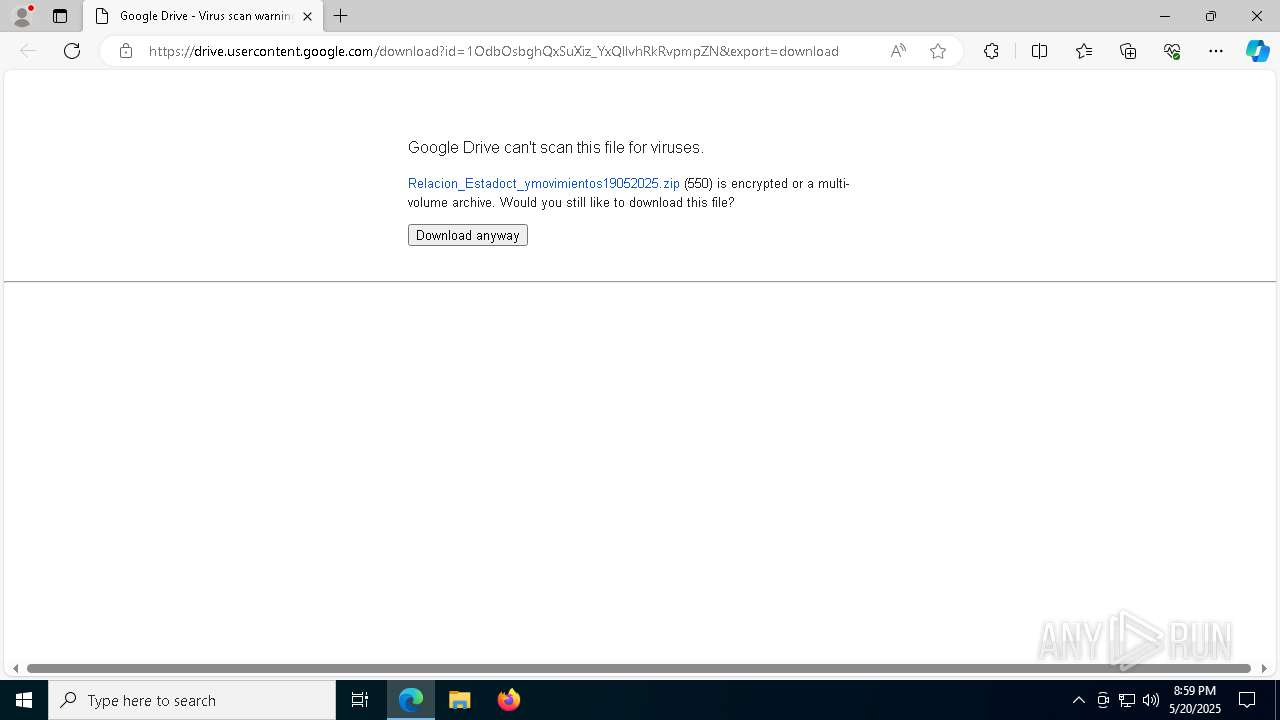
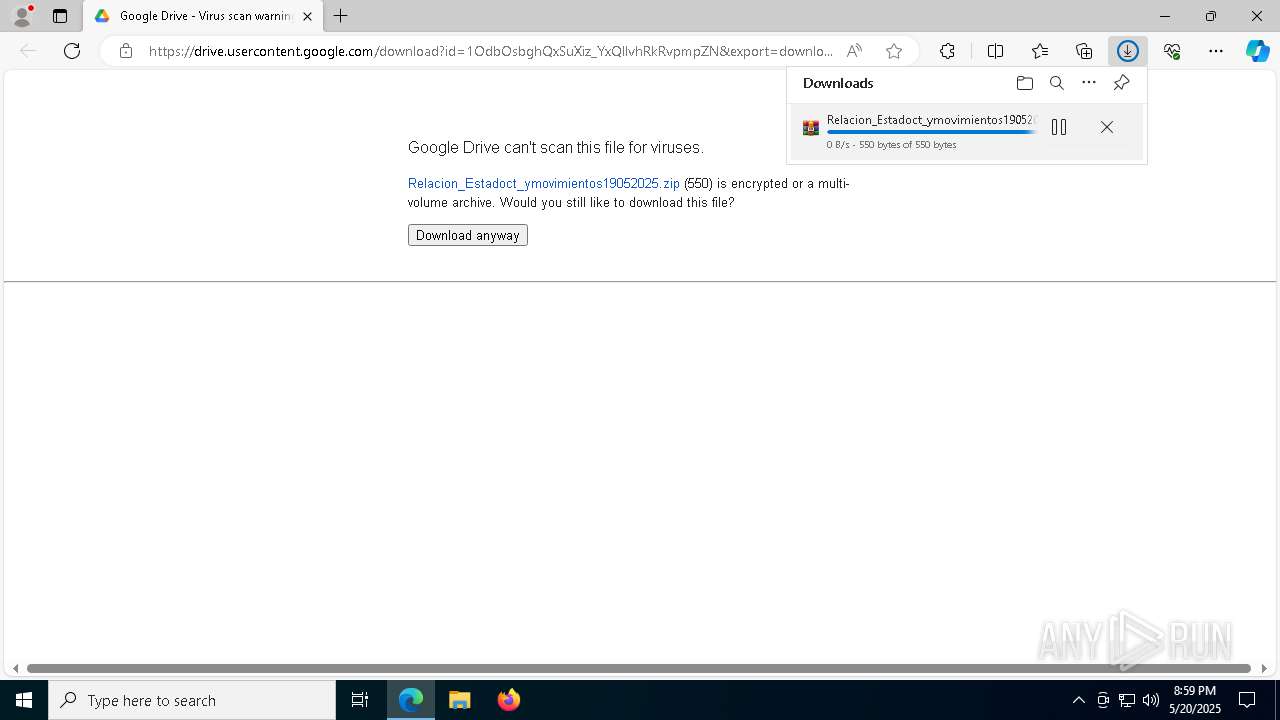
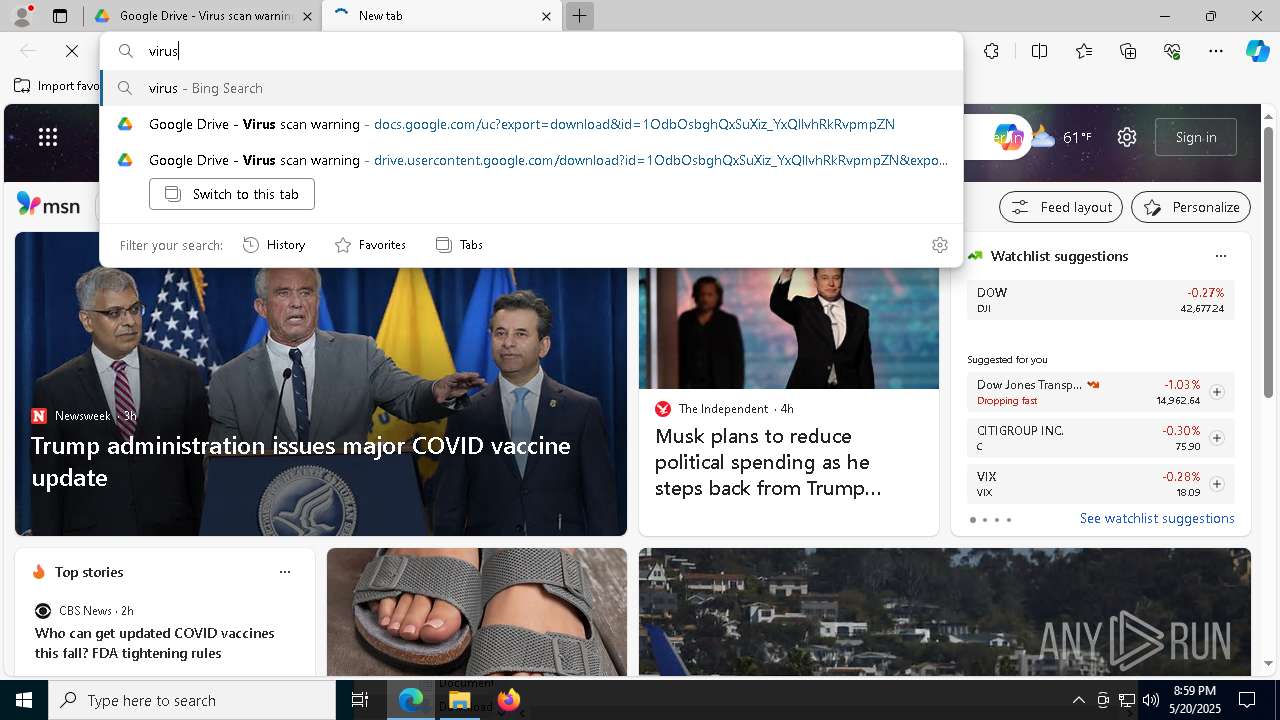
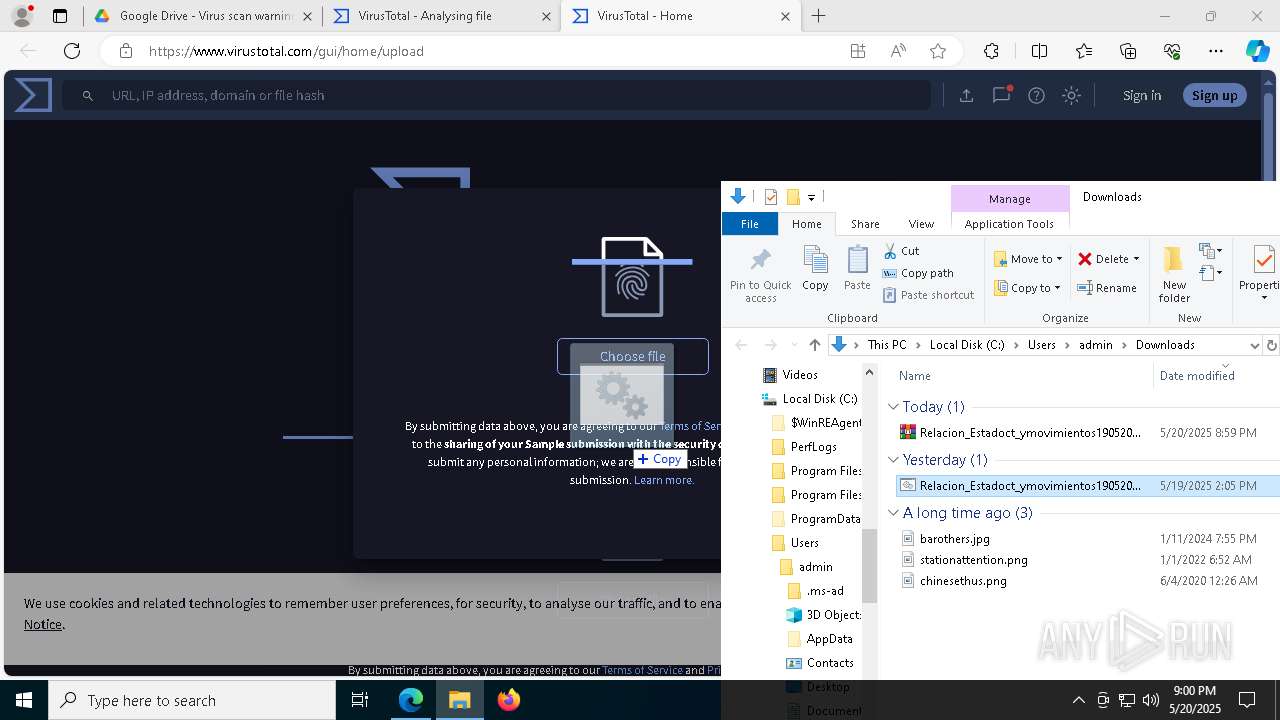
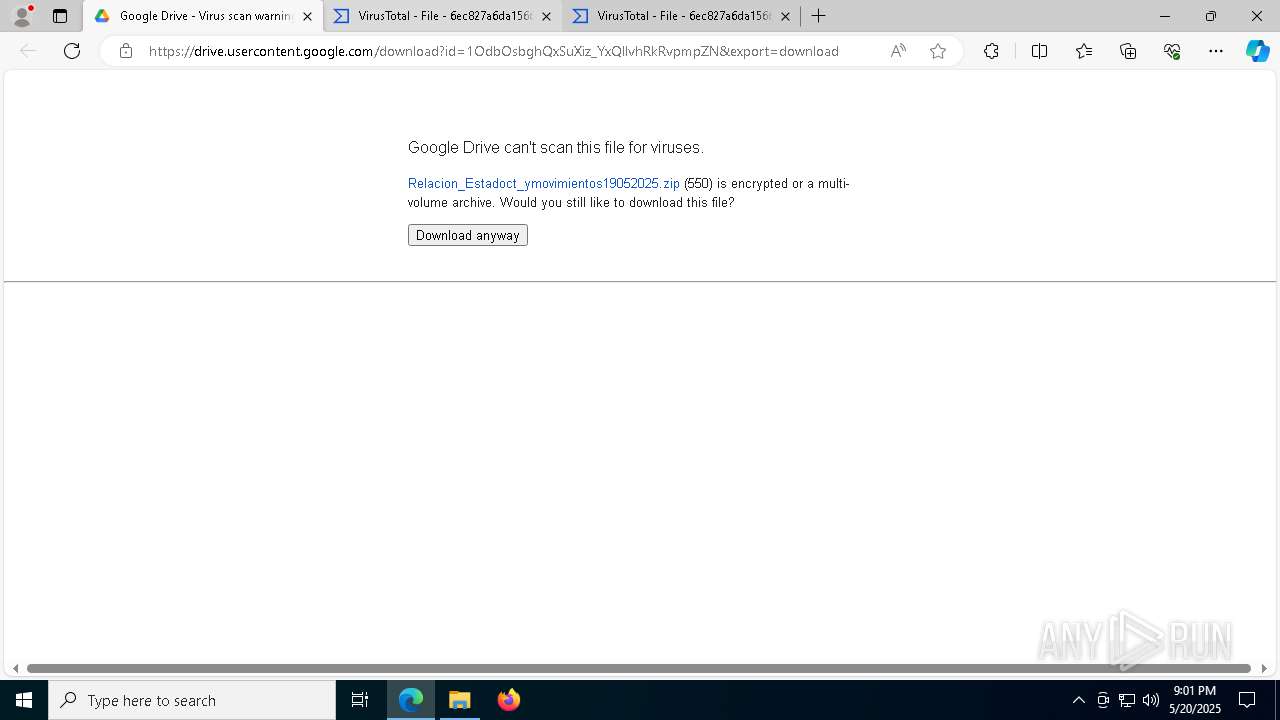
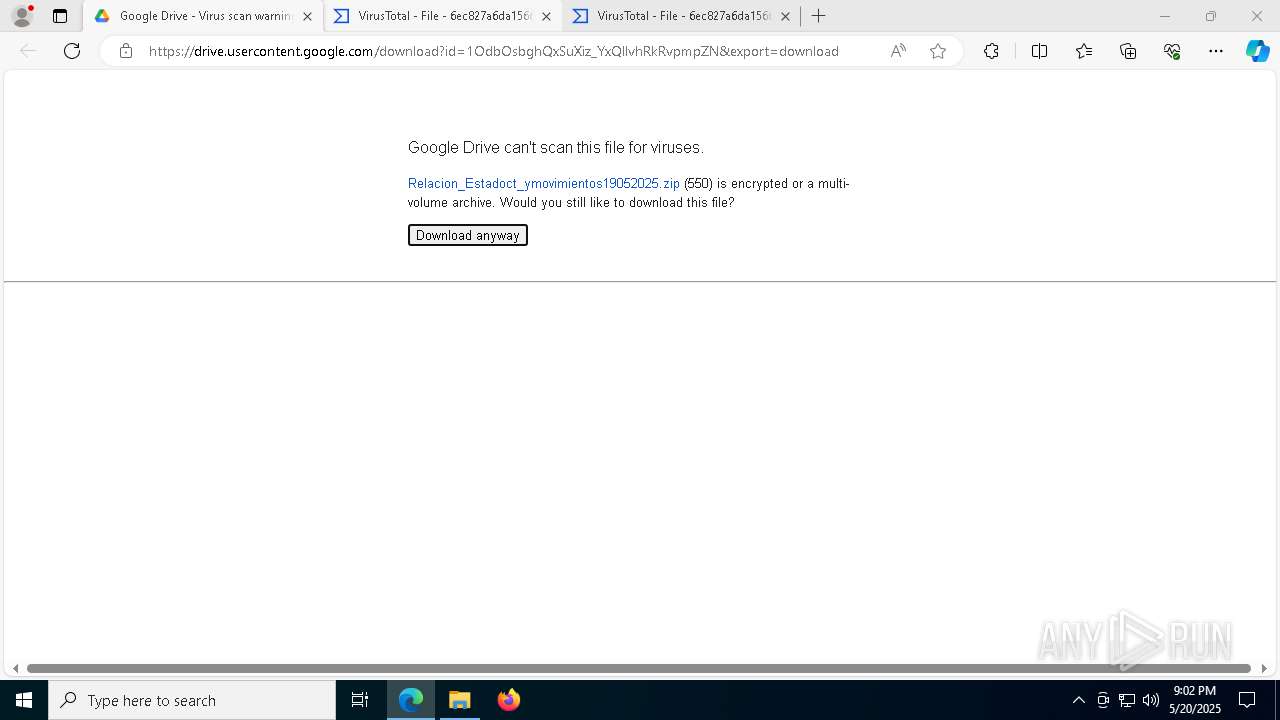
| URL: | https://docs.google.com/uc?export=download&id=1OdbOsbghQxSuXiz_YxQllvhRkRvpmpZN |
| Full analysis: | https://app.any.run/tasks/32f4219c-6d76-4a36-bd4c-f87530144508 |
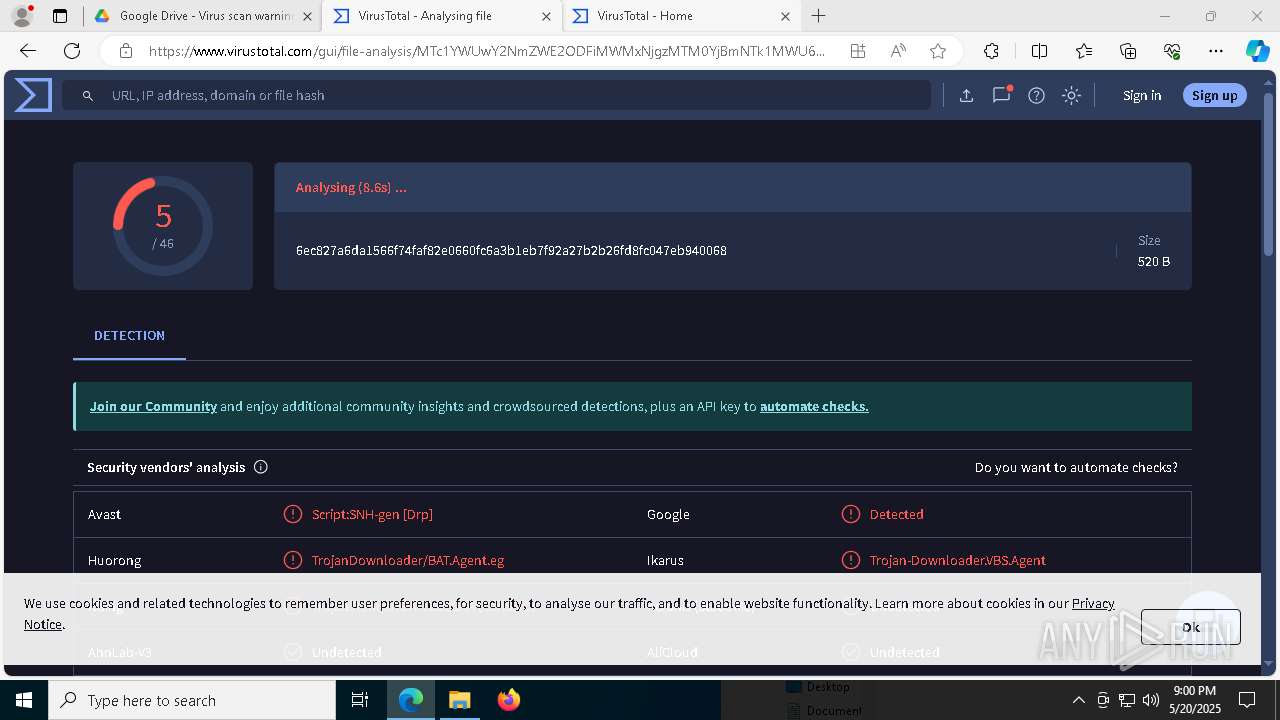
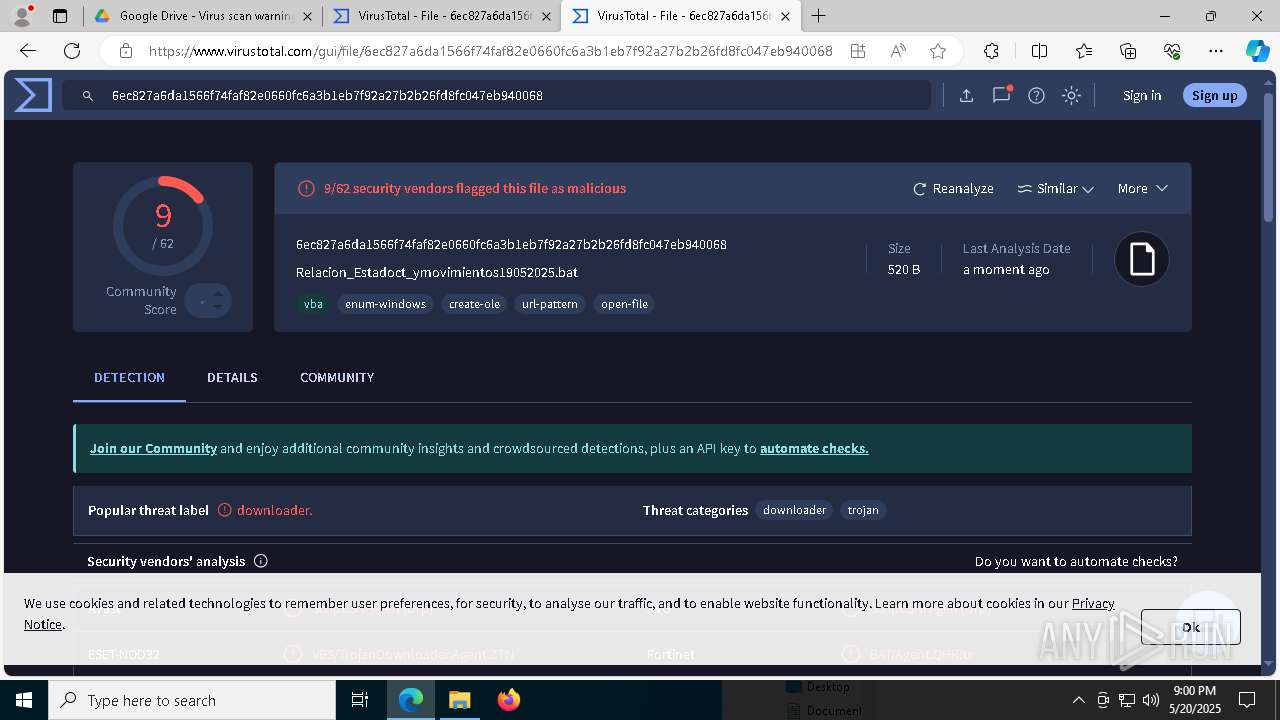
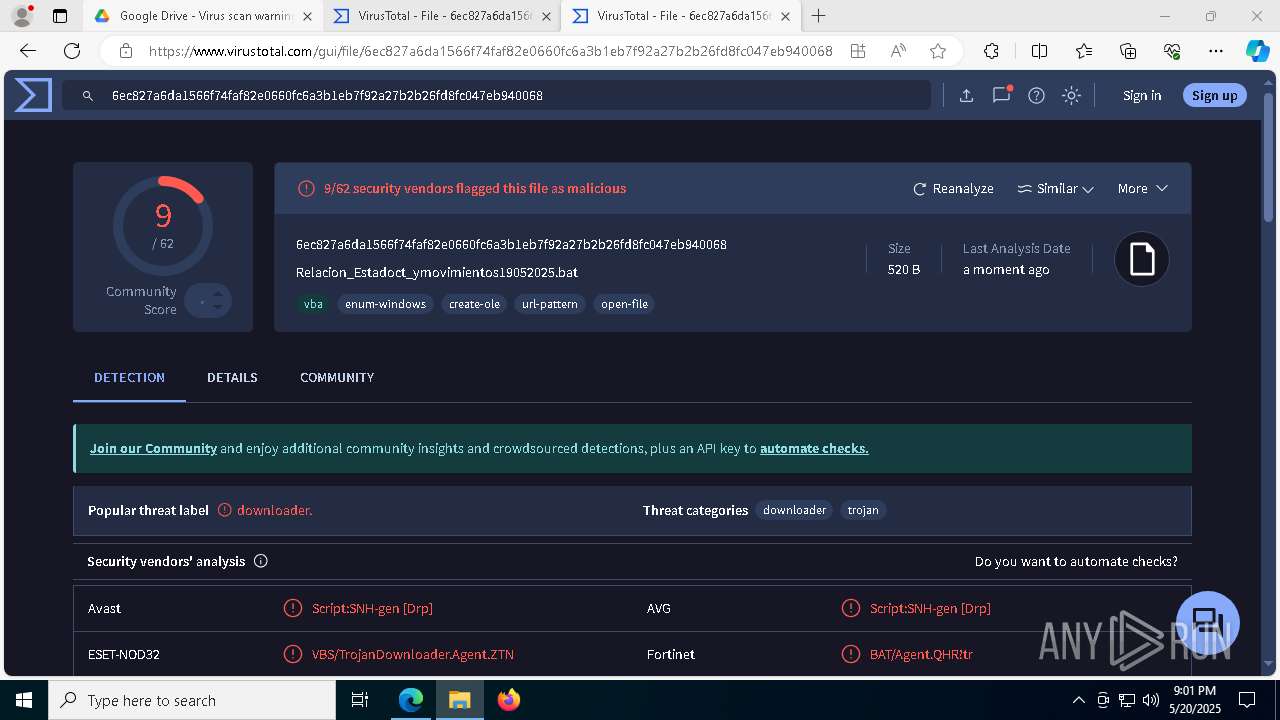
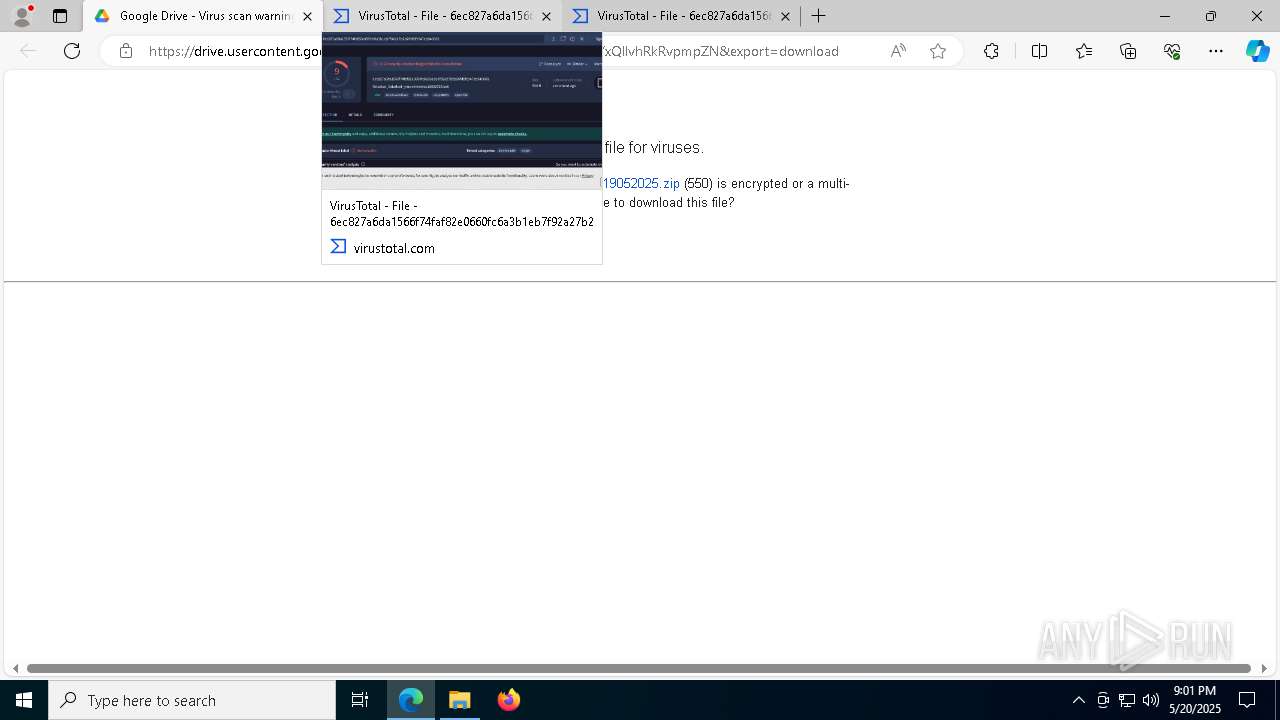
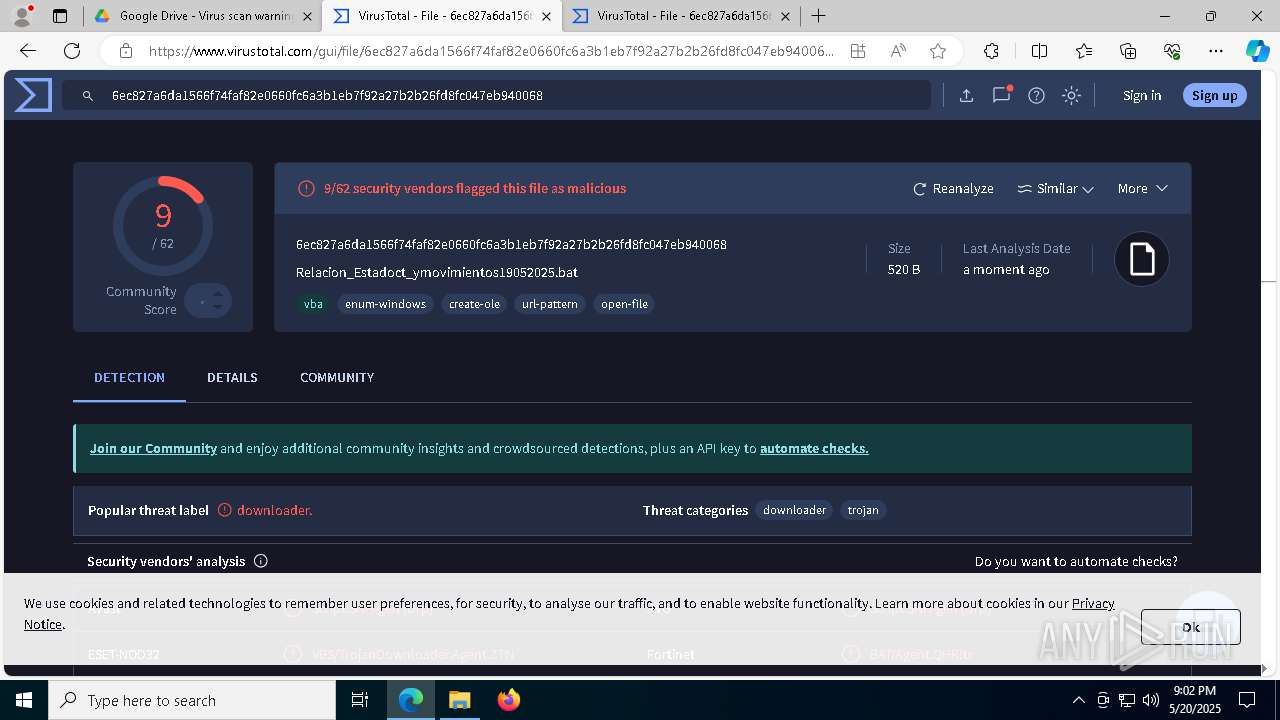
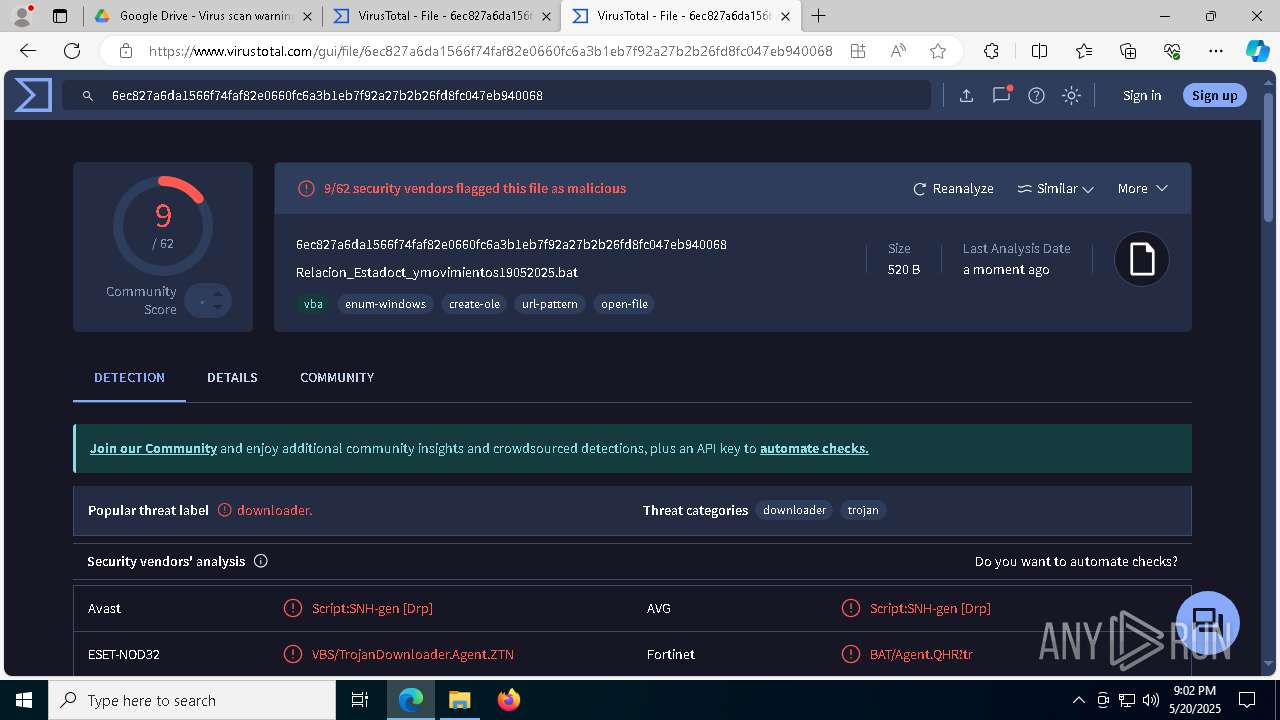
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 20, 2025, 20:59:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
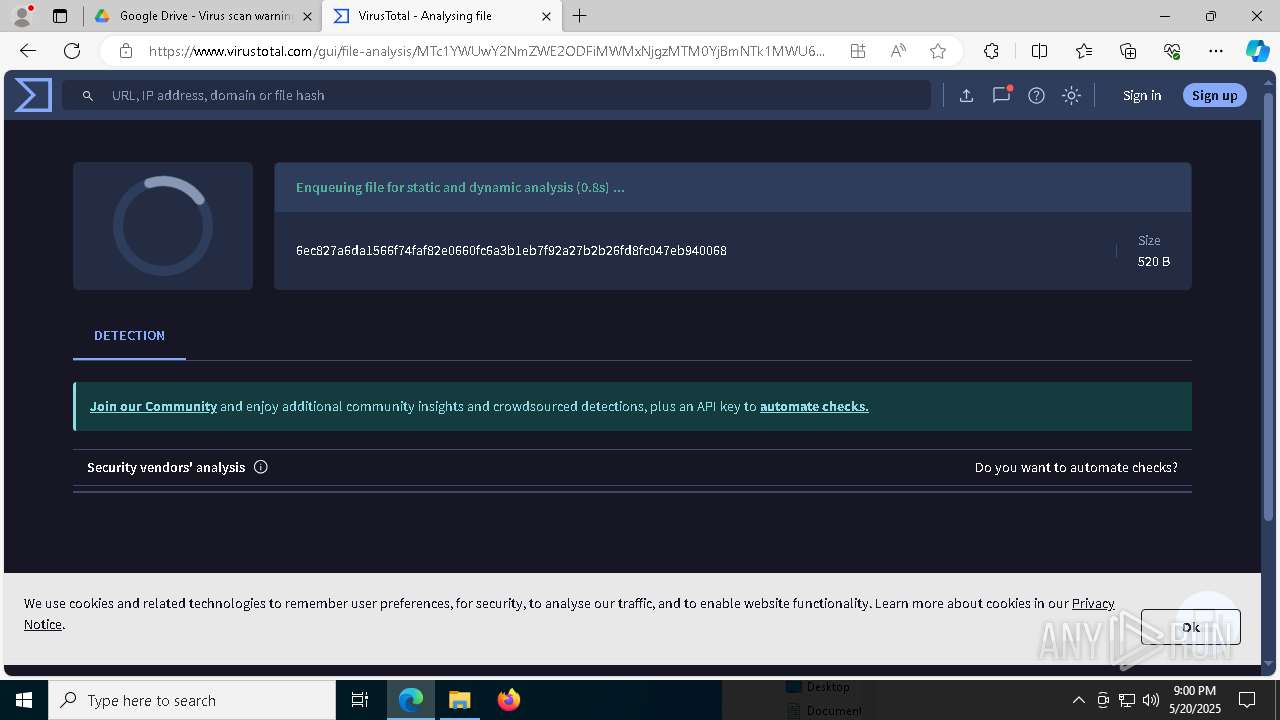
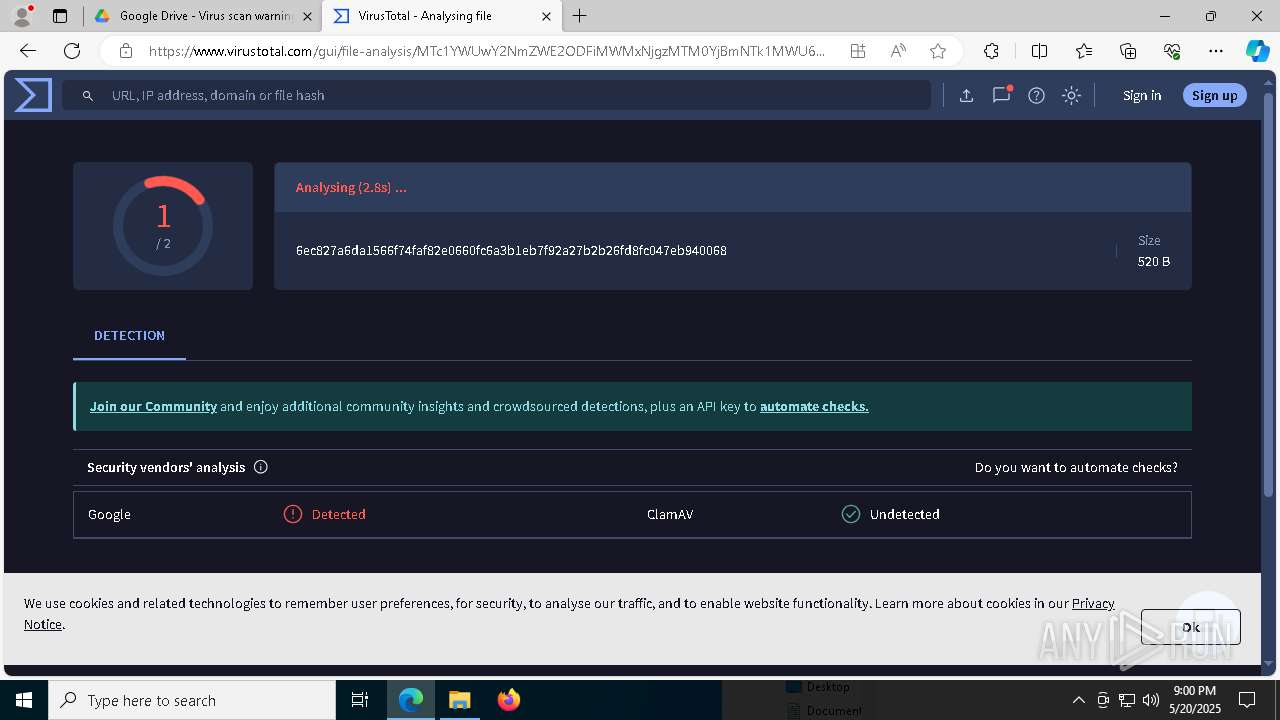
| MD5: | 76ACC94B0636312B4D15EFD716CBDED3 |
| SHA1: | 6544E2B7B5228644026742DCFB3CB3EB1D392DEA |
| SHA256: | 7D22F5766D7FC941BD0D792C0F834048F01388A15AF71707A23D1DE09BD9DEDC |
| SSDEEP: | 3:N8SP3u2NAaBrC2qsAOZMN3+2j:2Sm2BB+2Lz29 |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5376)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5376)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5376)
Run PowerShell with an invisible window
- powershell.exe (PID: 6592)
- powershell.exe (PID: 4932)
ASYNCRAT has been detected (SURICATA)
- InstallUtil.exe (PID: 5740)
SUSPICIOUS
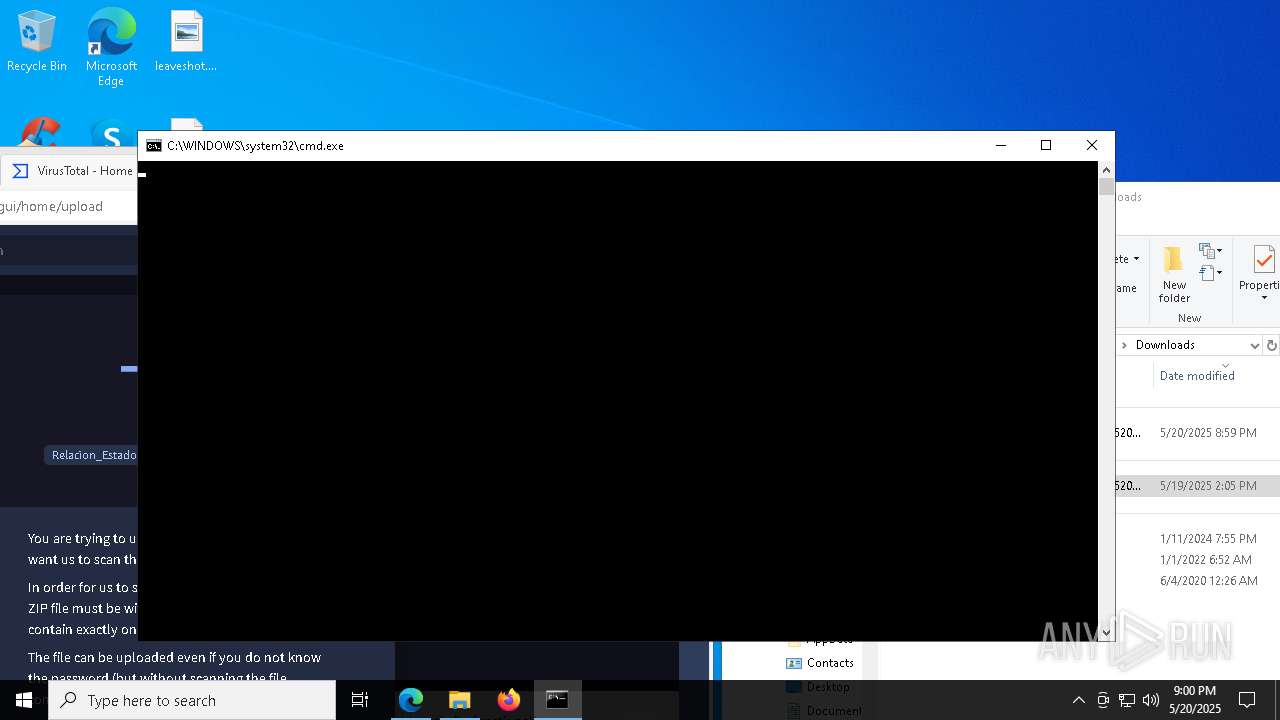
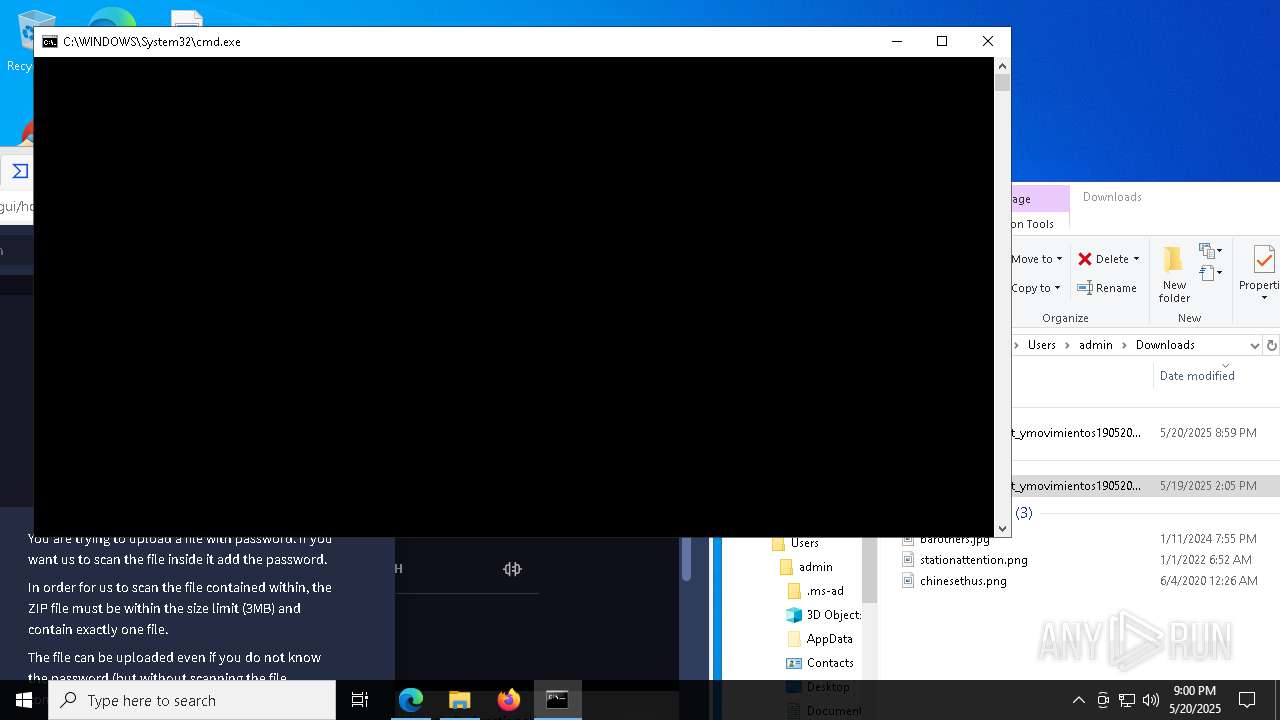
The process executes VB scripts
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6264)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6264)
Runs WScript without displaying logo
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5680)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5376)
Potential Corporate Privacy Violation
- wscript.exe (PID: 5376)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 4932)
- wscript.exe (PID: 5680)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5680)
Executes script without checking the security policy
- powershell.exe (PID: 6592)
- powershell.exe (PID: 4932)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5680)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5680)
Base64-obfuscated command line is found
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5680)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5680)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 5556)
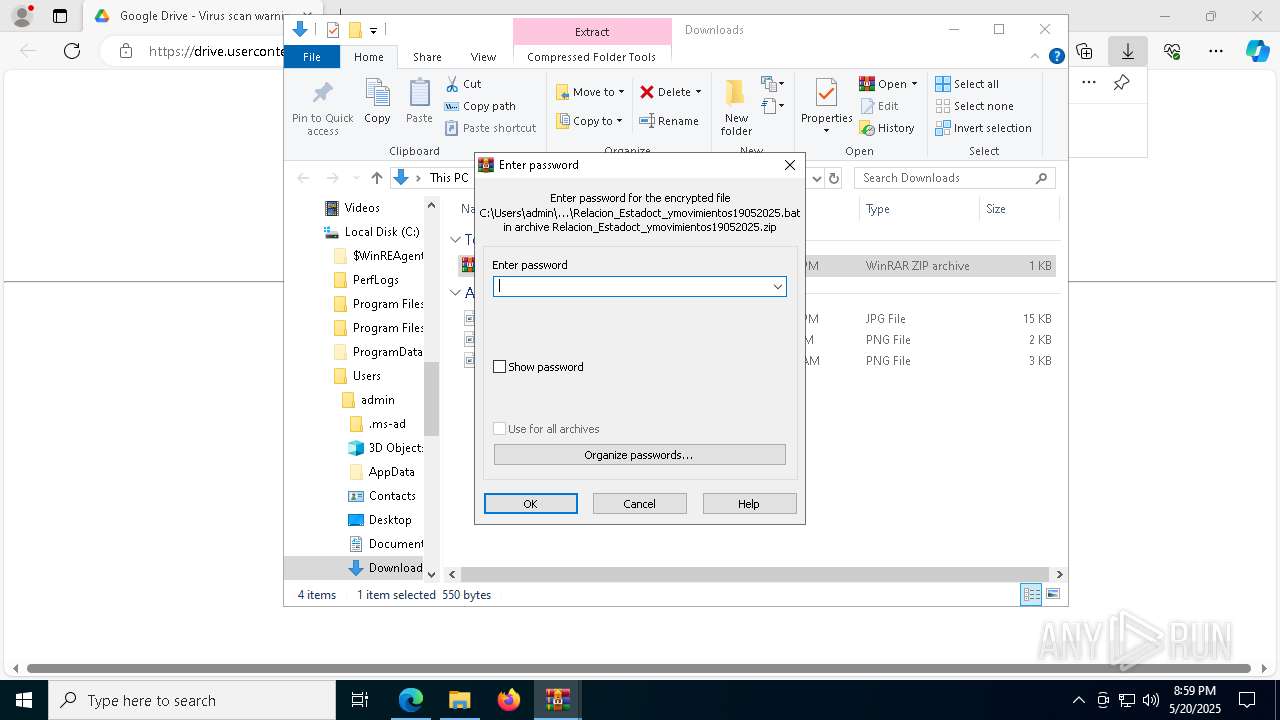
Executing commands from a ".bat" file
- powershell.exe (PID: 6592)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6592)
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 5740)
Connects to unusual port
- InstallUtil.exe (PID: 5740)
INFO
Checks supported languages
- identity_helper.exe (PID: 6988)
Reads the computer name
- identity_helper.exe (PID: 6988)
Application launched itself
- msedge.exe (PID: 6344)
Reads Environment values
- identity_helper.exe (PID: 6988)
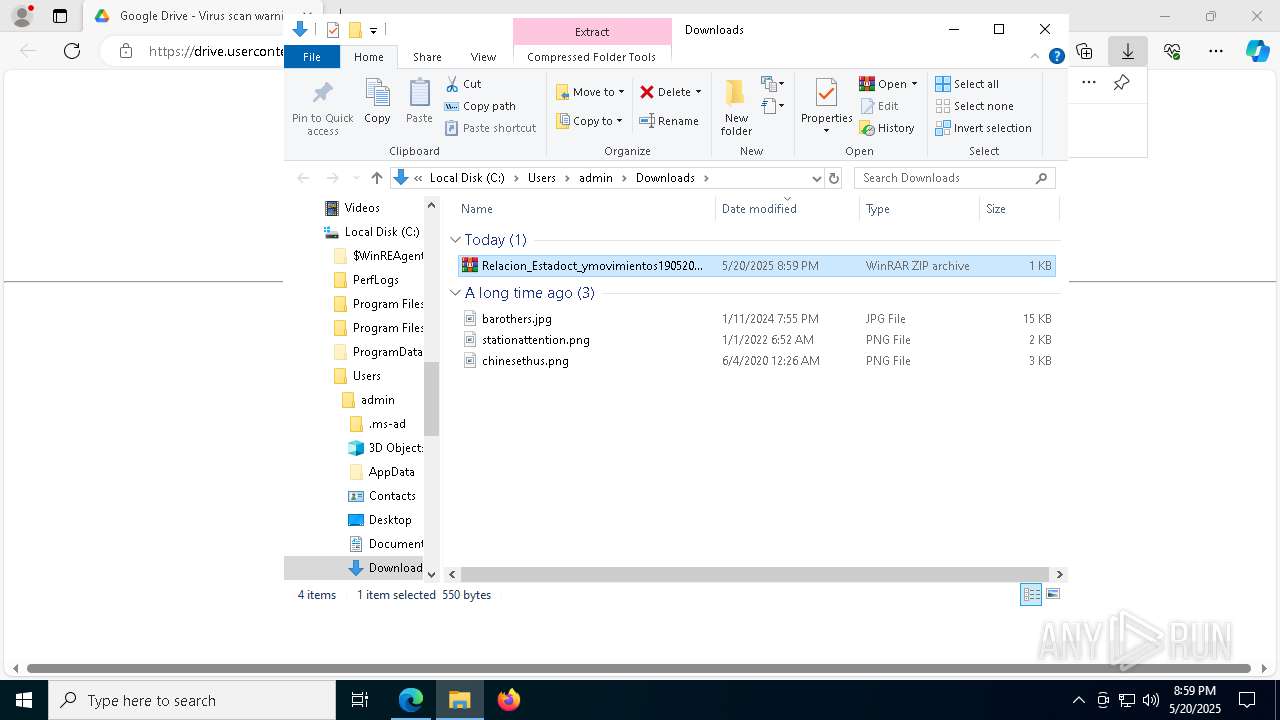
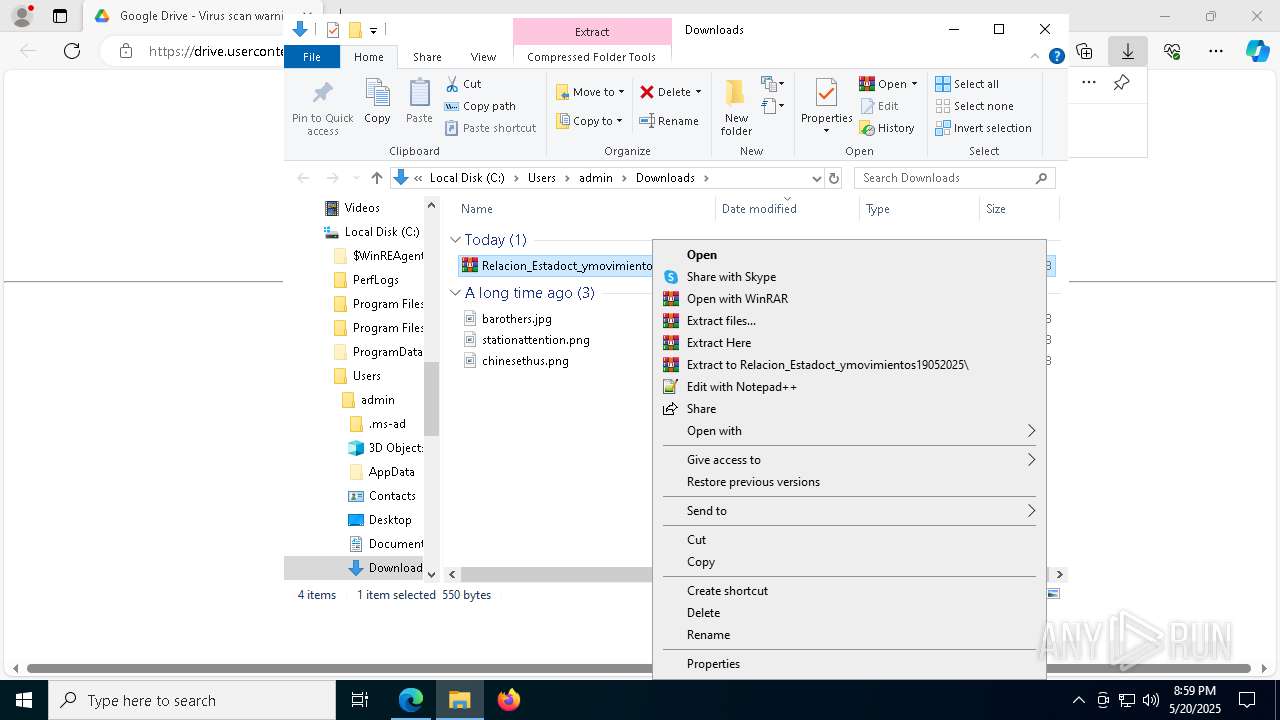
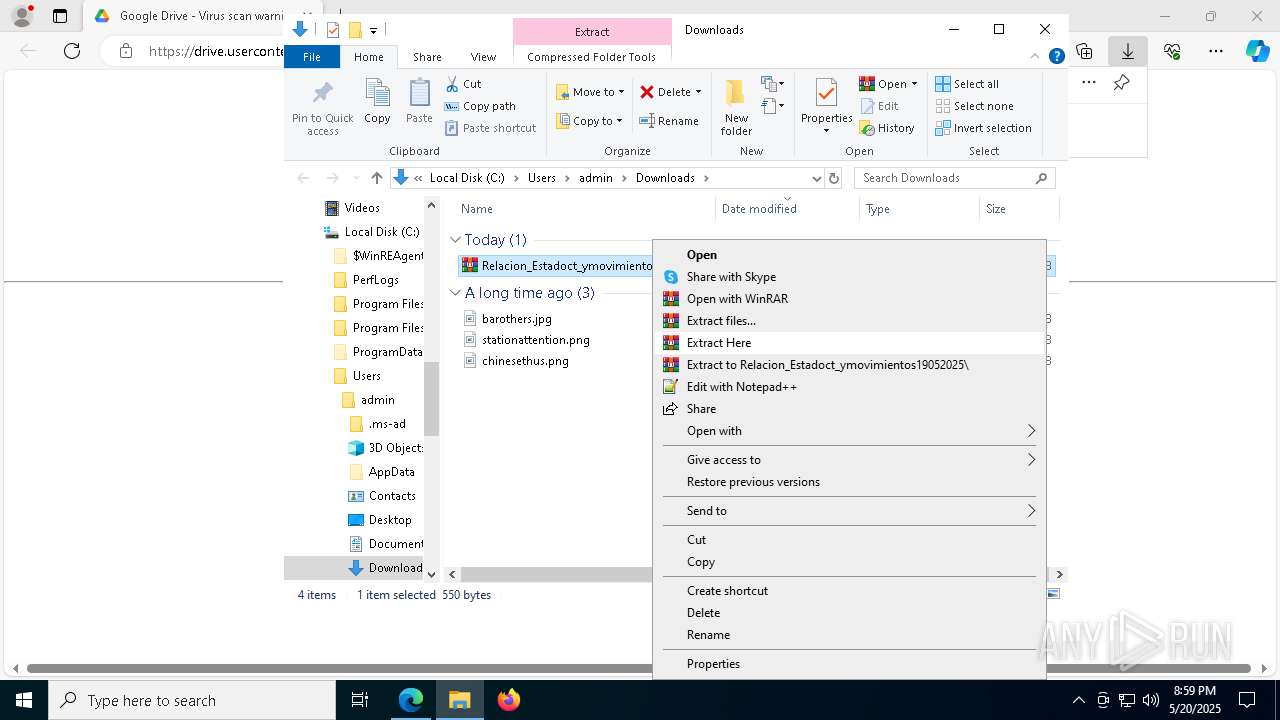
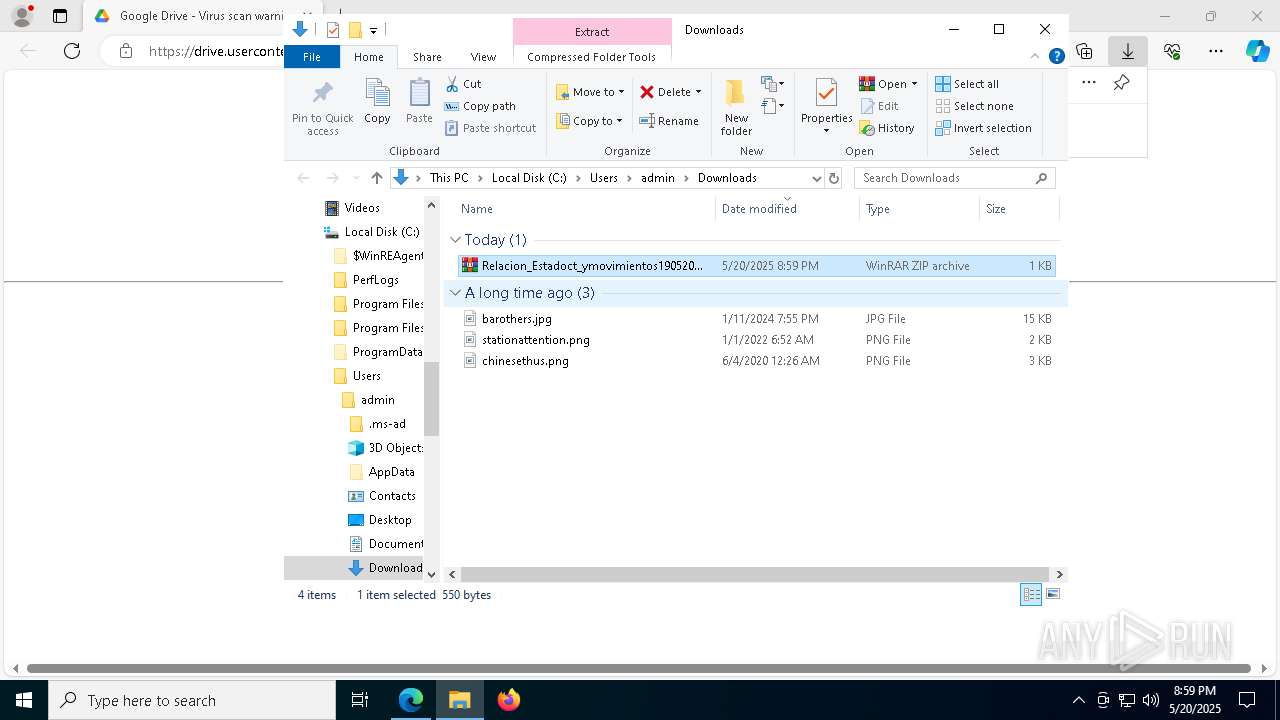
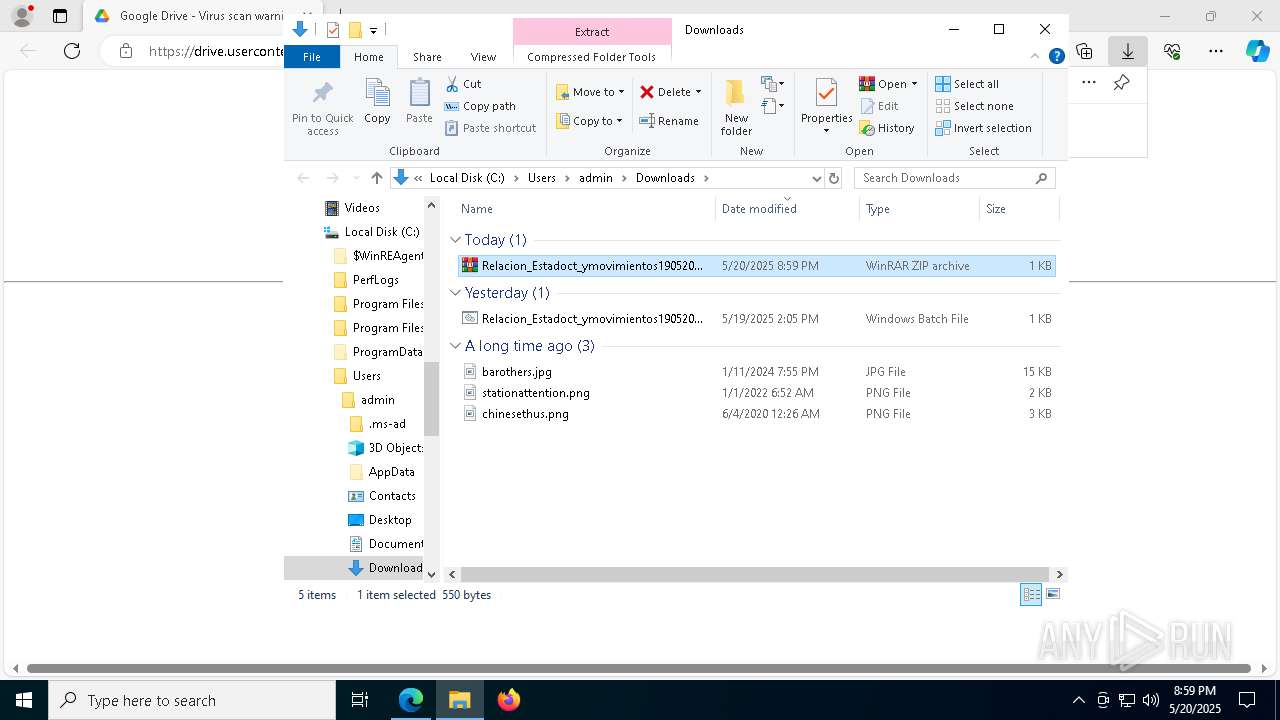
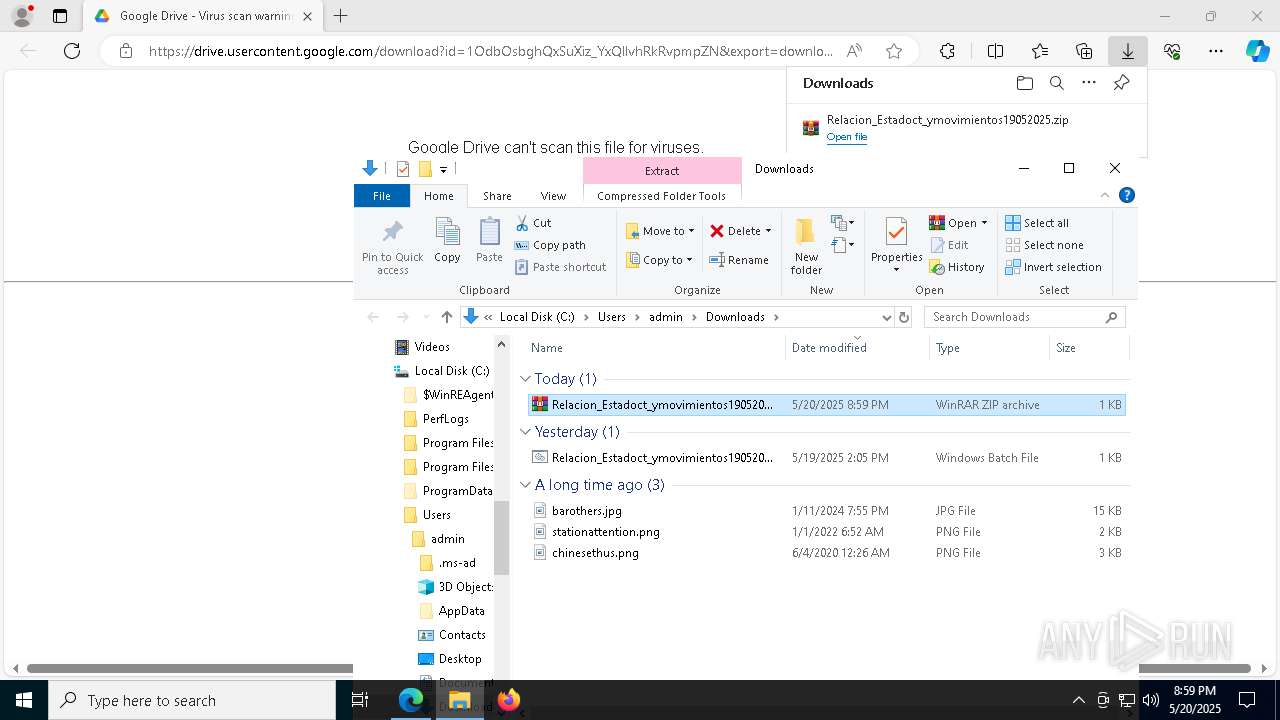
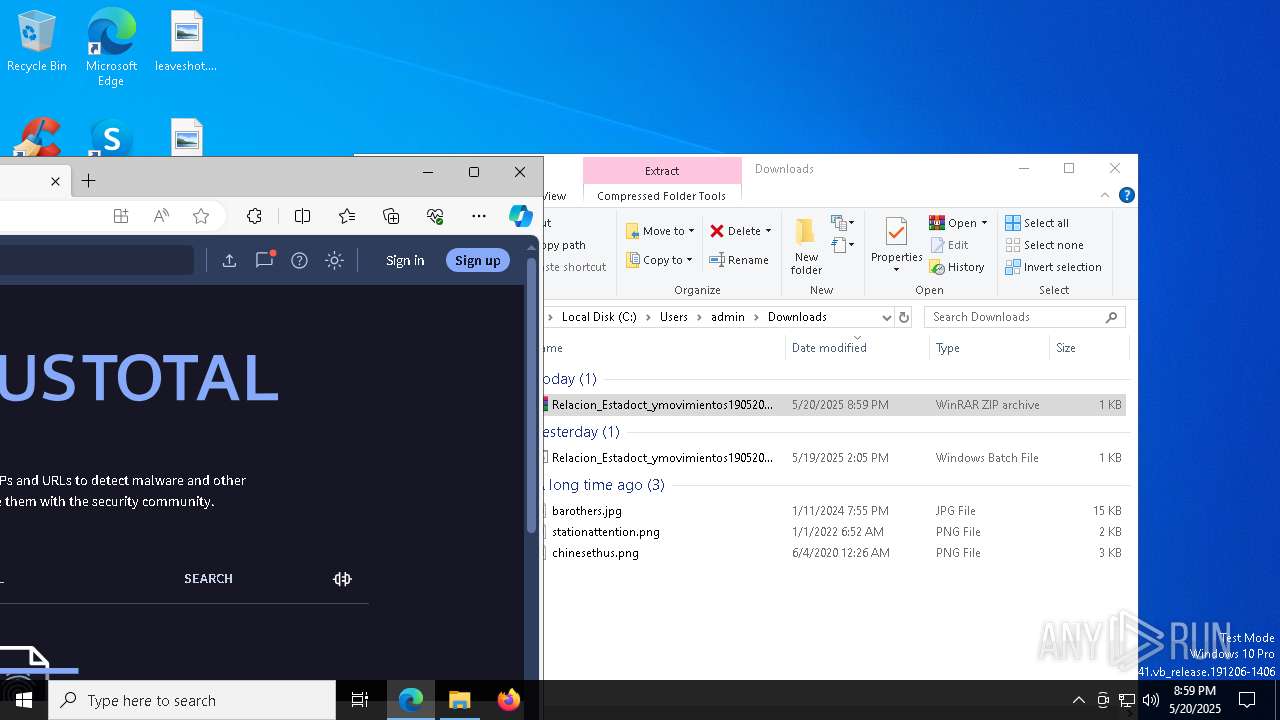
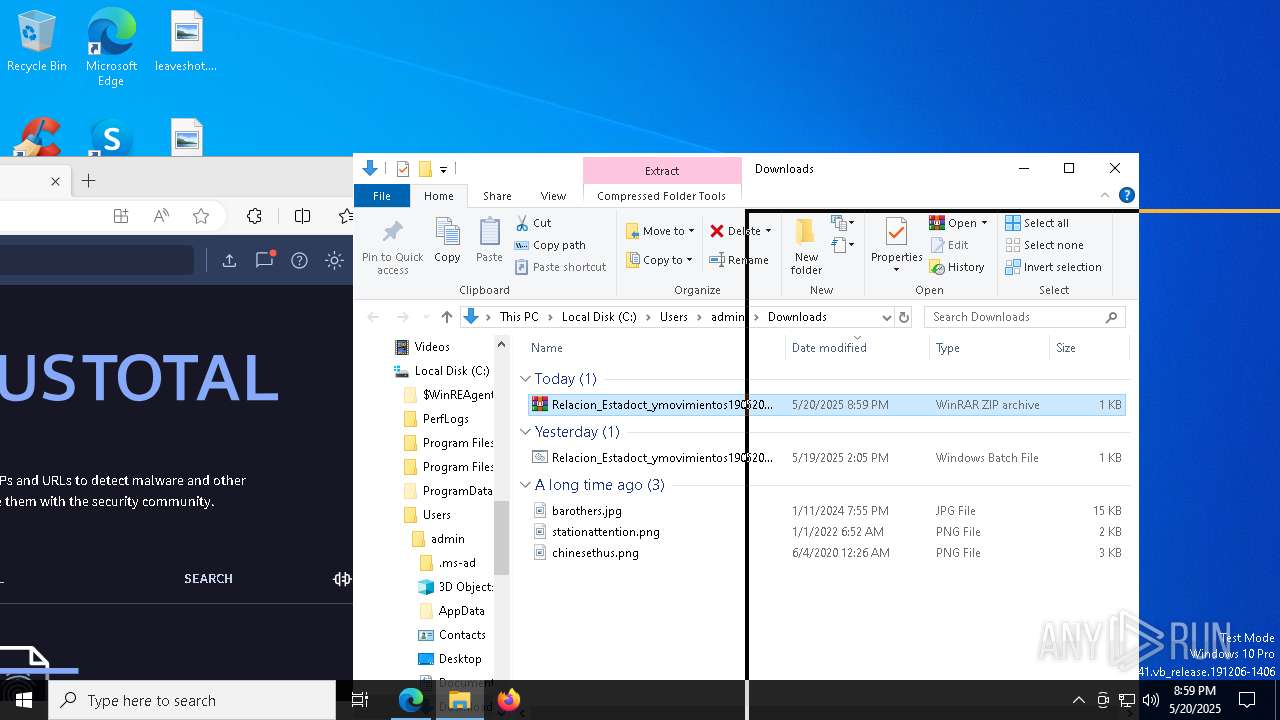
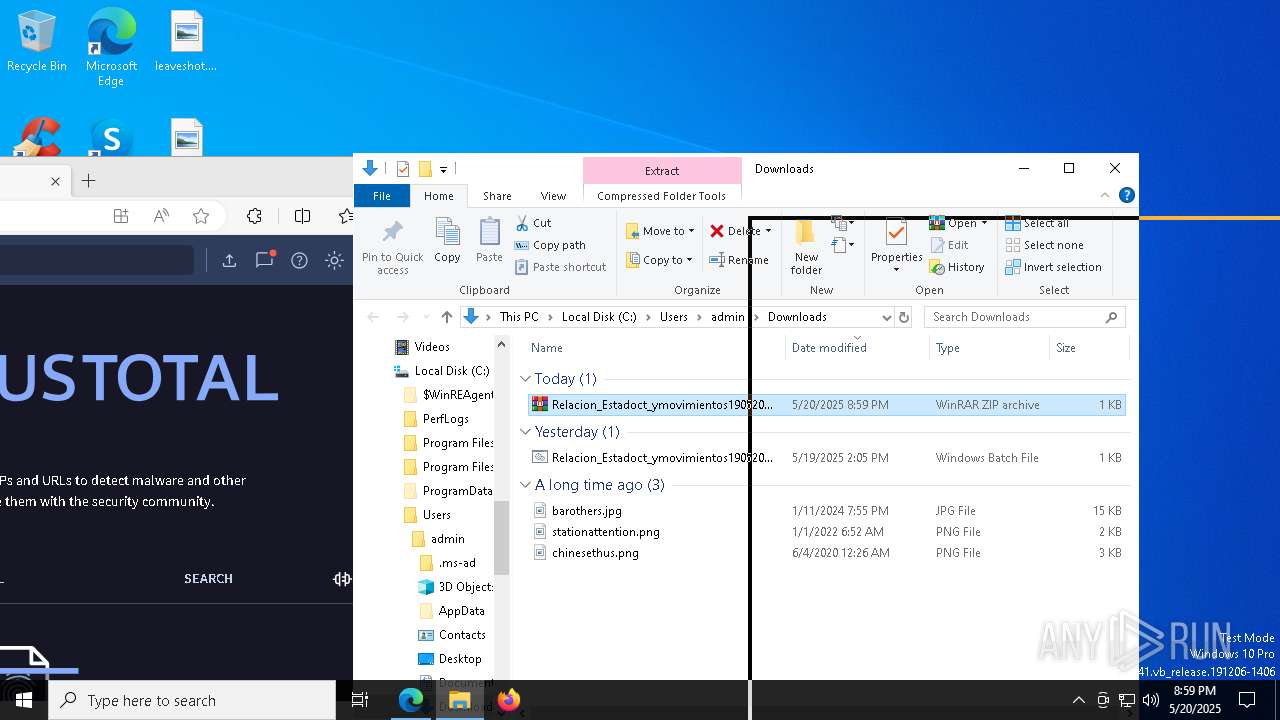
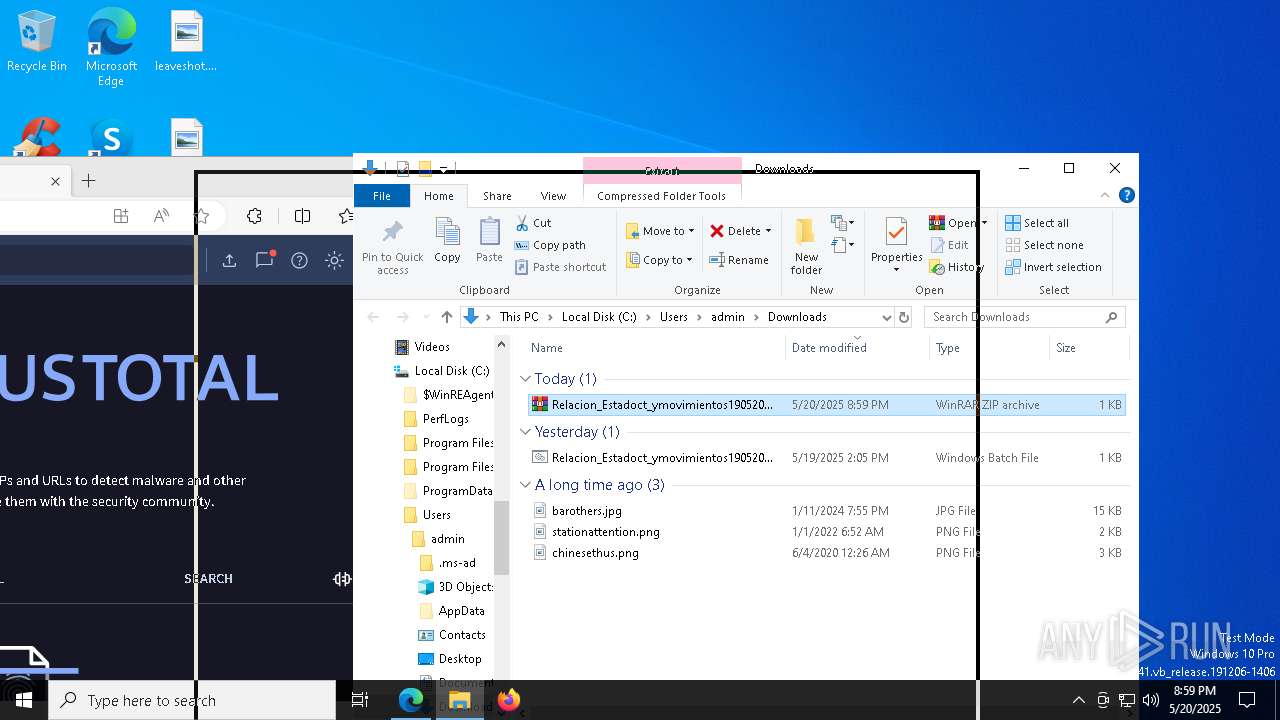
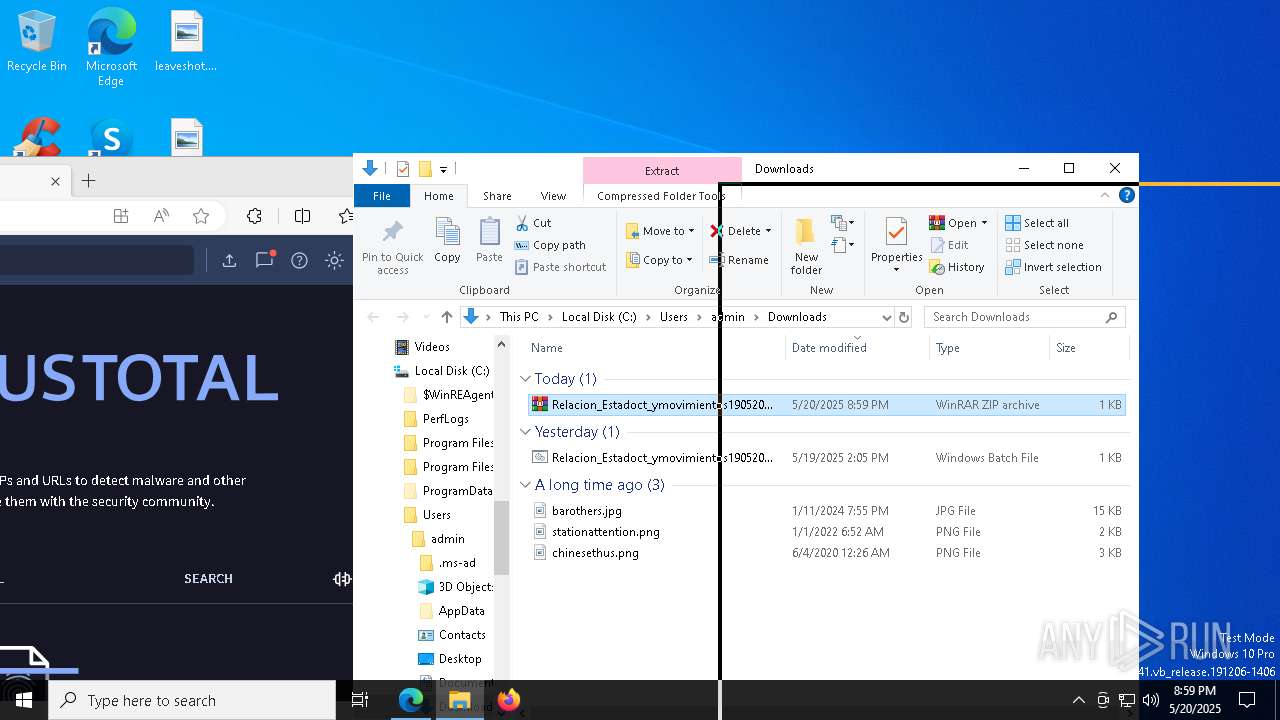
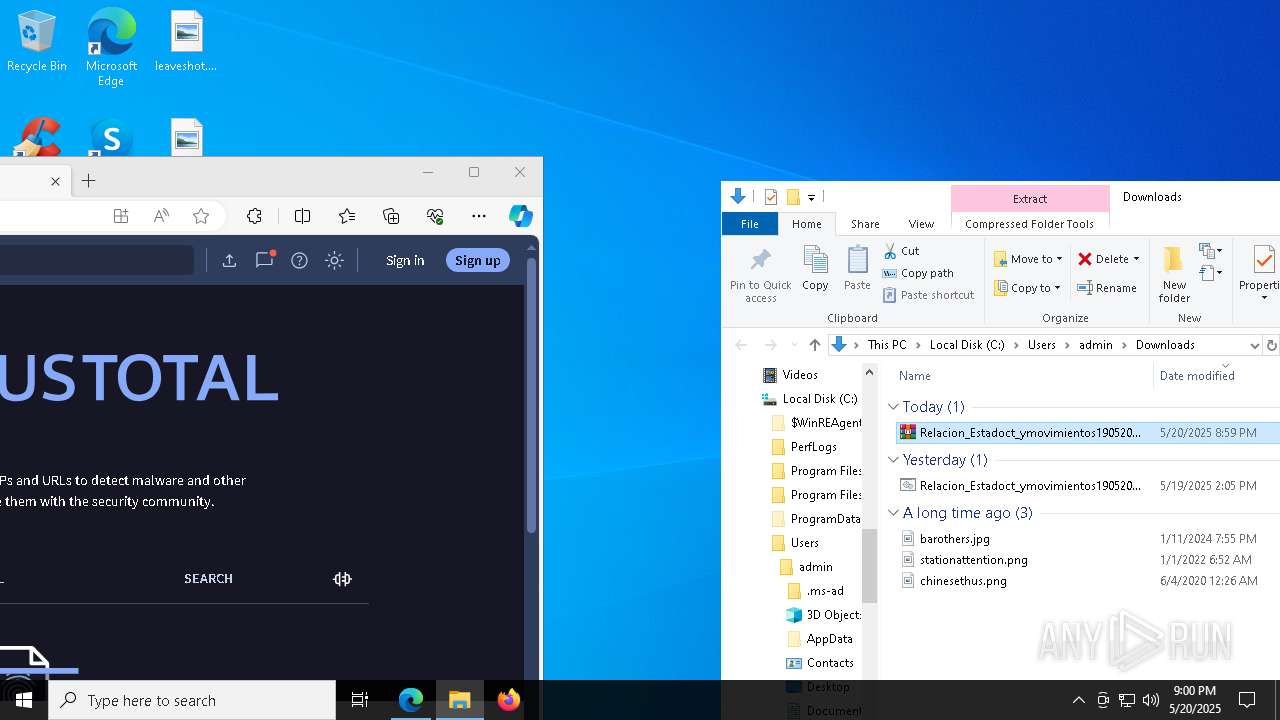
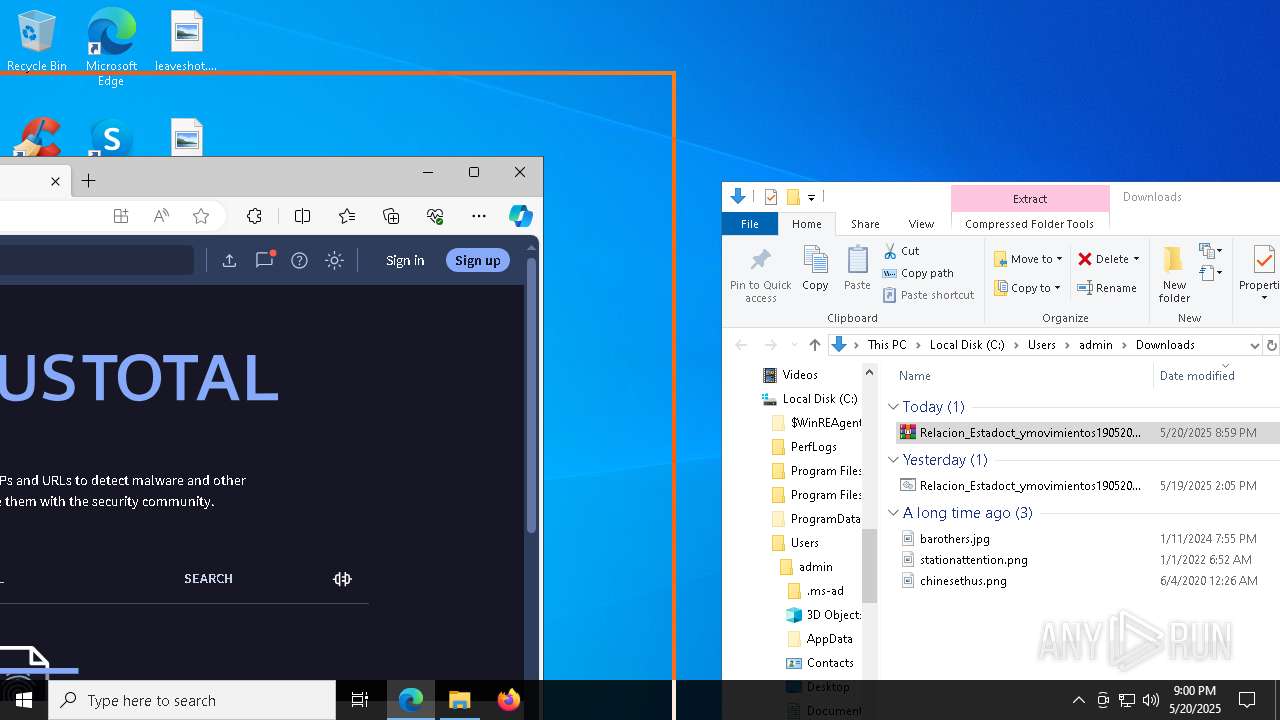
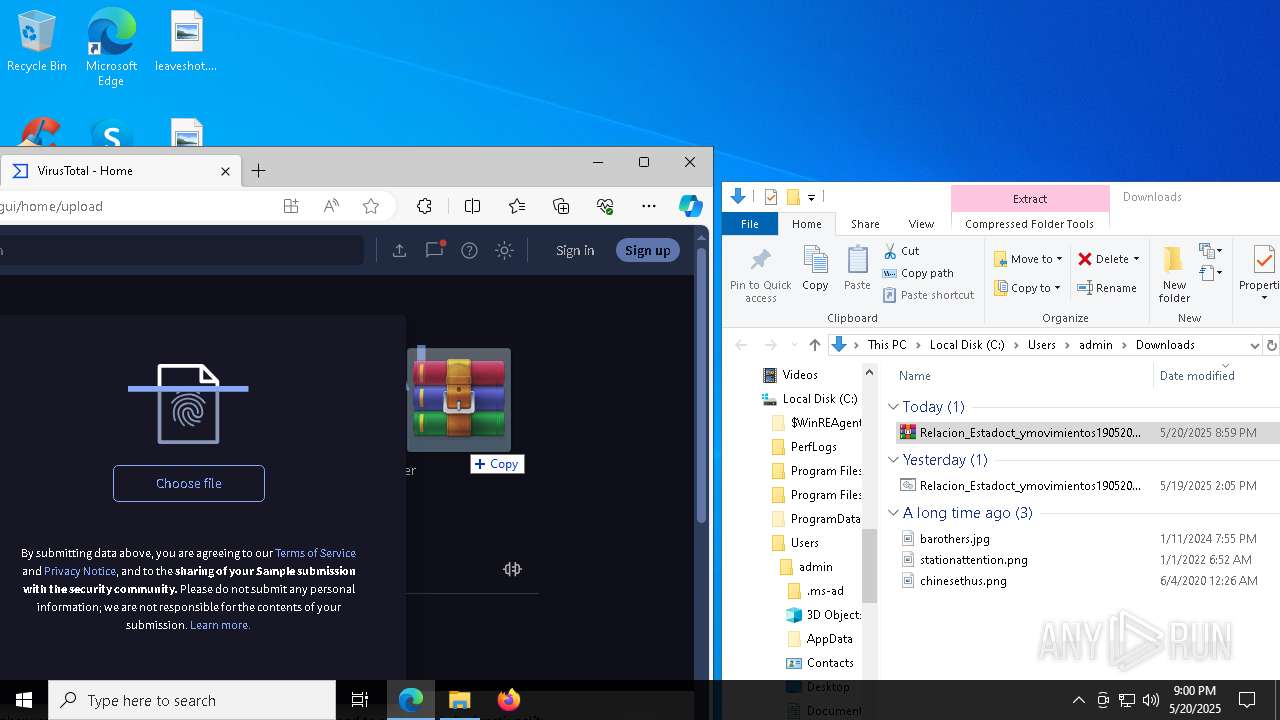
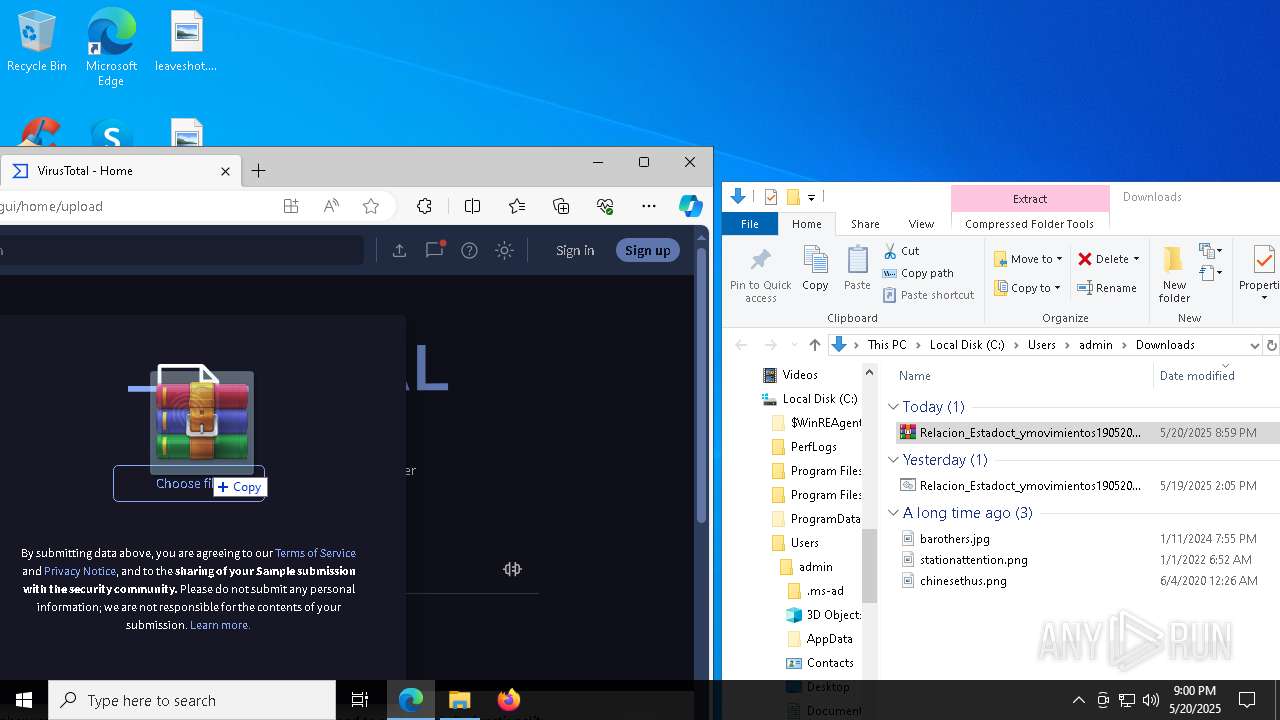
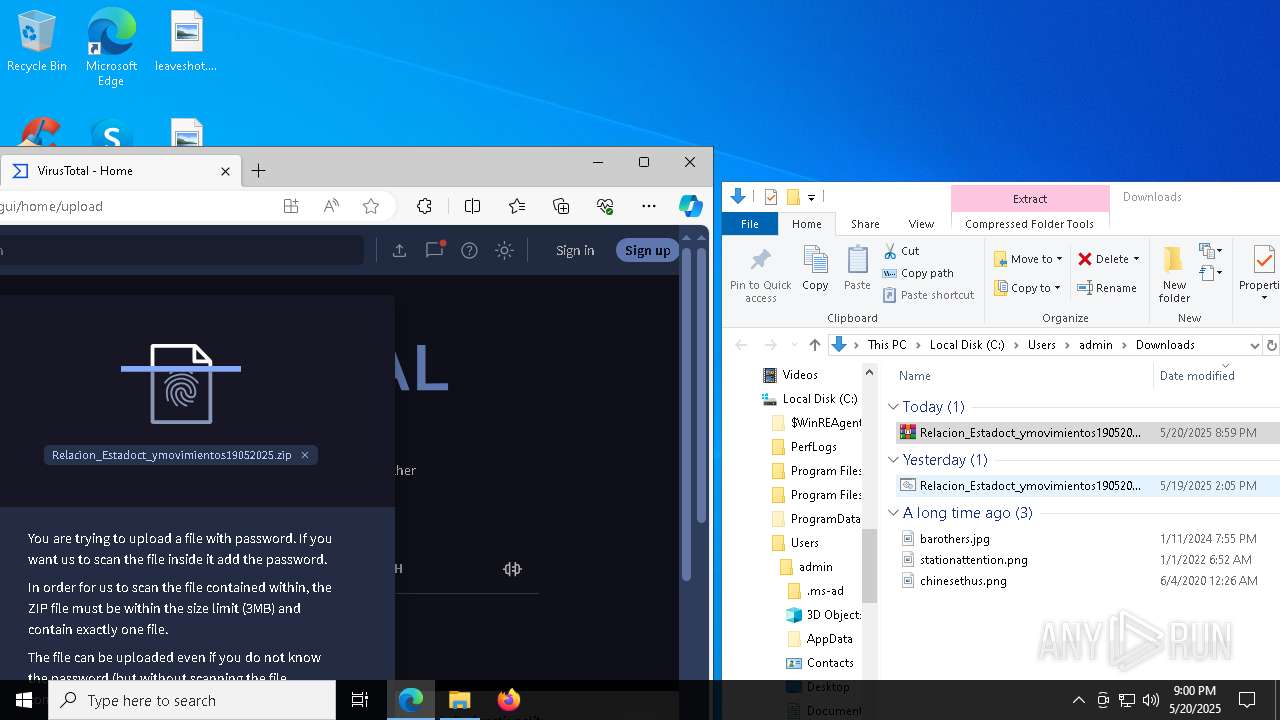
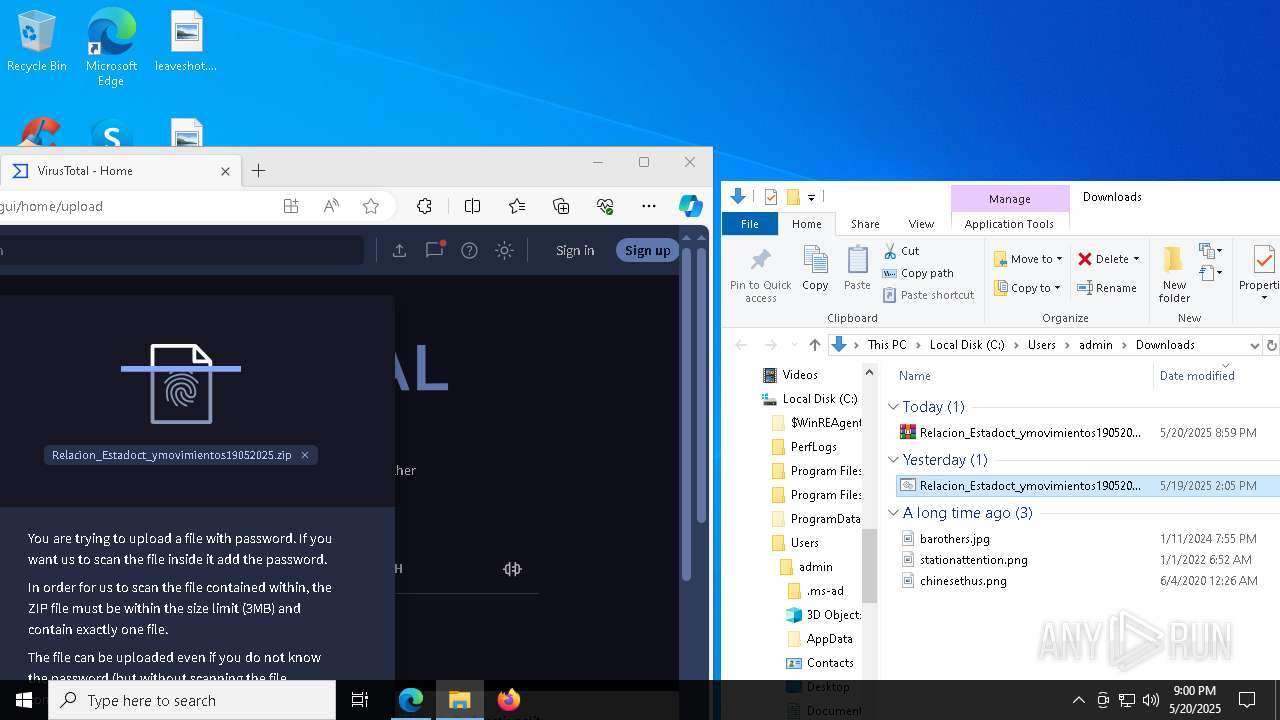
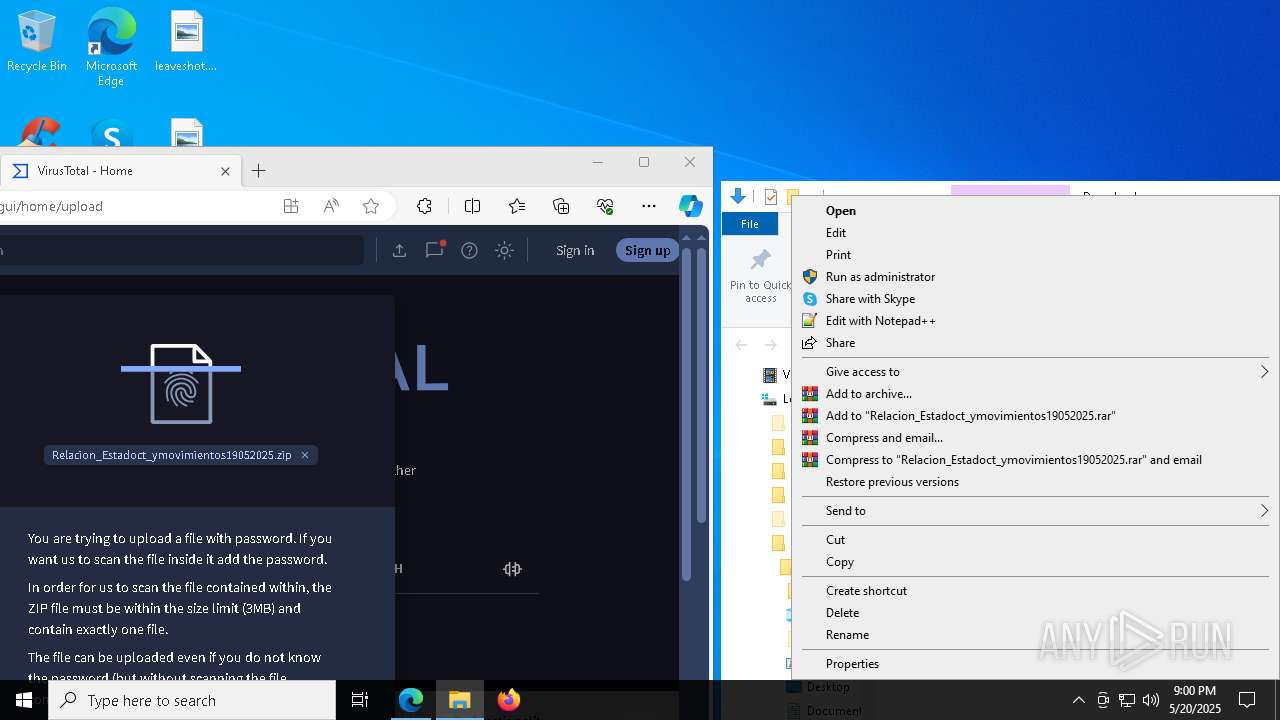
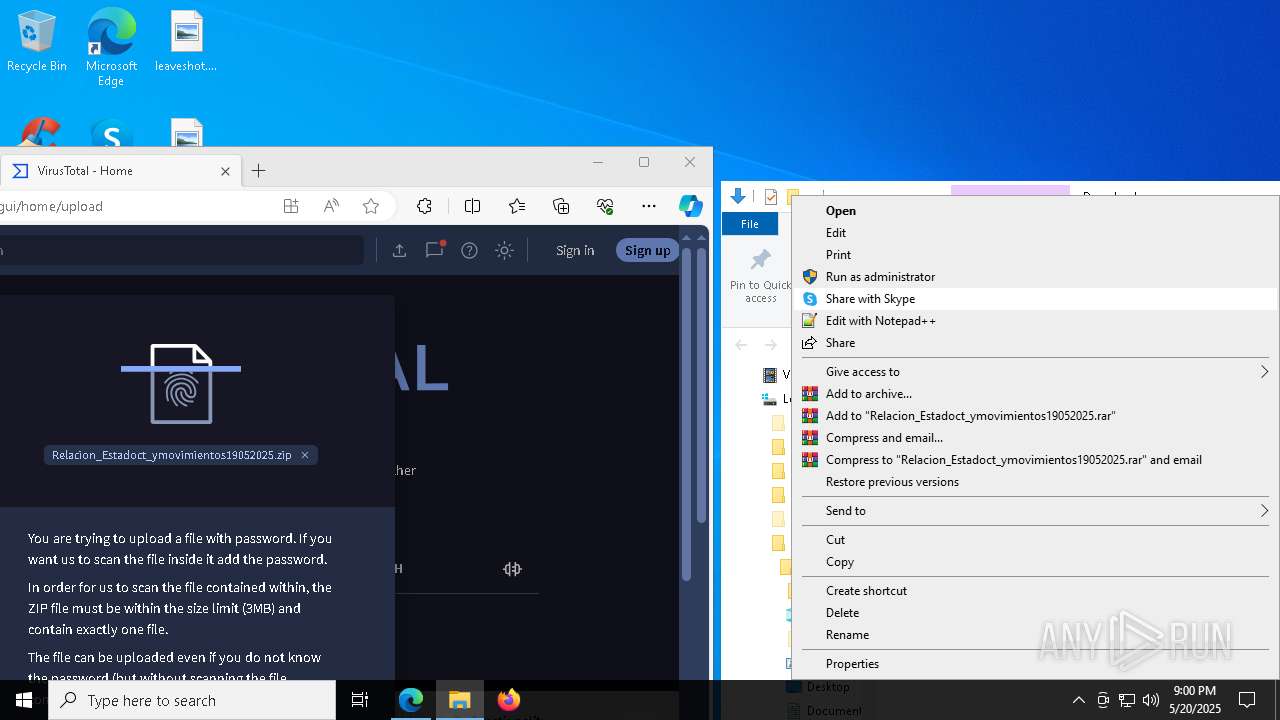
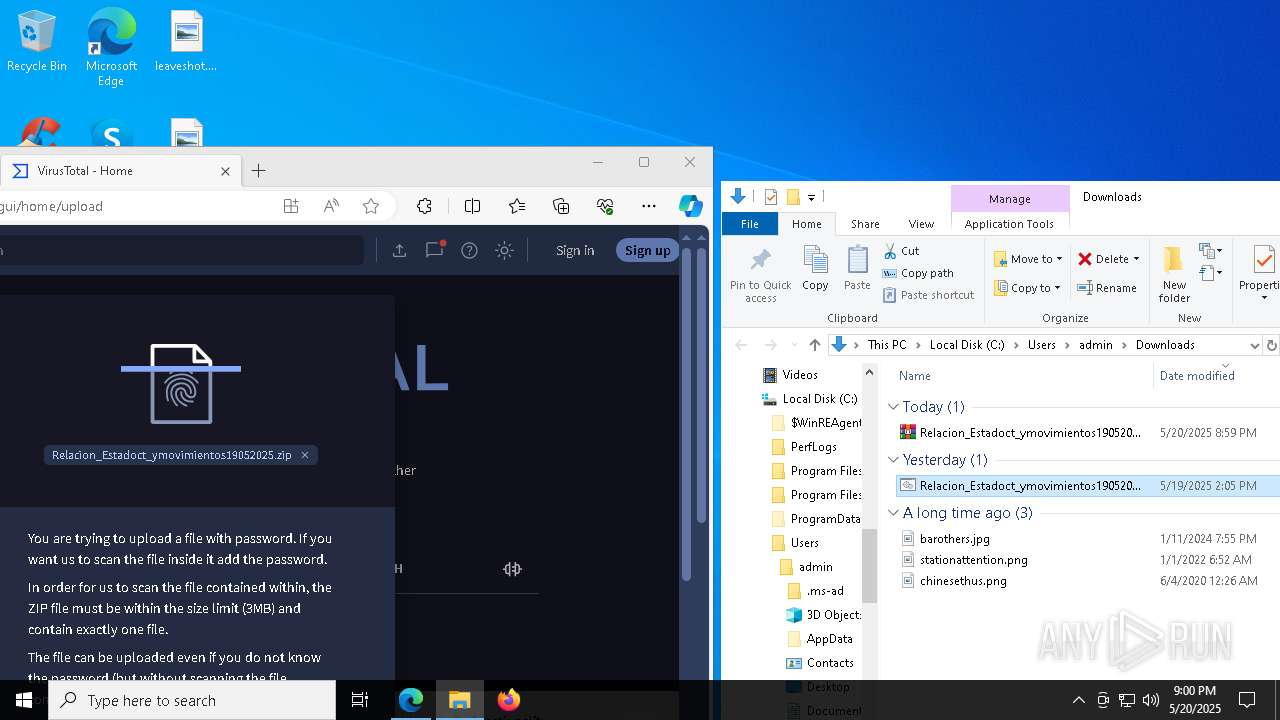
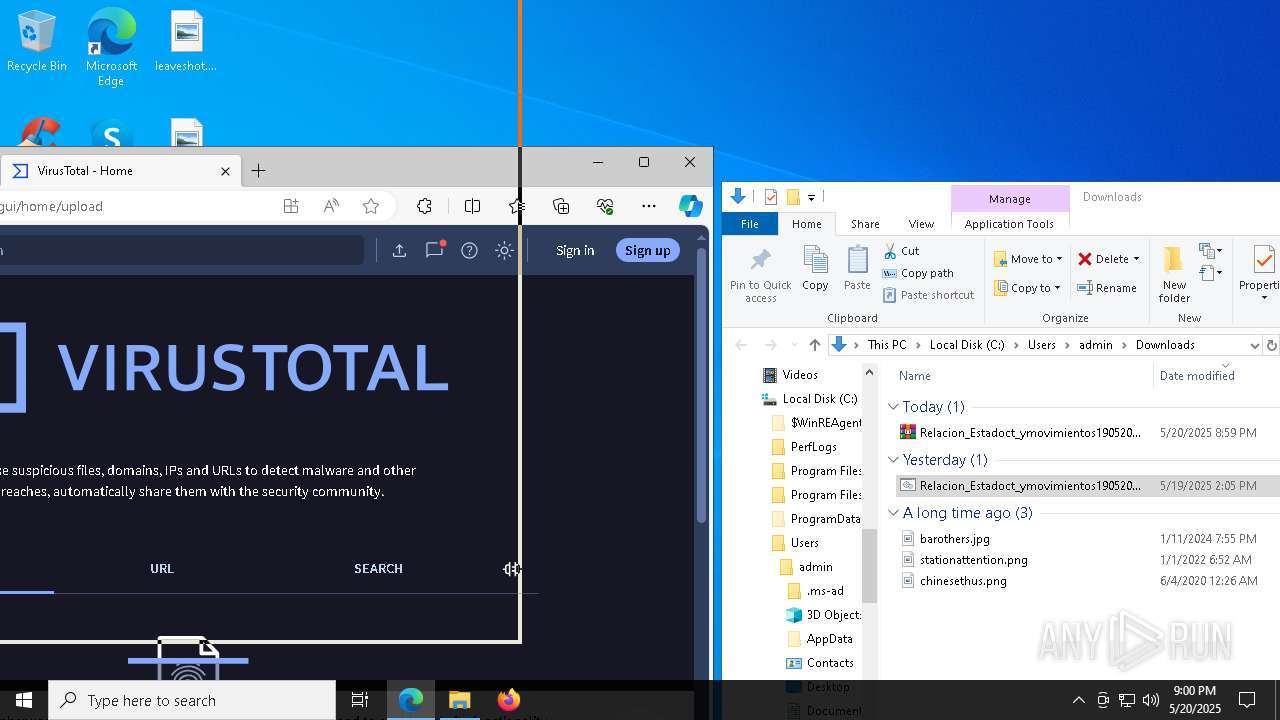
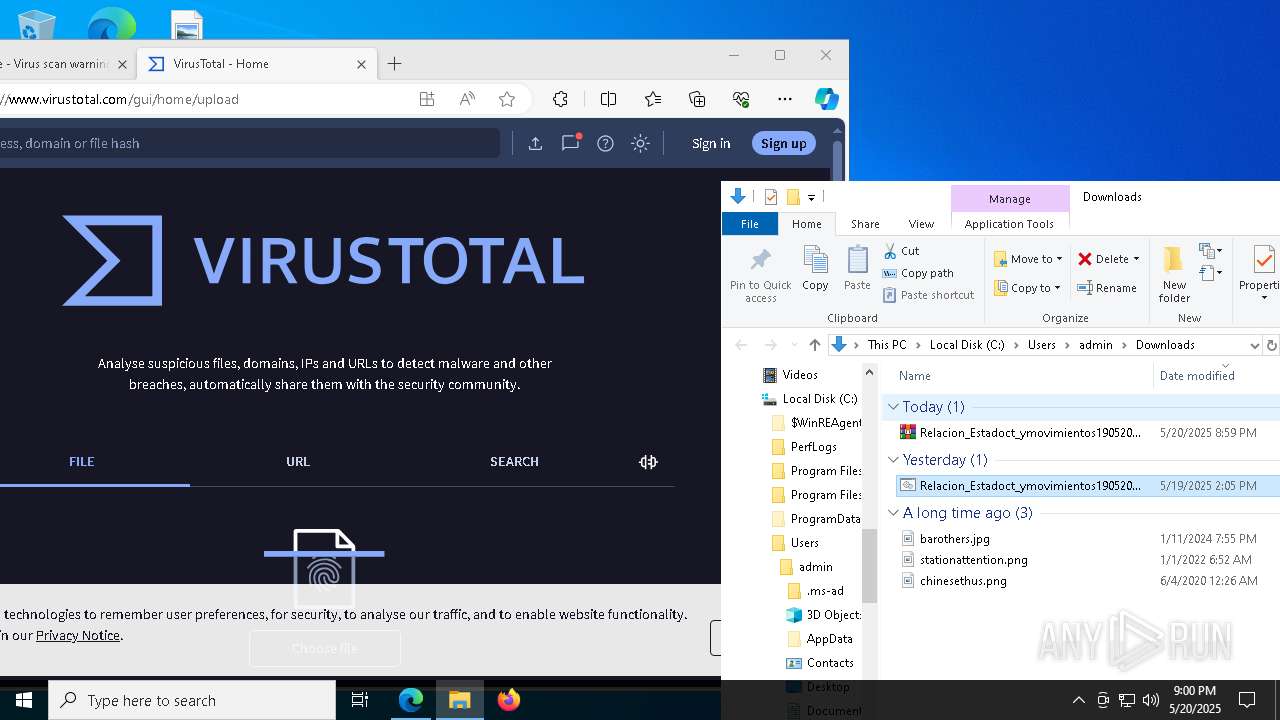
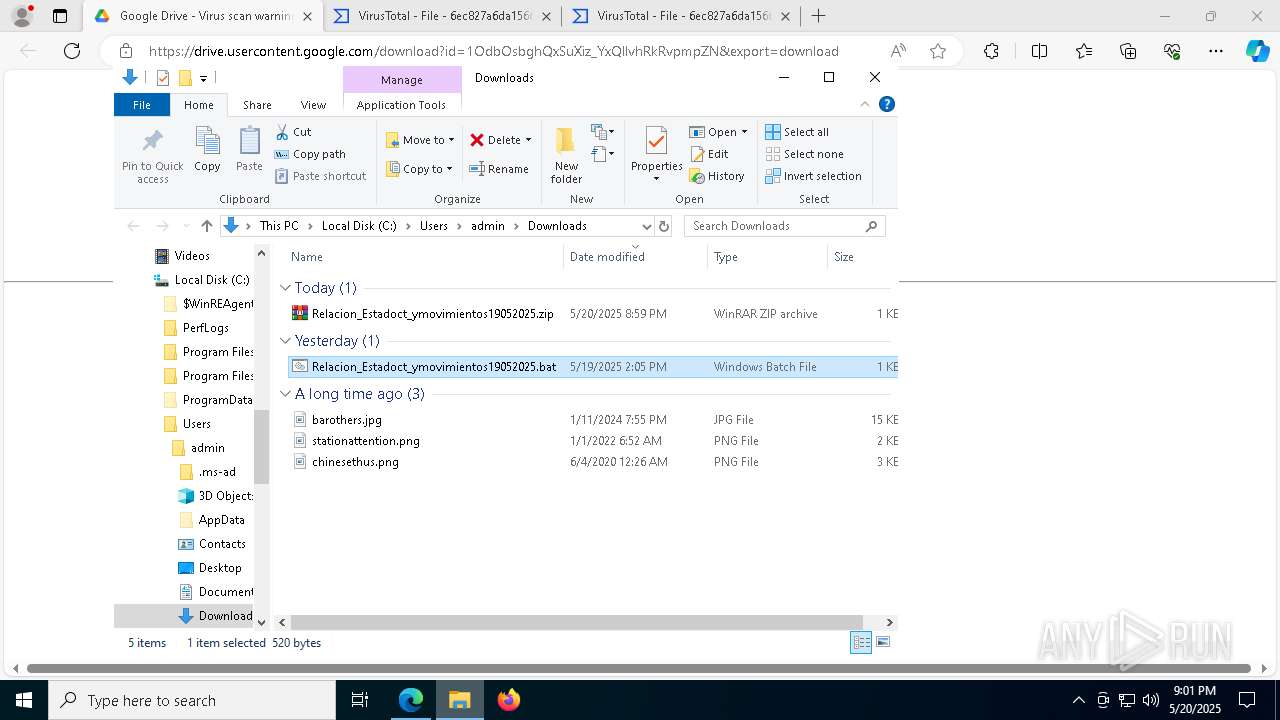
Manual execution by a user
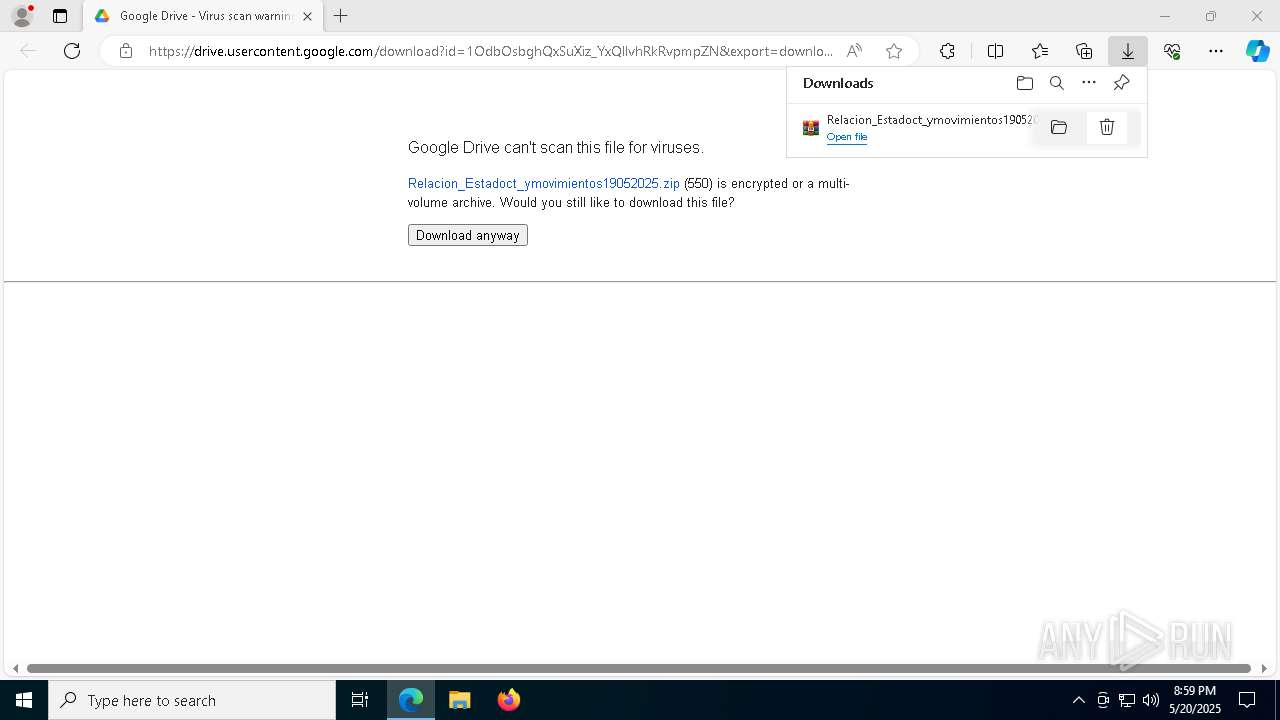
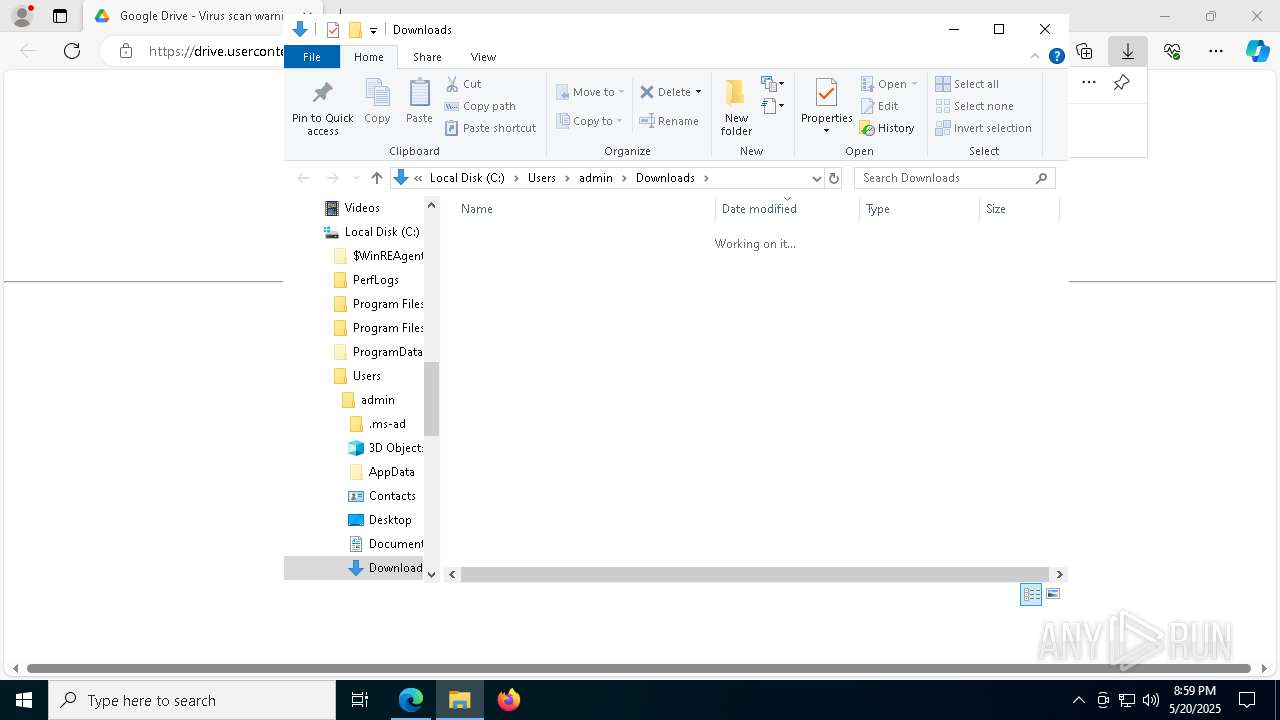
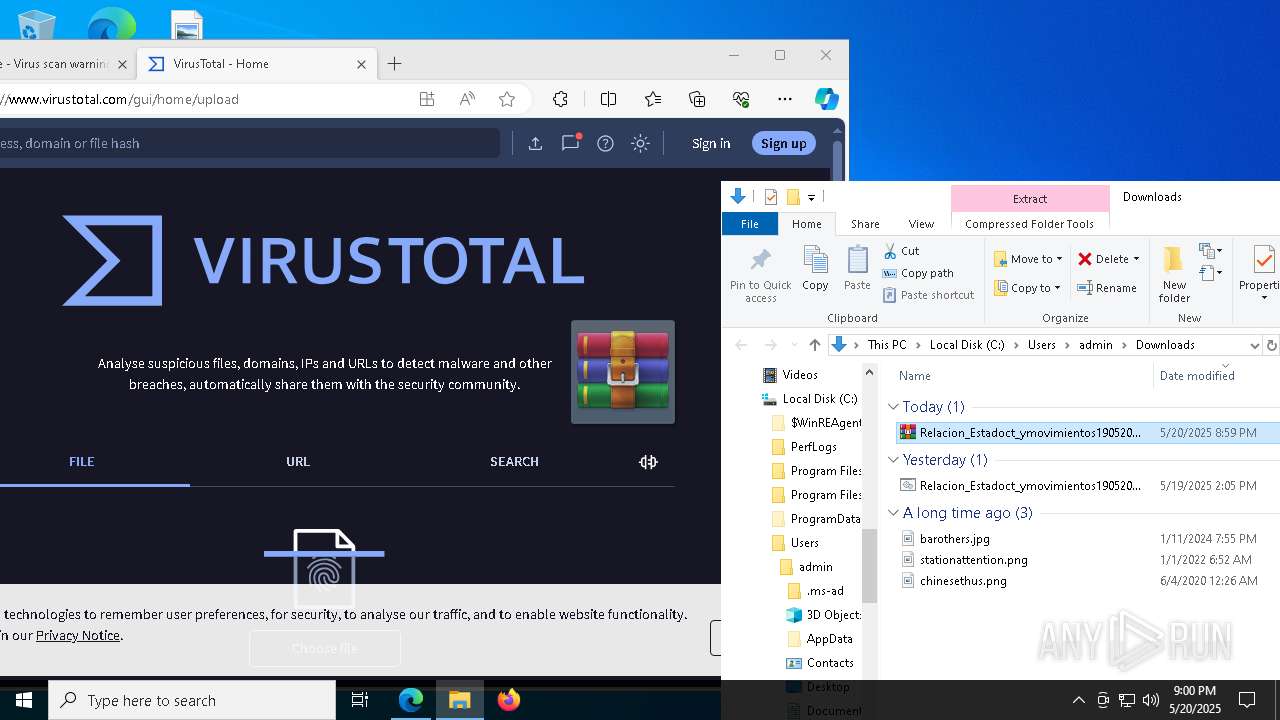
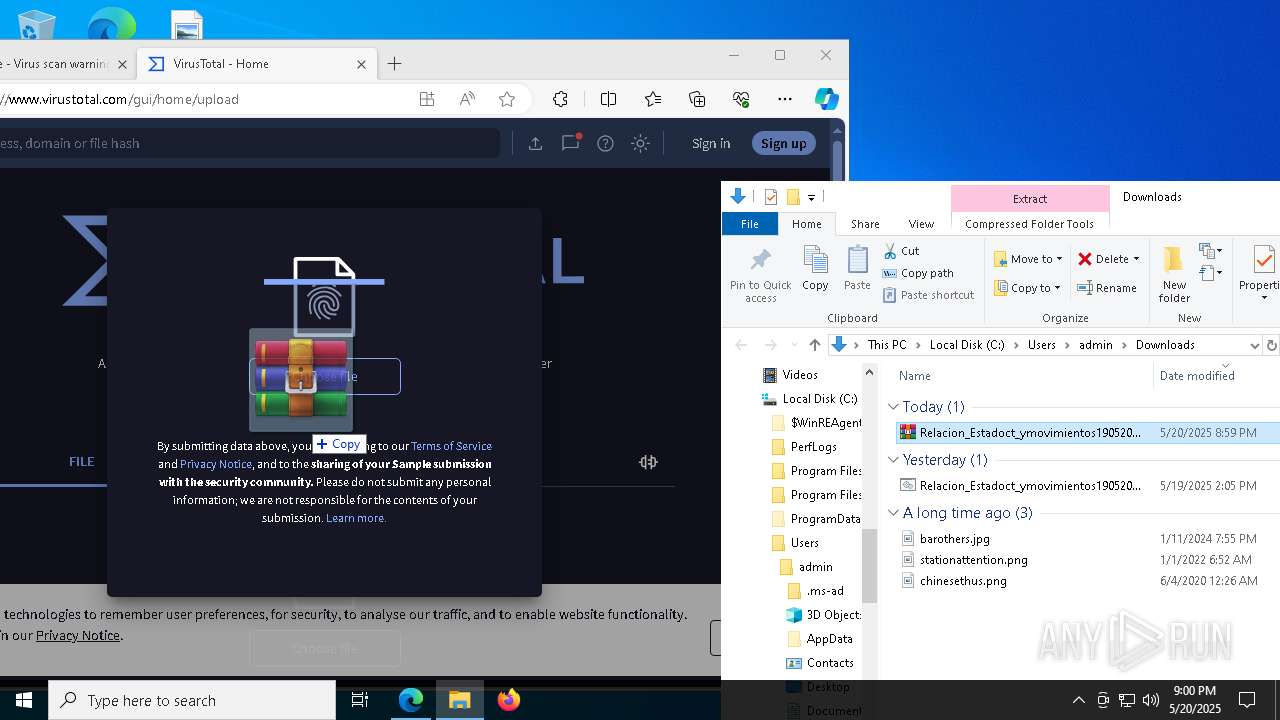
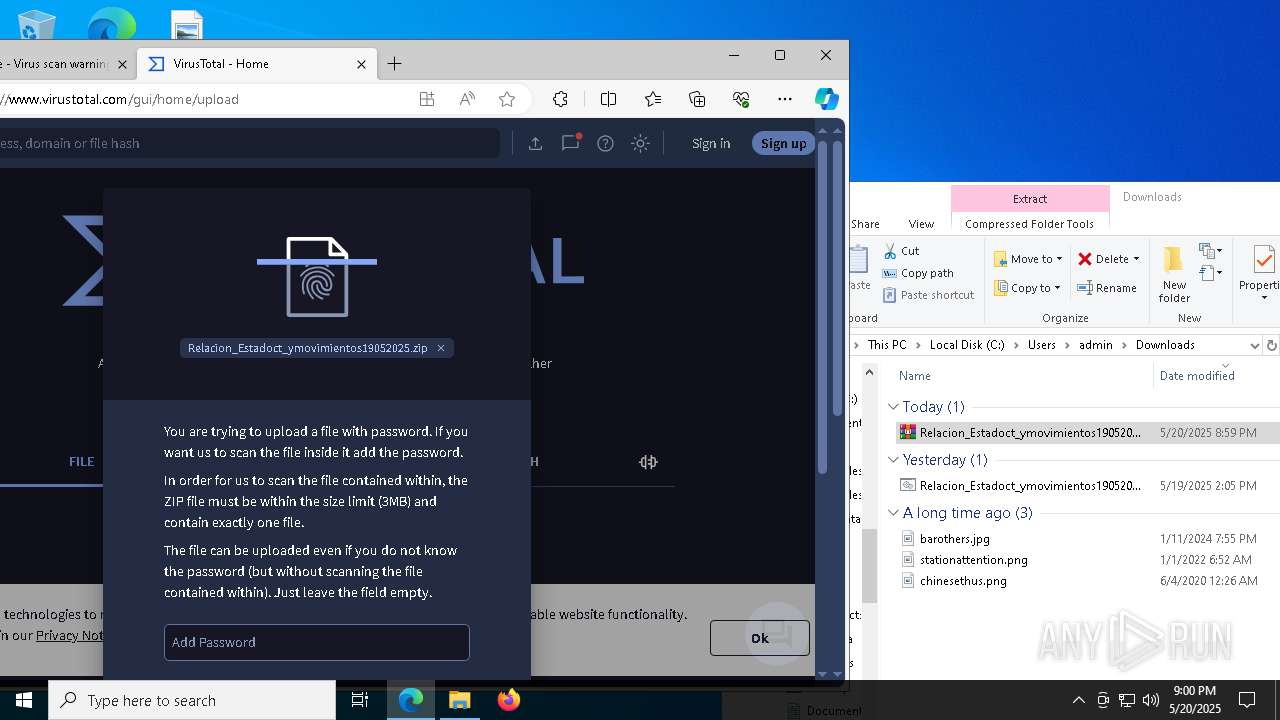
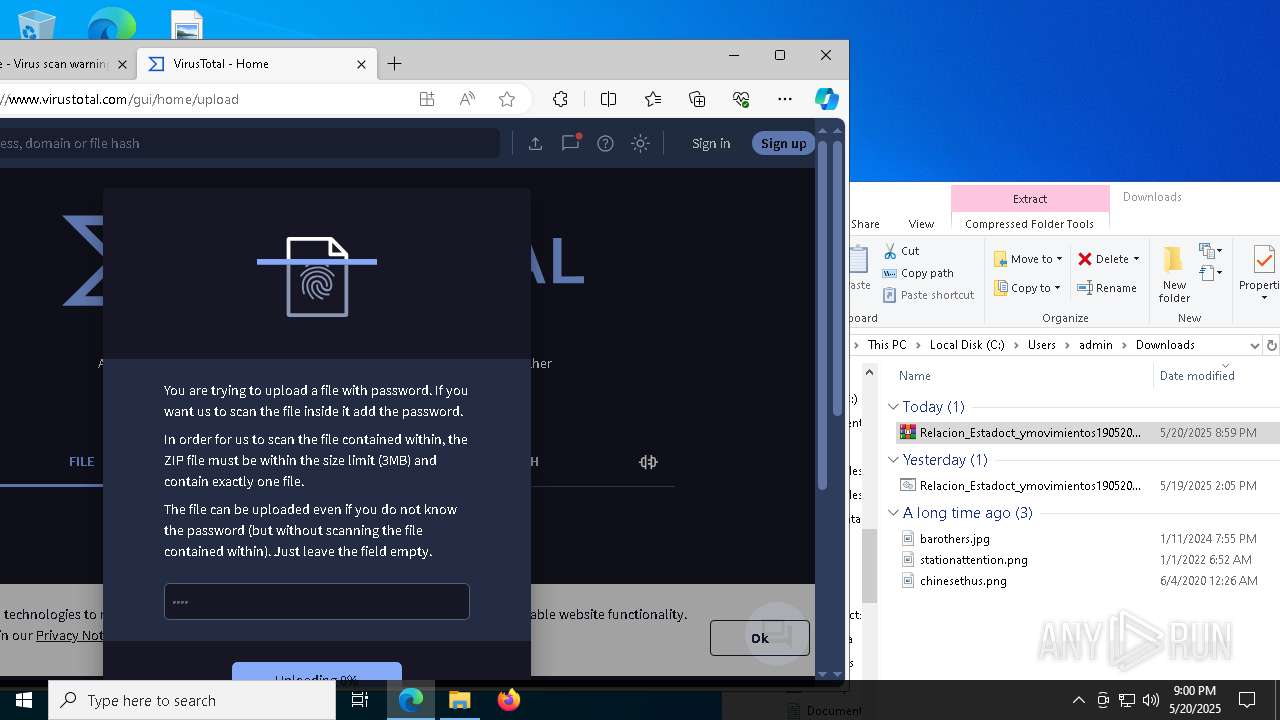
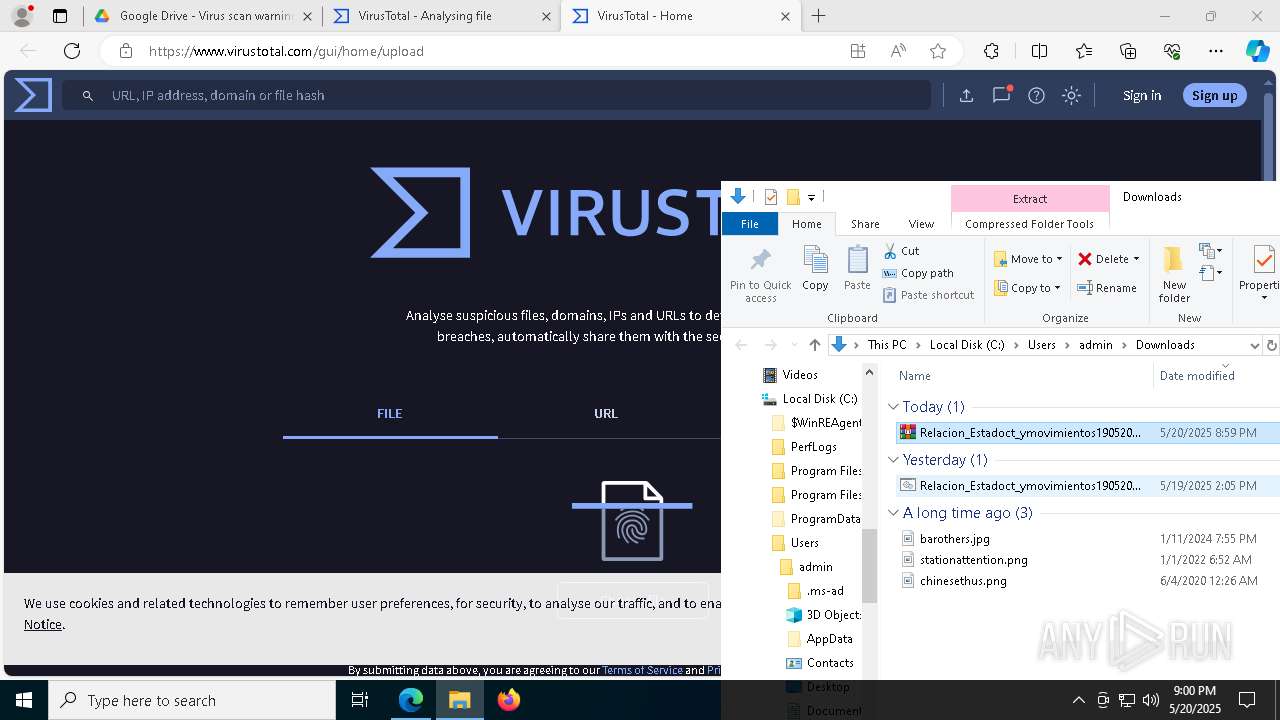
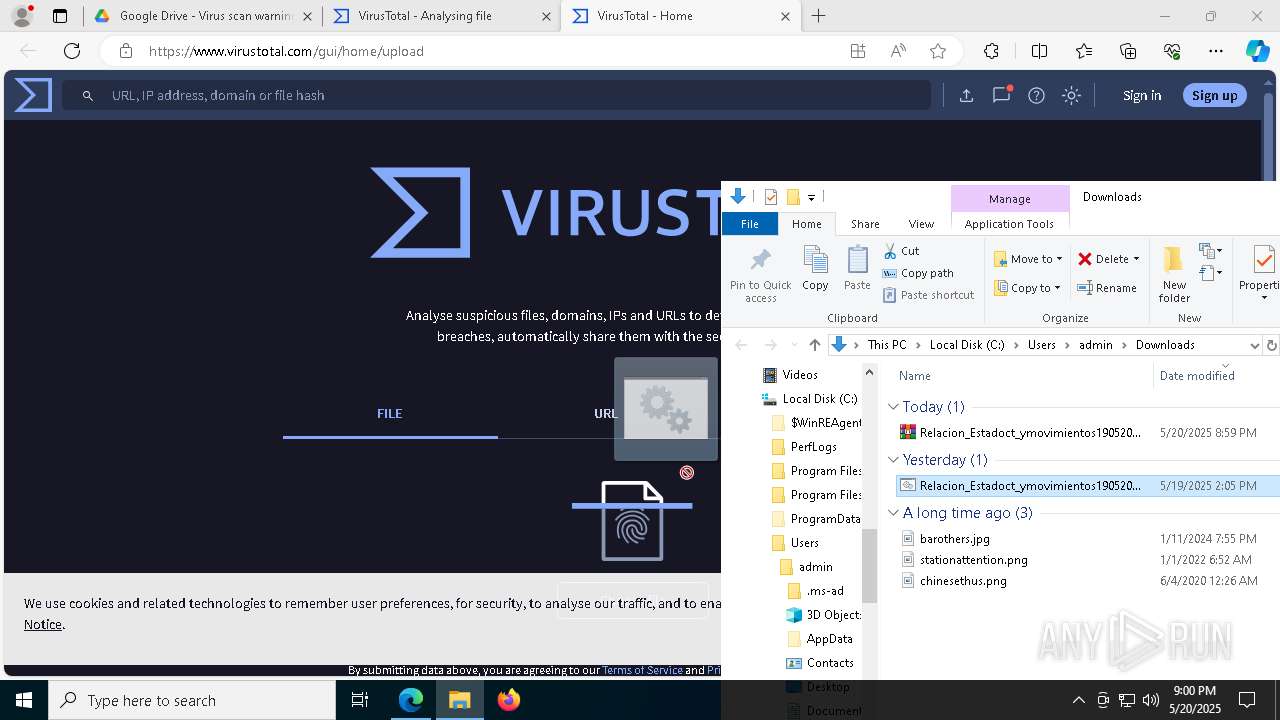
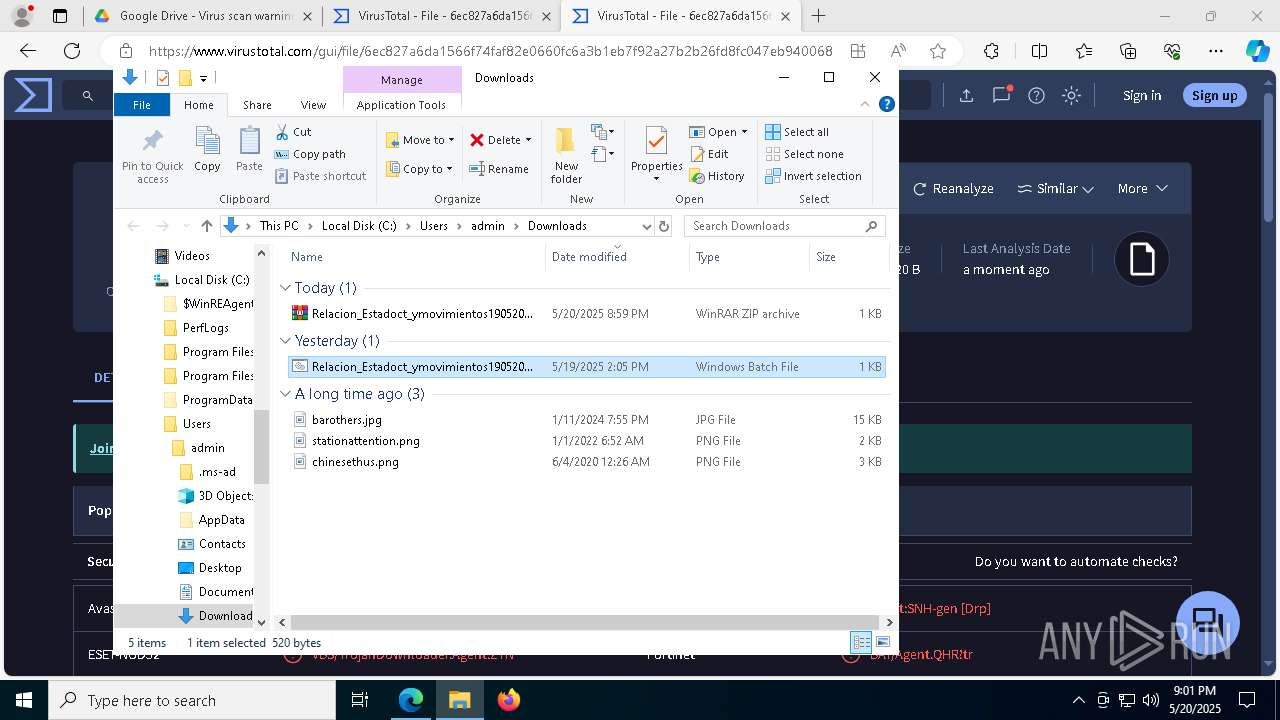
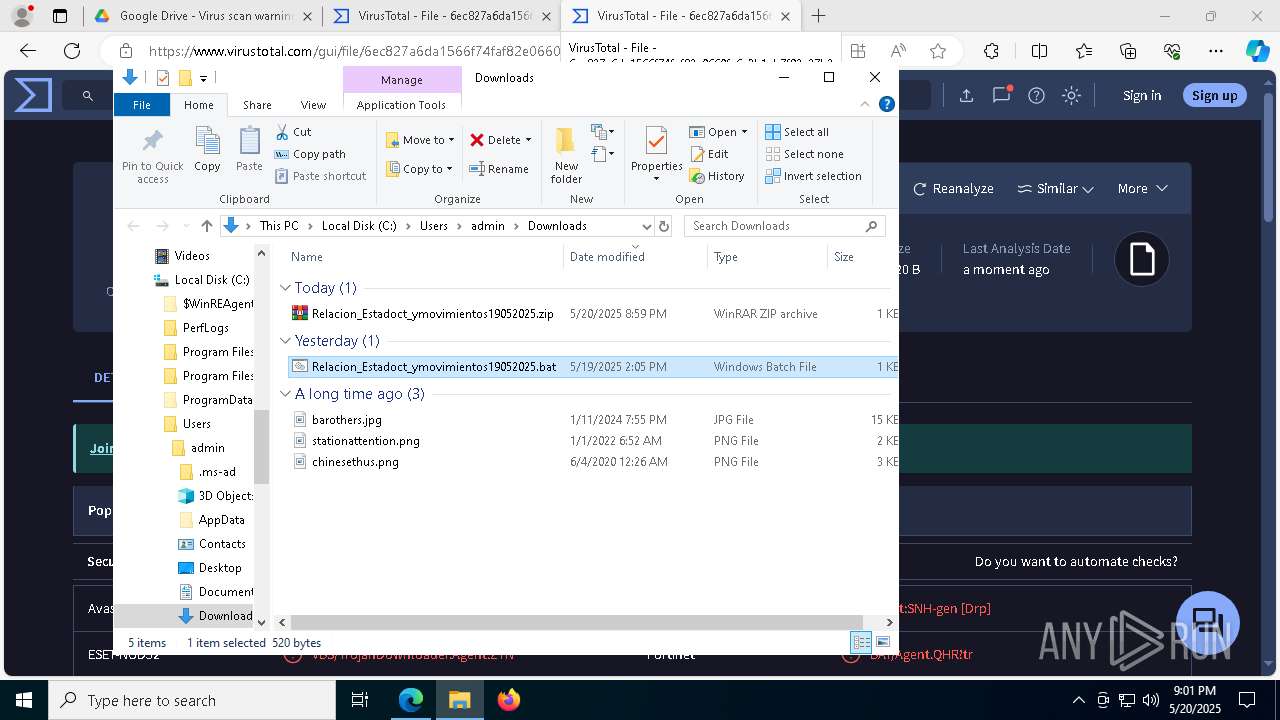
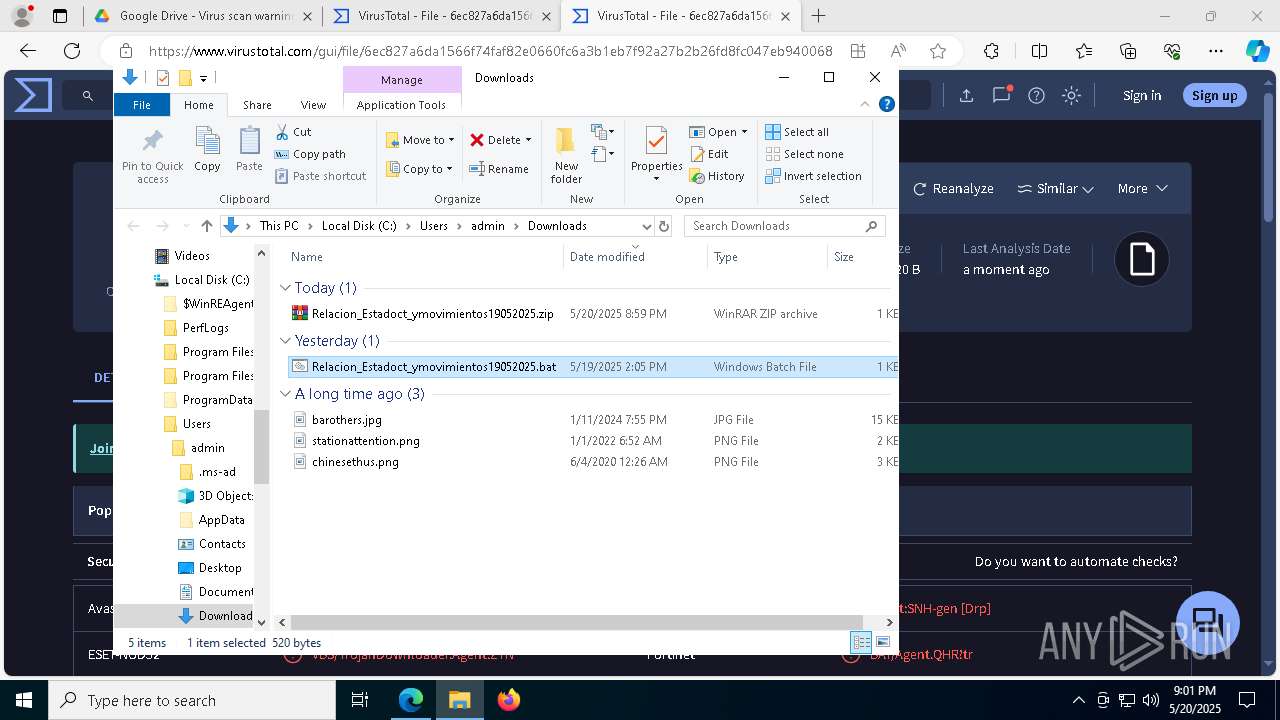
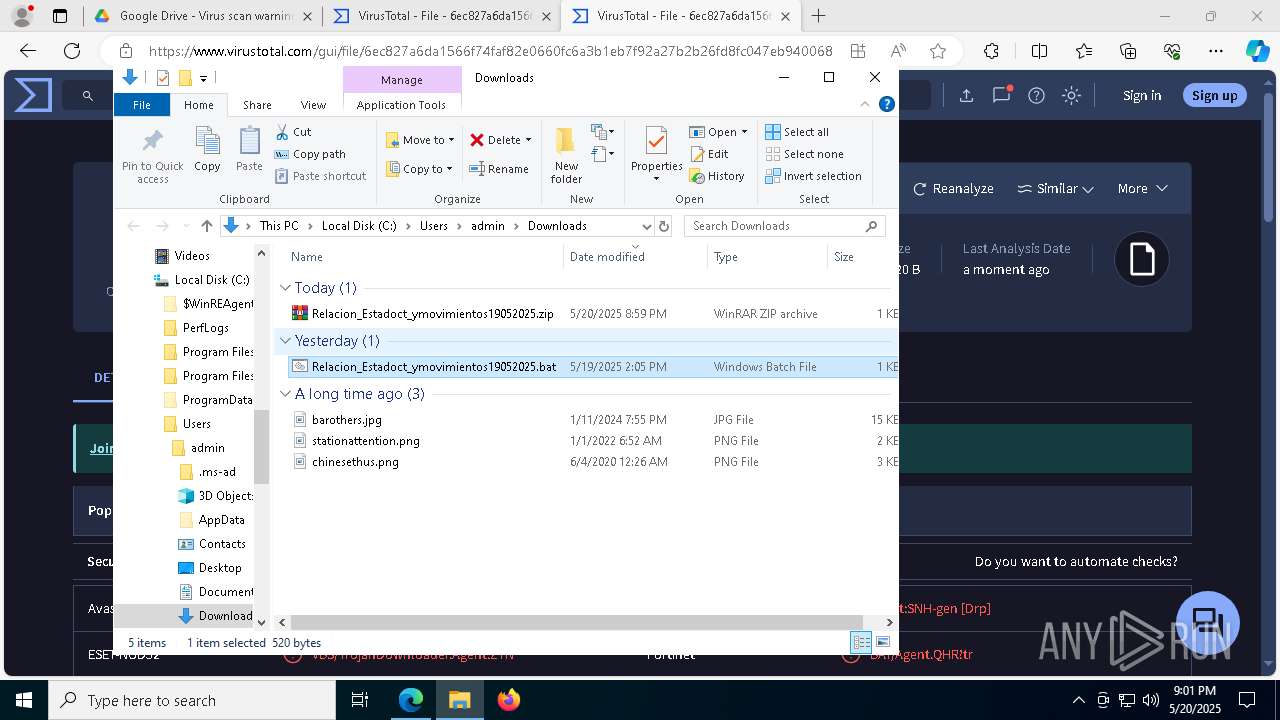
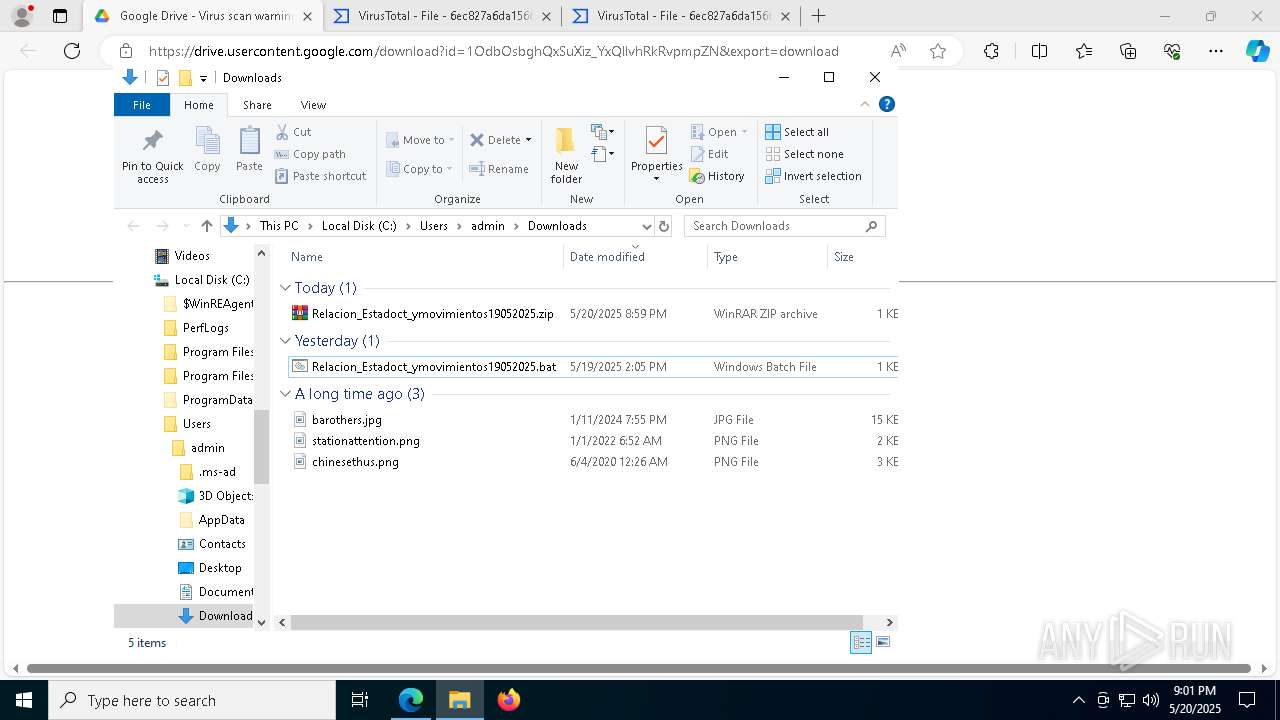
- WinRAR.exe (PID: 780)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6264)
Checks proxy server information
- wscript.exe (PID: 5376)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 6592)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 6592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
205
Monitored processes
69
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1316 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
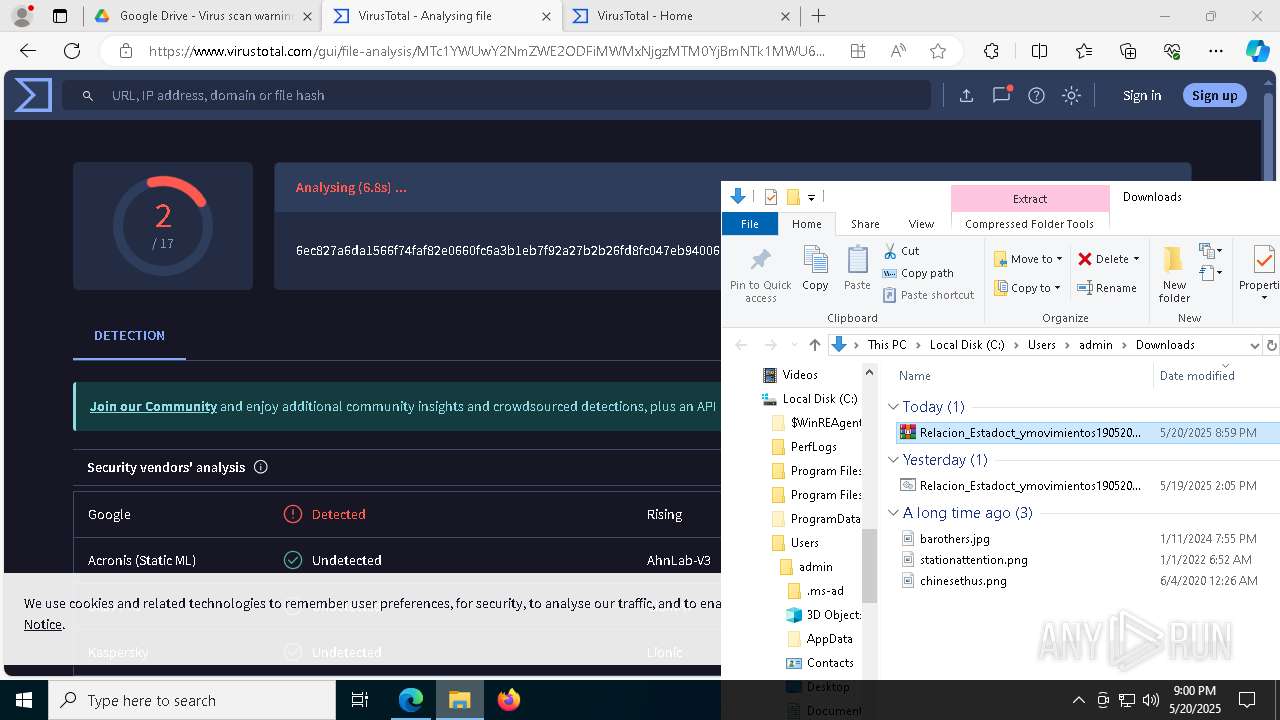
| 780 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Relacion_Estadoct_ymovimientos19052025.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8320 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6200 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=6964 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6496 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5732 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=6804 --field-trial-handle=2408,i,13314720061180682240,12978448501268608740,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
23 520
Read events
23 468
Write events
52
Delete events
0
Modification events
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DD179ECD2D942F00 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2B00AECD2D942F00 | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6D6A7362-E4A9-4671-B3F7-CE2711710E5F} | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {30F98225-0E61-476D-88E1-A86D05BDEB3B} | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EF859F5C-FE05-47E4-82A7-C04E959E3613} | |||
| (PID) Process: | (6344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6F52F0CD2D942F00 | |||
Executable files
32
Suspicious files
639
Text files
77
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bd95.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bd95.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bdb4.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bdc4.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 6344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
138
DNS requests
136
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
872 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1748298393&P2=404&P3=2&P4=maxtnHagSAyU0k34x8K4enN0SkNgwcjaArvF%2fJnx2cGPro4paYaJDbmhDllcbVAzRJduE62nQ%2f5x49e993joYQ%3d%3d | unknown | — | — | whitelisted |
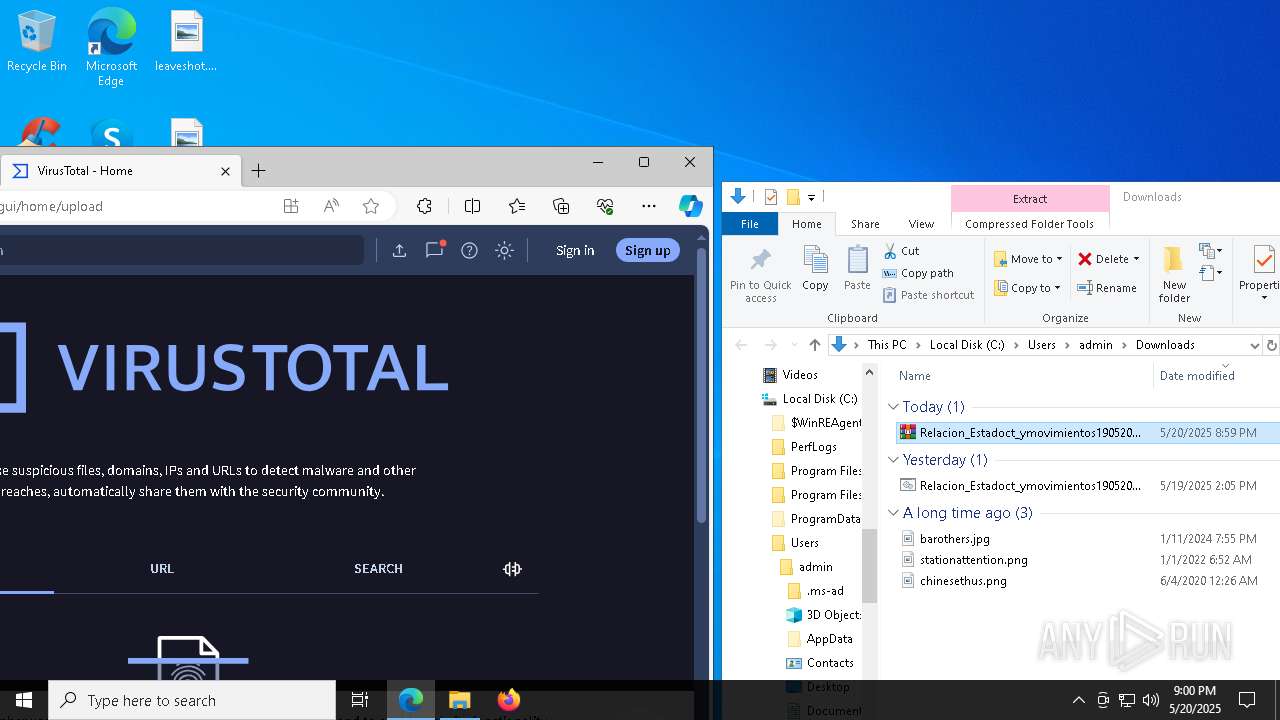
5376 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/58vg91No/0 | unknown | — | — | shared |
872 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1748298393&P2=404&P3=2&P4=maxtnHagSAyU0k34x8K4enN0SkNgwcjaArvF%2fJnx2cGPro4paYaJDbmhDllcbVAzRJduE62nQ%2f5x49e993joYQ%3d%3d | unknown | — | — | whitelisted |
872 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1748298393&P2=404&P3=2&P4=maxtnHagSAyU0k34x8K4enN0SkNgwcjaArvF%2fJnx2cGPro4paYaJDbmhDllcbVAzRJduE62nQ%2f5x49e993joYQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7412 | msedge.exe | 142.250.185.174:443 | docs.google.com | GOOGLE | US | whitelisted |
6344 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7412 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7412 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
docs.google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
5376 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5680 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
6592 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5740 | InstallUtil.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
5740 | InstallUtil.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |