| File name: | calc.exe |
| Full analysis: | https://app.any.run/tasks/6096c570-56a1-46a4-874c-509b669ea537 |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | March 20, 2020, 18:31:00 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F6F130BACB418E4C30414EC838A688AD |
| SHA1: | 7CA53DAC2D3BBAAF716D2F635FDE8A1AF678E9C3 |
| SHA256: | 7CFA85E9C1BED641E7377F9D9730869A232979754F06667A365F50644B83035B |
| SSDEEP: | 12288:8rfrCCL3rPv3Jzxln3s5u9wKn8XfQzSYmqHv4SfTZ7bAqW:gv3rPfJzxlc5u9h8vQzNmqhLZvAqW |
MALICIOUS
Application was injected by another process
- reg.exe (PID: 5376)
- reg.exe (PID: 4344)
Runs injected code in another process
- βιβλίαପୁସ୍ତକΔεपुस्.exe (PID: 3828)
Uses SVCHOST.EXE for hidden code execution
- βιβλίαପୁସ୍ତକΔεपुस्.exe (PID: 3828)
Loads the Task Scheduler COM API
- svchost.exe (PID: 4352)
Loads the Task Scheduler DLL interface
- svchost.exe (PID: 4352)
TRICKBOT was detected
- svchost.exe (PID: 4352)
Connects to CnC server
- svchost.exe (PID: 4352)
SUSPICIOUS
Creates files in the program directory
- calc.exe (PID: 5540)
Starts itself from another location
- calc.exe (PID: 5540)
Executable content was dropped or overwritten
- calc.exe (PID: 5540)
- svchost.exe (PID: 4352)
Modifies the open verb of a shell class
- reg.exe (PID: 5376)
- reg.exe (PID: 4344)
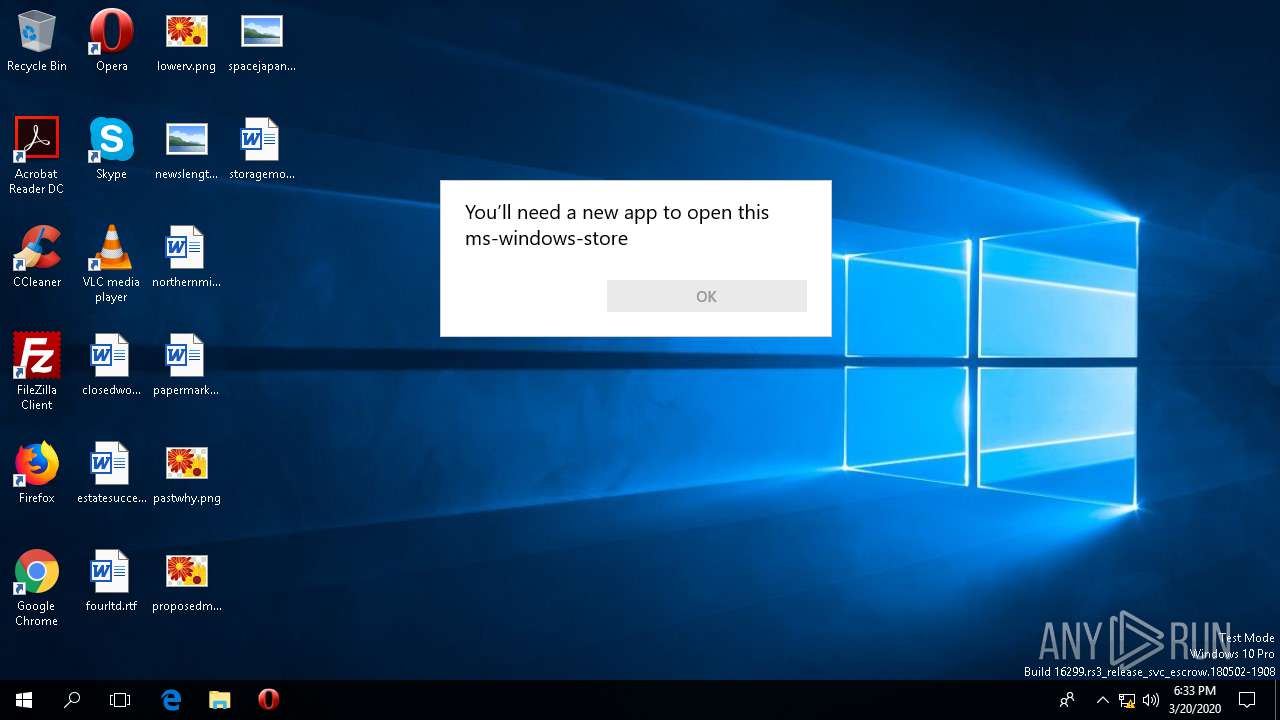
Executed via COM
- OpenWith.exe (PID: 1656)
Creates files in the user directory
- svchost.exe (PID: 4352)
Checks for external IP
- svchost.exe (PID: 4352)
Reads the machine GUID from the registry
- svchost.exe (PID: 4352)
INFO
Reads the software policy settings
- svchost.exe (PID: 4352)
Reads settings of System Certificates
- svchost.exe (PID: 4352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (35.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (27) |
| .exe | | | Win64 Executable (generic) (23.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:02 11:48:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 282624 |
| InitializedDataSize: | 487424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2bf14 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Feb-2020 10:48:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Feb-2020 10:48:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004444A | 0x00045000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5691 |
.rdata | 0x00046000 | 0x00051204 | 0x00052000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.21366 |
.data | 0x00098000 | 0x000069F4 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.22684 |
.rsrc | 0x0009F000 | 0x0001DA16 | 0x0001E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.98944 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94917 | 146 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.86316 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.80851 | 488 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.43174 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.37006 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.77209 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 1.88026 | 66 | UNKNOWN | English - United States | RT_STRING |
8 | 4.68884 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 7.88543 | 75214 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.2695 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
Total processes
95
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | WSReset.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\WINDOWS\system32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2412 | "C:\WINDOWS\system32\WSReset.exe" | C:\WINDOWS\system32\WSReset.exe | — | βιβλίαପୁସ୍ତକΔεपुस्.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: This tool resets the Windows Store without changing account settings or deleting installed apps Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3828 | "C:\ProgramData\βιβλίαପୁସ୍ତକΔεपुस्.exe" | C:\ProgramData\βιβλίαପୁସ୍ତକΔεपुस्.exe | — | calc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4344 | C:\WINDOWS\system32\reg add HKEY_CURRENT_USER\Software\Classes\AppX82a6gwre4fdg3bt635tn5ctqjf8msdd2\shell\open\command /t REG_SZ /d "C:\WINDOWS\system32\cmd.exe /c start C:\ProgramData\βιβλίαପୁସ୍ତକΔεपुस्.exe" /f | C:\WINDOWS\system32\reg.exe | sihost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4352 | C:\WINDOWS\system32\svchost.exe | C:\WINDOWS\system32\svchost.exe | βιβλίαପୁସ୍ତକΔεपुस्.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | C:\WINDOWS\system32\reg add HKEY_CURRENT_USER\Software\Classes\AppX82a6gwre4fdg3bt635tn5ctqjf8msdd2\shell\open\command /v "DelegateExecute" /t REG_SZ /d "" /f | C:\WINDOWS\system32\reg.exe | sihost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5540 | "C:\Users\admin\AppData\Local\Temp\calc.exe" | C:\Users\admin\AppData\Local\Temp\calc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 602
Read events
5 553
Write events
41
Delete events
8
Modification events
| (PID) Process: | (5540) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5540) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5540) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5540) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4344) reg.exe | Key: | HKEY_CLASSES_ROOT\AppX82a6gwre4fdg3bt635tn5ctqjf8msdd2\shell\open\command |
| Operation: | write | Name: | |
Value: C:\WINDOWS\system32\cmd.exe /c start C:\ProgramData\βιβλίαପୁସ୍ତକΔεपुस्.exe | |||
| (PID) Process: | (5376) reg.exe | Key: | HKEY_CLASSES_ROOT\AppX82a6gwre4fdg3bt635tn5ctqjf8msdd2\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (3828) βιβλίαପୁସ୍ତକΔεपुस्.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3828) βιβλίαପୁସ୍ତକΔεपुस्.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3828) βιβλίαପୁସ୍ତକΔεपुस्.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3828) βιβλίαପୁସ୍ତକΔεपुस्.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5540 | calc.exe | C:\ProgramData\βιβλίαପୁସ୍ତକΔεपुस्.exe | executable | |
MD5:— | SHA256:— | |||
| 4352 | svchost.exe | C:\Users\admin\AppData\Roaming\elementFit\profiles.ini | text | |
MD5:— | SHA256:— | |||
| 3828 | βιβλίαପୁସ୍ତକΔεपुस्.exe | C:\Users\admin\AppData\Local\Temp\log5CC8.tmp | text | |
MD5:— | SHA256:— | |||
| 4352 | svchost.exe | C:\Users\admin\AppData\Roaming\elementFit\βιβλίαପୁସ୍ତକΔεपुस्.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
3
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4352 | svchost.exe | GET | 200 | 216.239.32.21:80 | http://myexternalip.com/raw | US | text | 14 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4352 | svchost.exe | 51.254.164.245:443 | — | OVH SAS | FR | malicious |
4352 | svchost.exe | 216.239.32.21:80 | myexternalip.com | Google Inc. | US | whitelisted |
4352 | svchost.exe | 185.14.31.252:443 | — | ITL Company | NL | unknown |
3700 | svchost.exe | 52.158.29.237:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win-ppe.data.microsoft.com |
| whitelisted |
myexternalip.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4352 | svchost.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 19 |
4352 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
4352 | svchost.exe | A Network Trojan was detected | ET TROJAN ABUSE.CH SSL Blacklist Malicious SSL certificate detected (Dridex/Trickbot CnC) |
4352 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist SSL certificate detected (Trickbot) |
4352 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Check myexternalip.com |
4352 | svchost.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |