| File name: | g39b2cx(4).exe |
| Full analysis: | https://app.any.run/tasks/5bf53be0-8a21-4c3d-8d5a-f548c6d6d6db |
| Verdict: | Malicious activity |
| Threats: | Dridex is a very evasive and technically complex banking trojan. Despite being based on a relatively old malware code, it was substantially updated over the years and became capable of using very effective infiltration techniques that make this malware especially dangerous. |
| Analysis date: | April 20, 2021, 00:47:50 |
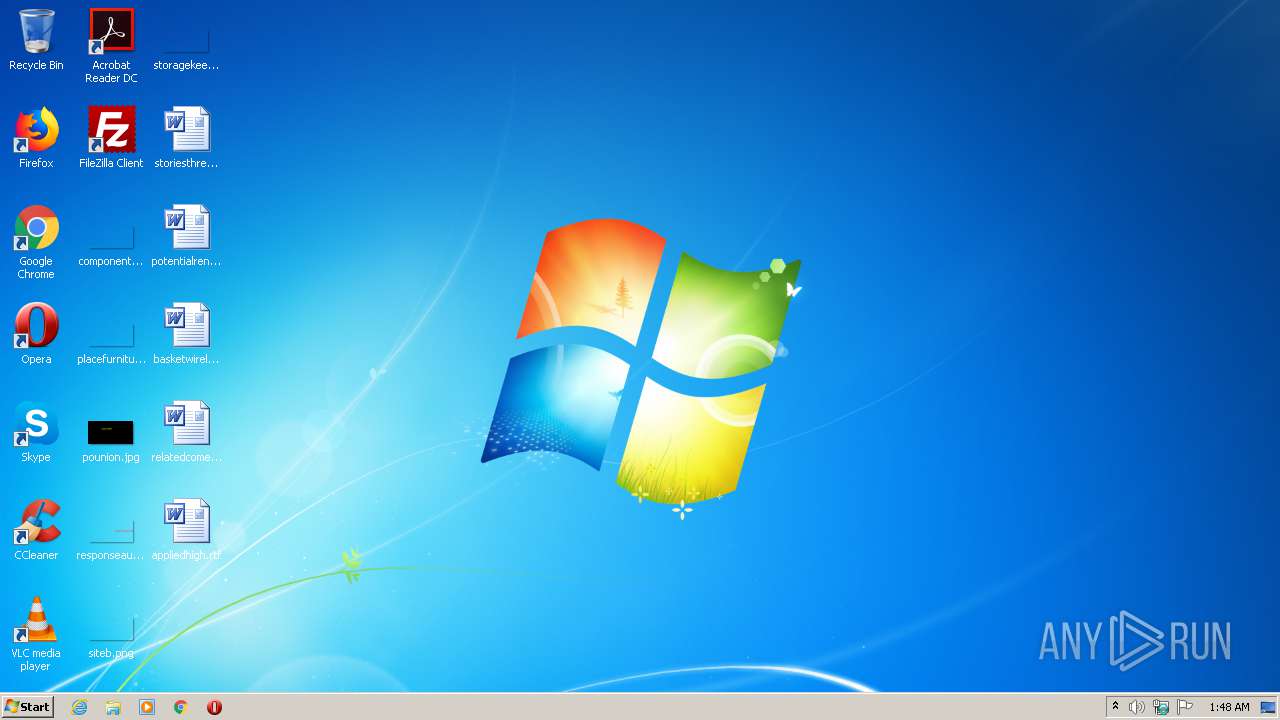
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 107A3BEF0DA9AB2B42E3E0F9F843093B |
| SHA1: | FC5D6FC2CBB1D95864F5ED26B50E4EBE68333EAB |
| SHA256: | 7C9D5724064693DFEEF76FD4DA8D6F159EF0E6707E67C4A692A03E94F4A6E27A |
| SSDEEP: | 1536:LAMgYHctDjzbvvY6gfkcGZVbd+3o0BDla:LTg0ctHzs9k5p0Ygl |
MALICIOUS
DRIDEX was detected
- edgCCED.exe (PID: 2296)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3260)
Creates files in the Windows directory
- sdbinst.exe (PID: 2544)
Starts CMD.EXE for commands execution
- iscsicli.exe (PID: 3904)
Creates a software uninstall entry
- sdbinst.exe (PID: 2544)
Removes files from Windows directory
- sdbinst.exe (PID: 2204)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| ProductVersion: | 6.00.2601.5512 |
|---|---|
| ProductName: | Операционная система Microsoft® Windows® |
| OriginalFileName: | twext.dll |
| LegalCopyright: | © Корпорация Майкрософт. Все права защищены. |
| InternalName: | twext |
| FileVersion: | 6.00.3601.5512 (xpsp.080413-2105) |
| FileDescription: | Свойства: Предыдущие версии |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Unicode |
| LanguageCode: | Russian |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 6.0.2601.5512 |
| FileVersionNumber: | 6.0.3601.5512 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x18260 |
| UninitializedDataSize: | 4608 |
| InitializedDataSize: | 57344 |
| CodeSize: | 22016 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2018:06:11 01:13:00+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2018 23:13:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Свойства: Предыдущие версии |
| FileVersion: | 6.00.3601.5512 (xpsp.080413-2105) |
| InternalName: | twext |
| LegalCopyright: | © Корпорация Майкрософт. Все права защищены. |
| OriginalFilename: | twext.dll |
| ProductName: | Операционная система Microsoft® Windows® |
| ProductVersion: | 6.00.2601.5512 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 10-Jun-2018 23:13:00 |
| Pointer to Symbol Table: | 0x00013A00 |
| Number of symbols: | 526 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.data | 0x00001000 | 0x000021C0 | 0x00002200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE, IMAGE_SCN_TYPE_DSECT | 0.680125 |
a1 | 0x00004000 | 0x000034C4 | 0x00003600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.33952 |
a3 | 0x00008000 | 0x00003570 | 0x00003600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.39311 |
a2 | 0x0000C000 | 0x00002207 | 0x00002400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.20506 |
eq43 | 0x0000F000 | 0x00002251 | 0x00002400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.45828 |
.edata | 0x00012000 | 0x00000037 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.506642 |
.text0 | 0x00013000 | 0x000055F4 | 0x00005600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.87691 |
.bss | 0x00019000 | 0x00001008 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001B000 | 0x00000438 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.74907 |
.rsrc | 0x0001C000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.64671 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.00179 | 908 | Latin 1 / Western European | Russian - Russia | RT_VERSION |
123 | 4.87791 | 668 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
REGINST | 5.81403 | 2113 | Latin 1 / Western European | Russian - Russia | REGINST |
Total processes
51
Monitored processes
10
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1448 | "C:\Users\admin\AppData\Local\Temp\g39b2cx(4).exe" | C:\Users\admin\AppData\Local\Temp\g39b2cx(4).exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Свойства: Предыдущие версии Exit code: 0 Version: 6.00.3601.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
| 2204 | sdbinst /q /u "C:\Users\admin\AppData\LocalLow\fHCmUSG.sdb" | C:\Windows\system32\sdbinst.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Application Compatibility Database Installer Exit code: 0 Version: 6.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | C:\Users\admin\AppData\Local\edgCCED.exe C:\Users\admin\AppData\Local\Temp\G39B2C~1.EXE | C:\Users\admin\AppData\Local\edgCCED.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Свойства: Предыдущие версии Exit code: 0 Version: 6.00.3601.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
| 2544 | "C:\Windows\System32\sdbinst.exe" /q "C:\Users\admin\AppData\LocalLow\fHCmUSG.sdb" | C:\Windows\System32\sdbinst.exe | g39b2cx(4).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Application Compatibility Database Installer Exit code: 0 Version: 6.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Custom\iscsicli.exe" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | cmd /c C:\Users\admin\AppData\LocalLow\fHCmUSG.bat | C:\Windows\System32\cmd.exe | — | iscsicli.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3276 | "C:\Windows\System32\sdbinst.exe" /q "C:\Users\admin\AppData\LocalLow\fHCmUSG.sdb" | C:\Windows\System32\sdbinst.exe | — | g39b2cx(4).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Compatibility Database Installer Exit code: 3221226540 Version: 6.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | "C:\Windows\System32\iscsicli.exe" | C:\Windows\System32\iscsicli.exe | — | g39b2cx(4).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: iSCSI Discovery tool Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3864 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\InstalledSDB\{f48a0c57-7c48-461c-9957-ab255ddc986e}" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | "C:\Windows\System32\iscsicli.exe" | C:\Windows\System32\iscsicli.exe | g39b2cx(4).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: iSCSI Discovery tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
89
Read events
70
Write events
15
Delete events
4
Modification events
| (PID) Process: | (1448) g39b2cx(4).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1448) g39b2cx(4).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Custom\iscsicli.exe |
| Operation: | write | Name: | {f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb |
Value: 5E939CD57E35D701 | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb |
| Operation: | write | Name: | DisplayName |
Value: iscsicli | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb |
| Operation: | write | Name: | UninstallString |
Value: %windir%\system32\sdbinst.exe -u "C:\Windows\AppPatch\Custom\{f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb" | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\InstalledSDB\{f48a0c57-7c48-461c-9957-ab255ddc986e} |
| Operation: | write | Name: | DatabasePath |
Value: C:\Windows\AppPatch\Custom\{f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\InstalledSDB\{f48a0c57-7c48-461c-9957-ab255ddc986e} |
| Operation: | write | Name: | DatabaseType |
Value: 65536 | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\InstalledSDB\{f48a0c57-7c48-461c-9957-ab255ddc986e} |
| Operation: | write | Name: | DatabaseDescription |
Value: iscsicli | |||
| (PID) Process: | (2544) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\InstalledSDB\{f48a0c57-7c48-461c-9957-ab255ddc986e} |
| Operation: | write | Name: | DatabaseInstallTimeStamp |
Value: 5E939CD57E35D701 | |||
| (PID) Process: | (2204) sdbinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Custom\iscsicli.exe |
| Operation: | delete value | Name: | {f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb |
Value: 5E939CD57E35D701 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1448 | g39b2cx(4).exe | C:\Users\admin\AppData\LocalLow\fHCmUSG.sdb | sdb | |
MD5:— | SHA256:— | |||
| 1448 | g39b2cx(4).exe | C:\Users\admin\AppData\LocalLow\fHCmUSG.bat | text | |
MD5:— | SHA256:— | |||
| 2544 | sdbinst.exe | C:\Windows\AppPatch\Custom\{f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb | sdb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2296 | edgCCED.exe | POST | — | 92.63.88.83:80 | http://FSLc3.us/ | LV | — | — | malicious |
2296 | edgCCED.exe | POST | — | 188.120.225.17:8080 | http://HCUawGgJ6.biz:8080/ | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2296 | edgCCED.exe | 92.63.88.83:80 | — | SIA MWTV | LV | malicious |
2296 | edgCCED.exe | 188.120.225.17:8080 | — | JSC ISPsystem | RU | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2296 | edgCCED.exe | A Network Trojan was detected | ET TROJAN Dridex POST Retrieving Second Stage M2 |
2296 | edgCCED.exe | A Network Trojan was detected | ET TROJAN Dridex POST Retrieving Second Stage M2 |