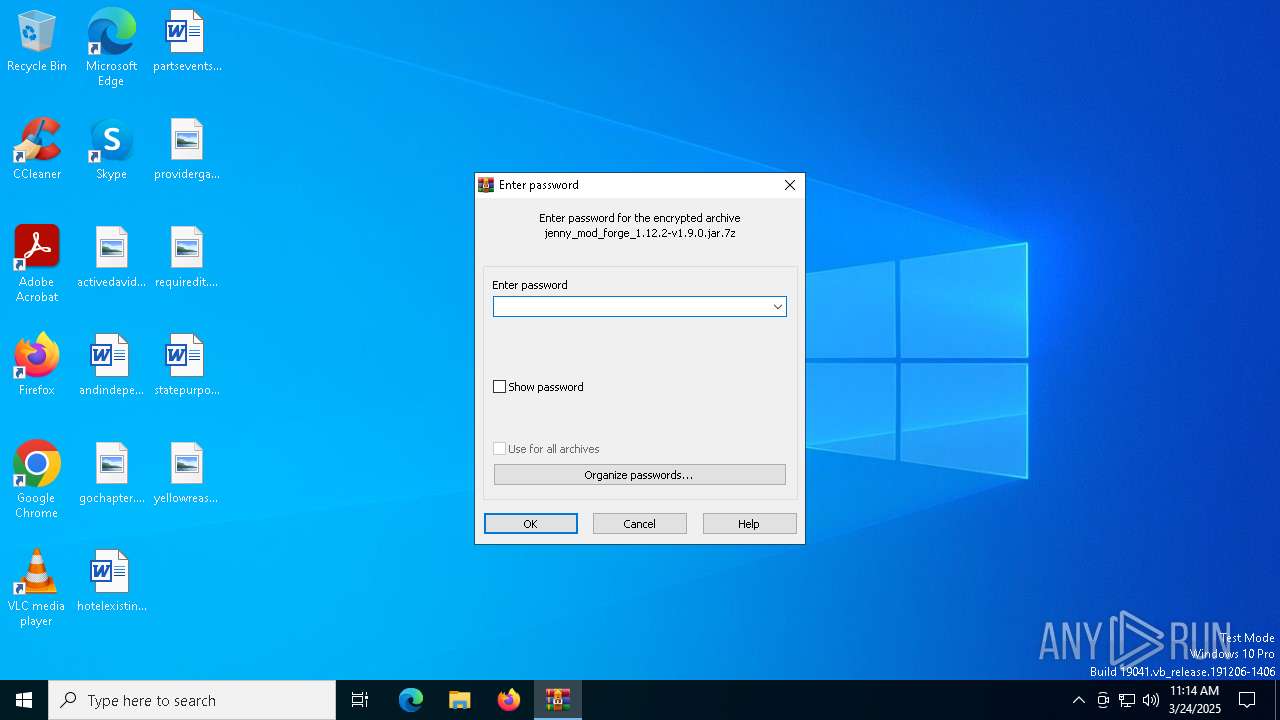
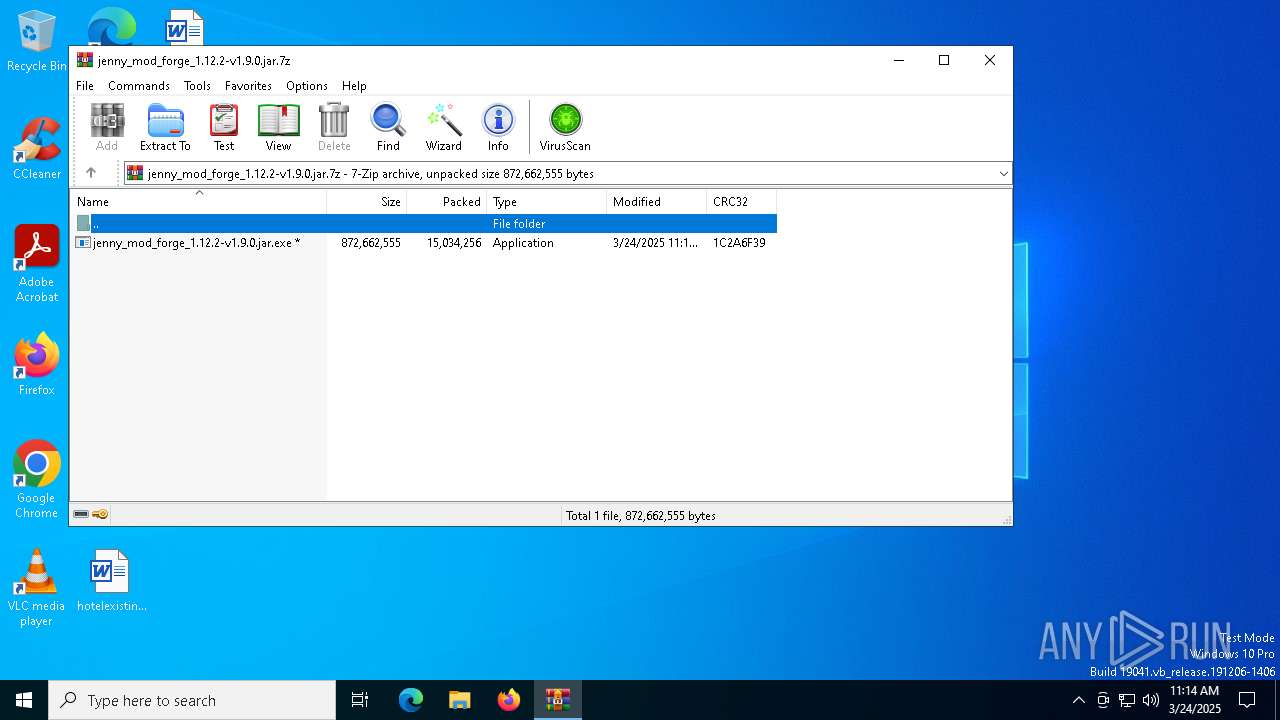
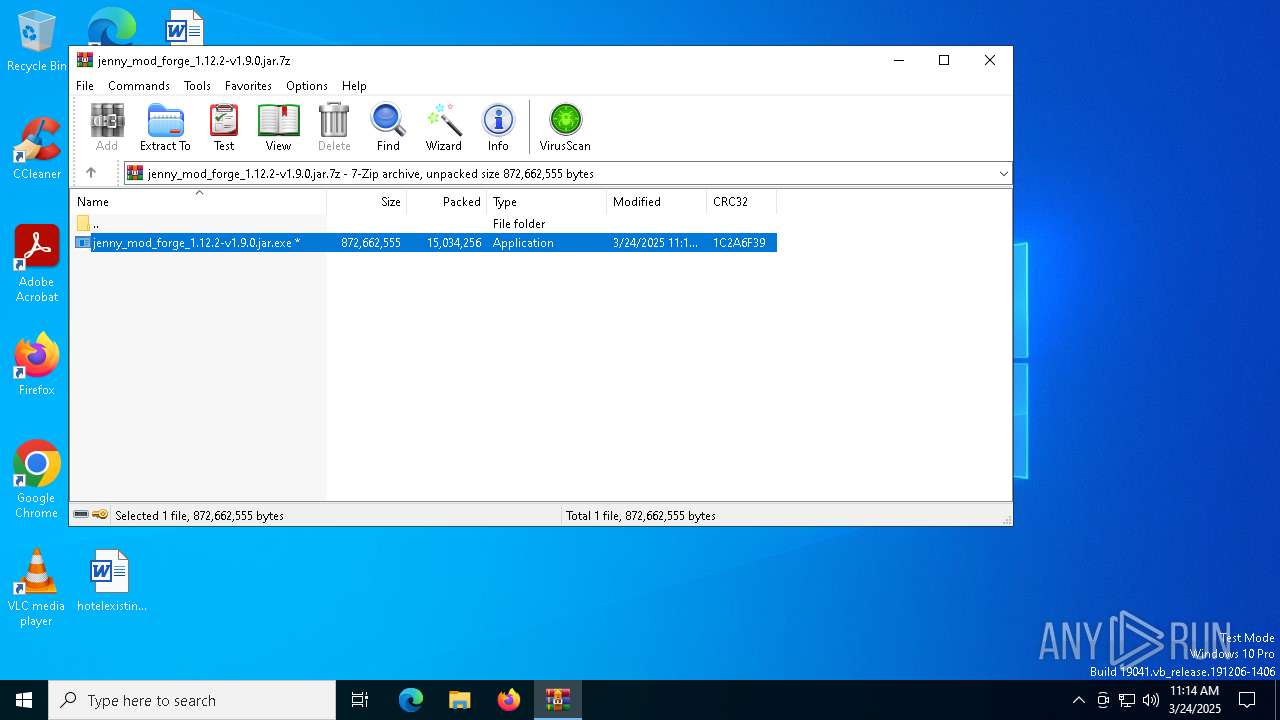
| File name: | jenny_mod_forge_1.12.2-v1.9.0.jar.7z |
| Full analysis: | https://app.any.run/tasks/943cd5ff-4ff6-458a-b6f0-ec83bd130cfc |
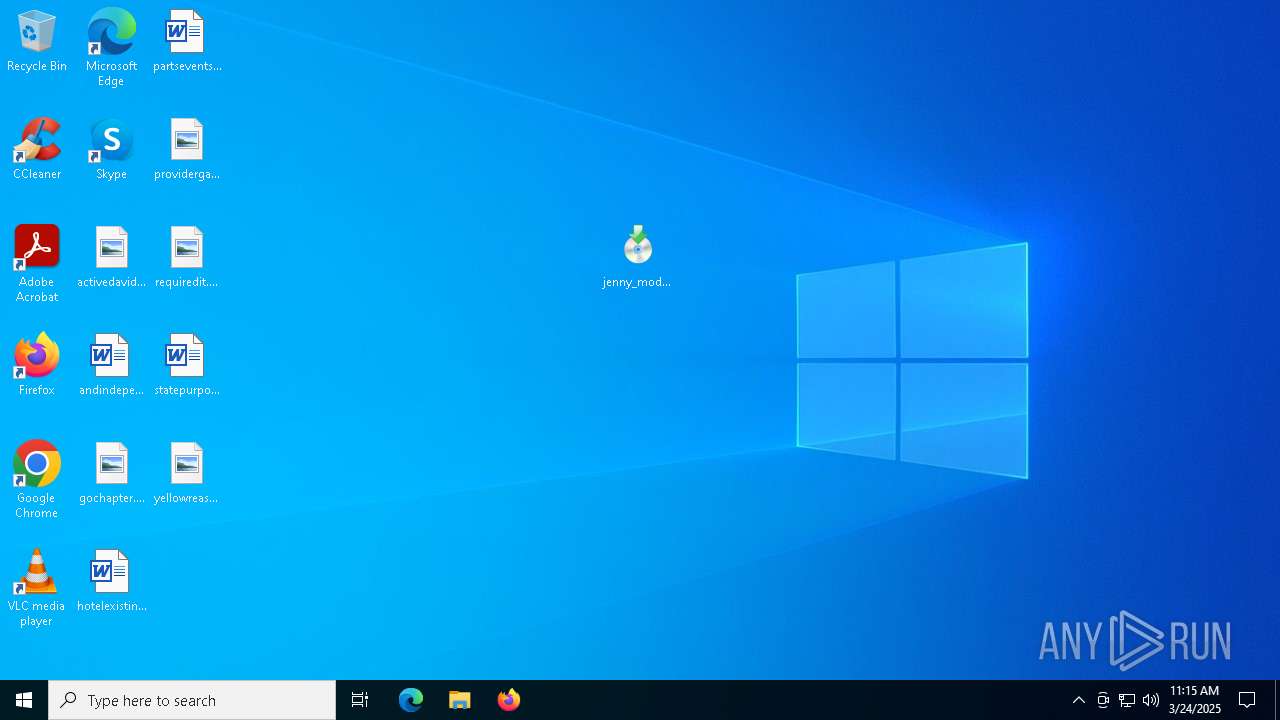
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 24, 2025, 11:13:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 90A9FF279CB5113608426C6715363031 |
| SHA1: | 785BEC8A9D06AFF93BFD96A11C570688A0BD4C55 |
| SHA256: | 7CB504B8C926EBA6EE8B9273826A4F9AED871880141AAB7FB51D9BD9E65147F8 |
| SSDEEP: | 98304:NkdFQGUAkE4Yf/YhrKdIl444lQs5VOVpFAWaEdvPHZXfXB2op4NXZTbTfbVCkBVK:Ehzy+m77hvphJYRQIsIb44rHS |
MALICIOUS
AutoIt loader has been detected (YARA)
- Deployment.com (PID: 536)
LUMMA mutex has been found
- Deployment.com (PID: 536)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- Deployment.com (PID: 536)
Connects to the CnC server
- svchost.exe (PID: 2196)
SUSPICIOUS
Starts CMD.EXE for commands execution
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- cmd.exe (PID: 2108)
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 3268)
- cmd.exe (PID: 6424)
Executing commands from a ".bat" file
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 3268)
Get information on the list of running processes
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6424)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6424)
Application launched itself
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6424)
Starts application with an unusual extension
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6424)
The executable file from the user directory is run by the CMD process
- Deployment.com (PID: 536)
- Deployment.com (PID: 5988)
Starts the AutoIt3 executable file
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6424)
There is functionality for taking screenshot (YARA)
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- Deployment.com (PID: 536)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- Deployment.com (PID: 536)
INFO
Create files in a temporary directory
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- extrac32.exe (PID: 4244)
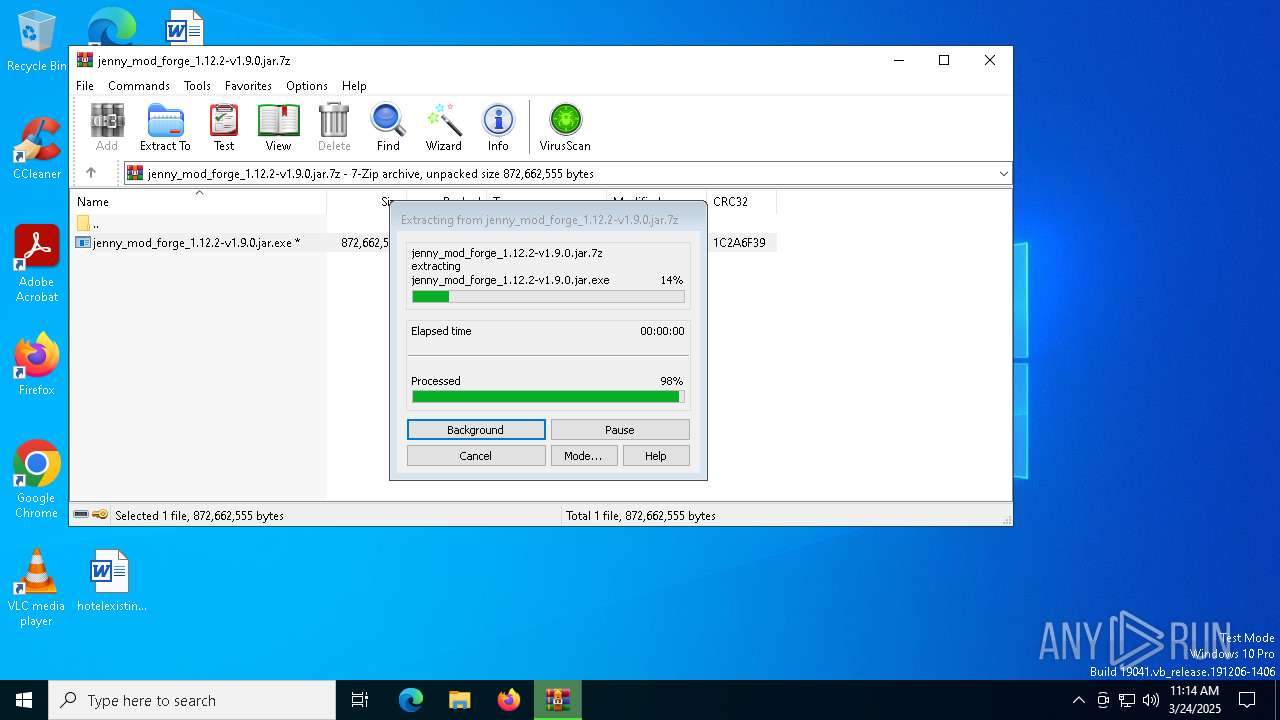
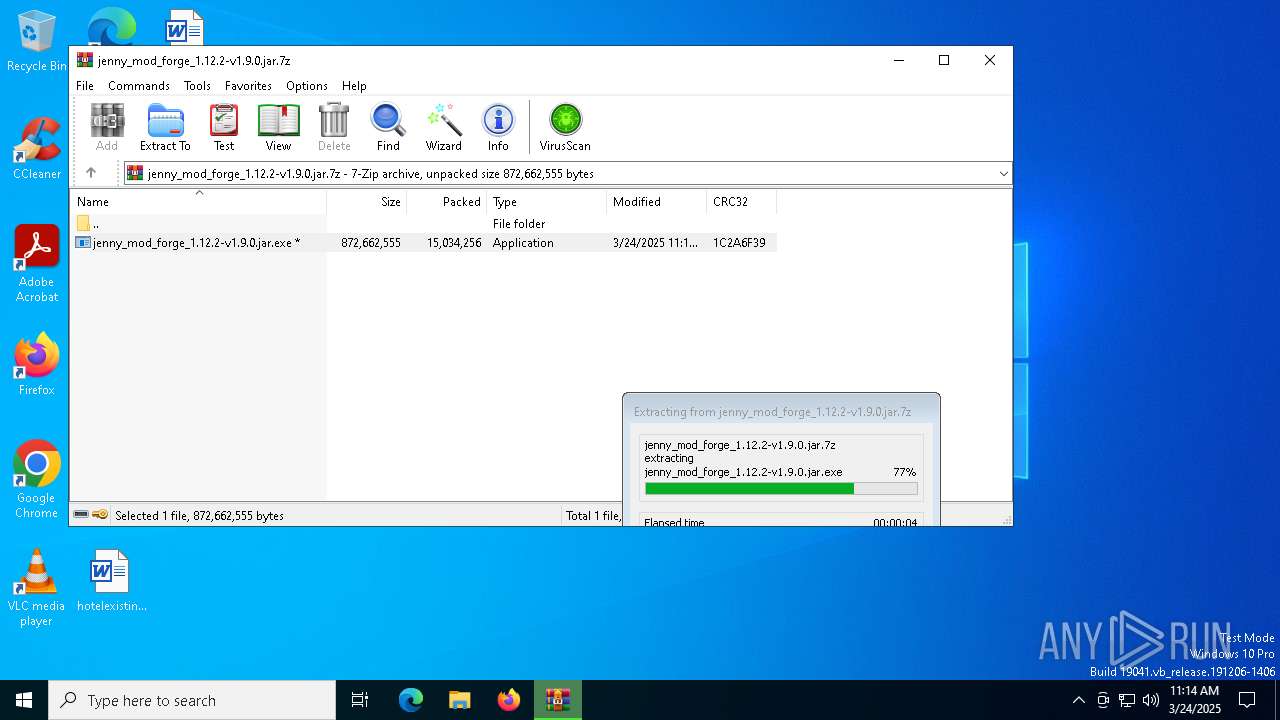
Manual execution by a user
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 3268)
Reads the computer name
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- extrac32.exe (PID: 6824)
- Deployment.com (PID: 5988)
Checks supported languages
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 4756)
- Deployment.com (PID: 536)
- jenny_mod_forge_1.12.2-v1.9.0.jar.exe (PID: 3268)
Creates a new folder
- cmd.exe (PID: 3888)
- cmd.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
160
Monitored processes
31
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | cmd /c copy /b 303996\Deployment.com + Increasing + Accepted + Poultry + Approximate + Eu + Internal + Proceed + Respond + Sg + Lime 303996\Deployment.com | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | Deployment.com p | C:\Users\admin\AppData\Local\Temp\303996\Deployment.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 632 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | cmd /c copy /b 303996\Deployment.com + Increasing + Accepted + Poultry + Approximate + Eu + Internal + Proceed + Respond + Sg + Lime 303996\Deployment.com | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\jenny_mod_forge_1.12.2-v1.9.0.jar.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1532 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\WINDOWS\system32\CMD.exe" /c copy Ancient.vssm Ancient.vssm.bat & Ancient.vssm.bat | C:\Windows\SysWOW64\cmd.exe | — | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 553
Read events
3 534
Write events
19
Delete events
0
Modification events
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\jenny_mod_forge_1.12.2-v1.9.0.jar.7z | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
0
Suspicious files
21
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1272 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1272.16021\jenny_mod_forge_1.12.2-v1.9.0.jar.exe | — | |
MD5:— | SHA256:— | |||
| 4756 | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | C:\Users\admin\AppData\Local\Temp\Ancient.vssm | text | |
MD5:1525F5A30D0A5223DE9A96701CBC820C | SHA256:40DFC0457F6927173CF3B3F2AD6C272E0E8DED1F52BF8822F1BA937F4699C138 | |||
| 4756 | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | C:\Users\admin\AppData\Local\Temp\Urls.vssm | compressed | |
MD5:746FDC941A4CC28DDEB09E6D6CA3B967 | SHA256:52A69082E64FF709BA6E9BA4450B31E624BD180EC2B8D3731416F9B591D7BE8B | |||
| 4756 | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | C:\Users\admin\AppData\Local\Temp\Wma.vssm | binary | |
MD5:B3B14CBEB12D2FB8E63893C83BA0B366 | SHA256:6948DC453B5CFF1AC31042AA0C01CD797C49051FEAE8DA3D89D51B6933A30B2B | |||
| 4756 | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | C:\Users\admin\AppData\Local\Temp\Lawsuit.vssm | binary | |
MD5:FAD5BA5A90EACEFD1E9E41825E53A2CE | SHA256:E37AF8BFFD4B76E2543F1A4E2808EB5D9FBECBC40D615348D1397B5C52DE1505 | |||
| 4756 | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | C:\Users\admin\AppData\Local\Temp\Contracting.vssm | binary | |
MD5:13968FF70669776D1BBA8C82FD287C24 | SHA256:17075FBBC49DAA3B44A6C0B9D99988547FE4E33B9C36DBB014EC3FD72AD33A6E | |||
| 4756 | jenny_mod_forge_1.12.2-v1.9.0.jar.exe | C:\Users\admin\AppData\Local\Temp\Commands.vssm | binary | |
MD5:0541AE05DCBEA06AC2FA8FED504B2293 | SHA256:C129AF7E0DE81AAC2586BC32585D4E04C5AB045B8D43EFF82DBA176DC6A0ACE6 | |||
| 4244 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Sg | binary | |
MD5:8443ADBD90E41B7EF2A6B5C4533D4695 | SHA256:7EC3360CAF11864059438A3D66436FA852EF8DC91E9E0D8BBFCFA82C9546D261 | |||
| 4244 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Poultry | binary | |
MD5:9FEA4B6CDC7FF84A1B34AC96D7306FFE | SHA256:CB3D77F4F09F946E53F63C987E5C8AA29CF46BC5D41E9DEDD19E0C59A0047DE4 | |||
| 4244 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Proceed | binary | |
MD5:48749BFD279EEE64ABCD83FF0BC1AF8C | SHA256:7D528776CC7A9D75FF6E012D6E25C8A879BC3152120D810AC633A194515701D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
26
DNS requests
19
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2392 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2392 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6988 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6988 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6988 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
mMmjKMiIHEaaClnynaAFUsK.mMmjKMiIHEaaClnynaAFUsK |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (sighbtseeing .shop) |
536 | Deployment.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (esccapewz .run in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (esccapewz .run) |
536 | Deployment.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (esccapewz .run in TLS SNI) |
536 | Deployment.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (esccapewz .run in TLS SNI) |