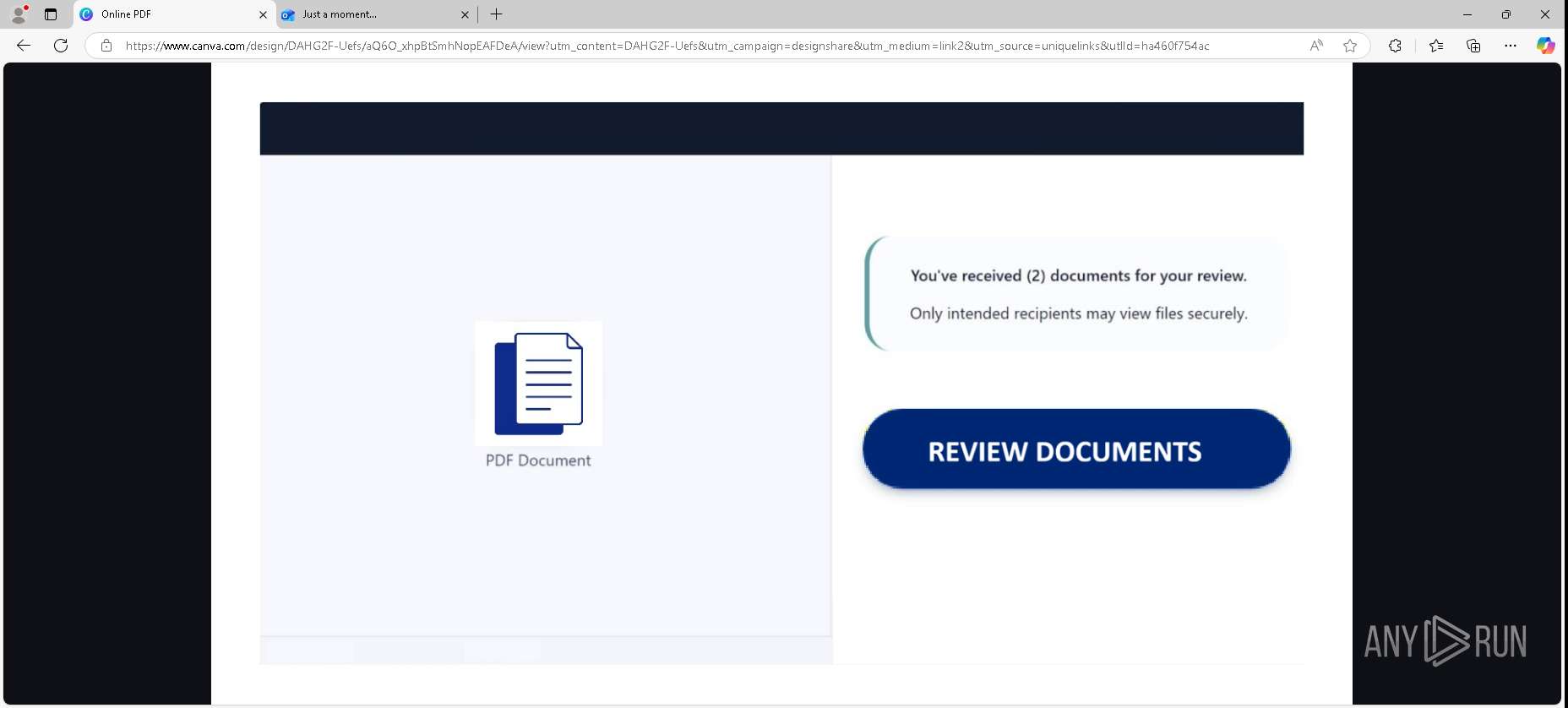
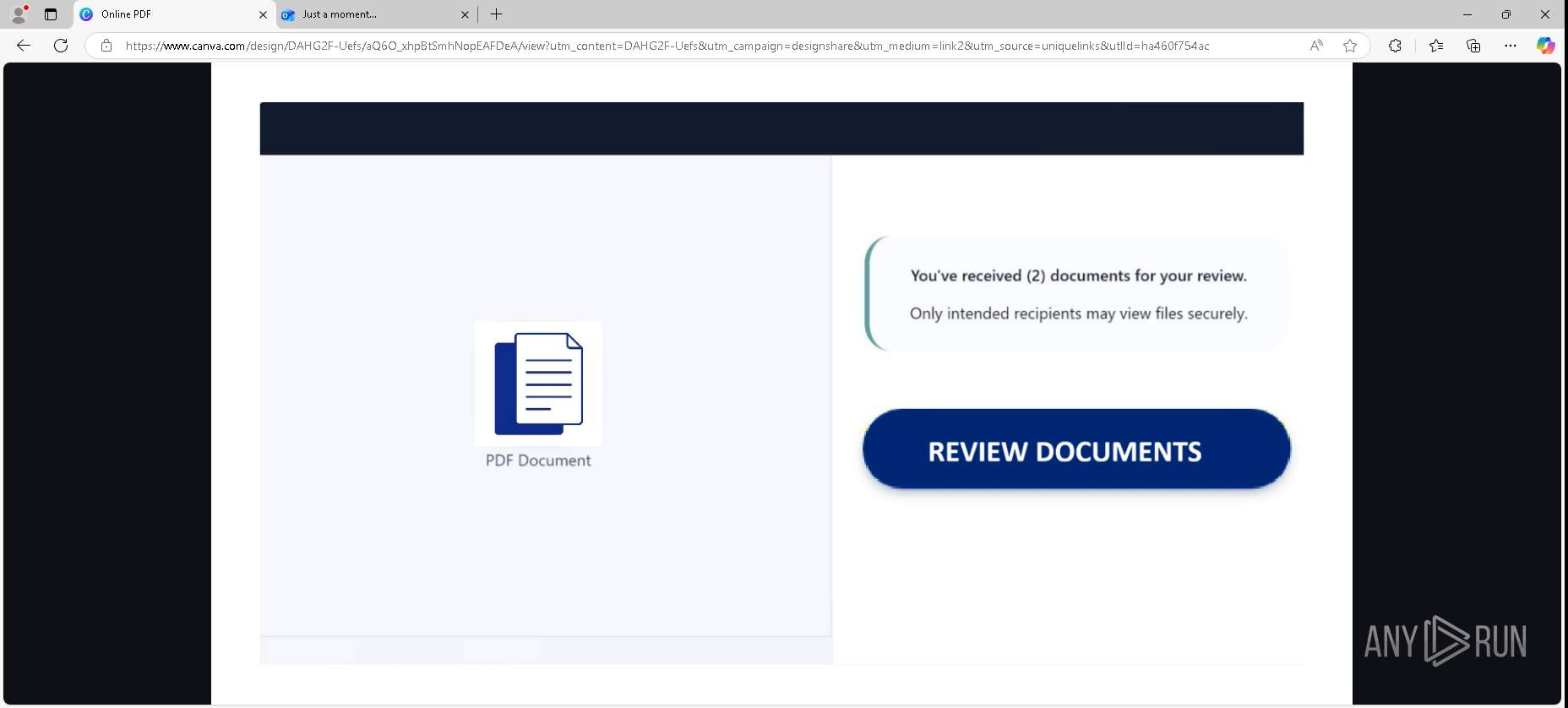
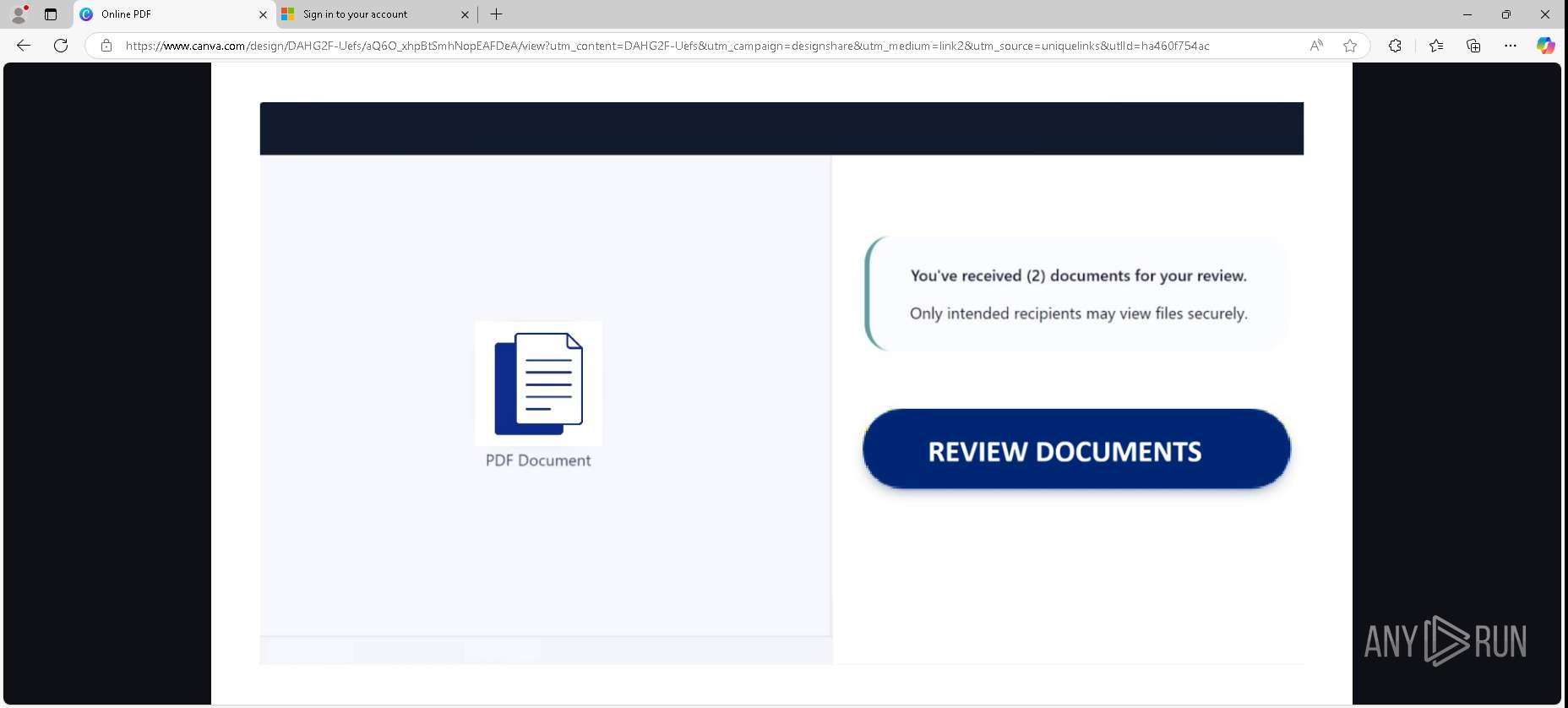
| URL: | https://www.canva.com/design/DAHG2F-Uefs/aQ6O_xhpBtSmhNopEAFDeA/view?utm_content=DAHG2F-Uefs&utm_campaign=designshare&utm_medium=link2&utm_source=uniquelinks&utlId=ha460f754ac |
| Full analysis: | https://app.any.run/tasks/2692cf81-ed6e-4dc1-b02b-f1438e6f32b3 |
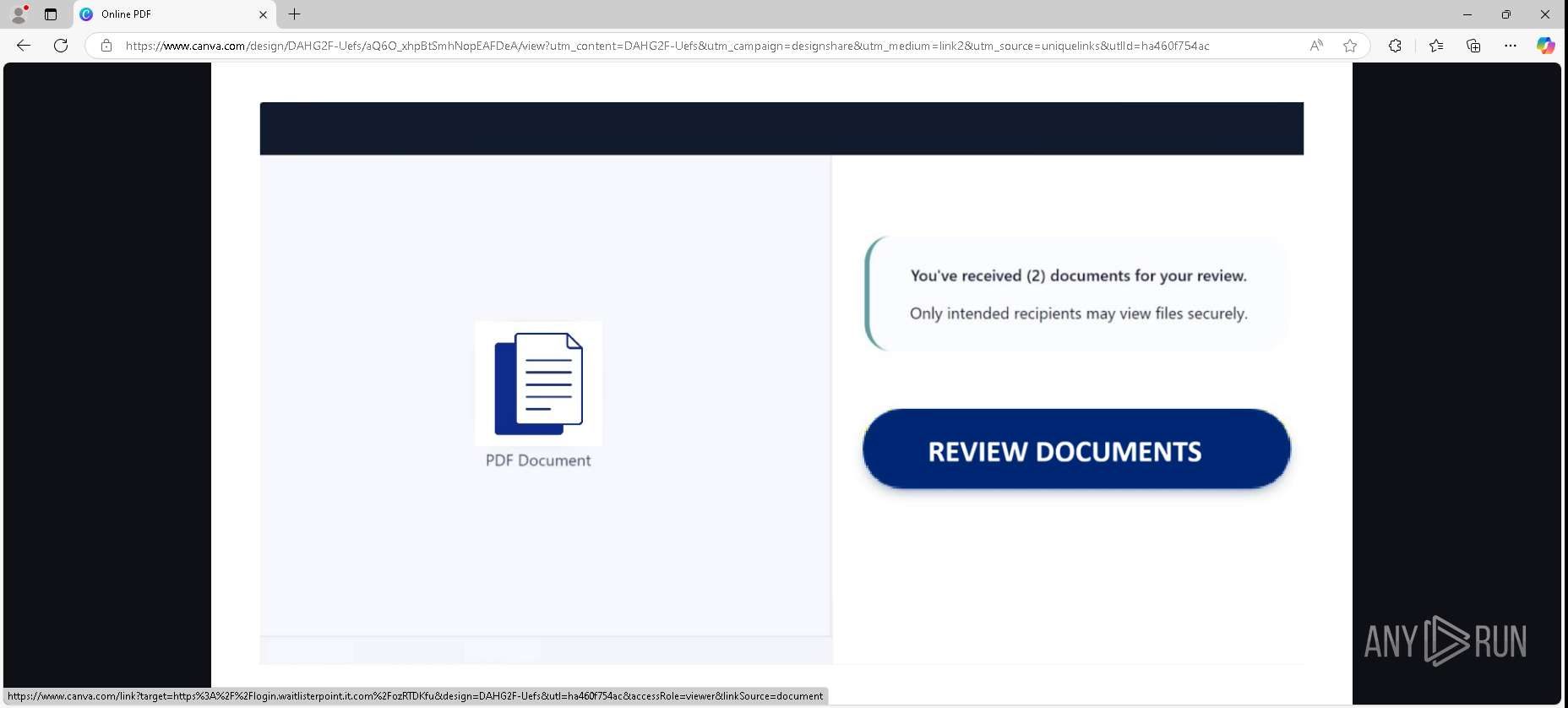
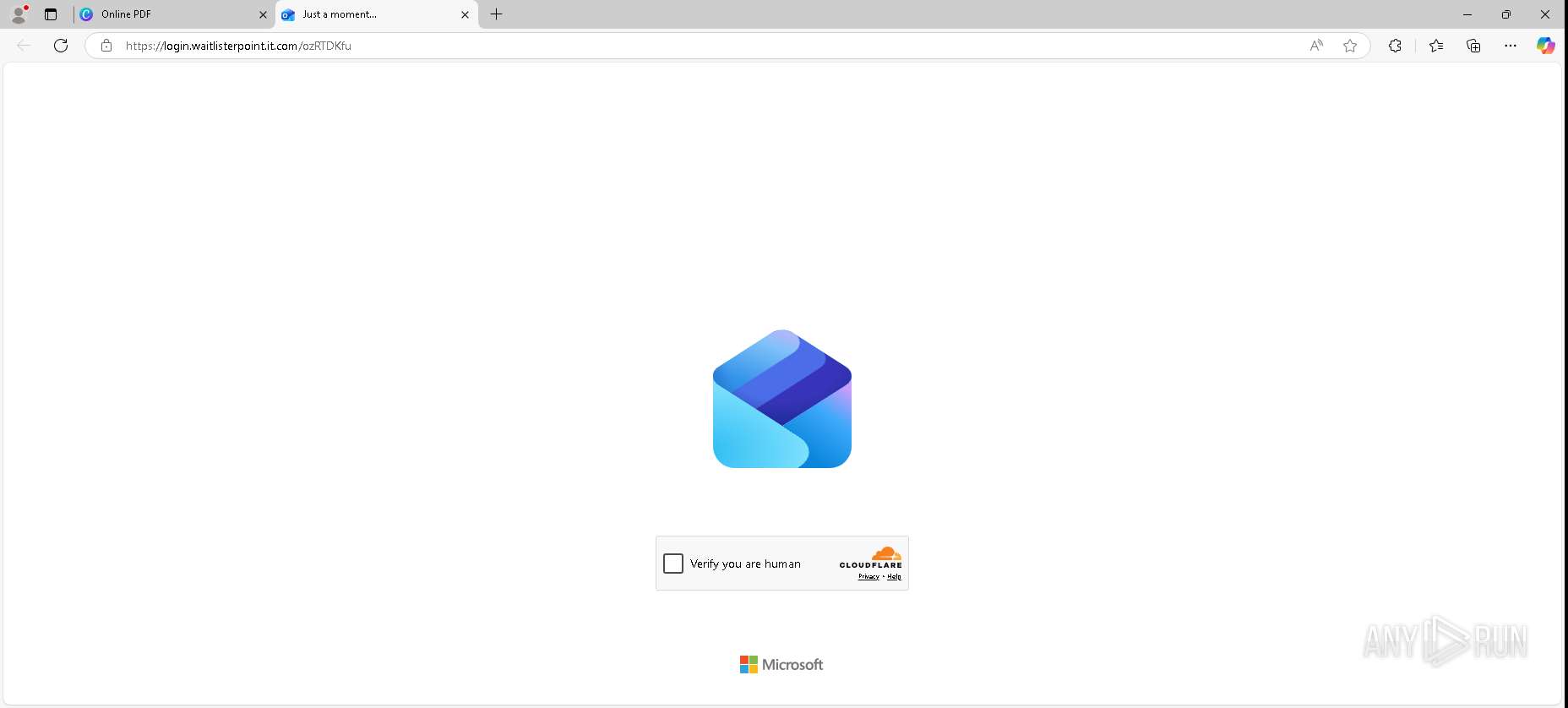
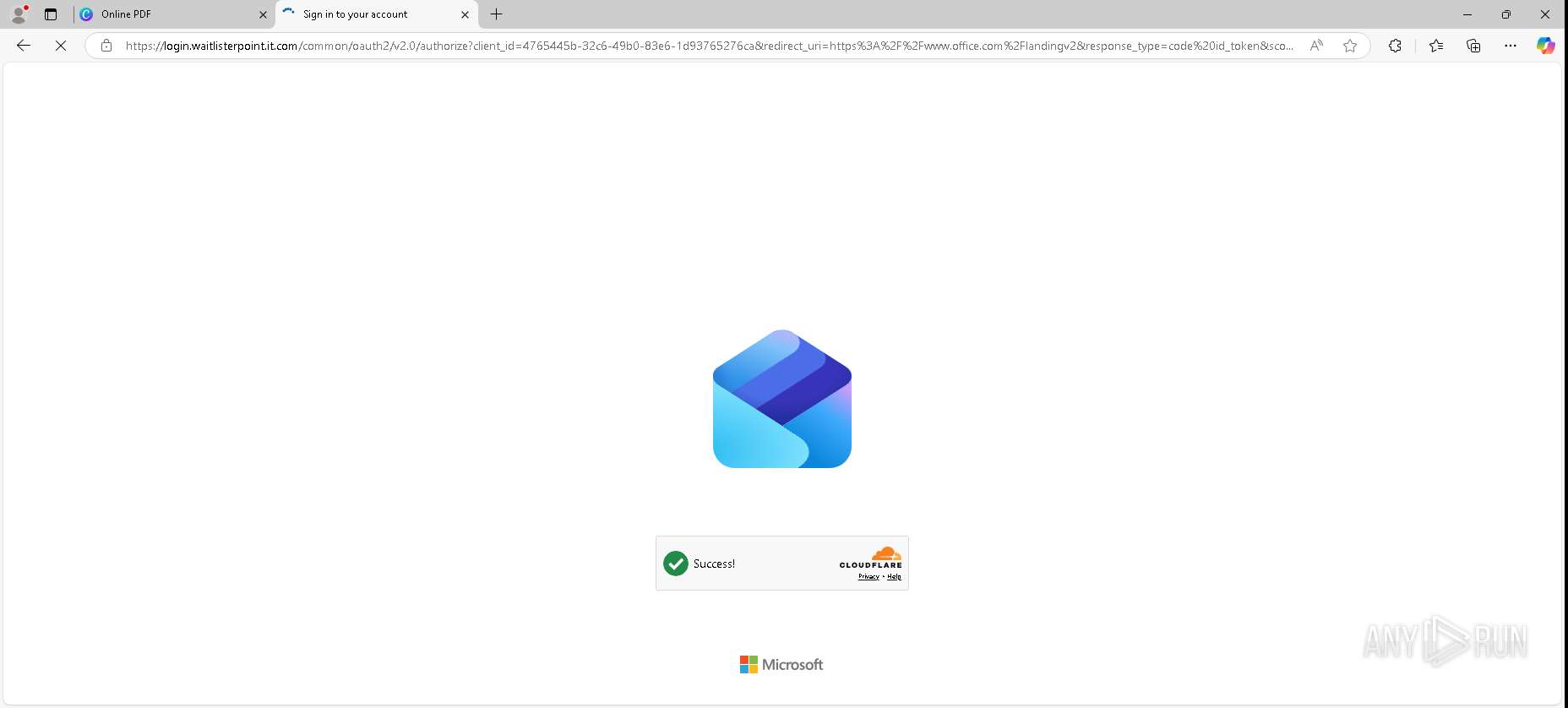
| Verdict: | Malicious activity |
| Threats: | EvilProxy is a phishing-as-a-service (PhaaS) platform that enables cybercriminals to bypass multi-factor authentication (MFA) and hijack user sessions. It leverages reverse proxy techniques to harvest credentials and session cookies, posing a serious threat to both individuals and enterprises. |
| Analysis date: | April 14, 2026, 21:08:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MD5: | 167EEF71FF6DD690FA9C5EA47BFA5E92 |
| SHA1: | D6655ACBC89311EB1FD6C0AB04D4D2F45DD0541F |
| SHA256: | 7C4C1145E5B9E1C383064E484D60B884B9E25D54C86634CA9D0AC1F6DC936345 |
| SSDEEP: | 3:N8DSLHTiAWDGhcNdNqwrcIBSCGAL+VJhMu2omAGN/MRI6jRIYzTEtQWYMUQt9DE2:2OLNvwrcFCXitNmtN/MRIHTiWhJth7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
0
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
218
TCP/UDP connections
138
DNS requests
114
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4076 | RUXIMICS.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=188&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5336 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3593&FlightIds=&UpdateOfferedDays=344&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%206%20Model%2014%20Stepping%203&sku=48&ActivationChannel=Retail&AttrDataVer=188&IsMDMEnrolled=0&ProcessorCores=4&ProcessorModel=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&TotalPhysicalRAM=4096&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260246&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
4076 | RUXIMICS.exe | GET | 200 | 184.24.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7028 | msedge.exe | GET | 200 | 184.86.251.4:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | US | text | 665 Kb | whitelisted |
7028 | msedge.exe | GET | 200 | 104.16.103.112:443 | https://static.canva.com/web/48c83f65e2484aac.ltr.css | US | text | 495 b | unknown |
7028 | msedge.exe | GET | 200 | 104.16.103.112:443 | https://static.canva.com/web/7ec0857c35bc5ee6.runtime.js | US | binary | 76.4 Kb | unknown |
7028 | msedge.exe | GET | 200 | 104.16.103.112:443 | https://static.canva.com/web/08e648cf7e3cae3b.vendor.js | US | binary | 49.4 Kb | unknown |
7028 | msedge.exe | GET | 200 | 104.16.103.112:443 | https://static.canva.com/web/ae308b157dbe89f4.s4le6a.vendor.js | US | text | 250 Kb | unknown |
7028 | msedge.exe | GET | 200 | 104.16.102.112:443 | https://static.canva.com/web/f8172e2a5199e07f.strings.js | US | binary | 24.3 Kb | unknown |
7028 | msedge.exe | GET | 200 | 104.16.103.112:443 | https://static.canva.com/web/5fa0a8136ddb0aa3.en.js | US | binary | 835 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4076 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5208 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | whitelisted |
7028 | msedge.exe | 104.16.102.112:443 | www.canva.com | CLOUDFLARENET | US | whitelisted |
4076 | RUXIMICS.exe | 184.24.77.15:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7028 | msedge.exe | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5336 | MoUsoCoreWorker.exe | 184.24.77.15:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5208 | svchost.exe | 184.24.77.15:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4076 | RUXIMICS.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.canva.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
static.canva.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
o13855.ingest.sentry.io |
| whitelisted |
chunk-composing.canva.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
4076 | RUXIMICS.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |