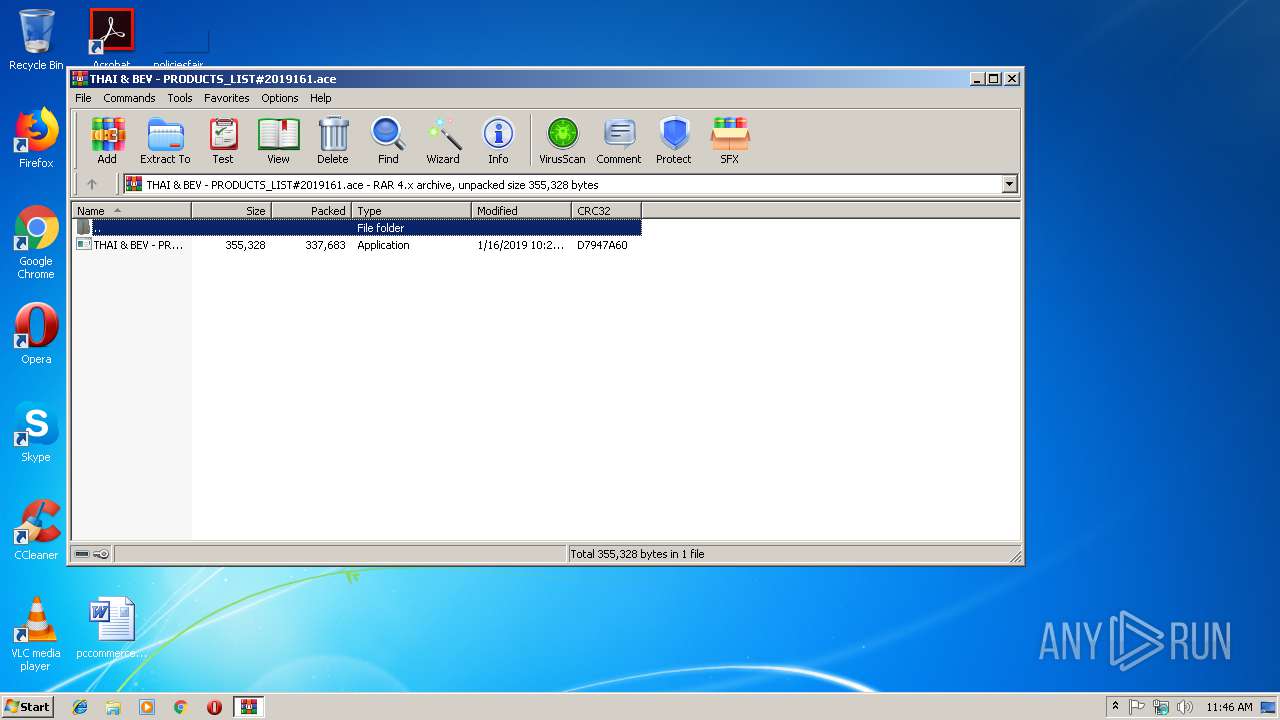
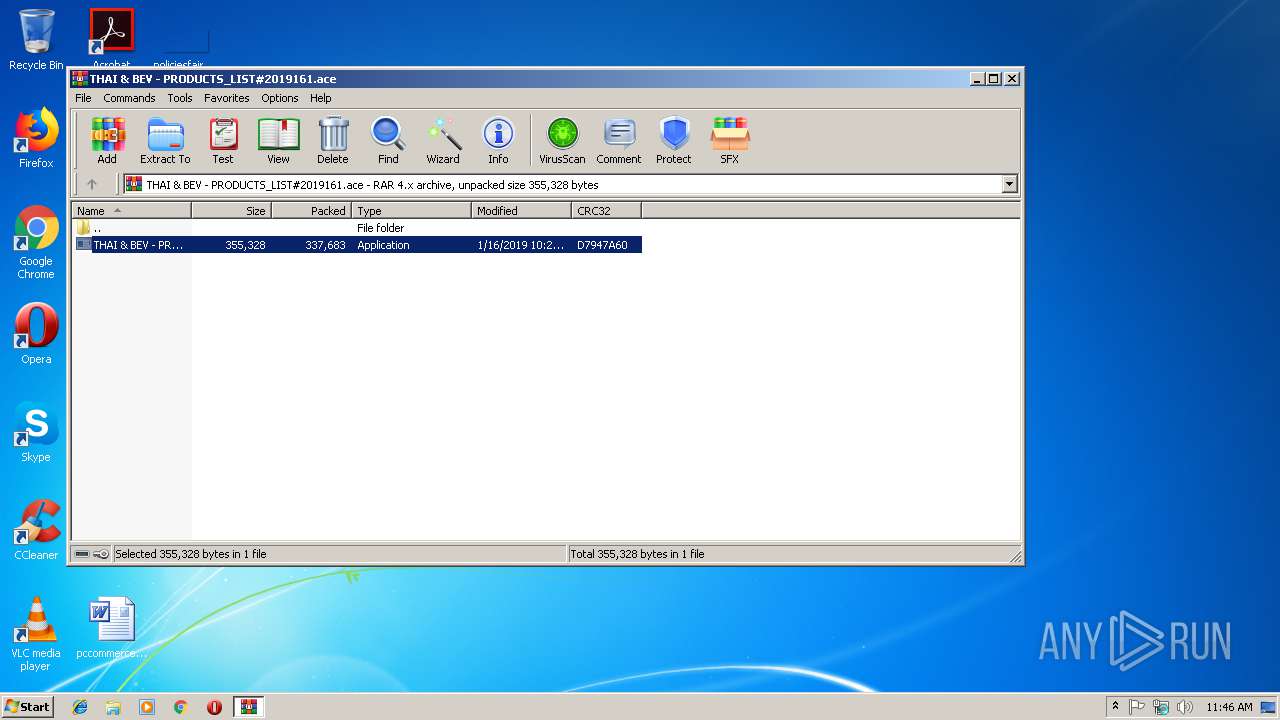
| File name: | THAI & BEV - PRODUCTS_LIST#2019161.ace |
| Full analysis: | https://app.any.run/tasks/cd01c882-5e97-40b6-aeb4-4eb05366a8ff |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 18, 2019, 11:46:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 5C2AD061043178BA0139735BC29E8B4C |
| SHA1: | 54353D7CB0739491892C7CA0EC718EF7D301BF5E |
| SHA256: | 7CB31EA6EC5A36588AD224BF8E2570BB0C016E0FE2C51A0883399959BAEF4CAE |
| SSDEEP: | 6144:v0j7SOy/dz5y0vTiRqqCv1LxMylql+ql/cz+d9KAARi2gNTEdF6blPY:v0/St5yiH5wylY/cSd0Zs2gNToF8S |
MALICIOUS
Application was dropped or rewritten from another process
- THAI & BEV - PRODUCTS_LIST#2019161.exe (PID: 2704)
- roam.exe (PID: 2788)
- roam.exe (PID: 2360)
Changes the autorun value in the registry
- roam.exe (PID: 2788)
- mstsc.exe (PID: 3048)
FORMBOOK was detected
- explorer.exe (PID: 284)
Formbook was detected
- mstsc.exe (PID: 3048)
- Firefox.exe (PID: 2556)
Actions looks like stealing of personal data
- mstsc.exe (PID: 3048)
Connects to CnC server
- explorer.exe (PID: 284)
Stealing of credential data
- mstsc.exe (PID: 3048)
SUSPICIOUS
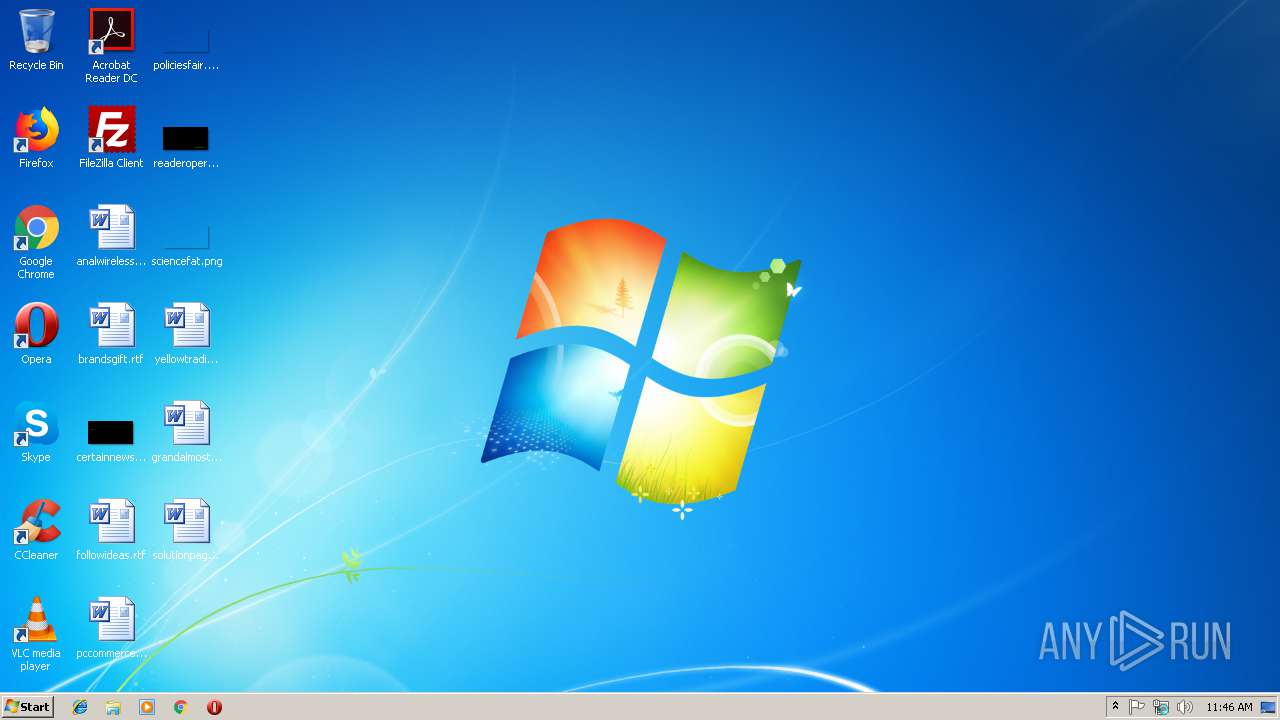
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2972)
- cmd.exe (PID: 2632)
Creates files in the user directory
- cmd.exe (PID: 2632)
- mstsc.exe (PID: 3048)
Application launched itself
- roam.exe (PID: 2788)
Starts CMD.EXE for commands execution
- THAI & BEV - PRODUCTS_LIST#2019161.exe (PID: 2704)
- mstsc.exe (PID: 3048)
Loads DLL from Mozilla Firefox
- mstsc.exe (PID: 3048)
INFO
Creates files in the user directory
- Firefox.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 337747 |
|---|---|
| UncompressedSize: | 355328 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:01:16 10:29:00 |
| PackingMethod: | Normal |
| ArchivedFileName: | THAI & BEV - PRODUCTS_LIST#2019161.exe |
Total processes
41
Monitored processes
10
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe | — | roam.exe | |||||||||||
User: admin Company: Energy East Corporation Integrity Level: MEDIUM Description: Complete capacity lifecycle management for your virtual infrastructure Exit code: 0 Version: 11.6.17.1 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | mstsc.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2632 | "C:\Windows\System32\cmd.exe" /c copy "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.48497\THAI & BEV - PRODUCTS_LIST#2019161.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe" | C:\Windows\System32\cmd.exe | THAI & BEV - PRODUCTS_LIST#2019161.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.48497\THAI & BEV - PRODUCTS_LIST#2019161.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.48497\THAI & BEV - PRODUCTS_LIST#2019161.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Energy East Corporation Integrity Level: MEDIUM Description: Complete capacity lifecycle management for your virtual infrastructure Exit code: 0 Version: 11.6.17.1 Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe | cmd.exe | ||||||||||||
User: admin Company: Energy East Corporation Integrity Level: MEDIUM Description: Complete capacity lifecycle management for your virtual infrastructure Exit code: 0 Version: 11.6.17.1 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\THAI & BEV - PRODUCTS_LIST#2019161.ace" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3048 | "C:\Windows\System32\mstsc.exe" | C:\Windows\System32\mstsc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3800 | /c del "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe" | C:\Windows\System32\cmd.exe | — | mstsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4088 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe" | C:\Windows\System32\cmd.exe | — | THAI & BEV - PRODUCTS_LIST#2019161.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 294
Read events
2 261
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\THAI & BEV - PRODUCTS_LIST#2019161.ace | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (284) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ace\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (284) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ace\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
2
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | mstsc.exe | C:\Users\admin\AppData\Roaming\-M479700\-M4logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2632 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\roam.exe | executable | |
MD5:— | SHA256:— | |||
| 2972 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.48497\THAI & BEV - PRODUCTS_LIST#2019161.exe | executable | |
MD5:— | SHA256:— | |||
| 3048 | mstsc.exe | C:\Users\admin\AppData\Roaming\-M479700\-M4logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 2556 | Firefox.exe | C:\Users\admin\AppData\Roaming\-M479700\-M4logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 3048 | mstsc.exe | C:\Users\admin\AppData\Roaming\-M479700\-M4logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 3048 | mstsc.exe | C:\Users\admin\AppData\Roaming\-M479700\-M4logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
21
DNS requests
13
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
284 | explorer.exe | GET | — | 107.148.41.15:80 | http://www.pw247.net/h339/?q6Q=qjiR0sPZCorML17B51jBdHZOtn+dqwmygNz+nQCpj2aUSQnHfG9vxFHAm00JJH76Tm70iw==&rVmd=LLrLh&sql=1 | US | — | — | malicious |
284 | explorer.exe | GET | — | 183.111.182.214:80 | http://www.woosinelec.com/h339/?q6Q=MdNA1nJUvQwYjfbsKBDovxHskF7aYblIglrW+NL1oexeonkUgIDp/G5ladNXhH4ESJnf+A==&rVmd=LLrLh&sql=1 | KR | — | — | malicious |
284 | explorer.exe | GET | — | 45.34.81.84:80 | http://www.leifengdige.com/h339/?q6Q=iOCafhqF6RLdE4CTzzjM5C35c0BE8aImnZ/ZH/DMEYdSWYc6qU3yeX6vsAA8C0kx1wzeeg==&rVmd=LLrLh&sql=1 | US | — | — | malicious |
284 | explorer.exe | GET | — | 39.109.17.118:80 | http://www.coolryuu.com/h339/?q6Q=AnknrfF9zqLVNPq+mhbx5cGEme2+yN2YFhJr/xJvEKfTimySDlkbcQdqGxDJbHL7rZ1QZA==&rVmd=LLrLh&sql=1 | HK | — | — | malicious |
284 | explorer.exe | POST | — | 107.148.41.15:80 | http://www.pw247.net/h339/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 107.148.41.15:80 | http://www.pw247.net/h339/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.waterandskin.com/h339/ | US | — | — | shared |
284 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.waterandskin.com/h339/ | US | — | — | shared |
284 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.waterandskin.com/h339/ | US | — | — | shared |
284 | explorer.exe | POST | — | 183.111.182.214:80 | http://www.woosinelec.com/h339/ | KR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
284 | explorer.exe | 47.105.32.89:80 | www.haruite.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
284 | explorer.exe | 107.148.41.15:80 | www.pw247.net | PEG TECH INC | US | malicious |
284 | explorer.exe | 183.111.182.214:80 | www.woosinelec.com | Korea Telecom | KR | malicious |
284 | explorer.exe | 23.20.239.12:80 | www.waterandskin.com | Amazon.com, Inc. | US | shared |
284 | explorer.exe | 39.109.17.118:80 | www.coolryuu.com | Huayun Data Holdings Limited | HK | malicious |
284 | explorer.exe | 45.34.81.84:80 | www.leifengdige.com | Psychz Networks | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.clubmaker-online.net |
| unknown |
www.haruite.com |
| malicious |
www.pw247.net |
| malicious |
www.waterandskin.com |
| shared |
www.woosinelec.com |
| malicious |
www.bianlitaobao.com |
| unknown |
www.leifengdige.com |
| malicious |
www.ie.world |
| unknown |
www.neiyi555.com |
| unknown |
www.coolryuu.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
16 ETPRO signatures available at the full report