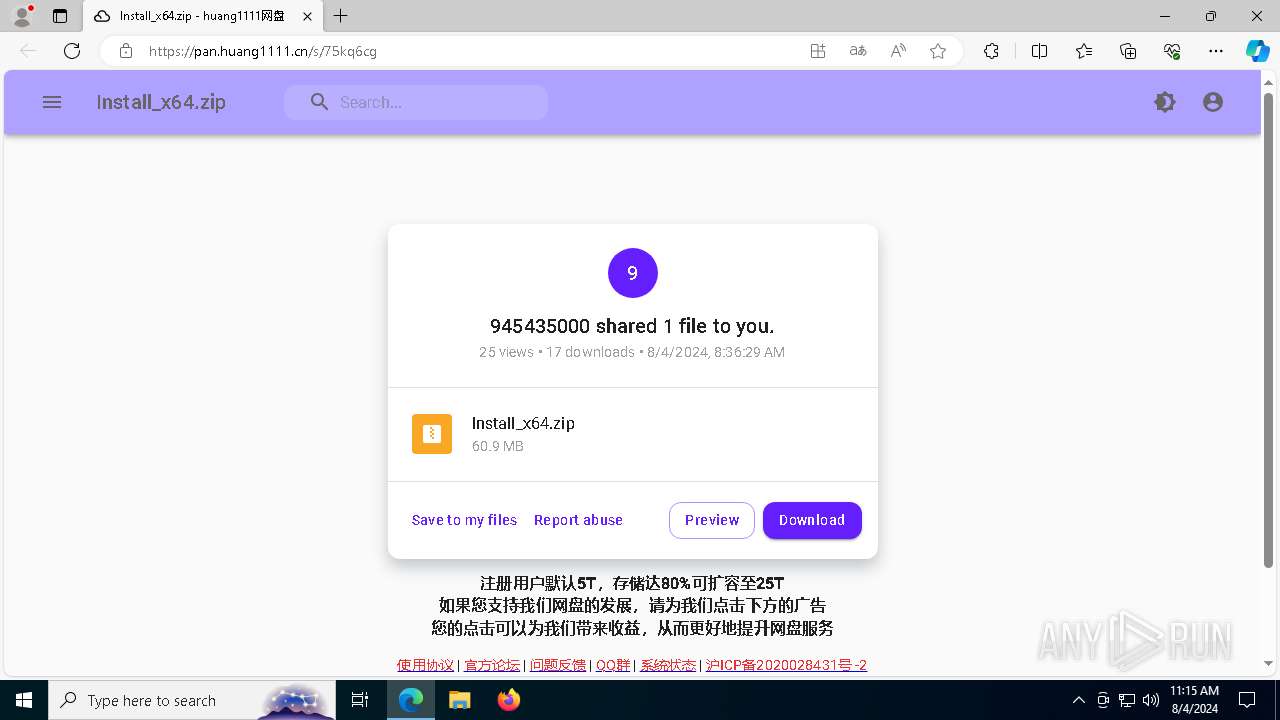
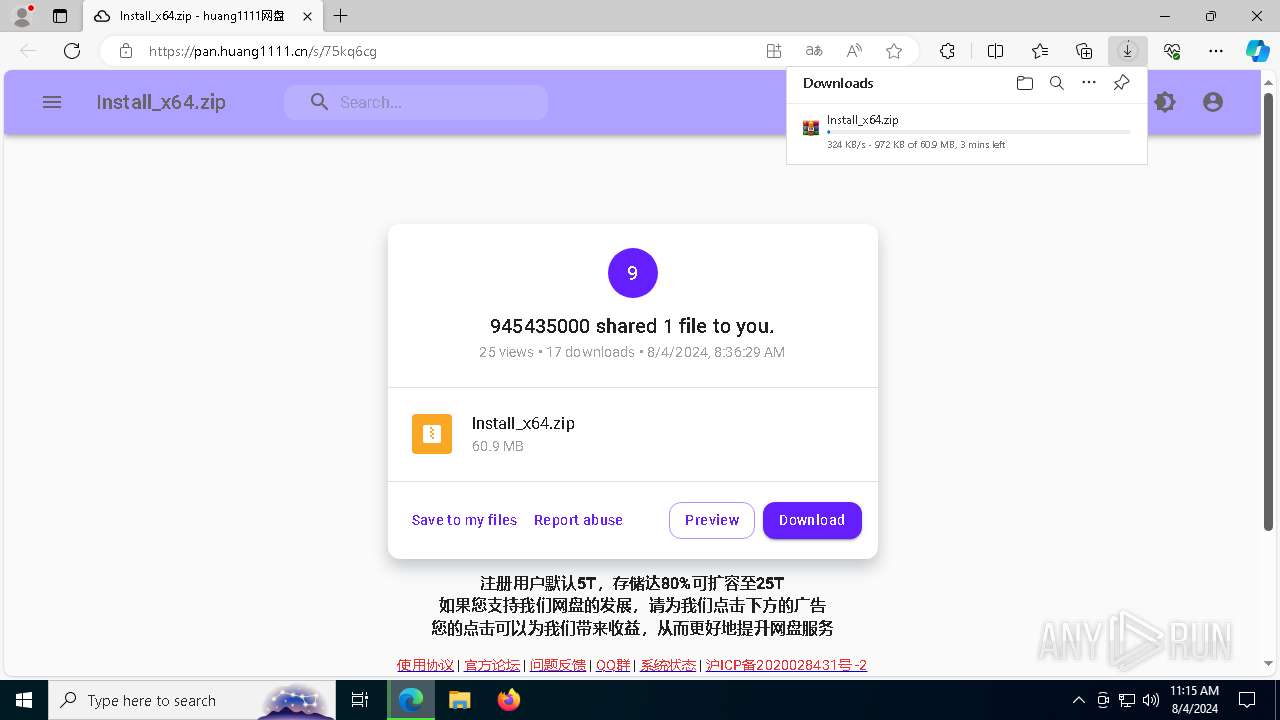
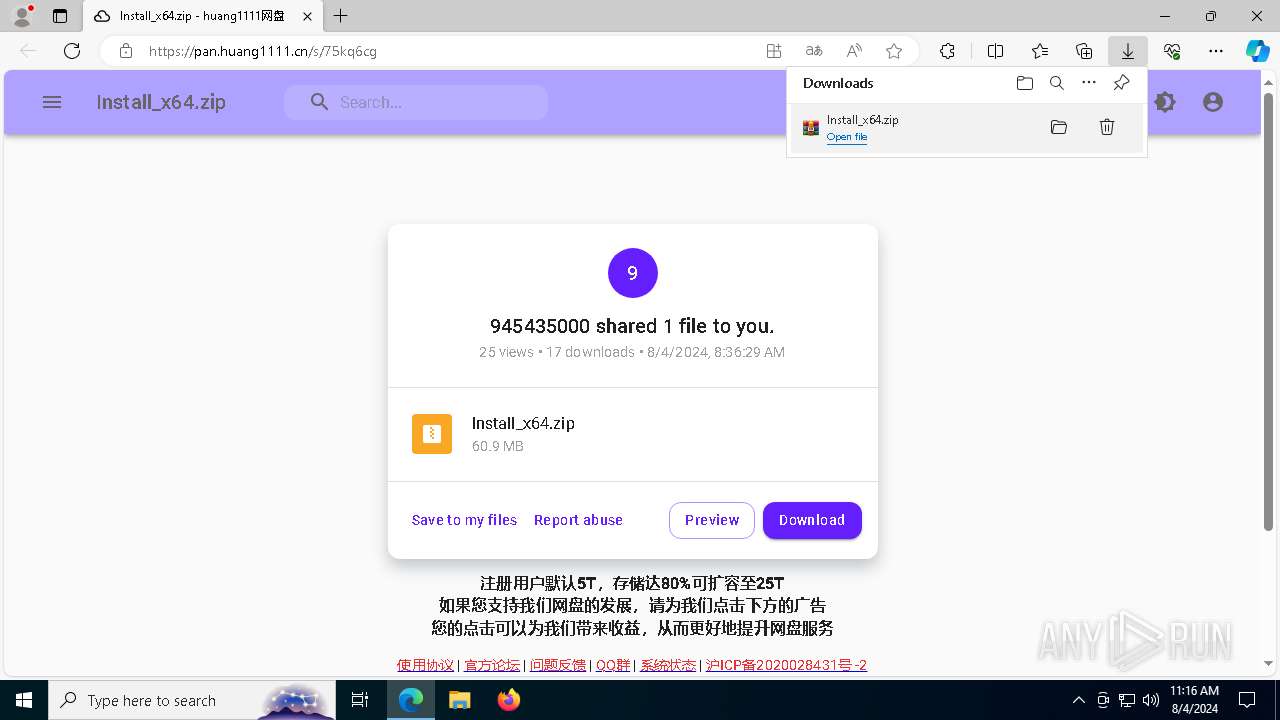
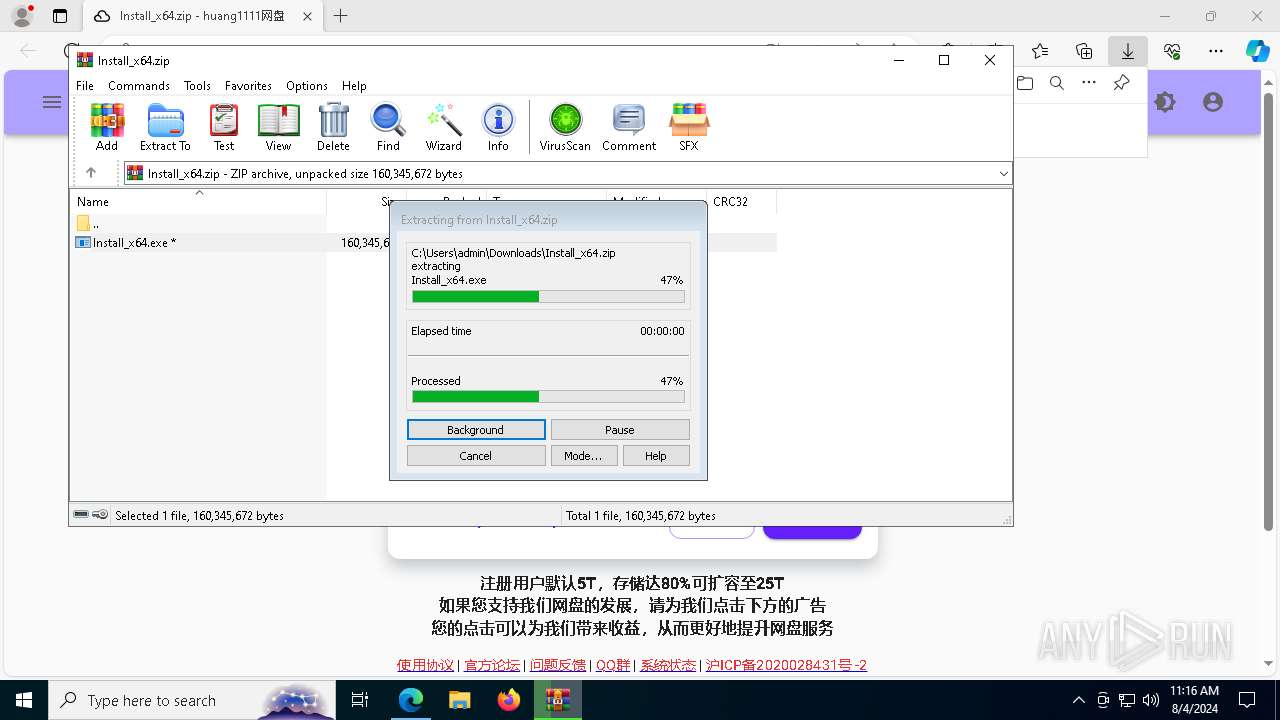
| URL: | https://pan.huang1111.cn/s/75kq6cg |
| Full analysis: | https://app.any.run/tasks/1b7d9900-a4fc-4ff3-b4a0-900e98e1bc67 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | August 04, 2024, 11:14:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3F285B6209DDD40DB7D1131EB1AABE45 |
| SHA1: | 6C7CF88AAA5DC4622AEBD0AE3B34145228B99604 |
| SHA256: | 7C4C8A947A42769734F698656813A4097A51E33D5F7E95E0C8CD0759EC094C65 |
| SSDEEP: | 3:N8A/NQiX7NAGC:2A/CiX7OGC |
MALICIOUS
Adds path to the Windows Defender exclusion list
- Install_x64.exe (PID: 4168)
RHADAMANTHYS has been detected (SURICATA)
- OpenWith.exe (PID: 6828)
- OOBE-Maintenance.exe (PID: 1044)
- dllhost.exe (PID: 5512)
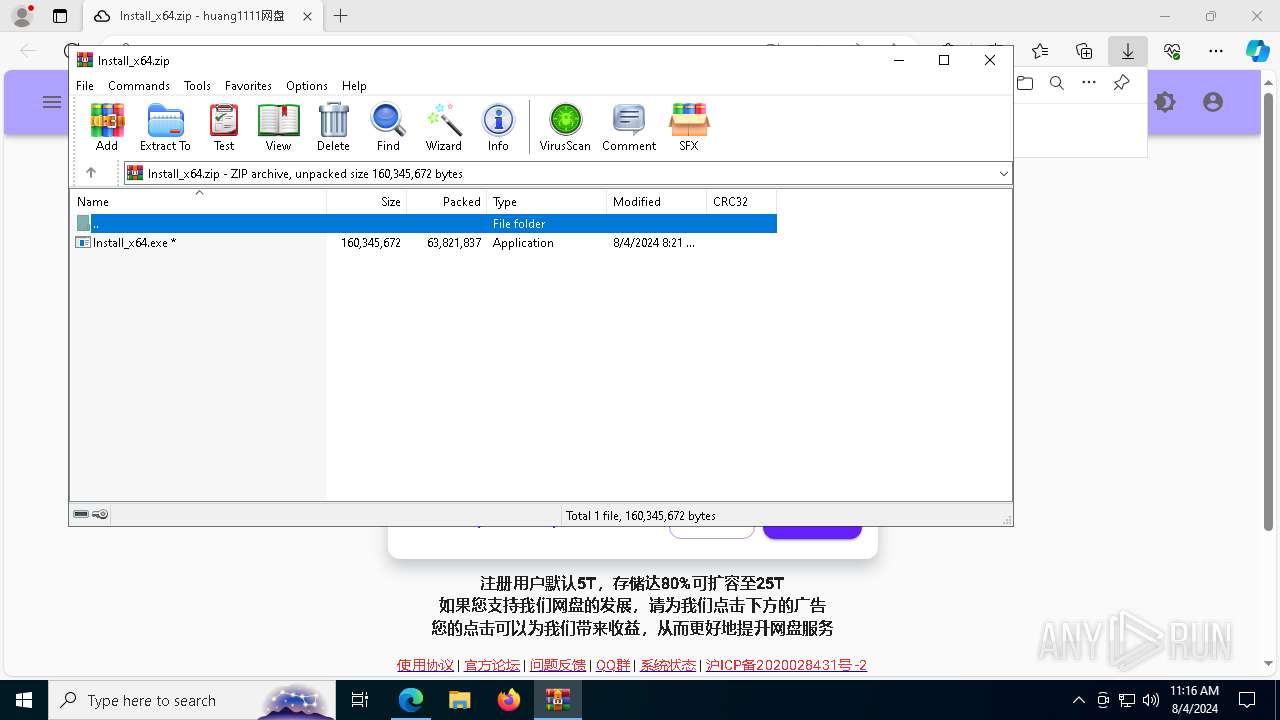
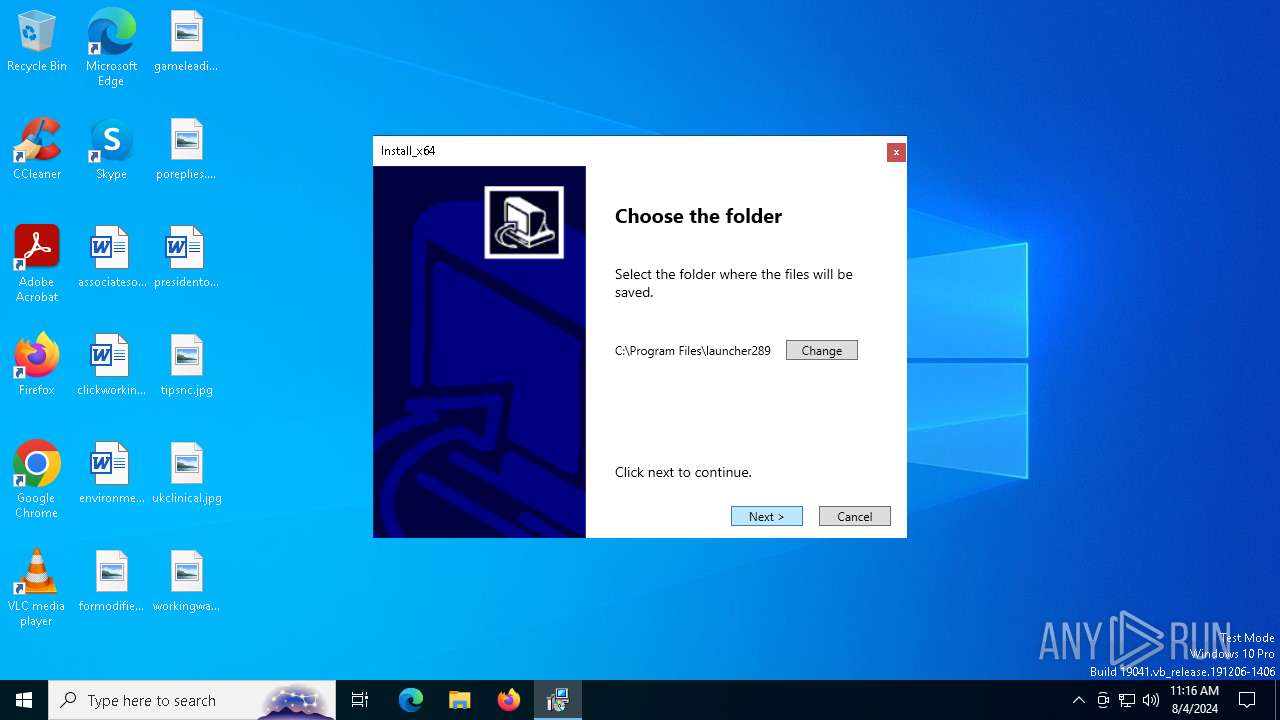
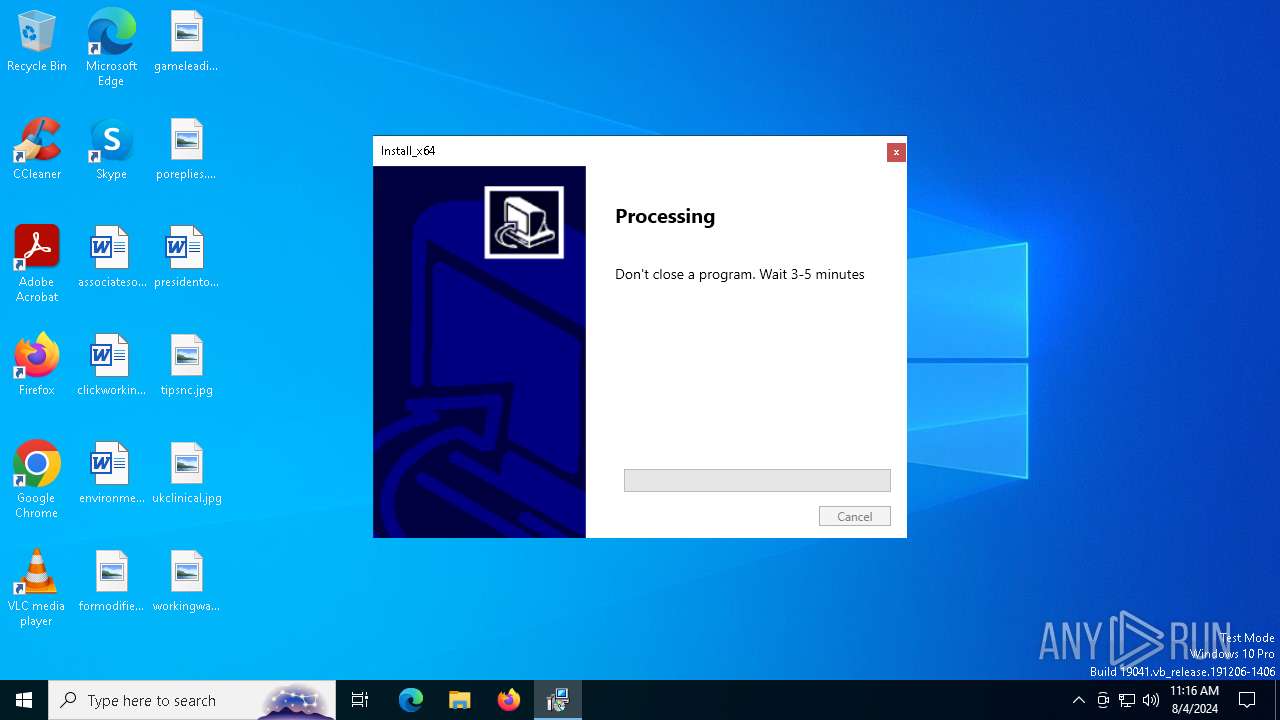
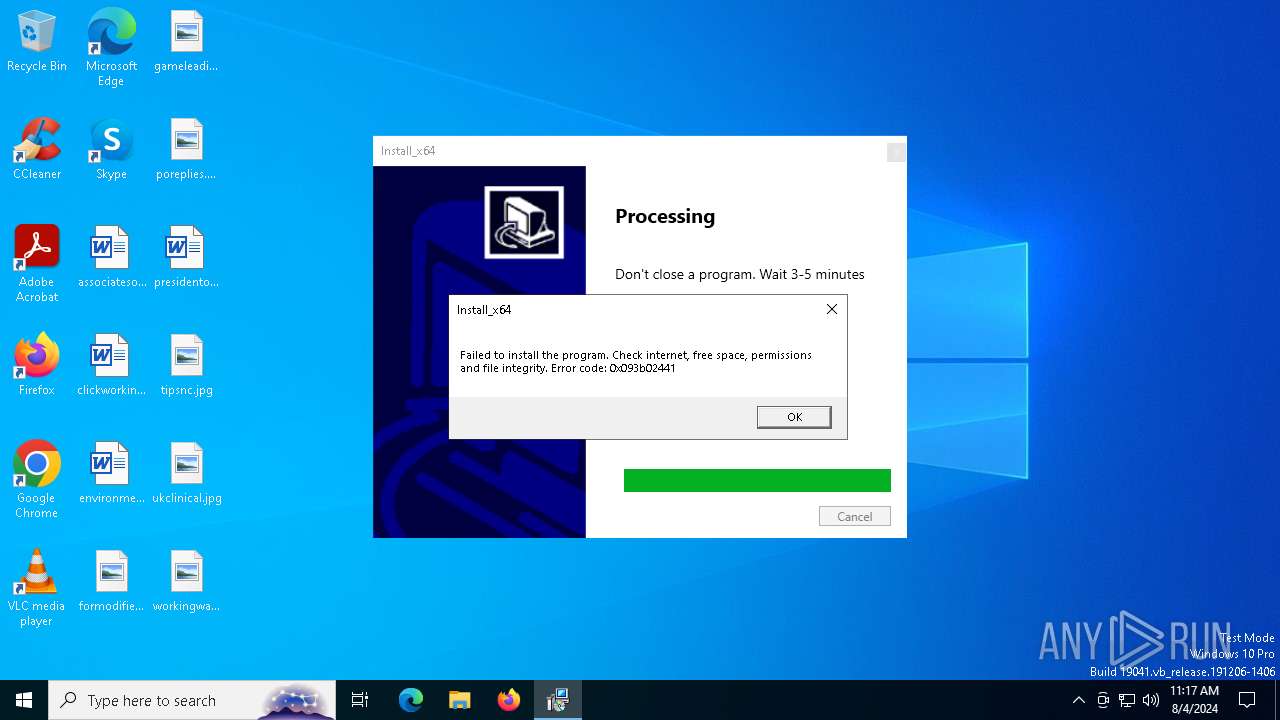
Drops the executable file immediately after the start
- Install_x64.exe (PID: 4168)
Stealers network behavior
- OOBE-Maintenance.exe (PID: 1044)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 1044)
Bypass execution policy to execute commands
- powershell.exe (PID: 7464)
Changes powershell execution policy (Bypass)
- BitLockerToGo.exe (PID: 7880)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7464)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7464)
Actions looks like stealing of personal data
- powershell.exe (PID: 7464)
- BitLockerToGo.exe (PID: 6740)
- OOBE-Maintenance.exe (PID: 1044)
SUSPICIOUS
Reads security settings of Internet Explorer
- cookie_exporter.exe (PID: 904)
- WinRAR.exe (PID: 936)
- Install_x64.exe (PID: 4168)
Possible Social Engineering Attempted
- msedge.exe (PID: 6748)
Process drops legitimate windows executable
- Install_x64.exe (PID: 4168)
Executable content was dropped or overwritten
- Install_x64.exe (PID: 4168)
The process creates files with name similar to system file names
- Install_x64.exe (PID: 4168)
Starts POWERSHELL.EXE for commands execution
- Install_x64.exe (PID: 4168)
- BitLockerToGo.exe (PID: 7880)
Script adds exclusion path to Windows Defender
- Install_x64.exe (PID: 4168)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7652)
The process drops C-runtime libraries
- Install_x64.exe (PID: 4168)
Contacting a server suspected of hosting an CnC
- OpenWith.exe (PID: 6828)
- OOBE-Maintenance.exe (PID: 1044)
- dllhost.exe (PID: 5512)
Executes application which crashes
- BitLockerToGo.exe (PID: 6484)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6828)
Connects to unusual port
- OpenWith.exe (PID: 6828)
- OOBE-Maintenance.exe (PID: 1044)
- dllhost.exe (PID: 5512)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 1044)
Searches for installed software
- BitLockerToGo.exe (PID: 6740)
- OOBE-Maintenance.exe (PID: 1044)
Request a resource from the Internet using PowerShell's cmdlet
- BitLockerToGo.exe (PID: 7880)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7464)
Starts CMD.EXE for commands execution
- BitLockerToGo.exe (PID: 7880)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7464)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7464)
Identifying current user with WHOAMI command
- powershell.exe (PID: 7464)
Checks for external IP
- svchost.exe (PID: 2256)
- powershell.exe (PID: 7464)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 7464)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7464)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- powershell.exe (PID: 7464)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7464)
INFO
Checks supported languages
- identity_helper.exe (PID: 3908)
- cookie_exporter.exe (PID: 904)
- Install_x64.exe (PID: 4168)
- identity_helper.exe (PID: 32)
- 1.exe (PID: 6324)
- BitLockerToGo.exe (PID: 6484)
- 2.exe (PID: 6932)
- BitLockerToGo.exe (PID: 6740)
- 3.exe (PID: 1964)
- BitLockerToGo.exe (PID: 7880)
- wmplayer.exe (PID: 964)
Application launched itself
- msedge.exe (PID: 6508)
- msedge.exe (PID: 2340)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6508)
- msedge.exe (PID: 2340)
Reads Environment values
- identity_helper.exe (PID: 3908)
- cookie_exporter.exe (PID: 904)
- identity_helper.exe (PID: 32)
Reads the computer name
- cookie_exporter.exe (PID: 904)
- identity_helper.exe (PID: 3908)
- Install_x64.exe (PID: 4168)
- identity_helper.exe (PID: 32)
- BitLockerToGo.exe (PID: 6740)
Checks proxy server information
- cookie_exporter.exe (PID: 904)
- Install_x64.exe (PID: 4168)
- powershell.exe (PID: 7464)
The process uses the downloaded file
- msedge.exe (PID: 5916)
- msedge.exe (PID: 6508)
- WinRAR.exe (PID: 936)
Create files in a temporary directory
- Install_x64.exe (PID: 4168)
- 2.exe (PID: 6932)
Creates files in the program directory
- Install_x64.exe (PID: 4168)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7652)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7652)
Reads the software policy settings
- Install_x64.exe (PID: 4168)
- BitLockerToGo.exe (PID: 6740)
Reads the machine GUID from the registry
- wmplayer.exe (PID: 964)
Disables trace logs
- powershell.exe (PID: 7464)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7464)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7464)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7464)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7464)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7464)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7464)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7464)
Attempting to use instant messaging service
- svchost.exe (PID: 2256)
- powershell.exe (PID: 7464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
235
Monitored processes
92
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5036 --field-trial-handle=2412,i,645018052269917379,12060092702404343165,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6868 --field-trial-handle=2304,i,11462876606029175361,112428086236646013,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5480 --field-trial-handle=2412,i,645018052269917379,12060092702404343165,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | cookie_exporter.exe --cookie-json=776 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\cookie_exporter.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
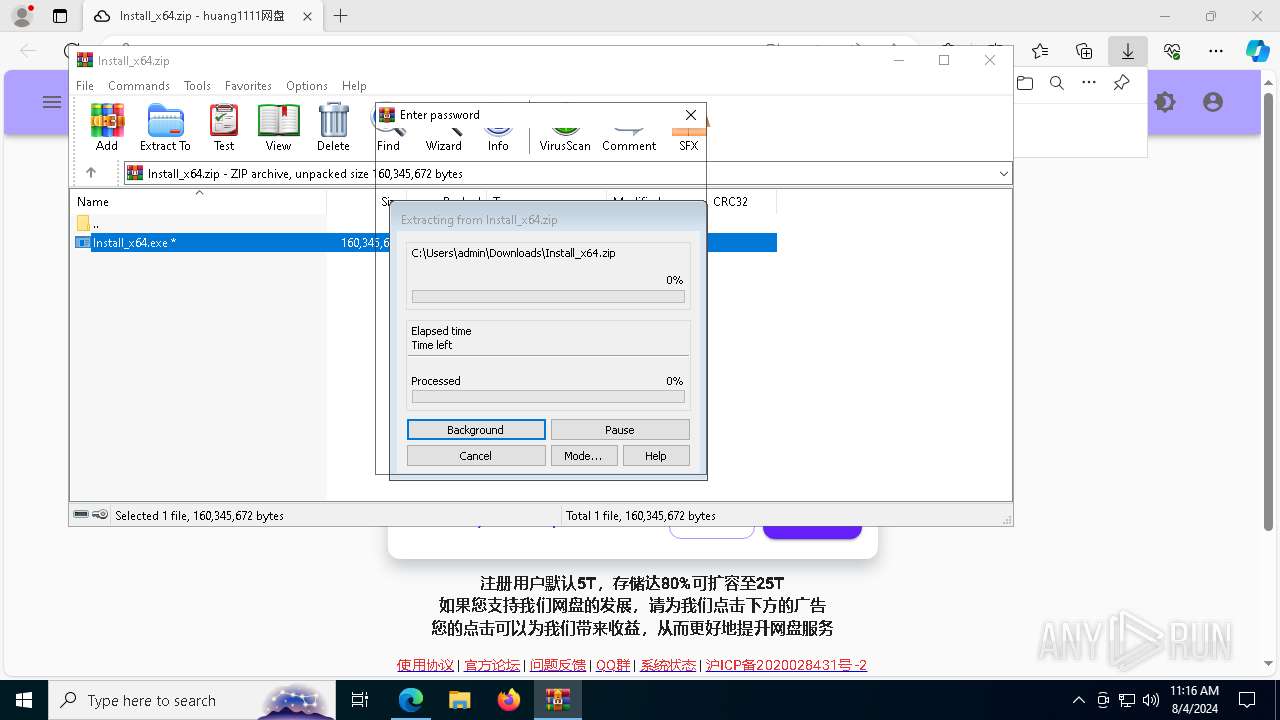
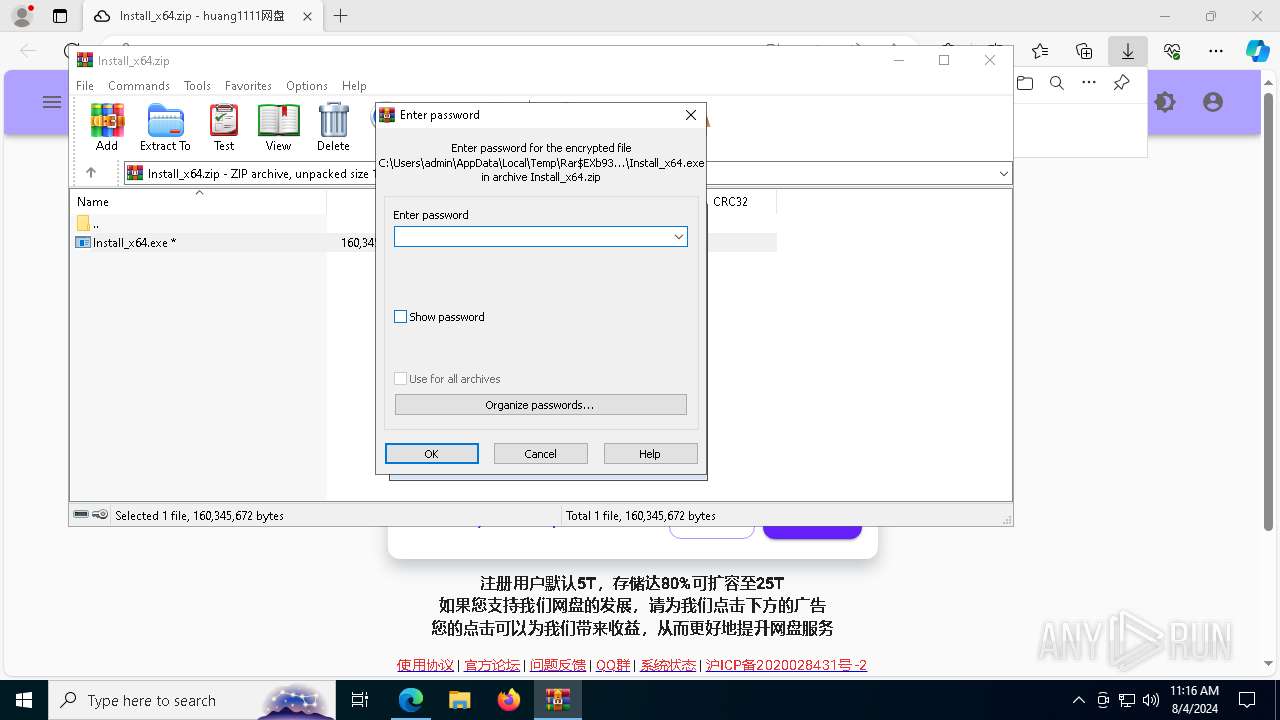
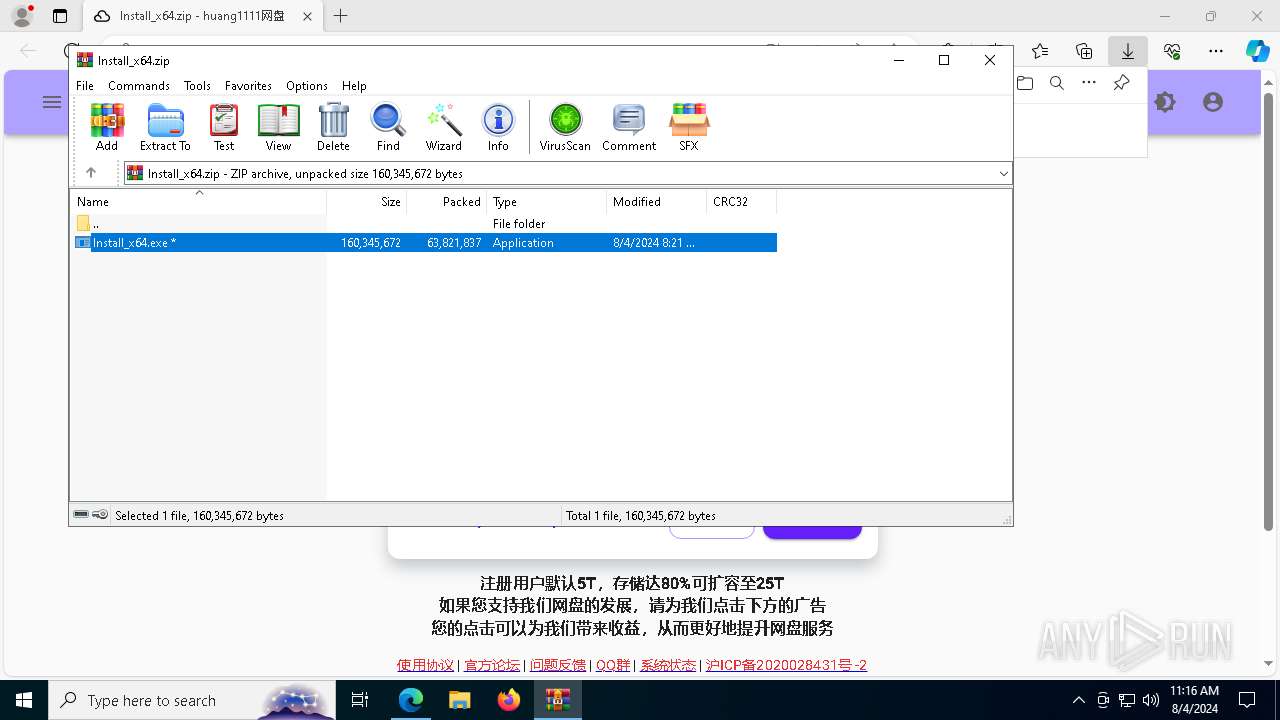
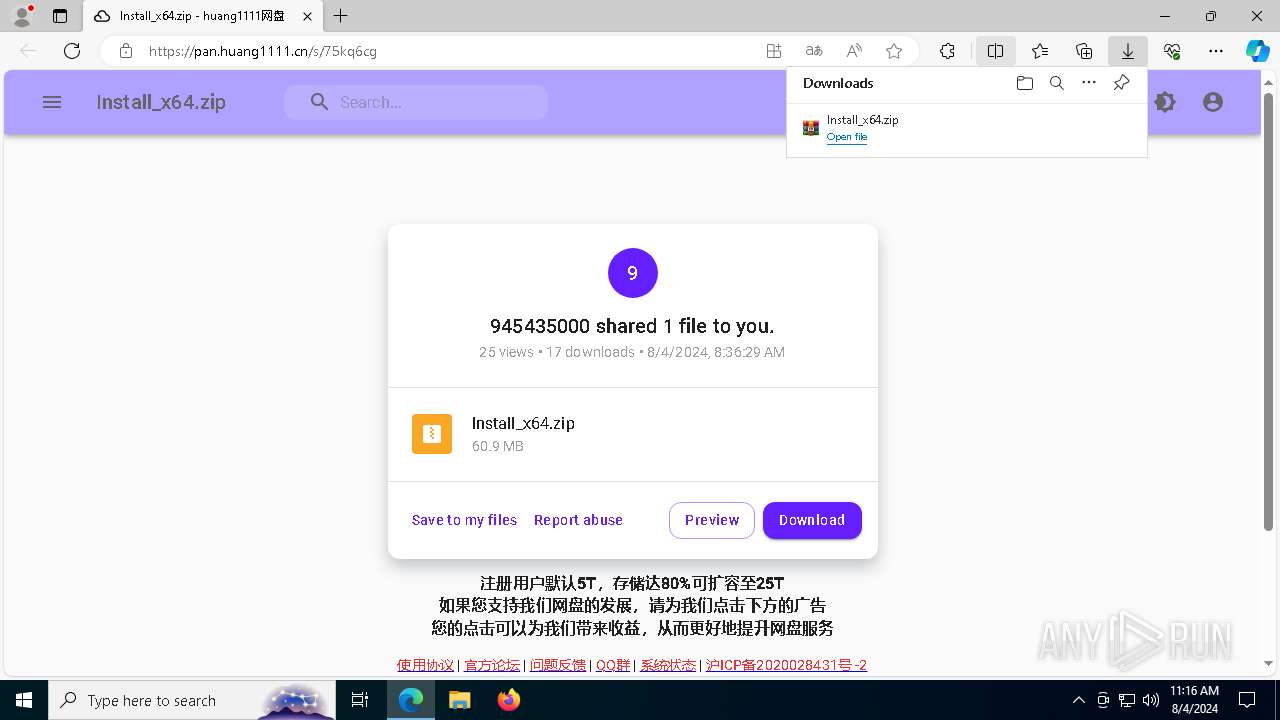
| 936 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Install_x64.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Windows Media Player\wmplayer.exe" | C:\Program Files\Windows Media Player\wmplayer.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Player Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
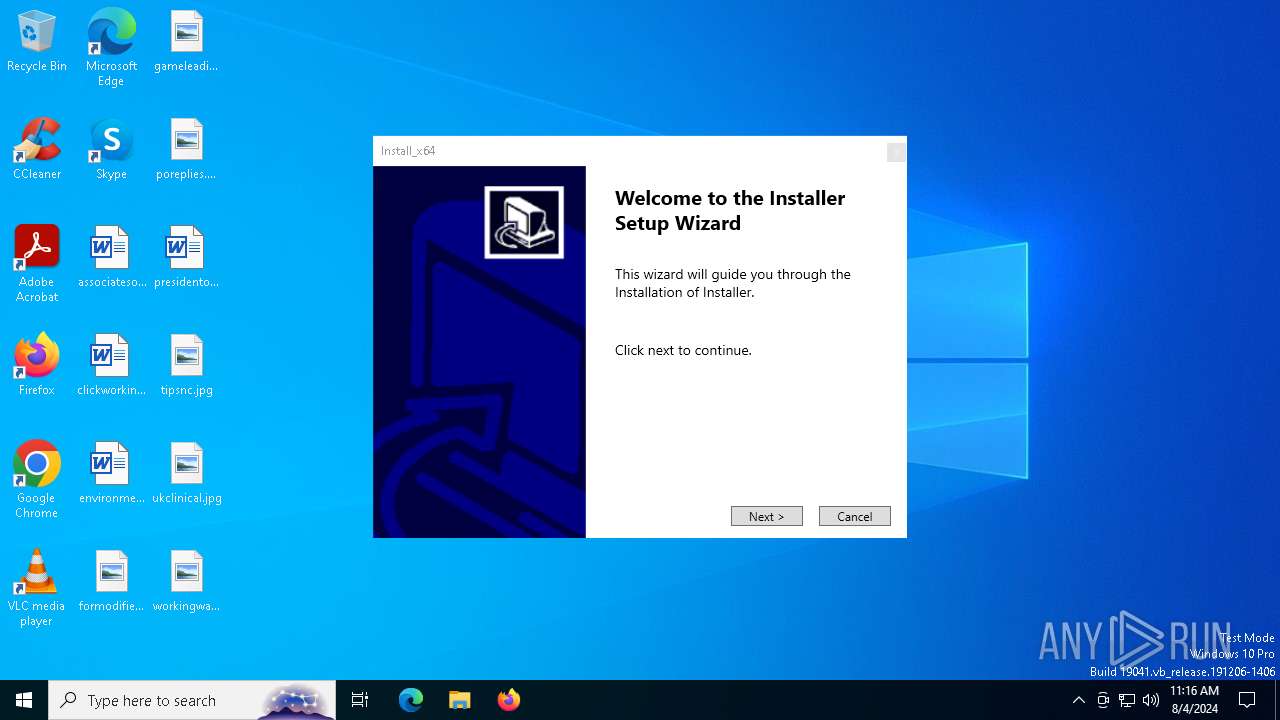
| 1044 | "C:\WINDOWS\system32\OOBE-Maintenance.exe" | C:\Windows\System32\OOBE-Maintenance.exe | Install_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: OOBE-Maintenance Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5384 --field-trial-handle=2412,i,645018052269917379,12060092702404343165,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1860 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7fffcb775fd8,0x7fffcb775fe4,0x7fffcb775ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 4294967295 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\launcher289\3.exe" | C:\Program Files\launcher289\3.exe | — | Install_x64.exe | |||||||||||
User: admin Company: Markus Welz Integrity Level: HIGH Description: SpotOnTheMouse Setup Exit code: 666 Version: Modules
| |||||||||||||||
Total events
48 342
Read events
47 875
Write events
459
Delete events
8
Modification events
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31123039 | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6328) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
454
Suspicious files
246
Text files
165
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe54f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe54f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe5511.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe5511.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe5511.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
154
DNS requests
132
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7188 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7240 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4100 | svchost.exe | HEAD | 200 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/72e62a8f-bc19-44e7-b14b-c0d389408307?P1=1723337672&P2=404&P3=2&P4=jcofoD2tSItc5UwXbiA%2fUrvh96kfPDsTfFvjjHuTWU%2f2y0yHf9CKsRtl1GoLgR8aYOWJUgQi3pIqJ90zPO55mQ%3d%3d | unknown | — | — | whitelisted |
4100 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/72e62a8f-bc19-44e7-b14b-c0d389408307?P1=1723337672&P2=404&P3=2&P4=jcofoD2tSItc5UwXbiA%2fUrvh96kfPDsTfFvjjHuTWU%2f2y0yHf9CKsRtl1GoLgR8aYOWJUgQi3pIqJ90zPO55mQ%3d%3d | unknown | — | — | whitelisted |
4100 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/72e62a8f-bc19-44e7-b14b-c0d389408307?P1=1723337672&P2=404&P3=2&P4=jcofoD2tSItc5UwXbiA%2fUrvh96kfPDsTfFvjjHuTWU%2f2y0yHf9CKsRtl1GoLgR8aYOWJUgQi3pIqJ90zPO55mQ%3d%3d | unknown | — | — | whitelisted |
4100 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/72e62a8f-bc19-44e7-b14b-c0d389408307?P1=1723337672&P2=404&P3=2&P4=jcofoD2tSItc5UwXbiA%2fUrvh96kfPDsTfFvjjHuTWU%2f2y0yHf9CKsRtl1GoLgR8aYOWJUgQi3pIqJ90zPO55mQ%3d%3d | unknown | — | — | whitelisted |
4100 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/72e62a8f-bc19-44e7-b14b-c0d389408307?P1=1723337672&P2=404&P3=2&P4=jcofoD2tSItc5UwXbiA%2fUrvh96kfPDsTfFvjjHuTWU%2f2y0yHf9CKsRtl1GoLgR8aYOWJUgQi3pIqJ90zPO55mQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1184 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4064 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6748 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6508 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6748 | msedge.exe | 188.114.96.9:443 | pan.huang1111.cn | CLOUDFLARENET | NL | unknown |
6748 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6748 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
pan.huang1111.cn |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
a.h1static.cn |
| unknown |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing TLS SNI (.sharepoint .com) |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing TLS SNI (.sharepoint .com) |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing DNS (.sharepoint .com) |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to SharePoint public/private file sharing DNS (.sharepoint .com) |
6748 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Accessing SharePoint content without a legitimate Microsoft Sign-In |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1044 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
1044 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
1044 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
8 ETPRO signatures available at the full report