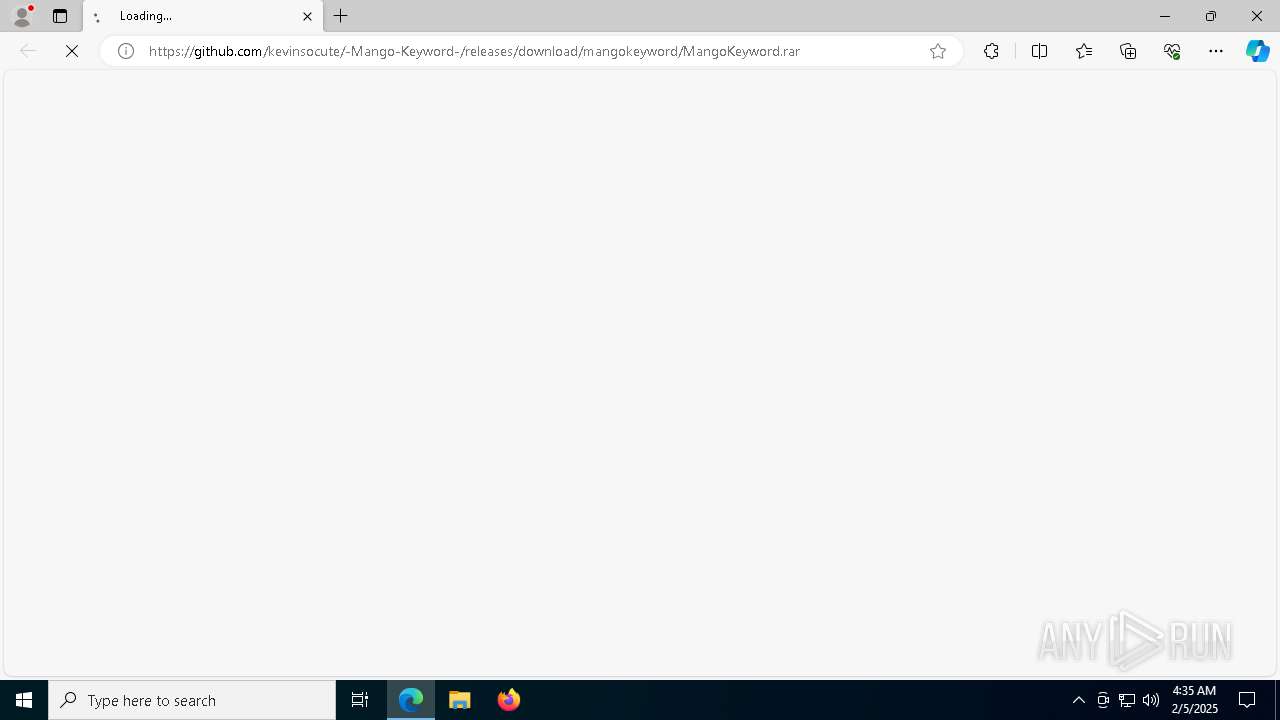
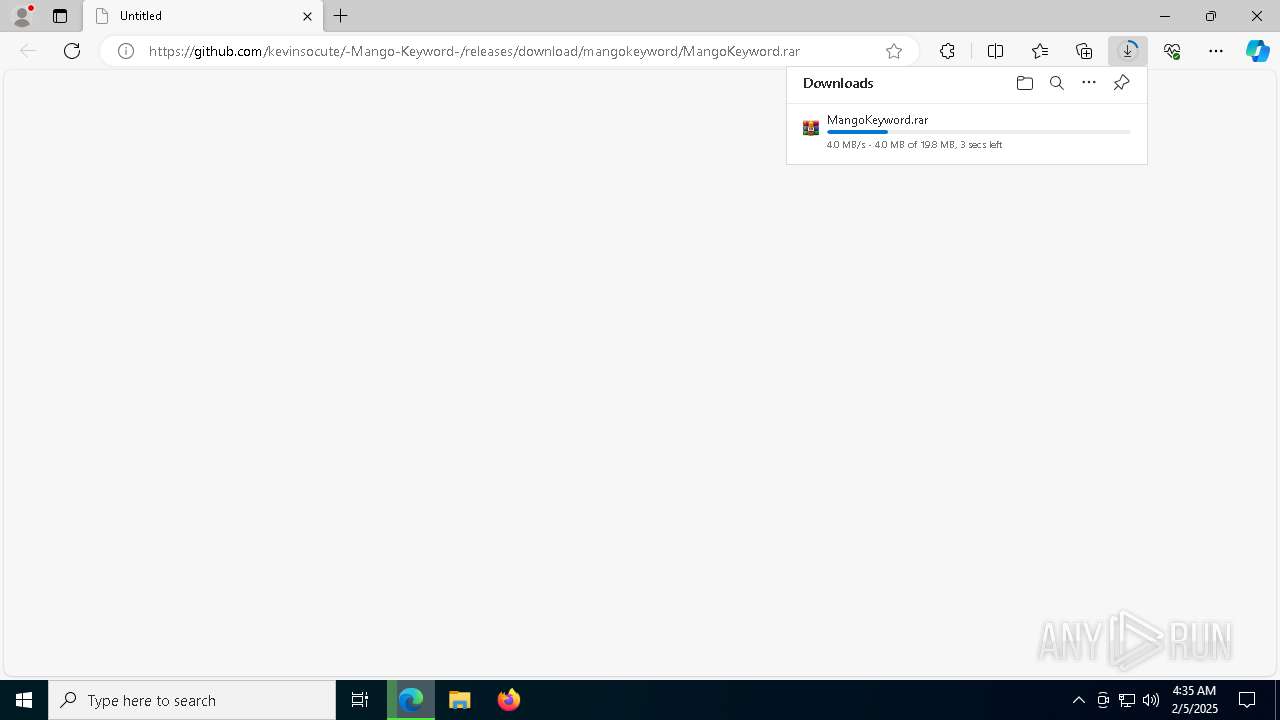
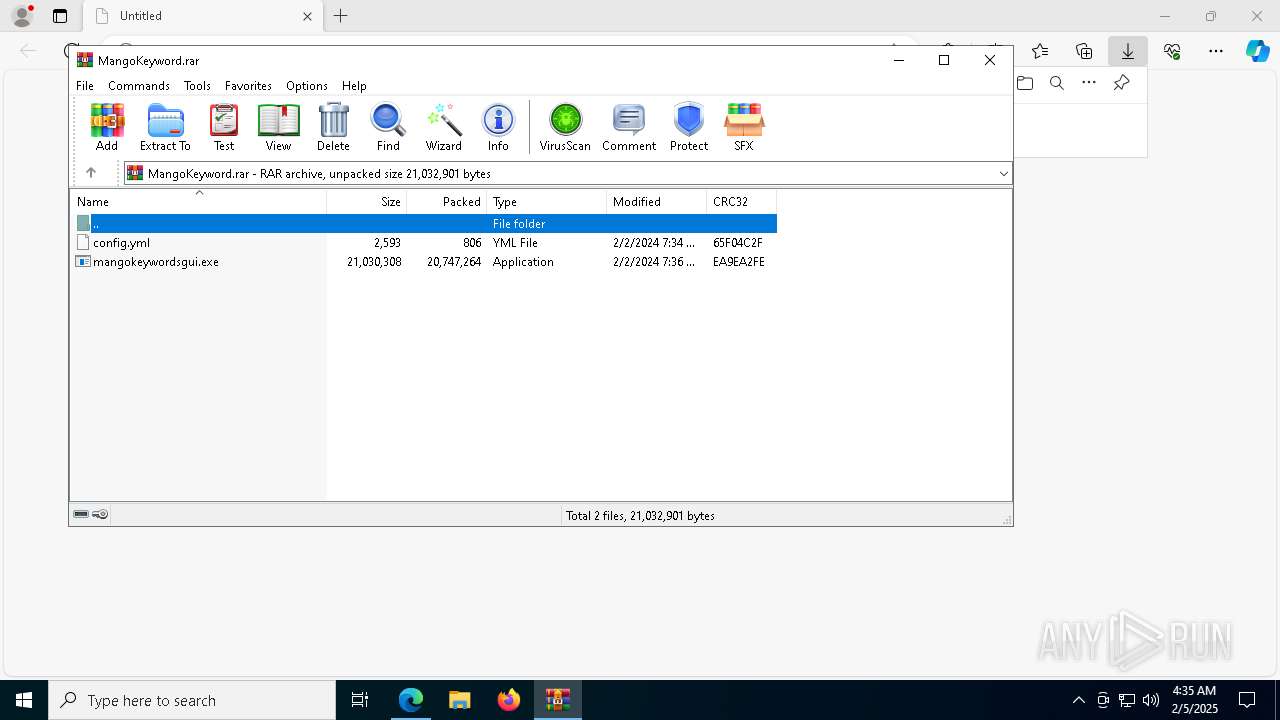
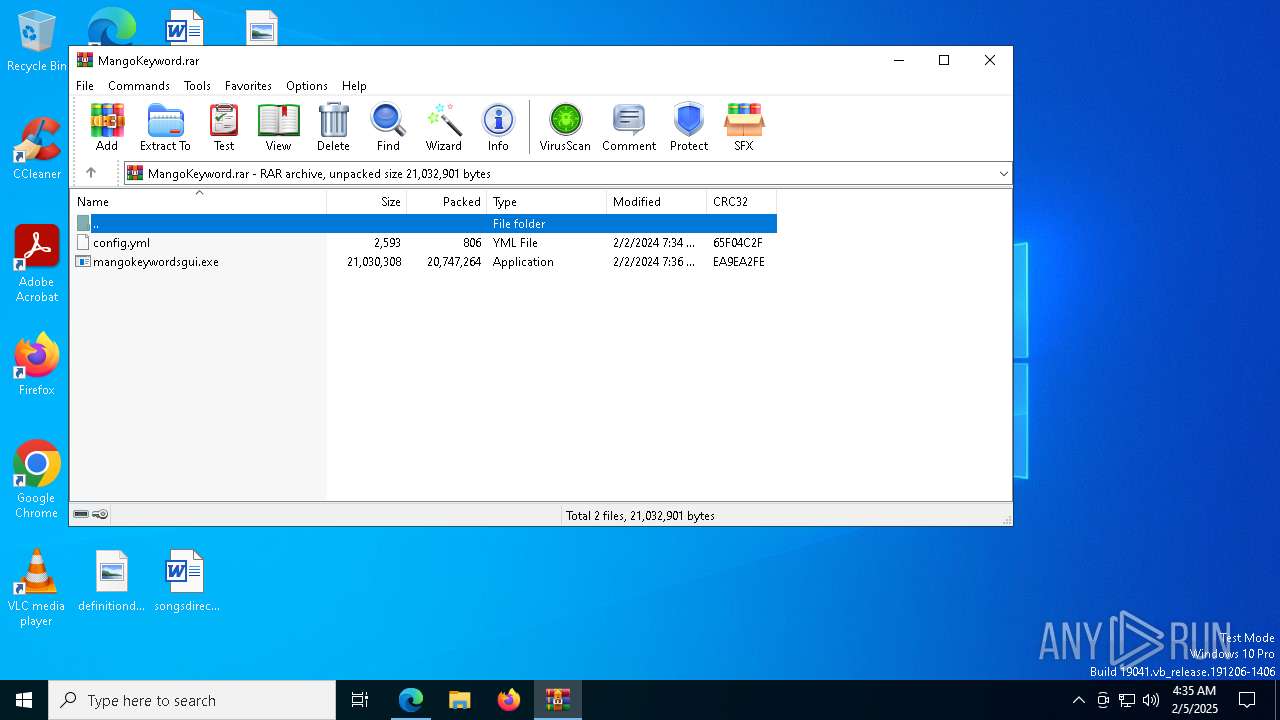
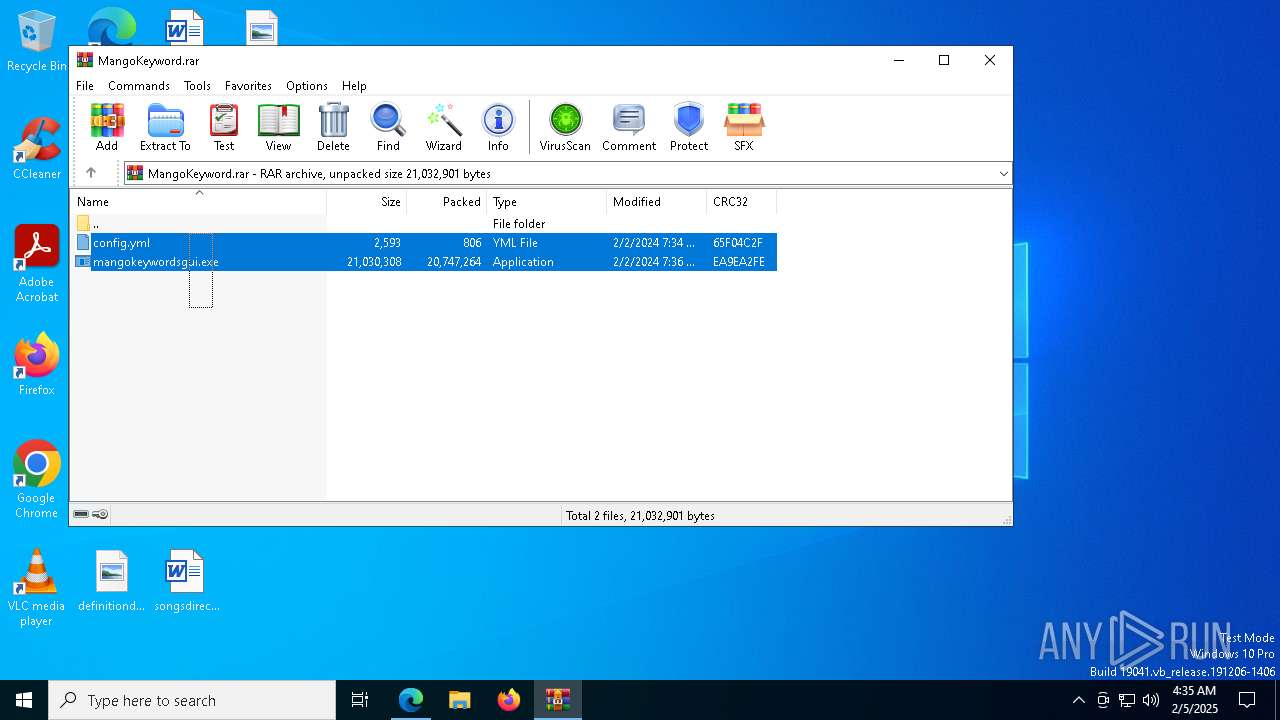
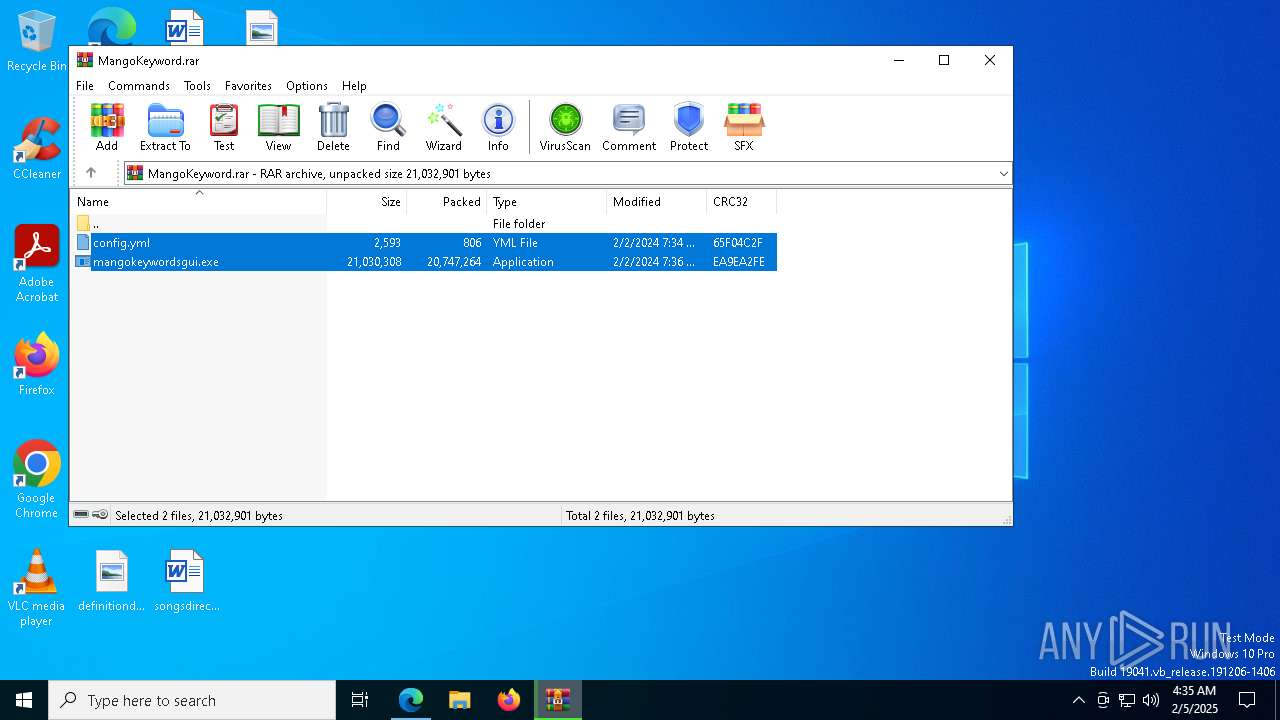
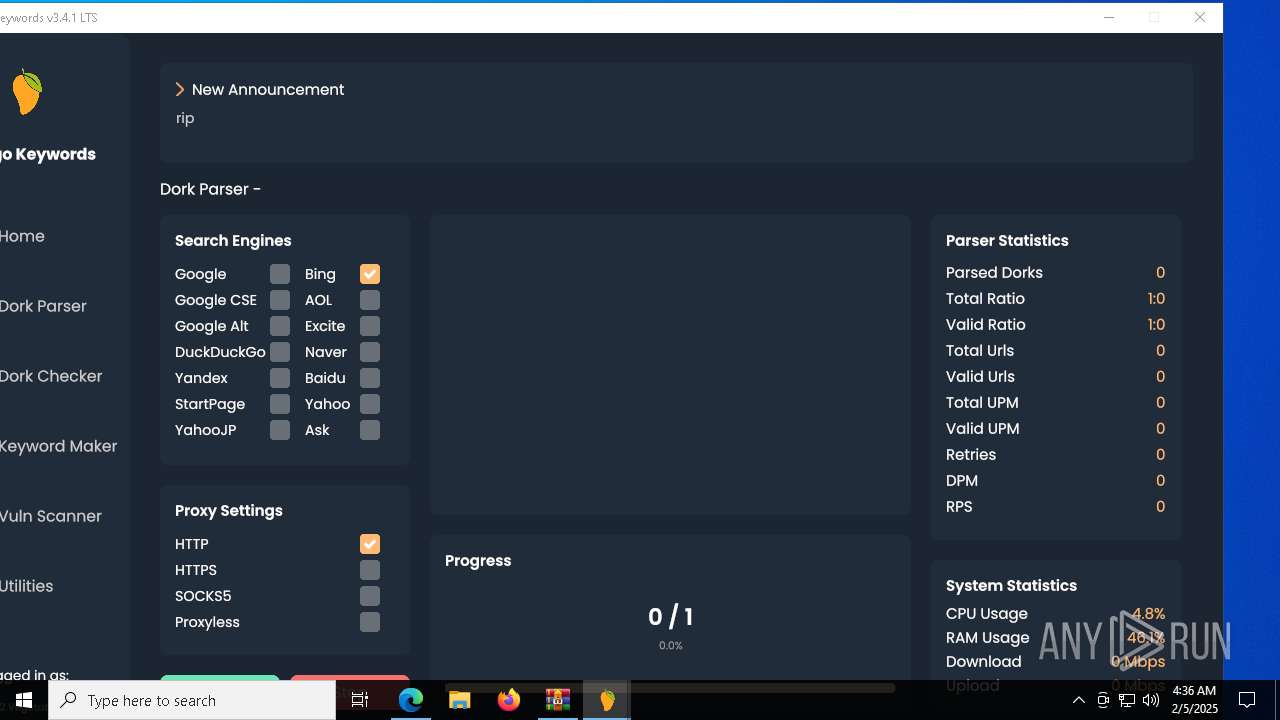
| URL: | https://github.com/kevinsocute/-Mango-Keyword-/releases/download/mangokeyword/MangoKeyword.rar |
| Full analysis: | https://app.any.run/tasks/760173c2-2222-4a17-84d7-632d0a611261 |
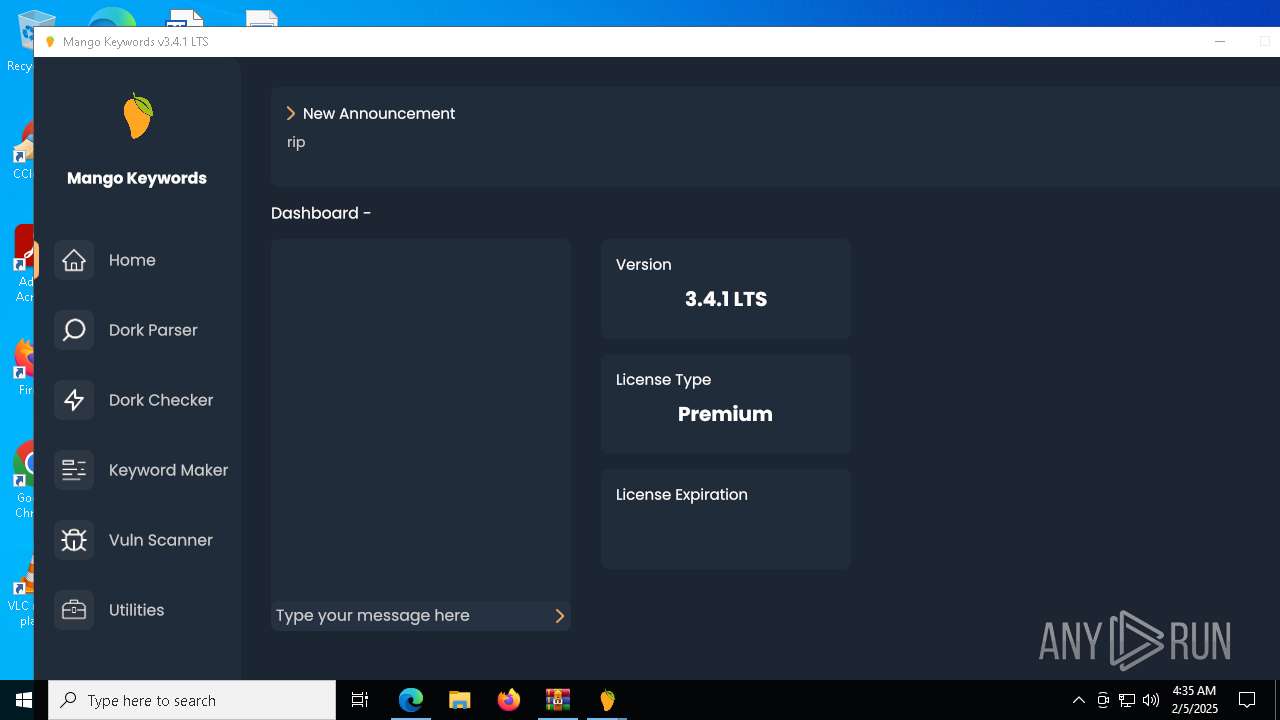
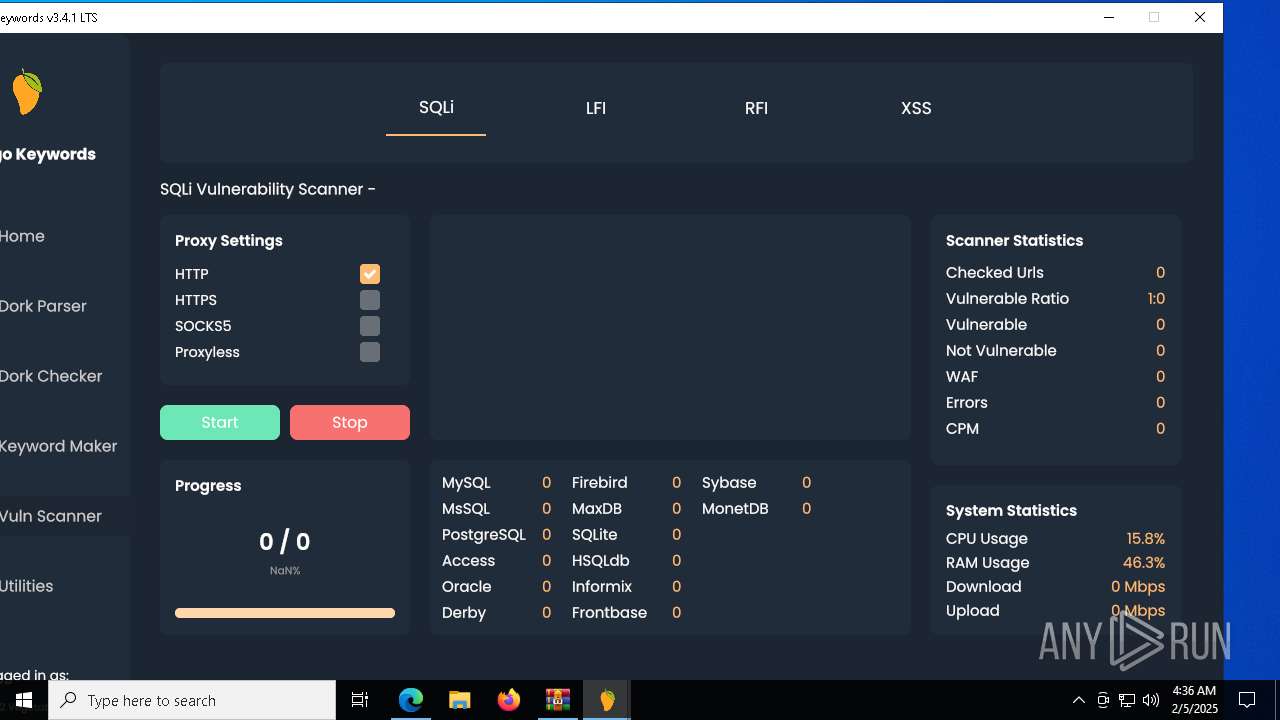
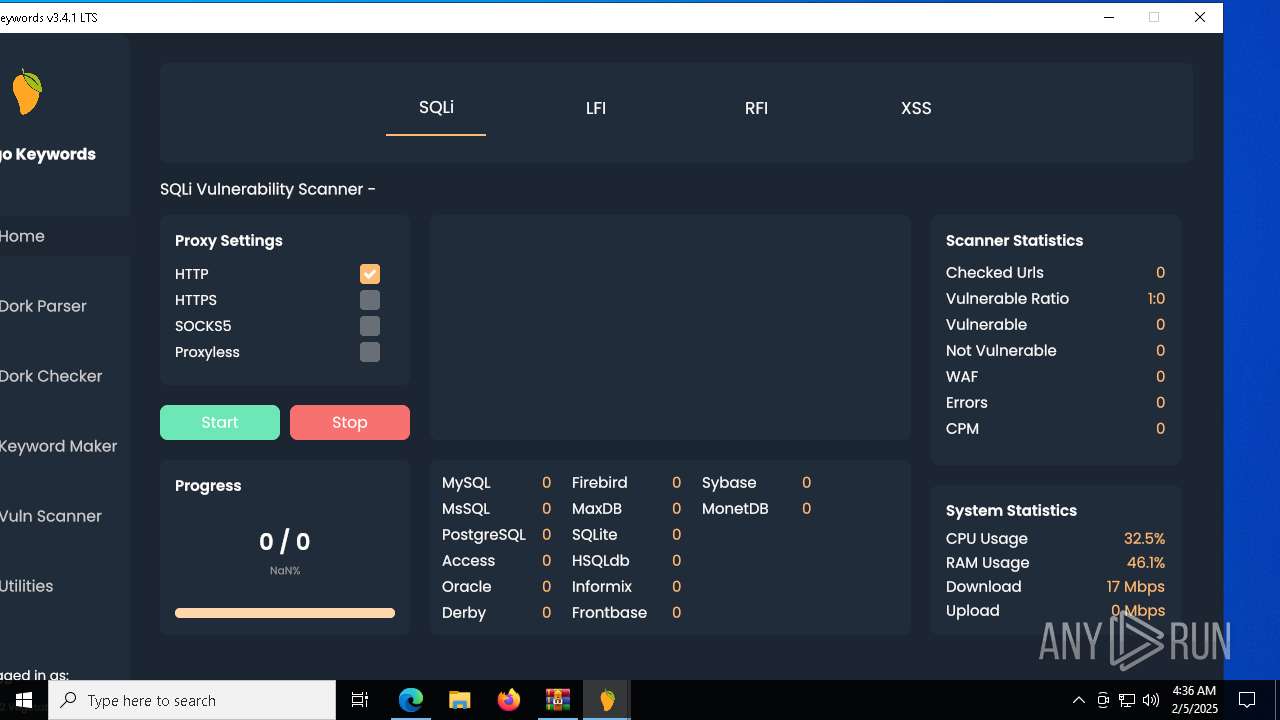
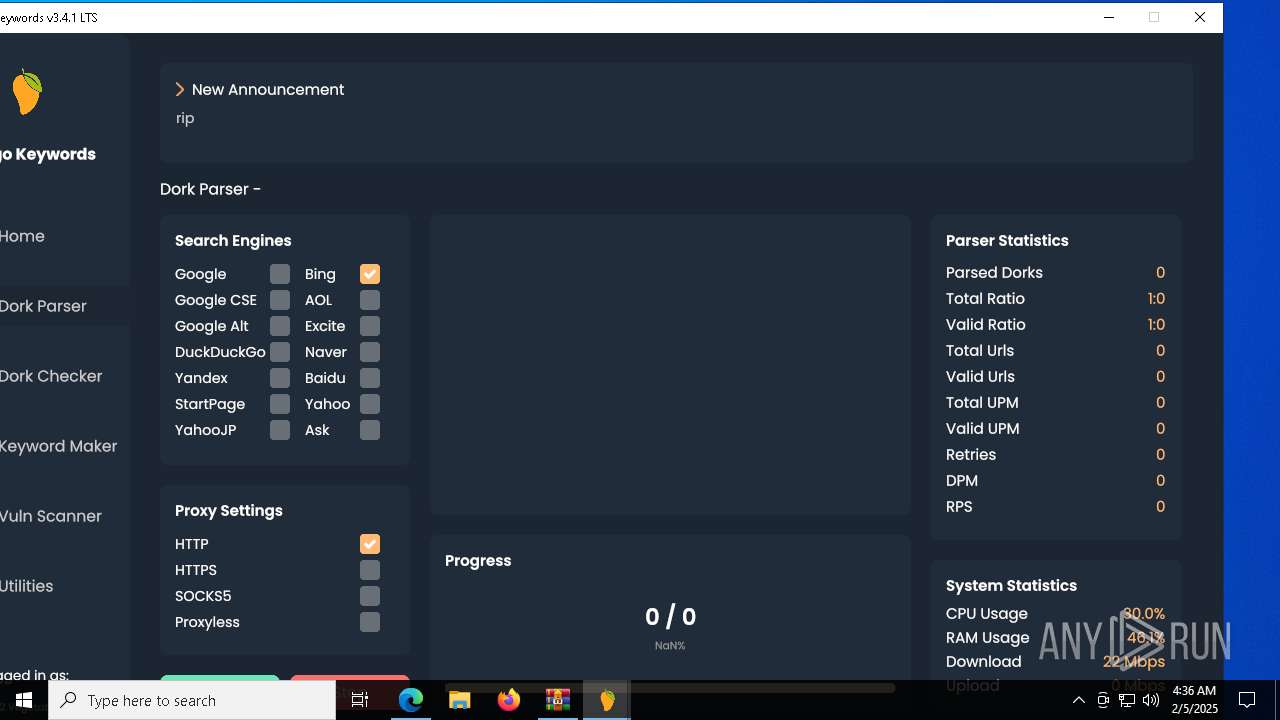
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 05, 2025, 04:35:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6A449E669BBA61F5DEBF64AAFE388B4A |
| SHA1: | A46D48B4A84AEF7B02EA0721987797DA4C3D500A |
| SHA256: | 7BF98F43E0F74B15D9DD8418D1B1A637BF6B50B4E09910BBEF042A2879AC9890 |
| SSDEEP: | 3:N8tEd+AAiKGEAKIZLJ/dAr2kC55M5ig5SYEX:2uorcTZLNXzO5f57+ |
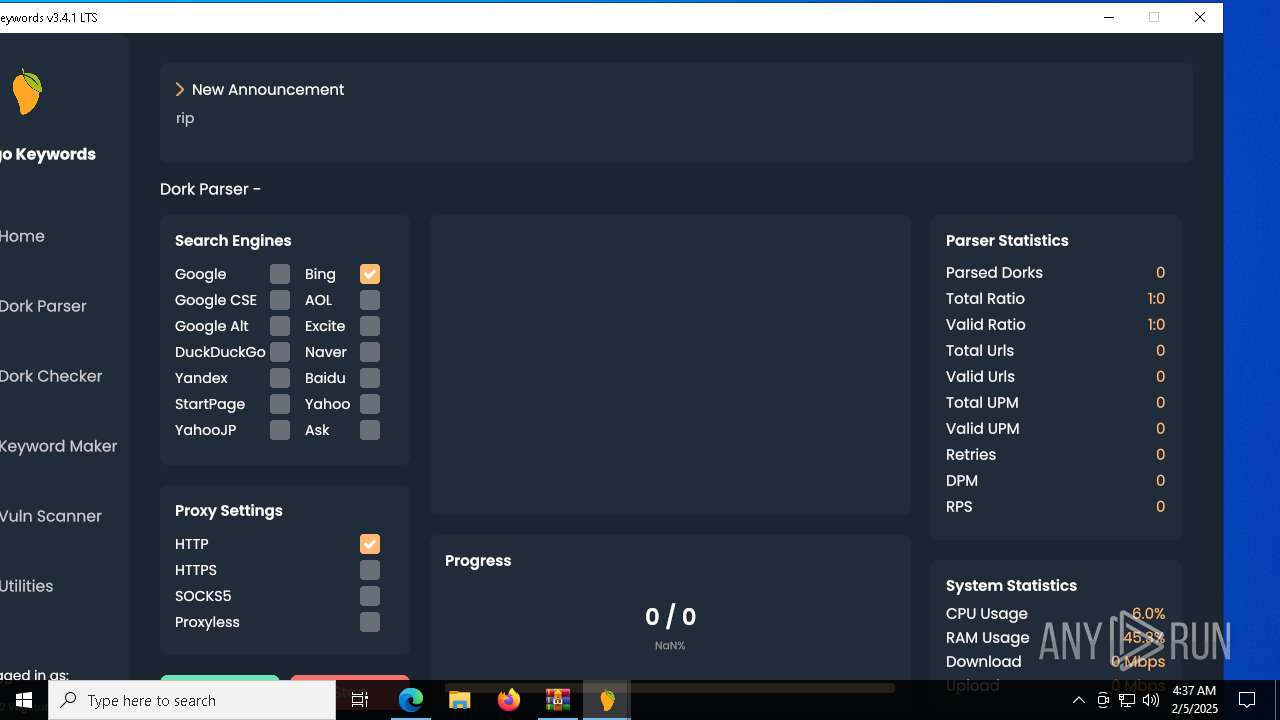
MALICIOUS
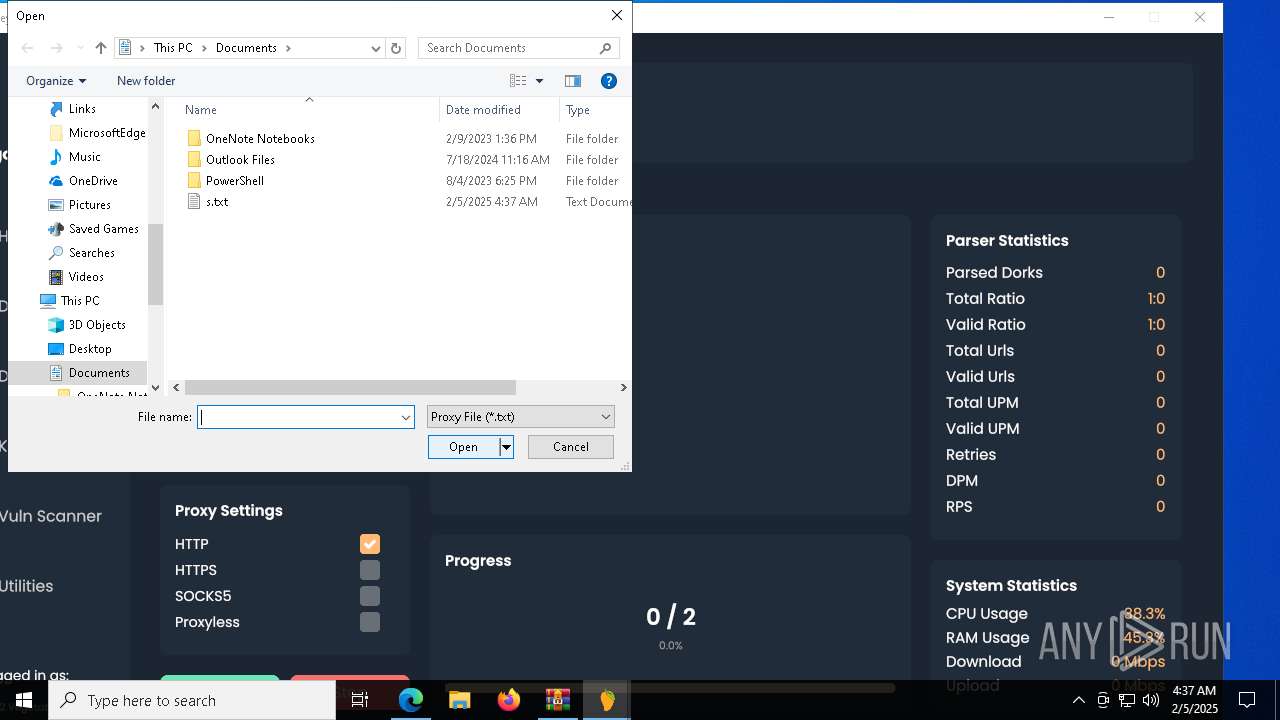
Adds extension to the Windows Defender exclusion list
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 5244)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
SUSPICIOUS
Reads the BIOS version
- mangokeywordsgui.exe (PID: 5240)
- mangokeywordsgui.exe (PID: 6004)
- svchost.exe (PID: 6404)
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
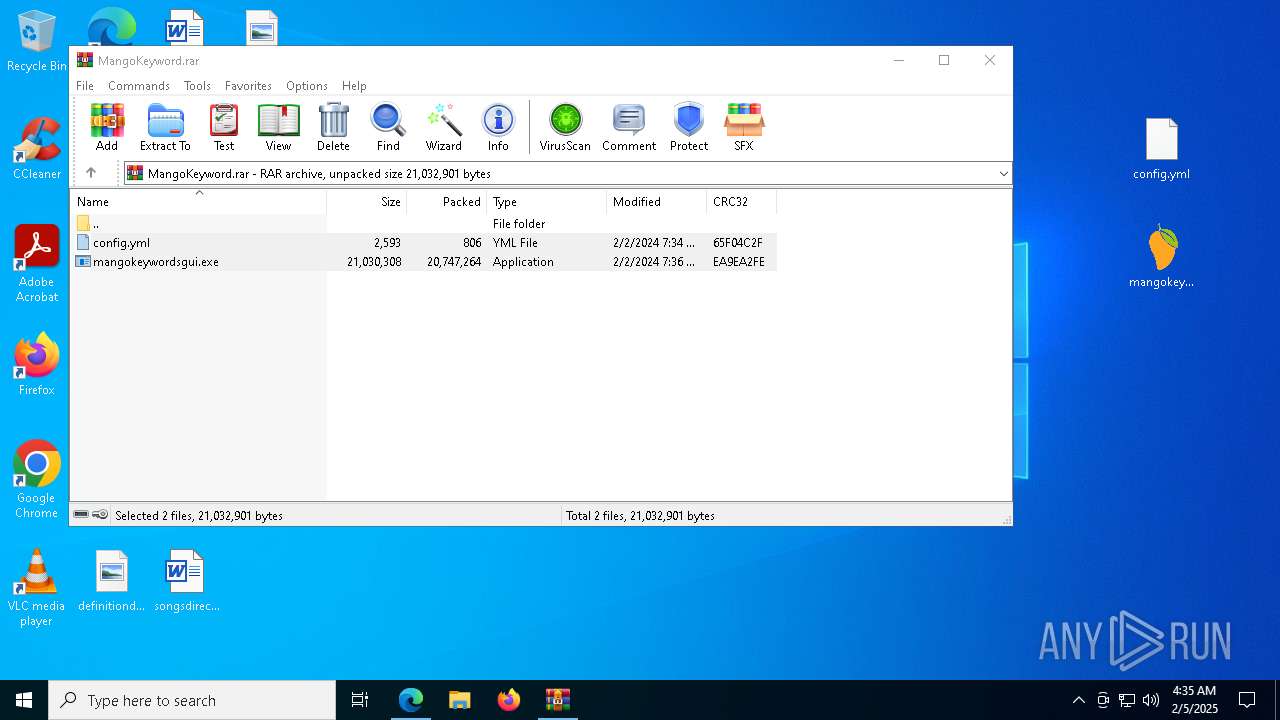
Executable content was dropped or overwritten
- mangokeywordsgui.exe (PID: 5240)
- mangokeywordsgui.exe (PID: 6004)
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Process drops legitimate windows executable
- mangokeywordsgui.exe (PID: 5240)
Process drops python dynamic module
- mangokeywordsgui.exe (PID: 5240)
Application launched itself
- mangokeywordsgui.exe (PID: 5240)
The process drops C-runtime libraries
- mangokeywordsgui.exe (PID: 5240)
Loads Python modules
- mangokeywordsgui.exe (PID: 6004)
The process creates files with name similar to system file names
- mangokeywordsgui.exe (PID: 6004)
Starts CMD.EXE for commands execution
- mangokeywordsgui.exe (PID: 6004)
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 6404)
- mangokeywordsgui.exe (PID: 6160)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1392)
- cmd.exe (PID: 4944)
Starts process via Powershell
- powershell.exe (PID: 8048)
Starts POWERSHELL.EXE for commands execution
- svchost.exe (PID: 6404)
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
The process checks if it is being run in the virtual environment
- mangokeywordsgui.exe (PID: 6160)
Starts SC.EXE for service management
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Manipulates environment variables
- powershell.exe (PID: 7692)
- powershell.exe (PID: 188)
Script adds exclusion extension to Windows Defender
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Script adds exclusion path to Windows Defender
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Stops a currently running service
- sc.exe (PID: 644)
- sc.exe (PID: 6068)
- sc.exe (PID: 8024)
- sc.exe (PID: 1200)
- sc.exe (PID: 7428)
- sc.exe (PID: 7624)
- sc.exe (PID: 3992)
- sc.exe (PID: 3436)
- sc.exe (PID: 5568)
- sc.exe (PID: 4228)
- sc.exe (PID: 7960)
Process uninstalls Windows update
- wusa.exe (PID: 3792)
- wusa.exe (PID: 7192)
Uses powercfg.exe to modify the power settings
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
There is functionality for taking screenshot (YARA)
- mangokeywordsgui.exe (PID: 6160)
Creates a new Windows service
- sc.exe (PID: 7332)
Windows service management via SC.EXE
- sc.exe (PID: 7336)
- sc.exe (PID: 3688)
Executes as Windows Service
- updater.exe (PID: 5640)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 5640)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2192)
Connects to unusual port
- cmd.exe (PID: 2084)
Reads security settings of Internet Explorer
- mangokeywordsgui.exe (PID: 6160)
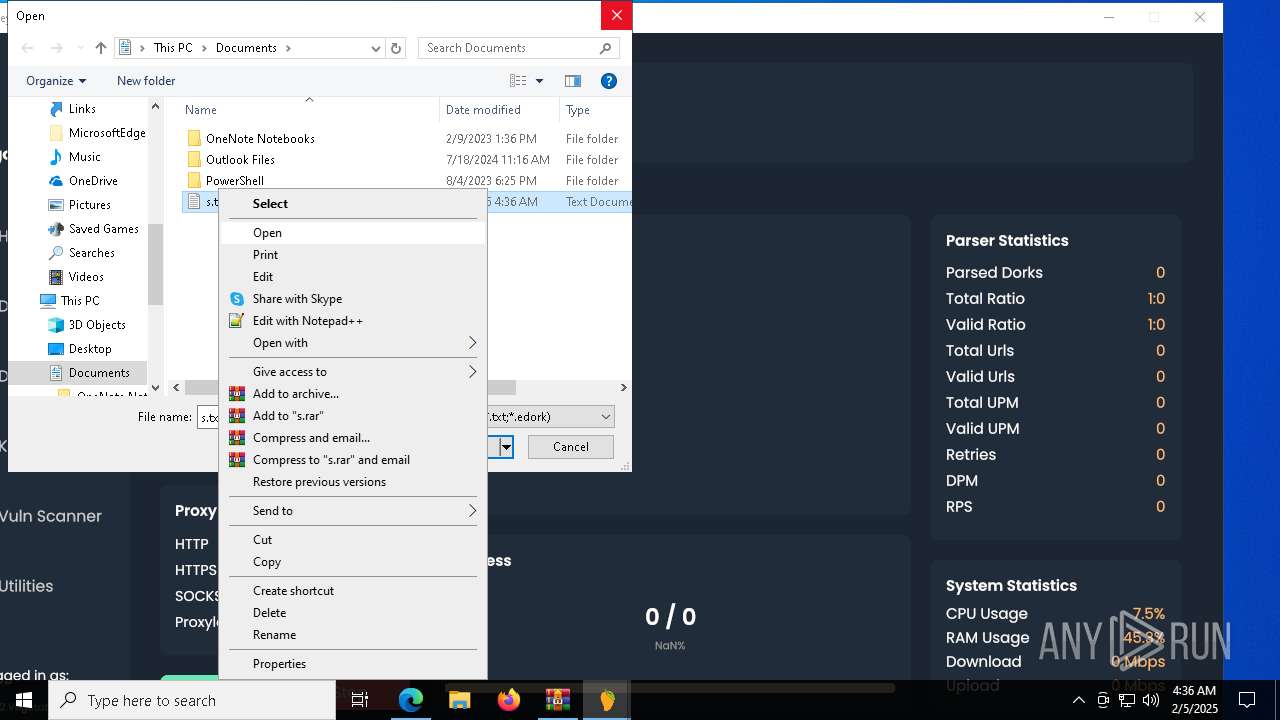
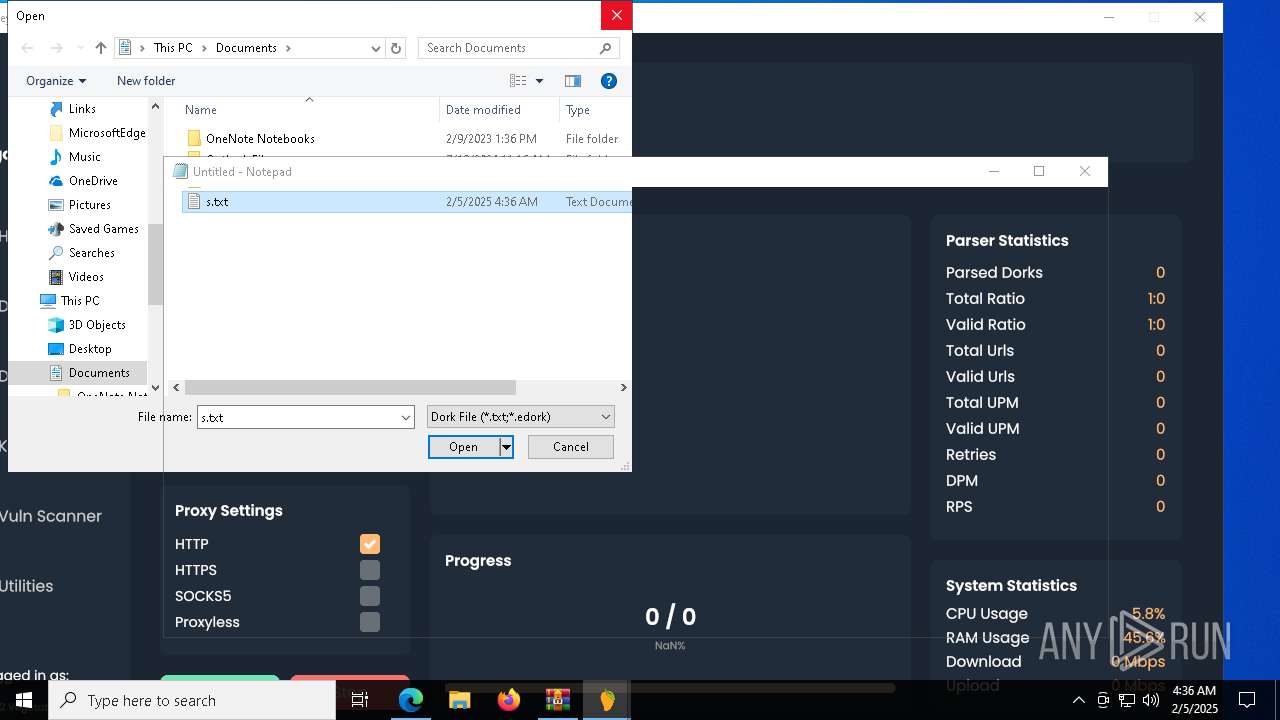
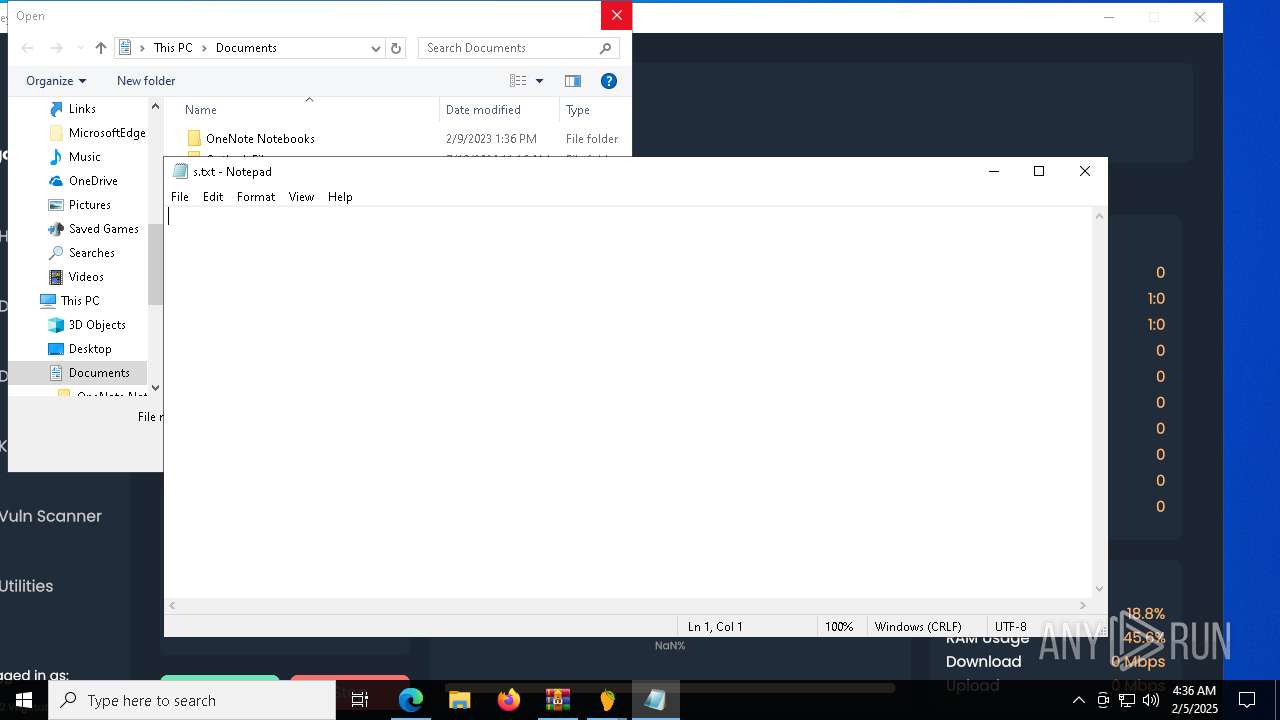
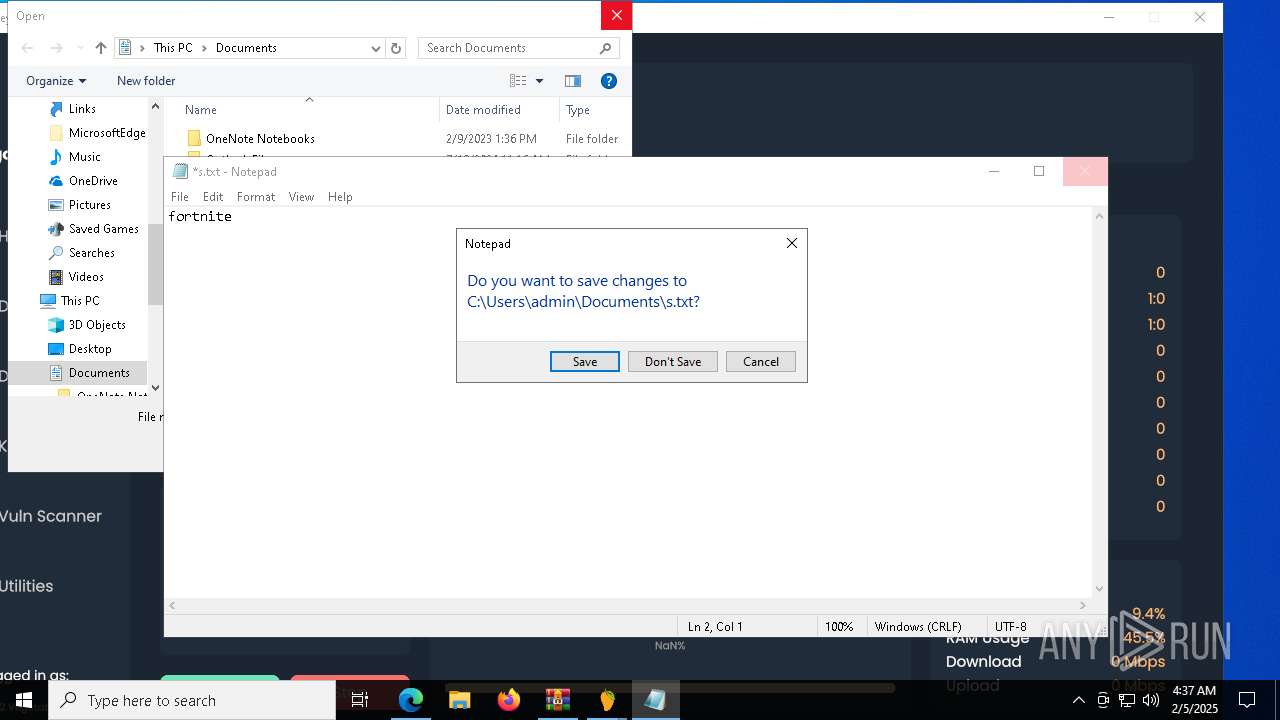
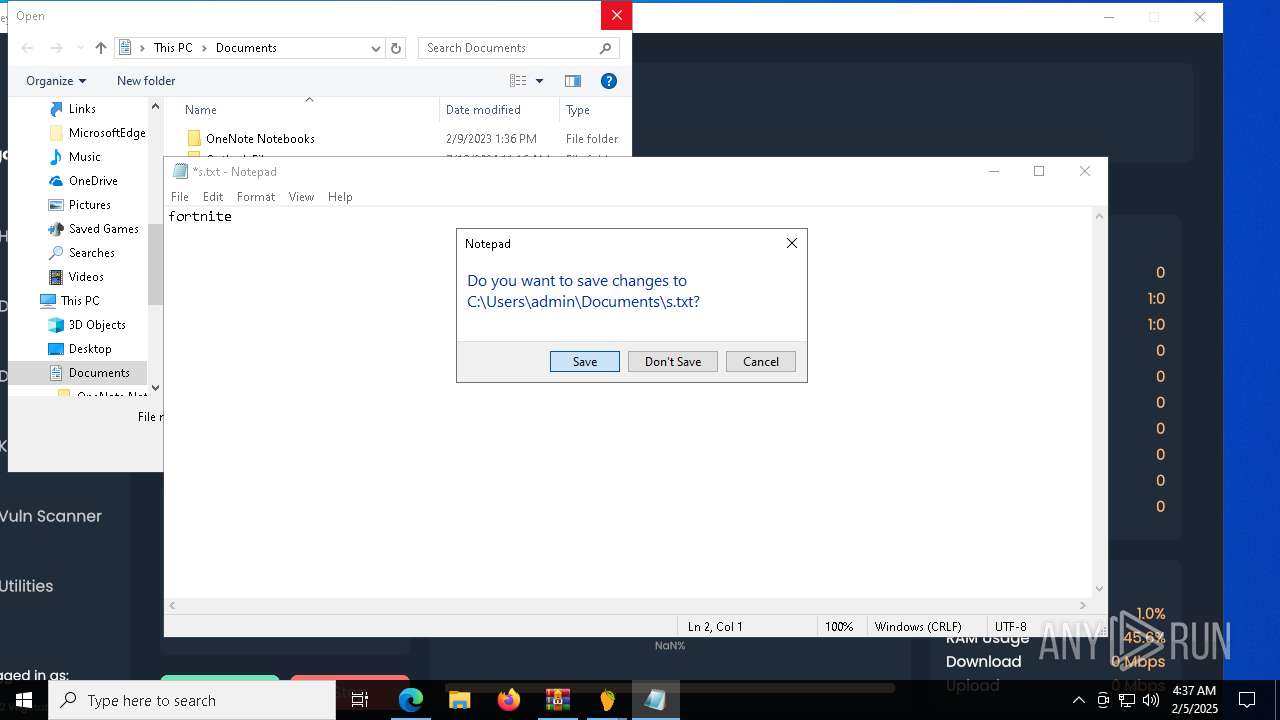
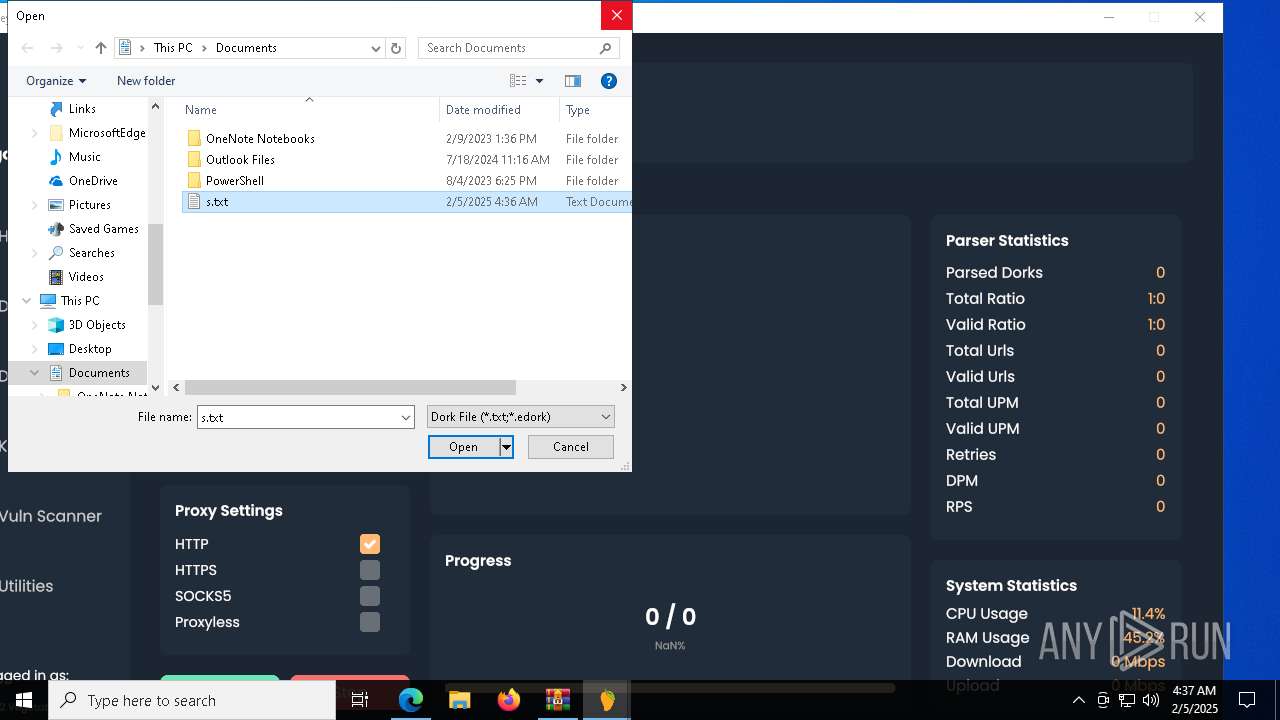
Start notepad (likely ransomware note)
- mangokeywordsgui.exe (PID: 6160)
INFO
Reads the computer name
- identity_helper.exe (PID: 7720)
- mangokeywordsgui.exe (PID: 5240)
- mangokeywordsgui.exe (PID: 6160)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6272)
- mangokeywordsgui.exe (PID: 6160)
Checks supported languages
- identity_helper.exe (PID: 7720)
- mangokeywordsgui.exe (PID: 5240)
- mangokeywordsgui.exe (PID: 6004)
- mangokeywordsgui.exe (PID: 6160)
- svchost.exe (PID: 6404)
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Application launched itself
- msedge.exe (PID: 6272)
Reads Environment values
- identity_helper.exe (PID: 7720)
The sample compiled with english language support
- mangokeywordsgui.exe (PID: 5240)
- msedge.exe (PID: 7712)
Create files in a temporary directory
- mangokeywordsgui.exe (PID: 5240)
- mangokeywordsgui.exe (PID: 6004)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2972)
- msedge.exe (PID: 7712)
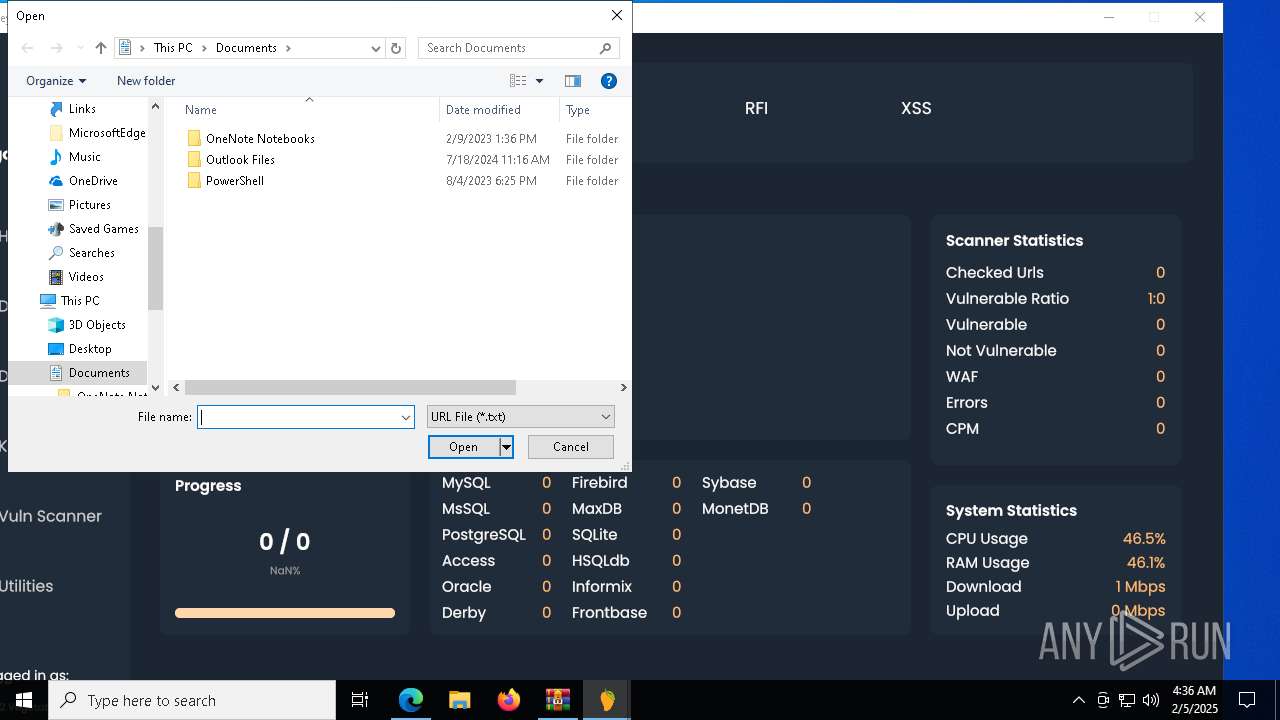
Manual execution by a user
- mangokeywordsgui.exe (PID: 5240)
Reads the machine GUID from the registry
- mangokeywordsgui.exe (PID: 6160)
Creates files or folders in the user directory
- mangokeywordsgui.exe (PID: 6160)
The executable file from the user directory is run by the Powershell process
- svchost.exe (PID: 2324)
Process checks whether UAC notifications are on
- svchost.exe (PID: 2324)
- updater.exe (PID: 5640)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 188)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 188)
Application based on Rust
- mangokeywordsgui.exe (PID: 6160)
Creates files in the program directory
- svchost.exe (PID: 2324)
The sample compiled with japanese language support
- updater.exe (PID: 5640)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6032)
Process checks computer location settings
- mangokeywordsgui.exe (PID: 6160)
Reads the software policy settings
- mangokeywordsgui.exe (PID: 6160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
261
Monitored processes
128
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramData) -ExclusionExtension '.exe' -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4140 --field-trial-handle=2308,i,16251731930959115946,3551566573988463871,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7056 --field-trial-handle=2308,i,16251731930959115946,3551566573988463871,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | C:\WINDOWS\system32\sc.exe stop WaaSMedicSvc | C:\Windows\System32\sc.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | C:\WINDOWS\system32\sc.exe stop wuauserv | C:\Windows\System32\sc.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1392 | C:\WINDOWS\system32\cmd.exe /c "attrib +h C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Windows\SysWOW64\cmd.exe | — | mangokeywordsgui.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4204 --field-trial-handle=2308,i,16251731930959115946,3551566573988463871,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1732 | C:\WINDOWS\system32\cmd.exe /c "START C:\Users\admin\AppData\Local\Temp\mangokeywordsgui.exe" | C:\Windows\SysWOW64\cmd.exe | — | mangokeywordsgui.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 916
Read events
42 725
Write events
179
Delete events
12
Modification events
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 918366EFF38B2F00 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F7437BEFF38B2F00 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590672 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C35B2E53-04B9-4754-81F0-720ECFA9A58F} | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590672 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E327733C-D2A3-4A43-AC30-425A604F99D1} | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC94AAEFF38B2F00 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
24
Suspicious files
499
Text files
110
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1357b8.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1357b8.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1357c8.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1357c8.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1357d7.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
77
DNS requests
70
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7992 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6188 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7992 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6632 | msedge.exe | GET | 200 | 146.75.118.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1739203880&P2=404&P3=2&P4=YRxQAKqa7ZjWHcXnTaSYv7db55zRZ8ttb2bpEsIA1BOjW%2b13UVhZfXrPwQHyUqMeQ44TbbzJ024AnQtxhl6GOQ%3d%3d | unknown | — | — | whitelisted |
6632 | msedge.exe | GET | 200 | 146.75.118.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739203878&P2=404&P3=2&P4=KHLS7vygZiAnZdzxzm0kthGqJqmM2%2bMAd%2fEIQPDFQVizqH2Py2kDy6p%2buszisXPEKtDtRfnPaVlkAXeQLOwgmQ%3d%3d | unknown | — | — | whitelisted |
6632 | msedge.exe | GET | 200 | 146.75.118.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739203878&P2=404&P3=2&P4=nycVIdBlPqEmTGsJZVWaLCPyBPx5G8OWBiU7kKzecSt3JveeVNJek9tz3suvvH9i925got74rvf5zvCc8C4qOg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2632 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.78.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6632 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6272 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER Observed DNS Query to Cryptocurrency Mining Pool Domain (xmr .2miners .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2192 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |