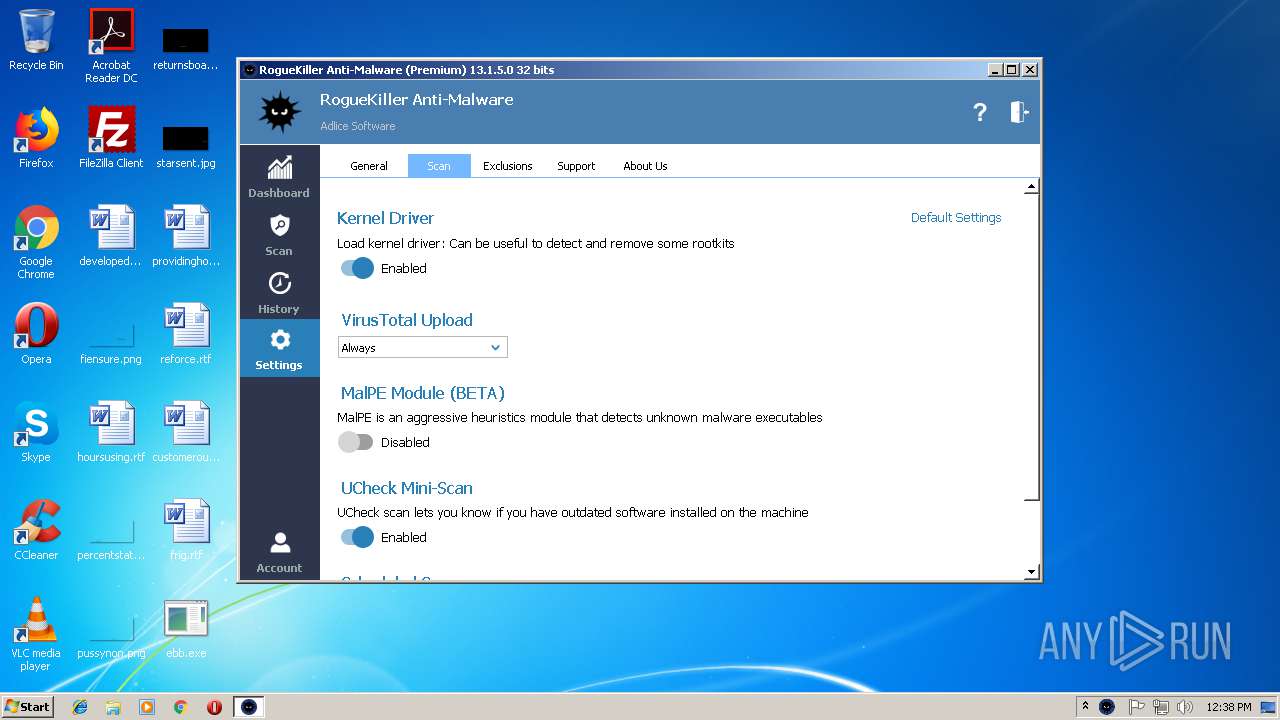
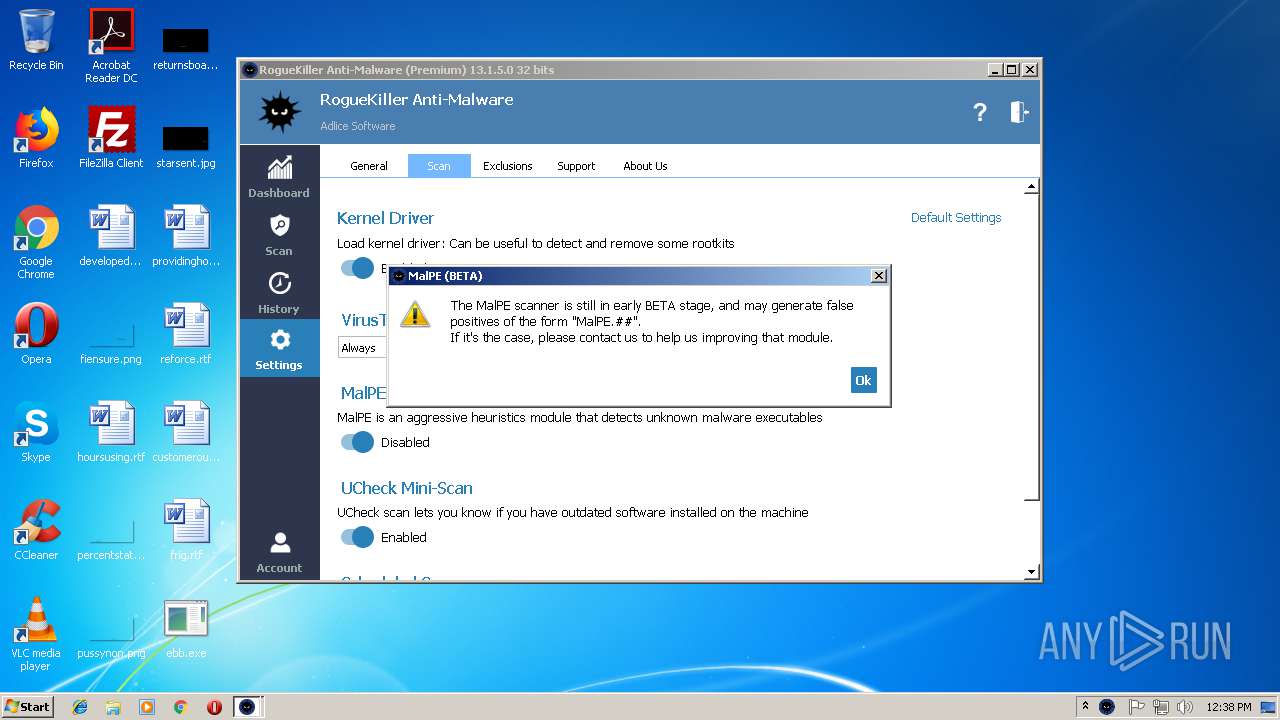
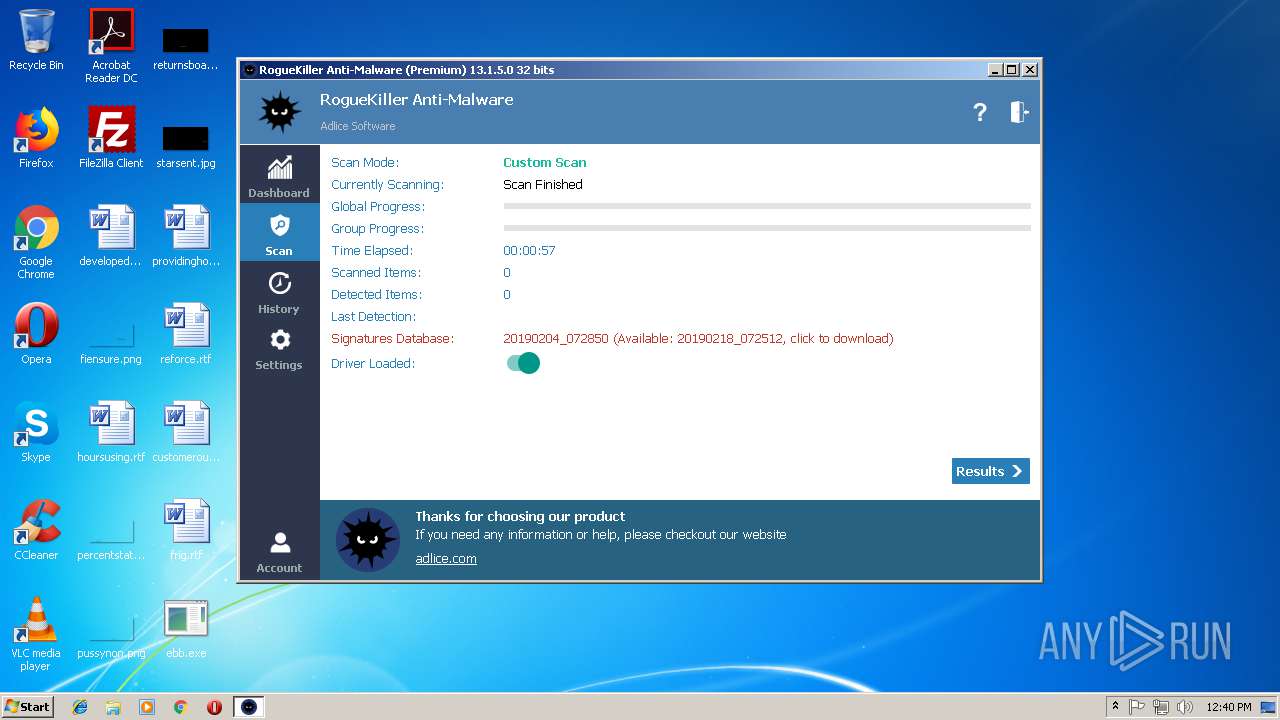
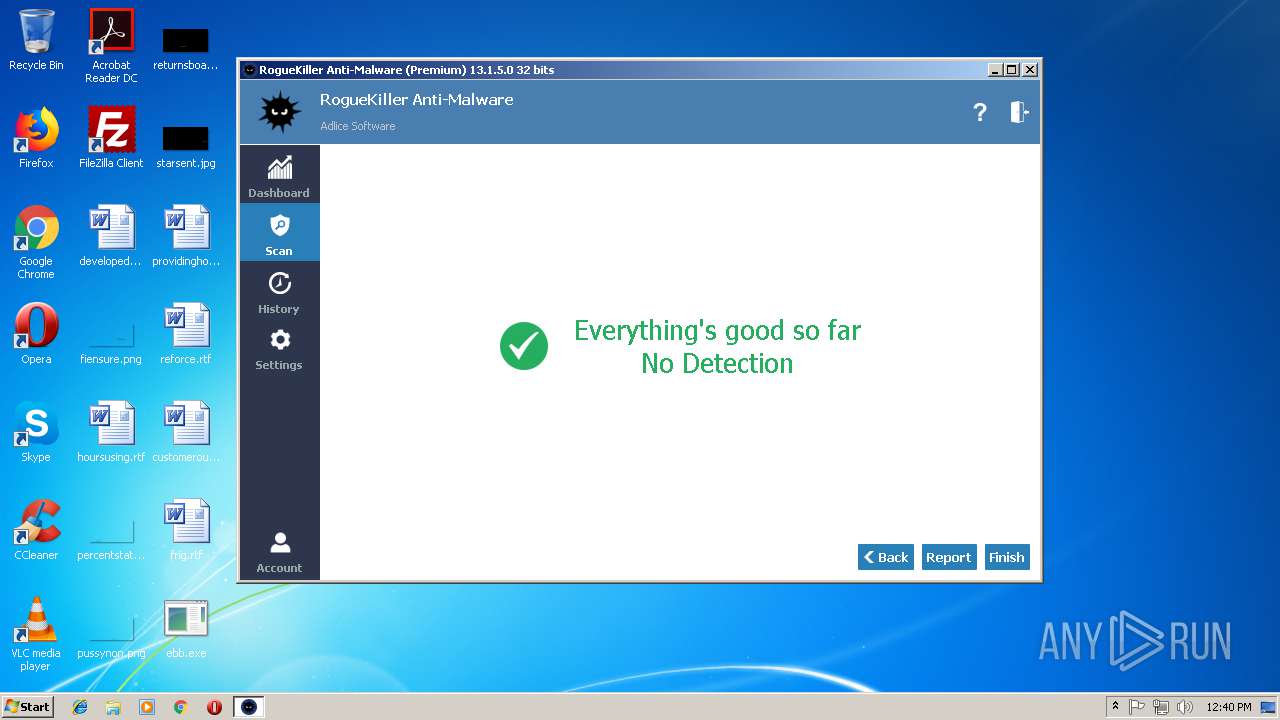
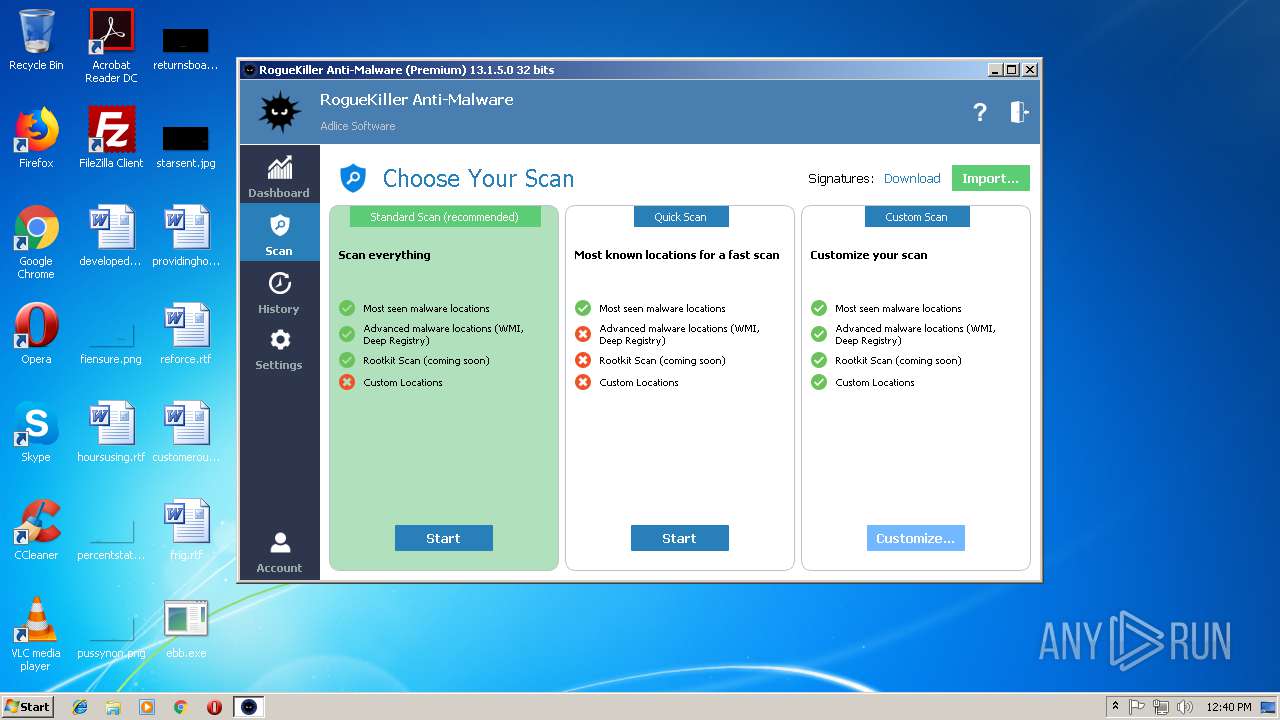
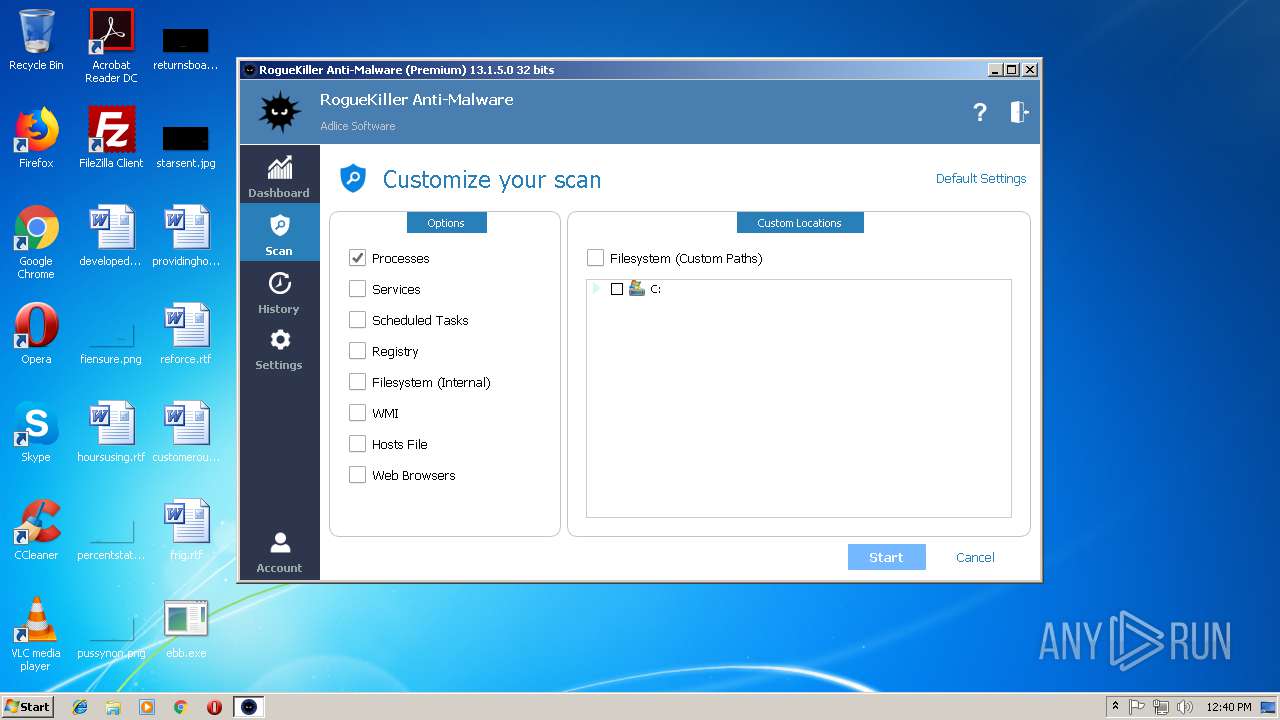
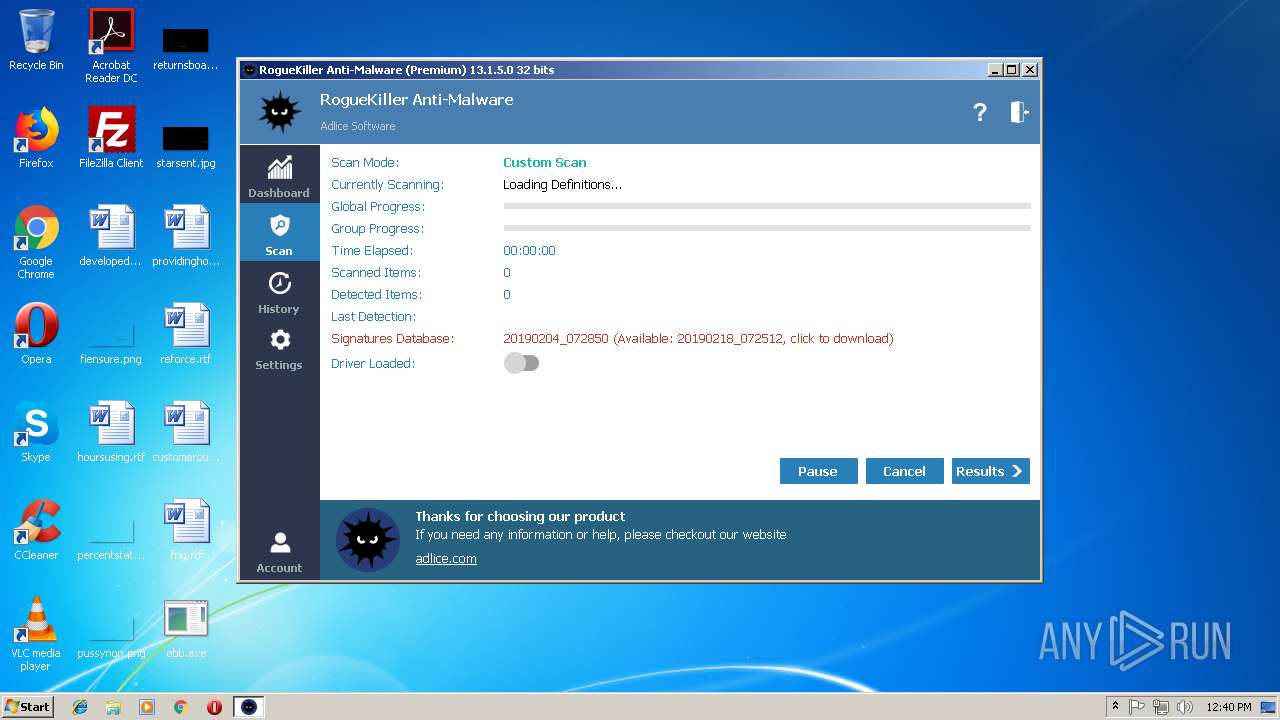
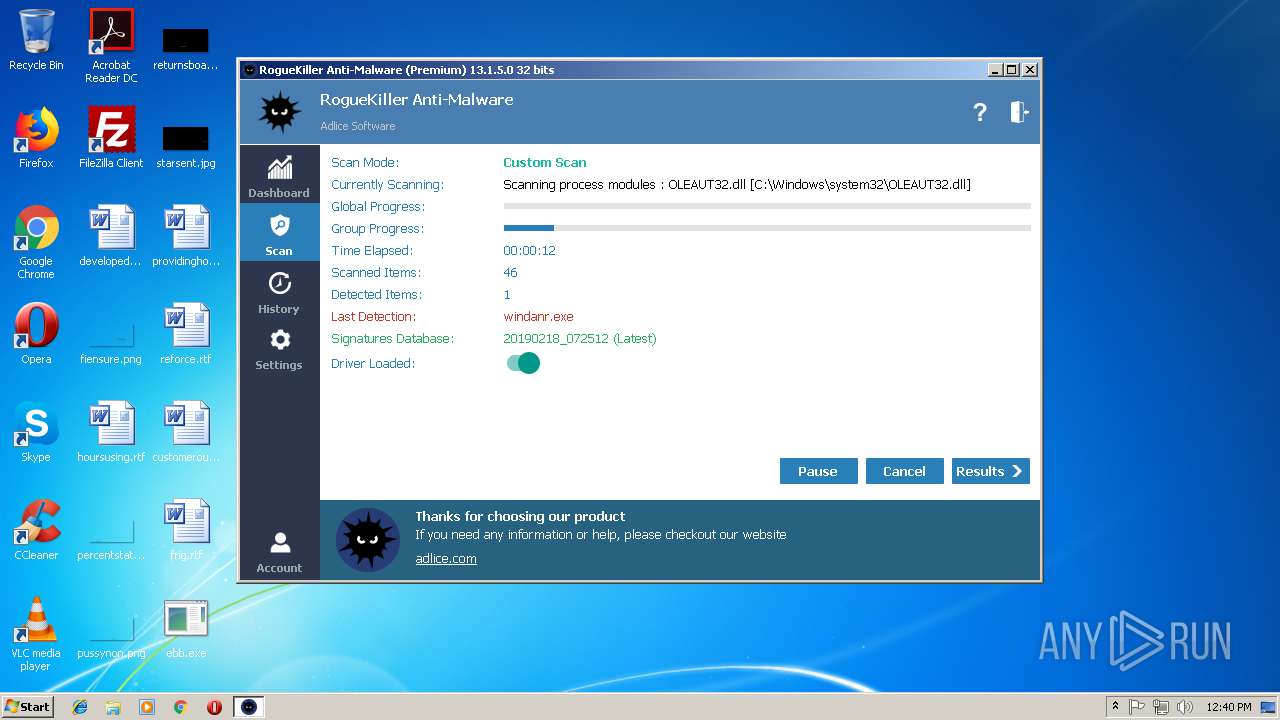
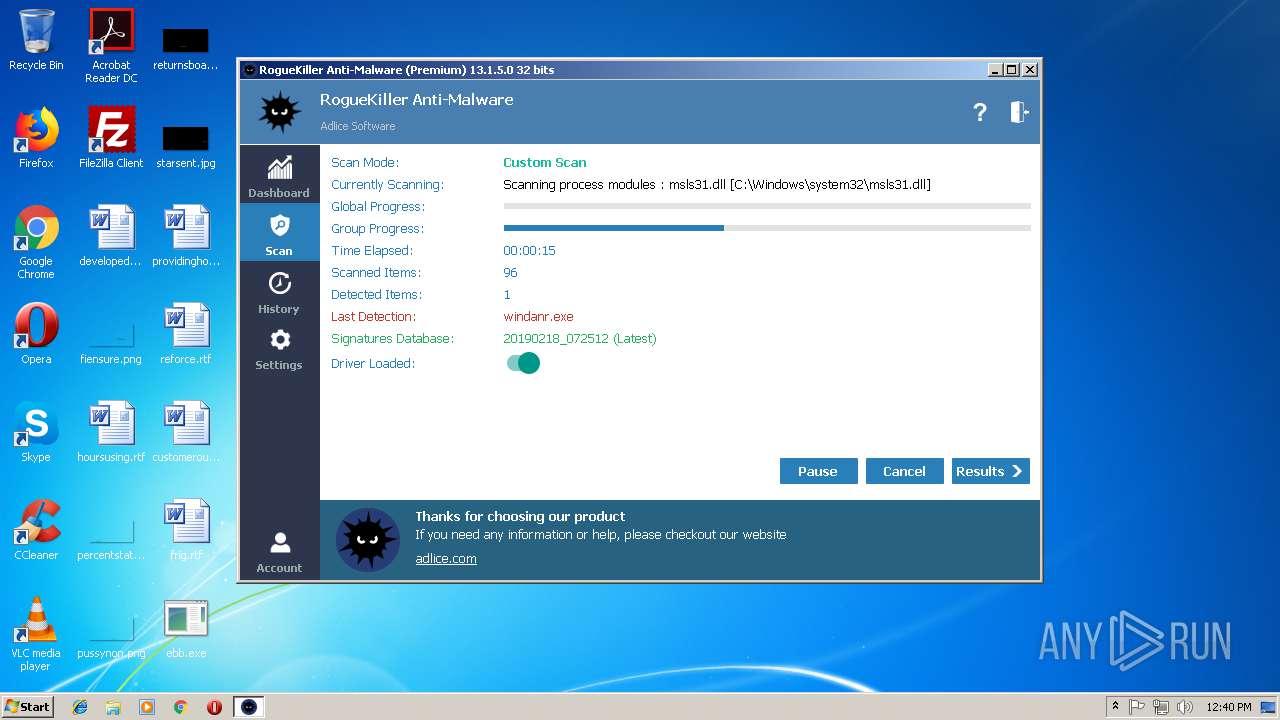
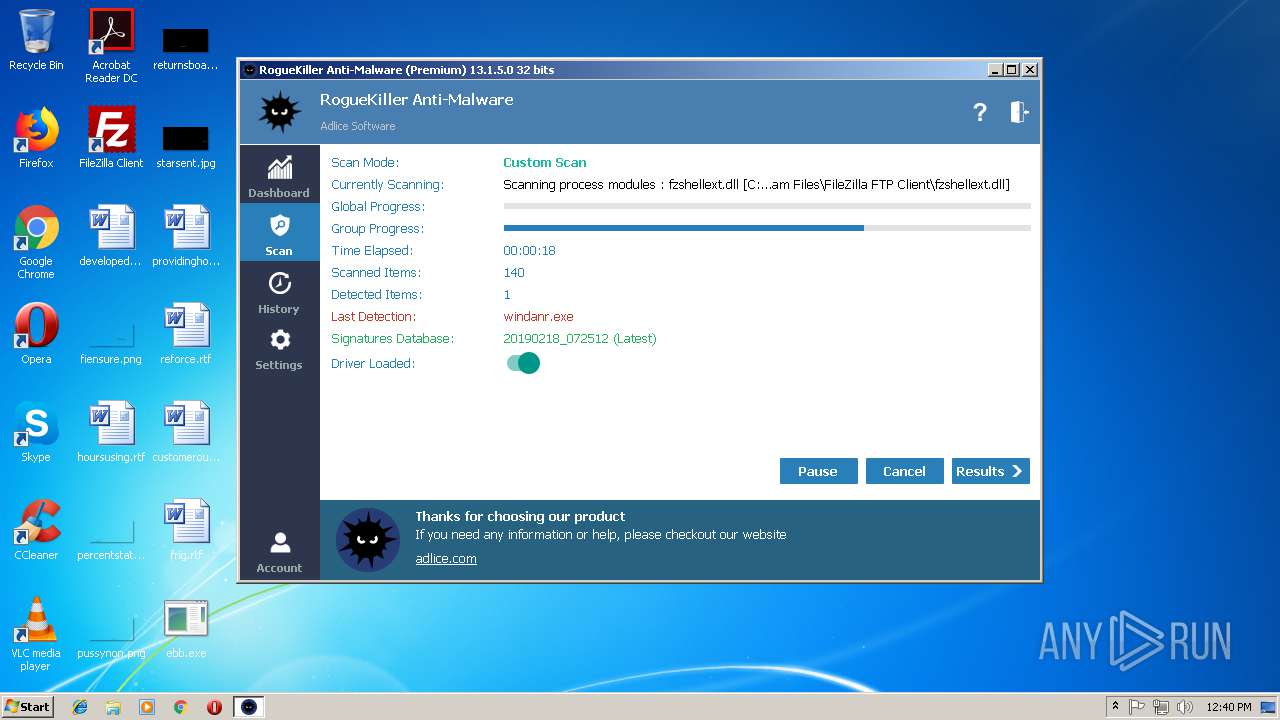
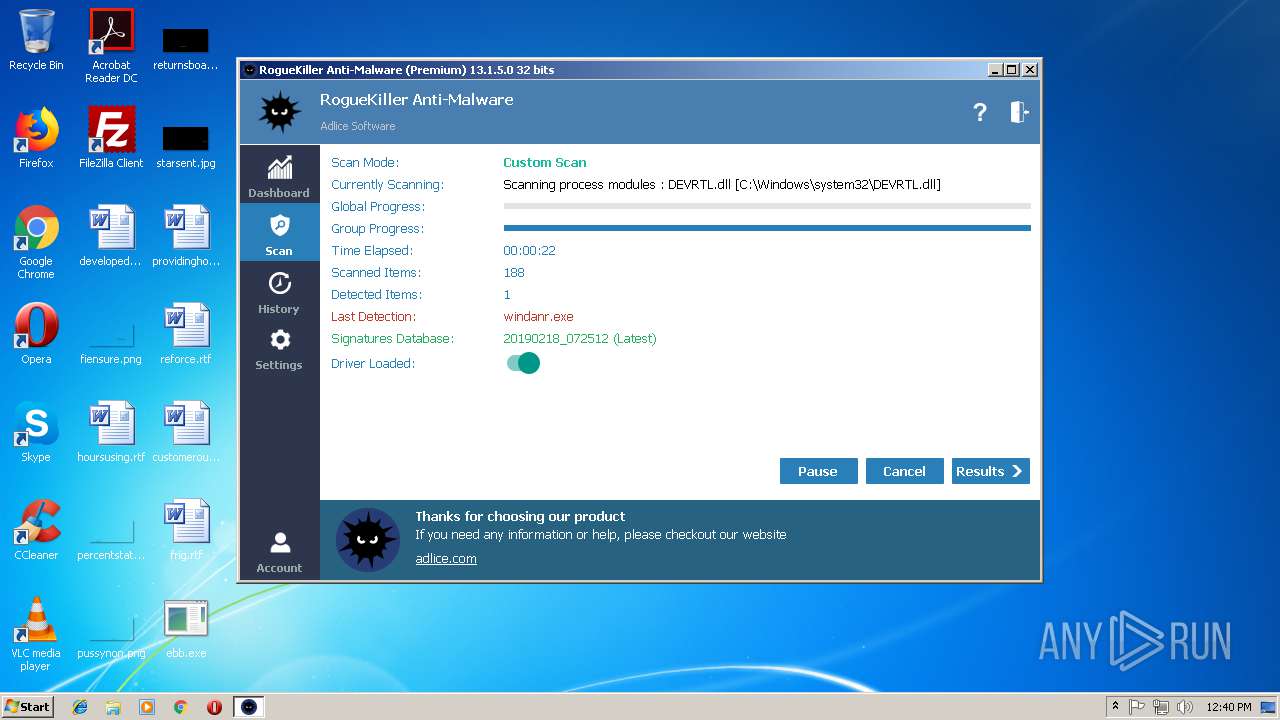
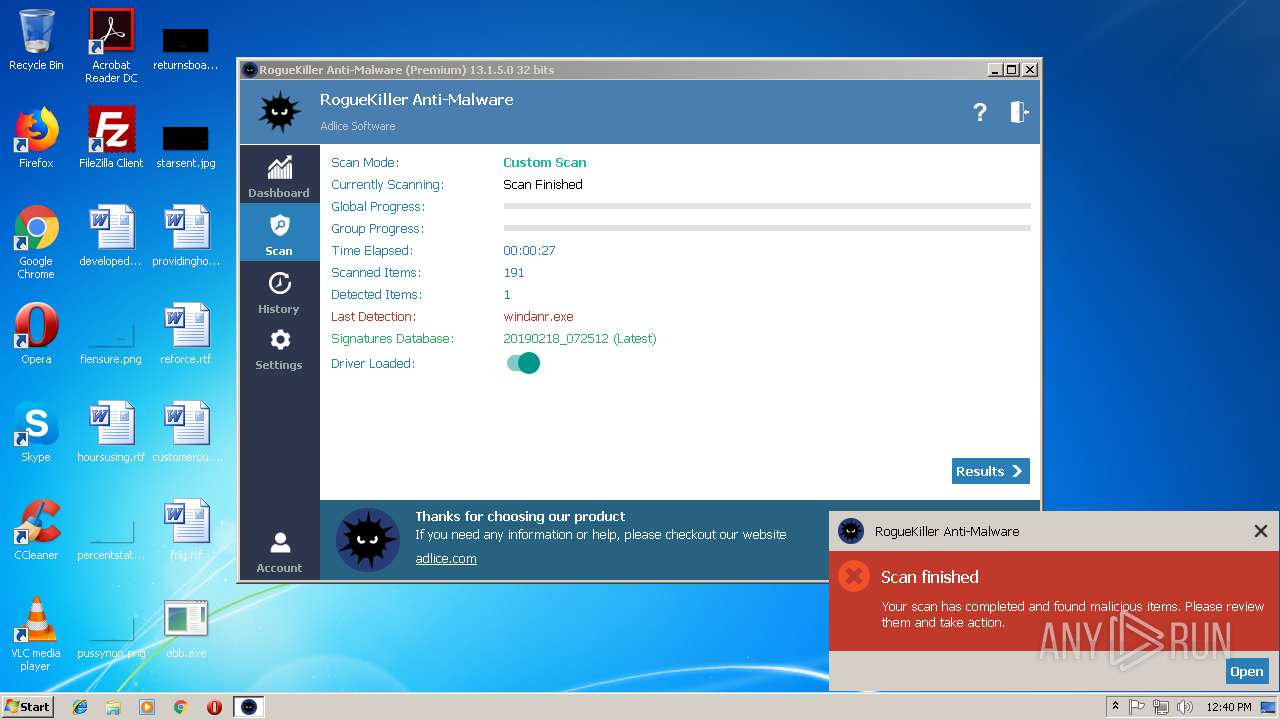
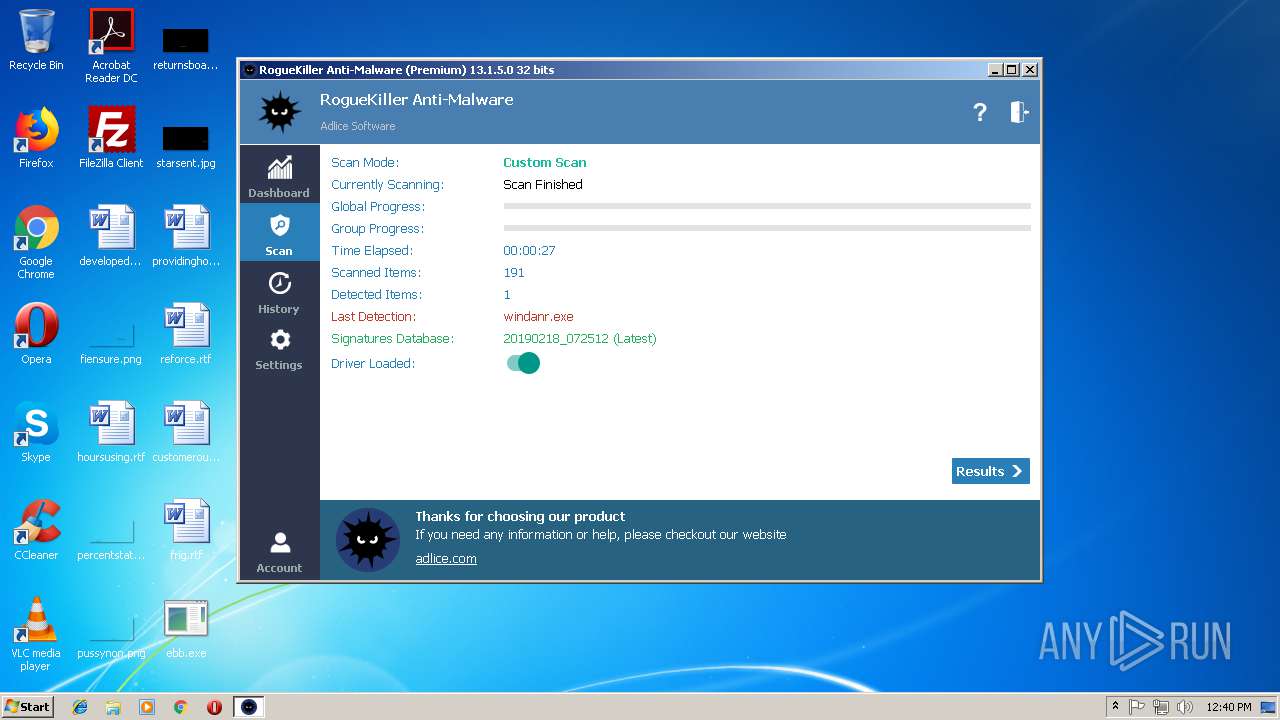
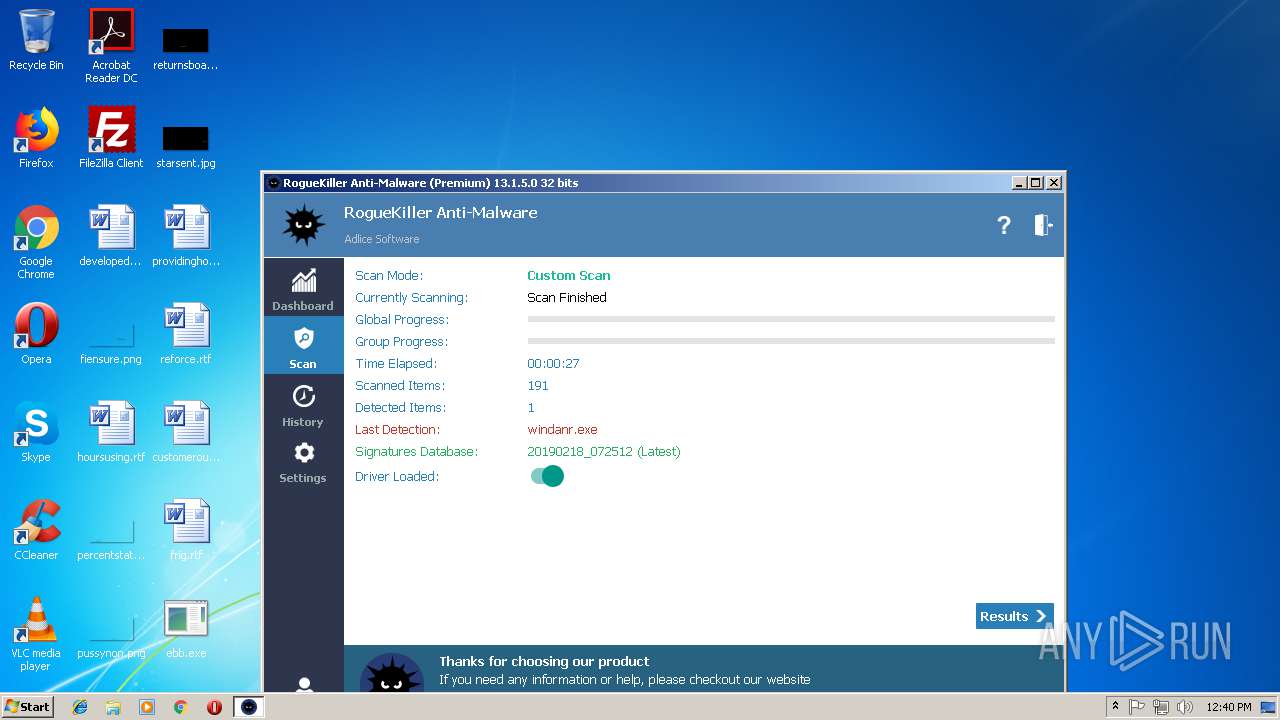
- RogueKiller_portable32.exe (PID: 3584)
- schtasks.exe (PID: 2392)
- schtasks.exe (PID: 3116)
- schtasks.exe (PID: 3348)
- schtasks.exe (PID: 672)
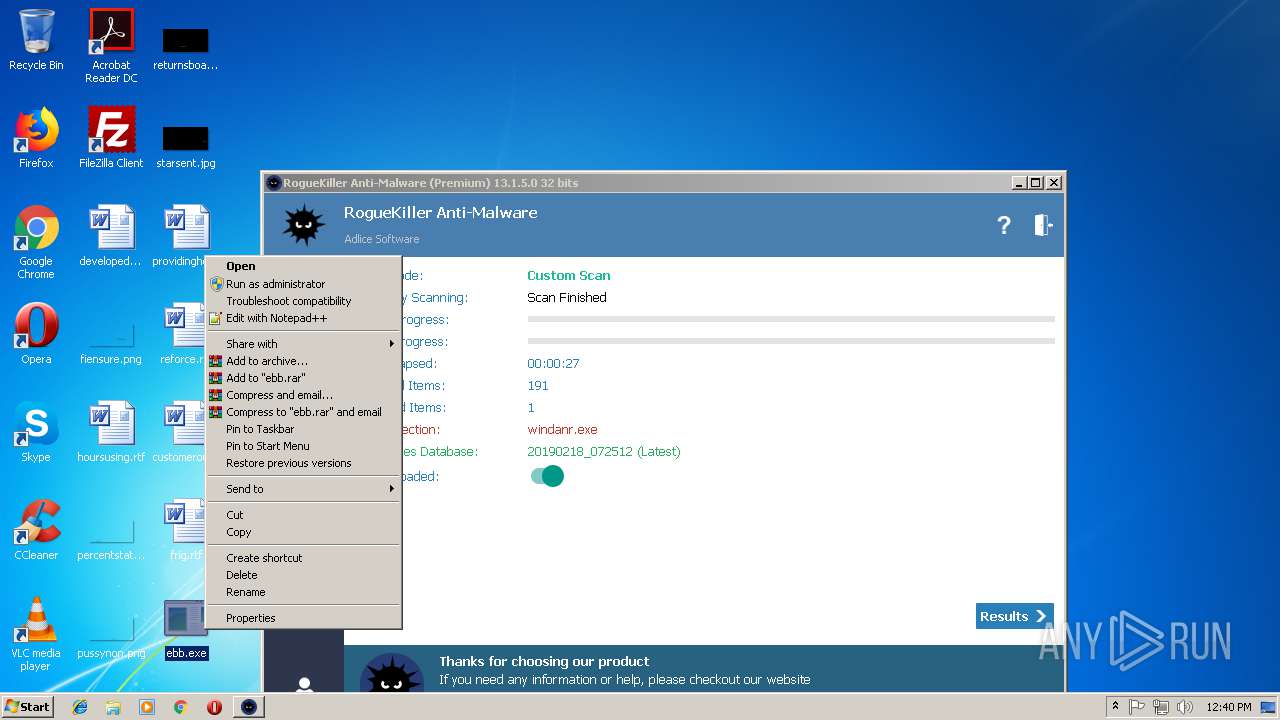
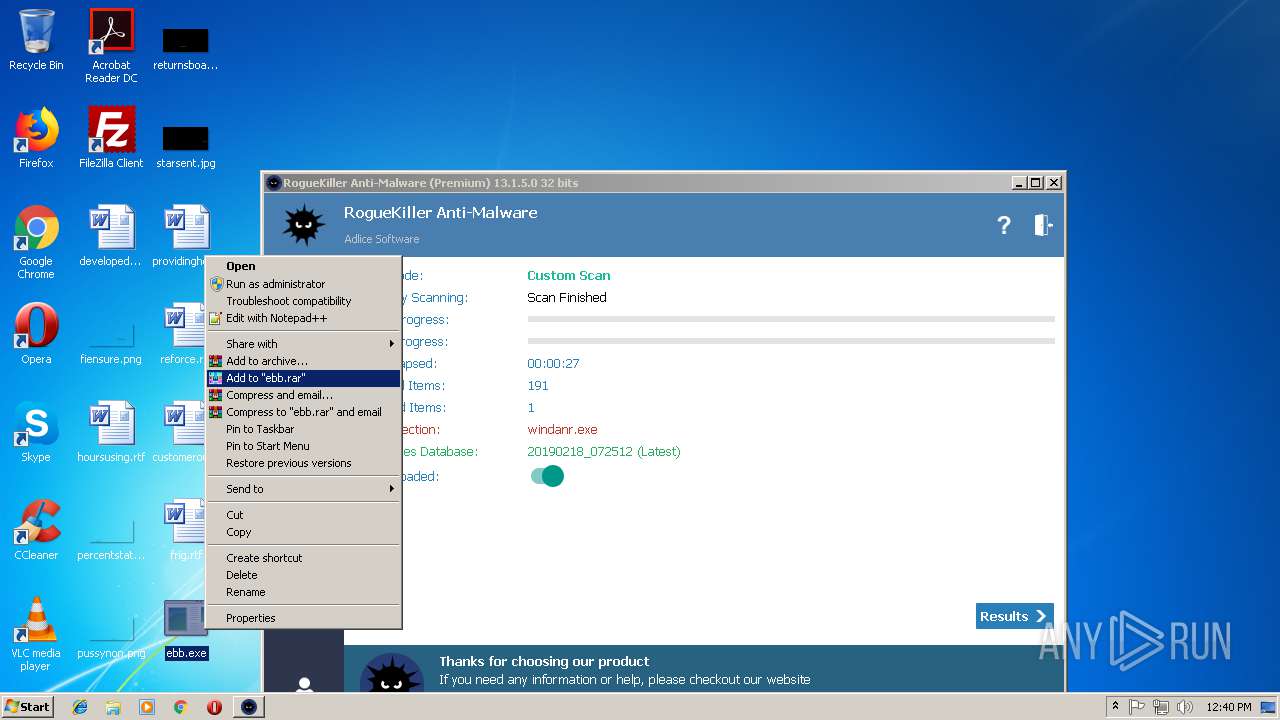
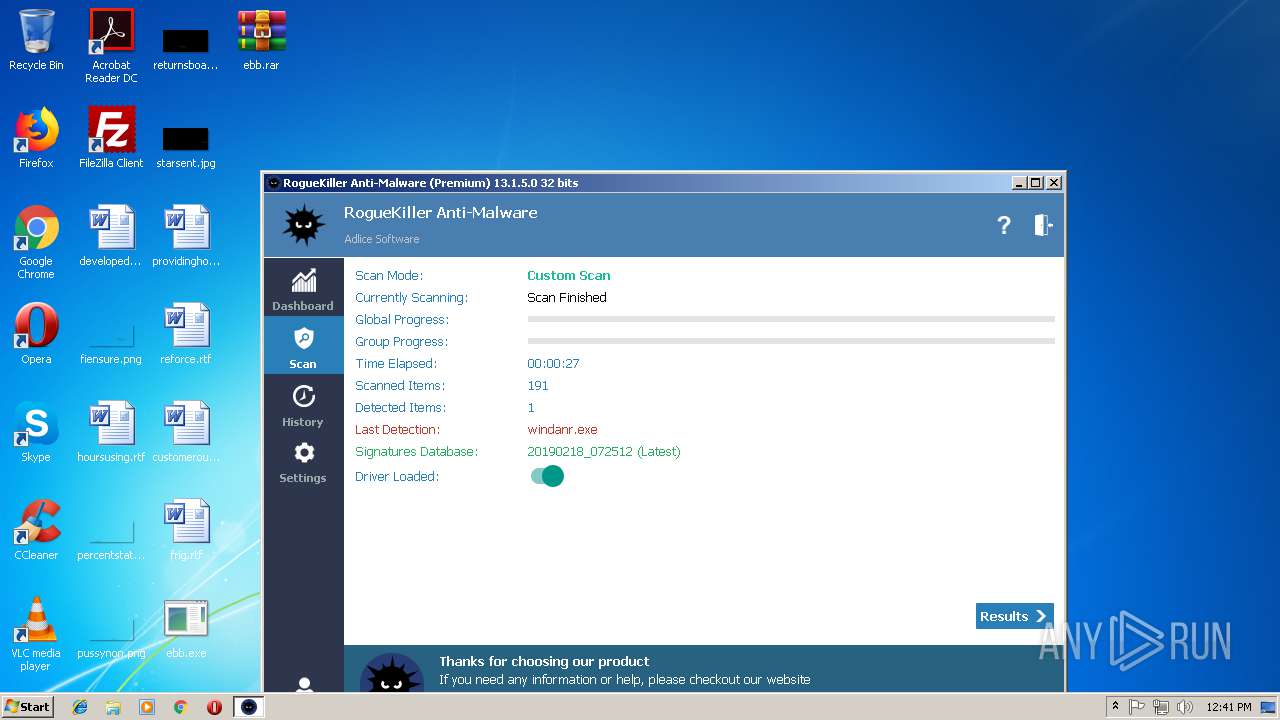
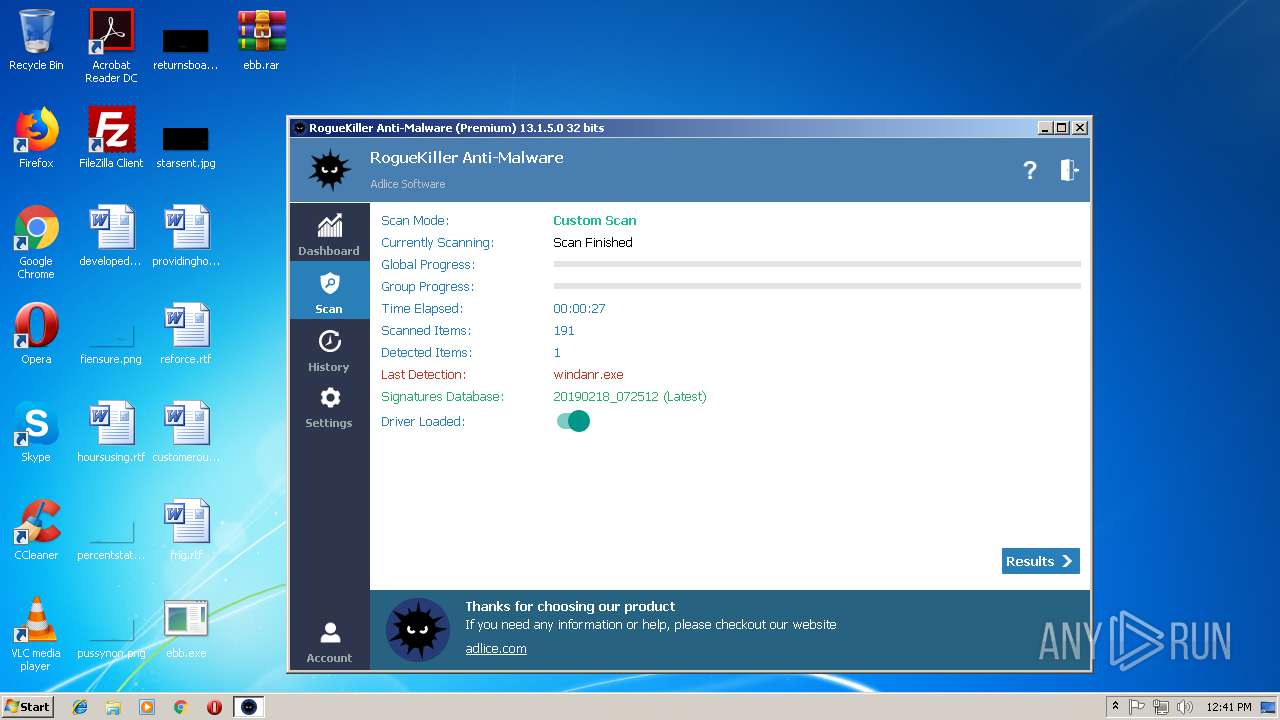
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 3024)
- RegAsm.exe (PID: 2188)
- RegAsm.exe (PID: 3264)
- RegAsm.exe (PID: 2920)
- RegAsm.exe (PID: 2108)
Stealing of credential data
- vbc.exe (PID: 4028)
- vbc.exe (PID: 3372)
- vbc.exe (PID: 3004)
- vbc.exe (PID: 2144)
- vbc.exe (PID: 3396)
- vbc.exe (PID: 4076)
- vbc.exe (PID: 3868)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 700)
- vbc.exe (PID: 1324)
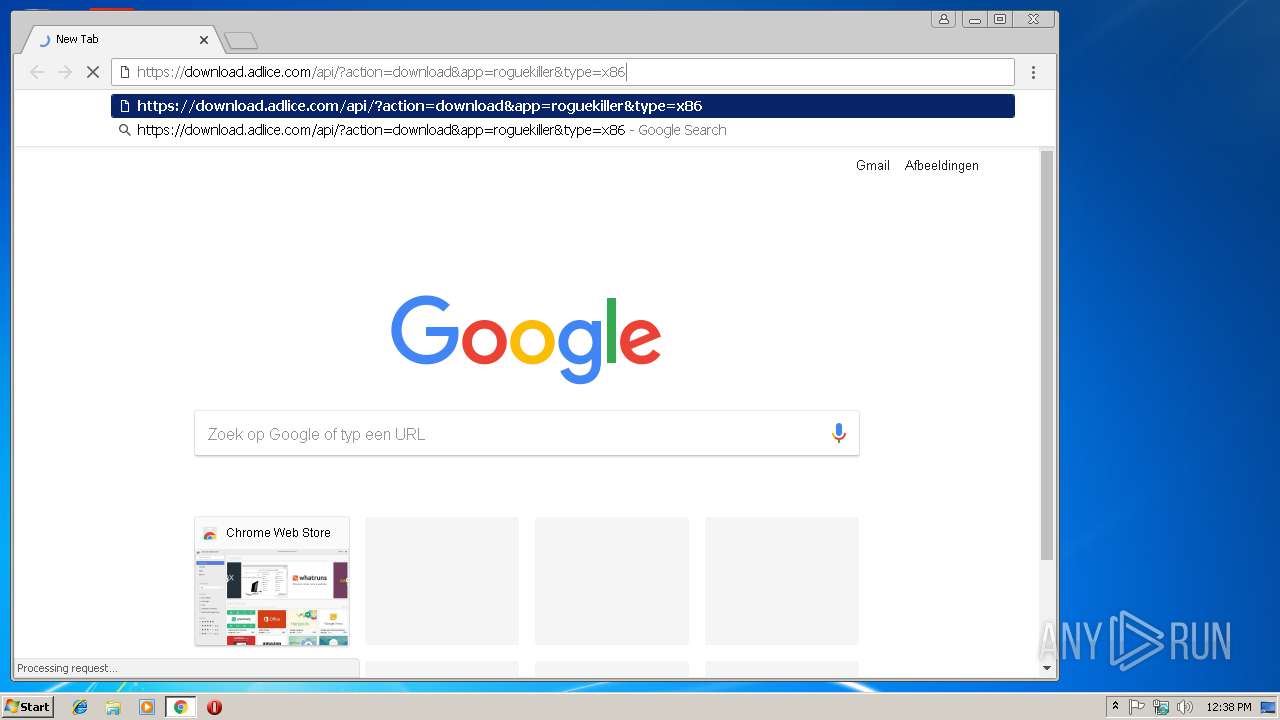
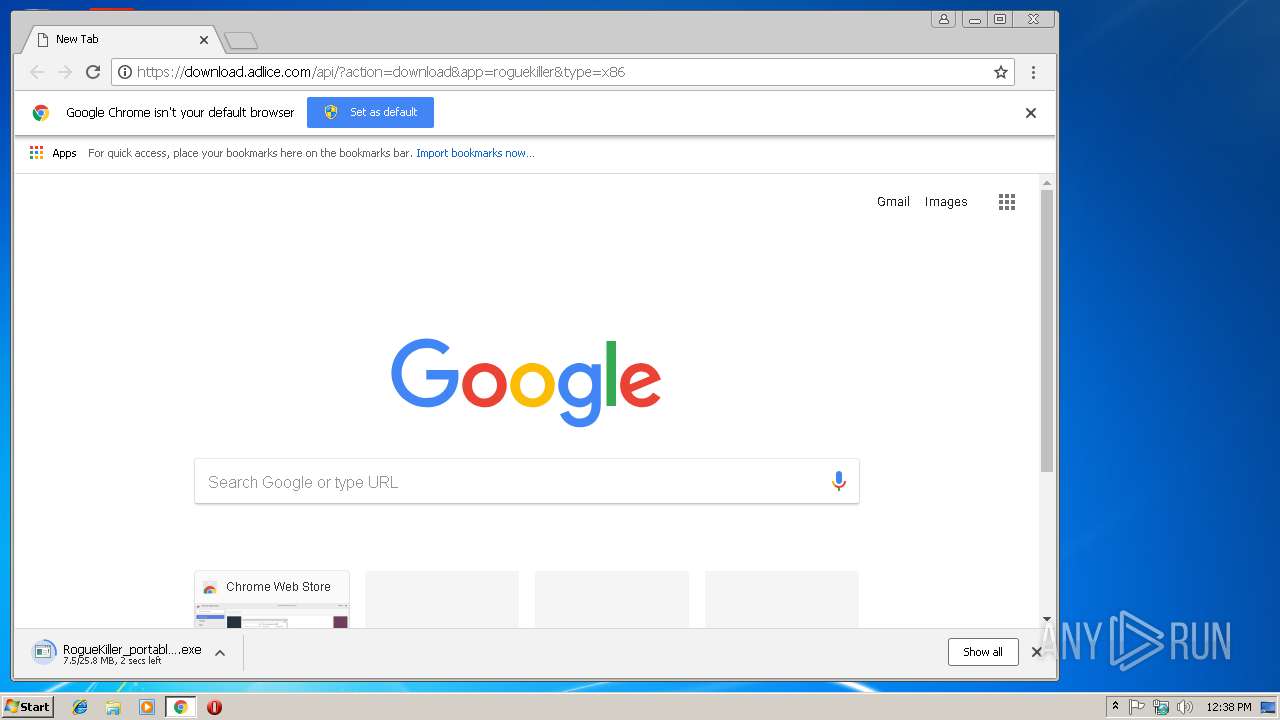
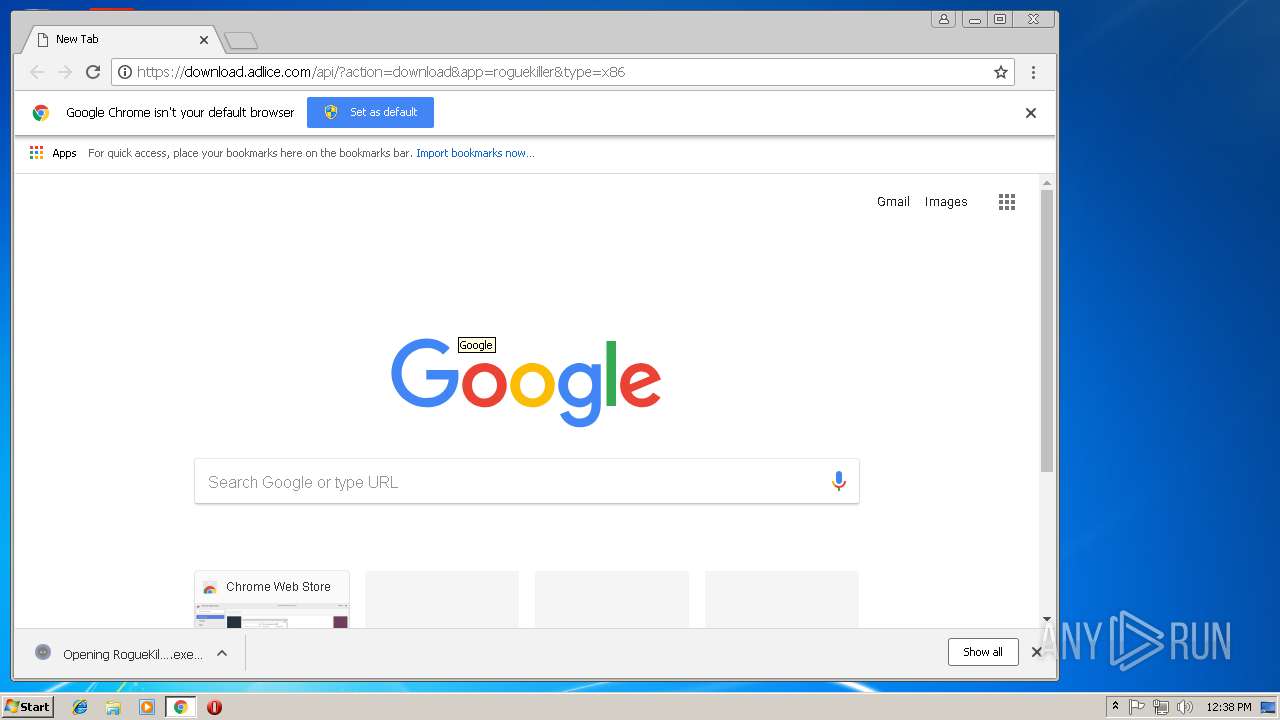
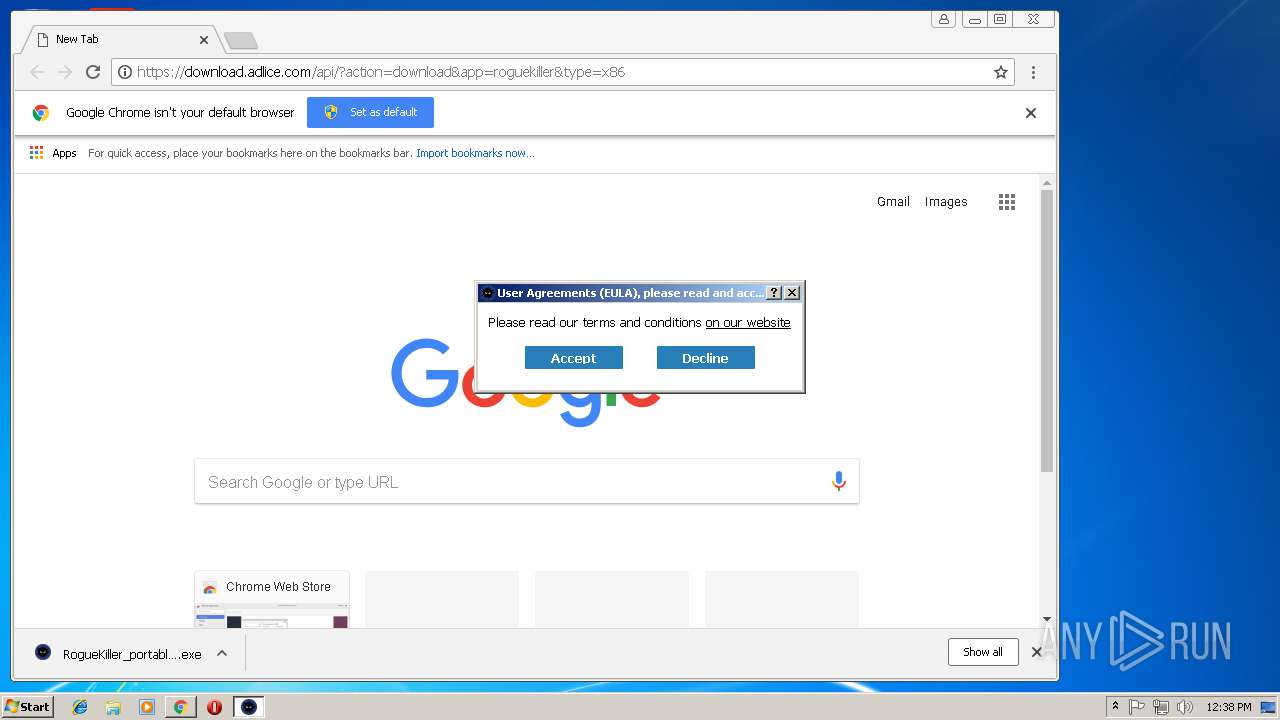
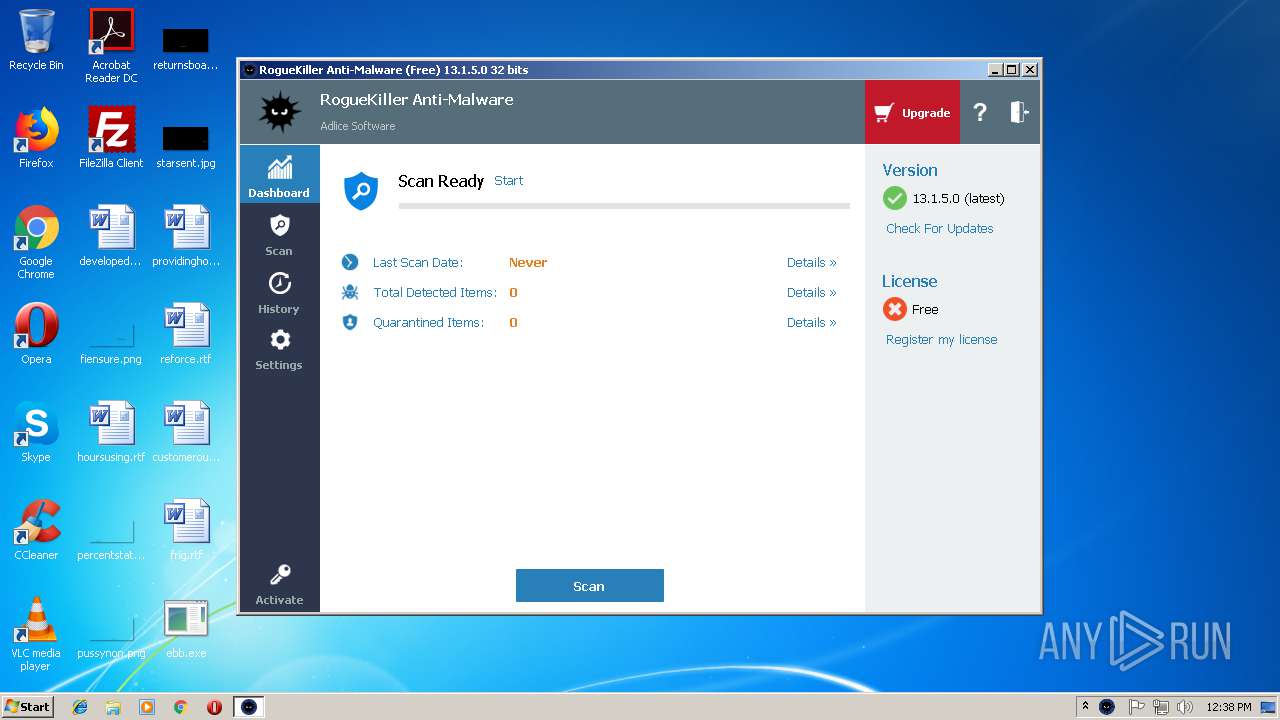
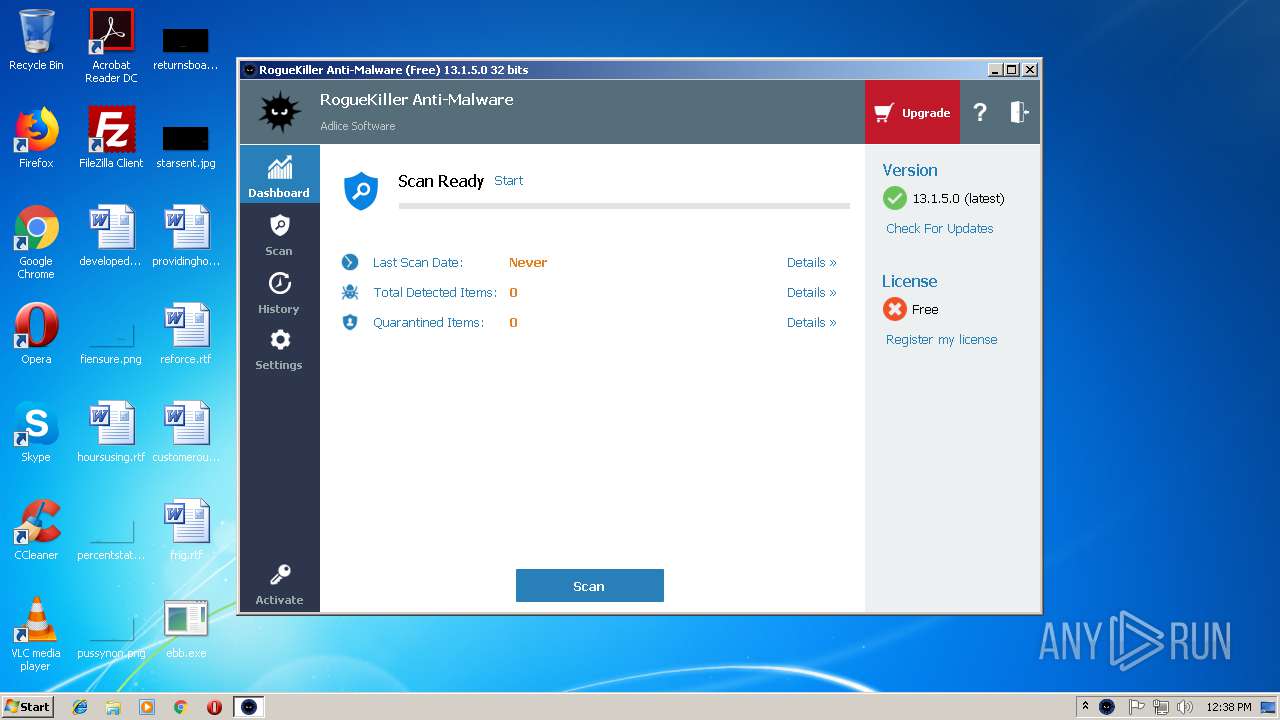
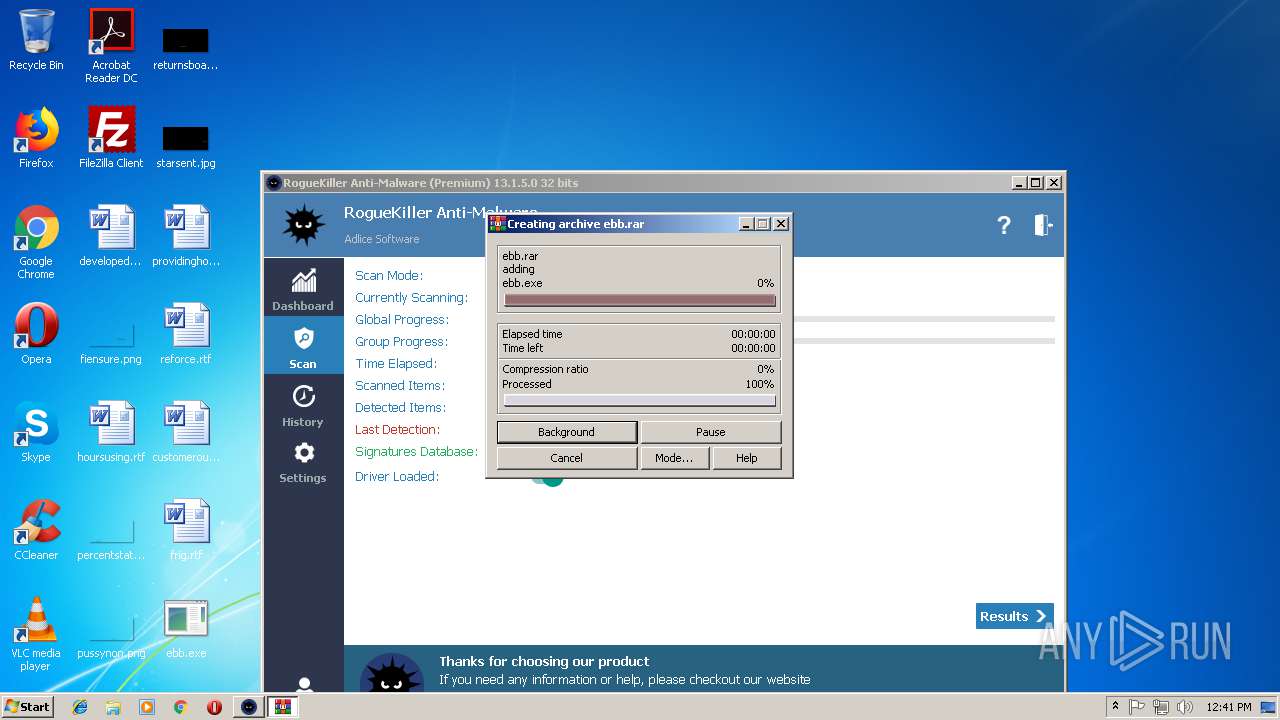
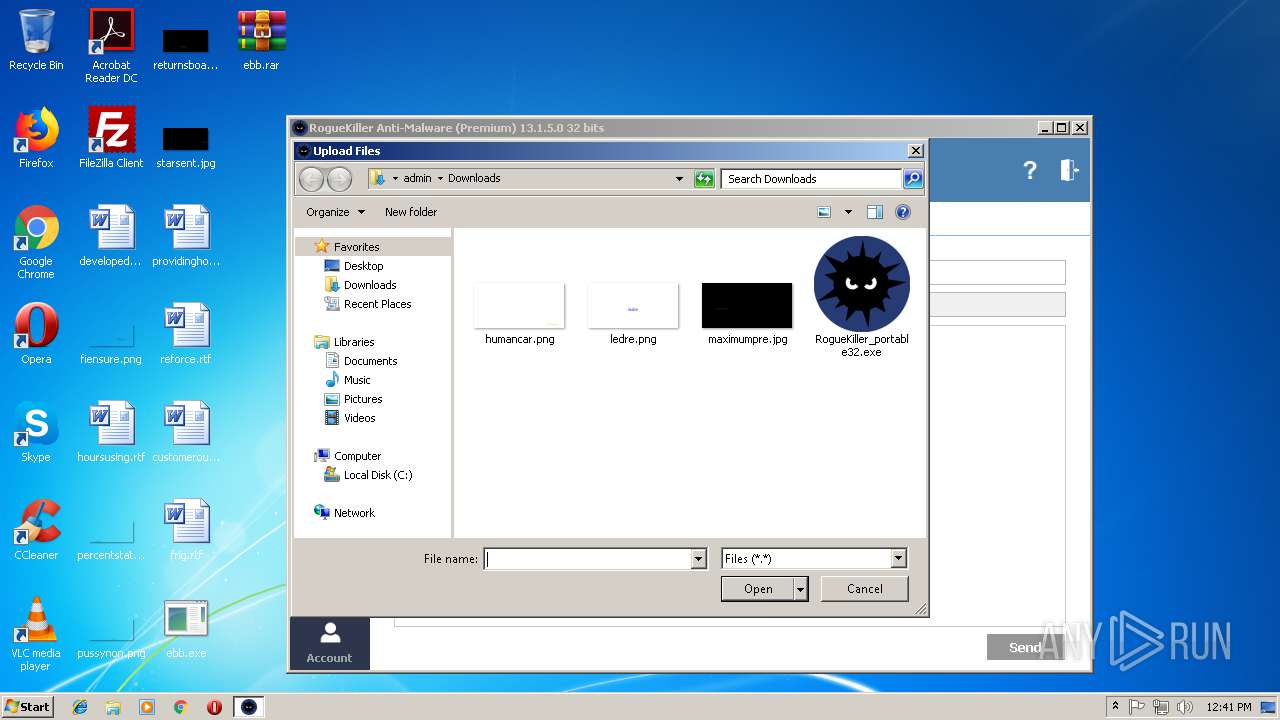
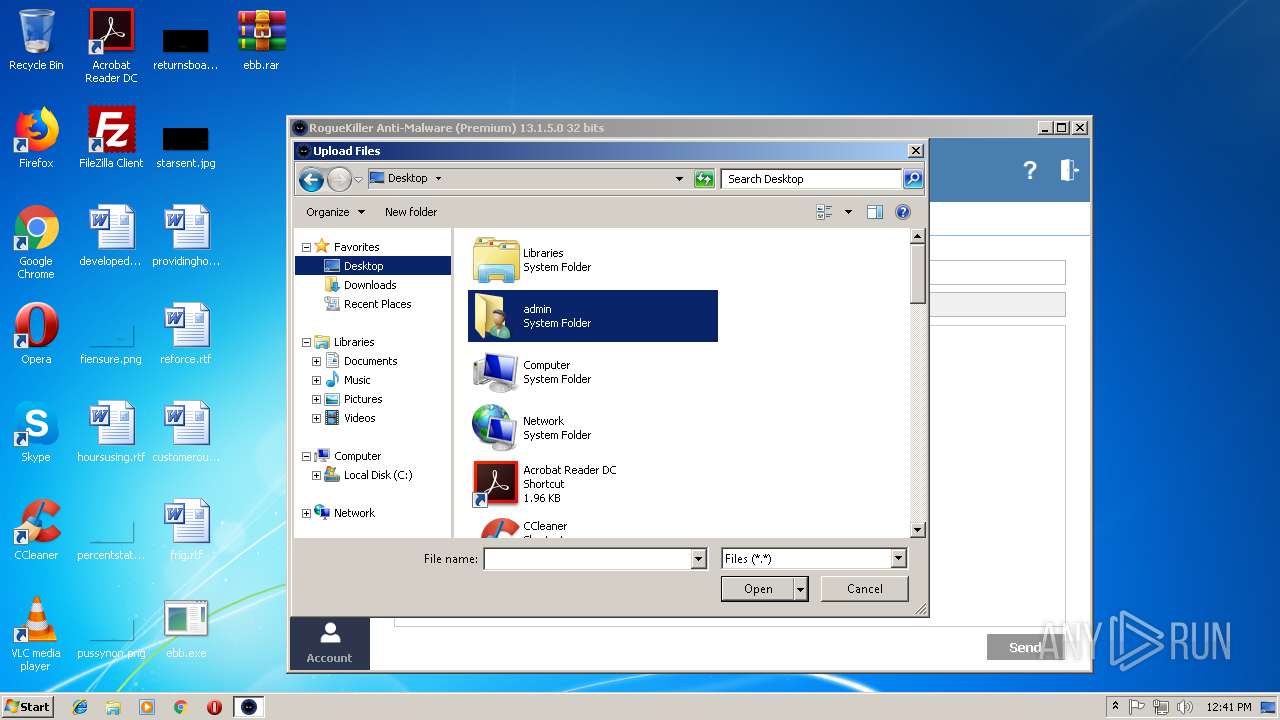
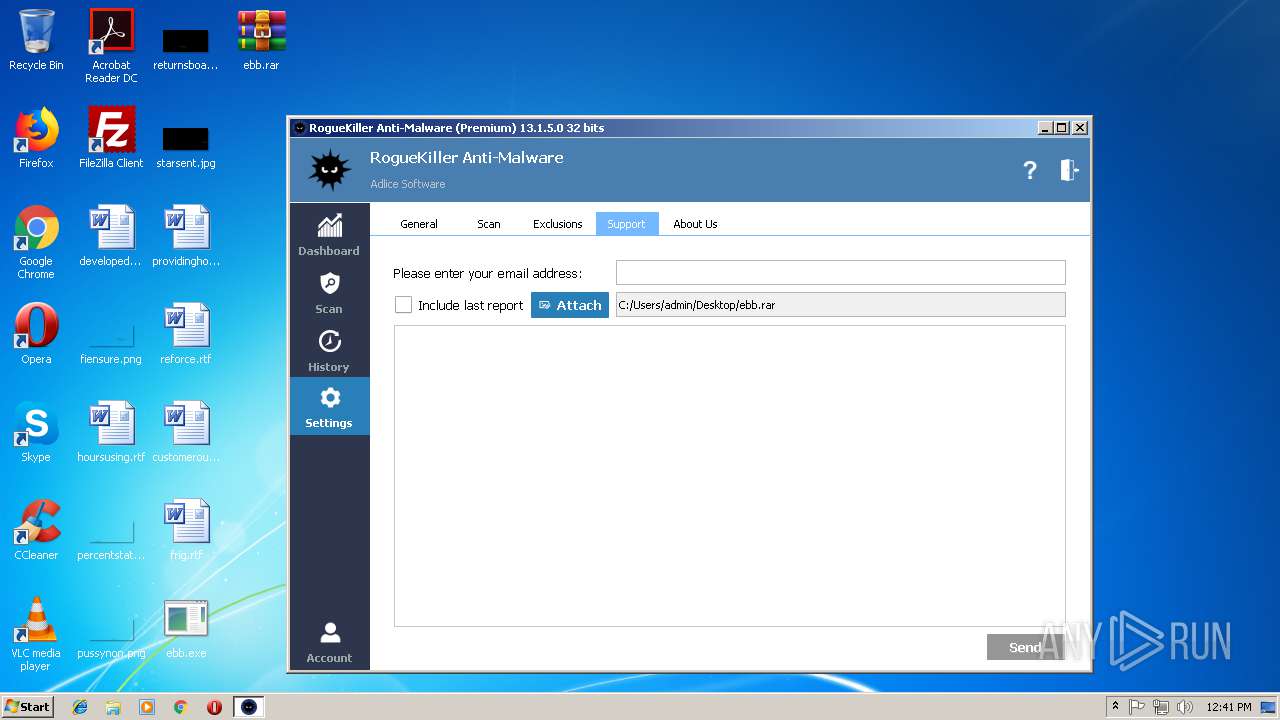
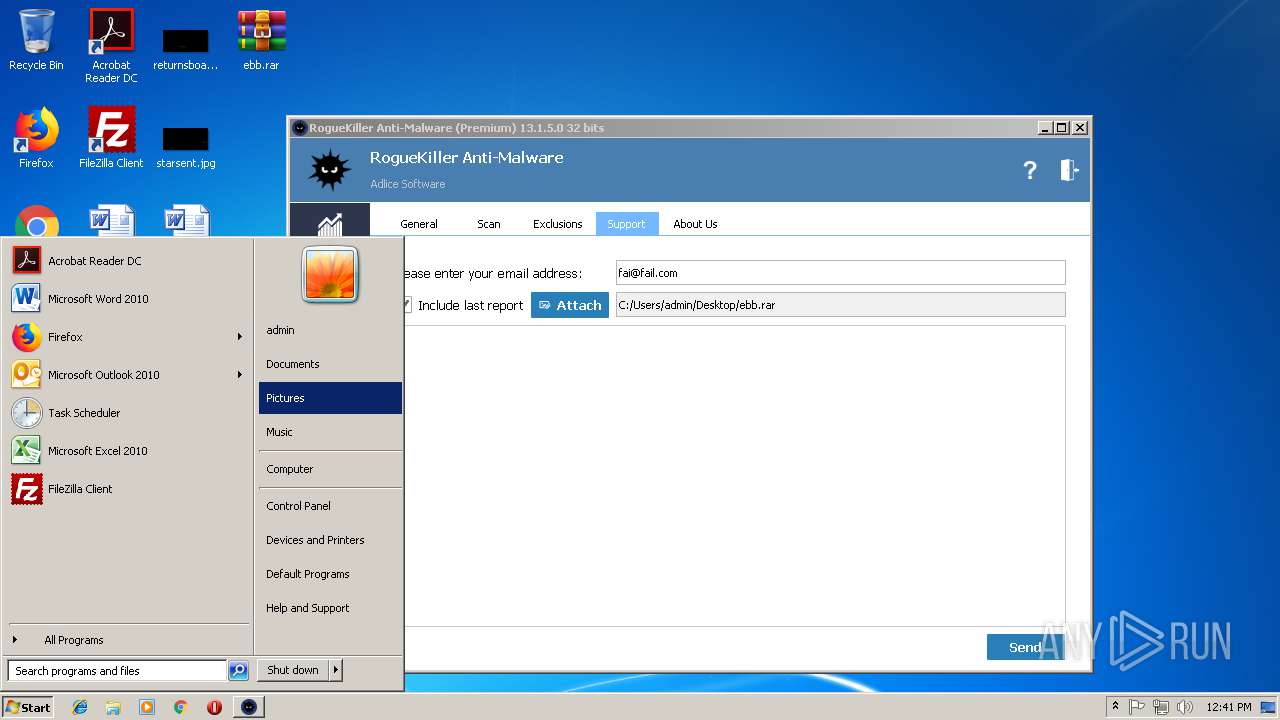
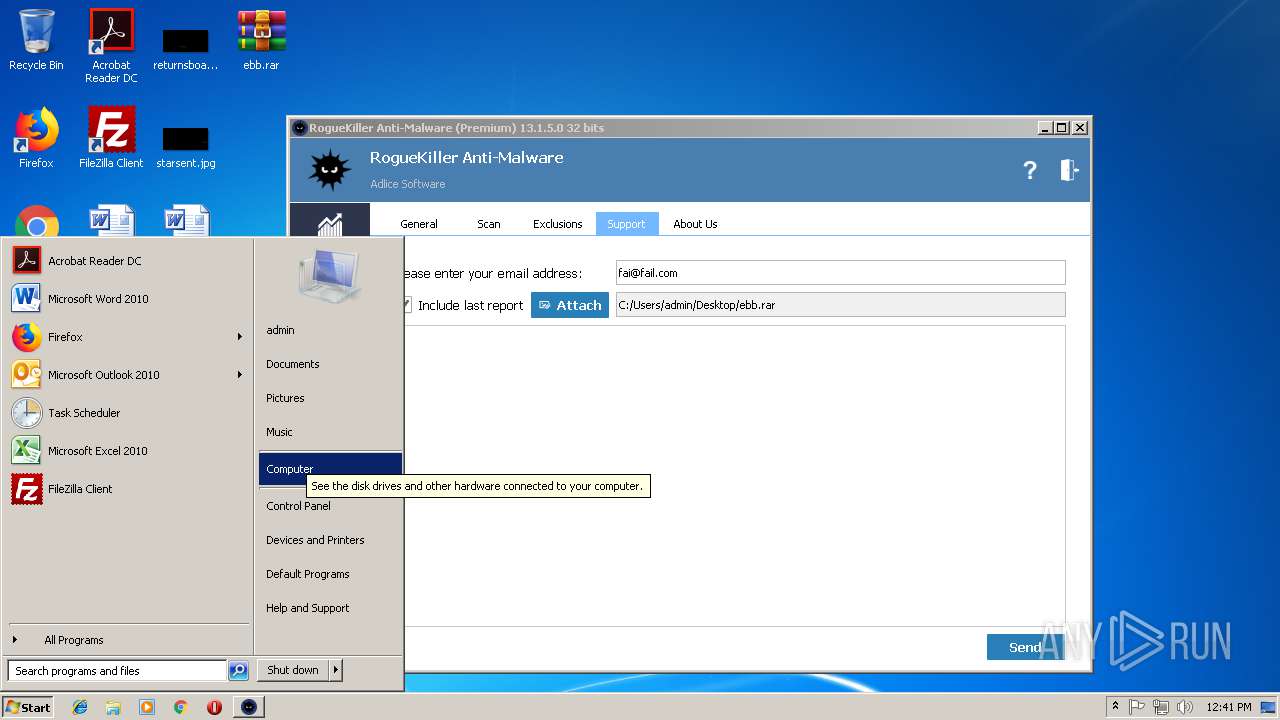
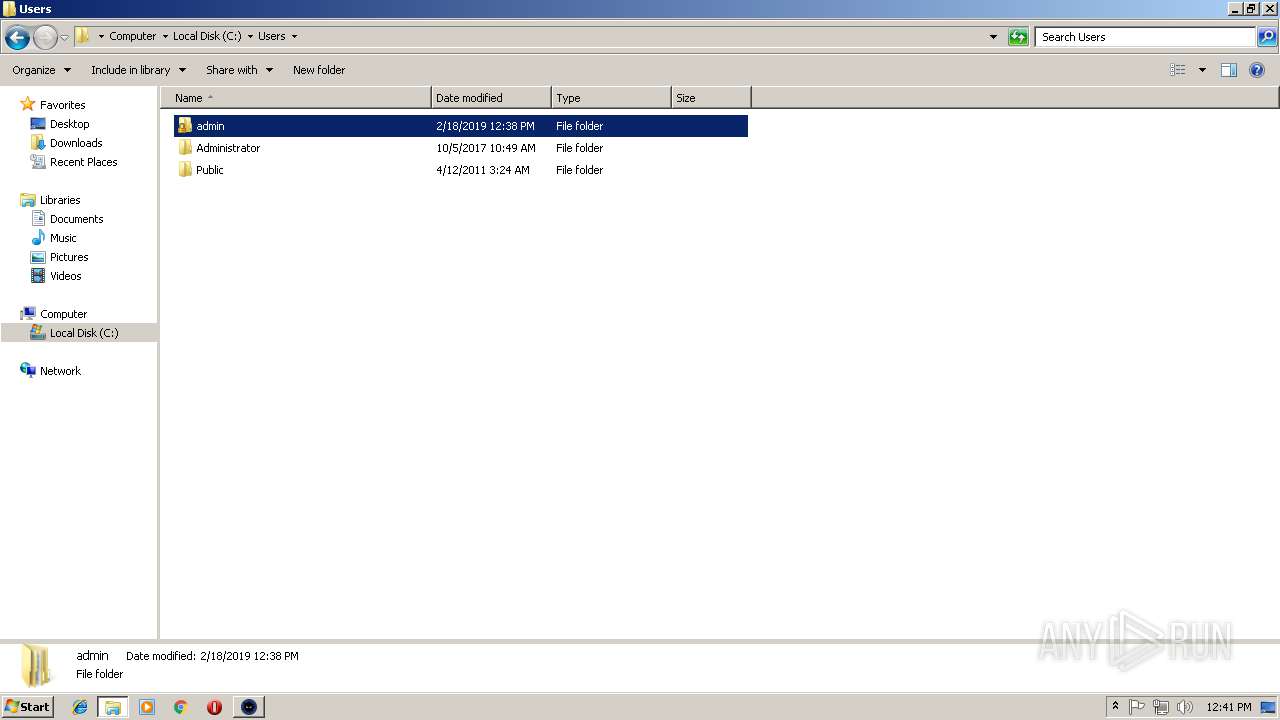
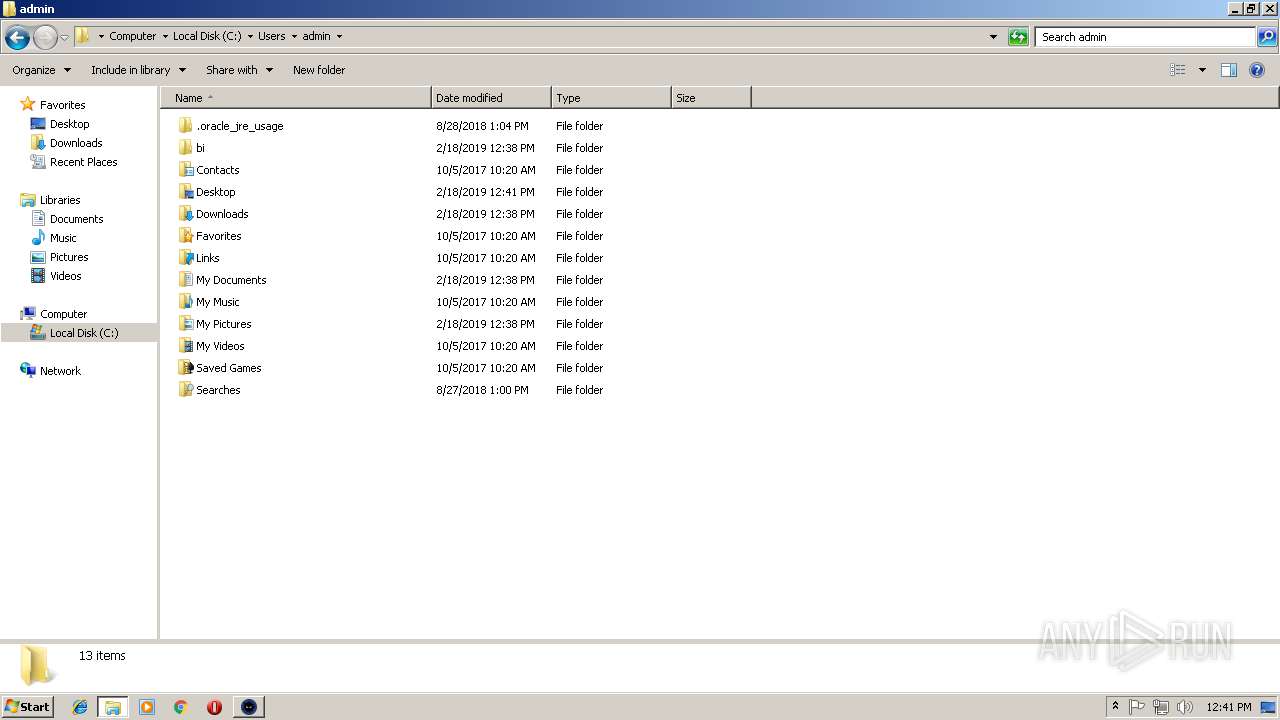
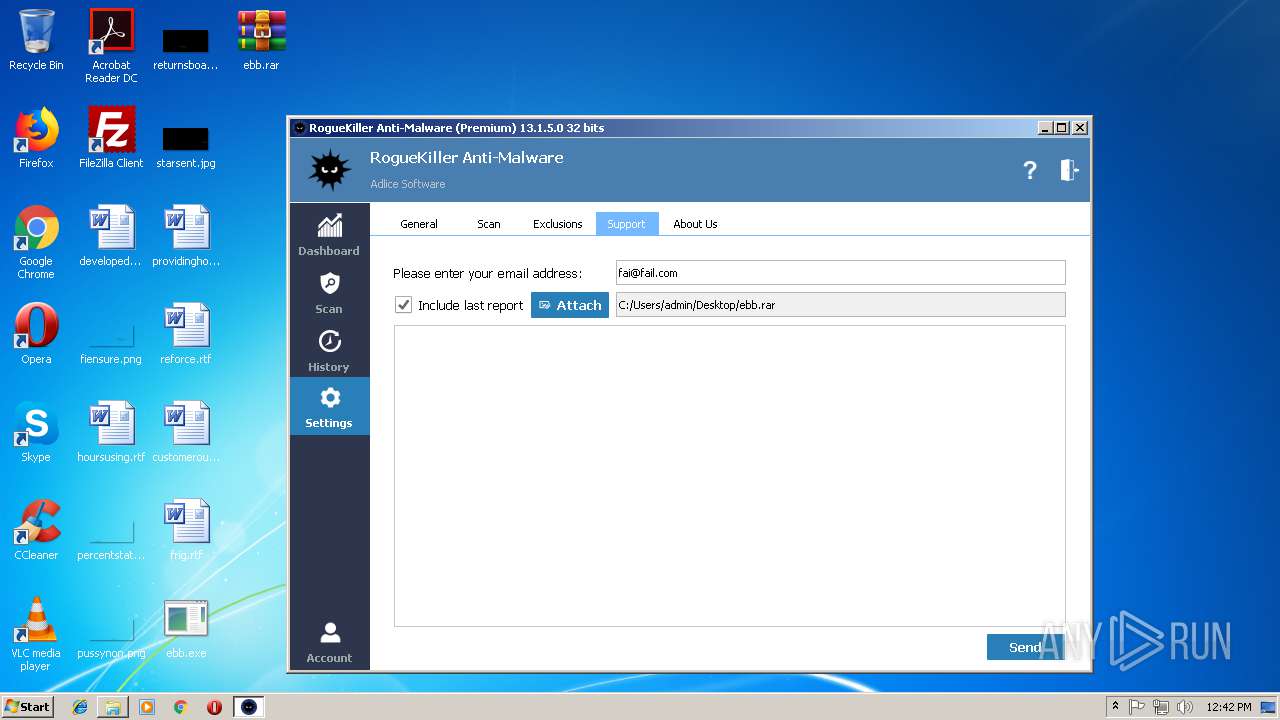
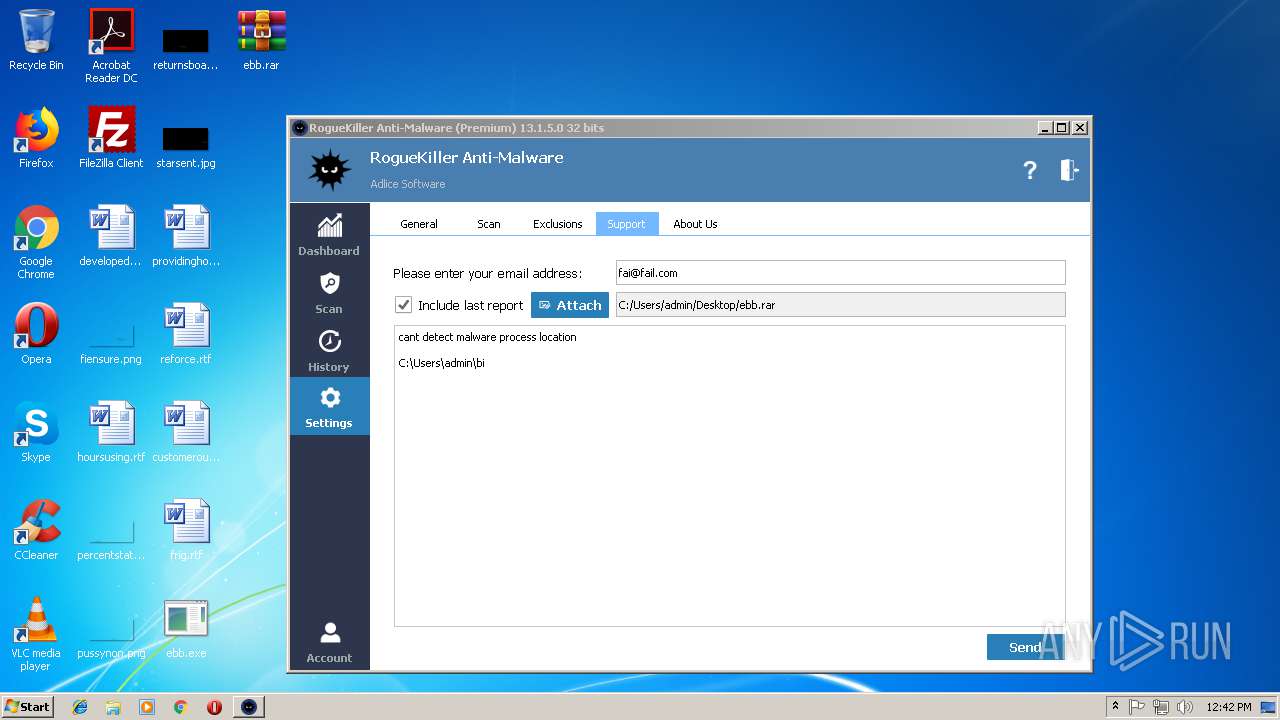
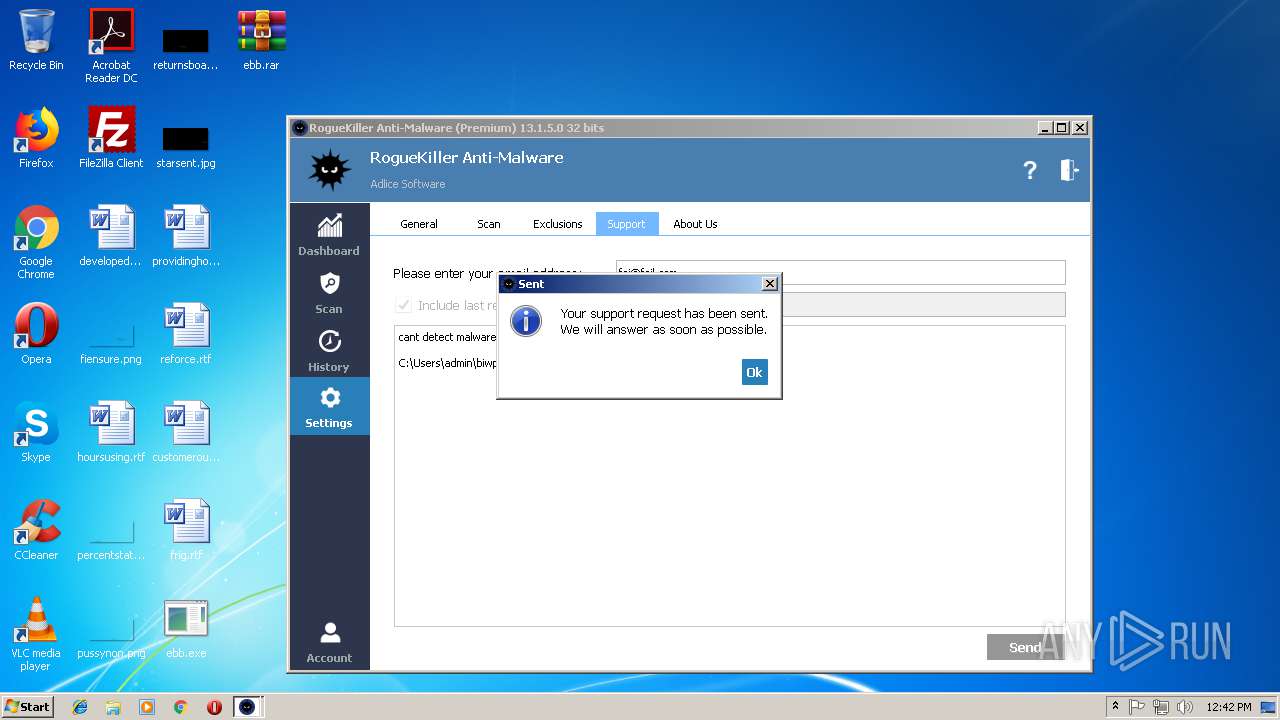
Application was dropped or rewritten from another process
- RogueKiller_portable32.exe (PID: 3396)
- RogueKiller_portable32.exe (PID: 3584)
Actions looks like stealing of personal data
- vbc.exe (PID: 4028)
- vbc.exe (PID: 3372)
- vbc.exe (PID: 3004)
- vbc.exe (PID: 2144)
- vbc.exe (PID: 4076)
- vbc.exe (PID: 3396)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 3868)
- vbc.exe (PID: 1324)
- vbc.exe (PID: 700)
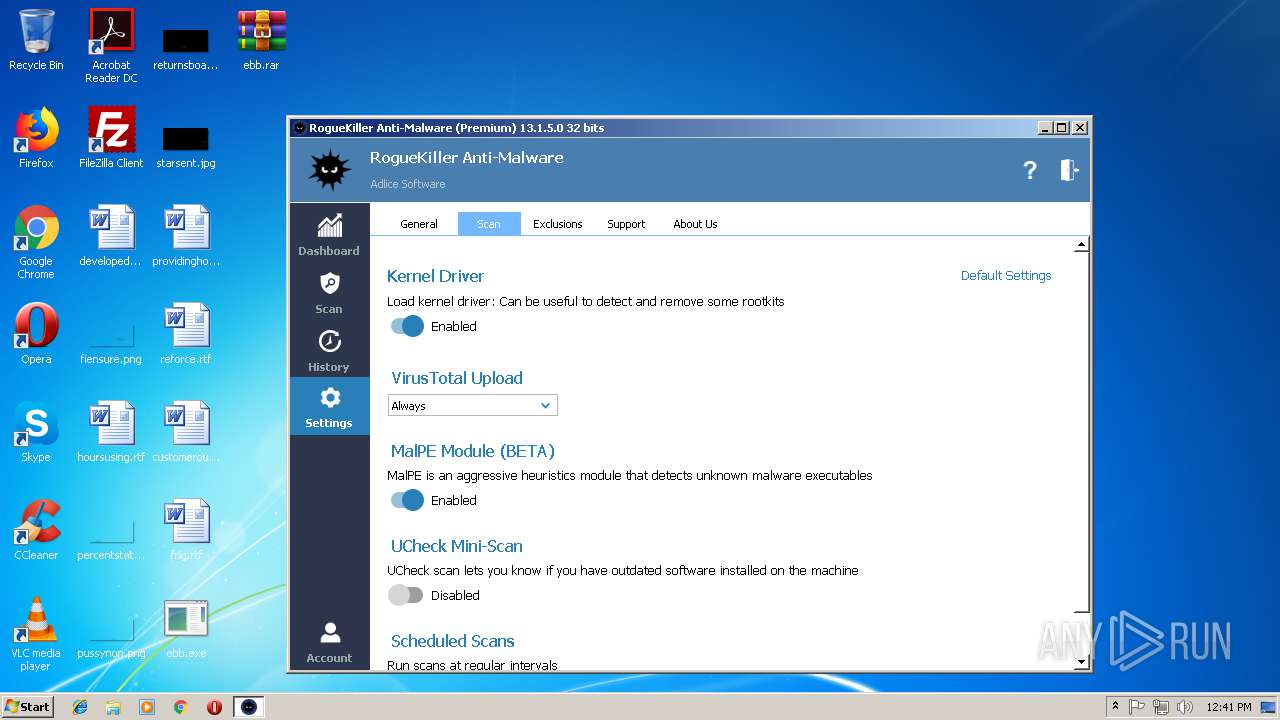
Loads the Task Scheduler DLL interface
- RogueKiller_portable32.exe (PID: 3584)
SUSPICIOUS
Executes scripts
- RegAsm.exe (PID: 3024)
- RegAsm.exe (PID: 2188)
- RegAsm.exe (PID: 3264)
- RegAsm.exe (PID: 2920)
- RegAsm.exe (PID: 2108)
Executable content was dropped or overwritten
- ebb.exe (PID: 3680)
- chrome.exe (PID: 2980)
- RogueKiller_portable32.exe (PID: 3584)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 4028)
- vbc.exe (PID: 3004)
- vbc.exe (PID: 3396)
- vbc.exe (PID: 2564)
- vbc.exe (PID: 1324)
Low-level read access rights to disk partition
- RogueKiller_portable32.exe (PID: 3584)
Reads Internet Cache Settings
- RogueKiller_portable32.exe (PID: 3584)
Creates files in the program directory
- RogueKiller_portable32.exe (PID: 3584)
Connects to SMTP port
- RegAsm.exe (PID: 3024)
- RegAsm.exe (PID: 3264)
- RegAsm.exe (PID: 2188)
- RegAsm.exe (PID: 2920)
- RegAsm.exe (PID: 2108)
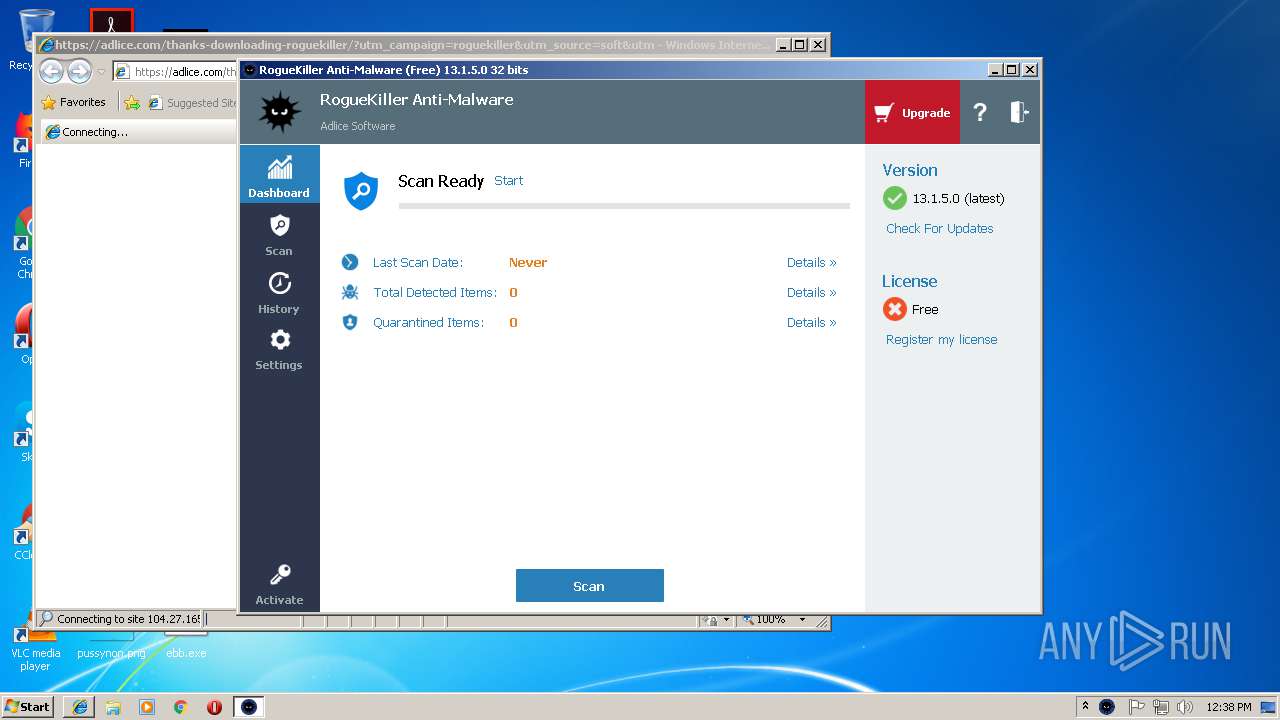
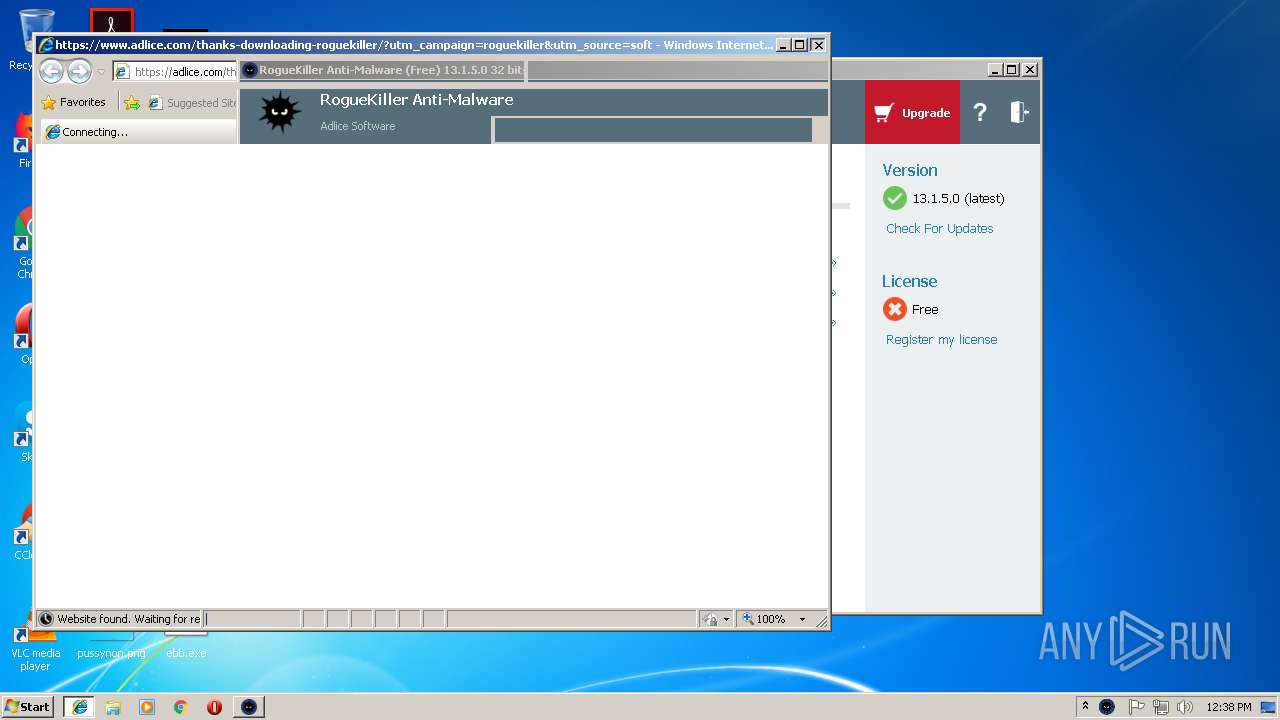
Starts Internet Explorer
- RogueKiller_portable32.exe (PID: 3584)
Creates or modifies windows services
- RogueKiller_portable32.exe (PID: 3584)
Creates files in the driver directory
- RogueKiller_portable32.exe (PID: 3584)
Creates files in the Windows directory
- RogueKiller_portable32.exe (PID: 3584)
Removes files from Windows directory
- RogueKiller_portable32.exe (PID: 3584)
INFO
Application launched itself
- chrome.exe (PID: 2980)
Reads settings of System Certificates
- chrome.exe (PID: 2980)
- RogueKiller_portable32.exe (PID: 3584)
Reads Internet Cache Settings
- chrome.exe (PID: 2980)
Changes internet zones settings
- iexplore.exe (PID: 2932)
Creates files in the user directory
- iexplore.exe (PID: 2644)
Reads internet explorer settings
- iexplore.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:17 20:42:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 1453056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Feb-2019 19:42:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Feb-2019 19:42:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x001269E0 | 0x00126A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49084 |
.reloc | 0x001EF000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 3.65355 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 3.43704 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 4.16139 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 4.07494 | 2216 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 2.18302 | 1384 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
87
Monitored processes
41
Malicious processes
17
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Windows\System32\schtasks.exe" /create /tn rstrui /tr "C:\Users\admin\bi\wpnpinst.exe" /sc minute /mo 1 /F | C:\Windows\System32\schtasks.exe | — | wpnpinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 700 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp4941.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 1324 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp4549.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2056 | C:\Users\admin\bi\wpnpinst.exe | C:\Users\admin\bi\wpnpinst.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2108 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | wpnpinst.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2144 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp8A8F.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2188 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | wpnpinst.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,17491939788117469754,1978106703392745970,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=C86A6AF3BE27C0260FCAC38D36BD6641 --mojo-platform-channel-handle=3744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,17491939788117469754,1978106703392745970,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3BBD3ED4BB489F7874E1E5219D8A54BC --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3BBD3ED4BB489F7874E1E5219D8A54BC --renderer-client-id=6 --mojo-platform-channel-handle=3212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2392 | "C:\Windows\System32\schtasks.exe" /create /tn rstrui /tr "C:\Users\admin\bi\wpnpinst.exe" /sc minute /mo 1 /F | C:\Windows\System32\schtasks.exe | — | wpnpinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 307
Read events
1 991
Write events
308
Delete events
8
Modification events
| (PID) Process: | (3680) ebb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3680) ebb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2980-13194967102858625 |
Value: 259 | |||
Executable files
4
Suspicious files
87
Text files
87
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5acea9bb-8ec6-45e5-a9fa-f305db4764f4.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
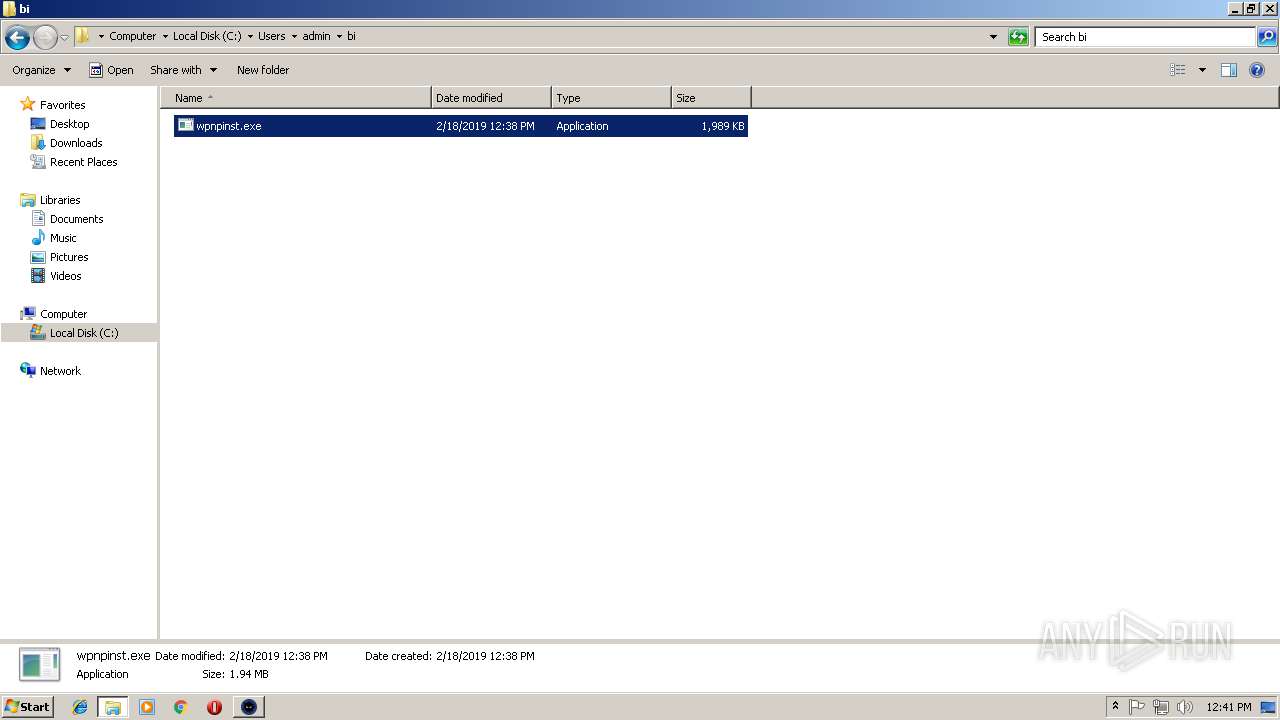
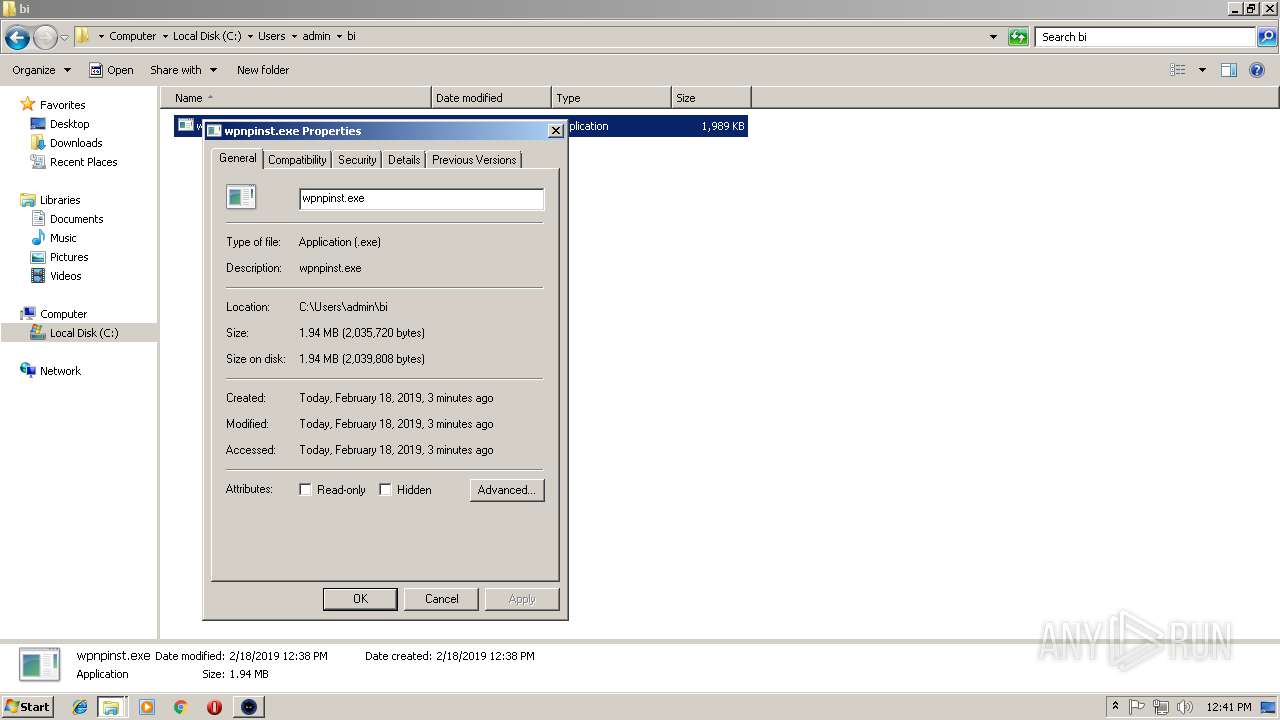
| 3680 | ebb.exe | C:\Users\admin\bi\wpnpinst.exe | executable | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19cba3.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
50
DNS requests
27
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3264 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 12 b | shared |
2188 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 12 b | shared |
2920 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 12 b | shared |
2932 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2108 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 12 b | shared |
3024 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 12 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.22.35:443 | www.google.de | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.nl |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3024 | RegAsm.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Request (HawkEye) |
2188 | RegAsm.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Request (HawkEye) |
3264 | RegAsm.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Request (HawkEye) |
2920 | RegAsm.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Request (HawkEye) |
2108 | RegAsm.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Request (HawkEye) |
10 ETPRO signatures available at the full report
Process | Message |
|---|---|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|