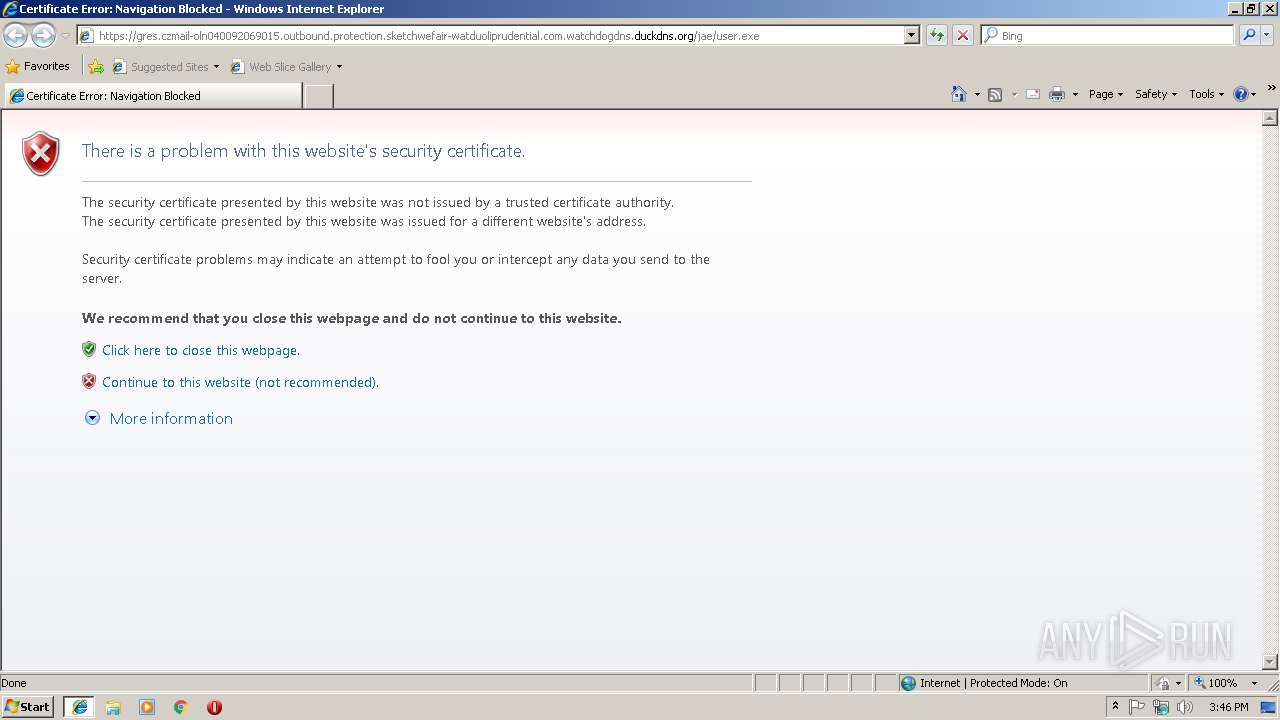
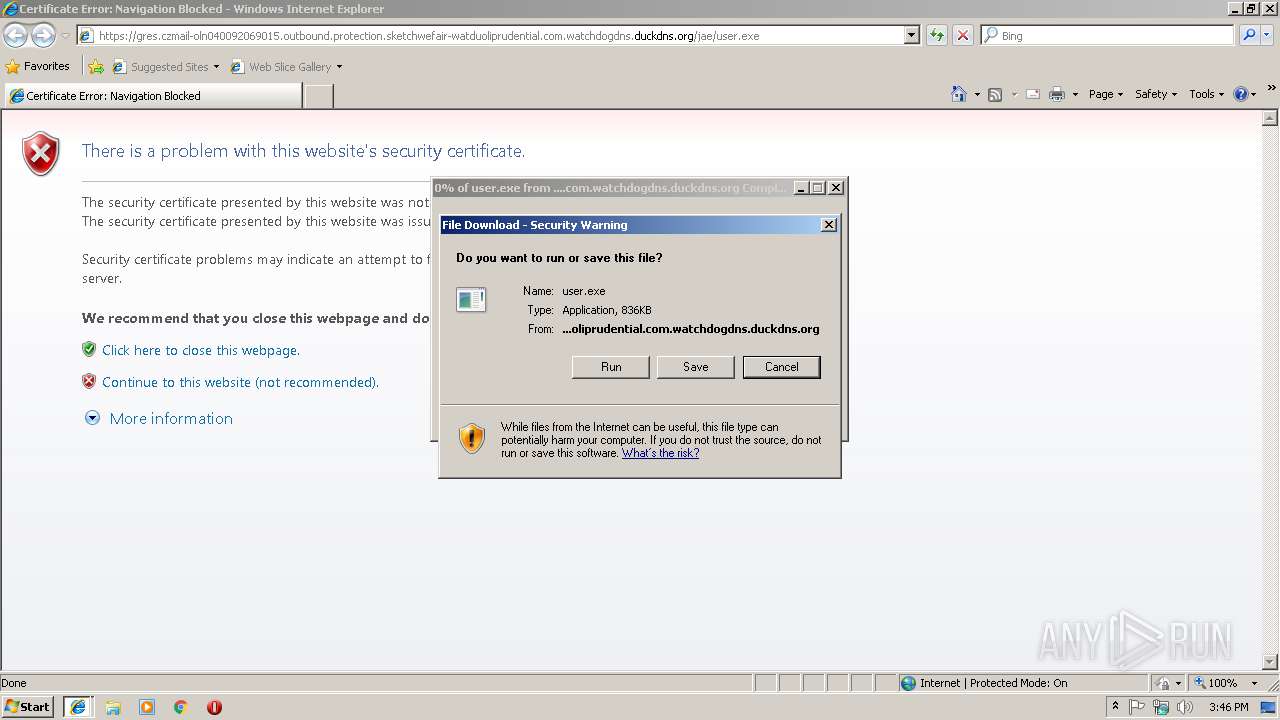
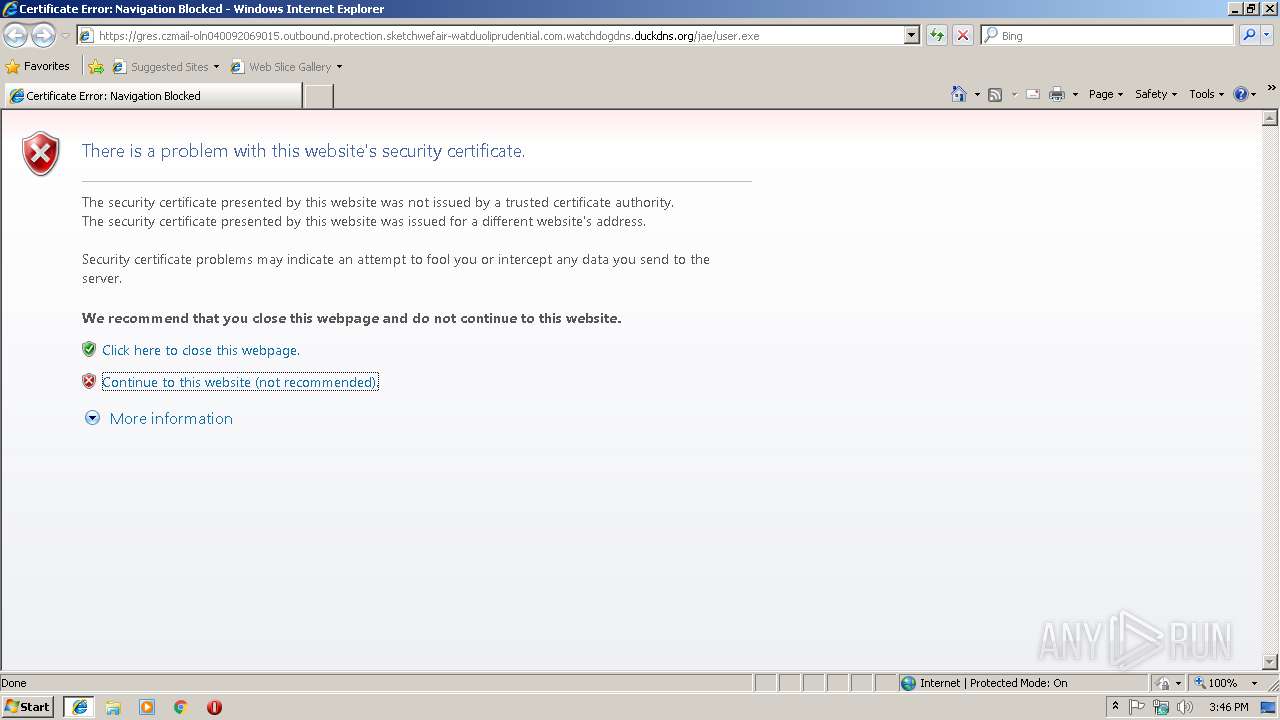
| URL: | https://gres.czmail-oln040092069015.outbound.protection.sketchwefair-watduoliprudential.com.watchdogdns.duckdns.org/jae/user.exe |
| Full analysis: | https://app.any.run/tasks/690aa41a-93ed-407e-9a90-93c5a16bcfd7 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | February 18, 2019, 15:45:27 |
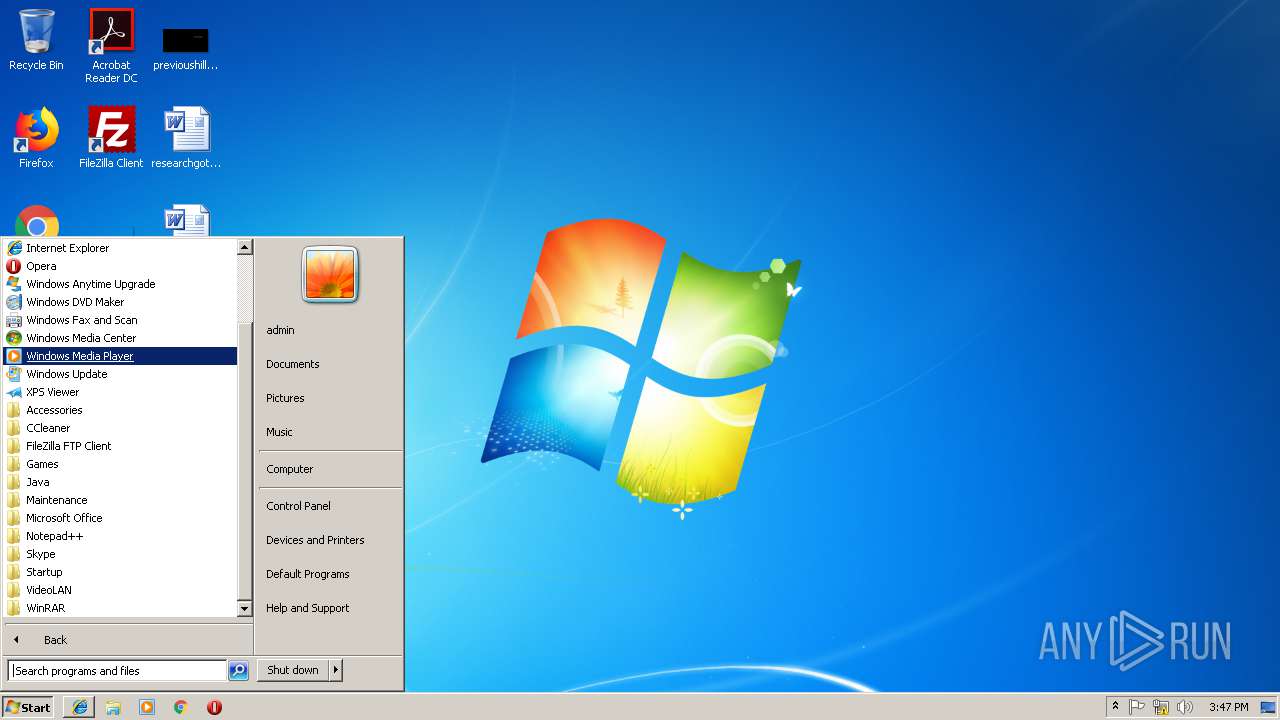
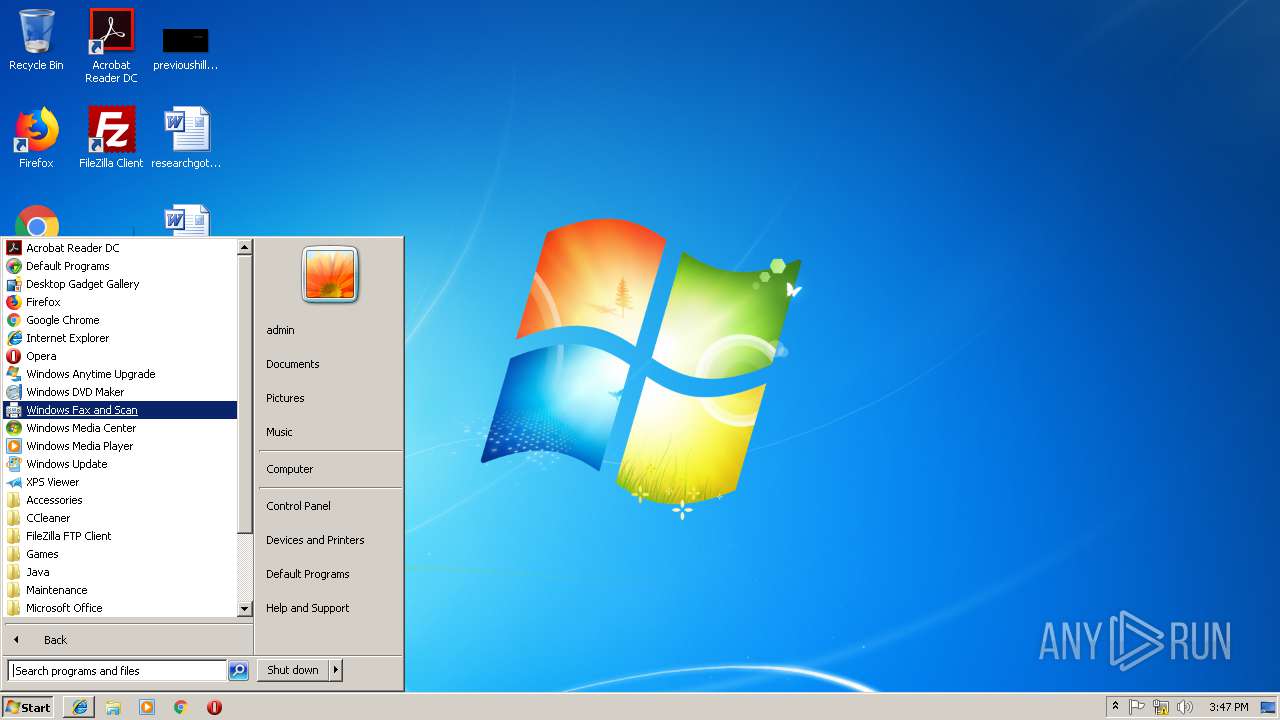
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4F81D1DAFE7C9C62CD4D14E22E1C1FB1 |
| SHA1: | 307E6C5E81FD8D0405B8366CFE32F5AF6277063A |
| SHA256: | 7C79F5006A6FC929FAE8F1E05E704C5B69AA2C0C8679CDDE55659B46CA70F5A2 |
| SSDEEP: | 3:N82AMI5qzcGFKFeBhaAGRKOyqsJO1kTXCyaWi8AL0A:22UKK0haAGRVyqsQGXSWlAl |
MALICIOUS
Application was dropped or rewritten from another process
- user[1].exe (PID: 3212)
- user[1].exe (PID: 3560)
- vvmptj8pgfi8.exe (PID: 3508)
- vvmptj8pgfi8.exe (PID: 2312)
Connects to CnC server
- explorer.exe (PID: 284)
Changes the autorun value in the registry
- chkdsk.exe (PID: 3280)
FORMBOOK was detected
- explorer.exe (PID: 284)
Formbook was detected
- chkdsk.exe (PID: 3280)
- Firefox.exe (PID: 2816)
Actions looks like stealing of personal data
- chkdsk.exe (PID: 3280)
Loads dropped or rewritten executable
- chkdsk.exe (PID: 3280)
Stealing of credential data
- cmd.exe (PID: 2428)
- chkdsk.exe (PID: 3280)
SUSPICIOUS
Starts Internet Explorer
- explorer.exe (PID: 284)
Application launched itself
- user[1].exe (PID: 3560)
- vvmptj8pgfi8.exe (PID: 3508)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3256)
- explorer.exe (PID: 284)
- DllHost.exe (PID: 2644)
- chkdsk.exe (PID: 3280)
Creates files in the user directory
- chkdsk.exe (PID: 3280)
Starts CMD.EXE for commands execution
- chkdsk.exe (PID: 3280)
Loads DLL from Mozilla Firefox
- chkdsk.exe (PID: 3280)
Creates files in the program directory
- DllHost.exe (PID: 2644)
INFO
Application launched itself
- iexplore.exe (PID: 2976)
Changes internet zones settings
- iexplore.exe (PID: 2976)
Reads internet explorer settings
- iexplore.exe (PID: 3256)
Reads Internet Cache Settings
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3256)
Creates files in the user directory
- Firefox.exe (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
13
Malicious processes
4
Suspicious processes
0
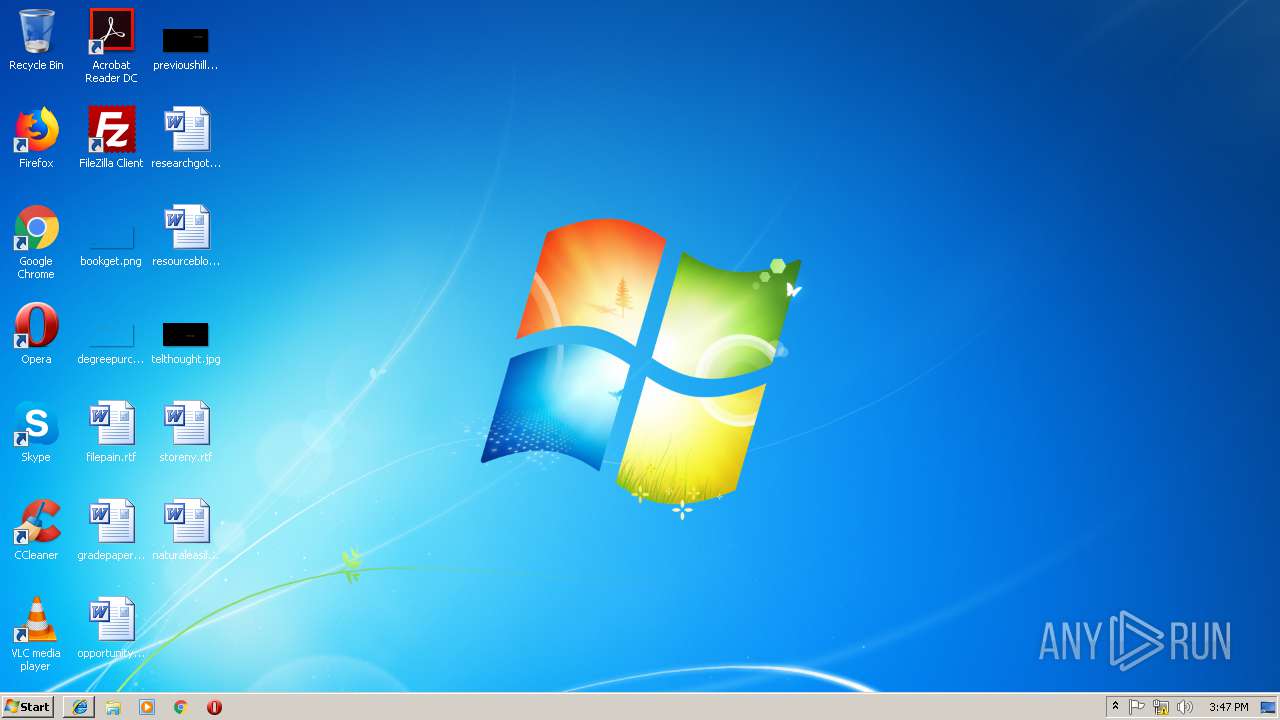
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Wm628\vvmptj8pgfi8.exe" | C:\Program Files\Wm628\vvmptj8pgfi8.exe | — | vvmptj8pgfi8.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2428 | /c copy "C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data" "C:\Users\admin\AppData\Local\Temp\DB1" /V | C:\Windows\System32\cmd.exe | chkdsk.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | chkdsk.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2888 | "C:\Windows\System32\services.exe" | C:\Windows\System32\services.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\user[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\user[1].exe | — | user[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2976 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3280 | "C:\Windows\System32\chkdsk.exe" | C:\Windows\System32\chkdsk.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Check Disk Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 193
Read events
2 494
Write events
2 696
Delete events
3
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3FA6BB81-3394-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200010012000F002D002C002700 | |||
Executable files
5
Suspicious files
81
Text files
14
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEE3C.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEE3D.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEE4E.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEE4F.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2907.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2908.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2938.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2939.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
15
DNS requests
8
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
284 | explorer.exe | GET | — | 50.116.64.44:80 | http://www.qskystudio.com/wa/?NVDPll=zUPmGBTcumcQ84AxUehNif7H2a8EeuFxL86ReWp2a2nL/ryaSQ0kTJ9TKLFW9a+zGTkyuQ==&Wz=H2g49vWHQZclu&sql=1 | US | — | — | malicious |
284 | explorer.exe | POST | — | 50.116.64.44:80 | http://www.qskystudio.com/wa/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 50.116.64.44:80 | http://www.qskystudio.com/wa/ | US | — | — | malicious |
284 | explorer.exe | GET | 200 | 192.64.115.176:80 | http://www.skylod.com/wa/?NVDPll=4v4zjVxlCQAsyTZxYMjBQegLqvW+jDeGWAiwLvaoNiVJFn7AHBOayqRXsd7SC+lNyT6yvg==&Wz=H2g49vWHQZclu&sql=1 | US | binary | 323 Kb | malicious |
284 | explorer.exe | POST | — | 192.64.115.176:80 | http://www.skylod.com/wa/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 192.64.115.176:80 | http://www.skylod.com/wa/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 50.116.64.44:80 | http://www.qskystudio.com/wa/ | US | — | — | malicious |
3256 | iexplore.exe | GET | 200 | 67.27.151.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
284 | explorer.exe | GET | 404 | 45.39.170.155:80 | http://www.cryptoaltex.com/wa/?NVDPll=qifVH0mniBjdj7DvQY2G0tpEI1LJ2kislspVqwfdpD74V/kBJnMXCVcqpWuJpmgnnx6Cew==&Wz=H2g49vWHQZclu | US | html | 1.22 Kb | malicious |
2976 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2976 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3256 | iexplore.exe | 23.249.161.100:443 | gres.czmail-oln040092069015.outbound.protection.sketchwefair-watduoliprudential.com.watchdogdns.duckdns.org | ColoCrossing | US | malicious |
3256 | iexplore.exe | 8.248.113.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3256 | iexplore.exe | 67.27.151.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
284 | explorer.exe | 45.39.170.155:80 | www.cryptoaltex.com | EGIHosting | US | malicious |
284 | explorer.exe | 192.64.115.176:80 | www.skylod.com | Namecheap, Inc. | US | malicious |
284 | explorer.exe | 50.116.64.44:80 | www.qskystudio.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gres.czmail-oln040092069015.outbound.protection.sketchwefair-watduoliprudential.com.watchdogdns.duckdns.org |
| malicious |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.cryptoaltex.com |
| malicious |
www.qskystudio.com |
| malicious |
www.skylod.com |
| malicious |
www.paddlepass.info |
| unknown |
www.tv16366.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
7 ETPRO signatures available at the full report