| File name: | Order_4500150357.7z |
| Full analysis: | https://app.any.run/tasks/7fd9c6f8-78ee-428d-af37-2a51a2663379 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | June 11, 2025, 01:58:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
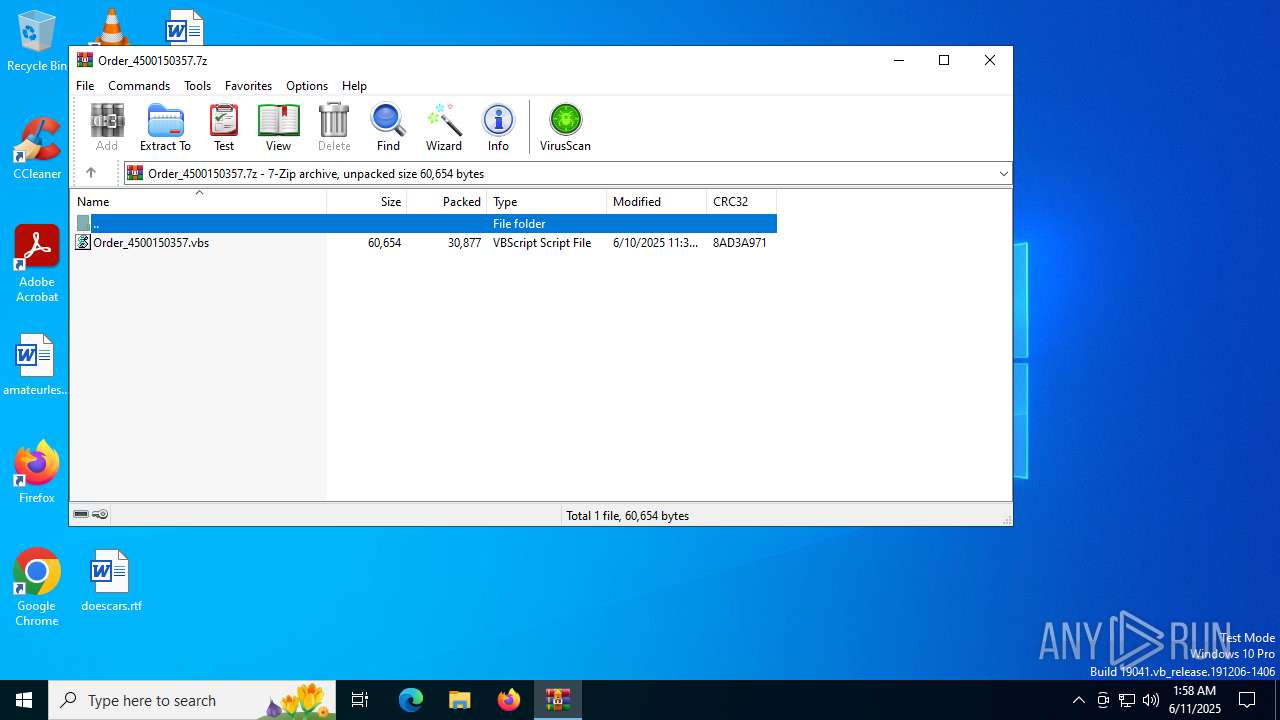
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | F2296B140FBF101148F85C23BB7E14F4 |
| SHA1: | A1C290661B5D2E610A34F74BFD238A9FFC794204 |
| SHA256: | 7E0CF773198DAD96A9B75B2299438CDC85A4DD4B184DE0E2A2B927FBBA74917E |
| SSDEEP: | 768:c6LqhzRSzF1fs3uD8lTDveqfAklvgmf8Ec1ss222:FLcFSzo3uw1vLQmkEfs222 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2580)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6748)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 6748)
REMCOS mutex has been found
- msiexec.exe (PID: 6004)
Steals credentials from Web Browsers
- svchost.exe (PID: 6400)
REMCOS has been detected
- msiexec.exe (PID: 6004)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 6004)
SUSPICIOUS
The process checks if it is being run in the virtual environment
- powershell.exe (PID: 6748)
- powershell.exe (PID: 6900)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 6900)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 7008)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7008)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7008)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 6900)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6748)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 6900)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 6748)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6900)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 6004)
Connects to unusual port
- msiexec.exe (PID: 6004)
INFO
Manual execution by a user
- wscript.exe (PID: 7008)
- powershell.exe (PID: 6900)
Disables trace logs
- powershell.exe (PID: 6748)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 6900)
Reads the software policy settings
- slui.exe (PID: 1472)
- msiexec.exe (PID: 6004)
Checks proxy server information
- slui.exe (PID: 1472)
- powershell.exe (PID: 6748)
- msiexec.exe (PID: 6004)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6748)
- powershell.exe (PID: 6900)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6900)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6900)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6004)
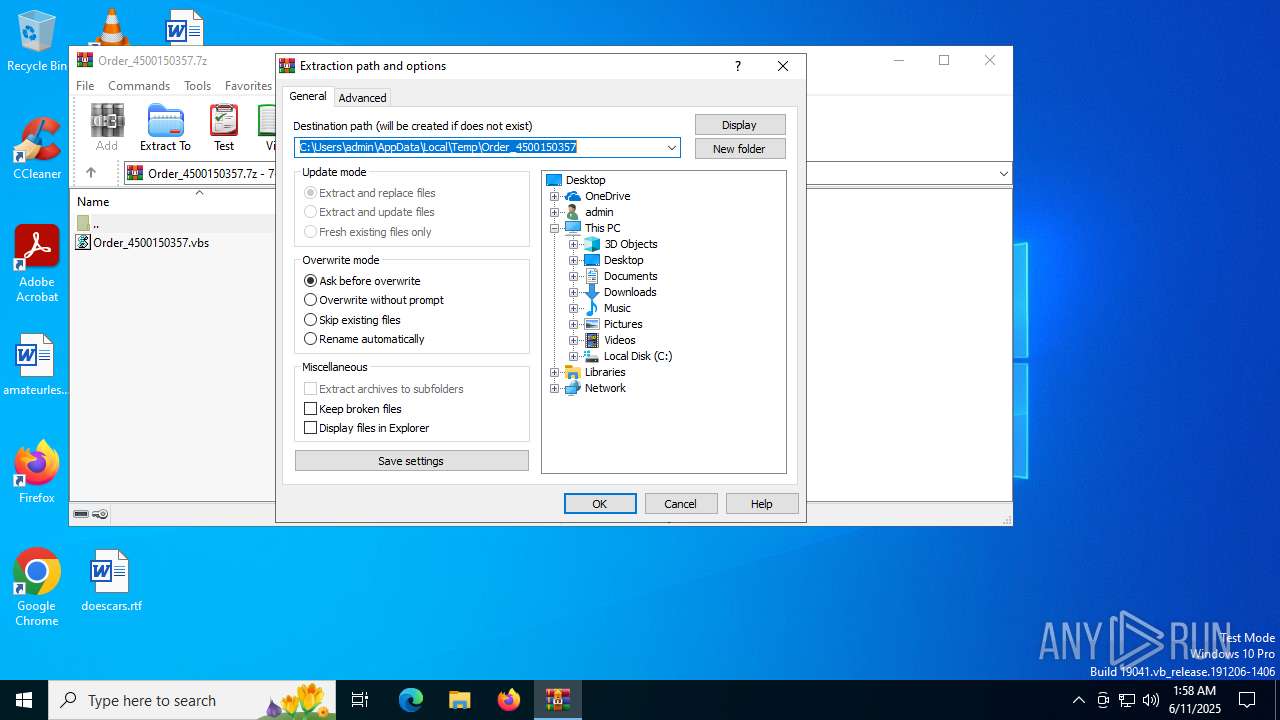
Creates files or folders in the user directory
- msiexec.exe (PID: 6004)
Create files in a temporary directory
- svchost.exe (PID: 1192)
- svchost.exe (PID: 6400)
- svchost.exe (PID: 2040)
The sample compiled with english language support
- msiexec.exe (PID: 6004)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:06:10 23:33:24+00:00 |
| ArchivedFileName: | Order_4500150357.vbs |
Total processes
158
Monitored processes
20
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\fxycxxcqwchv" | C:\Windows\SysWOW64\svchost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\prduyqnskkzapqw" | C:\Windows\SysWOW64\svchost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\prduyqnskkzapqw" | C:\Windows\SysWOW64\svchost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | C:\Windows\SysWOW64\svchost.exe /stext "C:\Users\admin\AppData\Local\Temp\atjfzixmysrnzxkpdeh" | C:\Windows\SysWOW64\svchost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Order_4500150357.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2664 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 529
Read events
34 491
Write events
25
Delete events
13
Modification events
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Order_4500150357.7z | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
3
Suspicious files
4
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6400 | svchost.exe | C:\Users\admin\AppData\Local\Temp\bhvA696.tmp | — | |
MD5:— | SHA256:— | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0uwb0bdb.mq3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6900 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_m4vt354j.cdq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2288 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:72FA9F7200DB0066481D7B43A28F111A | SHA256:59BF3B28298B7DDC4B606CECB06B2226CE953D7E39FD4067A38E0C79B5A183C1 | |||
| 6900 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tpemjm4k.nis.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:0D141314657E1F1C37ECB4021F0709E2 | SHA256:6141E278A09FC965A36A225A9BB3C8A1F94BD3DC6D3302F58DA5F918BC9C1DDF | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fnfxbw1z.twz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2580 | WinRAR.exe | C:\Users\admin\Desktop\Order_4500150357.vbs | text | |
MD5:FB06E19B7A14CC857C7505ED4516B849 | SHA256:E494B55C70462C381D094642BE734D0427E0F9A1F29182C64D7C80E43DDFFB8F | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Roaming\Ruelike.uni | text | |
MD5:37C3E2D85941B2FDD516688DD8761EDF | SHA256:D7678EABAC3A14BE9442D2761C649574B4B4AA9AAB1ED02CE56E95BA90EC628E | |||
| 6900 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h5ft4y31.qg4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
24
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1816 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5124 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5124 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6004 | msiexec.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6004 | msiexec.exe | GET | 200 | 65.9.66.2:80 | http://r11.c.lencr.org/69.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3108 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1816 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1816 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2200 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2200 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2200 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
6004 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
6004 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
6004 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
6004 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |