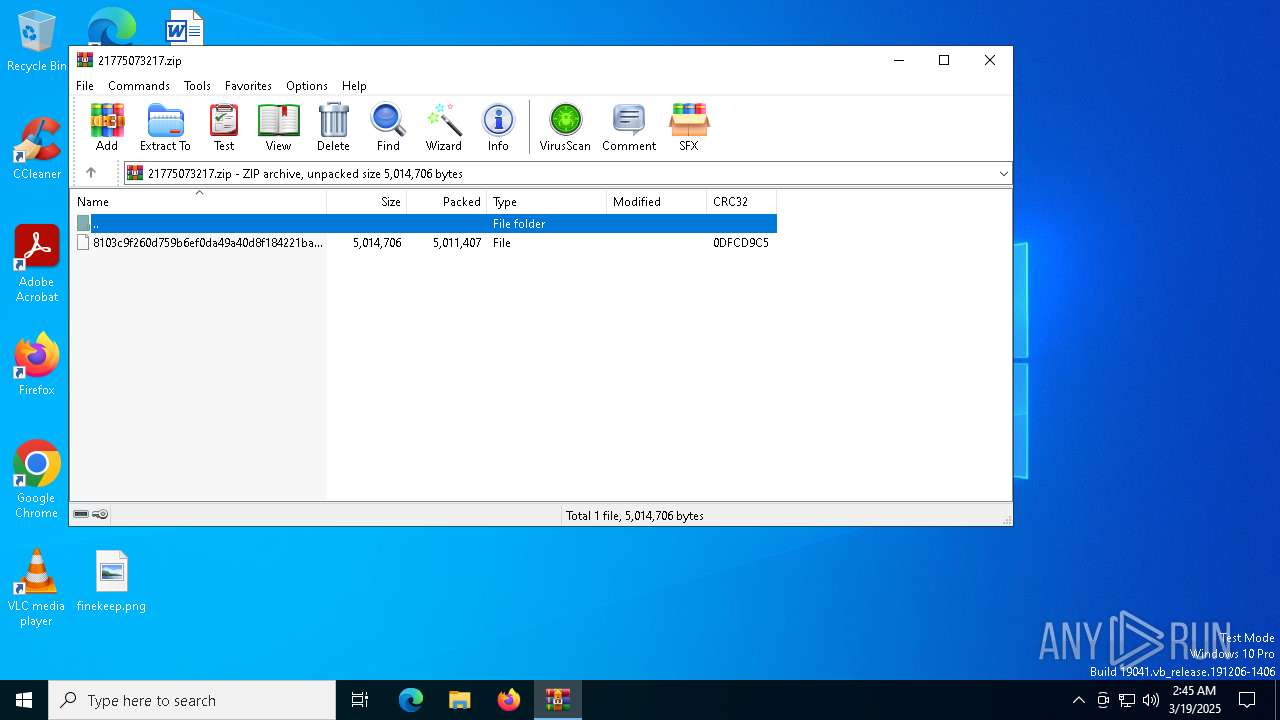
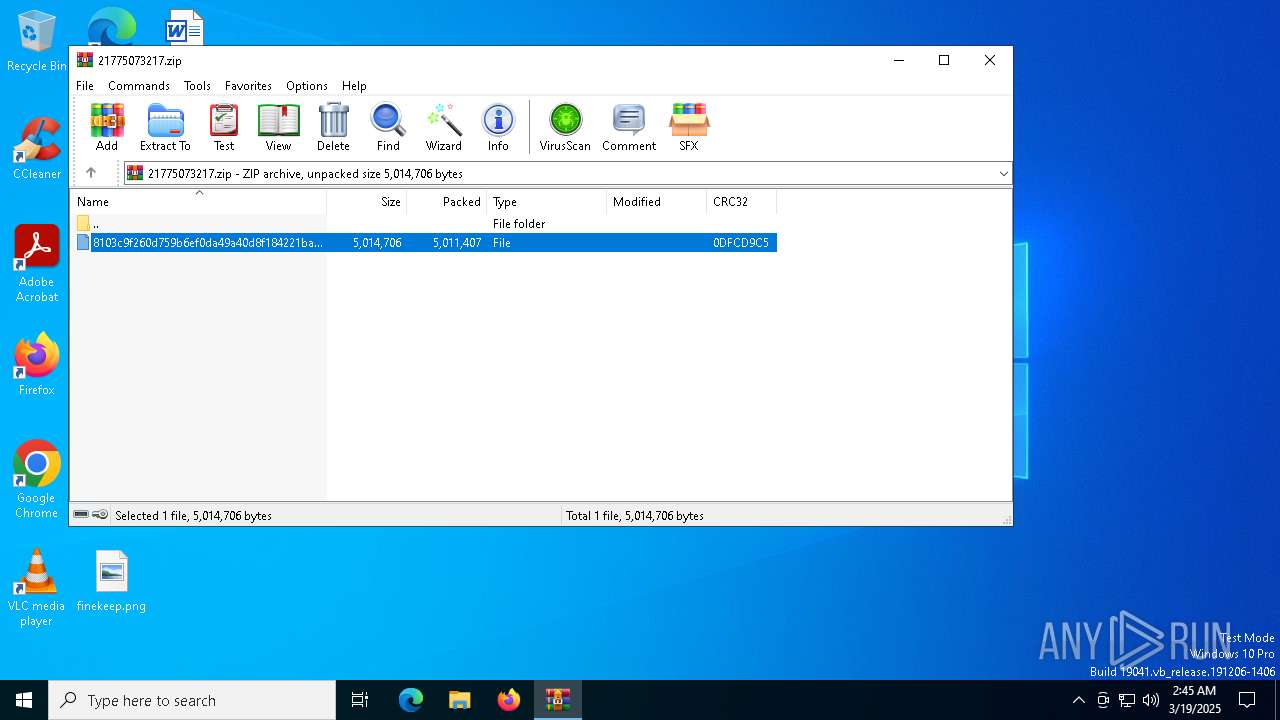
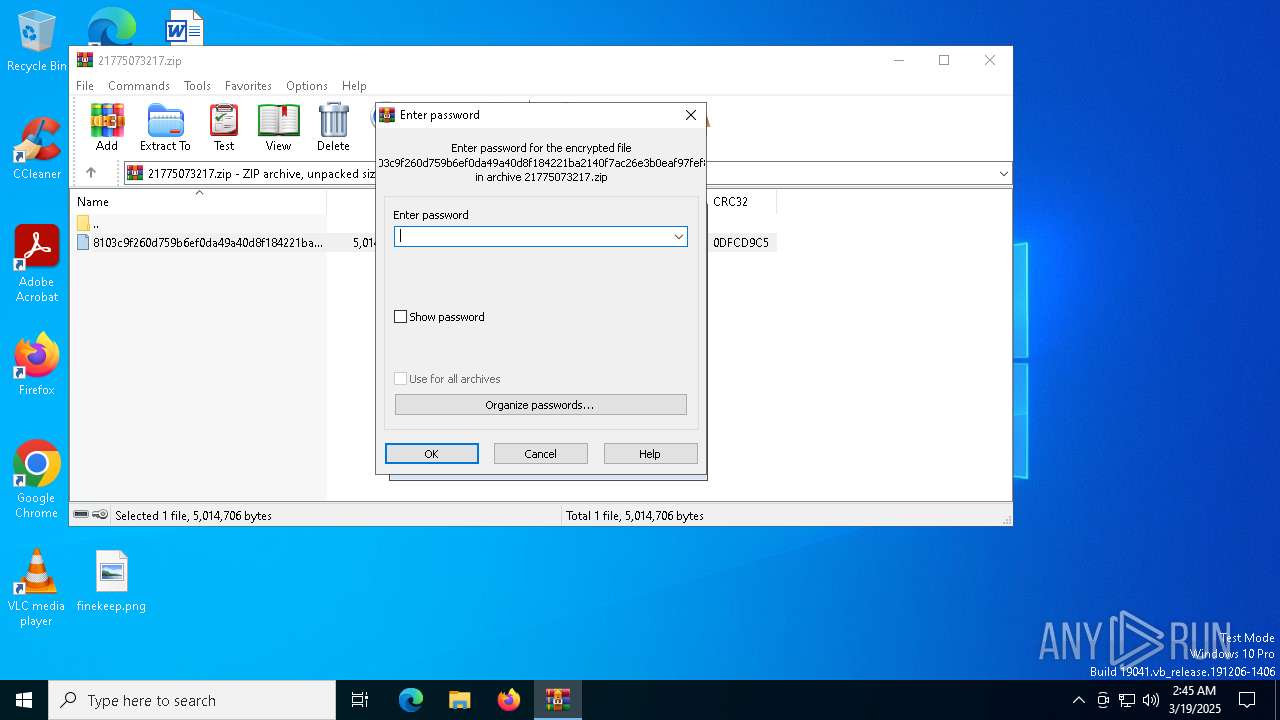
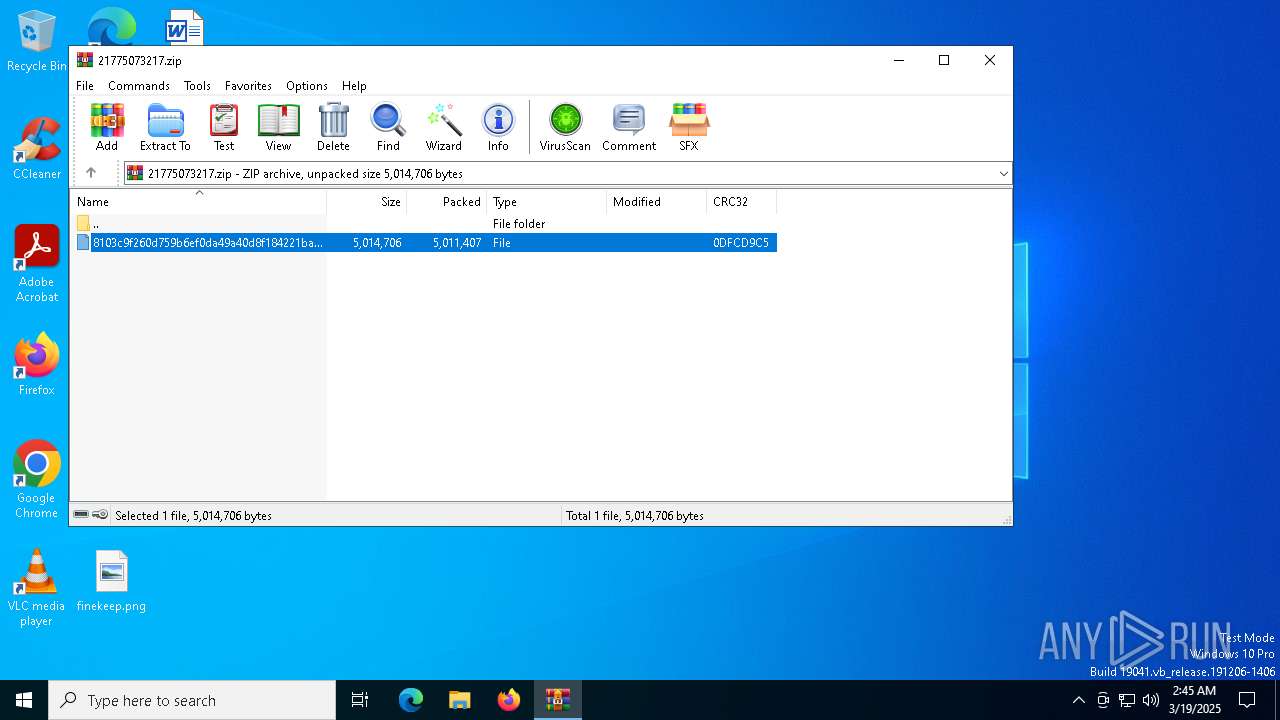
| File name: | 21775073217.zip |
| Full analysis: | https://app.any.run/tasks/91121863-4ec6-4e73-9008-3a185bd841f8 |
| Verdict: | Malicious activity |
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | March 19, 2025, 02:45:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
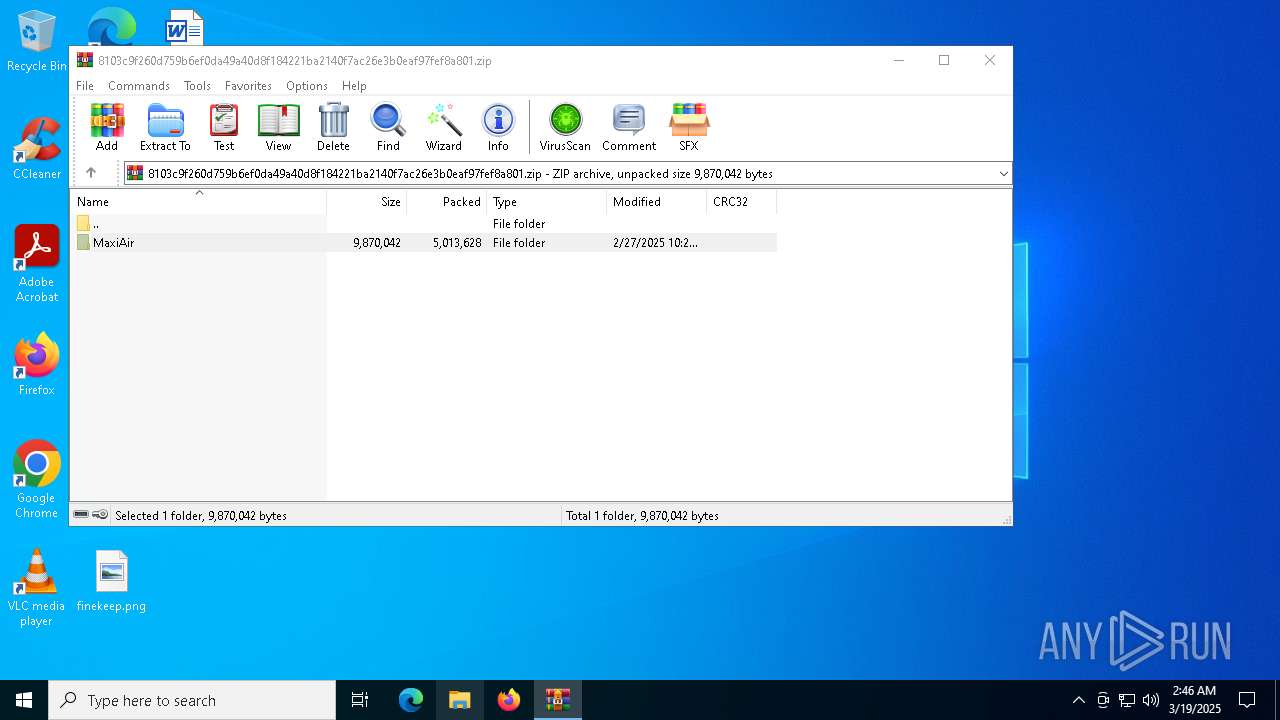
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 962A014E14574F1F5EEFF407856CC901 |
| SHA1: | CA71D5BA61AC8355A0FA1AB341F45204800E66C8 |
| SHA256: | 7E2621900840A97F733F65B32C2317FD3AD2043C08BF07A6E7F609BAA643EA19 |
| SSDEEP: | 98304:z3+9SIQQHNwL6vzQhY7CNNj7z8o87TKk2sDtPyn518a3uNO5Kc+/0Qu7BOCoDGl5:ef8uRE+Cx |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 4920)
XORed URL has been found (YARA)
- MSBuild.exe (PID: 5680)
ARECHCLIENT2 has been detected (YARA)
- MSBuild.exe (PID: 5680)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 5680)
ARECHCLIENT2 has been detected (SURICATA)
- MSBuild.exe (PID: 5680)
SUSPICIOUS
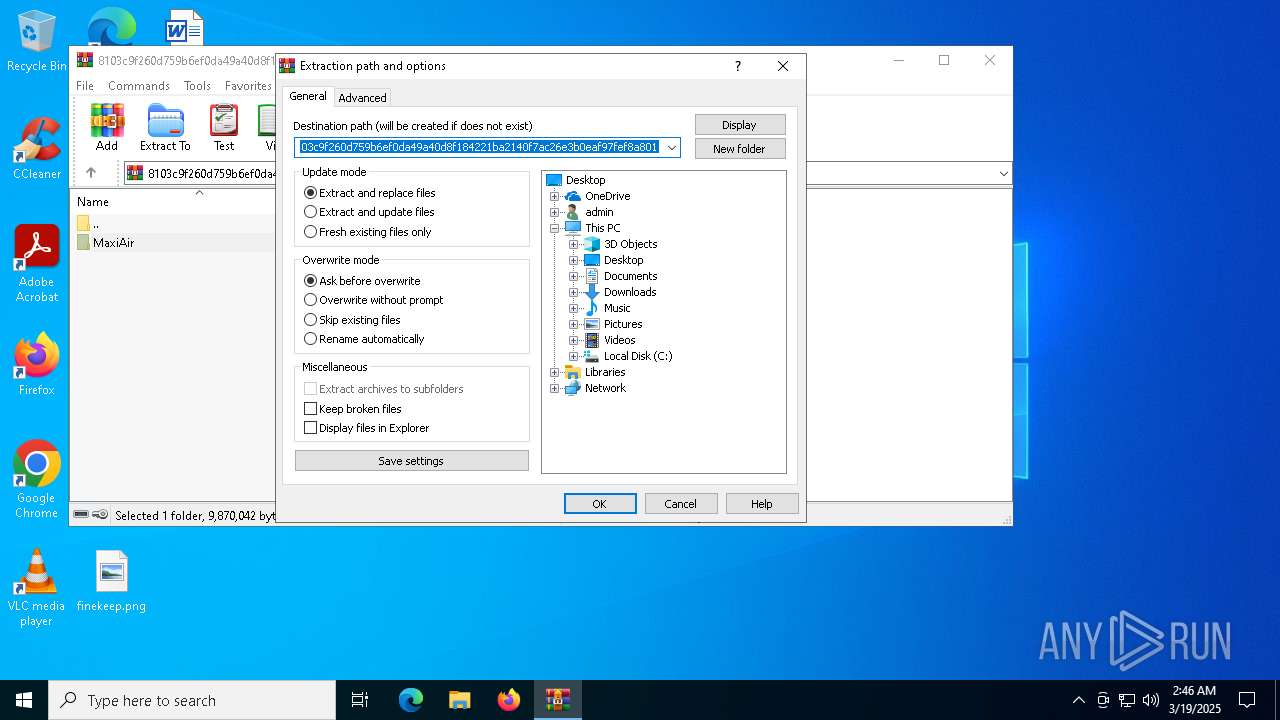
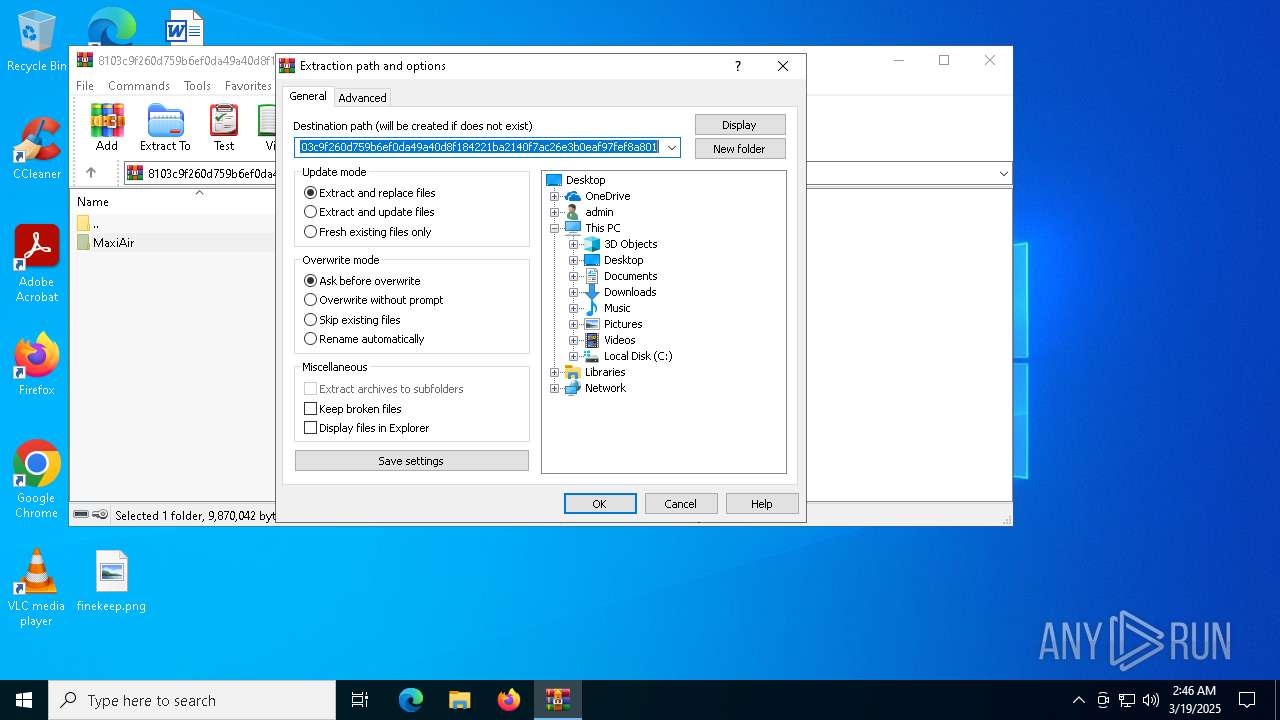
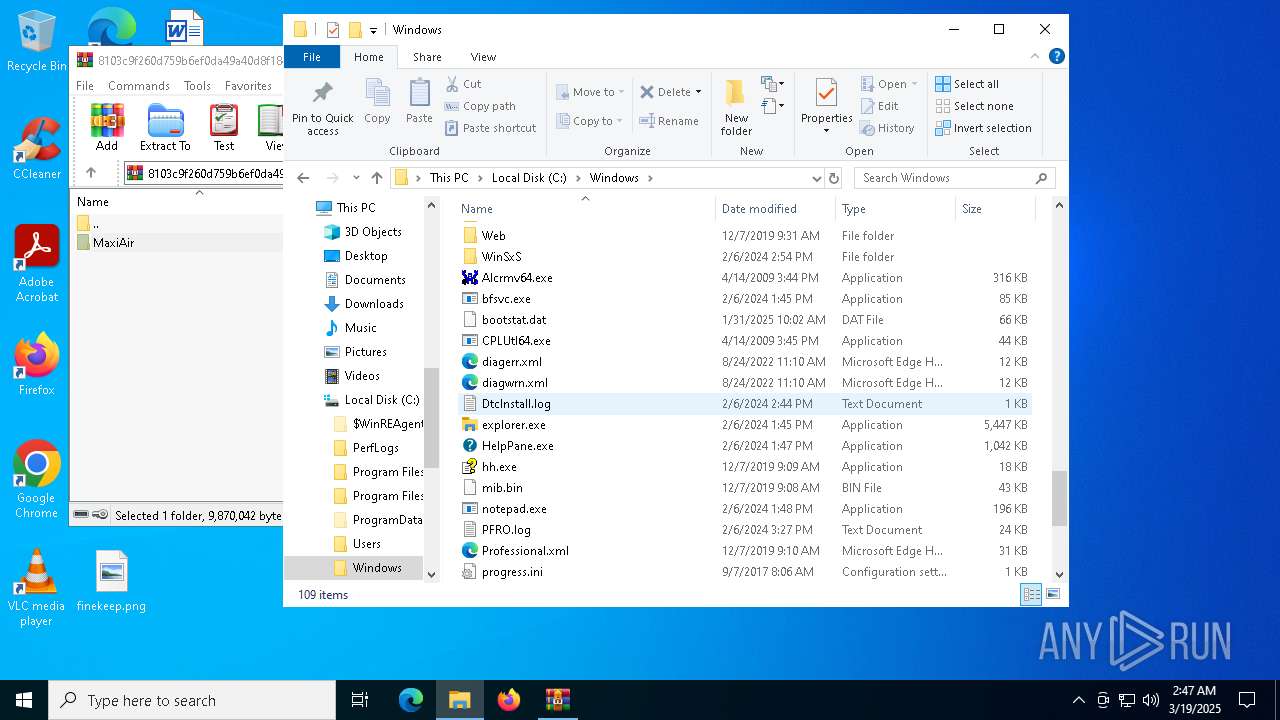
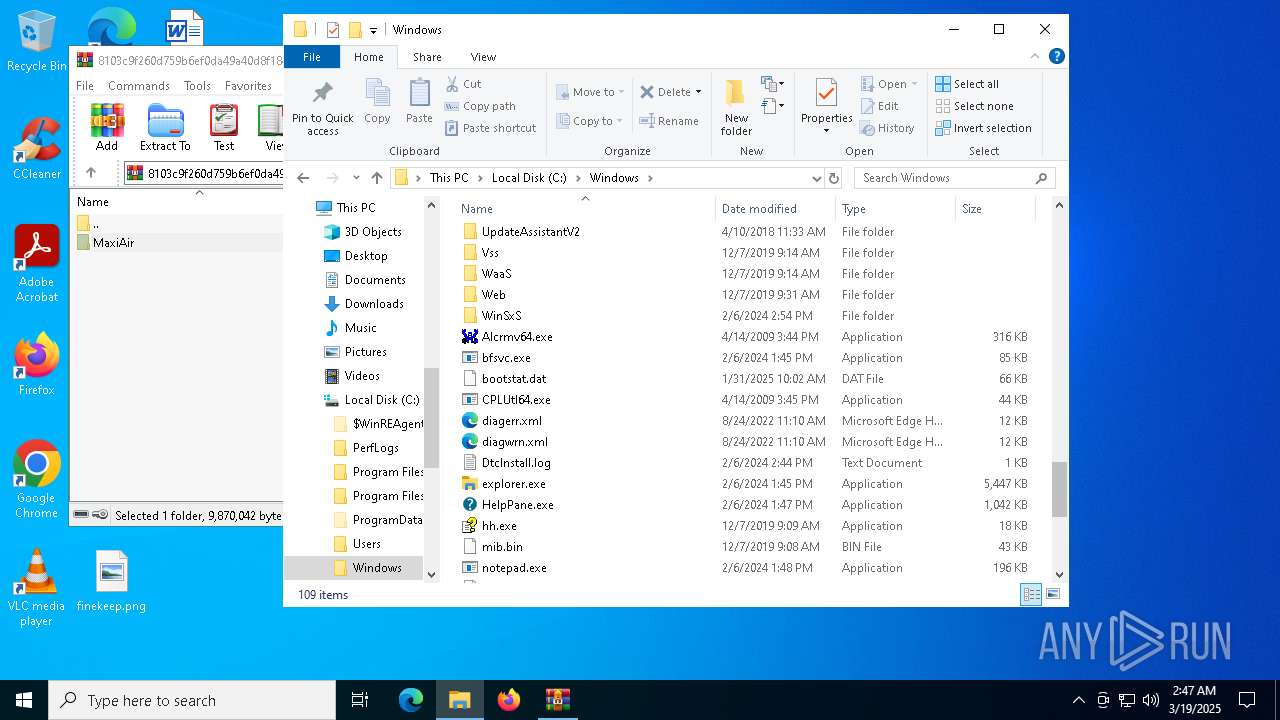
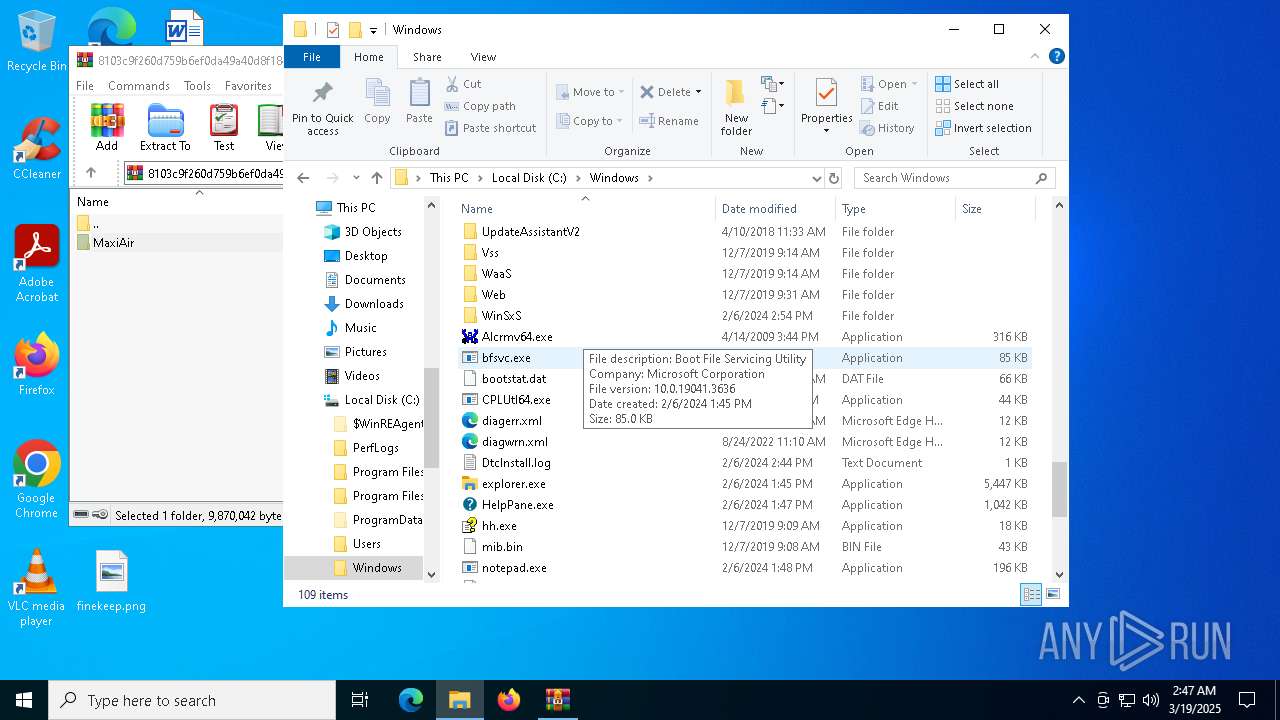
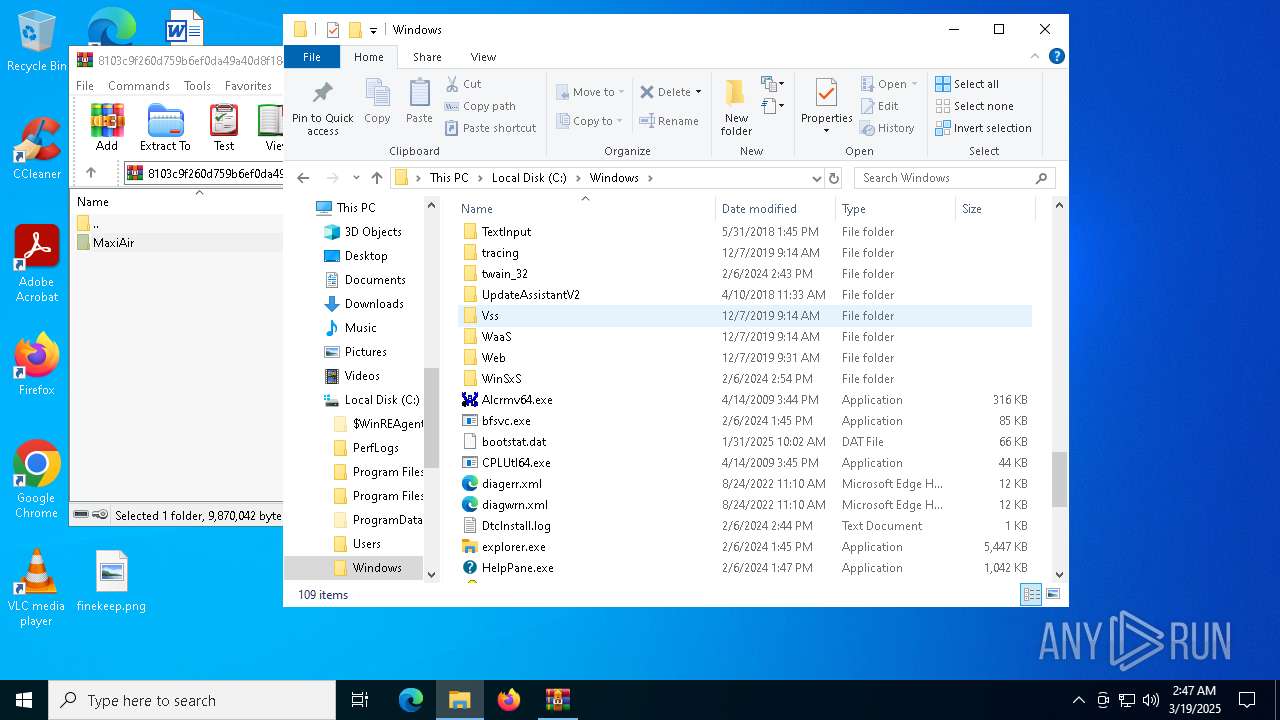
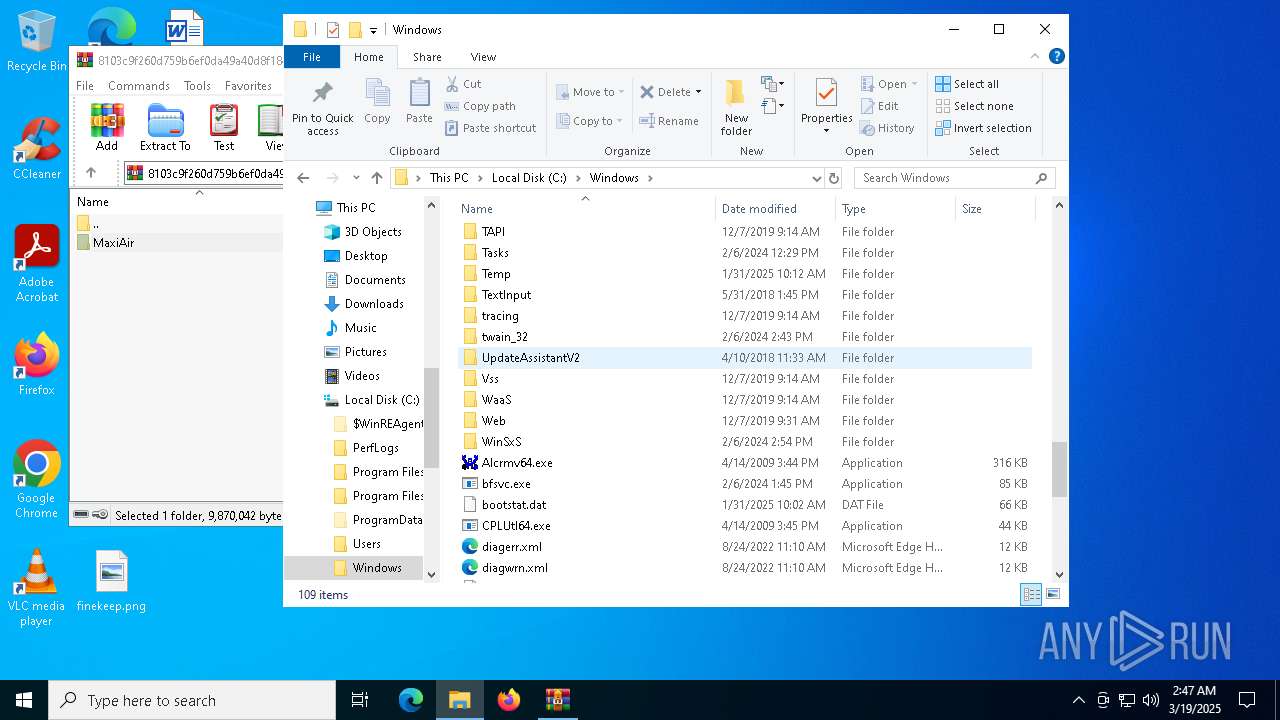
Process drops legitimate windows executable
- WinRAR.exe (PID: 2432)
- WinRAR.exe (PID: 8020)
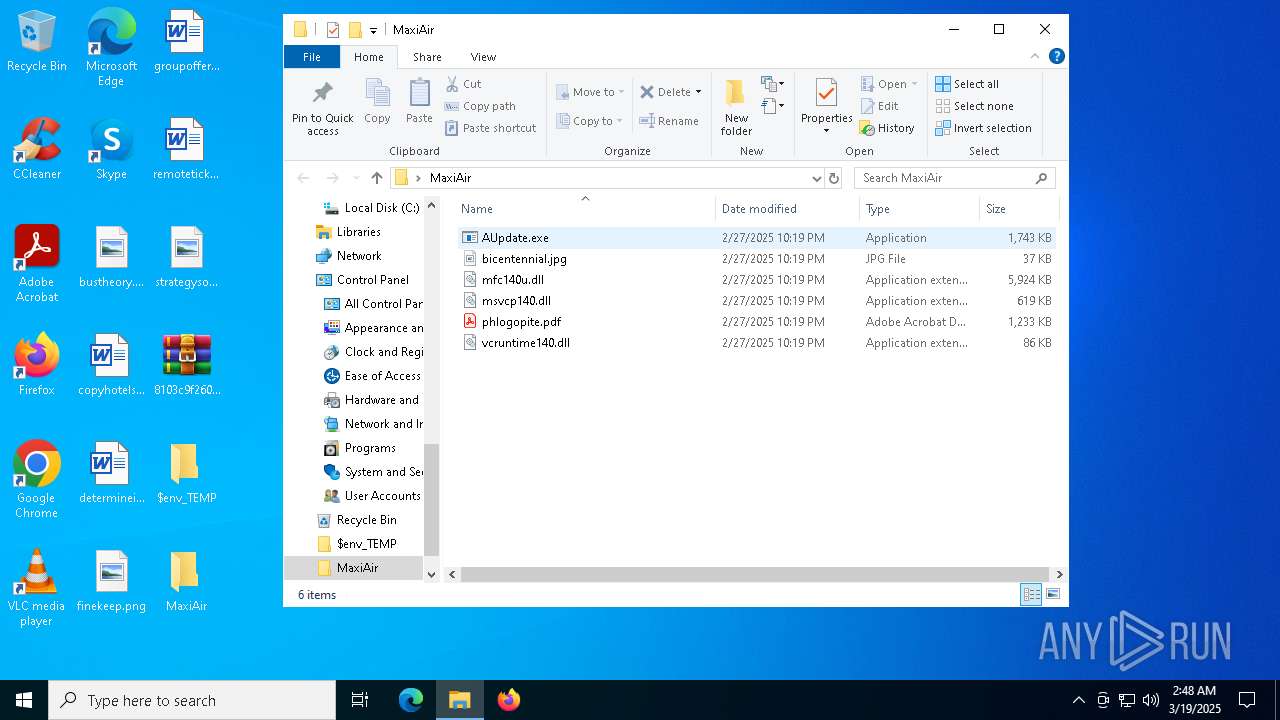
- AUpdate.exe (PID: 7264)
Executable content was dropped or overwritten
- AUpdate.exe (PID: 7264)
The process drops C-runtime libraries
- AUpdate.exe (PID: 7264)
Starts CMD.EXE for commands execution
- AUpdate.exe (PID: 7264)
- AUpdate.exe (PID: 1328)
Connects to unusual port
- MSBuild.exe (PID: 5680)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2432)
- WinRAR.exe (PID: 8020)
- AUpdate.exe (PID: 7264)
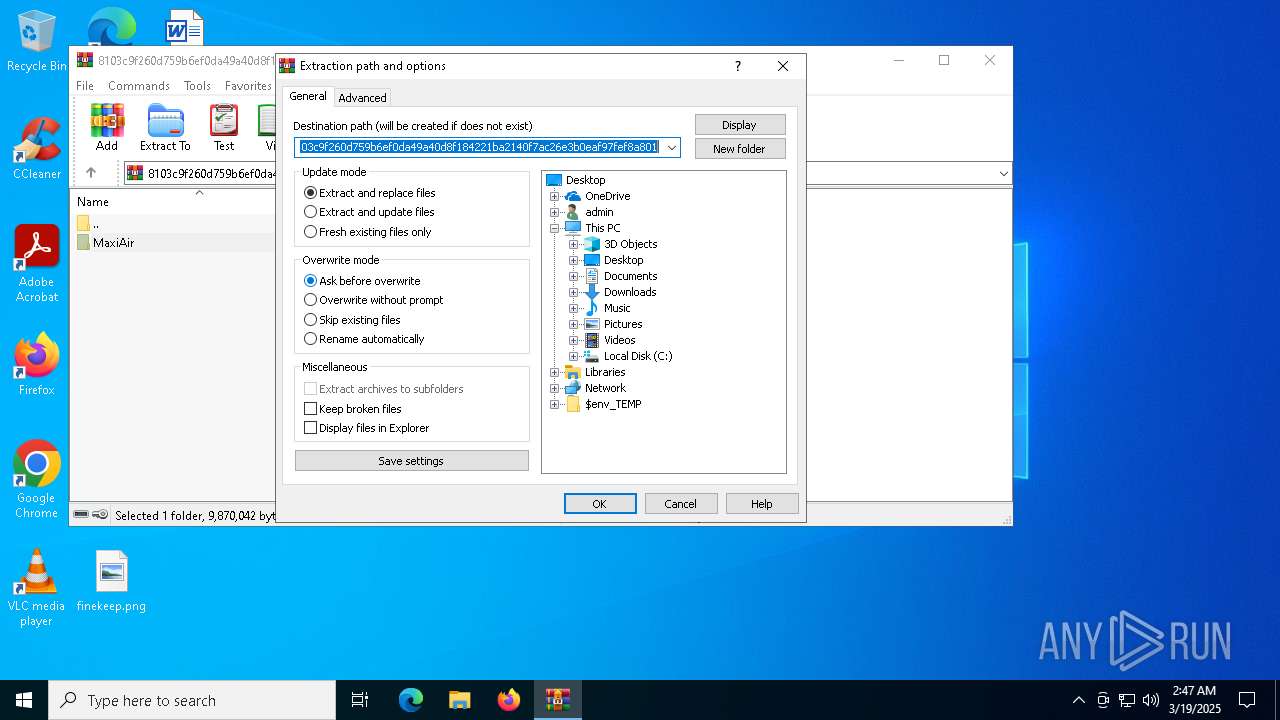
Manual execution by a user
- WinRAR.exe (PID: 8020)
- AUpdate.exe (PID: 7264)
Reads the software policy settings
- slui.exe (PID: 7212)
- slui.exe (PID: 4892)
Checks proxy server information
- slui.exe (PID: 4892)
- MSBuild.exe (PID: 5680)
Checks supported languages
- AUpdate.exe (PID: 7264)
- AUpdate.exe (PID: 1328)
- MSBuild.exe (PID: 5680)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8020)
Reads the computer name
- AUpdate.exe (PID: 7264)
- AUpdate.exe (PID: 1328)
- MSBuild.exe (PID: 5680)
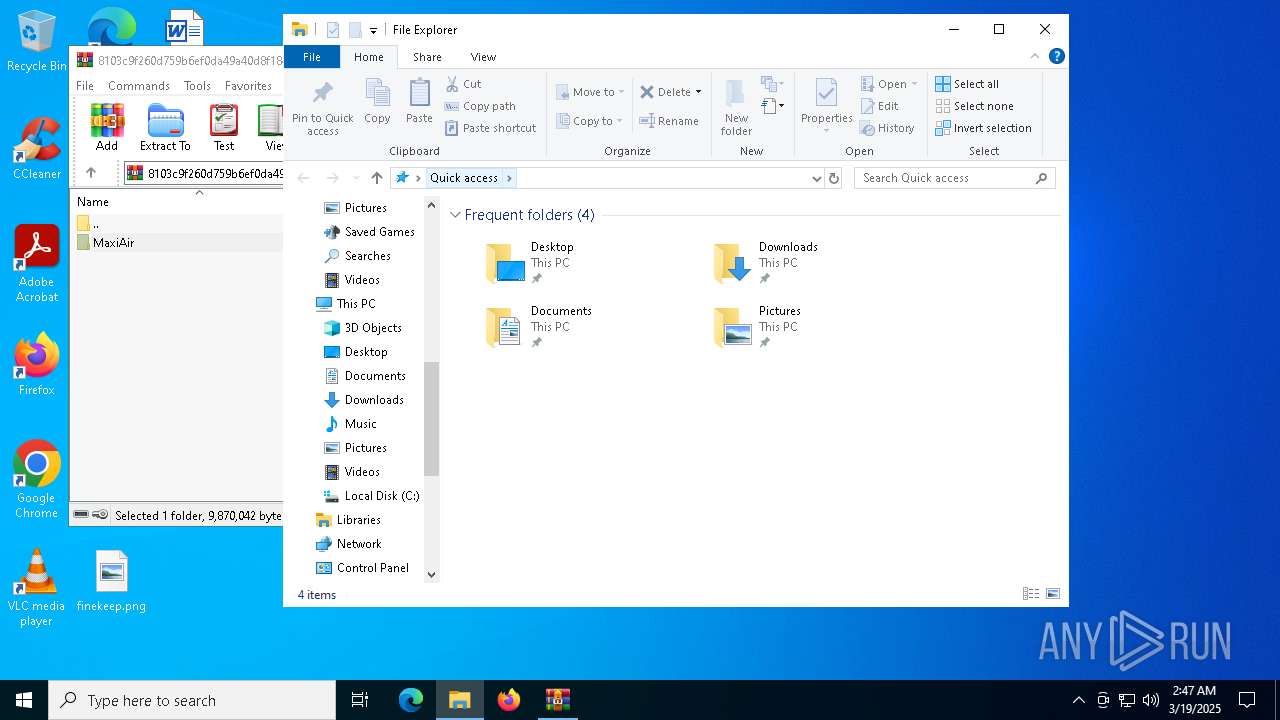
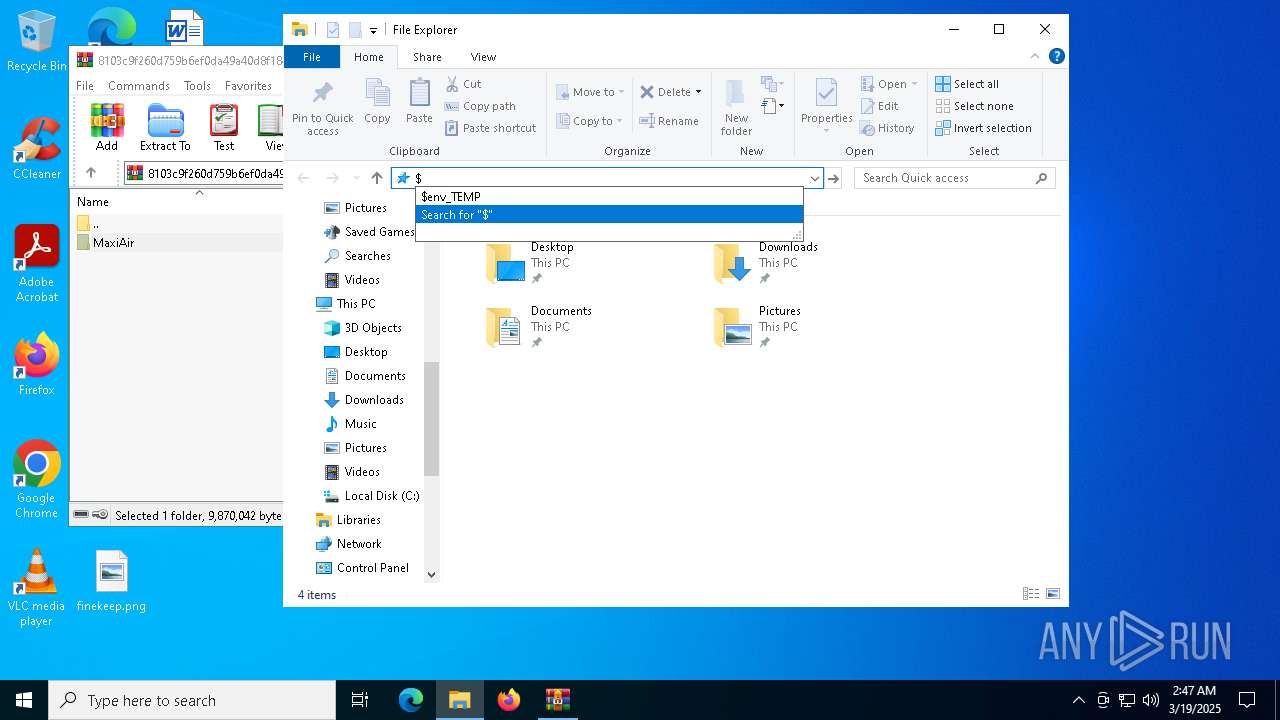
Creates files or folders in the user directory
- AUpdate.exe (PID: 7264)
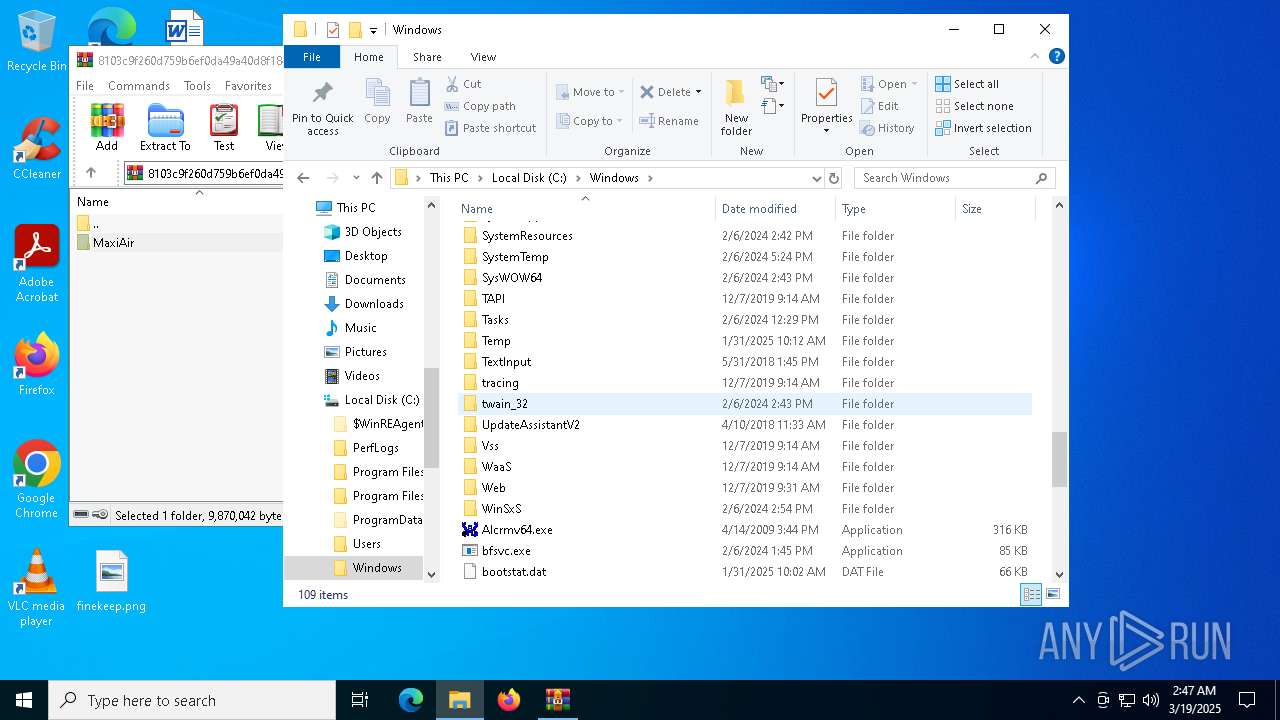
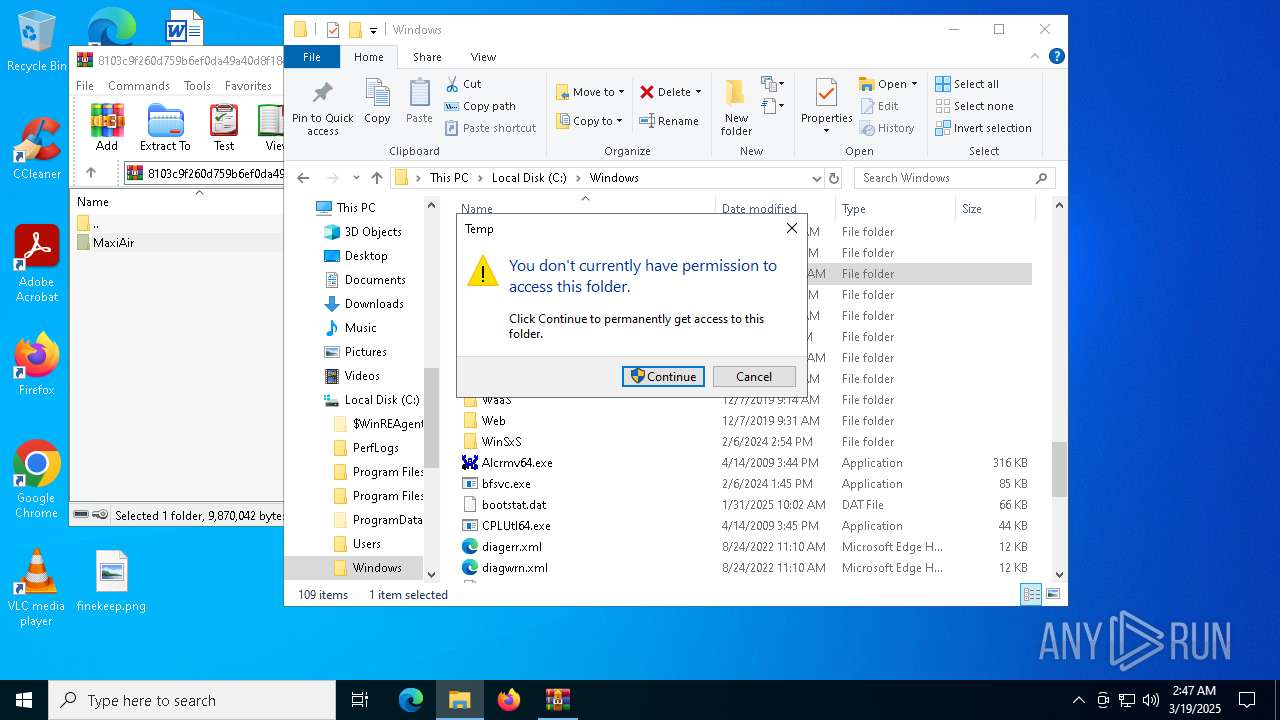
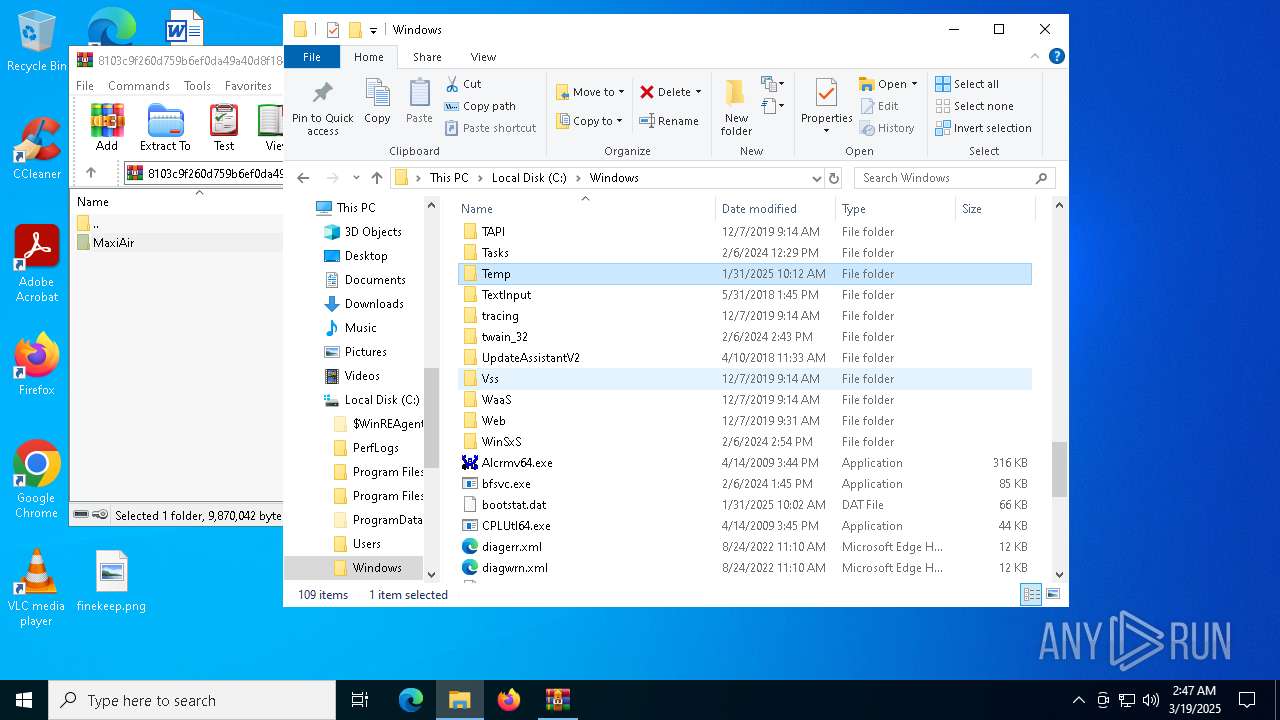
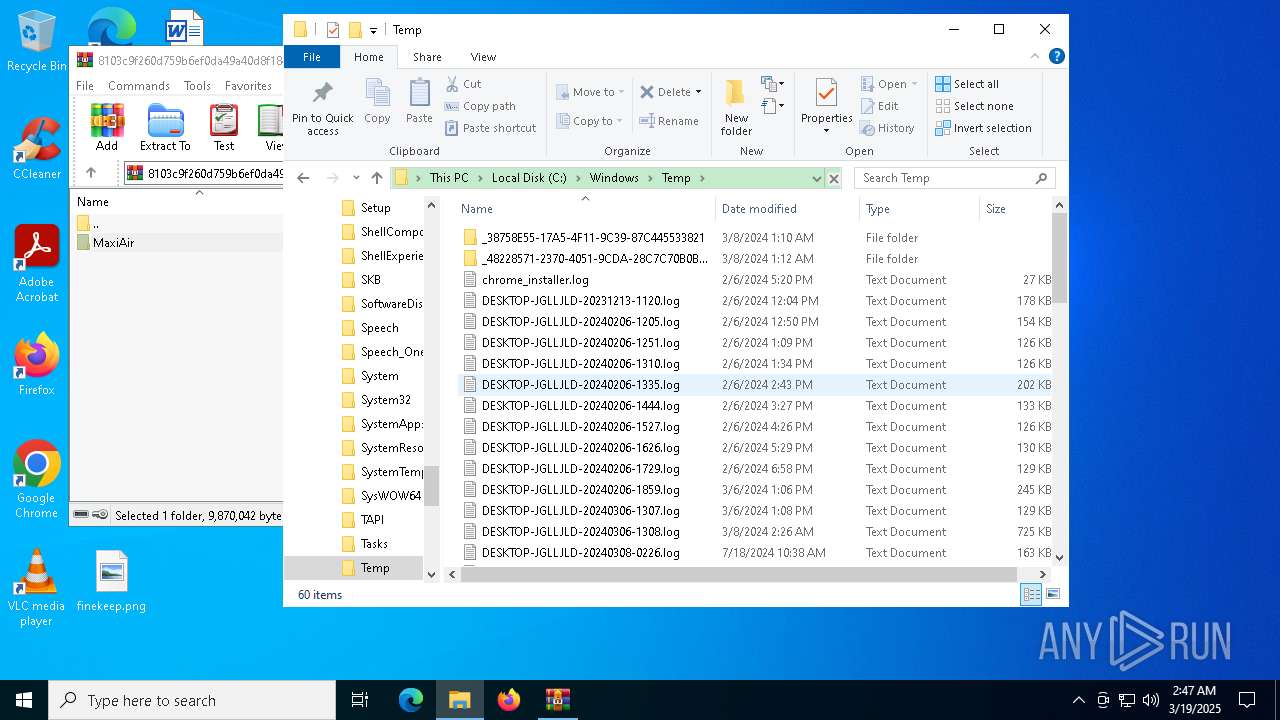
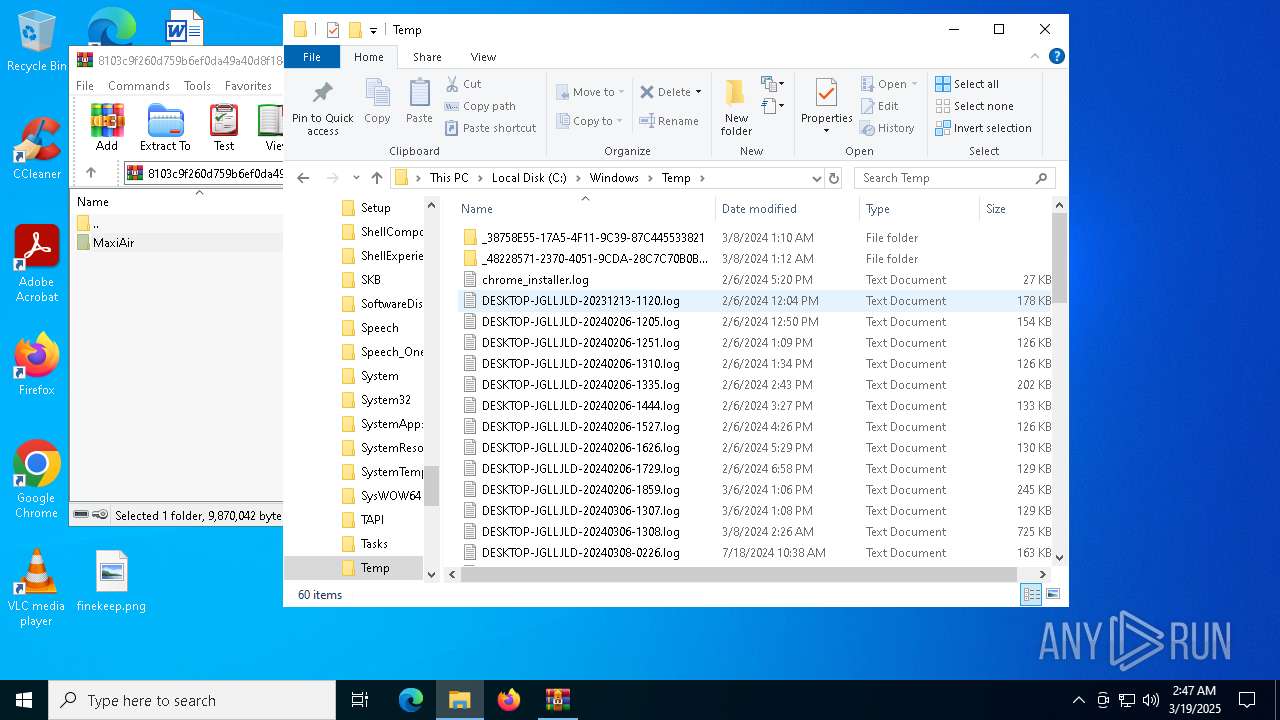
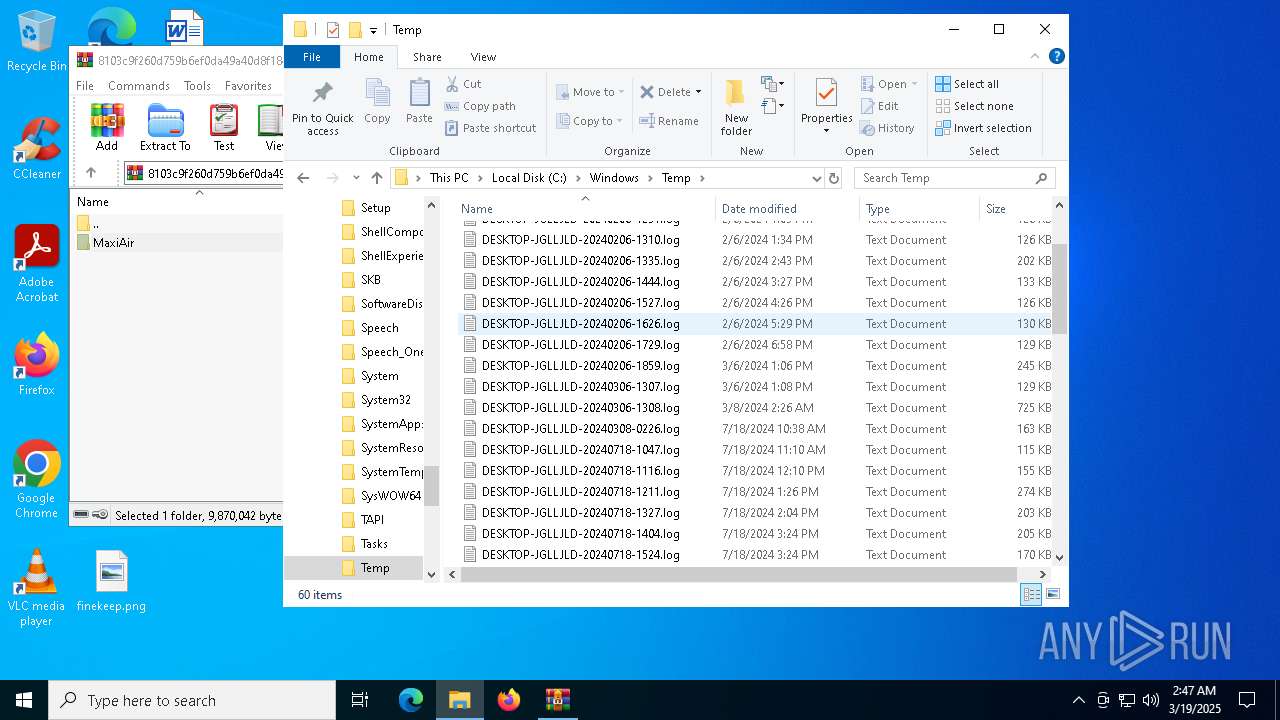
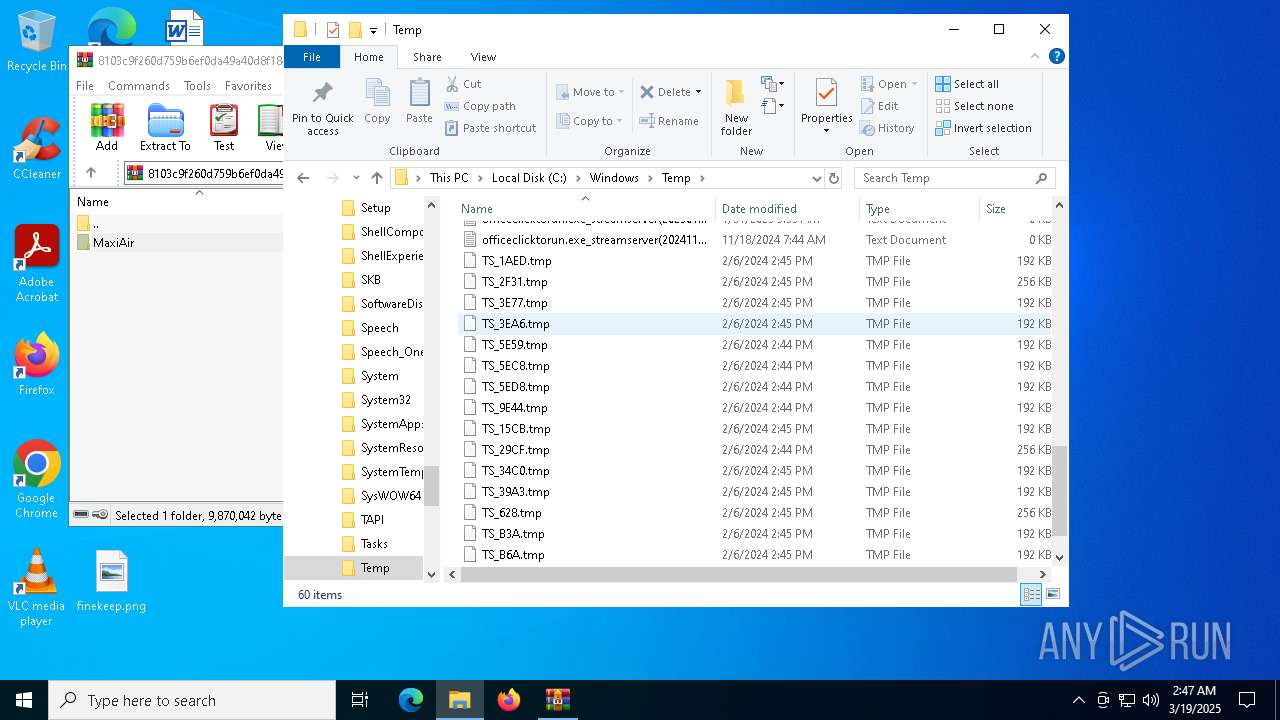
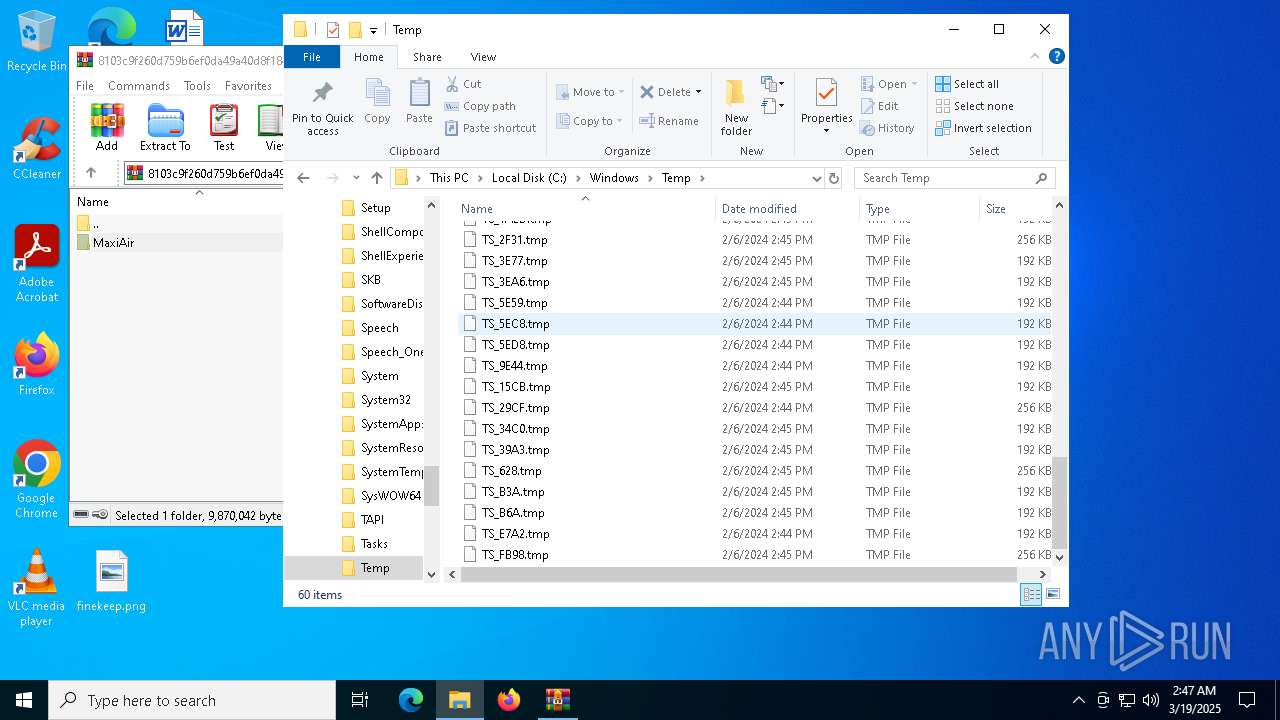
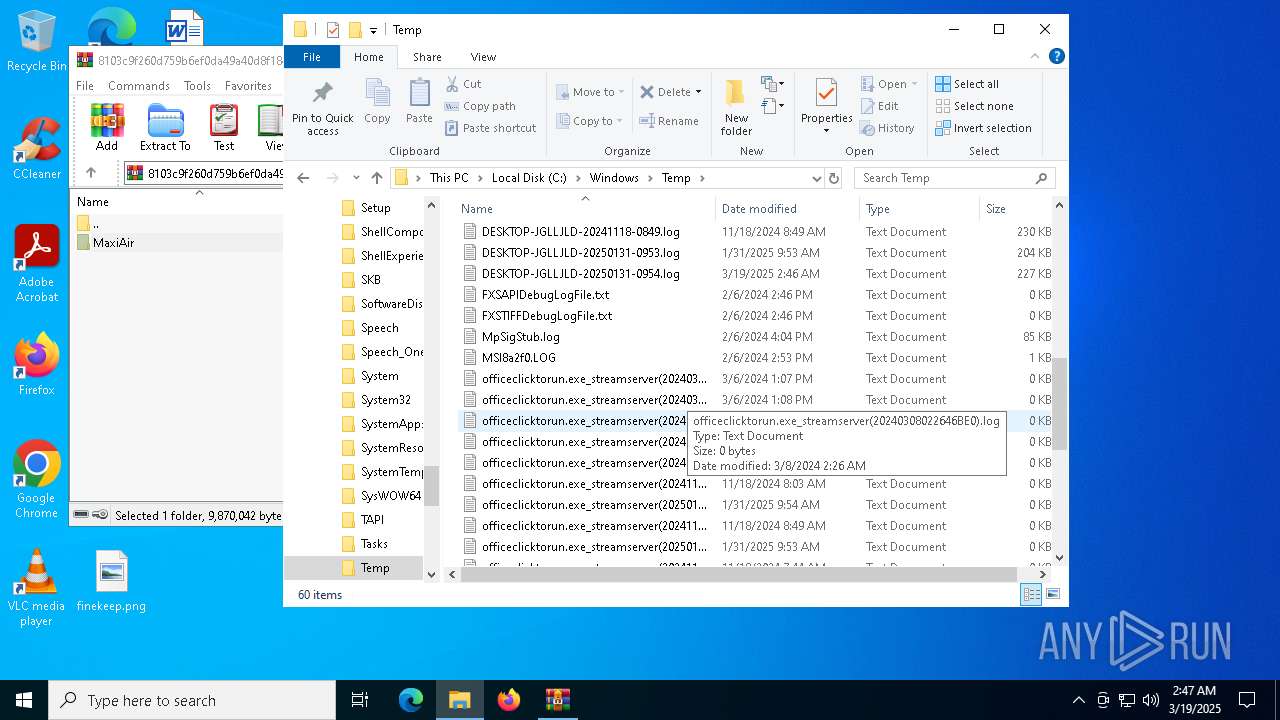
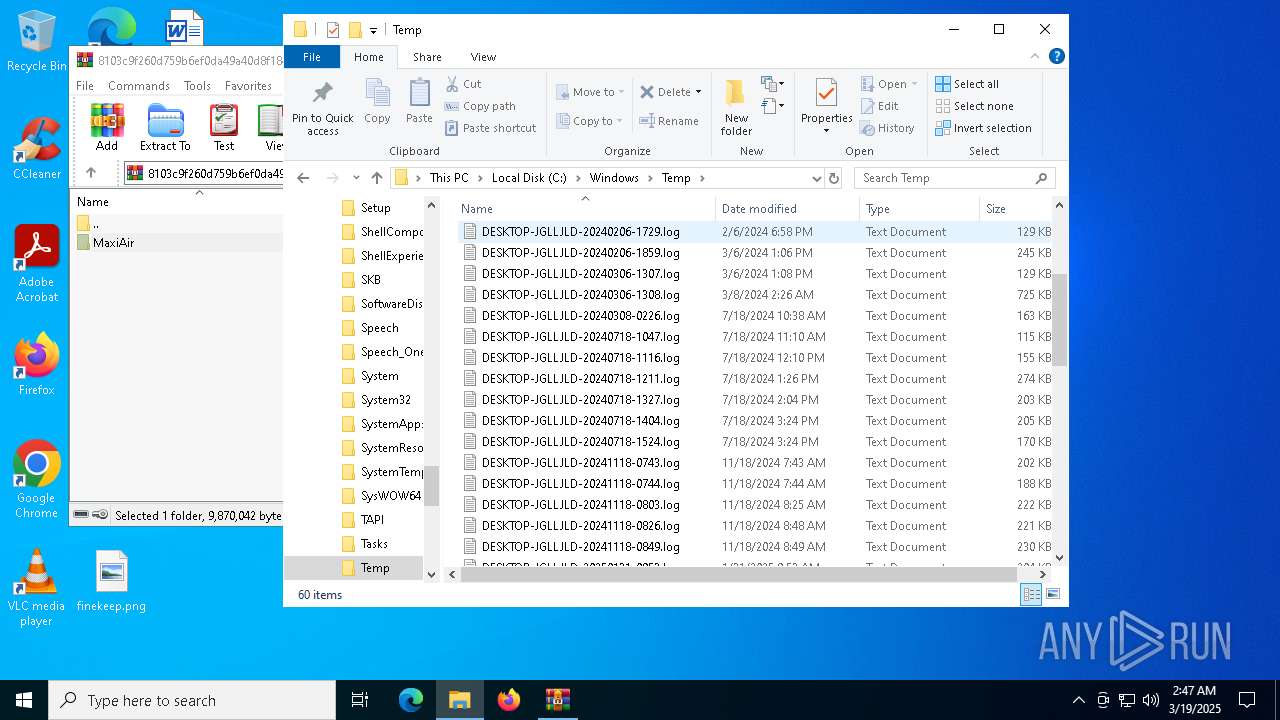
Create files in a temporary directory
- AUpdate.exe (PID: 7264)
- AUpdate.exe (PID: 1328)
- MSBuild.exe (PID: 5680)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 4920)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 5680)
Disables trace logs
- MSBuild.exe (PID: 5680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5680) MSBuild.exe
Decrypted-URLs (3)http://dl.google.com/chrome/install/375.126/chrome_installer.exeb
https://github.com
https://pastebin.com/raw/DWCCqGB0wKo+g
TRiD
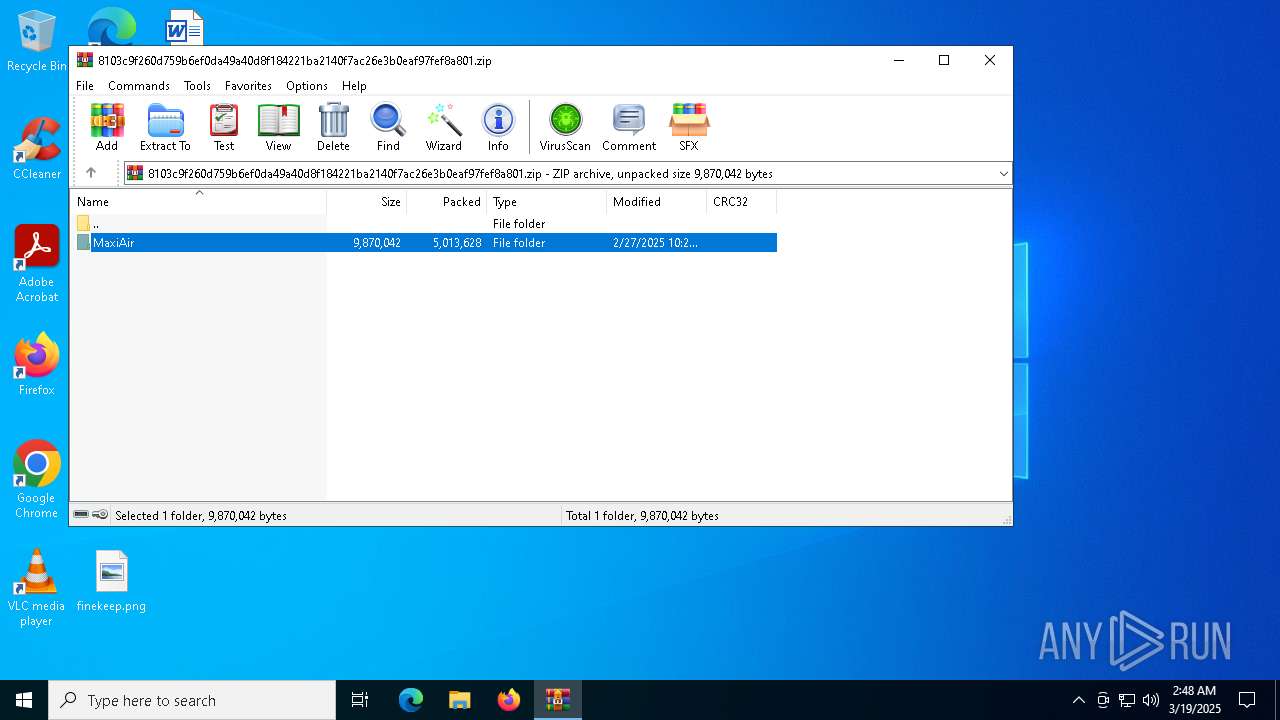
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
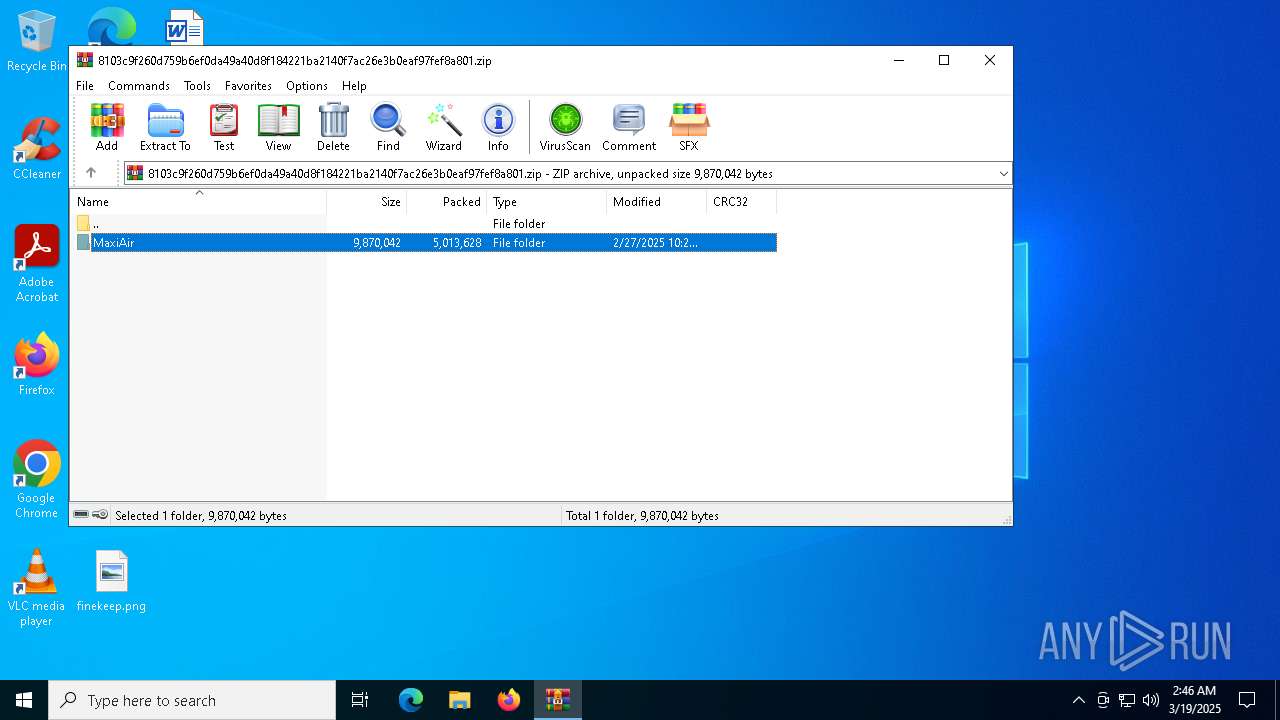
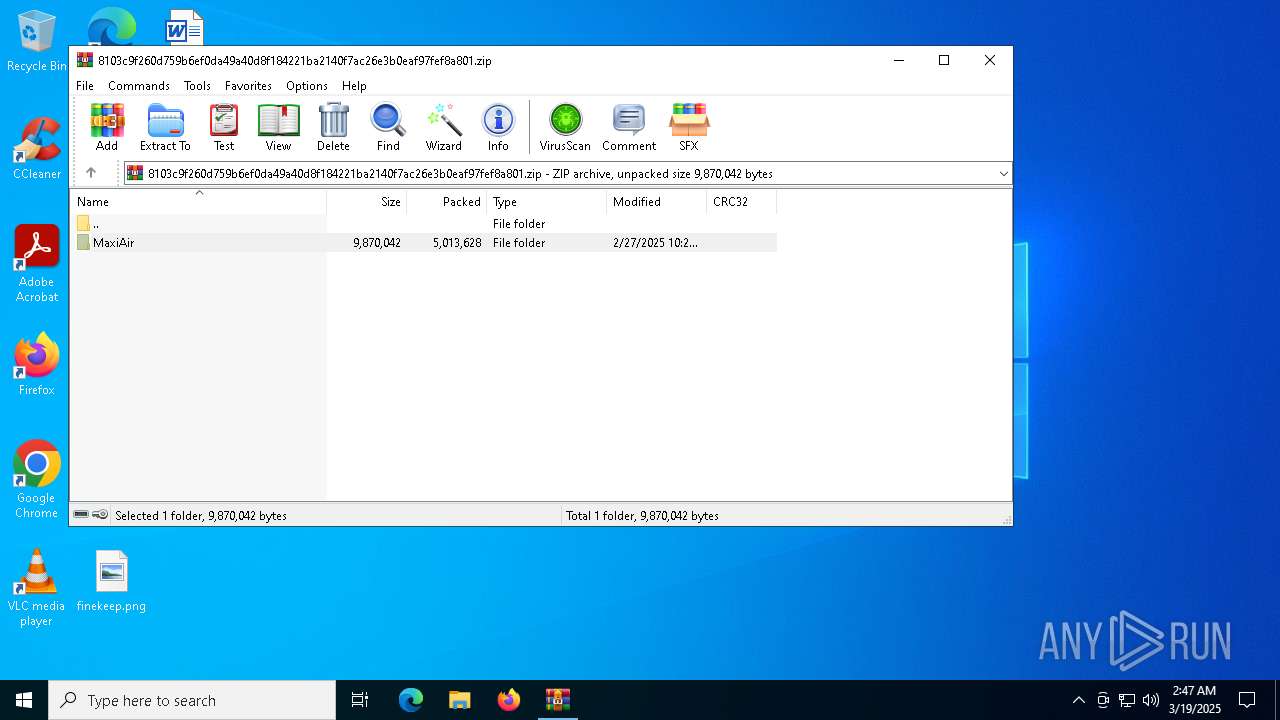
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x0dfcd9c5 |
| ZipCompressedSize: | 5011407 |
| ZipUncompressedSize: | 5014706 |
| ZipFileName: | 8103c9f260d759b6ef0da49a40d8f184221ba2140f7ac26e3b0eaf97fef8a801 |
Total processes
156
Monitored processes
15
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
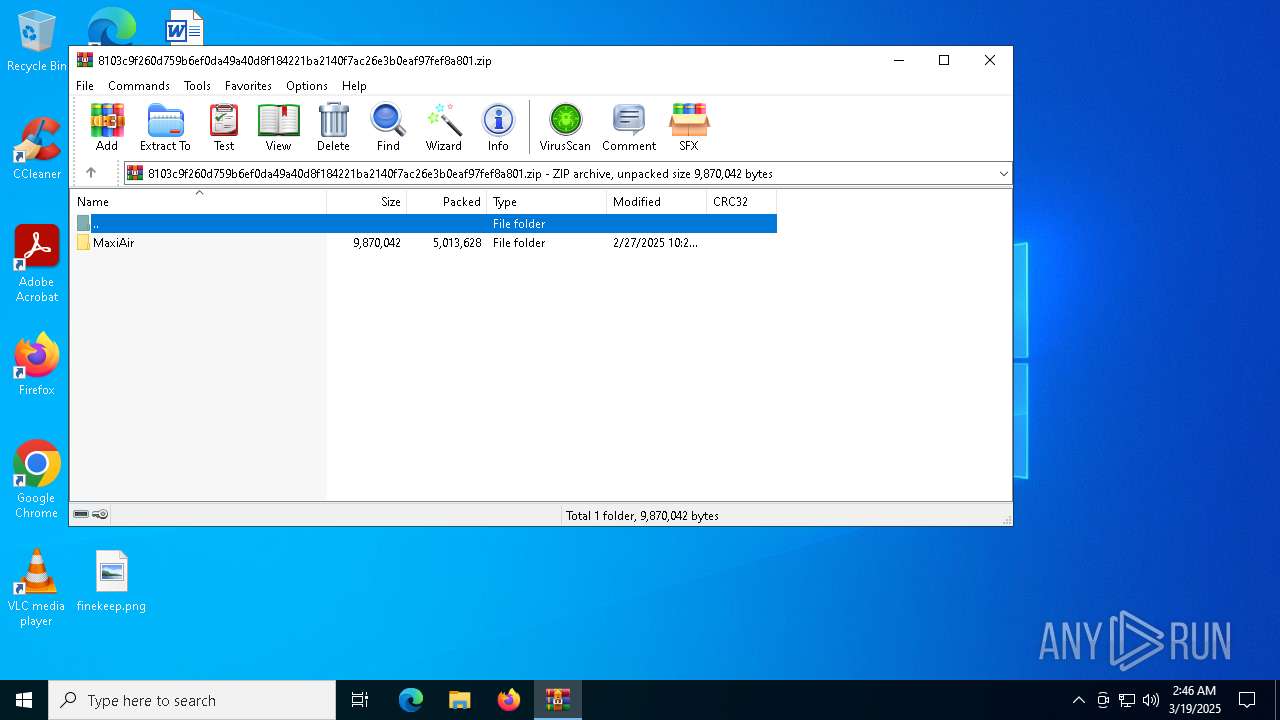
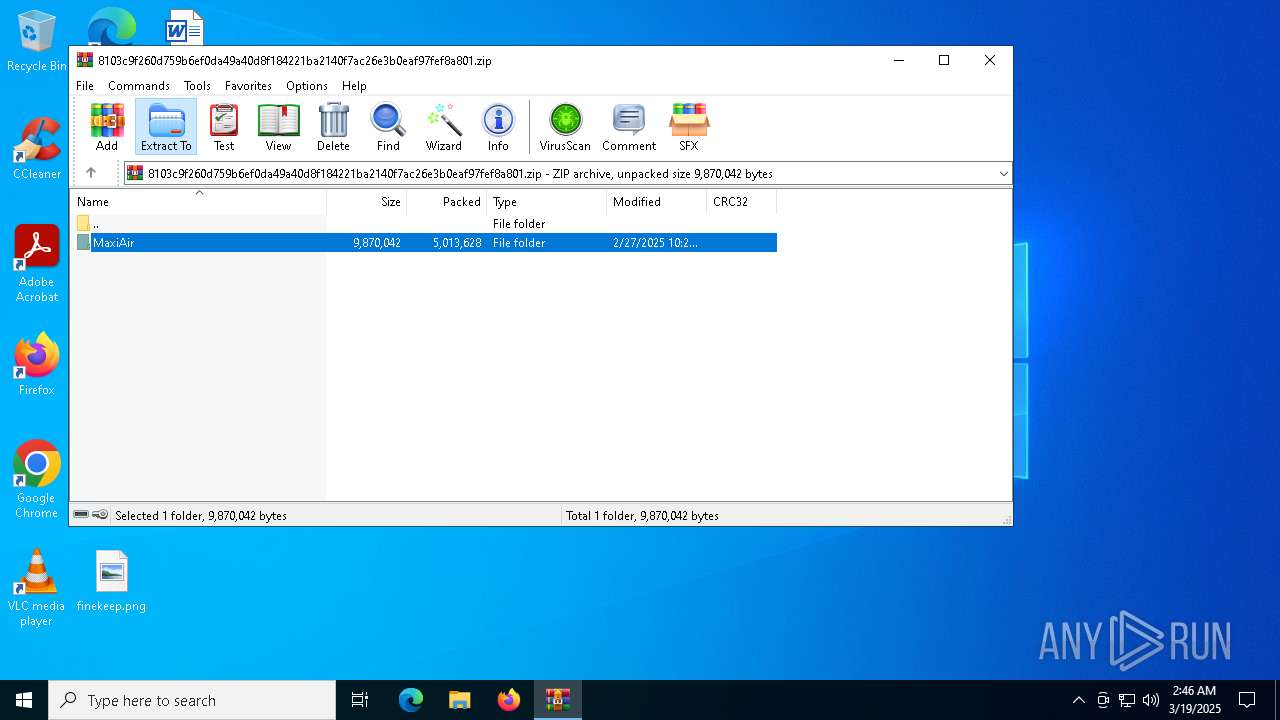
| 1328 | "C:\Users\admin\Desktop\MaxiAir\AUpdate.exe" | C:\Users\admin\Desktop\MaxiAir\AUpdate.exe | — | dllhost.exe | |||||||||||
User: admin Company: CheckMAL Inc. Integrity Level: HIGH Description: AppCheck Anti-Ransomware Service Exit code: 1 Version: 3.1.39.3 Modules
| |||||||||||||||
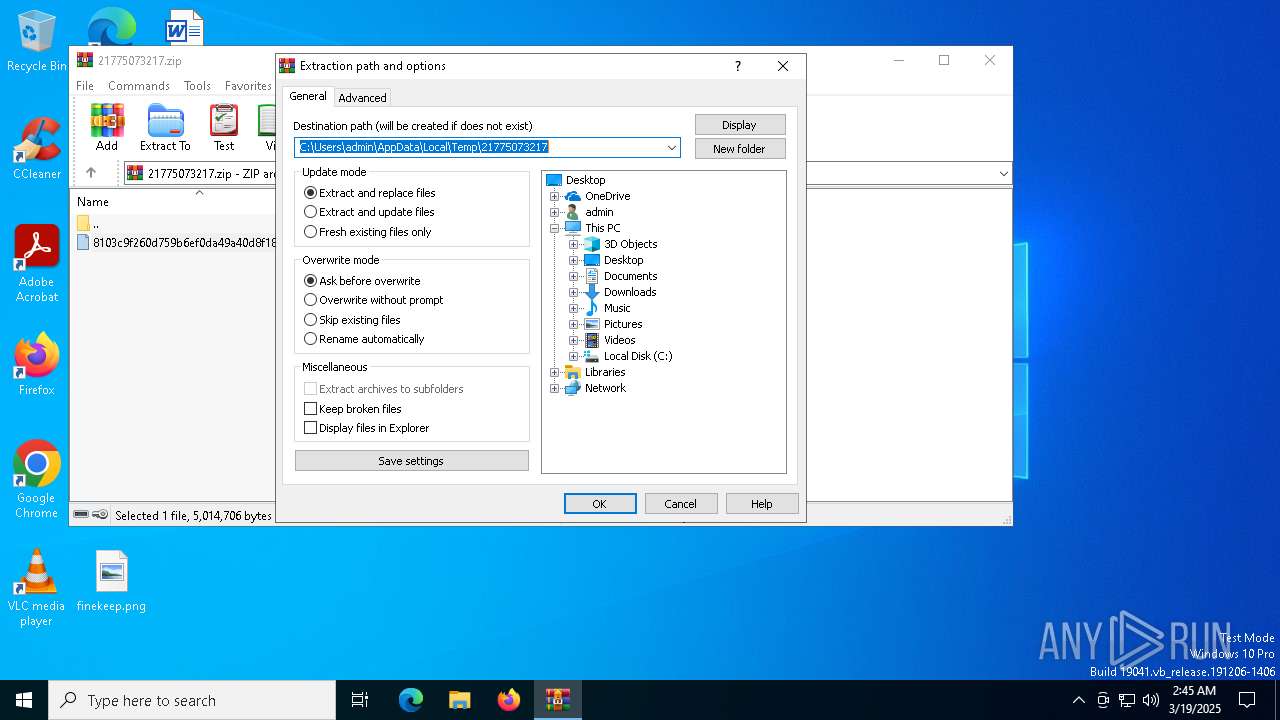
| 2432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\21775073217.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4424 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5680 | C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
xor-url(PID) Process(5680) MSBuild.exe Decrypted-URLs (3)http://dl.google.com/chrome/install/375.126/chrome_installer.exeb https://github.com https://pastebin.com/raw/DWCCqGB0wKo+g | |||||||||||||||
| 5984 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | AUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | AUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 044
Read events
6 958
Write events
61
Delete events
25
Modification events
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\21775073217.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
11
Suspicious files
14
Text files
0
Unknown types
0
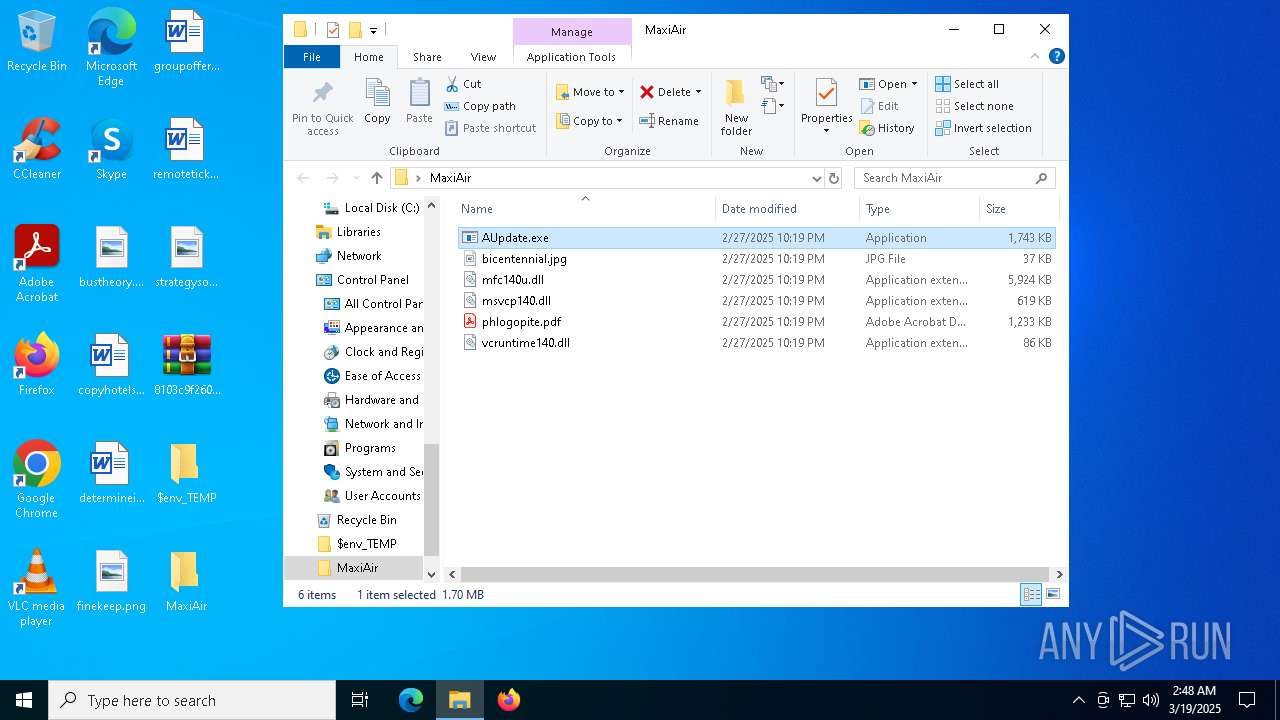
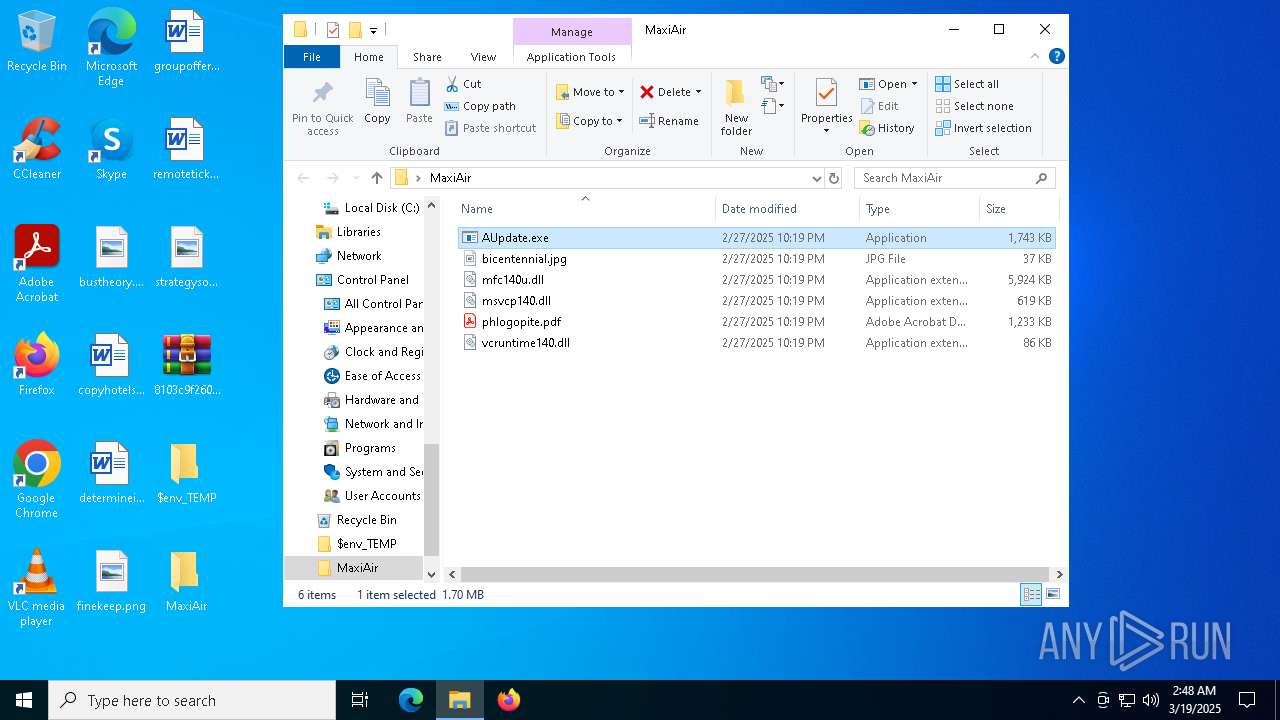
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
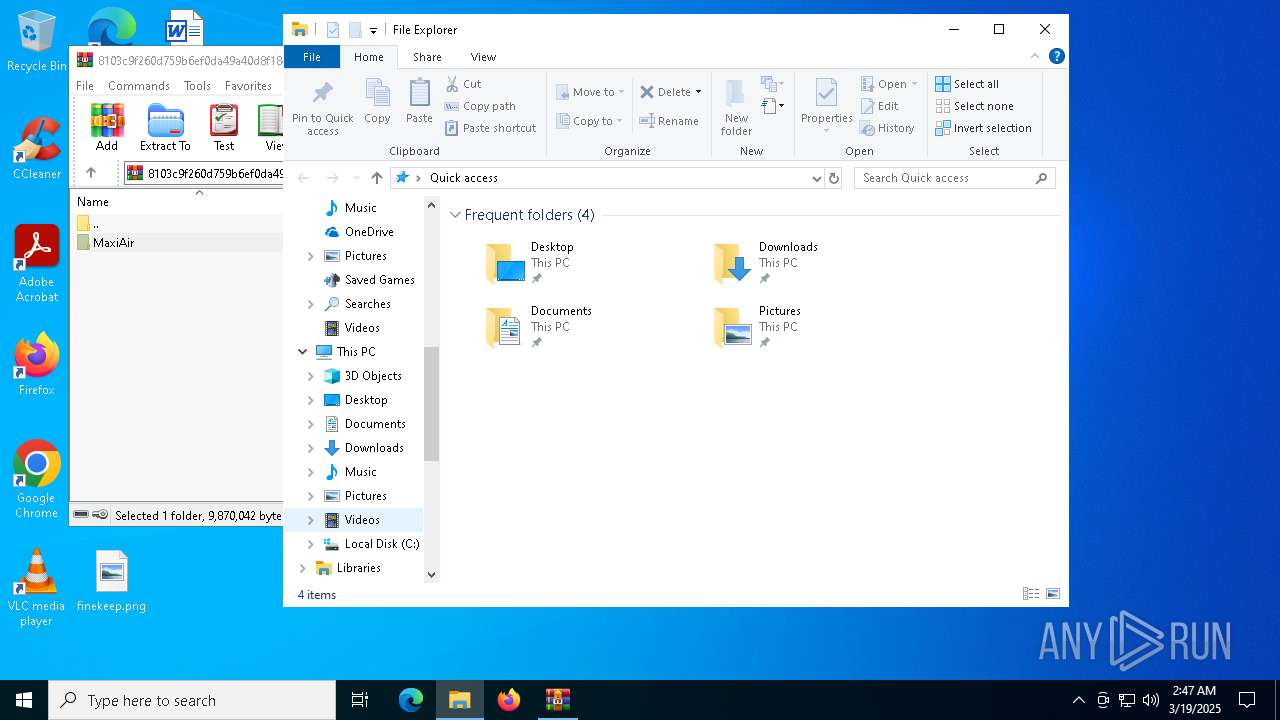
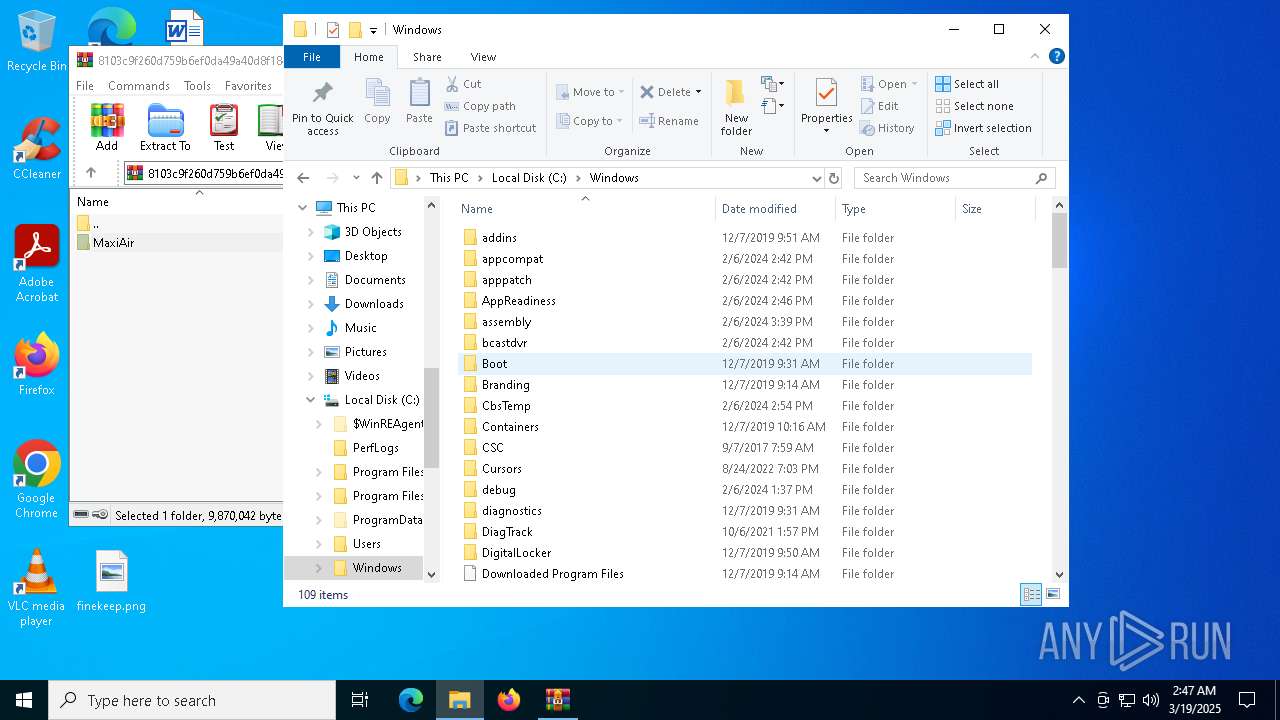
| 2432 | WinRAR.exe | C:\Users\admin\Desktop\8103c9f260d759b6ef0da49a40d8f184221ba2140f7ac26e3b0eaf97fef8a801 | compressed | |
MD5:C46D115580B54EF1FCFDF2A1AA48D623 | SHA256:8103C9F260D759B6EF0DA49A40D8F184221BA2140F7AC26E3B0EAF97FEF8A801 | |||
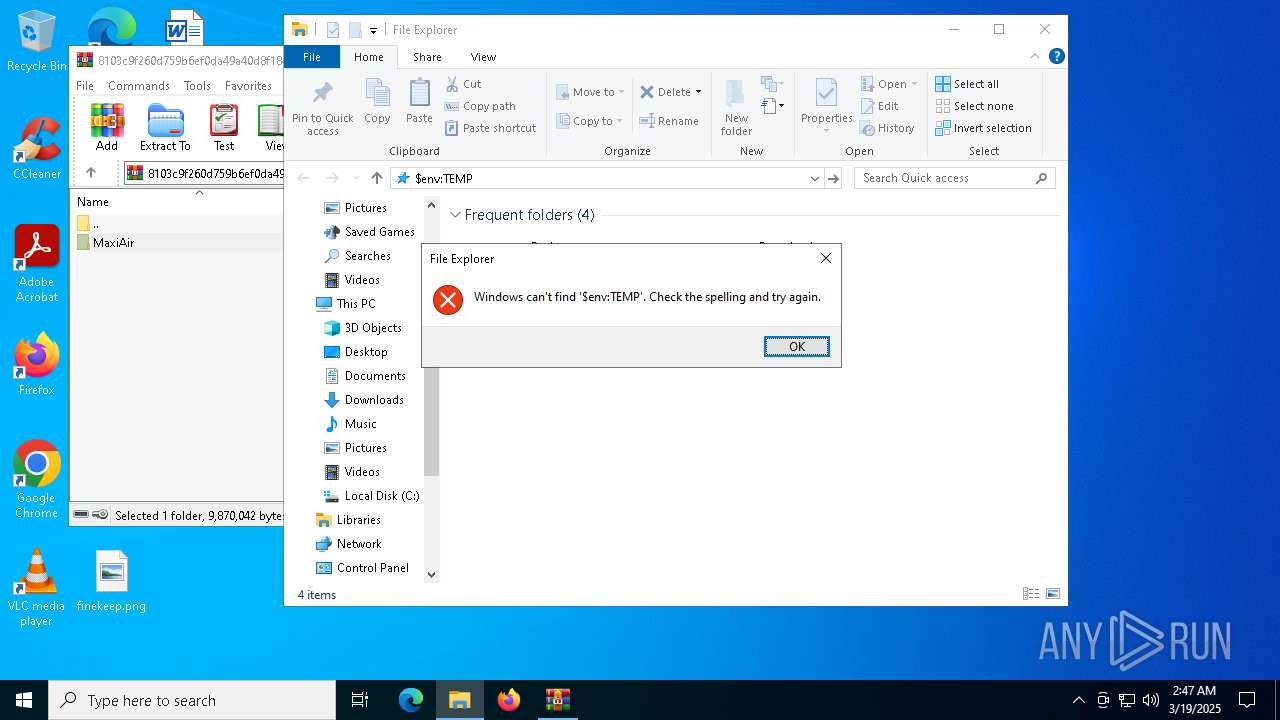
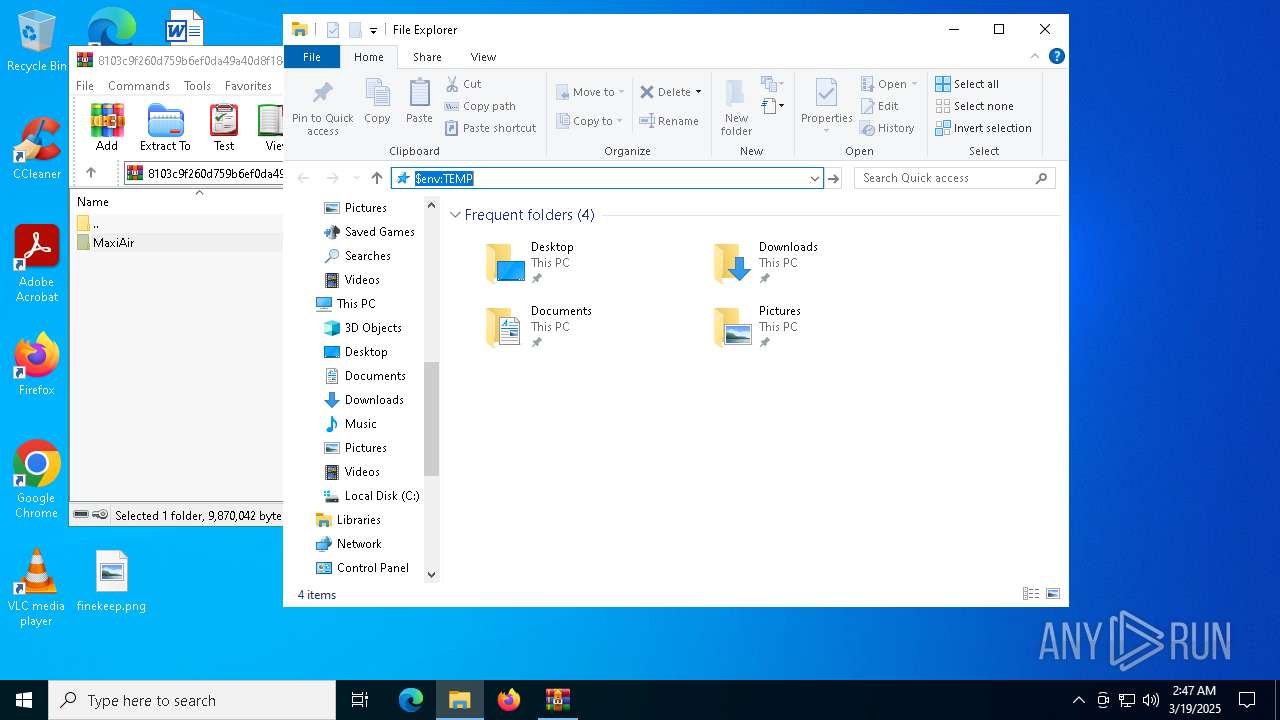
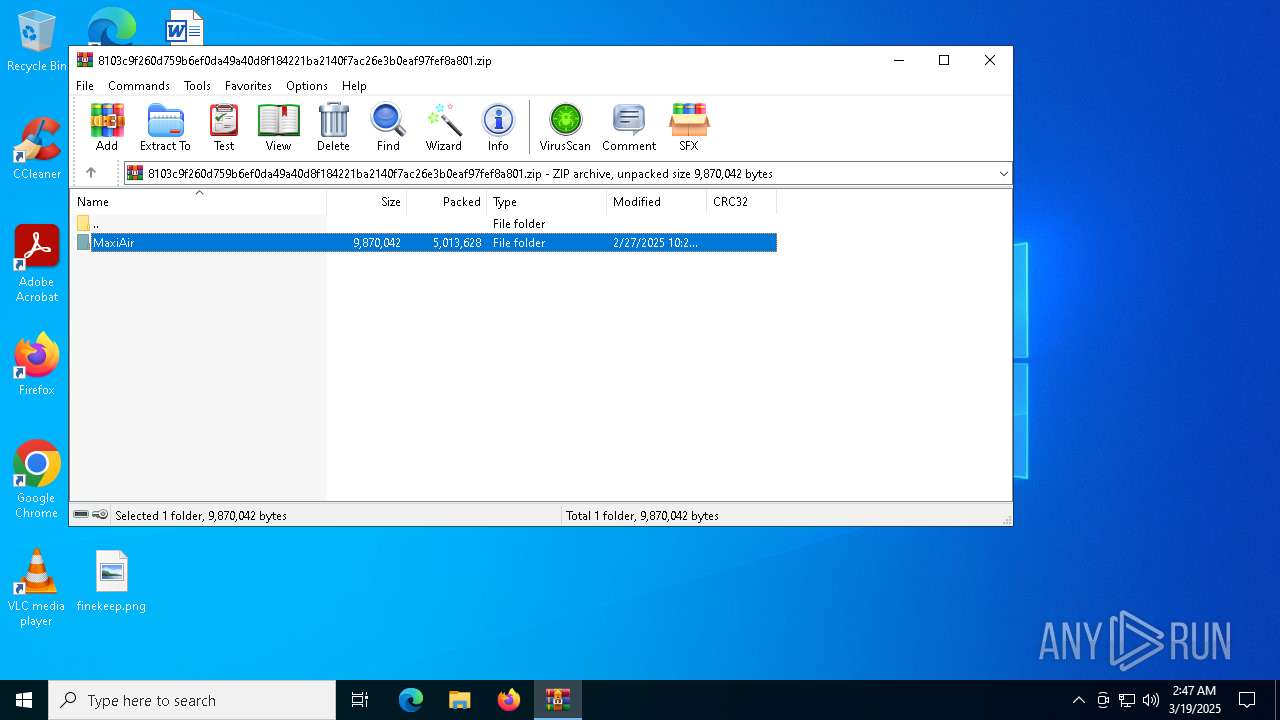
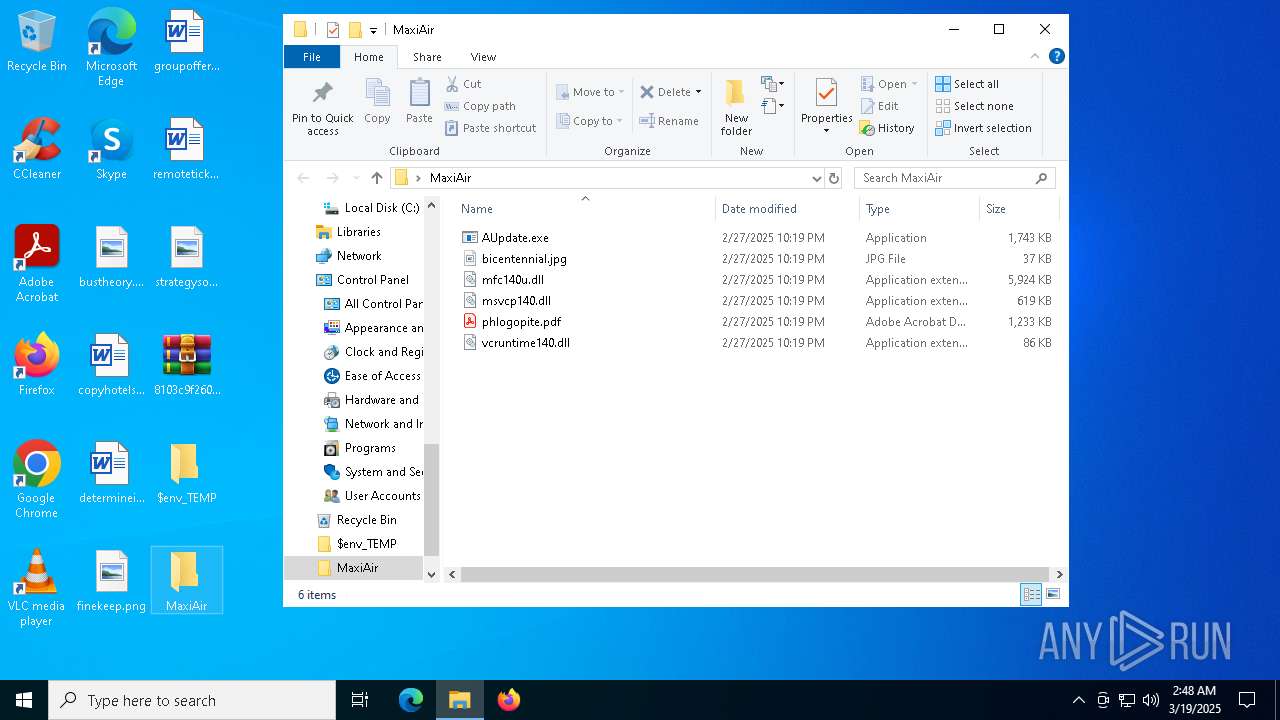
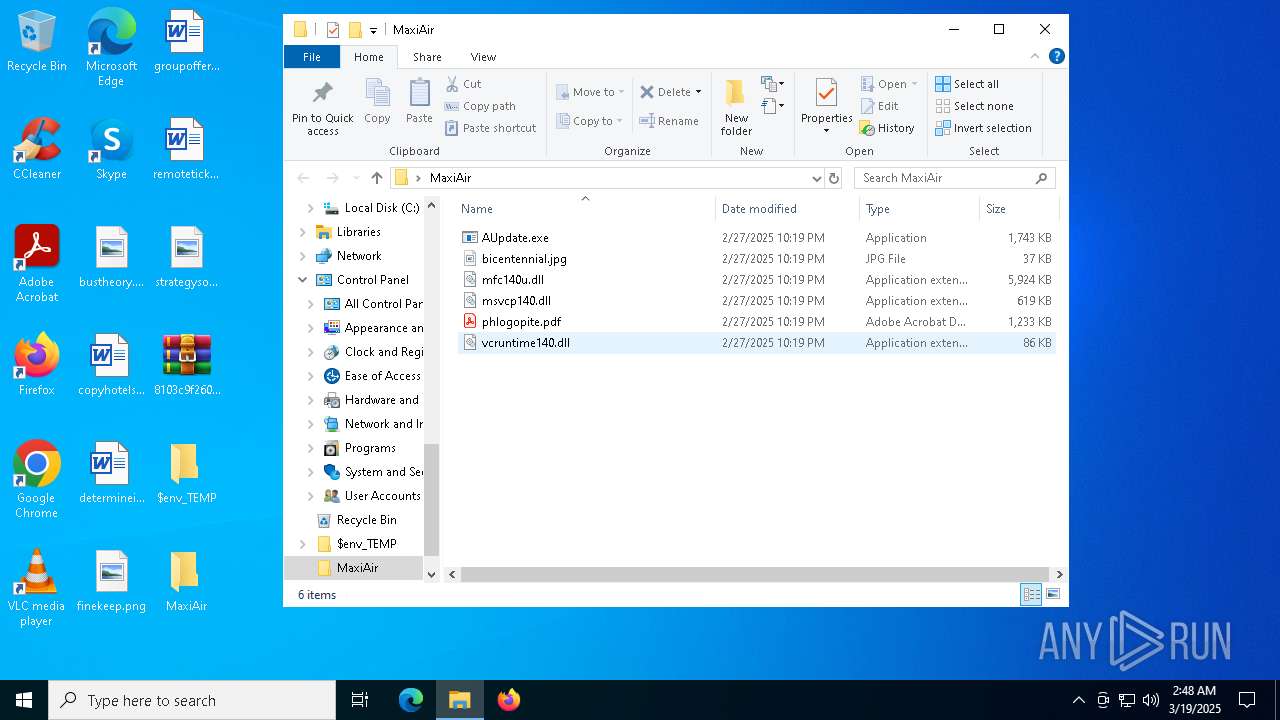
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\$env_TEMP\MaxiAir\mfc140u.dll | executable | |
MD5:C5C438012DF690E76F75B0FF2EC7BCF3 | SHA256:8372441605FE9E2F015DB86BAC37B47E3037E90CAF3E89E02174315A55CAE5CC | |||
| 5984 | cmd.exe | C:\Users\admin\AppData\Local\Temp\werpixsingef | — | |
MD5:— | SHA256:— | |||
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\$env_TEMP\MaxiAir\AUpdate.exe | executable | |
MD5:18247442E0F9378E739F650FD51ACB4E | SHA256:A5BF40C29313EB9F0E711BEE0D63B411EF35E80BA0FBDCC5964D0539DB59290E | |||
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\$env_TEMP\MaxiAir\vcruntime140.dll | executable | |
MD5:EDF9D5C18111D82CF10EC99F6AFA6B47 | SHA256:D89C7B863FC1AC3A179D45D5FE1B9FD35FB6FBD45171CA68D0D68AB1C1AD04FB | |||
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\$env_TEMP\MaxiAir\phlogopite.pdf | binary | |
MD5:EBF86463E3547936464D441D54D1541E | SHA256:0EB101B99603B06A6A8795C5103ADAF28C6EB17EC13034085888C1775506F23B | |||
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\$env_TEMP\MaxiAir\bicentennial.jpg | binary | |
MD5:ECBE765E4B5654A8921D42B0102B4597 | SHA256:7A2C4D02774723B11E1C34E25F2D480A1E6BCA7902486D09A9E50D61539ACE10 | |||
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\$env_TEMP\MaxiAir\msvcp140.dll | executable | |
MD5:9FF712C25312821B8AEC84C4F8782A34 | SHA256:517CD3AAC2177A357CCA6032F07AD7360EE8CA212A02DD6E1301BF6CFADE2094 | |||
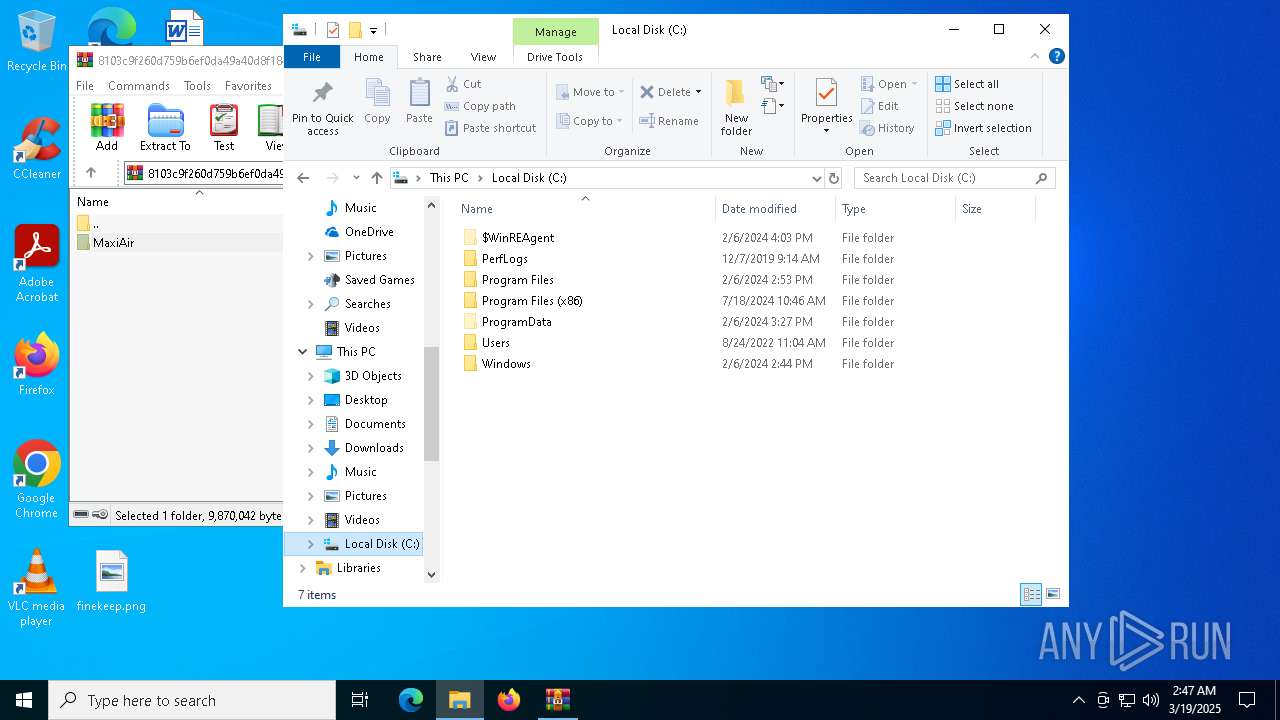
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\MaxiAir\AUpdate.exe | executable | |
MD5:18247442E0F9378E739F650FD51ACB4E | SHA256:A5BF40C29313EB9F0E711BEE0D63B411EF35E80BA0FBDCC5964D0539DB59290E | |||
| 8020 | WinRAR.exe | C:\Users\admin\Desktop\MaxiAir\bicentennial.jpg | binary | |
MD5:ECBE765E4B5654A8921D42B0102B4597 | SHA256:7A2C4D02774723B11E1C34E25F2D480A1E6BCA7902486D09A9E50D61539ACE10 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7520 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5680 | MSBuild.exe | GET | 200 | 92.255.85.36:9000 | http://92.255.85.36:9000/wbinjget?q=EF680CC9EFE0A8BCEC05D07897760CE8 | unknown | — | — | malicious |
7944 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7944 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7520 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5680 | MSBuild.exe | A Network Trojan was detected | ET MALWARE Arechclient2 Backdoor/SecTopRAT Related Activity M2 (GET) |