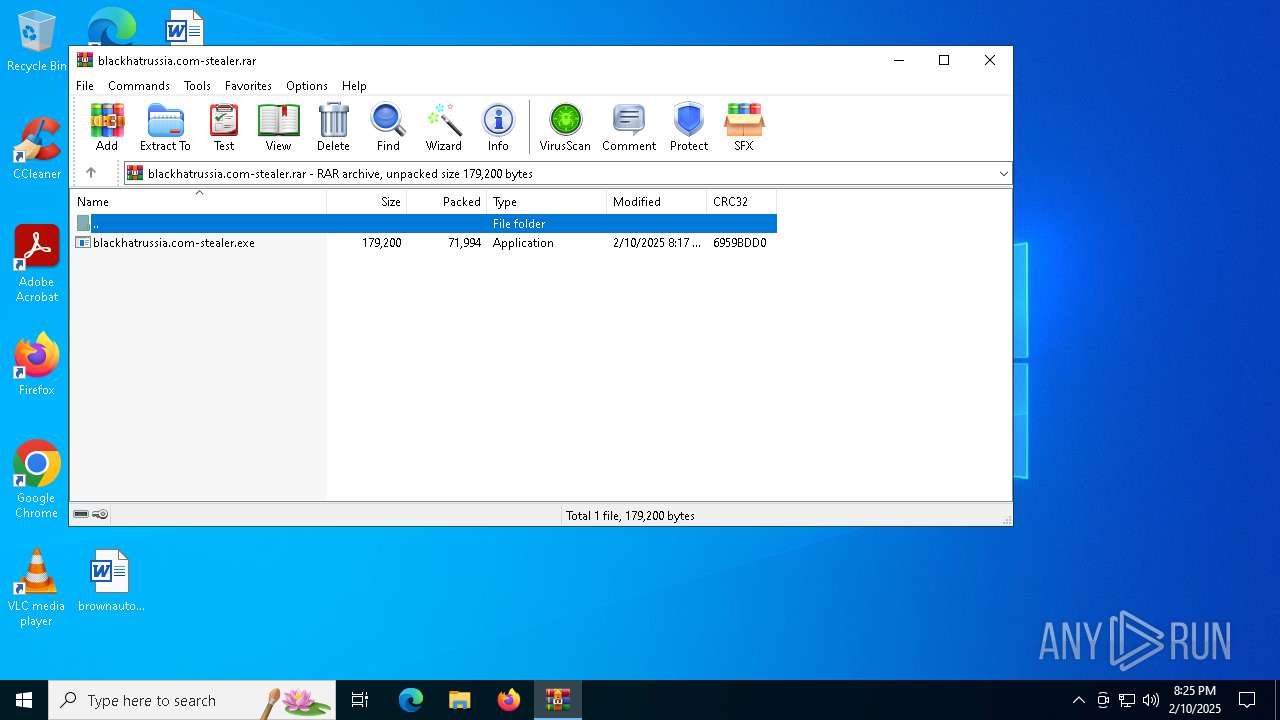
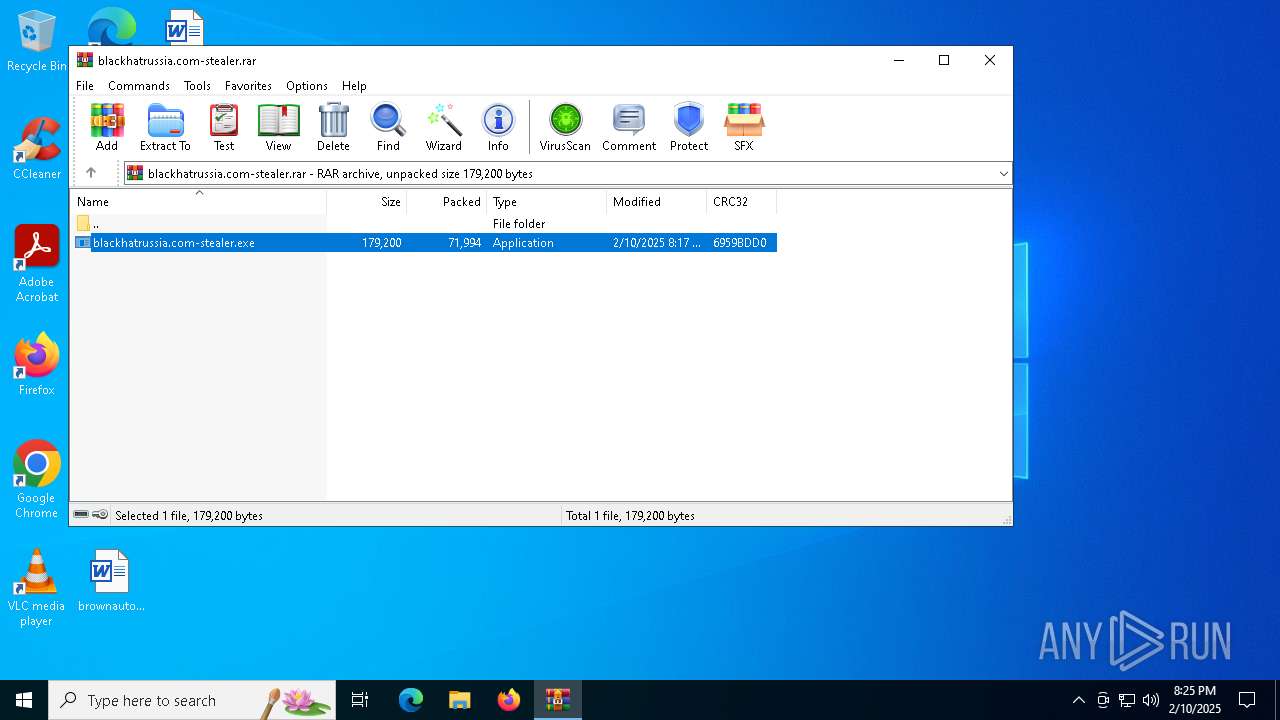
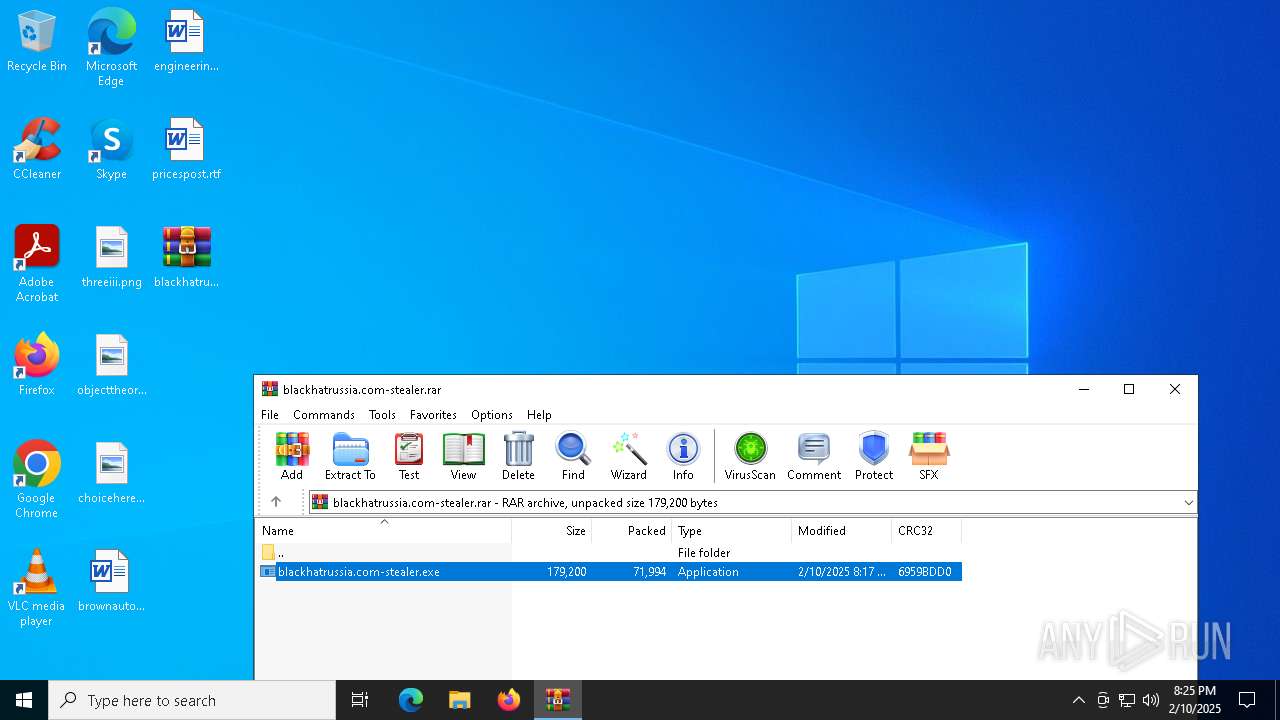
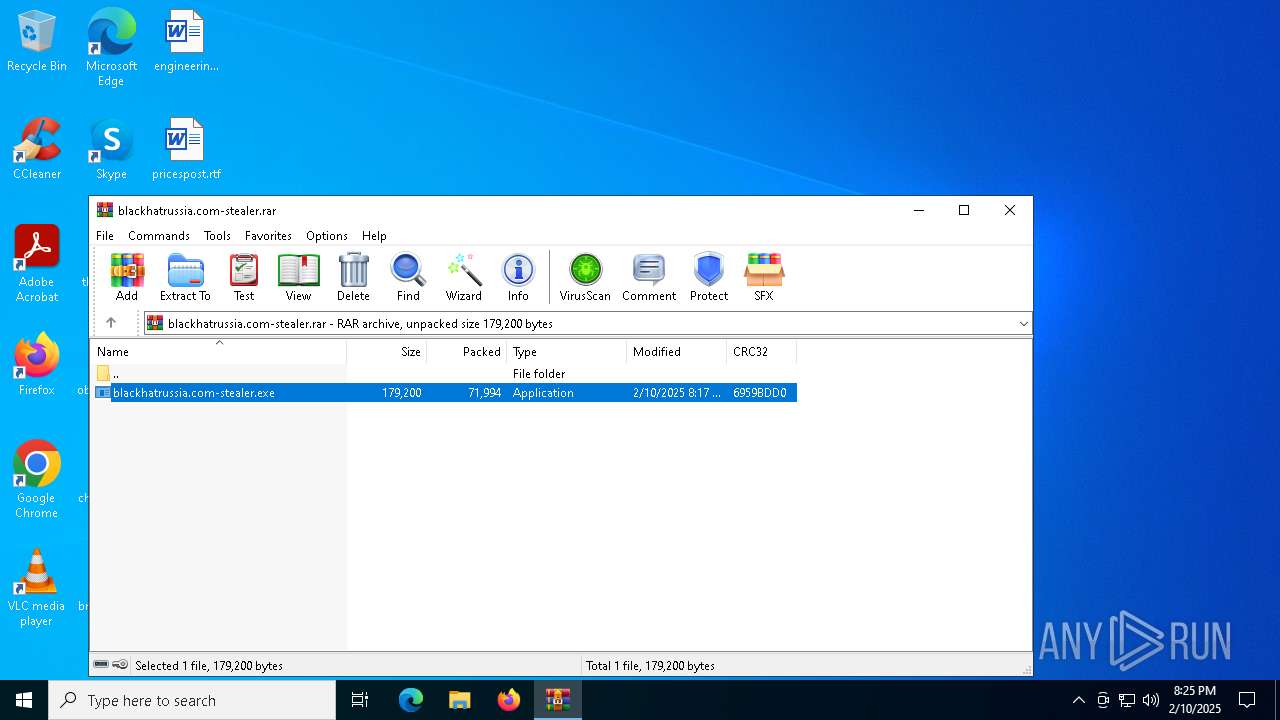
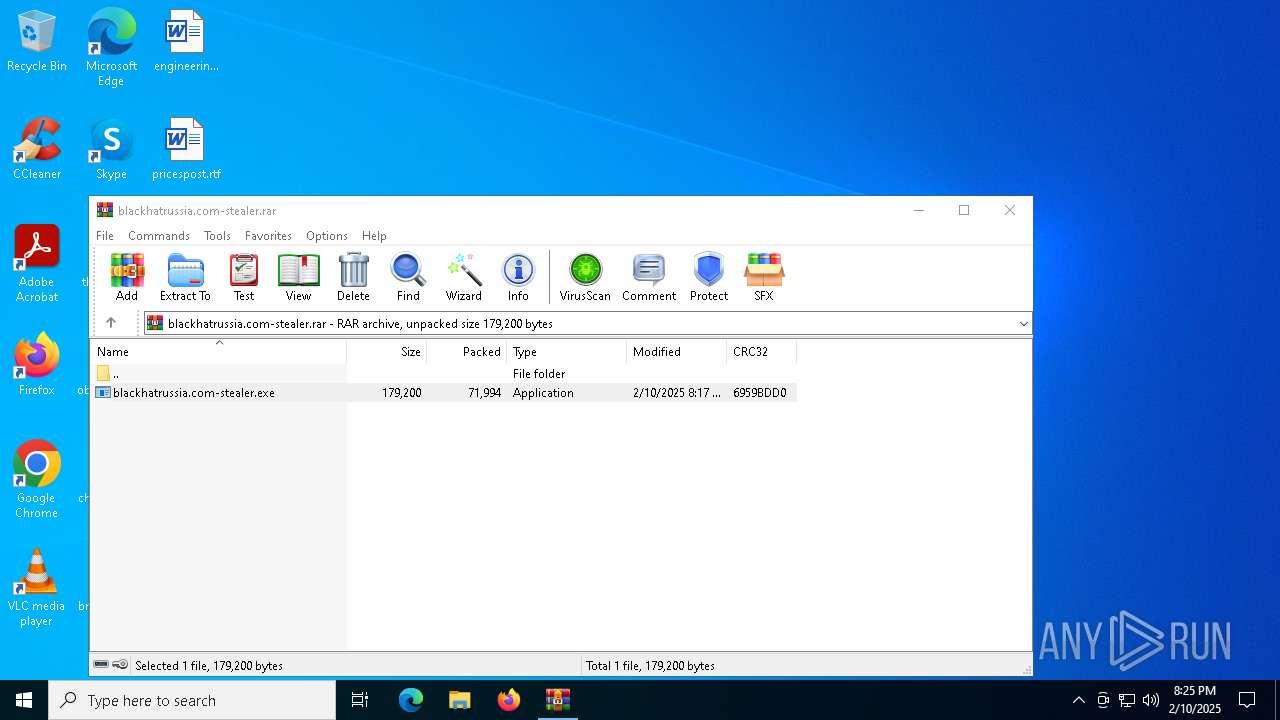
| File name: | blackhatrussia.com-stealer.rar |
| Full analysis: | https://app.any.run/tasks/fda55b6a-68c3-4daf-81d0-8c689b3491bc |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | February 10, 2025, 20:25:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 703F4C13178BEBF51BF0D544ECACA4E9 |
| SHA1: | F9656C76A9475E8AE3CB54D4EF9E0E5F6FE327FD |
| SHA256: | 7DE7CA7B0DA02374C2BC3132FD699C7AA44572AC99DB9E12120F29739522B4CA |
| SSDEEP: | 1536:+HQ45xbAWx09Z5o2sA1bybq1uGrWX+yxerNjvly8adzvf1Y/pJ/bG:+w45xtx09DsA1a6uVVerFIXvsLTG |
MALICIOUS
Steals credentials from Web Browsers
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Actions looks like stealing of personal data
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
ASYNCRAT has been detected (MUTEX)
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
STORMKITTY has been detected (YARA)
- blackhatrussia.com-stealer.exe (PID: 6260)
SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7072)
- cmd.exe (PID: 6136)
Starts application with an unusual extension
- cmd.exe (PID: 2212)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 4420)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 2212)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 4420)
- cmd.exe (PID: 6136)
Possible usage of Discord/Telegram API has been detected (YARA)
- blackhatrussia.com-stealer.exe (PID: 6260)
Starts CMD.EXE for commands execution
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Write to the desktop.ini file (may be used to cloak folders)
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Checks for external IP
- blackhatrussia.com-stealer.exe (PID: 6260)
- svchost.exe (PID: 2192)
- blackhatrussia.com-stealer.exe (PID: 904)
Potential Corporate Privacy Violation
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
The process connected to a server suspected of theft
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5032)
INFO
Checks supported languages
- blackhatrussia.com-stealer.exe (PID: 6260)
- chcp.com (PID: 6224)
- chcp.com (PID: 7124)
- blackhatrussia.com-stealer.exe (PID: 904)
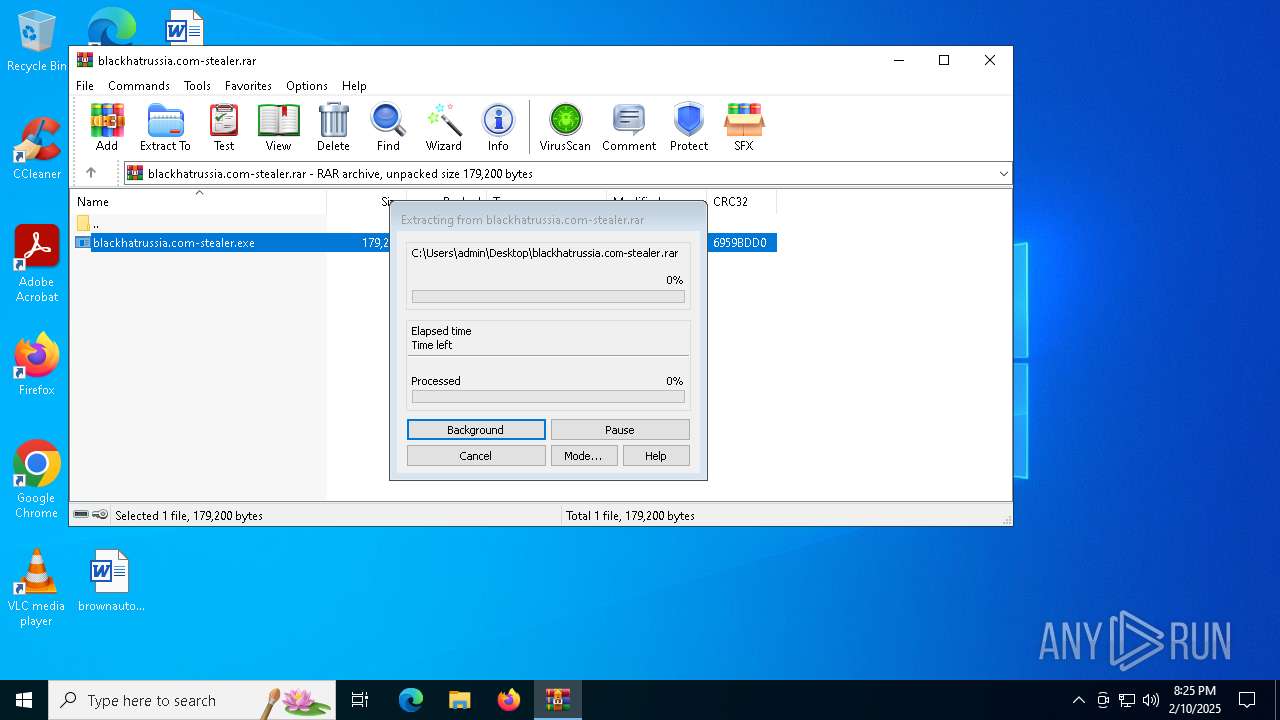
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5032)
Changes the display of characters in the console
- cmd.exe (PID: 2212)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 4420)
Reads CPU info
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Create files in a temporary directory
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Reads the software policy settings
- blackhatrussia.com-stealer.exe (PID: 6260)
Checks proxy server information
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Manual execution by a user
- blackhatrussia.com-stealer.exe (PID: 904)
Disables trace logs
- blackhatrussia.com-stealer.exe (PID: 6260)
- blackhatrussia.com-stealer.exe (PID: 904)
Reads the machine GUID from the registry
- blackhatrussia.com-stealer.exe (PID: 904)
- blackhatrussia.com-stealer.exe (PID: 6260)
Creates files or folders in the user directory
- blackhatrussia.com-stealer.exe (PID: 904)
- blackhatrussia.com-stealer.exe (PID: 6260)
Reads the computer name
- blackhatrussia.com-stealer.exe (PID: 6260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
StormKitty
(PID) Process(6260) blackhatrussia.com-stealer.exe
C2 (1)127.0.0.1
Ports (3)6606
7707
8808
Credentials
Protocoltelegram
URLnull
Token7444260377:AAEA1PnIs0V-tJJH1WTn8_RH4ktpdTCxsiE
ChatId-1002417137503
Version
BotnetDefault
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE9jCCAt6gAwIBAgIQAKQXqY8ZdB/modqi69mWGTANBgkqhkiG9w0BAQ0FADAcMRowGAYDVQQDDBFXb3JsZFdpbmQgU3RlYWxlcjAgFw0yMTA3MTMwNDUxMDZaGA85OTk5MTIzMTIzNTk1OVowHDEaMBgGA1UEAwwRV29ybGRXaW5kIFN0ZWFsZXIwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQCnRXYoxuLqqgXdcvIAYWb9DuVRl5ZpdpPfoIgmb7Y9A9AuiddKNm4is8EvIlEh98bQD4OB...
Server_SignatureJ7XpD4w+JaFzTixc0nCmiRA4ZP4bPCIpEYYGofNxvC1+0OsFQr56oTWwQMosnOTB64TZRGSdXVHKzjVchQf7X5Uwu/KQU61NPArjxWVScwKZXOGS4ZNzsWbrxgztkmlyRlQgvEq4rdFsqy1bfvHEoQ/s9aDXBNoLPPjJOexTRQSGuZYMpGSUD+ZUiVwPqqFWTb8KcjEMyABMeXGKfia2e9u8ePKpWv4HSiOfl6N47tTtIfN2FW/2mCX7BOnIZwCl3UxaQnITN812tHD1enX9TK86R91F02c0wabnf4oC07S3...
Keys
AESe5e3972eba013063607e705973dfdf80a8555bcfd8fe09651da2ab43b5773d9b
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 71994 |
| UncompressedSize: | 179200 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | blackhatrussia.com-stealer.exe |
Total processes
148
Monitored processes
22
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Users\admin\Desktop\blackhatrussia.com-stealer.exe" | C:\Users\admin\Desktop\blackhatrussia.com-stealer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "cmd.exe" /C chcp 65001 && netsh wlan show networks mode=bssid | C:\Windows\SysWOW64\cmd.exe | — | blackhatrussia.com-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4420 | "cmd.exe" /C chcp 65001 && netsh wlan show networks mode=bssid | C:\Windows\SysWOW64\cmd.exe | — | blackhatrussia.com-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | findstr All | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5032 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\blackhatrussia.com-stealer.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5972 | netsh wlan show networks mode=bssid | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6136 | "cmd.exe" /C chcp 65001 && netsh wlan show profile | findstr All | C:\Windows\SysWOW64\cmd.exe | — | blackhatrussia.com-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 428
Read events
10 406
Write events
22
Delete events
0
Modification events
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\blackhatrussia.com-stealer.rar | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5032) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6260) blackhatrussia.com-stealer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\blackhatrussia_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6260) blackhatrussia.com-stealer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\blackhatrussia_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
2
Suspicious files
42
Text files
54
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\desktop.ini | text | |
MD5:29EAE335B77F438E05594D86A6CA22FF | SHA256:88856962CEF670C087EDA4E07D8F78465BEEABB6143B96BD90F884A80AF925B4 | |||
| 5032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5032.42712\blackhatrussia.com-stealer.exe | executable | |
MD5:0E0E20939CD1DD5DA091EFD4183D2D09 | SHA256:8F0EC6494DC4A6EC51A734207CE96C3BB18EFC12F4098C90EE70D6071A4FC2DB | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Downloads\desktop.ini | text | |
MD5:3A37312509712D4E12D27240137FF377 | SHA256:B029393EA7B7CF644FB1C9F984F57C1980077562EE2E15D0FFD049C4C48098D3 | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\copygrade.png | binary | |
MD5:2F3D8F8AAF944CC1C8D523E94FC3EF78 | SHA256:8ABD310C0D6A8EC0671A3AEF9E8DE1DE1E907E98232549C4135A542BB82556C9 | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Desktop\choicehere.png | binary | |
MD5:D20876954426A236EBFE97E72F96DB42 | SHA256:E217FF685DA19BCAE4B9A846498083789FEF7E43FBA5DAFDD094F9C1FD39B91E | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Desktop\brownauto.rtf | text | |
MD5:830937AE8739A9D19BA5F3C950F79787 | SHA256:54815246E25AA119214061FE698B8D6E4AB9E7B23284A17CEA5BBA3ED2F1E9BF | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Documents\customersactive.rtf | text | |
MD5:01B50647D1A038D89B3DDE47E6943073 | SHA256:A5B12AE1AE456E870FE6F19E9836C33F83BFE23BE1BD2ACE52D19262D23FDABF | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Documents\desktop.ini | text | |
MD5:ECF88F261853FE08D58E2E903220DA14 | SHA256:CAFEC240D998E4B6E92AD1329CD417E8E9CBD73157488889FD93A542DE4A4844 | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Documents\blogsocial.rtf | text | |
MD5:83633D5624E3B3AD779569510889D941 | SHA256:10BA5CD9886D835FC084947391B5481F1FF20C22CBC48D8D720BF56C6FCE7F04 | |||
| 6260 | blackhatrussia.com-stealer.exe | C:\Users\admin\AppData\Local\eb6ac490e04191317f0bea9d91713320\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Downloads\viewchange.png | binary | |
MD5:259204B85C98C80FD64D249267649AB9 | SHA256:92CD32692B2AE3846756A3A76BD78180DC94C1C37FD643769845318F949E06B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
18
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6260 | blackhatrussia.com-stealer.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | whitelisted |
6376 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3736 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3736 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
904 | blackhatrussia.com-stealer.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 92.123.104.33:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6260 | blackhatrussia.com-stealer.exe | 104.16.184.241:80 | icanhazip.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
icanhazip.com |
| whitelisted |
api.mylnikov.org |
| unknown |
api.telegram.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6260 | blackhatrussia.com-stealer.exe | Attempted Information Leak | ET INFO IP Check Domain (icanhazip. com in HTTP Host) |
6260 | blackhatrussia.com-stealer.exe | Potential Corporate Privacy Violation | ET INFO Observed Wifi Geolocation Domain (api .mylnikov .org in TLS SNI) |
6260 | blackhatrussia.com-stealer.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
2192 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
6260 | blackhatrussia.com-stealer.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6260 | blackhatrussia.com-stealer.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
6260 | blackhatrussia.com-stealer.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6260 | blackhatrussia.com-stealer.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |